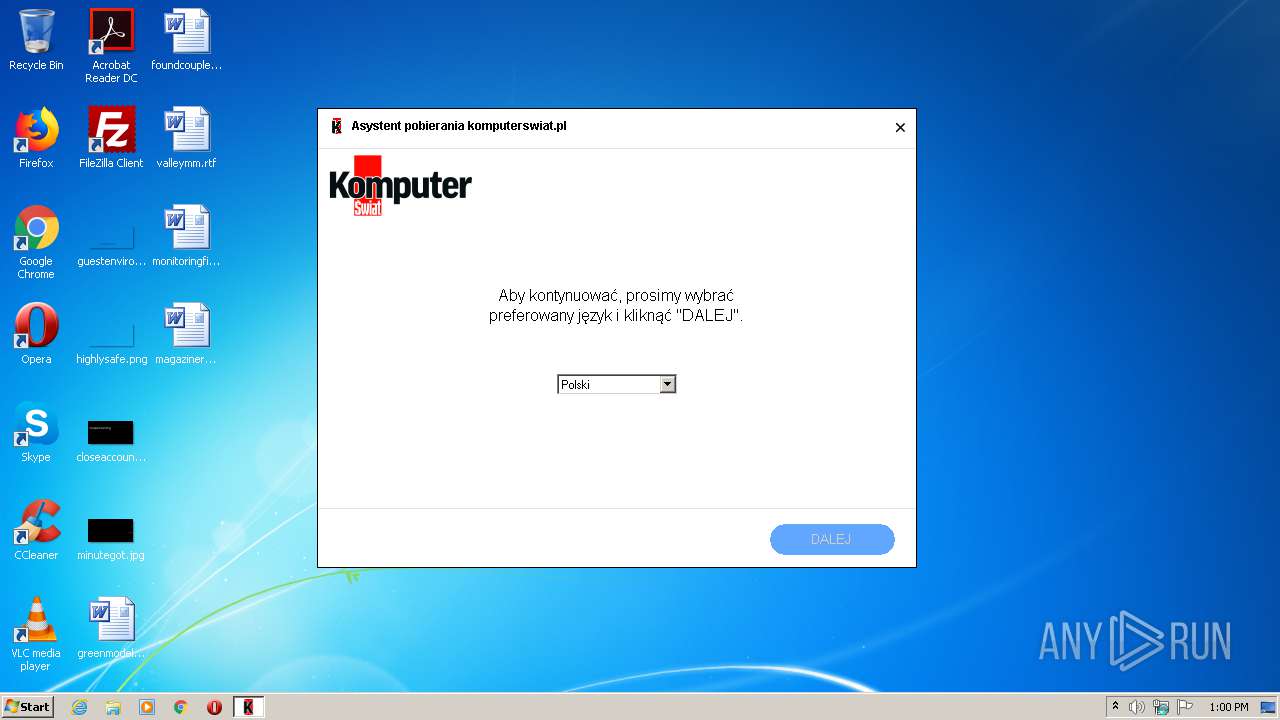
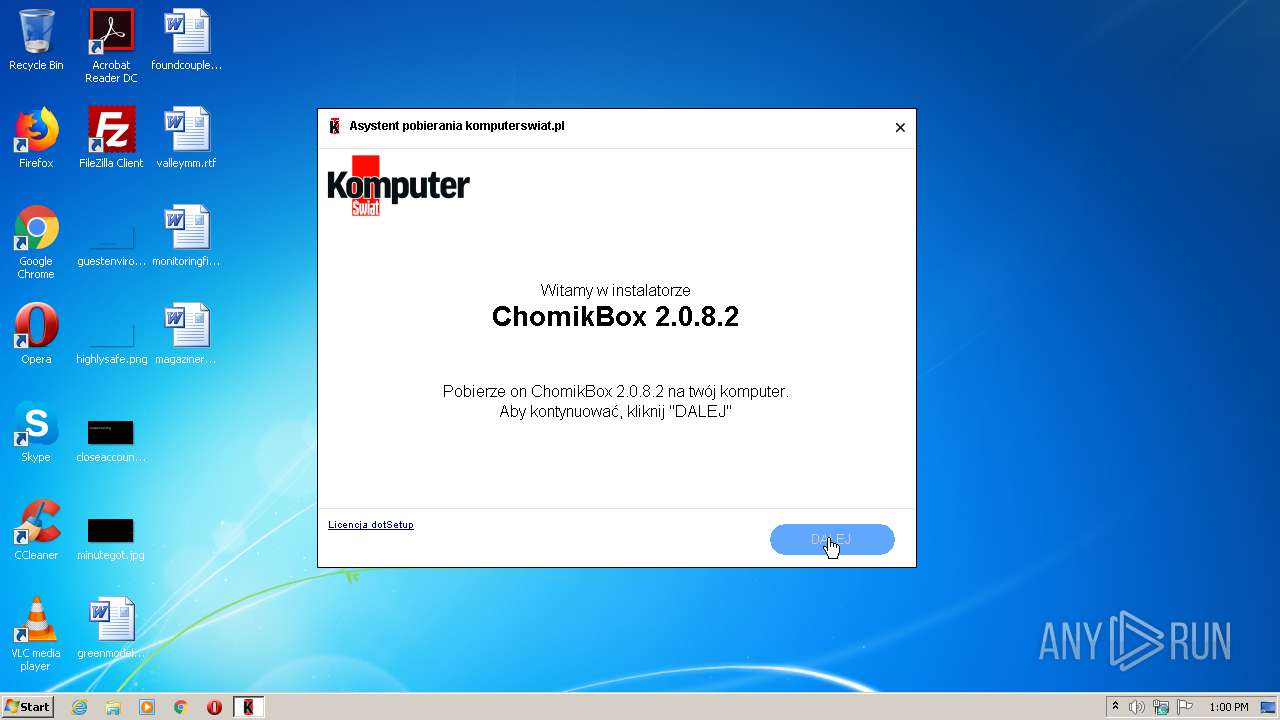
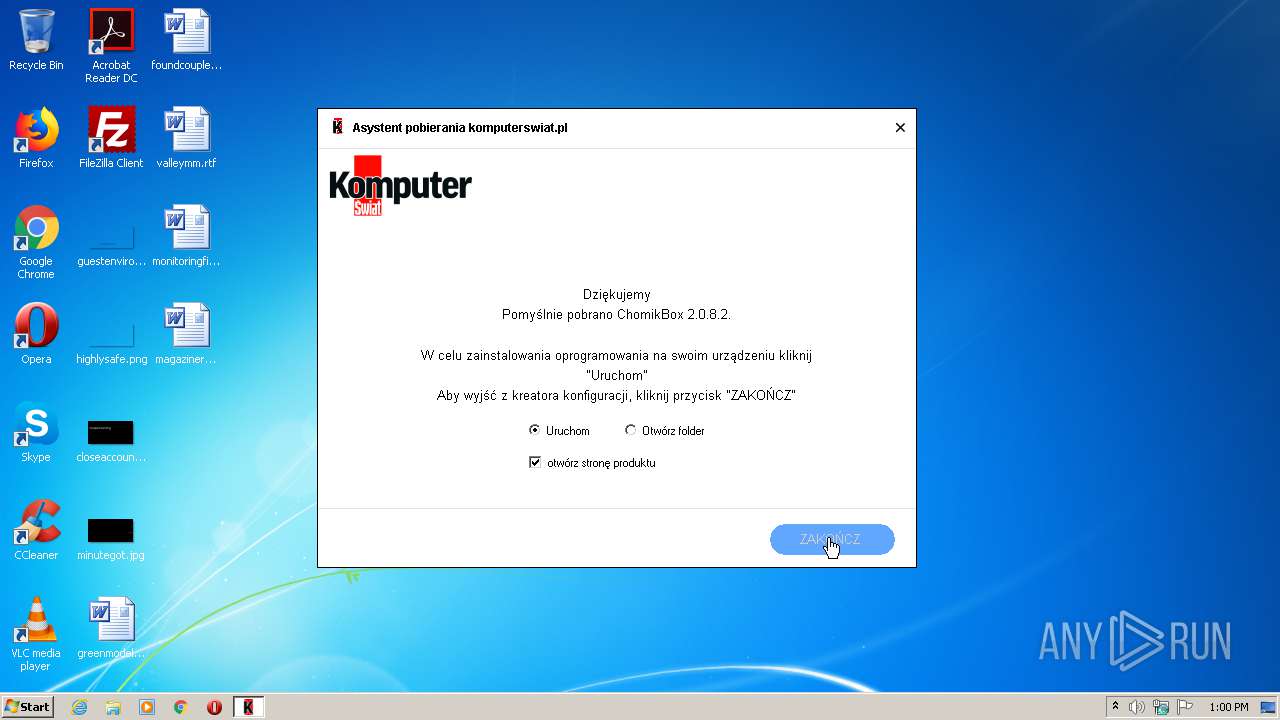
| File name: | chomikbox-2-0-8-2-ks_v0.75.035.702.6.exe |
| Full analysis: | https://app.any.run/tasks/b1820c59-f0f0-4eb4-aaac-95e82b01ff67 |
| Verdict: | Malicious activity |
| Analysis date: | March 16, 2021, 13:00:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 4335AA0C887E3A8036B911C6E7B9511F |
| SHA1: | 0CE0D0892B47B536183E452CE20DB758ADE5326C |
| SHA256: | 2E44291101B394306111B01C422654CA26AAD786C7FBB38CBE4E0D2DABBE6D42 |
| SSDEEP: | 6144:7jG9wdH/i86u8LK34krStiYmH7KyXlxkfm9MF3yKXMzeDQaTDXCN/LK34krStiYp:7jGAt6fHfXKLHcH1HUirVo |
MALICIOUS
Changes settings of System certificates
- chomikbox-2-0-8-2-ks_v0.75.035.702.6.exe (PID: 2464)
SUSPICIOUS
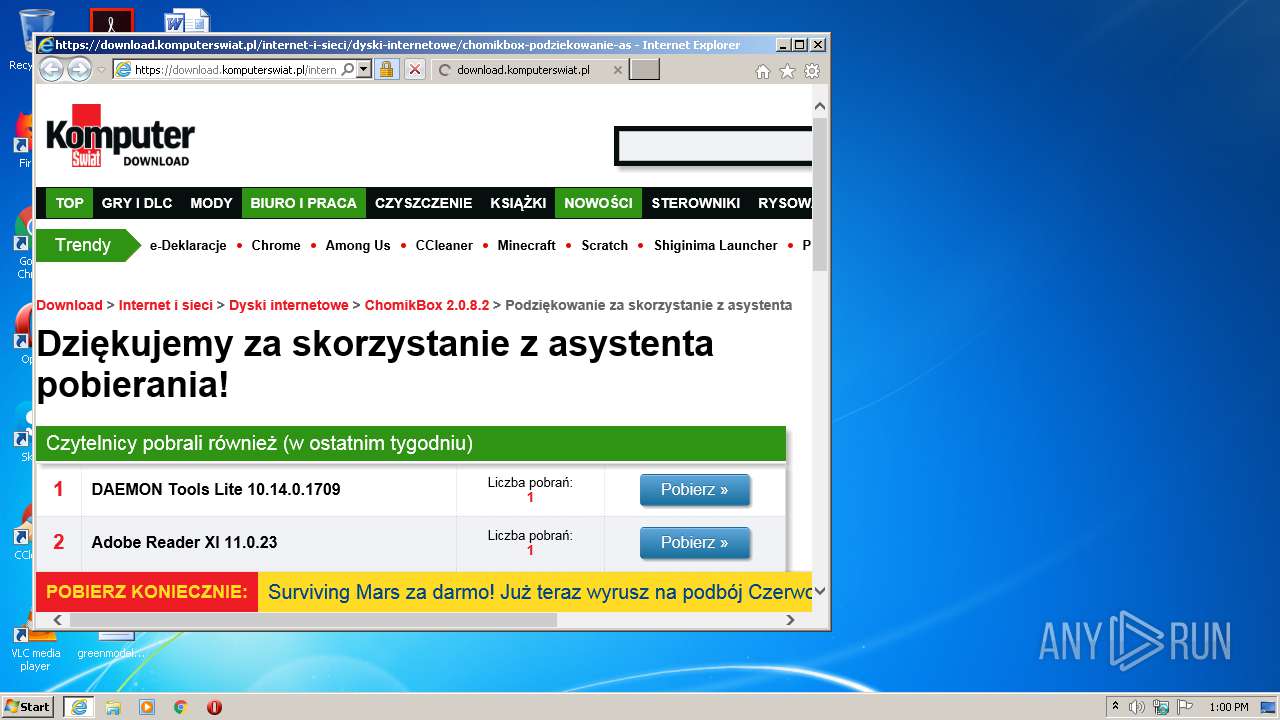
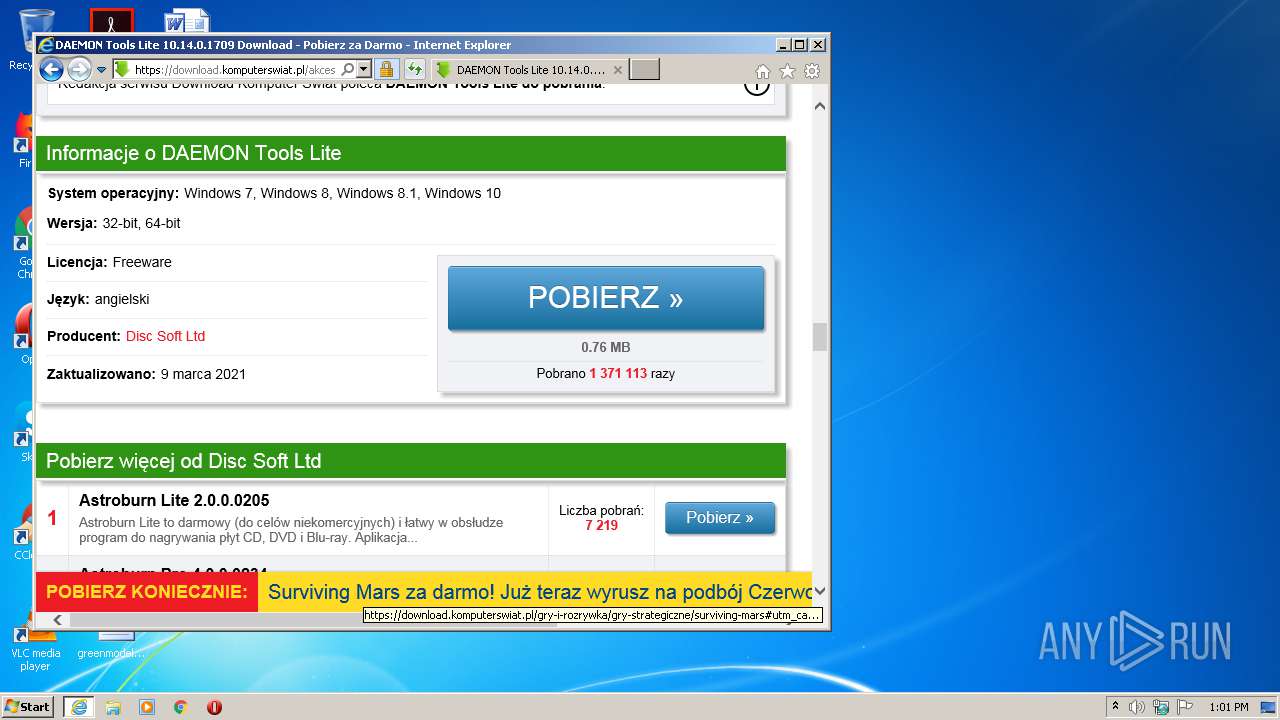
Starts Internet Explorer
- chomikbox-2-0-8-2-ks_v0.75.035.702.6.exe (PID: 2464)
Adds / modifies Windows certificates
- chomikbox-2-0-8-2-ks_v0.75.035.702.6.exe (PID: 2464)
INFO
Reads settings of System Certificates
- chomikbox-2-0-8-2-ks_v0.75.035.702.6.exe (PID: 2464)
- iexplore.exe (PID: 2684)
Changes internet zones settings
- iexplore.exe (PID: 2532)
Application launched itself
- iexplore.exe (PID: 2532)
Reads internet explorer settings
- iexplore.exe (PID: 2684)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2684)
Changes settings of System certificates
- iexplore.exe (PID: 2684)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:03:07 14:17:49+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 996864 |
| InitializedDataSize: | 322560 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xf543e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.88.5.7737 |
| ProductVersionNumber: | 1.88.5.7737 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | Product Installer |
| CompanyName: | - |
| FileDescription: | Product Installer |
| FileVersion: | 1.88.5.7737 |
| InternalName: | komputerswiat.pl.exe |
| LegalCopyright: | Copyright dotSetup.io Open Source Project |
| LegalTrademarks: | - |
| OriginalFileName: | komputerswiat.pl.exe |
| ProductName: | Product Installer |
| ProductVersion: | 1.88.5.7737 |
| AssemblyVersion: | 1.88.5.7737 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 07-Mar-2021 13:17:49 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 07-Mar-2021 13:17:49 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x000F3454 | 0x000F3600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.16602 |
.rsrc | 0x000F6000 | 0x0004E912 | 0x0004EA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.94626 |
.reloc | 0x00146000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.99436 | 3132 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 4.26407 | 2440 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 4.1107 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 3.53253 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 3.4777 | 16936 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 3.20475 | 38056 | UNKNOWN | UNKNOWN | RT_ICON |
7 | 3.2231 | 67624 | UNKNOWN | UNKNOWN | RT_ICON |
8 | 3.22825 | 152104 | UNKNOWN | UNKNOWN | RT_ICON |
9 | 7.96026 | 24702 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 3.04988 | 132 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
45
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2452 | "C:\Users\admin\AppData\Local\Temp\chomikbox-2-0-8-2-ks_v0.75.035.702.6.exe" | C:\Users\admin\AppData\Local\Temp\chomikbox-2-0-8-2-ks_v0.75.035.702.6.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Product Installer Exit code: 0 Version: 1.88.5.7737 | |||||||||||||||
| 2464 | "C:\Users\admin\AppData\Local\Temp\chomikbox-2-0-8-2-ks_v0.75.035.702.6.exe" | C:\Users\admin\AppData\Local\Temp\chomikbox-2-0-8-2-ks_v0.75.035.702.6.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Product Installer Exit code: 0 Version: 1.88.5.7737 Modules
| |||||||||||||||
| 2532 | "C:\Program Files\Internet Explorer\iexplore.exe" https://download.komputerswiat.pl/internet-i-sieci/dyski-internetowe/chomikbox-podziekowanie-asystent | C:\Program Files\Internet Explorer\iexplore.exe | chomikbox-2-0-8-2-ks_v0.75.035.702.6.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2684 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2532 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
563
Read events
454
Write events
108
Delete events
1
Modification events
| (PID) Process: | (2464) chomikbox-2-0-8-2-ks_v0.75.035.702.6.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\ASP.NET_4.0.30319\Names |
| Operation: | write | Name: | QNnuDyjew5qmvqZxJtVaaDdDz17DCpnRB3dU6NnNQoNVrNBAyh5Od1tTe5kMVAM6Mkn1AOsSeDDZ4QOsrgRBy5wJzpKN0EG7qFSkYcHCDd8bpVtvdONeYb |
Value: 2464 | |||
| (PID) Process: | (2464) chomikbox-2-0-8-2-ks_v0.75.035.702.6.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\chomikbox-2-0-8-2-ks_v0_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2464) chomikbox-2-0-8-2-ks_v0.75.035.702.6.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\chomikbox-2-0-8-2-ks_v0_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2464) chomikbox-2-0-8-2-ks_v0.75.035.702.6.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\chomikbox-2-0-8-2-ks_v0_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2464) chomikbox-2-0-8-2-ks_v0.75.035.702.6.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\chomikbox-2-0-8-2-ks_v0_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2464) chomikbox-2-0-8-2-ks_v0.75.035.702.6.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\chomikbox-2-0-8-2-ks_v0_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2464) chomikbox-2-0-8-2-ks_v0.75.035.702.6.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\chomikbox-2-0-8-2-ks_v0_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2464) chomikbox-2-0-8-2-ks_v0.75.035.702.6.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\chomikbox-2-0-8-2-ks_v0_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2464) chomikbox-2-0-8-2-ks_v0.75.035.702.6.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\chomikbox-2-0-8-2-ks_v0_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2464) chomikbox-2-0-8-2-ks_v0.75.035.702.6.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\chomikbox-2-0-8-2-ks_v0_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
Executable files
0
Suspicious files
13
Text files
12
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2684 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\CabFC3A.tmp | — | |
MD5:— | SHA256:— | |||
| 2684 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\TarFC3B.tmp | — | |
MD5:— | SHA256:— | |||
| 2684 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B398B80134F72209547439DB21AB308D_9487BC0D4381A7CDEB9A8CC43F66D27C | binary | |
MD5:6B679B8DD4CFA82DEA18F9BC06BC45BE | SHA256:70CEBB8FB1F9F5A3B753F836FA2FECD293C35B8AEEEB8AC768A920AAE6ADE258 | |||
| 2684 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\program[1].css | text | |
MD5:C987041BD0823CD9659FBB1F813D72E1 | SHA256:2B6D165A4EC58EF25AB223167F094C87E1193FFEA9596F27F75A58C829E30A99 | |||
| 2684 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\4344B8AF97AF3A423D9EE52899963CDE_CC35AD600E92FE357702D189E8696FB7 | binary | |
MD5:4199B9F45CB19ED5E18C3FA042A54E2F | SHA256:5281DCB30BCCE628F467AA3A72D3B29EB8330F5833CB55587E065B6A13B21889 | |||
| 2684 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\program[1].js | html | |
MD5:4ABA69B692EED7FD6F18BE9EAD2BF18C | SHA256:375A9B315FD49BF5F49D3DDB0A58BB2F8914F5541FC76C4FD4C5939658C4C5A3 | |||
| 2684 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B398B80134F72209547439DB21AB308D_9487BC0D4381A7CDEB9A8CC43F66D27C | der | |
MD5:687EA658DF2D0E8B3B0C90592285CA2D | SHA256:4077F084E3DA7BA954B7341B3487515A7103FE39666F85C97A7B02D71AFA8491 | |||
| 2684 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\4344B8AF97AF3A423D9EE52899963CDE_CC35AD600E92FE357702D189E8696FB7 | der | |
MD5:64D5F171082C0CA3A6C5B1F670F037E1 | SHA256:B2E0053EFEF24E9786A1F8D70FAEEF376FDB19DBAE43E2E1954B9407D1631D6E | |||
| 2684 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CC197601BE0898B7B0FCC91FA15D8A69_86E94C22F35768FEEA4B871CD37D6677 | binary | |
MD5:0C1B266A17CB09621F3F7122C071DD08 | SHA256:26D5B5FAA30F28F286A58979B540D10FA1CB63A1CD553969F36DB4320A2BE37A | |||
| 2684 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\gtm[1].js | text | |
MD5:F355D6B02DFF5DA4F6366E2F33D11500 | SHA256:1773A345BC6D8BE9D5AB9E7AF416A773359D07E8E22D7ABAF23177A1DD51216A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
21
DNS requests
12
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2684 | iexplore.exe | GET | 200 | 172.217.20.3:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEECx%2Fl4bakX1AwAAAADLnko%3D | US | der | 471 b | whitelisted |
2532 | iexplore.exe | GET | 200 | 13.107.21.200:80 | http://www.bing.com/favicon.ico | US | image | 4.19 Kb | whitelisted |
2684 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://status.geotrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR3enuod9bxDxzpICGW%2B2sabjf17QQUkFj%2FsJx1qFFUd7Ht8qNDFjiebMUCEAj19pz1MuvejhQ2bMKhzzY%3D | US | der | 471 b | whitelisted |
2684 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAVG%2Fhgj9%2BGUHaOfzhTEYXM%3D | US | der | 471 b | whitelisted |
2464 | chomikbox-2-0-8-2-ks_v0.75.035.702.6.exe | GET | 301 | 213.180.141.188:80 | http://files-download.playpc.pl/InternetISieci/DyskiInternetowe/Chomikbox/chomikbox_1.msi | PL | html | 162 b | shared |
2684 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://status.geotrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR3enuod9bxDxzpICGW%2B2sabjf17QQUkFj%2FsJx1qFFUd7Ht8qNDFjiebMUCEAj19pz1MuvejhQ2bMKhzzY%3D | US | der | 471 b | whitelisted |
2684 | iexplore.exe | GET | 200 | 172.217.20.3:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
2684 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAVG%2Fhgj9%2BGUHaOfzhTEYXM%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2464 | chomikbox-2-0-8-2-ks_v0.75.035.702.6.exe | 212.77.101.100:443 | wp.hit.gemius.pl | Wirtualna Polska S.A. | PL | unknown |
2464 | chomikbox-2-0-8-2-ks_v0.75.035.702.6.exe | 13.225.84.4:443 | d2zwxa7ylh6bmb.cloudfront.net | — | US | unknown |
— | — | 213.180.141.188:443 | files-download.playpc.pl | Grupa Onet.pl S.A. | PL | suspicious |
2464 | chomikbox-2-0-8-2-ks_v0.75.035.702.6.exe | 213.180.141.188:443 | files-download.playpc.pl | Grupa Onet.pl S.A. | PL | suspicious |
2464 | chomikbox-2-0-8-2-ks_v0.75.035.702.6.exe | 213.180.141.188:80 | files-download.playpc.pl | Grupa Onet.pl S.A. | PL | suspicious |
2684 | iexplore.exe | 213.180.141.155:443 | download.komputerswiat.pl | Grupa Onet.pl S.A. | PL | unknown |
— | — | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2684 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2684 | iexplore.exe | 142.250.186.40:443 | www.googletagmanager.com | Google Inc. | US | suspicious |
2684 | iexplore.exe | 172.217.20.3:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
d2zwxa7ylh6bmb.cloudfront.net |
| whitelisted |
wp.hit.gemius.pl |
| unknown |
files-download.playpc.pl |
| shared |
download.komputerswiat.pl |
| malicious |
ocsp.digicert.com |
| whitelisted |
status.geotrust.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
— | — | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2464 | chomikbox-2-0-8-2-ks_v0.75.035.702.6.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2464 | chomikbox-2-0-8-2-ks_v0.75.035.702.6.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |