| File name: | SecuriteInfo.com.Trojan.PWS.Lumma.822.15822.29024 |
| Full analysis: | https://app.any.run/tasks/b95a0e46-4e34-4e32-a5f9-d3b05bd41ce7 |
| Verdict: | Malicious activity |
| Analysis date: | May 15, 2025, 15:36:08 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 10 sections |
| MD5: | F7E561A8281C305E47BB461232173FAC |
| SHA1: | 6074567B3AFD4B0DCE5E95BAF35B0703B07BBB0F |
| SHA256: | 2E349D637A8CE63A26B6FF2223EB503ABFB25686B0947E32368F346CA1FDCCC5 |
| SSDEEP: | 98304:AbU856cbwQGHg5TcZSFPLyU2GcoXJEU7iBvZ0fqL0XLJM0u90I2PmfUNQDE3kRDX:Ckonf3N0 |
MALICIOUS
Executing a file with an untrusted certificate
- SecuriteInfo.com.Trojan.PWS.Lumma.822.15822.29024.exe (PID: 5332)
- SecuriteInfo.com.Trojan.PWS.Lumma.822.15822.29024.exe (PID: 4892)
SUSPICIOUS
Executable content was dropped or overwritten
- SecuriteInfo.com.Trojan.PWS.Lumma.822.15822.29024.exe (PID: 5332)
- SecuriteInfo.com.Trojan.PWS.Lumma.822.15822.29024.exe (PID: 4892)
- SecuriteInfo.com.Trojan.PWS.Lumma.822.15822.29024.tmp (PID: 900)
Reads security settings of Internet Explorer
- SecuriteInfo.com.Trojan.PWS.Lumma.822.15822.29024.tmp (PID: 6872)
Reads the Windows owner or organization settings
- SecuriteInfo.com.Trojan.PWS.Lumma.822.15822.29024.tmp (PID: 900)
Windows service management via SC.EXE
- sc.exe (PID: 6132)
INFO
Create files in a temporary directory
- SecuriteInfo.com.Trojan.PWS.Lumma.822.15822.29024.exe (PID: 5332)
- SecuriteInfo.com.Trojan.PWS.Lumma.822.15822.29024.exe (PID: 4892)
- SecuriteInfo.com.Trojan.PWS.Lumma.822.15822.29024.tmp (PID: 900)
Checks supported languages
- SecuriteInfo.com.Trojan.PWS.Lumma.822.15822.29024.tmp (PID: 6872)
- SecuriteInfo.com.Trojan.PWS.Lumma.822.15822.29024.exe (PID: 5332)
- SecuriteInfo.com.Trojan.PWS.Lumma.822.15822.29024.exe (PID: 4892)
- SecuriteInfo.com.Trojan.PWS.Lumma.822.15822.29024.tmp (PID: 900)
Reads the computer name
- SecuriteInfo.com.Trojan.PWS.Lumma.822.15822.29024.tmp (PID: 6872)
- SecuriteInfo.com.Trojan.PWS.Lumma.822.15822.29024.tmp (PID: 900)
Process checks computer location settings
- SecuriteInfo.com.Trojan.PWS.Lumma.822.15822.29024.tmp (PID: 6872)
Detects InnoSetup installer (YARA)
- SecuriteInfo.com.Trojan.PWS.Lumma.822.15822.29024.exe (PID: 5332)
- SecuriteInfo.com.Trojan.PWS.Lumma.822.15822.29024.tmp (PID: 6872)
- SecuriteInfo.com.Trojan.PWS.Lumma.822.15822.29024.exe (PID: 4892)
- SecuriteInfo.com.Trojan.PWS.Lumma.822.15822.29024.tmp (PID: 900)
Reads the software policy settings
- slui.exe (PID: 1328)
Checks proxy server information
- slui.exe (PID: 1328)
Compiled with Borland Delphi (YARA)
- SecuriteInfo.com.Trojan.PWS.Lumma.822.15822.29024.tmp (PID: 6872)
- SecuriteInfo.com.Trojan.PWS.Lumma.822.15822.29024.tmp (PID: 900)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (67.7) |
|---|---|---|
| .exe | | | Win32 EXE PECompact compressed (generic) (25.6) |
| .exe | | | Win32 Executable (generic) (2.7) |
| .exe | | | Win16/32 Executable Delphi generic (1.2) |
| .exe | | | Generic Win/DOS Executable (1.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:10:12 11:15:57+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 682496 |
| InitializedDataSize: | 105984 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xa7ed0 |
| OSVersion: | 6 |
| ImageVersion: | 6 |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 5.0.5.235 |
| ProductVersionNumber: | 5.0.5.235 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
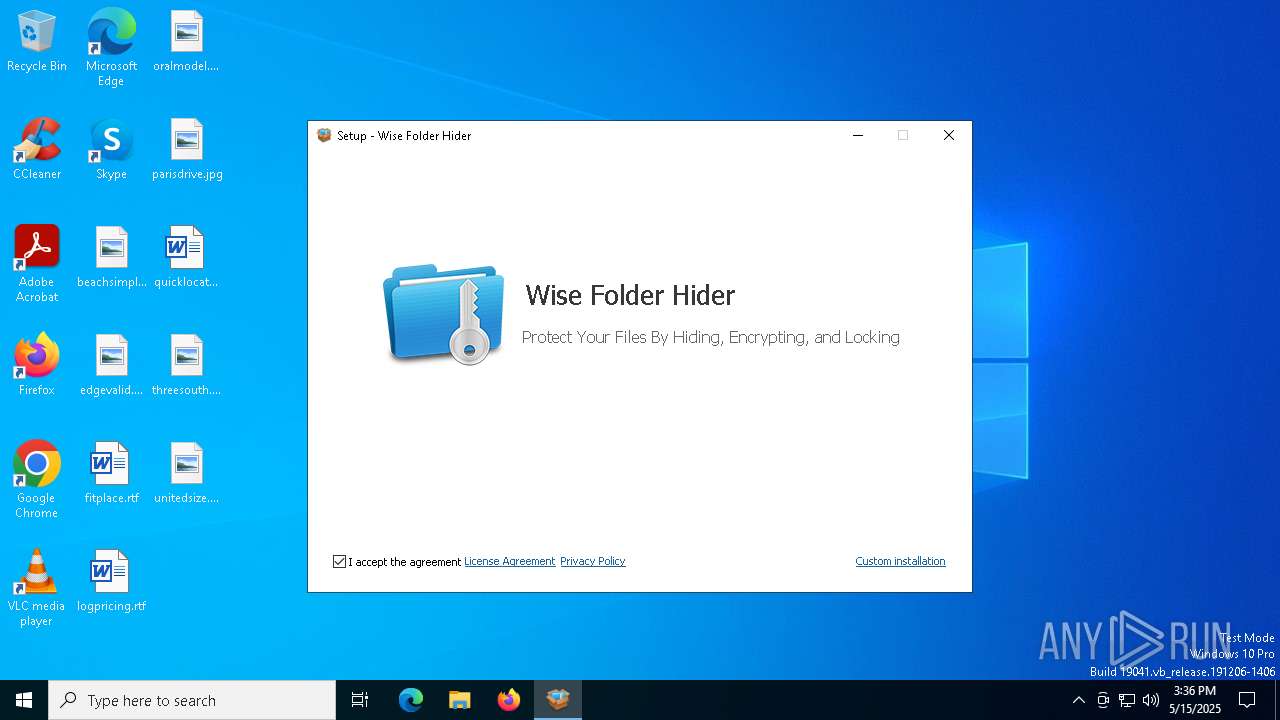
| CompanyName: | WiseCleaner.com |
| FileDescription: | Wise Folder Hider |
| FileVersion: | 5.0.5 |
| LegalCopyright: | WiseCleaner.com |
| OriginalFileName: | |
| ProductName: | Wise Folder Hider |
| ProductVersion: | 5.0.5 |
Total processes
138
Monitored processes
7
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 900 | "C:\Users\admin\AppData\Local\Temp\is-SJICK.tmp\SecuriteInfo.com.Trojan.PWS.Lumma.822.15822.29024.tmp" /SL5="$90296,5967459,789504,C:\Users\admin\AppData\Local\Temp\SecuriteInfo.com.Trojan.PWS.Lumma.822.15822.29024.exe" /SPAWNWND=$1602DC /NOTIFYWND=$4030A | C:\Users\admin\AppData\Local\Temp\is-SJICK.tmp\SecuriteInfo.com.Trojan.PWS.Lumma.822.15822.29024.tmp | SecuriteInfo.com.Trojan.PWS.Lumma.822.15822.29024.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Version: 51.1052.0.0 Modules
| |||||||||||||||
| 1328 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4892 | "C:\Users\admin\AppData\Local\Temp\SecuriteInfo.com.Trojan.PWS.Lumma.822.15822.29024.exe" /SPAWNWND=$1602DC /NOTIFYWND=$4030A | C:\Users\admin\AppData\Local\Temp\SecuriteInfo.com.Trojan.PWS.Lumma.822.15822.29024.exe | SecuriteInfo.com.Trojan.PWS.Lumma.822.15822.29024.tmp | ||||||||||||
User: admin Company: WiseCleaner.com Integrity Level: HIGH Description: Wise Folder Hider Version: 5.0.5 Modules
| |||||||||||||||
| 5332 | "C:\Users\admin\AppData\Local\Temp\SecuriteInfo.com.Trojan.PWS.Lumma.822.15822.29024.exe" | C:\Users\admin\AppData\Local\Temp\SecuriteInfo.com.Trojan.PWS.Lumma.822.15822.29024.exe | explorer.exe | ||||||||||||
User: admin Company: WiseCleaner.com Integrity Level: MEDIUM Description: Wise Folder Hider Version: 5.0.5 Modules
| |||||||||||||||
| 6132 | "sc.exe" start wisefs | C:\Windows\SysWOW64\sc.exe | — | SecuriteInfo.com.Trojan.PWS.Lumma.822.15822.29024.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 1060 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6468 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6872 | "C:\Users\admin\AppData\Local\Temp\is-EVH59.tmp\SecuriteInfo.com.Trojan.PWS.Lumma.822.15822.29024.tmp" /SL5="$4030A,5967459,789504,C:\Users\admin\AppData\Local\Temp\SecuriteInfo.com.Trojan.PWS.Lumma.822.15822.29024.exe" | C:\Users\admin\AppData\Local\Temp\is-EVH59.tmp\SecuriteInfo.com.Trojan.PWS.Lumma.822.15822.29024.tmp | — | SecuriteInfo.com.Trojan.PWS.Lumma.822.15822.29024.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Version: 51.1052.0.0 Modules
| |||||||||||||||
Total events
837
Read events
837
Write events
0
Delete events
0
Modification events
Executable files
3
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 900 | SecuriteInfo.com.Trojan.PWS.Lumma.822.15822.29024.tmp | C:\Users\admin\AppData\Local\Temp\is-0DA9J.tmp\_isetup\_setup64.tmp | executable | |
MD5:E4211D6D009757C078A9FAC7FF4F03D4 | SHA256:388A796580234EFC95F3B1C70AD4CB44BFDDC7BA0F9203BF4902B9929B136F95 | |||
| 4892 | SecuriteInfo.com.Trojan.PWS.Lumma.822.15822.29024.exe | C:\Users\admin\AppData\Local\Temp\is-SJICK.tmp\SecuriteInfo.com.Trojan.PWS.Lumma.822.15822.29024.tmp | executable | |
MD5:5BD71F6C3B6FAC7FDAA75633F0AF9F52 | SHA256:0FC8B95D74EC17858ECA1A81A053BB02AD0C40CC9163A6B2A839F7703F098308 | |||
| 900 | SecuriteInfo.com.Trojan.PWS.Lumma.822.15822.29024.tmp | C:\Users\admin\AppData\Local\Temp\is-0DA9J.tmp\license.txt | text | |
MD5:4A0F1A666912E64F1BA811FC24D7135F | SHA256:D6B418C619BA7456B594DFF10C3FACE4AC28609A64F2BF5E635292D7FF4F57E5 | |||
| 900 | SecuriteInfo.com.Trojan.PWS.Lumma.822.15822.29024.tmp | C:\Users\admin\AppData\Local\Temp\is-0DA9J.tmp\Icon_128.bmp | image | |
MD5:FCAF2D7E995620747896987C88270A42 | SHA256:A3959B1A40B71908B24DBEA5972DE0F5FFADAEE5B15E1D3CE8F976EFC432B390 | |||
| 5332 | SecuriteInfo.com.Trojan.PWS.Lumma.822.15822.29024.exe | C:\Users\admin\AppData\Local\Temp\is-EVH59.tmp\SecuriteInfo.com.Trojan.PWS.Lumma.822.15822.29024.tmp | executable | |
MD5:5BD71F6C3B6FAC7FDAA75633F0AF9F52 | SHA256:0FC8B95D74EC17858ECA1A81A053BB02AD0C40CC9163A6B2A839F7703F098308 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
19
DNS requests
14
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.19.11.105:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.19.11.105:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4620 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4620 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.19.11.105:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
— | — | 2.19.11.105:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6544 | svchost.exe | 40.126.32.133:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |