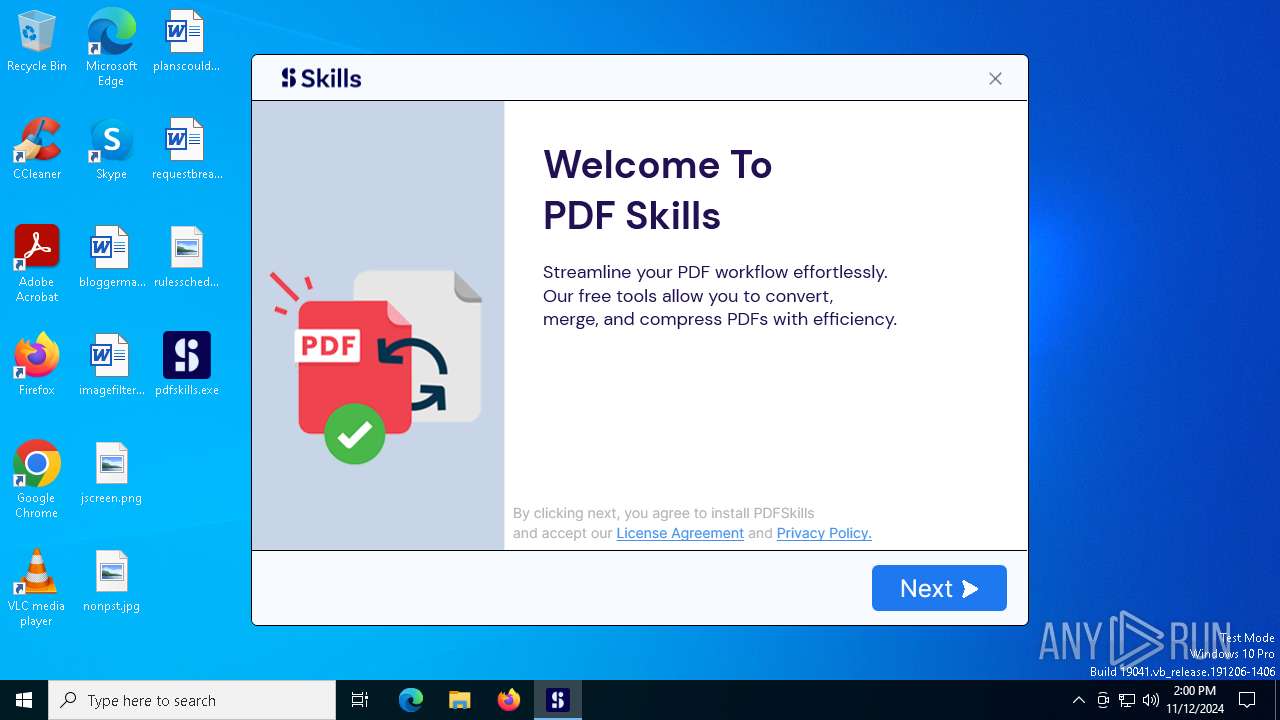
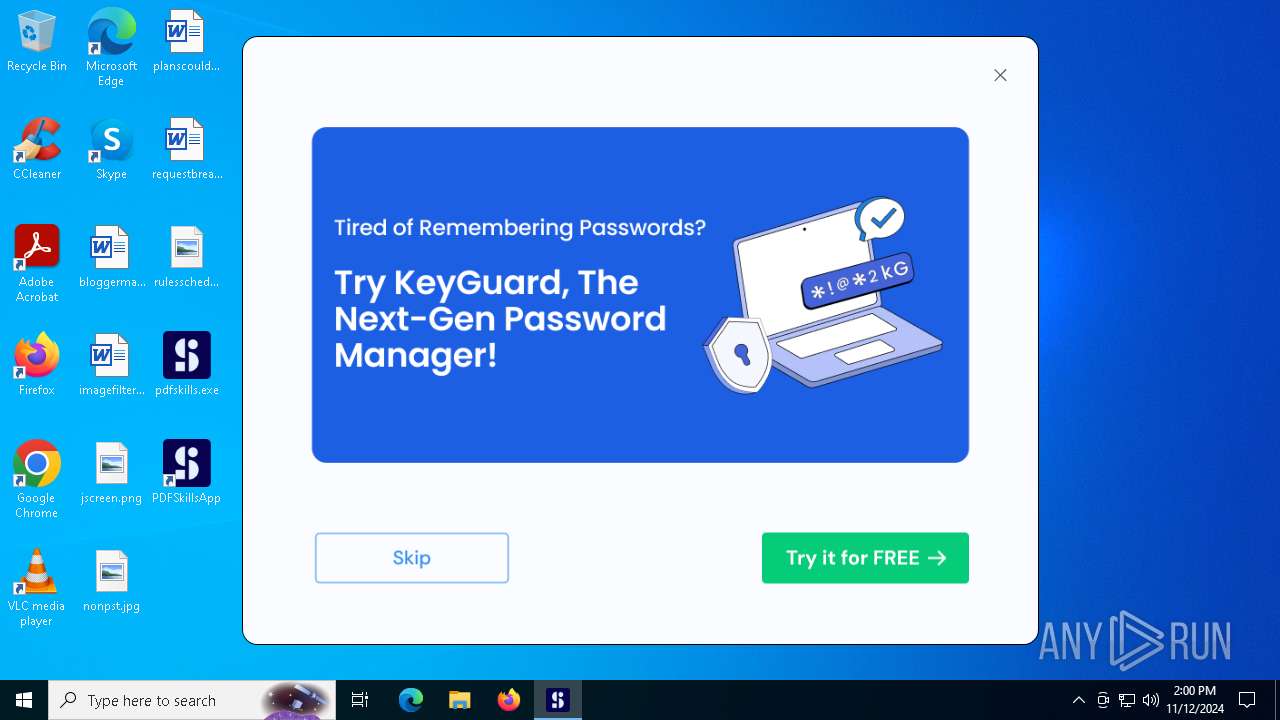
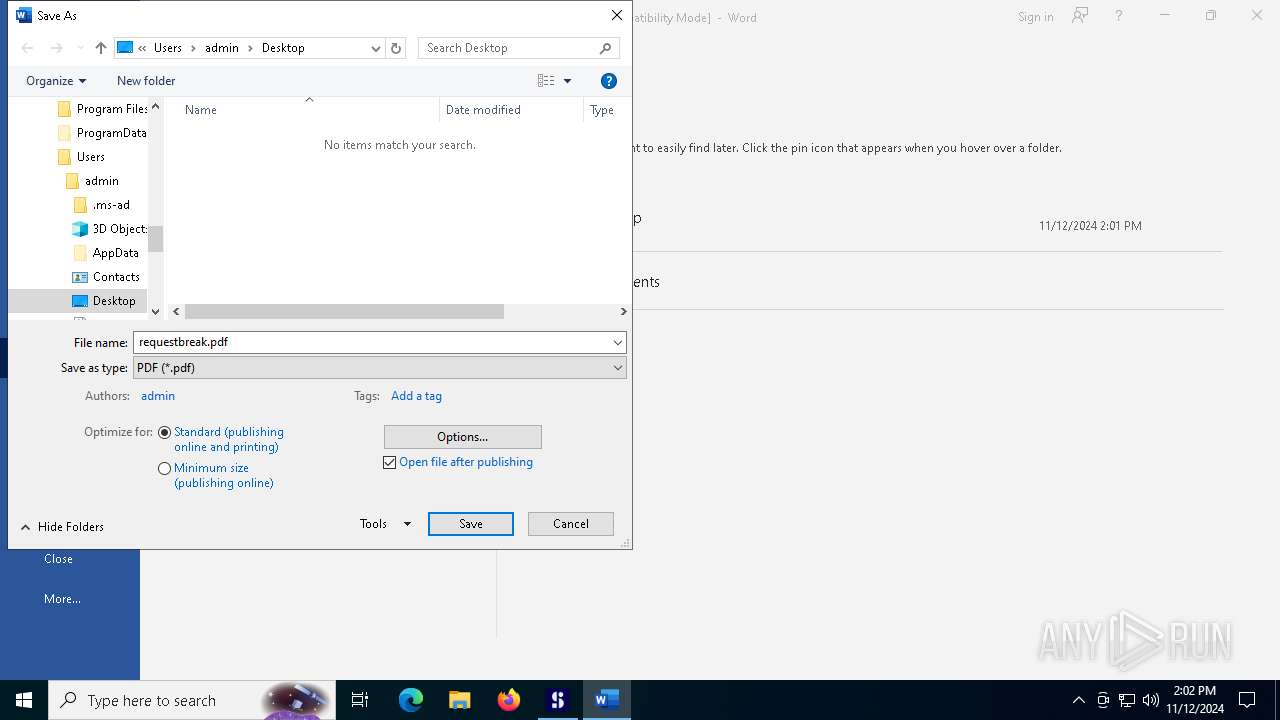
| File name: | pdfskills.exe |
| Full analysis: | https://app.any.run/tasks/b807b807-7f7d-4115-ac74-88e44c95d6b0 |
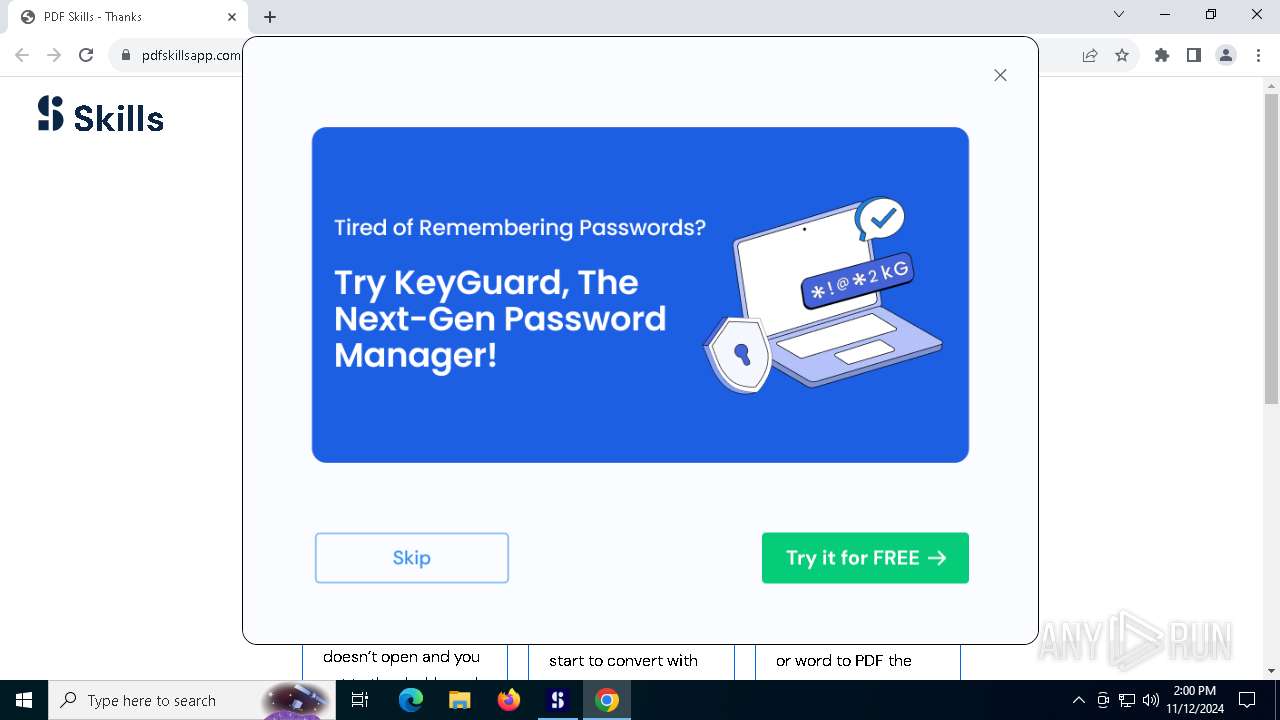
| Verdict: | Malicious activity |
| Analysis date: | November 12, 2024, 13:59:53 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64 Mono/.Net assembly, for MS Windows, 2 sections |
| MD5: | 3FED63BA4527B108772F0B932D48A875 |
| SHA1: | 66BCE2303A39E2F676502E5C77D3D3746730F33B |
| SHA256: | 2DC119979DB7AF6999E4E003CDD827987F5D60035049A8F9998A66EDA1864453 |
| SSDEEP: | 98304:UWw4DuwYxT2ZyydrgUxeLSzW8Uxj2iXrVfYdcPnqzdFhb4+yH1ZK304Qb9M:xeg1 |
MALICIOUS
Changes powershell execution policy (RemoteSigned)
- pdfskills.exe (PID: 1440)
SUSPICIOUS
Reads security settings of Internet Explorer
- pdfskills.exe (PID: 1440)
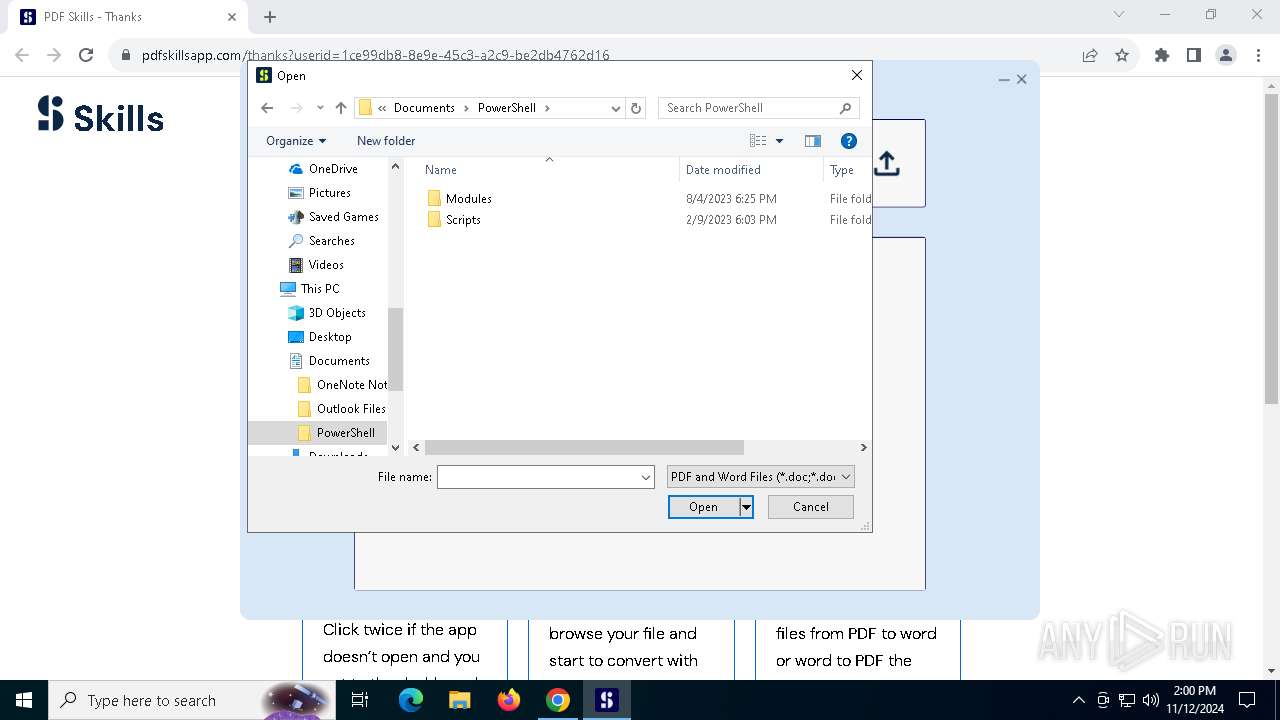
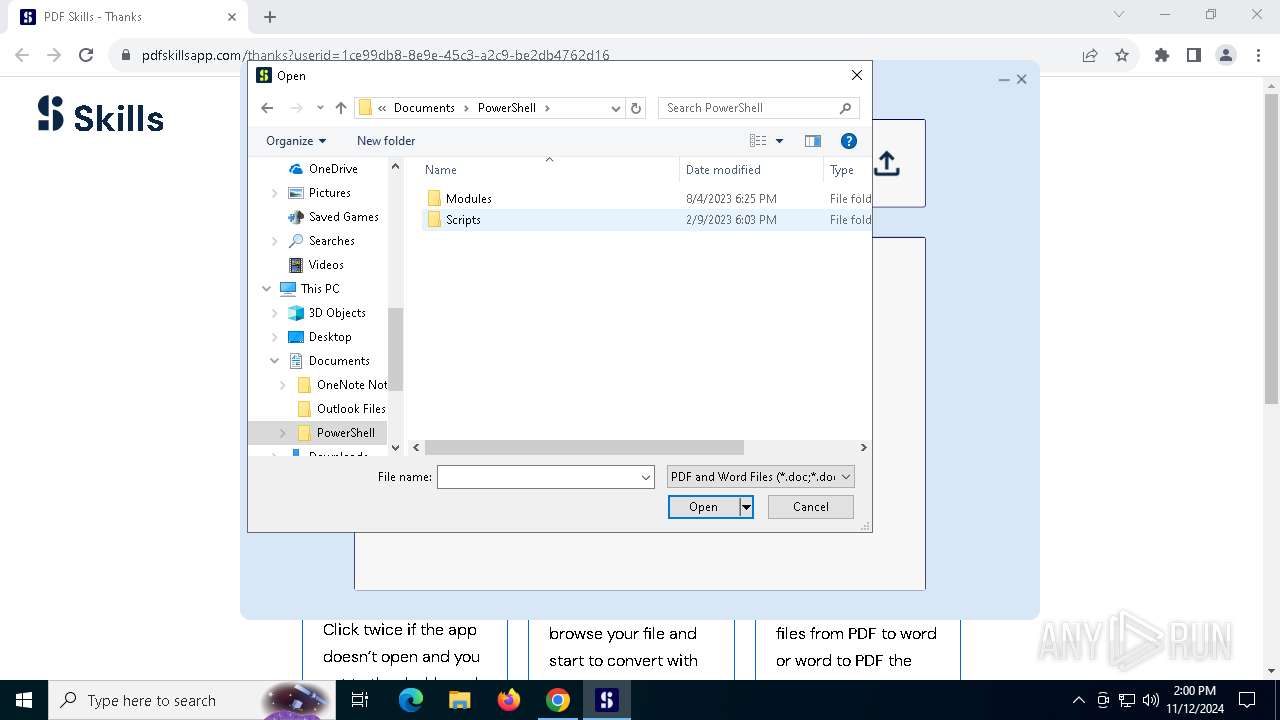
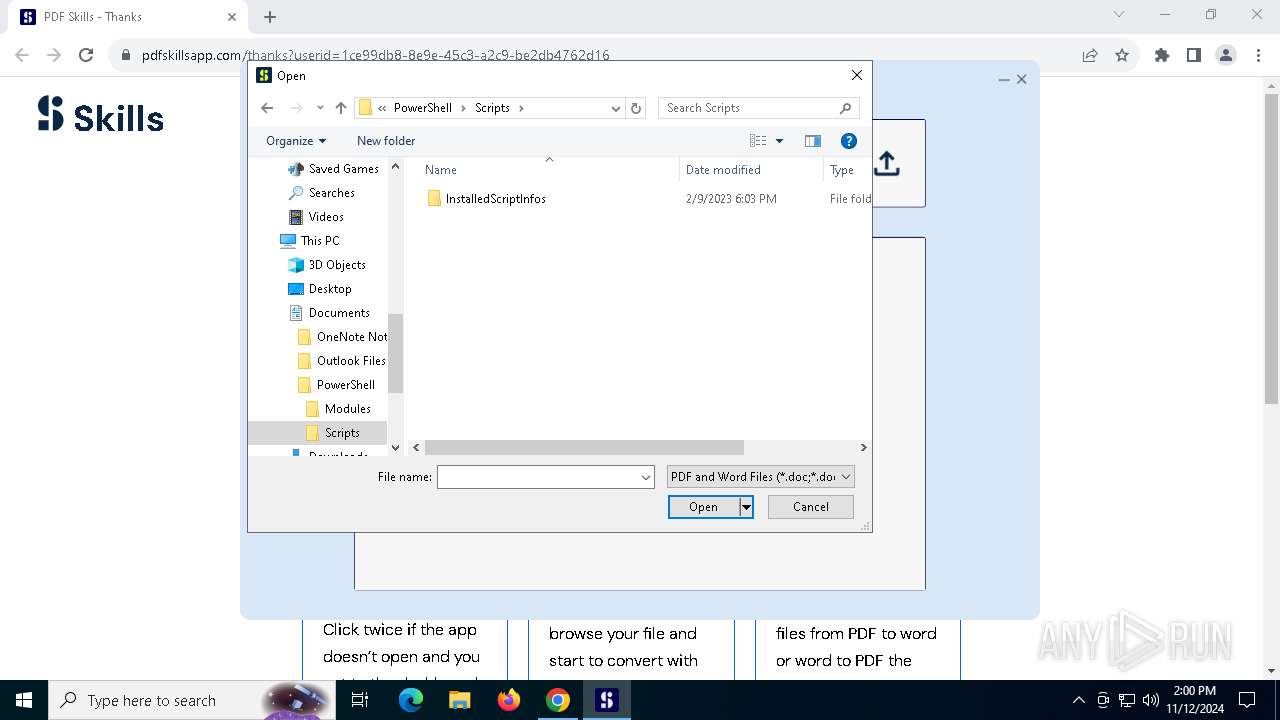
Gets path to any of the special folders (POWERSHELL)
- powershell.exe (PID: 4464)
The process drops C-runtime libraries
- pdfskills.exe (PID: 1440)
Process drops legitimate windows executable
- pdfskills.exe (PID: 1440)
Executable content was dropped or overwritten
- pdfskills.exe (PID: 1440)
The process executes Powershell scripts
- pdfskills.exe (PID: 1440)
Starts POWERSHELL.EXE for commands execution
- pdfskills.exe (PID: 1440)
Sets XML DOM element text (SCRIPT)
- splwow64.exe (PID: 7020)
INFO
Checks supported languages
- pdfskills.exe (PID: 1440)
Creates files or folders in the user directory
- pdfskills.exe (PID: 1440)
Reads the machine GUID from the registry
- pdfskills.exe (PID: 1440)
Reads the computer name
- pdfskills.exe (PID: 1440)
Disables trace logs
- pdfskills.exe (PID: 1440)
Reads Environment values
- pdfskills.exe (PID: 1440)
Checks proxy server information
- pdfskills.exe (PID: 1440)
The process uses the downloaded file
- powershell.exe (PID: 4464)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 4464)
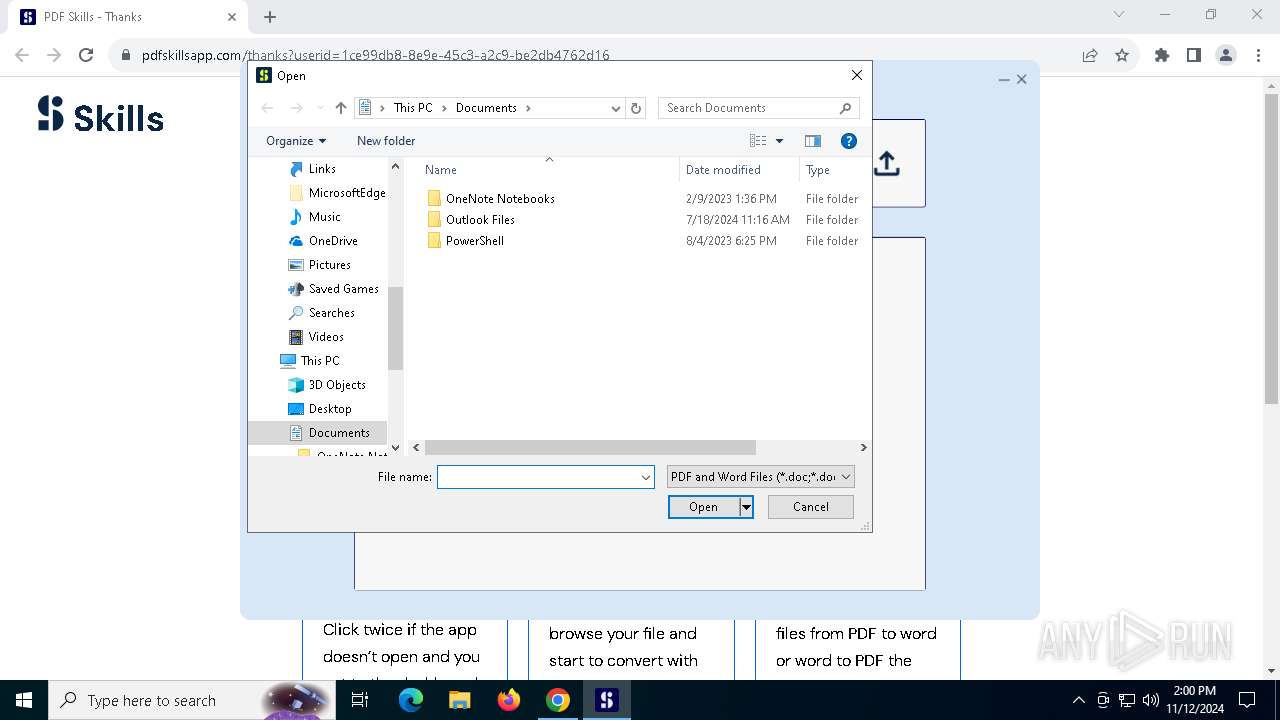
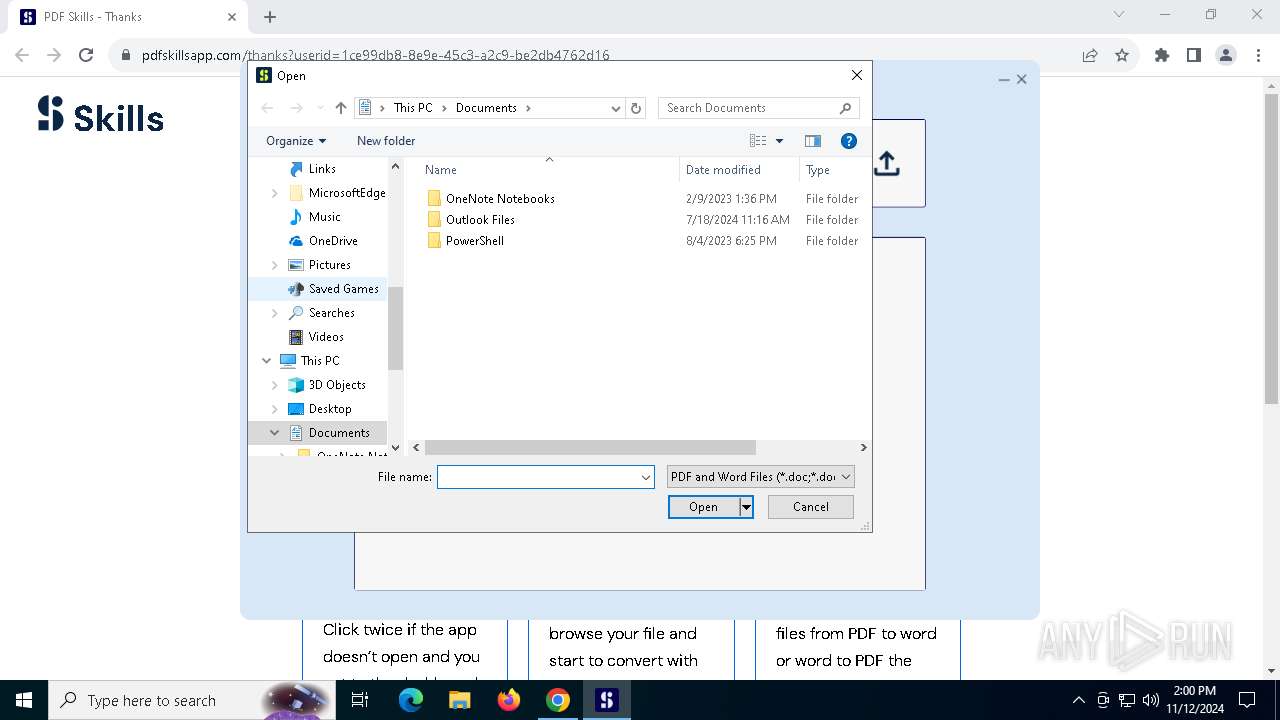
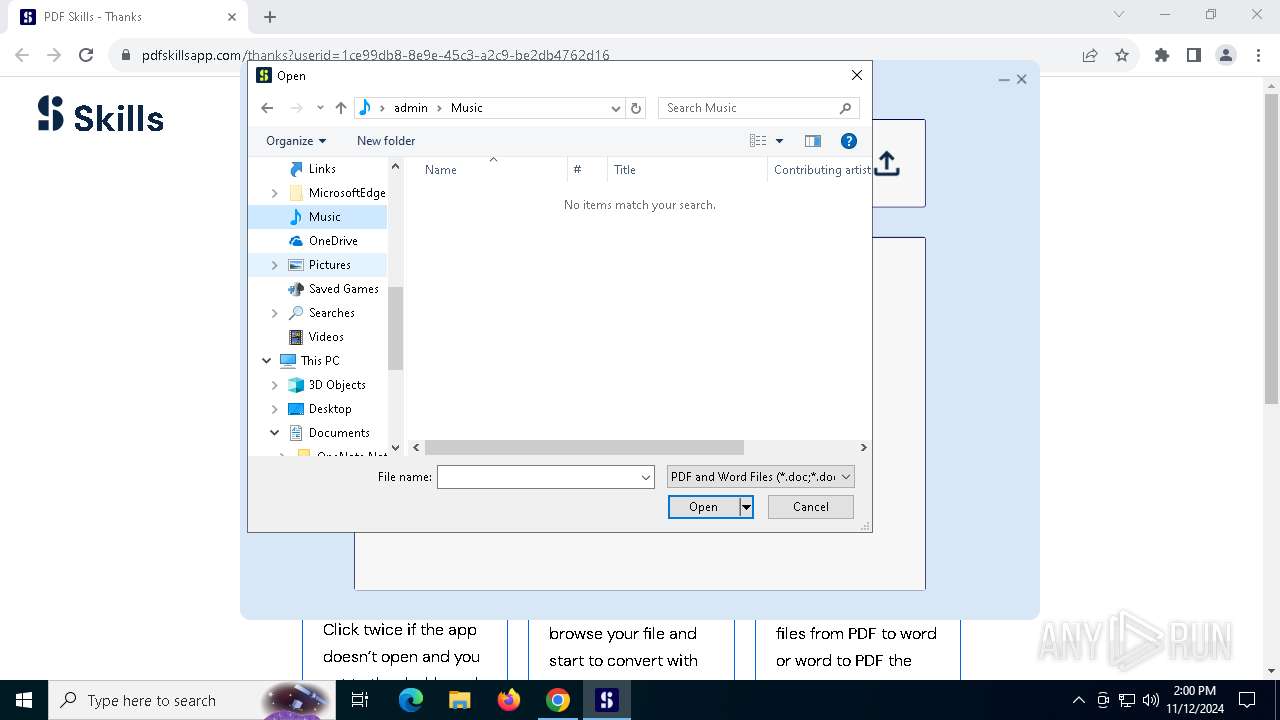
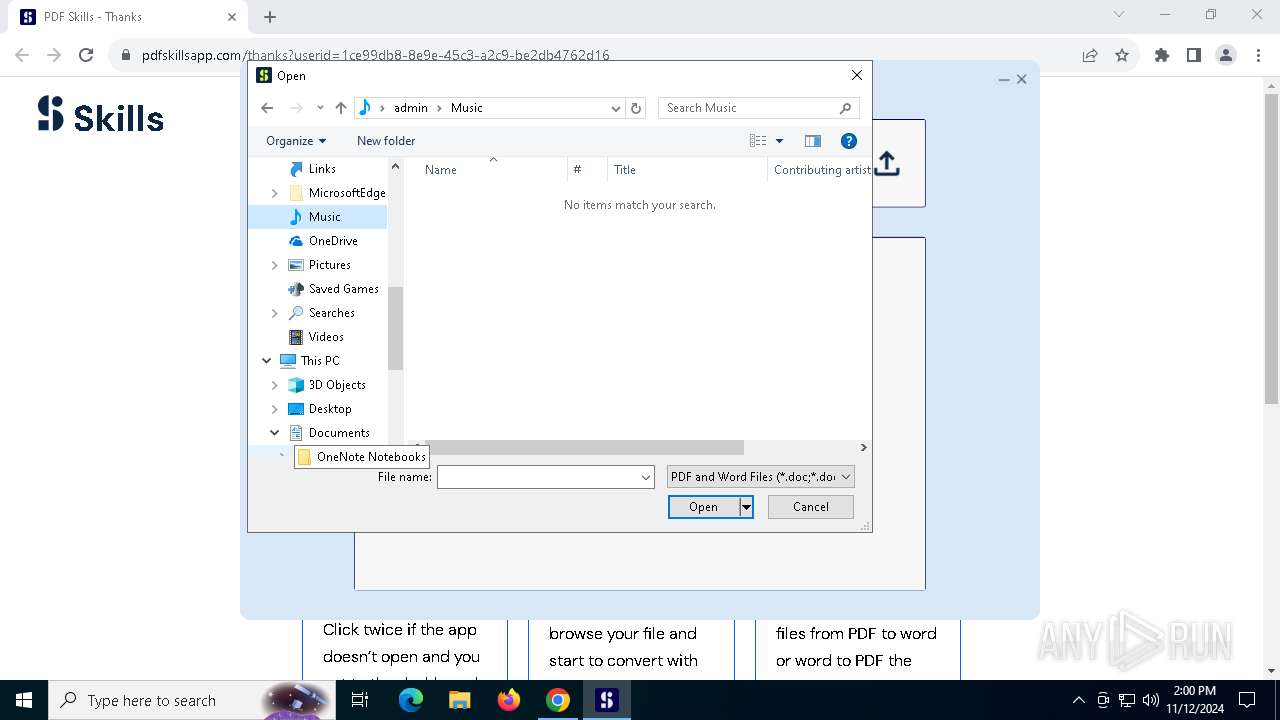
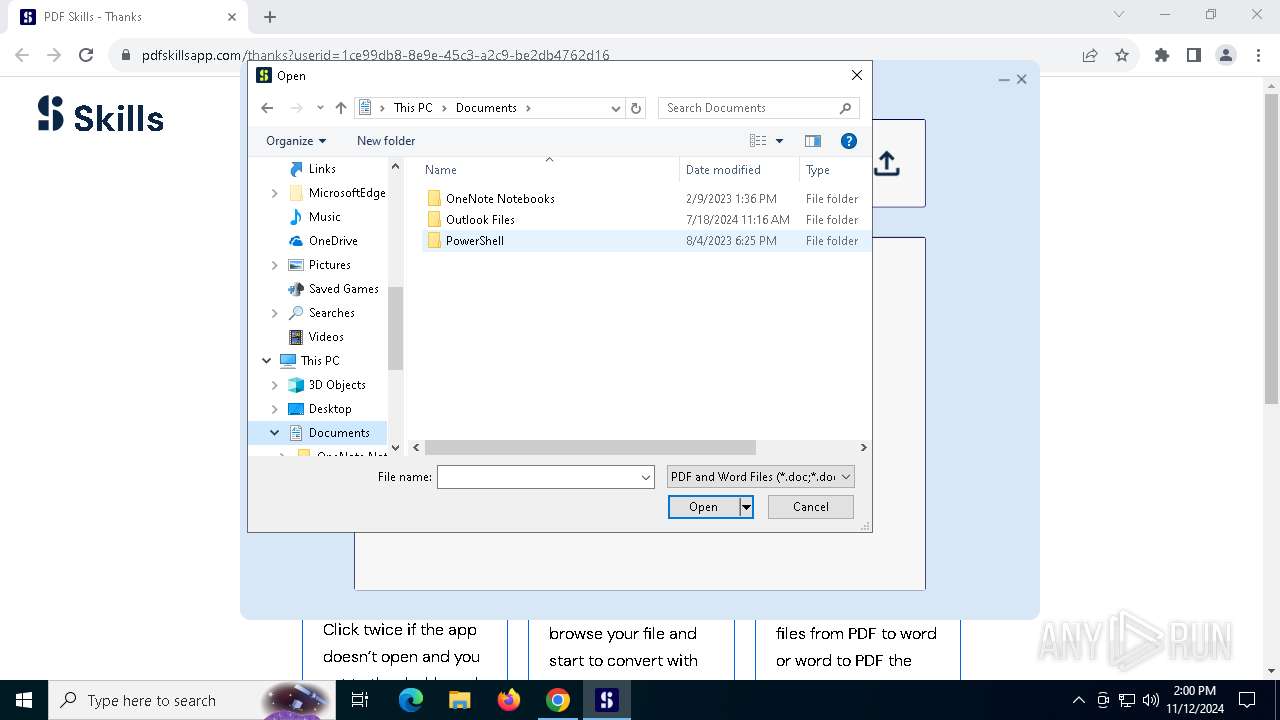
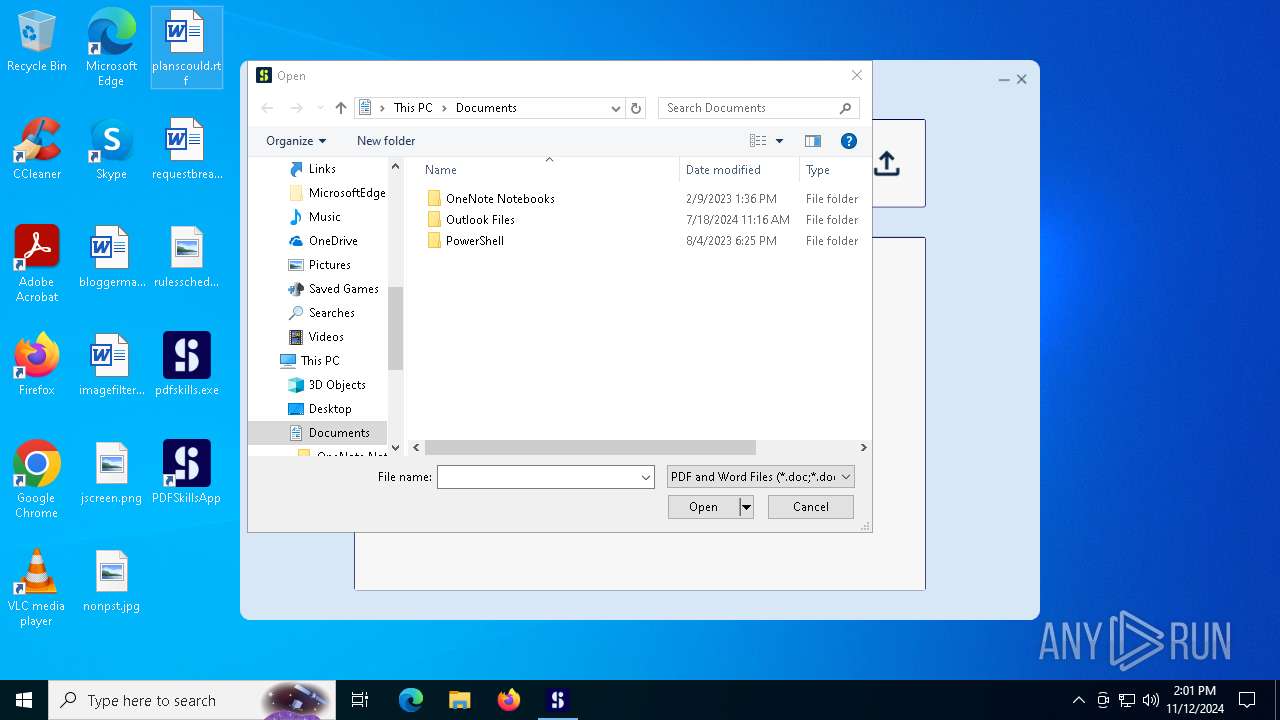
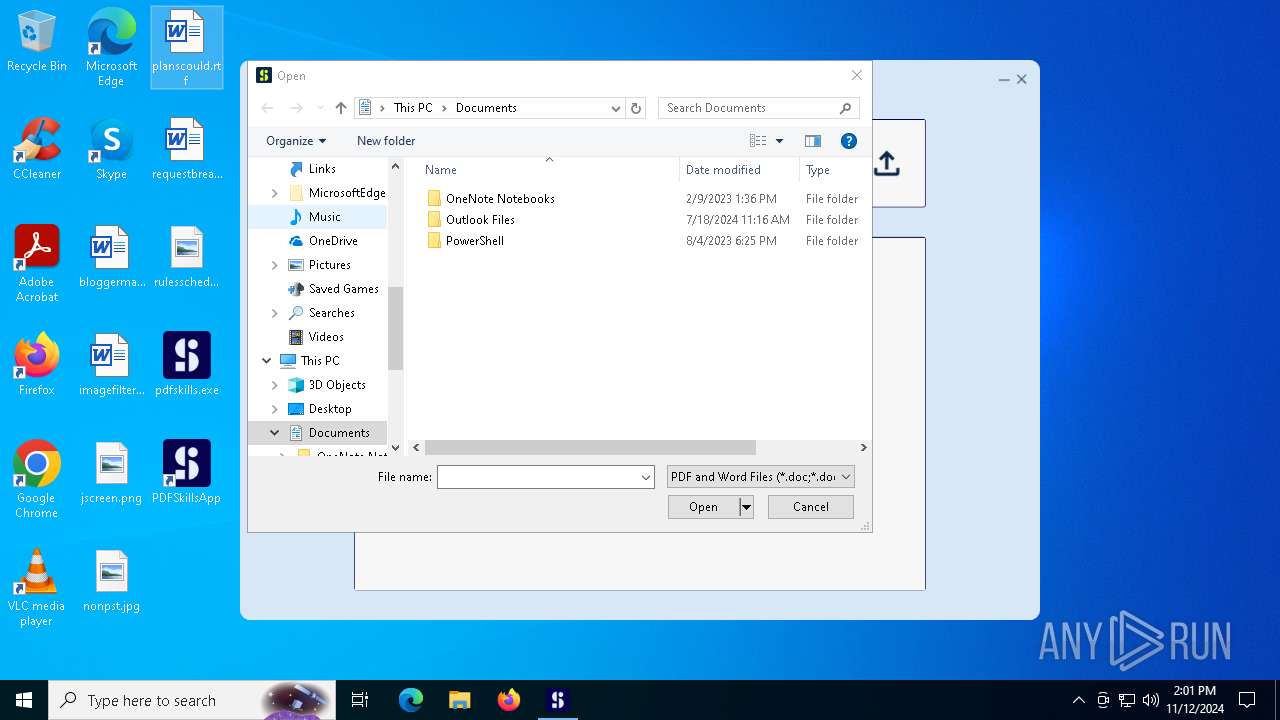
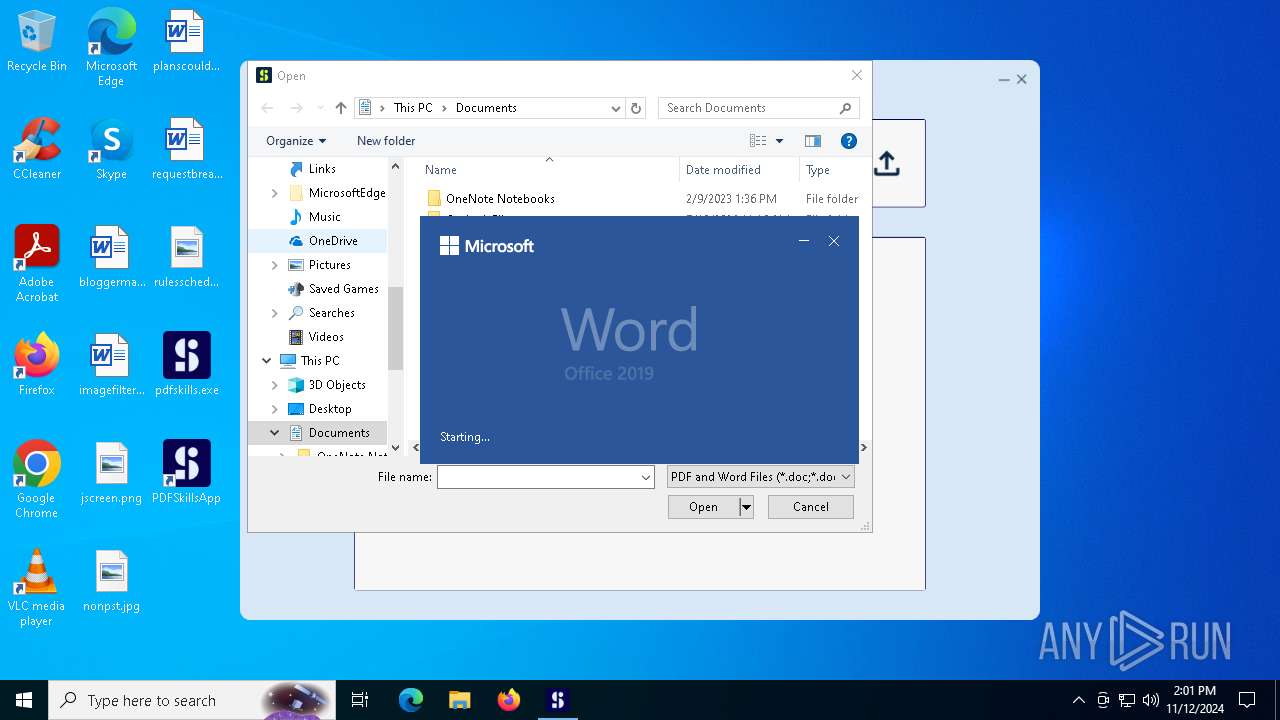
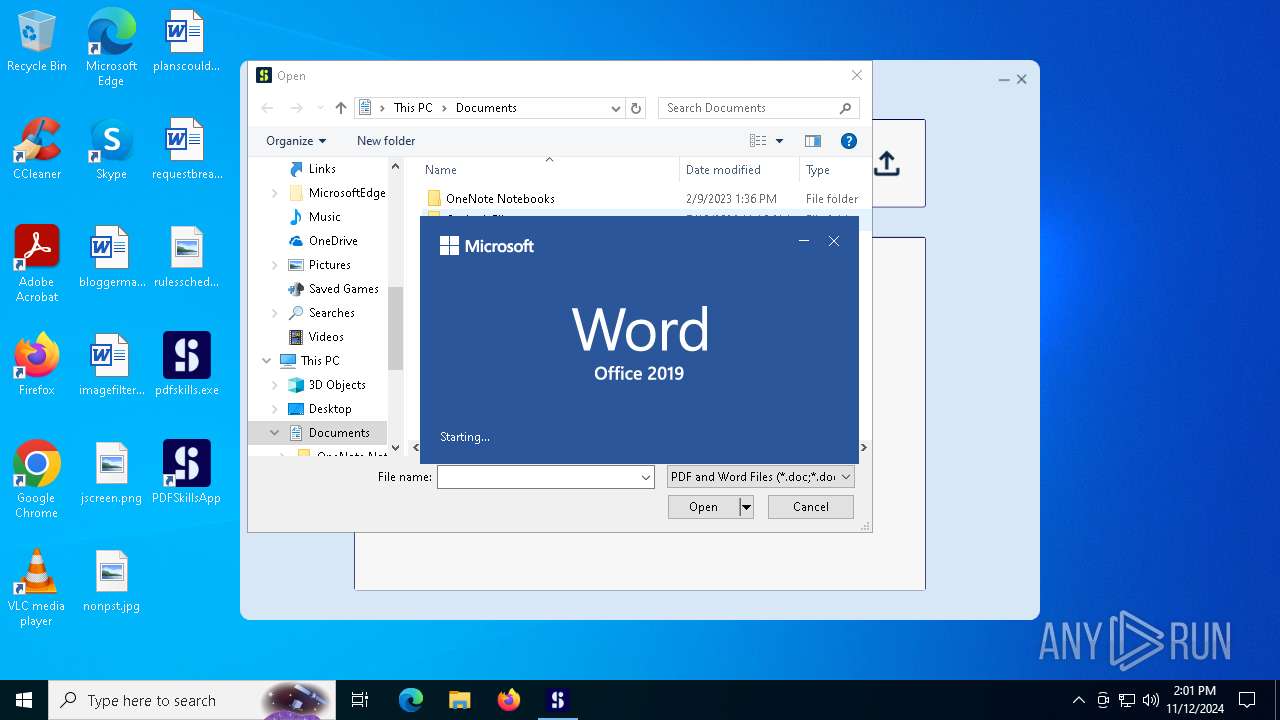
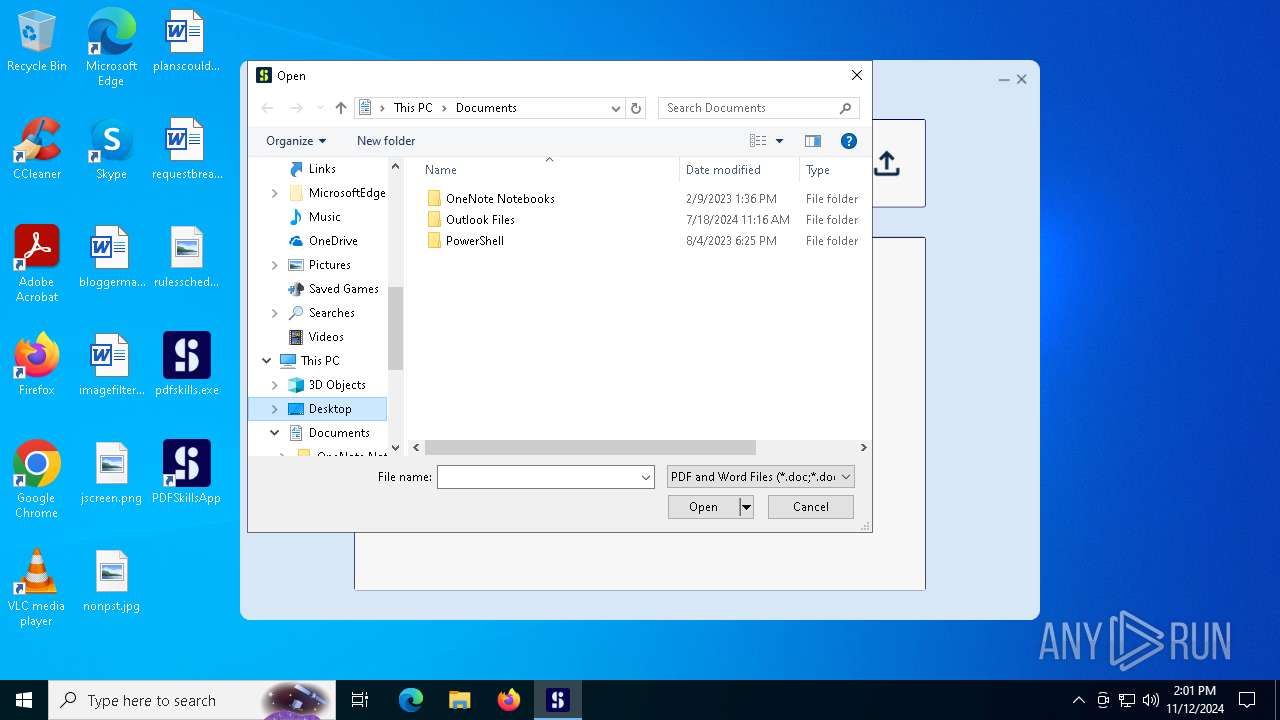
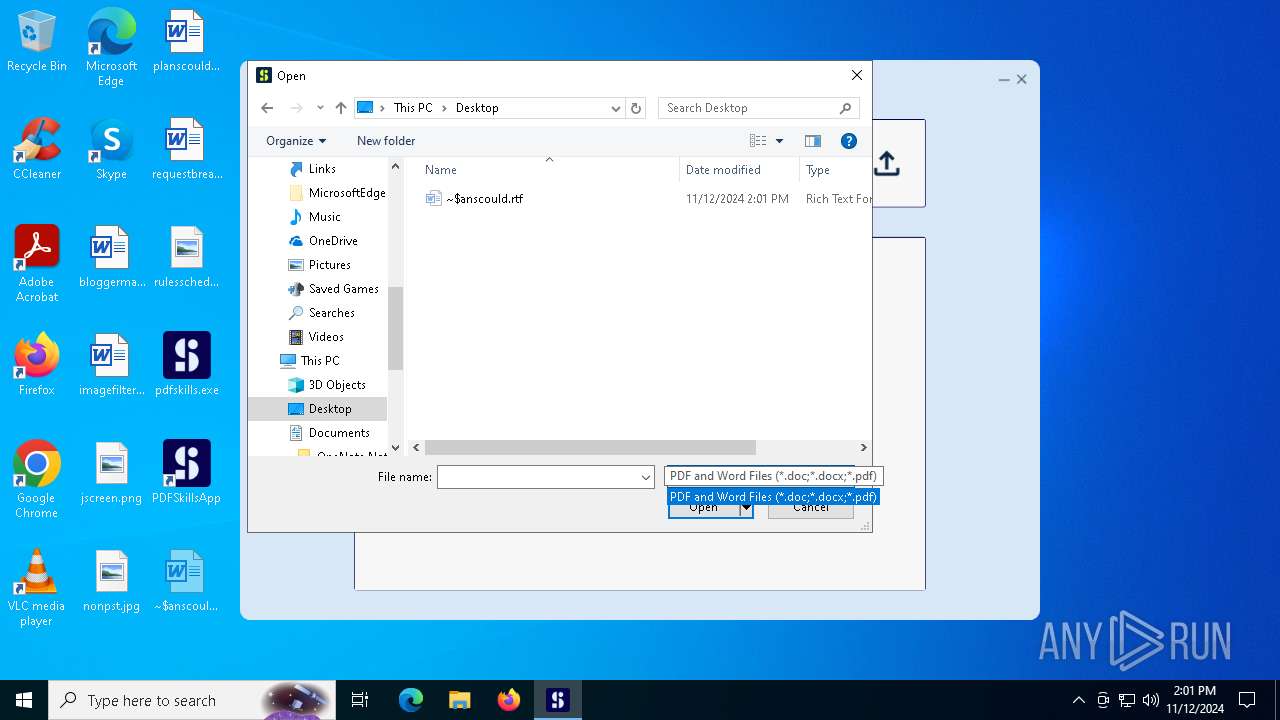
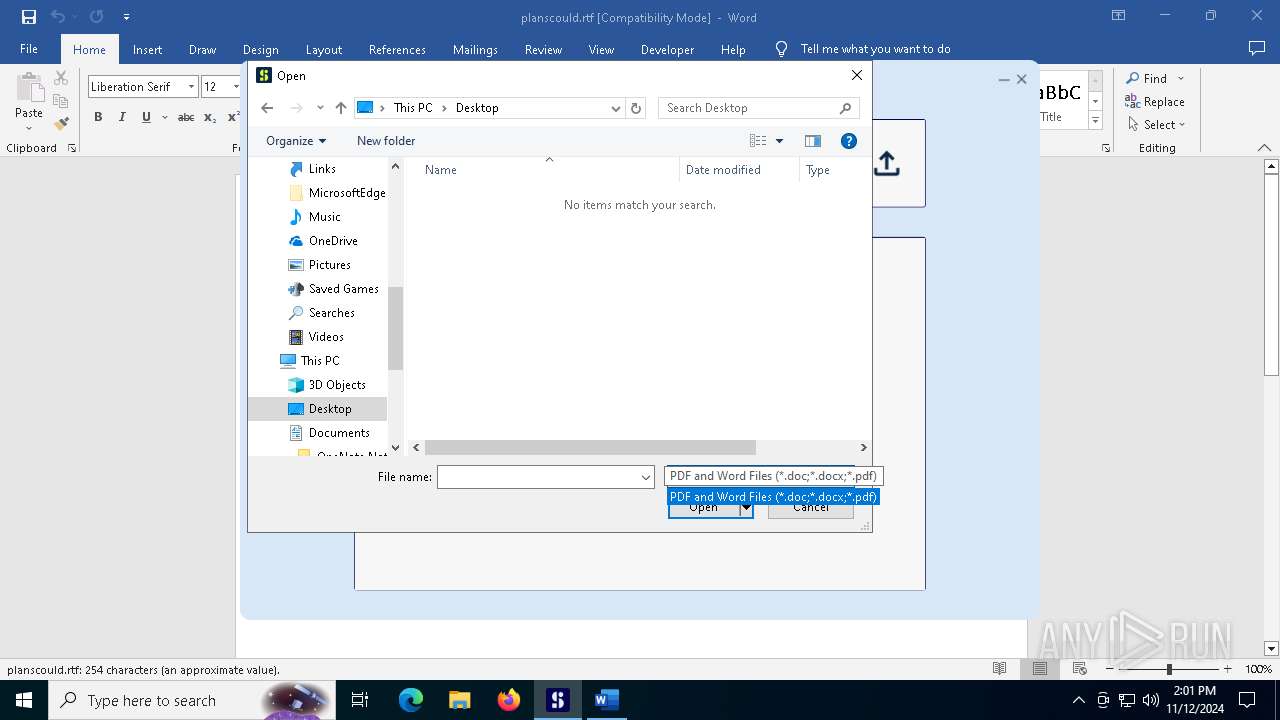
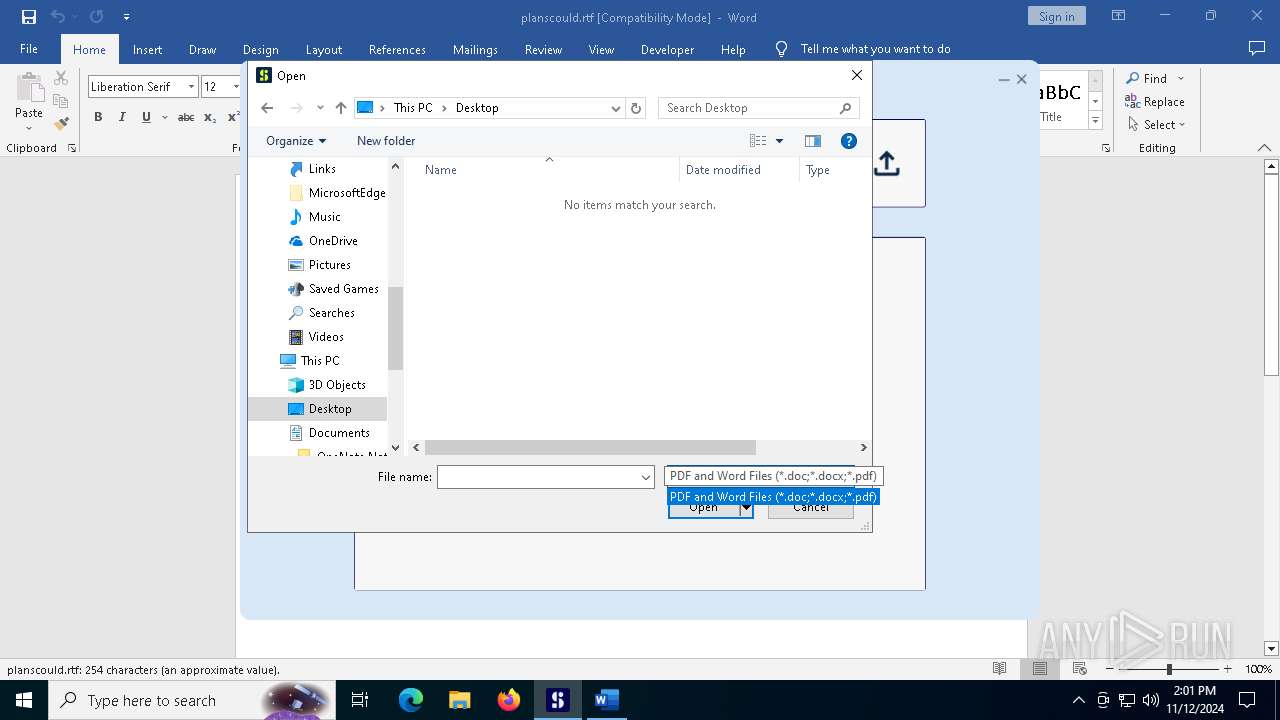
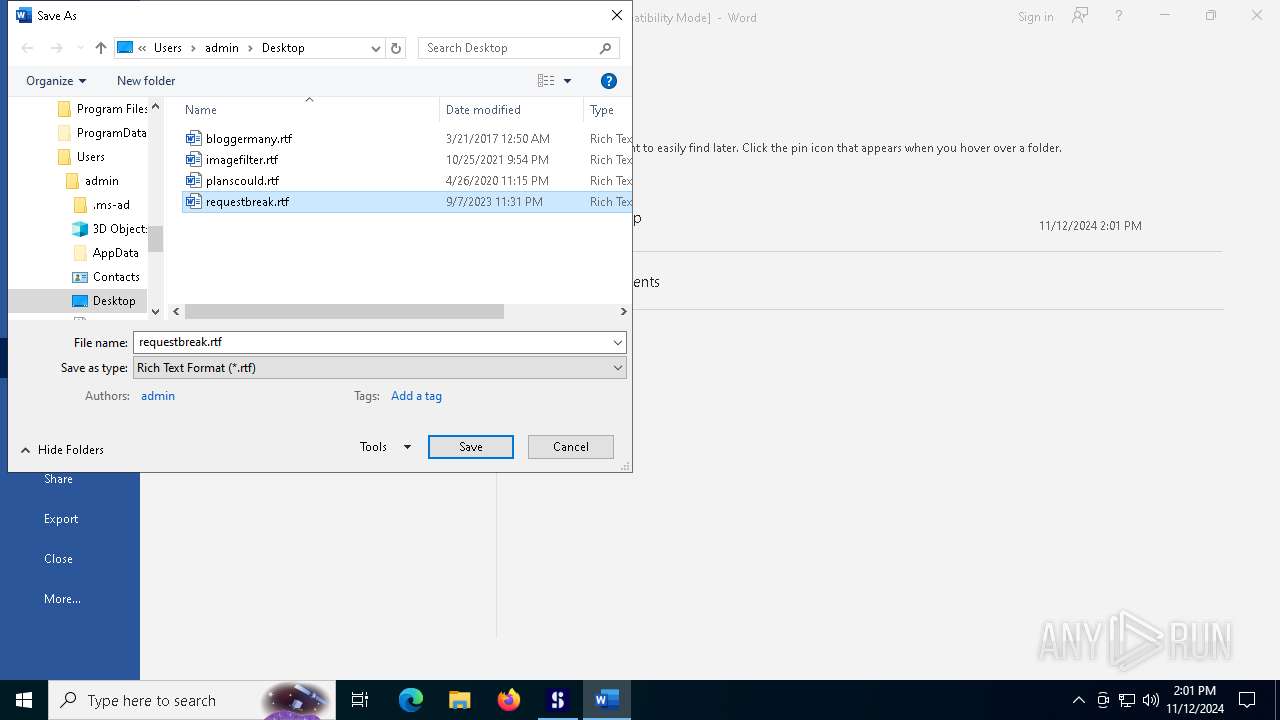
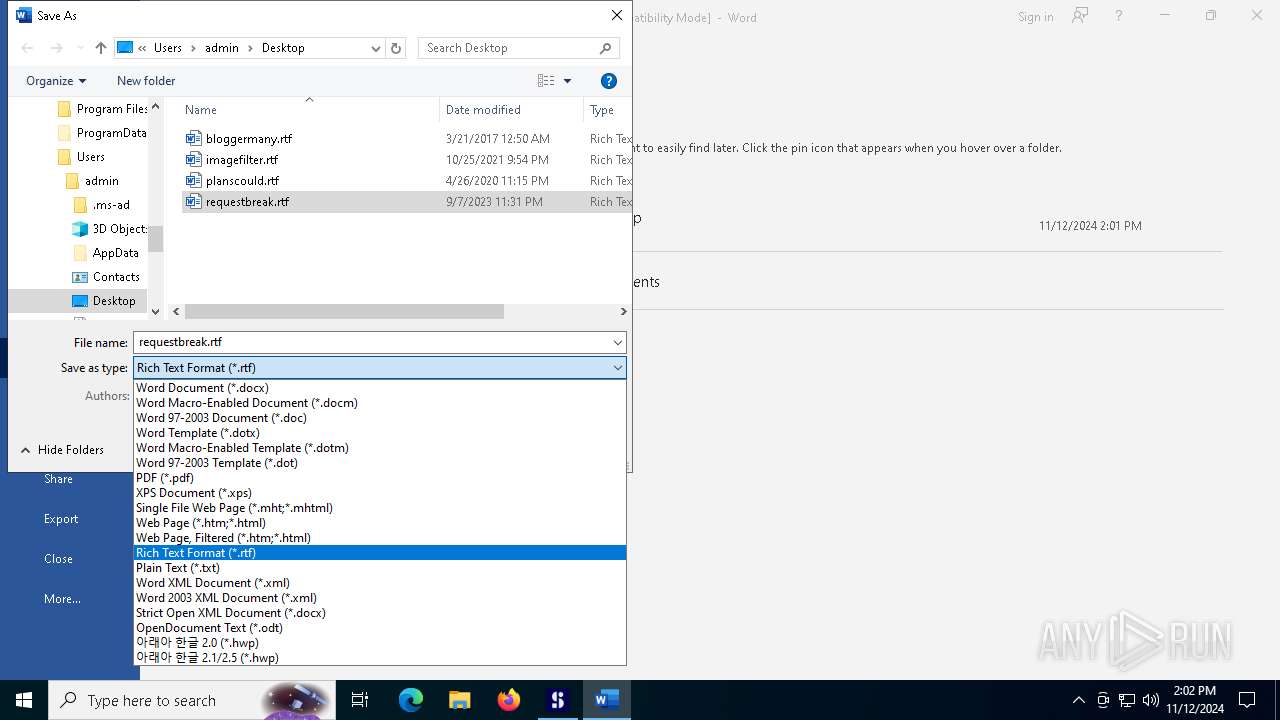
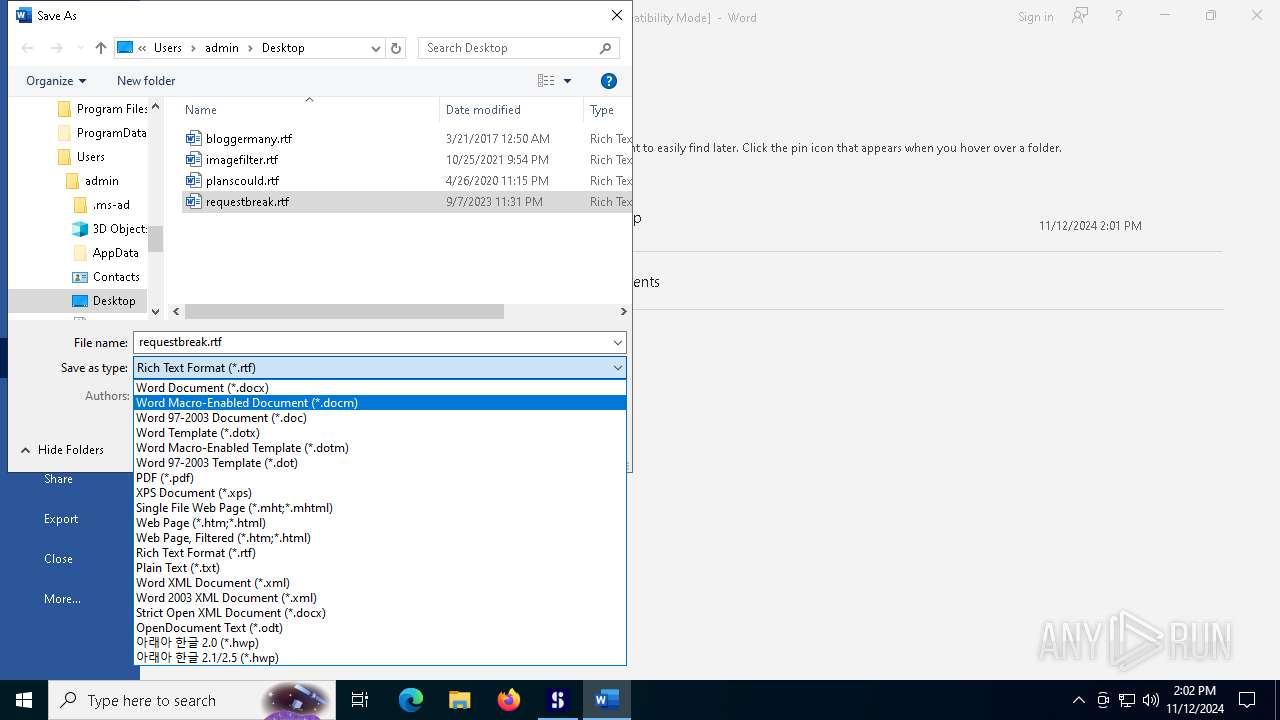
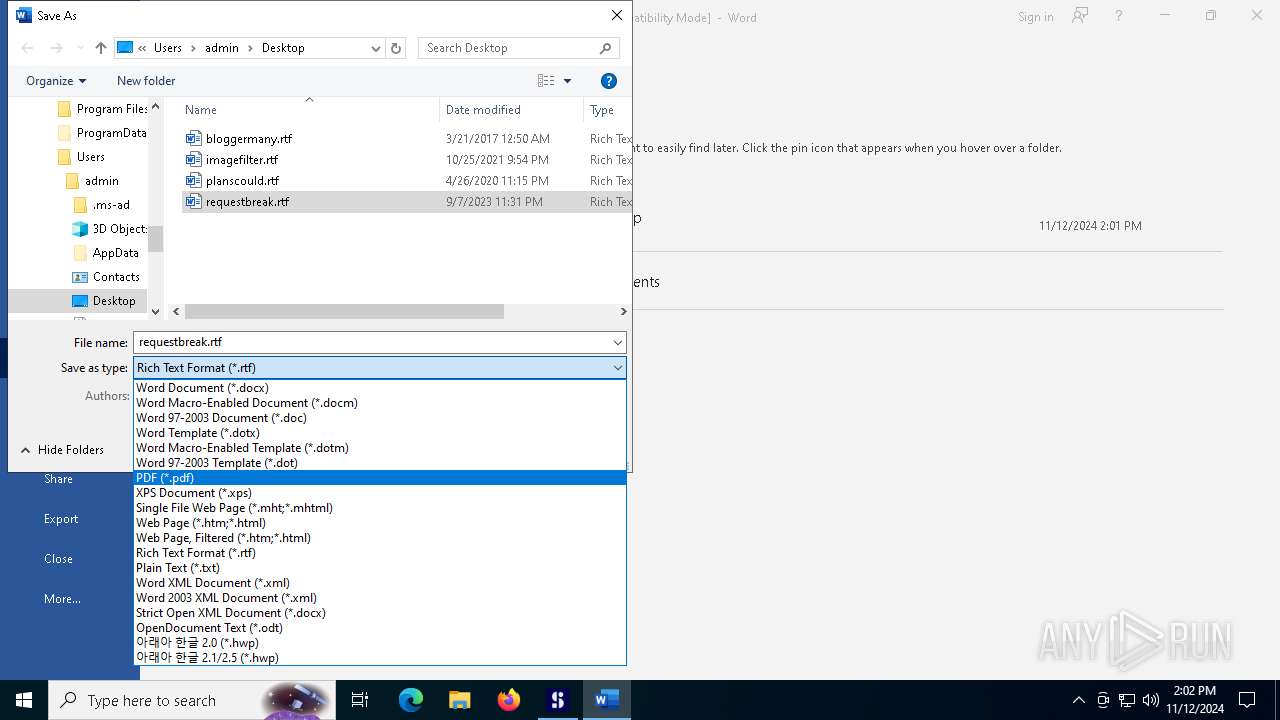
Manual execution by a user
- WINWORD.EXE (PID: 7452)
Application launched itself
- chrome.exe (PID: 7568)
- Acrobat.exe (PID: 6760)
- AcroCEF.exe (PID: 6888)
Reads the software policy settings
- pdfskills.exe (PID: 1440)
Sends debugging messages
- Acrobat.exe (PID: 1500)
- WINWORD.EXE (PID: 7452)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2045:06:10 17:16:52+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 48 |
| CodeSize: | 2272768 |
| InitializedDataSize: | 17408 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x0000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 247.8.41.102 |
| ProductVersionNumber: | 247.8.41.102 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | PDFSkills |
| FileVersion: | 247.8.41.102 |
| InternalName: | PDFSkills.exe |
| LegalCopyright: | Copyright © 2015-2023 RED ROOT All rights reserved |
| LegalTrademarks: | - |
| OriginalFileName: | PDFSkills.exe |
| ProductName: | PDFSkills |
| ProductVersion: | 247.8.41.102 |
| AssemblyVersion: | 247.8.41.102 |
Total processes
181
Monitored processes
43
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 616 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=3444 --field-trial-handle=1944,i,12692758985808166024,5010466715472422569,262144 --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1376 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=6020 --field-trial-handle=1944,i,12692758985808166024,5010466715472422569,262144 --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
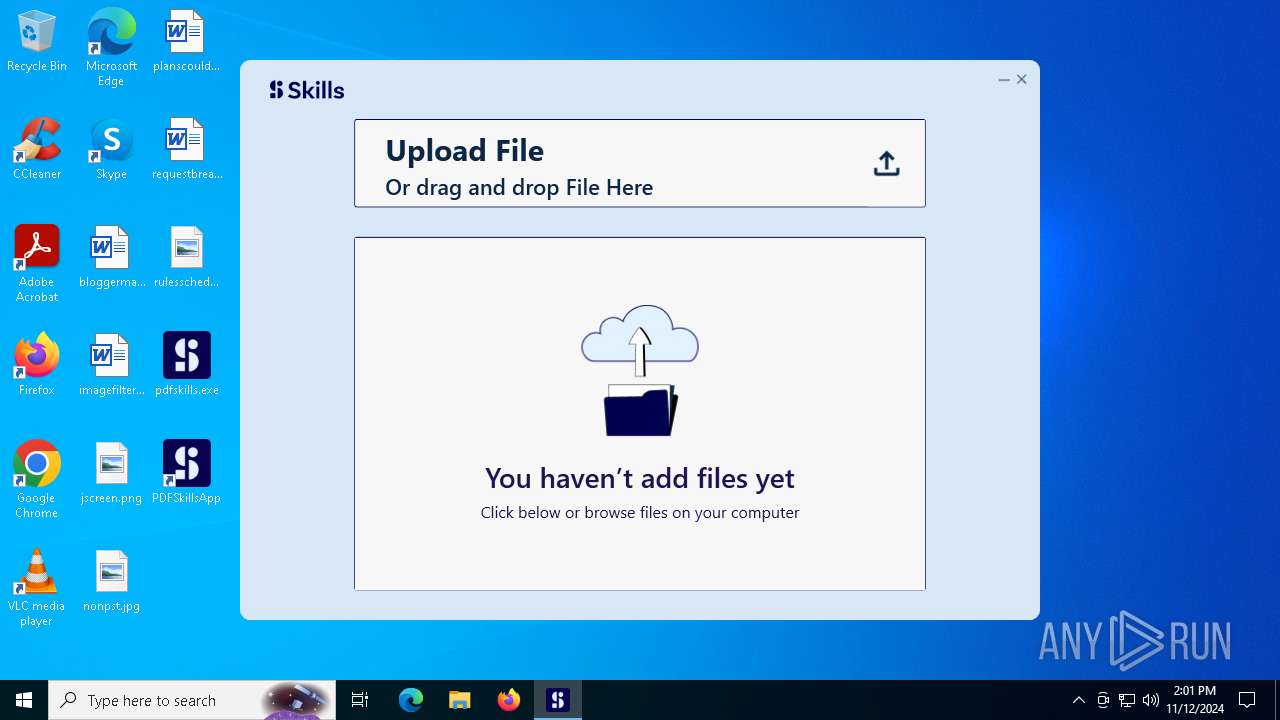
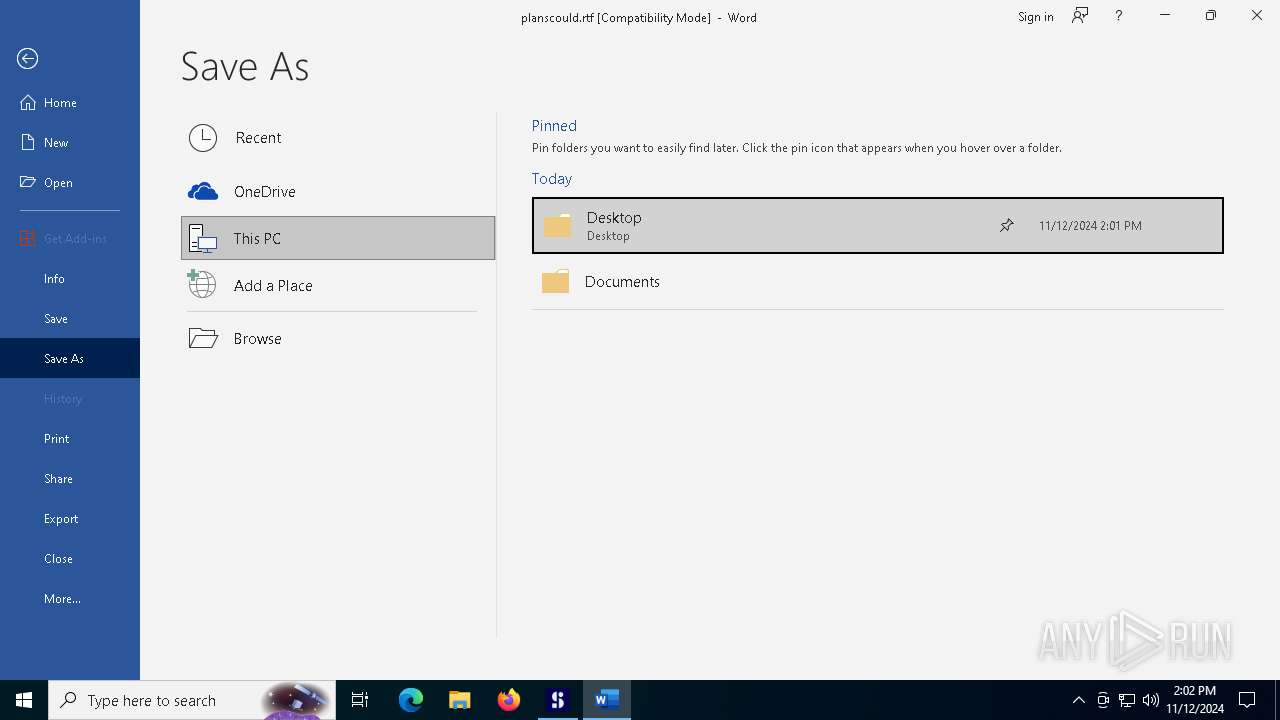
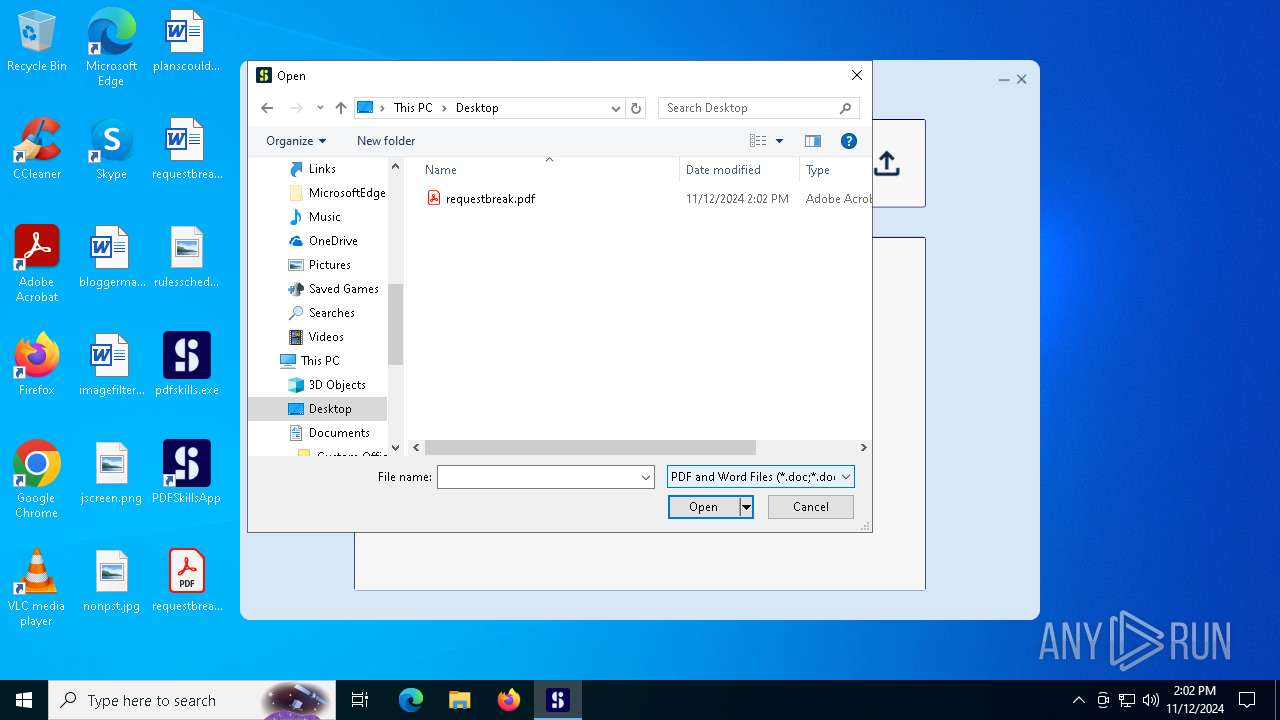
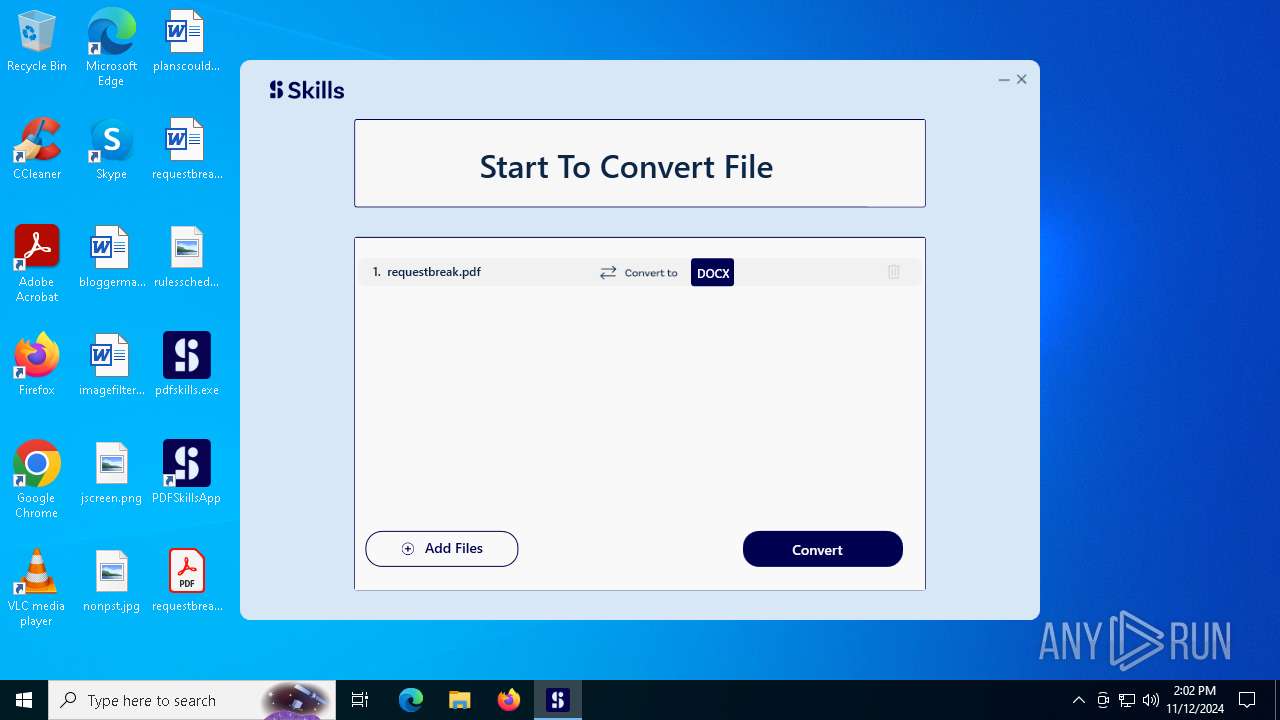
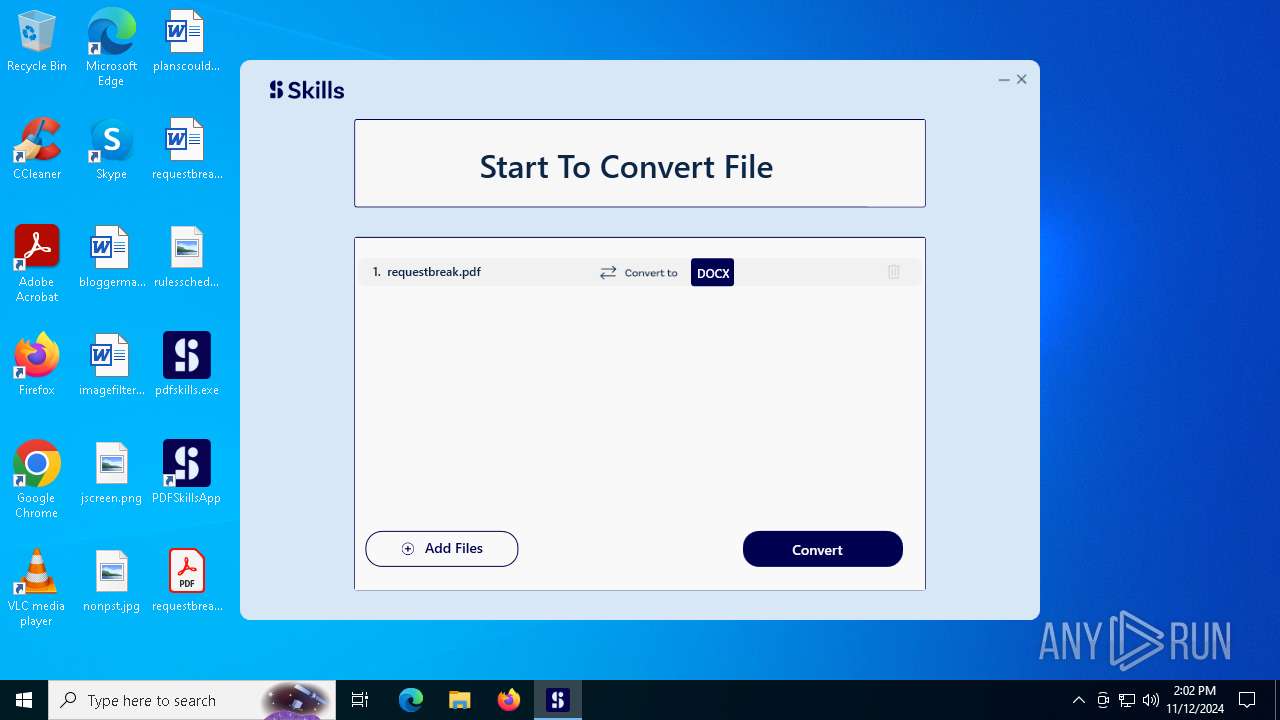
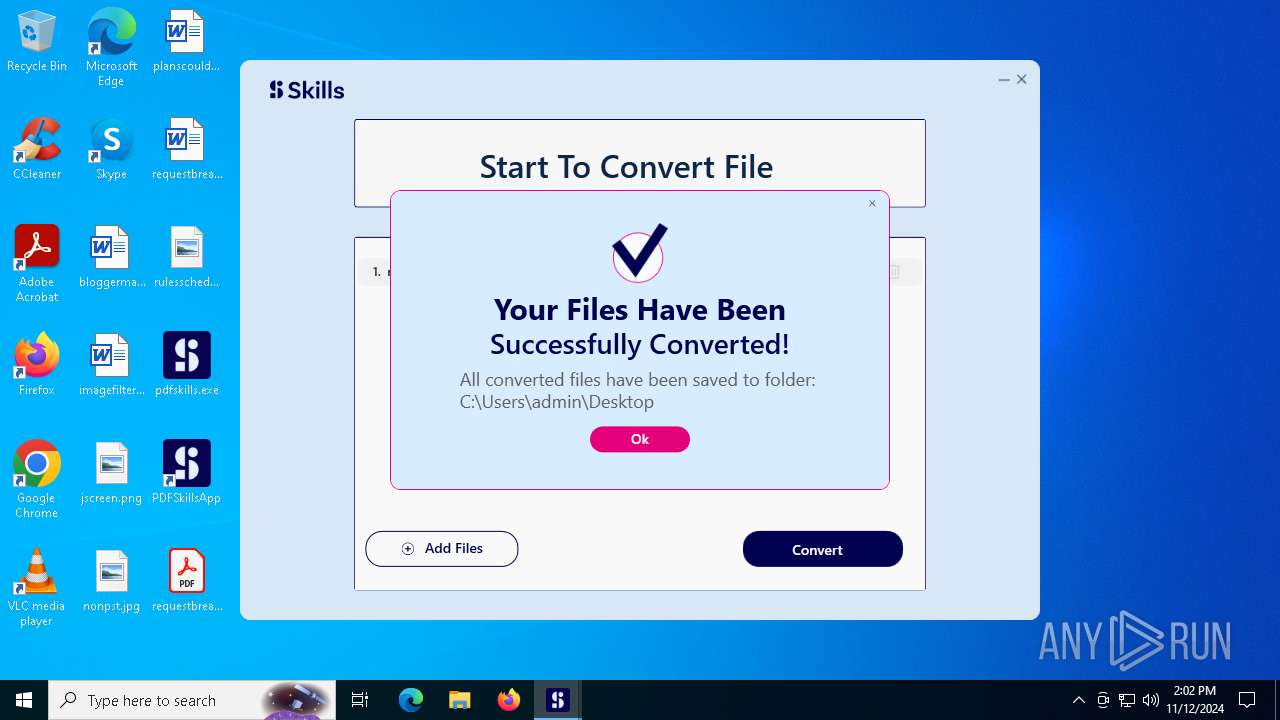
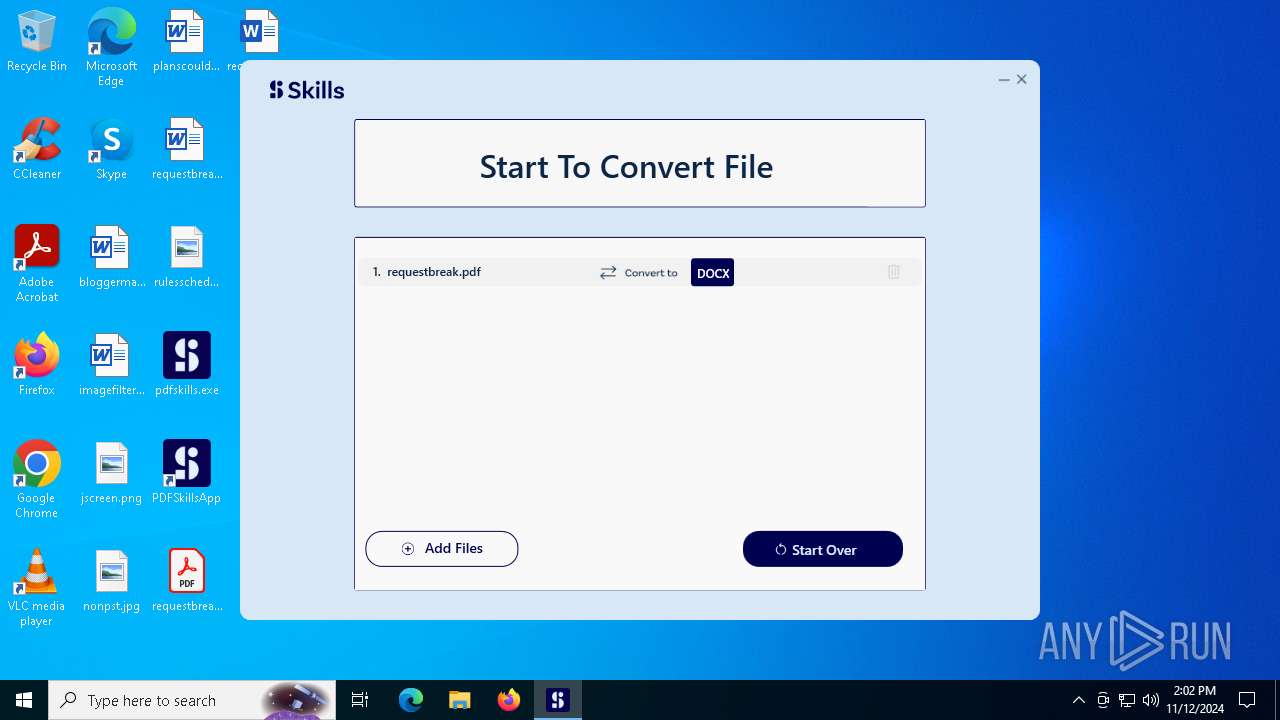
| 1440 | "C:\Users\admin\Desktop\pdfskills.exe" | C:\Users\admin\Desktop\pdfskills.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: PDFSkills Exit code: 0 Version: 247.8.41.102 Modules
| |||||||||||||||
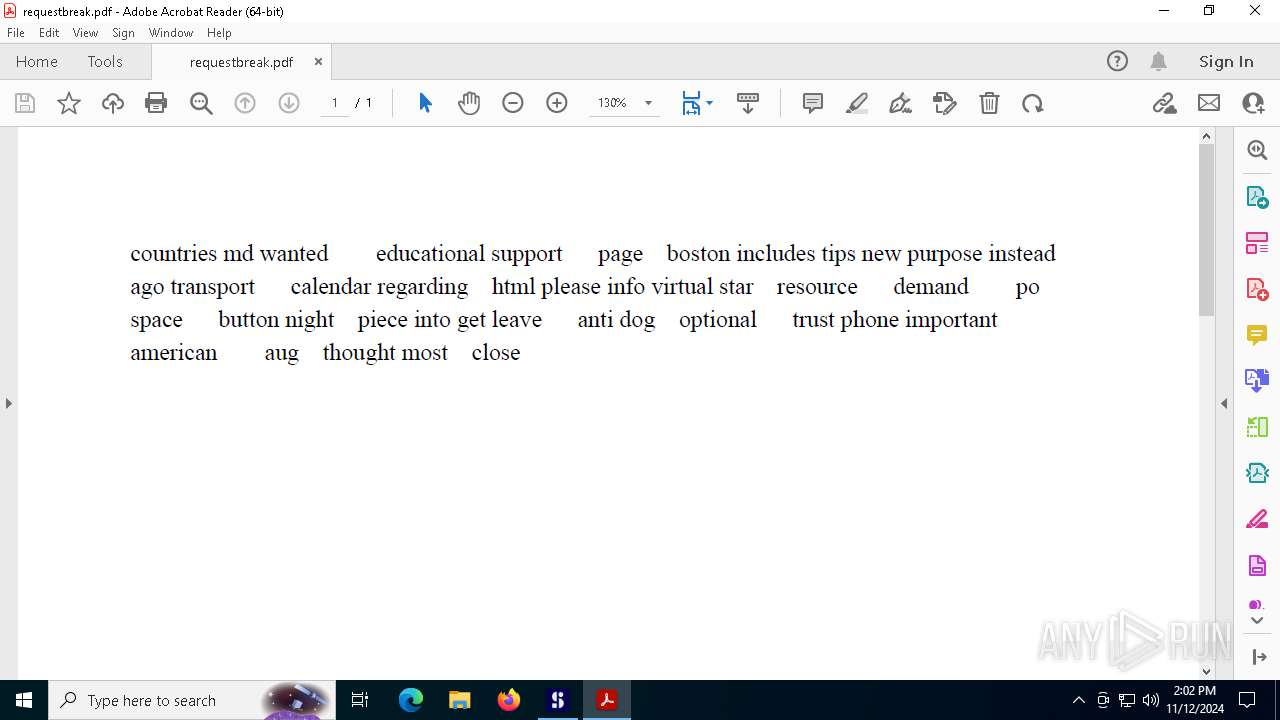
| 1500 | "C:\Program Files\Adobe\Acrobat DC\Acrobat\Acrobat.exe" --type=renderer /prefetch:1 "C:\Users\admin\Desktop\requestbreak.pdf" | C:\Program Files\Adobe\Acrobat DC\Acrobat\Acrobat.exe | — | Acrobat.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe Acrobat Exit code: 1 Version: 23.1.20093.0 Modules
| |||||||||||||||
| 1732 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5636 --field-trial-handle=1944,i,12692758985808166024,5010466715472422569,262144 --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
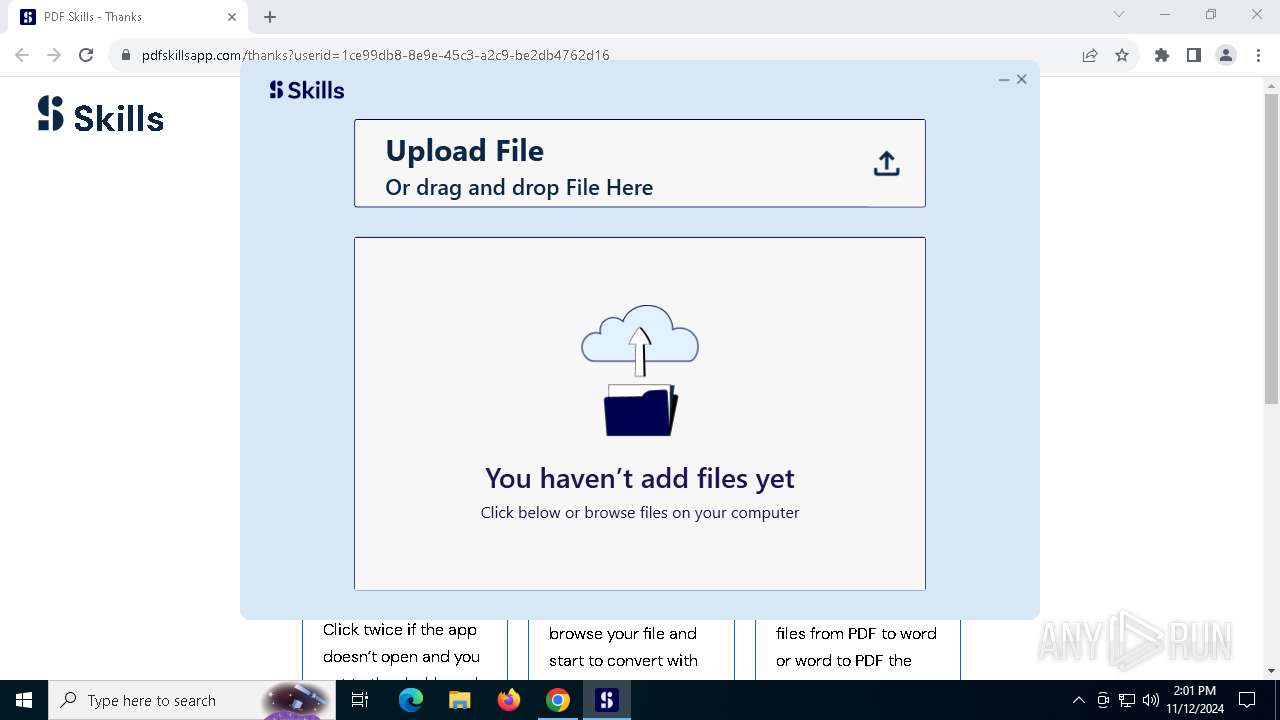
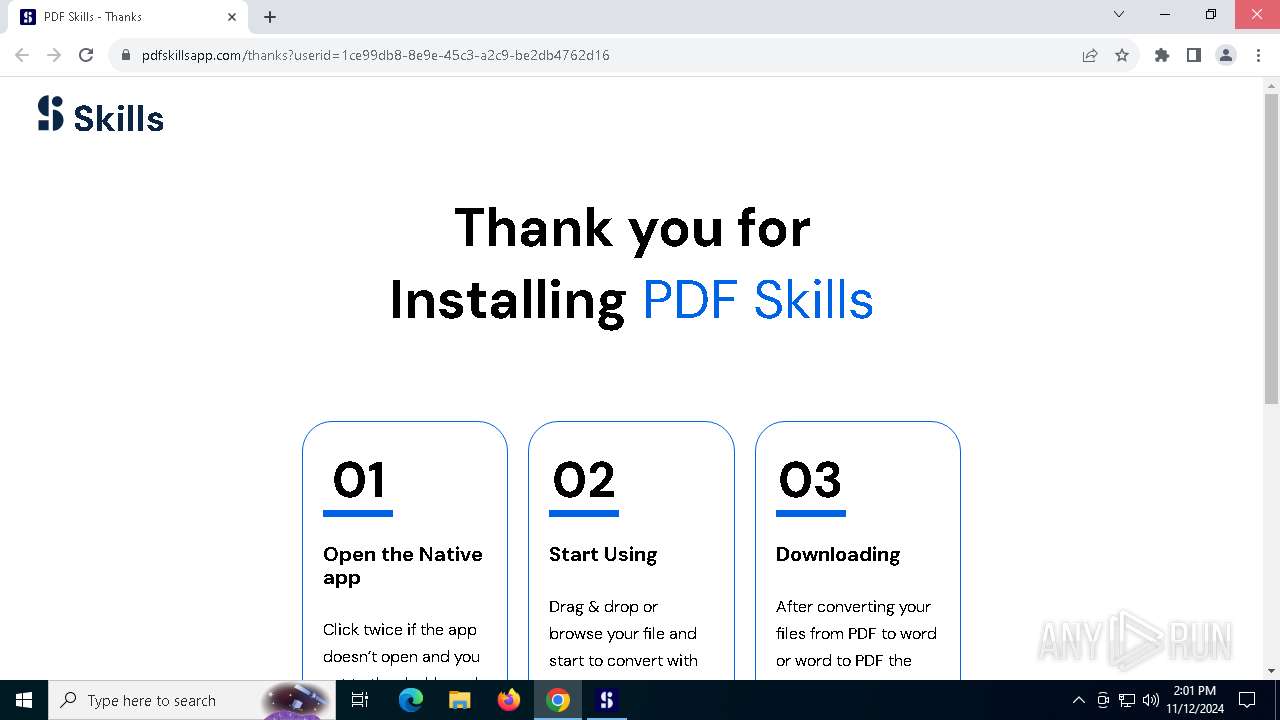
| 2236 | "C:\Users\admin\AppData\Local\PDFSkills\PDFSkillsApp.exe" | C:\Users\admin\AppData\Local\PDFSkills\PDFSkillsApp.exe | pdfskills.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: PDFSkillsApp Exit code: 0 Version: 56.20.0.1 Modules
| |||||||||||||||
| 3864 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5992 --field-trial-handle=1944,i,12692758985808166024,5010466715472422569,262144 --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 4340 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.ProcessorMetrics --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5172 --field-trial-handle=1944,i,12692758985808166024,5010466715472422569,262144 --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 4436 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=3444 --field-trial-handle=1944,i,12692758985808166024,5010466715472422569,262144 --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 4464 | "powershell.exe" -ep RemoteSigned -File "C:\Users\admin\AppData\Local\PDFSkills\update_task_ad.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | pdfskills.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
64 309
Read events
62 224
Write events
1 935
Delete events
150
Modification events
| (PID) Process: | (1440) pdfskills.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\pdfskills_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1440) pdfskills.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\pdfskills_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (1440) pdfskills.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\pdfskills_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (1440) pdfskills.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\pdfskills_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (1440) pdfskills.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\pdfskills_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (1440) pdfskills.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\pdfskills_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (1440) pdfskills.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\pdfskills_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (1440) pdfskills.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\pdfskills_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1440) pdfskills.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\pdfskills_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (1440) pdfskills.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\pdfskills_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
36
Suspicious files
322
Text files
157
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
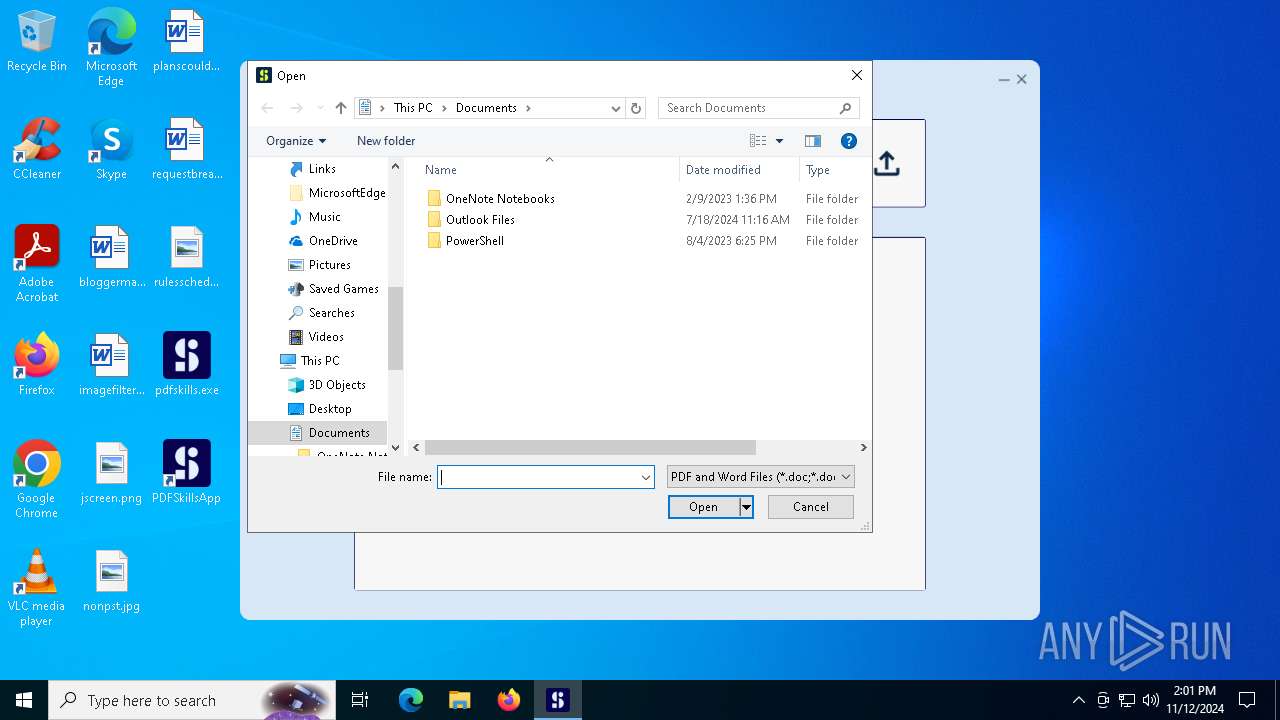
| 1440 | pdfskills.exe | C:\Users\admin\AppData\Local\PDFSkills\skillsUserId.txt | text | |
MD5:4E9CD6B46F97DEB05E22B66A4598AB12 | SHA256:283AC91DB741B576CA84AF3796F44E2FA979D79B2F4F3883633E987EBFCF4B9F | |||
| 1440 | pdfskills.exe | C:\Users\admin\AppData\Local\PDFSkills\vcruntime140.dll | executable | |
MD5:E9B690FBE5C4B96871214379659DD928 | SHA256:A06C9EA4F815DAC75D2C99684D433FBFC782010FAE887837A03F085A29A217E8 | |||
| 1440 | pdfskills.exe | C:\Users\admin\AppData\Local\PDFSkills\msvcp140_1.dll | executable | |
MD5:7B0A25EEE764D8747F02CB3ED980F07A | SHA256:1274292F4CC655F295272B37E08A9683B8BB8C419B61EA2E1F43EB4D22F02F90 | |||
| 1440 | pdfskills.exe | C:\Users\admin\AppData\Local\PDFSkills\Libraries.dll | executable | |
MD5:08B1B14B4573E95BDB5E6DDCA74D2513 | SHA256:EE803D254AF9E2FE4781E3335164D24BEC31512A229E607A3A93254D47177F52 | |||
| 4464 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ozsxqzwg.pk3.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1440 | pdfskills.exe | C:\Users\admin\AppData\Local\PDFSkills\update_task_ad.ps1 | text | |
MD5:FA05939FDF91FE62329AF5B16AF33D14 | SHA256:C7CBC315F533F124FD6ED468F7E333A276A1891CD4C6A5B720058D54E053EC32 | |||
| 4464 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_1evpwvrn.f4f.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4464 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:004696345D01443652122CA79EC582E5 | SHA256:ED79DC3ECA9EC686F96BCAD2C13927A3E685B3B03C90EA625C4BA4406F8F3B01 | |||
| 1440 | pdfskills.exe | C:\Users\admin\AppData\Local\PDFSkills\Updates.zip | compressed | |
MD5:906BA67CCE42C628A2EB3A9060A99E67 | SHA256:E1BAF755EFA1B73C7C6DCEF6280D83E478EB8AB0EBA4D5CD92B1F8014D36060B | |||
| 1440 | pdfskills.exe | C:\Users\admin\AppData\Local\PDFSkills\concrt140.dll | executable | |
MD5:9485D003573E0EAF7952AB23CC82EF7B | SHA256:5E0E8EAC57B86E2DE7CA7D6E8D34DDDEA602CE3660208FB53947A027635D59A1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
16
TCP/UDP connections
147
DNS requests
88
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5488 | MoUsoCoreWorker.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | US | binary | 312 b | whitelisted |
8152 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 418 b | whitelisted |
8152 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 408 b | whitelisted |
7452 | WINWORD.EXE | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | US | binary | 471 b | whitelisted |
6904 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | binary | 471 b | whitelisted |
7452 | WINWORD.EXE | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | US | binary | 471 b | whitelisted |
7452 | WINWORD.EXE | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicCodSigPCA_08-31-2010.crl | DE | binary | 564 b | whitelisted |
7452 | WINWORD.EXE | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/microsoftrootcert.crl | DE | binary | 767 b | whitelisted |
7452 | WINWORD.EXE | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicrosoftTimeStampPCA.crl | DE | binary | 519 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6944 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5488 | MoUsoCoreWorker.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5488 | MoUsoCoreWorker.exe | 23.52.120.96:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4020 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4360 | SearchApp.exe | 2.23.209.142:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
1440 | pdfskills.exe | 198.71.59.132:443 | val.skillcli.com | IONOS SE | US | unknown |
1552 | svchost.exe | 40.126.32.76:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
val.skillcli.com |
| unknown |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
th.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7728 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
7728 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
Process | Message |
|---|---|
WINWORD.EXE | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
WINWORD.EXE | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
WINWORD.EXE | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
WINWORD.EXE | Thumbnail Cache: Attempting to replace an entry that is in use
|