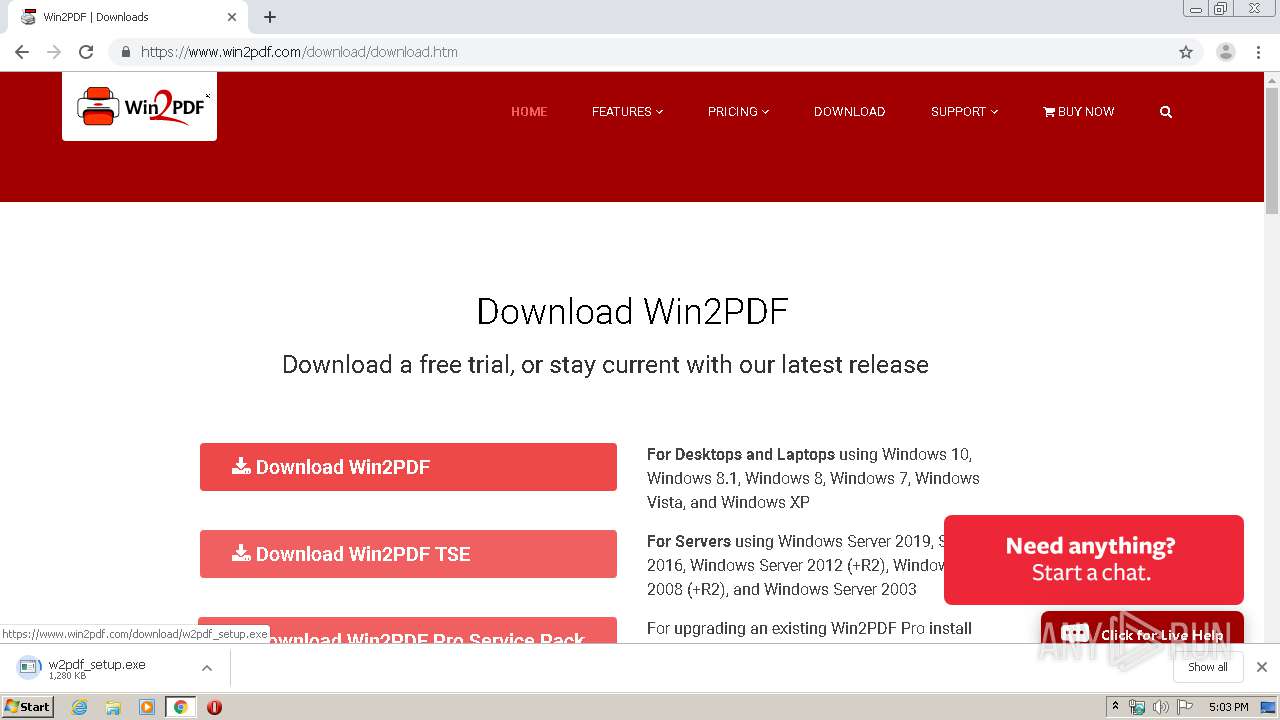
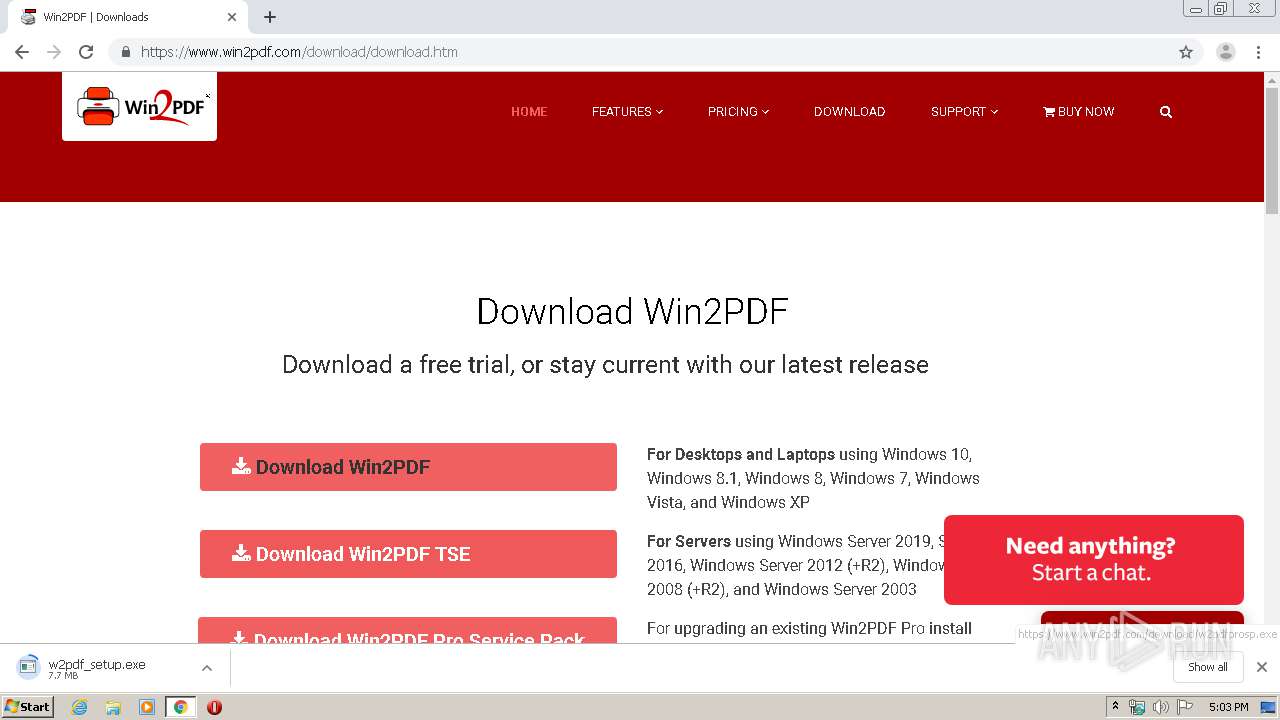
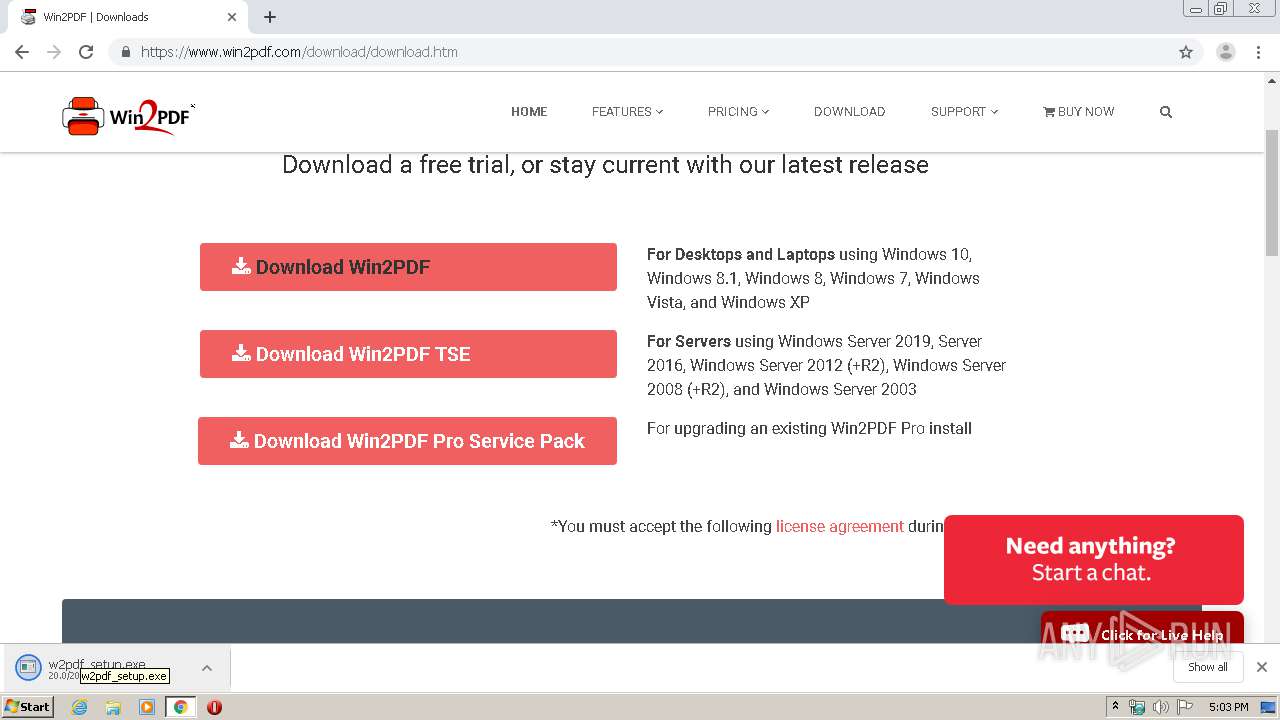
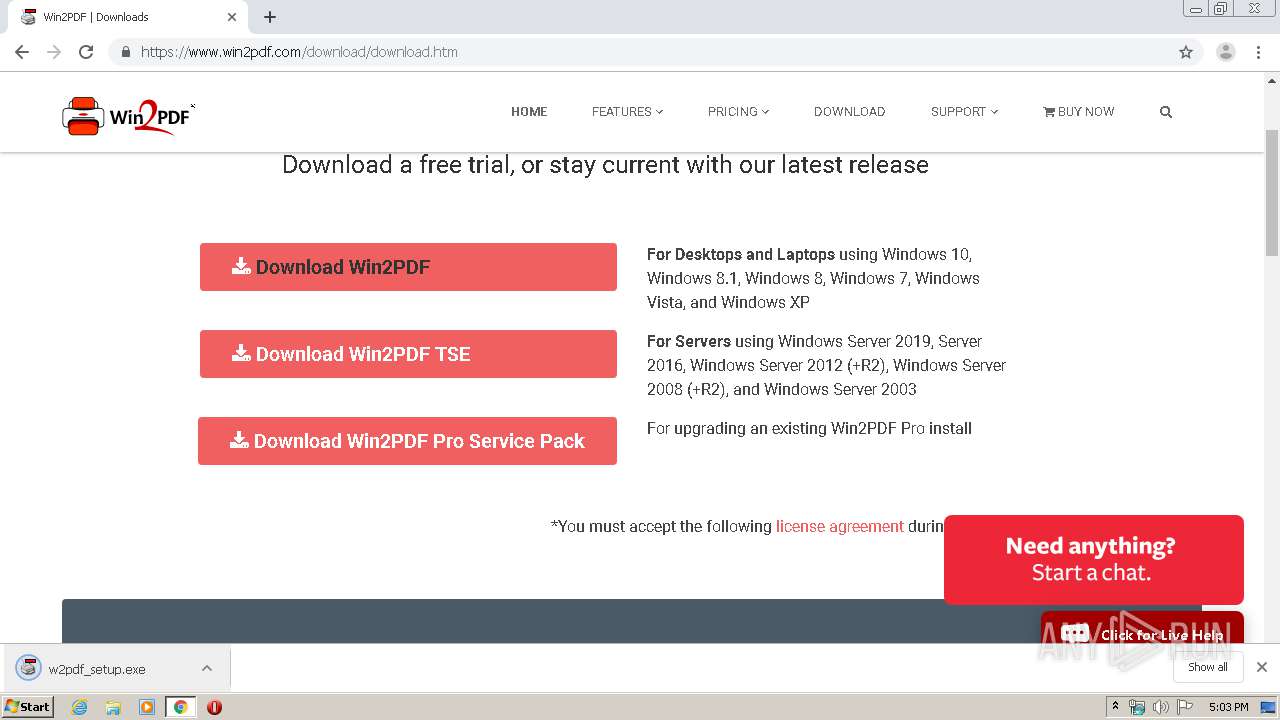
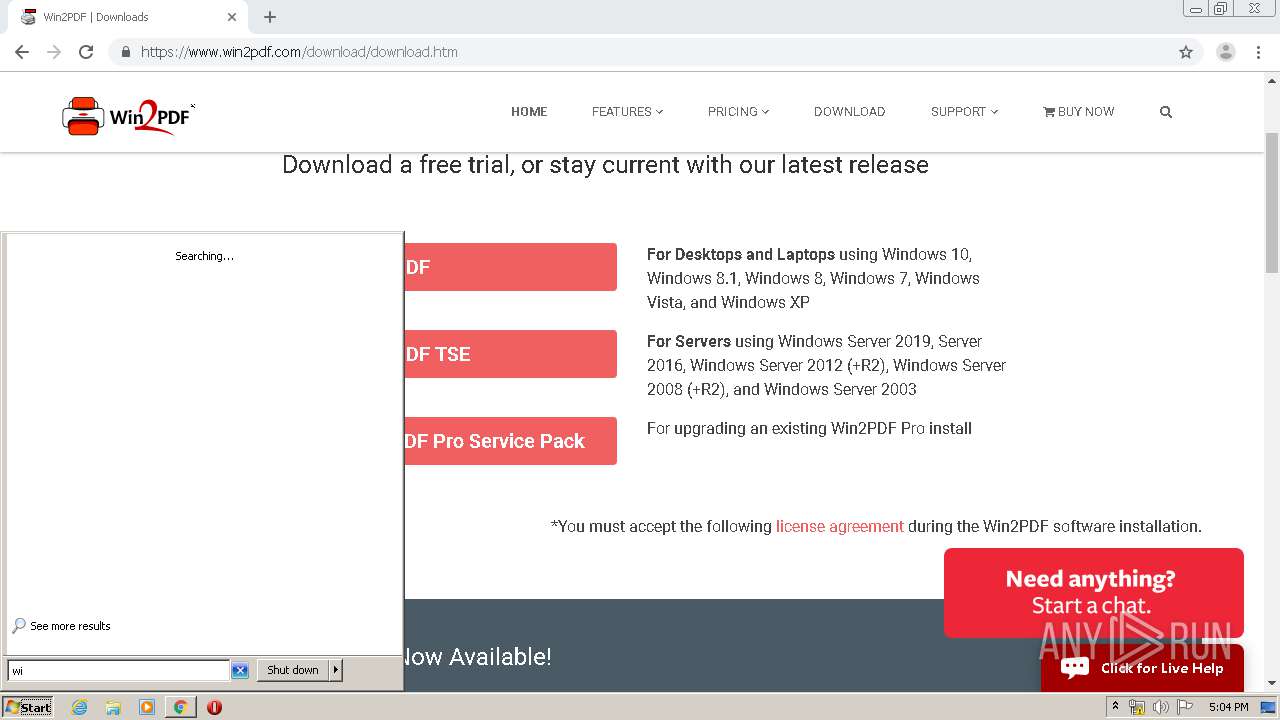
| URL: | https://www.win2pdf.com/ |
| Full analysis: | https://app.any.run/tasks/d57dc14d-c192-4370-875a-2514dbf17a25 |
| Verdict: | Malicious activity |
| Analysis date: | April 10, 2020, 16:02:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 56AEF5AC6385811D2201BF6FFB3B6660 |
| SHA1: | 2BE370D828045754FA8FAE72EE22469201B35236 |
| SHA256: | 2E117C1A29101849A10AAD988F7CA58E8A2D867CFBCFEFC1DB847B17AC305F8F |
| SSDEEP: | 3:N8DSLLVBDLRn:2OLhBDtn |
MALICIOUS
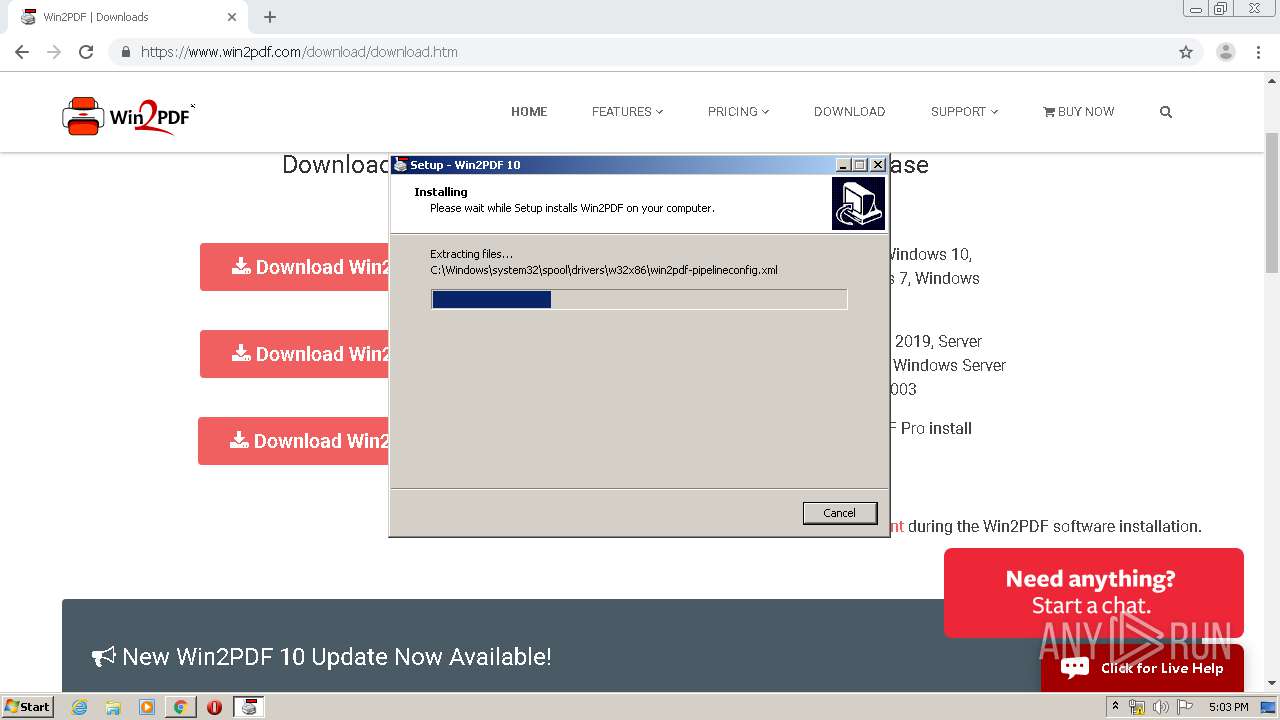
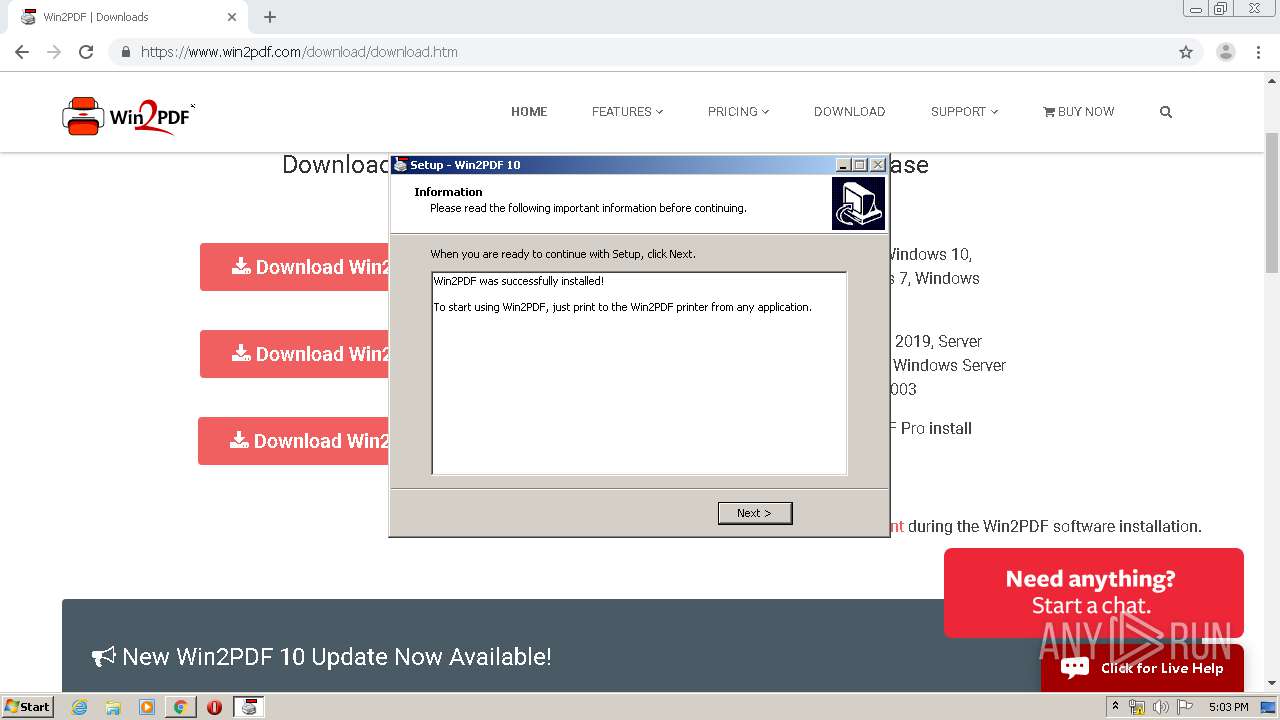
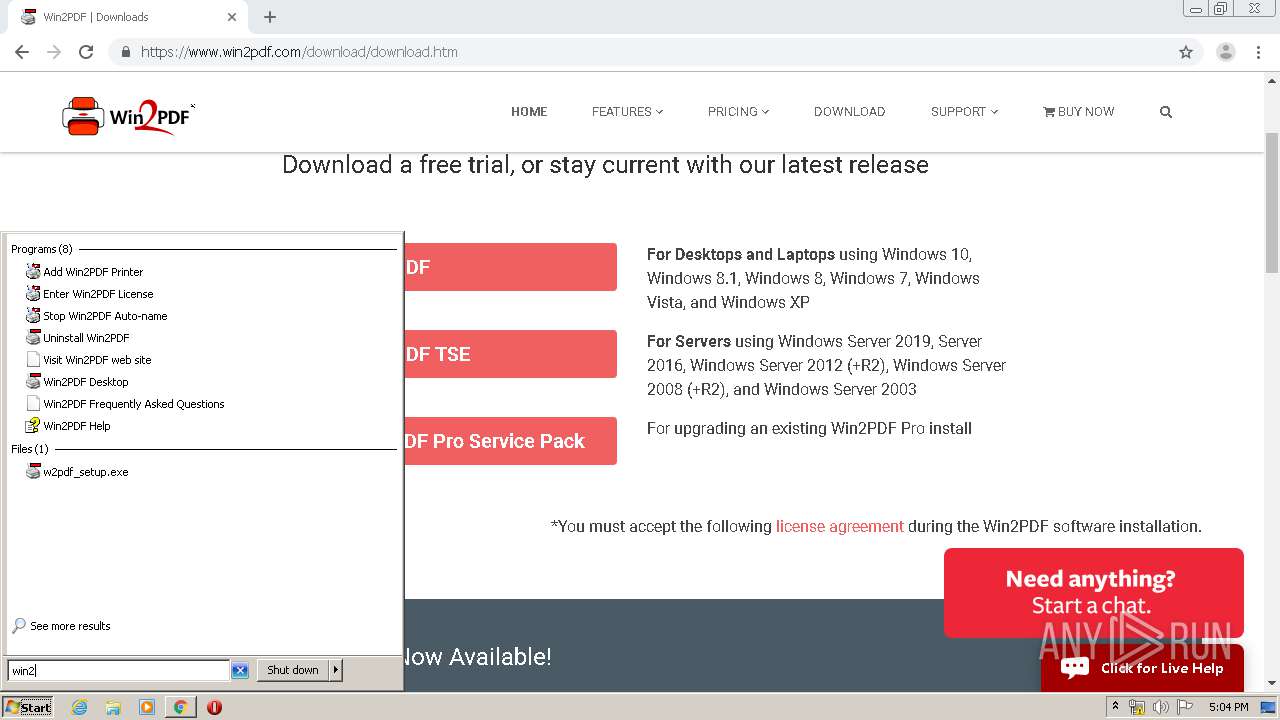
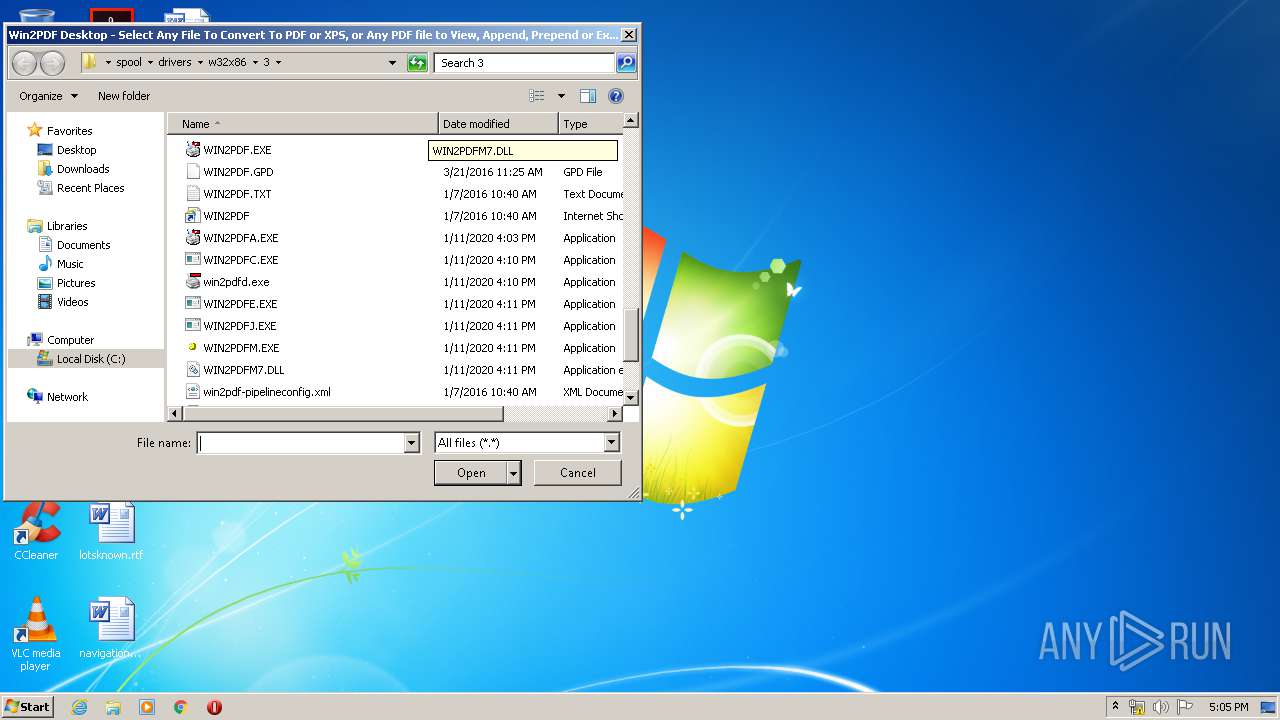
Application was dropped or rewritten from another process
- w2pdf_setup.exe (PID: 3088)
- w2pdf_setup.exe (PID: 2372)
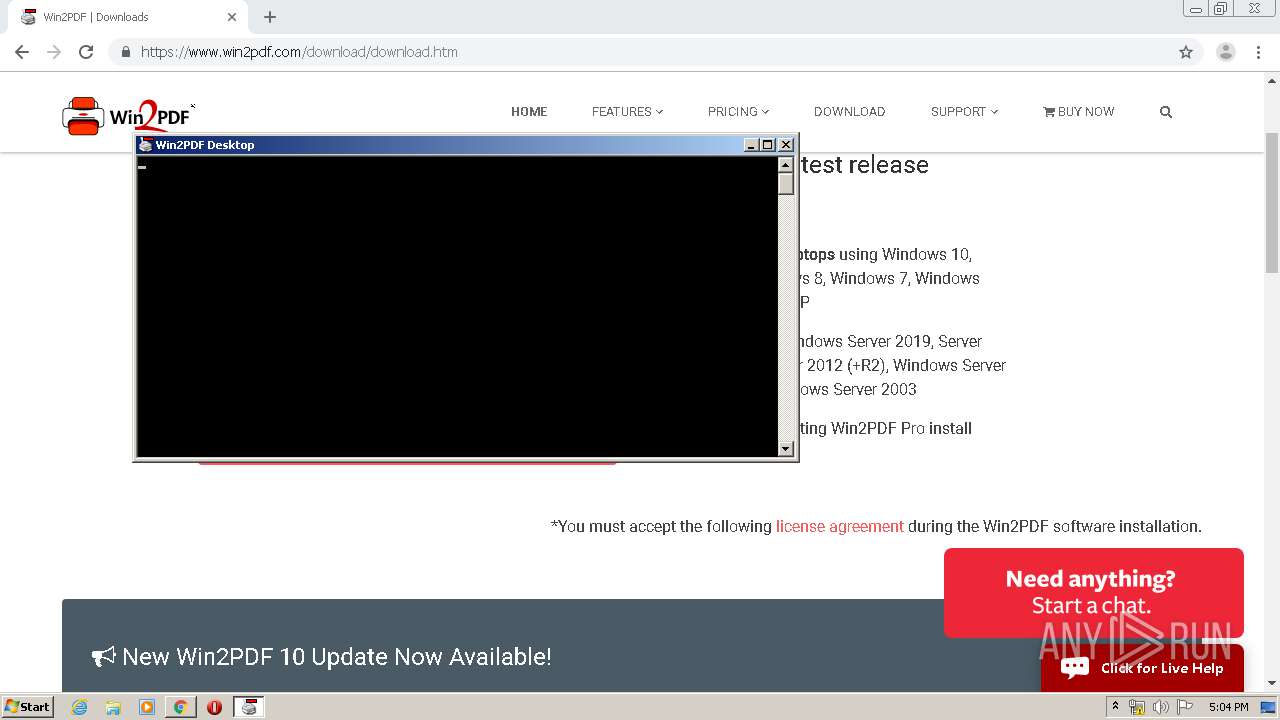
- WIN2PDF.exe (PID: 3868)
- WIN2PDF.exe (PID: 1944)
- win2pdfd.exe (PID: 3716)
- win2pdfd.exe (PID: 3744)
Loads dropped or rewritten executable
- spoolsv.exe (PID: 1188)
- WIN2PDF.exe (PID: 1944)
- WIN2PDF.exe (PID: 3868)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 3364)
- chrome.exe (PID: 3896)
- w2pdf_setup.exe (PID: 3088)
- w2pdf_setup.tmp (PID: 2072)
- w2pdf_setup.exe (PID: 2372)
- cmd.exe (PID: 2720)
- cmd.exe (PID: 3368)
- cmd.exe (PID: 4020)
- cmd.exe (PID: 1688)
- cmd.exe (PID: 2280)
- cmd.exe (PID: 3968)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3364)
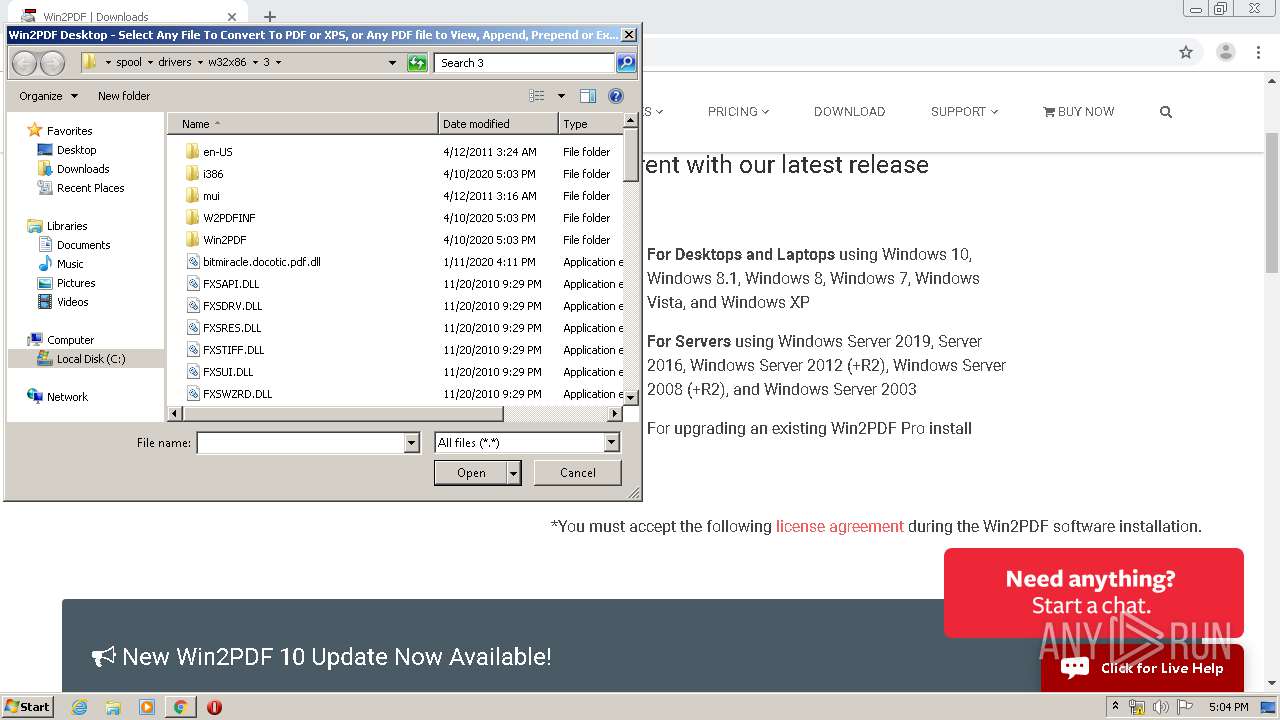
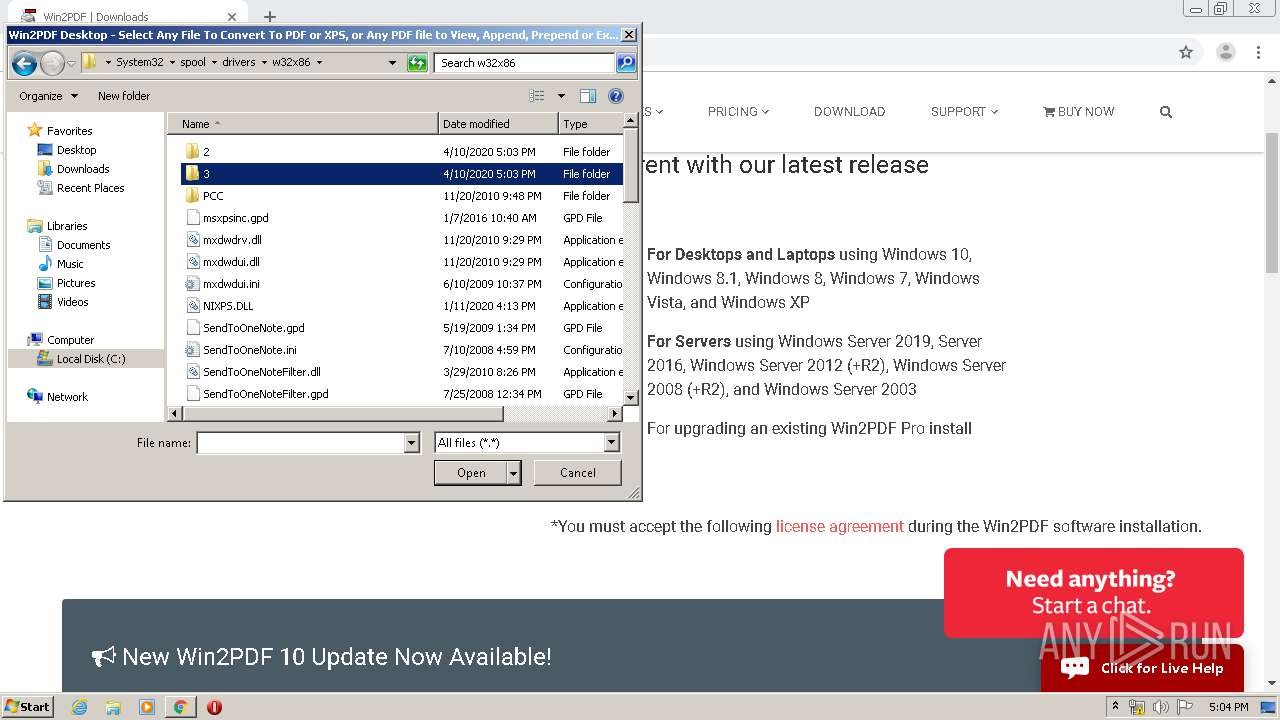
Creates files in the Windows directory
- w2pdf_setup.tmp (PID: 2072)
- cmd.exe (PID: 3376)
- cmd.exe (PID: 3376)
- spoolsv.exe (PID: 1188)
- cmd.exe (PID: 3368)
Creates files in the user directory
- w2pdf_setup.tmp (PID: 2072)
Starts CMD.EXE for commands execution
- w2pdf_setup.tmp (PID: 2072)
Removes files from Windows directory
- spoolsv.exe (PID: 1188)
Reads Internet Cache Settings
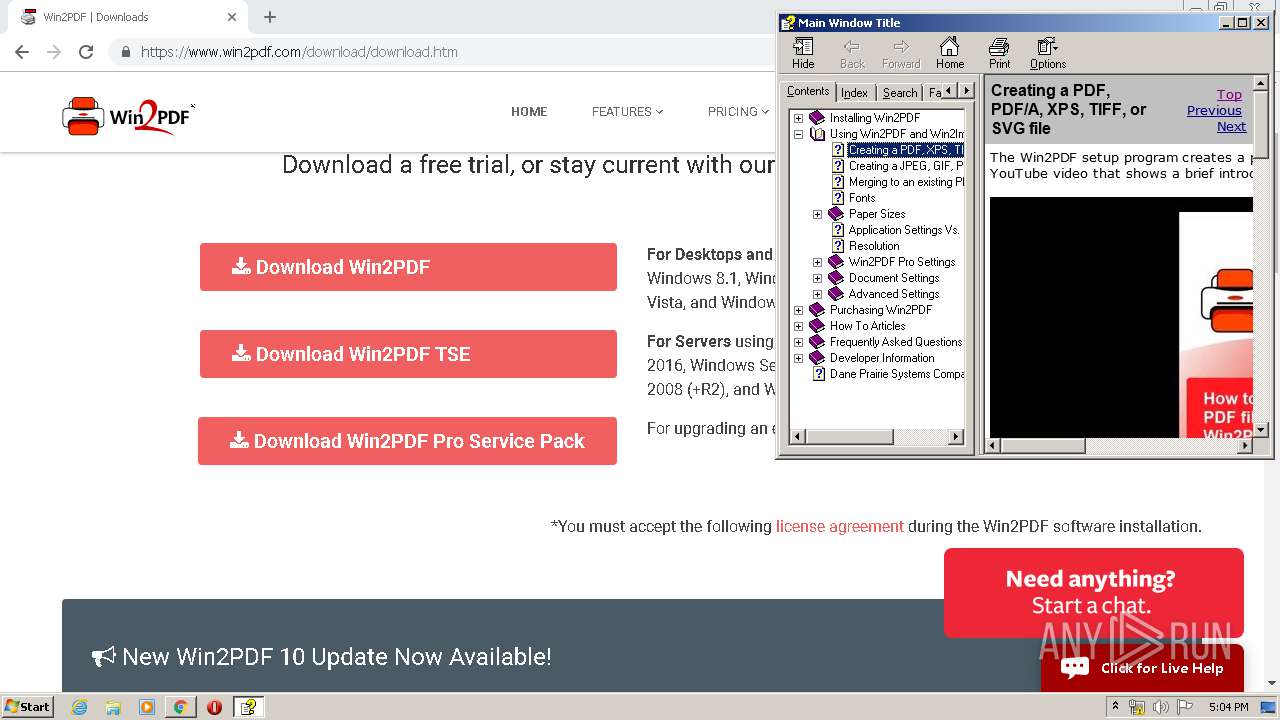
- hh.exe (PID: 2772)
Reads internet explorer settings
- hh.exe (PID: 2772)
INFO
Reads the hosts file
- chrome.exe (PID: 3364)
- chrome.exe (PID: 3896)
Application launched itself
- chrome.exe (PID: 3364)
Reads settings of System Certificates
- chrome.exe (PID: 3364)
Reads Internet Cache Settings
- chrome.exe (PID: 3364)
Application was dropped or rewritten from another process
- w2pdf_setup.tmp (PID: 2928)
- w2pdf_setup.tmp (PID: 2072)
Loads dropped or rewritten executable
- w2pdf_setup.tmp (PID: 2072)
Creates files in the program directory
- w2pdf_setup.tmp (PID: 2072)
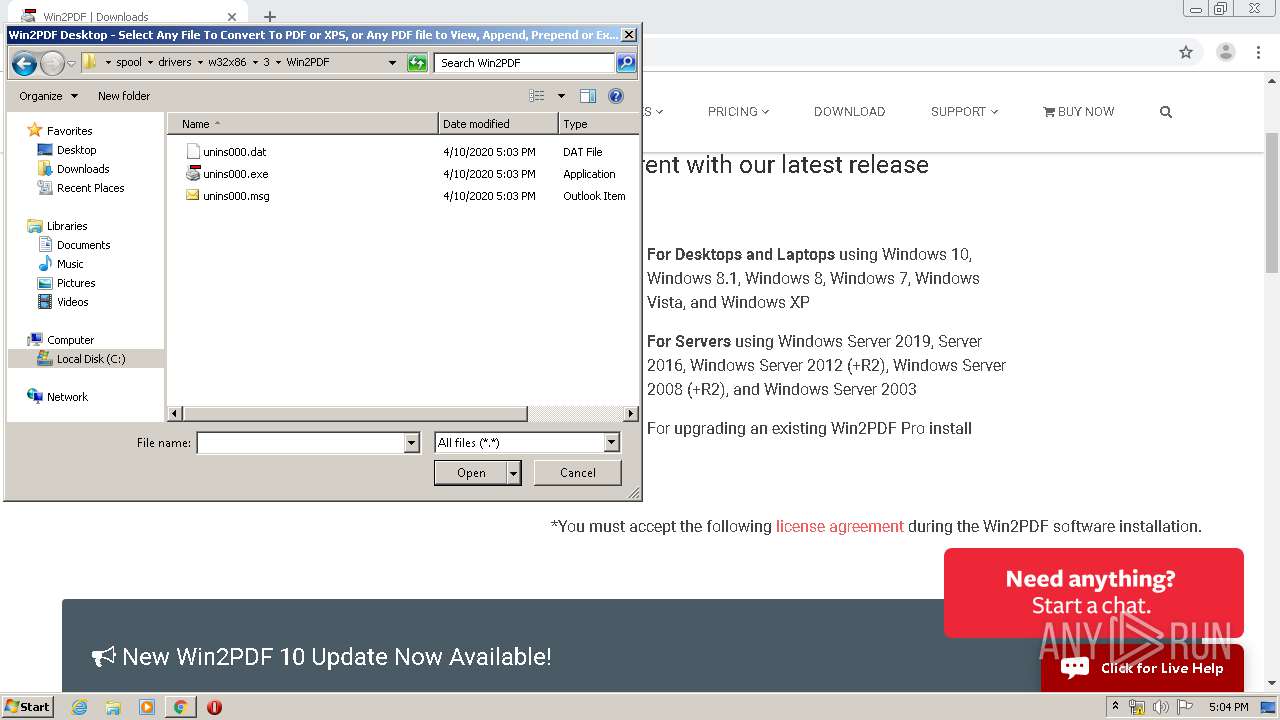
Creates a software uninstall entry
- w2pdf_setup.tmp (PID: 2072)
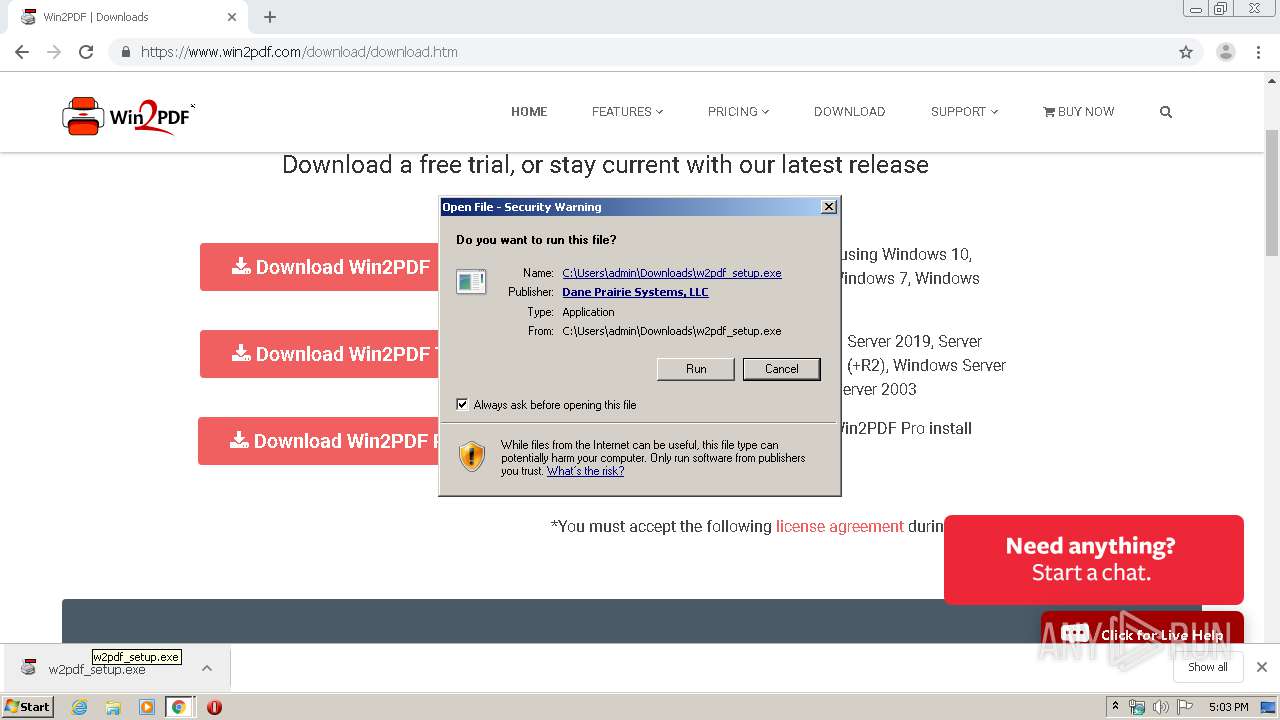
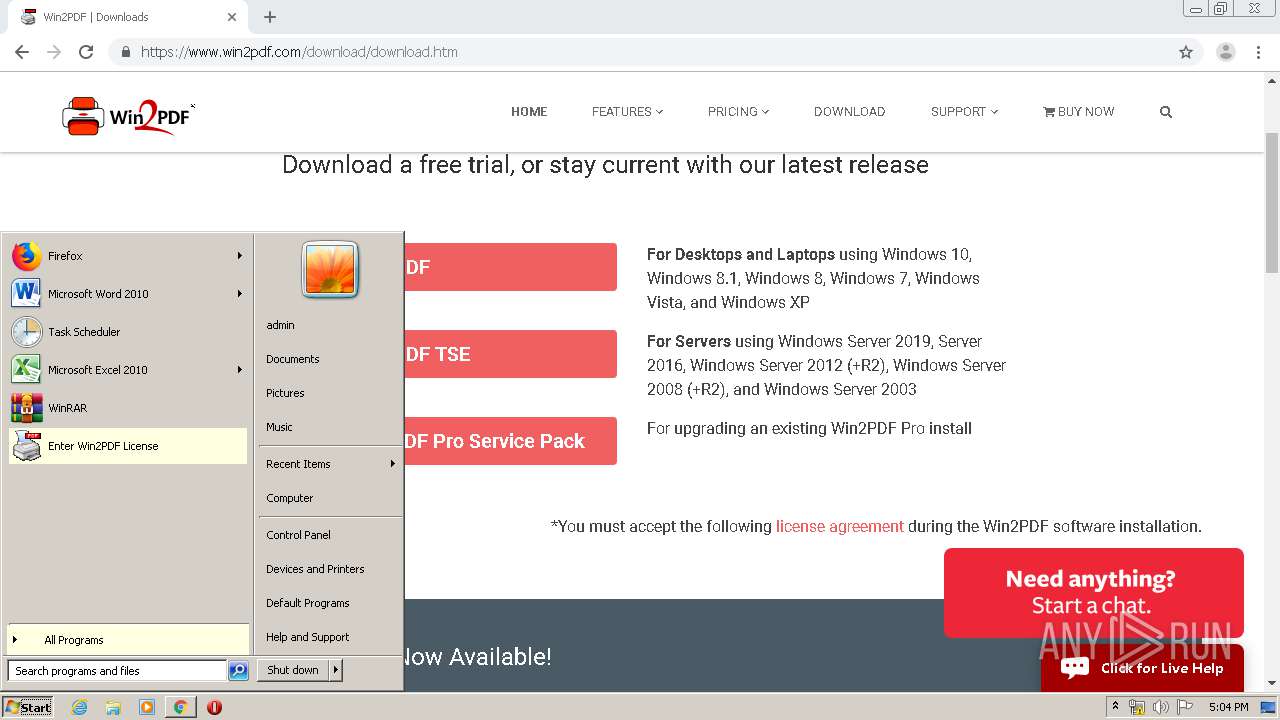
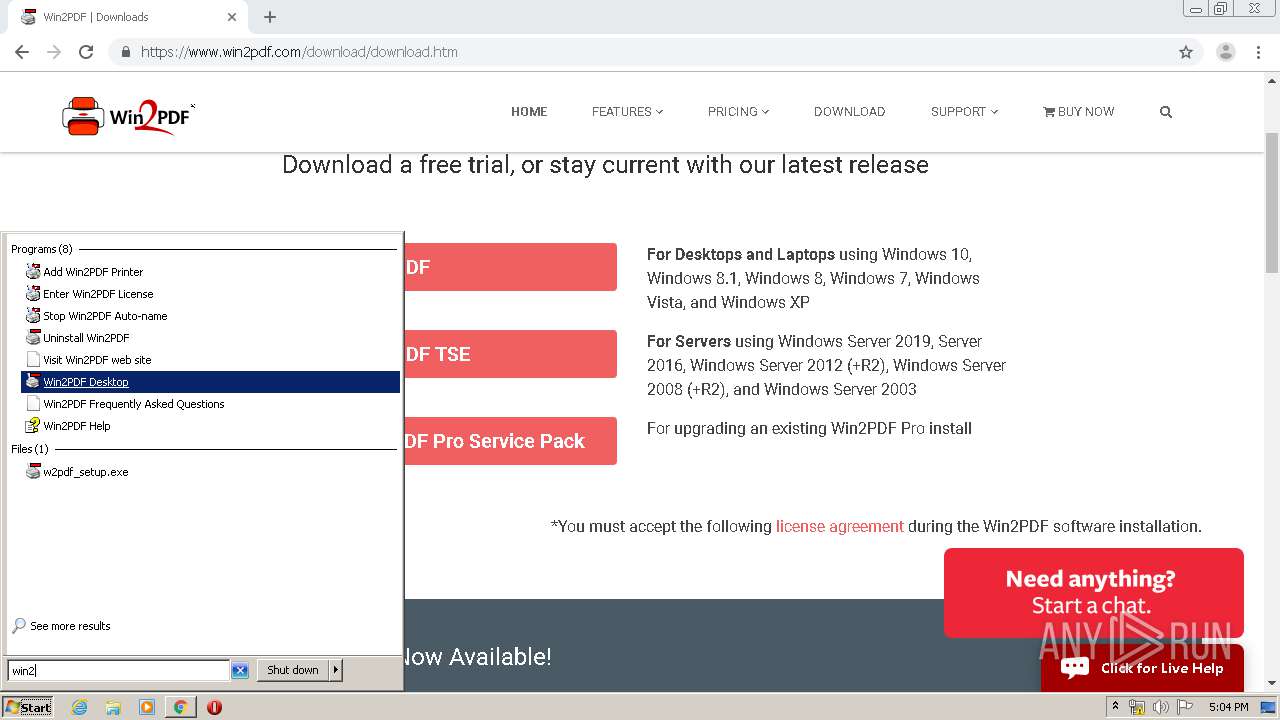
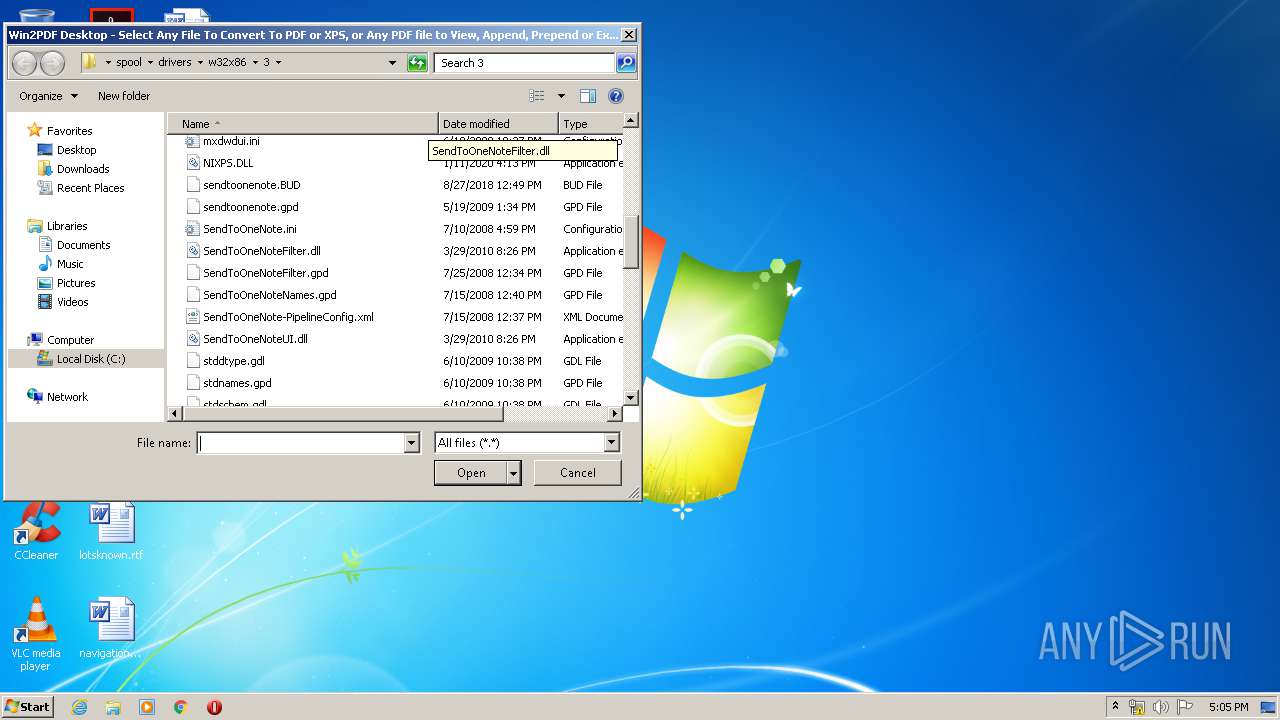
Manual execution by user
- win2pdfd.exe (PID: 3716)
- win2pdfd.exe (PID: 3744)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
107
Monitored processes
52
Malicious processes
6
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 608 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,13799753511880481531,17514590137264624288,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17168877743549308820 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3548 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 912 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,13799753511880481531,17514590137264624288,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5737800755380671228 --mojo-platform-channel-handle=5144 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 916 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,13799753511880481531,17514590137264624288,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4317027586371333004 --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1060 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1188 | C:\Windows\System32\spoolsv.exe | C:\Windows\System32\spoolsv.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Spooler SubSystem App Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1688 | "C:\Windows\system32\cmd.exe" /c copy %systemroot%\system32\spool\drivers\w32x86\3\xpssvcs.dll %systemroot%\system32\spool\drivers\w32x86\ | C:\Windows\system32\cmd.exe | w2pdf_setup.tmp | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1840 | "C:\Windows\system32\cmd.exe" /c copy %systemroot%\system32\spool\drivers\w32x86\3\stddtype.gdl %systemroot%\system32\spool\drivers\w32x86\ | C:\Windows\system32\cmd.exe | — | w2pdf_setup.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
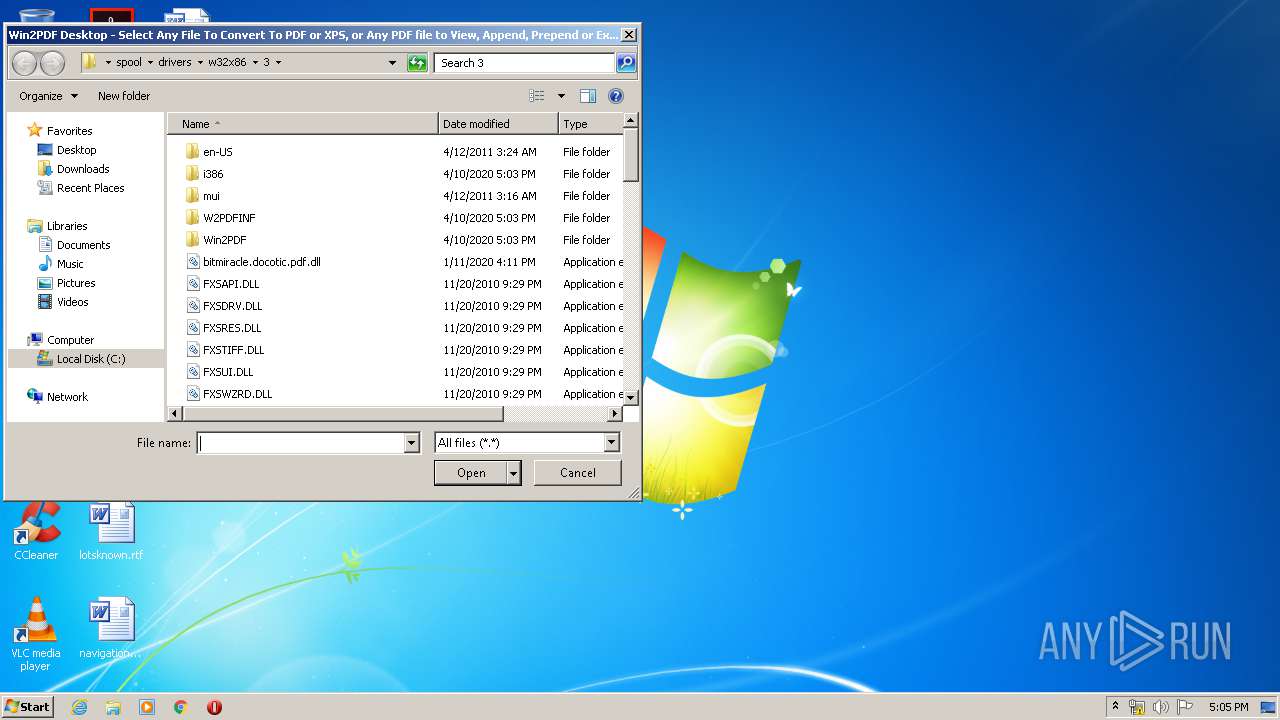
| 1944 | "C:\Windows\system32\spool\drivers\w32x86\3\WIN2PDF.exe" -addxpsprinter -warnings -none | C:\Windows\system32\spool\drivers\w32x86\3\WIN2PDF.exe | — | w2pdf_setup.tmp | |||||||||||
User: admin Company: Dane Prairie Systems, LLC - http://www.win2pdf.com Integrity Level: HIGH Description: Win2PDF Application Exit code: 0 Version: 10.0.62 Modules
| |||||||||||||||
| 2064 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,13799753511880481531,17514590137264624288,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5493009813873864399 --mojo-platform-channel-handle=4748 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2072 | "C:\Users\admin\AppData\Local\Temp\is-CA1E0.tmp\w2pdf_setup.tmp" /SL5="$80246,20588844,76288,C:\Users\admin\Downloads\w2pdf_setup.exe" /SPAWNWND=$801FE /NOTIFYWND=$90130 | C:\Users\admin\AppData\Local\Temp\is-CA1E0.tmp\w2pdf_setup.tmp | w2pdf_setup.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 2244 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,13799753511880481531,17514590137264624288,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13734564843222753722 --mojo-platform-channel-handle=5052 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
3 991
Read events
2 994
Write events
985
Delete events
12
Modification events
| (PID) Process: | (3364) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3364) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3364) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3364) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3364) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3528) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3364-13231008169175875 |
Value: 259 | |||
| (PID) Process: | (3364) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3364) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3364) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (3364) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
58
Suspicious files
81
Text files
310
Unknown types
33
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E9098A9-D24.pma | — | |
MD5:— | SHA256:— | |||
| 3364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\fc059caf-9170-4360-b67a-6f89e97d01fa.tmp | — | |
MD5:— | SHA256:— | |||
| 3364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFa6e20b.TMP | text | |
MD5:— | SHA256:— | |||
| 3364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\metadata\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFa6e3f0.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
54
DNS requests
31
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3896 | chrome.exe | GET | 302 | 172.217.21.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 519 b | whitelisted |
3896 | chrome.exe | GET | 302 | 172.217.21.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 524 b | whitelisted |
3364 | chrome.exe | GET | 304 | 8.248.113.254:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 56.0 Kb | whitelisted |
3364 | chrome.exe | GET | 200 | 8.248.113.254:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 56.0 Kb | whitelisted |
3896 | chrome.exe | GET | 200 | 173.194.163.108:80 | http://r6---sn-5go7yne6.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=bs&mip=82.102.22.104&mm=28&mn=sn-5go7yne6&ms=nvh&mt=1586534415&mv=m&mvi=5&pl=24&shardbypass=yes | US | crx | 862 Kb | whitelisted |
3896 | chrome.exe | GET | 200 | 173.194.150.199:80 | http://r1---sn-5goeen7k.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=QJ&mip=82.102.22.104&mm=28&mn=sn-5goeen7k&ms=nvh&mt=1586534415&mv=m&mvi=0&pl=24&shardbypass=yes | US | crx | 293 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3896 | chrome.exe | 172.217.22.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3896 | chrome.exe | 172.217.21.205:443 | accounts.google.com | Google Inc. | US | whitelisted |
3896 | chrome.exe | 104.26.6.112:443 | www.win2pdf.com | Cloudflare Inc | US | unknown |
3896 | chrome.exe | 172.217.23.138:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3896 | chrome.exe | 104.16.133.229:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | suspicious |
3896 | chrome.exe | 104.17.23.75:443 | embed.videodelivery.net | Cloudflare Inc | US | shared |
3896 | chrome.exe | 104.16.132.229:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | suspicious |
3896 | chrome.exe | 185.172.148.132:443 | seal-minnesota.bbb.org | proinity GmbH | DE | malicious |
3896 | chrome.exe | 172.217.18.163:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3896 | chrome.exe | 93.184.220.42:443 | static.olark.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.win2pdf.com |
| unknown |
accounts.google.com |
| shared |
fonts.googleapis.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
ajax.cloudflare.com |
| whitelisted |
embed.videodelivery.net |
| whitelisted |
seal-minnesota.bbb.org |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.google.com |
| malicious |
Threats
Process | Message |
|---|---|
spoolsv.exe | Enabling event logging 0xff, Win2PDF 10.0.62 http://www.win2pdf.com |
spoolsv.exe | DrvPrinterEvent 3. |
spoolsv.exe | DrvPrinterEvent 3, returned 1, returning TRUE |
spoolsv.exe | DrvPrinterEvent 3. |
spoolsv.exe | DrvPrinterEvent 3, returned 1, returning TRUE |