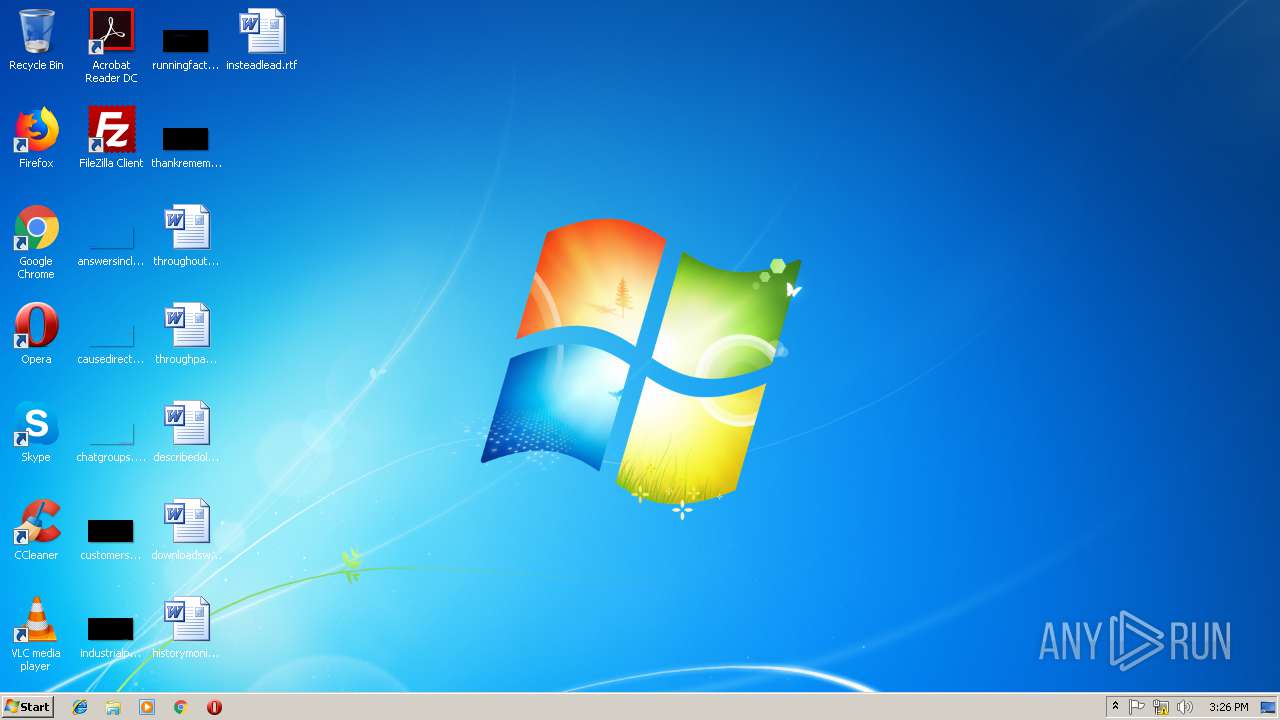
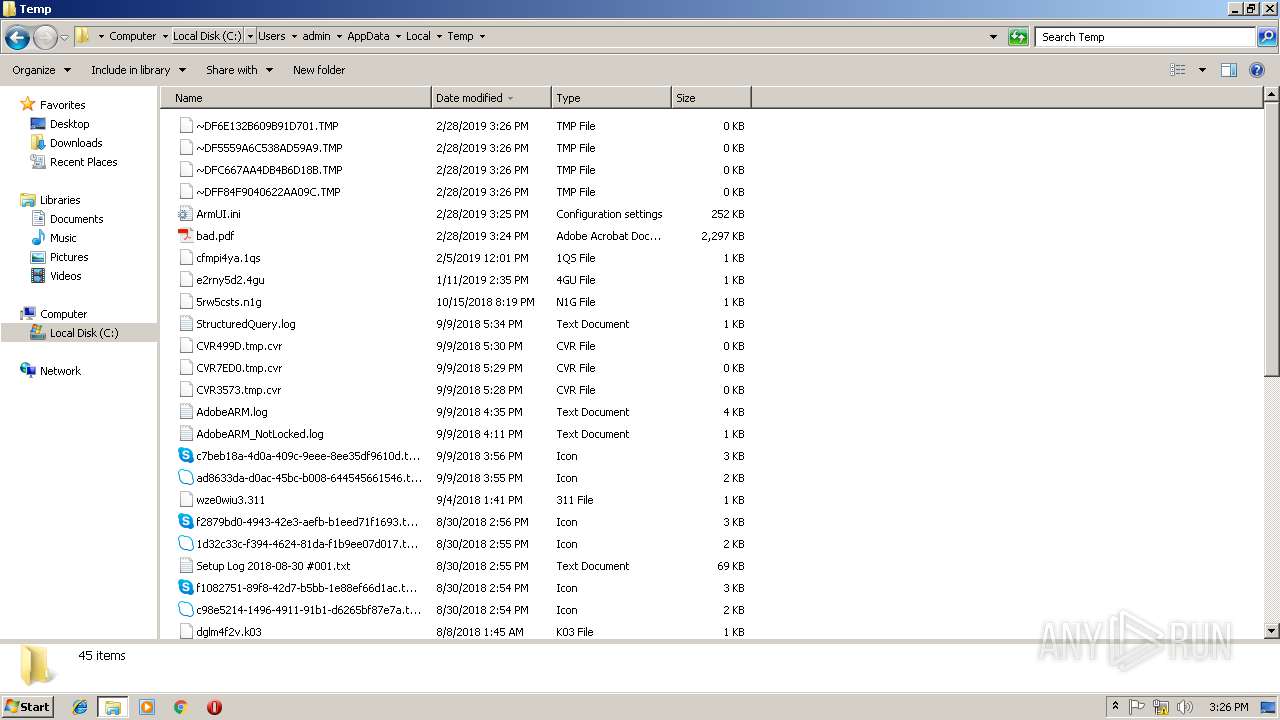
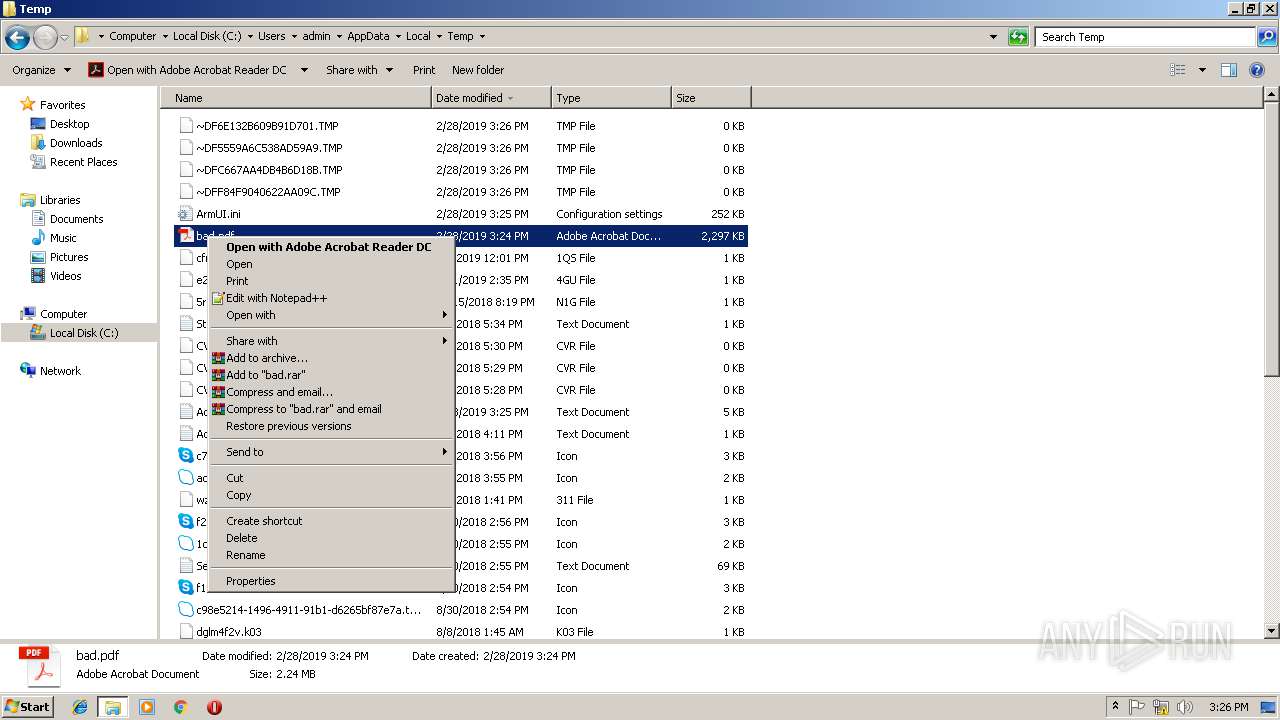
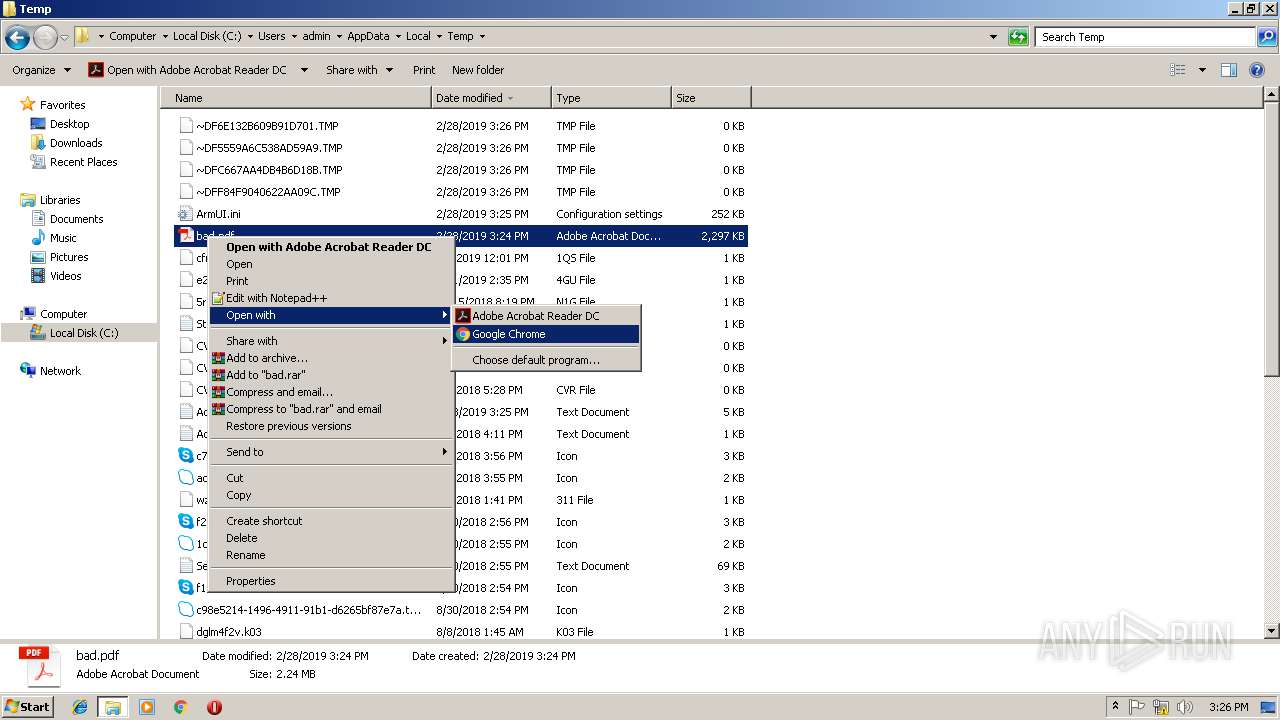
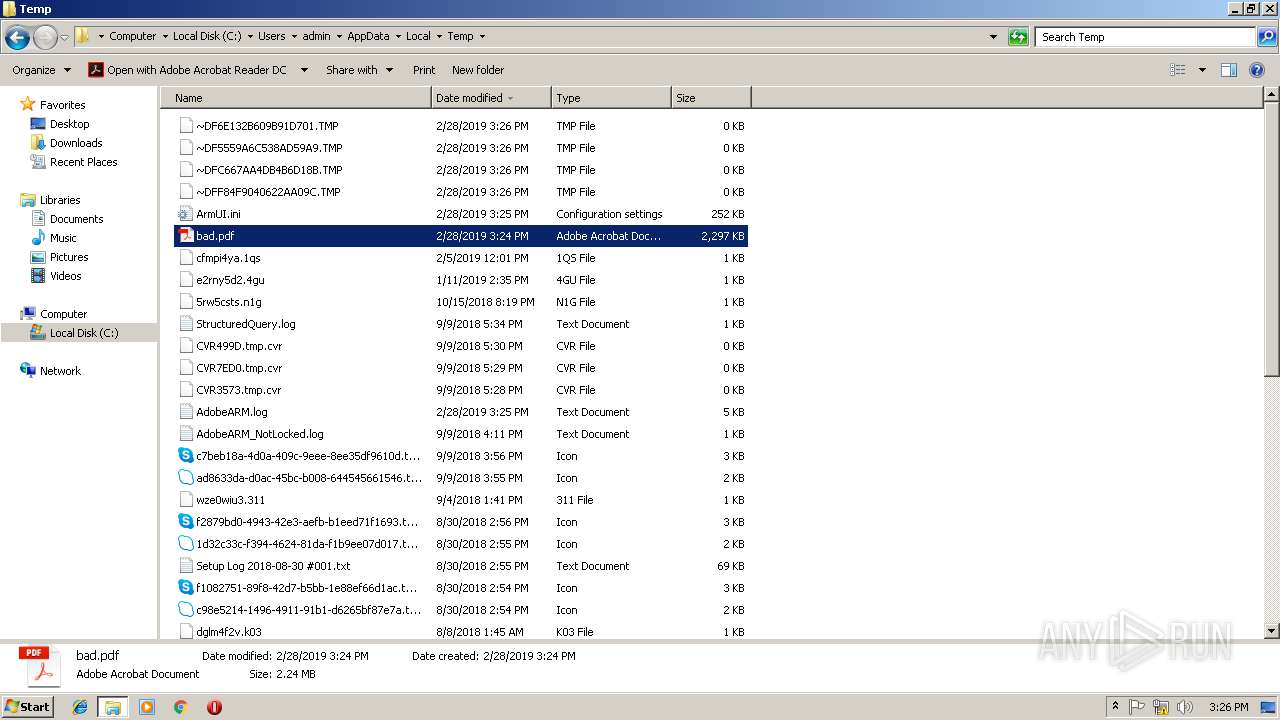
| File name: | bad.pdf |
| Full analysis: | https://app.any.run/tasks/dd11f554-3dae-4efd-8f48-a2b1b0791025 |
| Verdict: | No threats detected |
| Analysis date: | February 28, 2019, 15:24:36 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/pdf |
| File info: | PDF document, version 1.4 |
| MD5: | 13090C4E8338FA2769A29356DE72B306 |
| SHA1: | 38A063BC252E5DA687CA176C79D2A7CDD0F369A9 |
| SHA256: | 2DD6ADE4D0D4DC8224B28F8819B1C49BB7AE4025933E737AC8069C496D88BB43 |
| SSDEEP: | 49152:bQZxoPxZ+9iVCZ3At3T0GN75rR0TnUlL0Vv5rkp3kq:sZSP+lZQt3v75d0TnUy55rRq |
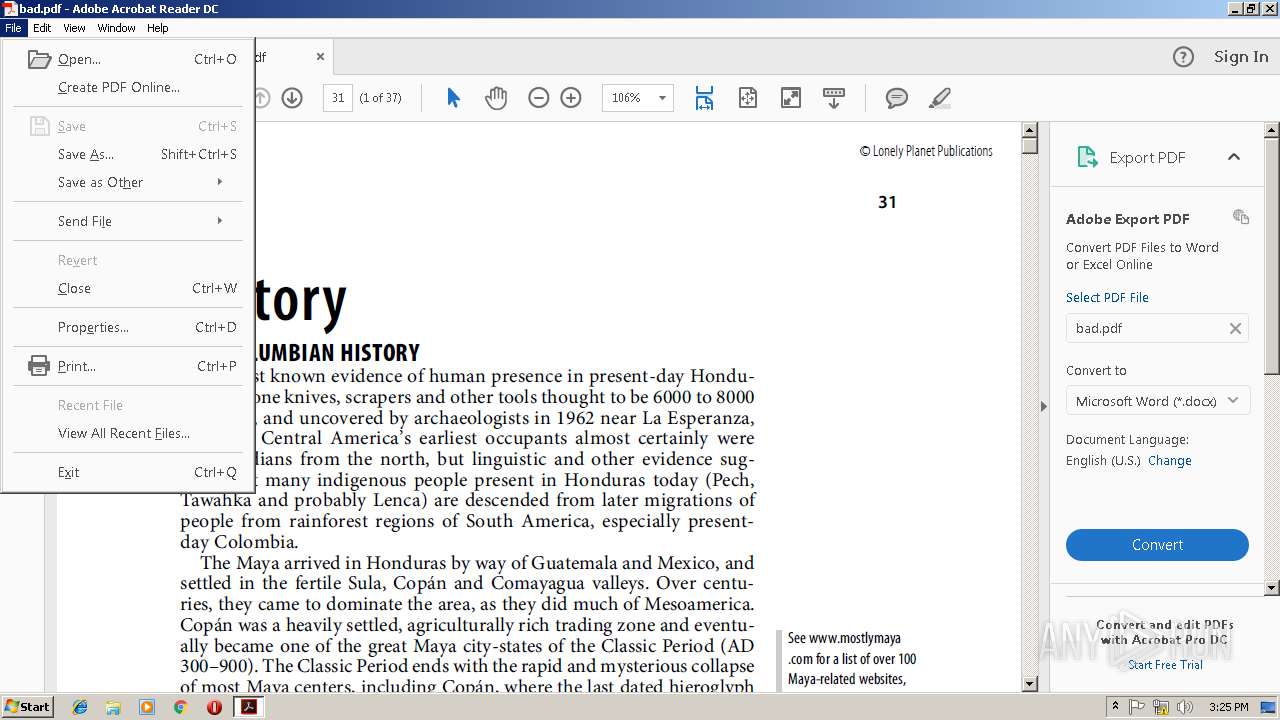
MALICIOUS
Loads the Task Scheduler COM API
- MsiExec.exe (PID: 2856)
- MsiExec.exe (PID: 3372)
SUSPICIOUS
Creates files in the program directory
- AdobeARM.exe (PID: 2952)
Executable content was dropped or overwritten
- AdobeARM.exe (PID: 2952)
INFO
Application launched itself
- AcroRd32.exe (PID: 2996)
- chrome.exe (PID: 3540)
- RdrCEF.exe (PID: 2088)
- msiexec.exe (PID: 3316)
Creates files in the program directory
- msiexec.exe (PID: 3316)
Creates a software uninstall entry
- msiexec.exe (PID: 3316)
Reads settings of System Certificates
- chrome.exe (PID: 3540)
- msiexec.exe (PID: 3316)
Creates files in the user directory
- AcroRd32.exe (PID: 2996)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| | | Adobe Portable Document Format (100) |
EXIF
| PDFVersion: | 1.4 |
|---|---|
| Linearized: | No |
| PageCount: | 37 |
| ModifyDate: | 2007:05:01 11:32:17+10:00 |
| CreateDate: | 2007:03:22 11:00:42+11:00 |
| Title: | honduras-the-bay-islands-history.indd |
| Creator: | PScript5.dll Version 5.2.2 |
| Author: | - |
| Producer: | Acrobat Distiller 6.0.1 (Windows) |
XMP
| XMPToolkit: | XMP toolkit 2.9.1-14, framework 1.6 |
|---|---|
| About: | uuid:f26ba470-ee1e-46b0-b235-6d70bf3b6408 |
| Producer: | Acrobat Distiller 6.0.1 (Windows) |
| CreateDate: | 2007:03:22 11:00:42+11:00 |
| CreatorTool: | PScript5.dll Version 5.2.2 |
| ModifyDate: | 2007:05:01 11:32:17+10:00 |
| MetadataDate: | 2007:05:01 11:32:17+10:00 |
| DocumentID: | uuid:87e4644e-30f8-469d-94b2-6fb0f37fce39 |
| Format: | application/pdf |
| Title: | honduras-the-bay-islands-history.indd |
| Creator: | - |
Total processes
54
Monitored processes
23
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1244 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x6f6c00b0,0x6f6c00c0,0x6f6c00cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2088 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --backgroundcolor=16448250 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | AcroRd32.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe RdrCEF Exit code: 3221225547 Version: 15.23.20053.211670 Modules
| |||||||||||||||
| 2344 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" --type=renderer "C:\Users\admin\AppData\Local\Temp\bad.pdf" | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | — | AcroRd32.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe Acrobat Reader DC Exit code: 1 Version: 15.23.20070.215641 Modules
| |||||||||||||||
| 2532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=920,16120838280228670182,11040168073650714532,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=35EE402DB6B7770E36B5254CCB56957F --mojo-platform-channel-handle=900 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2648 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\Reader_sl.exe" | C:\Program Files\Adobe\Acrobat Reader DC\Reader\Reader_sl.exe | — | AdobeARM.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Acrobat SpeedLauncher Exit code: 0 Version: 15.23.20053.211670 Modules
| |||||||||||||||
| 2664 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2780 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=920,16120838280228670182,11040168073650714532,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=BA436916BF5FEA83EA81CB5E5EFA7E24 --mojo-platform-channel-handle=1460 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2856 | C:\Windows\system32\MsiExec.exe -Embedding 5EB7C0187D38D93CA33427DCA42205E9 M Global\MSI0000 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2860 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=920,16120838280228670182,11040168073650714532,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=F57D5A2811159BBE19051F7F37046C8F --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=F57D5A2811159BBE19051F7F37046C8F --renderer-client-id=5 --mojo-platform-channel-handle=3224 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2952 | "C:\Program Files\Common Files\Adobe\ARM\1.0\AdobeARM.exe" /PRODUCT:Reader /VERSION:15.0 /MODE:3 | C:\Program Files\Common Files\Adobe\ARM\1.0\AdobeARM.exe | AcroRd32.exe | ||||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Reader and Acrobat Manager Exit code: 0 Version: 1.824.27.2646 Modules
| |||||||||||||||
Total events
1 569
Read events
1 299
Write events
246
Delete events
24
Modification events
| (PID) Process: | (2344) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\ExitSection |
| Operation: | write | Name: | bLastExitNormal |
Value: 0 | |||
| (PID) Process: | (2344) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Adobe Acrobat\DC\DiskCabs |
| Operation: | write | Name: | bJSCache_GlobData |
Value: 1 | |||
| (PID) Process: | (2344) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Adobe Acrobat\DC\DiskCabs |
| Operation: | write | Name: | bJSCache_GlobSettings |
Value: 0 | |||
| (PID) Process: | (2344) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\AVGeneral |
| Operation: | write | Name: | bExpandRHPInViewer |
Value: 1 | |||
| (PID) Process: | (2344) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\NoTimeOut |
| Operation: | write | Name: | smailto |
Value: 5900 | |||
| (PID) Process: | (2996) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2996) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2996) AcroRd32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2952) AdobeARM.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Adobe ARM\1.0\ARM |
| Operation: | write | Name: | iSpeedLauncherLogonTime |
Value: 680815E7A080D401 | |||
| (PID) Process: | (2952) AdobeARM.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
2
Suspicious files
12
Text files
82
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2344 | AcroRd32.exe | C:\Users\admin\AppData\LocalLow\Adobe\Acrobat\DC\ReaderMessages-journal | — | |
MD5:— | SHA256:— | |||
| 2344 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9R571f1w_rqxdgr_1t4.tmp | — | |
MD5:— | SHA256:— | |||
| 2344 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9R1vkijos_rqxdgt_1t4.tmp | — | |
MD5:— | SHA256:— | |||
| 2344 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9R5ik3rq_rqxdgu_1t4.tmp | — | |
MD5:— | SHA256:— | |||
| 2344 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9R1e3j2o5_rqxdgv_1t4.tmp | — | |
MD5:— | SHA256:— | |||
| 2344 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9Rgeo2j0_rqxdgs_1t4.tmp | — | |
MD5:— | SHA256:— | |||
| 2952 | AdobeARM.exe | C:\Users\admin\AppData\Local\Temp\Tmp9DF5.tmp | — | |
MD5:— | SHA256:— | |||
| 2952 | AdobeARM.exe | C:\Users\admin\AppData\Local\Temp\Tmp9E05.tmp | — | |
MD5:— | SHA256:— | |||
| 2952 | AdobeARM.exe | C:\Users\admin\AppData\Local\Temp\TmpC41.tmp | — | |
MD5:— | SHA256:— | |||
| 2952 | AdobeARM.exe | C:\Users\admin\AppData\Local\Temp\Tmp28D2.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
23
DNS requests
12
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3540 | chrome.exe | POST | 200 | 91.103.1.84:80 | http://unprotected-pdf.ds388b363d1ym0.r-lp.readnotify.com/nocache/ds388b363d1ymA/pdf.fdf?page=0&DMCA_WARNING=It_is_a_criminal_offence_to_remove_or_disable_this_copyright_protection_technology&Search_Google_for_details=DMCA+eBook | IE | text | 86 b | malicious |
2996 | AcroRd32.exe | GET | 304 | 2.16.186.32:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/281_15_23_20070.zip | unknown | — | — | whitelisted |
2996 | AcroRd32.exe | GET | 304 | 2.16.186.32:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/278_15_23_20070.zip | unknown | — | — | whitelisted |
2996 | AcroRd32.exe | GET | 304 | 2.16.186.32:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/277_15_23_20070.zip | unknown | — | — | whitelisted |
2996 | AcroRd32.exe | GET | 304 | 2.16.186.32:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/message.zip | unknown | — | — | whitelisted |
2996 | AcroRd32.exe | GET | 304 | 2.16.186.32:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/280_15_23_20070.zip | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2996 | AcroRd32.exe | 2.16.186.32:80 | acroipm2.adobe.com | Akamai International B.V. | — | whitelisted |
2996 | AcroRd32.exe | 2.18.233.74:443 | armmf.adobe.com | Akamai International B.V. | — | whitelisted |
— | — | 2.18.233.74:443 | armmf.adobe.com | Akamai International B.V. | — | whitelisted |
— | — | 2.18.68.206:443 | ardownload2.adobe.com | Akamai International B.V. | — | whitelisted |
2996 | AcroRd32.exe | 34.233.37.232:443 | files.acrobat.com | Amazon.com, Inc. | US | unknown |
3540 | chrome.exe | 172.217.22.99:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3540 | chrome.exe | 172.217.16.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3540 | chrome.exe | 91.103.1.84:80 | unprotected-pdf.ds388b363d1ym0.r-lp.readnotify.com | Cork Internet Exchange Limited | IE | malicious |
3540 | chrome.exe | 216.58.207.77:443 | accounts.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
fdf.0.ds388b363d1ym0.r-lp.readnotify.com |
| unknown |
acroipm2.adobe.com |
| whitelisted |
armmf.adobe.com |
| whitelisted |
ardownload2.adobe.com |
| whitelisted |
files.acrobat.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
accounts.google.com |
| shared |
unprotected-pdf.ds388b363d1ym0.r-lp.readnotify.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |