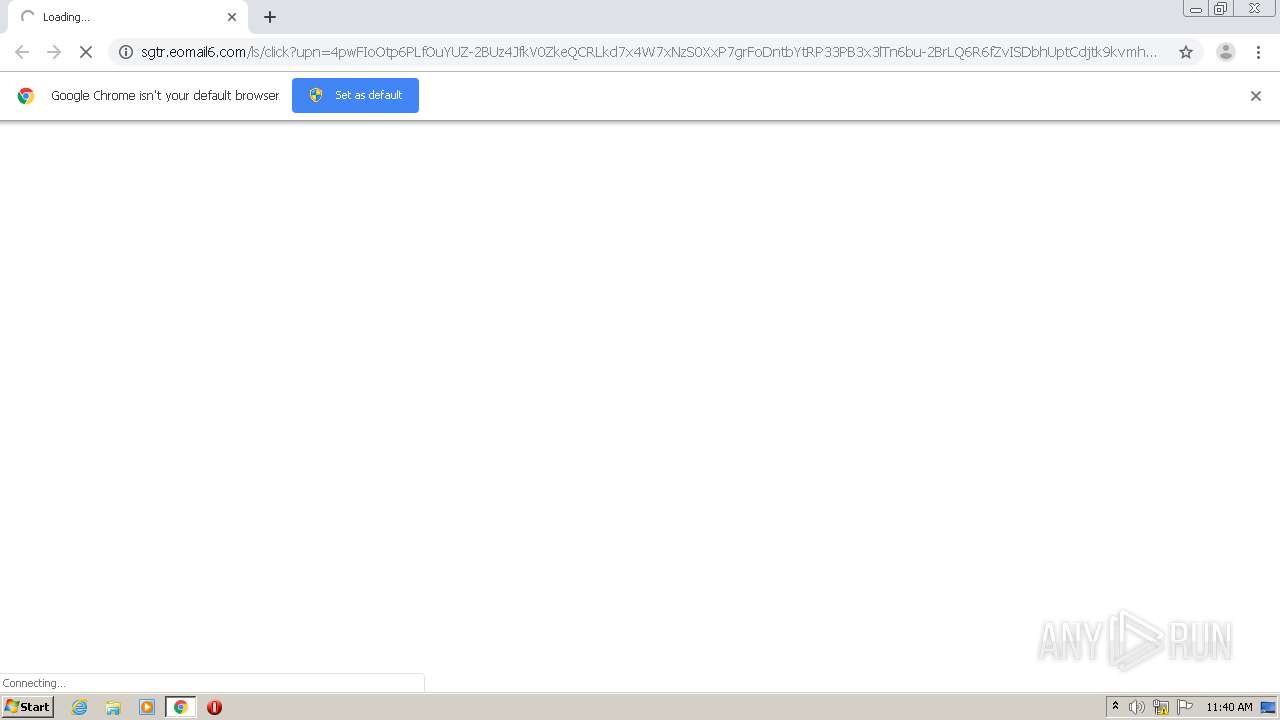
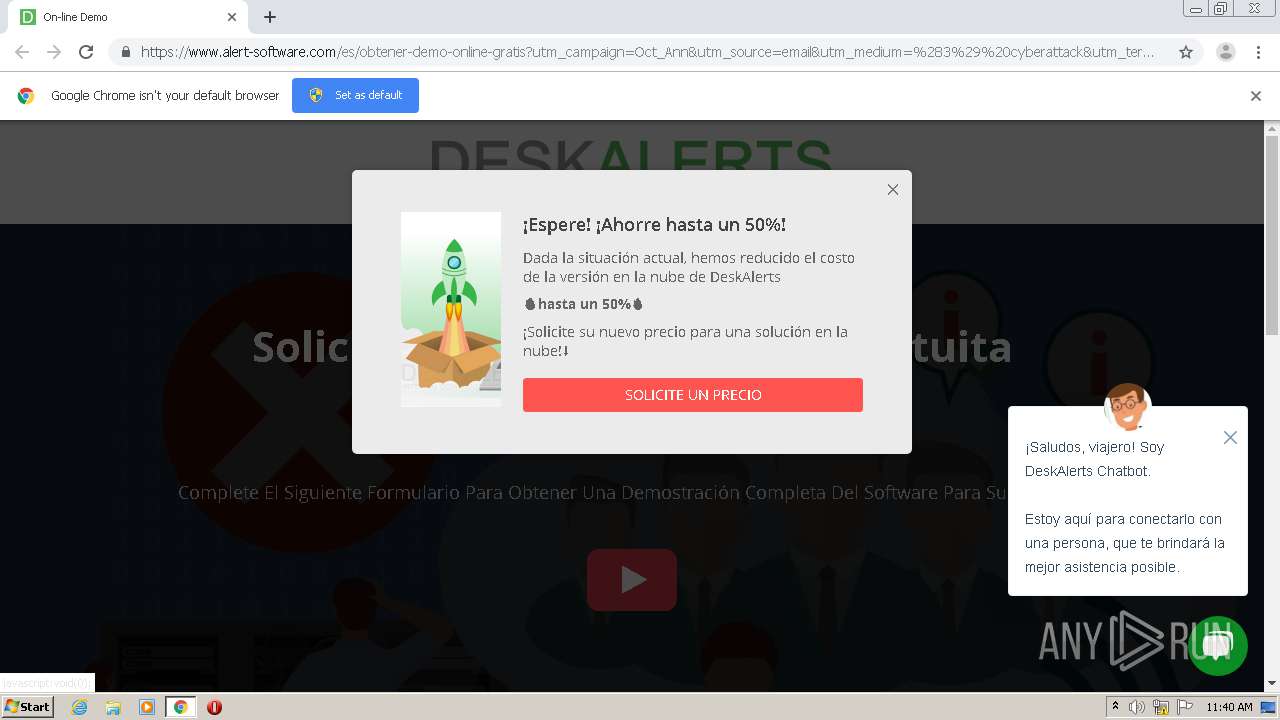
| URL: | http://sgtr.eomail6.com/ls/click?upn=4pwFIoOtp6PLfOuYUZ-2BUz4JfkV0ZkeQCRLkd7x4W7xNzS0XxP7grFoDntbYtRP33PB3x3lTn6bu-2BrLQ6R6fZvISDbhUptCdjtk9kvmhpIof21fMTYQknbGcL6in659YcySctxdPN7SlMlXwSyVWtrEeWGeiQE77J8h8scSN9EcZyuz81ptYM-2BCaVWVCNdVv1ChtnPX-2BJzKur-2B0TGhVsNFj67sltxv-2BBw1RFWSoeoXNsaCul-2B-2FSe-2FH5cz0l8p-2BogJF5TT_mSllOFscLbgTD69Yd5M4ie7J29nbkU-2BTSecdbQNDCjojX6QqcMGyQQz6HohWbFvzOacBw-2BdCClHHPFnBJnQSFaCc8-2F-2BhgGMuwT4QLbPj4eGdWlbpN0OHLivNdIyMSGfMaYizMgYvHLHcOylMmuzwomuCSjRjRewvMk5-2B-2BDAj6cabQG-2FSoL7zJLhP1W23X6drQXxAg-2FKr3yEK1Dg8EY63Gn1RFc6qwW8DZ6vbsScmWps4IJWGxMAnte9R0mnMLFQY4bbxG5v4n6QKrEgMoFWmgj6cJ0cgs5cxNMbIXq2lcMwSOUjOaZeH0LgPznp5Qhpn8BrxPG8Z-2FEWOaDRnLulHf5mv6OA9bkJWIILg-2B9ZN4hS7Y7mpuDkWQYs-2FXPMA-2Fb4cyllPDFOTfOfeZfJbMSD5AMBsCDJzvkBS-2FgHyYBZd0ZPODnNxvia8GuPCXAr9sAjjJImUdOcVMX5ZayD6H6KJTRXDb9wj3ppZqMscwCnK5ZUe-2F2baVMIc90Wdb7blBs49IcHIoNBV1lWePx9JGbaA3YnRQgvWSE0OqvQlN-2FbmGhE0F4275DQPZ3MmEbX-2BaPcNvrJ0VZ4QDISKJPNssRHeV0nZyVK0aIhf4-2BPwdOh5PzSlvwTpE4KSABF7m-2FFMoqtCJKWTGm04MDDjiFSsFrKxHMAROa29Aydy3pwKyYdaxT0sCrLJCFQ-2BlImyEJeYuRWNp-2FMz82pB1QGvvwP4muKSp5sYVFUENcBRaCNxHm1AzA4U3hT3HjTmTM3ZEXR8E2KUiTCaTA4iDaKB2oR1G7e2FtGAKo4zBthY4VcAKU2ARZMalaeUPz7EU5ludgTBiRlRTYj-2BgVoUS02CnUT7jrLloGZzDGHUJUbRD7ehRiZOSYPKzBv2YtGCpa-2BCC4IiqXbVW4ivZb-2FD-2BmeILXww-2F16AOA-3D-3D |
| Full analysis: | https://app.any.run/tasks/8e791a8a-17e1-43d4-a3fd-e719aa80055d |
| Verdict: | Malicious activity |
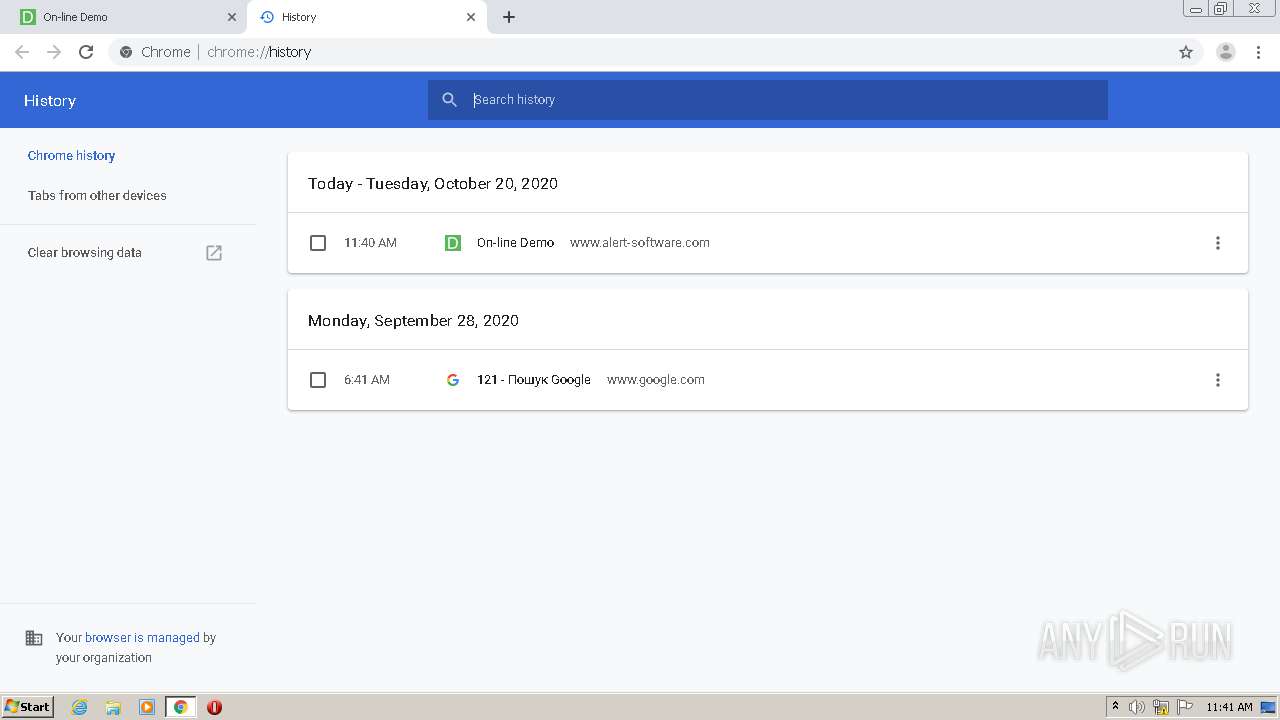
| Analysis date: | October 20, 2020, 10:40:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 28439F5115C609CAC8D66619205D527E |
| SHA1: | A2CFD6CA75A11B0C02203A1D77310B3C061B3964 |
| SHA256: | 2DF9BE0BD26817997A431547D349D7961F22EA25683F7AE5BED5E108D9708D3C |
| SSDEEP: | 24:noNeS50MPzegOdB+gRW4qfQr4aOgggzXIDfpQLLjX+haYC7eBm:nAlBeTDZW4r4aBjz/KgYHk |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads settings of System Certificates
- chrome.exe (PID: 2068)
Reads the hosts file
- chrome.exe (PID: 2068)
- chrome.exe (PID: 2508)
Application launched itself
- chrome.exe (PID: 2508)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
55
Monitored processes
19
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1136 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,2776373049604161251,3083540290480618165,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9042141953274239514 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2380 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1336 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2556 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1436 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,2776373049604161251,3083540290480618165,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=8398004985033886943 --mojo-platform-channel-handle=3668 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1452 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,2776373049604161251,3083540290480618165,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=5803506351052198738 --mojo-platform-channel-handle=3756 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2068 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,2776373049604161251,3083540290480618165,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=4319921922032110353 --mojo-platform-channel-handle=1528 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2080 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,2776373049604161251,3083540290480618165,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15929594614087881387 --mojo-platform-channel-handle=3808 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2108 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,2776373049604161251,3083540290480618165,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15558607137646398677 --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2216 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2224 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,2776373049604161251,3083540290480618165,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7464968599530864652 --renderer-client-id=15 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1788 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2240 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,2776373049604161251,3083540290480618165,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13035419857793958232 --mojo-platform-channel-handle=500 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2508 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://sgtr.eomail6.com/ls/click?upn=4pwFIoOtp6PLfOuYUZ-2BUz4JfkV0ZkeQCRLkd7x4W7xNzS0XxP7grFoDntbYtRP33PB3x3lTn6bu-2BrLQ6R6fZvISDbhUptCdjtk9kvmhpIof21fMTYQknbGcL6in659YcySctxdPN7SlMlXwSyVWtrEeWGeiQE77J8h8scSN9EcZyuz81ptYM-2BCaVWVCNdVv1ChtnPX-2BJzKur-2B0TGhVsNFj67sltxv-2BBw1RFWSoeoXNsaCul-2B-2FSe-2FH5cz0l8p-2BogJF5TT_mSllOFscLbgTD69Yd5M4ie7J29nbkU-2BTSecdbQNDCjojX6QqcMGyQQz6HohWbFvzOacBw-2BdCClHHPFnBJnQSFaCc8-2F-2BhgGMuwT4QLbPj4eGdWlbpN0OHLivNdIyMSGfMaYizMgYvHLHcOylMmuzwomuCSjRjRewvMk5-2B-2BDAj6cabQG-2FSoL7zJLhP1W23X6drQXxAg-2FKr3yEK1Dg8EY63Gn1RFc6qwW8DZ6vbsScmWps4IJWGxMAnte9R0mnMLFQY4bbxG5v4n6QKrEgMoFWmgj6cJ0cgs5cxNMbIXq2lcMwSOUjOaZeH0LgPznp5Qhpn8BrxPG8Z-2FEWOaDRnLulHf5mv6OA9bkJWIILg-2B9ZN4hS7Y7mpuDkWQYs-2FXPMA-2Fb4cyllPDFOTfOfeZfJbMSD5AMBsCDJzvkBS-2FgHyYBZd0ZPODnNxvia8GuPCXAr9sAjjJImUdOcVMX5ZayD6H6KJTRXDb9wj3ppZqMscwCnK5ZUe-2F2baVMIc90Wdb7blBs49IcHIoNBV1lWePx9JGbaA3YnRQgvWSE0OqvQlN-2FbmGhE0F4275DQPZ3MmEbX-2BaPcNvrJ0VZ4QDISKJPNssRHeV0nZyVK0aIhf4-2BPwdOh5PzSlvwTpE4KSABF7m-2FFMoqtCJKWTGm04MDDjiFSsFrKxHMAROa29Aydy3pwKyYdaxT0sCrLJCFQ-2BlImyEJeYuRWNp-2FMz82pB1QGvvwP4muKSp5sYVFUENcBRaCNxHm1AzA4U3hT3HjTmTM3ZEXR8E2KUiTCaTA4iDaKB2oR1G7e2FtGAKo4zBthY4VcAKU2ARZMalaeUPz7EU5ludgTBiRlRTYj-2BgVoUS02CnUT7jrLloGZzDGHUJUbRD7ehRiZOSYPKzBv2YtGCpa-2BCC4IiqXbVW4ivZb-2FD-2BmeILXww-2F16AOA-3D-3D" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
771
Read events
689
Write events
78
Delete events
4
Modification events
| (PID) Process: | (1336) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2508-13247664022901125 |
Value: 259 | |||
| (PID) Process: | (2508) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2508) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2508) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2508) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2508) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2508) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2508) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2508) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2508) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
100
Text files
95
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2508 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F8EBE97-9CC.pma | — | |
MD5:— | SHA256:— | |||
| 2508 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\942b87c2-e9b7-4da2-9534-7b413af6504d.tmp | — | |
MD5:— | SHA256:— | |||
| 2508 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2508 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2508 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2508 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2508 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF2d41b1.TMP | text | |
MD5:— | SHA256:— | |||
| 2508 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2508 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF2d4163.TMP | text | |
MD5:— | SHA256:— | |||
| 2508 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF2d4173.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
67
DNS requests
47
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2068 | chrome.exe | GET | 302 | 167.89.123.54:80 | http://sgtr.eomail6.com/ls/click?upn=4pwFIoOtp6PLfOuYUZ-2BUz4JfkV0ZkeQCRLkd7x4W7xNzS0XxP7grFoDntbYtRP33PB3x3lTn6bu-2BrLQ6R6fZvISDbhUptCdjtk9kvmhpIof21fMTYQknbGcL6in659YcySctxdPN7SlMlXwSyVWtrEeWGeiQE77J8h8scSN9EcZyuz81ptYM-2BCaVWVCNdVv1ChtnPX-2BJzKur-2B0TGhVsNFj67sltxv-2BBw1RFWSoeoXNsaCul-2B-2FSe-2FH5cz0l8p-2BogJF5TT_mSllOFscLbgTD69Yd5M4ie7J29nbkU-2BTSecdbQNDCjojX6QqcMGyQQz6HohWbFvzOacBw-2BdCClHHPFnBJnQSFaCc8-2F-2BhgGMuwT4QLbPj4eGdWlbpN0OHLivNdIyMSGfMaYizMgYvHLHcOylMmuzwomuCSjRjRewvMk5-2B-2BDAj6cabQG-2FSoL7zJLhP1W23X6drQXxAg-2FKr3yEK1Dg8EY63Gn1RFc6qwW8DZ6vbsScmWps4IJWGxMAnte9R0mnMLFQY4bbxG5v4n6QKrEgMoFWmgj6cJ0cgs5cxNMbIXq2lcMwSOUjOaZeH0LgPznp5Qhpn8BrxPG8Z-2FEWOaDRnLulHf5mv6OA9bkJWIILg-2B9ZN4hS7Y7mpuDkWQYs-2FXPMA-2Fb4cyllPDFOTfOfeZfJbMSD5AMBsCDJzvkBS-2FgHyYBZd0ZPODnNxvia8GuPCXAr9sAjjJImUdOcVMX5ZayD6H6KJTRXDb9wj3ppZqMscwCnK5ZUe-2F2baVMIc90Wdb7blBs49IcHIoNBV1lWePx9JGbaA3YnRQgvWSE0OqvQlN-2FbmGhE0F4275DQPZ3MmEbX-2BaPcNvrJ0VZ4QDISKJPNssRHeV0nZyVK0aIhf4-2BPwdOh5PzSlvwTpE4KSABF7m-2FFMoqtCJKWTGm04MDDjiFSsFrKxHMAROa29Aydy3pwKyYdaxT0sCrLJCFQ-2BlImyEJeYuRWNp-2FMz82pB1QGvvwP4muKSp5sYVFUENcBRaCNxHm1AzA4U3hT3HjTmTM3ZEXR8E2KUiTCaTA4iDaKB2oR1G7e2FtGAKo4zBthY4VcAKU2ARZMalaeUPz7EU5ludgTBiRlRTYj-2BgVoUS02CnUT7jrLloGZzDGHUJUbRD7ehRiZOSYPKzBv2YtGCpa-2BCC4IiqXbVW4ivZb-2FD-2BmeILXww-2F16AOA-3D-3D | US | html | 207 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
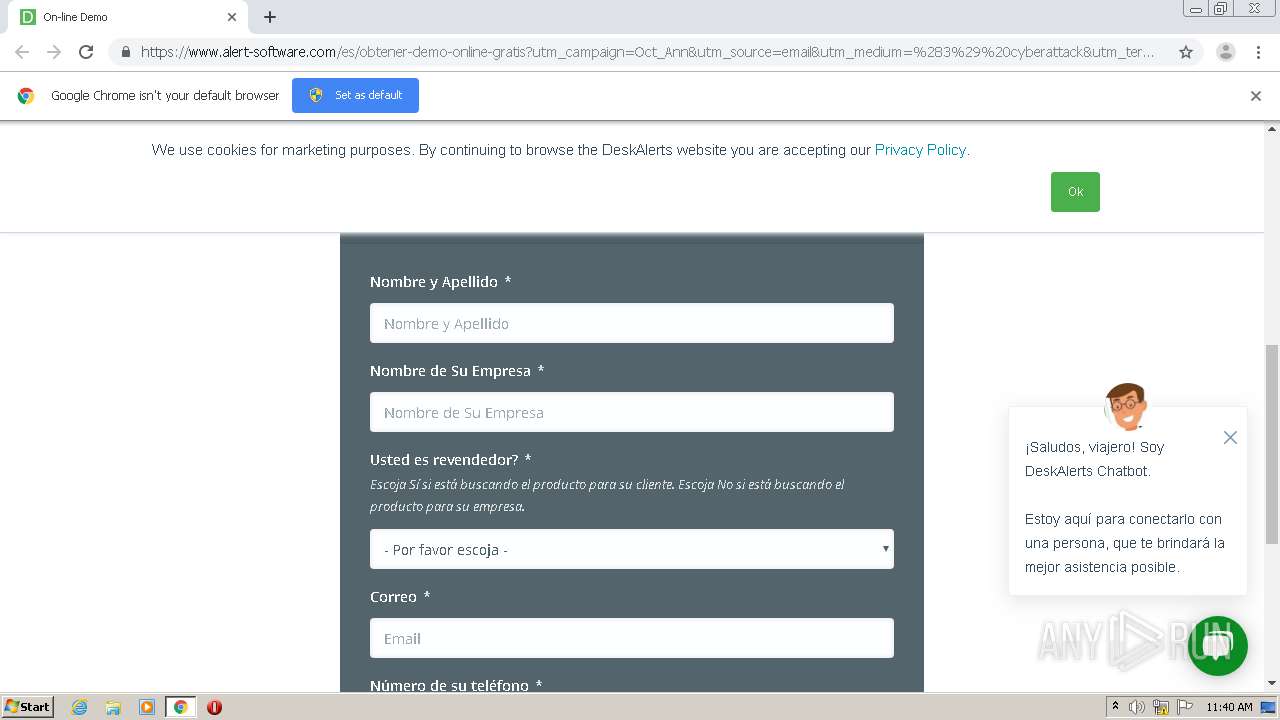
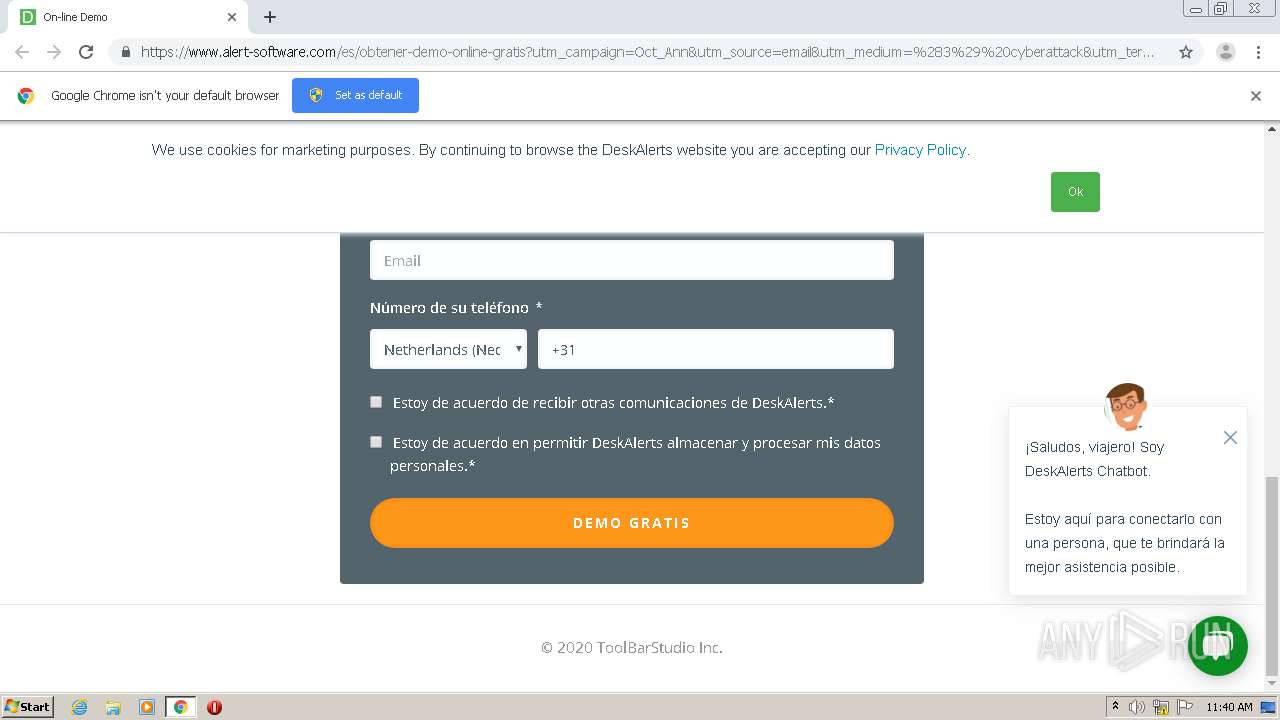
2068 | chrome.exe | 104.17.118.180:443 | www.alert-software.com | Cloudflare Inc | US | shared |
2068 | chrome.exe | 74.125.140.155:443 | stats.g.doubleclick.net | Google Inc. | US | whitelisted |
2068 | chrome.exe | 172.217.18.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2068 | chrome.exe | 172.217.16.141:443 | accounts.google.com | Google Inc. | US | suspicious |
2068 | chrome.exe | 167.89.123.54:80 | sgtr.eomail6.com | SendGrid, Inc. | US | suspicious |
— | — | 167.89.123.54:80 | sgtr.eomail6.com | SendGrid, Inc. | US | suspicious |
2068 | chrome.exe | 104.17.120.180:443 | www.alert-software.com | Cloudflare Inc | US | shared |
2068 | chrome.exe | 172.217.16.194:443 | www.googleadservices.com | Google Inc. | US | whitelisted |
2068 | chrome.exe | 104.17.244.204:443 | cdn2.hubspot.net | Cloudflare Inc | US | shared |
2068 | chrome.exe | 142.250.74.206:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
sgtr.eomail6.com |
| suspicious |
www.alert-software.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
cdn2.hubspot.net |
| whitelisted |
www.googleadservices.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
snap.licdn.com |
| whitelisted |
cdn.jsdelivr.net |
| whitelisted |
Threats
Process | Message |
|---|---|
chrome.exe | Too long restart command line passed |
chrome.exe | |
chrome.exe | Too long restart command line passed |