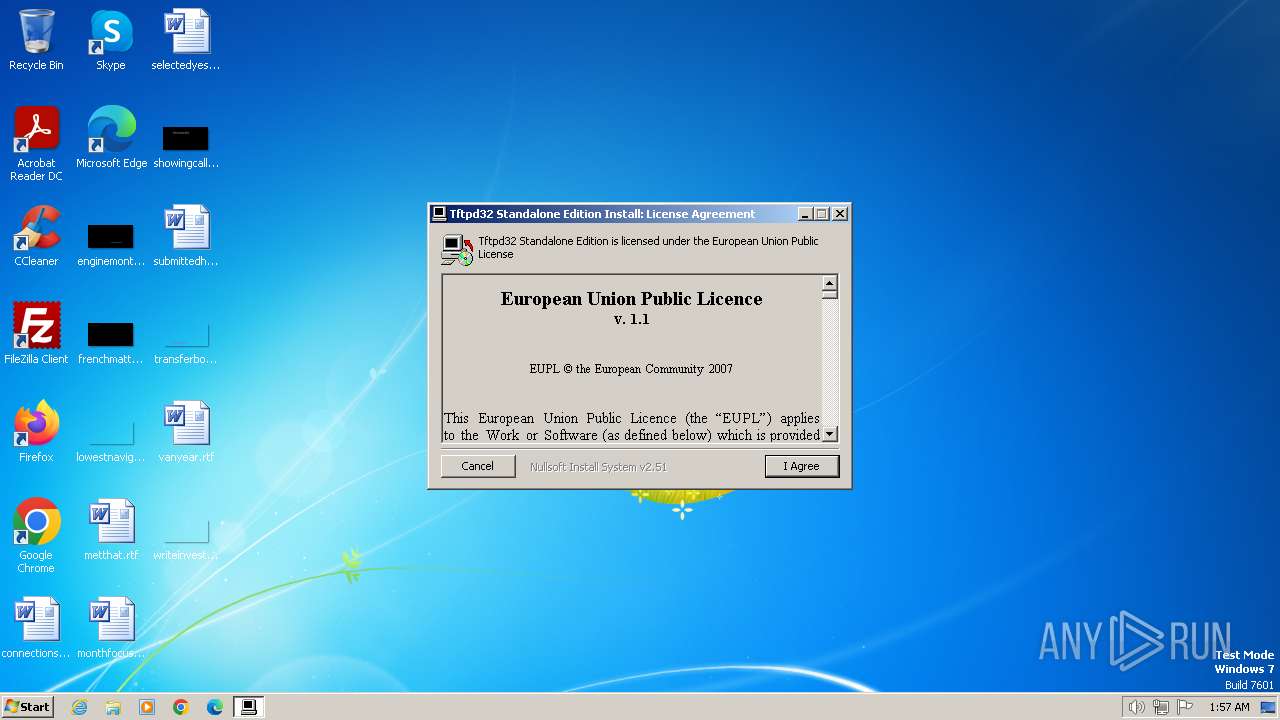
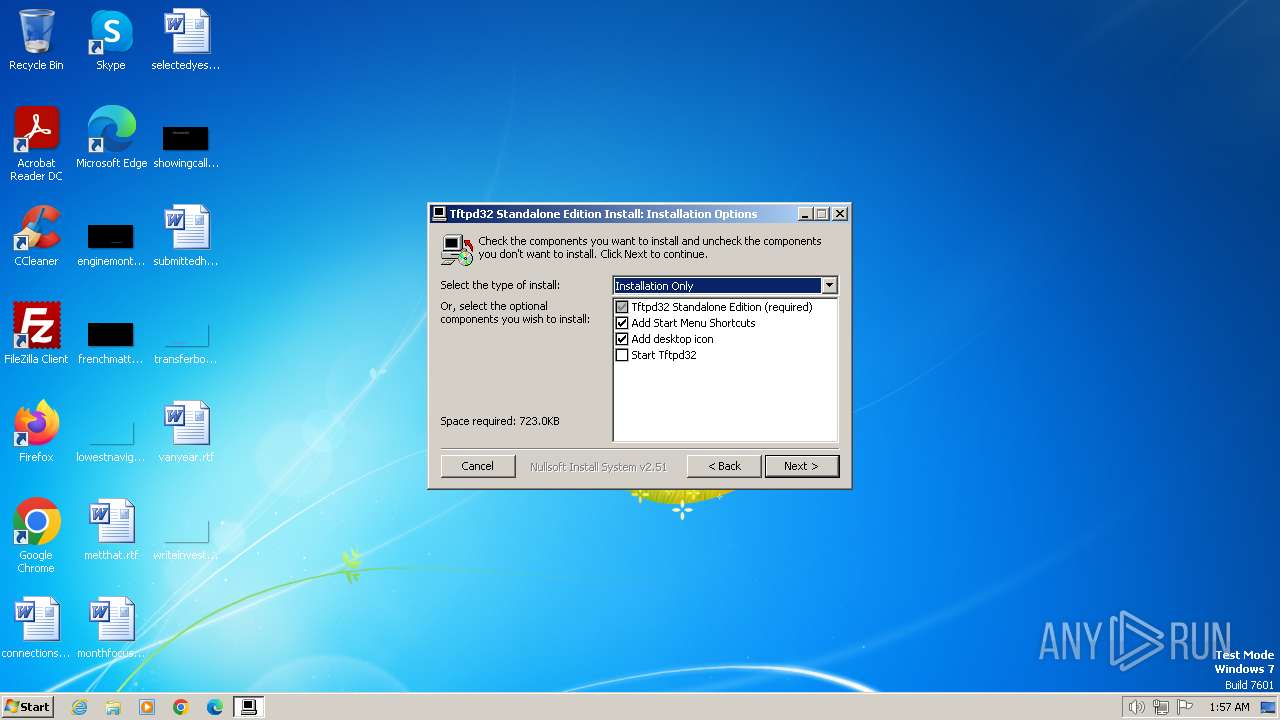
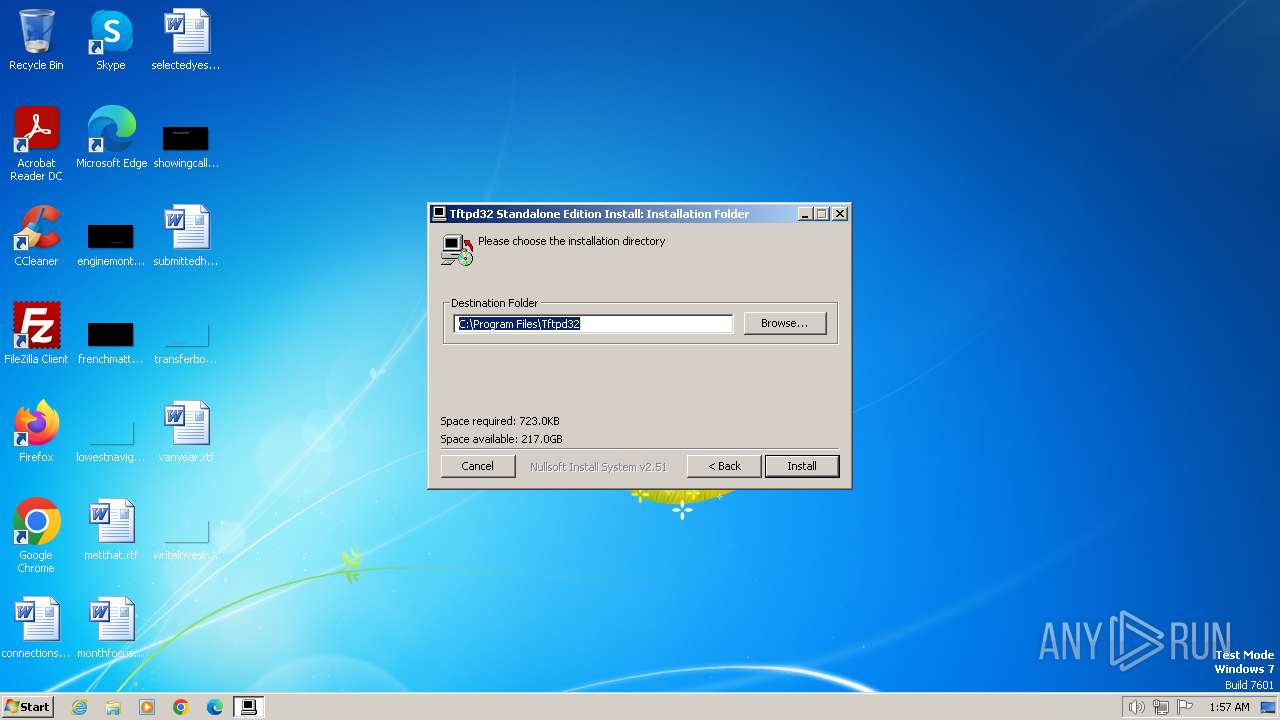
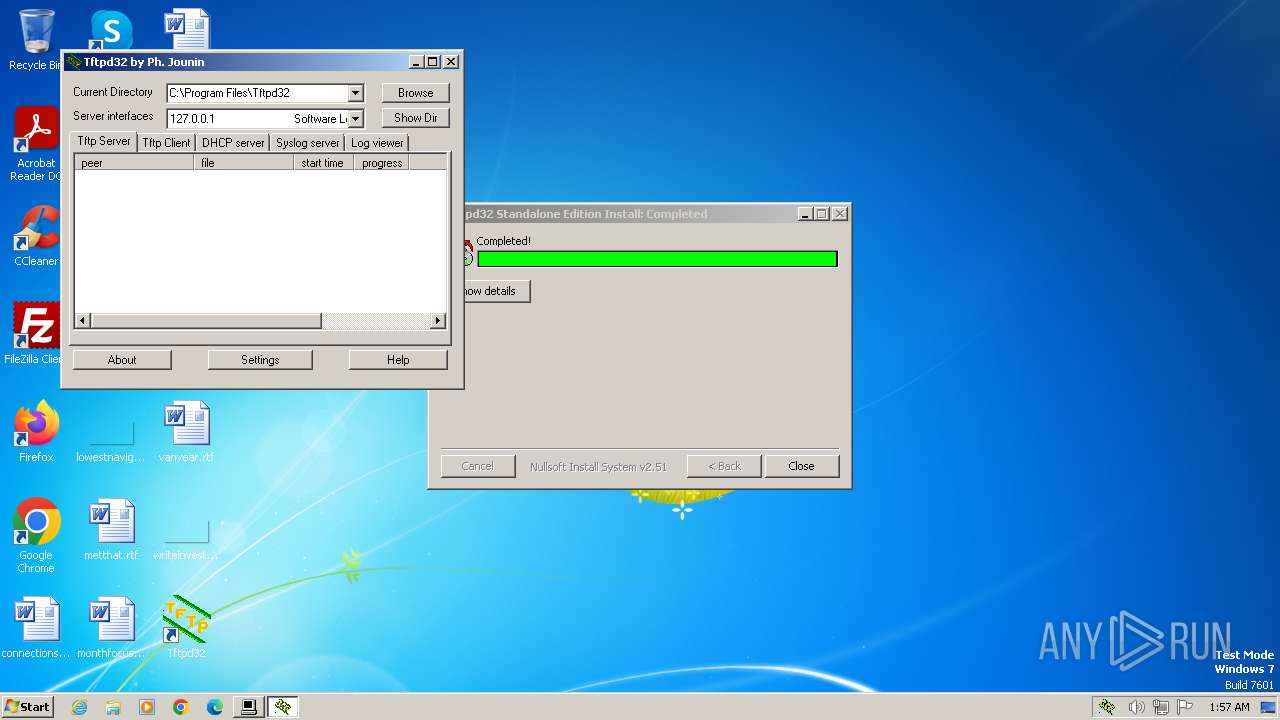
| File name: | Tftpd32-4.64-setup.exe |
| Full analysis: | https://app.any.run/tasks/cd32099e-239d-4f21-9bce-0f8ba9a24ef3 |
| Verdict: | Malicious activity |
| Analysis date: | February 13, 2024, 01:57:13 |
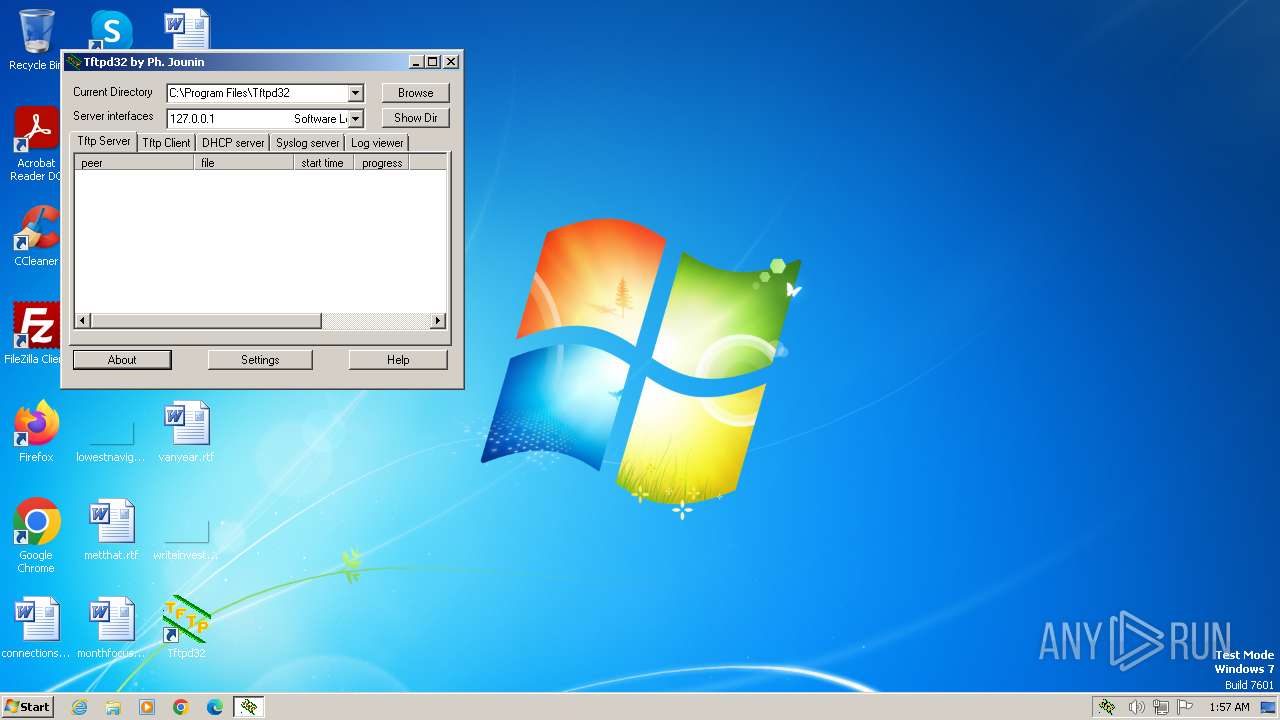
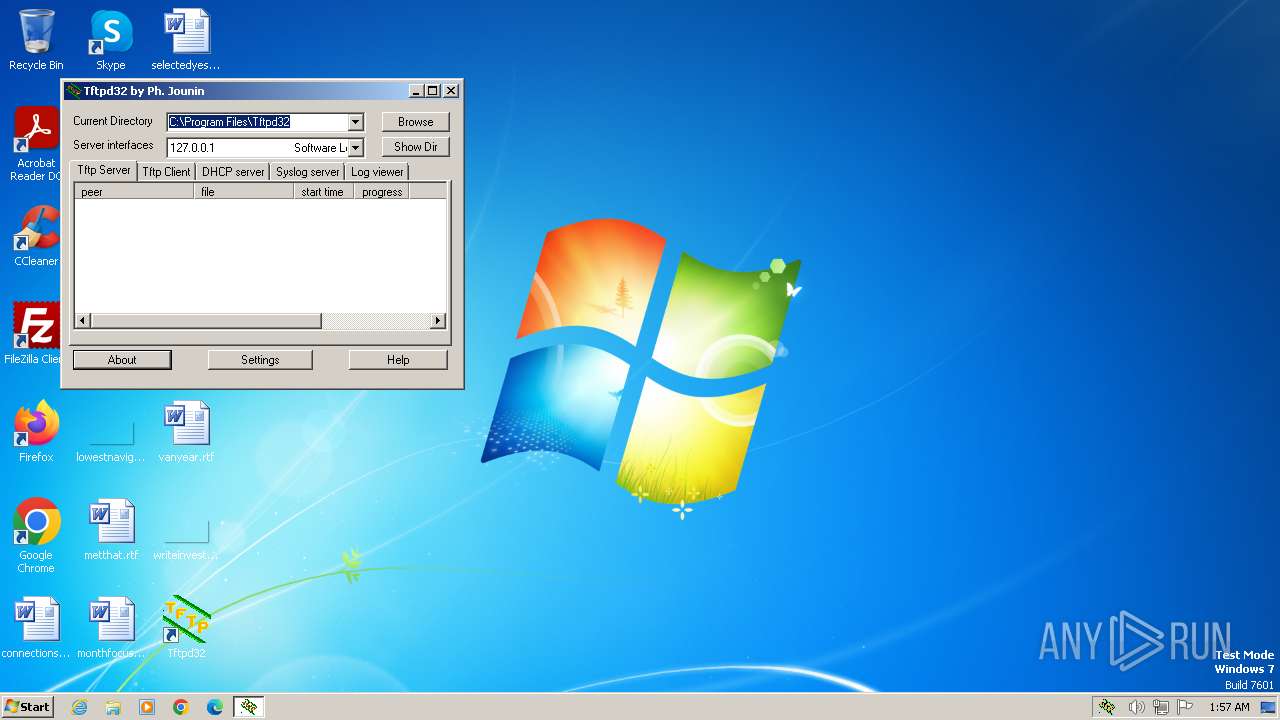
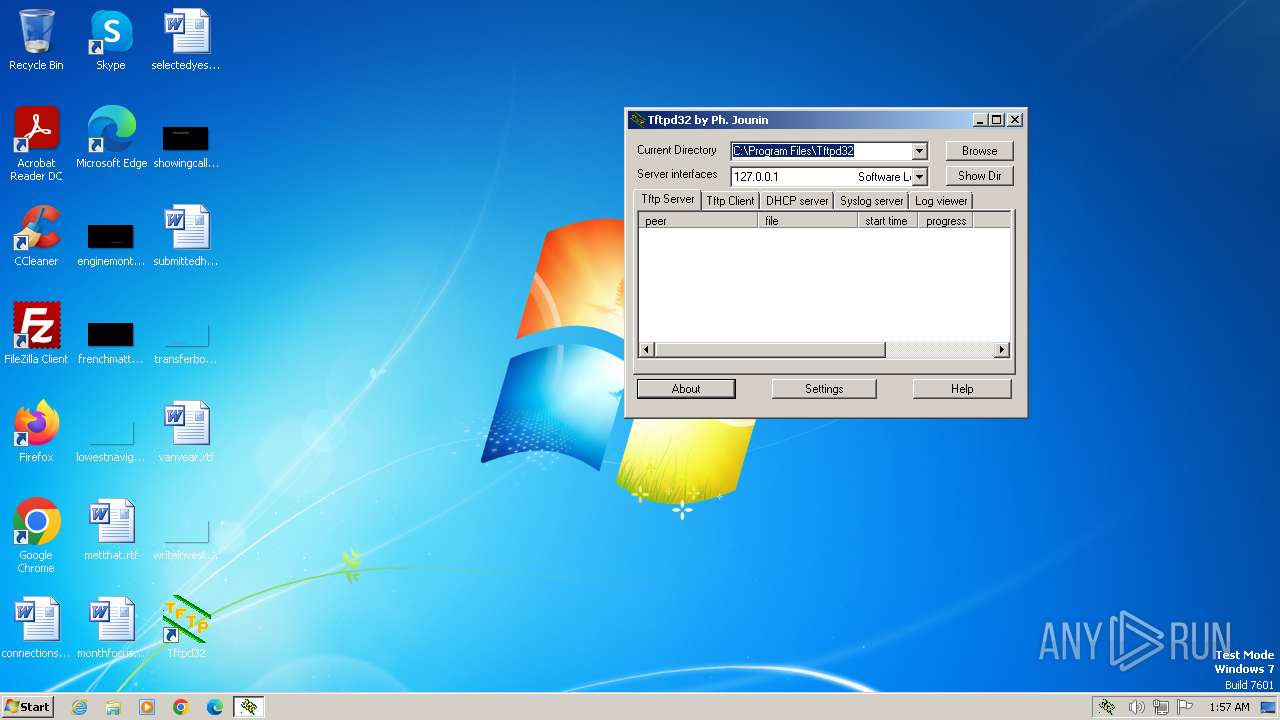
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 4A77C0A4701C751144D2D6161935F7F7 |
| SHA1: | 77D4D5E42D37C5389FC74BB0DFCF9D5B35A6DCE2 |
| SHA256: | 2DE0849E81686EF91AB4DFCA1C589247C7D8EDB937051B2DD3D4B9F16C8CB3FC |
| SSDEEP: | 12288:sJ+gA6RPCuLmMl06EpwUG5IAeKPOFwTM84qpcy+qtv2tSoTqLQby463:swgA6RPCUmMlQqIWWFA4qphN28o+LQeb |
MALICIOUS
Drops the executable file immediately after the start
- Tftpd32-4.64-setup.exe (PID: 2848)
SUSPICIOUS
Creates a software uninstall entry
- Tftpd32-4.64-setup.exe (PID: 2848)
Executable content was dropped or overwritten
- Tftpd32-4.64-setup.exe (PID: 2848)
Reads security settings of Internet Explorer
- tftpd32.exe (PID: 2304)
Reads the Internet Settings
- tftpd32.exe (PID: 2304)
- hh.exe (PID: 4000)
Reads Microsoft Outlook installation path
- hh.exe (PID: 4000)
Reads Internet Explorer settings
- hh.exe (PID: 4000)
INFO
Reads the computer name
- Tftpd32-4.64-setup.exe (PID: 2848)
- tftpd32.exe (PID: 2304)
Checks supported languages
- tftpd32.exe (PID: 2304)
- Tftpd32-4.64-setup.exe (PID: 2848)
Creates files or folders in the user directory
- Tftpd32-4.64-setup.exe (PID: 2848)
- hh.exe (PID: 4000)
Creates files in the program directory
- hh.exe (PID: 4000)
- Tftpd32-4.64-setup.exe (PID: 2848)
Reads the machine GUID from the registry
- hh.exe (PID: 4000)
Create files in a temporary directory
- hh.exe (PID: 4000)
Reads security settings of Internet Explorer
- hh.exe (PID: 4000)
Checks proxy server information
- hh.exe (PID: 4000)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:04:02 03:20:13+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 24576 |
| InitializedDataSize: | 164864 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x312a |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
43
Monitored processes
4
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
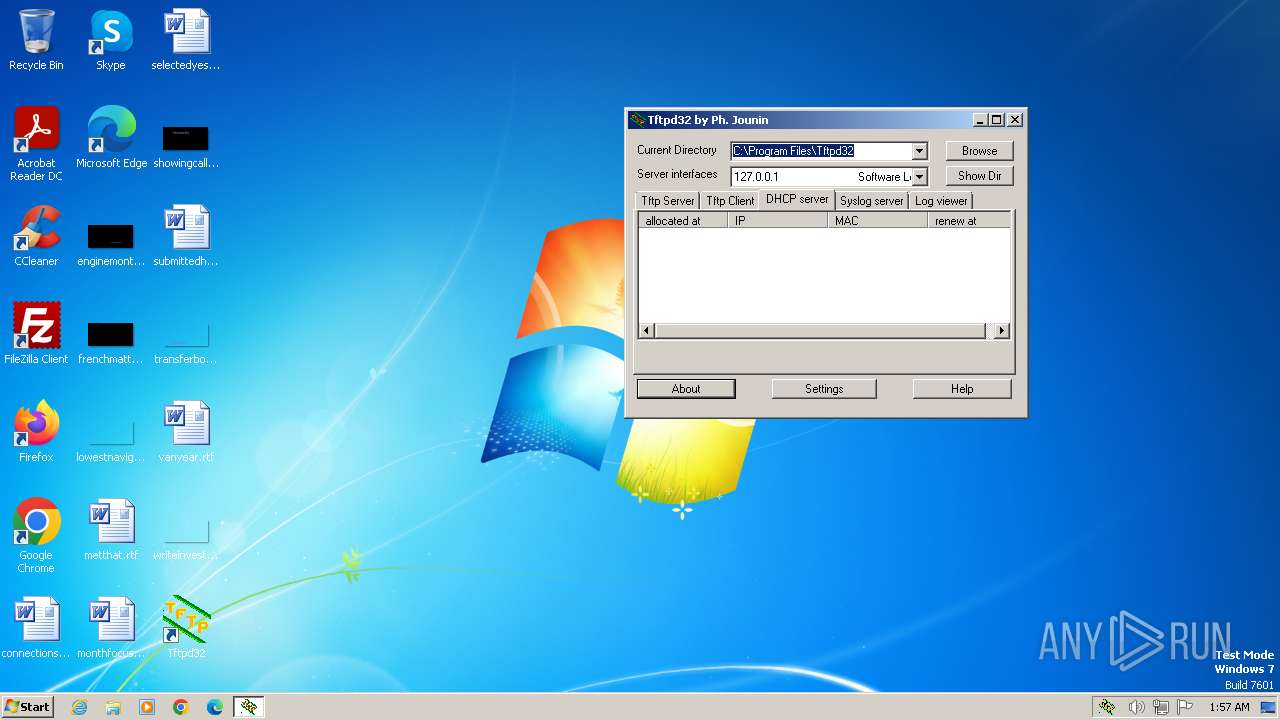
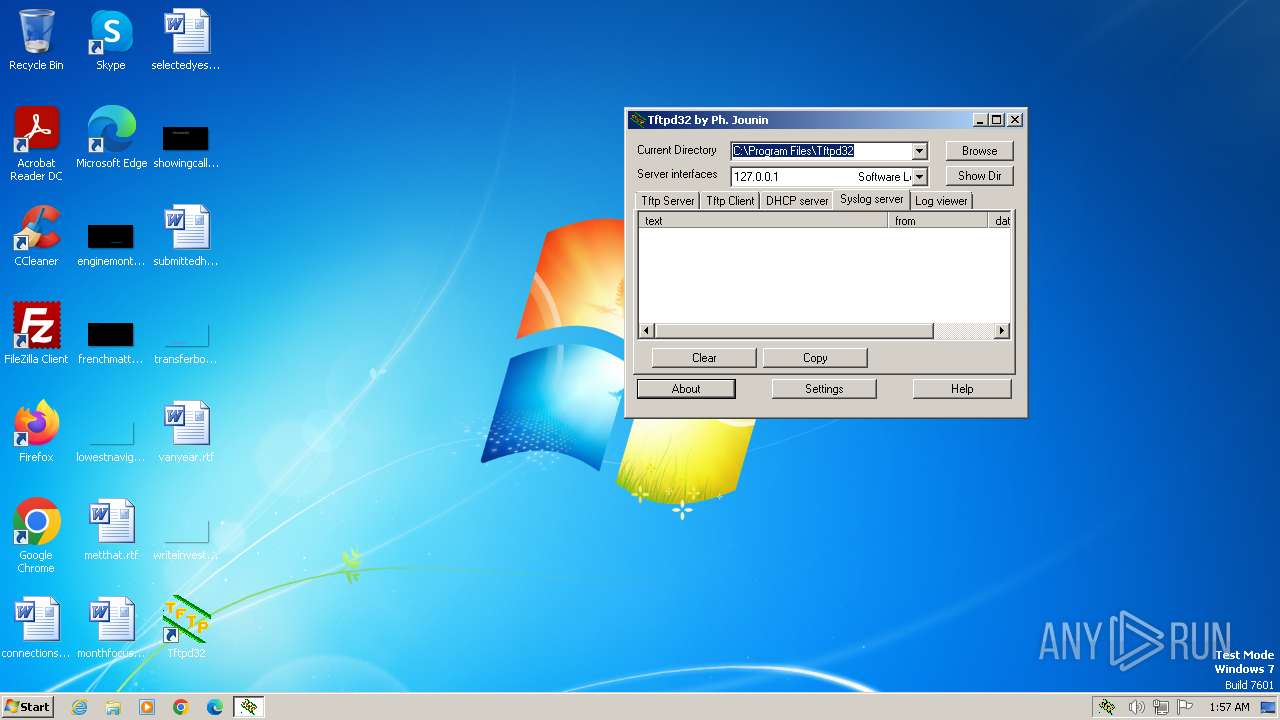
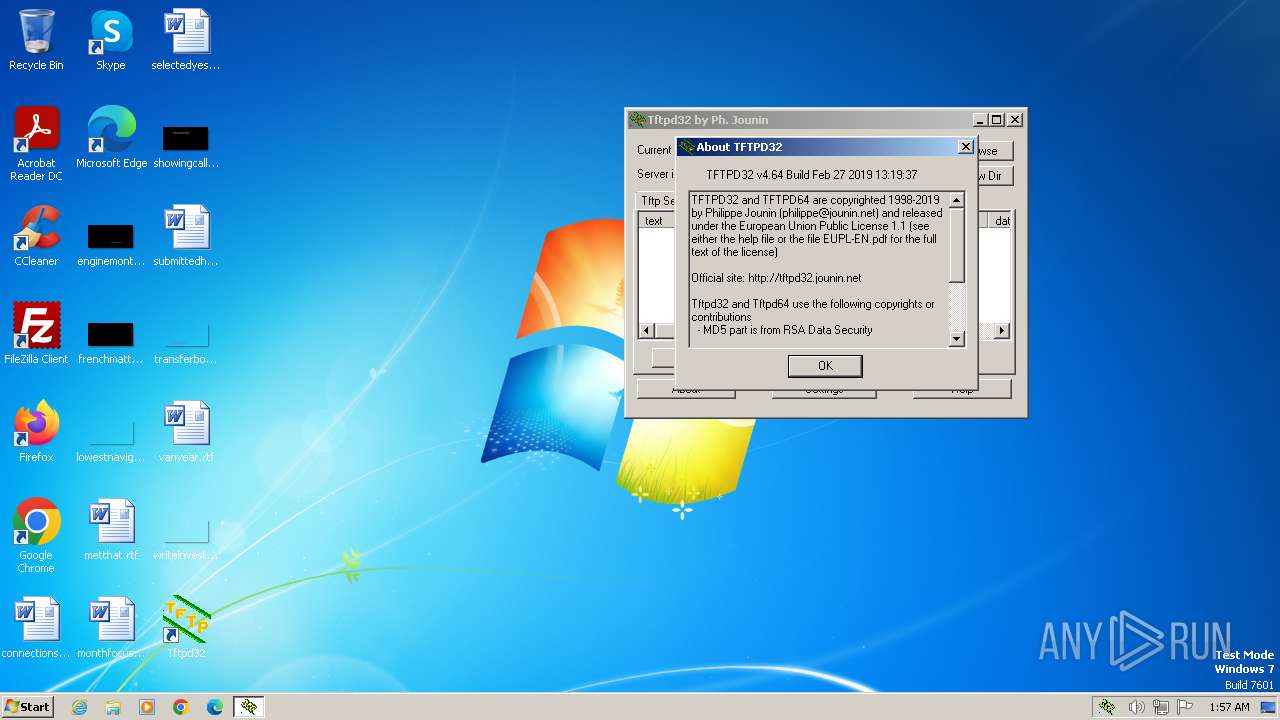
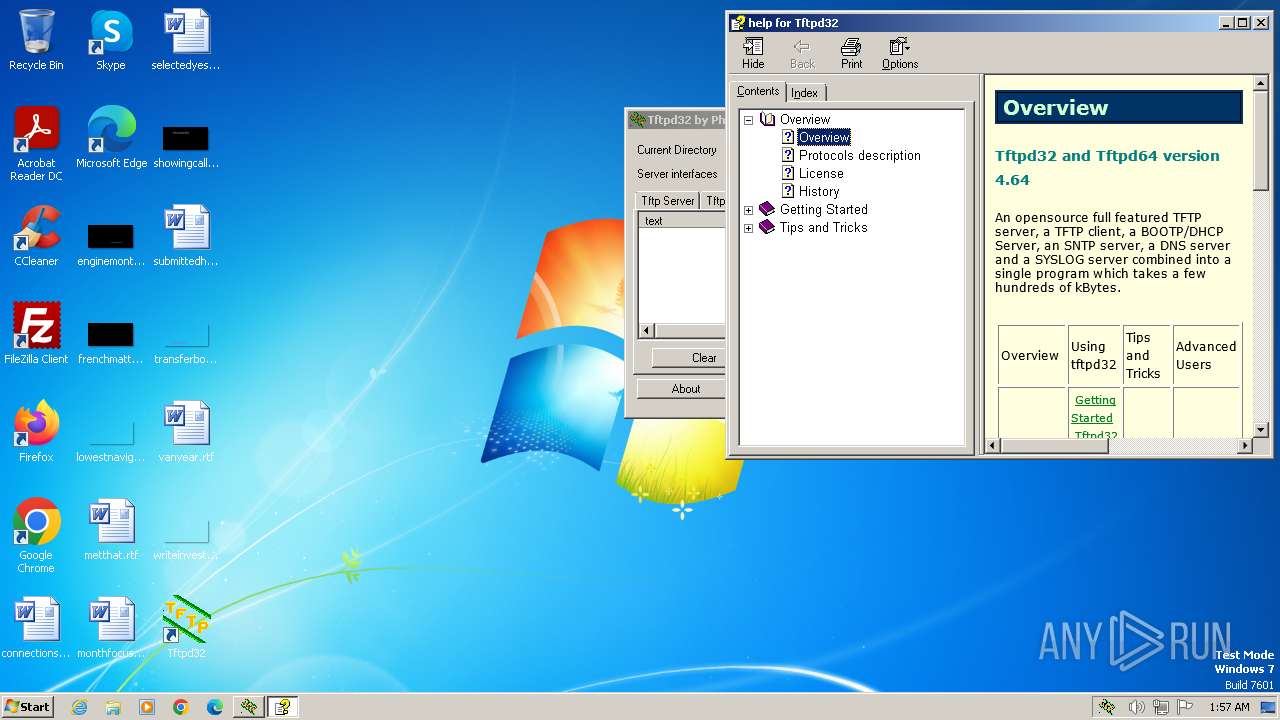
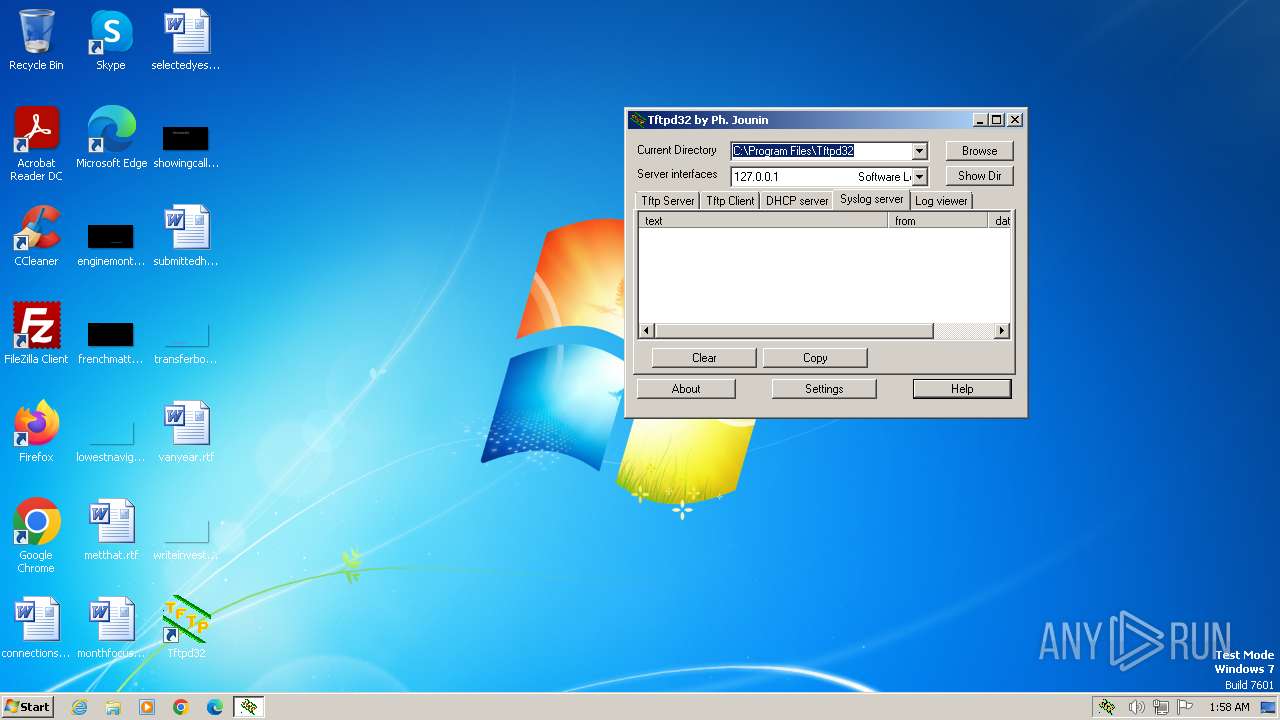
| 2304 | "C:\Program Files\Tftpd32\Tftpd32.exe" | C:\Program Files\Tftpd32\tftpd32.exe | Tftpd32-4.64-setup.exe | ||||||||||||
User: admin Company: Ph. Jounin Integrity Level: HIGH Description: TFTP server Exit code: 0 Modules
| |||||||||||||||
| 2848 | "C:\Users\admin\AppData\Local\Temp\Tftpd32-4.64-setup.exe" | C:\Users\admin\AppData\Local\Temp\Tftpd32-4.64-setup.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3652 | "C:\Users\admin\AppData\Local\Temp\Tftpd32-4.64-setup.exe" | C:\Users\admin\AppData\Local\Temp\Tftpd32-4.64-setup.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 4000 | "C:\Windows\hh.exe" C:\Program Files\Tftpd32\Tftpd32.chm | C:\Windows\hh.exe | — | tftpd32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft® HTML Help Executable Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
4 400
Read events
4 374
Write events
24
Delete events
2
Modification events
| (PID) Process: | (2848) Tftpd32-4.64-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Tftpd32 |
| Operation: | write | Name: | Install_Dir |
Value: C:\Program Files\Tftpd32 | |||
| (PID) Process: | (2848) Tftpd32-4.64-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Tftpd32 |
| Operation: | write | Name: | DisplayName |
Value: Tftpd32 Standalone Edition (remove only) | |||
| (PID) Process: | (2848) Tftpd32-4.64-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Tftpd32 |
| Operation: | write | Name: | UninstallString |
Value: "C:\Program Files\Tftpd32\uninstall.exe" | |||
| (PID) Process: | (2848) Tftpd32-4.64-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Tftpd32 |
| Operation: | write | Name: | NoModify |
Value: 1 | |||
| (PID) Process: | (2848) Tftpd32-4.64-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Tftpd32 |
| Operation: | write | Name: | NoRepair |
Value: 1 | |||
| (PID) Process: | (2304) tftpd32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2304) tftpd32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2304) tftpd32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2304) tftpd32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (4000) hh.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
3
Suspicious files
8
Text files
2
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4000 | hh.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\style[1].css | text | |
MD5:299697A50846097E56D45A7B018E31E8 | SHA256:86E2B6DEB97EC52E9C718C1AE59C1BE804A5F80E94EFCD044E4529E9927246D6 | |||
| 2848 | Tftpd32-4.64-setup.exe | C:\Program Files\Tftpd32\uninstall.exe | executable | |
MD5:81982BE80DEC4E8462EF03FD5E44F406 | SHA256:181A386BA1B874C4F2779A27181332374F640A89333C88E70309B829324DB07C | |||
| 4000 | hh.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\it_works[1].jpg | image | |
MD5:F2A6CC3DDD6209061C00F8301B364E2E | SHA256:48D0D20F7DE3AF20E835C00710A12AFA55512EE3672B18D649E34DED3FF34846 | |||
| 4000 | hh.exe | C:\Users\admin\AppData\Local\Temp\~DFEB296ECC21988BB1.TMP | gmc | |
MD5:BF619EAC0CDF3F68D496EA9344137E8B | SHA256:076A27C79E5ACE2A3D47F9DD2E83E4FF6EA8872B3C2218F66C92B89B55F36560 | |||
| 2848 | Tftpd32-4.64-setup.exe | C:\Program Files\Tftpd32\tftpd32.exe | executable | |
MD5:733ED472EDBBA6FCCFF0A74882CD6B51 | SHA256:C270EBD42AC19805F58BDA8A0A34898ADD80CDAFF3594038C3C9B47FDB0FA06A | |||
| 2848 | Tftpd32-4.64-setup.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Tftpd32\Tftpd32.lnk | binary | |
MD5:232E76333D3A6C0BCCF6B279D9DDCA97 | SHA256:B96AF275B7091456D595B1565185849F53A808F71904B39CF60BAE7B16DE624B | |||
| 2848 | Tftpd32-4.64-setup.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Tftpd32\Tftpd32 Settings.lnk | binary | |
MD5:E36886E038AE6B7FF09C7403493FD99B | SHA256:9FD506E70601E8948BD13CAB1E08D8E07477E6A0A6137F2EDB89CF8024B406A0 | |||
| 2848 | Tftpd32-4.64-setup.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Tftpd32\Uninstall.lnk | binary | |
MD5:F79D2D6E7C87C3258A09B9024E82C604 | SHA256:B0AF69621B4A4CD141BA47F58A089B316CF4195ECE521809D0FB4F76BF338986 | |||
| 2848 | Tftpd32-4.64-setup.exe | C:\Program Files\Tftpd32\EUPL-EN.pdf | ||
MD5:254B5DDBC15269E72BA3A0508681A70C | SHA256:CD5D9E2A925D8DAA92D083FD8C1CEA48DF1BCFFFD857F4F93E2148FDDC5001EC | |||
| 2848 | Tftpd32-4.64-setup.exe | C:\Program Files\Tftpd32\tftpd32.ini | text | |
MD5:C973075D00B0BF2D5C4CB18155AD92FB | SHA256:0C00CBDAE4E3F2F430CA803E2E08BB3CBBA4E83CF9024DBB64DA212B8034E60D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
DNS requests
Threats
Process | Message |
|---|---|
tftpd32.exe | Th 2624 :opening comm socket
|
tftpd32.exe | Th 2624 :Console disconnected |
tftpd32.exe | Th 2328 :Port 17152 may be reused
|
tftpd32.exe | Th 1040 :connected to console
|
tftpd32.exe | Th 2624 :Verify Console/GUI parameters
|
tftpd32.exe | Th 2624 :Version check OK
|
tftpd32.exe | Th 1040 :GUI Version check OK
|
tftpd32.exe | Th 2624 :Console connected |
tftpd32.exe | Th 864 :Scheduler signal received |
tftpd32.exe | Th 1040 :GUI: new service 4 status 4
|