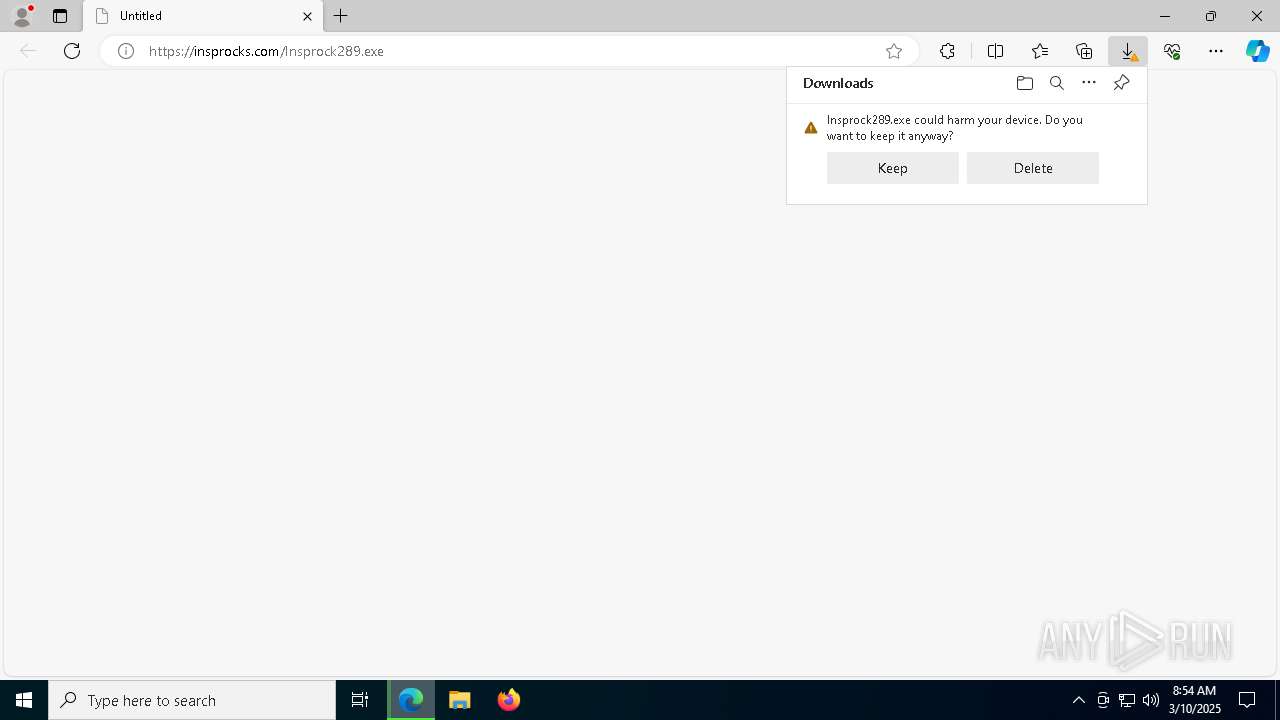
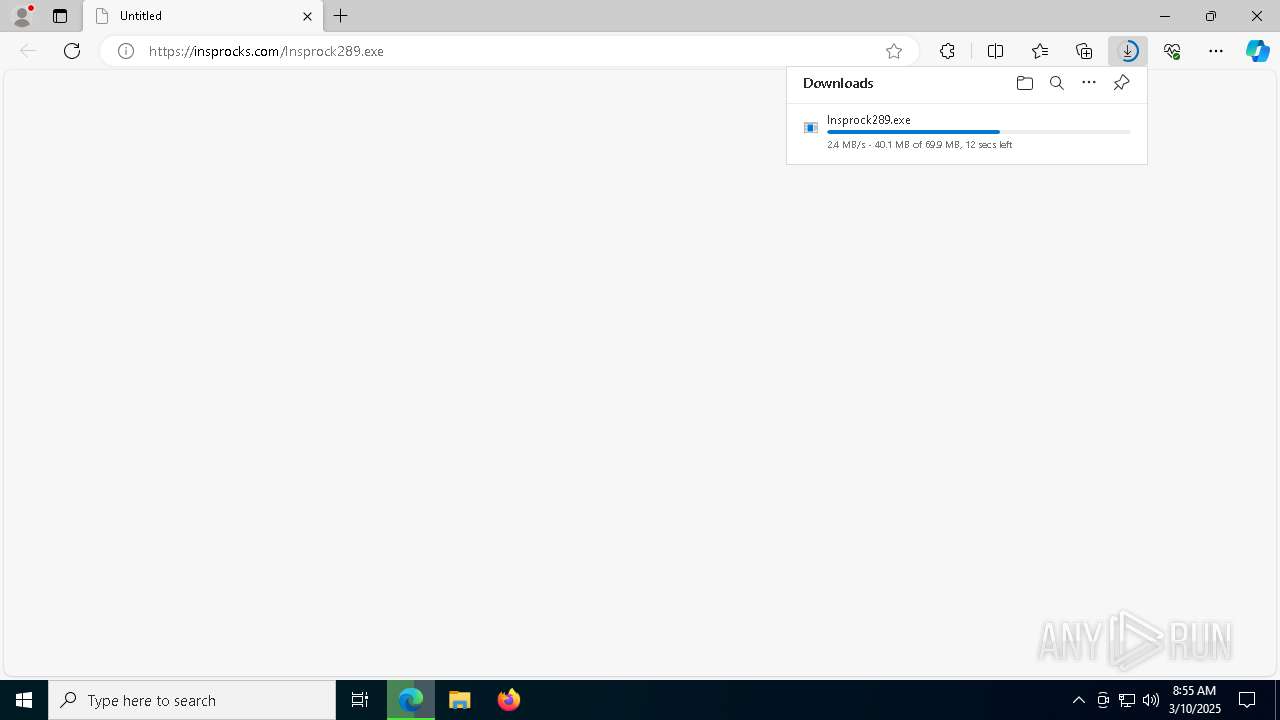
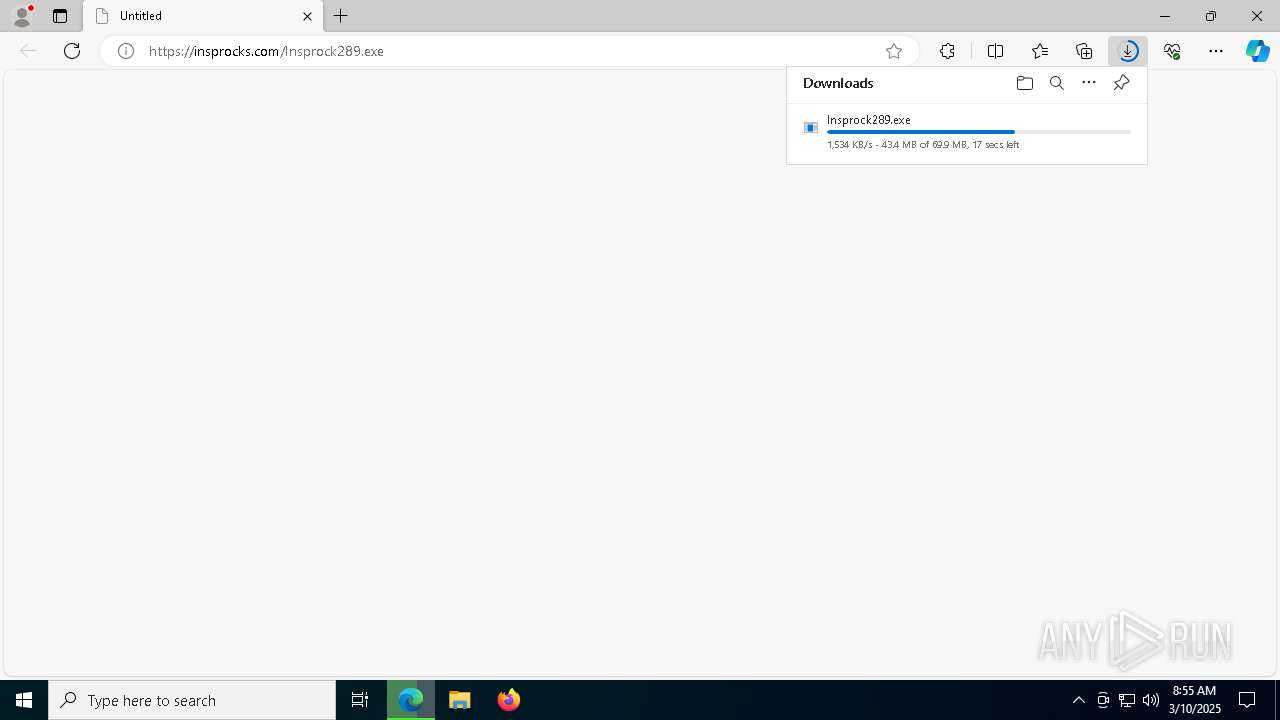
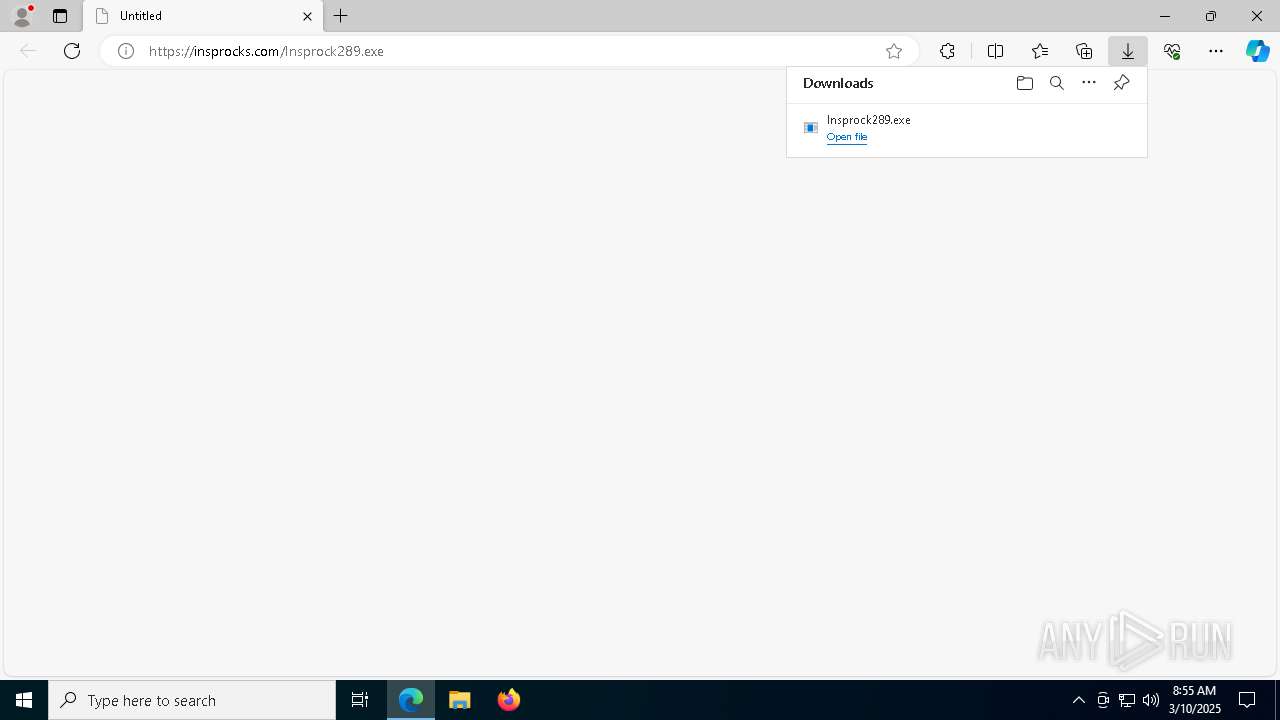
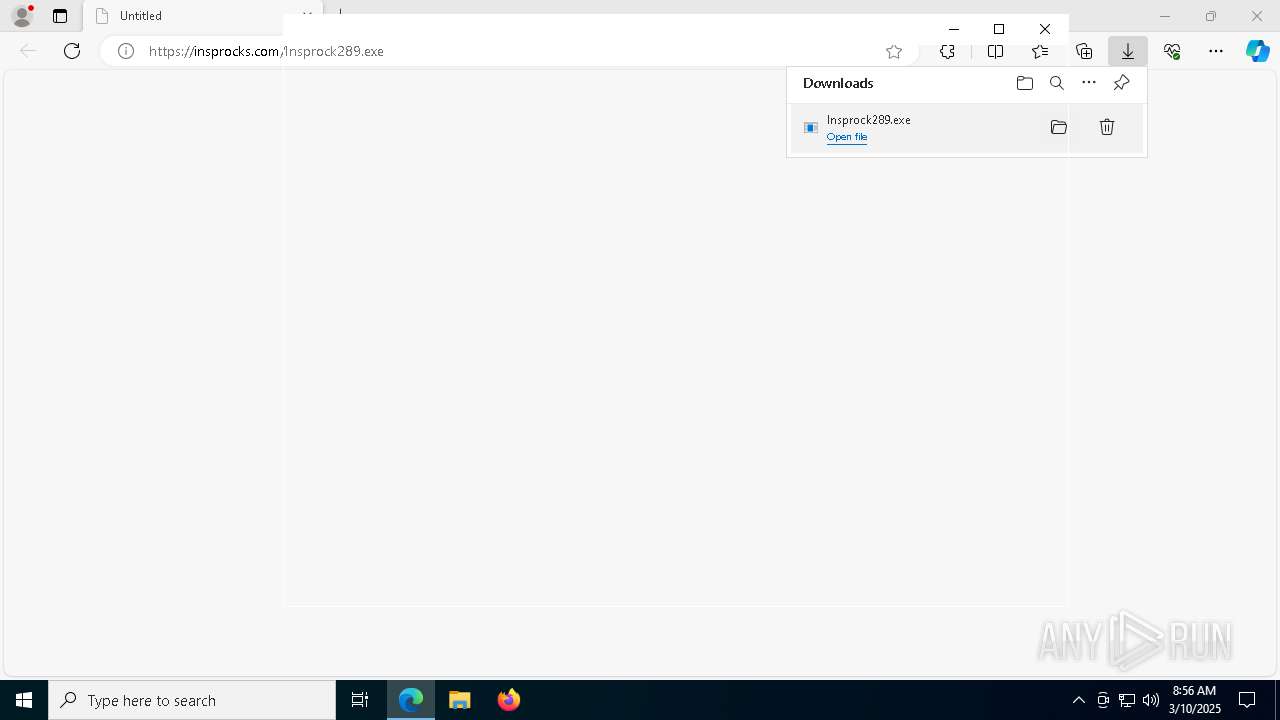
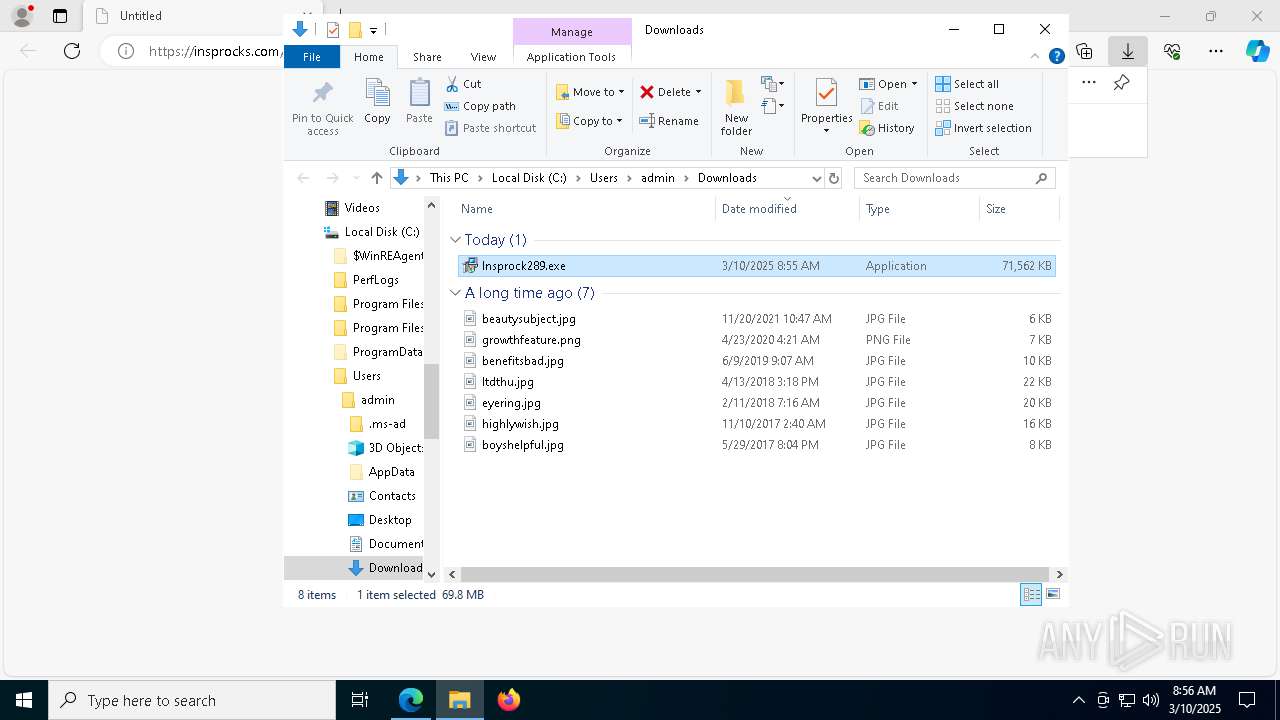
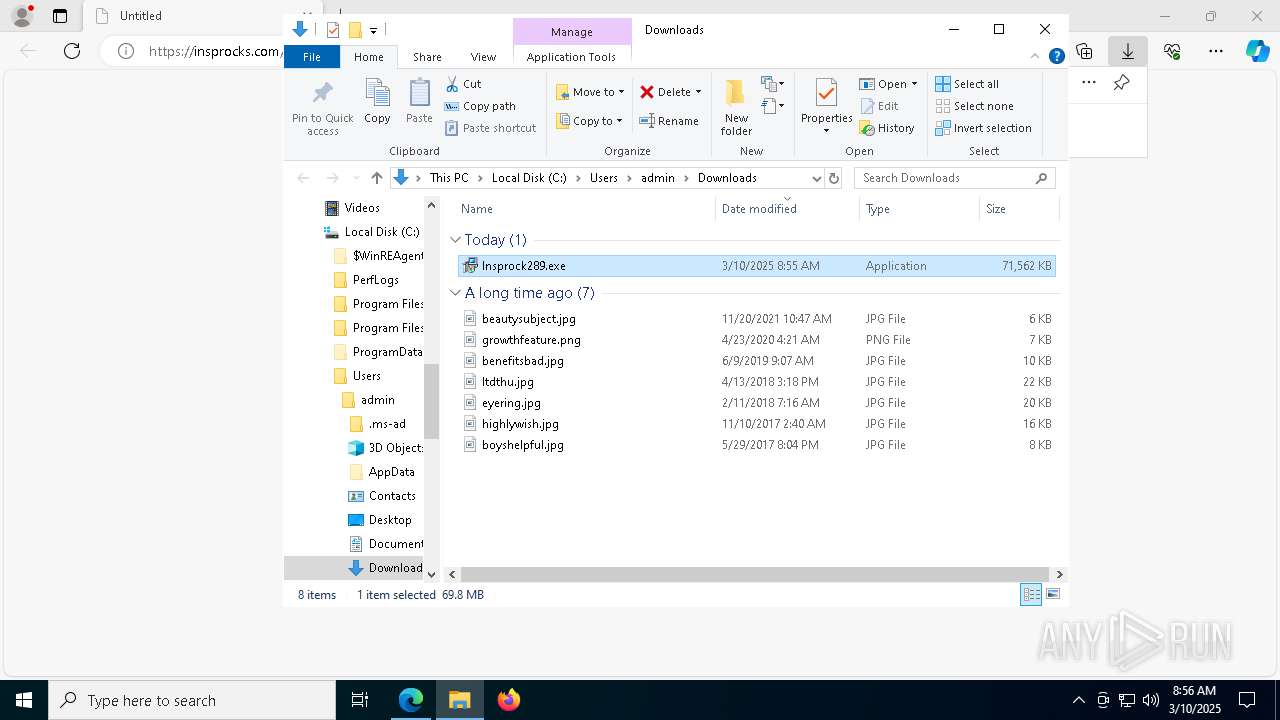
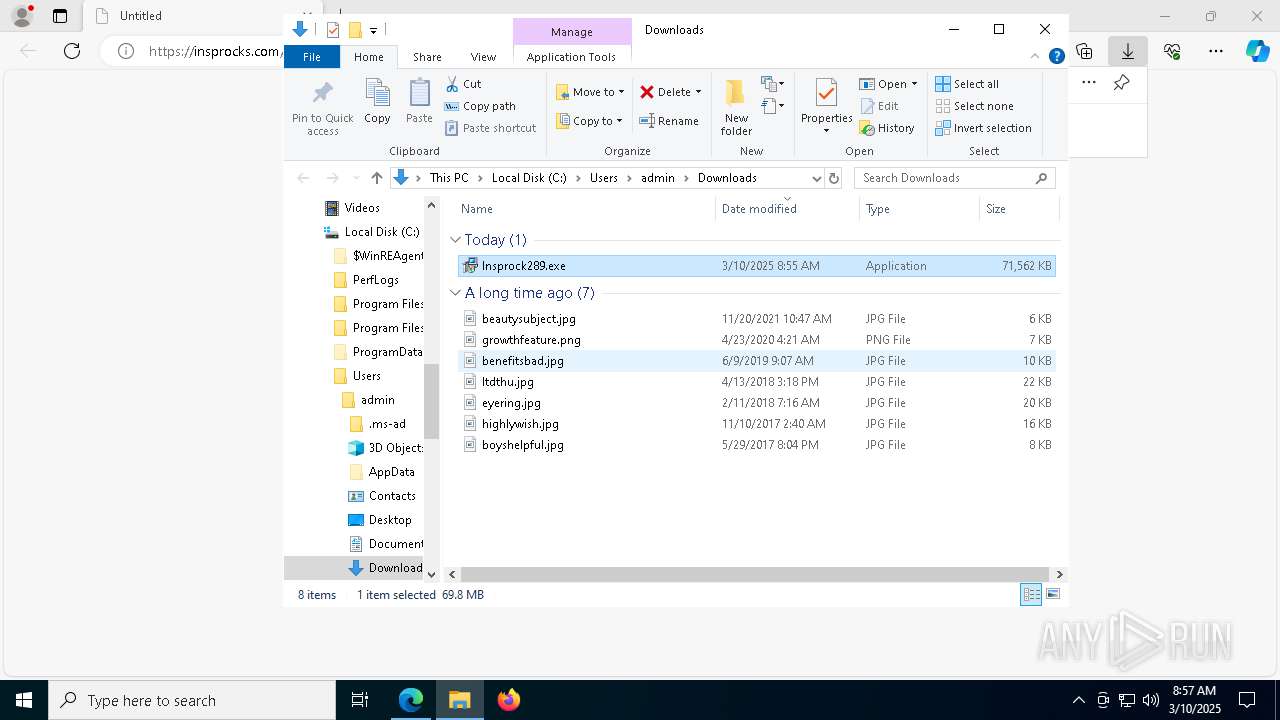
| URL: | https://insprocks.com/Insprock289.exe |
| Full analysis: | https://app.any.run/tasks/8a153f4c-f0b2-48e3-915c-5e4a766444bd |
| Verdict: | Malicious activity |
| Analysis date: | March 10, 2025, 08:54:41 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 83E55D7060B3833A53BFEA2F89B4B1F8 |
| SHA1: | 957A18B3E1EAC8DE3AEB536E5BA3902E4C465A21 |
| SHA256: | 2DFFDCD33897B7343DEE0F04793088B86DCB71E6B09FB9CAF5DB5D26C21974D8 |
| SSDEEP: | 3:N8LVX9nN4UAdA:2hX9J |
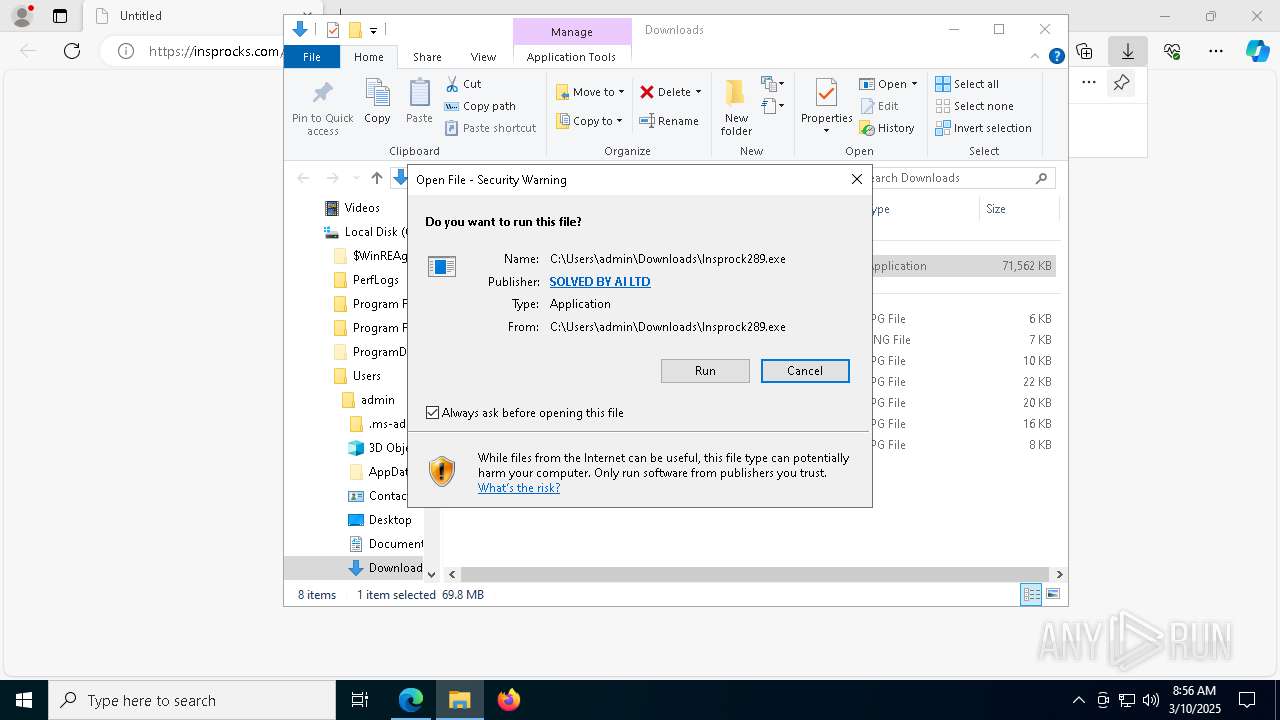
MALICIOUS
Executing a file with an untrusted certificate
- Insprock289.exe (PID: 8152)
Changes powershell execution policy (Unrestricted)
- Three.exe (PID: 7968)
SUSPICIOUS
Creates file in the systems drive root
- explorer.exe (PID: 5492)
The process creates files with name similar to system file names
- Insprock289.exe (PID: 8152)
Malware-specific behavior (creating "System.dll" in Temp)
- Insprock289.exe (PID: 8152)
Executable content was dropped or overwritten
- Insprock289.exe (PID: 8152)
Drops 7-zip archiver for unpacking
- Insprock289.exe (PID: 8152)
Reads security settings of Internet Explorer
- Insprock289.exe (PID: 8152)
Process drops legitimate windows executable
- Insprock289.exe (PID: 8152)
Starts CMD.EXE for commands execution
- Three.exe (PID: 7968)
Starts POWERSHELL.EXE for commands execution
- Three.exe (PID: 7968)
The process hides Powershell's copyright startup banner
- Three.exe (PID: 7968)
Starts application with an unusual extension
- cmd.exe (PID: 4844)
There is functionality for taking screenshot (YARA)
- Insprock289.exe (PID: 8152)
- Three.exe (PID: 776)
Application launched itself
- Three.exe (PID: 7968)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 7828)
The process bypasses the loading of PowerShell profile settings
- Three.exe (PID: 7968)
Connects to the server without a host name
- Three.exe (PID: 7968)
INFO
The sample compiled with english language support
- msedge.exe (PID: 5596)
- Insprock289.exe (PID: 8152)
- msedge.exe (PID: 7932)
Checks supported languages
- identity_helper.exe (PID: 5728)
- Insprock289.exe (PID: 8152)
- chcp.com (PID: 1164)
- Three.exe (PID: 776)
- Three.exe (PID: 5132)
- Three.exe (PID: 7968)
Executable content was dropped or overwritten
- msedge.exe (PID: 5596)
- msedge.exe (PID: 7932)
Reads Environment values
- identity_helper.exe (PID: 5728)
Reads the software policy settings
- slui.exe (PID: 1056)
- explorer.exe (PID: 5492)
Reads the computer name
- identity_helper.exe (PID: 5728)
- Insprock289.exe (PID: 8152)
- Three.exe (PID: 7968)
- Three.exe (PID: 776)
- Three.exe (PID: 5132)
Reads security settings of Internet Explorer
- explorer.exe (PID: 5492)
Creates files or folders in the user directory
- explorer.exe (PID: 5492)
- Three.exe (PID: 7968)
Checks proxy server information
- explorer.exe (PID: 5492)
- Three.exe (PID: 7968)
Create files in a temporary directory
- Insprock289.exe (PID: 8152)
Changes the display of characters in the console
- cmd.exe (PID: 4844)
Application launched itself
- msedge.exe (PID: 5596)
Process checks computer location settings
- Three.exe (PID: 7968)
Reads the machine GUID from the registry
- Three.exe (PID: 7968)
Node.js compiler has been detected
- Three.exe (PID: 7968)
- Three.exe (PID: 5132)
- Three.exe (PID: 776)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 1164)
- powershell.exe (PID: 7000)
- powershell.exe (PID: 8980)
- powershell.exe (PID: 9036)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
238
Monitored processes
103
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 680 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x290,0x294,0x298,0x288,0x2a0,0x7ffc88115fd8,0x7ffc88115fe4,0x7ffc88115ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 776 | "C:\Users\admin\AppData\Local\Temp\2tzicnRZuZfCGIckIZC2YPlrndK\Three.exe" --type=gpu-process --user-data-dir="C:\Users\admin\AppData\Roaming\Scatter" --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --field-trial-handle=1980,i,10373005449671425352,1264111479795943645,262144 --disable-features=SpareRendererForSitePerProcess,WinDelaySpellcheckServiceInit,WinRetrieveSuggestionsOnlyOnDemand --variations-seed-version --mojo-platform-channel-handle=1972 /prefetch:2 | C:\Users\admin\AppData\Local\Temp\2tzicnRZuZfCGIckIZC2YPlrndK\Three.exe | — | Three.exe | |||||||||||
User: admin Company: Rack Integrity Level: LOW Description: Leave labor wave Exit code: 0 Version: 0.7.4 Modules
| |||||||||||||||
| 856 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7504 --field-trial-handle=2296,i,802674942655746656,17095422681898899351,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 920 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1012 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7580 --field-trial-handle=2296,i,802674942655746656,17095422681898899351,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1056 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1128 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_search_indexer.mojom.SearchIndexerInterfaceBroker --lang=en-US --service-sandbox-type=search_indexer --message-loop-type-ui --no-appcompat-clear --mojo-platform-channel-handle=6808 --field-trial-handle=2296,i,802674942655746656,17095422681898899351,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1164 | chcp | C:\Windows\SysWOW64\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1164 | C:\WINDOWS\system32\WindowsPowerShell\v1.0\powershell.exe -NoProfile -NoLogo -InputFormat Text -NoExit -ExecutionPolicy Unrestricted -Command - | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | Three.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1180 | C:\WINDOWS\system32\WindowsPowerShell\v1.0\powershell.exe -NoProfile -NoLogo -InputFormat Text -NoExit -ExecutionPolicy Unrestricted -Command - | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | Three.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
126 796
Read events
126 750
Write events
46
Delete events
0
Modification events
| (PID) Process: | (5492) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\5\ApplicationViewManagement\W32:0000000000060292 |
| Operation: | write | Name: | VirtualDesktop |
Value: 1000000030304456BFA0DB55E4278845B426357D5B5F97B3 | |||
| (PID) Process: | (5492) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\5\ApplicationViewManagement\W32:0000000000030276 |
| Operation: | write | Name: | VirtualDesktop |
Value: 1000000030304456BFA0DB55E4278845B426357D5B5F97B3 | |||
| (PID) Process: | (2284) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2284) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2284) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2284) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2284) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2284) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | DisableFirstRunCustomize |
Value: 1 | |||
| (PID) Process: | (5596) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (5596) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
Executable files
30
Suspicious files
466
Text files
127
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5596 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10bc4d.TMP | — | |
MD5:— | SHA256:— | |||
| 5596 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5596 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10bc4d.TMP | — | |
MD5:— | SHA256:— | |||
| 5596 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5596 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10bc5c.TMP | — | |
MD5:— | SHA256:— | |||
| 5596 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5596 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10bc5c.TMP | — | |
MD5:— | SHA256:— | |||
| 5596 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5596 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10bc5c.TMP | — | |
MD5:— | SHA256:— | |||
| 5596 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
96
TCP/UDP connections
58
DNS requests
63
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7932 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
2772 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1741808917&P2=404&P3=2&P4=Z9ByG4Yp4RQb9NZXUCpXQICdcDmMRdoXXe2pP5N6jKzuFEO5XKQOWEpE532dP2xk3fS4Z68A%2bbDotII7evosNg%3d%3d | unknown | — | — | whitelisted |
5124 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2772 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1741808917&P2=404&P3=2&P4=Z9ByG4Yp4RQb9NZXUCpXQICdcDmMRdoXXe2pP5N6jKzuFEO5XKQOWEpE532dP2xk3fS4Z68A%2bbDotII7evosNg%3d%3d | unknown | — | — | whitelisted |
5124 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2772 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1741812517&P2=404&P3=2&P4=Yugir%2b89O7FcQ990m6MQ2CKbwm4%2b6aEQi5r6pGo7GXssmnkJewistDfZySTLoIIk7bBuKYW3cG34T2P43Dcf8Q%3d%3d | unknown | — | — | whitelisted |
2772 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1741808917&P2=404&P3=2&P4=Z9ByG4Yp4RQb9NZXUCpXQICdcDmMRdoXXe2pP5N6jKzuFEO5XKQOWEpE532dP2xk3fS4Z68A%2bbDotII7evosNg%3d%3d | unknown | — | — | whitelisted |
2772 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1741812517&P2=404&P3=2&P4=Yugir%2b89O7FcQ990m6MQ2CKbwm4%2b6aEQi5r6pGo7GXssmnkJewistDfZySTLoIIk7bBuKYW3cG34T2P43Dcf8Q%3d%3d | unknown | — | — | whitelisted |
2772 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1741812517&P2=404&P3=2&P4=Yugir%2b89O7FcQ990m6MQ2CKbwm4%2b6aEQi5r6pGo7GXssmnkJewistDfZySTLoIIk7bBuKYW3cG34T2P43Dcf8Q%3d%3d | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7280 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7280 | msedge.exe | 13.107.21.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5596 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7280 | msedge.exe | 104.21.96.1:443 | insprocks.com | CLOUDFLARENET | — | unknown |
7280 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7280 | msedge.exe | 142.250.186.67:443 | update.googleapis.com | GOOGLE | US | whitelisted |
7280 | msedge.exe | 13.107.246.44:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
insprocks.com |
| unknown |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
edgeservices.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
update.googleapis.com |
| whitelisted |