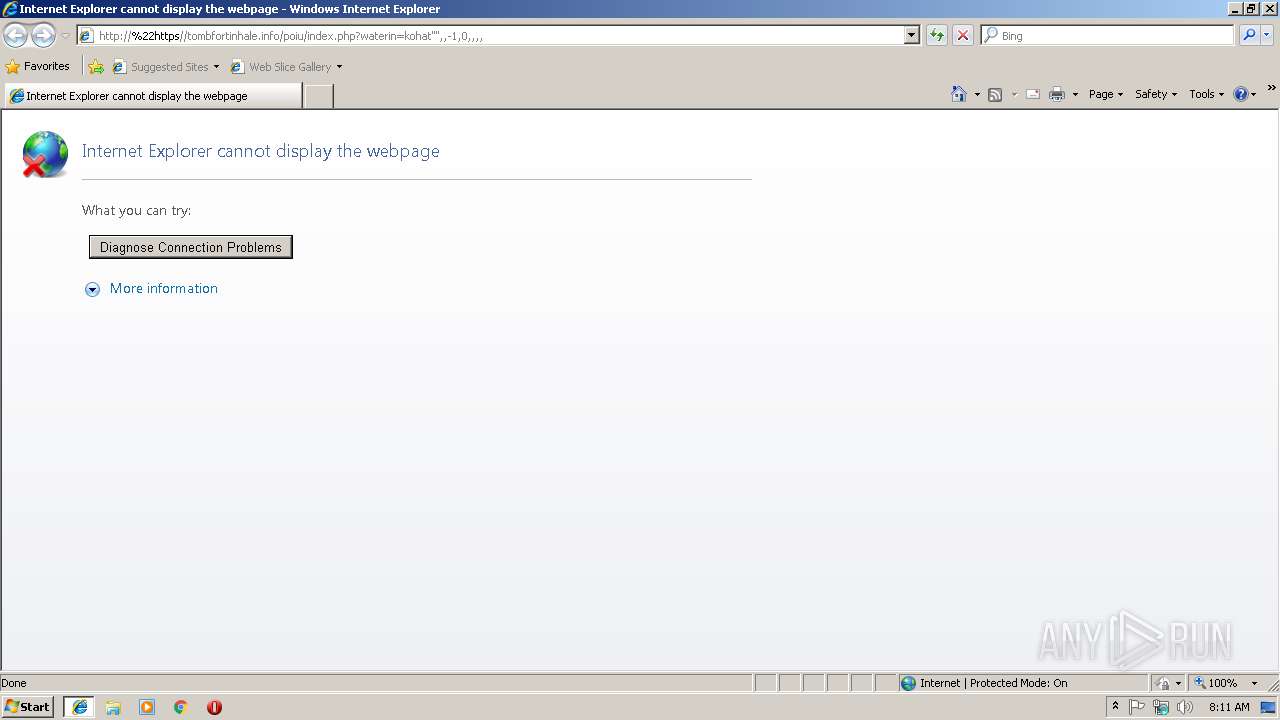
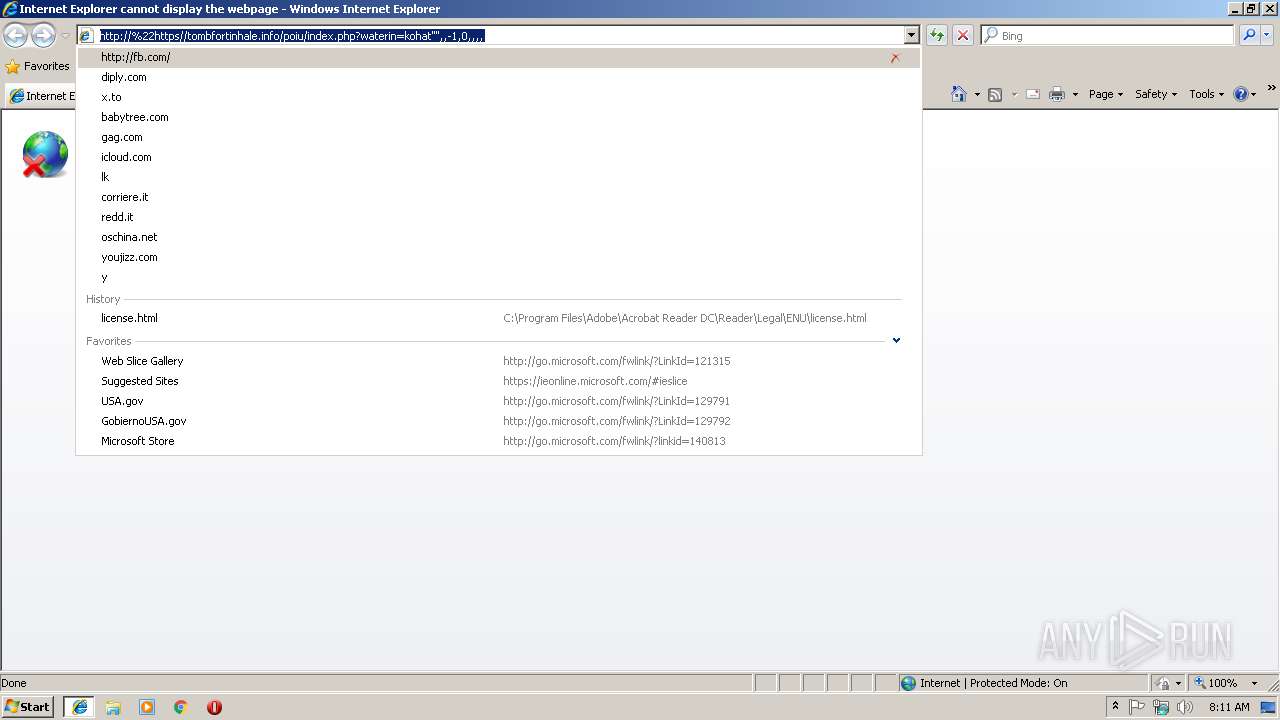
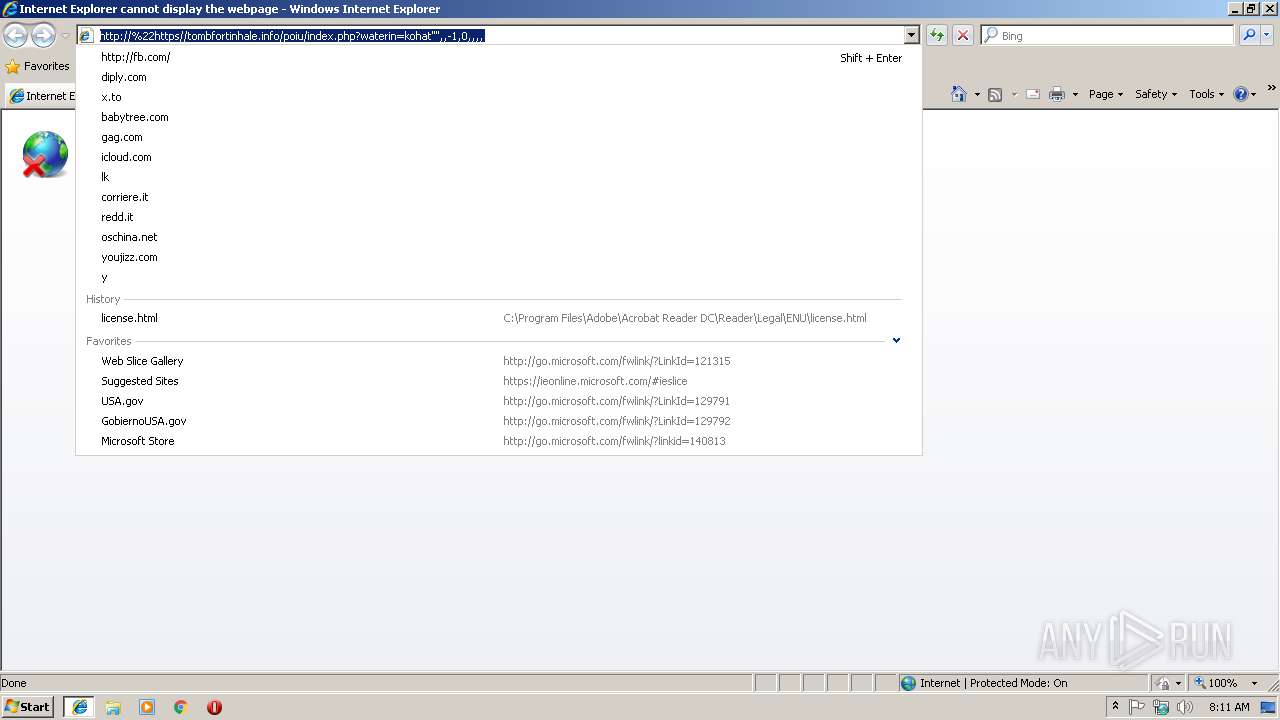
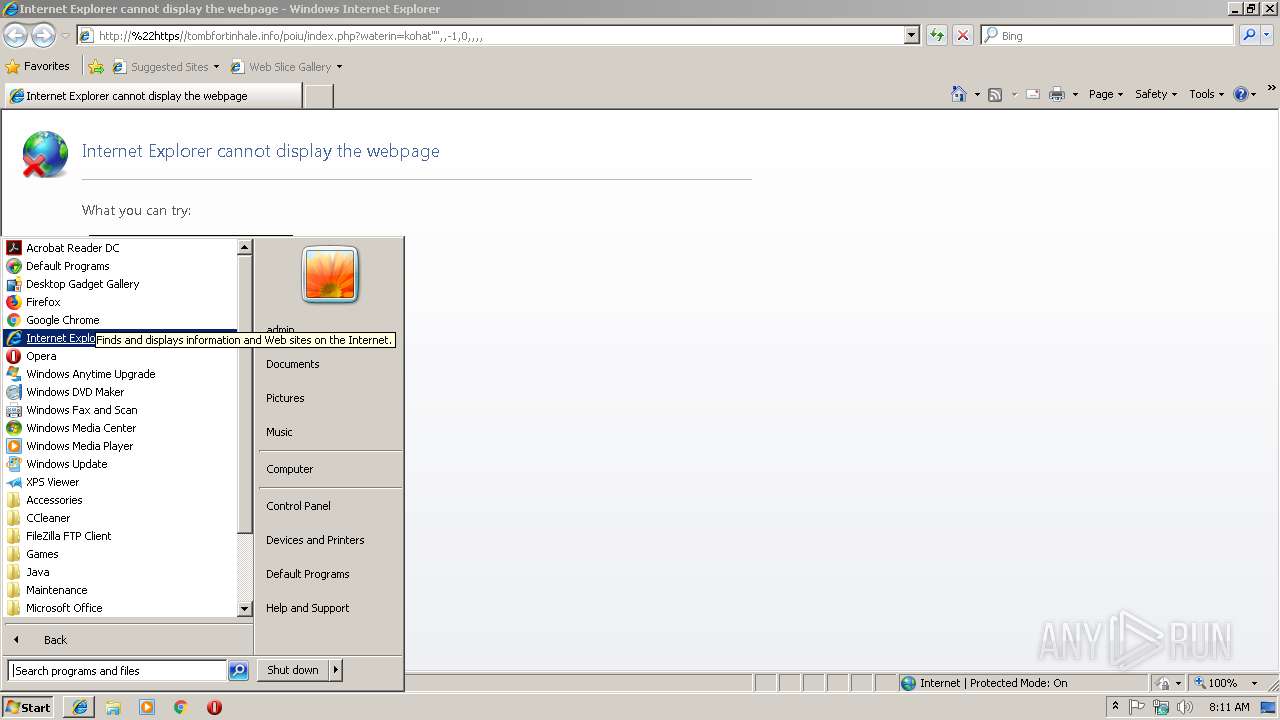
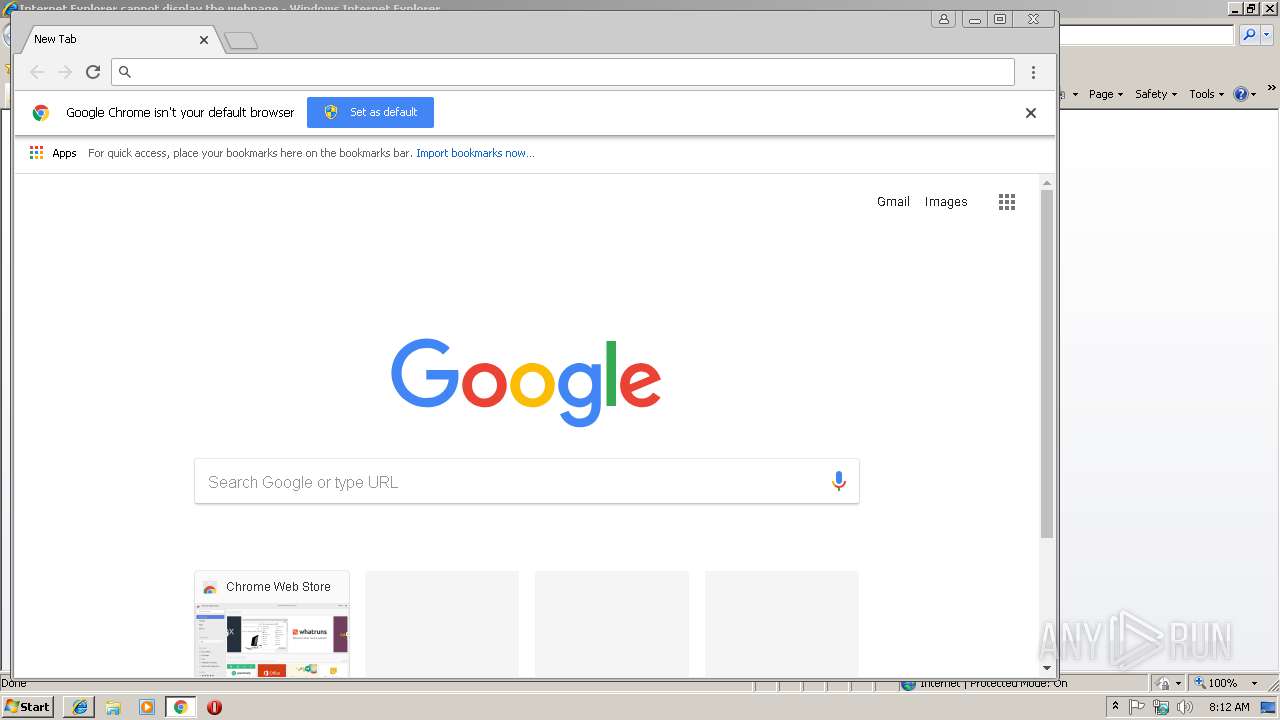
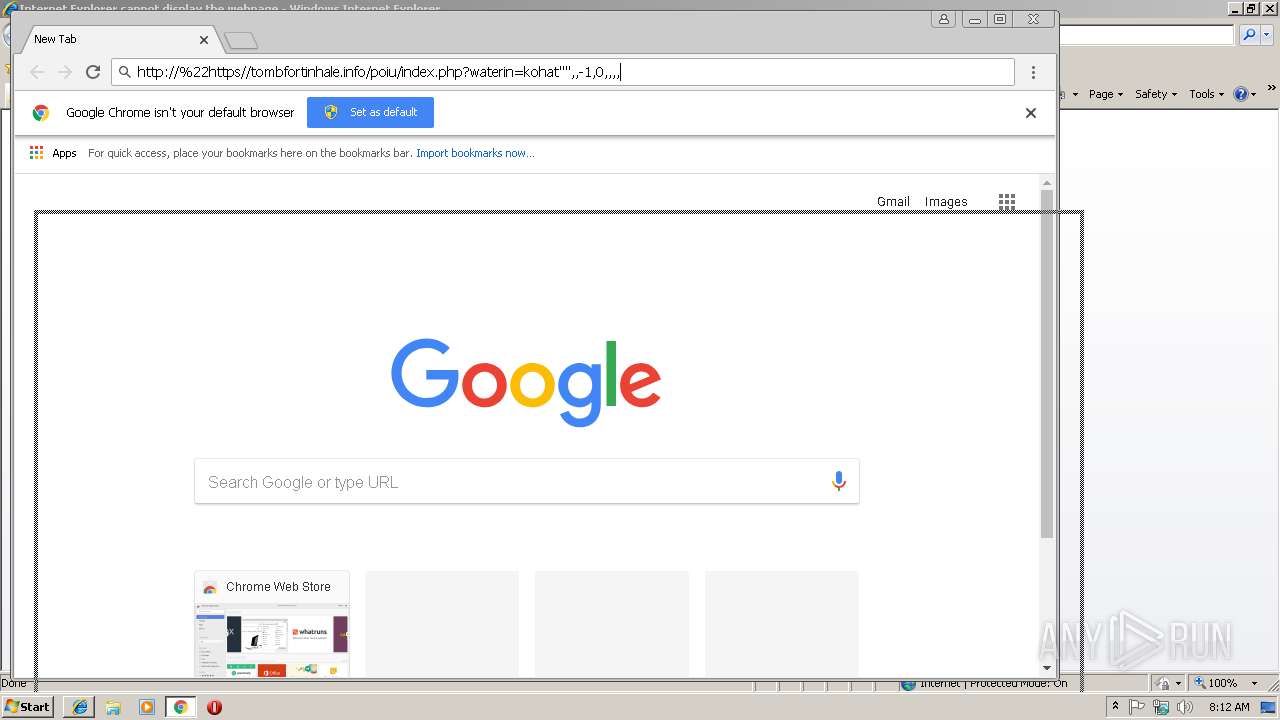
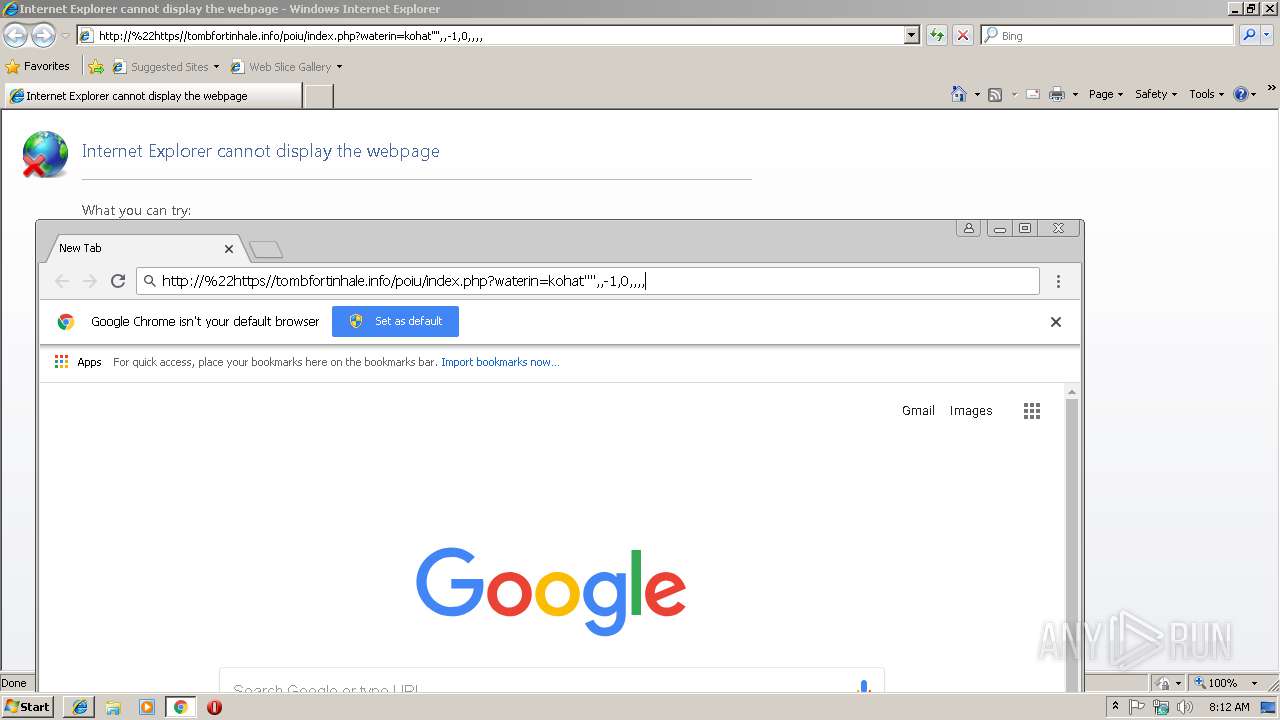
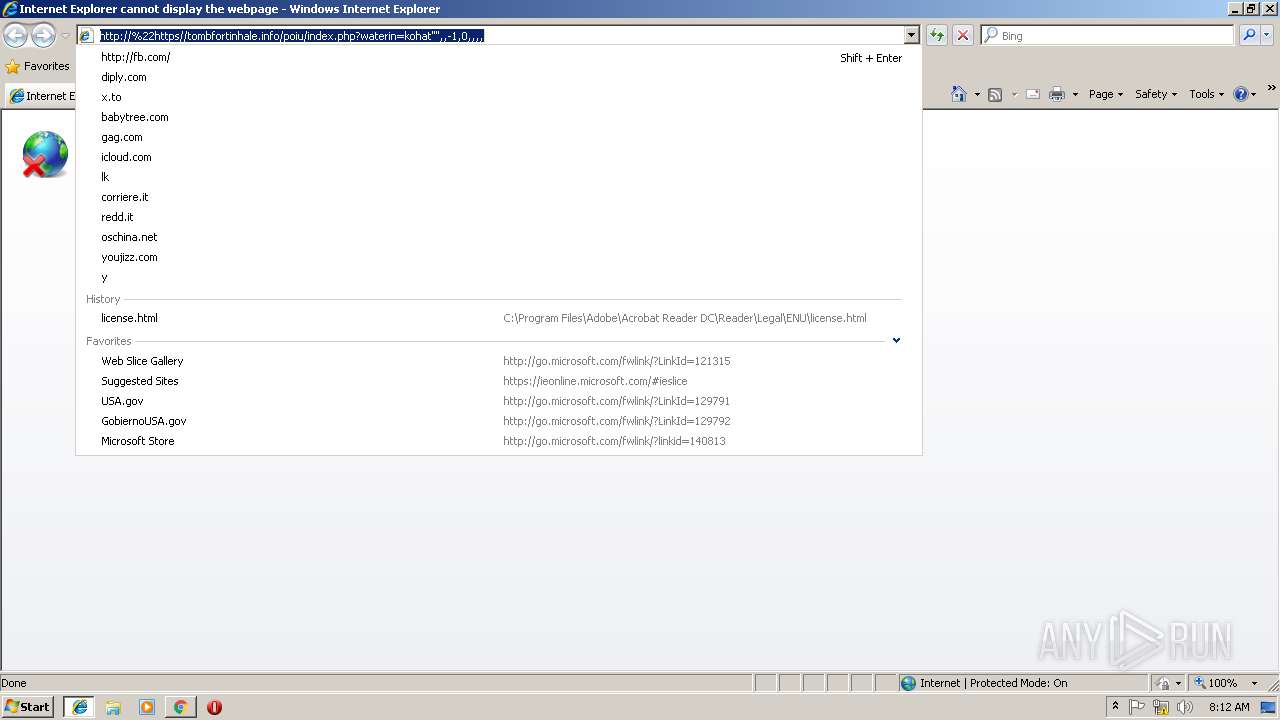
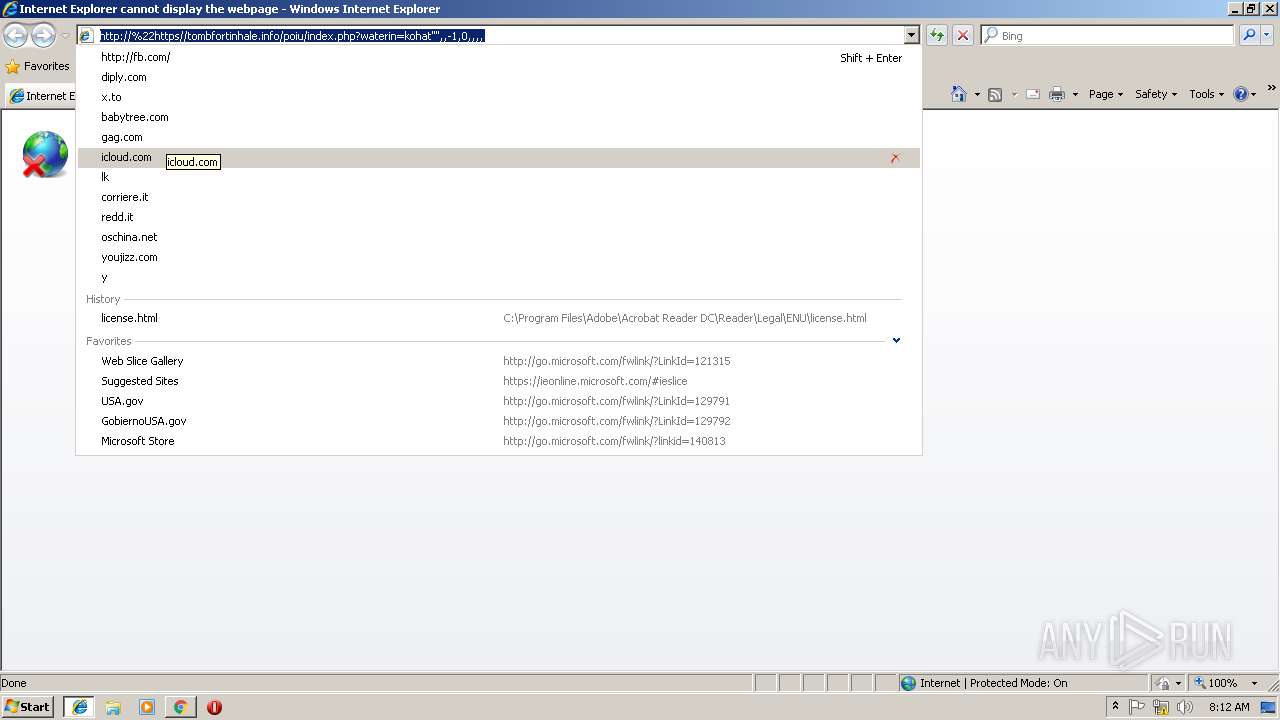
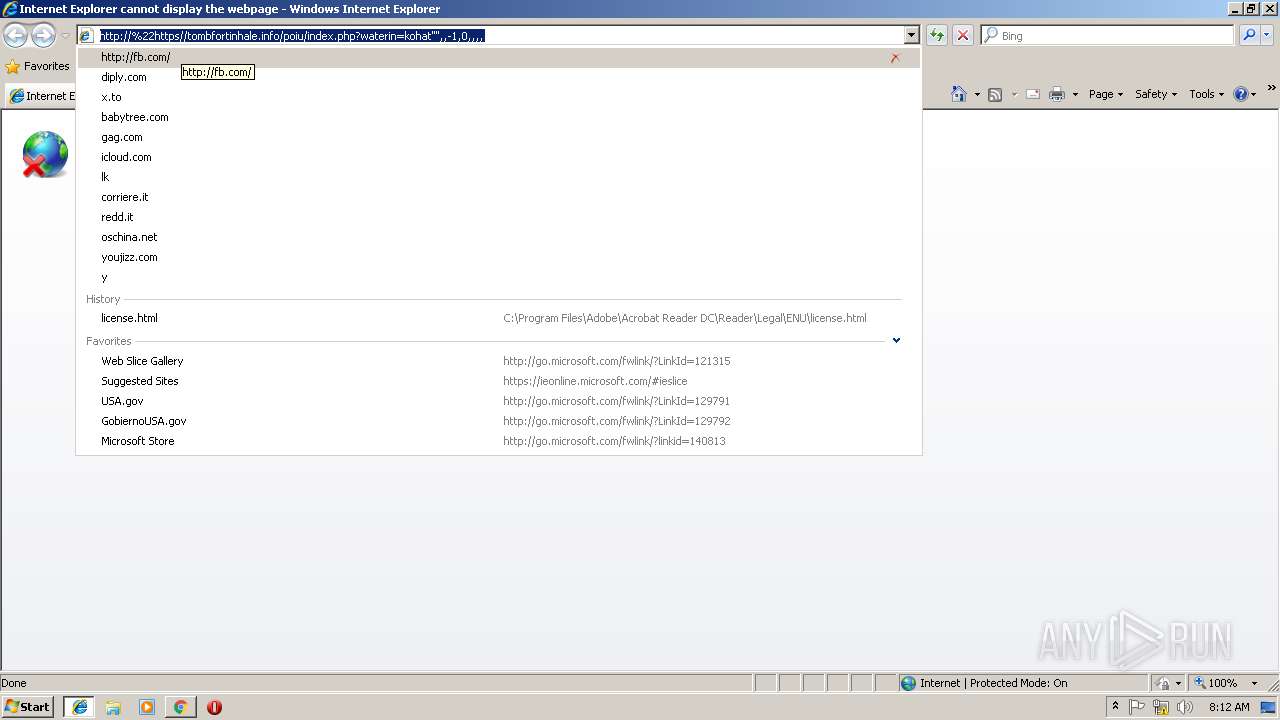
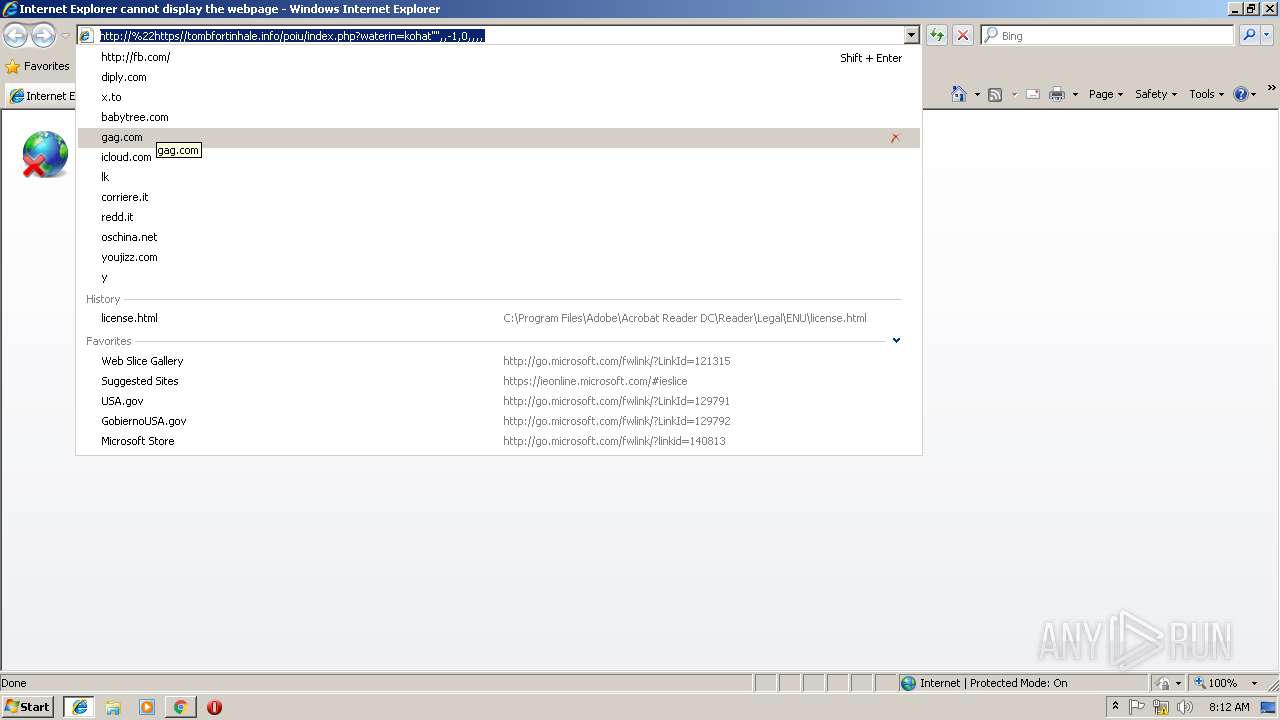
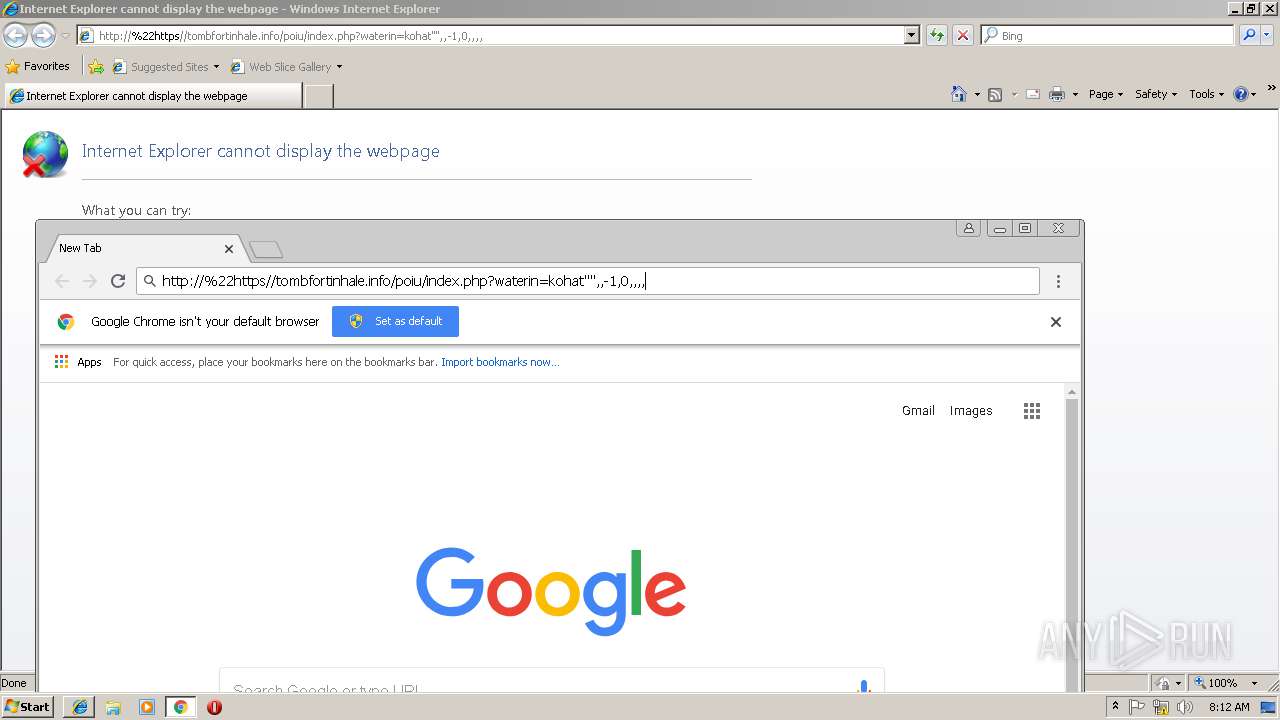
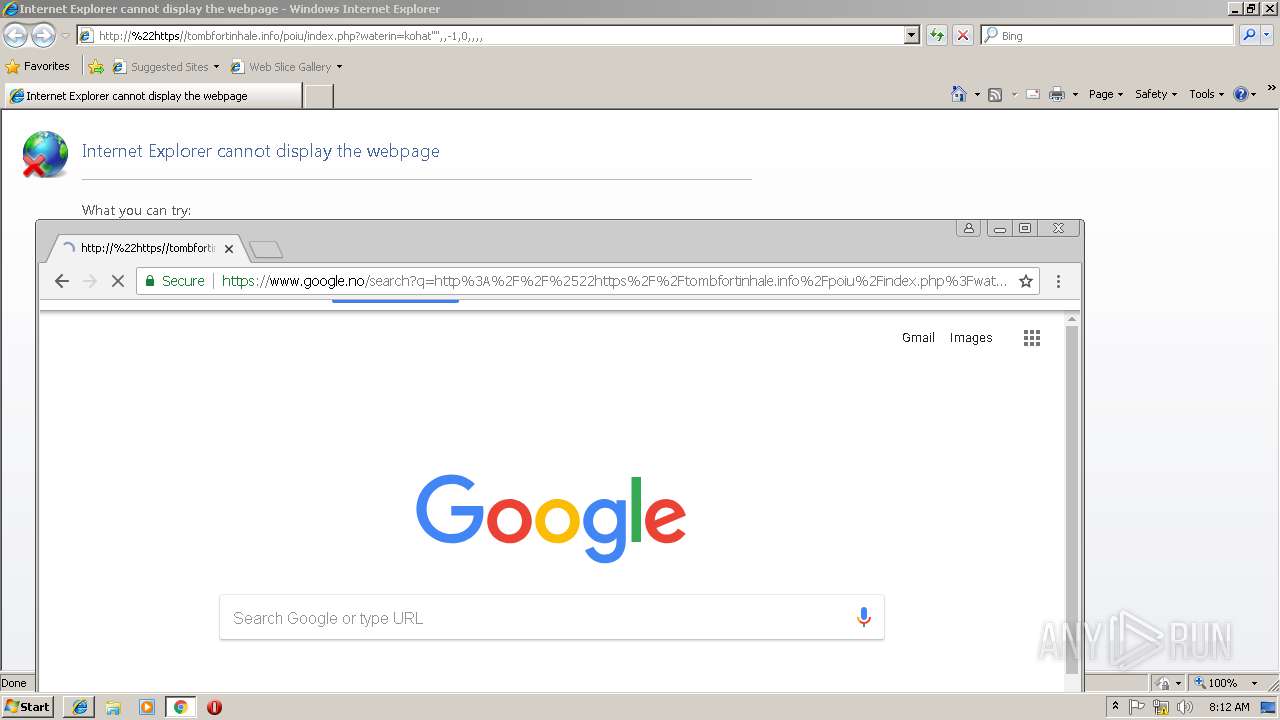
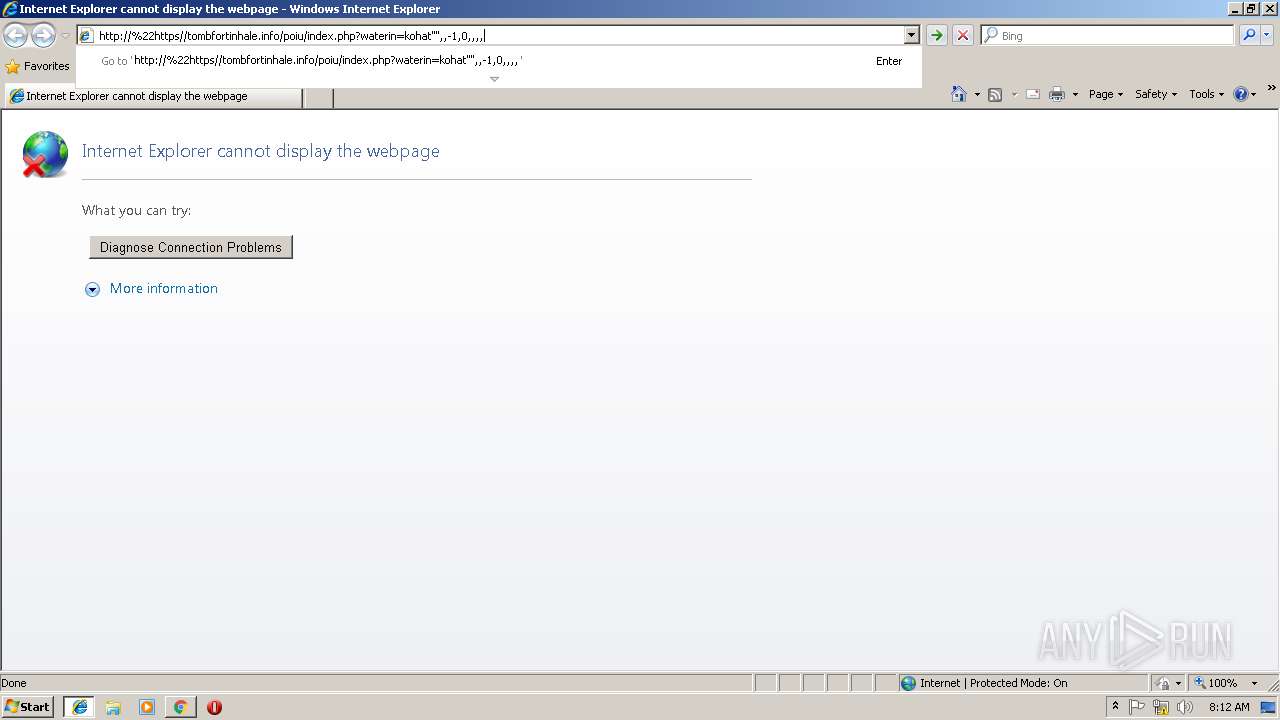
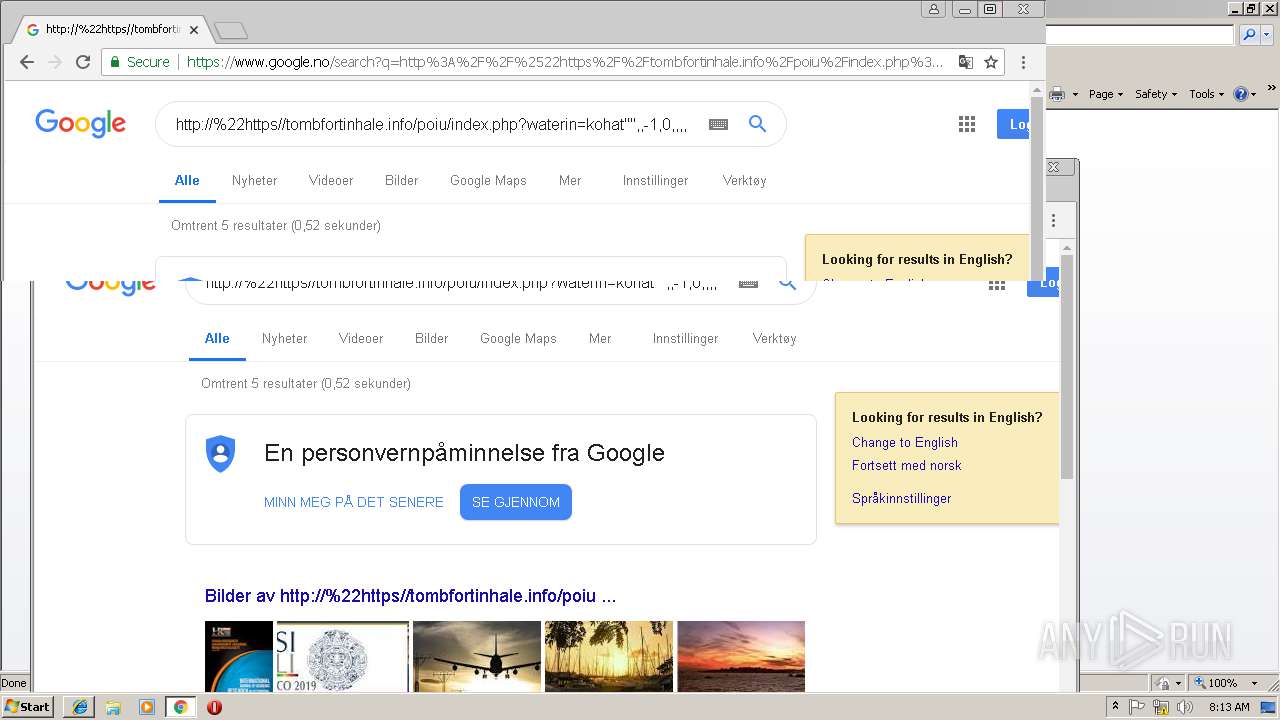
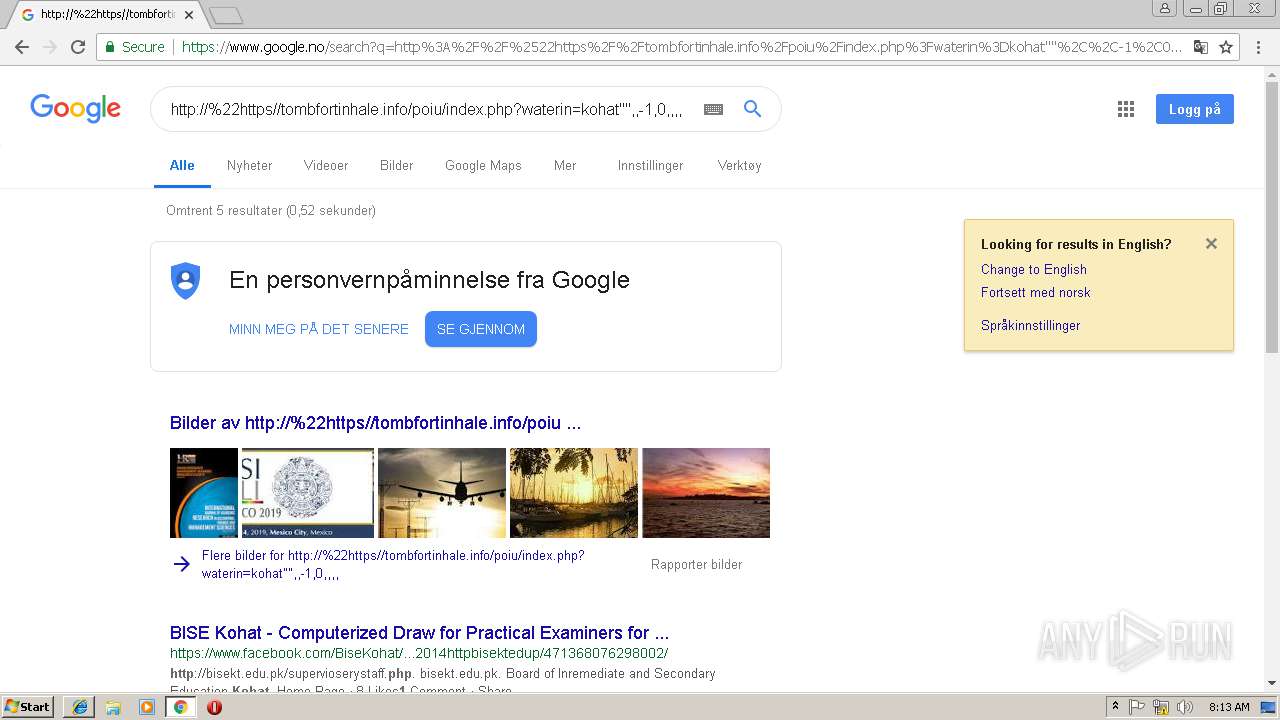
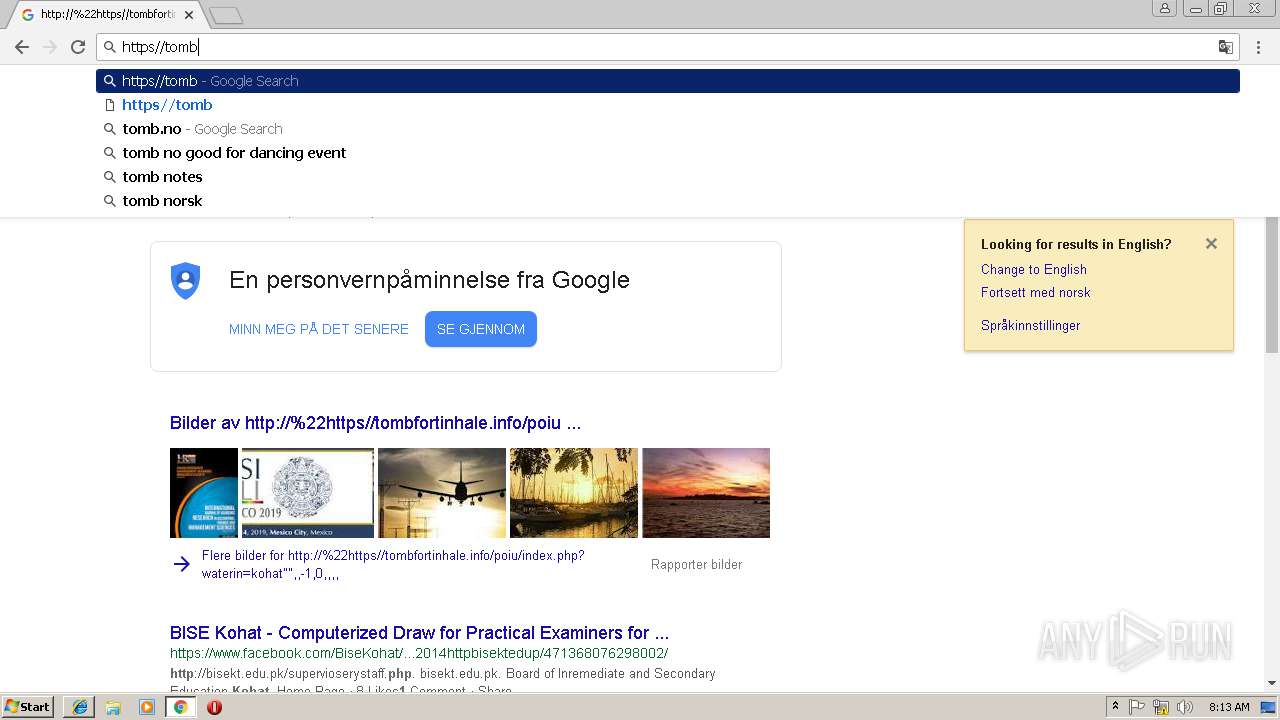
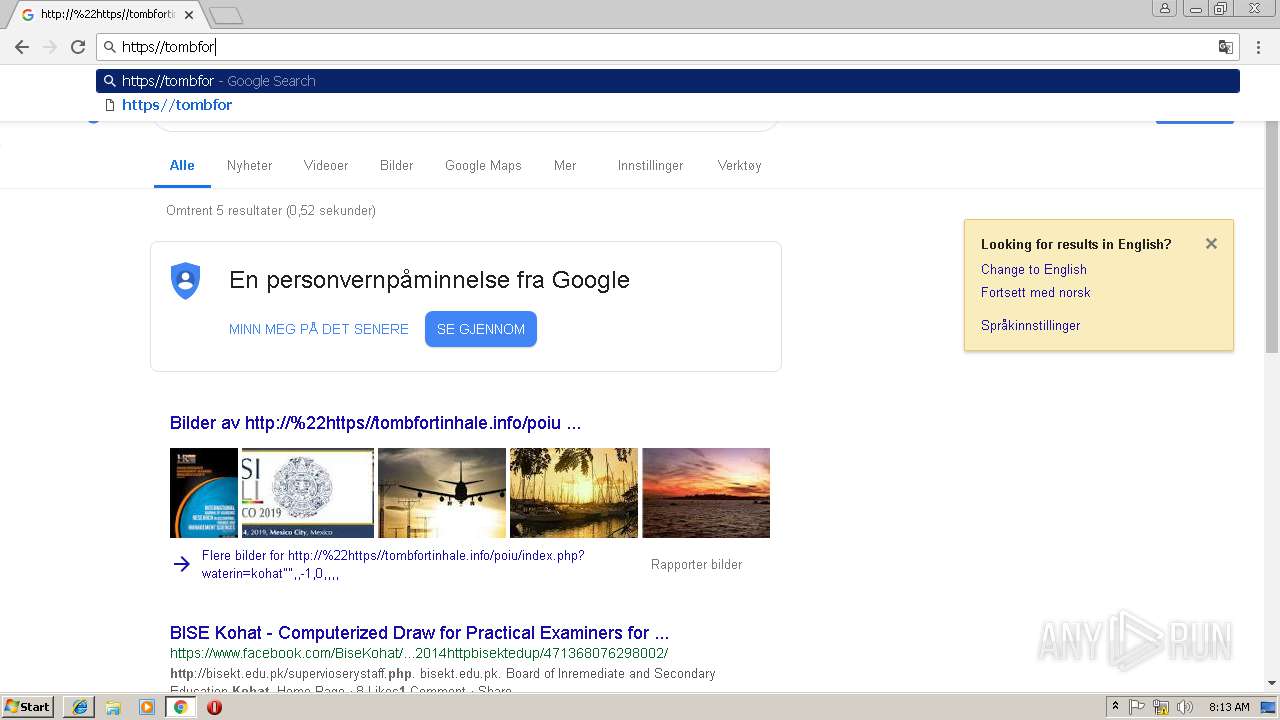
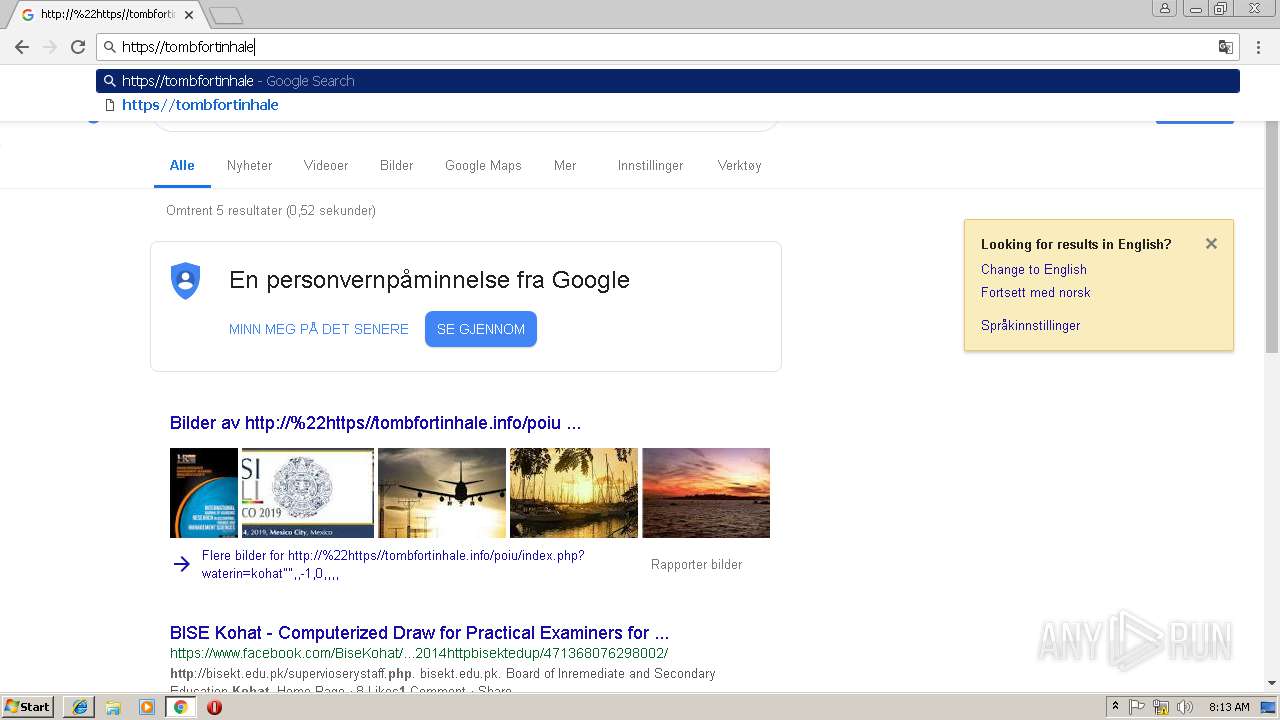
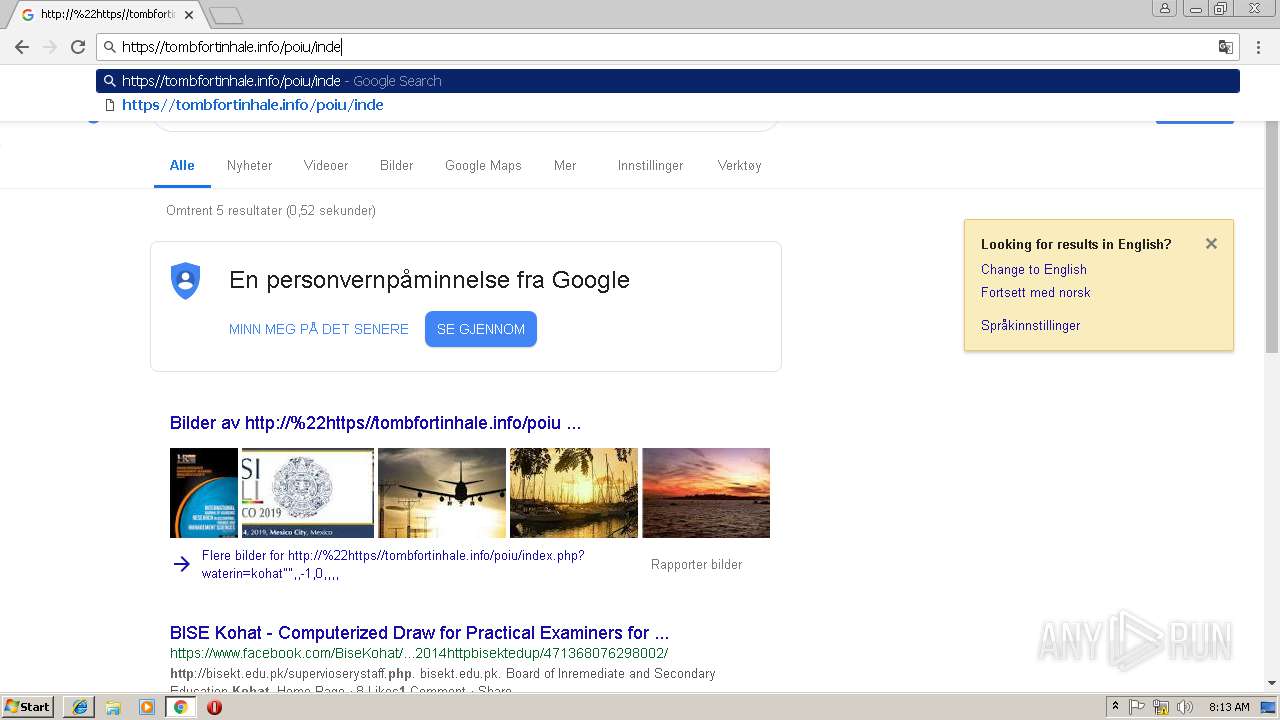
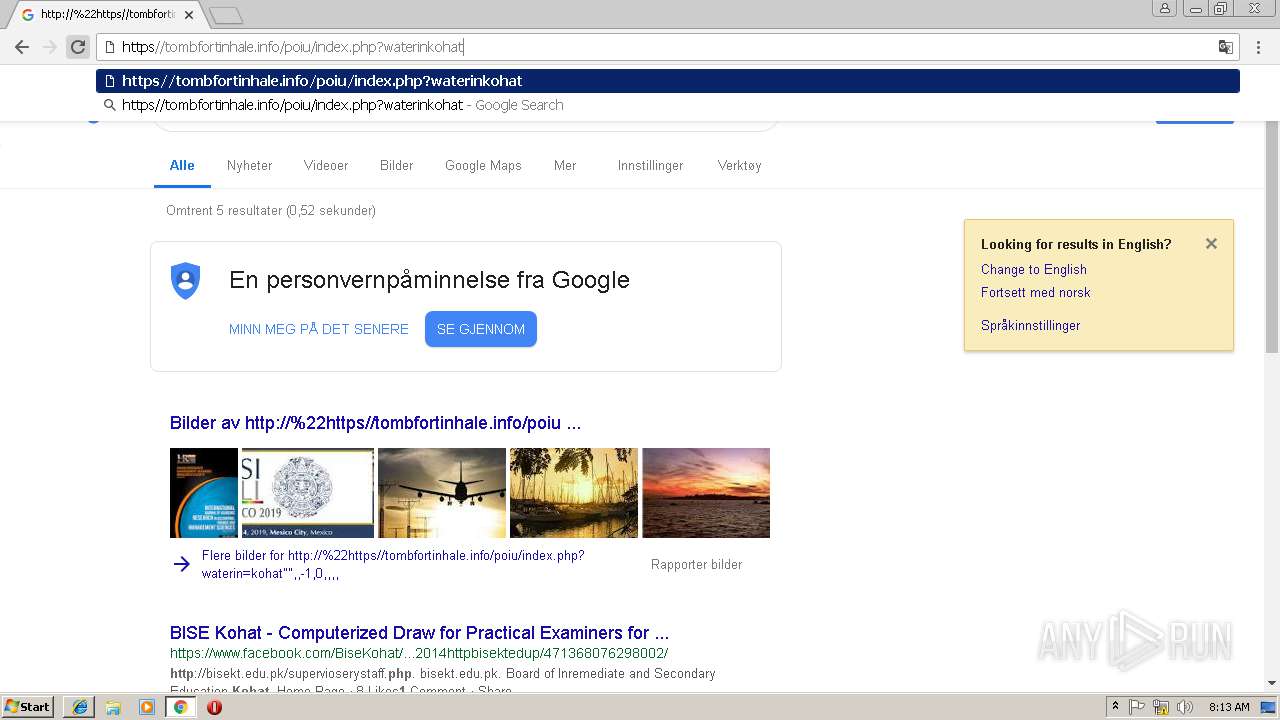
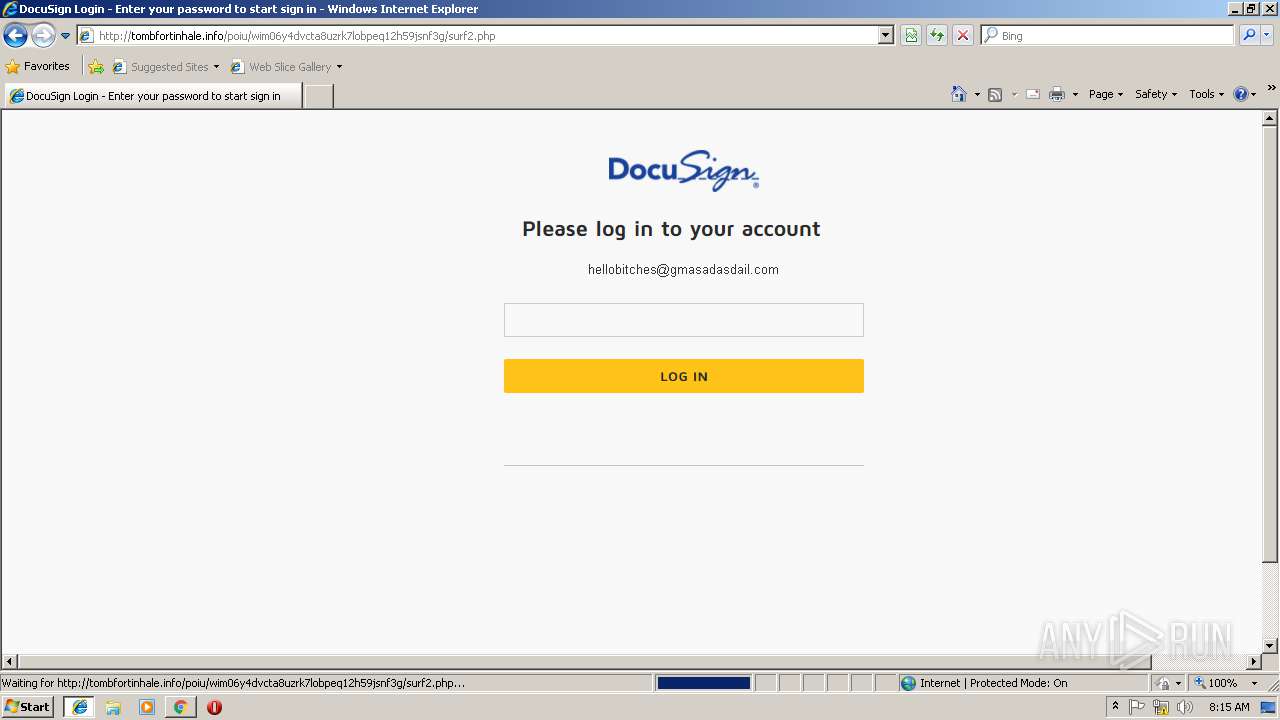
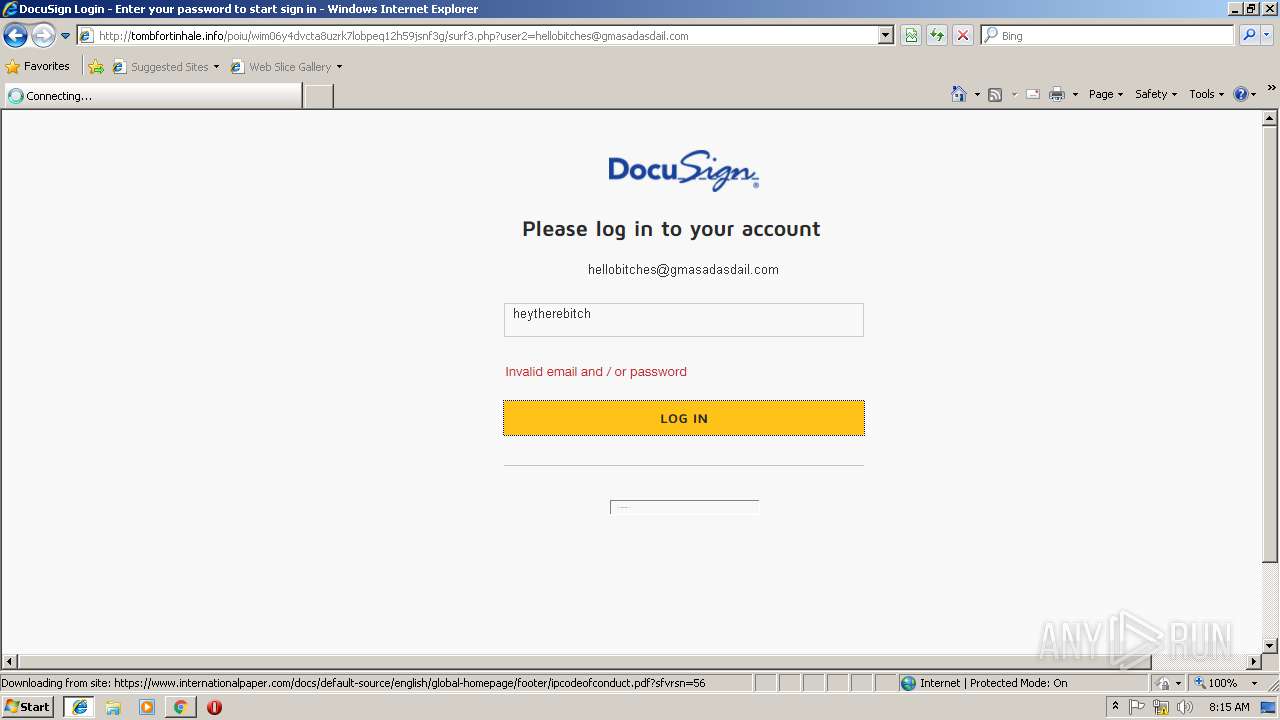
| URL: | https://tombfortinhale.info/poiu/index.php?waterin=kohat" |
| Full analysis: | https://app.any.run/tasks/9b463e0a-e2b2-4098-8d7b-a85d745d261b |
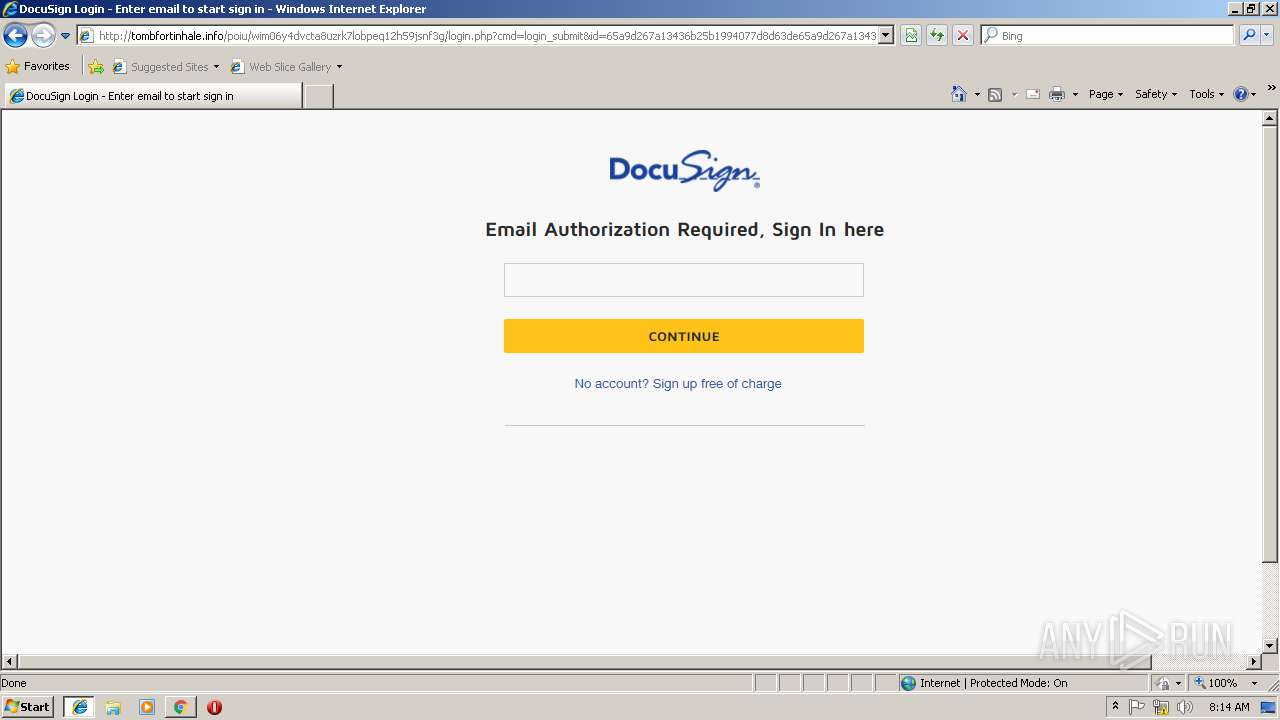
| Verdict: | Malicious activity |
| Analysis date: | January 11, 2019, 08:11:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | F63C6CE8FF57A4ECA63272EEB0ED1B0F |
| SHA1: | F75A9F27820F4DE6D4C073400507DF8FCD3BD810 |
| SHA256: | 2DF83CDD75D55C8BFFF246DCC9945D51E5B9411C1F7BF72C09EC2EC84E505C40 |
| SSDEEP: | 3:N8CIxWxWKVbHZs/h:2CIxuWqbHe5 |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
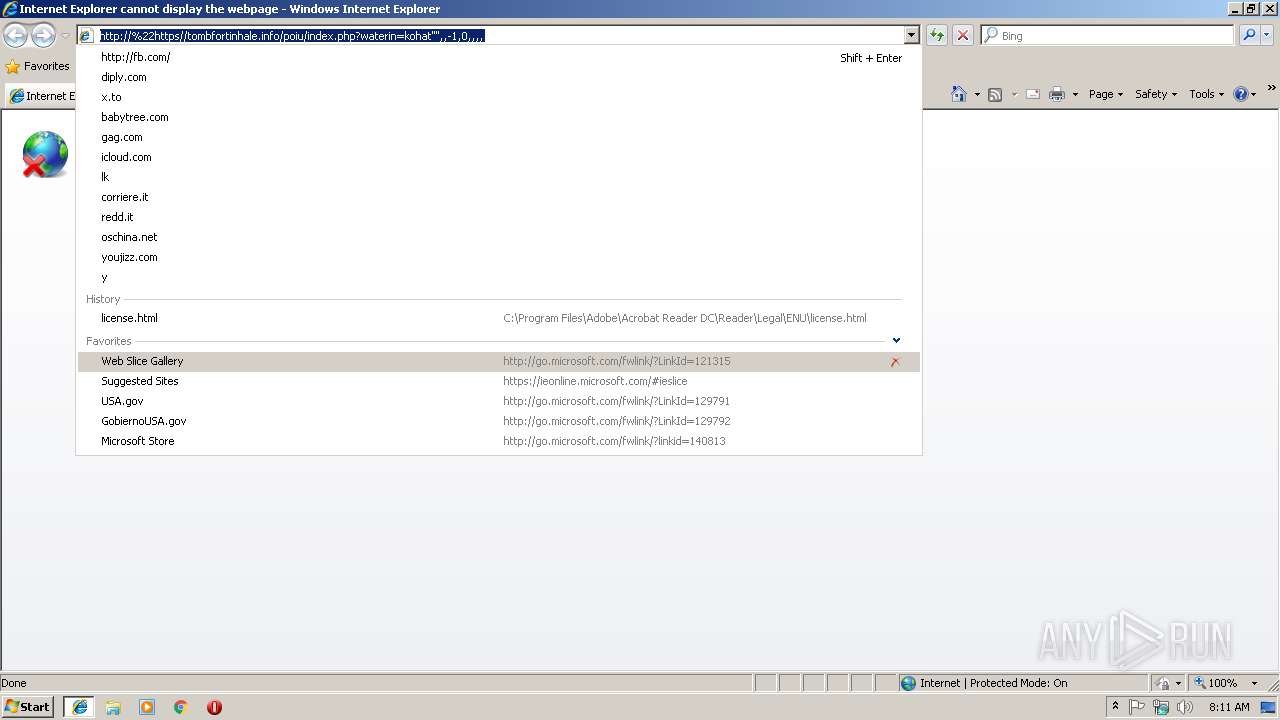
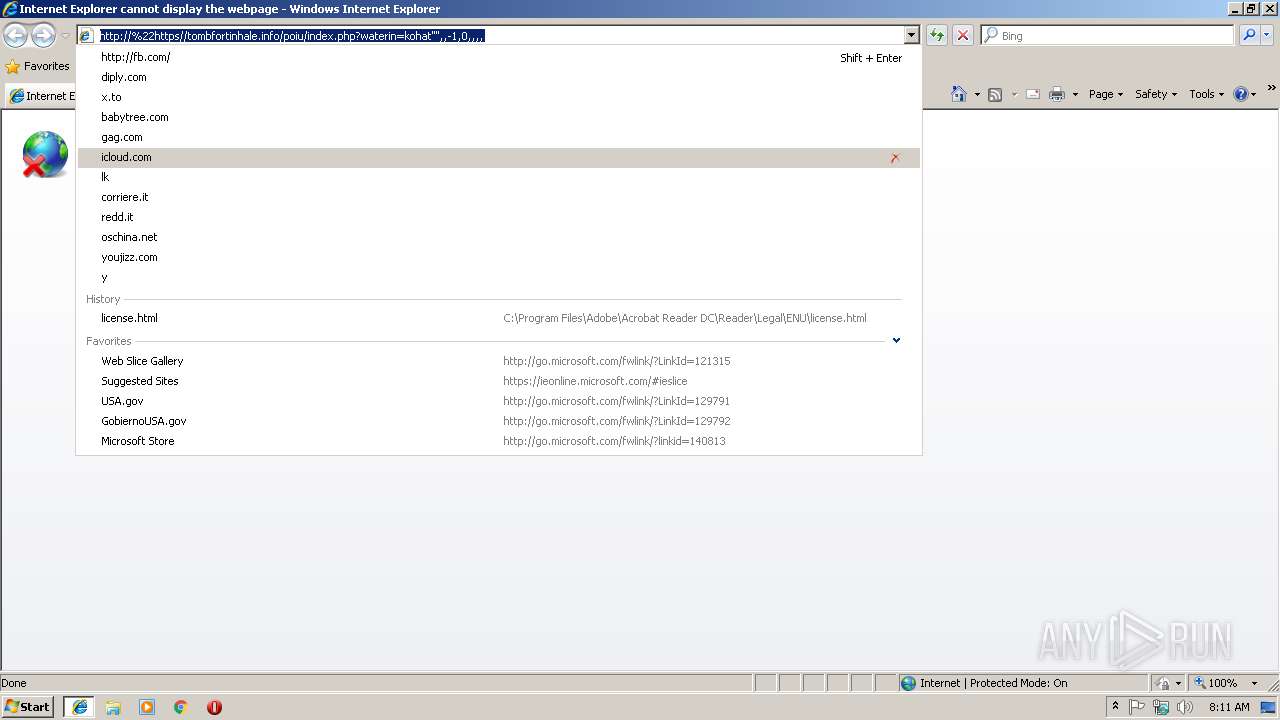
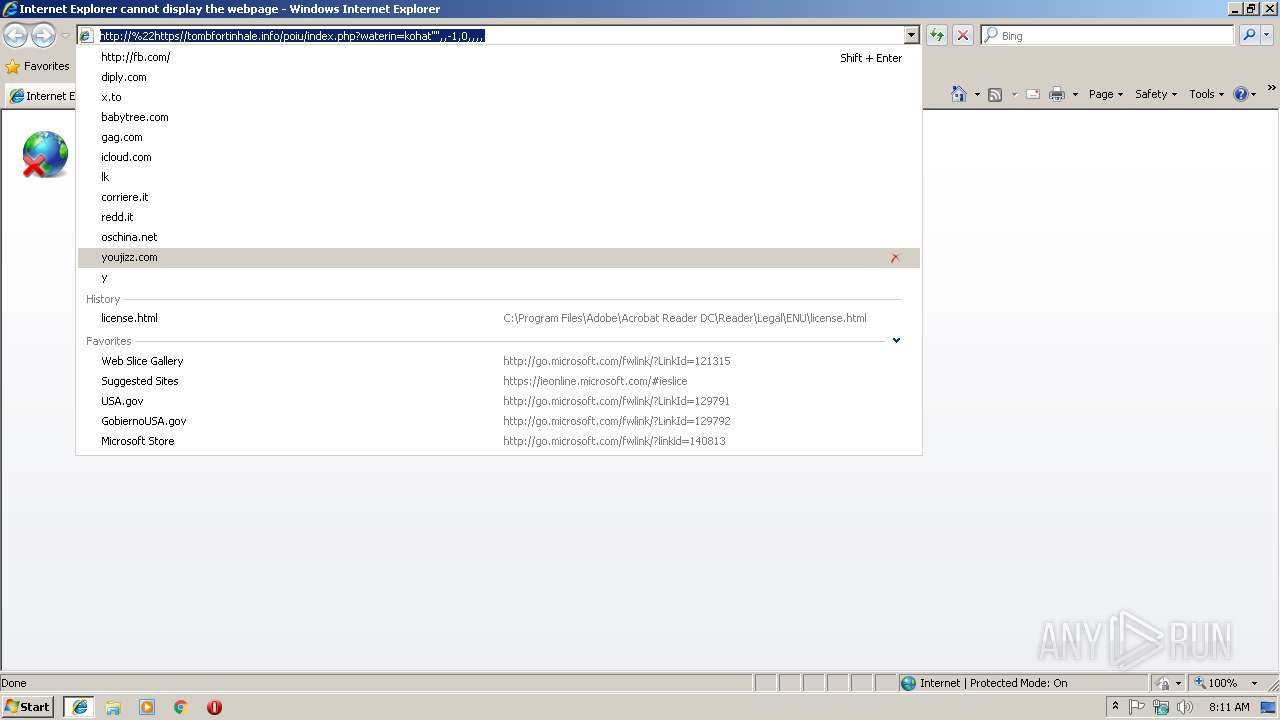
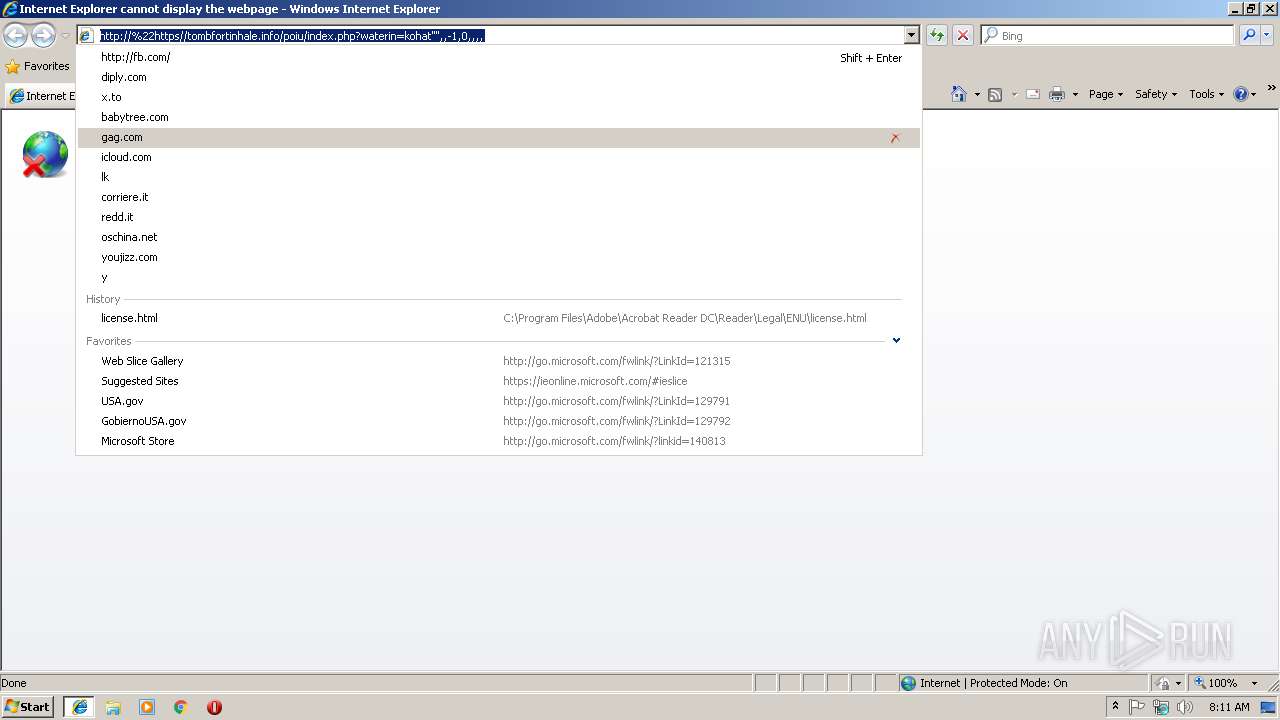
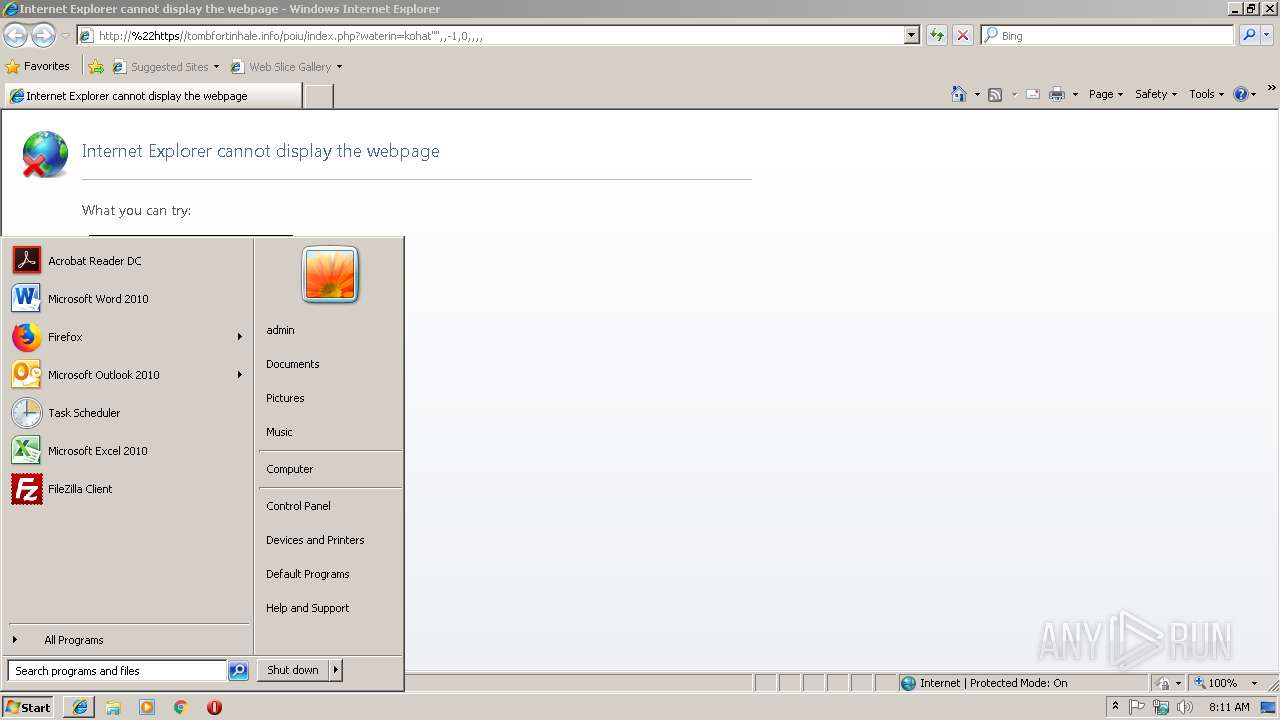
Reads internet explorer settings
- iexplore.exe (PID: 3256)
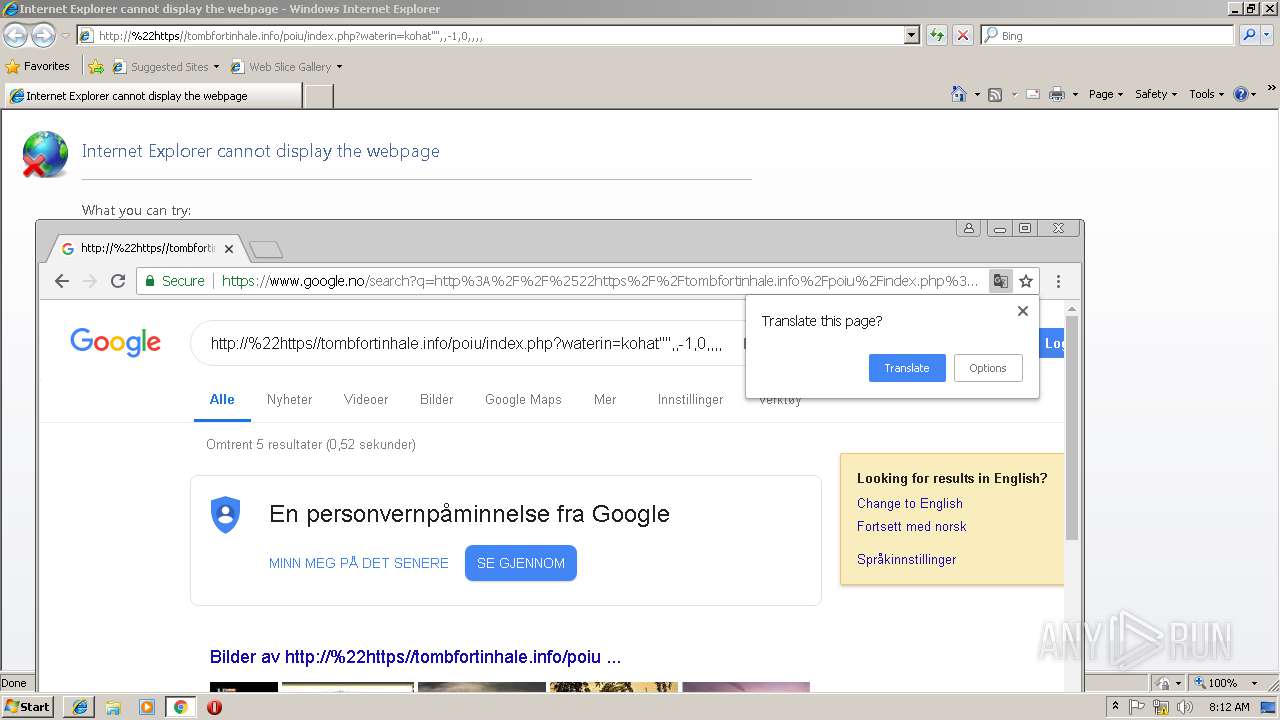
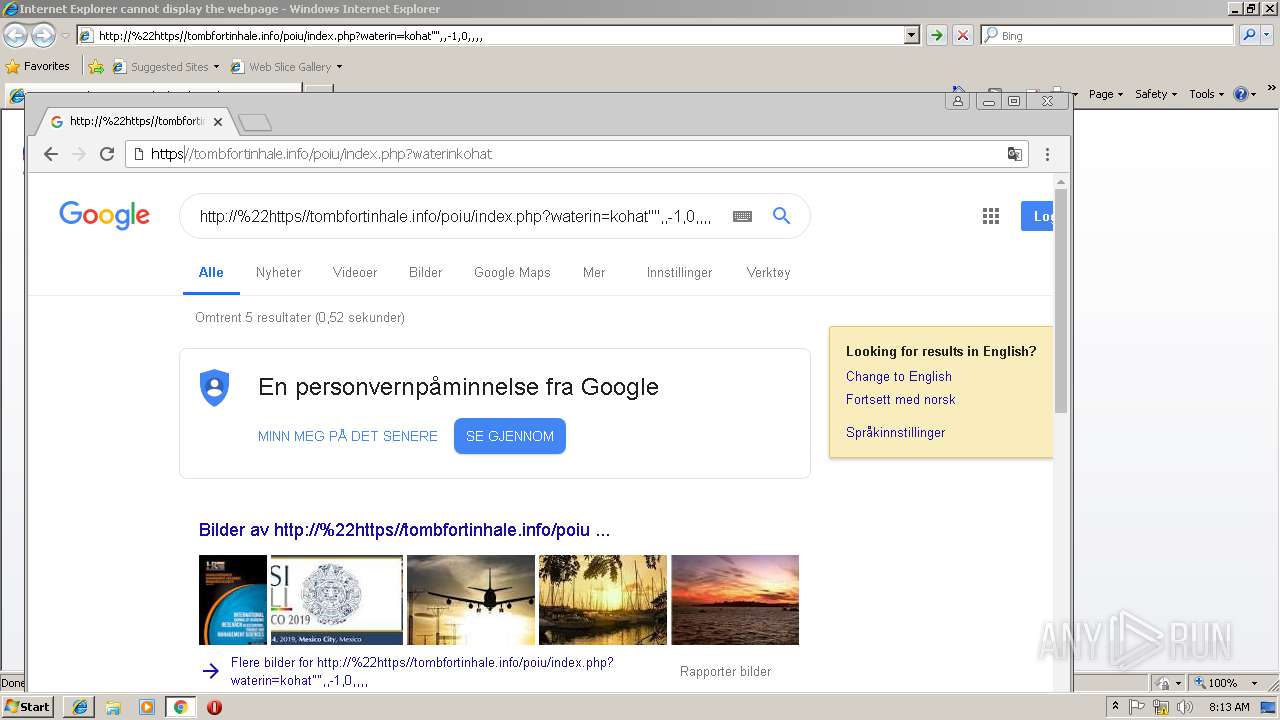
Application launched itself
- iexplore.exe (PID: 2972)
- chrome.exe (PID: 2460)
- RdrCEF.exe (PID: 3904)
Reads settings of System Certificates
- chrome.exe (PID: 2460)
Creates files in the user directory
- iexplore.exe (PID: 3256)
Reads Internet Cache Settings
- iexplore.exe (PID: 3256)
Changes internet zones settings
- iexplore.exe (PID: 2972)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
55
Monitored processes
23
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 416 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" /o /eo /l /b /id 3256 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | iexplore.exe | ||||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Acrobat Reader DC Exit code: 0 Version: 15.23.20070.215641 Modules
| |||||||||||||||
| 560 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=908,5155504341040494669,13447804381796605670,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=EE31B03AEF6BD38855CAA0B583ED0950 --mojo-platform-channel-handle=3704 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1076 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=908,5155504341040494669,13447804381796605670,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=52AD914B57D9F881E7B305B45957BAF0 --mojo-platform-channel-handle=608 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1780 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=908,5155504341040494669,13447804381796605670,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=D9C932A24C41A8907C81D715169A6D0E --mojo-platform-channel-handle=1672 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2408 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=renderer --disable-3d-apis --disable-databases --disable-direct-npapi-requests --disable-file-system --disable-notifications --disable-shared-workers --disable-direct-write --lang=en-US --lang=en-US --log-severity=disable --product-version="ReaderServices/15.23.20053 Chrome/45.0.2454.85" --device-scale-factor=1 --enable-delegated-renderer --num-raster-threads=2 --gpu-rasterization-msaa-sample-count=8 --content-image-texture-target=3553 --video-image-texture-target=3553 --disable-accelerated-video-decode --disable-webrtc-hw-encoding --disable-gpu-compositing --channel="3904.2.674285620\1070213719" --allow-no-sandbox-job /prefetch:673131151 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 0 Version: 15.23.20053.211670 Modules
| |||||||||||||||
| 2460 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2556 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" /o /eo /l /b /id 3256 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | — | iexplore.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe Acrobat Reader DC Exit code: 0 Version: 15.23.20070.215641 Modules
| |||||||||||||||
| 2560 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=renderer --disable-3d-apis --disable-databases --disable-direct-npapi-requests --disable-file-system --disable-notifications --disable-shared-workers --disable-direct-write --lang=en-US --lang=en-US --log-severity=disable --product-version="ReaderServices/15.23.20053 Chrome/45.0.2454.85" --device-scale-factor=1 --enable-delegated-renderer --num-raster-threads=2 --gpu-rasterization-msaa-sample-count=8 --content-image-texture-target=3553 --video-image-texture-target=3553 --disable-accelerated-video-decode --disable-webrtc-hw-encoding --disable-gpu-compositing --channel="3904.0.1418294372\1819642980" --allow-no-sandbox-job /prefetch:673131151 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 0 Version: 15.23.20053.211670 Modules
| |||||||||||||||
| 2576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2464 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2656 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=908,5155504341040494669,13447804381796605670,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1B835D78D7CE9A7A51CA6A99DC916940 --mojo-platform-channel-handle=3740 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
1 298
Read events
1 122
Write events
169
Delete events
7
Modification events
| (PID) Process: | (2972) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2972) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2972) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2972) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2972) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2972) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2972) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {79BDEE23-1578-11E9-AA93-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2972) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2972) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 3 | |||
| (PID) Process: | (2972) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E307010005000B0008000B001400AD03 | |||
Executable files
0
Suspicious files
63
Text files
131
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2972 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2972 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2460 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 2460 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\b23aeb29-3879-43bd-9262-8eaffafe7027.tmp | — | |
MD5:— | SHA256:— | |||
| 2460 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2460 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2460 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2460 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2972 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[3].png | image | |
MD5:9FB559A691078558E77D6848202F6541 | SHA256:6D8A01DC7647BC218D003B58FE04049E24A9359900B7E0CEBAE76EDF85B8B914 | |||
| 3256 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\PP6KS563\down[1] | image | |
MD5:555E83CE7F5D280D7454AF334571FB25 | SHA256:70F316A5492848BB8242D49539468830B353DDAA850964DB4E60A6D2D7DB4880 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
29
TCP/UDP connections
37
DNS requests
22
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2972 | iexplore.exe | GET | — | 178.159.36.107:80 | http://tombfortinhale.info/poiu/wim06y4dvcta8uzrk7lobpeq12h59jsnf3g/images/favicon.ico | RU | — | — | malicious |
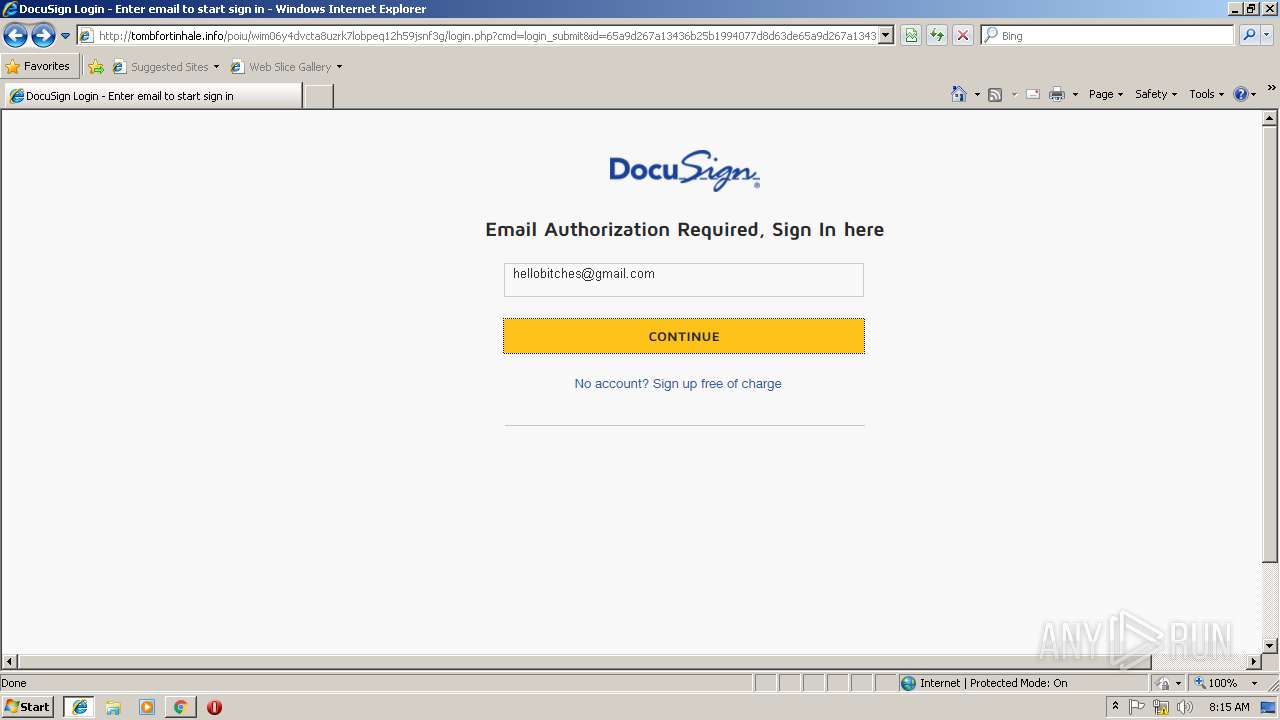
3256 | iexplore.exe | GET | 200 | 178.159.36.107:80 | http://tombfortinhale.info/poiu/wim06y4dvcta8uzrk7lobpeq12h59jsnf3g/login.php?cmd=login_submit&id=65a9d267a13436b25b1994077d8d63de65a9d267a13436b25b1994077d8d63de&session=65a9d267a13436b25b1994077d8d63de65a9d267a13436b25b1994077d8d63de | RU | html | 2.09 Kb | malicious |
3256 | iexplore.exe | GET | 302 | 178.159.36.107:80 | http://tombfortinhale.info/poiu/wim06y4dvcta8uzrk7lobpeq12h59jsnf3g/ | RU | html | 276 b | malicious |
3256 | iexplore.exe | GET | 200 | 178.159.36.107:80 | http://tombfortinhale.info/poiu/wim06y4dvcta8uzrk7lobpeq12h59jsnf3g/images/n1.png | RU | image | 14.9 Kb | malicious |
2972 | iexplore.exe | GET | 200 | 178.159.36.107:80 | http://tombfortinhale.info/poiu/wim06y4dvcta8uzrk7lobpeq12h59jsnf3g/images/favicon.ico | RU | image | 21.7 Kb | malicious |
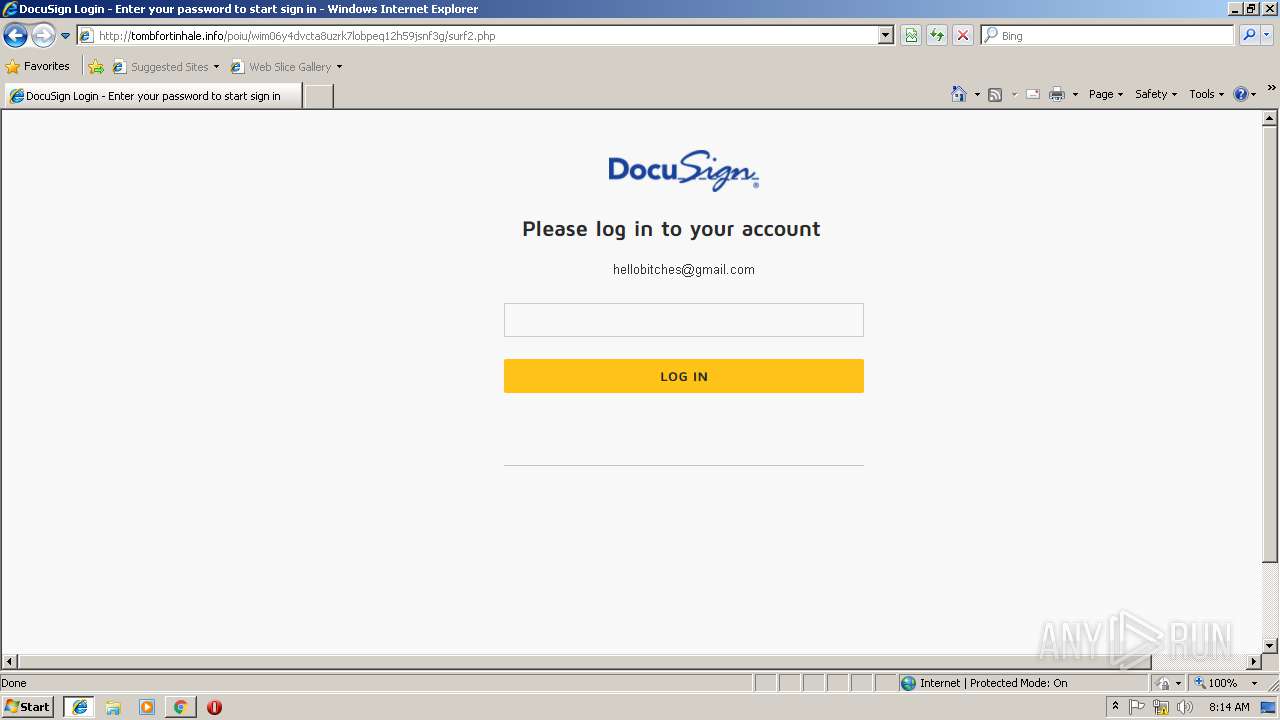
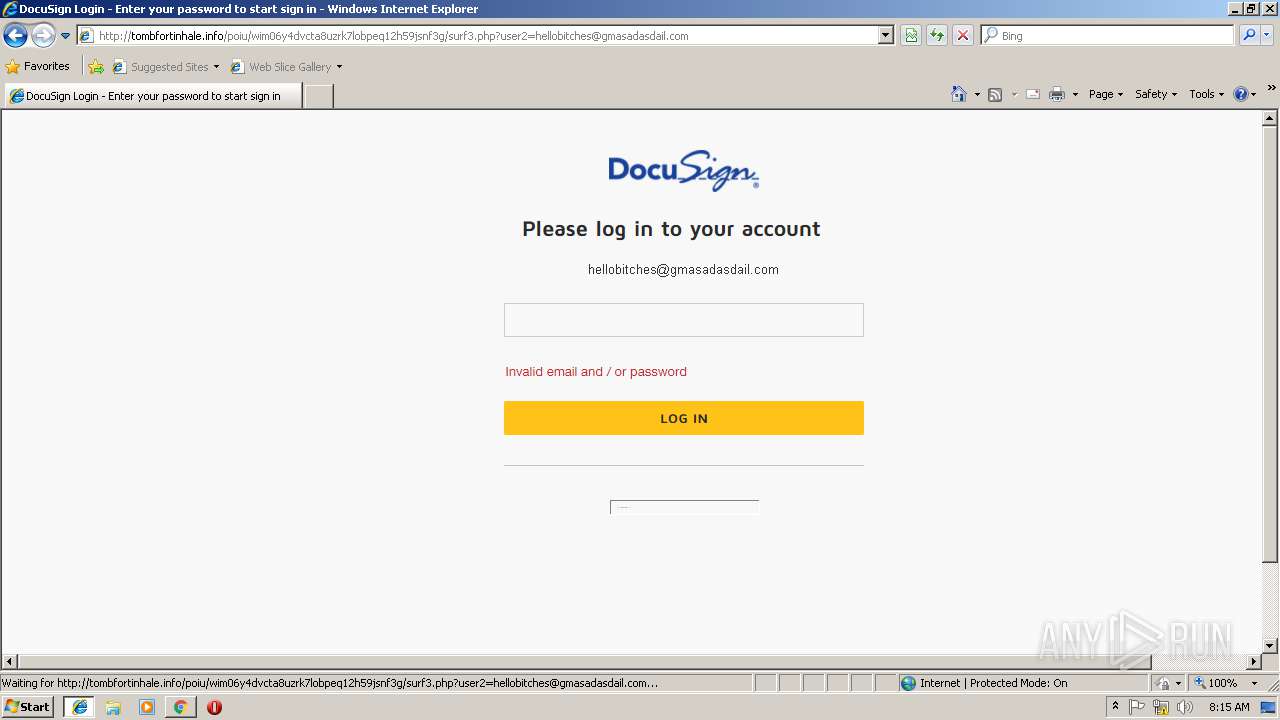
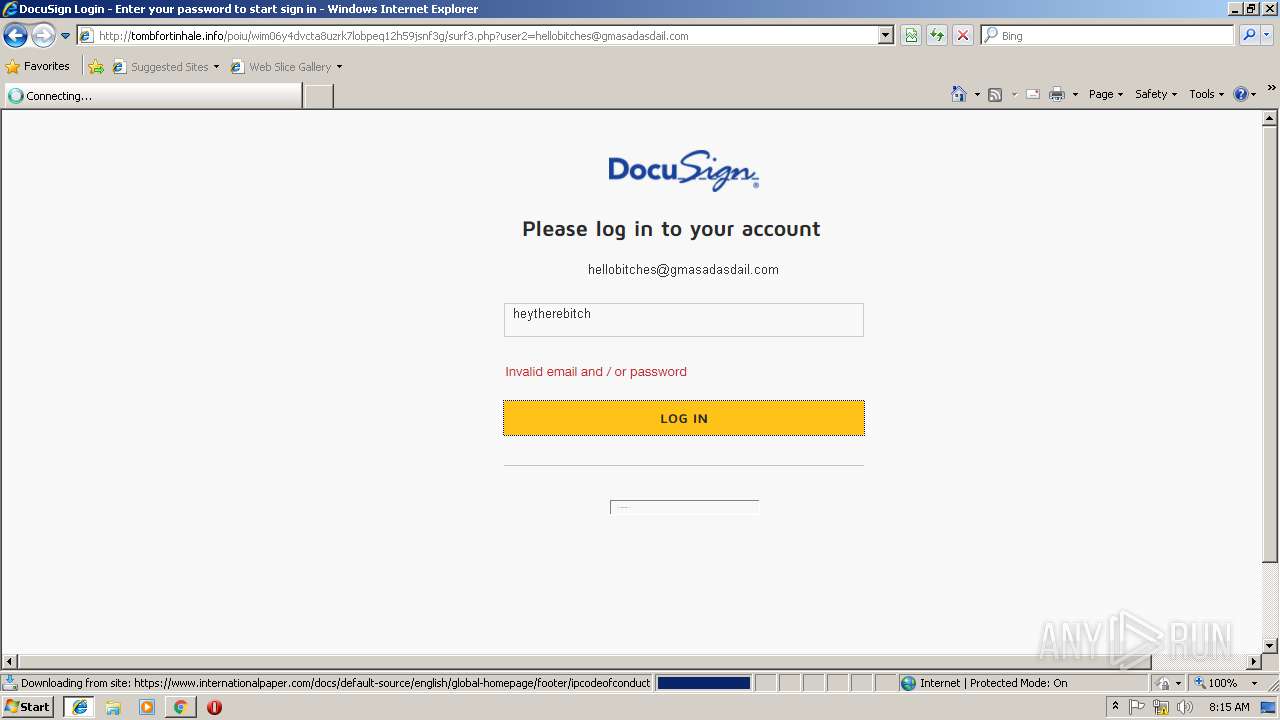
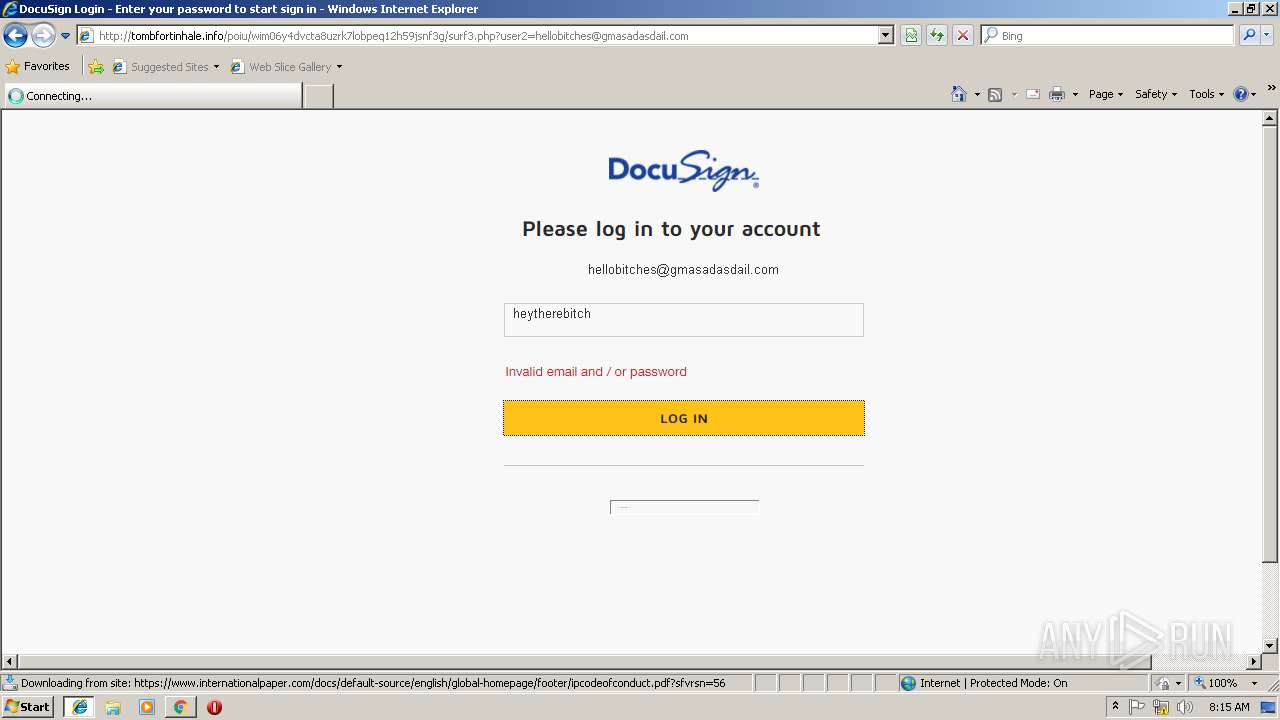
3256 | iexplore.exe | POST | — | 178.159.36.107:80 | http://tombfortinhale.info/poiu/wim06y4dvcta8uzrk7lobpeq12h59jsnf3g/surf2.php | RU | — | — | malicious |
3256 | iexplore.exe | GET | 200 | 178.159.36.107:80 | http://tombfortinhale.info/poiu/wim06y4dvcta8uzrk7lobpeq12h59jsnf3g/images/n5.png | RU | image | 12.9 Kb | malicious |
3256 | iexplore.exe | GET | 200 | 178.159.36.107:80 | http://tombfortinhale.info/poiu/wim06y4dvcta8uzrk7lobpeq12h59jsnf3g/images/cntineu.png | RU | image | 1.13 Kb | malicious |
3256 | iexplore.exe | POST | 302 | 178.159.36.107:80 | http://tombfortinhale.info/poiu/wim06y4dvcta8uzrk7lobpeq12h59jsnf3g/need1.php?name=$id | RU | — | — | malicious |
3256 | iexplore.exe | POST | 200 | 178.159.36.107:80 | http://tombfortinhale.info/poiu/wim06y4dvcta8uzrk7lobpeq12h59jsnf3g/surf2.php | RU | html | 2.80 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
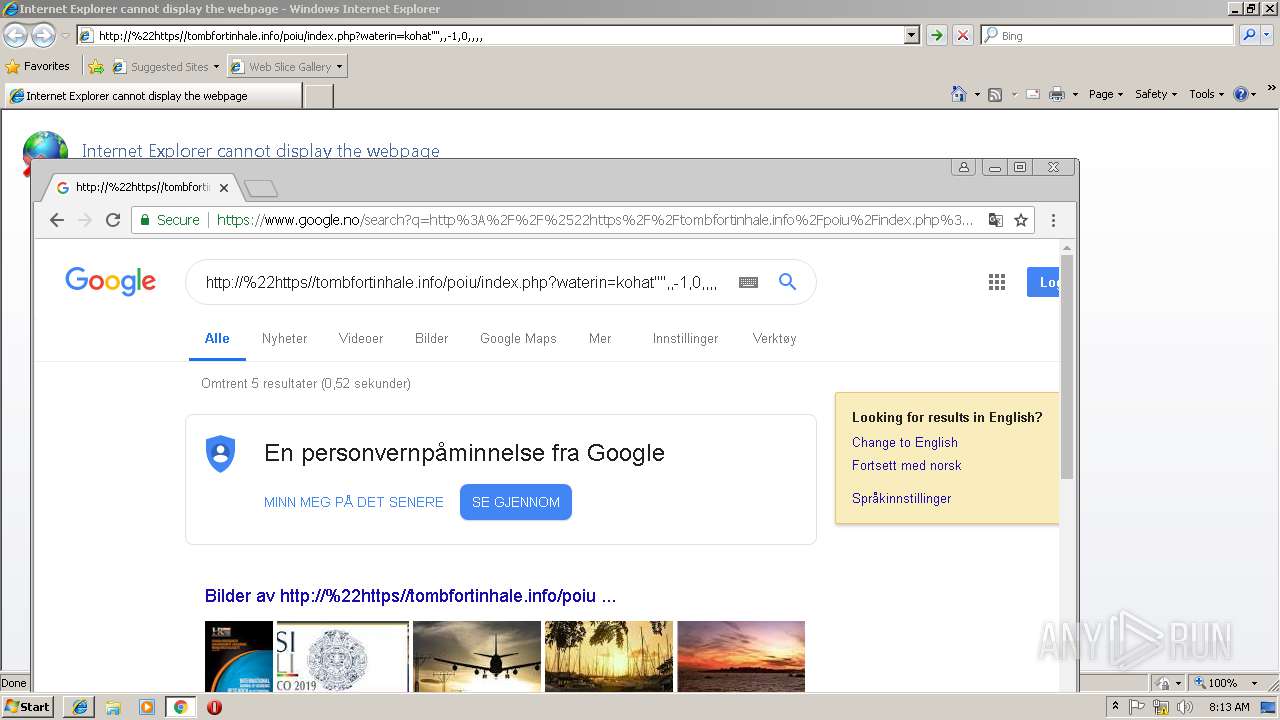
2460 | chrome.exe | 216.58.208.35:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2460 | chrome.exe | 216.58.207.77:443 | accounts.google.com | Google Inc. | US | whitelisted |
2460 | chrome.exe | 216.58.206.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2460 | chrome.exe | 172.217.16.206:443 | apis.google.com | Google Inc. | US | whitelisted |
2460 | chrome.exe | 172.217.16.132:443 | www.google.com | Google Inc. | US | whitelisted |
2460 | chrome.exe | 172.217.18.99:443 | www.google.no | Google Inc. | US | whitelisted |
2460 | chrome.exe | 172.217.22.42:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2460 | chrome.exe | 172.217.21.227:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2460 | chrome.exe | 172.217.18.174:443 | clients4.google.com | Google Inc. | US | whitelisted |
2460 | chrome.exe | 216.58.208.34:443 | adservice.google.no | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
www.google.de |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
www.google.com |
| malicious |
www.google.no |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3256 | iexplore.exe | A Network Trojan was detected | SC PHISHING PDF/Phishing - unknown malware |
3256 | iexplore.exe | A Network Trojan was detected | MALWARE [PTsecurity] Google Drive Phishing Landing |
3256 | iexplore.exe | A Network Trojan was detected | ET INFO Suspicious HTML Decimal Obfuscated Title - Possible Phishing Landing Apr 19 2017 |
3256 | iexplore.exe | A Network Trojan was detected | ET INFO Suspicious HTML Decimal Obfuscated Title - Possible Phishing Landing Apr 19 2017 |
3256 | iexplore.exe | A Network Trojan was detected | ET INFO Suspicious HTML Decimal Obfuscated Title - Possible Phishing Landing Apr 19 2017 |
3256 | iexplore.exe | A Network Trojan was detected | ET INFO Suspicious HTML Decimal Obfuscated Title - Possible Phishing Landing Apr 19 2017 |
5 ETPRO signatures available at the full report