| File name: | AutoClicker.exe |
| Full analysis: | https://app.any.run/tasks/f0b0c843-fb05-472e-b384-cdd327f4379b |
| Verdict: | Malicious activity |
| Analysis date: | June 16, 2019, 05:35:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 7ECFC8CD7455DD9998F7DAD88F2A8A9D |
| SHA1: | 1751D9389ADB1E7187AFA4938A3559E58739DCE6 |
| SHA256: | 2E67D5E7D96AEC62A9DDA4C0259167A44908AF863C2B3AF2A019723205ABBA9E |
| SSDEEP: | 12288:GaWzgMg7v3qnCiWErQohh0F49CJ8lnybQg9BFg9UmTRHlM:BaHMv6CGrjBnybQg+mmhG |
MALICIOUS
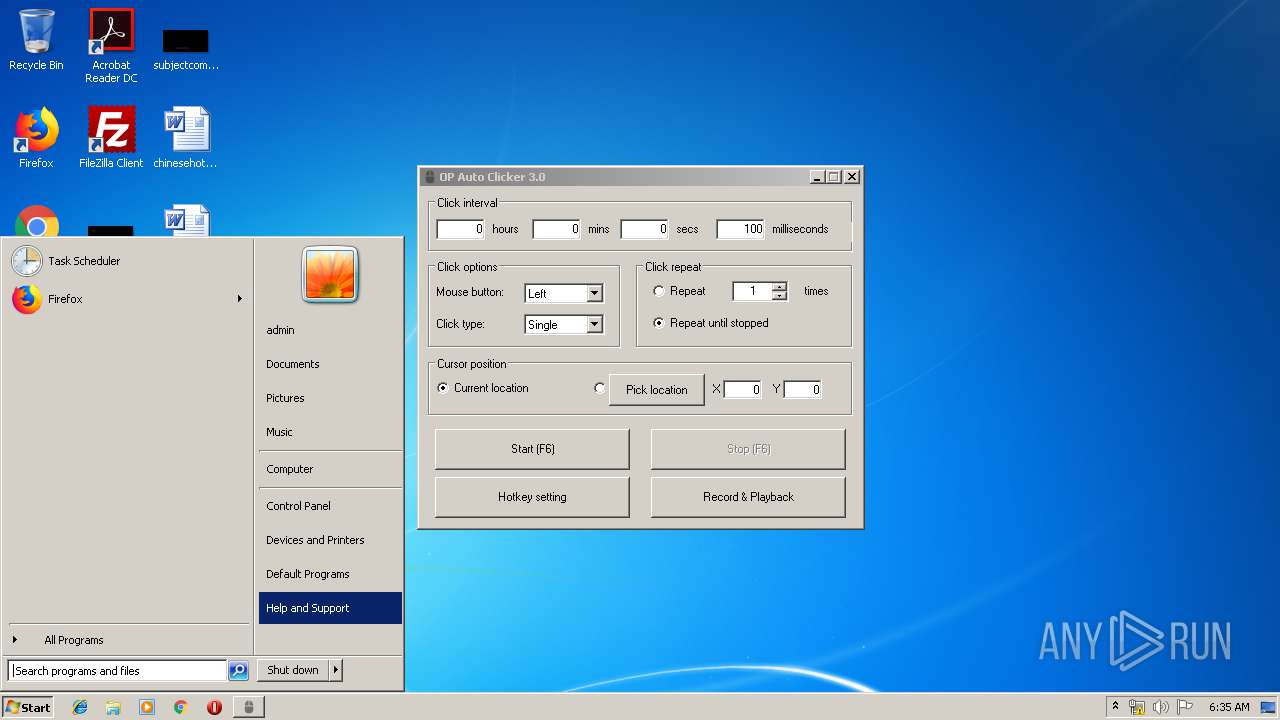
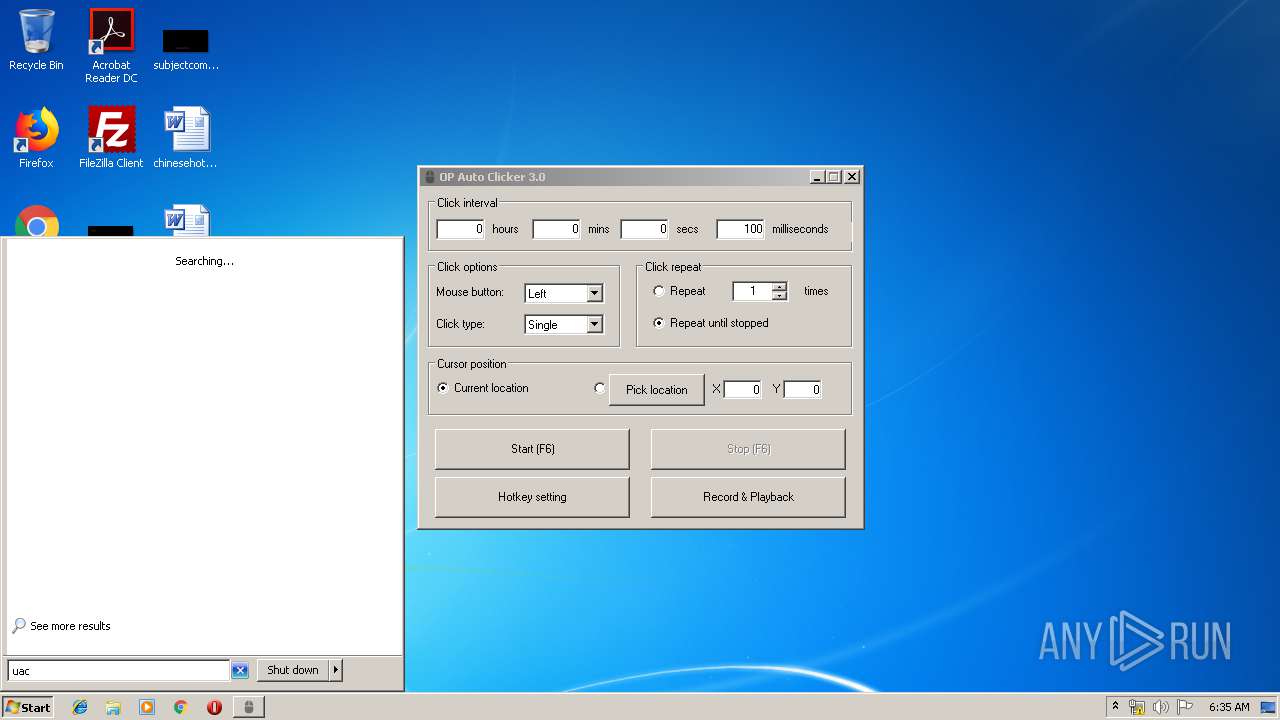
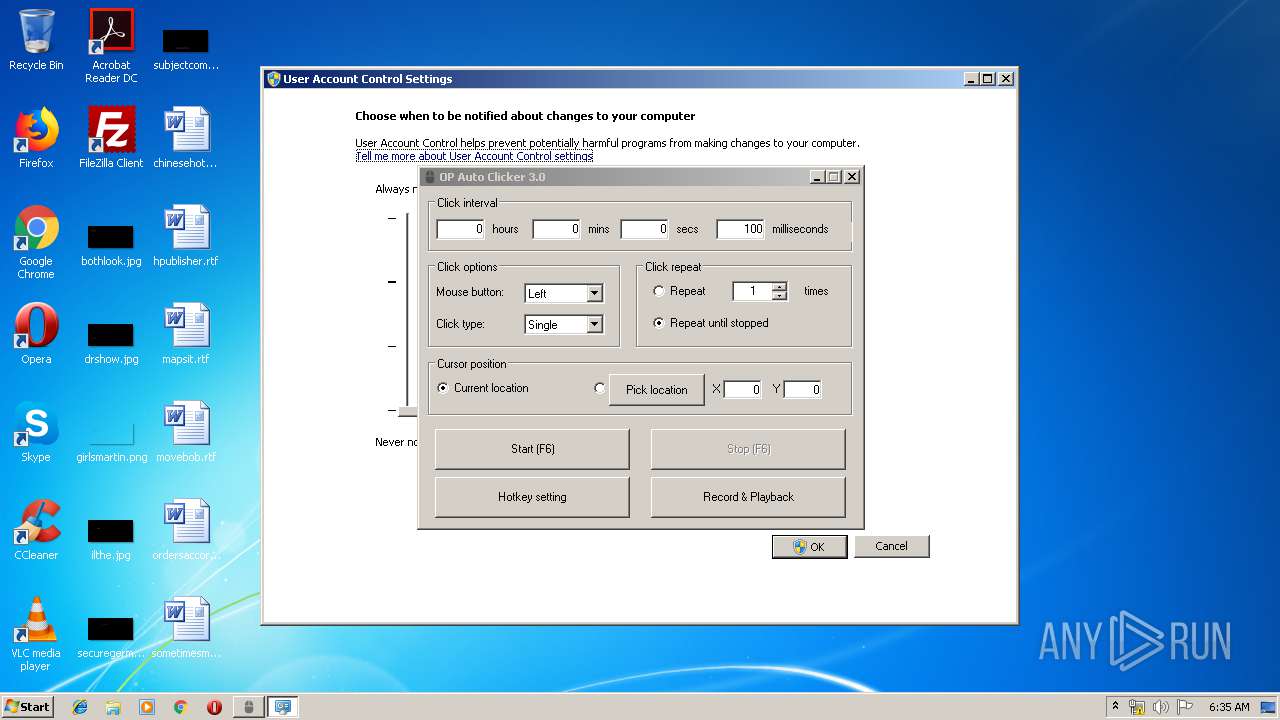
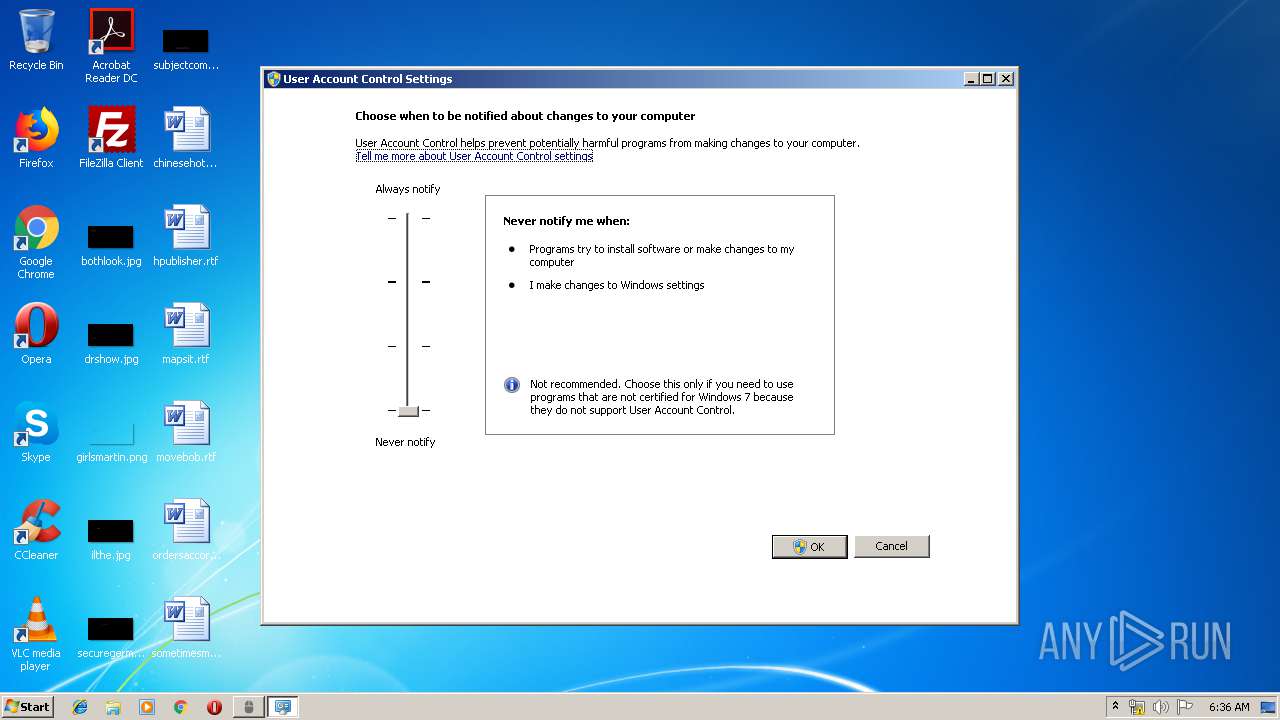
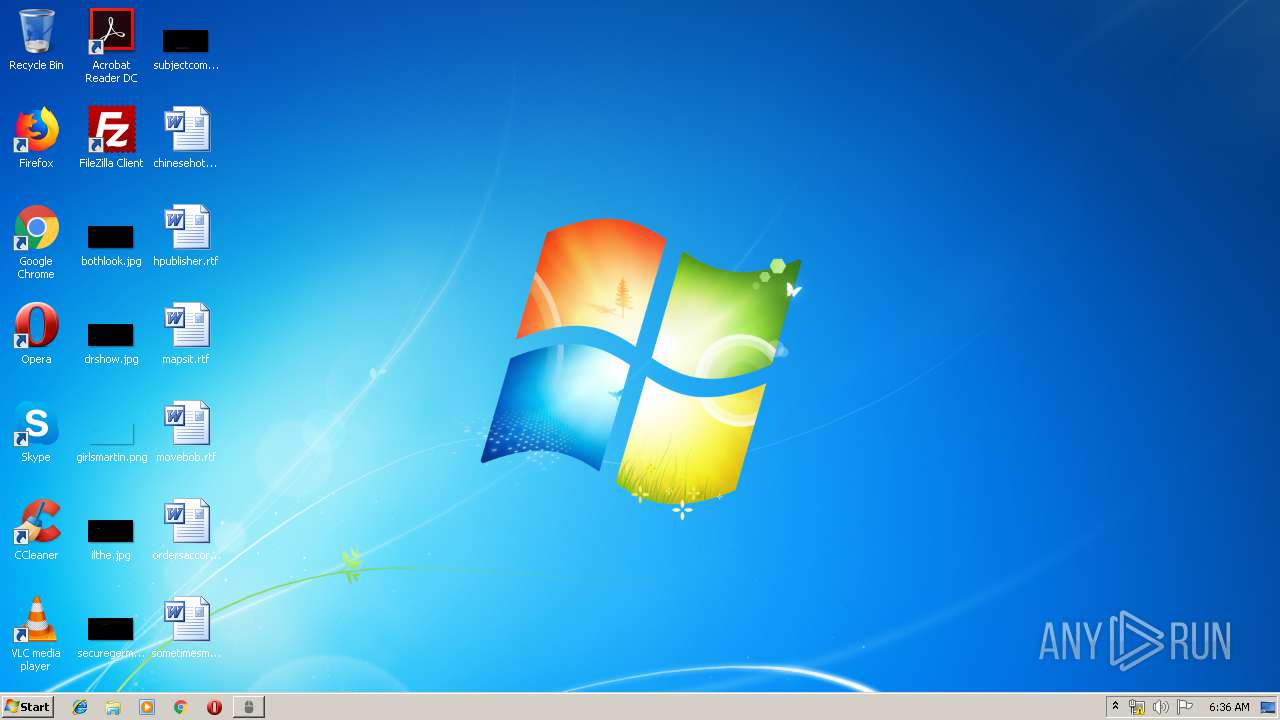
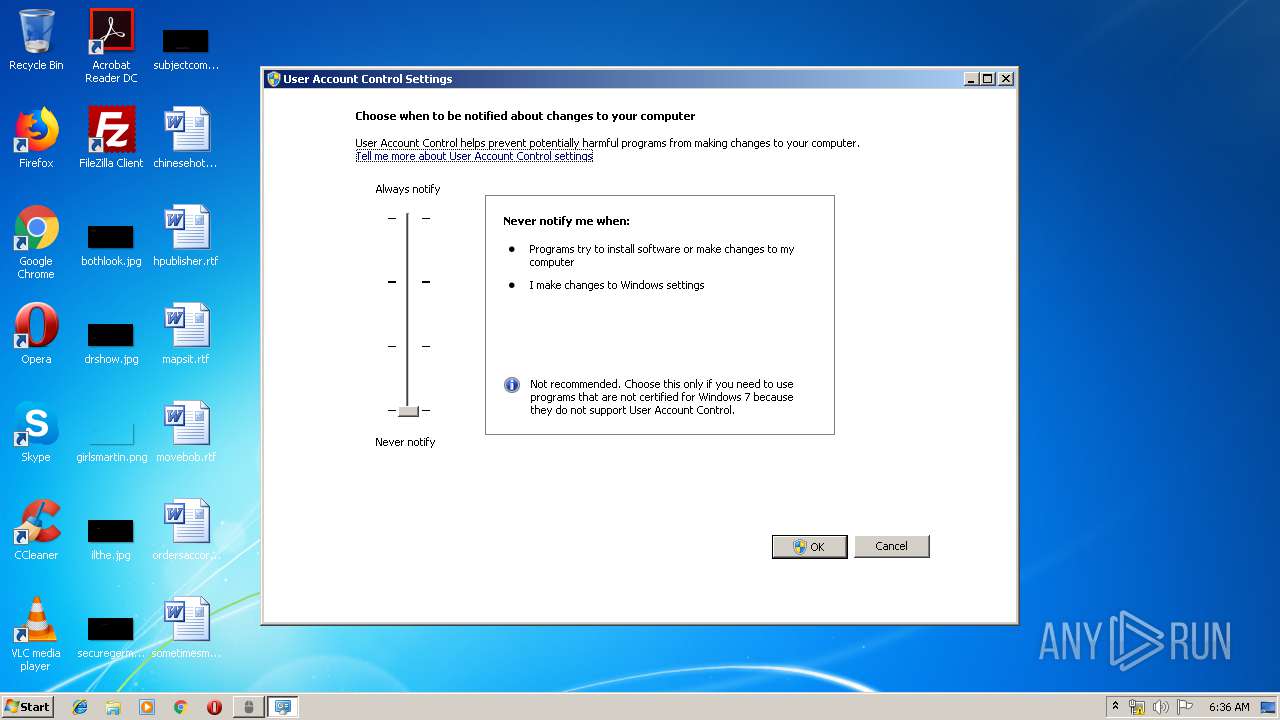
UAC/LUA settings modification
- DllHost.exe (PID: 3104)
- DllHost.exe (PID: 124)
SUSPICIOUS
Executed via COM
- DllHost.exe (PID: 1512)
- DllHost.exe (PID: 3104)
- DllHost.exe (PID: 124)
- DllHost.exe (PID: 2152)
INFO
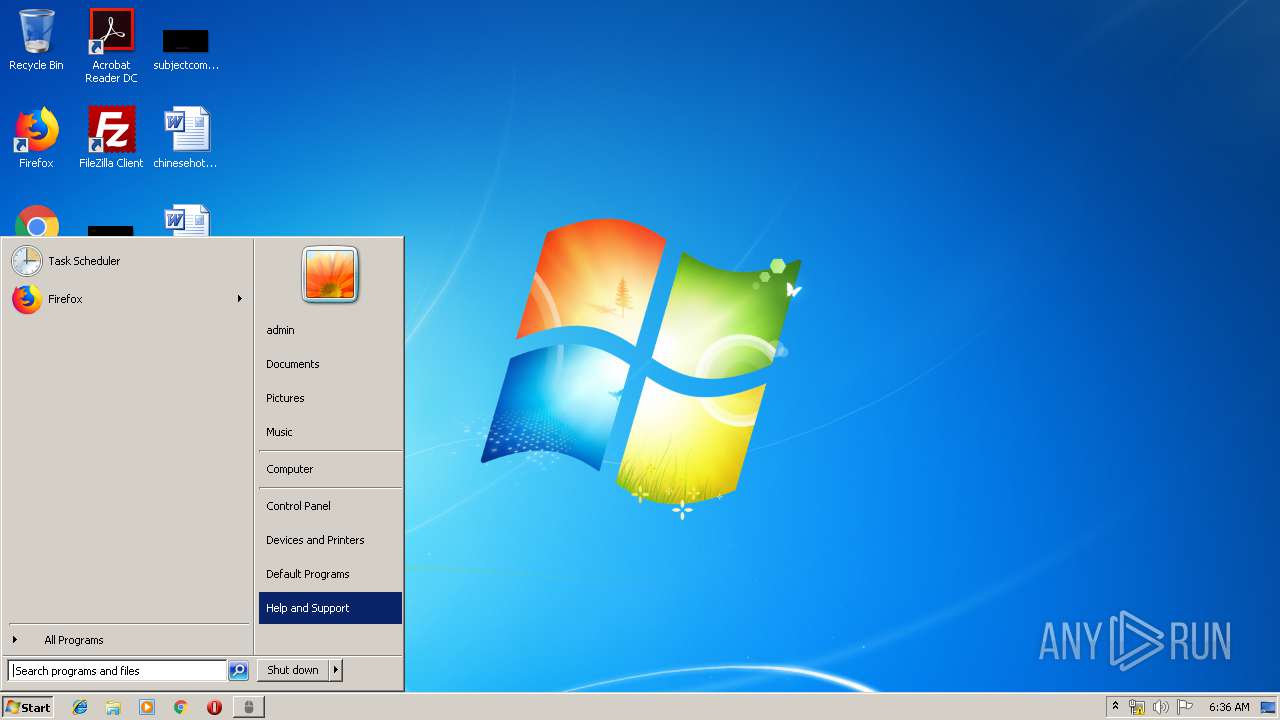
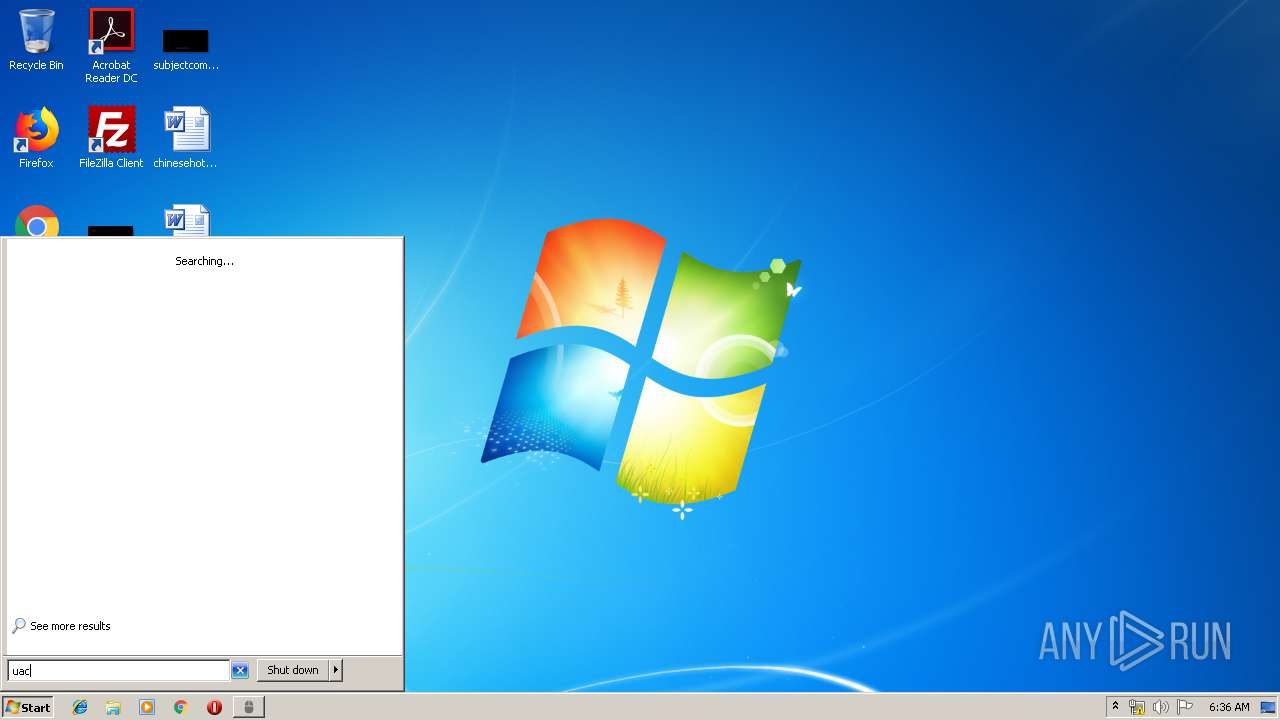
Manual execution by user
- UserAccountControlSettings.exe (PID: 2164)
- UserAccountControlSettings.exe (PID: 3628)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:03:14 21:01:24+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 524800 |
| InitializedDataSize: | 126976 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x16310 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.0.0.0 |
| ProductVersionNumber: | 3.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Comments: | www.opautoclicker.com |
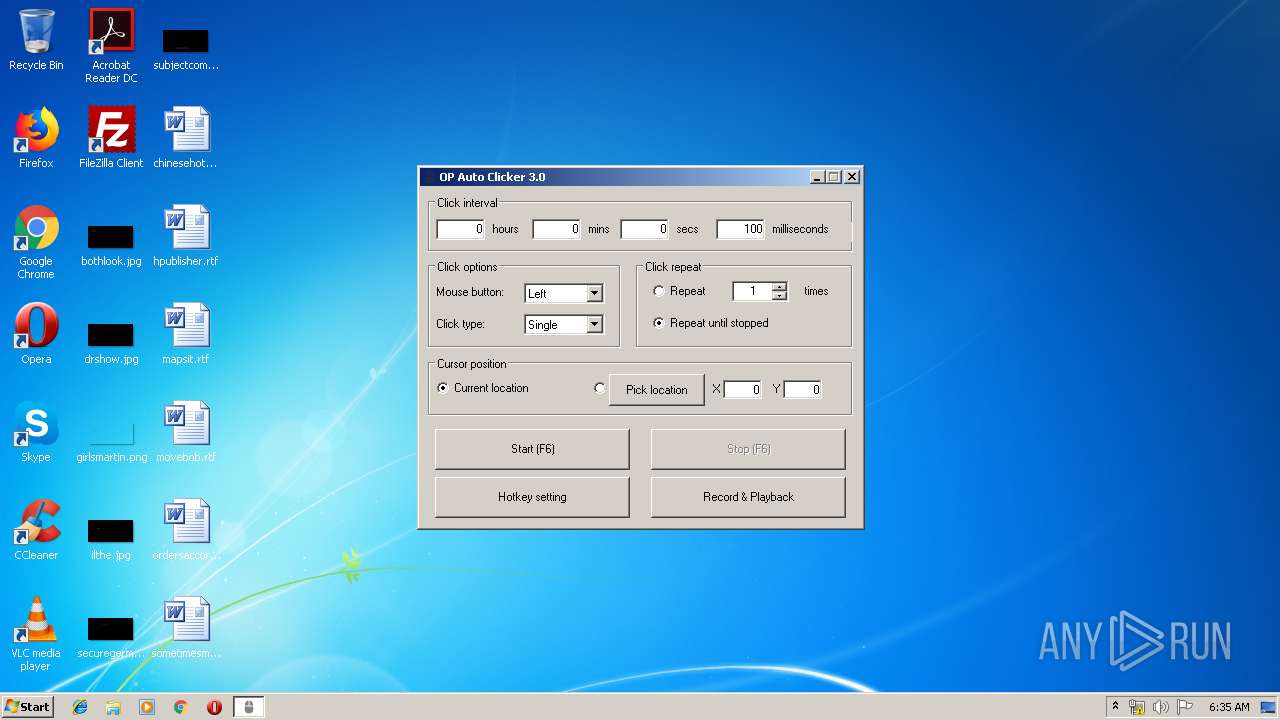
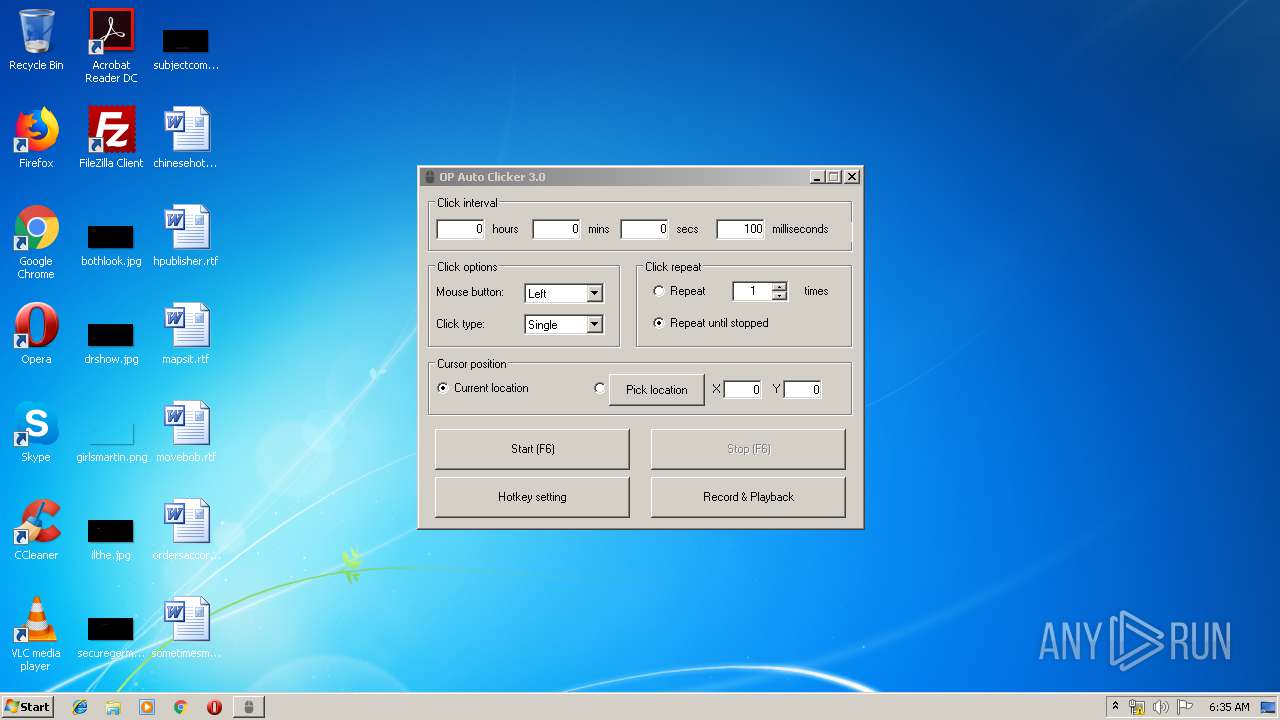
| FileDescription: | OP Auto Clicker |
| FileVersion: | 3 |
| LegalCopyright: | www.opautoclicker.com |
| ProductName: | OP Auto Clicker |
| ProductVersion: | 3 |
Total processes
50
Monitored processes
9
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 124 | C:\Windows\system32\DllHost.exe /Processid:{EA2C6B24-C590-457B-BAC8-4A0F9B13B5B8} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1512 | C:\Windows\system32\DllHost.exe /Processid:{06C792F8-6212-4F39-BF70-E8C0AC965C23} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2116 | "C:\Users\admin\AppData\Local\Temp\AutoClicker.exe" | C:\Users\admin\AppData\Local\Temp\AutoClicker.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: OP Auto Clicker Exit code: 0 Version: 3.0 Modules
| |||||||||||||||
| 2148 | "C:\Windows\system32\UserAccountControlSettings.exe" /applySettings | C:\Windows\system32\UserAccountControlSettings.exe | DllHost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: UserAccountControlSettings Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2152 | C:\Windows\system32\DllHost.exe /Processid:{06C792F8-6212-4F39-BF70-E8C0AC965C23} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2164 | "C:\Windows\system32\UserAccountControlSettings.exe" | C:\Windows\system32\UserAccountControlSettings.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: UserAccountControlSettings Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3104 | C:\Windows\system32\DllHost.exe /Processid:{EA2C6B24-C590-457B-BAC8-4A0F9B13B5B8} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3536 | "C:\Windows\system32\UserAccountControlSettings.exe" /applySettings | C:\Windows\system32\UserAccountControlSettings.exe | DllHost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: UserAccountControlSettings Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3628 | "C:\Windows\system32\UserAccountControlSettings.exe" | C:\Windows\system32\UserAccountControlSettings.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: UserAccountControlSettings Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
102
Read events
88
Write events
14
Delete events
0
Modification events
| (PID) Process: | (1512) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1512) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3104) DllHost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | EnableLUA |
Value: 0 | |||
| (PID) Process: | (3104) DllHost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | ConsentPromptBehaviorAdmin |
Value: 0 | |||
| (PID) Process: | (3104) DllHost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | PromptOnSecureDesktop |
Value: 0 | |||
| (PID) Process: | (2152) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2152) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (124) DllHost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | EnableLUA |
Value: 1 | |||
| (PID) Process: | (124) DllHost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | ConsentPromptBehaviorAdmin |
Value: 2 | |||
| (PID) Process: | (124) DllHost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | PromptOnSecureDesktop |
Value: 1 | |||
Executable files
0
Suspicious files
0
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2116 | AutoClicker.exe | C:\Users\admin\AppData\Local\Temp\uuehsle | — | |
MD5:— | SHA256:— | |||
| 2116 | AutoClicker.exe | C:\Users\admin\AppData\Local\Temp\ACLib\record.ico | image | |
MD5:1111E06679F96FF28C1E229B06CE7B41 | SHA256:59D5E9106E907FA61A560294A51C14ABCDE024FDD690E41A7F4D6C88DB7287A6 | |||
| 2116 | AutoClicker.exe | C:\Users\admin\AppData\Local\Temp\ACLib\playback.ico | image | |
MD5:A20254EA7F9EF810C1681FA314EDAA28 | SHA256:5375290E66A20BFF81FB4D80346756F2D442184789681297CD1B84446A3FE80D | |||
| 2116 | AutoClicker.exe | C:\Users\admin\AppData\Local\Temp\ACLib\stop.ico | image | |
MD5:7824CEFAD2522BE614AE5B7BDBF88339 | SHA256:9E869F60EA0A0DE06C7D562FF56D1AC53C534849C919E4B12344E73513649483 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report