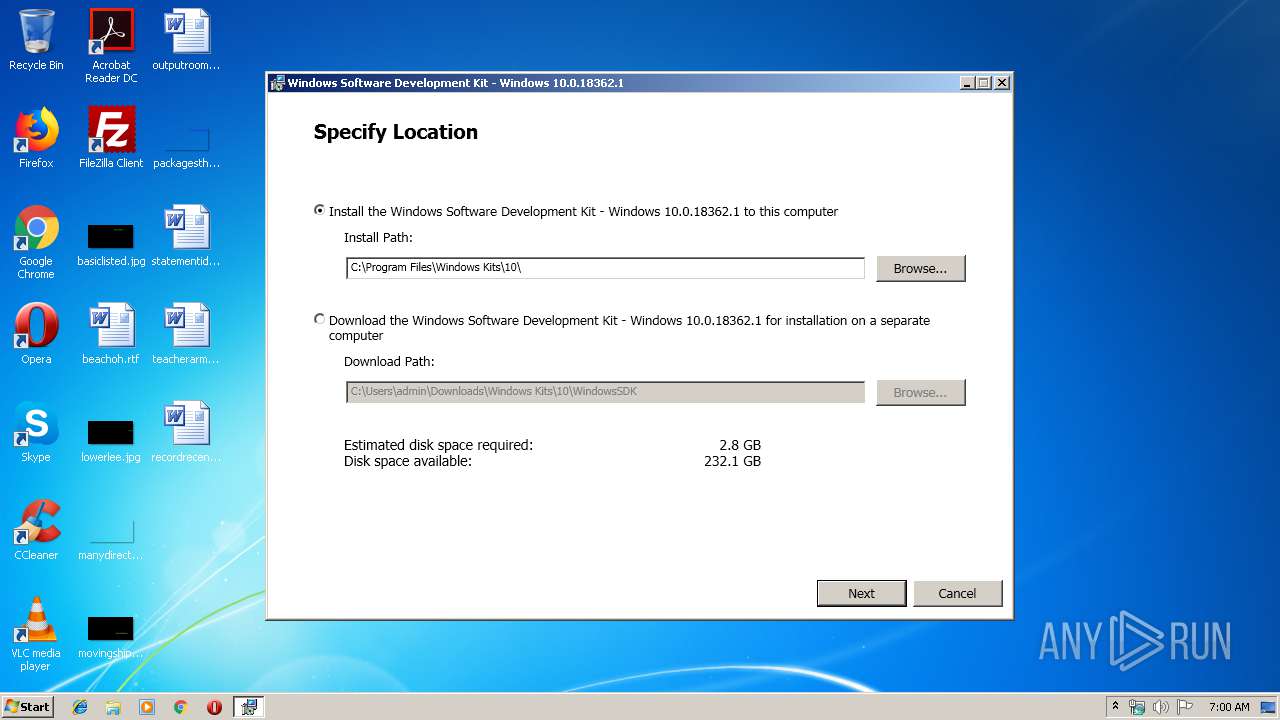
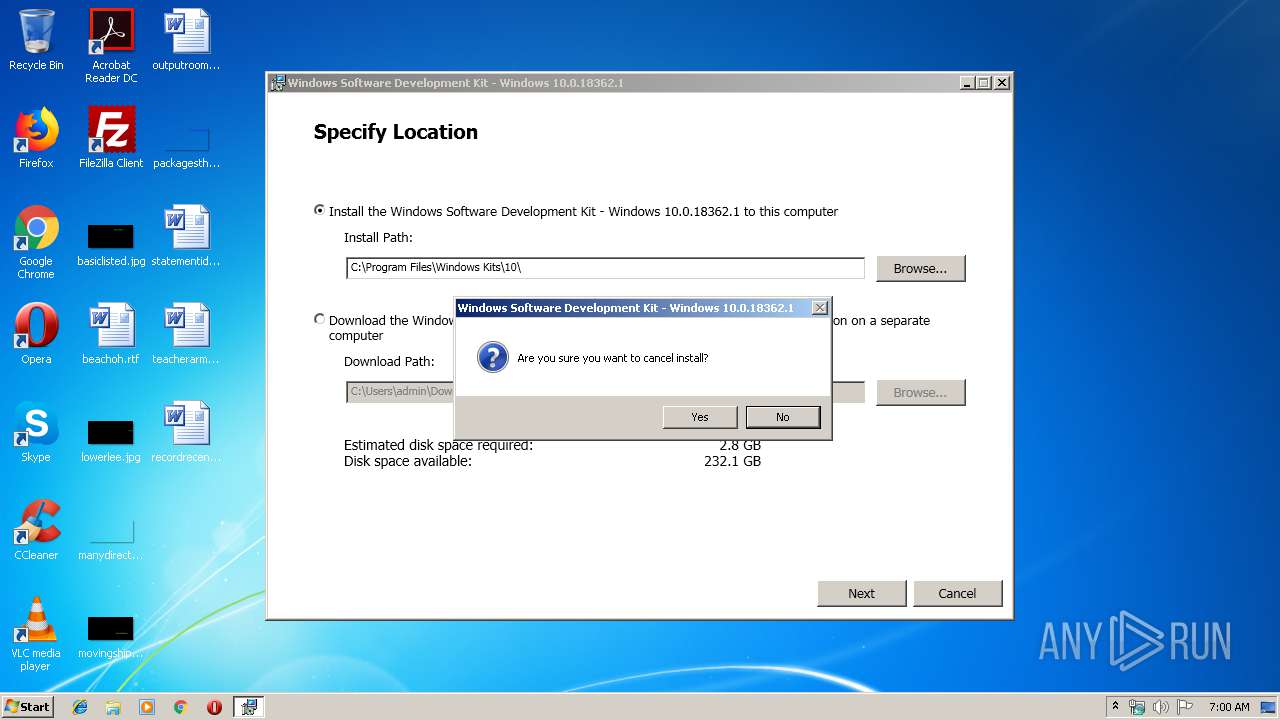
| File name: | winsdksetup.exe |
| Full analysis: | https://app.any.run/tasks/c5db3940-938f-4a52-9e4f-625d3e67ace0 |
| Verdict: | Malicious activity |
| Analysis date: | July 04, 2019, 05:59:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 31BBF735442CC6BDBE416274256B0210 |
| SHA1: | 7A977B61B0BB49A30D77A3B37ECB9C847D9E983D |
| SHA256: | 2E28117E82B4D02FE30D564B835ACE9976612609271265872F20F2256A9C506B |
| SSDEEP: | 24576:+UAsBeZYyYoMGYVl2Jjx81ShVISGzDfrs43MFXtYRUSS9C8MVO:BedMfQW1ShVISQPs62XtztMVO |
MALICIOUS
Loads dropped or rewritten executable
- winsdksetup.exe (PID: 1352)
SUSPICIOUS
Executable content was dropped or overwritten
- winsdksetup.exe (PID: 1352)
- winsdksetup.exe (PID: 3188)
Creates files in the program directory
- winsdksetup.exe (PID: 1352)
Starts itself from another location
- winsdksetup.exe (PID: 3188)
INFO
Dropped object may contain Bitcoin addresses
- winsdksetup.exe (PID: 1352)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:05:04 00:56:03+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.13 |
| CodeSize: | 303616 |
| InitializedDataSize: | 403456 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2e33e |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 10.1.18362.1 |
| ProductVersionNumber: | 10.1.18362.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Microsoft Corporation |
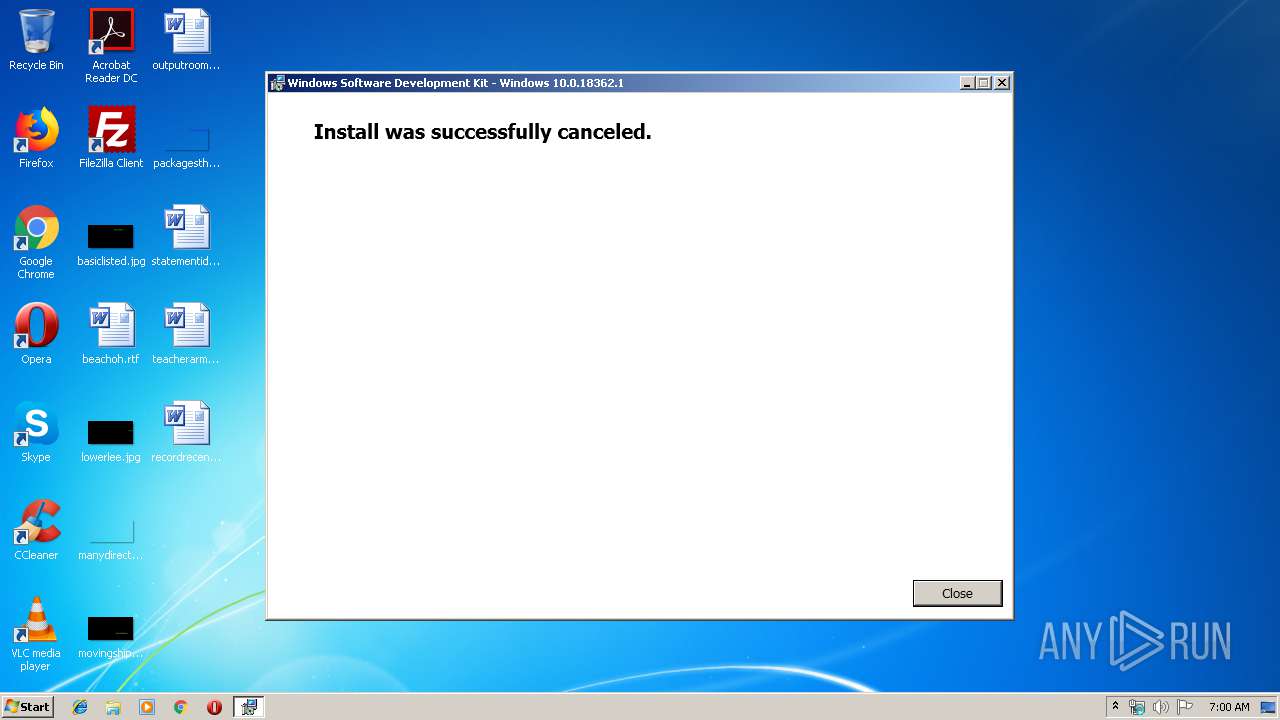
| FileDescription: | Windows Software Development Kit - Windows 10.0.18362.1 |
| FileVersion: | 10.1.18362.1 |
| InternalName: | setup |
| LegalCopyright: | Copyright (c) Microsoft Corporation. All rights reserved. |
| OriginalFileName: | winsdksetup.exe |
| ProductName: | Windows Software Development Kit - Windows 10.0.18362.1 |
| ProductVersion: | 10.1.18362.1 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 03-May-2018 22:56:03 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Microsoft Corporation |
| FileDescription: | Windows Software Development Kit - Windows 10.0.18362.1 |
| FileVersion: | 10.1.18362.1 |
| InternalName: | setup |
| LegalCopyright: | Copyright (c) Microsoft Corporation. All rights reserved. |
| OriginalFilename: | winsdksetup.exe |
| ProductName: | Windows Software Development Kit - Windows 10.0.18362.1 |
| ProductVersion: | 10.1.18362.1 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000118 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 03-May-2018 22:56:03 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0004A1D7 | 0x0004A200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.55637 |
.rdata | 0x0004C000 | 0x0001F5D0 | 0x0001F600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.13906 |
.data | 0x0006C000 | 0x0000172C | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.17124 |
.wixburn8 | 0x0006E000 | 0x00000038 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.512776 |
.rsrc | 0x0006F000 | 0x0003E514 | 0x0003E600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.94803 |
.reloc | 0x000AE000 | 0x00003E04 | 0x00004000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.71441 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.30829 | 1234 | Latin 1 / Western European | English - United States | RT_MANIFEST |
Imports
ADVAPI32.dll |
Cabinet.dll (delay-loaded) |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
RPCRT4.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
34
Monitored processes
2
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1352 | "C:\Users\admin\AppData\Local\Temp\{1E37448D-ECF5-4E5F-9943-4A8175BEB1B5}\.cr\winsdksetup.exe" -burn.clean.room="C:\Users\admin\AppData\Local\Temp\winsdksetup.exe" -burn.filehandle.attached=148 -burn.filehandle.self=156 | C:\Users\admin\AppData\Local\Temp\{1E37448D-ECF5-4E5F-9943-4A8175BEB1B5}\.cr\winsdksetup.exe | winsdksetup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Software Development Kit - Windows 10.0.18362.1 Exit code: 0 Version: 10.1.18362.1 Modules
| |||||||||||||||
| 3188 | "C:\Users\admin\AppData\Local\Temp\winsdksetup.exe" | C:\Users\admin\AppData\Local\Temp\winsdksetup.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Software Development Kit - Windows 10.0.18362.1 Exit code: 0 Version: 10.1.18362.1 Modules
| |||||||||||||||
Total events
90
Read events
87
Write events
3
Delete events
0
Modification events
| (PID) Process: | (1352) winsdksetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: winsdksetup.exe | |||
| (PID) Process: | (1352) winsdksetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\CTF\CUAS\DefaultCompositionWindow |
| Operation: | write | Name: | Left |
Value: 0 | |||
| (PID) Process: | (1352) winsdksetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\CTF\CUAS\DefaultCompositionWindow |
| Operation: | write | Name: | Top |
Value: 0 | |||
Executable files
12
Suspicious files
0
Text files
9
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1352 | winsdksetup.exe | C:\Users\admin\AppData\Local\Temp\{A0E604C8-62E6-4693-BE48-2B86F9B84F85}\.ba\NetfxLicense.rtf | text | |
MD5:EC356D9BB20437848228F5C480FD111C | SHA256:48AE54DD5A7DCA60DE835C384648433099C702BAB71EB3339D88B96424DB500E | |||
| 1352 | winsdksetup.exe | C:\Users\admin\AppData\Local\Temp\{A0E604C8-62E6-4693-BE48-2B86F9B84F85}\.ba\mbapreq.png | image | |
MD5:A356956FD269567B8F4612A33802637B | SHA256:A401A225ADDAF89110B4B0F6E8CF94779E7C0640BCDD2D670FFCF05AAB0DAD03 | |||
| 1352 | winsdksetup.exe | C:\Users\admin\AppData\Local\Temp\{A0E604C8-62E6-4693-BE48-2B86F9B84F85}\.ba\mbahost.dll | executable | |
MD5:2BA10D77A0DD711803D905EA64444369 | SHA256:36547E04B852794C0DB49EC3C64D7DEE428E3AC933B965A85D52785481E01A07 | |||
| 1352 | winsdksetup.exe | C:\Users\admin\AppData\Local\Temp\{A0E604C8-62E6-4693-BE48-2B86F9B84F85}\.ba\license.rtf | text | |
MD5:1C2304FD72C13D32E690924A5CB0F150 | SHA256:863A7B97EBD8FC2BA102FD7F12183CC75E281C5637F9A6CCB341CD0A2CFED297 | |||
| 1352 | winsdksetup.exe | C:\Users\admin\AppData\Local\Temp\{A0E604C8-62E6-4693-BE48-2B86F9B84F85}\.ba\mbapreq.thm | xml | |
MD5:9F63155A23573D3E522CD28E982658B1 | SHA256:DF05AC2A44327303B718B9FC05D306047EC387EE551664B8EB9B3E48DF24B5F9 | |||
| 1352 | winsdksetup.exe | C:\Users\admin\AppData\Local\Temp\{A0E604C8-62E6-4693-BE48-2B86F9B84F85}\.ba\Microsoft.Bootstrapper.dll | executable | |
MD5:2FE33C4EEC81898D68C1B1ABF186CCEC | SHA256:FD48FC4D1E5DDB6F0B9C7E098E58A095B13726CE69EA1A98996B2A68BDC5F114 | |||
| 1352 | winsdksetup.exe | C:\Users\admin\AppData\Local\Temp\{A0E604C8-62E6-4693-BE48-2B86F9B84F85}\.ba\BootstrapperCore.config | xml | |
MD5:57AA0F7B5F6F076454F075A88BCC0CC9 | SHA256:361079F9F118E11EA3F05D75FD3874664C94334F453177242C8E32F0881A3527 | |||
| 1352 | winsdksetup.exe | C:\Users\admin\AppData\Local\Temp\{A0E604C8-62E6-4693-BE48-2B86F9B84F85}\.ba\Microsoft.Bootstrapper.Presentation.dll | executable | |
MD5:28A709345DC0BD3E55C0C7A0B4C68BEE | SHA256:10DD4F2220903EBD9D4842126FA457835EAC0E0495F129B6CD36905F3DC6B779 | |||
| 1352 | winsdksetup.exe | C:\Users\admin\AppData\Local\Temp\{A0E604C8-62E6-4693-BE48-2B86F9B84F85}\.ba\BootstrapperCore.dll | executable | |
MD5:789476090439024462CF3694B8090B7D | SHA256:9C900B865AAAB23622C23E6F2EB22DFC881109351FE06F07CD7CC69C80CB55D2 | |||
| 1352 | winsdksetup.exe | C:\Users\admin\AppData\Local\Temp\{A0E604C8-62E6-4693-BE48-2B86F9B84F85}\.ba\mbapreq.wxl | xml | |
MD5:2598179319ADF312D99FC4F9379572D3 | SHA256:B3204B5CCFB0E5E7B43D8448B2B9E179423F1B139E53AA72616C498246090C3C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report