| File name: | Tftpd32-4.64-setup.exe |
| Full analysis: | https://app.any.run/tasks/acd55e2d-b42a-4f43-9dac-8c61954bc323 |
| Verdict: | Suspicious activity |
| Analysis date: | September 14, 2020, 13:43:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
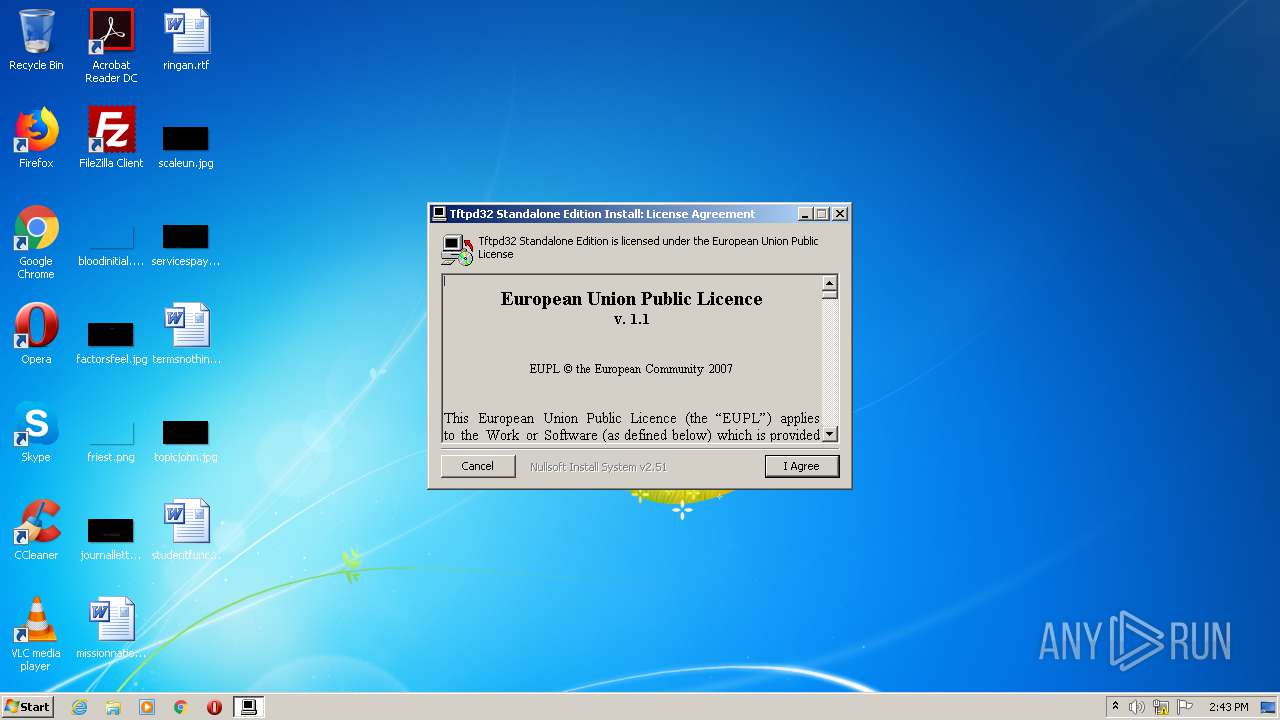
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 4A77C0A4701C751144D2D6161935F7F7 |
| SHA1: | 77D4D5E42D37C5389FC74BB0DFCF9D5B35A6DCE2 |
| SHA256: | 2DE0849E81686EF91AB4DFCA1C589247C7D8EDB937051B2DD3D4B9F16C8CB3FC |
| SSDEEP: | 12288:sJ+gA6RPCuLmMl06EpwUG5IAeKPOFwTM84qpcy+qtv2tSoTqLQby463:swgA6RPCUmMlQqIWWFA4qphN28o+LQeb |
MALICIOUS
No malicious indicators.SUSPICIOUS
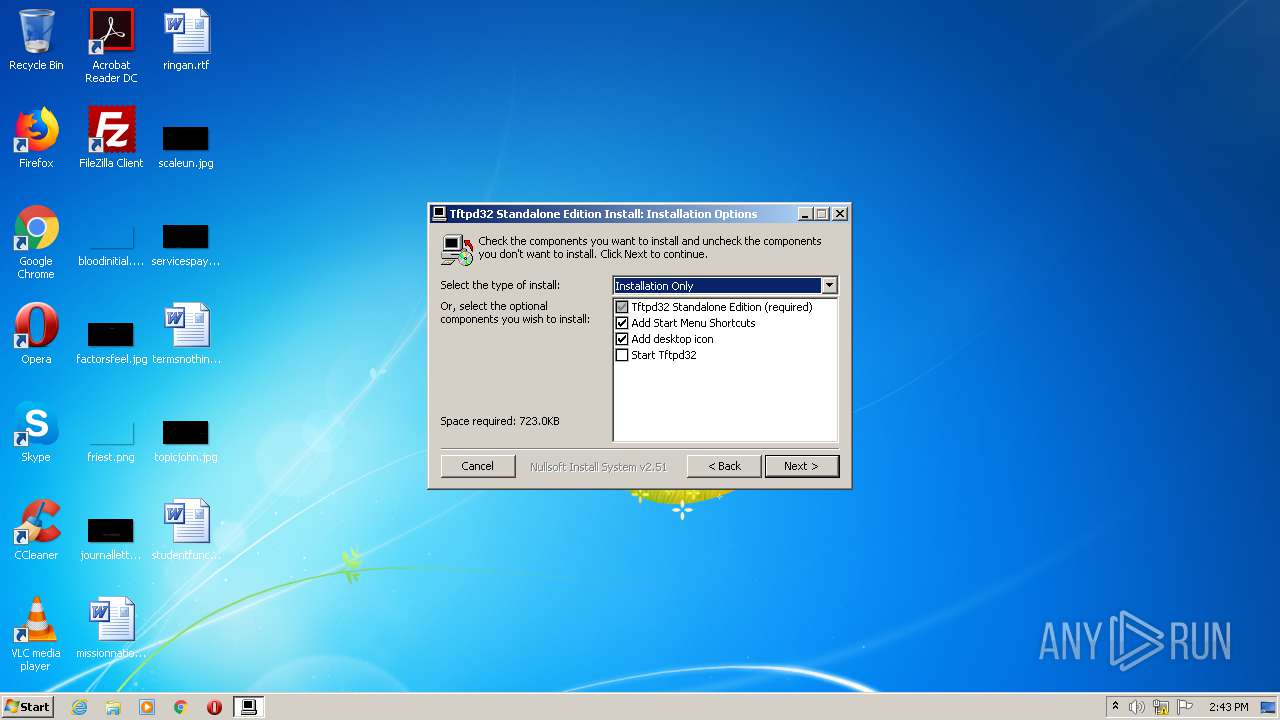
Creates files in the program directory
- Tftpd32-4.64-setup.exe (PID: 2552)
Creates a software uninstall entry
- Tftpd32-4.64-setup.exe (PID: 2552)
Creates files in the user directory
- Tftpd32-4.64-setup.exe (PID: 2552)
Executable content was dropped or overwritten
- Tftpd32-4.64-setup.exe (PID: 2552)
INFO
Dropped object may contain Bitcoin addresses
- Tftpd32-4.64-setup.exe (PID: 2552)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:04:02 05:20:13+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 24576 |
| InitializedDataSize: | 164864 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x312a |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 02-Apr-2016 03:20:13 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000C8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 02-Apr-2016 03:20:13 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005E66 | 0x00006000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.44066 |
.rdata | 0x00007000 | 0x000012A2 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.05833 |
.data | 0x00009000 | 0x00025D18 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.18773 |
.ndata | 0x0002F000 | 0x00008000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00037000 | 0x000013C8 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.28935 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.19285 | 727 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 2.76386 | 296 | UNKNOWN | English - United States | RT_ICON |
102 | 2.74309 | 184 | UNKNOWN | English - United States | RT_DIALOG |
103 | 1.97134 | 34 | UNKNOWN | English - United States | RT_GROUP_ICON |
104 | 2.6935 | 316 | UNKNOWN | English - United States | RT_DIALOG |
105 | 2.66174 | 256 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.89971 | 284 | UNKNOWN | English - United States | RT_DIALOG |
107 | 2.62276 | 196 | UNKNOWN | English - United States | RT_DIALOG |
110 | 3.22336 | 872 | UNKNOWN | English - United States | RT_BITMAP |
111 | 2.48825 | 96 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
42
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2552 | "C:\Users\admin\AppData\Local\Temp\Tftpd32-4.64-setup.exe" | C:\Users\admin\AppData\Local\Temp\Tftpd32-4.64-setup.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3992 | "C:\Users\admin\AppData\Local\Temp\Tftpd32-4.64-setup.exe" | C:\Users\admin\AppData\Local\Temp\Tftpd32-4.64-setup.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
Total events
383
Read events
378
Write events
5
Delete events
0
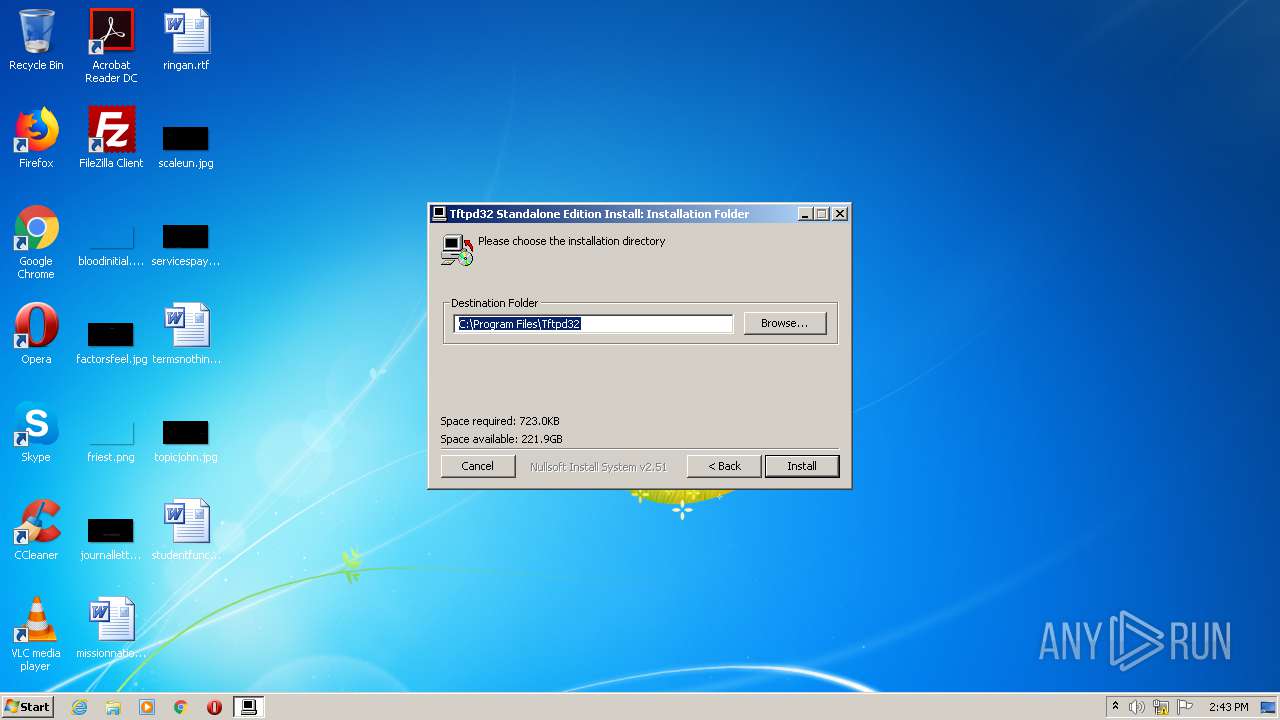
Modification events
| (PID) Process: | (2552) Tftpd32-4.64-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Tftpd32 |
| Operation: | write | Name: | Install_Dir |
Value: C:\Program Files\Tftpd32 | |||
| (PID) Process: | (2552) Tftpd32-4.64-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Tftpd32 |
| Operation: | write | Name: | DisplayName |
Value: Tftpd32 Standalone Edition (remove only) | |||
| (PID) Process: | (2552) Tftpd32-4.64-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Tftpd32 |
| Operation: | write | Name: | UninstallString |
Value: "C:\Program Files\Tftpd32\uninstall.exe" | |||
| (PID) Process: | (2552) Tftpd32-4.64-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Tftpd32 |
| Operation: | write | Name: | NoModify |
Value: 1 | |||
| (PID) Process: | (2552) Tftpd32-4.64-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Tftpd32 |
| Operation: | write | Name: | NoRepair |
Value: 1 | |||
Executable files
2
Suspicious files
1
Text files
1
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2552 | Tftpd32-4.64-setup.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Tftpd32\Tftpd32 Settings.lnk | lnk | |
MD5:— | SHA256:— | |||
| 2552 | Tftpd32-4.64-setup.exe | C:\Users\admin\Desktop\Tftpd32.lnk | lnk | |
MD5:— | SHA256:— | |||
| 2552 | Tftpd32-4.64-setup.exe | C:\Program Files\Tftpd32\tftpd32.exe | executable | |
MD5:733ED472EDBBA6FCCFF0A74882CD6B51 | SHA256:C270EBD42AC19805F58BDA8A0A34898ADD80CDAFF3594038C3C9B47FDB0FA06A | |||
| 2552 | Tftpd32-4.64-setup.exe | C:\Program Files\Tftpd32\EUPL-EN.pdf | ||
MD5:254B5DDBC15269E72BA3A0508681A70C | SHA256:CD5D9E2A925D8DAA92D083FD8C1CEA48DF1BCFFFD857F4F93E2148FDDC5001EC | |||
| 2552 | Tftpd32-4.64-setup.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Tftpd32\Tftpd32.lnk | lnk | |
MD5:— | SHA256:— | |||
| 2552 | Tftpd32-4.64-setup.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Tftpd32\Uninstall.lnk | lnk | |
MD5:— | SHA256:— | |||
| 2552 | Tftpd32-4.64-setup.exe | C:\Program Files\Tftpd32\uninstall.exe | executable | |
MD5:81982BE80DEC4E8462EF03FD5E44F406 | SHA256:181A386BA1B874C4F2779A27181332374F640A89333C88E70309B829324DB07C | |||
| 2552 | Tftpd32-4.64-setup.exe | C:\Program Files\Tftpd32\tftpd32.ini | text | |
MD5:C973075D00B0BF2D5C4CB18155AD92FB | SHA256:0C00CBDAE4E3F2F430CA803E2E08BB3CBBA4E83CF9024DBB64DA212B8034E60D | |||
| 2552 | Tftpd32-4.64-setup.exe | C:\Program Files\Tftpd32\tftpd32.chm | chm | |
MD5:DE0095E371874836FB50CD3400D7B204 | SHA256:810A0F52703D051B30D5ECD219C72B0599964DE34D1C1912367271C87D4725BF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report