| File name: | SHS-08312024-120025-7-1ff-22621.1.amd64fre.ni_release.220506-1250.etl |
| Full analysis: | https://app.any.run/tasks/840faecf-e813-41ae-8304-ad1a0e3e2231 |
| Verdict: | Malicious activity |
| Analysis date: | September 04, 2024, 15:22:11 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/octet-stream |
| File info: | data |
| MD5: | B2C8598AA9980DFF3E19F68D8A851790 |
| SHA1: | AC9FCCFDEBCB06D3D94AAB4FE0669DE276D9402D |
| SHA256: | 2E6476C2FB283FC1DF5827452D0FE0C001A0AA64A867E791FB8E46C0CF69BE1F |
| SSDEEP: | 768:BDNTIaUuYM2jWhGrFYXoMceoWK4xodRRLwJVzFZ6V7:BDNPGxYYMzoWK4URLmLEV7 |
MALICIOUS
No malicious indicators.SUSPICIOUS
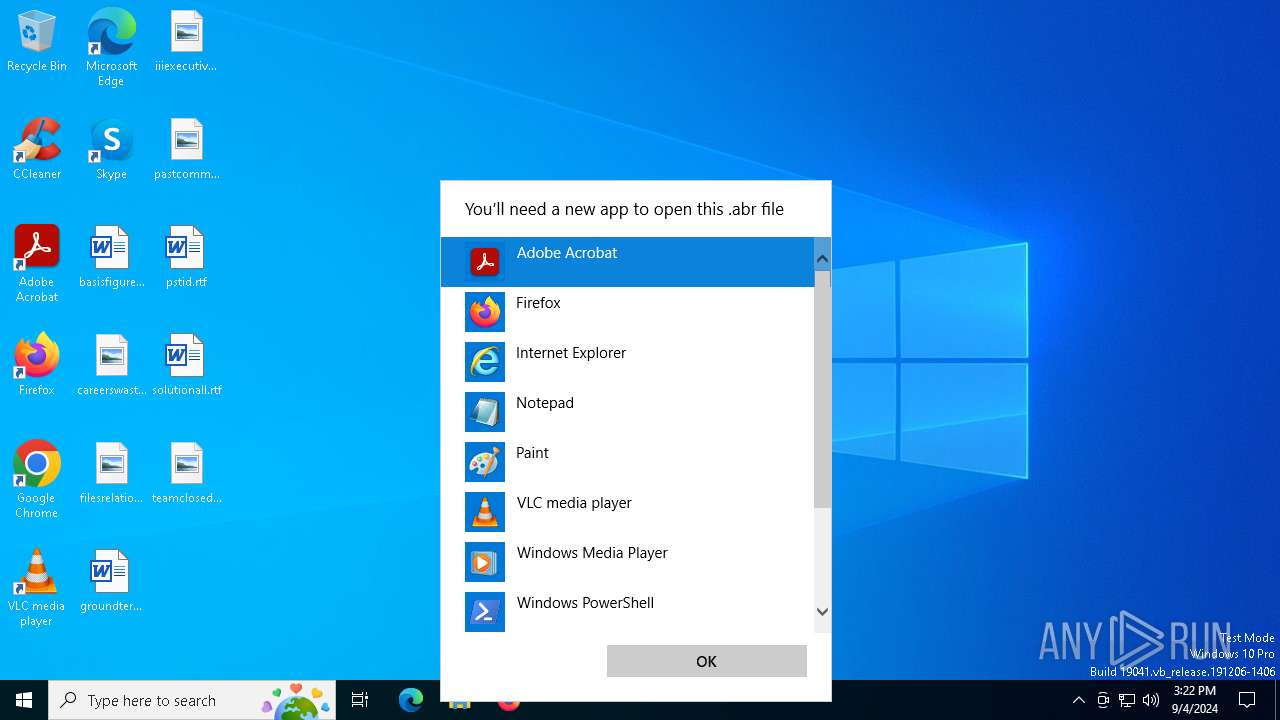
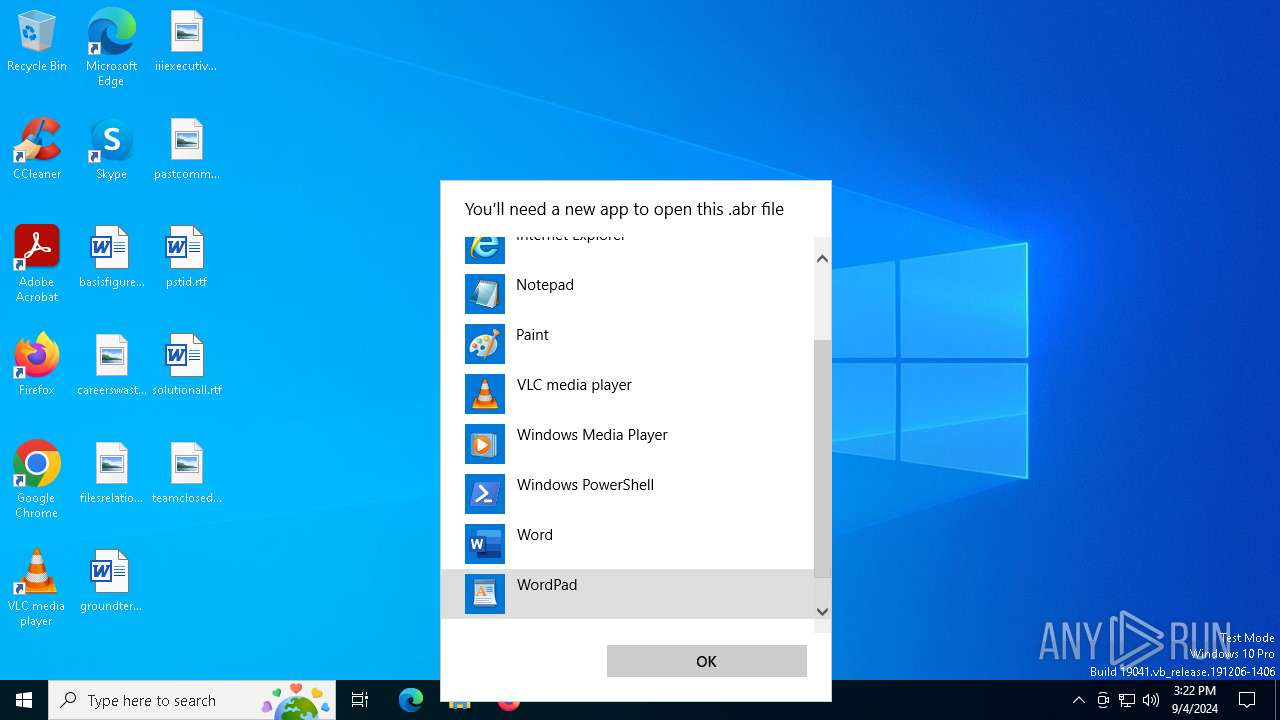
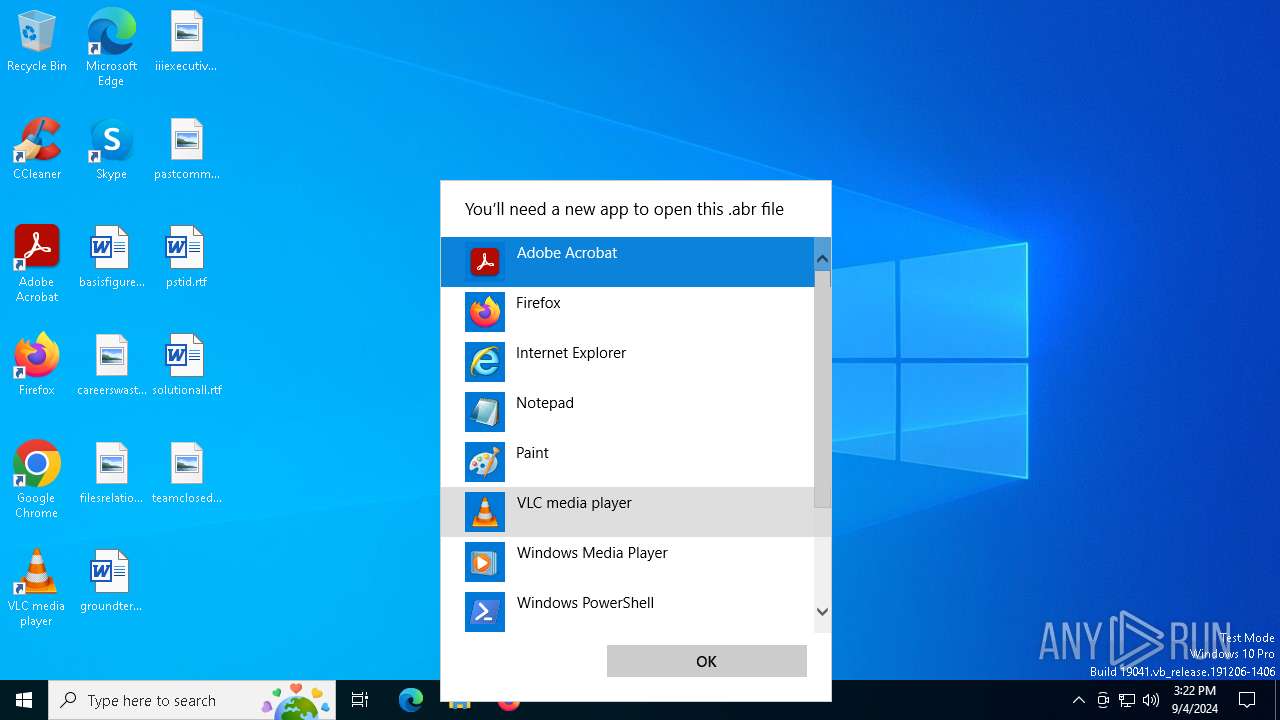
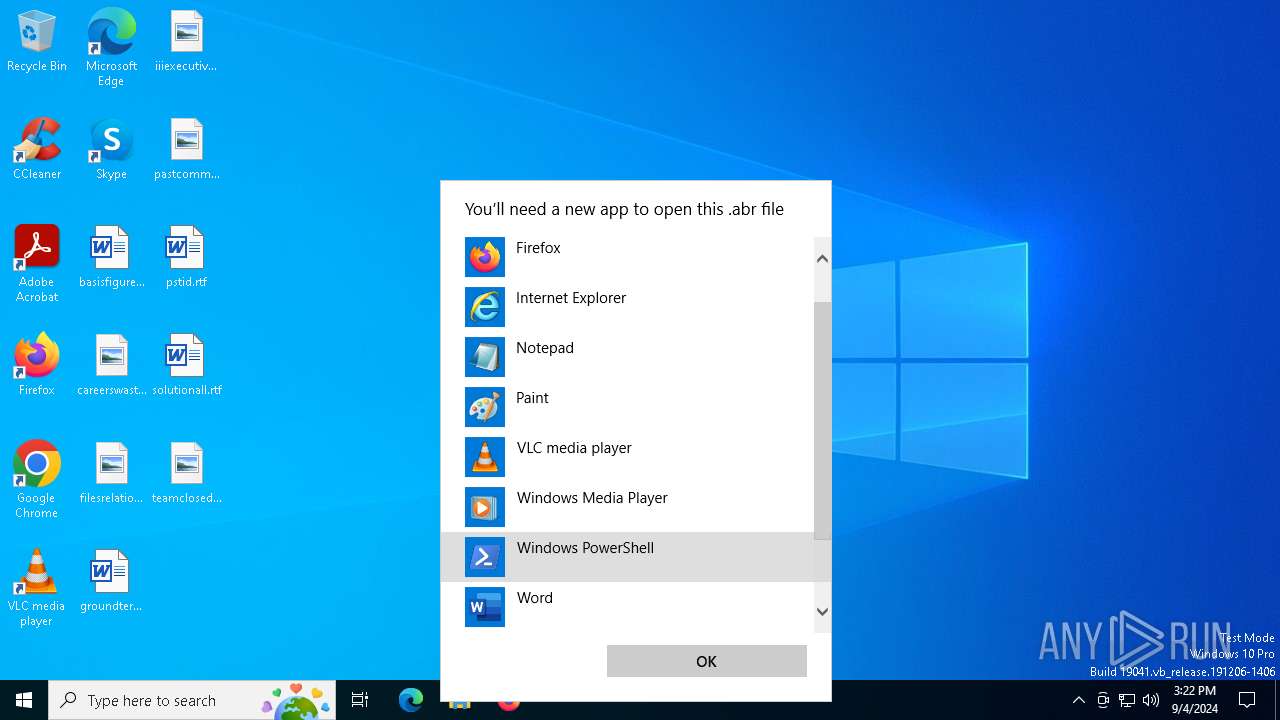
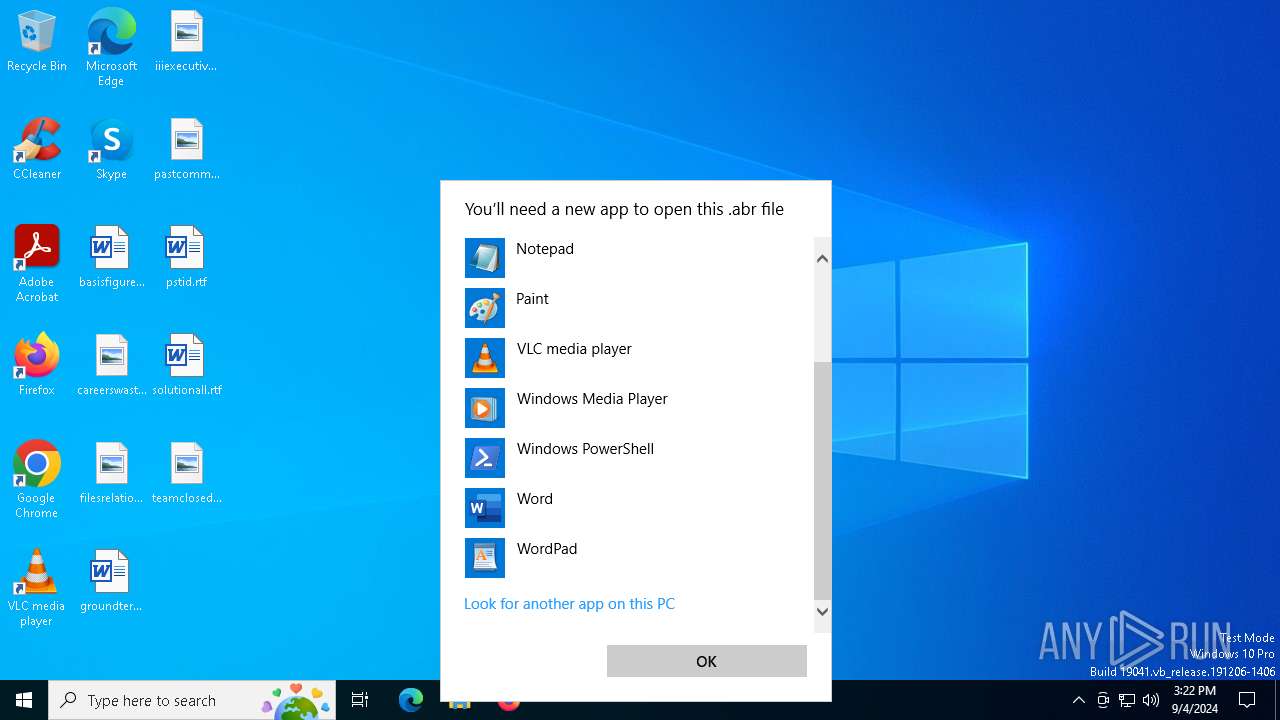
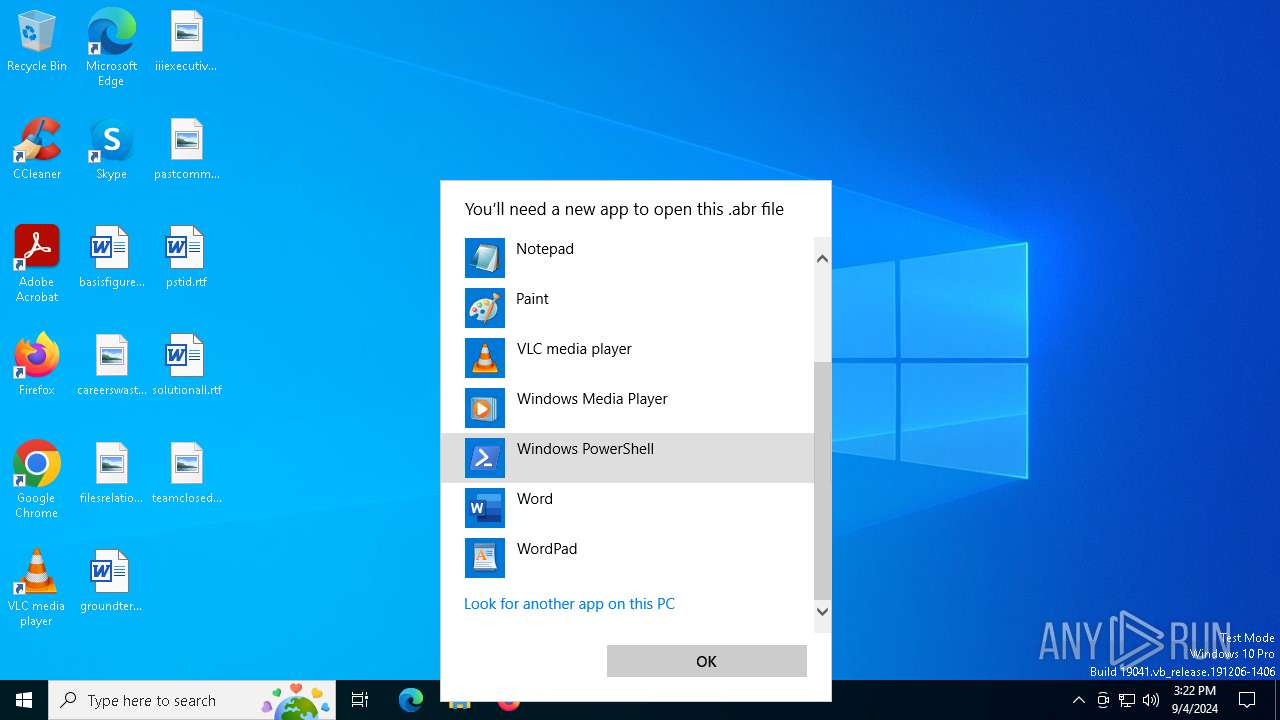
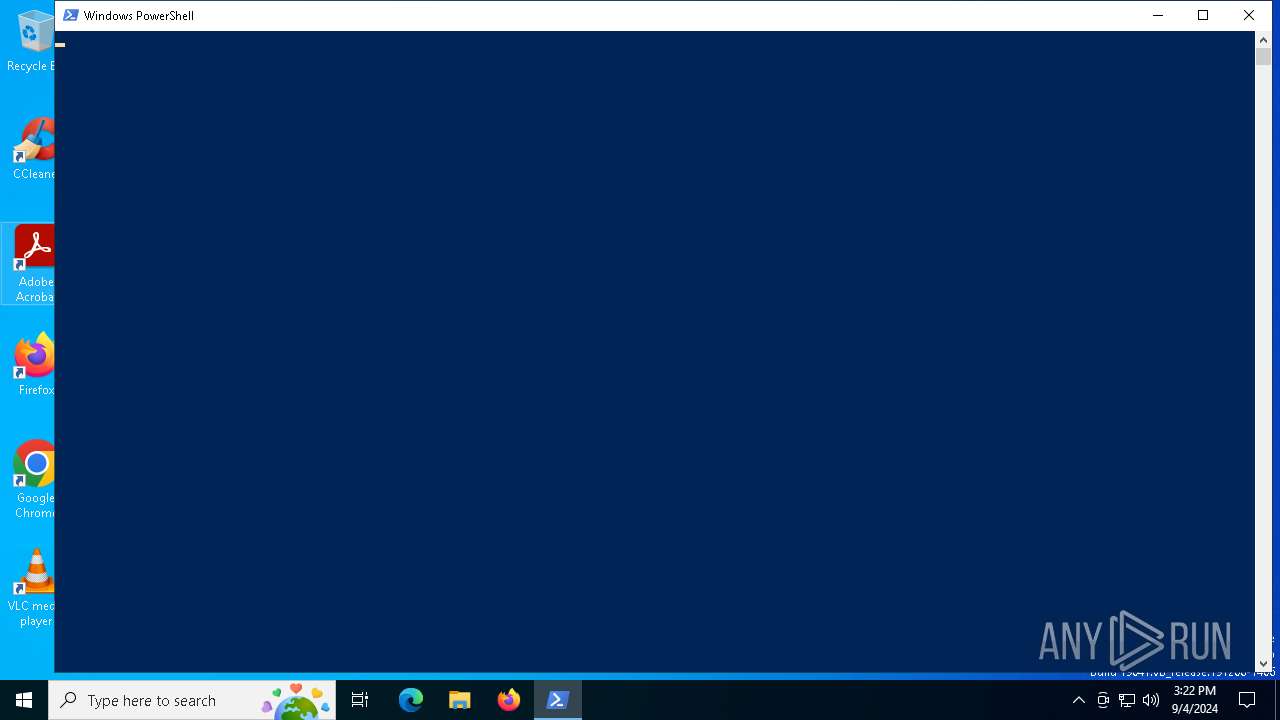
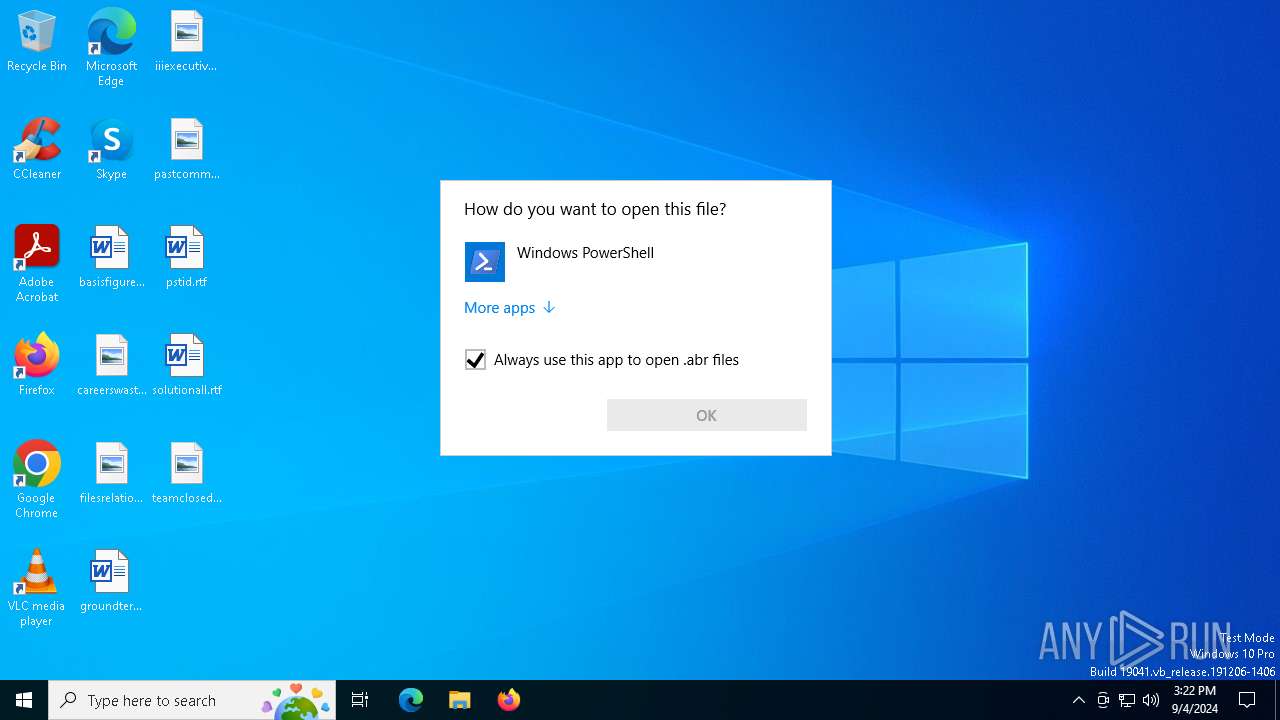
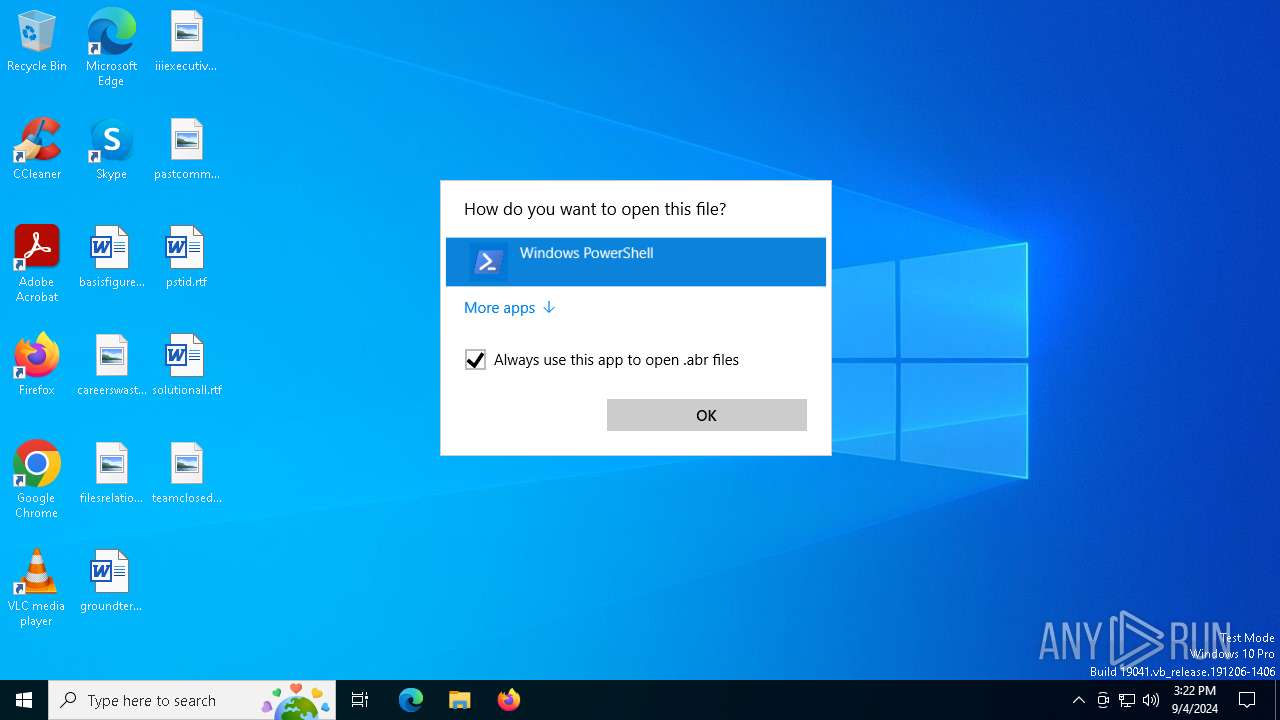
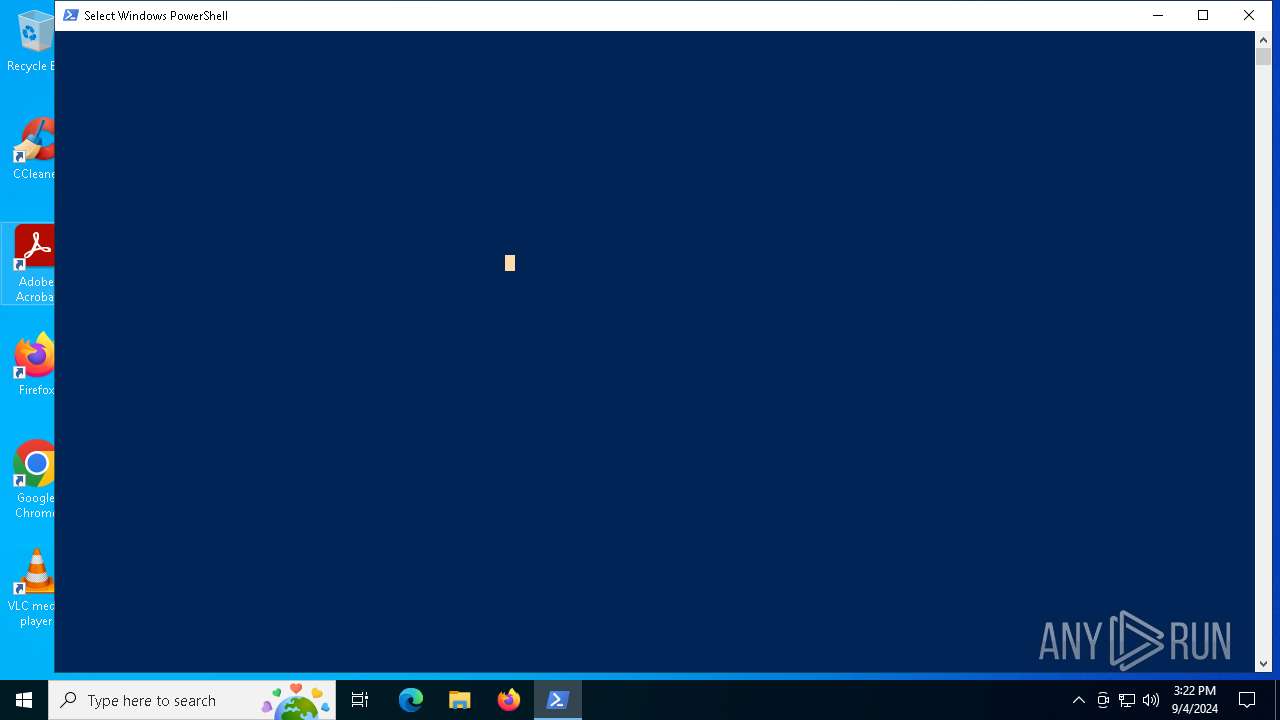
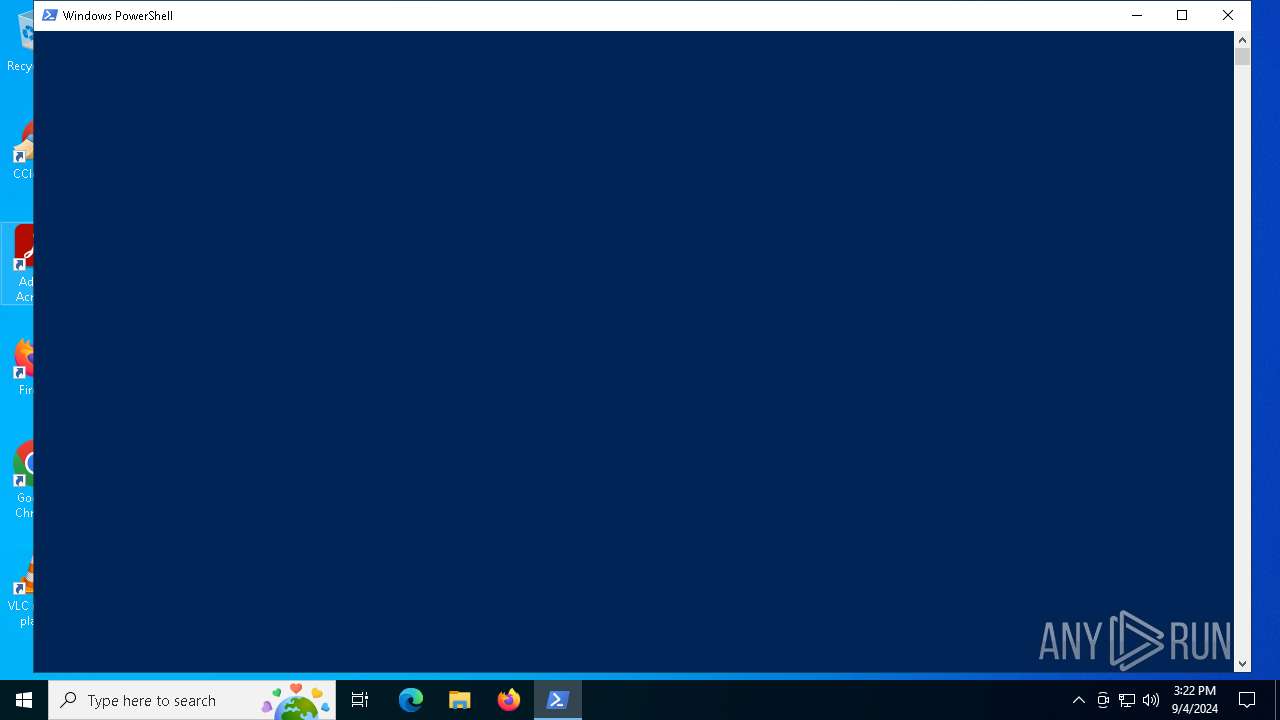
Starts POWERSHELL.EXE for commands execution
- OpenWith.exe (PID: 3728)
- OpenWith.exe (PID: 4020)
- powershell.exe (PID: 6372)
- powershell.exe (PID: 2264)
- powershell.exe (PID: 4996)
- powershell.exe (PID: 6580)
- powershell.exe (PID: 5744)
- powershell.exe (PID: 4708)
- powershell.exe (PID: 3352)
- powershell.exe (PID: 7016)
- powershell.exe (PID: 4996)
- powershell.exe (PID: 1616)
- powershell.exe (PID: 2036)
- powershell.exe (PID: 5092)
- powershell.exe (PID: 1060)
- powershell.exe (PID: 3700)
- powershell.exe (PID: 2684)
- powershell.exe (PID: 1060)
- powershell.exe (PID: 3700)
Application launched itself
- powershell.exe (PID: 6372)
- powershell.exe (PID: 4996)
- powershell.exe (PID: 2264)
- powershell.exe (PID: 6580)
- powershell.exe (PID: 3352)
- powershell.exe (PID: 1060)
- powershell.exe (PID: 3700)
- powershell.exe (PID: 5744)
- powershell.exe (PID: 7016)
- powershell.exe (PID: 4996)
- powershell.exe (PID: 2036)
- powershell.exe (PID: 1616)
- powershell.exe (PID: 5092)
- powershell.exe (PID: 1060)
- powershell.exe (PID: 3700)
- powershell.exe (PID: 2684)
- powershell.exe (PID: 4708)
INFO
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 3728)
- OpenWith.exe (PID: 4020)
Reads security settings of Internet Explorer
- OpenWith.exe (PID: 4020)
- OpenWith.exe (PID: 3728)
The process uses the downloaded file
- powershell.exe (PID: 6948)
- powershell.exe (PID: 6372)
- OpenWith.exe (PID: 4020)
- OpenWith.exe (PID: 3728)
- powershell.exe (PID: 2264)
- powershell.exe (PID: 4996)
- powershell.exe (PID: 6580)
- powershell.exe (PID: 5744)
- powershell.exe (PID: 3700)
- powershell.exe (PID: 3352)
- powershell.exe (PID: 4996)
- powershell.exe (PID: 2036)
- powershell.exe (PID: 1616)
- powershell.exe (PID: 5092)
- powershell.exe (PID: 3700)
- powershell.exe (PID: 1060)
- powershell.exe (PID: 2684)
- powershell.exe (PID: 7016)
- powershell.exe (PID: 1060)
- powershell.exe (PID: 4708)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
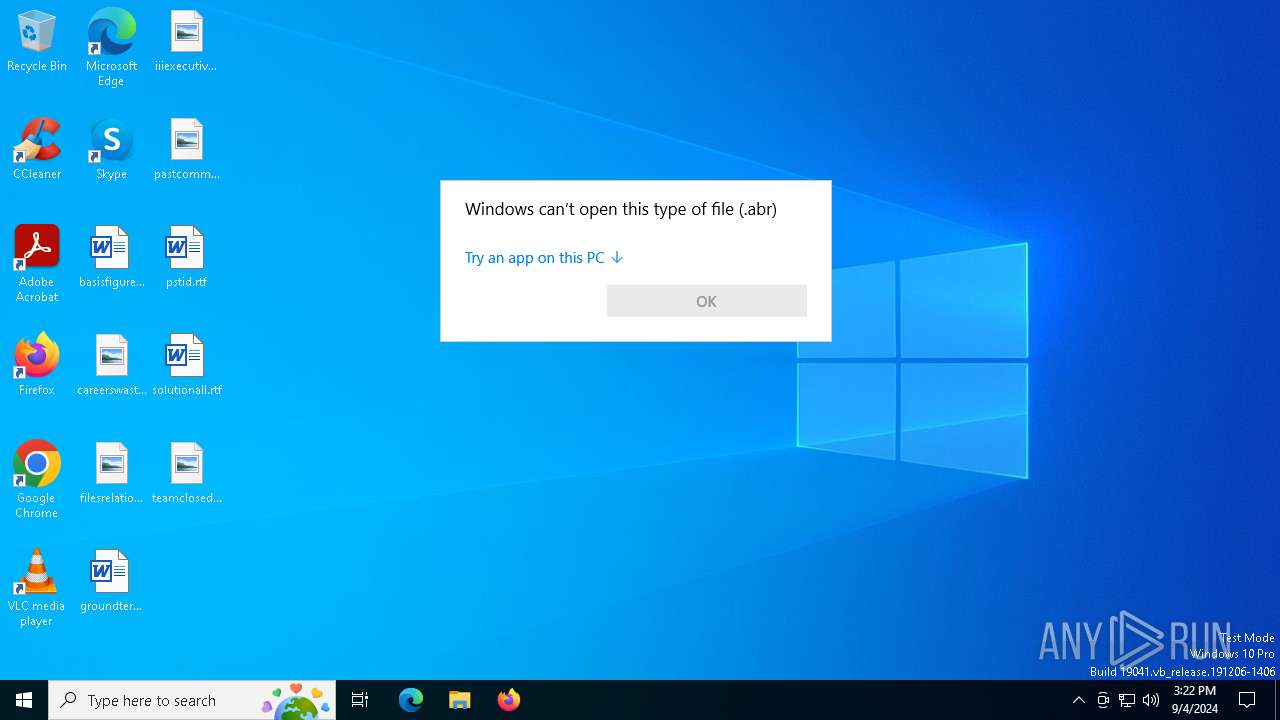
| .abr | | | Adobe PhotoShop Brush (98.1) |
|---|---|---|
| .dbf | | | Sybase iAnywhere database files (1.8) |
Total processes
166
Monitored processes
40
Malicious processes
4
Suspicious processes
7
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 8 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 400 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 888 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1060 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" "C:\WINDOWS\SHS-08312024-120025-7-1ff-22621.1.amd64fre.ni_release.220506-1250.etl.abr" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1060 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" "C:\WINDOWS\SHS-08312024-120025-7-1ff-22621.1.amd64fre.ni_release.220506-1250.etl.abr" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1332 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1568 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1616 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" "C:\WINDOWS\SHS-08312024-120025-7-1ff-22621.1.amd64fre.ni_release.220506-1250.etl.abr" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2024 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2036 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" "C:\WINDOWS\SHS-08312024-120025-7-1ff-22621.1.amd64fre.ni_release.220506-1250.etl.abr" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
87 848
Read events
87 824
Write events
24
Delete events
0
Modification events
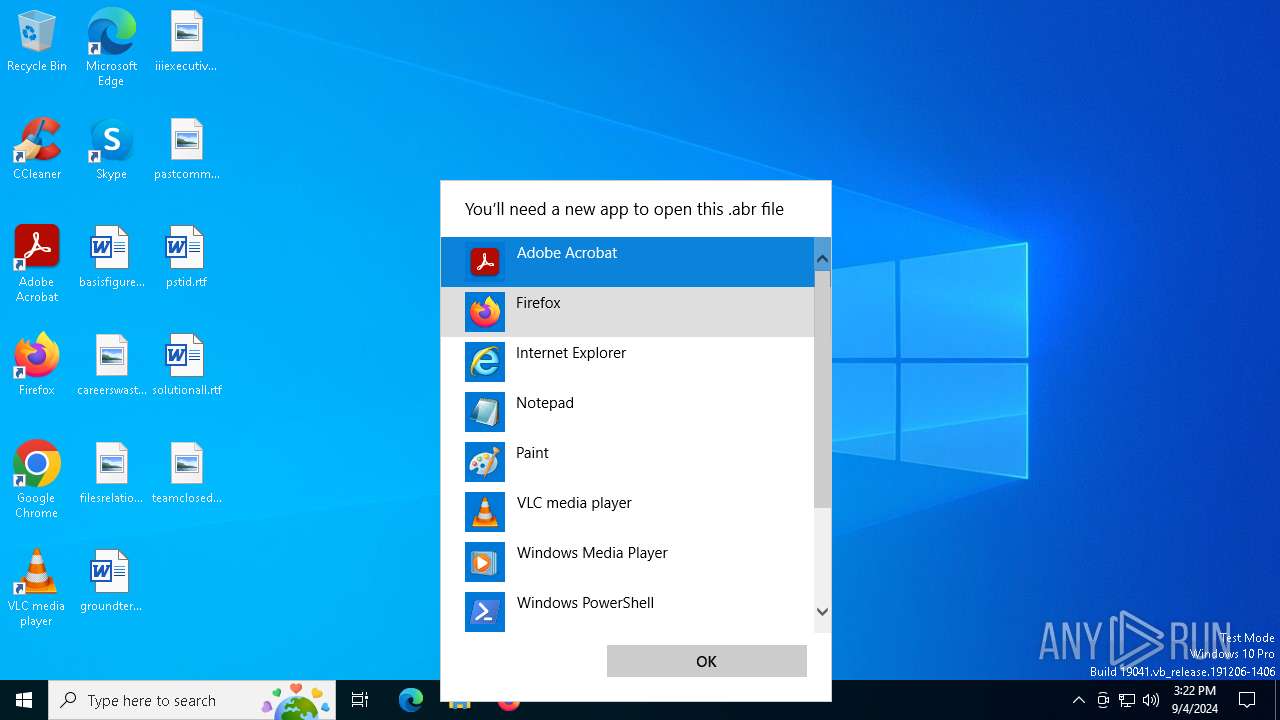
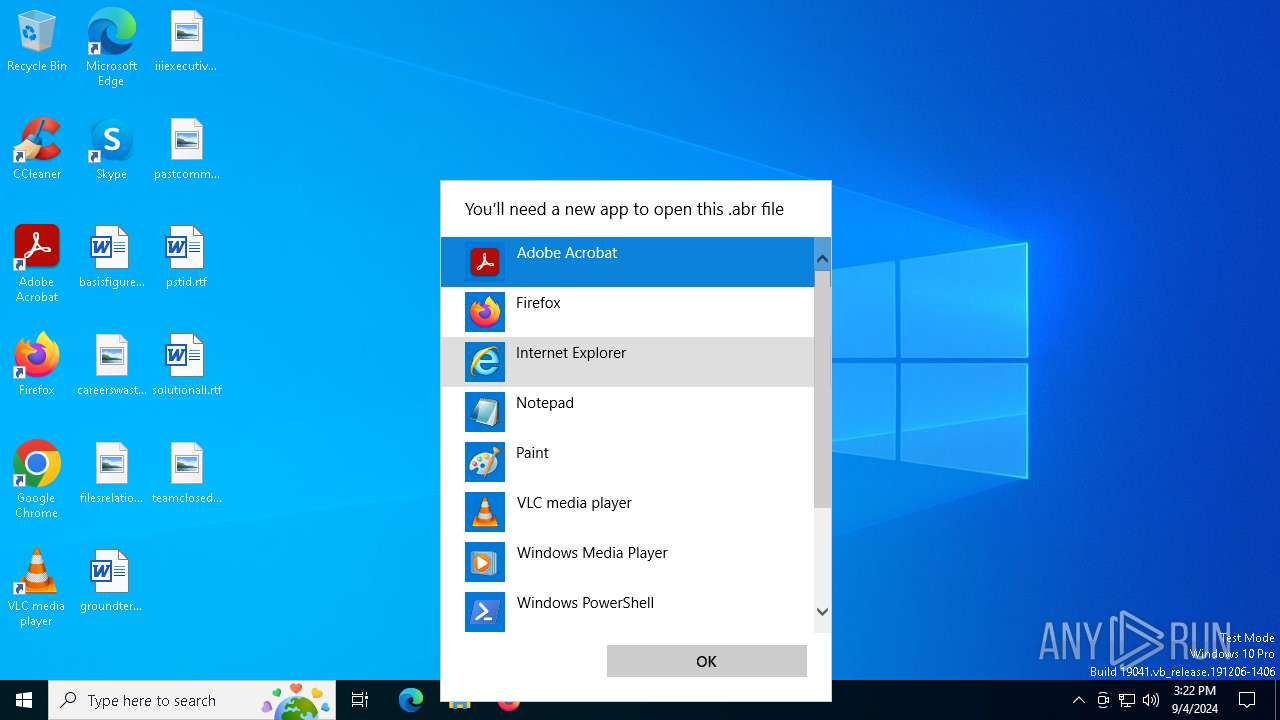
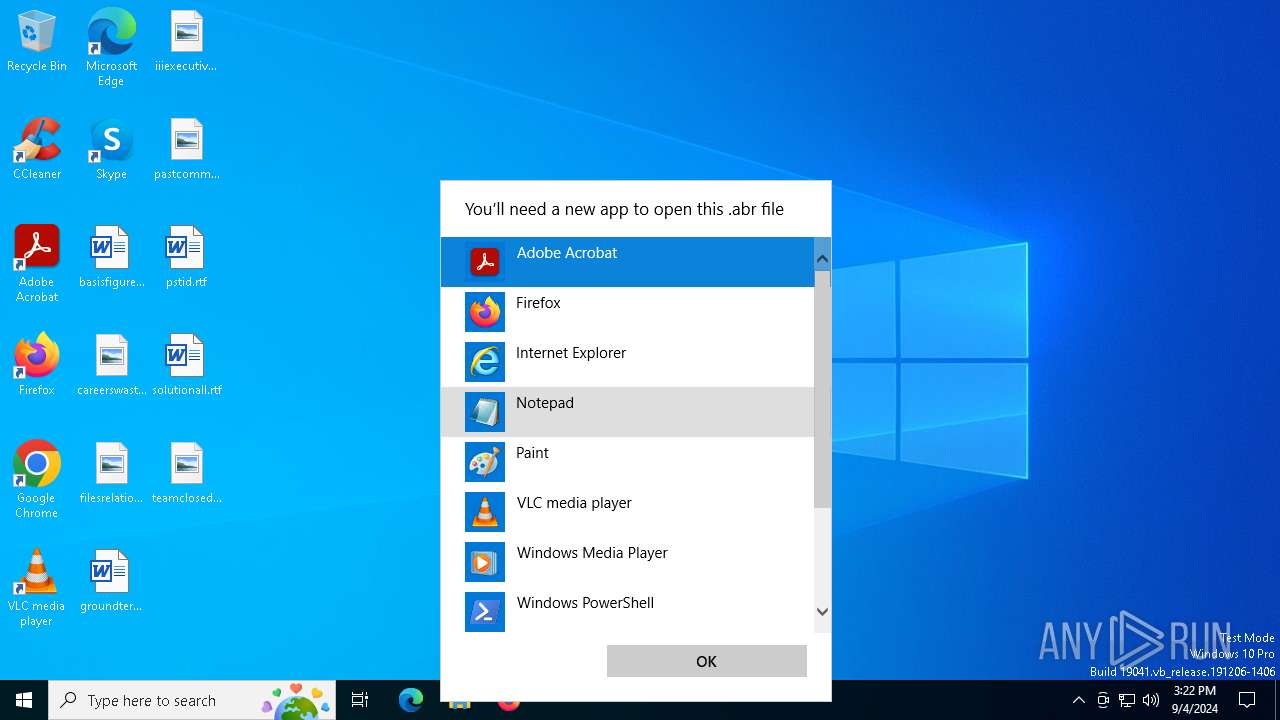
| (PID) Process: | (4020) OpenWith.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.abr\UserChoice |
| Operation: | write | Name: | ProgId |
Value: Applications\powershell.exe | |||
| (PID) Process: | (4020) OpenWith.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.abr\UserChoice |
| Operation: | write | Name: | Hash |
Value: jT2nFkulZmk= | |||
| (PID) Process: | (4020) OpenWith.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.abr\OpenWithProgids |
| Operation: | write | Name: | abr_auto_file |
Value: | |||
| (PID) Process: | (4020) OpenWith.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.abr\OpenWithList |
| Operation: | write | Name: | MRUList |
Value: a | |||
| (PID) Process: | (4020) OpenWith.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | GlobalAssocChangedCounter |
Value: 93 | |||
| (PID) Process: | (6372) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.abr\OpenWithProgids |
| Operation: | write | Name: | abr_auto_file |
Value: | |||
| (PID) Process: | (2264) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.abr\OpenWithProgids |
| Operation: | write | Name: | abr_auto_file |
Value: | |||
| (PID) Process: | (4996) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.abr\OpenWithProgids |
| Operation: | write | Name: | abr_auto_file |
Value: | |||
| (PID) Process: | (6580) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.abr\OpenWithProgids |
| Operation: | write | Name: | abr_auto_file |
Value: | |||
| (PID) Process: | (3352) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.abr\OpenWithProgids |
| Operation: | write | Name: | abr_auto_file |
Value: | |||
Executable files
0
Suspicious files
58
Text files
36
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6372 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\HKHK047JYAT5I6AR1KY4.temp | binary | |
MD5:7587D5C0AF28AE6D62A153A302C789DA | SHA256:A63CE858D9EA15FA7419F467DF6A9F65B86EEE986063AF3A9489AF6D2D24EB54 | |||
| 6948 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:BCDFD4DF6D5C8EBCACA4CC0DF28B3078 | SHA256:2475A7579377DB757CD7EB4E44F9C1AAF3F5F48D8E6235C9A19A876612DC33E1 | |||
| 6948 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:F8AEACF94571F1D71E96B6D0BFA021DC | SHA256:C62996BEBFAB185704D0D40EE21FDC725BE7BCE967A3885514F6C0FB3E8B87E6 | |||
| 6948 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_x5g1zsiv.5xn.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6948 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_1arpu2tq.p4q.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6948 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\QYDQM25GTP1FEEB8P5UW.temp | binary | |
MD5:F8AEACF94571F1D71E96B6D0BFA021DC | SHA256:C62996BEBFAB185704D0D40EE21FDC725BE7BCE967A3885514F6C0FB3E8B87E6 | |||
| 6948 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF12f209.TMP | binary | |
MD5:D040F64E9E7A2BB91ABCA5613424598E | SHA256:D04E0A6940609BD6F3B561B0F6027F5CA4E8C5CF0FB0D0874B380A0374A8D670 | |||
| 4996 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:E62CD792A9754238C64752A7E41DCDCA | SHA256:74D1DBA1AAB32C686BAE1613212AEF3B8410B640DF00307AEE4071DD410CEC25 | |||
| 6372 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF1317a2.TMP | binary | |
MD5:F8AEACF94571F1D71E96B6D0BFA021DC | SHA256:C62996BEBFAB185704D0D40EE21FDC725BE7BCE967A3885514F6C0FB3E8B87E6 | |||
| 2264 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:EFA0805C29C5C7AFD7B01A616A0EBC5C | SHA256:F36A24C9CDBC9067CD1E26C667637178577DE6BBF13C82C4BCD3884171FE42C0 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
33
DNS requests
14
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1828 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1496 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1496 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6012 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3260 | svchost.exe | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1828 | svchost.exe | 40.126.32.74:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1828 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
6012 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |