| URL: | https://www.utorrent.com/web/compare/ |
| Full analysis: | https://app.any.run/tasks/2c936066-cabd-4cac-a993-e188776f5eda |
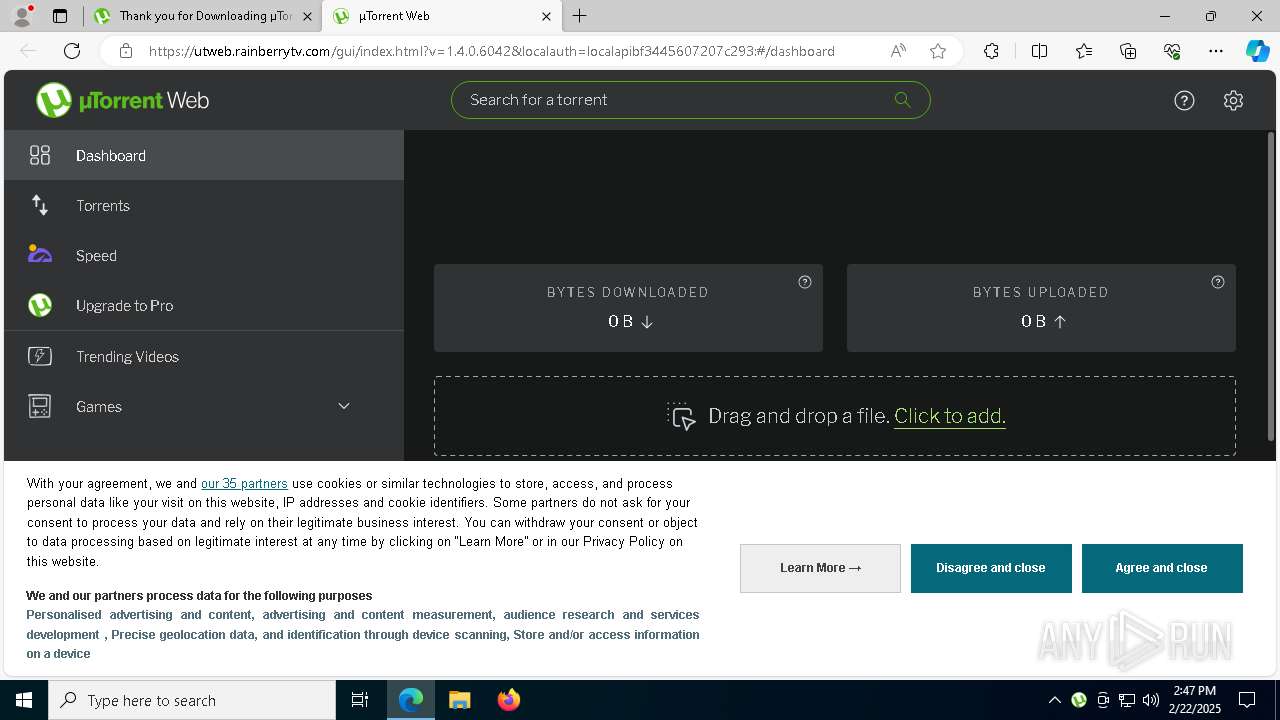
| Verdict: | Malicious activity |
| Threats: | Stealers are a group of malicious software that are intended for gaining unauthorized access to users’ information and transferring it to the attacker. The stealer malware category includes various types of programs that focus on their particular kind of data, including files, passwords, and cryptocurrency. Stealers are capable of spying on their targets by recording their keystrokes and taking screenshots. This type of malware is primarily distributed as part of phishing campaigns. |
| Analysis date: | February 22, 2025, 14:46:38 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 8E5FEBAB64DAA677846C63DE52250A76 |
| SHA1: | 89841174E4A2FBFB7344513751D2C0E1D8220DFA |
| SHA256: | 2DEEF058FF2405DD97D6C314E37090850CECF1C952B90BEC27DF90467E31B38A |
| SSDEEP: | 3:N8DSL6RLKOoF:2OL6RLCF |
MALICIOUS
Changes the autorun value in the registry
- utweb.exe (PID: 5432)
BITTORRENT has been detected (SURICATA)
- utweb.exe (PID: 5432)
Steals credentials from Web Browsers
- avg_secure_browser_setup.exe (PID: 8168)
Actions looks like stealing of personal data
- avg_secure_browser_setup.exe (PID: 8168)
- UnifiedStub-installer.exe (PID: 7920)
SUSPICIOUS
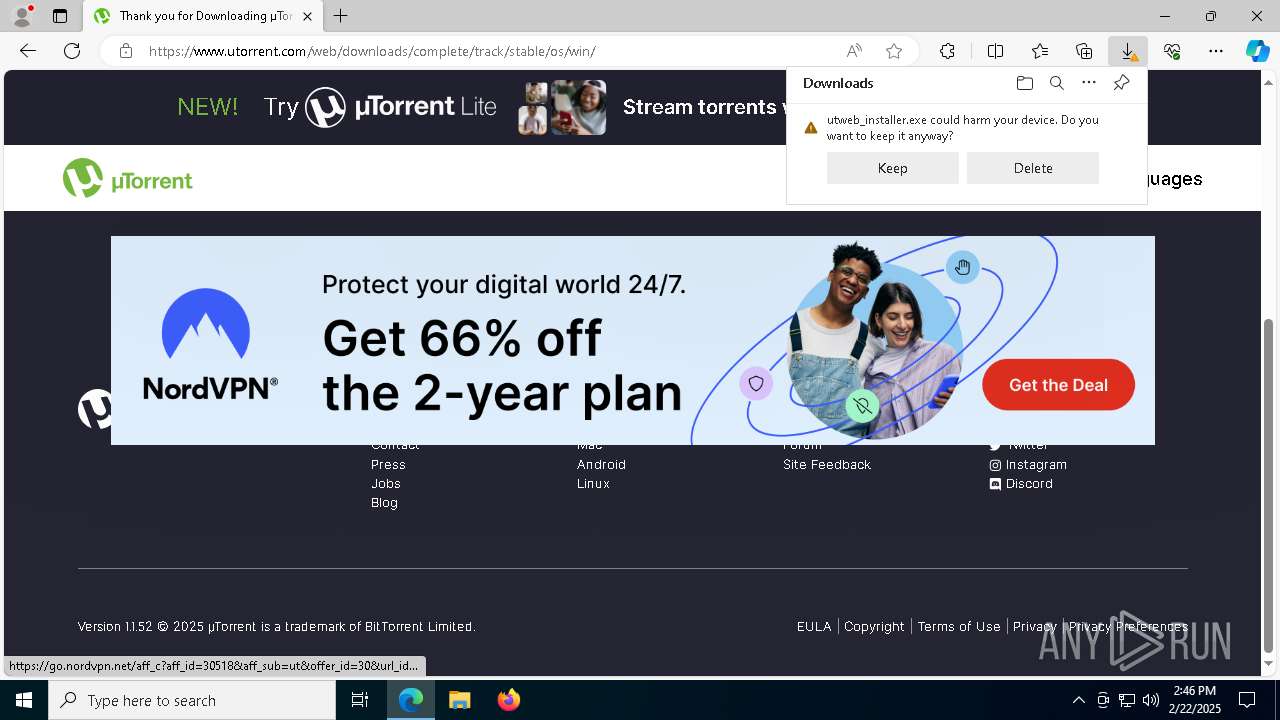
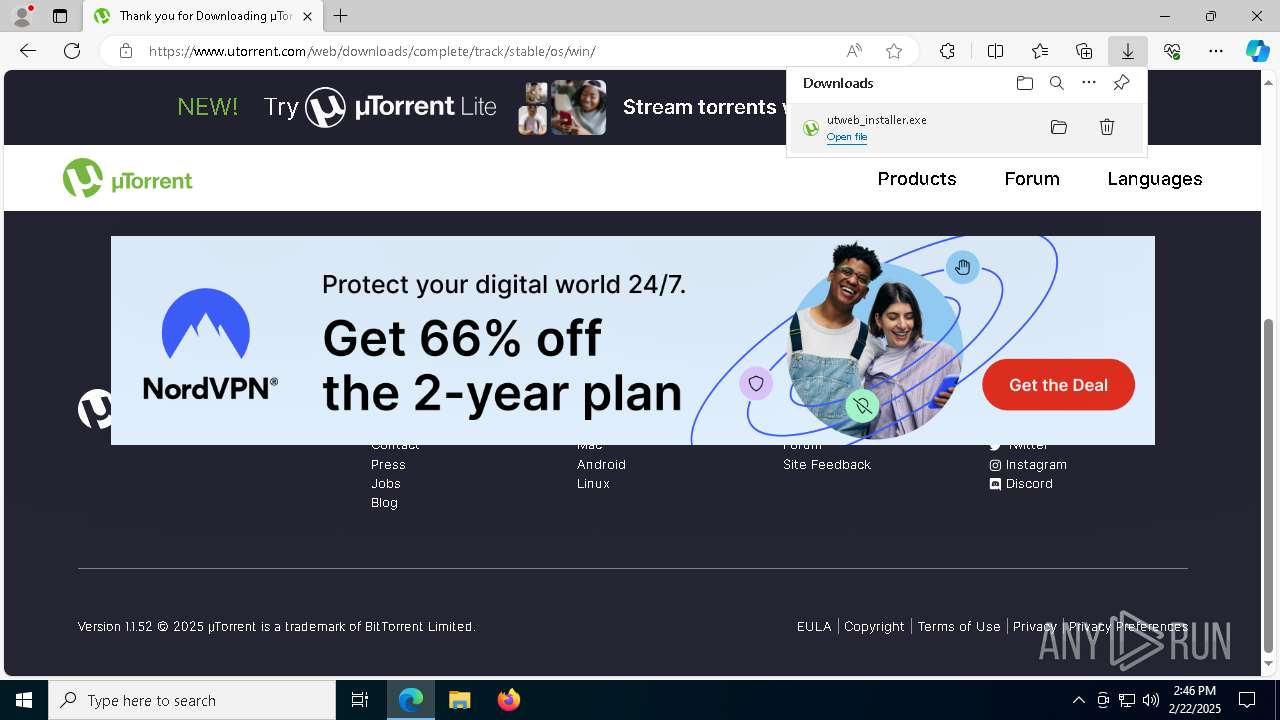
Executable content was dropped or overwritten
- utweb_installer.exe (PID: 520)
- beta (PID: 4528)
- avg_secure_browser_setup.exe (PID: 8168)
- saBSI.exe (PID: 7980)
- vtkysdzd.exe (PID: 6328)
- rsStubActivator.exe (PID: 8012)
- saBSI.exe (PID: 7372)
- AVGBrowserUpdateSetup.exe (PID: 7736)
- UnifiedStub-installer.exe (PID: 7920)
- utweb.exe (PID: 5432)
- AVGBrowserUpdate.exe (PID: 5748)
Starts application with an unusual extension
- utweb_installer.exe (PID: 520)
Malware-specific behavior (creating "System.dll" in Temp)
- beta (PID: 4528)
The process creates files with name similar to system file names
- beta (PID: 4528)
Creates a software uninstall entry
- beta (PID: 4528)
- UnifiedStub-installer.exe (PID: 7920)
Reads security settings of Internet Explorer
- beta (PID: 4528)
- utweb_installer.exe (PID: 520)
- saBSI.exe (PID: 7980)
- avg_secure_browser_setup.exe (PID: 8168)
- rsStubActivator.exe (PID: 8012)
- utweb.exe (PID: 5432)
- saBSI.exe (PID: 7372)
- AVGBrowserUpdate.exe (PID: 5748)
Checks Windows Trust Settings
- saBSI.exe (PID: 7980)
- saBSI.exe (PID: 7372)
- avg_secure_browser_setup.exe (PID: 8168)
- utweb.exe (PID: 5432)
Reads the BIOS version
- avg_secure_browser_setup.exe (PID: 8168)
Adds/modifies Windows certificates
- saBSI.exe (PID: 7980)
- utweb.exe (PID: 5432)
The process verifies whether the antivirus software is installed
- avg_secure_browser_setup.exe (PID: 8168)
- saBSI.exe (PID: 7372)
- AVGBrowserUpdate.exe (PID: 2292)
- AVGBrowserUpdateComRegisterShell64.exe (PID: 6096)
- AVGBrowserUpdateComRegisterShell64.exe (PID: 5916)
- AVGBrowserUpdate.exe (PID: 7852)
- AVGBrowserUpdateComRegisterShell64.exe (PID: 3996)
- AVGBrowserUpdate.exe (PID: 6212)
- AVGBrowserUpdate.exe (PID: 5748)
- AVGBrowserUpdate.exe (PID: 7880)
- AVGBrowserUpdate.exe (PID: 7768)
Reads the date of Windows installation
- rsStubActivator.exe (PID: 8012)
Searches for installed software
- avg_secure_browser_setup.exe (PID: 8168)
- UnifiedStub-installer.exe (PID: 7920)
Process drops legitimate windows executable
- vtkysdzd.exe (PID: 6328)
Potential Corporate Privacy Violation
- utweb.exe (PID: 5432)
- AVGBrowserUpdate.exe (PID: 7768)
Executes as Windows Service
- rsSyncSvc.exe (PID: 4704)
- AVGBrowserUpdate.exe (PID: 7768)
Disables SEHOP
- AVGBrowserUpdate.exe (PID: 5748)
Starts itself from another location
- AVGBrowserUpdate.exe (PID: 5748)
Creates/Modifies COM task schedule object
- AVGBrowserUpdateComRegisterShell64.exe (PID: 3996)
- AVGBrowserUpdate.exe (PID: 7852)
- AVGBrowserUpdateComRegisterShell64.exe (PID: 6096)
- AVGBrowserUpdateComRegisterShell64.exe (PID: 5916)
- AVGBrowserUpdate.exe (PID: 5748)
INFO
The sample compiled with english language support
- msedge.exe (PID: 6816)
- utweb_installer.exe (PID: 520)
- msedge.exe (PID: 6460)
- beta (PID: 4528)
- avg_secure_browser_setup.exe (PID: 8168)
- rsStubActivator.exe (PID: 8012)
- saBSI.exe (PID: 7980)
- vtkysdzd.exe (PID: 6328)
- AVGBrowserUpdateSetup.exe (PID: 7736)
- UnifiedStub-installer.exe (PID: 7920)
- utweb.exe (PID: 5432)
- AVGBrowserUpdate.exe (PID: 5748)
Reads the software policy settings
- utweb_installer.exe (PID: 520)
- rsStubActivator.exe (PID: 8012)
- saBSI.exe (PID: 7980)
- saBSI.exe (PID: 7372)
- avg_secure_browser_setup.exe (PID: 8168)
- UnifiedStub-installer.exe (PID: 7920)
- utweb.exe (PID: 5432)
- AVGBrowserUpdate.exe (PID: 7880)
- AVGBrowserUpdate.exe (PID: 7768)
Reads the computer name
- utweb_installer.exe (PID: 520)
- identity_helper.exe (PID: 7904)
- beta (PID: 4528)
- saBSI.exe (PID: 7980)
- rsStubActivator.exe (PID: 8012)
- avg_secure_browser_setup.exe (PID: 8168)
- utweb.exe (PID: 5432)
- saBSI.exe (PID: 7372)
- UnifiedStub-installer.exe (PID: 7920)
- rsSyncSvc.exe (PID: 4764)
- rsSyncSvc.exe (PID: 4704)
- AVGBrowserUpdate.exe (PID: 5748)
- helper.exe (PID: 4596)
- AVGBrowserUpdate.exe (PID: 2292)
- AVGBrowserUpdate.exe (PID: 7852)
- AVGBrowserUpdate.exe (PID: 6212)
- AVGBrowserUpdate.exe (PID: 7768)
- AVGBrowserUpdate.exe (PID: 7880)
Executable content was dropped or overwritten
- msedge.exe (PID: 6816)
- msedge.exe (PID: 6460)
Create files in a temporary directory
- utweb_installer.exe (PID: 520)
- beta (PID: 4528)
- rsStubActivator.exe (PID: 8012)
- avg_secure_browser_setup.exe (PID: 8168)
- saBSI.exe (PID: 7372)
- vtkysdzd.exe (PID: 6328)
- AVGBrowserUpdate.exe (PID: 7768)
Checks proxy server information
- utweb_installer.exe (PID: 520)
- beta (PID: 4528)
- rsStubActivator.exe (PID: 8012)
- saBSI.exe (PID: 7980)
- avg_secure_browser_setup.exe (PID: 8168)
- saBSI.exe (PID: 7372)
- UnifiedStub-installer.exe (PID: 7920)
- utweb.exe (PID: 5432)
- AVGBrowserUpdate.exe (PID: 7880)
Reads Environment values
- identity_helper.exe (PID: 7904)
- rsStubActivator.exe (PID: 8012)
- avg_secure_browser_setup.exe (PID: 8168)
- UnifiedStub-installer.exe (PID: 7920)
Reads the machine GUID from the registry
- utweb_installer.exe (PID: 520)
- rsStubActivator.exe (PID: 8012)
- saBSI.exe (PID: 7980)
- utweb.exe (PID: 5432)
- saBSI.exe (PID: 7372)
- avg_secure_browser_setup.exe (PID: 8168)
- UnifiedStub-installer.exe (PID: 7920)
- AVGBrowserUpdate.exe (PID: 5748)
- AVGBrowserUpdate.exe (PID: 7768)
Checks supported languages
- utweb_installer.exe (PID: 520)
- beta (PID: 4528)
- identity_helper.exe (PID: 7904)
- rsStubActivator.exe (PID: 8012)
- saBSI.exe (PID: 7980)
- avg_secure_browser_setup.exe (PID: 8168)
- utweb.exe (PID: 5432)
- vtkysdzd.exe (PID: 6328)
- saBSI.exe (PID: 7372)
- UnifiedStub-installer.exe (PID: 7920)
- rsSyncSvc.exe (PID: 4764)
- AVGBrowserUpdateSetup.exe (PID: 7736)
- rsSyncSvc.exe (PID: 4704)
- helper.exe (PID: 4596)
- AVGBrowserUpdate.exe (PID: 2292)
- AVGBrowserUpdateComRegisterShell64.exe (PID: 3996)
- AVGBrowserUpdateComRegisterShell64.exe (PID: 6096)
- AVGBrowserUpdateComRegisterShell64.exe (PID: 5916)
- AVGBrowserUpdate.exe (PID: 7852)
- AVGBrowserUpdate.exe (PID: 6212)
- AVGBrowserUpdate.exe (PID: 7768)
- AVGBrowserUpdate.exe (PID: 5748)
- AVGBrowserUpdate.exe (PID: 7880)
Application launched itself
- msedge.exe (PID: 6460)
Creates files or folders in the user directory
- beta (PID: 4528)
- utweb.exe (PID: 5432)
- avg_secure_browser_setup.exe (PID: 8168)
- helper.exe (PID: 4596)
The sample compiled with arabic language support
- utweb_installer.exe (PID: 520)
- AVGBrowserUpdateSetup.exe (PID: 7736)
- AVGBrowserUpdate.exe (PID: 5748)
Creates files in the program directory
- saBSI.exe (PID: 7980)
- saBSI.exe (PID: 7372)
- UnifiedStub-installer.exe (PID: 7920)
- AVGBrowserUpdateSetup.exe (PID: 7736)
- AVGBrowserUpdate.exe (PID: 5748)
- AVGBrowserUpdate.exe (PID: 7768)
Disables trace logs
- rsStubActivator.exe (PID: 8012)
- UnifiedStub-installer.exe (PID: 7920)
Process checks computer location settings
- avg_secure_browser_setup.exe (PID: 8168)
- utweb_installer.exe (PID: 520)
- rsStubActivator.exe (PID: 8012)
- AVGBrowserUpdate.exe (PID: 5748)
The sample compiled with german language support
- AVGBrowserUpdateSetup.exe (PID: 7736)
- AVGBrowserUpdate.exe (PID: 5748)
The sample compiled with Indonesian language support
- AVGBrowserUpdateSetup.exe (PID: 7736)
- AVGBrowserUpdate.exe (PID: 5748)
The sample compiled with french language support
- AVGBrowserUpdateSetup.exe (PID: 7736)
- AVGBrowserUpdate.exe (PID: 5748)
The sample compiled with japanese language support
- AVGBrowserUpdateSetup.exe (PID: 7736)
- AVGBrowserUpdate.exe (PID: 5748)
The sample compiled with Italian language support
- AVGBrowserUpdateSetup.exe (PID: 7736)
- AVGBrowserUpdate.exe (PID: 5748)
The sample compiled with korean language support
- AVGBrowserUpdateSetup.exe (PID: 7736)
- AVGBrowserUpdate.exe (PID: 5748)
The sample compiled with polish language support
- AVGBrowserUpdateSetup.exe (PID: 7736)
- AVGBrowserUpdate.exe (PID: 5748)
The sample compiled with bulgarian language support
- AVGBrowserUpdateSetup.exe (PID: 7736)
- AVGBrowserUpdate.exe (PID: 5748)
The sample compiled with czech language support
- AVGBrowserUpdateSetup.exe (PID: 7736)
- AVGBrowserUpdate.exe (PID: 5748)
The sample compiled with swedish language support
- AVGBrowserUpdateSetup.exe (PID: 7736)
- AVGBrowserUpdate.exe (PID: 5748)
The sample compiled with turkish language support
- AVGBrowserUpdateSetup.exe (PID: 7736)
- AVGBrowserUpdate.exe (PID: 5748)
The sample compiled with chinese language support
- AVGBrowserUpdateSetup.exe (PID: 7736)
- AVGBrowserUpdate.exe (PID: 5748)
The sample compiled with portuguese language support
- AVGBrowserUpdateSetup.exe (PID: 7736)
- AVGBrowserUpdate.exe (PID: 5748)
The sample compiled with russian language support
- AVGBrowserUpdateSetup.exe (PID: 7736)
- AVGBrowserUpdate.exe (PID: 5748)
The sample compiled with slovak language support
- AVGBrowserUpdateSetup.exe (PID: 7736)
- AVGBrowserUpdate.exe (PID: 5748)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
188
Monitored processes
60
Malicious processes
20
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 520 | "C:\Users\admin\Downloads\utweb_installer.exe" | C:\Users\admin\Downloads\utweb_installer.exe | msedge.exe | ||||||||||||
User: admin Company: u Torrent Web Integrity Level: HIGH Description: u Torrent Web Exit code: 0 Version: 3.2.0.11264 Modules
| |||||||||||||||
| 540 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=33 --mojo-platform-channel-handle=7216 --field-trial-handle=2304,i,4463061170488512214,944751608890266835,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 644 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4236 --field-trial-handle=2304,i,4463061170488512214,944751608890266835,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2292 | "C:\Program Files (x86)\AVG\Browser\Update\AVGBrowserUpdate.exe" /regsvc | C:\Program Files (x86)\AVG\Browser\Update\AVGBrowserUpdate.exe | — | AVGBrowserUpdate.exe | |||||||||||
User: admin Company: Gen Digital Inc. Integrity Level: HIGH Description: AVG Browser Exit code: 0 Version: 1.8.1693.6 Modules
| |||||||||||||||
| 3420 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=1524 --field-trial-handle=2304,i,4463061170488512214,944751608890266835,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 3692 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --extension-process --renderer-sub-type=extension --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --mojo-platform-channel-handle=4136 --field-trial-handle=2304,i,4463061170488512214,944751608890266835,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 3996 | "C:\Program Files (x86)\AVG\Browser\Update\1.8.1693.6\AVGBrowserUpdateComRegisterShell64.exe" | C:\Program Files (x86)\AVG\Browser\Update\1.8.1693.6\AVGBrowserUpdateComRegisterShell64.exe | — | AVGBrowserUpdate.exe | |||||||||||
User: admin Company: Gen Digital Inc. Integrity Level: HIGH Description: AVG Browser Com Register Shell 64 Exit code: 0 Version: 1.8.1693.6 Modules
| |||||||||||||||
| 4528 | "C:\Users\admin\AppData\Local\Temp\ISV82DF.tmp\beta" /S | C:\Users\admin\AppData\Local\Temp\ISV82DF.tmp\beta | utweb_installer.exe | ||||||||||||
User: admin Company: BitTorrent Limited Integrity Level: HIGH Description: uTorrent Web Exit code: 0 Version: 1.4.0.6042 Modules
| |||||||||||||||
| 4596 | helper/helper.exe 49958 -- ut_web/1.4.0.6042 hval/a4cf0cea2bf1ef11b4ea18f7786f96ee | C:\Users\admin\AppData\Roaming\uTorrent Web\helper\helper.exe | utweb.exe | ||||||||||||
User: admin Company: BitTorrent Inc. Integrity Level: HIGH Description: µTorrent Helper Version: 2.1.8.2789 Modules
| |||||||||||||||
| 4704 | "C:\Program Files\ReasonLabs\Common\rsSyncSvc.exe" -pn:EPP -lpn:rav_antivirus -url:https://update.reasonsecurity.com/v2/live -bn:ReasonLabs -dt:10 | C:\Program Files\ReasonLabs\Common\rsSyncSvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Reason Software Company Inc. Integrity Level: SYSTEM Description: Reason Security Synchronize Service Version: 1.8.5.0 Modules
| |||||||||||||||
Total events
26 396
Read events
26 005
Write events
338
Delete events
53
Modification events
| (PID) Process: | (6460) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6460) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6460) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6460) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6460) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 307B6B75528D2F00 | |||
| (PID) Process: | (6460) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 0D938875528D2F00 | |||
| (PID) Process: | (6460) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262900 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {02767A0C-BB2A-45C1-858F-5DB5B3E7D744} | |||
| (PID) Process: | (6460) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262900 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {6DAF4AA4-9FE6-48DE-AE66-6E379FEEAED6} | |||
| (PID) Process: | (6460) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262900 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {A248A703-A67C-40AB-9CFF-0176C6533FE8} | |||
| (PID) Process: | (6460) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262900 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {4E5478D7-39B8-4E4C-B9A4-B794FF1088C0} | |||
Executable files
269
Suspicious files
267
Text files
126
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6460 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF134bb2.TMP | — | |
MD5:— | SHA256:— | |||
| 6460 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6460 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF134bb2.TMP | — | |
MD5:— | SHA256:— | |||
| 6460 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF134bb2.TMP | — | |
MD5:— | SHA256:— | |||
| 6460 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6460 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6460 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF134bc2.TMP | — | |
MD5:— | SHA256:— | |||
| 6460 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6460 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF134bc2.TMP | — | |
MD5:— | SHA256:— | |||
| 6460 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
35
TCP/UDP connections
270
DNS requests
133
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.253.202:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.32.238.34:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6448 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
2828 | SIHClient.exe | GET | 200 | 2.16.253.202:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2828 | SIHClient.exe | GET | 200 | 2.16.253.202:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4528 | beta | POST | 200 | 52.206.117.199:80 | http://i-4101.b-6042.utweb.bench.utorrent.com/e?i=4101 | unknown | — | — | whitelisted |
4528 | beta | POST | 200 | 52.206.117.199:80 | http://i-4101.b-6042.utweb.bench.utorrent.com/e?i=4101 | unknown | — | — | whitelisted |
5432 | utweb.exe | GET | — | 43.159.94.102:80 | http://btinstall-artifacts.bittorrent.com/helper_ui/helper_web_ui.btinstall | unknown | — | — | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3220 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.32.238.34:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 2.16.253.202:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5064 | SearchApp.exe | 2.16.204.152:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
3976 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
www.utorrent.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4528 | beta | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |
4528 | beta | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |
5432 | utweb.exe | Misc activity | INFO [ANY.RUN] P2P BitTorrent Protocol |
5432 | utweb.exe | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
5432 | utweb.exe | Potentially Bad Traffic | ET INFO Executable served from Amazon S3 |
7768 | AVGBrowserUpdate.exe | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
Process | Message |
|---|---|
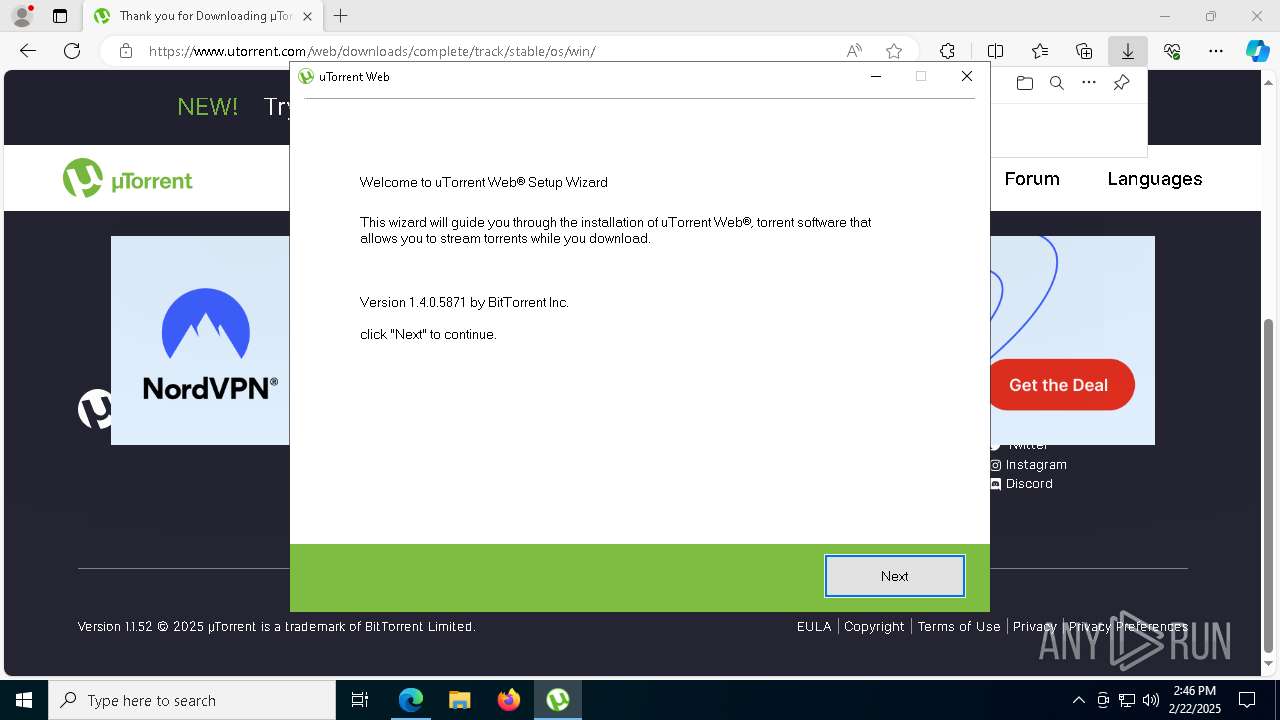
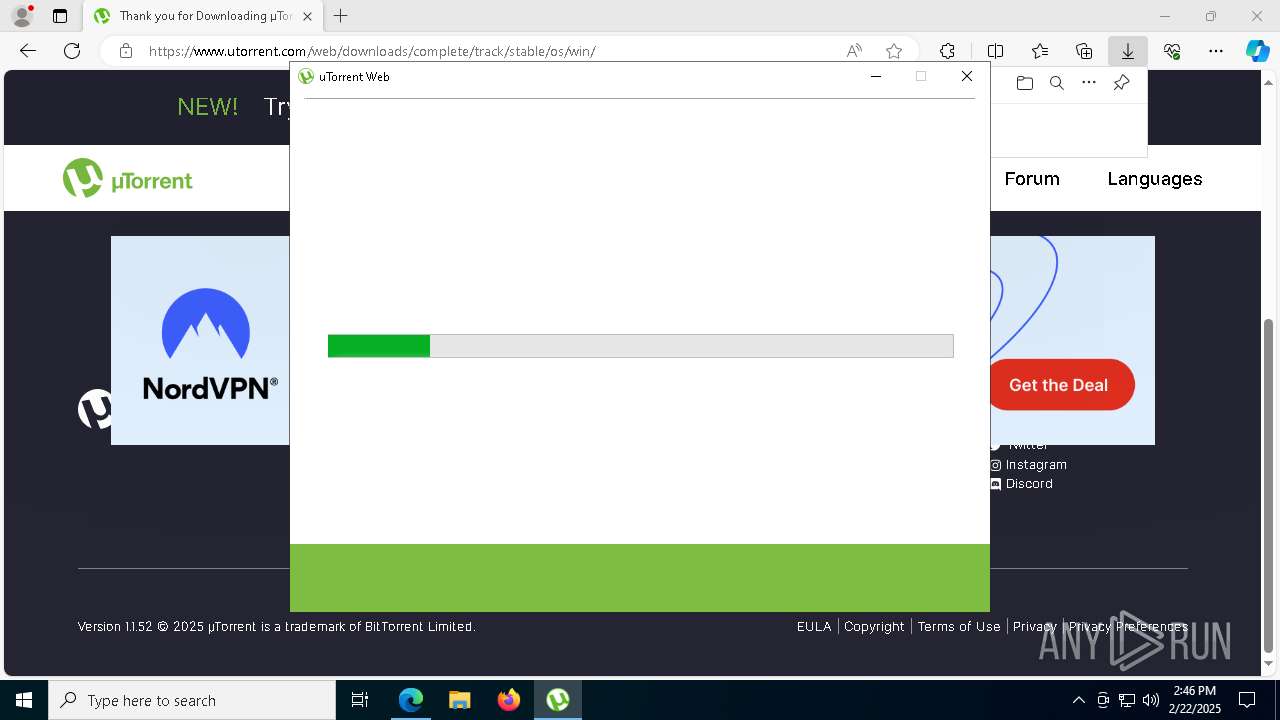
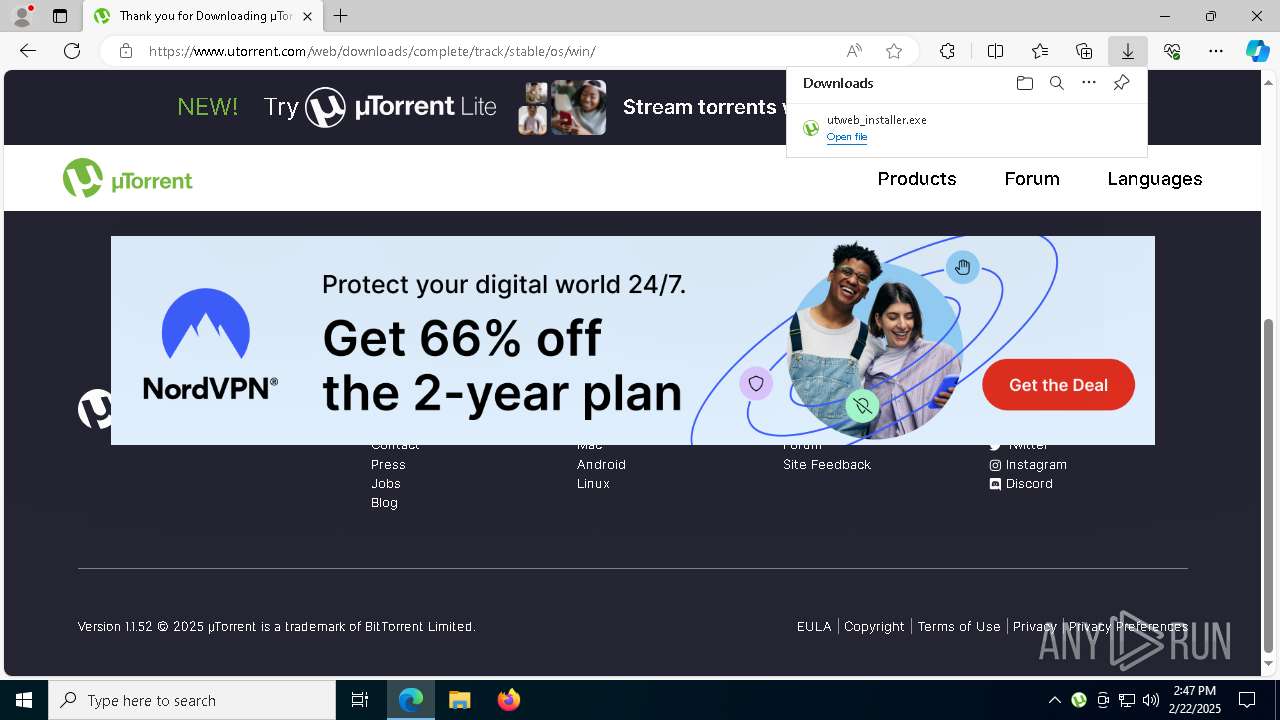
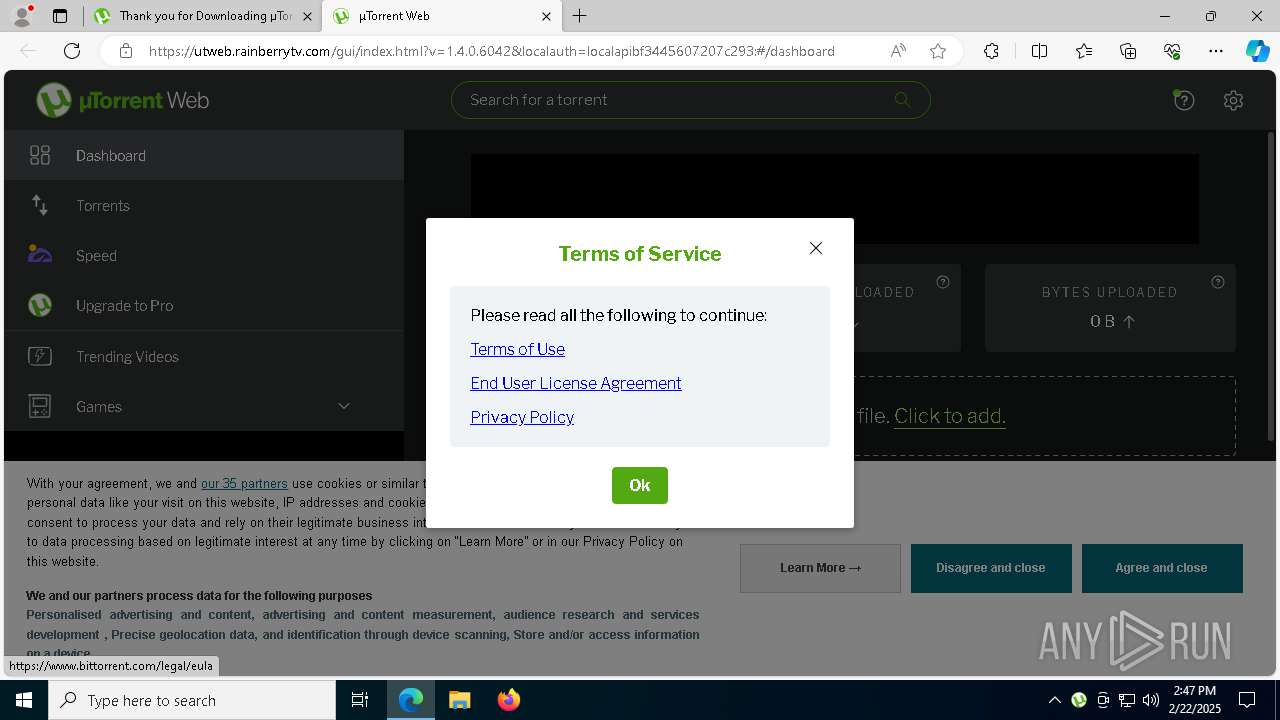
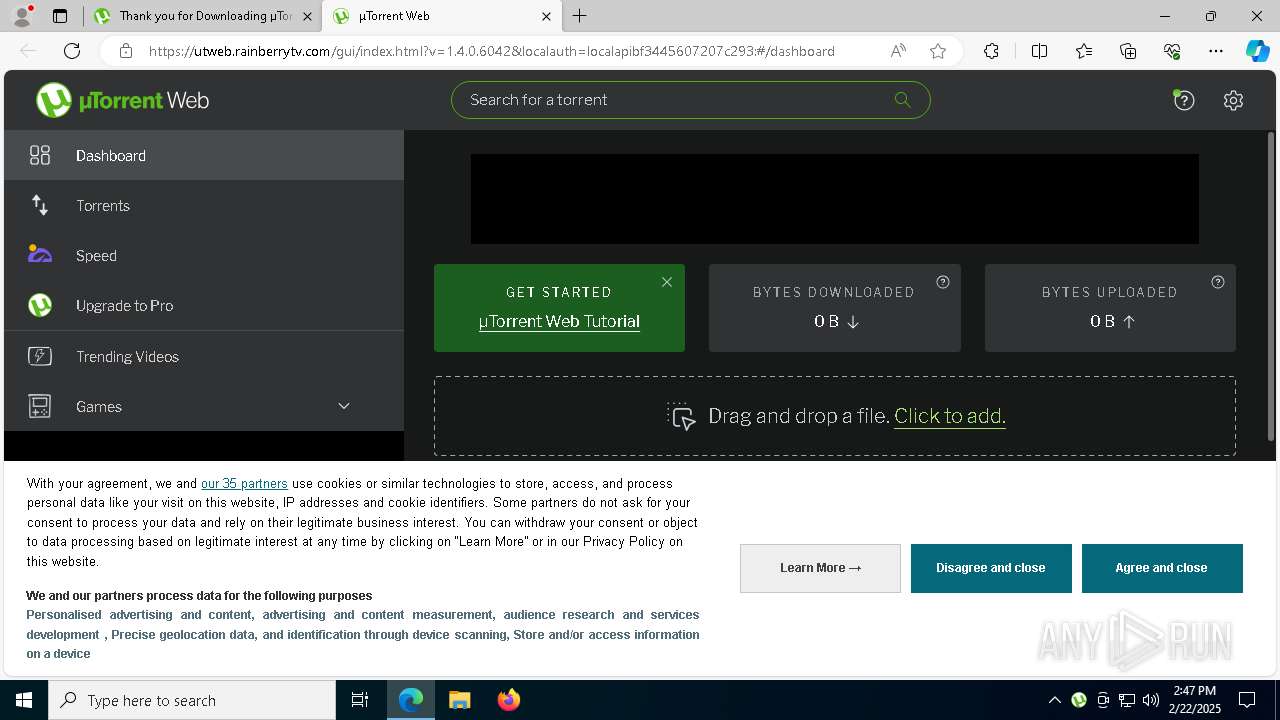
utweb_installer.exe | LoadingPage
|
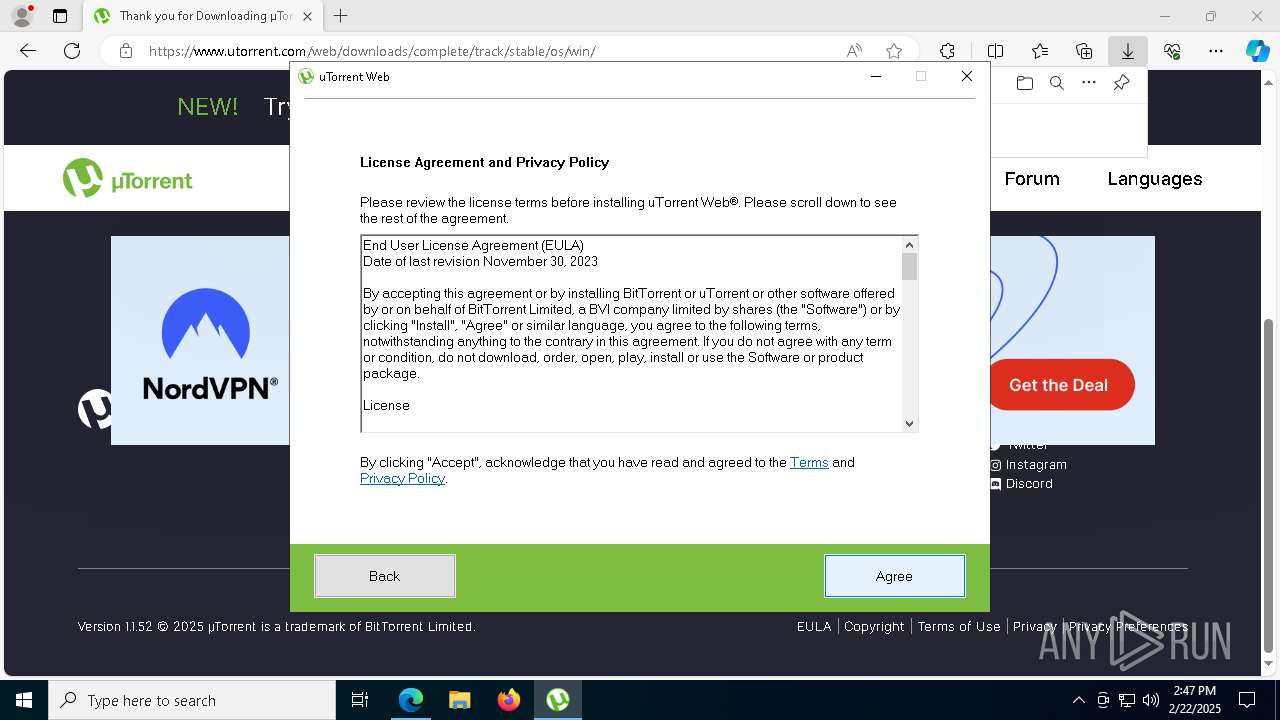
utweb_installer.exe | LicensePage
|
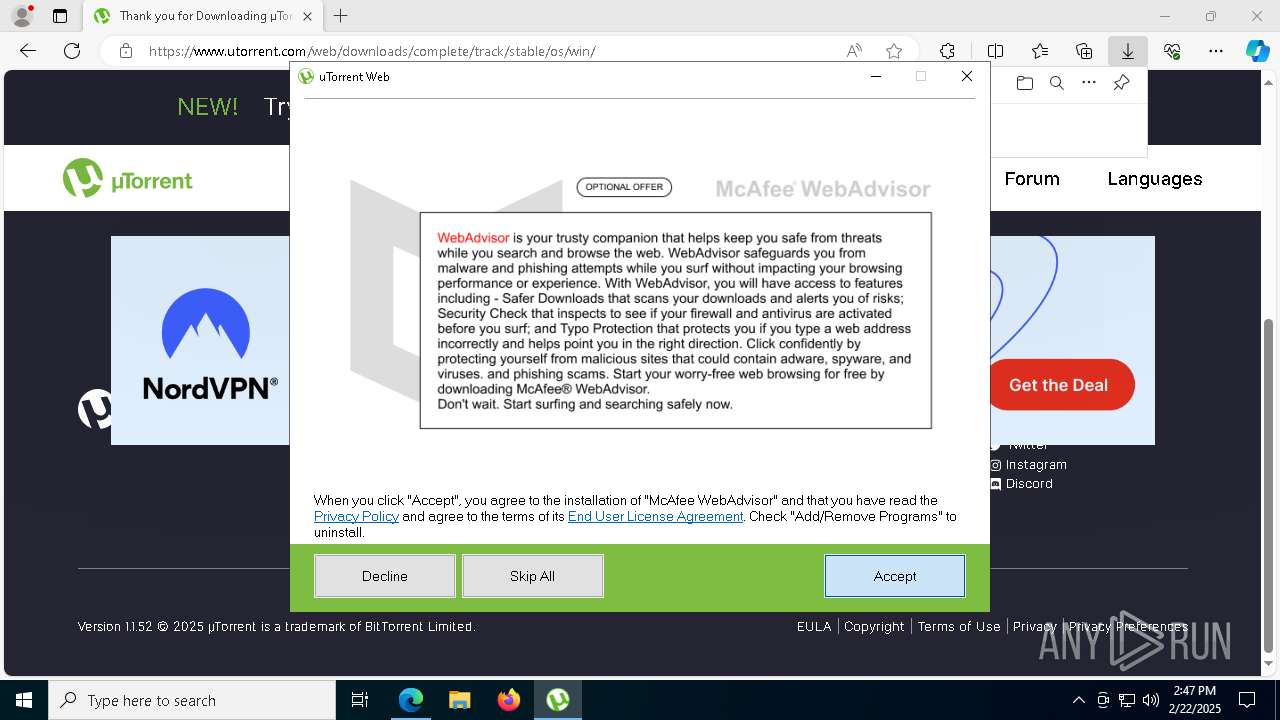
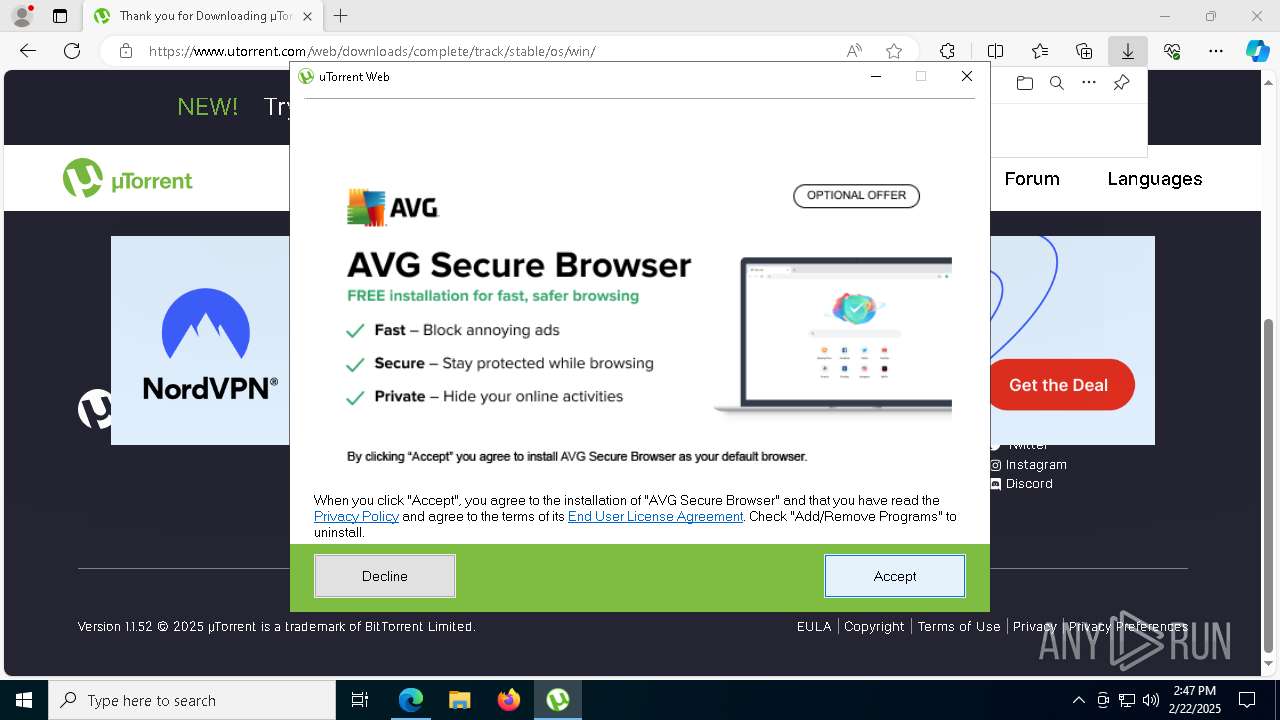
utweb_installer.exe | ProductPage
|
utweb_installer.exe | ProductPage
|
utweb_installer.exe | ProductPage
|
utweb_installer.exe | DownloadPageISV
|
utweb_installer.exe | FinishPageISV
|
saBSI.exe | NCPrivateLoadAndValidateMPTDll: Looking in current directory
|
saBSI.exe | NCPrivateLoadAndValidateMPTDll: Looking in EXE directory
|
saBSI.exe | NotComDllGetInterface: C:\Users\admin\AppData\Local\Temp\ISV82DF.tmp\saBSI\saBSI.exe loading C:\Users\admin\AppData\Local\Temp\ISV82DF.tmp\saBSI\mfeaaca.dll, WinVerifyTrust failed with 80092003
|