| File name: | loa-hf.364009.exe |
| Full analysis: | https://app.any.run/tasks/7ced9255-6de4-4717-9cee-8d09927b644f |
| Verdict: | Malicious activity |
| Analysis date: | August 05, 2020, 21:47:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | C42CBA0D5EDD65C1E7A4639B7EC310D7 |
| SHA1: | 5A9FB33FFA9FEACD930B80047B383C65D2A1522F |
| SHA256: | 2E1FD75F63533C7F129D0E5637B0BA15F38D25D4900D5E720166DC0A217A338A |
| SSDEEP: | 24576:e6LMTIdHk3OsK83f9ngqWfAktinXZSwGld3WkWIJEer+4ITGsq81cXd:egYYHqf1gOktiZSwGl5WDQER4qdyN |
MALICIOUS
Loads dropped or rewritten executable
- loa-hf.364009.exe (PID: 2500)
Application was dropped or rewritten from another process
- loa-hf-plugin.exe (PID: 3968)
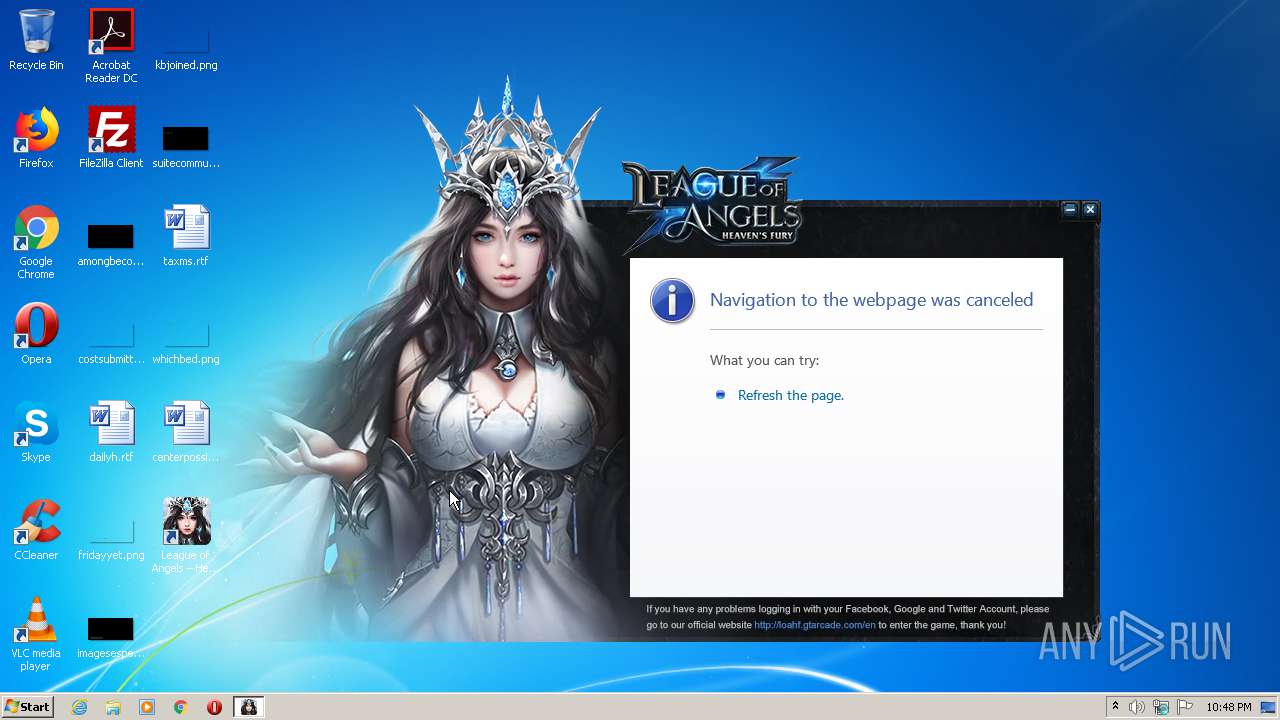
Connects to CnC server
- loa-hf-plugin.exe (PID: 3968)
SUSPICIOUS
Creates COM task schedule object
- loa-hf.364009.exe (PID: 2500)
Modifies the open verb of a shell class
- loa-hf-plugin.exe (PID: 3968)
Creates files in the user directory
- loa-hf-plugin.exe (PID: 3968)
Creates a software uninstall entry
- loa-hf-plugin.exe (PID: 3968)
Reads internet explorer settings
- loa-hf-plugin.exe (PID: 3968)
Executable content was dropped or overwritten
- loa-hf.364009.exe (PID: 2500)
Reads Internet Cache Settings
- loa-hf-plugin.exe (PID: 3968)
INFO
Reads settings of System Certificates
- loa-hf-plugin.exe (PID: 3968)
- iexplore.exe (PID: 2428)
- iexplore.exe (PID: 1560)
- iexplore.exe (PID: 3648)
- iexplore.exe (PID: 2284)
Manual execution by user
- iexplore.exe (PID: 1560)
- iexplore.exe (PID: 2432)
- iexplore.exe (PID: 3560)
Reads Internet Cache Settings
- iexplore.exe (PID: 1560)
- iexplore.exe (PID: 2428)
- iexplore.exe (PID: 3648)
- iexplore.exe (PID: 2432)
- iexplore.exe (PID: 2284)
- iexplore.exe (PID: 2528)
Changes internet zones settings
- iexplore.exe (PID: 1560)
- iexplore.exe (PID: 2432)
Application launched itself
- iexplore.exe (PID: 1560)
- iexplore.exe (PID: 2432)
Creates files in the user directory
- iexplore.exe (PID: 2428)
- iexplore.exe (PID: 3648)
- iexplore.exe (PID: 1560)
- iexplore.exe (PID: 2284)
Reads internet explorer settings
- iexplore.exe (PID: 2428)
- iexplore.exe (PID: 3648)
- iexplore.exe (PID: 2528)
- iexplore.exe (PID: 2284)
Changes settings of System certificates
- iexplore.exe (PID: 1560)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1560)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:07:21 09:01:23+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 120320 |
| InitializedDataSize: | 1015808 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x530b |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.100.26 |
| ProductVersionNumber: | 1.0.100.26 |
| FileFlagsMask: | 0x0017 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| FileDescription: | setup Application |
| FileVersion: | 1, 0, 100, |
| InternalName: | setup |
| LegalCopyright: | Copyright (C) 2015 |
| OriginalFileName: | setup.exe |
| ProductName: | setup Application |
| ProductVersion: | 1, 0, 100, |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 21-Jul-2020 07:01:23 |
| Detected languages: |
|
| Debug artifacts: |
|
| FileDescription: | setup Application |
| FileVersion: | 1, 0, 100, |
| InternalName: | setup |
| LegalCopyright: | Copyright (C) 2015 |
| OriginalFilename: | setup.exe |
| ProductName: | setup Application |
| ProductVersion: | 1, 0, 100, |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 21-Jul-2020 07:01:23 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001D59A | 0x0001D600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.65966 |
.rdata | 0x0001F000 | 0x00007CB8 | 0x00007E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.09369 |
.data | 0x00027000 | 0x00003540 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.55978 |
.gfids | 0x0002B000 | 0x00000118 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.04775 |
.rsrc | 0x0002C000 | 0x000EDE24 | 0x000EE000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.99685 |
.reloc | 0x0011A000 | 0x000014E4 | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.46857 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.10479 | 1816 | Latin 1 / Western European | English - United States | RT_MANIFEST |
107 | 1.7815 | 20 | Latin 1 / Western European | Chinese - PRC | RT_GROUP_ICON |
129 | 7.99978 | 954056 | Latin 1 / Western European | Chinese - PRC | PACKAGE |
130 | 4.94764 | 252 | Latin 1 / Western European | Chinese - PRC | CONFIG |
Imports
KERNEL32.dll |
SHELL32.dll |
ole32.dll |
Total processes
47
Monitored processes
9
Malicious processes
2
Suspicious processes
0
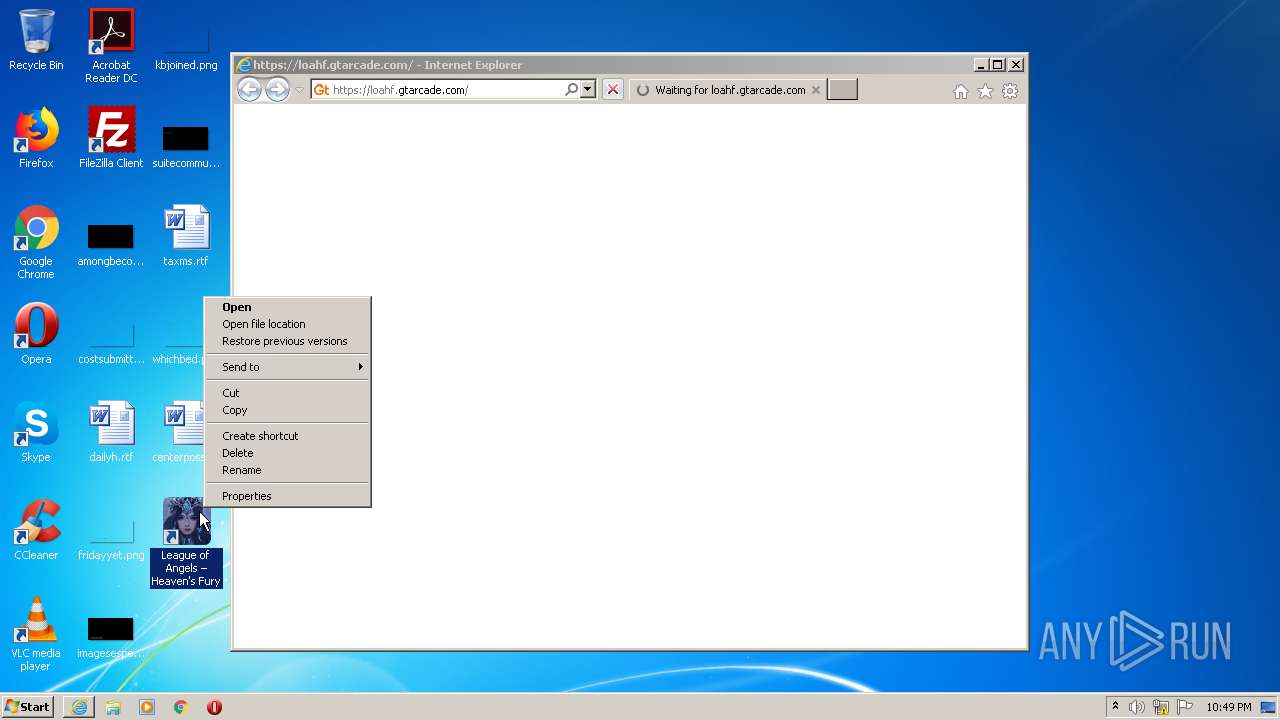
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1560 | "C:\Program Files\Internet Explorer\iexplore.exe" https://loahf.gtarcade.com/ | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2284 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2432 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2428 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1560 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2432 | "C:\Program Files\Internet Explorer\iexplore.exe" https://loahf.gtarcade.com/ | C:\Program Files\Internet Explorer\iexplore.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2500 | "C:\Users\admin\AppData\Local\Temp\loa-hf.364009.exe" | C:\Users\admin\AppData\Local\Temp\loa-hf.364009.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: setup Application Exit code: 0 Version: 1, 0, 100, Modules
| |||||||||||||||
| 2528 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2432 CREDAT:2626820 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3560 | "C:\Program Files\Internet Explorer\iexplore.exe" | C:\Program Files\Internet Explorer\iexplore.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3648 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1560 CREDAT:3216654 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3968 | "C:\Users\admin\AppData\Local\JuleGame\LOA\loa-hf-plugin.exe" /checkinstall;/silent;/identify=364009; | C:\Users\admin\AppData\Local\JuleGame\LOA\loa-hf-plugin.exe | loa-hf.364009.exe | ||||||||||||
User: admin Company: Chengdu Jule Game technology co.,ltd Integrity Level: MEDIUM Description: Game Loader. Exit code: 0 Version: 1.0.100.26 Modules
| |||||||||||||||
Total events
5 186
Read events
4 932
Write events
247
Delete events
7
Modification events
| (PID) Process: | (3968) loa-hf-plugin.exe | Key: | HKEY_CURRENT_USER\Software\julegame\clientid |
| Operation: | write | Name: | LOA |
Value: {184CDA6C-1C95-4E4E-B99C-A6284D8F50BA} | |||
| (PID) Process: | (3968) loa-hf-plugin.exe | Key: | HKEY_CURRENT_USER\Software\julegame\path |
| Operation: | write | Name: | LOA |
Value: C:\Users\admin\AppData\Local\julegame\LOA\ | |||
| (PID) Process: | (3968) loa-hf-plugin.exe | Key: | HKEY_CLASSES_ROOT\loaclient |
| Operation: | write | Name: | URL Protocol |
Value: C:\Users\admin\AppData\Local\julegame\LOA\loa-hf-plugin.exe | |||
| (PID) Process: | (3968) loa-hf-plugin.exe | Key: | HKEY_CLASSES_ROOT\loaclient\shell\open\command |
| Operation: | write | Name: | (default) |
Value: "C:\Users\admin\AppData\Local\julegame\LOA\loa-hf-plugin.exe" "%1" | |||
| (PID) Process: | (3968) loa-hf-plugin.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\ApplicationAssociationToasts |
| Operation: | write | Name: | loaclient_loaclient |
Value: 0 | |||
| (PID) Process: | (3968) loa-hf-plugin.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\{DB7C3C1B-5C70-4696-A2F9-9FB6CA39E39B} |
| Operation: | write | Name: | DisplayName |
Value: League of Angels – Heaven's Fury | |||
| (PID) Process: | (3968) loa-hf-plugin.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\{DB7C3C1B-5C70-4696-A2F9-9FB6CA39E39B} |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Users\admin\AppData\Local\julegame\LOA\loa-hf-plugin.exe | |||
| (PID) Process: | (3968) loa-hf-plugin.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\{DB7C3C1B-5C70-4696-A2F9-9FB6CA39E39B} |
| Operation: | write | Name: | DisplayVersion |
Value: 1.0.0.0 | |||
| (PID) Process: | (3968) loa-hf-plugin.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\{DB7C3C1B-5C70-4696-A2F9-9FB6CA39E39B} |
| Operation: | write | Name: | Publisher |
Value: Jule Technology Co., Ltd | |||
| (PID) Process: | (3968) loa-hf-plugin.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\{DB7C3C1B-5C70-4696-A2F9-9FB6CA39E39B} |
| Operation: | write | Name: | UninstallString |
Value: "C:\Users\admin\AppData\Local\julegame\LOA\loa-hf-plugin.exe" /uninstall; | |||
Executable files
3
Suspicious files
31
Text files
96
Unknown types
16
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2428 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab1FA9.tmp | — | |
MD5:— | SHA256:— | |||
| 2428 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar1FAA.tmp | — | |
MD5:— | SHA256:— | |||
| 2500 | loa-hf.364009.exe | C:\Users\admin\AppData\Local\JuleGame\LOA\loa-hf-plugin.exe | executable | |
MD5:— | SHA256:— | |||
| 3968 | loa-hf-plugin.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\League of Angels – Heaven's Fury\League of Angels – Heaven's Fury.lnk | lnk | |
MD5:— | SHA256:— | |||
| 3968 | loa-hf-plugin.exe | C:\Users\admin\AppData\Local\julegame\LOA\game.ico | image | |
MD5:— | SHA256:— | |||
| 3968 | loa-hf-plugin.exe | C:\Users\admin\AppData\Local\JuleGame\LOA\gameupdater.log | text | |
MD5:— | SHA256:— | |||
| 3968 | loa-hf-plugin.exe | C:\Users\admin\Desktop\League of Angels – Heaven's Fury.lnk | lnk | |
MD5:— | SHA256:— | |||
| 2428 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\N1AIHEGJ.txt | text | |
MD5:— | SHA256:— | |||
| 2428 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B398B80134F72209547439DB21AB308D_9487BC0D4381A7CDEB9A8CC43F66D27C | der | |
MD5:— | SHA256:— | |||
| 2428 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B398B80134F72209547439DB21AB308D_9487BC0D4381A7CDEB9A8CC43F66D27C | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
17
TCP/UDP connections
86
DNS requests
31
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3968 | loa-hf-plugin.exe | POST | — | 104.17.158.108:80 | http://admin-loahf.gtarcade.com/dispatch/recordstat/plugin | US | — | — | suspicious |
2428 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAVG%2Fhgj9%2BGUHaOfzhTEYXM%3D | US | der | 471 b | whitelisted |
3968 | loa-hf-plugin.exe | POST | — | 104.17.158.108:80 | http://admin-loahf.gtarcade.com/dispatch/exelogin | US | — | — | suspicious |
2428 | iexplore.exe | GET | 200 | 172.217.18.99:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
2428 | iexplore.exe | GET | 200 | 172.217.18.99:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
1560 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
3648 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAtb9ltrp%2FvQiykNkEU33uA%3D | US | der | 471 b | whitelisted |
2428 | iexplore.exe | GET | 200 | 172.217.18.99:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDQ1xbKa56n3wIAAAAAcmxg | US | der | 472 b | whitelisted |
1560 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
2428 | iexplore.exe | GET | 200 | 172.217.18.99:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDM9j8%2B94pW6ggAAAAATZ8E | US | der | 472 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3968 | loa-hf-plugin.exe | 104.17.158.108:80 | admin-loahf.gtarcade.com | Cloudflare Inc | US | suspicious |
3968 | loa-hf-plugin.exe | 2.18.234.204:443 | loahf.gtarcade.com | Akamai International B.V. | — | whitelisted |
3968 | loa-hf-plugin.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2428 | iexplore.exe | 2.18.234.204:443 | loahf.gtarcade.com | Akamai International B.V. | — | whitelisted |
2428 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2428 | iexplore.exe | 172.217.18.104:443 | www.googletagmanager.com | Google Inc. | US | suspicious |
2428 | iexplore.exe | 216.58.206.14:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
2428 | iexplore.exe | 172.217.18.99:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
1560 | iexplore.exe | 2.18.234.204:443 | loahf.gtarcade.com | Akamai International B.V. | — | whitelisted |
1560 | iexplore.exe | 13.107.21.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
admin-loahf.gtarcade.com |
| suspicious |
loahf.gtarcade.com |
| unknown |
ocsp.digicert.com |
| whitelisted |
static.gtarcade.com |
| unknown |
upload.gtarcade.com |
| unknown |
www.googletagmanager.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
collect.gtarcade.com |
| unknown |
globalapi.gtarcade.com |
| unknown |
Threats
2 ETPRO signatures available at the full report