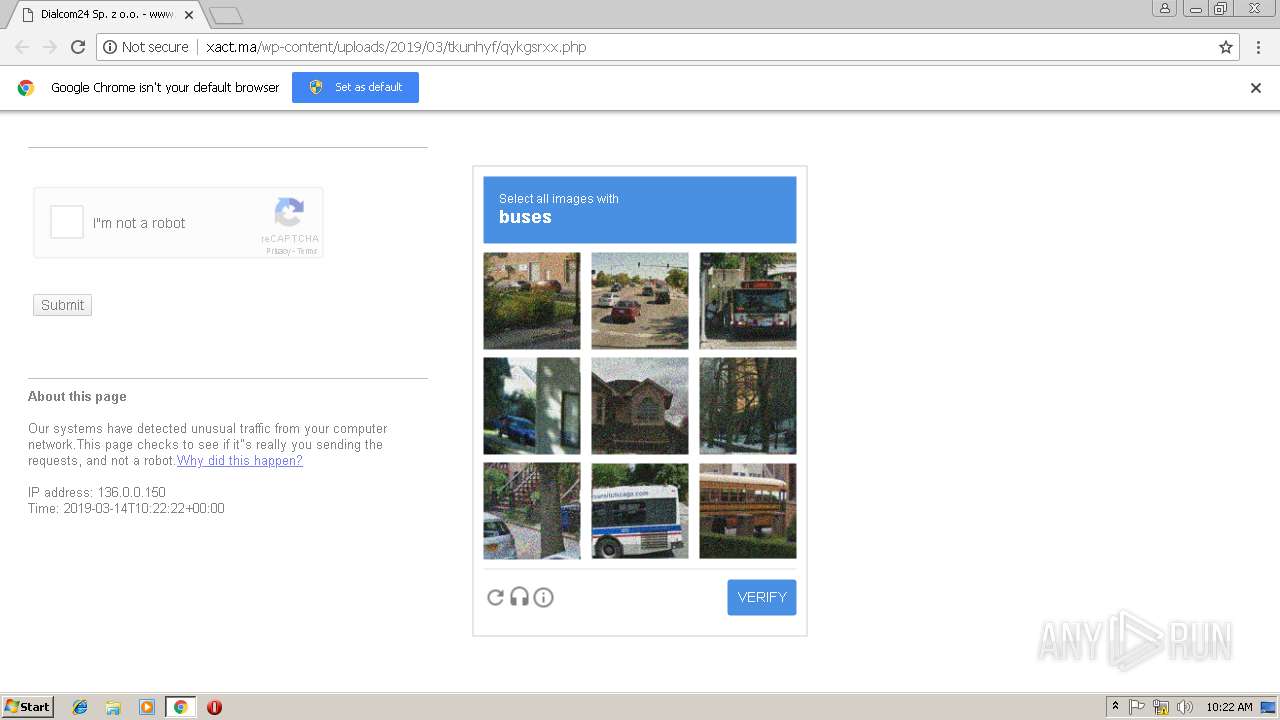
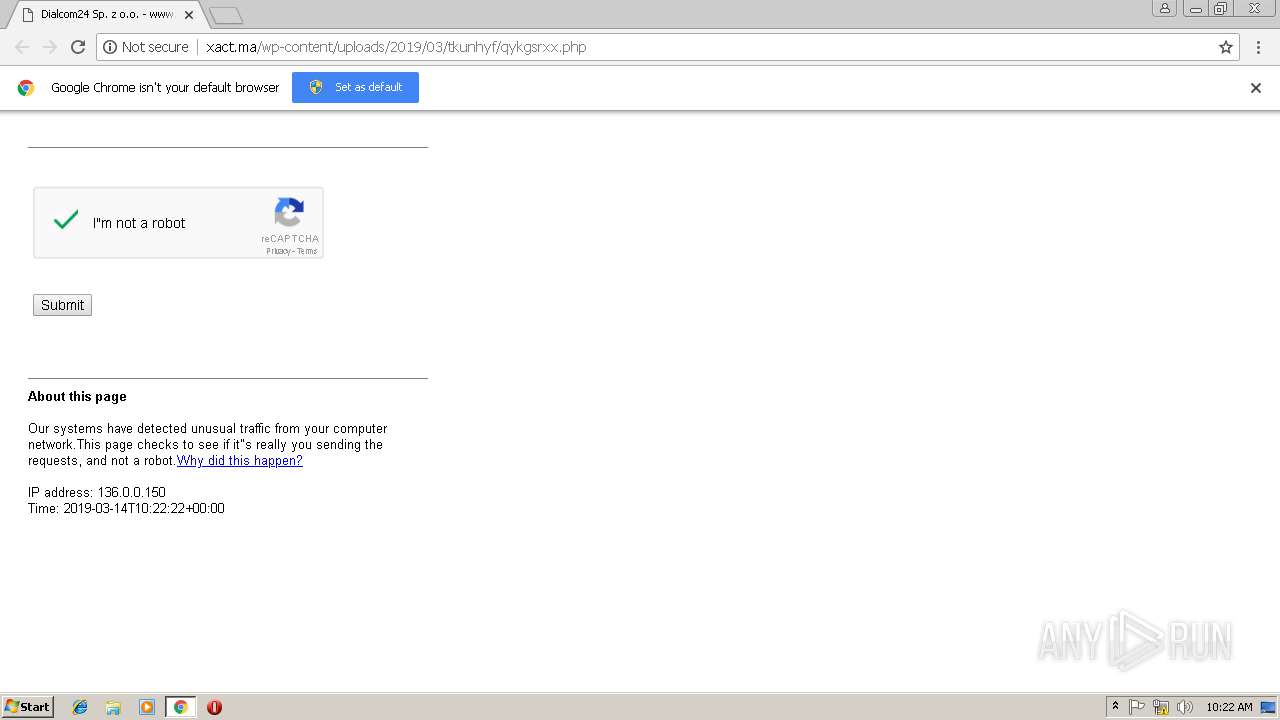
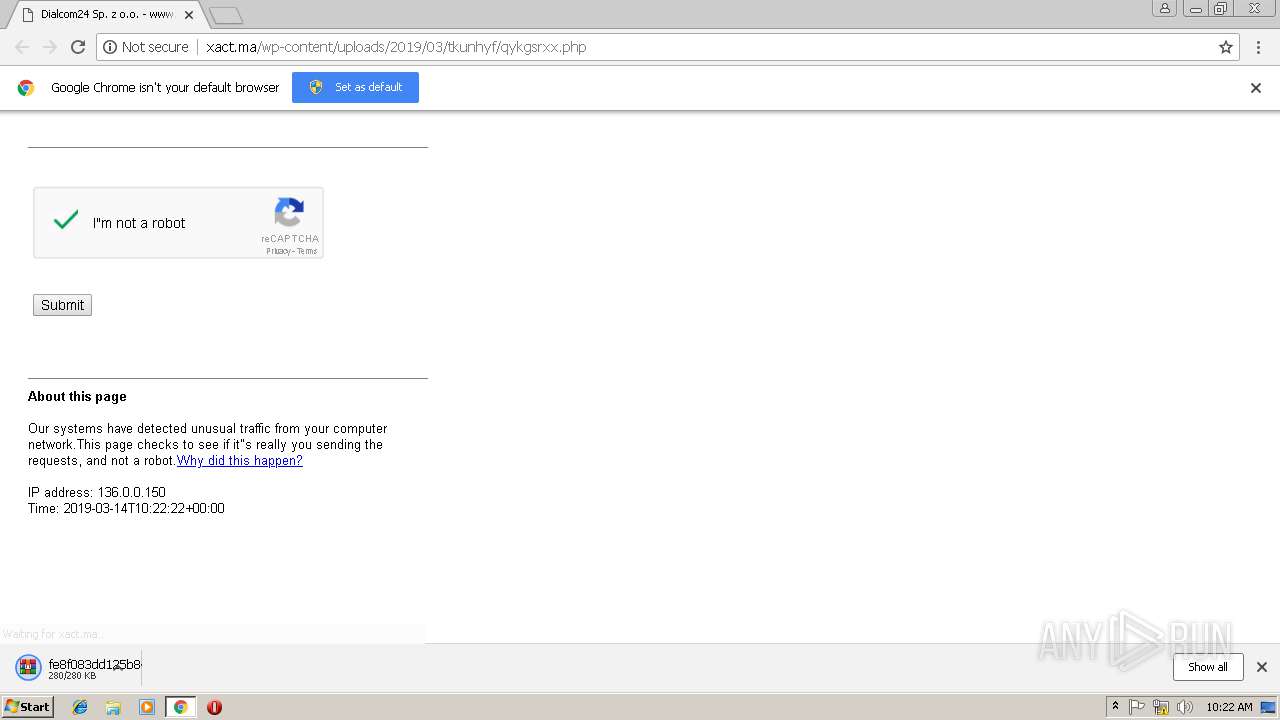
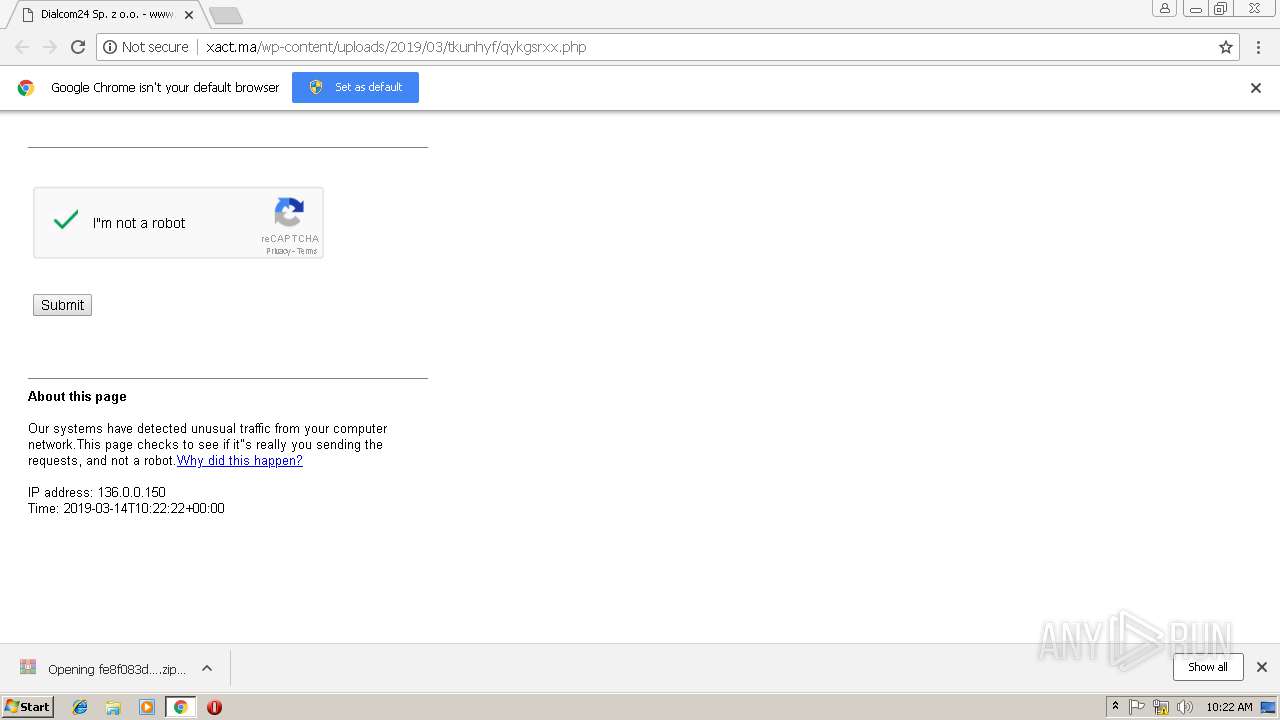
| URL: | http://xact.ma/wp-content/uploads/2019/03/tkunhyf/qykgsrxx.php |
| Full analysis: | https://app.any.run/tasks/e01238ed-636e-4479-8b8b-c34f127fea79 |
| Verdict: | Malicious activity |
| Analysis date: | March 14, 2019, 10:22:06 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 9724E7E6812455A3E8E9AD783CA9B49F |
| SHA1: | 5432DDFF1F472DE16C75473337757C6253D7F98A |
| SHA256: | 2E2D14D8267E110F092772C4527A4FF4D8E131CA932E26722B8C8780FFA6B9F3 |
| SSDEEP: | 3:N1KGEaK/GKlAQyX28KmKI7:CGXK/dlAZGqKi |
MALICIOUS
Registers / Runs the DLL via REGSVR32.EXE
- WScript.exe (PID: 3752)
Loads dropped or rewritten executable
- rundll32.exe (PID: 3164)
- regsvr32.exe (PID: 2332)
SUSPICIOUS
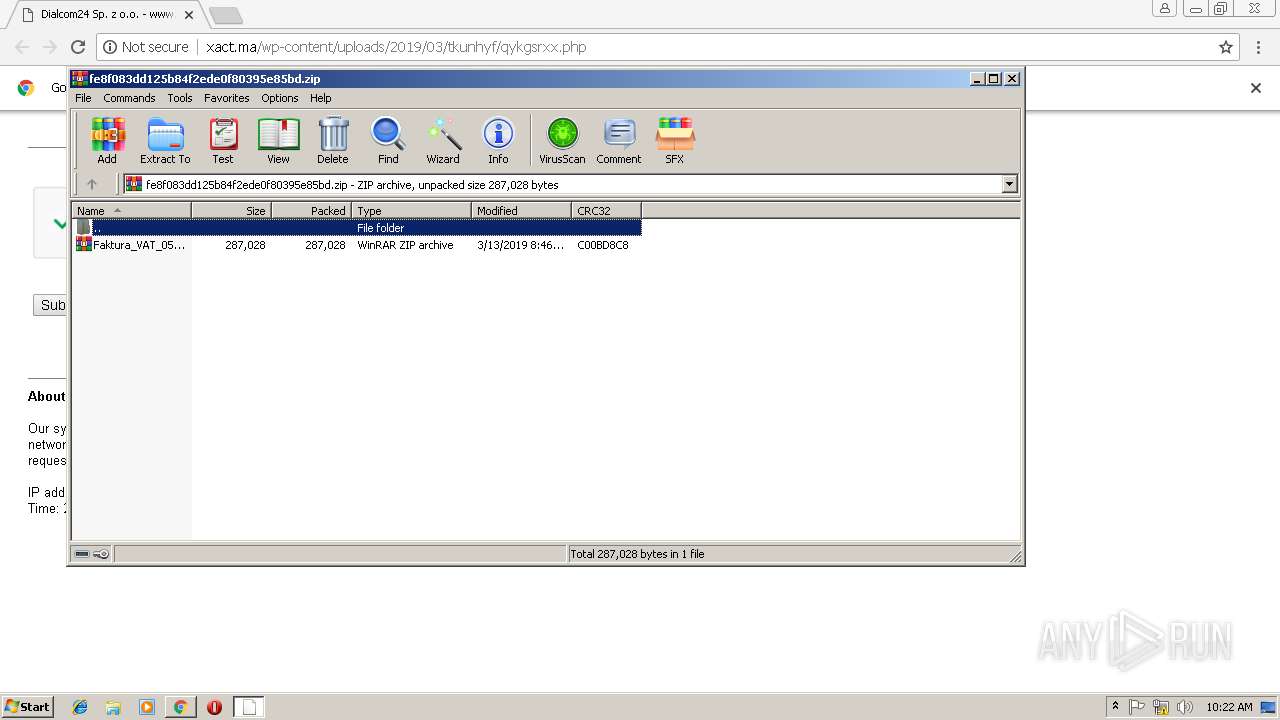
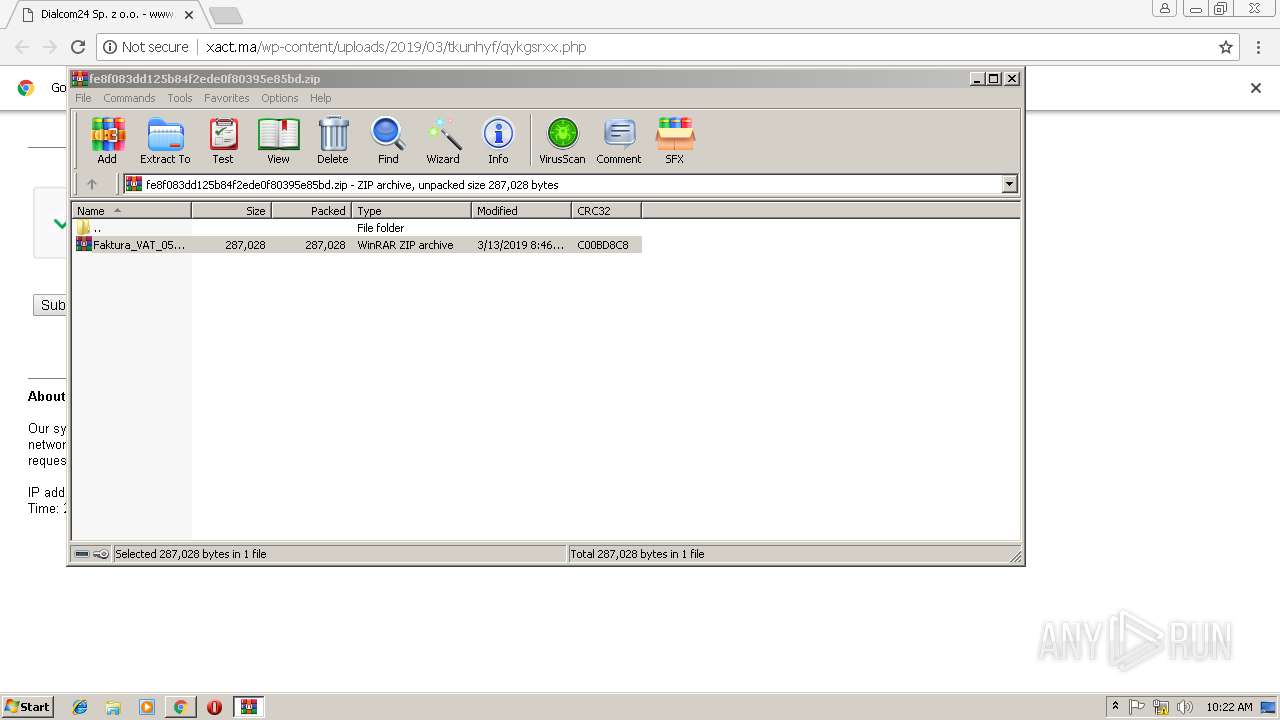
Application launched itself
- WinRAR.exe (PID: 3432)
Uses RUNDLL32.EXE to load library
- regsvr32.exe (PID: 2332)
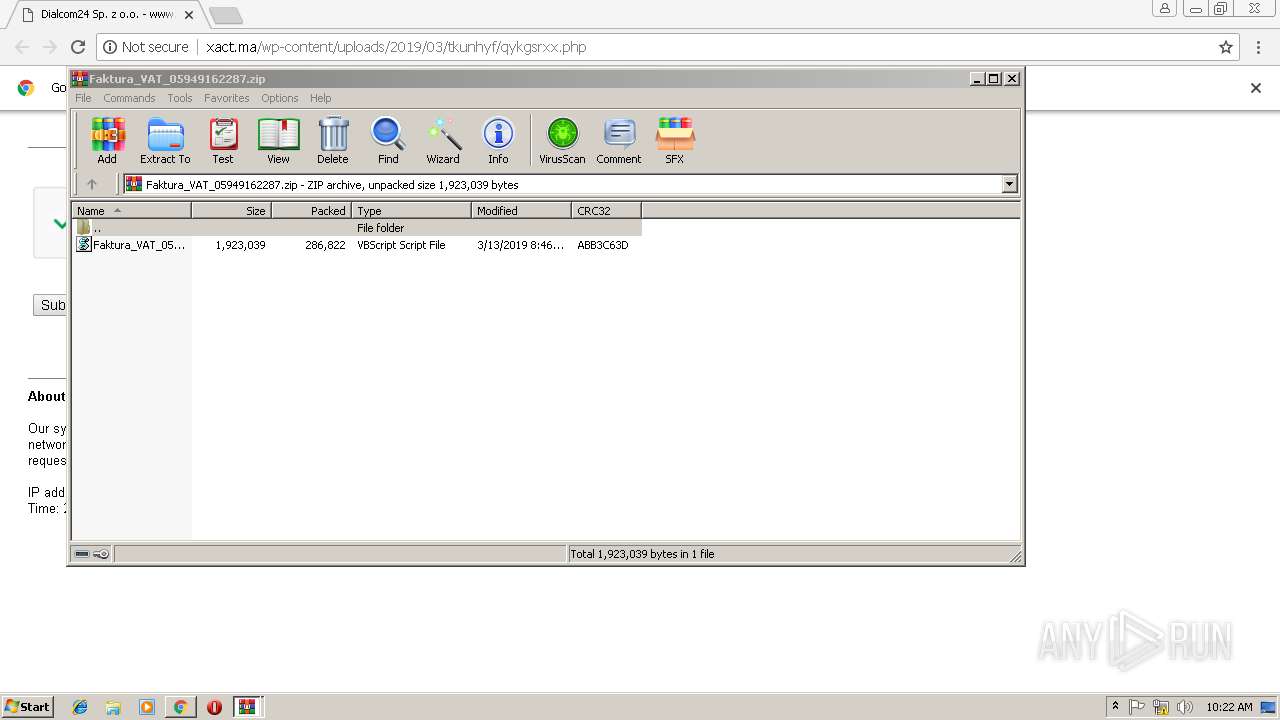
Executes scripts
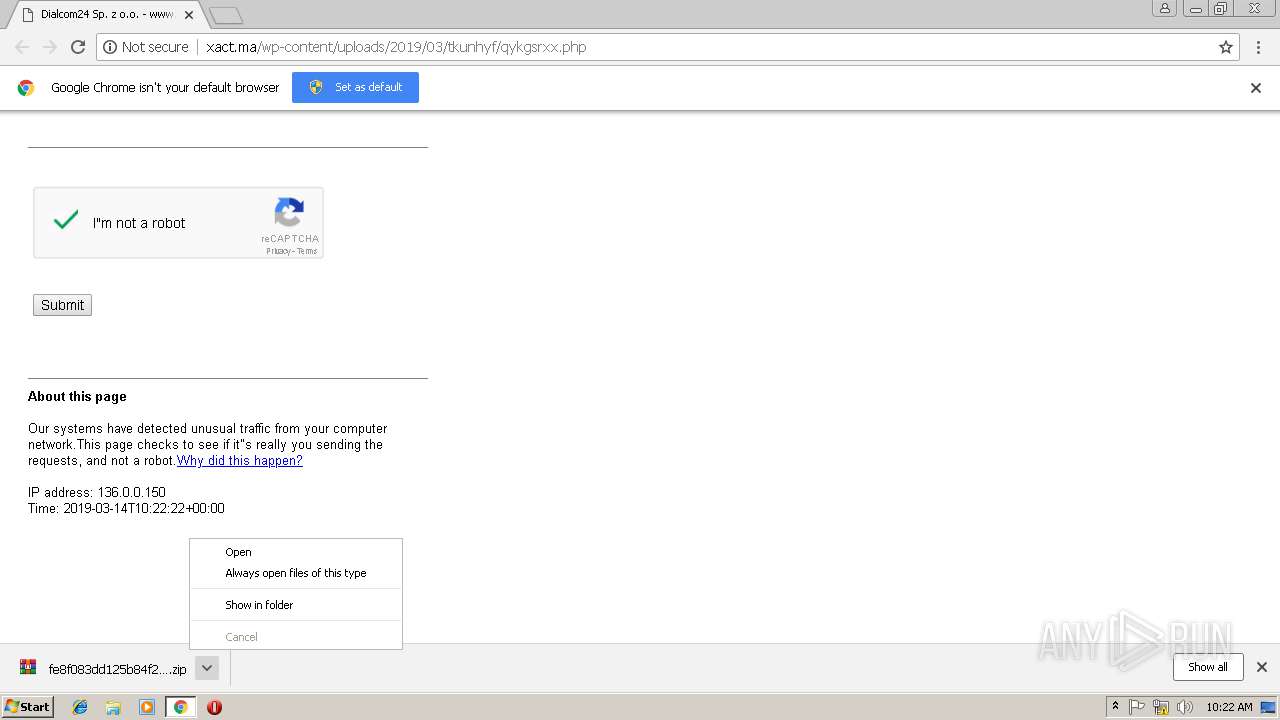
- WinRAR.exe (PID: 2972)
Executable content was dropped or overwritten
- WScript.exe (PID: 3752)
INFO
Reads settings of System Certificates
- chrome.exe (PID: 3008)
Creates files in the user directory
- chrome.exe (PID: 3008)
Application launched itself
- chrome.exe (PID: 3008)
Reads Internet Cache Settings
- chrome.exe (PID: 3008)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
45
Monitored processes
16
Malicious processes
3
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1488 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=960,6648249723427096982,15695952238347034389,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=AA494380577D90A2CDEFA9D0D1E41C19 --mojo-platform-channel-handle=992 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2332 | "C:\Windows\System32\regsvr32.exe" -s C:\Users\admin\AppData\Local\Temp/ofoM.dll | C:\Windows\System32\regsvr32.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft(C) Register Server Exit code: 4 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2432 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,6648249723427096982,15695952238347034389,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3198F6A4A7CCEE872EC55B3B258F649C --mojo-platform-channel-handle=524 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2760 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,6648249723427096982,15695952238347034389,131072 --enable-features=PasswordImport --service-pipe-token=7902E1C7612ABD71EF83087B4AAD65DB --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7902E1C7612ABD71EF83087B4AAD65DB --renderer-client-id=4 --mojo-platform-channel-handle=1904 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2968 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=960,6648249723427096982,15695952238347034389,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=857649C0A5A60BAAEA830F7EAF48F3B1 --mojo-platform-channel-handle=2368 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
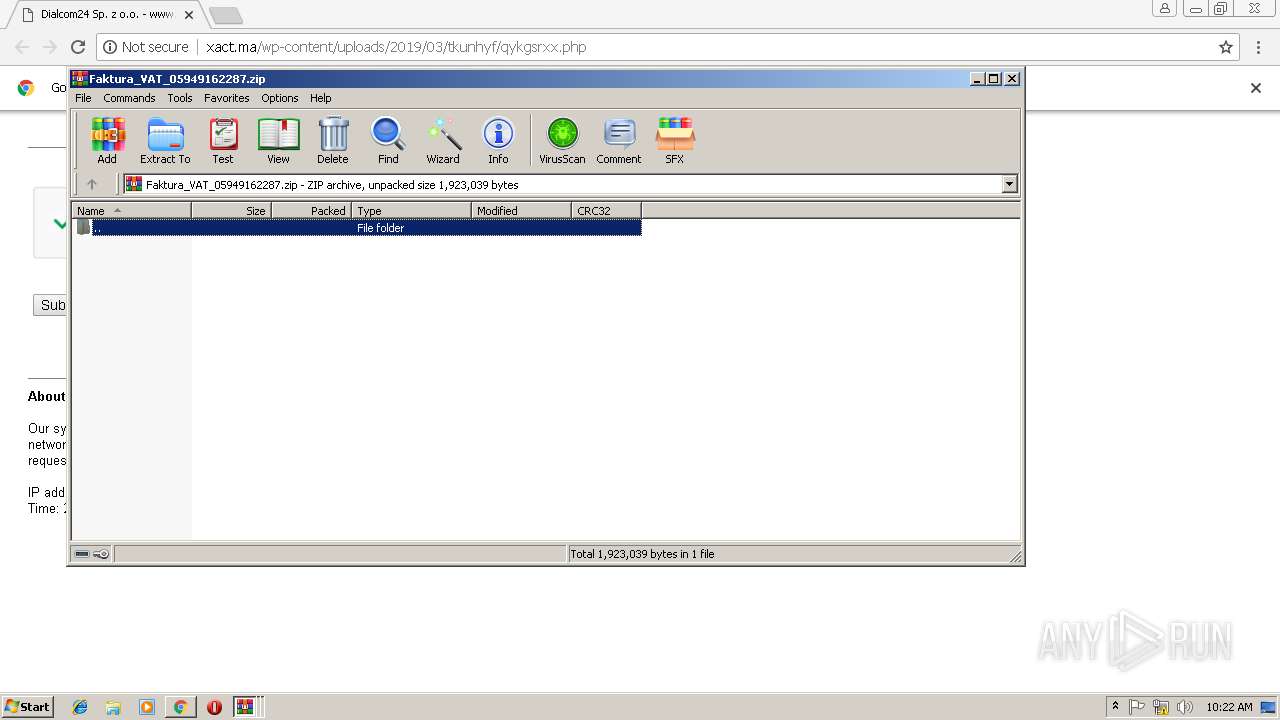
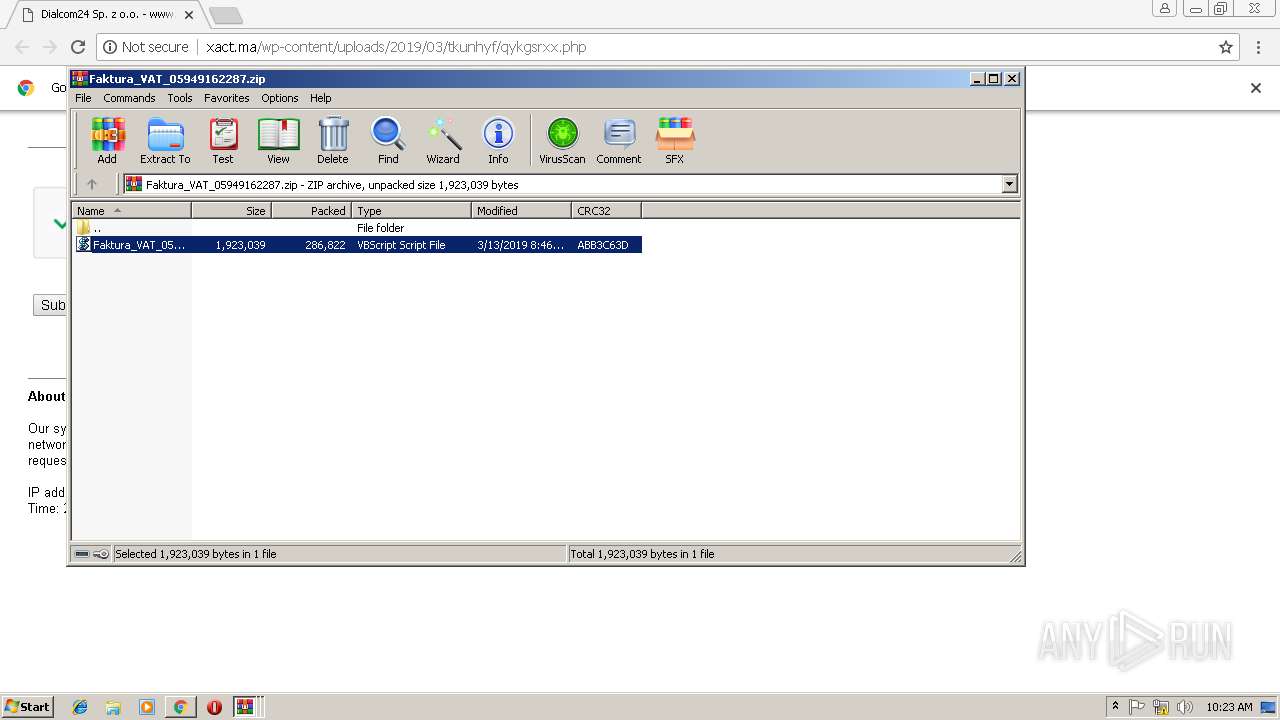
| 2972 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Rar$DIa3432.47144\Faktura_VAT_05949162287.zip | C:\Program Files\WinRAR\WinRAR.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2980 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3012 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3008 | "C:\Program Files\Google\Chrome\Application\chrome.exe" http://xact.ma/wp-content/uploads/2019/03/tkunhyf/qykgsrxx.php | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3164 | C:\Windows\system32\\rundll32.exe C:\Users\admin\AppData\Local\Temp\ofoM.dll,f0 | C:\Windows\system32\rundll32.exe | regsvr32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3308 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,6648249723427096982,15695952238347034389,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=72124732052E206C9DD5159D08AC92B3 --mojo-platform-channel-handle=3532 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
2 199
Read events
2 102
Write events
94
Delete events
3
Modification events
| (PID) Process: | (3008) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3008) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3008-13197032541103125 |
Value: 259 | |||
| (PID) Process: | (3008) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3008) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3008) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3008) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (3008) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3008-13197032541103125 |
Value: 259 | |||
| (PID) Process: | (3008) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3008) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
6
Suspicious files
23
Text files
59
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3008 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3008 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\114309e6-7f9f-4be9-bfa0-bbc6b3c866aa.tmp | — | |
MD5:— | SHA256:— | |||
| 3008 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3008 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3008 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\9c3c4e3e-8ea8-4b43-b045-922e118585df.tmp | — | |
MD5:— | SHA256:— | |||
| 3008 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3008 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 3008 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF20e505.TMP | text | |
MD5:— | SHA256:— | |||
| 3008 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF20e4d6.TMP | text | |
MD5:— | SHA256:— | |||
| 3008 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Translate Ranker Model | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
14
DNS requests
8
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3008 | chrome.exe | GET | 200 | 169.50.173.27:80 | http://xact.ma/favicon.ico | US | compressed | 126 Kb | suspicious |
3008 | chrome.exe | GET | 200 | 169.50.173.27:80 | http://xact.ma/wp-content/uploads/2019/03/tkunhyf/qykgsrxx.php | US | html | 126 Kb | suspicious |
3008 | chrome.exe | GET | 200 | 169.50.173.27:80 | http://xact.ma/wp-content/uploads/2019/03/tkunhyf/qykgsrxx.php?down2a69fff1221497043461fac383aecaf9 | US | compressed | 280 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3008 | chrome.exe | 172.217.22.67:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3008 | chrome.exe | 216.58.210.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3008 | chrome.exe | 169.50.173.27:80 | xact.ma | SoftLayer Technologies Inc. | US | suspicious |
3008 | chrome.exe | 216.58.207.42:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
3008 | chrome.exe | 172.217.22.78:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
3008 | chrome.exe | 216.58.207.67:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3164 | rundll32.exe | 62.187.103.29:443 | — | — | GB | malicious |
3164 | rundll32.exe | 130.108.146.177:443 | — | OARnet | US | malicious |
3164 | rundll32.exe | 214.161.108.156:443 | — | DoD Network Information Center | US | malicious |
3008 | chrome.exe | 172.217.16.142:443 | clients1.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
xact.ma |
| suspicious |
www.gstatic.com |
| whitelisted |
accounts.google.com |
| shared |
ajax.googleapis.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
clients1.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3164 | rundll32.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/Spy.Danabot.I |
3164 | rundll32.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/Spy.Danabot.I |
3164 | rundll32.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/Spy.Danabot.I |
3164 | rundll32.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/Spy.Danabot.I |