| File name: | Fliqlo.scr |
| Full analysis: | https://app.any.run/tasks/6f931efd-a0e3-4f15-94be-edd133d5ec05 |
| Verdict: | Malicious activity |
| Analysis date: | June 25, 2023, 18:02:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 6156DFBD547C0074F66D3A06D840A665 |
| SHA1: | 491611F7F8E112275A3E47E84B4E4C5788F2369F |
| SHA256: | 2E0A46B385F21C081F69C940BF850656538A43DD8A1860093B88737F4FF82F8D |
| SSDEEP: | 768:WZLE4ljuHcqfqoHreSORn52qiYmLEi9HejBq77777Ktou4LGM0cm:WZLE8qcq7u58YCEZB9BvCm |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads settings of System Certificates
- Fliqlo.scr.exe (PID: 3096)
Reads Microsoft Outlook installation path
- Fliqlo.scr.exe (PID: 3096)
Reads security settings of Internet Explorer
- Fliqlo.scr.exe (PID: 3096)
Reads the Internet Settings
- Fliqlo.scr.exe (PID: 3096)
Reads Internet Explorer settings
- Fliqlo.scr.exe (PID: 3096)
Checks Windows Trust Settings
- Fliqlo.scr.exe (PID: 3096)
INFO
The process checks LSA protection
- Fliqlo.scr.exe (PID: 3096)
Checks supported languages
- Fliqlo.scr.exe (PID: 3096)
Checks proxy server information
- Fliqlo.scr.exe (PID: 3096)
Reads the computer name
- Fliqlo.scr.exe (PID: 3096)
Reads the machine GUID from the registry
- Fliqlo.scr.exe (PID: 3096)
Create files in a temporary directory
- Fliqlo.scr.exe (PID: 3096)
Creates files or folders in the user directory
- Fliqlo.scr.exe (PID: 3096)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
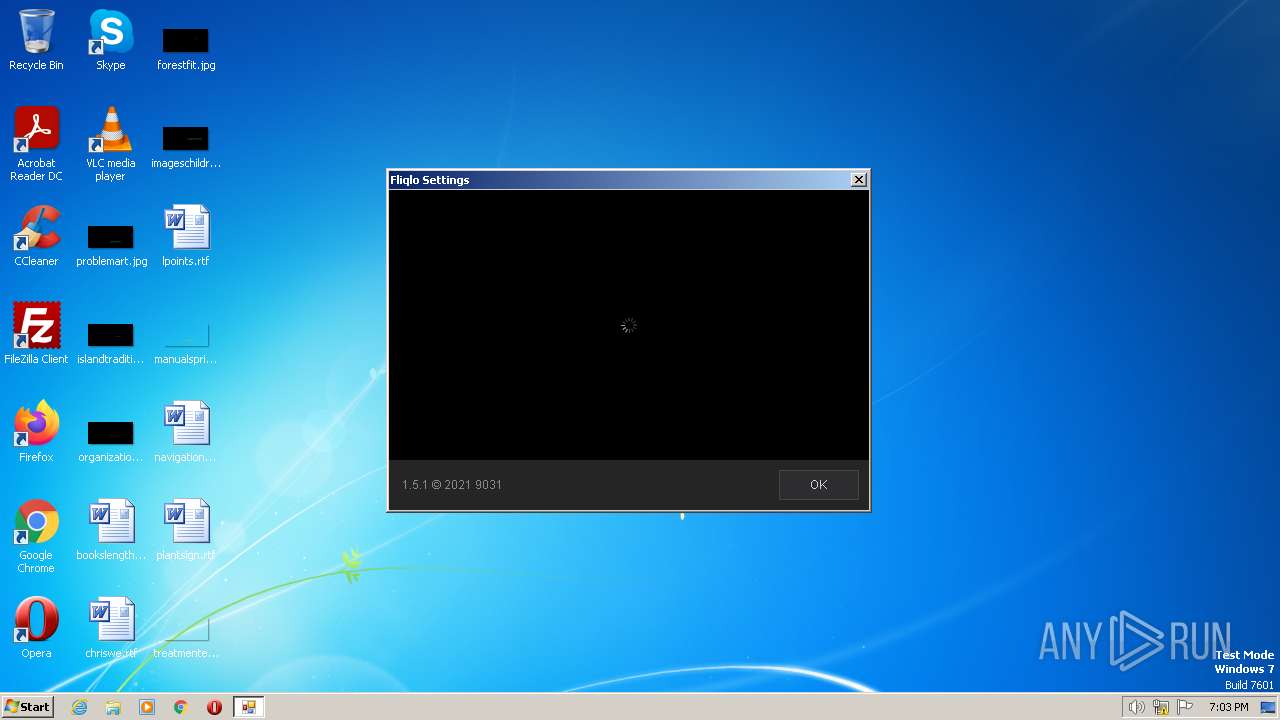
| AssemblyVersion: | 1.5.1.0 |
|---|---|
| ProductVersion: | 1.5.1 |
| ProductName: | Fliqlo |
| OriginalFileName: | Fliqlo.exe |
| LegalTrademarks: | - |
| LegalCopyright: | © 2021 9031 |
| InternalName: | Fliqlo.exe |
| FileVersion: | 1.5.1.0 |
| FileDescription: | Fliqlo |
| CompanyName: | 9031 |
| Comments: | Flip clock screensaver |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.5.1.0 |
| FileVersionNumber: | 1.5.1.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 6 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x9a6a |
| UninitializedDataSize: | - |
| InitializedDataSize: | 355840 |
| CodeSize: | 31744 |
| LinkerVersion: | 48 |
| PEType: | PE32 |
| ImageFileCharacteristics: | Executable, Large address aware |
| TimeStamp: | 2021:03:06 09:45:43+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 06-Mar-2021 09:45:43 |
| Comments: | Flip clock screensaver |
| CompanyName: | 9031 |
| FileDescription: | Fliqlo |
| FileVersion: | 1.5.1.0 |
| InternalName: | Fliqlo.exe |
| LegalCopyright: | © 2021 9031 |
| LegalTrademarks: | - |
| OriginalFilename: | Fliqlo.exe |
| ProductName: | Fliqlo |
| ProductVersion: | 1.5.1 |
| Assembly Version: | 1.5.1.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 06-Mar-2021 09:45:43 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x00007A70 | 0x00007C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.32001 |
.rsrc | 0x0000A000 | 0x00056A64 | 0x00056C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.94568 |
.reloc | 0x00062000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.0815394 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 3.97037 | 67624 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 4.09571 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 4.33695 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 4.34797 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 2.6474 | 76 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
37
Monitored processes
1
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3096 | "C:\Users\admin\AppData\Local\Temp\Fliqlo.scr.exe" | C:\Users\admin\AppData\Local\Temp\Fliqlo.scr.exe | explorer.exe | ||||||||||||
User: admin Company: 9031 Integrity Level: MEDIUM Description: Fliqlo Exit code: 0 Version: 1.5.1.0 Modules
| |||||||||||||||
Total events
6 583
Read events
6 553
Write events
29
Delete events
1
Modification events
| (PID) Process: | (3096) Fliqlo.scr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3096) Fliqlo.scr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3096) Fliqlo.scr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3096) Fliqlo.scr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3096) Fliqlo.scr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3096) Fliqlo.scr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000003D010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A80164000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3096) Fliqlo.scr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3096) Fliqlo.scr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3096) Fliqlo.scr.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3096) Fliqlo.scr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\DOMStorage\fliqlo.app |
| Operation: | write | Name: | Total |
Value: 3 | |||
Executable files
0
Suspicious files
16
Text files
8
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3096 | Fliqlo.scr.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:579E1ADCF2477AA69F6DF9350592E9F5 | SHA256:A11F7DA0A37A808049FEB8643CE3FF485F5F68F6A0BAB3F8E6F4883FEEC2CBEF | |||
| 3096 | Fliqlo.scr.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:EB0AE3ED4155EE785E7205AD21856BE7 | SHA256:1E0F84406DABD25ABDEEC54025B9AD1D3114B9219C3D7DB46BA42764466E7A2F | |||
| 3096 | Fliqlo.scr.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:0FD7E9860FC3267A7A979422173DA802 | SHA256:BC8CE0F2D14B5F131FBD93AC2325456F60332FA7D14CE5B180756D261B7A3BE2 | |||
| 3096 | Fliqlo.scr.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:F7DCB24540769805E5BB30D193944DCE | SHA256:6B88C6AC55BBD6FEA0EBE5A760D1AD2CFCE251C59D0151A1400701CB927E36EA | |||
| 3096 | Fliqlo.scr.exe | C:\Users\admin\AppData\Local\Temp\CabC9B6.tmp | compressed | |
MD5:3AC860860707BAAF32469FA7CC7C0192 | SHA256:D015145D551ECD14916270EFAD773BBC9FD57FAD2228D2C24559F696C961D904 | |||
| 3096 | Fliqlo.scr.exe | C:\Users\admin\AppData\Local\Temp\TarC9B7.tmp | cat | |
MD5:4FF65AD929CD9A367680E0E5B1C08166 | SHA256:C8733C93CC5AAF5CA206D06AF22EE8DBDEC764FB5085019A6A9181FEB9DFDEE6 | |||
| 3096 | Fliqlo.scr.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:3AC860860707BAAF32469FA7CC7C0192 | SHA256:D015145D551ECD14916270EFAD773BBC9FD57FAD2228D2C24559F696C961D904 | |||
| 3096 | Fliqlo.scr.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:60FE01DF86BE2E5331B0CDBE86165686 | SHA256:C08CCBC876CD5A7CDFA9670F9637DA57F6A1282198A9BC71FC7D7247A6E5B7A8 | |||
| 3096 | Fliqlo.scr.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B04D94D0CE8D119897ABB0853B0C53AD | binary | |
MD5:D4BA38BC9C264DE349F3BB8208B6FF8D | SHA256:D69812E94293A801540A152E683851D09958B92F7B2111CBAF932AF18B438BA9 | |||
| 3096 | Fliqlo.scr.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:85C9D59303F379B495D801226EC211B5 | SHA256:A9220699BBAE2901ED026DB8FF56EF885BB7FBC781A0870DC84F98E1CEC74C50 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
13
DNS requests
7
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3096 | Fliqlo.scr.exe | GET | 200 | 142.250.184.227:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
3096 | Fliqlo.scr.exe | GET | 200 | 2.19.117.11:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgNGpvatyBnvIjtFKbRtsWDwSg%3D%3D | GB | der | 503 b | shared |
3096 | Fliqlo.scr.exe | GET | 200 | 142.250.184.227:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | binary | 724 b | whitelisted |
3096 | Fliqlo.scr.exe | GET | 200 | 142.250.184.227:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEHewLUSPPyAaEPVUMepwEb8%3D | US | binary | 471 b | whitelisted |
3096 | Fliqlo.scr.exe | GET | 200 | 2.19.145.140:80 | http://x1.c.lencr.org/ | GB | der | 717 b | whitelisted |
3096 | Fliqlo.scr.exe | GET | 200 | 8.253.204.249:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?881b05aa8547f5d4 | US | compressed | 4.70 Kb | whitelisted |
3096 | Fliqlo.scr.exe | GET | 200 | 8.253.204.249:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?d25b7782f1d8208d | US | compressed | 62.3 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3096 | Fliqlo.scr.exe | 157.7.44.174:443 | fliqlo.app | GMO Internet,Inc | JP | suspicious |
1076 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3096 | Fliqlo.scr.exe | 8.253.204.249:80 | ctldl.windowsupdate.com | LEVEL3 | US | suspicious |
820 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3096 | Fliqlo.scr.exe | 2.19.145.140:80 | x1.c.lencr.org | AKAMAI-AS | GB | unknown |
3096 | Fliqlo.scr.exe | 142.250.184.227:80 | ocsp.pki.goog | GOOGLE | US | whitelisted |
3096 | Fliqlo.scr.exe | 2.19.117.11:80 | r3.o.lencr.org | Akamai International B.V. | GB | unknown |
3096 | Fliqlo.scr.exe | 216.239.32.36:443 | region1.google-analytics.com | GOOGLE | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
fliqlo.app |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
r3.o.lencr.org |
| shared |
www.googletagmanager.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
region1.google-analytics.com |
| whitelisted |