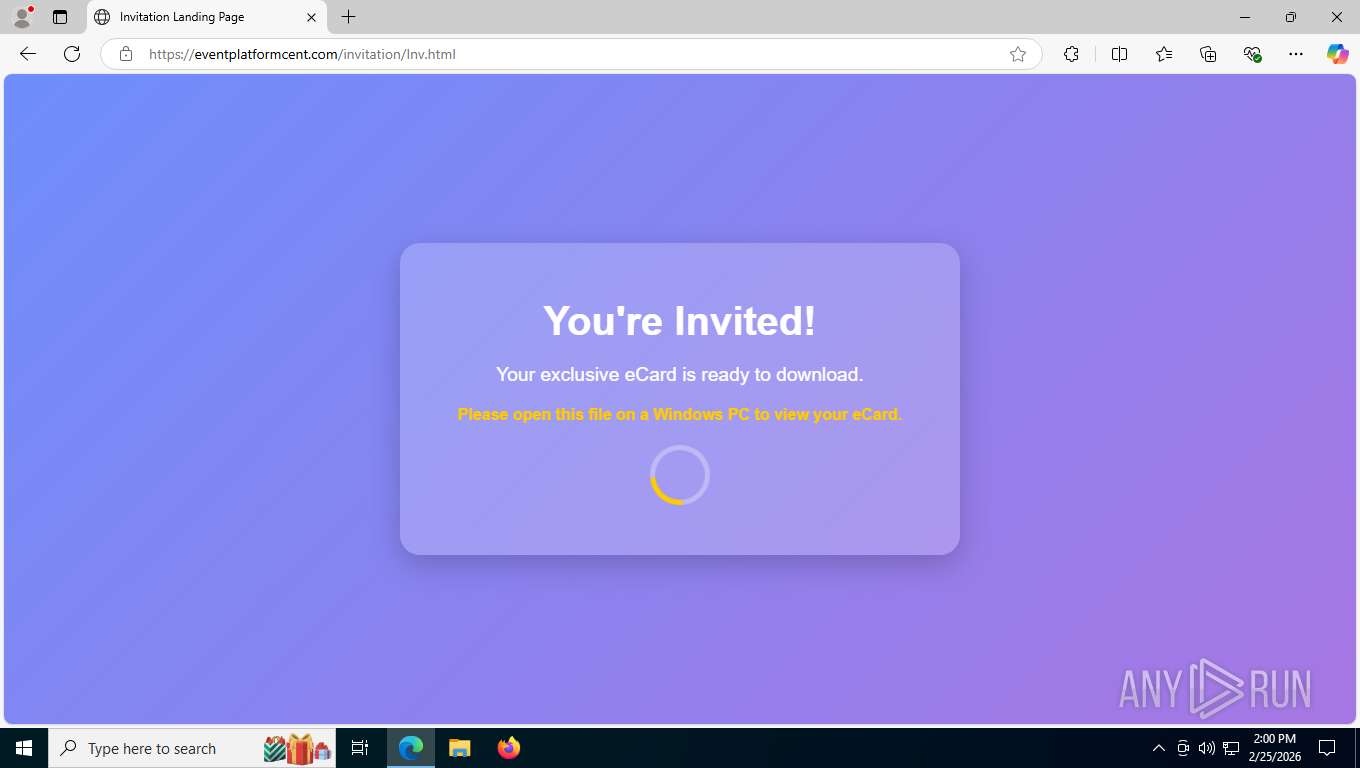
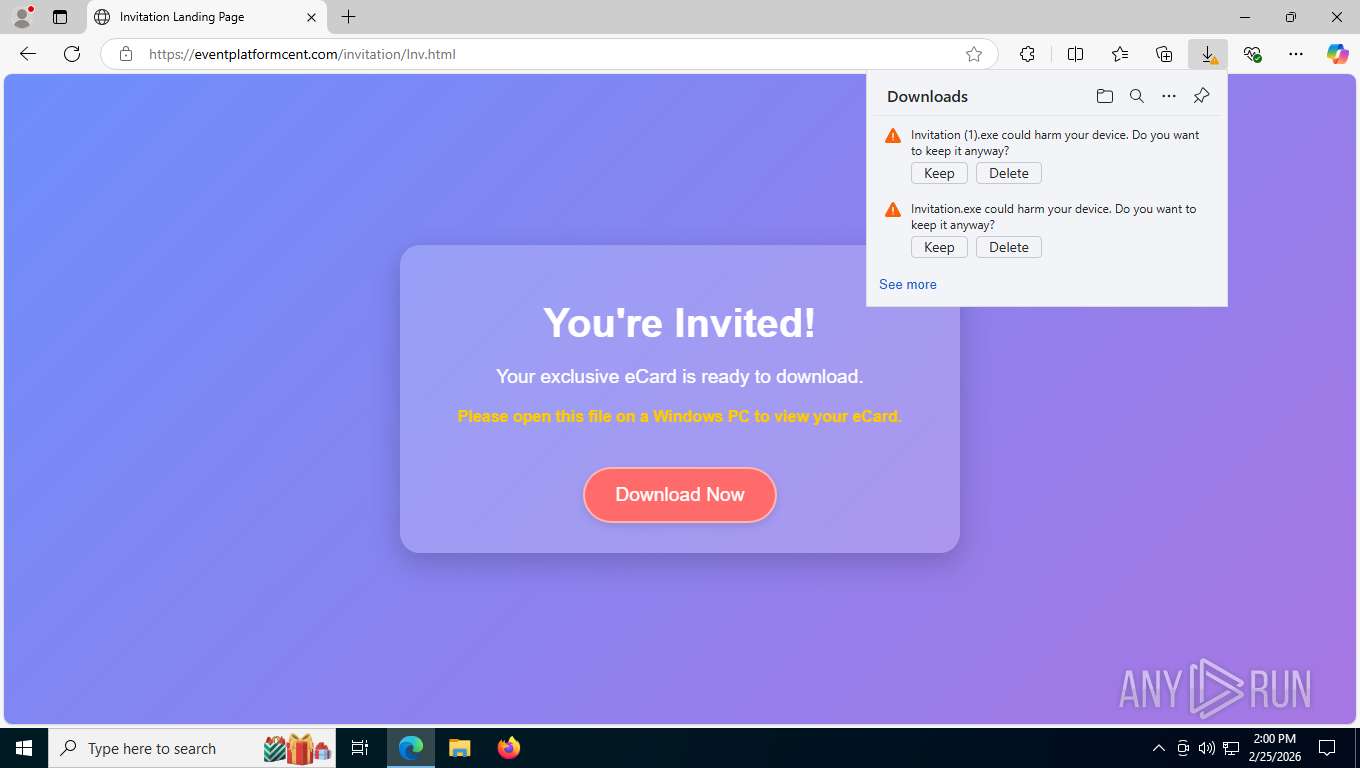
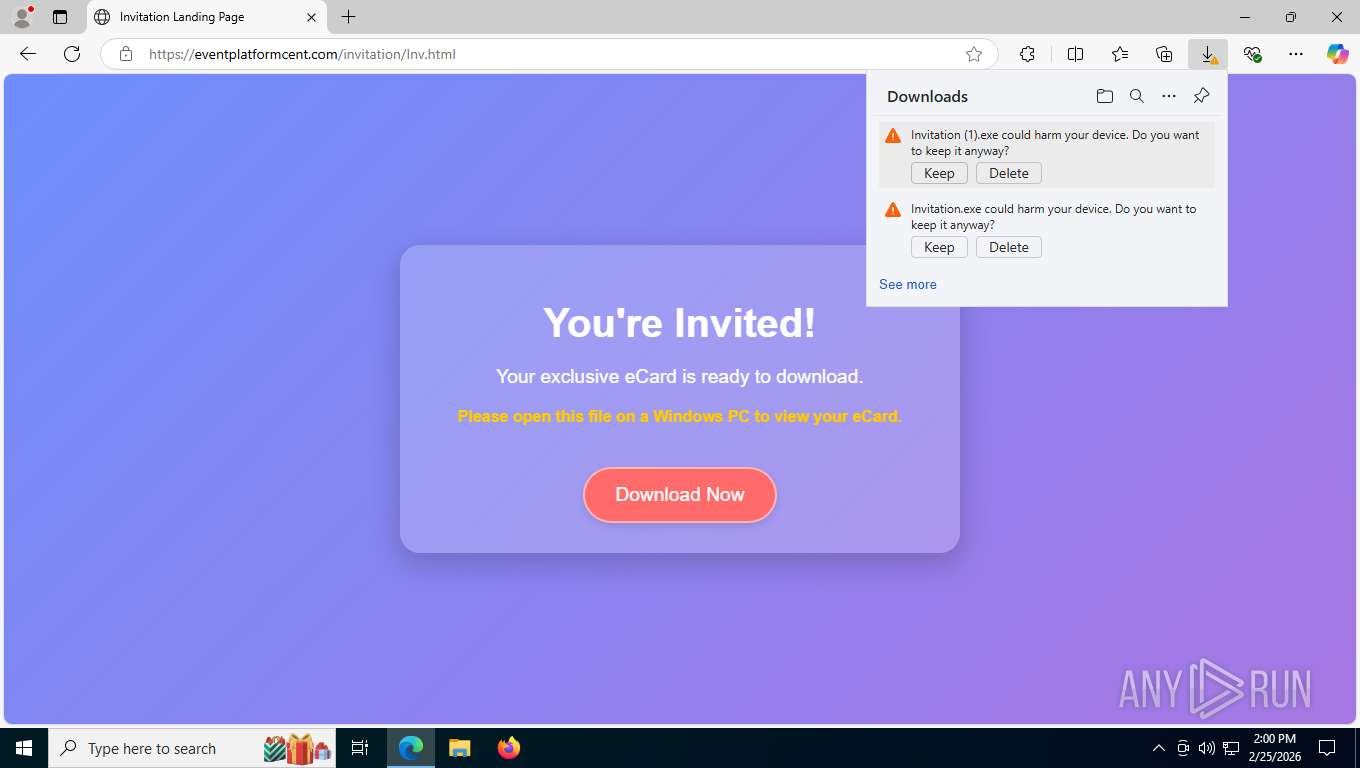
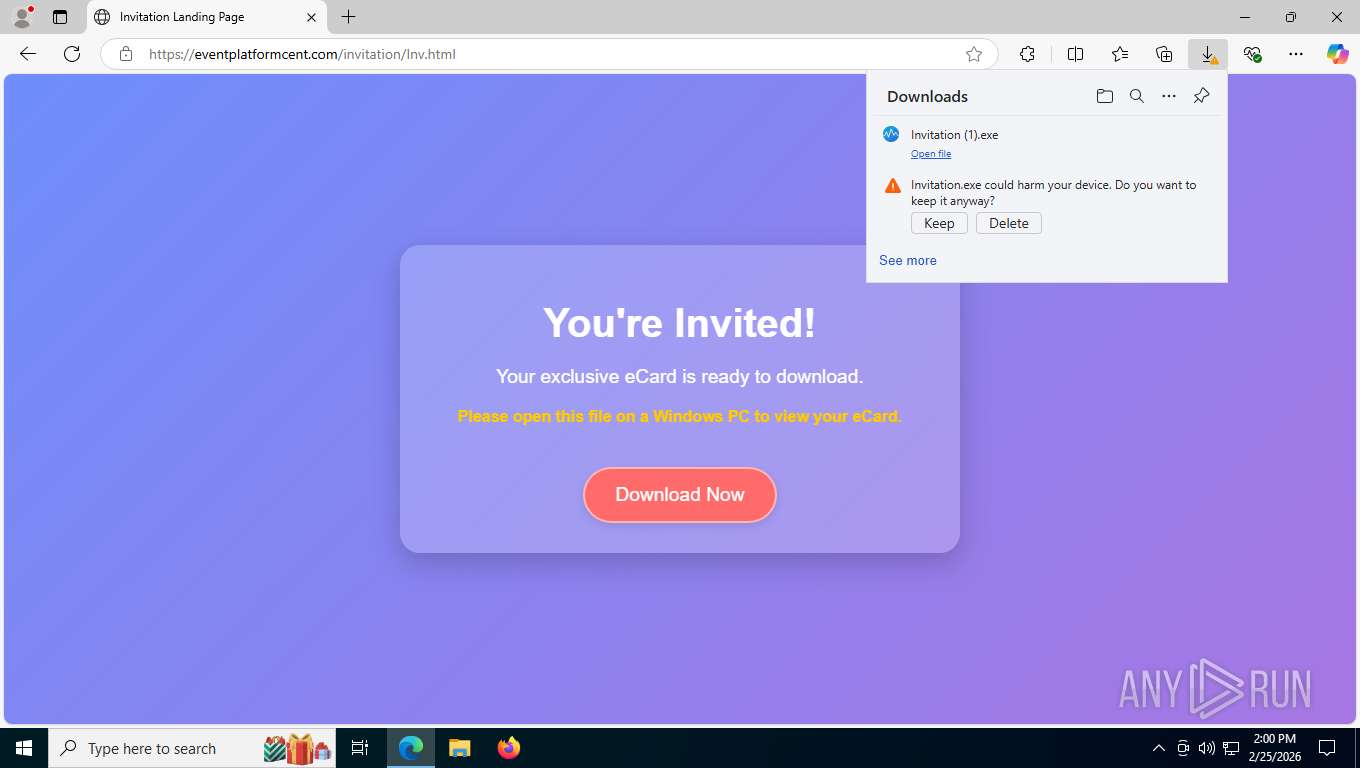
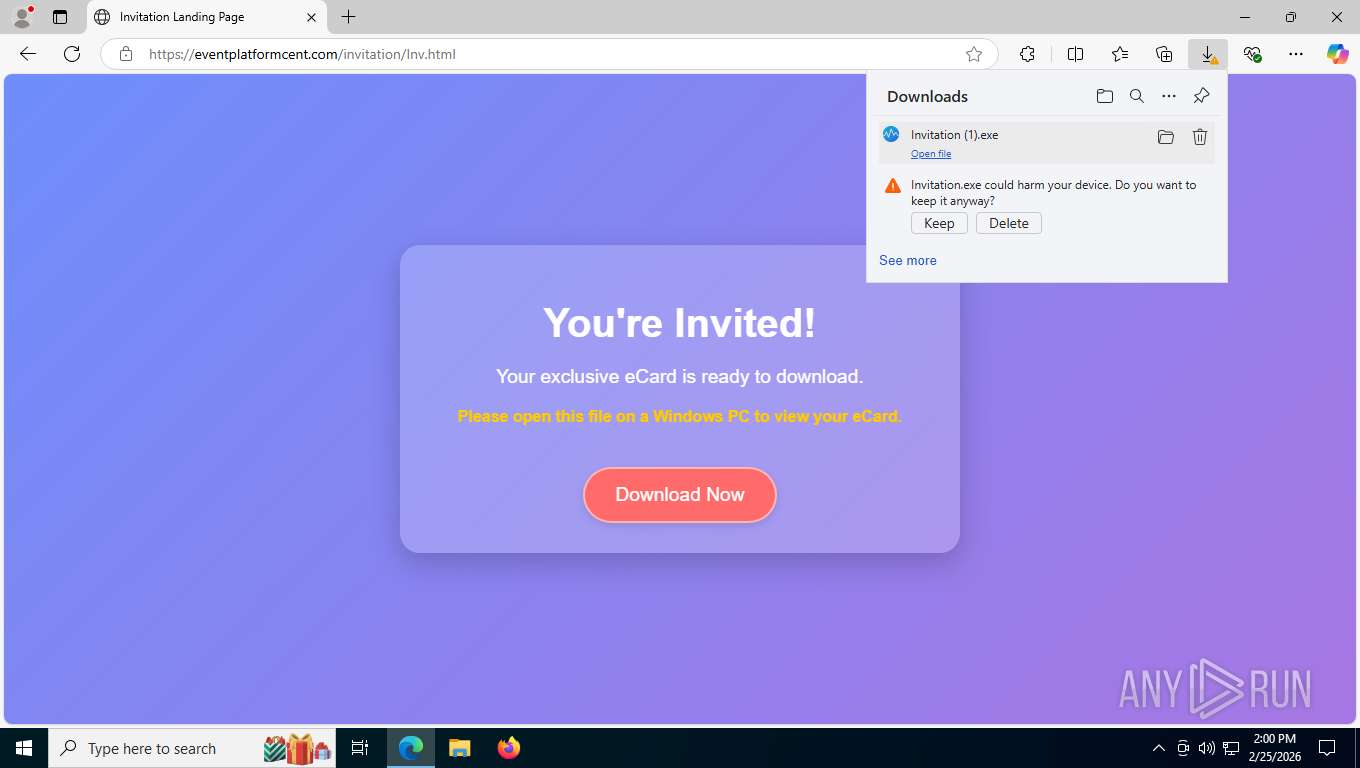
| URL: | http://machibestaydelight.com/christ |
| Full analysis: | https://app.any.run/tasks/e6801df8-e78a-4881-aa37-cccbebdc16ac |
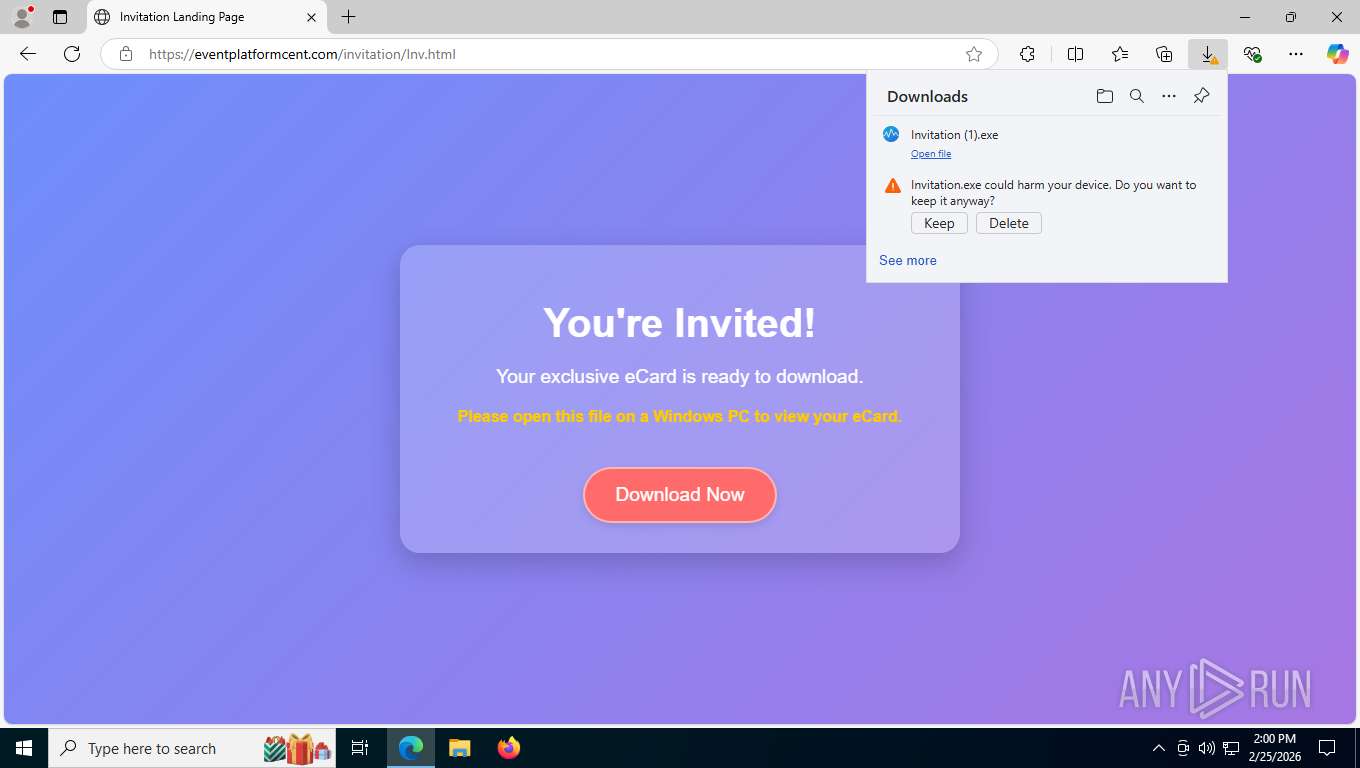
| Verdict: | Malicious activity |
| Analysis date: | February 25, 2026, 18:59:59 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | CA78B0A88B5C1C70D057E11E658F99C3 |
| SHA1: | F56D2C88B39C6B876020999EA613766E6645C736 |
| SHA256: | 2DD4740F99F34A06E47C659EB8905AA623B7CE86223B4297D79AE535663B2C32 |
| SSDEEP: | 3:N1KTgEc2VtaXMWR:CcEc2PacWR |
MALICIOUS
Changes the autorun value in the registry
- Invitation (1).exe (PID: 5868)
- Invitation (1).exe (PID: 6108)
Registers / Runs the DLL via REGSVR32.EXE
- CagService.exe (PID: 1584)
DATTO has been detected
- CagService.exe (PID: 1584)
SUSPICIOUS
The process creates files with name similar to system file names
- Invitation (1).exe (PID: 5868)
- CagService.exe (PID: 1584)
- Invitation (1).exe (PID: 6108)
Malware-specific behavior (creating "System.dll" in Temp)
- Invitation (1).exe (PID: 5868)
- Invitation (1).exe (PID: 6108)
Executable content was dropped or overwritten
- Invitation (1).exe (PID: 5868)
- Invitation (1).exe (PID: 6108)
- CagService.exe (PID: 1584)
Executes as Windows Service
- CagService.exe (PID: 1584)
Creates or modifies Windows services
- CagService.exe (PID: 1584)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 7516)
Searches for installed software
- CagService.exe (PID: 1584)
INFO
Application launched itself
- msedge.exe (PID: 7312)
Reads the computer name
- identity_helper.exe (PID: 1324)
- Invitation (1).exe (PID: 5868)
- CagService.exe (PID: 1584)
- Gui.exe (PID: 3796)
- Invitation (1).exe (PID: 6108)
- Gui.exe (PID: 4256)
Executable content was dropped or overwritten
- msedge.exe (PID: 6056)
- msedge.exe (PID: 7312)
Create files in a temporary directory
- Invitation (1).exe (PID: 5868)
- Invitation (1).exe (PID: 6108)
Reads Environment values
- identity_helper.exe (PID: 1324)
- CagService.exe (PID: 1584)
Creates files in the program directory
- Invitation (1).exe (PID: 5868)
- CagService.exe (PID: 1584)
- AEMAgent.exe (PID: 8700)
- Gui.exe (PID: 3796)
Checks supported languages
- identity_helper.exe (PID: 1324)
- Invitation (1).exe (PID: 5868)
- Invitation (1).exe (PID: 6108)
- Gui.exe (PID: 3796)
- CagService.exe (PID: 1584)
- AEMAgent.exe (PID: 8700)
- Gui.exe (PID: 4256)
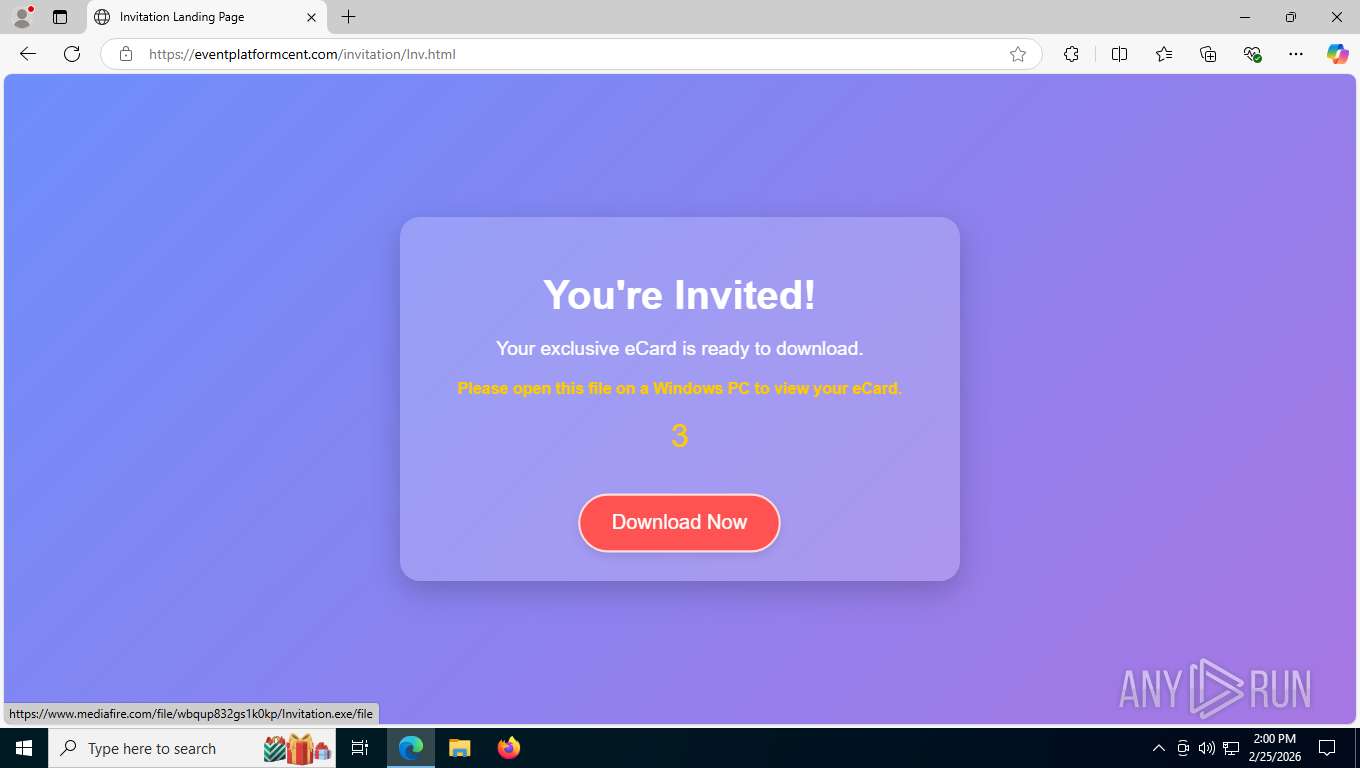
Launching a file from the Downloads directory
- msedge.exe (PID: 7312)
The sample compiled with english language support
- Invitation (1).exe (PID: 5868)
- CagService.exe (PID: 1584)
Creates a software uninstall entry
- Invitation (1).exe (PID: 5868)
- CagService.exe (PID: 1584)
- Invitation (1).exe (PID: 6108)
Launching a file from a Registry key
- Invitation (1).exe (PID: 5868)
- Invitation (1).exe (PID: 6108)
DATTO has been detected
- Invitation (1).exe (PID: 5868)
- CagService.exe (PID: 1584)
- Gui.exe (PID: 3796)
- CagService.exe (PID: 1584)
- AEMAgent.exe (PID: 8700)
- Invitation (1).exe (PID: 6108)
- Gui.exe (PID: 4256)
Reads security settings of Internet Explorer
- CagService.exe (PID: 1584)
- Gui.exe (PID: 3796)
- Gui.exe (PID: 4256)
Reads the machine GUID from the registry
- CagService.exe (PID: 1584)
- Gui.exe (PID: 3796)
- Gui.exe (PID: 4256)
Creates files or folders in the user directory
- Gui.exe (PID: 3796)
Checks proxy server information
- CagService.exe (PID: 1584)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
193
Monitored processes
42
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 752 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --pdf-upsell-enabled --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=9 --always-read-main-dll --field-trial-handle=5396,i,544767683151307543,6836198750751291055,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=3632 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1172 | "C:\Users\admin\Downloads\Invitation (1).exe" | C:\Users\admin\Downloads\Invitation (1).exe | — | msedge.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 1200 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5340,i,544767683151307543,6836198750751291055,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=5300 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1324 | "C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6352,i,544767683151307543,6836198750751291055,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=5568 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1352 | "C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6352,i,544767683151307543,6836198750751291055,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=5568 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1584 | "C:\Program Files (x86)\CentraStage\CagService.exe" | C:\Program Files (x86)\CentraStage\CagService.exe | services.exe | ||||||||||||
User: SYSTEM Company: CentraStage Integrity Level: SYSTEM Description: CentraStage Service Version: 4.4.10748.10748 Modules
| |||||||||||||||
| 1784 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --pdf-upsell-enabled --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=19 --always-read-main-dll --field-trial-handle=6380,i,544767683151307543,6836198750751291055,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=5464 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2456 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2780,i,544767683151307543,6836198750751291055,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=2788 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2760 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --pdf-upsell-enabled --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=6 --always-read-main-dll --field-trial-handle=3604,i,544767683151307543,6836198750751291055,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=3628 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2872 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | CagService.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
9 276
Read events
9 231
Write events
45
Delete events
0
Modification events
| (PID) Process: | (5868) Invitation (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | CentraStage |
Value: C:\Program Files (x86)\CentraStage\Gui.exe | |||
| (PID) Process: | (5868) Invitation (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\CentraStage |
| Operation: | write | Name: | DisplayName |
Value: CentraStage | |||
| (PID) Process: | (5868) Invitation (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\CentraStage |
| Operation: | write | Name: | UninstallString |
Value: "C:\Program Files (x86)\CentraStage\uninst.exe" | |||
| (PID) Process: | (5868) Invitation (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\CentraStage |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Program Files (x86)\CentraStage\CSIcon.ico | |||
| (PID) Process: | (5868) Invitation (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\CentraStage |
| Operation: | write | Name: | URLInfoAbout |
Value: http://www.centrastage.com | |||
| (PID) Process: | (5868) Invitation (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\CentraStage |
| Operation: | write | Name: | Publisher |
Value: CentraStage Limited | |||
| (PID) Process: | (5868) Invitation (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\CentraStage |
| Operation: | write | Name: | AgentFolderLocation |
Value: C:\ProgramData\CentraStage | |||
| (PID) Process: | (5868) Invitation (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\CentraStage |
| Operation: | write | Name: | AgentFolderStatus |
Value: 0 | |||
| (PID) Process: | (1584) CagService.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\cag |
| Operation: | write | Name: | URL Protocol |
Value: | |||
| (PID) Process: | (1584) CagService.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001_Classes\cag |
| Operation: | write | Name: | URL Protocol |
Value: | |||
Executable files
341
Suspicious files
37
Text files
115
Unknown types
35
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7312 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF1e5060.TMP | — | |
MD5:— | SHA256:— | |||
| 7312 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7312 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1e506f.TMP | — | |
MD5:— | SHA256:— | |||
| 7312 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7312 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1e509e.TMP | — | |
MD5:— | SHA256:— | |||
| 7312 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF1e509e.TMP | — | |
MD5:— | SHA256:— | |||
| 7312 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1e509e.TMP | — | |
MD5:— | SHA256:— | |||
| 7312 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1e509e.TMP | — | |
MD5:— | SHA256:— | |||
| 7312 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7312 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
71
TCP/UDP connections
72
DNS requests
73
Threats
21
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6056 | msedge.exe | OPTIONS | 200 | 35.190.80.1:443 | https://a.nel.cloudflare.com/report/v4?s=gxp5yMbDwLb4MYCaKaIPKIhy0Hu%2B%2FVCN9Ol1JUnw6ho9DMuzglBqHaVXi2QtbYeI7EYKRyxAYOJnHVegxwlZ3zTwazoBbBY6Ro49NO2%2FL81eEfYas5vM5fQCp0X85FxsYFPsweRwPlY%3D | unknown | — | — | unknown |
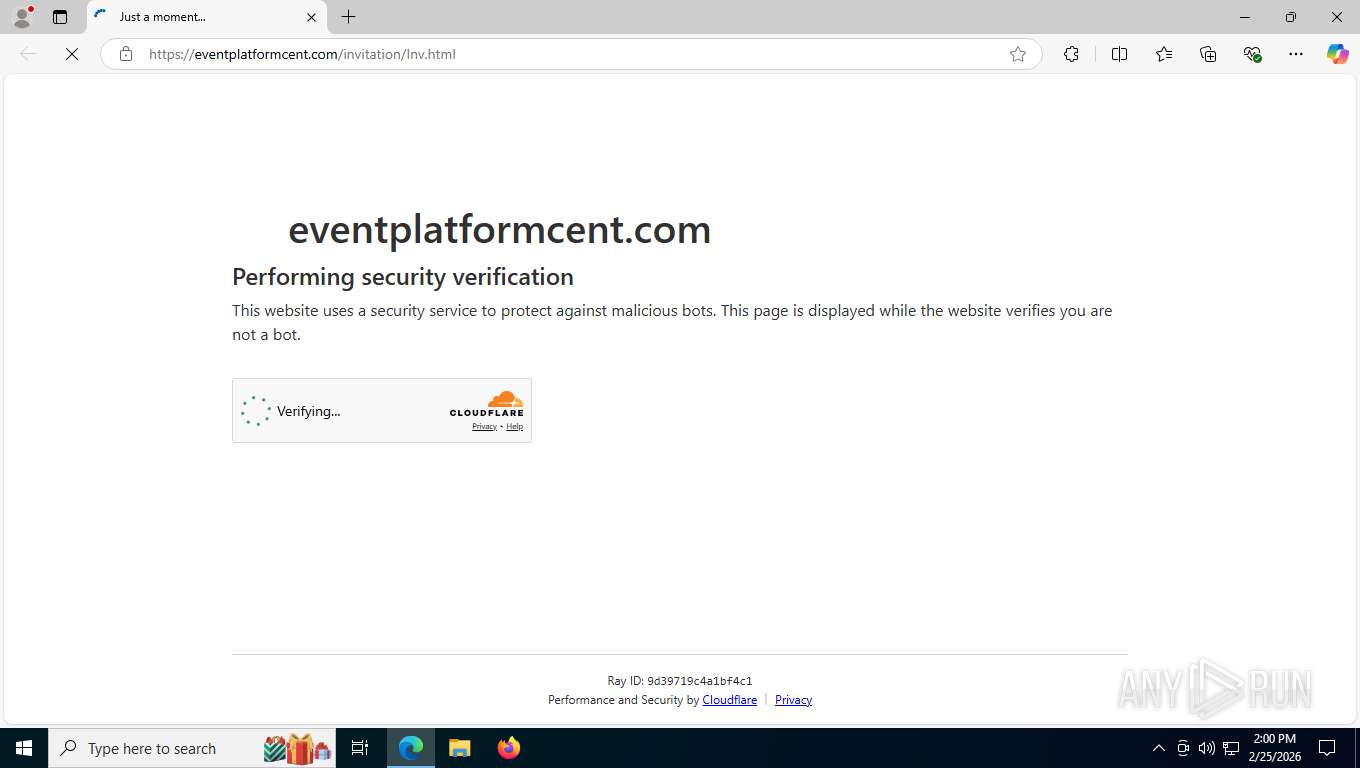
6056 | msedge.exe | GET | 302 | 104.21.54.166:443 | https://eventplatformcent.com/favicon.ico | unknown | — | — | unknown |
6056 | msedge.exe | GET | 301 | 170.10.160.66:80 | http://machibestaydelight.com/christ | unknown | — | — | unknown |
6056 | msedge.exe | GET | 200 | 150.171.22.17:443 | https://config.edge.skype.com/config/v1/Edge/133.0.3065.92?clientId=4489578223053569932&agents=Edge%2CEdgeConfig%2CEdgeServices%2CEdgeFirstRun%2CEdgeFirstRunConfig&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=66&mngd=0&installdate=1661339457&edu=0&soobedate=1504771245&bphint=2&fg=1&lbfgdate=1766135237&lafgdate=0 | unknown | text | 4.47 Kb | whitelisted |
6056 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:Hm1KxrlWxVTmAUiKUl20AabjT9WBvx_9zmaxjVNhONo&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
6056 | msedge.exe | GET | 200 | 150.171.27.11:443 | https://edge.microsoft.com/serviceexperimentation/v3/?osname=win&channel=stable&osver=10.0.19045&devicefamily=desktop&installdate=1661339457&clientversion=133.0.3065.92&experimentationmode=2&scpguard=0&scpfull=0&scpver=0 | unknown | text | 295 b | whitelisted |
6056 | msedge.exe | GET | 200 | 104.18.22.222:443 | https://copilot.microsoft.com/c/api/user/eligibility | unknown | text | 25 b | whitelisted |
6056 | msedge.exe | GET | 302 | 104.21.54.166:443 | https://eventplatformcent.com/favicon.ico | unknown | — | — | unknown |
6056 | msedge.exe | GET | 200 | 13.107.246.44:443 | https://api.edgeoffer.microsoft.com/edgeoffer/pb/experiments?appId=edge-extensions&country=US | unknown | — | 82 b | whitelisted |
6056 | msedge.exe | GET | 301 | 170.10.160.66:443 | https://machibestaydelight.com/christ | unknown | html | 795 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
7212 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3344 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
3412 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6056 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6056 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6056 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6056 | msedge.exe | 104.18.22.222:443 | copilot.microsoft.com | CLOUDFLARENET | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
machibestaydelight.com |
| unknown |
api.edgeoffer.microsoft.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
eventplatformcent.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6056 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
6056 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
6056 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
6056 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
6056 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
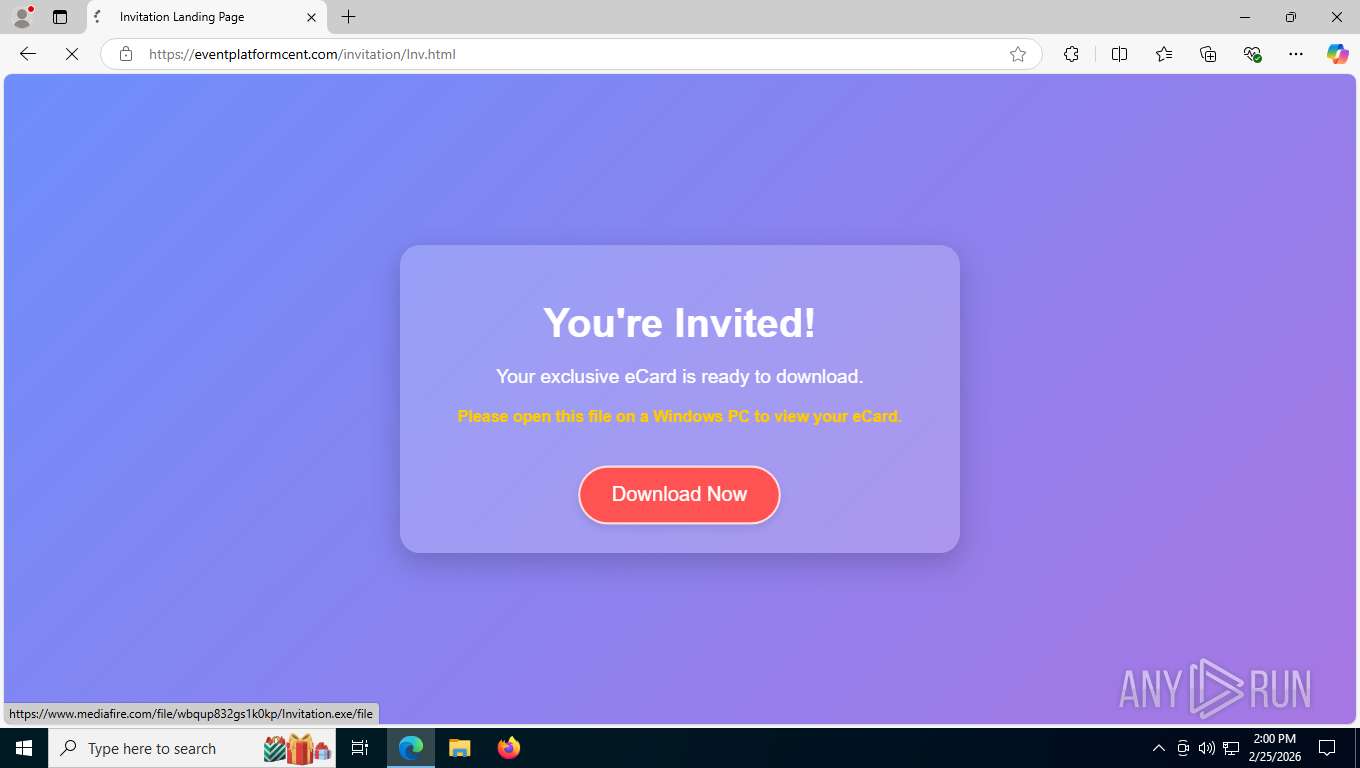
6056 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
6056 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
6056 | msedge.exe | Potentially Bad Traffic | ET INFO PE EXE or DLL Windows file download HTTP |
6056 | msedge.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2292 | svchost.exe | Misc activity | ET REMOTE_ACCESS DNS Query to Remote Monitoring and Management Domain (centrastage .net) |