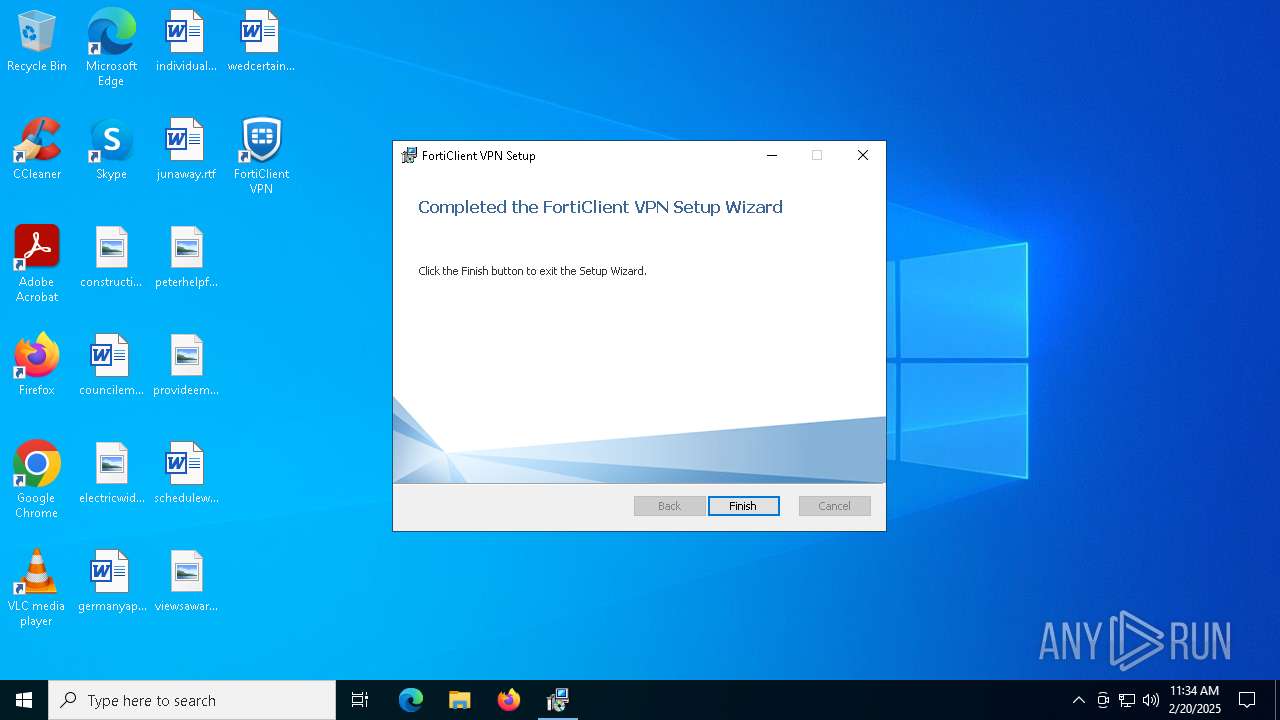
| File name: | FortiClientVPNOnlineInstaller (2).exe |
| Full analysis: | https://app.any.run/tasks/c7cfc10a-749d-4f20-a8d6-7d65cbd3608a |
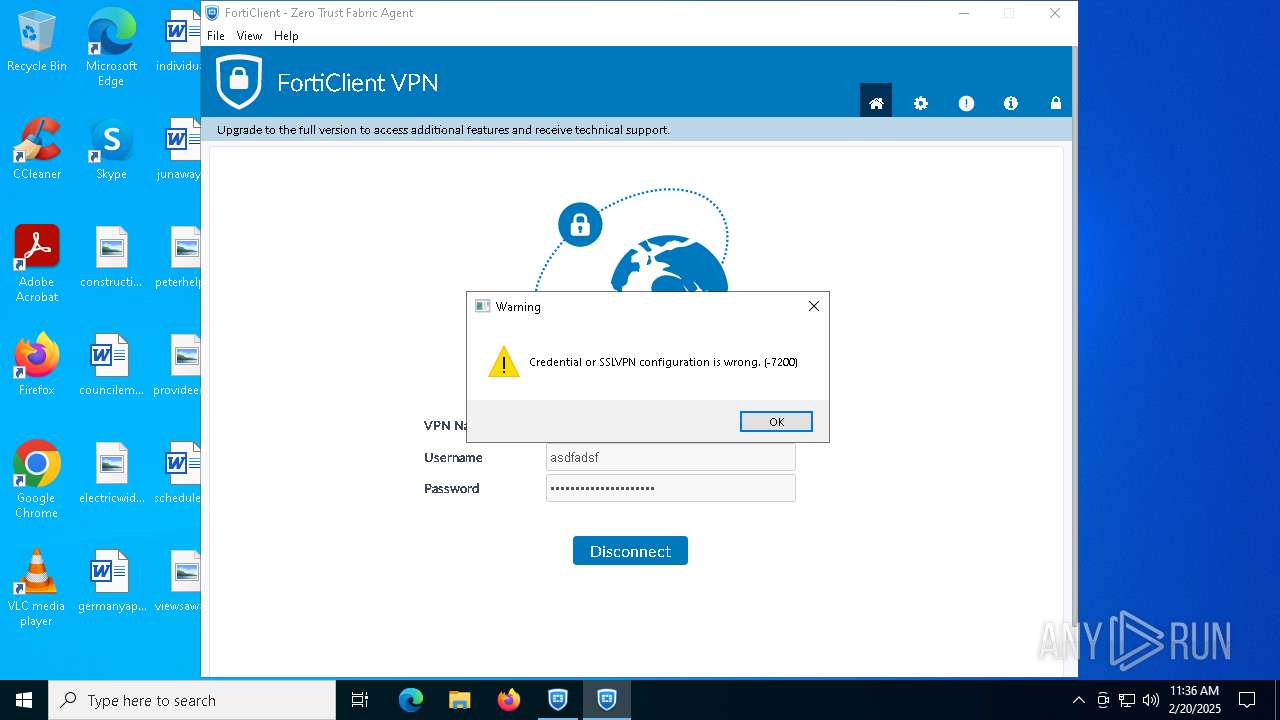
| Verdict: | Malicious activity |
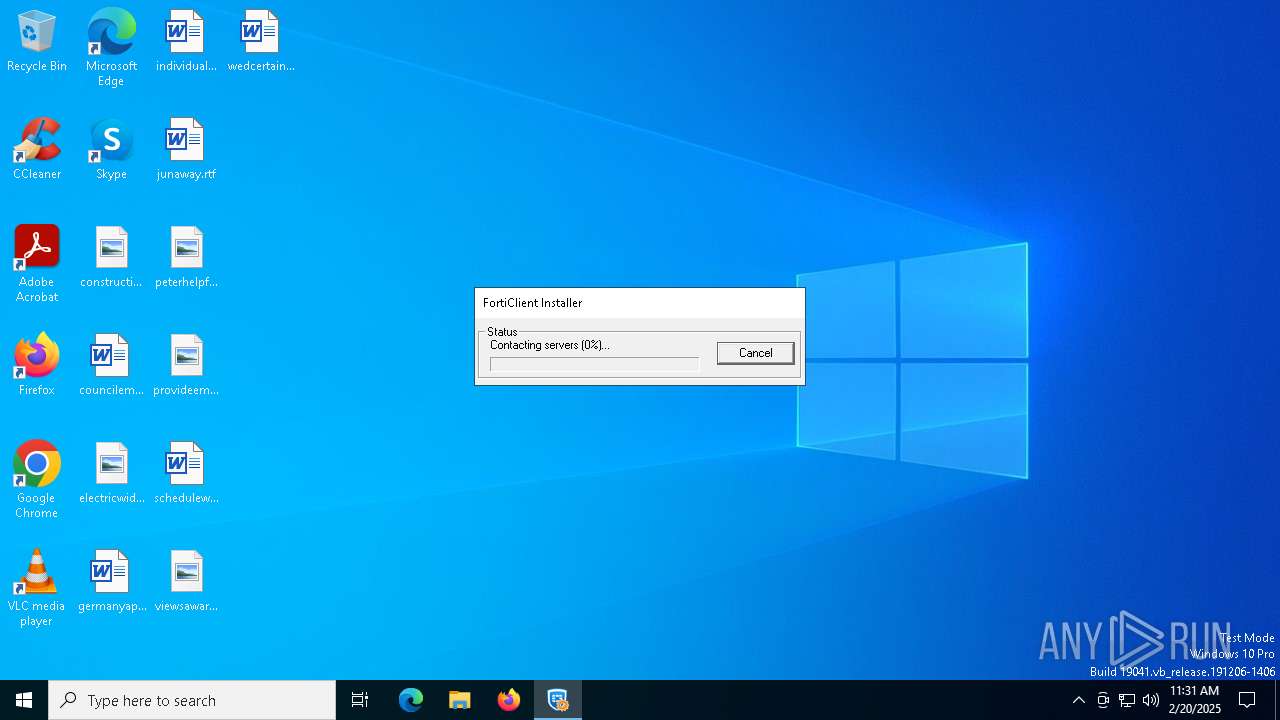
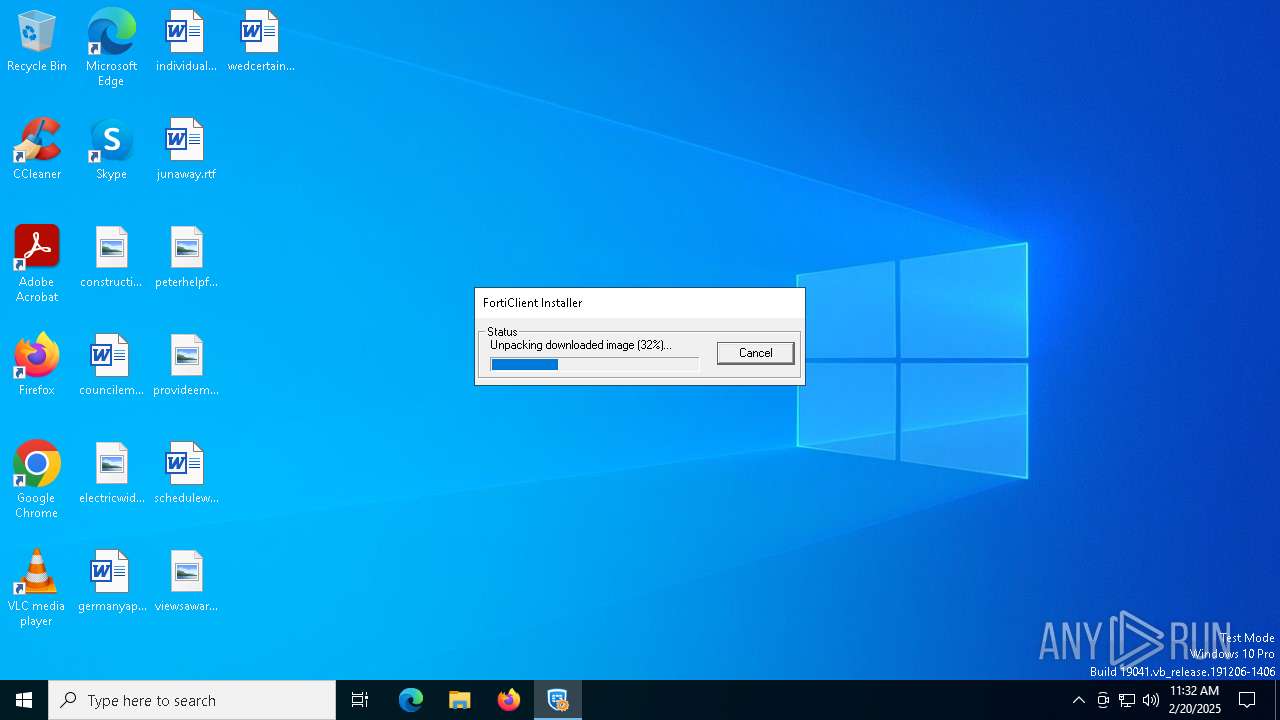
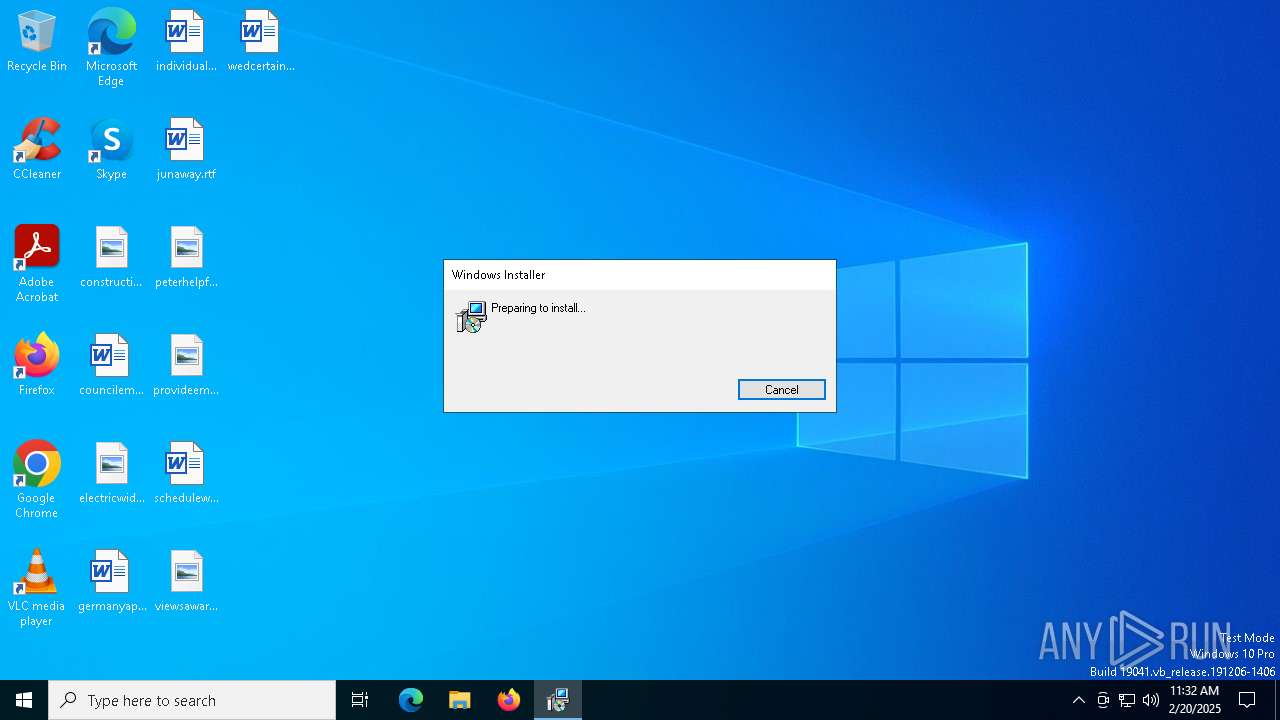
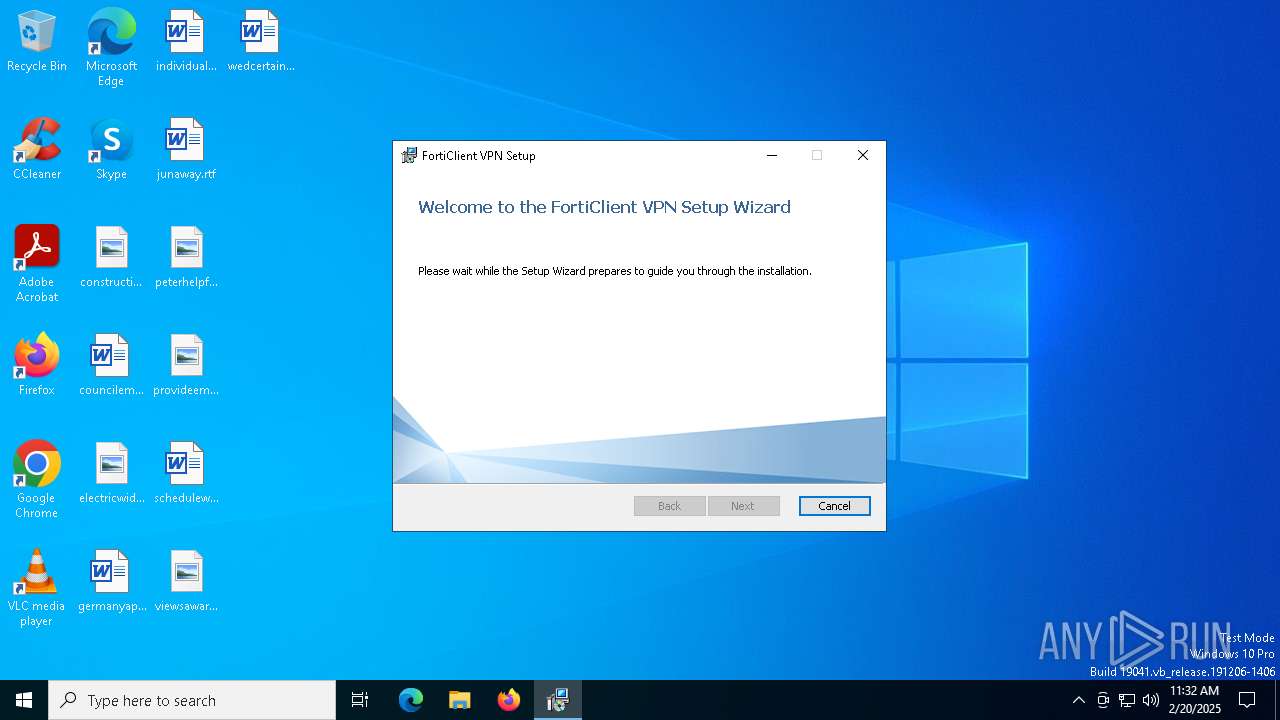
| Analysis date: | February 20, 2025, 11:31:21 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 6 sections |
| MD5: | 11BFC265FC53AC4756E4EF2759CA10EB |
| SHA1: | E3D2BF11618C39DFD036BB33EA96AA5F989FED25 |
| SHA256: | 2E520FAA2B71BA56643153B77C2908C0D6DA34A2F6F9ABAA7CBADAB9278DC99E |
| SSDEEP: | 98304:Fvs0nKhLE+vtgITiwgX672SJGqa1sI8XOcup2xvHdXPSmU8mdLRhQCX:c/2nL0a |
MALICIOUS
Changes the autorun value in the registry
- VC_redist.x64.exe (PID: 1760)
- VC_redist.x86.exe (PID: 5680)
Registers / Runs the DLL via REGSVR32.EXE
- scheduler.exe (PID: 4740)
Starts NET.EXE for service management
- FortiSSLVPNdaemon.exe (PID: 7108)
- net.exe (PID: 3000)
SUSPICIOUS
Application launched itself
- FortiClientVPNOnlineInstaller (2).exe (PID: 6344)
- VC_redist.x64.exe (PID: 7088)
- VC_redist.x64.exe (PID: 6736)
- FortiClient.exe (PID: 4308)
- VC_redist.x86.exe (PID: 3984)
- VC_redist.x86.exe (PID: 2356)
Reads security settings of Internet Explorer
- FortiClientVPNOnlineInstaller (2).exe (PID: 6344)
- FortiClientVPNOnlineInstaller (2).exe (PID: 6552)
- FortiClientVPN.exe (PID: 6188)
- VC_redist.x64.exe (PID: 6076)
- VC_redist.x64.exe (PID: 6736)
- VC_redist.x86.exe (PID: 5788)
- FortiElevate.exe (PID: 4724)
- scheduler.exe (PID: 4740)
- VC_redist.x86.exe (PID: 2356)
- FCDBLog.exe (PID: 1596)
- update_task.exe (PID: 6364)
Checks Windows Trust Settings
- FortiClientVPNOnlineInstaller (2).exe (PID: 6552)
- FortiClientVPN.exe (PID: 6188)
- msiexec.exe (PID: 6524)
- drvinst.exe (PID: 6092)
- drvinst.exe (PID: 2972)
- drvinst.exe (PID: 188)
- msiexec.exe (PID: 5308)
- scheduler.exe (PID: 4740)
Executable content was dropped or overwritten
- FortiClientVPN.exe (PID: 6188)
- drvinst.exe (PID: 2972)
- drvinst.exe (PID: 6860)
- drvinst.exe (PID: 6092)
- drvinst.exe (PID: 2792)
- drvinst.exe (PID: 188)
- VC_redist.x64.exe (PID: 2424)
- VC_redist.x64.exe (PID: 6076)
- VC_redist.x64.exe (PID: 6736)
- VC_redist.x64.exe (PID: 1760)
- VC_redist.x64.exe (PID: 4764)
- VC_redist.x86.exe (PID: 2996)
- VC_redist.x86.exe (PID: 5788)
- VC_redist.x86.exe (PID: 5680)
- VC_redist.x86.exe (PID: 2356)
- VC_redist.x86.exe (PID: 7060)
- update_task.exe (PID: 6364)
Reads the Windows owner or organization settings
- FortiClientVPN.exe (PID: 6188)
- msiexec.exe (PID: 6524)
Process drops legitimate windows executable
- msiexec.exe (PID: 6524)
- msiexec.exe (PID: 5308)
- VC_redist.x64.exe (PID: 6076)
- VC_redist.x64.exe (PID: 2424)
- VC_redist.x64.exe (PID: 1760)
- VC_redist.x86.exe (PID: 2996)
- VC_redist.x64.exe (PID: 4764)
- VC_redist.x86.exe (PID: 5680)
- VC_redist.x86.exe (PID: 5788)
- VC_redist.x86.exe (PID: 7060)
- update_task.exe (PID: 6364)
The process creates files with name similar to system file names
- msiexec.exe (PID: 6524)
- msiexec.exe (PID: 5308)
Drops a system driver (possible attempt to evade defenses)
- msiexec.exe (PID: 6524)
- drvinst.exe (PID: 2972)
- drvinst.exe (PID: 6092)
- drvinst.exe (PID: 188)
Creates files in the driver directory
- drvinst.exe (PID: 2972)
- msiexec.exe (PID: 5308)
- drvinst.exe (PID: 6092)
- msiexec.exe (PID: 6524)
- drvinst.exe (PID: 2792)
- drvinst.exe (PID: 188)
Creates or modifies Windows services
- drvinst.exe (PID: 6860)
- drvinst.exe (PID: 2792)
Adds/modifies Windows certificates
- msiexec.exe (PID: 5308)
- scheduler.exe (PID: 4740)
The process drops C-runtime libraries
- msiexec.exe (PID: 5308)
- msiexec.exe (PID: 6524)
Executes as Windows Service
- scheduler.exe (PID: 4740)
- VSSVC.exe (PID: 6780)
Creates/Modifies COM task schedule object
- msiexec.exe (PID: 6524)
- regsvr32.exe (PID: 2084)
Starts a Microsoft application from unusual location
- VC_redist.x64.exe (PID: 6076)
- VC_redist.x64.exe (PID: 1760)
- VC_redist.x86.exe (PID: 5788)
- VC_redist.x86.exe (PID: 5680)
Starts itself from another location
- VC_redist.x64.exe (PID: 6076)
- VC_redist.x86.exe (PID: 5788)
Searches for installed software
- dllhost.exe (PID: 644)
- VC_redist.x64.exe (PID: 4764)
- VC_redist.x86.exe (PID: 5788)
- VC_redist.x64.exe (PID: 6736)
- VC_redist.x86.exe (PID: 5680)
- VC_redist.x86.exe (PID: 7060)
- VC_redist.x86.exe (PID: 2356)
- update_task.exe (PID: 6364)
Creates a software uninstall entry
- VC_redist.x64.exe (PID: 1760)
- VC_redist.x86.exe (PID: 5680)
The process checks if it is being run in the virtual environment
- msiexec.exe (PID: 6524)
Reads the date of Windows installation
- FortiElevate.exe (PID: 4724)
- scheduler.exe (PID: 4740)
Checks for external IP
- FortiVPN.exe (PID: 1328)
Suspicious use of NETSH.EXE
- FortiSSLVPNdaemon.exe (PID: 7108)
INFO
Checks supported languages
- FortiClientVPNOnlineInstaller (2).exe (PID: 6344)
- FortiClientVPN.exe (PID: 6188)
- msiexec.exe (PID: 6348)
- msiexec.exe (PID: 6524)
- msiexec.exe (PID: 2212)
- msiexec.exe (PID: 5308)
- drvinst.exe (PID: 2972)
- drvinst.exe (PID: 6860)
- drvinst.exe (PID: 6092)
- drvinst.exe (PID: 2792)
- drvinst.exe (PID: 188)
- scheduler.exe (PID: 4740)
- VC_redist.x64.exe (PID: 2424)
- VC_redist.x64.exe (PID: 6076)
- VC_redist.x64.exe (PID: 1760)
- VC_redist.x64.exe (PID: 7088)
- VC_redist.x64.exe (PID: 6736)
- VC_redist.x86.exe (PID: 2996)
- VC_redist.x86.exe (PID: 5788)
- VC_redist.x64.exe (PID: 4764)
- VC_redist.x86.exe (PID: 5680)
- FortiClient.exe (PID: 4308)
- FortiClient.exe (PID: 7036)
- FortiClient.exe (PID: 5536)
- FortiClient.exe (PID: 720)
- FortiClient.exe (PID: 2776)
- FortiClient.exe (PID: 3060)
- FortiClientSecurity.exe (PID: 3524)
- FortiElevate.exe (PID: 4724)
- FortiClient.exe (PID: 968)
- VC_redist.x86.exe (PID: 3984)
- VC_redist.x86.exe (PID: 2356)
- FortiClient.exe (PID: 5464)
- FortiScand.exe (PID: 4528)
- FCDBLog.exe (PID: 1596)
- FCCOMInt.exe (PID: 6364)
- VC_redist.x86.exe (PID: 7060)
- FortiTray.exe (PID: 7112)
- FortiSSLVPNdaemon.exe (PID: 7108)
- FortiSettings.exe (PID: 4300)
- FortiVPN.exe (PID: 1328)
- update_task.exe (PID: 6364)
Process checks whether UAC notifications are on
- FortiClientVPNOnlineInstaller (2).exe (PID: 6344)
Create files in a temporary directory
- FortiClientVPNOnlineInstaller (2).exe (PID: 6344)
- FortiClientVPNOnlineInstaller (2).exe (PID: 6552)
- FortiClientVPN.exe (PID: 6188)
Reads the computer name
- FortiClientVPNOnlineInstaller (2).exe (PID: 6344)
- FortiClientVPN.exe (PID: 6188)
- msiexec.exe (PID: 6524)
- msiexec.exe (PID: 6348)
- msiexec.exe (PID: 2212)
- msiexec.exe (PID: 5308)
- drvinst.exe (PID: 6860)
- drvinst.exe (PID: 2972)
- drvinst.exe (PID: 6092)
- drvinst.exe (PID: 2792)
- drvinst.exe (PID: 188)
- scheduler.exe (PID: 4740)
- VC_redist.x64.exe (PID: 6076)
- VC_redist.x64.exe (PID: 1760)
- VC_redist.x64.exe (PID: 6736)
- VC_redist.x64.exe (PID: 4764)
- VC_redist.x86.exe (PID: 5788)
- VC_redist.x86.exe (PID: 5680)
- FortiClient.exe (PID: 4308)
- FortiClient.exe (PID: 5536)
- FortiElevate.exe (PID: 4724)
- FortiClient.exe (PID: 720)
- FortiClient.exe (PID: 2776)
- FortiClientSecurity.exe (PID: 3524)
- FortiClient.exe (PID: 3060)
- VC_redist.x86.exe (PID: 2356)
- VC_redist.x86.exe (PID: 7060)
- FortiScand.exe (PID: 4528)
- FCDBLog.exe (PID: 1596)
- FortiClient.exe (PID: 5464)
- FortiSSLVPNdaemon.exe (PID: 7108)
- FortiSettings.exe (PID: 4300)
- FortiVPN.exe (PID: 1328)
- FCCOMInt.exe (PID: 6364)
- FortiTray.exe (PID: 7112)
Creates files or folders in the user directory
- FortiClientVPNOnlineInstaller (2).exe (PID: 6552)
- FortiClient.exe (PID: 4308)
- FortiTray.exe (PID: 7112)
Process checks computer location settings
- FortiClientVPNOnlineInstaller (2).exe (PID: 6344)
- FortiElevate.exe (PID: 4724)
- FortiClient.exe (PID: 5464)
- FortiClient.exe (PID: 4308)
- FCDBLog.exe (PID: 1596)
- update_task.exe (PID: 6364)
Checks proxy server information
- FortiClientVPNOnlineInstaller (2).exe (PID: 6552)
- FortiClient.exe (PID: 4308)
Reads the machine GUID from the registry
- FortiClientVPNOnlineInstaller (2).exe (PID: 6552)
- FortiClientVPN.exe (PID: 6188)
- msiexec.exe (PID: 6524)
- drvinst.exe (PID: 2972)
- drvinst.exe (PID: 188)
- msiexec.exe (PID: 5308)
- drvinst.exe (PID: 6092)
- scheduler.exe (PID: 4740)
- VC_redist.x64.exe (PID: 1760)
- VC_redist.x86.exe (PID: 5680)
- FortiClient.exe (PID: 4308)
Reads the software policy settings
- FortiClientVPNOnlineInstaller (2).exe (PID: 6552)
- FortiClientVPN.exe (PID: 6188)
- msiexec.exe (PID: 6524)
- drvinst.exe (PID: 2972)
- drvinst.exe (PID: 6092)
- drvinst.exe (PID: 188)
- msiexec.exe (PID: 5308)
- scheduler.exe (PID: 4740)
- FortiTray.exe (PID: 7112)
The sample compiled with english language support
- FortiClientVPN.exe (PID: 6188)
- msiexec.exe (PID: 6524)
- msiexec.exe (PID: 5308)
- VC_redist.x64.exe (PID: 2424)
- VC_redist.x64.exe (PID: 6076)
- VC_redist.x64.exe (PID: 1760)
- VC_redist.x64.exe (PID: 6736)
- VC_redist.x64.exe (PID: 4764)
- VC_redist.x86.exe (PID: 2996)
- VC_redist.x86.exe (PID: 5788)
- VC_redist.x86.exe (PID: 5680)
- VC_redist.x86.exe (PID: 2356)
- VC_redist.x86.exe (PID: 7060)
- update_task.exe (PID: 6364)
Creates files in the program directory
- FortiClientVPN.exe (PID: 6188)
- VC_redist.x64.exe (PID: 1760)
- VC_redist.x86.exe (PID: 5680)
- FCDBLog.exe (PID: 1596)
- FortiSSLVPNdaemon.exe (PID: 7108)
- update_task.exe (PID: 6364)
Reads Environment values
- msiexec.exe (PID: 6348)
- msiexec.exe (PID: 2212)
- scheduler.exe (PID: 4740)
- FortiClient.exe (PID: 4308)
- FortiElevate.exe (PID: 4724)
- FortiClient.exe (PID: 5464)
- FortiClientSecurity.exe (PID: 3524)
- FCDBLog.exe (PID: 1596)
- FortiTray.exe (PID: 7112)
- FortiSSLVPNdaemon.exe (PID: 7108)
- FortiVPN.exe (PID: 1328)
- update_task.exe (PID: 6364)
Application launched itself
- msiexec.exe (PID: 6524)
Executable content was dropped or overwritten
- msiexec.exe (PID: 6524)
- msiexec.exe (PID: 5308)
Creates a software uninstall entry
- msiexec.exe (PID: 6524)
Manages system restore points
- SrTasks.exe (PID: 7136)
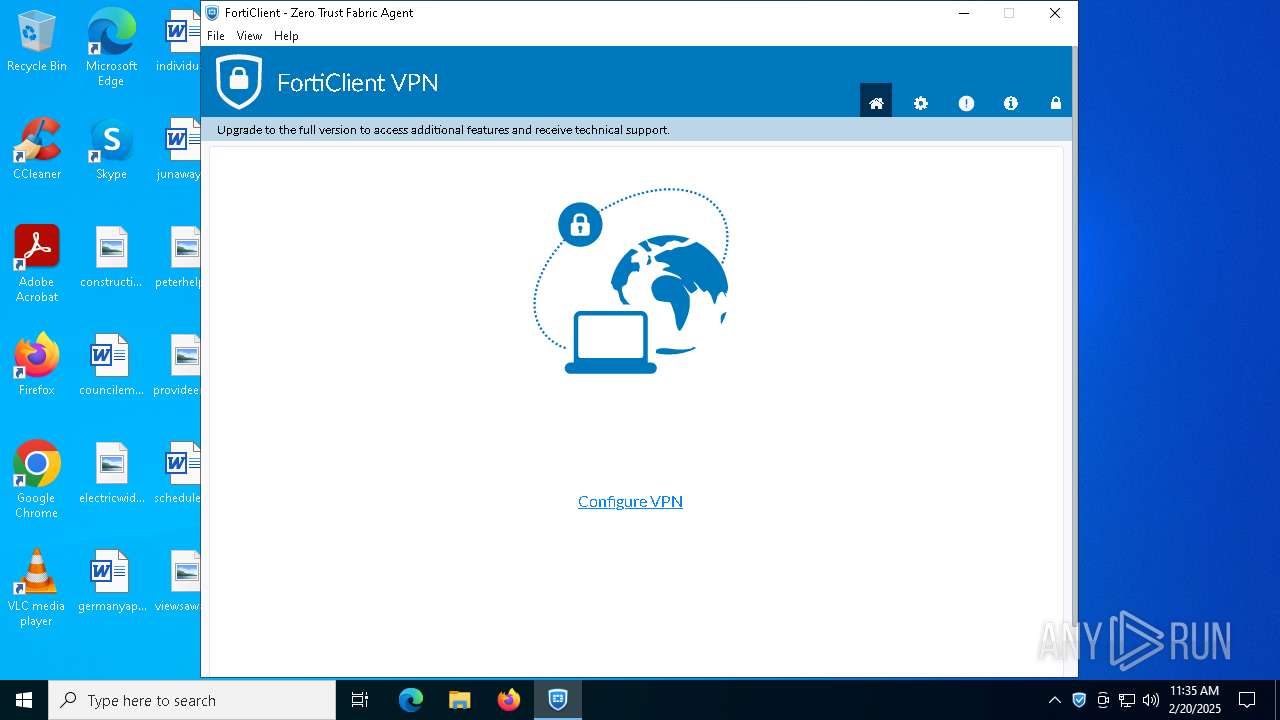
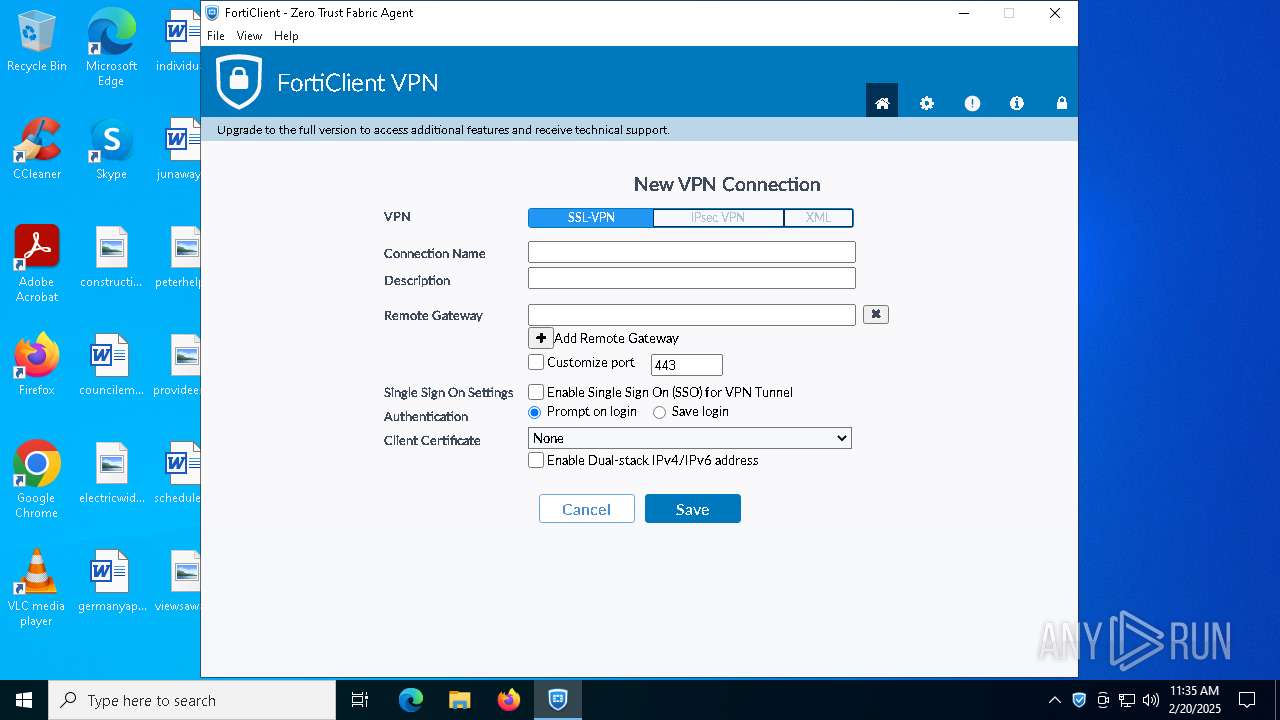
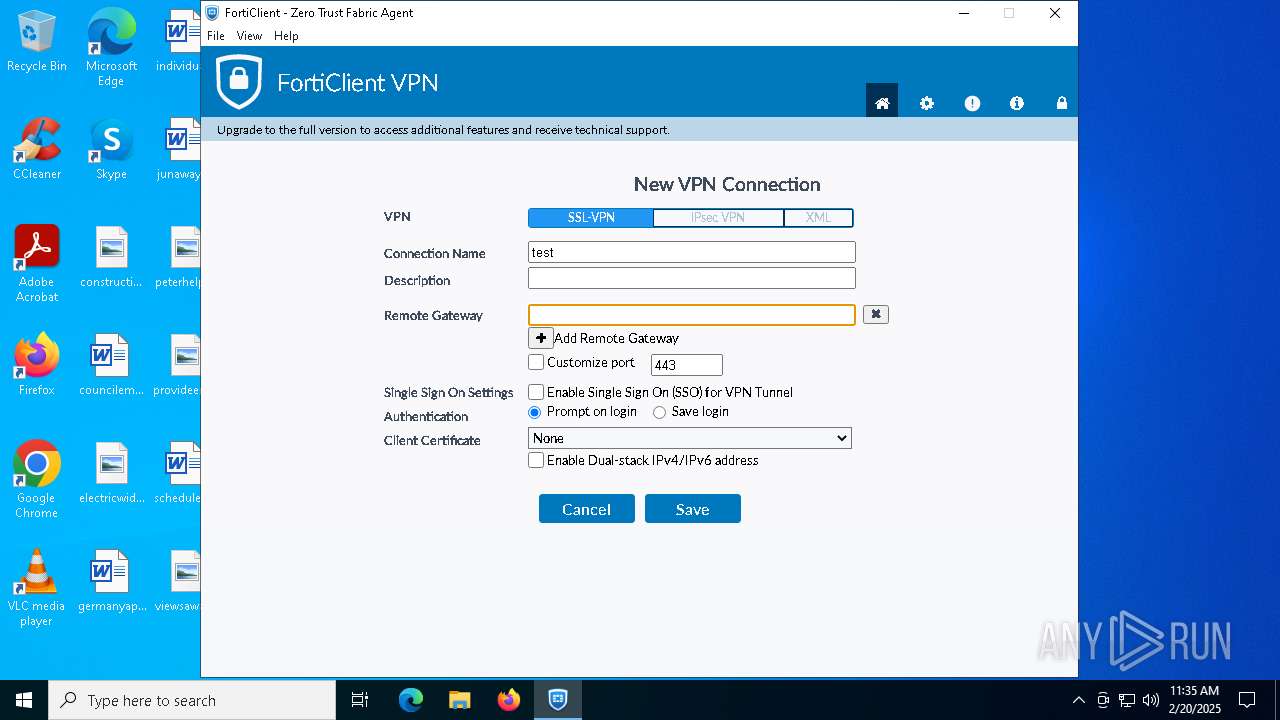
Manual execution by a user
- FortiClient.exe (PID: 4308)
Reads product name
- FortiClient.exe (PID: 4308)
- FortiClient.exe (PID: 5464)
Disables trace logs
- netsh.exe (PID: 2132)
- netsh.exe (PID: 6904)
- netsh.exe (PID: 7036)
- netsh.exe (PID: 1140)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:05:31 22:26:46+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.37 |
| CodeSize: | 1854464 |
| InitializedDataSize: | 951296 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x6fd60 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Total processes
207
Monitored processes
71
Malicious processes
21
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | DrvInst.exe "4" "1" "C:\Program Files\Common Files\Fortinet\FortiClient\7.4.2.1737\FortiFilter\FortiFilter.inf" "9" "4b264819b" "0000000000000214" "WinSta0\Default" "000000000000021C" "208" "C:\Program Files\Common Files\Fortinet\FortiClient\7.4.2.1737\FortiFilter" | C:\Windows\System32\drvinst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 644 | C:\WINDOWS\system32\DllHost.exe /Processid:{F32D97DF-E3E5-4CB9-9E3E-0EB5B4E49801} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: COM Surrogate Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 720 | "C:\Program Files\Fortinet\FortiClient\FortiClient.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --user-data-dir="C:\Users\admin\AppData\Local\FortiClient" --mojo-platform-channel-handle=2268 --field-trial-handle=1332,i,10233906692746323534,7905934548059676174,131072 --disable-features=SpareRendererForSitePerProcess,WinRetrieveSuggestionsOnlyOnDemand /prefetch:8 | C:\Program Files\Fortinet\FortiClient\FortiClient.exe | — | FortiClient.exe | |||||||||||
User: admin Company: Fortinet Inc. Integrity Level: MEDIUM Description: FortiClient Console Version: 7.4.2.1737 Modules
| |||||||||||||||
| 968 | "C:\Program Files\Fortinet\FortiClient\FortiClient.exe" --type=gpu-process --user-data-dir="C:\Users\admin\AppData\Local\FortiClient" --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAABgAAAAAAAAAGAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAACAAAAAAAAAA= --use-gl=disabled --mojo-platform-channel-handle=2636 --field-trial-handle=1332,i,10233906692746323534,7905934548059676174,131072 --disable-features=SpareRendererForSitePerProcess,WinRetrieveSuggestionsOnlyOnDemand /prefetch:2 | C:\Program Files\Fortinet\FortiClient\FortiClient.exe | — | FortiClient.exe | |||||||||||
User: admin Company: Fortinet Inc. Integrity Level: LOW Description: FortiClient Console Version: 7.4.2.1737 Modules
| |||||||||||||||
| 1064 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1140 | netsh interface ipv4 delete winsservers 28 all | C:\Windows\System32\netsh.exe | — | FortiSSLVPNdaemon.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Network Command Shell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1328 | FortiVPN.exe -s FC_{73EFB30F-1CAD-4a7a-AE2E-150282B6CE25}_000031 | C:\Program Files\Fortinet\FortiClient\FortiVPN.exe | scheduler.exe | ||||||||||||
User: SYSTEM Company: Fortinet Inc. Integrity Level: SYSTEM Description: FortiClient VPN Controller Version: 7.4.2.1737 Modules
| |||||||||||||||
| 1596 | FCDBLog.exe -s FC_{73EFB30F-1CAD-4a7a-AE2E-150282B6CE25}_000011 | C:\Program Files\Fortinet\FortiClient\FCDBLog.exe | — | scheduler.exe | |||||||||||
User: SYSTEM Company: Fortinet Inc. Integrity Level: SYSTEM Description: FortiClient Logging daemon Version: 7.4.2.1737 Modules
| |||||||||||||||
| 1760 | "C:\WINDOWS\Temp\{BEDBDA3B-0859-405B-8D98-8C35517A6E6D}\.be\VC_redist.x64.exe" -q -burn.elevated BurnPipe.{996A1503-79C5-4A39-8B88-96634BFF71CE} {00B56195-006B-482B-B17A-2802E7C73B2A} 6076 | C:\Windows\Temp\{BEDBDA3B-0859-405B-8D98-8C35517A6E6D}\.be\VC_redist.x64.exe | VC_redist.x64.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Visual C++ 2015-2022 Redistributable (x64) - 14.40.33810 Exit code: 3010 Version: 14.40.33810.0 Modules
| |||||||||||||||
| 2084 | "C:\Windows\System32\regsvr32.exe" /s "C:\Program Files\Fortinet\FortiClient\fccomintdll.dll" | C:\Windows\System32\regsvr32.exe | — | scheduler.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
68 568
Read events
65 475
Write events
2 377
Delete events
716
Modification events
| (PID) Process: | (6524) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\Folders |
| Operation: | write | Name: | C:\Config.Msi\ |
Value: | |||
| (PID) Process: | (6524) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\Rollback\Scripts |
| Operation: | write | Name: | C:\Config.Msi\1484a0.rbs |
Value: 31163275 | |||
| (PID) Process: | (6524) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\Rollback\Scripts |
| Operation: | write | Name: | C:\Config.Msi\1484a0.rbsLow |
Value: 989155600 | |||
| (PID) Process: | (6524) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Components\D8CB2D1BB5E89594398CF30B3D667629 |
| Operation: | write | Name: | 2DE6F49B0797D4E44954ED724539BA0A |
Value: C:\Program Files\Common Files\Fortinet\FortiClient\VC_redist.x64.exe | |||
| (PID) Process: | (6524) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Components\0853336E0ACA9F7459F6A63C4693343C |
| Operation: | write | Name: | 2DE6F49B0797D4E44954ED724539BA0A |
Value: C:\Program Files\Common Files\Fortinet\FortiClient\VC_redist.x86.exe | |||
| (PID) Process: | (6524) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Components\54E05C2EB36152F4CA01265EF0DB30D7 |
| Operation: | write | Name: | 2DE6F49B0797D4E44954ED724539BA0A |
Value: C:\Program Files\Fortinet\FortiClient\ | |||
| (PID) Process: | (6524) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Components\BAE2BC2062E17A349A4992D1428C964C |
| Operation: | write | Name: | 2DE6F49B0797D4E44954ED724539BA0A |
Value: C:\Program Files\Fortinet\FortiClient\ | |||
| (PID) Process: | (6524) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Components\2D32B215BCF6E554BB28AB2F4D4C0723 |
| Operation: | write | Name: | 2DE6F49B0797D4E44954ED724539BA0A |
Value: C:\Program Files\Fortinet\FortiClient\ | |||
| (PID) Process: | (6524) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Components\C715147F8E1E0C04680EAA2133FCFEC9 |
| Operation: | write | Name: | 2DE6F49B0797D4E44954ED724539BA0A |
Value: C:\Program Files\Fortinet\FortiClient\FCDBLog.exe | |||
| (PID) Process: | (6524) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Components\C34524D665DD7934496680EC41A66FD8 |
| Operation: | write | Name: | 2DE6F49B0797D4E44954ED724539BA0A |
Value: C:\Program Files\Fortinet\FortiClient\ | |||
Executable files
292
Suspicious files
336
Text files
153
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6552 | FortiClientVPNOnlineInstaller (2).exe | C:\Users\admin\AppData\Local\Temp\obj_1_a06604 | — | |
MD5:— | SHA256:— | |||
| 6552 | FortiClientVPNOnlineInstaller (2).exe | C:\Users\admin\AppData\Local\Temp\FortiClientVPN.exe | — | |
MD5:— | SHA256:— | |||
| 6188 | FortiClientVPN.exe | C:\Users\admin\AppData\Local\Temp\FCT_{625BC4BA-AC3E-4E4B-9996-EEED9D4287C3}\{D08B55B8-95D0-4C28-B166-BF1848E11FBA}\FortiClientVPN.msi | — | |
MD5:— | SHA256:— | |||
| 6188 | FortiClientVPN.exe | C:\ProgramData\Applications\Cache\{B94F6ED2-7970-4E4D-9445-DE275493ABA0}\7.4.2.1737\FortiClientVPN.msi | — | |
MD5:— | SHA256:— | |||
| 6524 | msiexec.exe | C:\Windows\Installer\14849f.msi | — | |
MD5:— | SHA256:— | |||
| 6552 | FortiClientVPNOnlineInstaller (2).exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\698460A0B6E60F2F602361424D832905_8BB23D43DE574E82F2BEE0DF0EC47EEB | binary | |
MD5:10EC8722E2BCC1FDDB97336698A96E93 | SHA256:0BAC17F8ED4EF52CFFEC20B2929600E8E3F67BEA6602E605CA3CC29A337CC06F | |||
| 6552 | FortiClientVPNOnlineInstaller (2).exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\698460A0B6E60F2F602361424D832905_8BB23D43DE574E82F2BEE0DF0EC47EEB | binary | |
MD5:D6DCD75872CD27510896D98D3F4C1A79 | SHA256:8D812CF0C6B42C4B3DB42D1EBA87AA1890CB8F48594FAFE01C3D77741134FBFE | |||
| 6188 | FortiClientVPN.exe | C:\Users\admin\AppData\Local\Temp\FortiClient00000.log | text | |
MD5:F3B25701FE362EC84616A93A45CE9998 | SHA256:B3D510EF04275CA8E698E5B3CBB0ECE3949EF9252F0CDC839E9EE347409A2209 | |||
| 6552 | FortiClientVPNOnlineInstaller (2).exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\C8E534EE129F27D55460CE17FD628216_1130D9B25898B0DB0D4F04DC5B93F141 | binary | |
MD5:B8067B4E22E2D6BDDBA9A23C0CE91534 | SHA256:8F688C3587C28ACD3D6D07CA6B5CFEB04F785A537995703618DB2D9F367D252A | |||
| 6188 | FortiClientVPN.exe | C:\Users\admin\AppData\Local\Temp\FCT_{625BC4BA-AC3E-4E4B-9996-EEED9D4287C3}\{D08B55B8-95D0-4C28-B166-BF1848E11FBA}\eula.rtf | text | |
MD5:A2D5B9CF17F6130977722E108FD5D23E | SHA256:9BA445C860FC2D1DDB3BBF68EF61C1C314845DD15F4052D470115CFD4DA851D1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
23
TCP/UDP connections
70
DNS requests
29
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | POST | — | 209.40.106.66:80 | http://209.40.106.66/fdsupdate | unknown | — | — | unknown |
4712 | MoUsoCoreWorker.exe | GET | 200 | 88.221.110.122:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | svchost.exe | GET | 200 | 88.221.110.122:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7112 | FortiTray.exe | GET | 200 | 172.217.16.131:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | — | — | whitelisted |
— | — | POST | 200 | 209.40.106.66:80 | http://209.40.106.66/fdsupdate | unknown | — | — | unknown |
7112 | FortiTray.exe | GET | 200 | 142.250.186.131:80 | http://o.pki.goog/wr2/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTQtSEi8EX%2BbYUTXd8%2ByMxD3s1zQQU3hse7XkV1D43JMMhu%2Bw0OW1CsjACEA0ypDTfVoO1CXSLPxUl4PQ%3D | unknown | — | — | whitelisted |
6552 | FortiClientVPNOnlineInstaller (2).exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | unknown | — | — | whitelisted |
6552 | FortiClientVPNOnlineInstaller (2).exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEA8ZK8C1K2FOF0Q2W4wIAOc%3D | unknown | — | — | whitelisted |
4740 | scheduler.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicCodSigPCA2011_2011-07-08.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 88.221.110.122:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | svchost.exe | 88.221.110.122:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
5496 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 2.23.227.215:443 | www.bing.com | Ooredoo Q.S.C. | QA | whitelisted |
— | — | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
1176 | svchost.exe | 40.126.32.68:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
forticlient.fortinet.net |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
1328 | FortiVPN.exe | Misc activity | ET INFO External IP Address Lookup Domain (ipify .org) in TLS SNI |
7112 | FortiTray.exe | Misc activity | ET INFO Google DNS Over HTTPS Certificate Inbound |
7112 | FortiTray.exe | Misc activity | ET INFO Observed Google DNS over HTTPS Domain (dns .google in TLS SNI) |
7112 | FortiTray.exe | Misc activity | ET INFO Google DNS Over HTTPS Certificate Inbound |
1328 | FortiVPN.exe | Misc activity | ET INFO External IP Address Lookup Domain (ipify .org) in TLS SNI |
Process | Message |
|---|---|
msiexec.exe | Failed to release Service
|
FortiClient.exe | [0220/113453.413:ERROR:crash_report_database_win.cc(614)] CreateDirectory C:\Users\admin\AppData\Roaming\FortiClient\logs\trace: The system cannot find the path specified. (0x3)
|
FortiClient.exe | LOG 107 |
FortiClient.exe | LOG 107 |
FortiClient.exe | LOG 107 |
FortiClient.exe | LOG 107 |
FortiClient.exe | LOG 107 |
FortiClient.exe | LOG 107 |
FortiClient.exe | LOG 107 |
FortiClient.exe | LOG 107 |