| File name: | AdobeGenP.exe |
| Full analysis: | https://app.any.run/tasks/991285dd-95de-492f-8fc6-65092e26f60a |
| Verdict: | Malicious activity |
| Analysis date: | December 27, 2024, 10:34:11 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 6 sections |
| MD5: | 94545CF2AF5429D6F72A46B18A0396C8 |
| SHA1: | 87980448560025CB09414F4BE36CCD4780D6EB58 |
| SHA256: | 2DD8C1AD0863BE3E76DC5F1E412C951F7DD06888EDEE97119732621BB059CCEC |
| SSDEEP: | 49152:YE/XUraxm5O9QMal0QRO8tnp/QsWVocOW1:Y9rem5Oid7Rj9G1 |
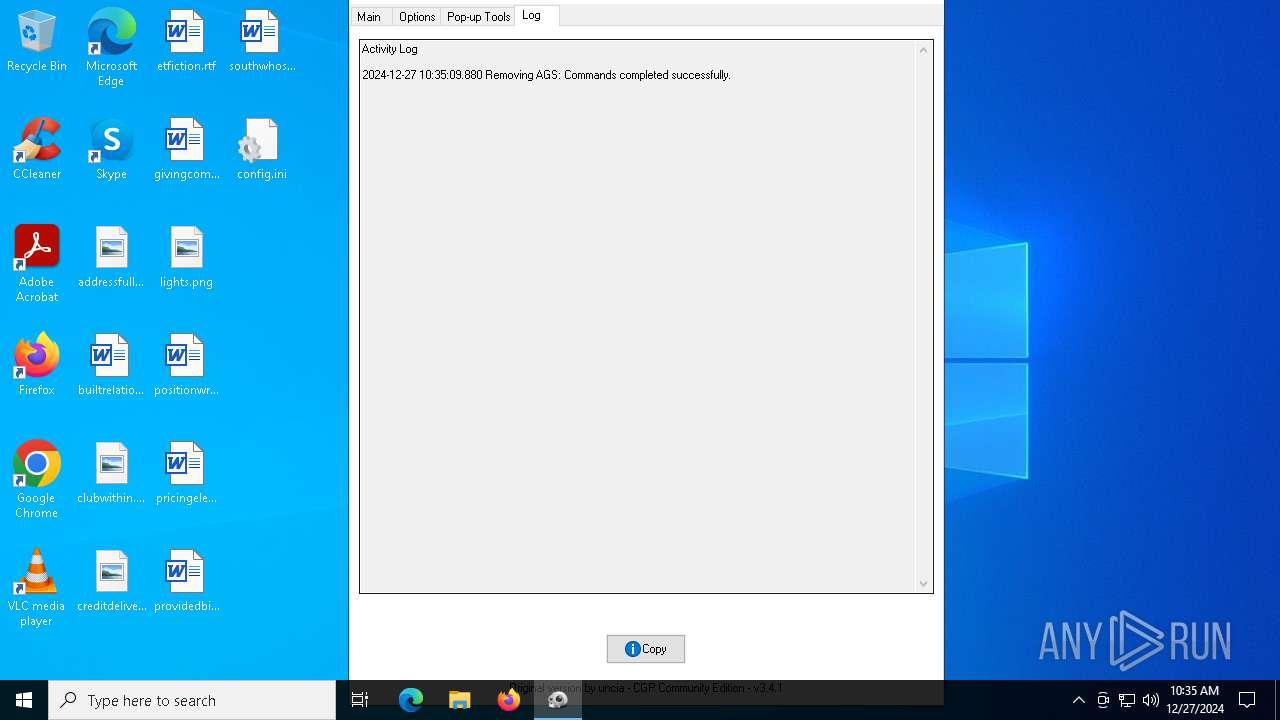
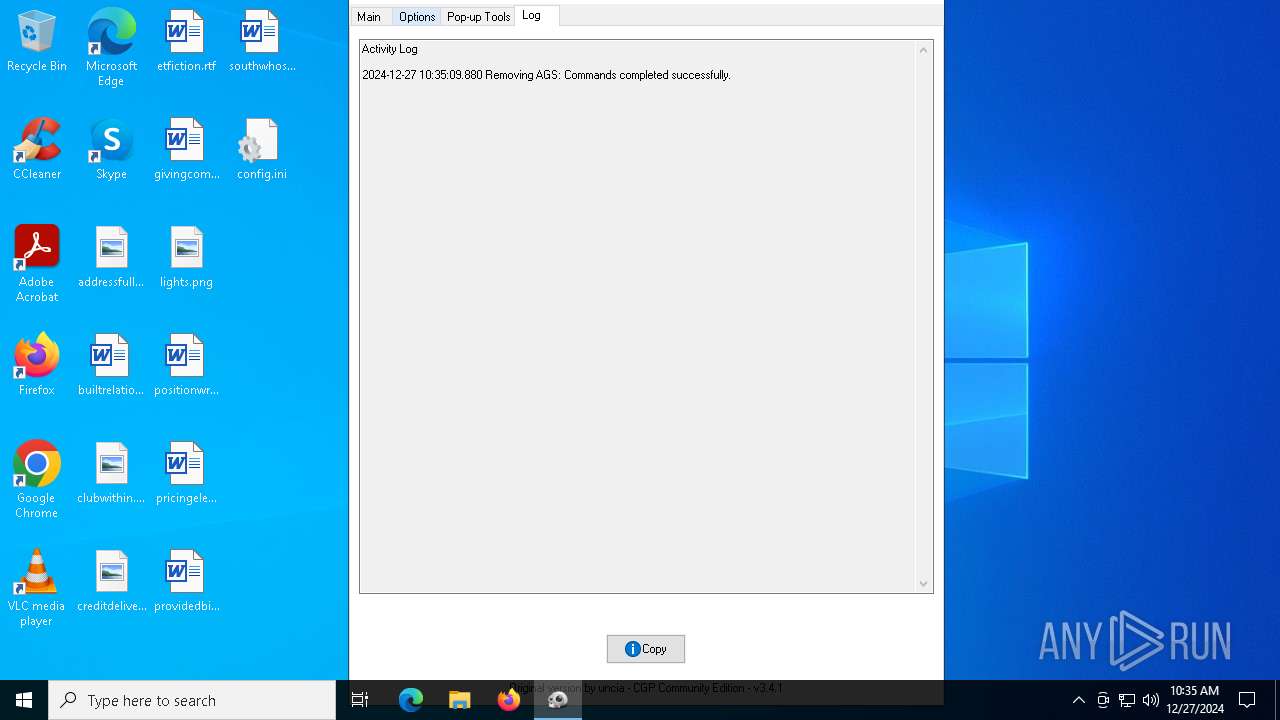
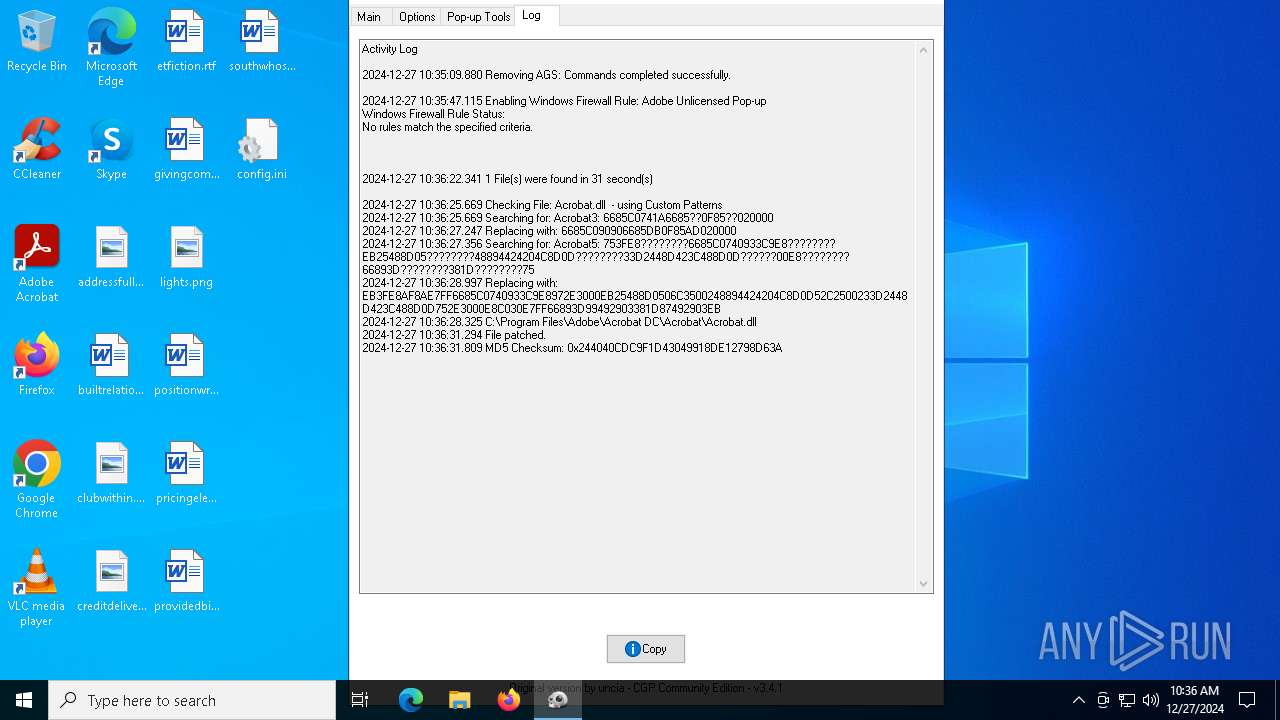
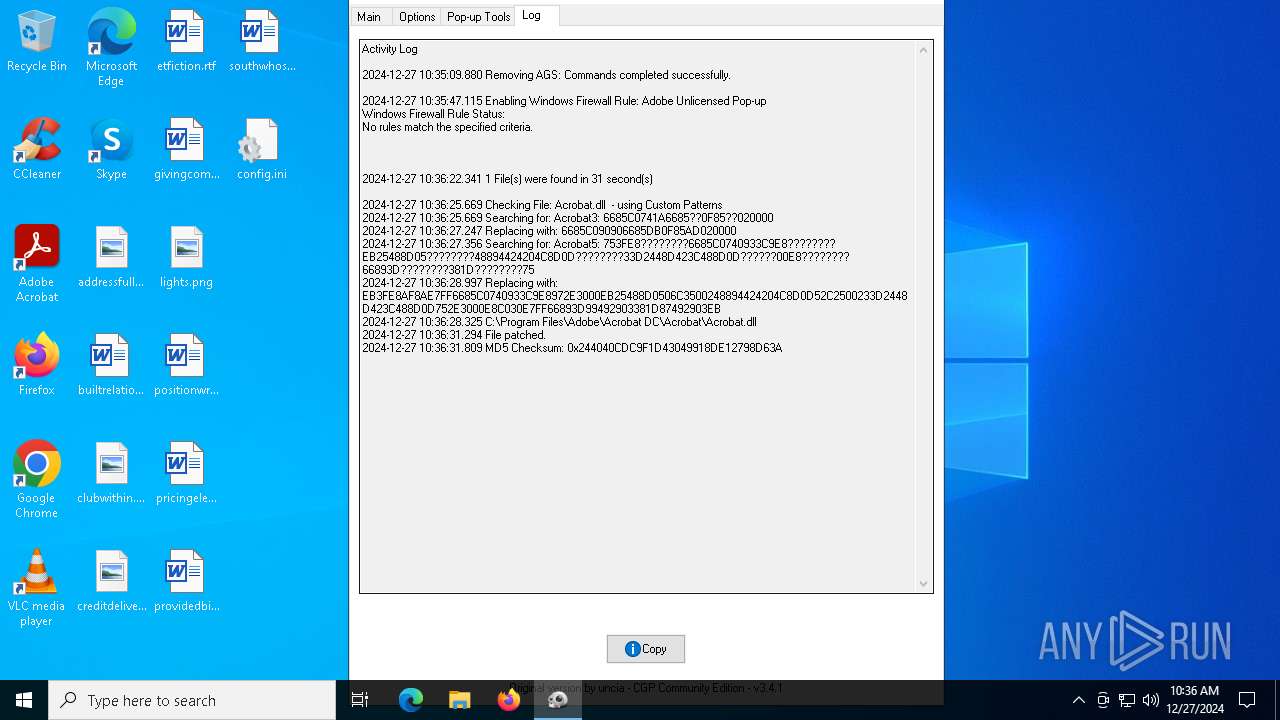
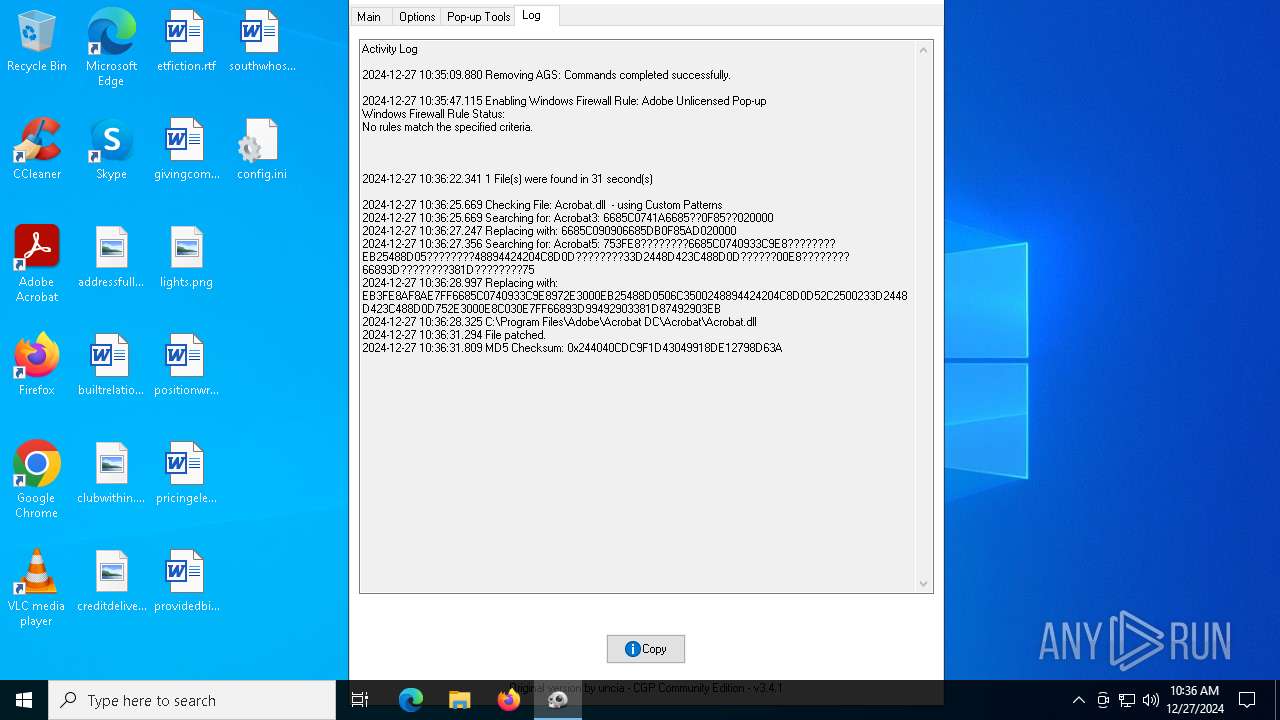
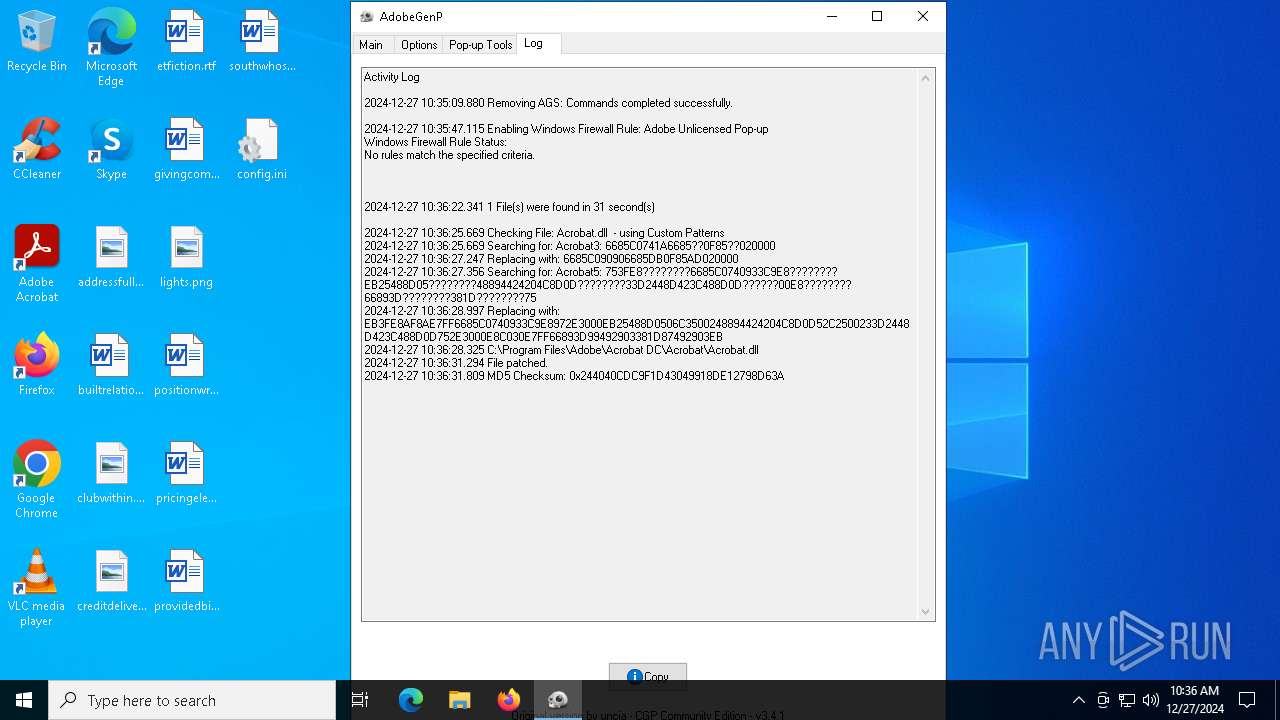
MALICIOUS
Executing a file with an untrusted certificate
- RunAsTI.exe (PID: 6948)
Changes powershell execution policy (Bypass)
- AdobeGenP.exe (PID: 7060)
Bypass execution policy to execute commands
- powershell.exe (PID: 3080)
- powershell.exe (PID: 1544)
SUSPICIOUS
Application launched itself
- RunAsTI.exe (PID: 6948)
Executable content was dropped or overwritten
- AdobeGenP.exe (PID: 6420)
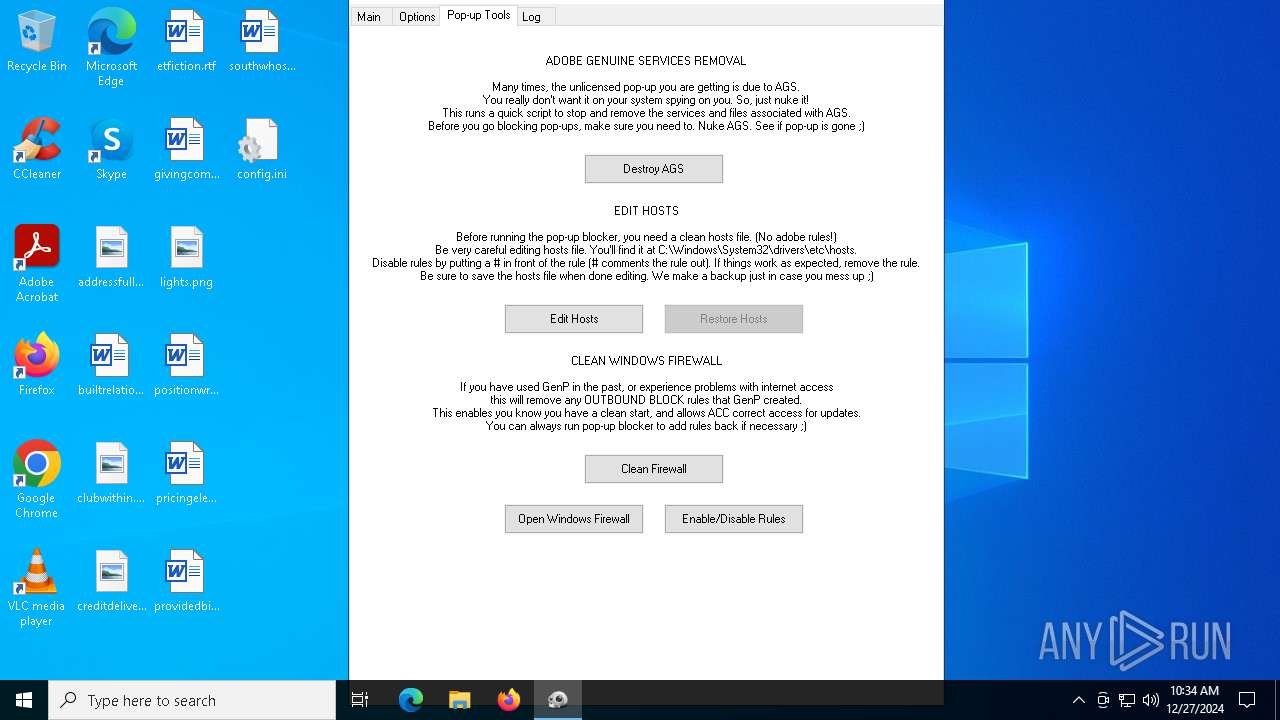
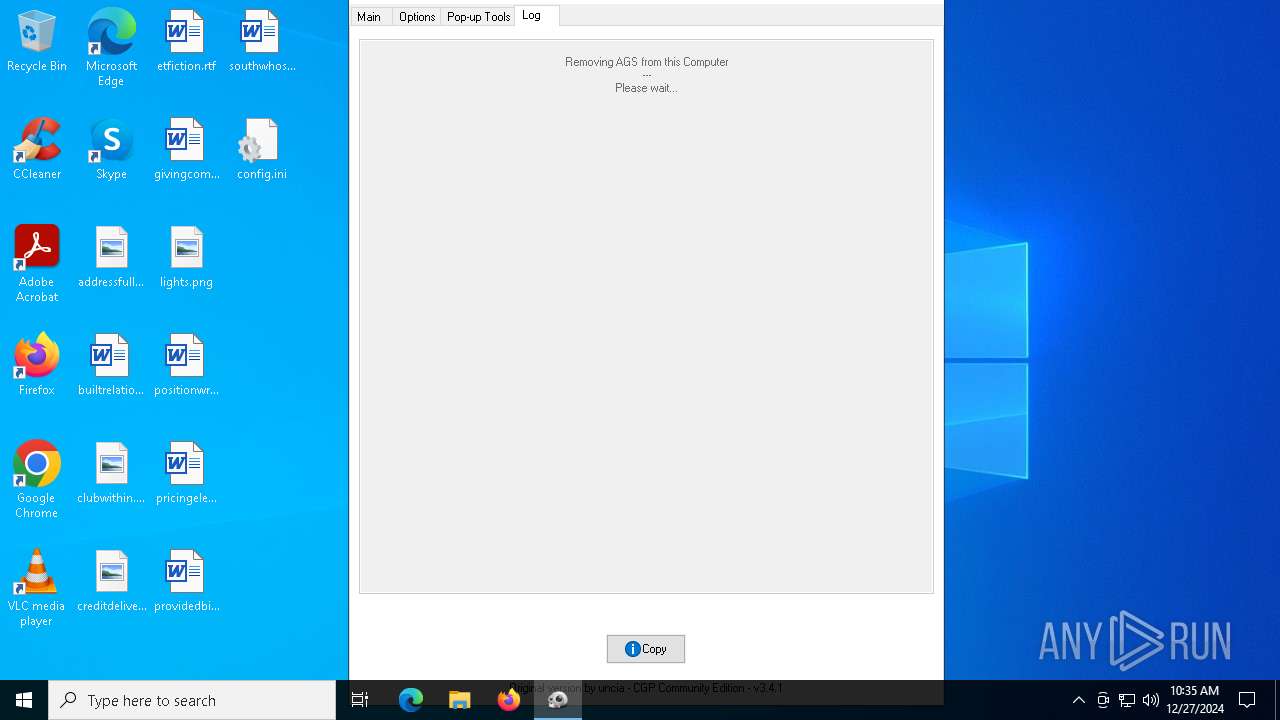
Removes files via Powershell
- powershell.exe (PID: 1544)
Likely accesses (executes) a file from the Public directory
- powershell.exe (PID: 1544)
Starts POWERSHELL.EXE for commands execution
- AdobeGenP.exe (PID: 7060)
Kill processes via PowerShell
- powershell.exe (PID: 1544)
Hides errors and continues executing the command without stopping
- powershell.exe (PID: 1544)
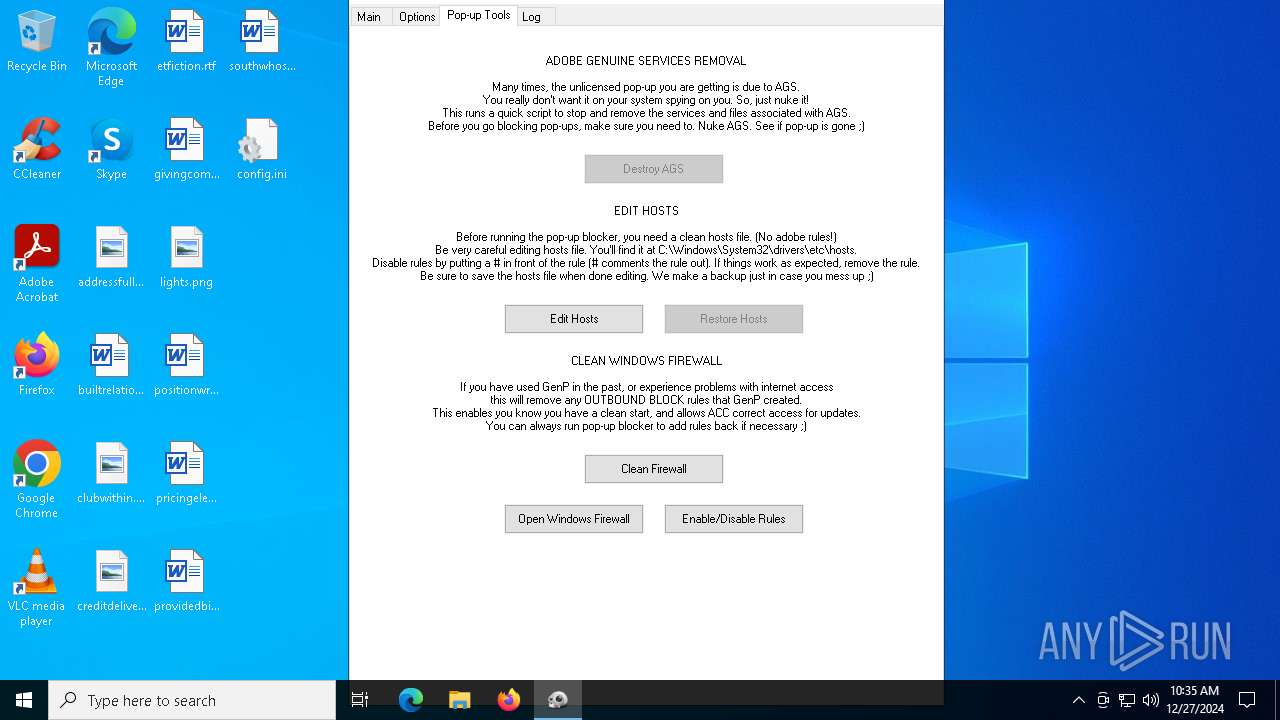
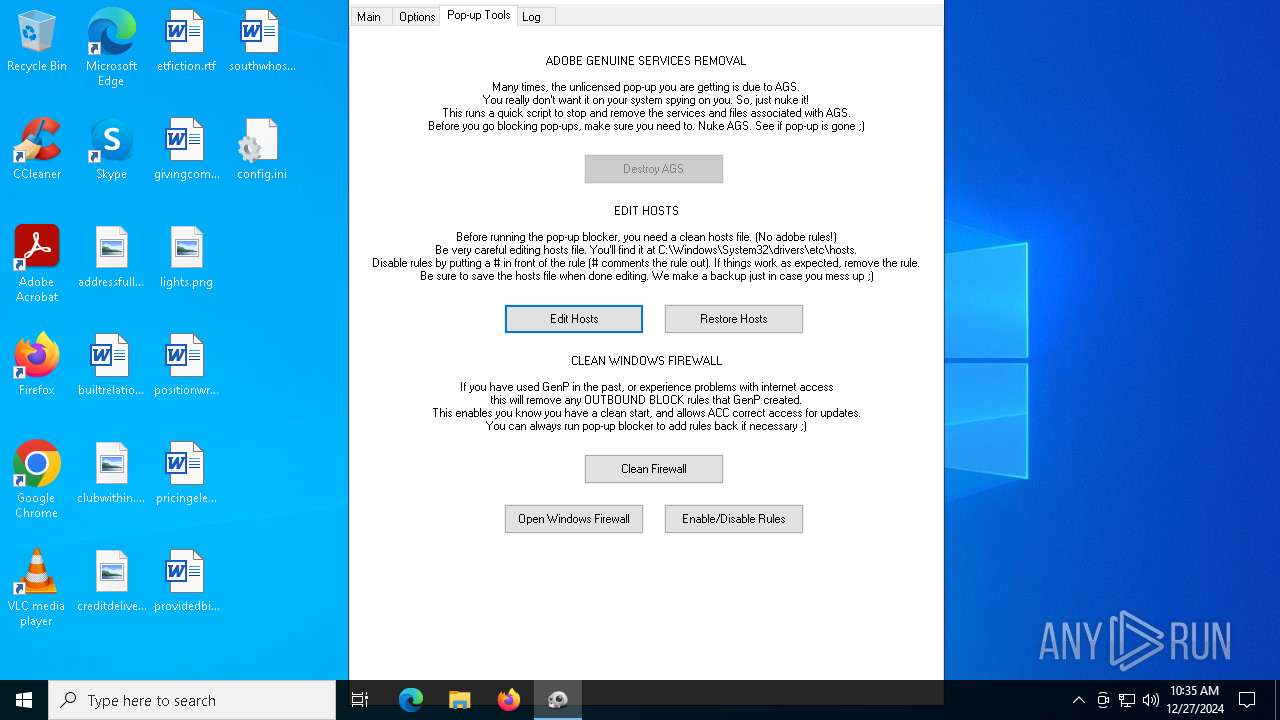
Start notepad (likely ransomware note)
- AdobeGenP.exe (PID: 7060)
Windows service management via SC.EXE
- sc.exe (PID: 6012)
- sc.exe (PID: 5096)
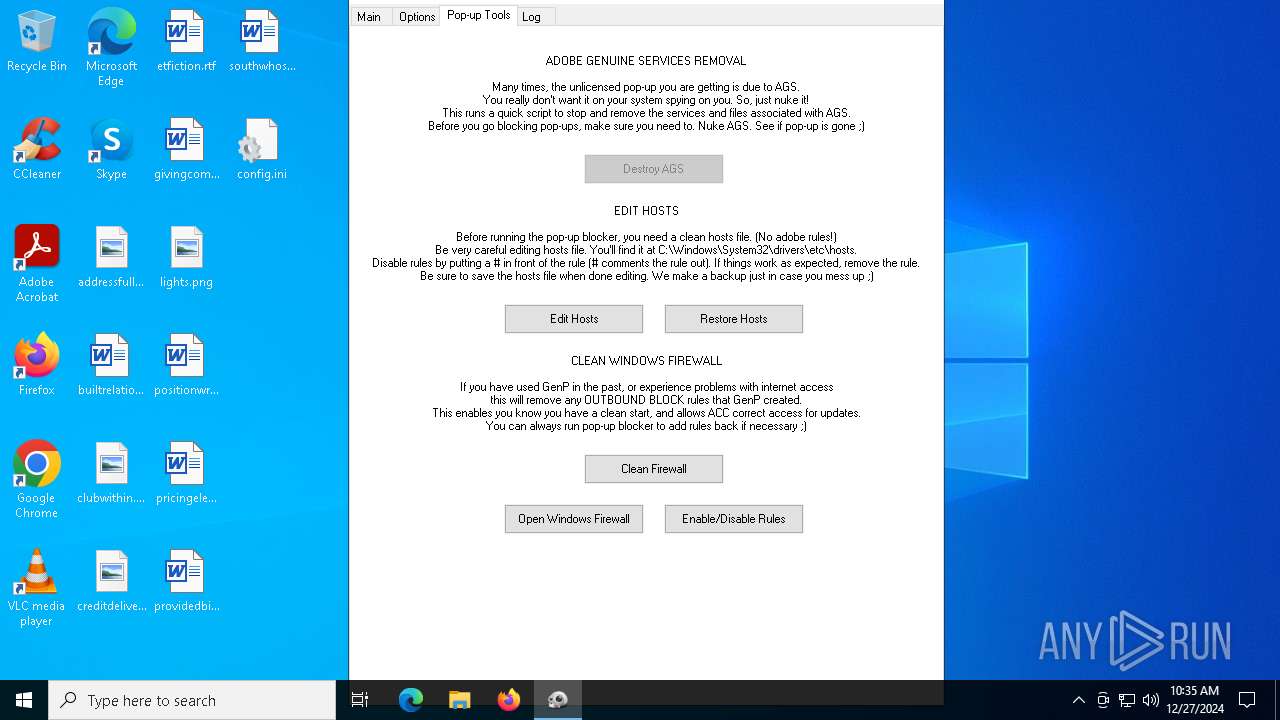
Uses NETSH.EXE to change the status of the firewall
- AdobeGenP.exe (PID: 7060)
Base64-obfuscated command line is found
- AdobeGenP.exe (PID: 7060)
Starts SC.EXE for service management
- powershell.exe (PID: 1544)
INFO
The sample compiled with english language support
- AdobeGenP.exe (PID: 6420)
Checks supported languages
- AdobeGenP.exe (PID: 6420)
- RunAsTI.exe (PID: 7008)
- RunAsTI.exe (PID: 6948)
- AdobeGenP.exe (PID: 7060)
Reads the computer name
- AdobeGenP.exe (PID: 6420)
- RunAsTI.exe (PID: 6948)
- RunAsTI.exe (PID: 7008)
- AdobeGenP.exe (PID: 7060)
Reads mouse settings
- AdobeGenP.exe (PID: 6420)
- AdobeGenP.exe (PID: 7060)
Create files in a temporary directory
- AdobeGenP.exe (PID: 6420)
The process uses AutoIt
- AdobeGenP.exe (PID: 6420)
The process uses the downloaded file
- powershell.exe (PID: 1544)
- powershell.exe (PID: 3080)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 1544)
- powershell.exe (PID: 3080)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 3080)
Reads the machine GUID from the registry
- AdobeGenP.exe (PID: 7060)
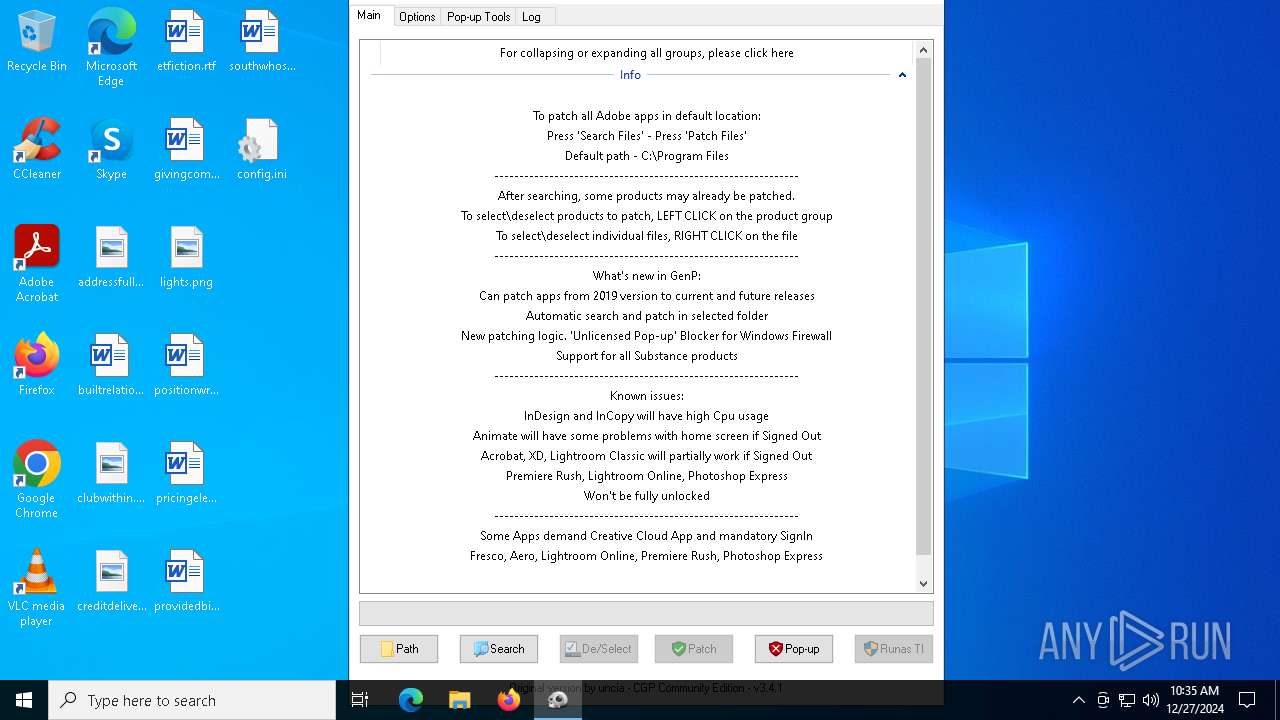
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2024:09:08 19:01:06+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.16 |
| CodeSize: | 734208 |
| InitializedDataSize: | 551936 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2549c |
| OSVersion: | 5.2 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.3.16.1 |
| ProductVersionNumber: | 3.3.16.1 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | English (British) |
| CharacterSet: | Unicode |
| FileVersion: | 3.3.16.1 |
| Comments: | AdobeGenP |
| FileDescription: | AdobeGenP |
| ProductName: | AdobeGenP |
| ProductVersion: | 3.3.16.1 |
| CompanyName: | AdobeGenP |
| LegalCopyright: | AdobeGenP |
| LegalTradeMarks: | AdobeGenP |
Total processes
142
Monitored processes
14
Malicious processes
4
Suspicious processes
1
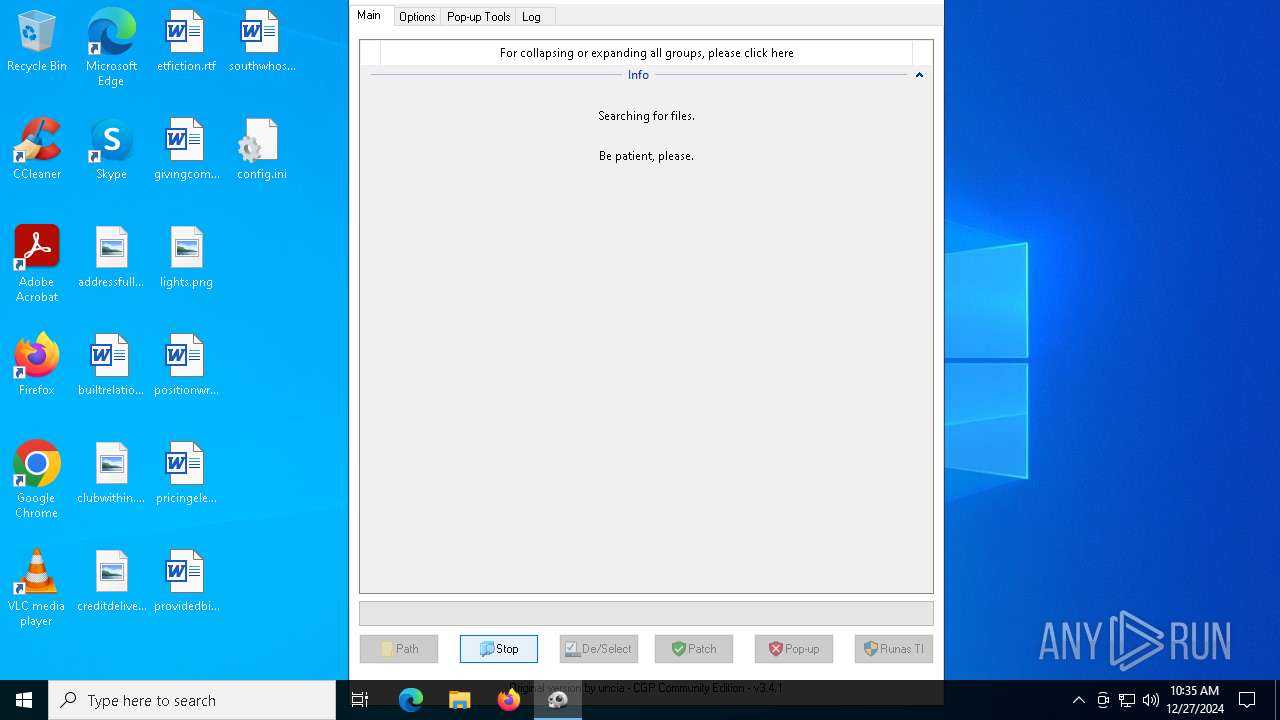
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
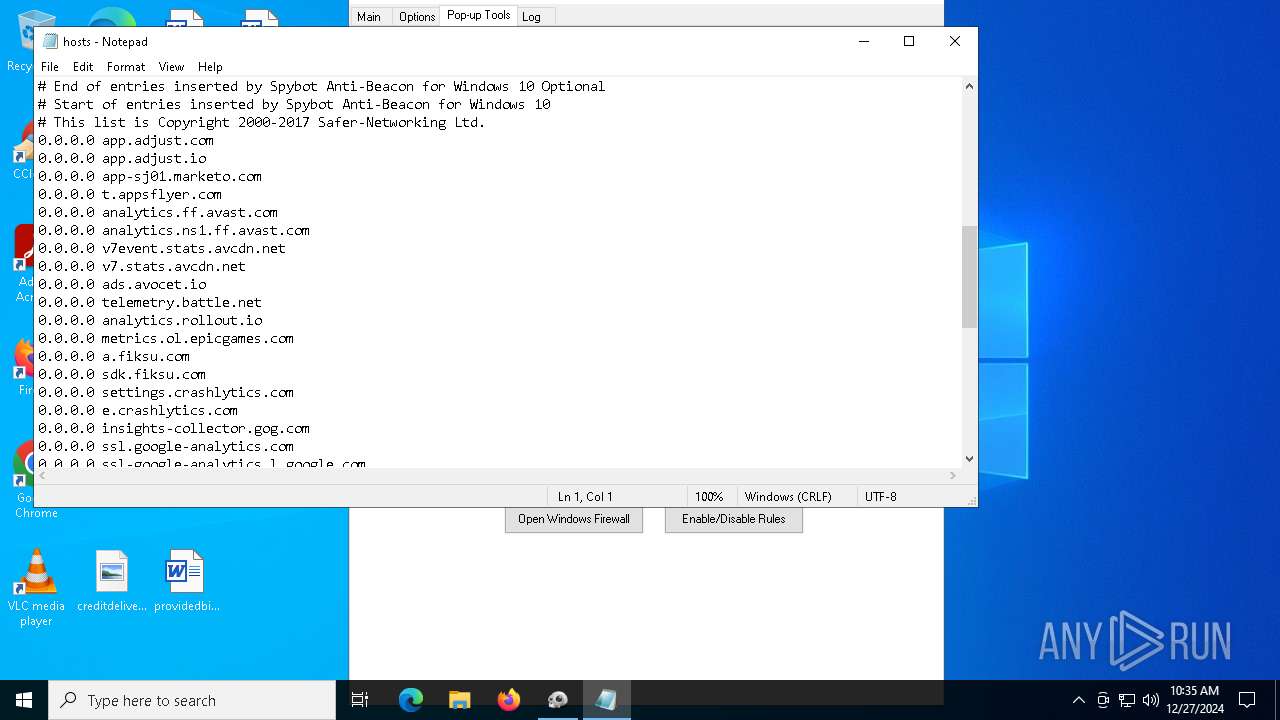
| 1544 | PowerShell Set-ExecutionPolicy Bypass -scope Process -Force;Stop-Process -Name "AGMService" -Force -ErrorAction SilentlyContinue;Stop-Process -Name "AGSService" -Force -ErrorAction SilentlyContinue;Remove-Item -Path "C:\Program Files (x86)\Common Files\Adobe\AdobeGCClient" -Recurse -Force -ErrorAction SilentlyContinue;Remove-Item -Path "C:\Program Files (x86)\Common Files\Adobe\OOBE\PDApp\AdobeGCClient" -Recurse -Force -ErrorAction SilentlyContinue;sc.exe delete "AGMService";sc.exe delete "AGSService";Remove-Item -Path "C:\Users\Public\Documents\AdobeGCData" -Recurse -Force -ErrorAction SilentlyContinue;Remove-Item -Path "C:\Windows\System32\Tasks\AdobeGCInvoker-1.0" -Force -ErrorAction SilentlyContinue;Remove-Item -Path "C:\Windows\System32\Tasks_Migrated\AdobeGCInvoker-1.0" -Force -ErrorAction SilentlyContinue;Remove-Item -Path "C:\Program Files (x86)\Adobe\Adobe Creative Cloud\Utils\AdobeGenuineValidator.exe" -Force -ErrorAction SilentlyContinue;Remove-Item -Path "C:\Windows\Temp\adobegc.log" -Force -ErrorAction SilentlyContinue;Remove-Item -Path "C:\Users\maxfa\AppData\Local\Temp\adobegc.log" -Force -ErrorAction SilentlyContinue; | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | AdobeGenP.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2072 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3080 | PowerShell Set-ExecutionPolicy Bypass -scope Process -Force;try{$name = (Get-NetFirewallRule -DisplayName 'Adobe Unlicensed Pop-up').Name} catch{$name='no'};If($name -ne 'no'){(Get-NetFirewallRule -Name $name).Enabled}; | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | AdobeGenP.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
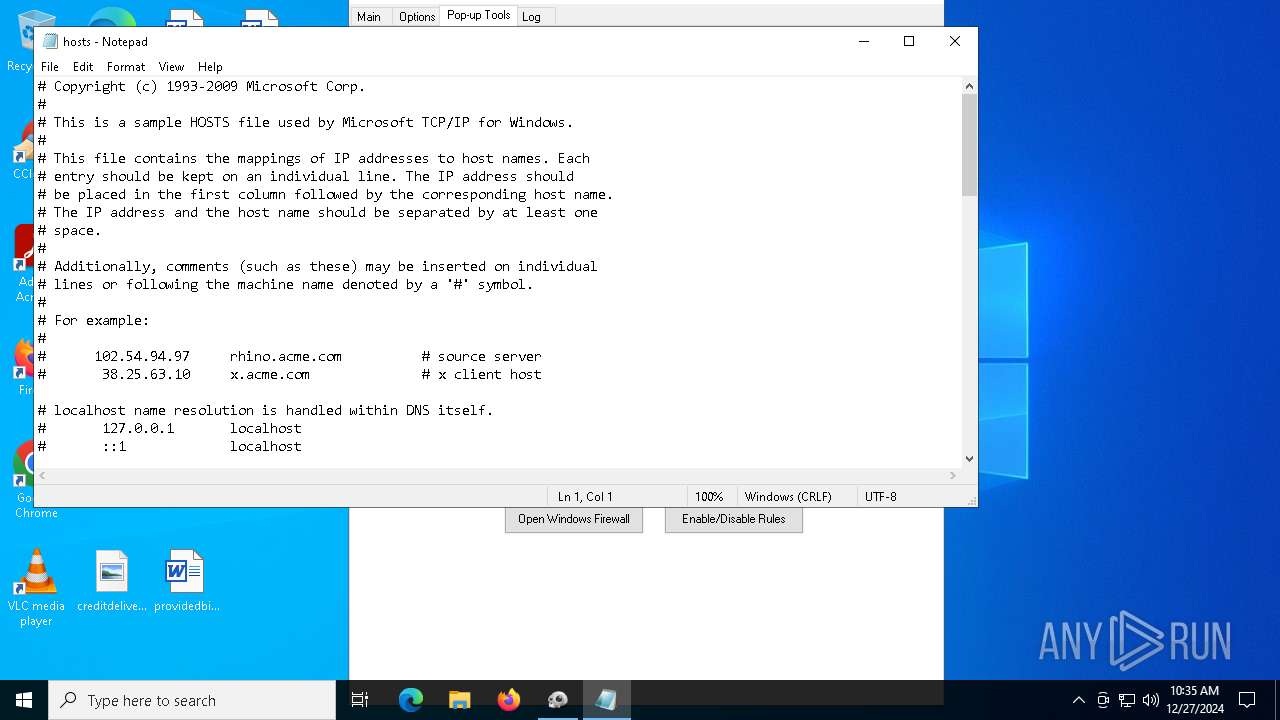
| 5040 | notepad.exe C:\Windows\System32\drivers\etc\hosts | C:\Windows\System32\notepad.exe | — | AdobeGenP.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Notepad Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5096 | "C:\WINDOWS\system32\sc.exe" delete AGSService | C:\Windows\System32\sc.exe | — | powershell.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Service Control Manager Configuration Tool Exit code: 1060 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6012 | "C:\WINDOWS\system32\sc.exe" delete AGMService | C:\Windows\System32\sc.exe | — | powershell.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Service Control Manager Configuration Tool Exit code: 1060 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6312 | "C:\Users\admin\Desktop\AdobeGenP.exe" | C:\Users\admin\Desktop\AdobeGenP.exe | — | explorer.exe | |||||||||||
User: admin Company: AdobeGenP Integrity Level: MEDIUM Description: AdobeGenP Exit code: 3221226540 Version: 3.3.16.1 Modules
| |||||||||||||||
| 6420 | "C:\Users\admin\Desktop\AdobeGenP.exe" | C:\Users\admin\Desktop\AdobeGenP.exe | explorer.exe | ||||||||||||
User: admin Company: AdobeGenP Integrity Level: HIGH Description: AdobeGenP Exit code: 6948 Version: 3.3.16.1 Modules
| |||||||||||||||
| 6484 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6616 | netsh advfirewall firewall set rule name="Adobe Unlicensed Pop-up" new enable=yes | C:\Windows\System32\netsh.exe | — | AdobeGenP.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Network Command Shell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
12 455
Read events
12 446
Write events
9
Delete events
0
Modification events
| (PID) Process: | (5040) notepad.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Notepad |
| Operation: | write | Name: | fWindowsOnlyEOL |
Value: 0 | |||
| (PID) Process: | (5040) notepad.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Notepad |
| Operation: | write | Name: | fPasteOriginalEOL |
Value: 0 | |||
| (PID) Process: | (5040) notepad.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Notepad |
| Operation: | write | Name: | fReverse |
Value: 0 | |||
| (PID) Process: | (5040) notepad.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Notepad |
| Operation: | write | Name: | fWrapAround |
Value: 0 | |||
| (PID) Process: | (5040) notepad.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Notepad |
| Operation: | write | Name: | fMatchCase |
Value: 0 | |||
| (PID) Process: | (5040) notepad.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosX |
Value: 26 | |||
| (PID) Process: | (5040) notepad.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosY |
Value: 26 | |||
| (PID) Process: | (5040) notepad.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosDX |
Value: 960 | |||
| (PID) Process: | (5040) notepad.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosDY |
Value: 489 | |||
Executable files
2
Suspicious files
3
Text files
11
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
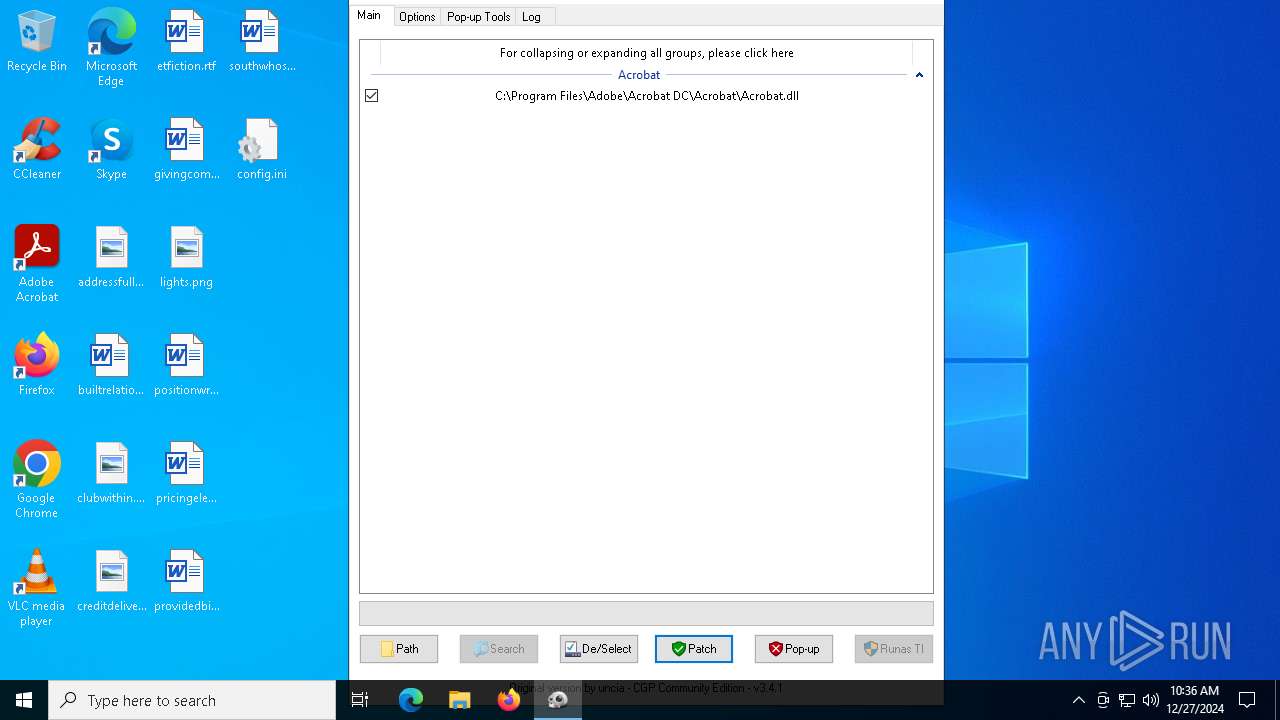
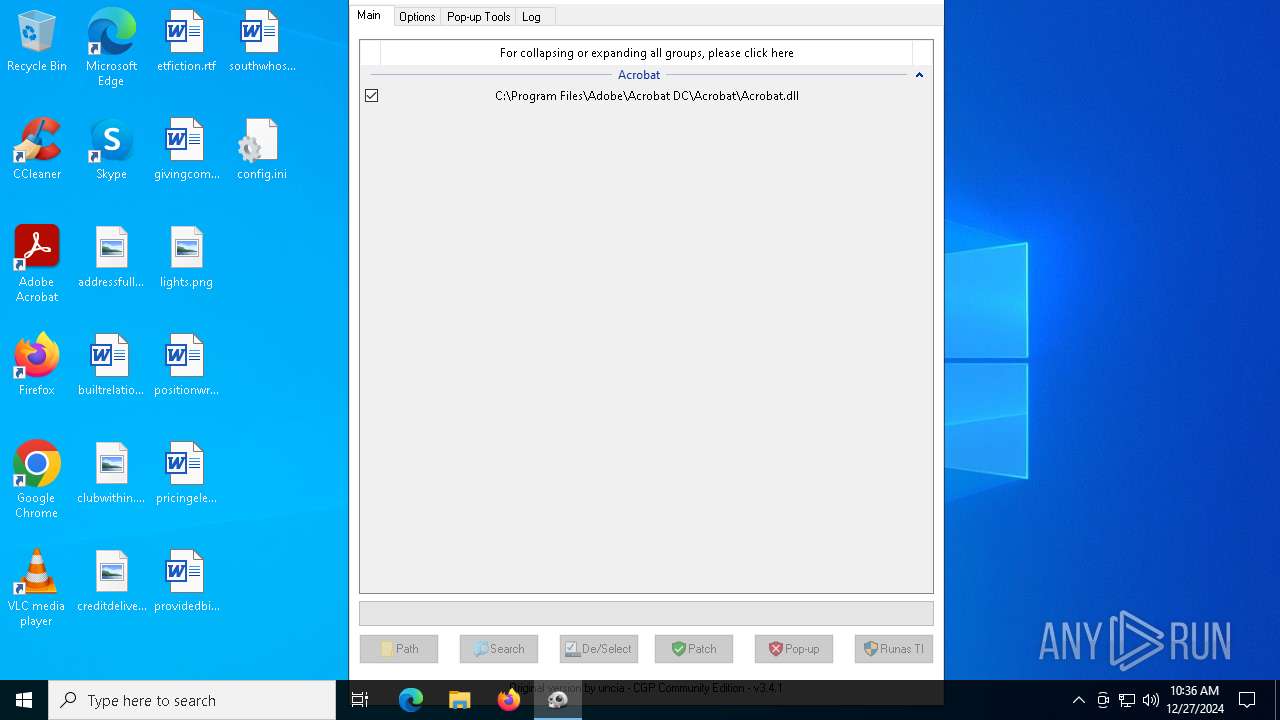
| 7060 | AdobeGenP.exe | C:\Program Files\Adobe\Acrobat DC\Acrobat\Acrobat.dll.bak | — | |
MD5:— | SHA256:— | |||
| 7060 | AdobeGenP.exe | C:\Program Files\Adobe\Acrobat DC\Acrobat\Acrobat.dll | — | |
MD5:— | SHA256:— | |||
| 6420 | AdobeGenP.exe | C:\Users\admin\AppData\Local\Temp\aut5A48.tmp | binary | |
MD5:C4702D8BC7278DAA3537B3F8A6BB3E0E | SHA256:17F942B988079D244CEC130FDF490C8FEEABA93C564DC0489BAE4991FF14EBE0 | |||
| 1544 | powershell.exe | C:\Windows\Temp\__PSScriptPolicyTest_ijehx4dt.rc4.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6420 | AdobeGenP.exe | C:\Windows\Temp\RunAsTI.exe | executable | |
MD5:80454E70784F1DDB0C91D41469E2498D | SHA256:A3E0BA70BA908DE8A75825C3A1FF36147E02C686280993C2CAA8A9A6968764B0 | |||
| 1544 | powershell.exe | C:\Windows\Temp\__PSScriptPolicyTest_1zg2muuy.1g1.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1544 | powershell.exe | C:\Windows\Temp\__PSScriptPolicyTest_jxbfzsd2.ang.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6420 | AdobeGenP.exe | C:\Users\admin\AppData\Local\Temp\autA1D2.tmp | binary | |
MD5:8AC5BF66322F28F9C31C15651735B825 | SHA256:2AB6CA4CD53C0E97AFAD7080FA07D30E49310502B66CBF8D7DD3E43F9084E8E6 | |||
| 7060 | AdobeGenP.exe | C:\Windows\System32\drivers\etc\hosts.bak | text | |
MD5:C40F0E533A52F202035621D27E732F5A | SHA256:408442168118E82FAF7D419AA4F0D8FA04F45A5E6D0E7065A9CDC723782C5AE3 | |||
| 3080 | powershell.exe | C:\Windows\Temp\__PSScriptPolicyTest_iukt4ksc.qoc.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
32
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2380 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
5300 | SIHClient.exe | GET | 200 | 23.37.237.227:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5300 | SIHClient.exe | GET | 200 | 23.37.237.227:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3220 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.16.164.49:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
5064 | SearchApp.exe | 2.23.209.131:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
4712 | MoUsoCoreWorker.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1176 | svchost.exe | 40.126.31.67:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1176 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| unknown |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |