| download: | index.html |
| Full analysis: | https://app.any.run/tasks/704113aa-4480-4e94-8289-03f404864eff |
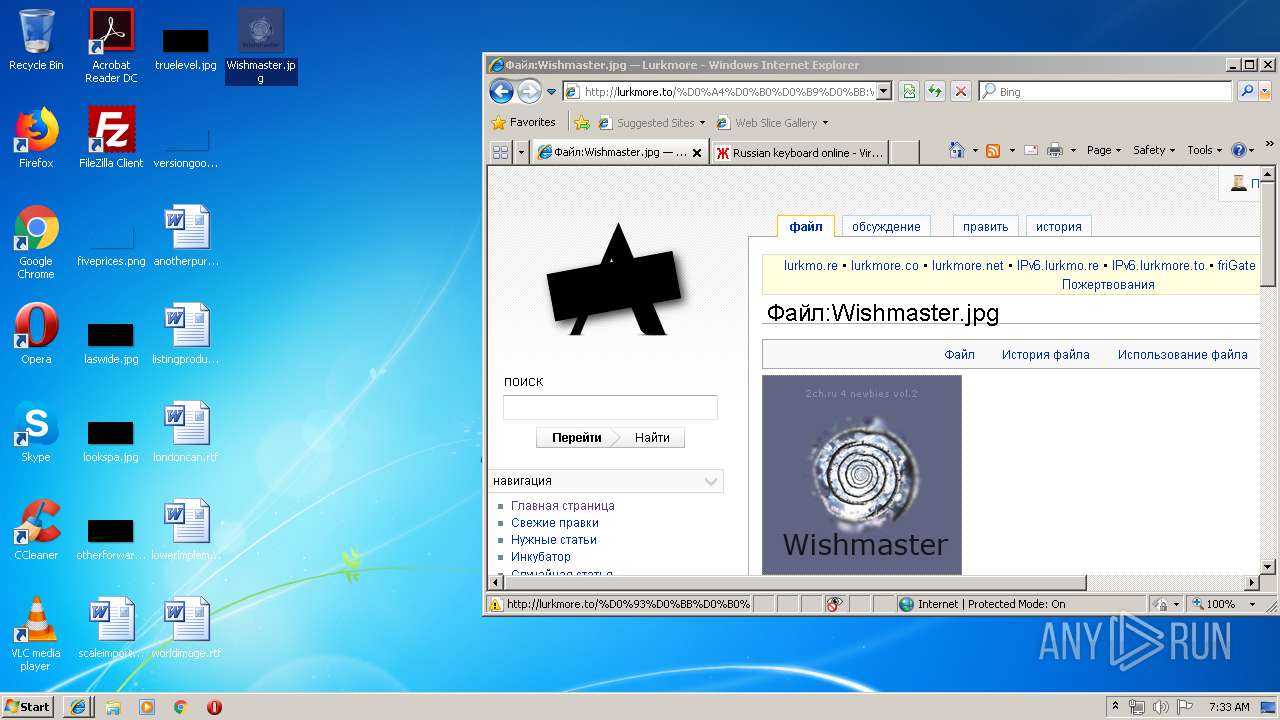
| Verdict: | Malicious activity |
| Analysis date: | August 18, 2019, 06:29:09 |
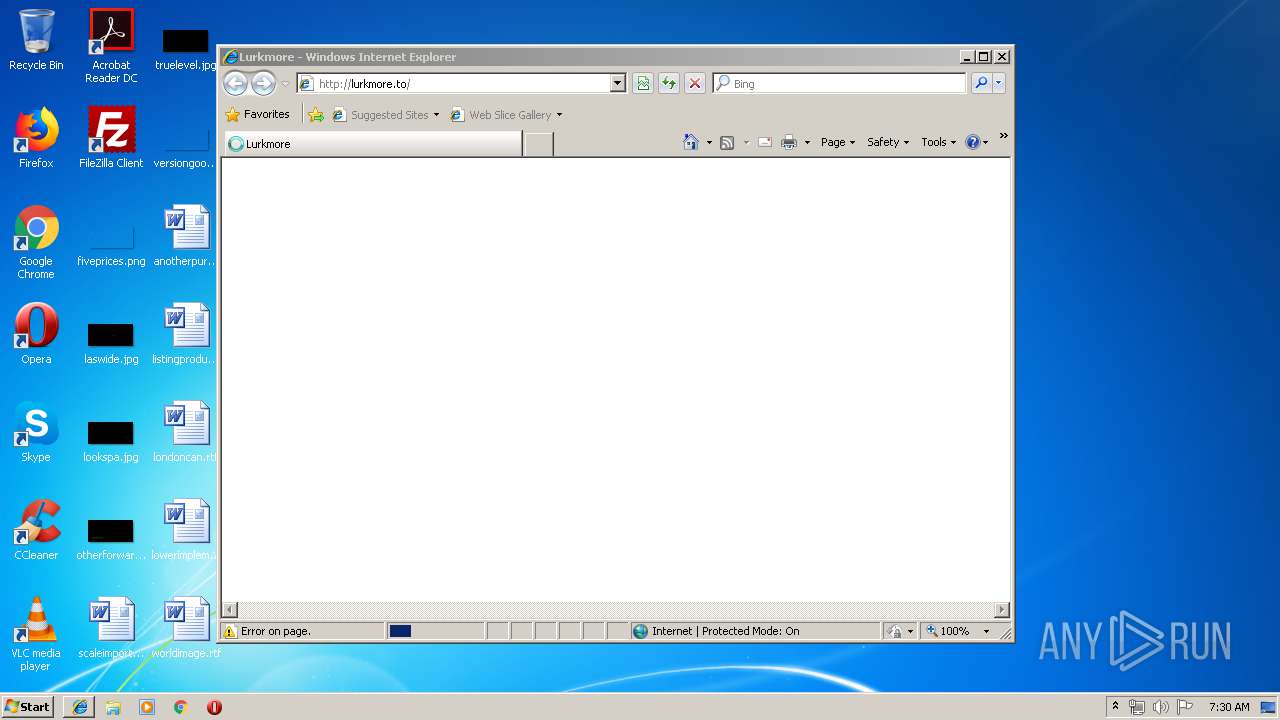
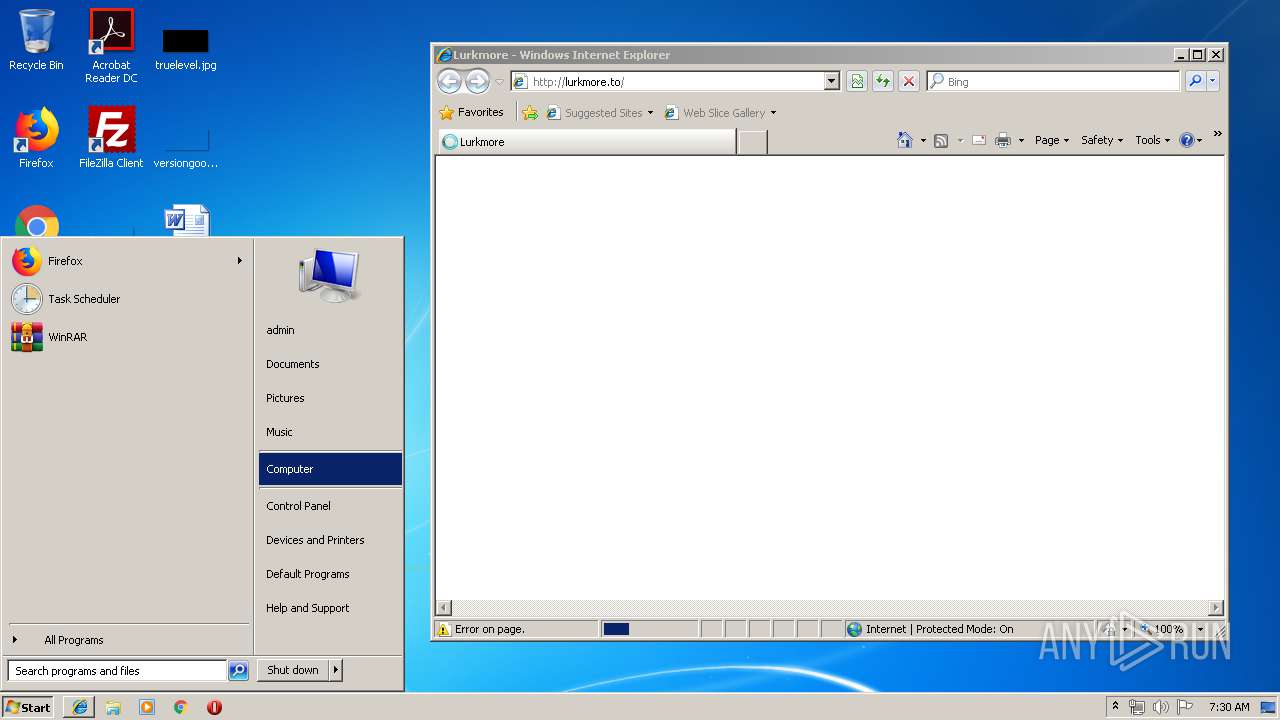
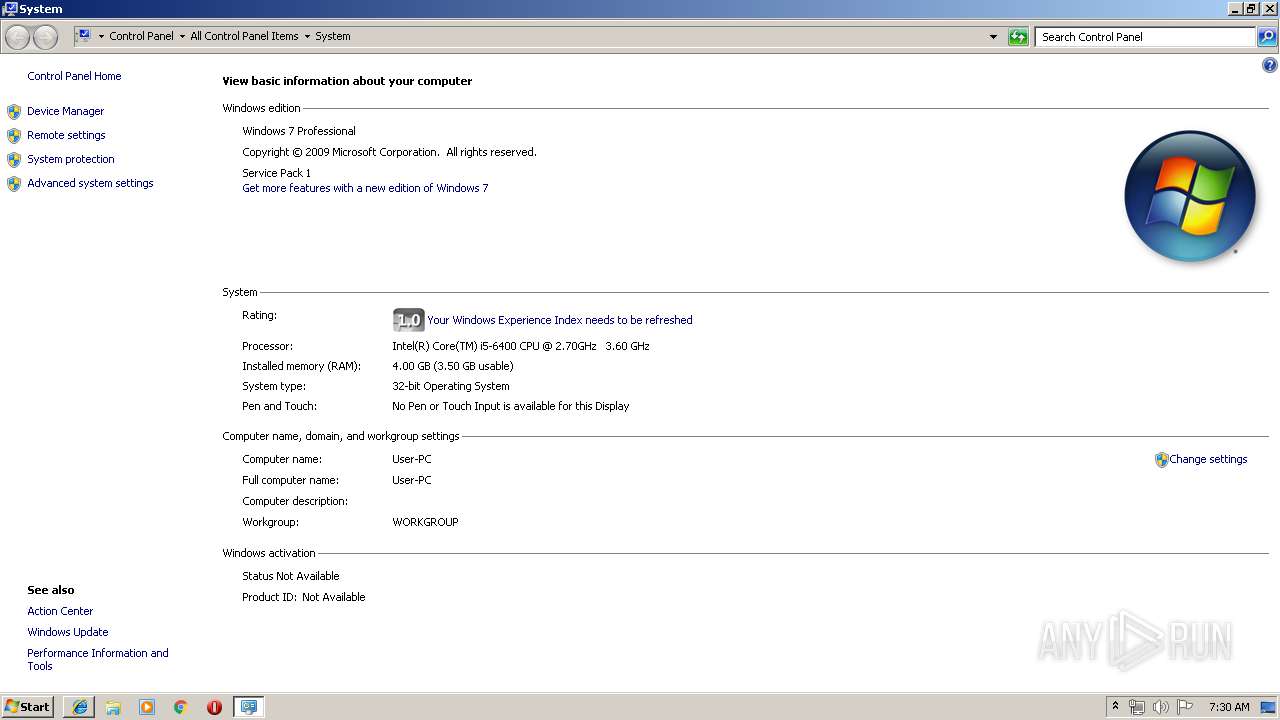
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, UTF-8 Unicode text, with very long lines |
| MD5: | 38BA37386419FDB1FC3B93E7CBBAC543 |
| SHA1: | 45D49C96782861161650AB2B5071D8EFC8897A23 |
| SHA256: | 2DBC51E3CFC77B35AA6EFB705394F2DE9FE199D0B0BCDE2751F05266A8759712 |
| SSDEEP: | 768:wPYhgn/DX3PLCj5qZMgGXbr+v65ntYQlV7UVBTz5Klp0z7Ha8KaVHNTPE+VQbx2:wPzn/DX3PLCdbr+v6oY4zIlp0X68KajT |
MALICIOUS
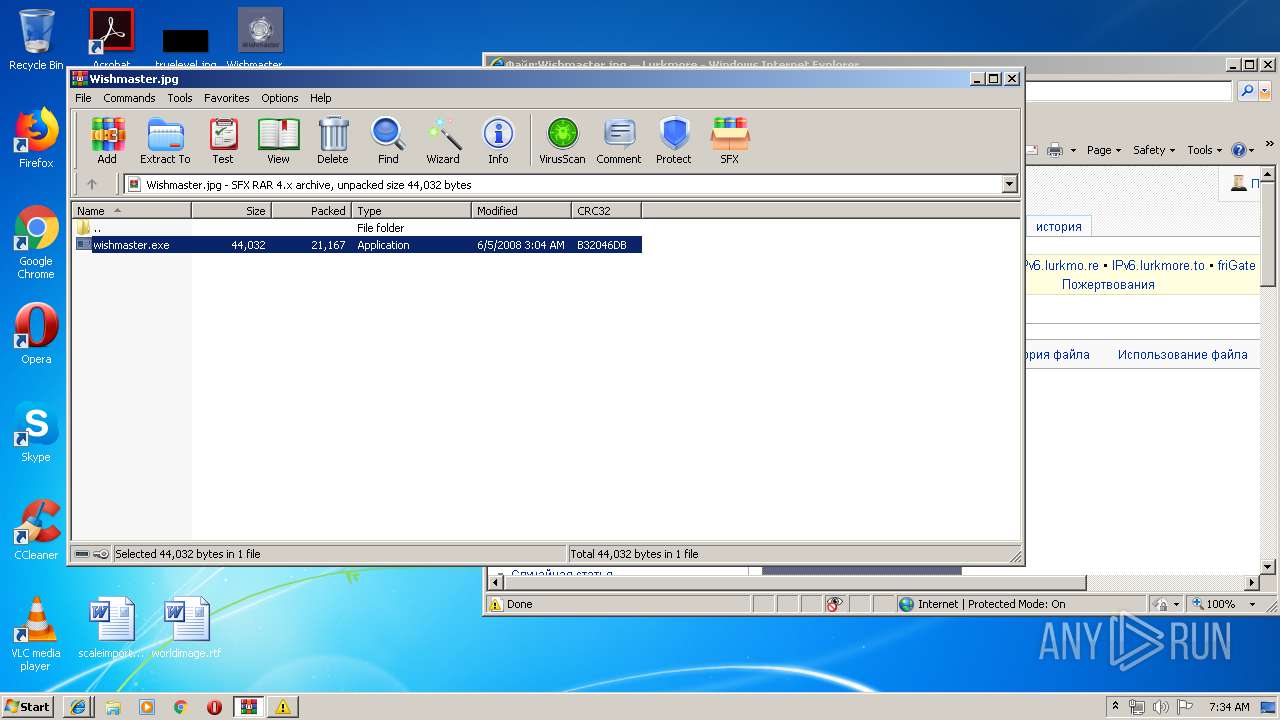
Application was dropped or rewritten from another process
- wishmaster.exe (PID: 1584)
SUSPICIOUS
Executed via COM
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 1524)
Executable content was dropped or overwritten
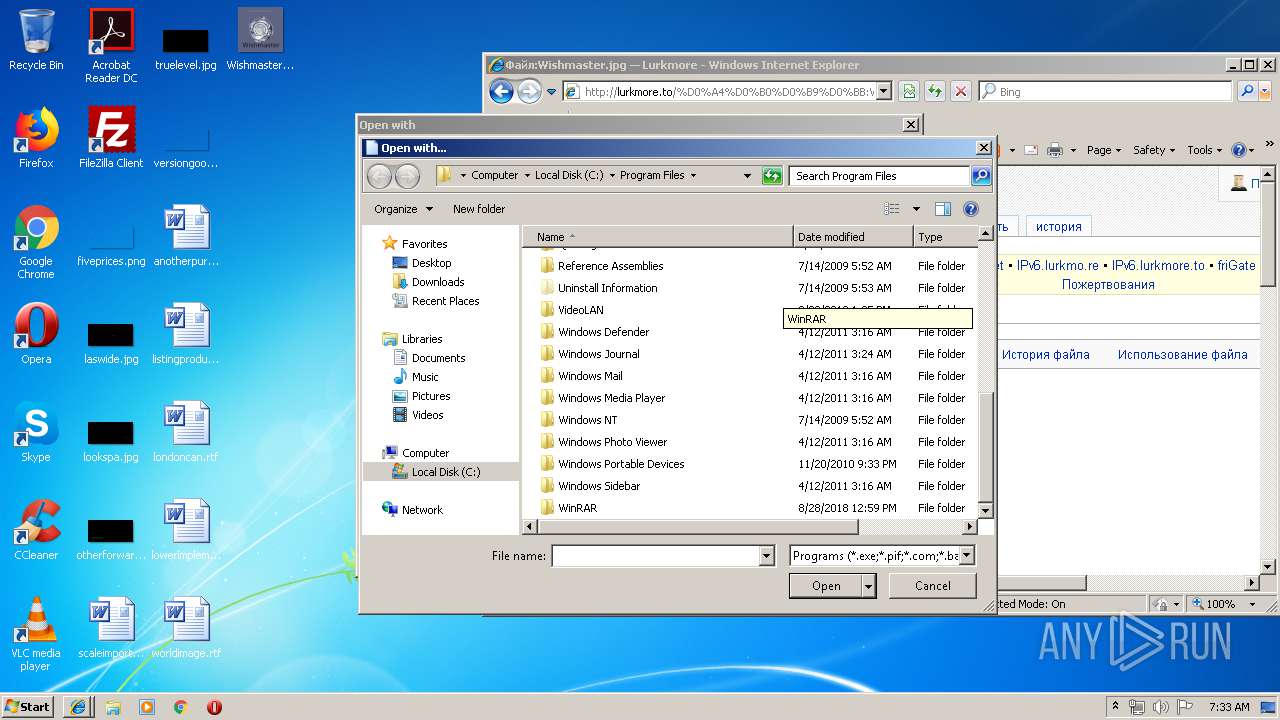
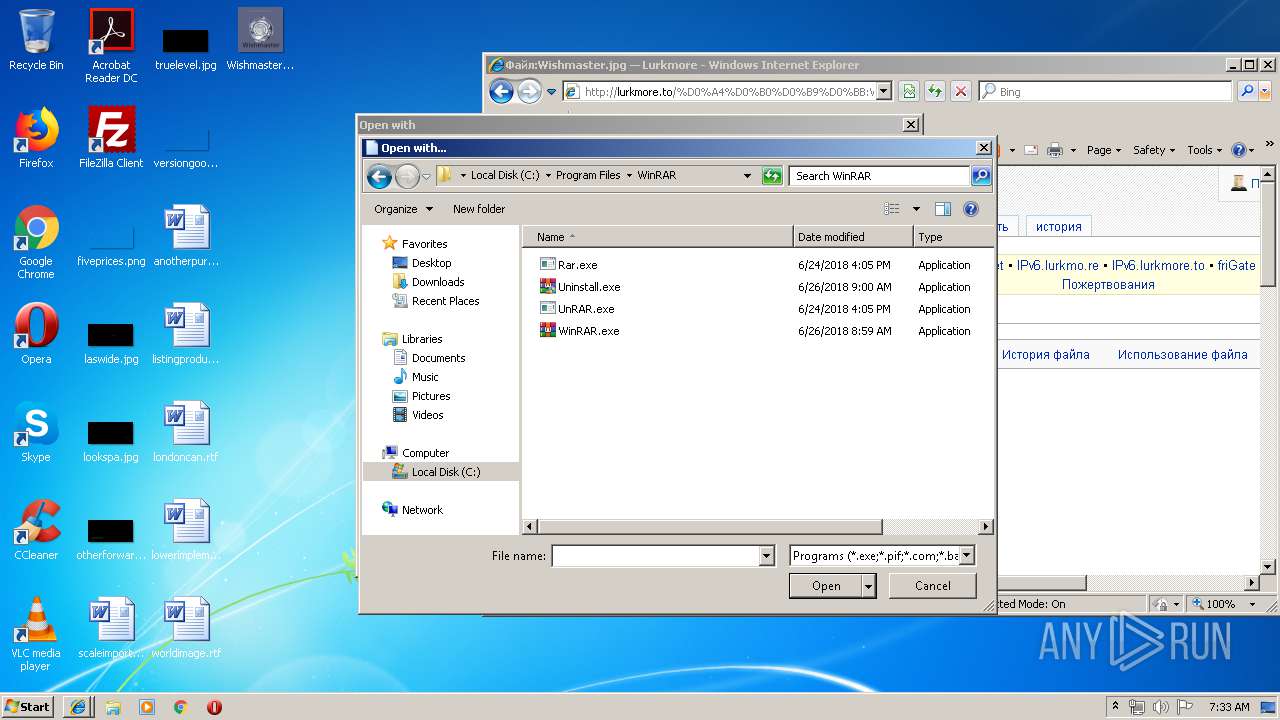
- WinRAR.exe (PID: 2824)
INFO
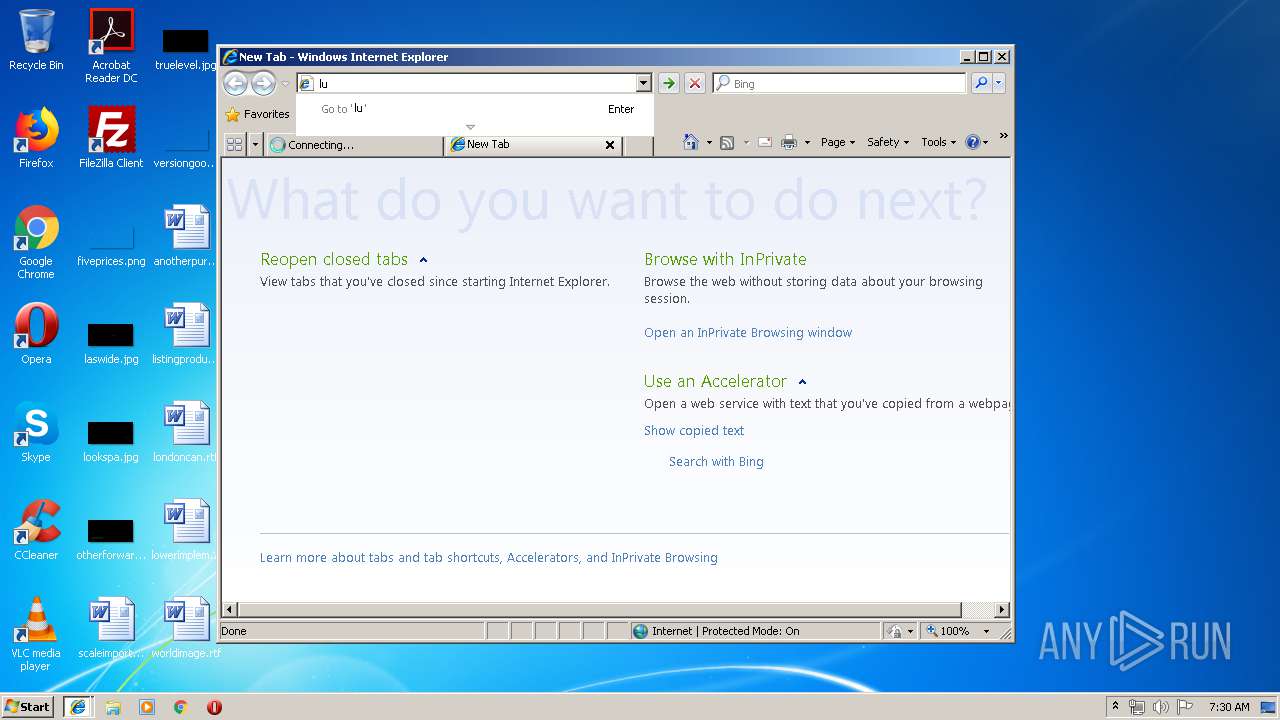
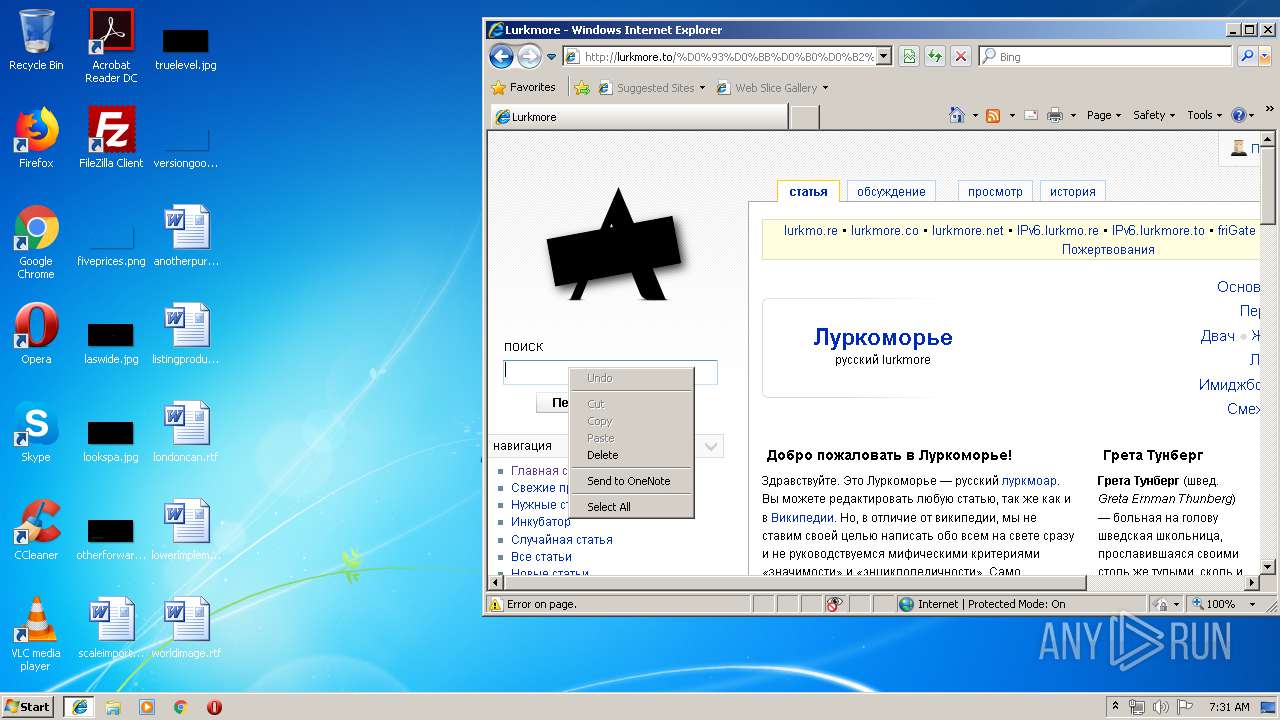
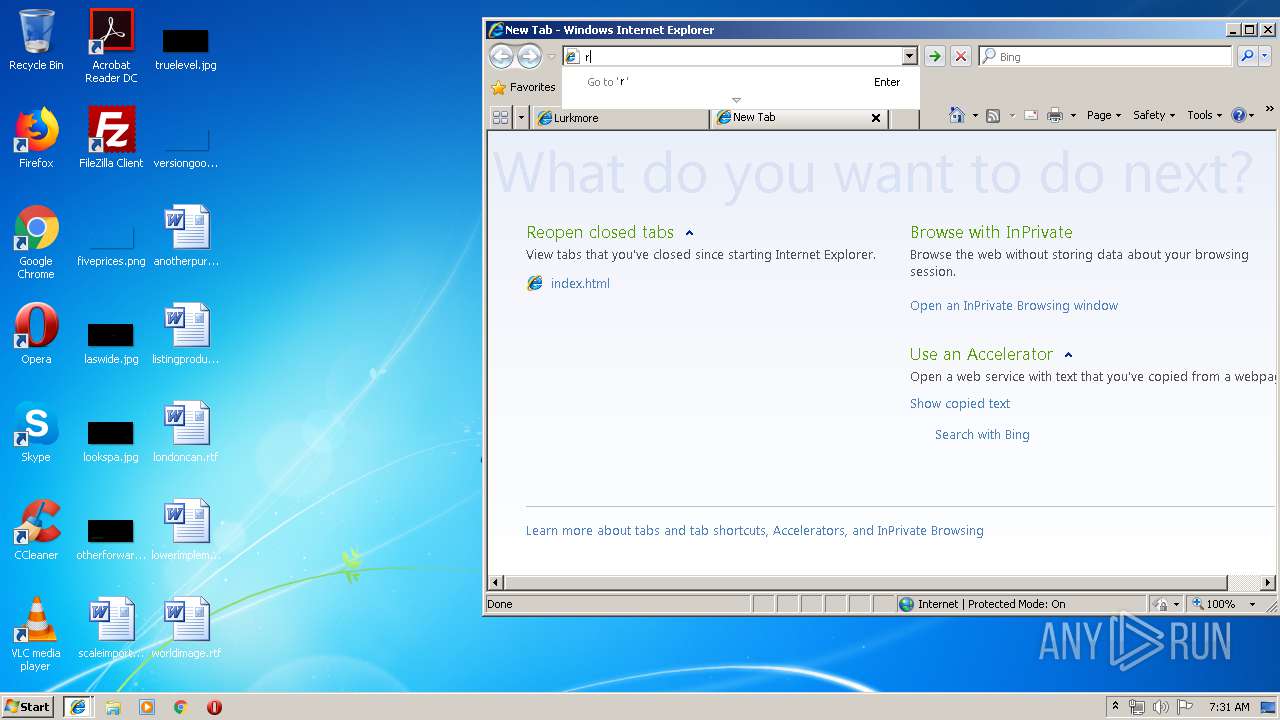
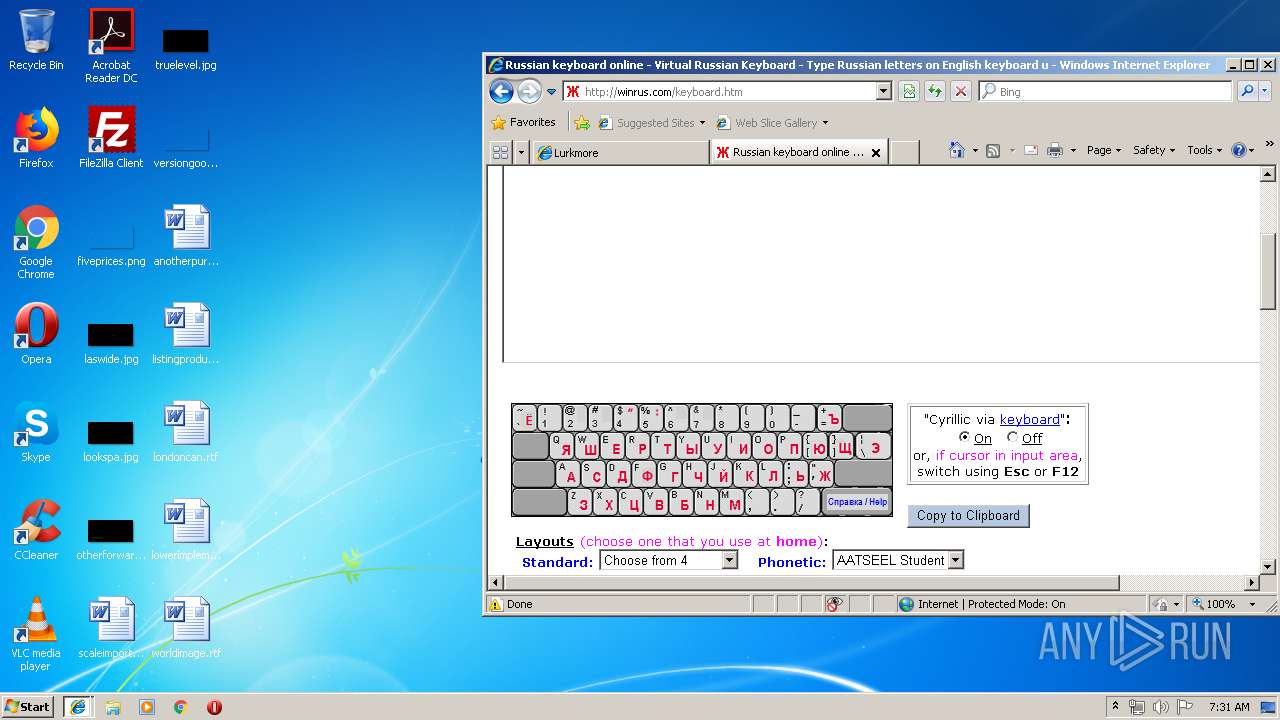
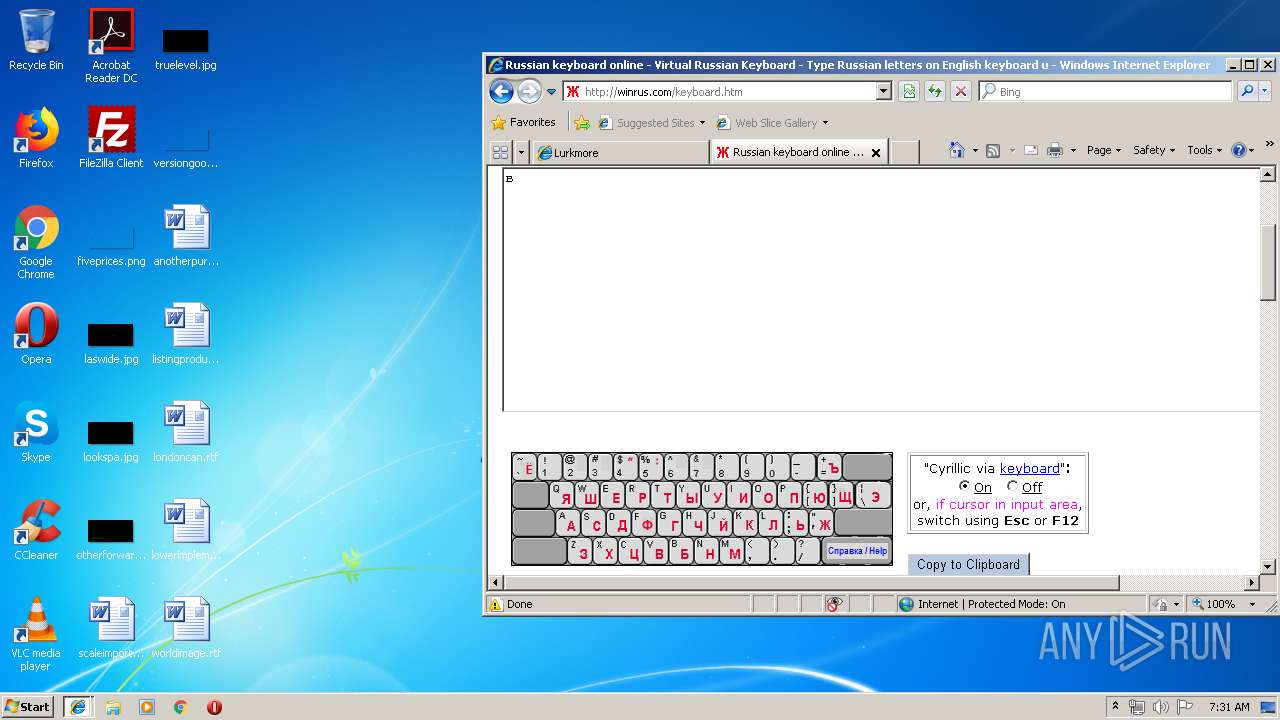
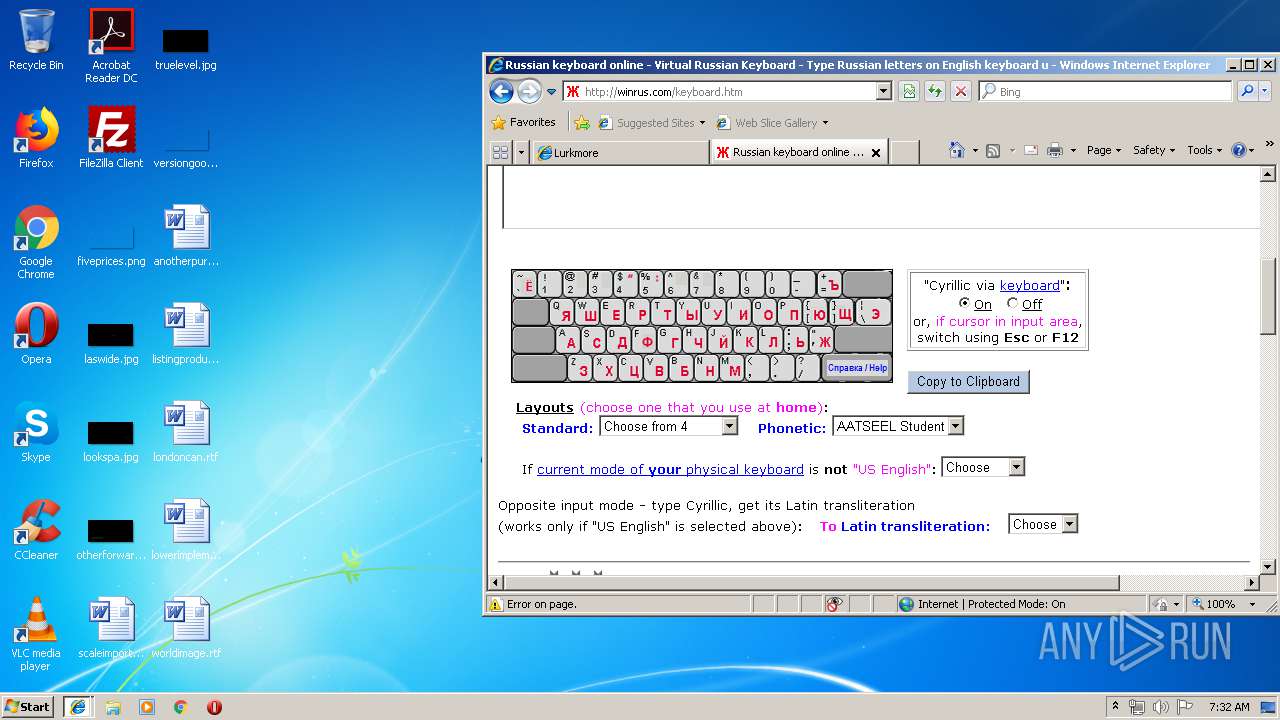
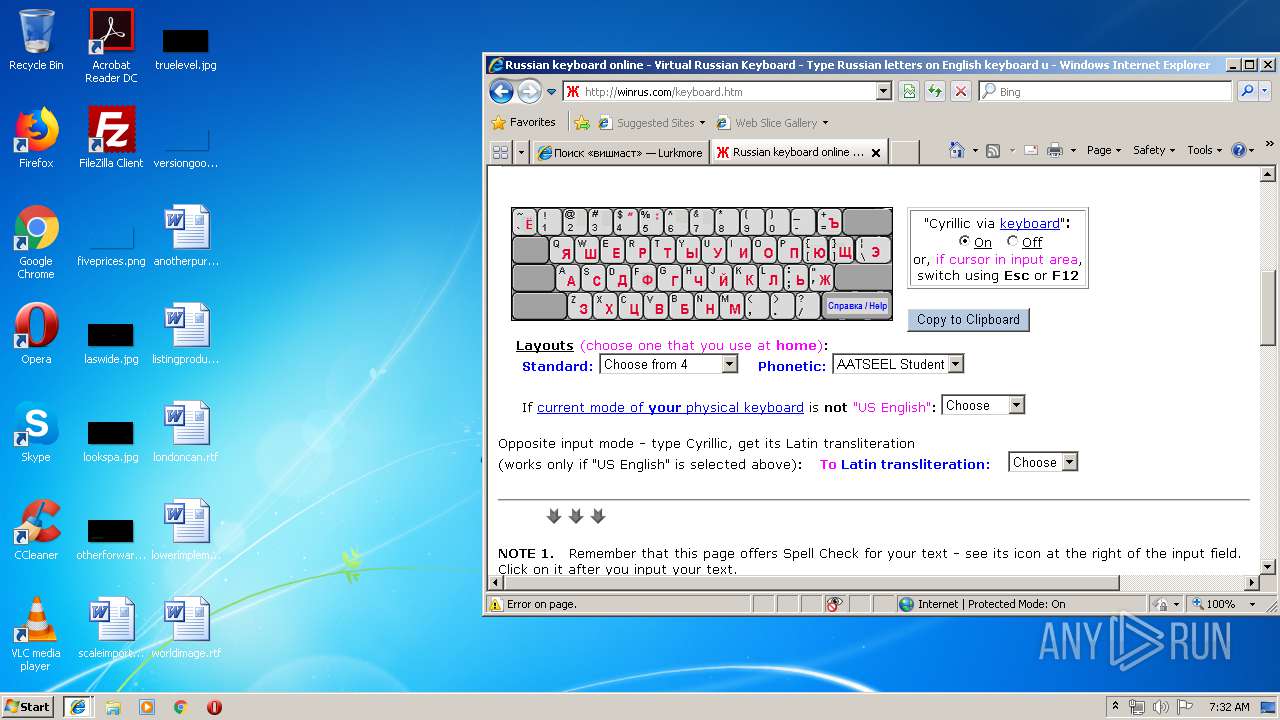
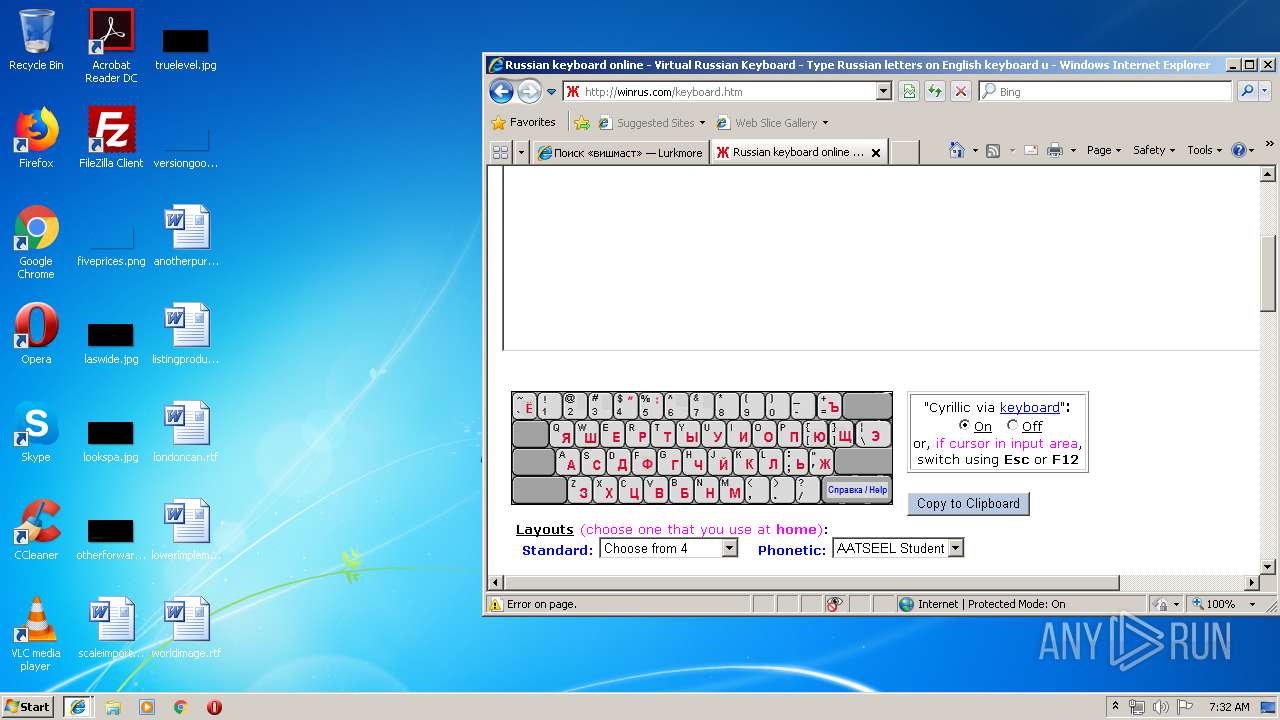
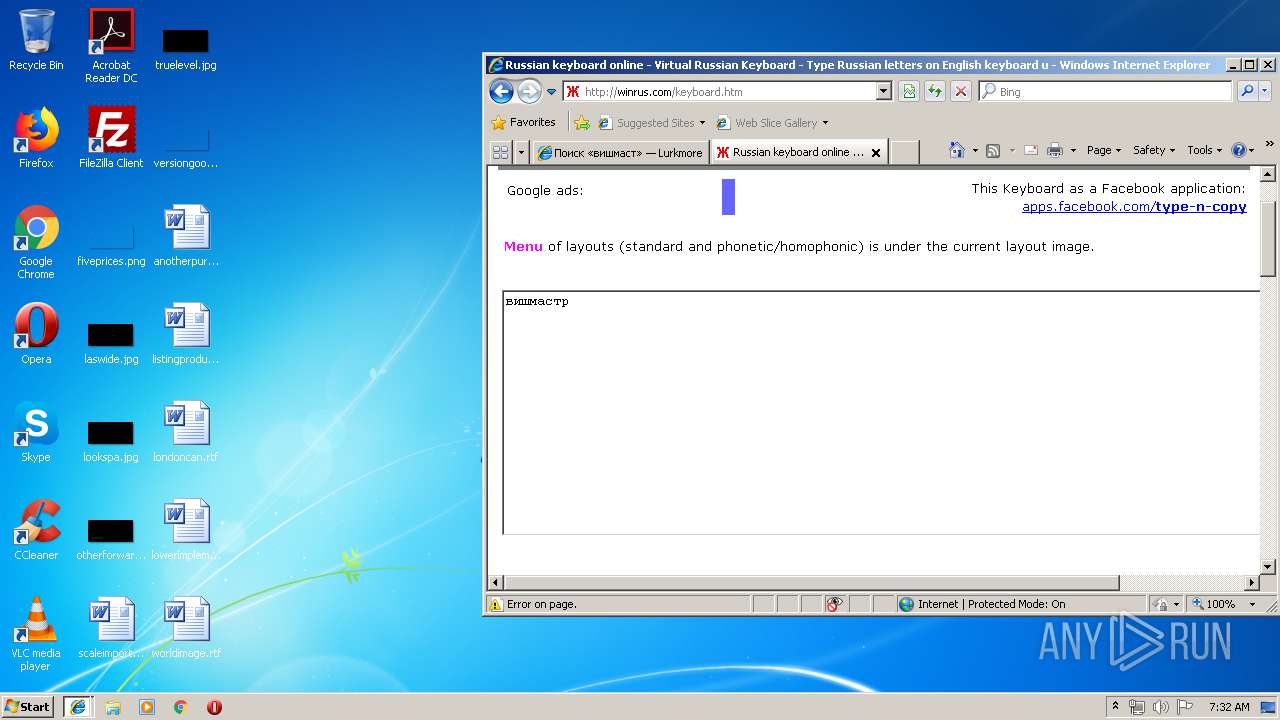
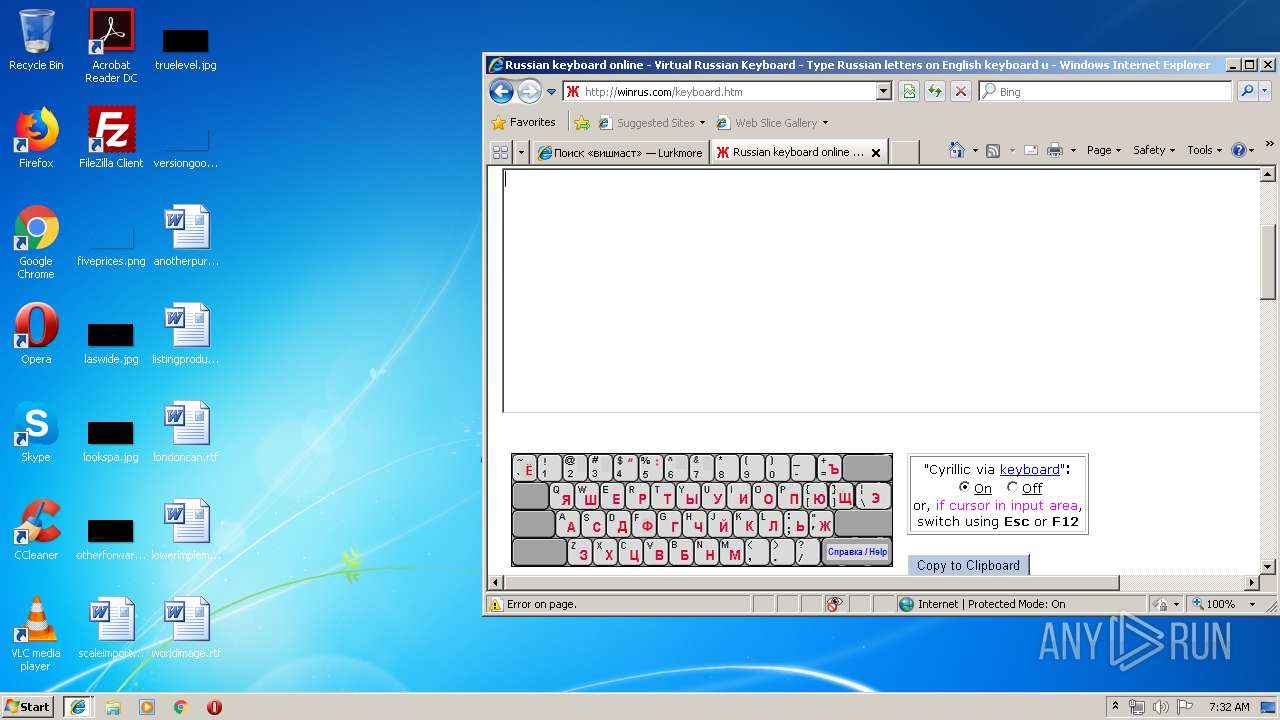
Application launched itself
- iexplore.exe (PID: 3352)
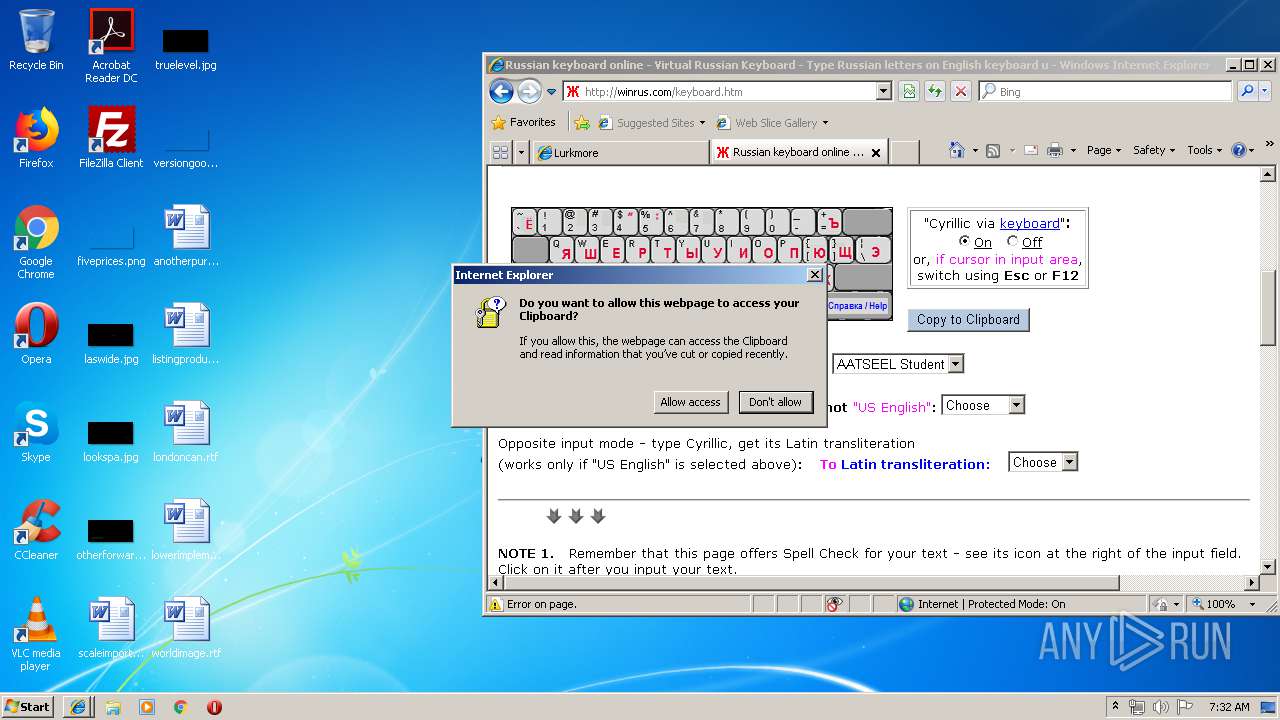
Changes internet zones settings
- iexplore.exe (PID: 3352)
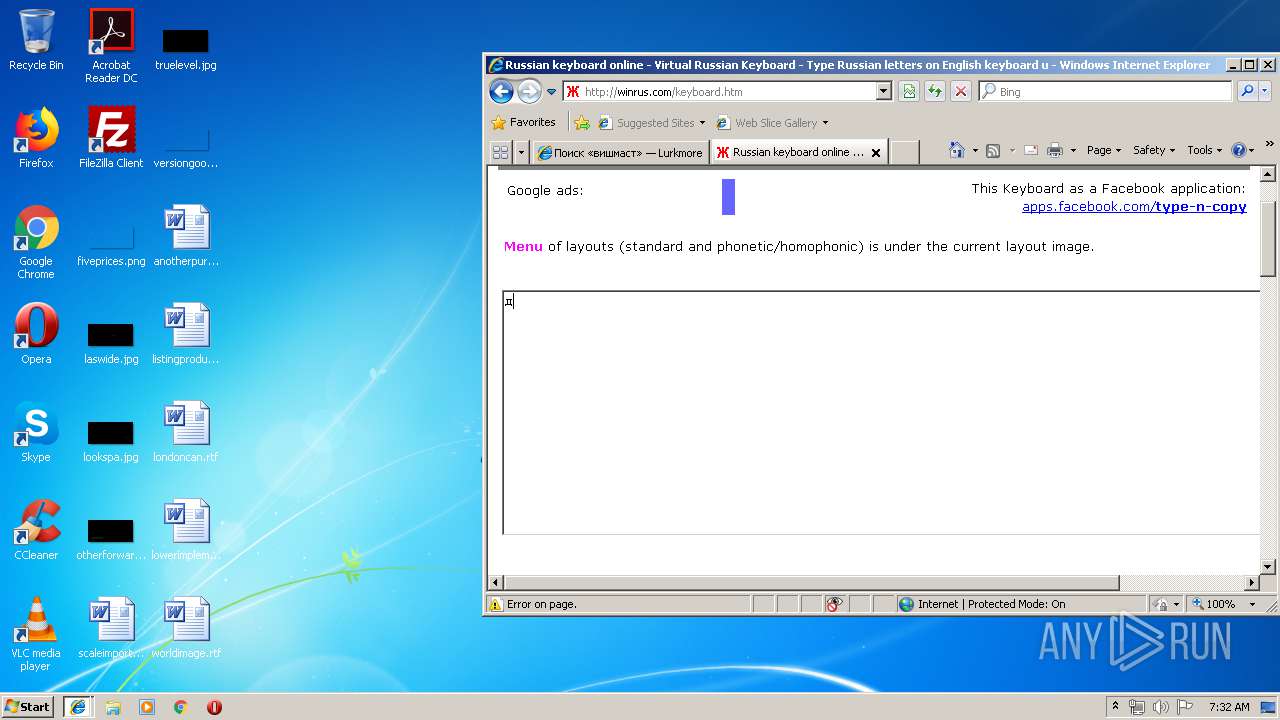
Reads internet explorer settings
- iexplore.exe (PID: 3820)
- iexplore.exe (PID: 3280)
- iexplore.exe (PID: 2400)
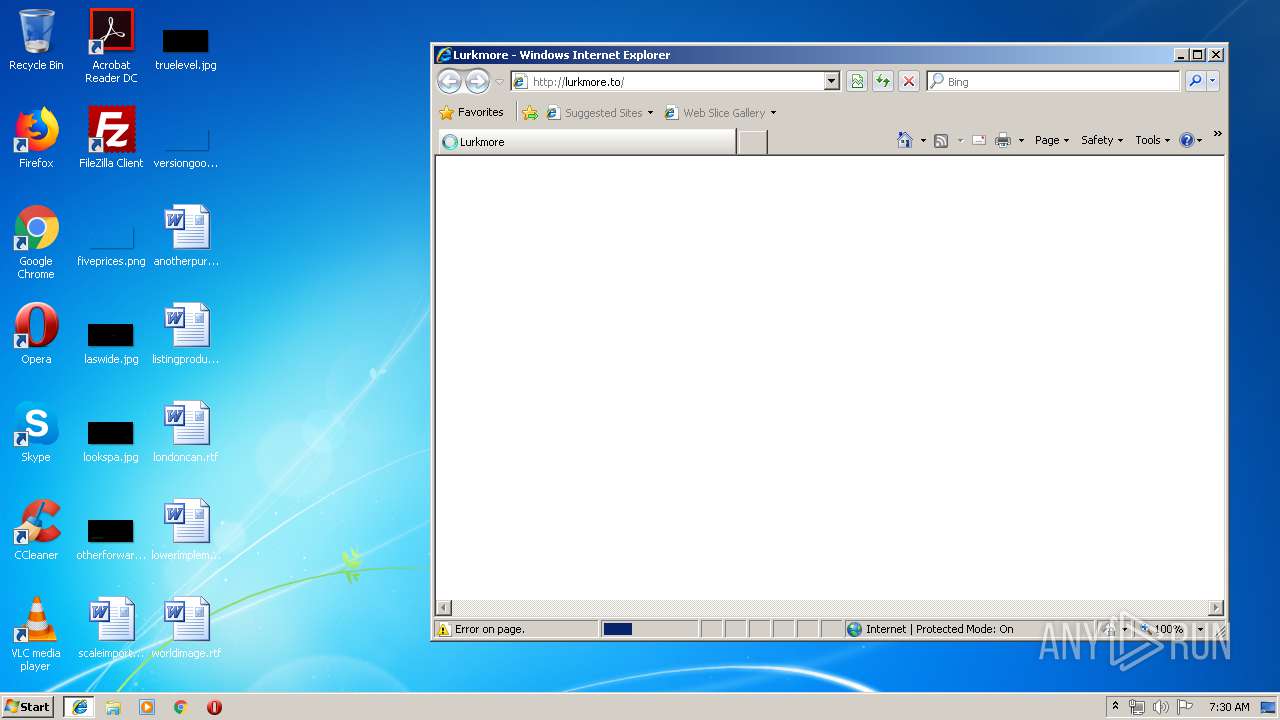
Creates files in the user directory
- iexplore.exe (PID: 3820)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 1524)
- iexplore.exe (PID: 2400)
- iexplore.exe (PID: 3280)
Reads Internet Cache Settings
- iexplore.exe (PID: 3280)
- iexplore.exe (PID: 3352)
- iexplore.exe (PID: 3820)
- iexplore.exe (PID: 2400)
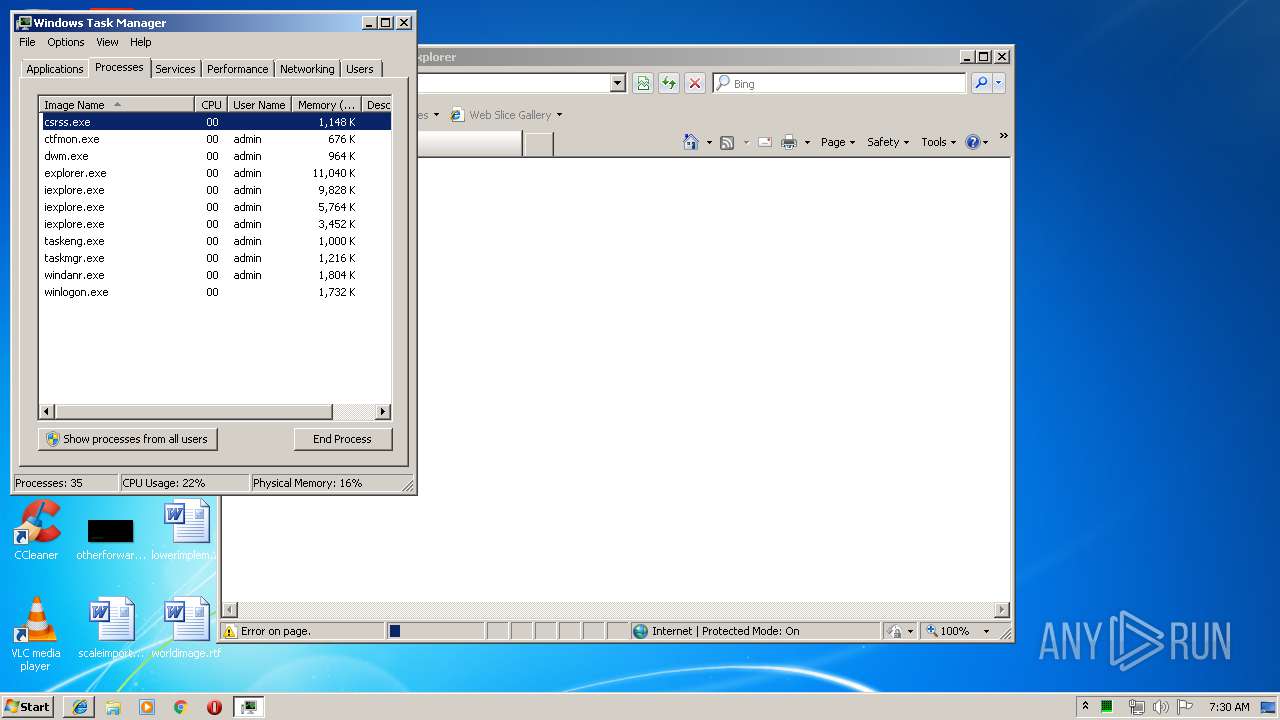
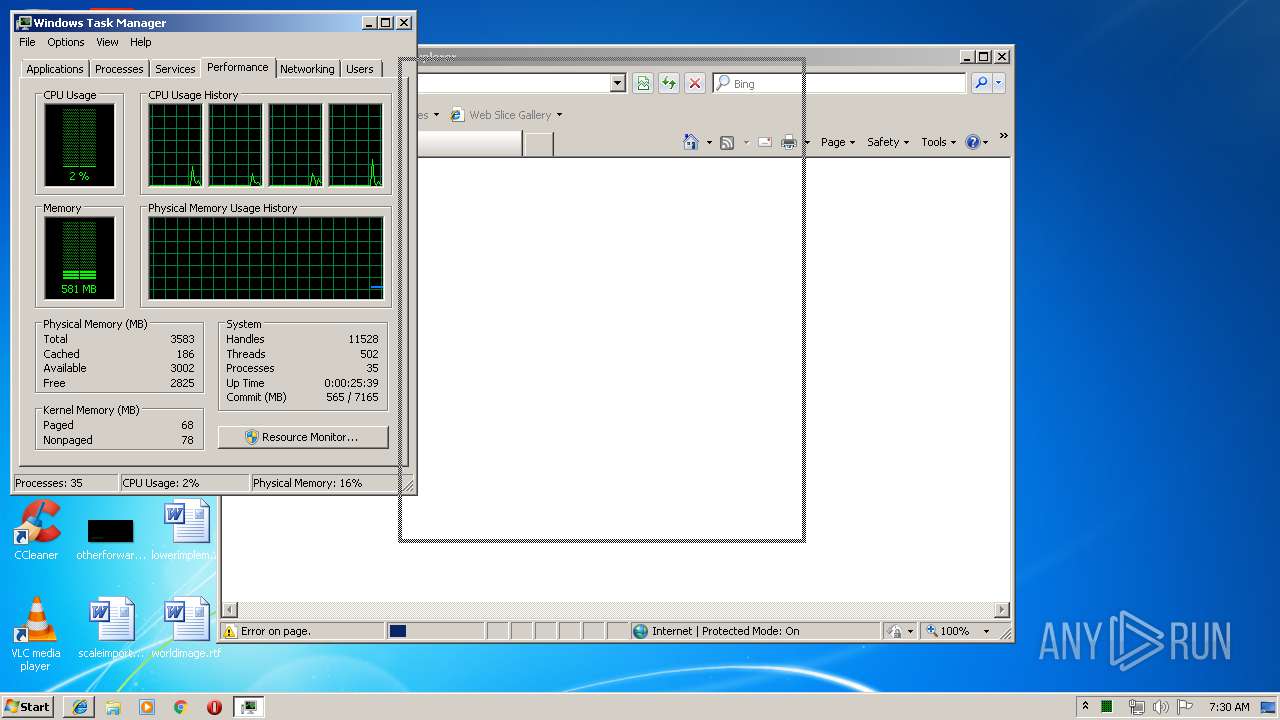
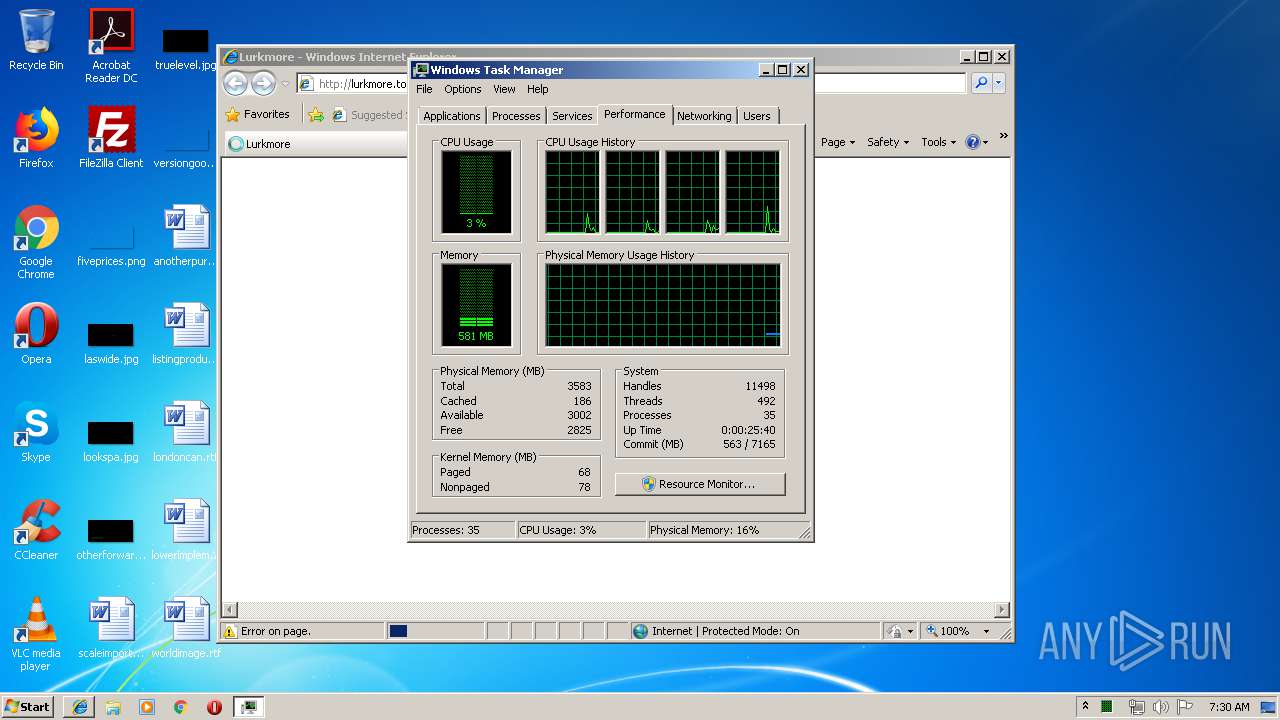
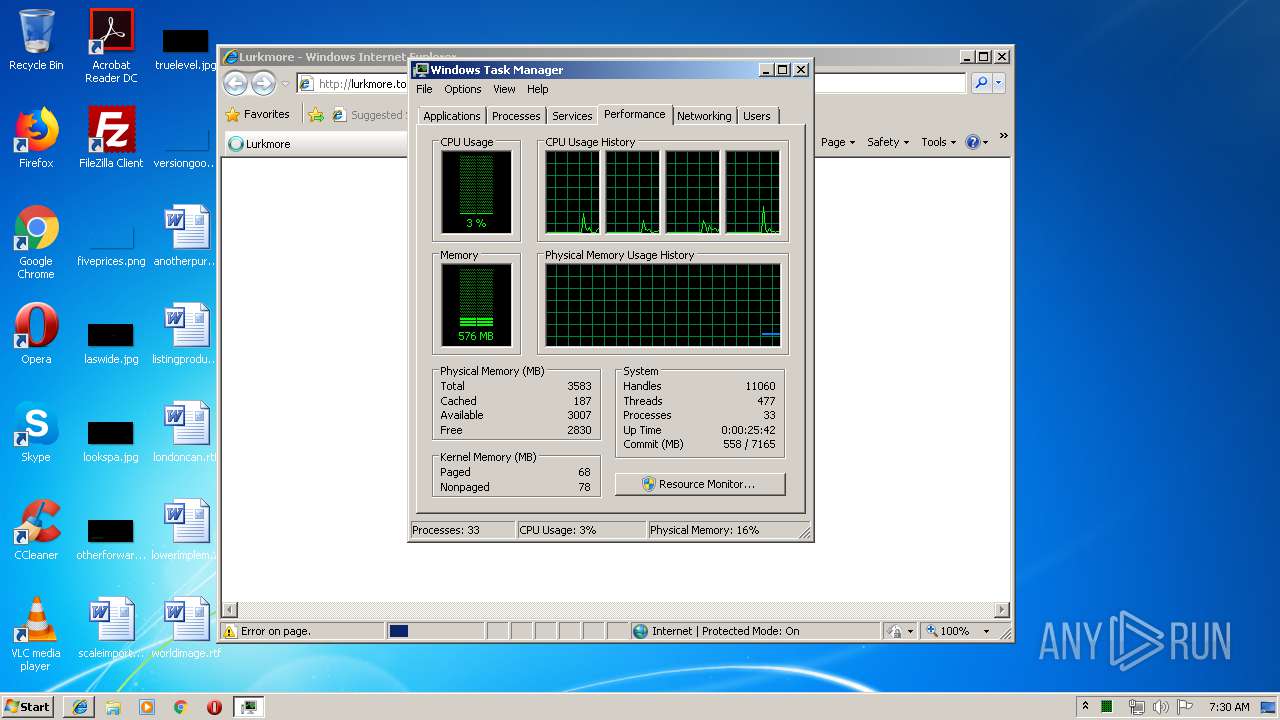
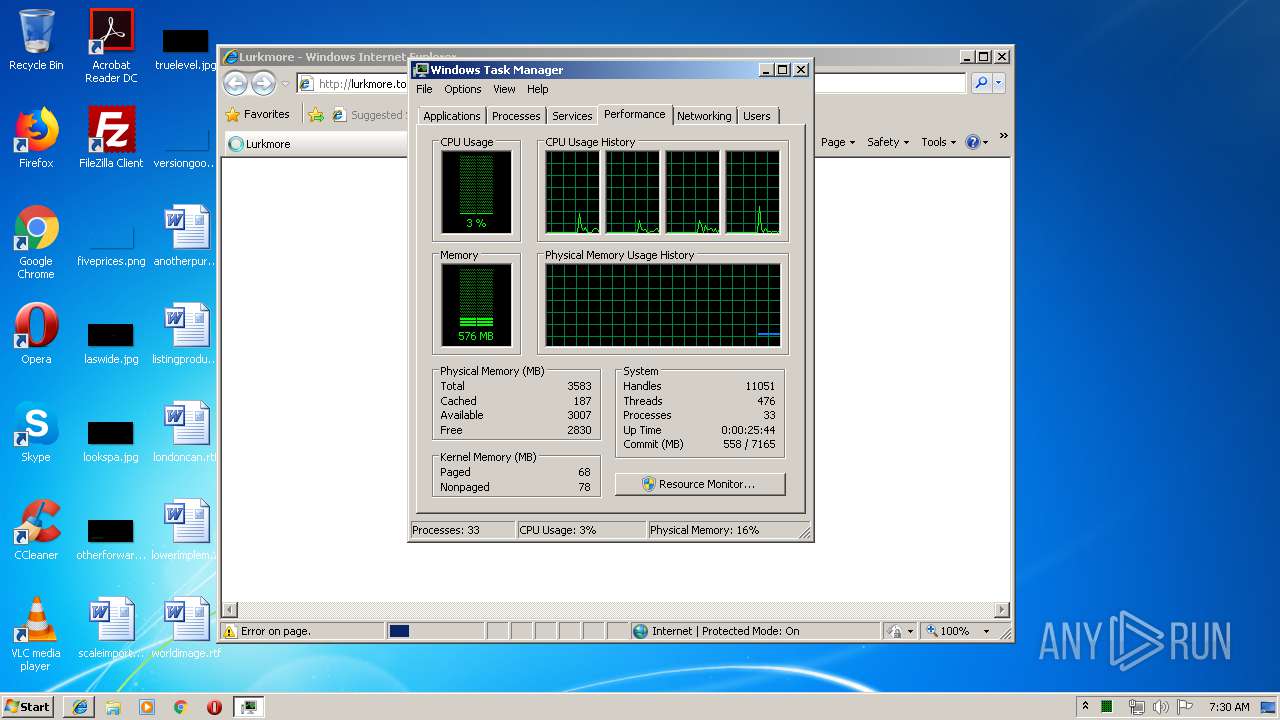
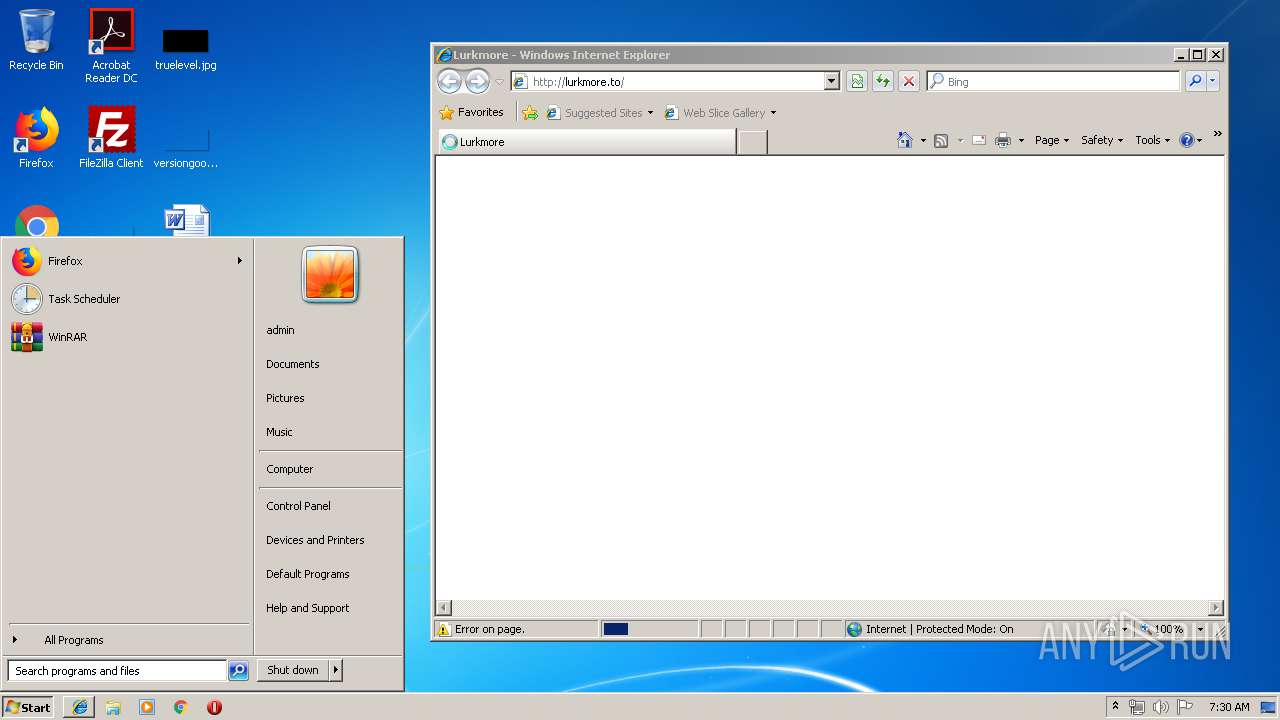
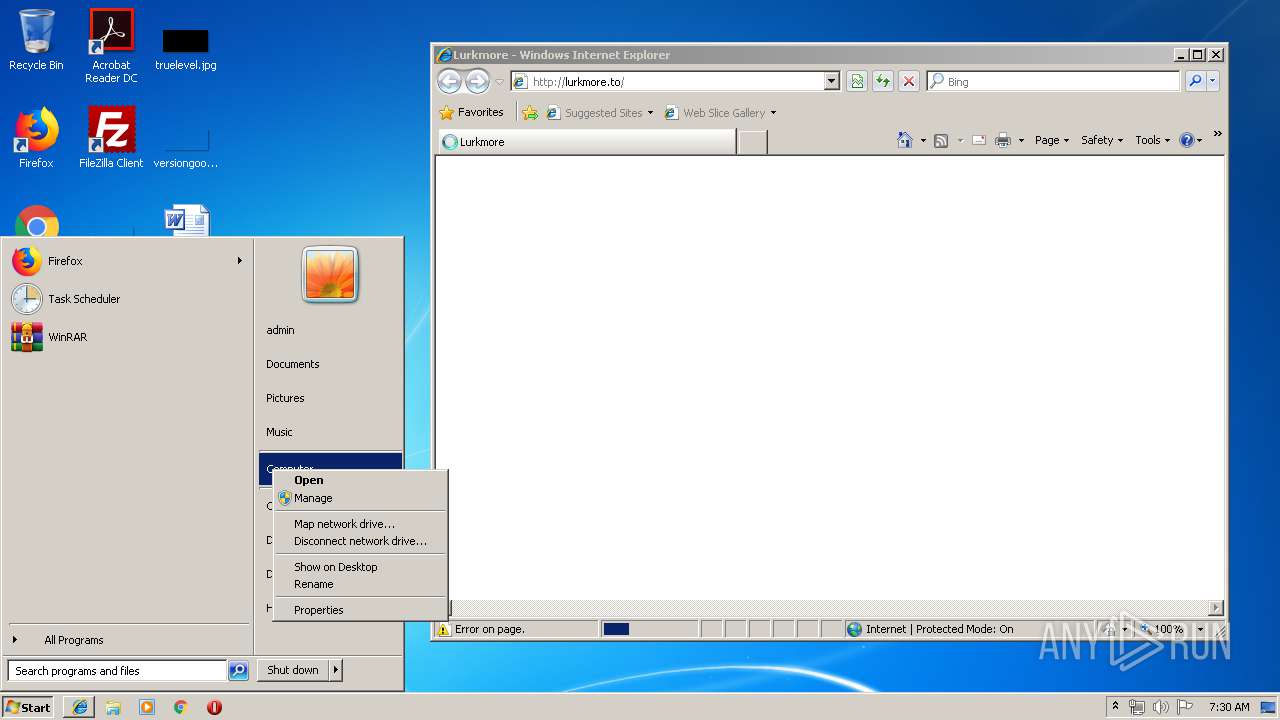
Manual execution by user
- taskmgr.exe (PID: 3476)
- control.exe (PID: 4060)
- rundll32.exe (PID: 4036)
Reads settings of System Certificates
- iexplore.exe (PID: 3280)
- iexplore.exe (PID: 2400)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 2400)
- iexplore.exe (PID: 3280)
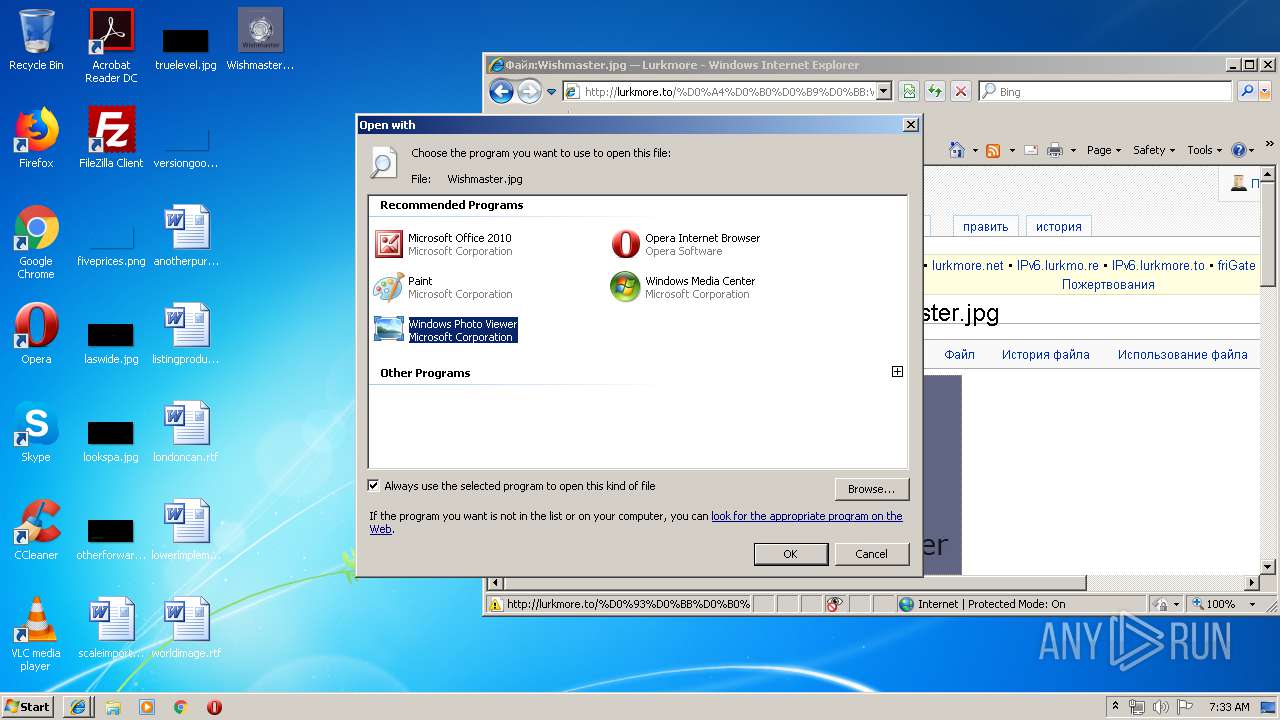
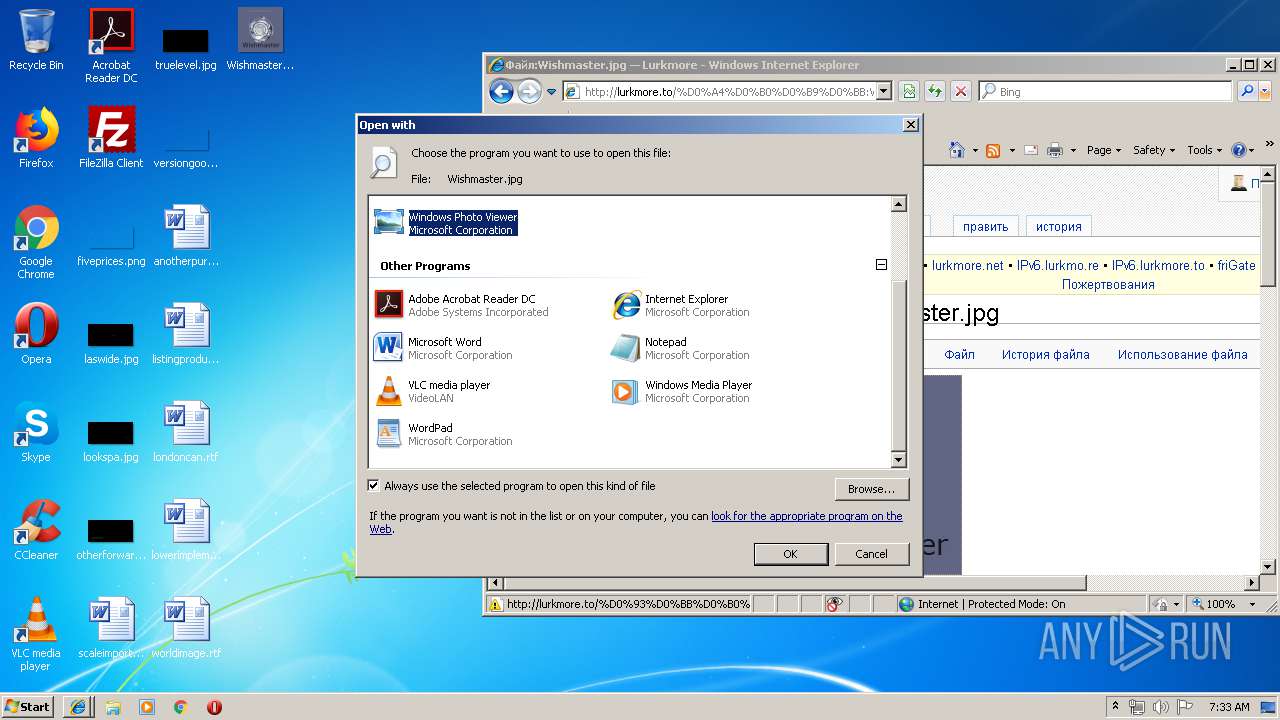
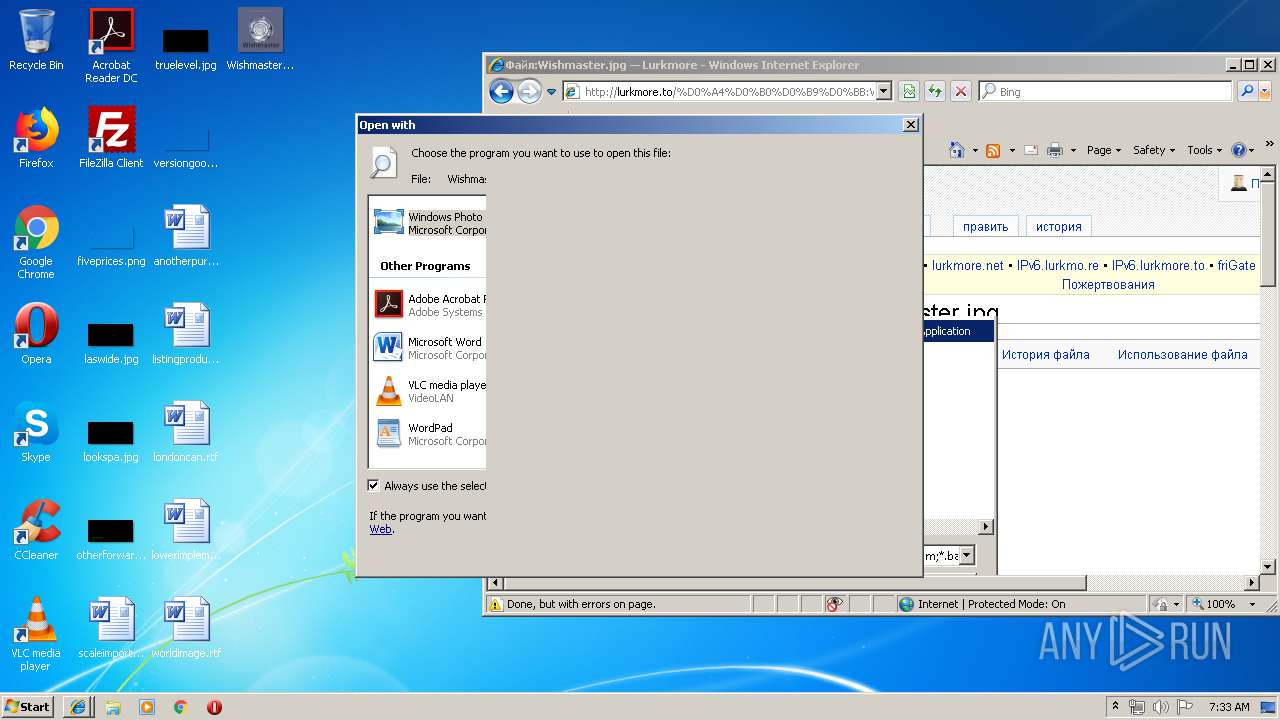
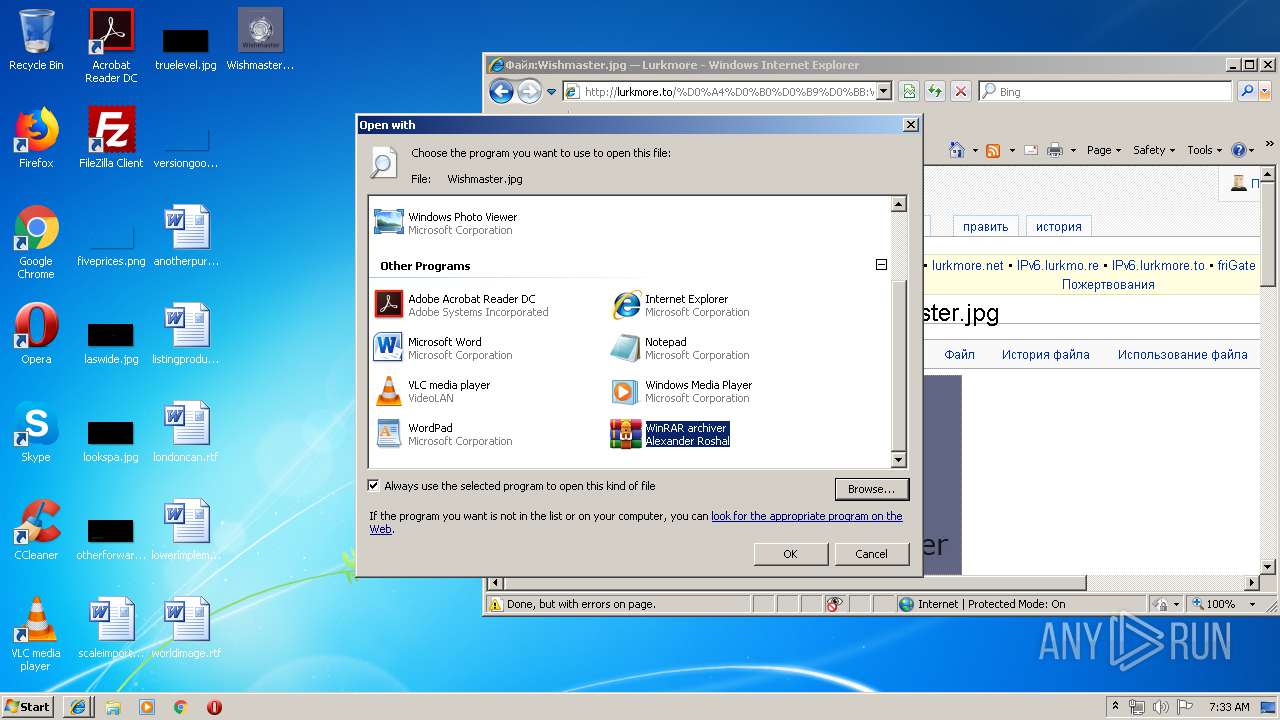
Modifies the open verb of a shell class
- rundll32.exe (PID: 4036)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .html | | | HyperText Markup Language (100) |
|---|
EXIF
HTML
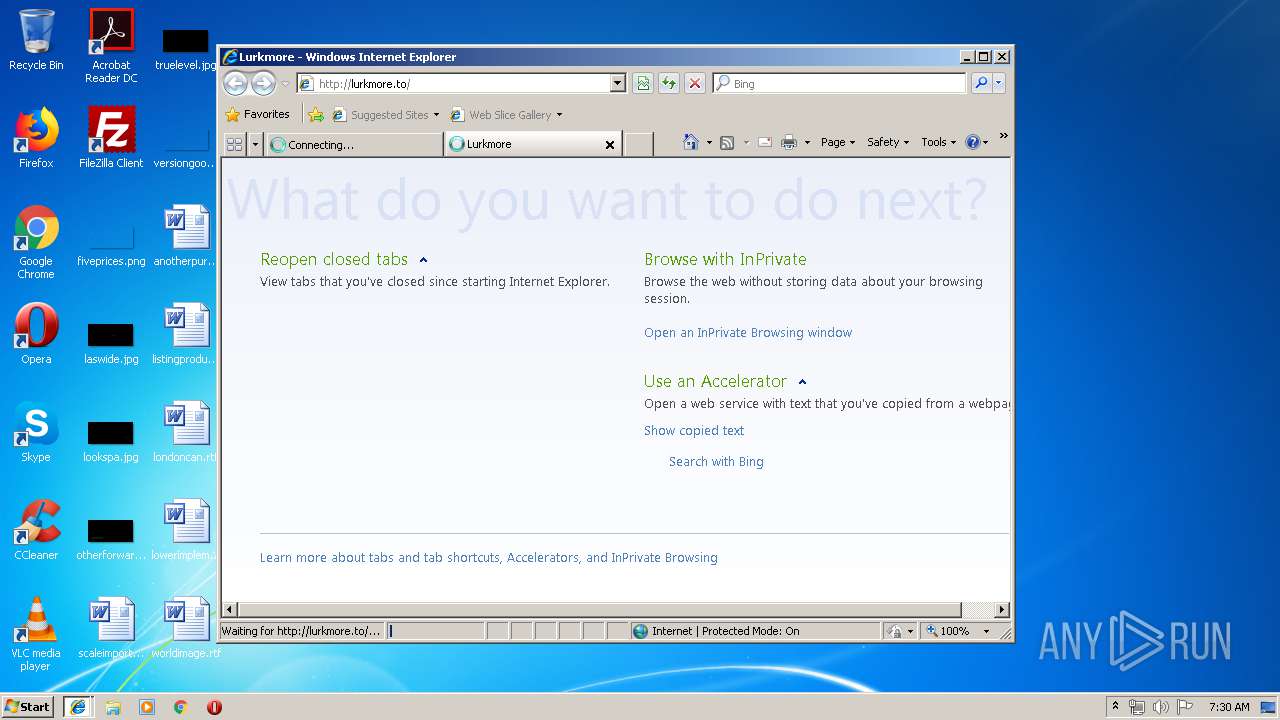
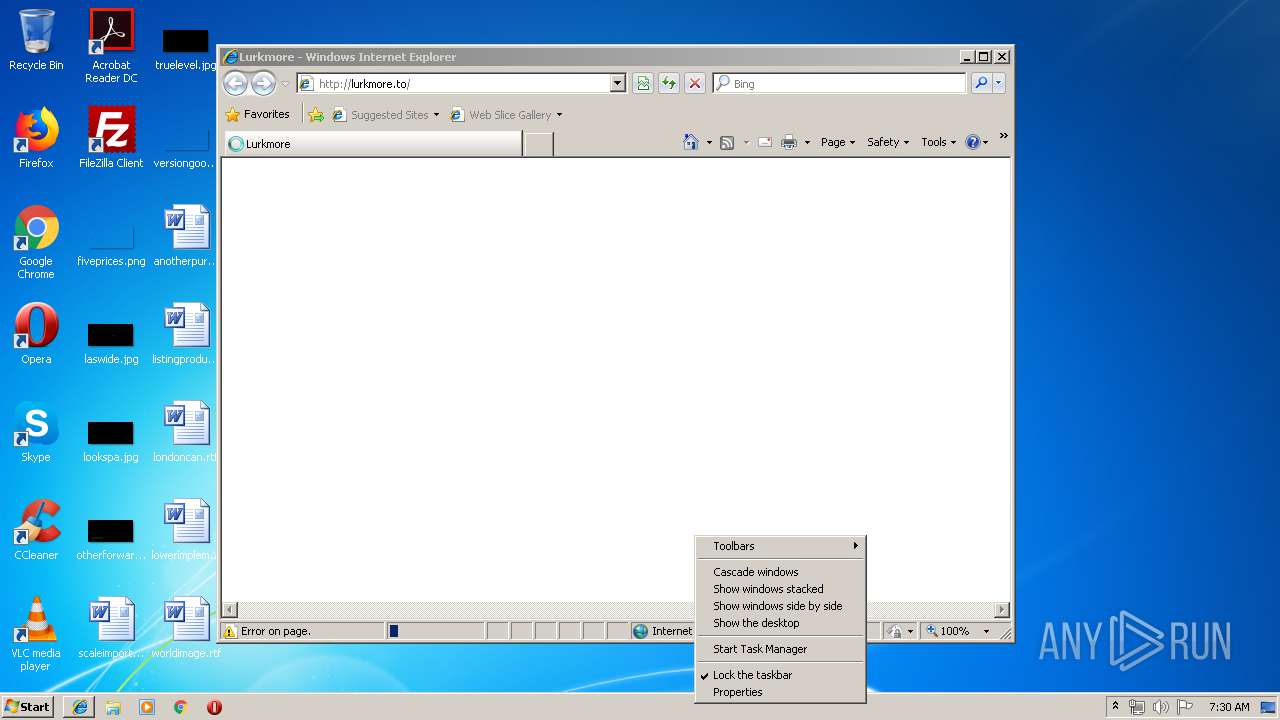
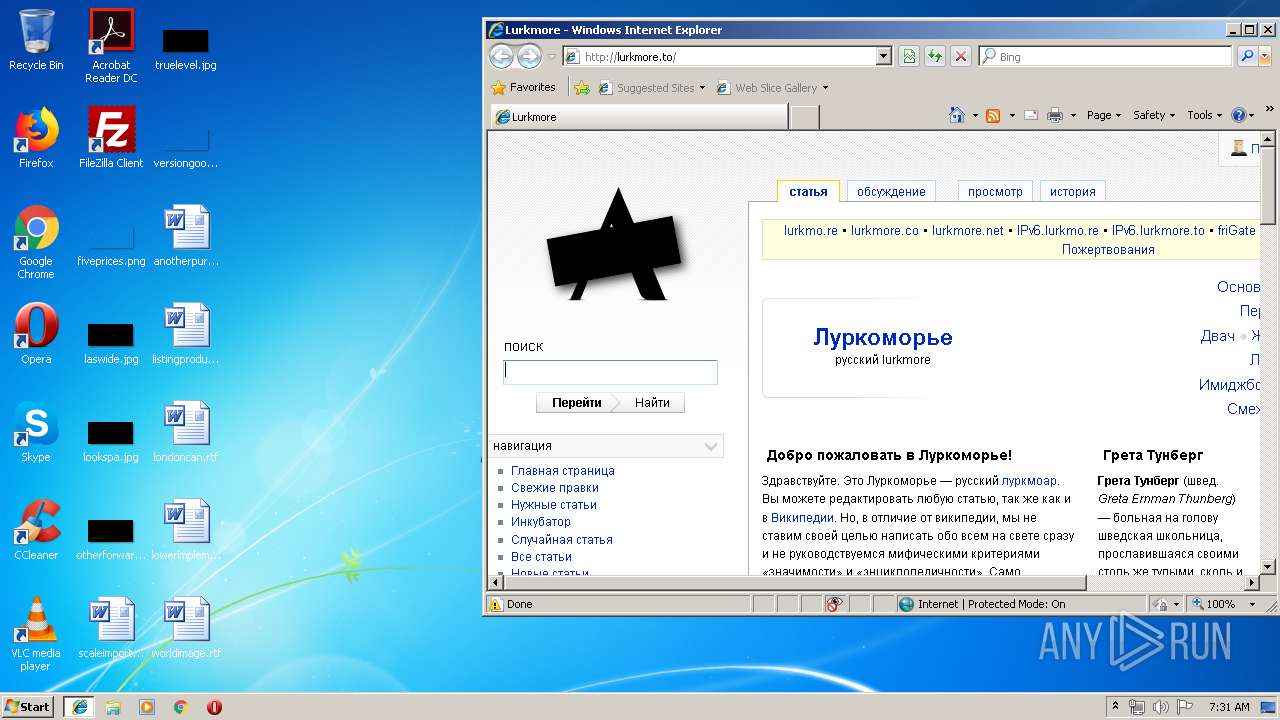
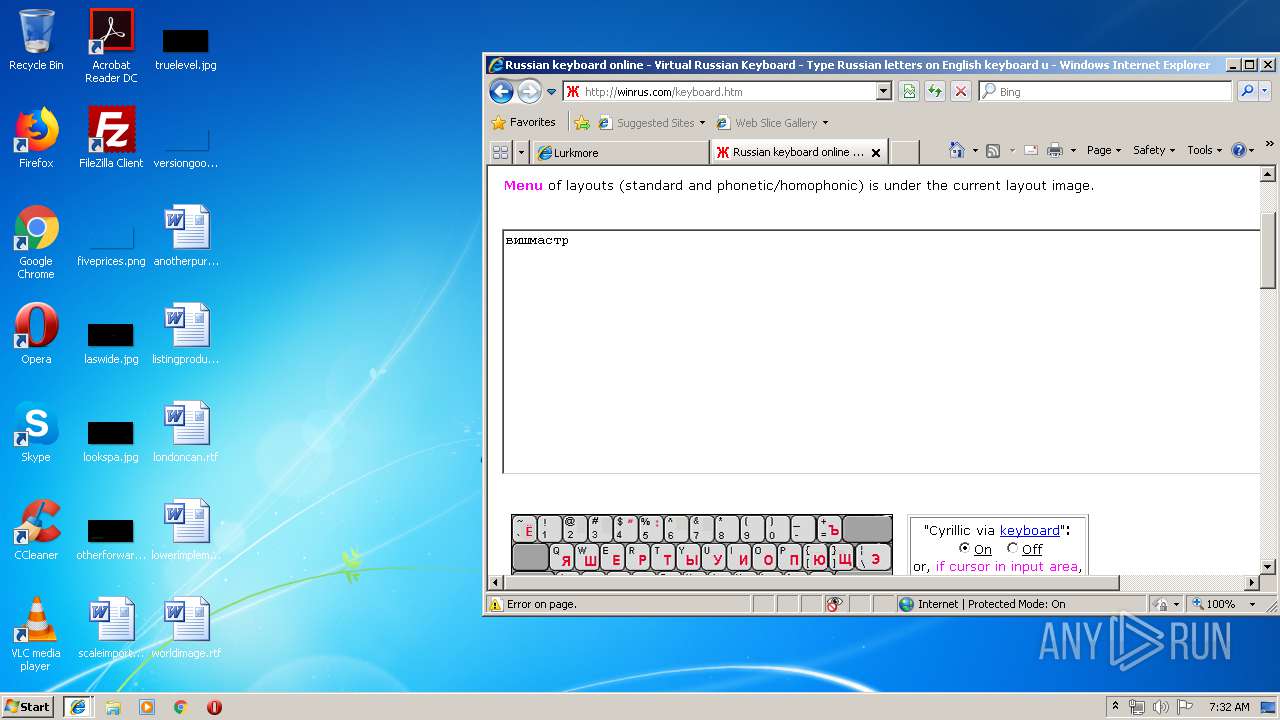
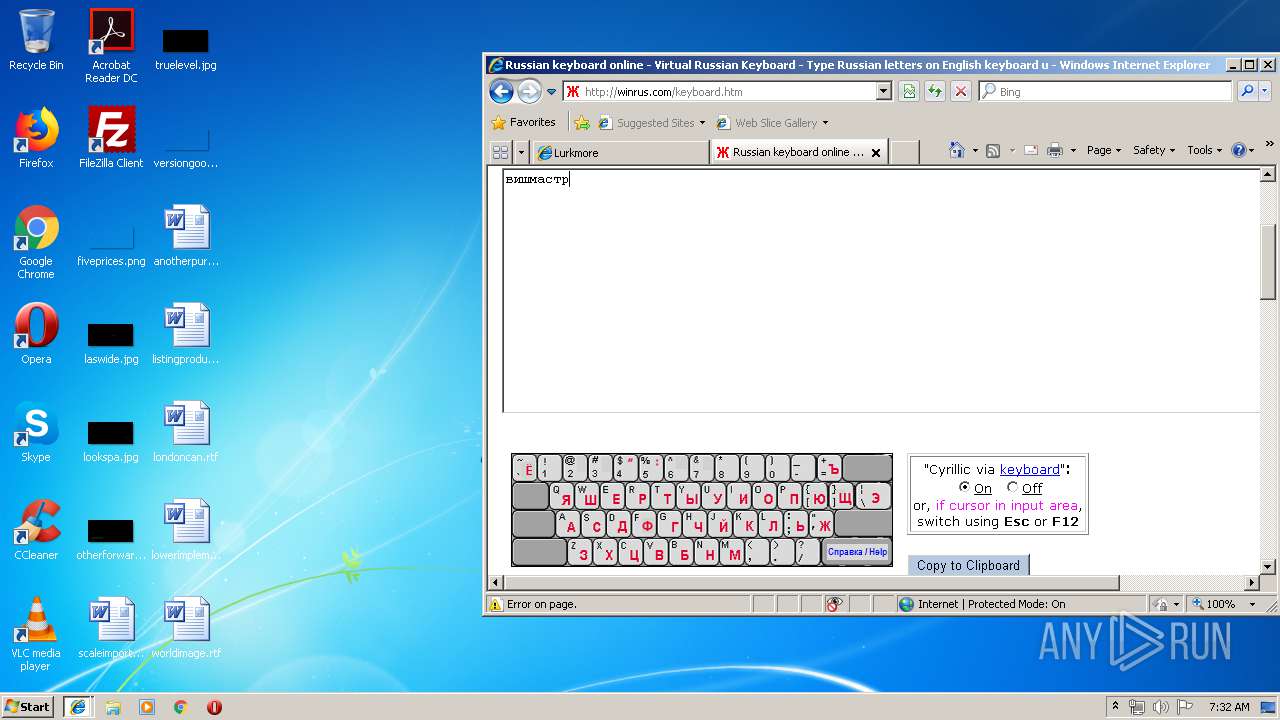
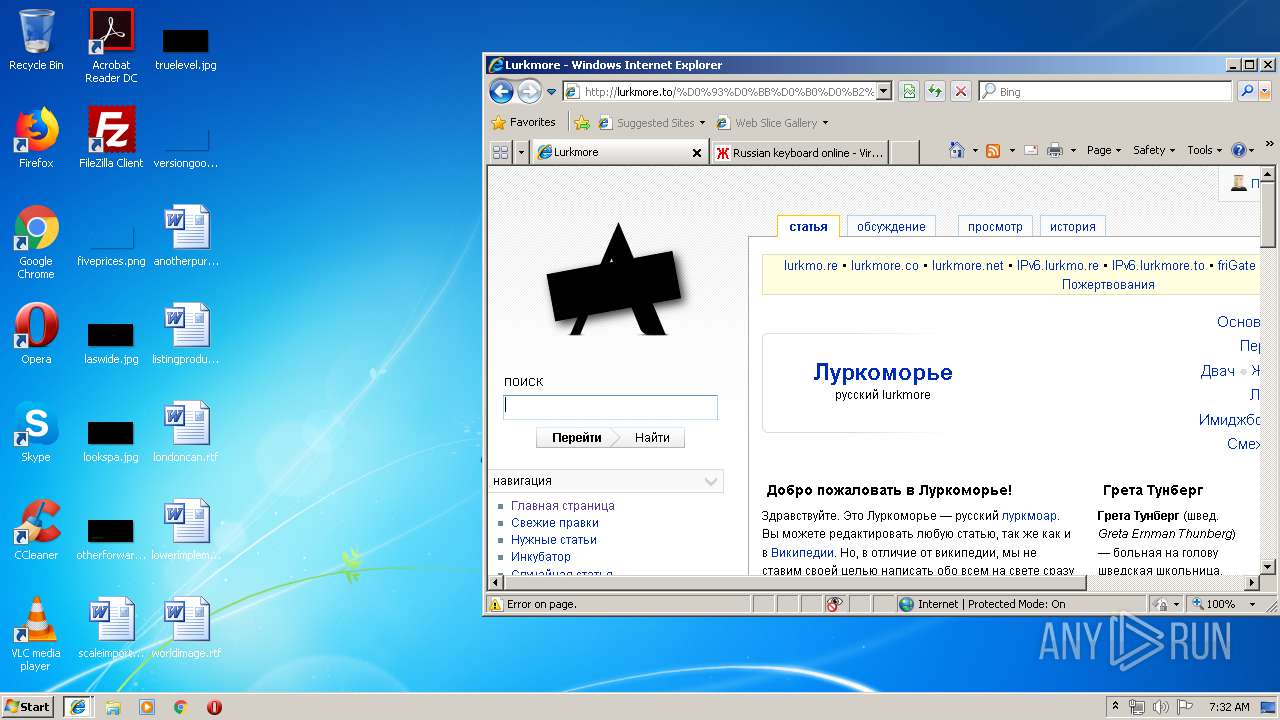
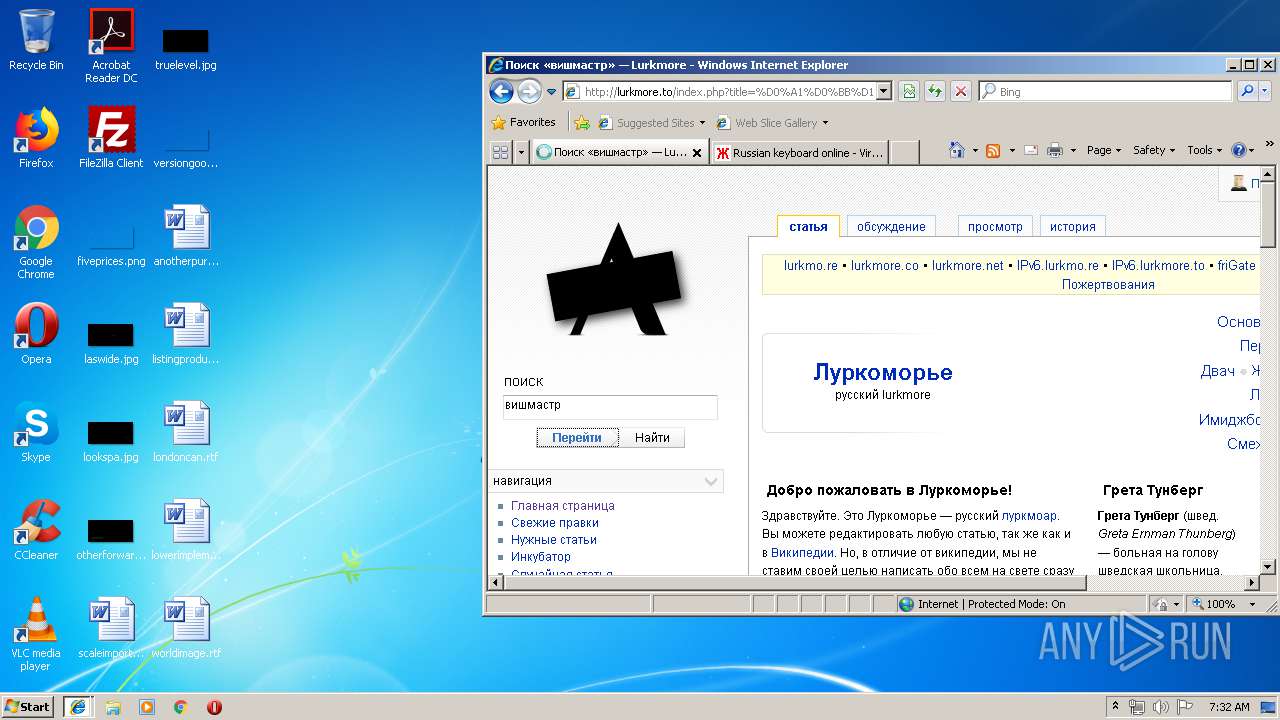
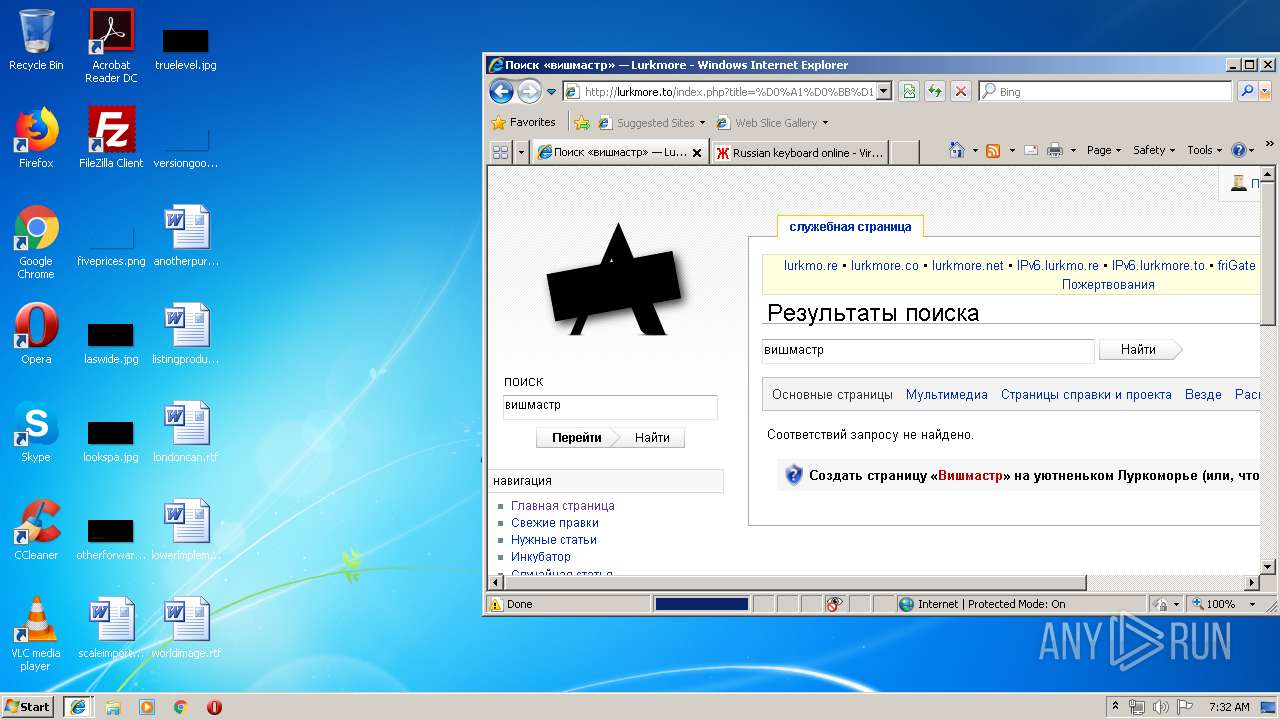
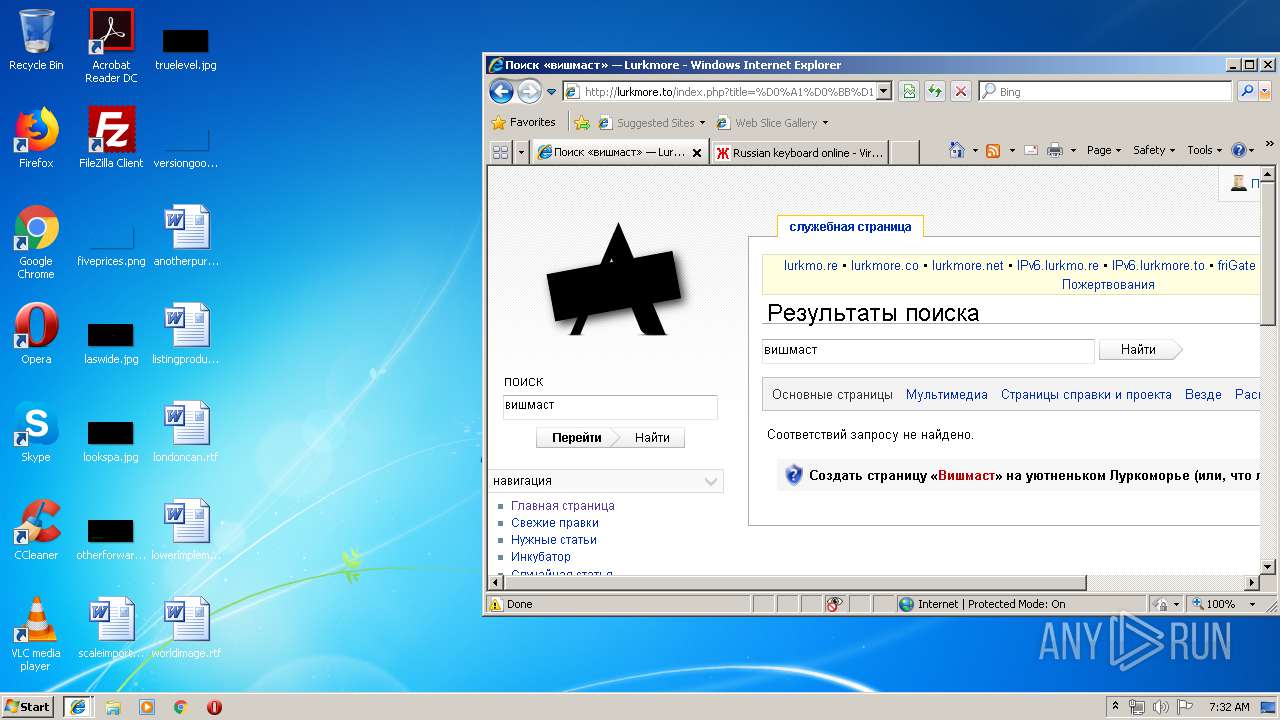
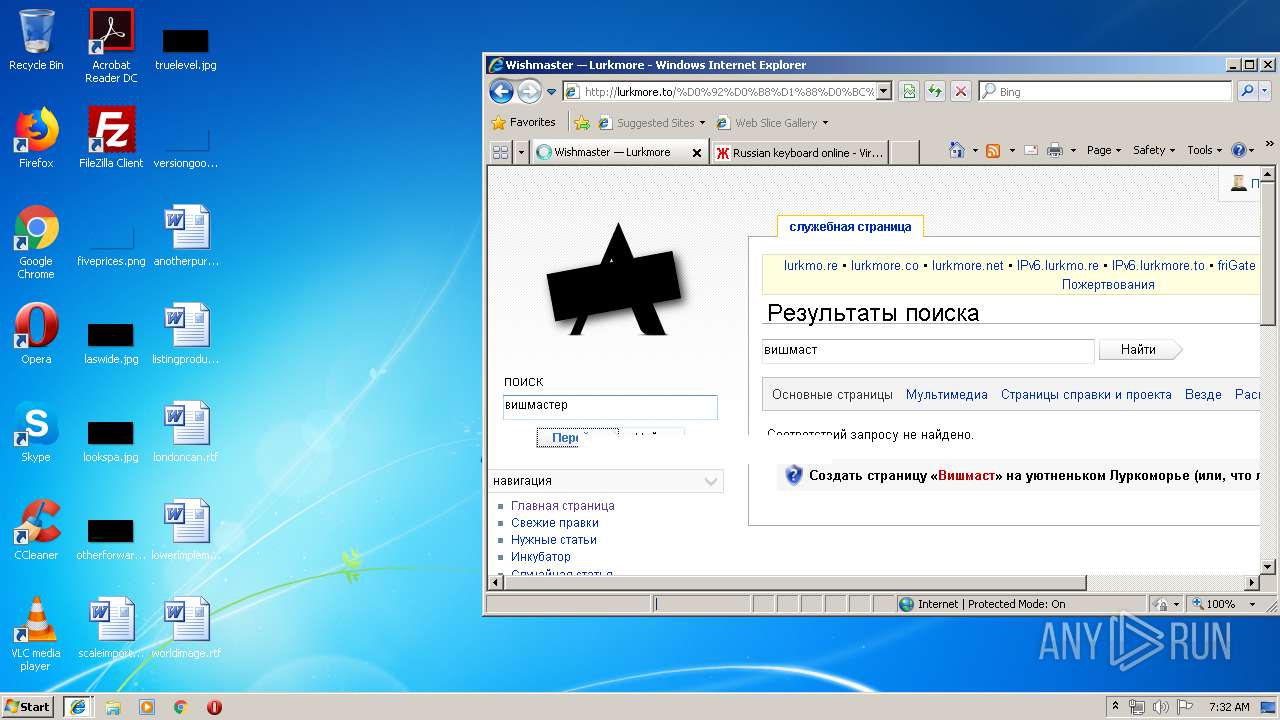
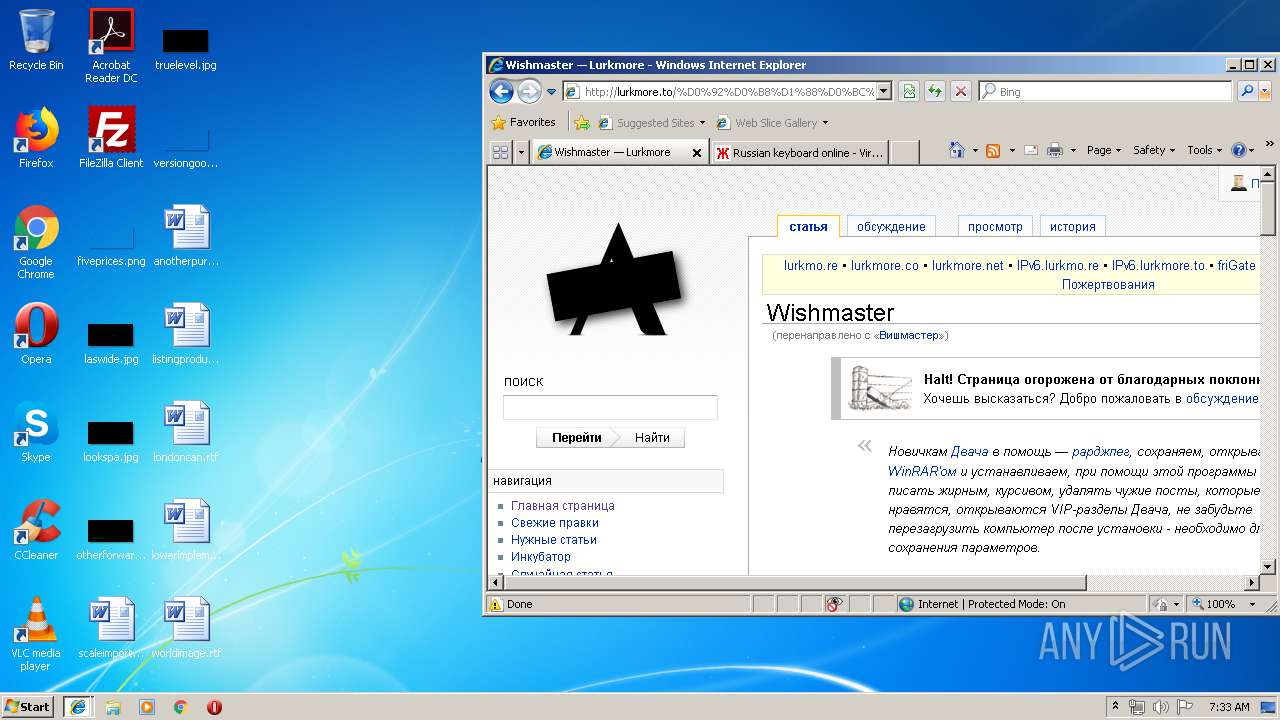
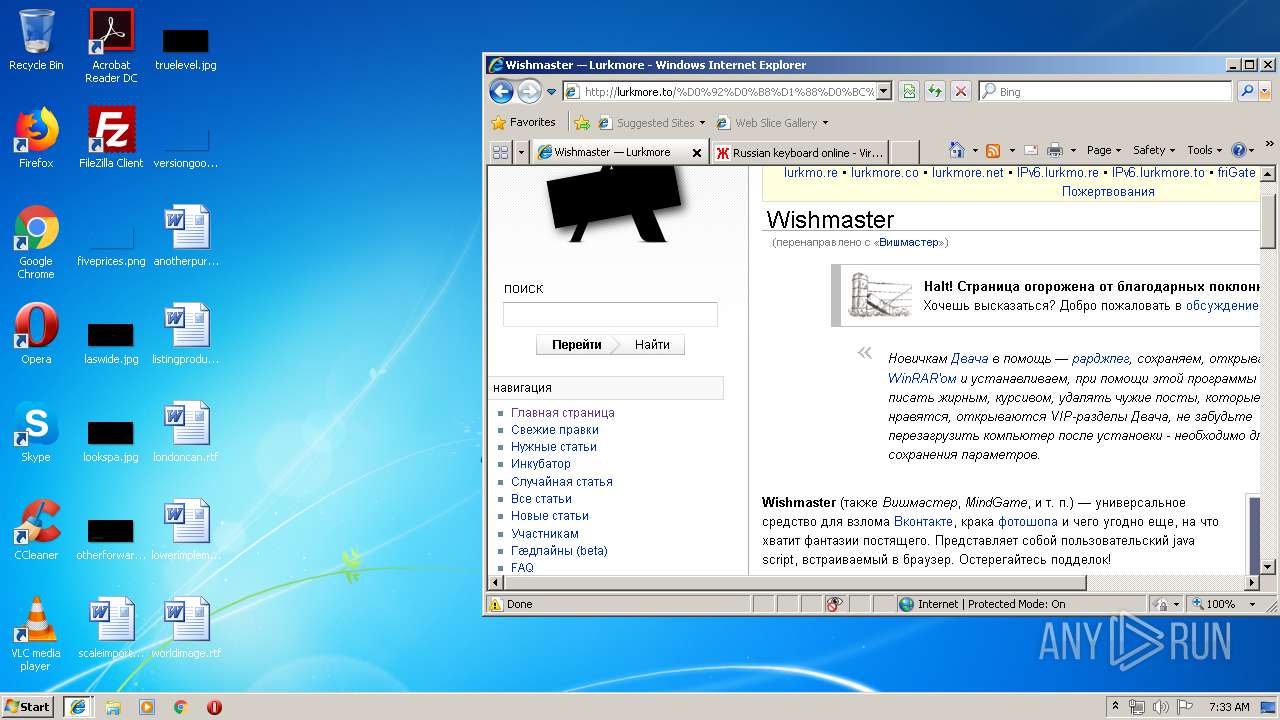
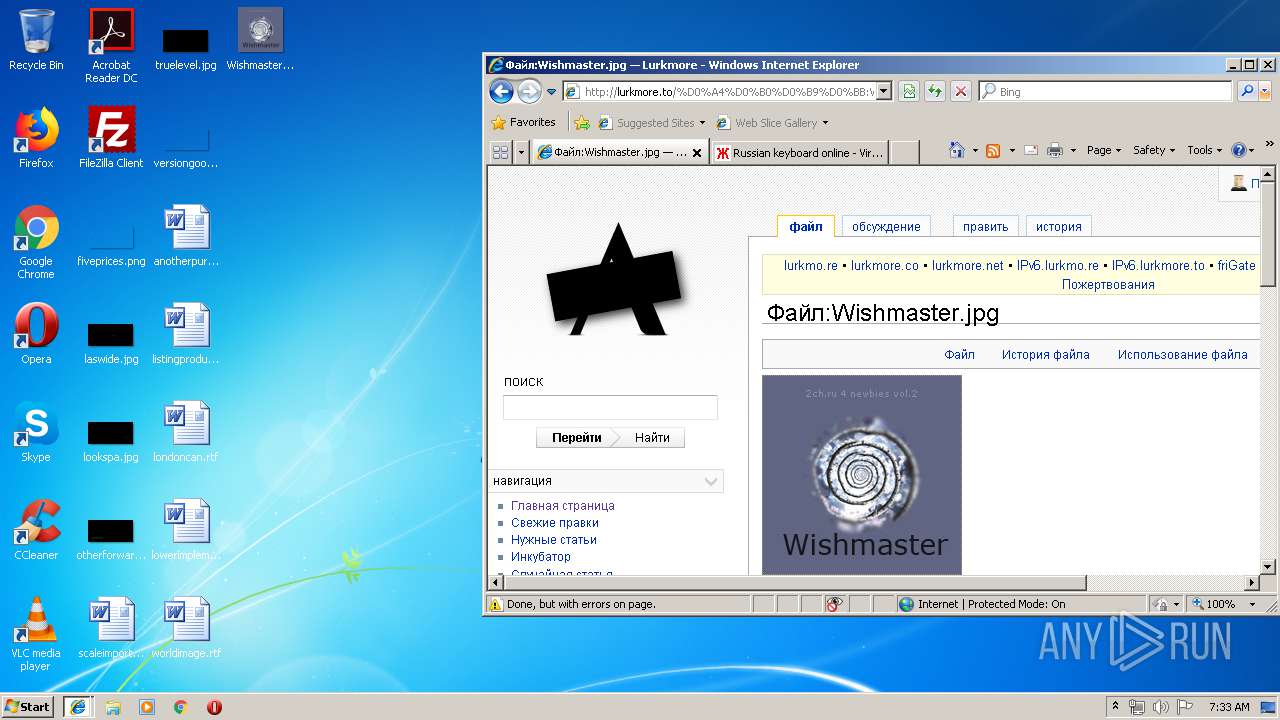
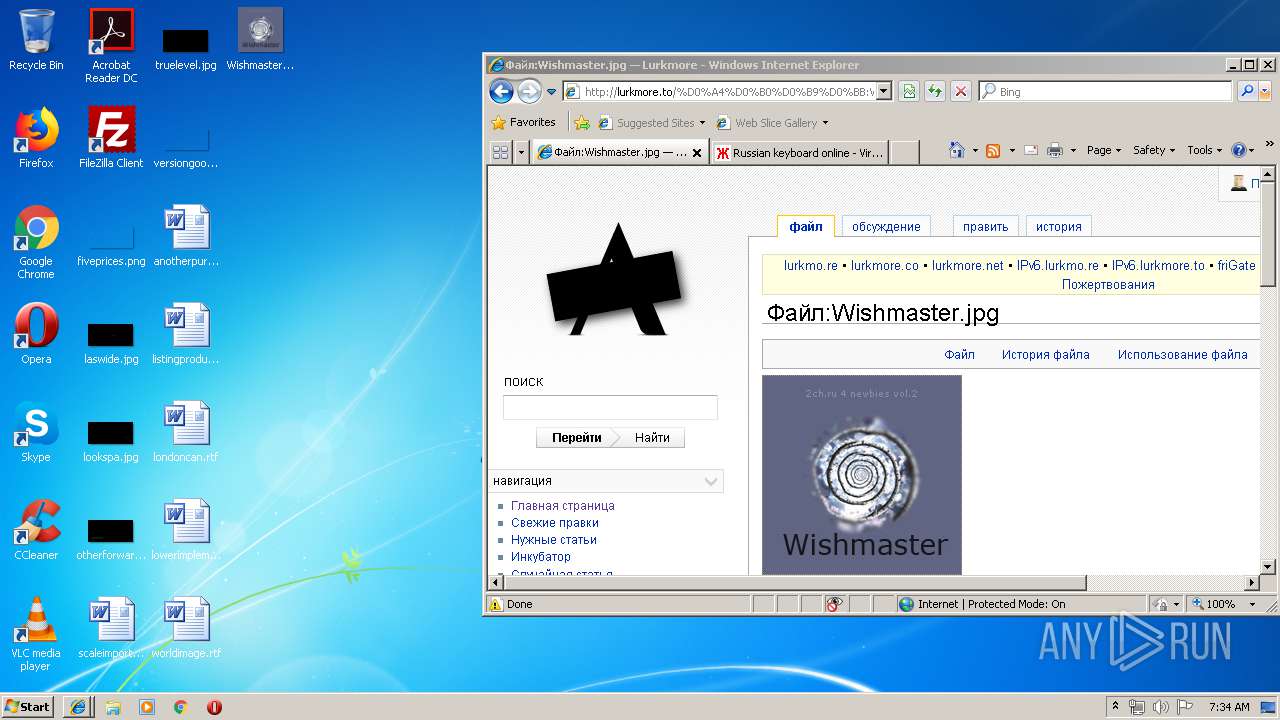
| Title: | Lurkmore |
|---|---|
| Generator: | MediaWiki 1.19.24 |
| Description: | Здравствуйте. Это Луркоморье — русский луркмоар. Вы можете редактировать любую статью, так же как и в Википедии. Но, в отличие от википедии, мы не ставим своей целью написать обо всем на свете сразу и не руководствуемся мифическими критериями «значимости» и «энциклопедичности». Само получается. |
| ResourceLoaderDynamicStyles: | - |
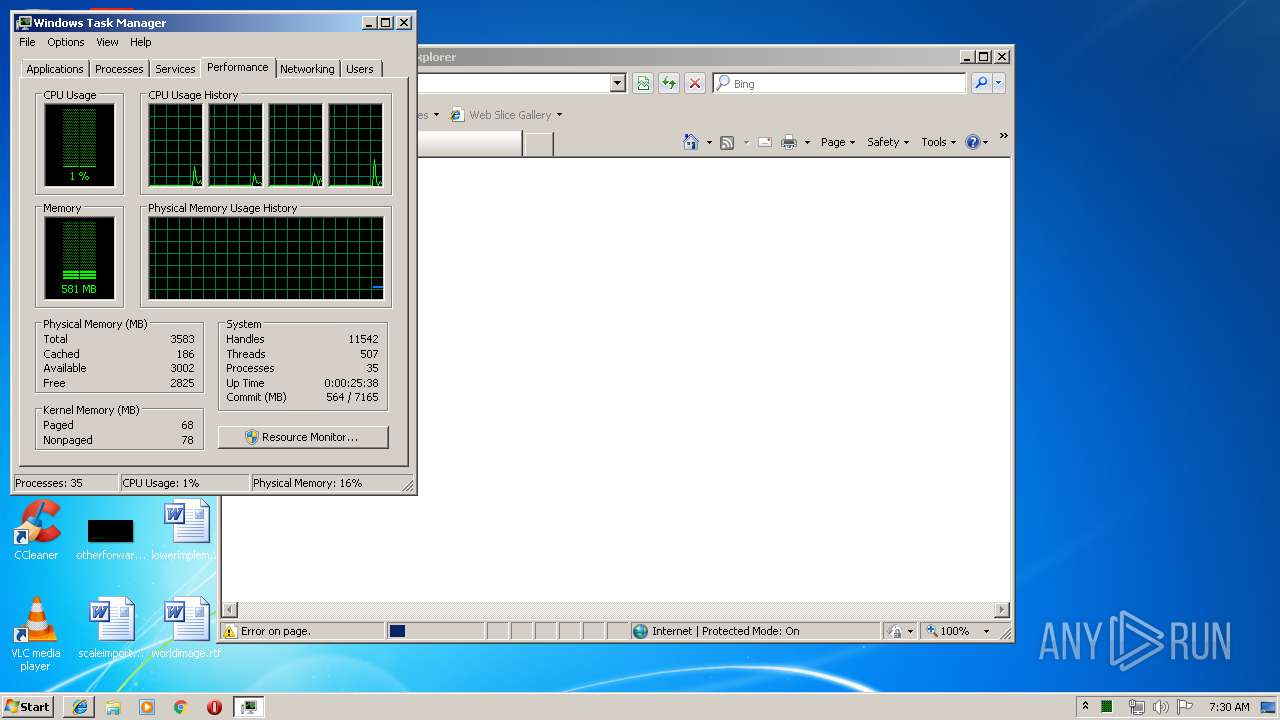
Total processes
56
Monitored processes
11
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1524 | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 26.0 r0 Exit code: 1073807364 Version: 26,0,0,131 Modules
| |||||||||||||||
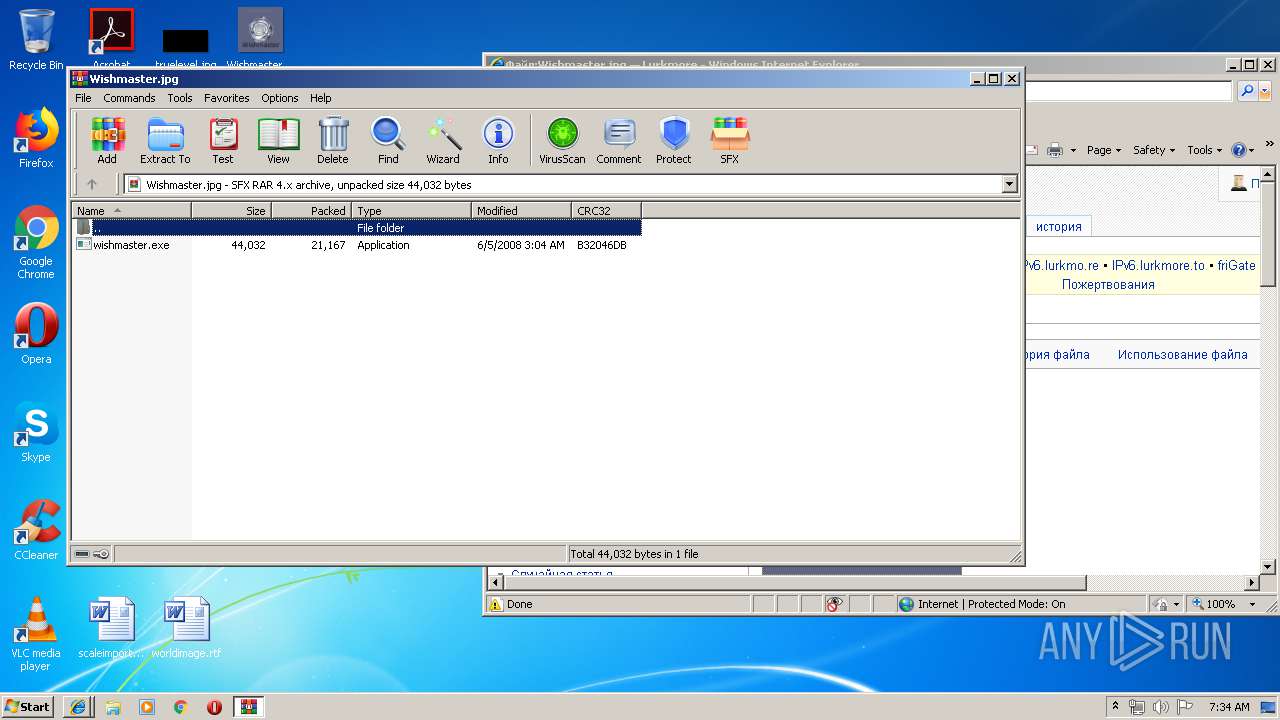
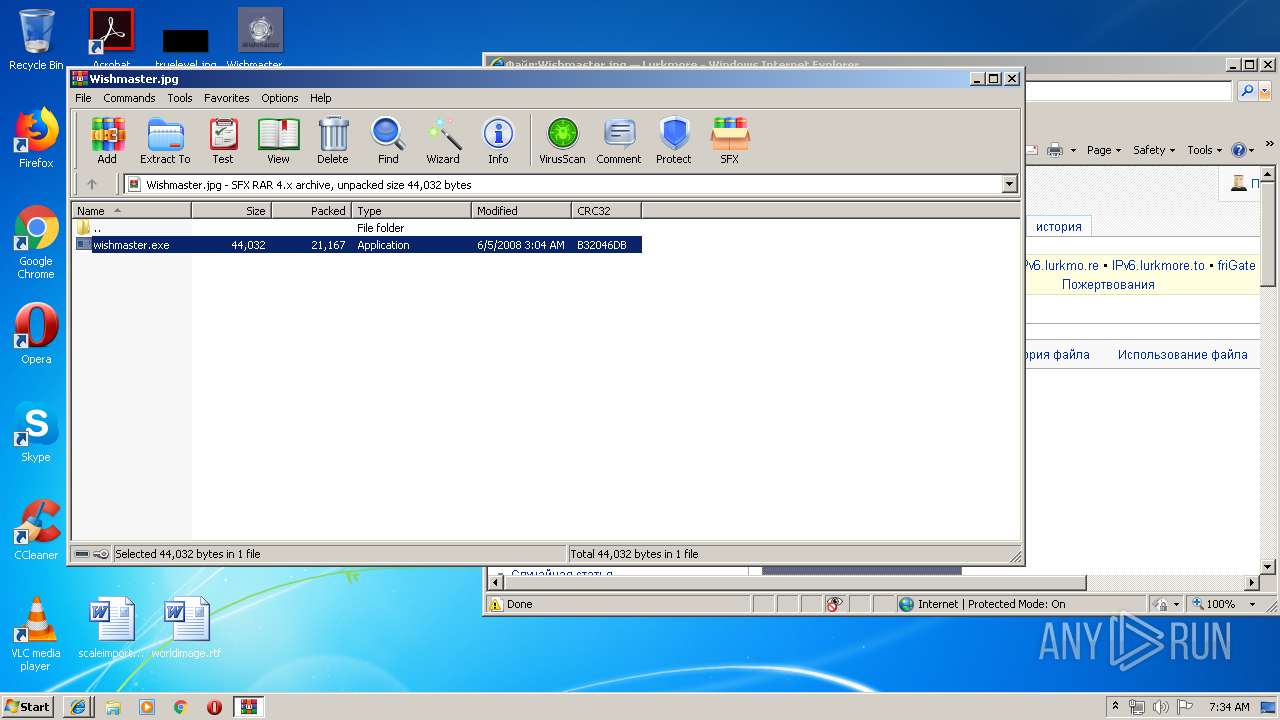
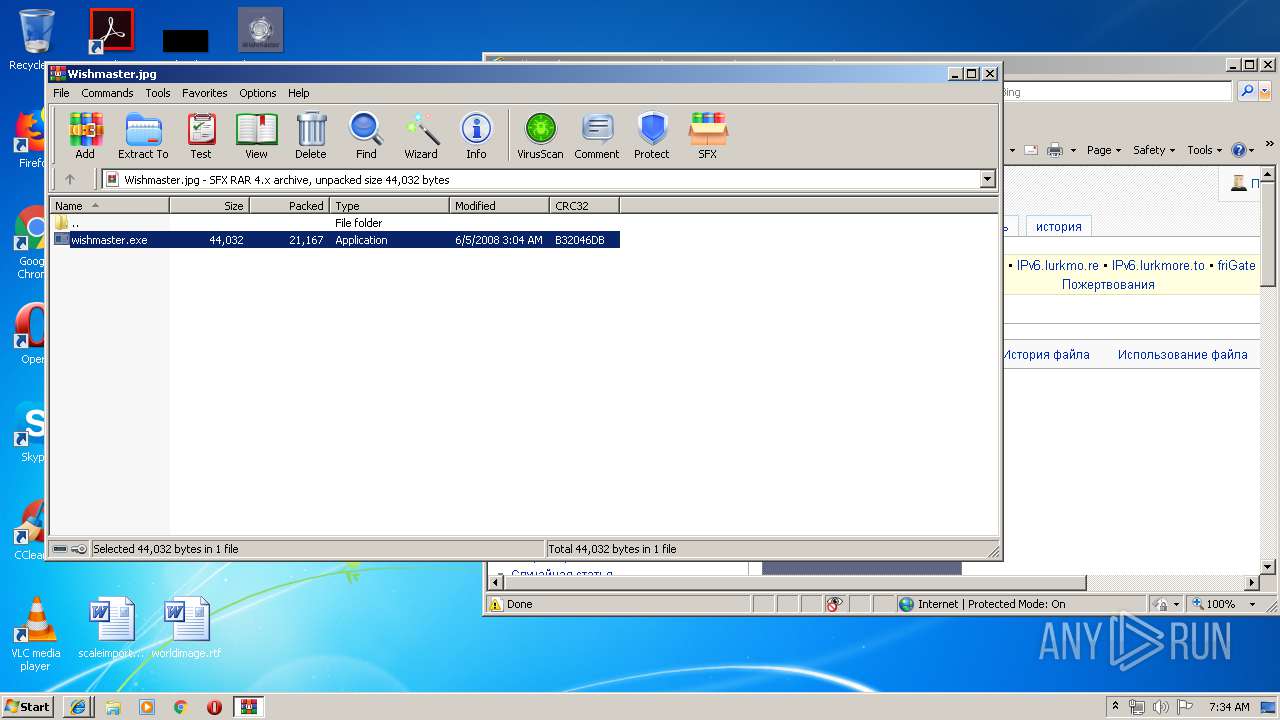
| 1584 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2824.5104\wishmaster.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2824.5104\wishmaster.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
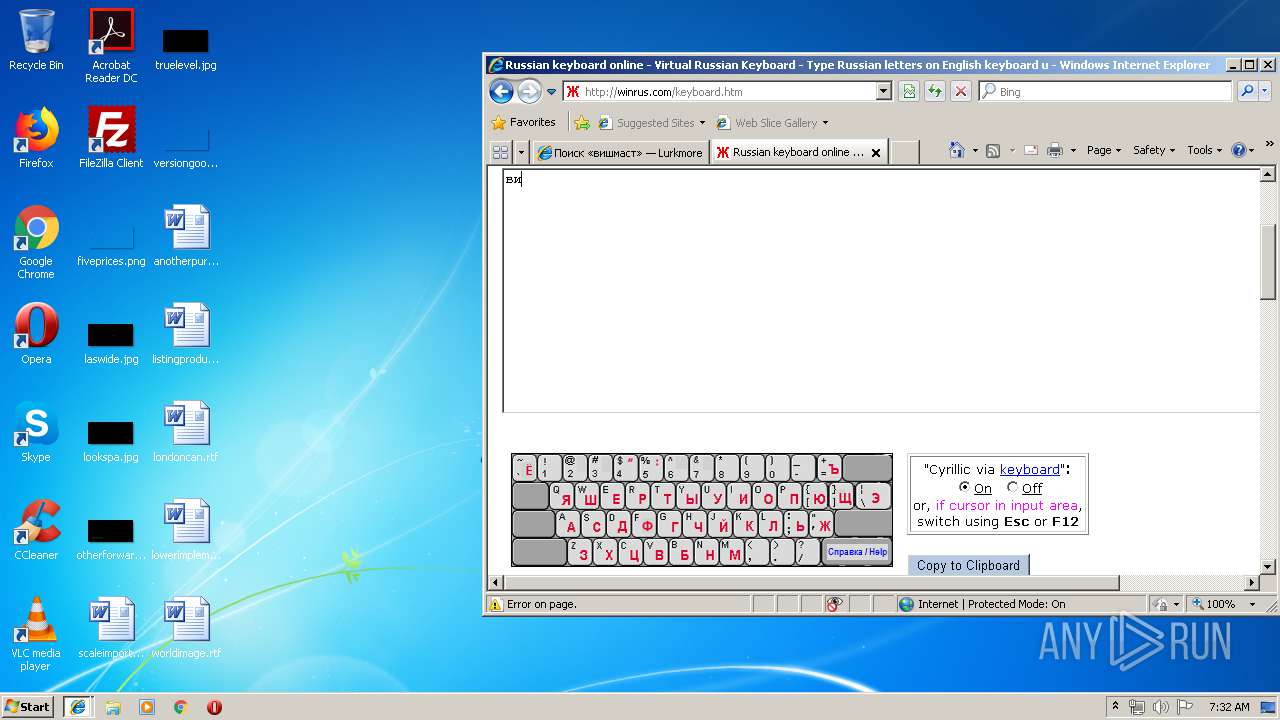
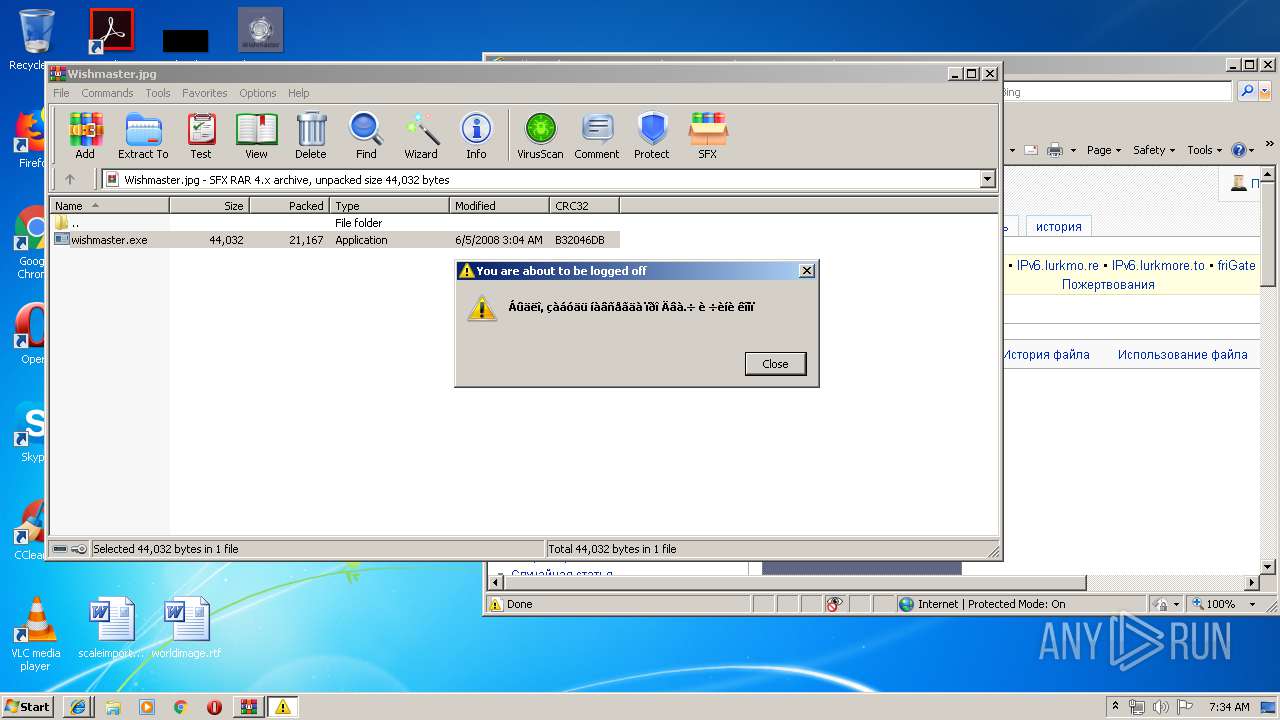
| 2388 | shutdown -r -t 10 -c "Áûäëî, çàáóäü íàâñåãäà ïðî Äâà.÷ è ÷èíè êîìï" | C:\Windows\system32\shutdown.exe | — | wishmaster.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shutdown and Annotation Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2400 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3352 CREDAT:6422 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
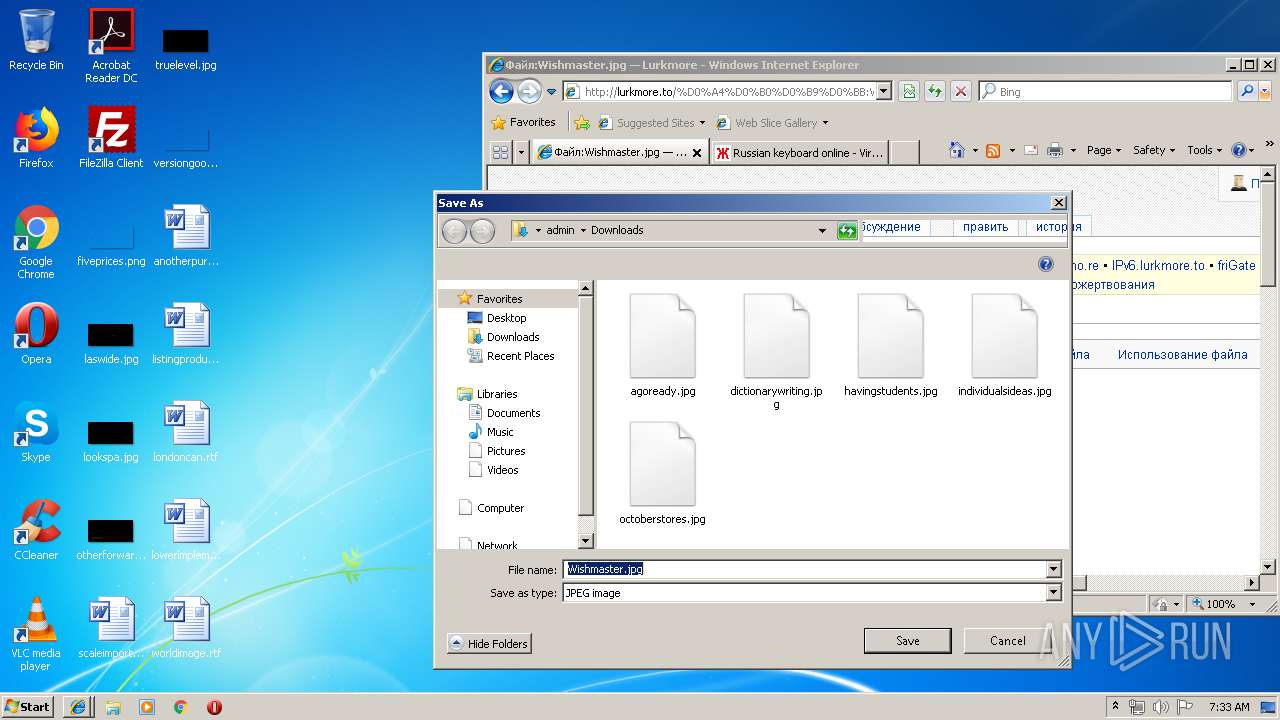
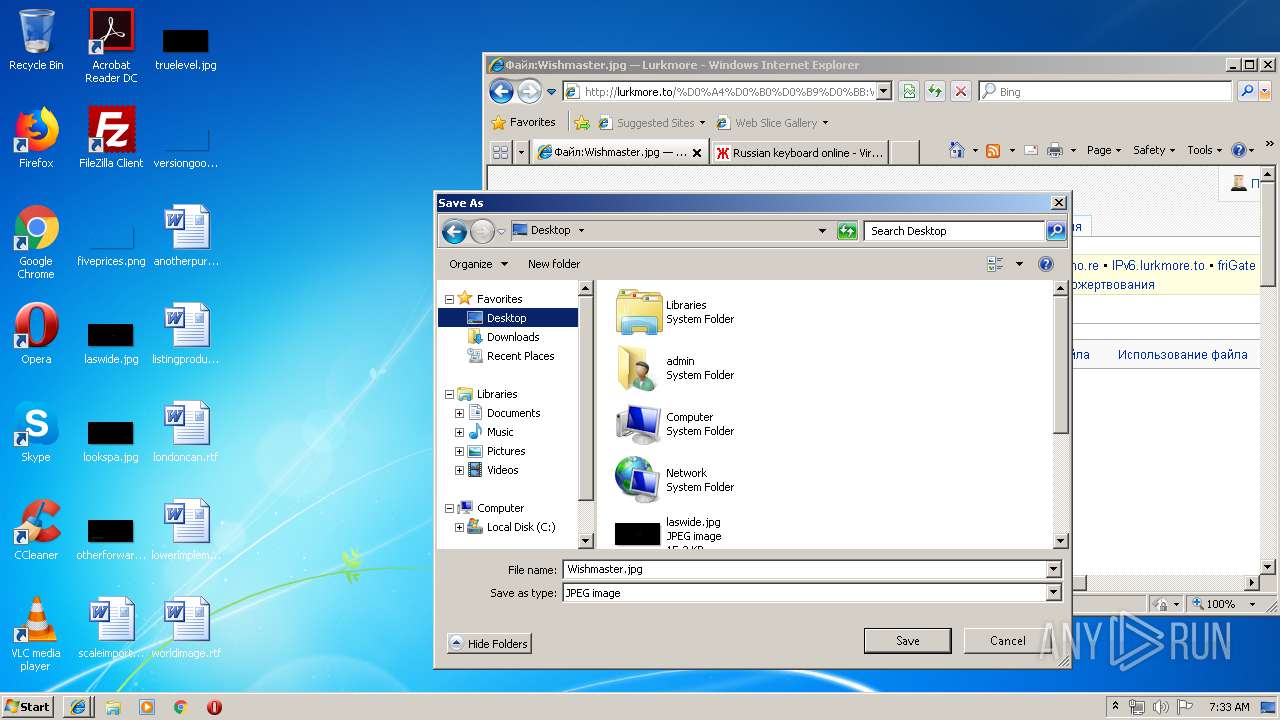
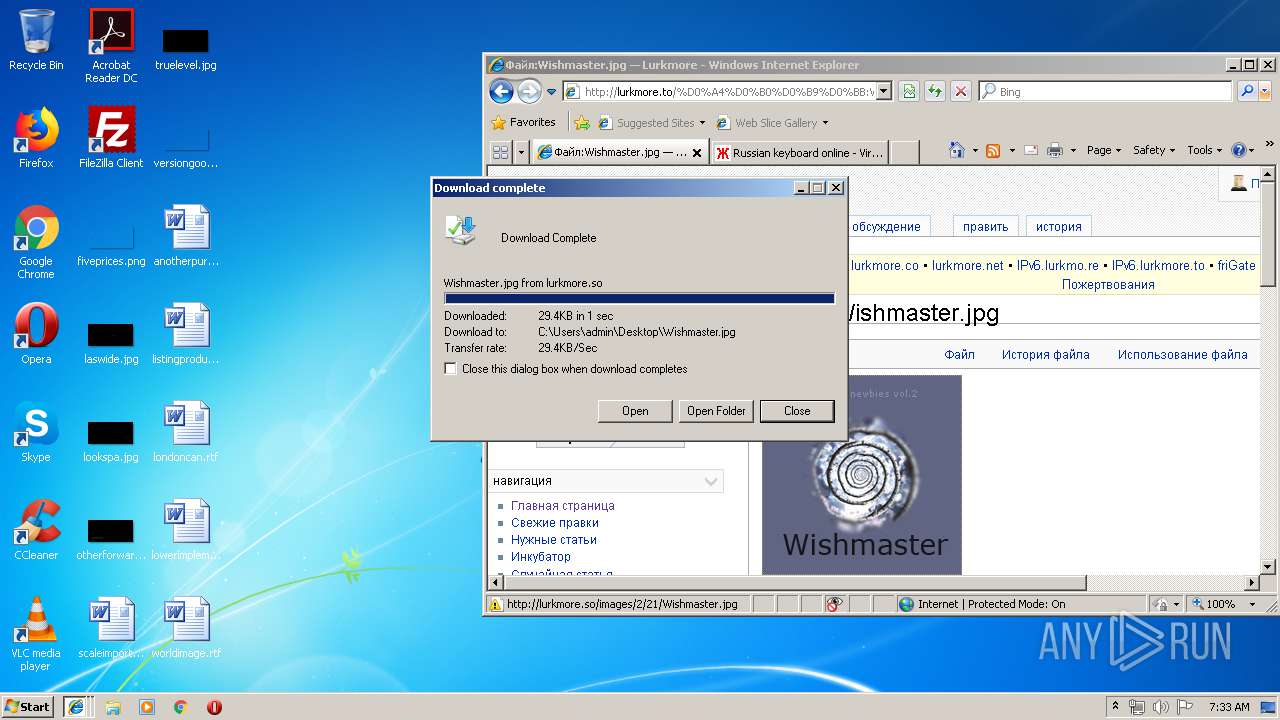
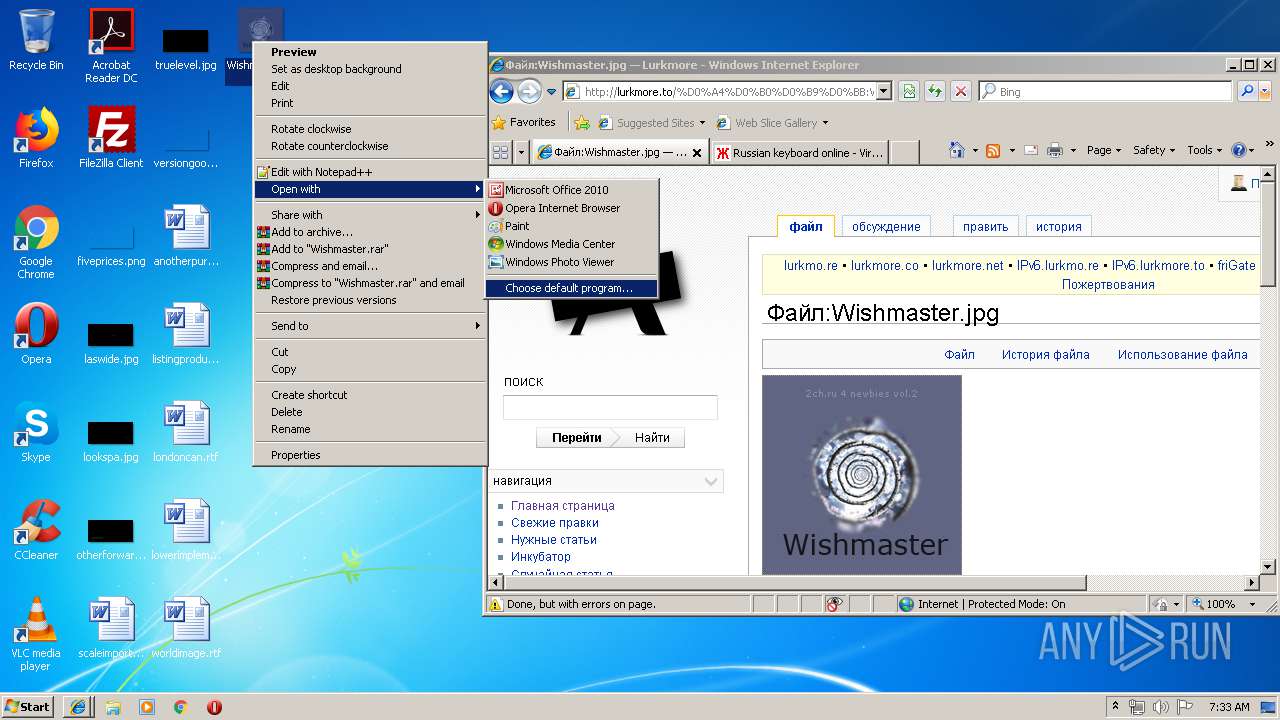
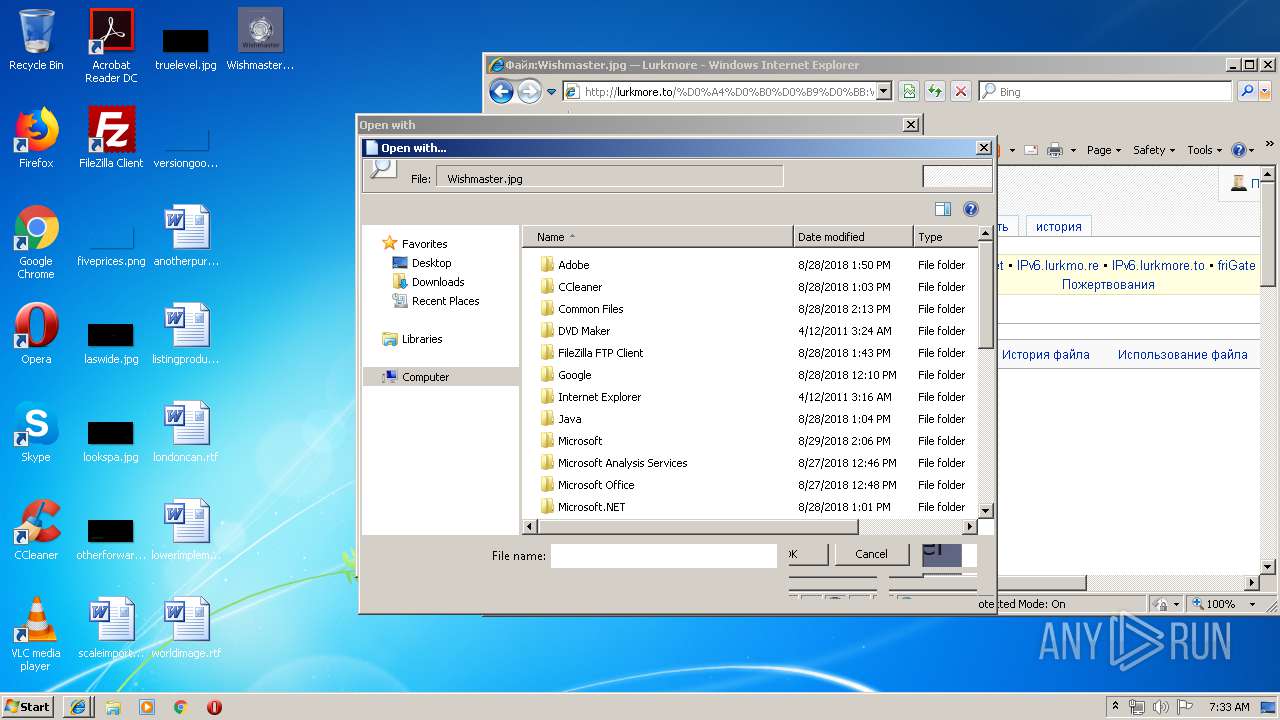
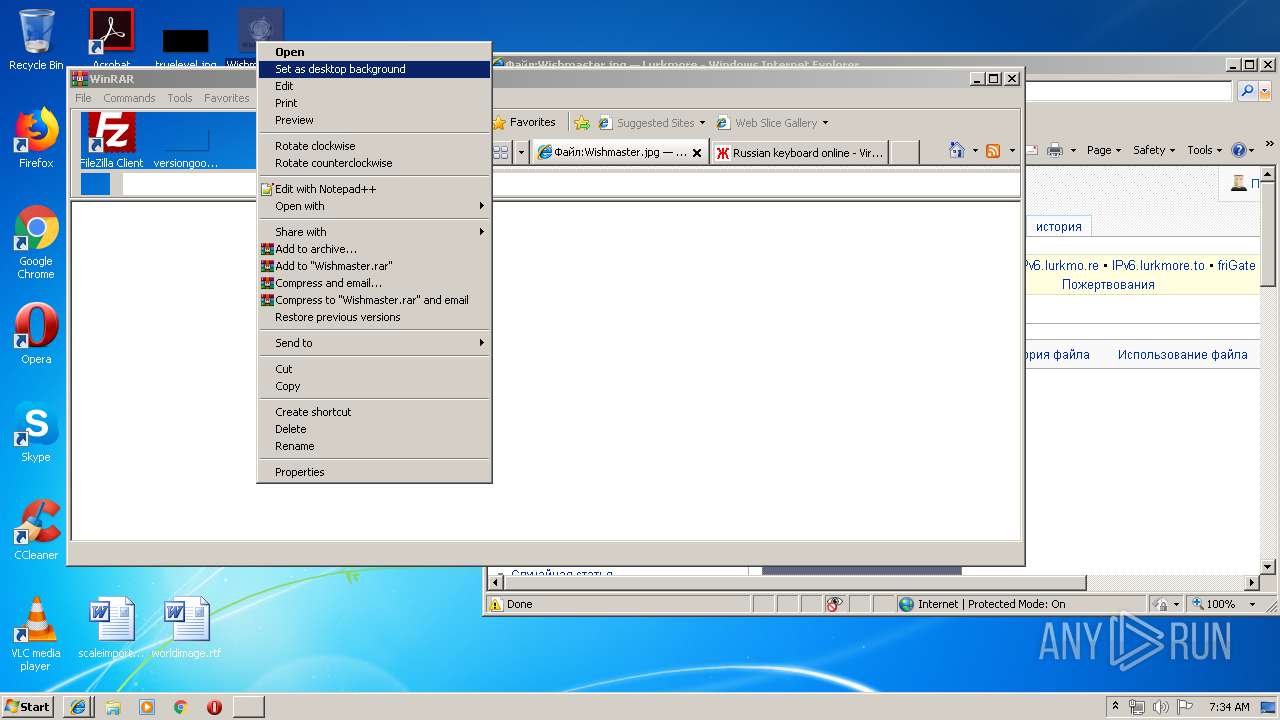
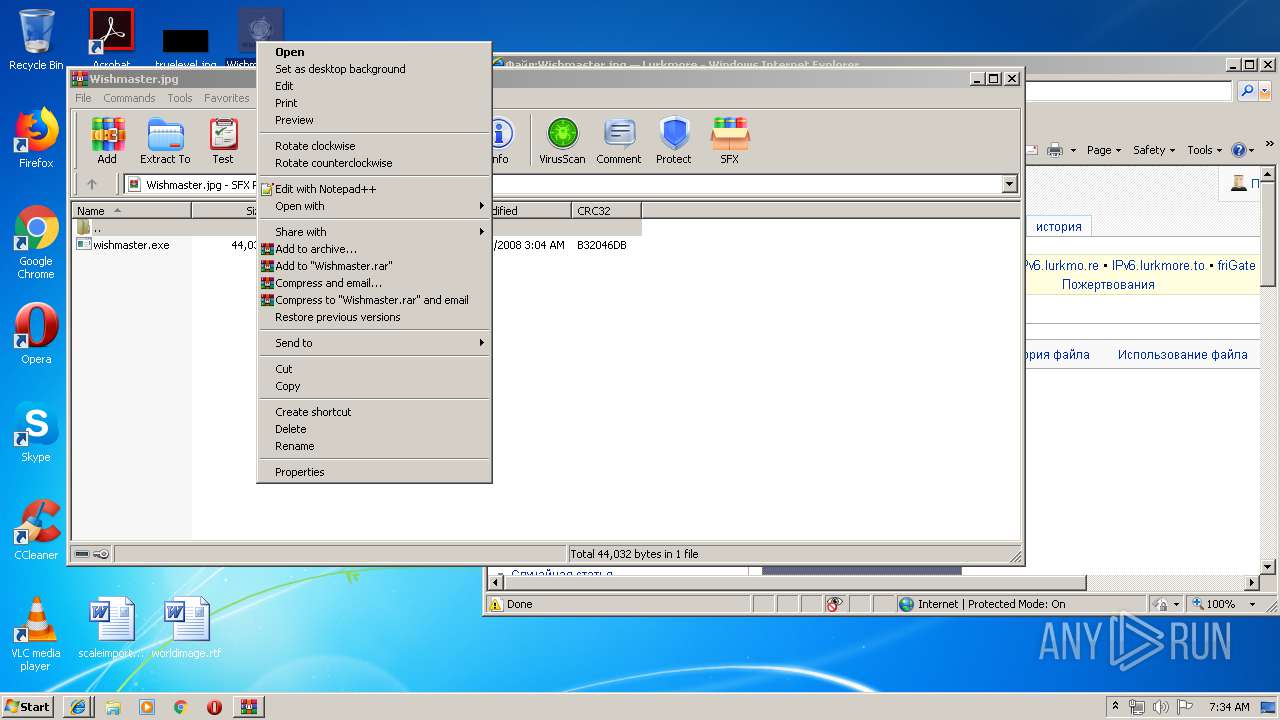
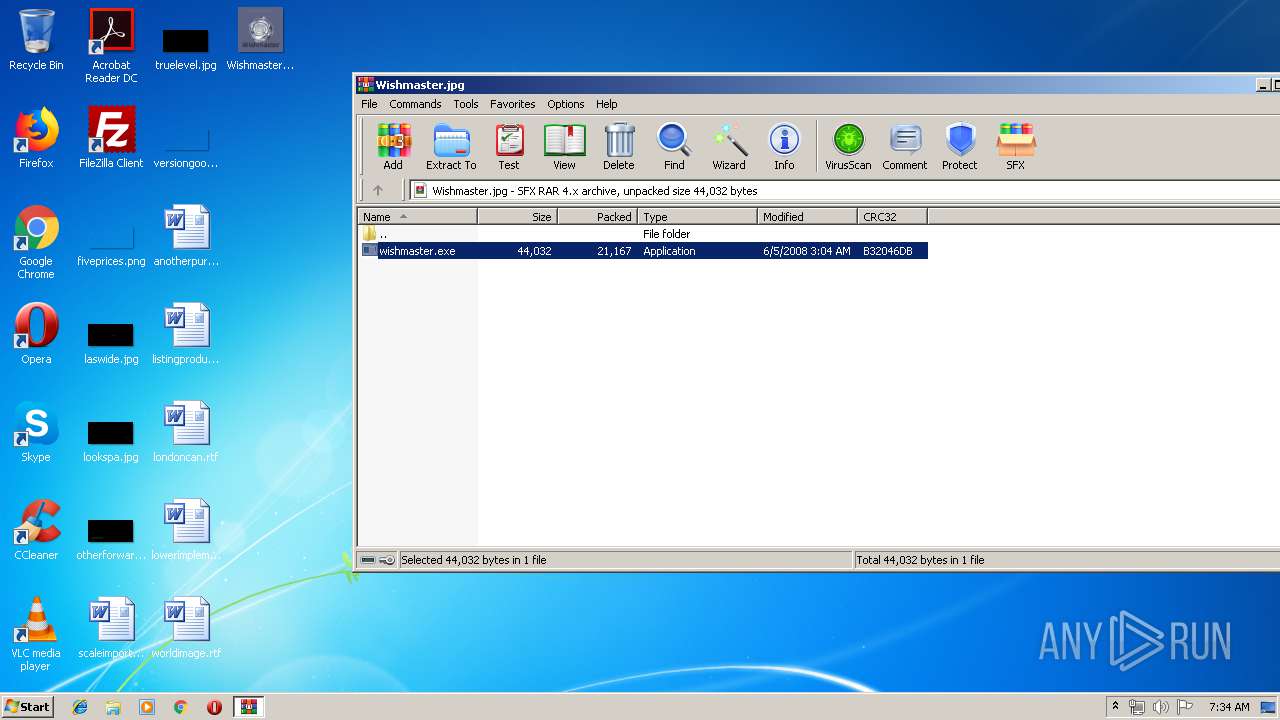
| 2824 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\Wishmaster.jpg" | C:\Program Files\WinRAR\WinRAR.exe | rundll32.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 1073807364 Version: 5.60.0 Modules
| |||||||||||||||
| 3280 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3352 CREDAT:137473 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3352 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\AppData\Local\Temp\index.html | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1073807364 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3476 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\system32\taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3820 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3352 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
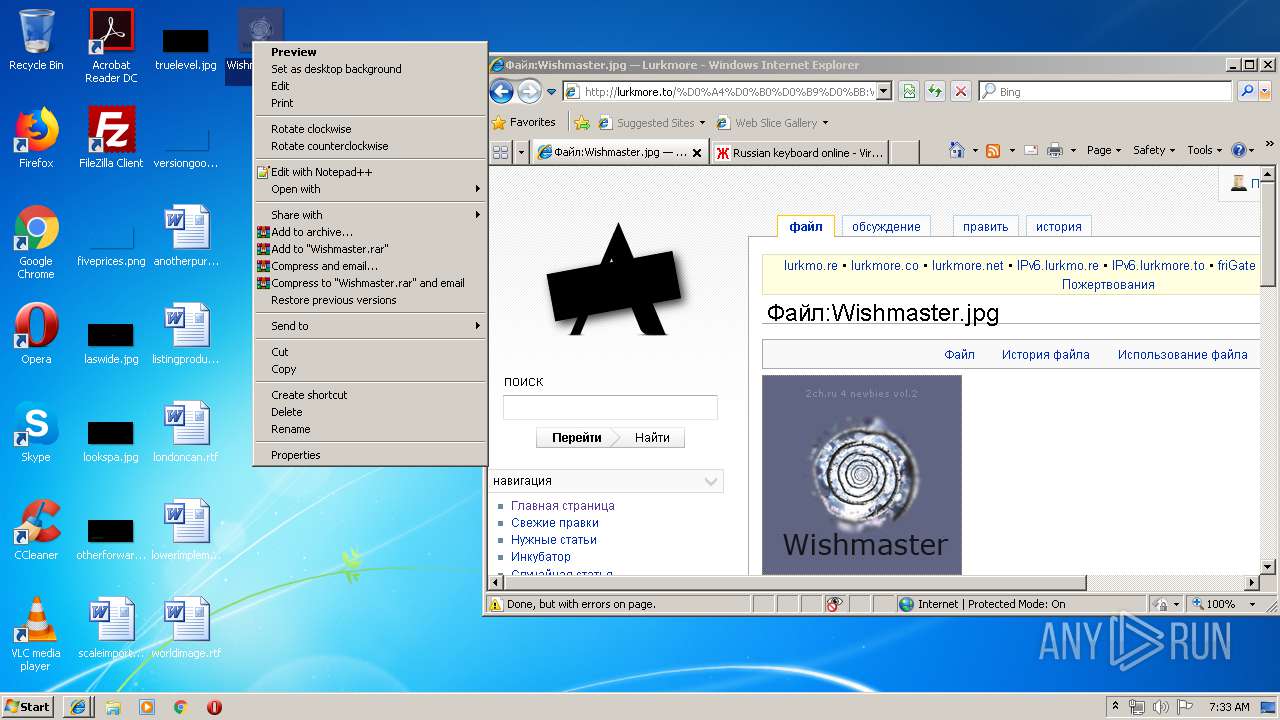
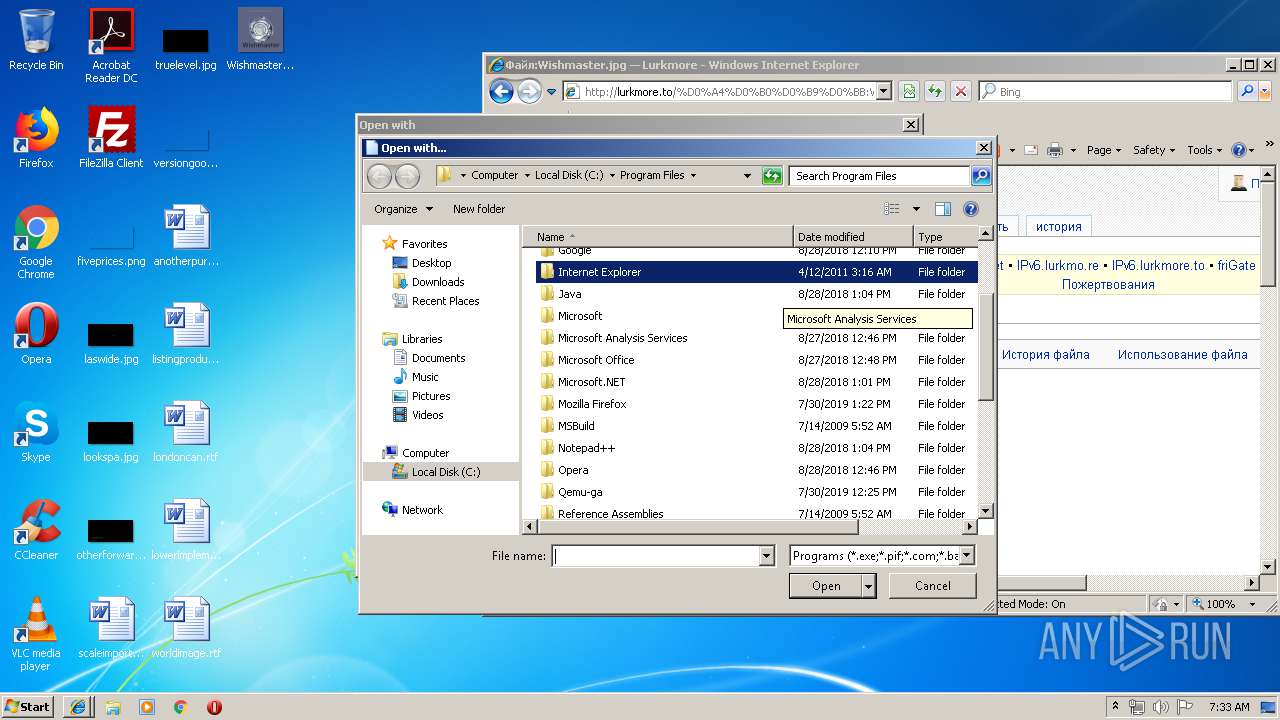
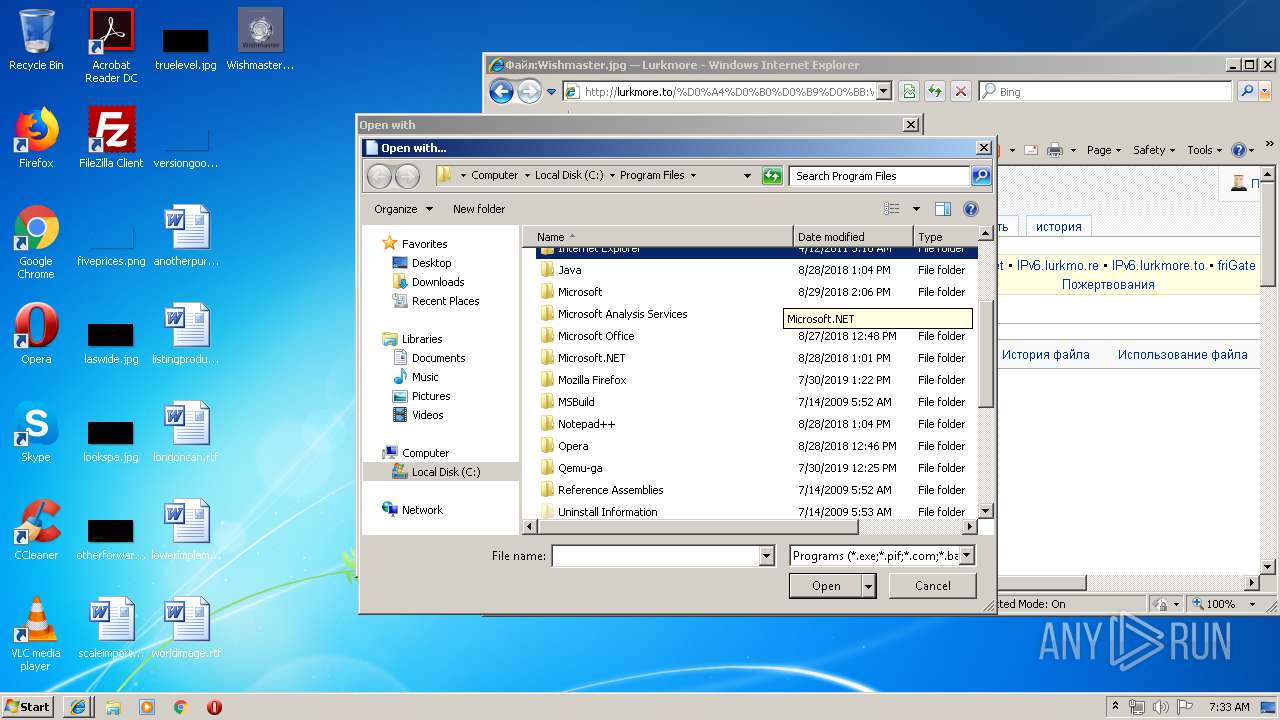
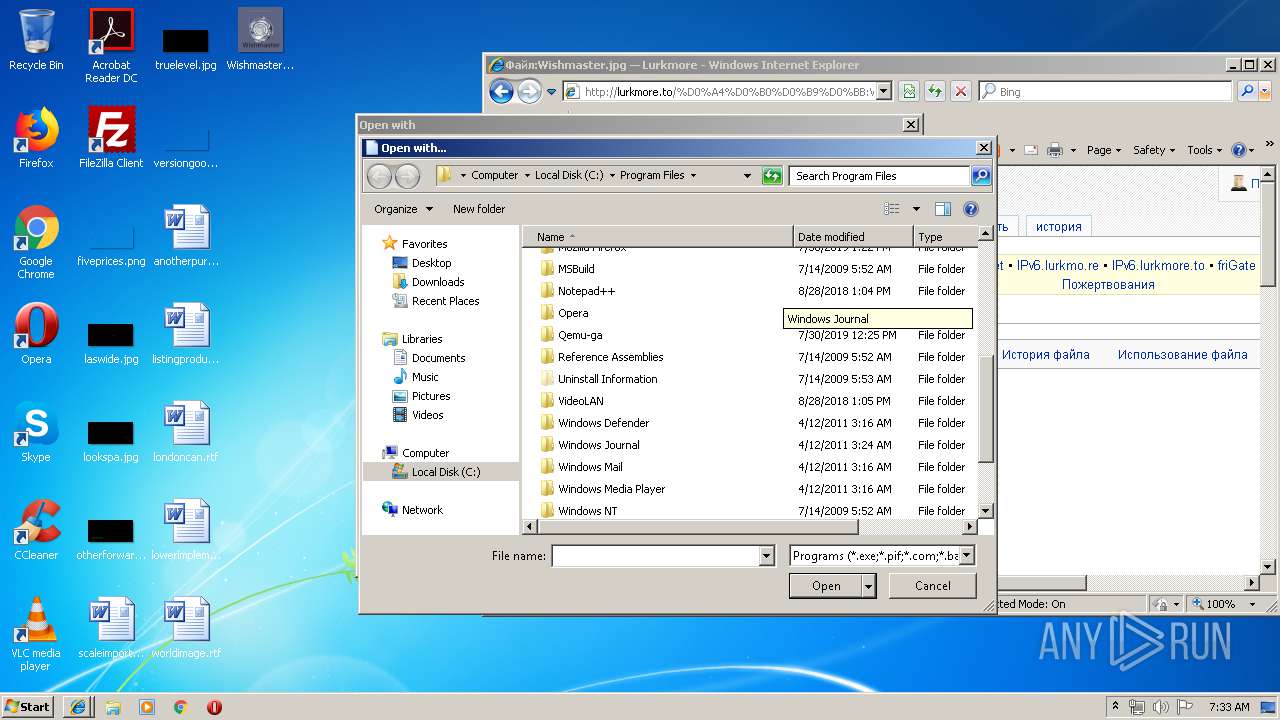
| 4036 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\Desktop\Wishmaster.jpg | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
3 001
Read events
2 468
Write events
528
Delete events
5
Modification events
| (PID) Process: | (3352) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3352) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3352) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3352) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (3352) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3352) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000092000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3352) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {85D60631-C181-11E9-B86F-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (3820) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{761497BB-D6F0-462C-B6EB-D4DAF1D92D43}\iexplore |
| Operation: | write | Name: | Type |
Value: 3 | |||
| (PID) Process: | (3820) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{761497BB-D6F0-462C-B6EB-D4DAF1D92D43}\iexplore |
| Operation: | write | Name: | Count |
Value: 2 | |||
| (PID) Process: | (3820) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{761497BB-D6F0-462C-B6EB-D4DAF1D92D43}\iexplore |
| Operation: | write | Name: | Time |
Value: E30708000000120006001D001A00AC02 | |||
Executable files
1
Suspicious files
4
Text files
235
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3352 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3352 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3280 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\QU1UU192\lurkmore_to[1].txt | — | |
MD5:— | SHA256:— | |||
| 3280 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 3352 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\StructuredQuery.log | text | |
MD5:— | SHA256:— | |||
| 3280 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@rareru[1].txt | text | |
MD5:— | SHA256:— | |||
| 3280 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\QU71T5GQ\load[1].php | text | |
MD5:— | SHA256:— | |||
| 3280 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\0A7I78I2\f[1].txt | text | |
MD5:— | SHA256:— | |||
| 3280 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\Low\History.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 3280 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\QU1UU192\lurkmore_to[1].htm | html | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
152
TCP/UDP connections
117
DNS requests
36
Threats
3
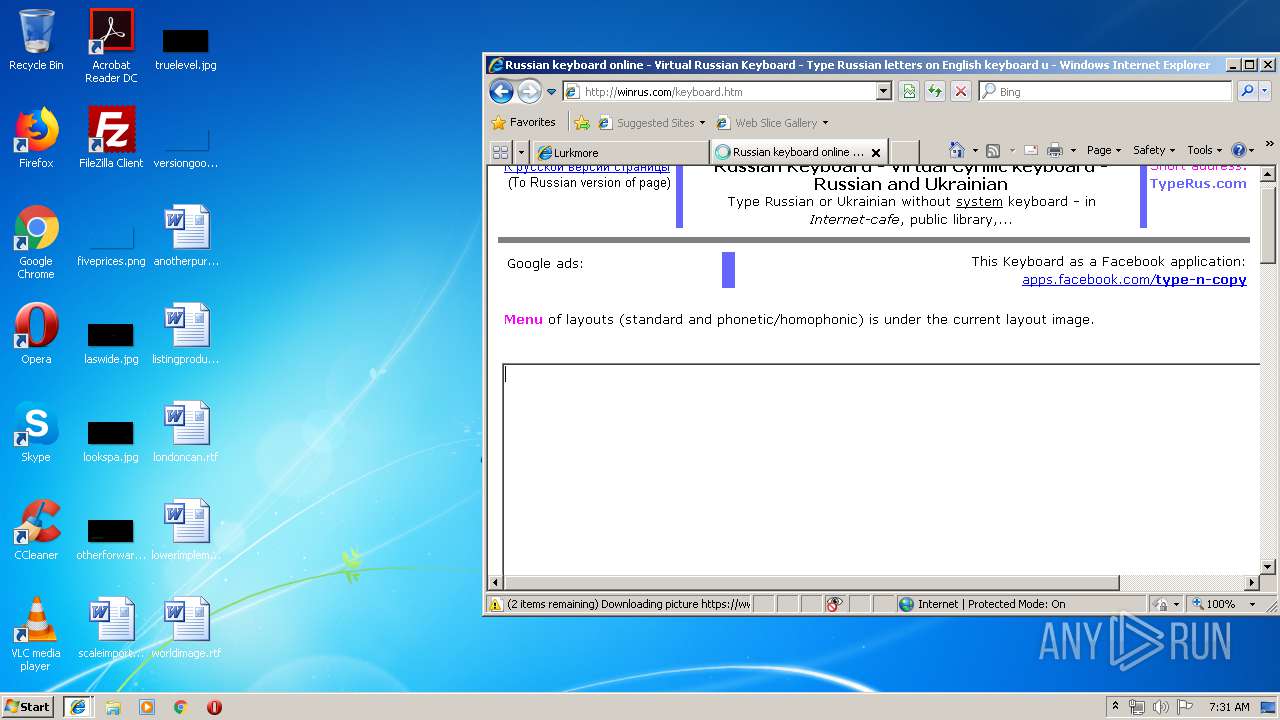
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3280 | iexplore.exe | GET | 302 | 188.42.191.196:80 | http://ads.betweendigital.com/sspmatch-js?randsalt=3324089784 | LU | — | — | whitelisted |
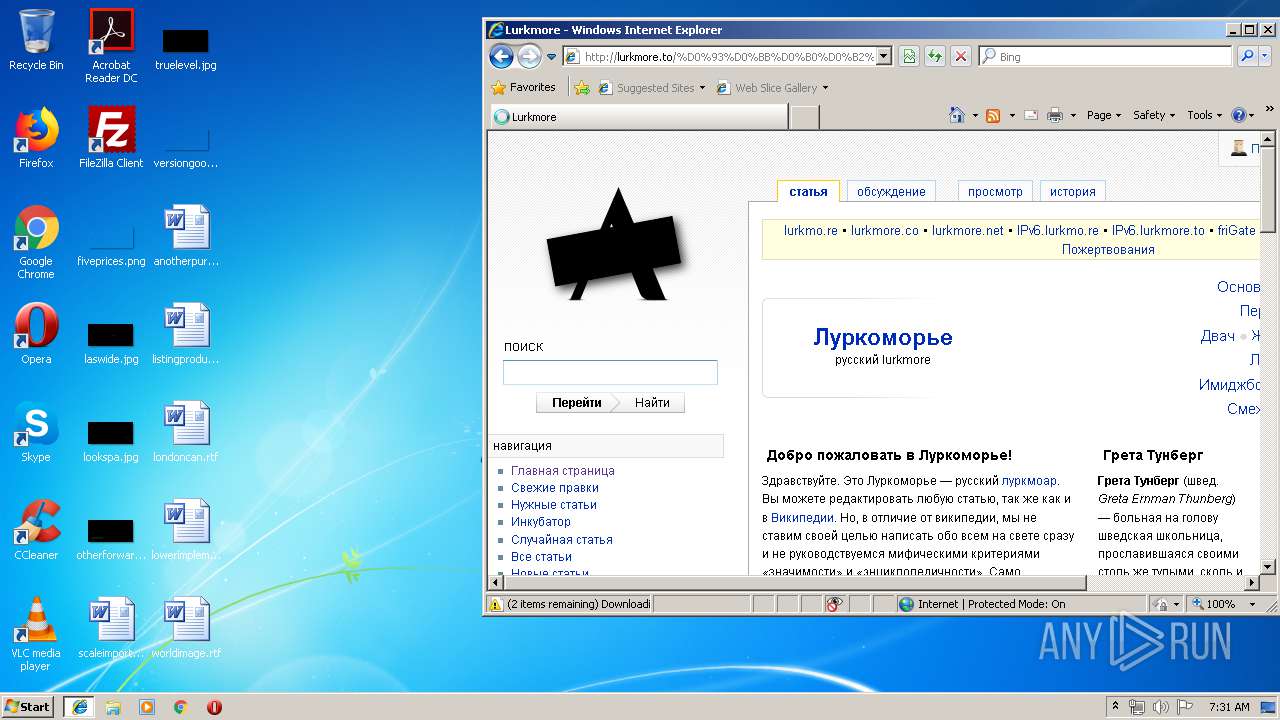
3280 | iexplore.exe | GET | 200 | 188.42.196.32:80 | http://lurkmore.to/load.php?debug=false&lang=ru&modules=mediawiki.legacy.commonPrint%2Cshared&only=styles&skin=ventus&* | LU | text | 13.0 Kb | whitelisted |
3280 | iexplore.exe | GET | 200 | 188.42.196.32:80 | http://lurkmore.to/ | LU | html | 13.2 Kb | whitelisted |
3280 | iexplore.exe | GET | 200 | 77.88.21.90:80 | http://an.yandex.ru/system/context.js | RU | text | 16.3 Kb | whitelisted |
3280 | iexplore.exe | GET | 200 | 188.42.196.32:80 | http://lurkmore.to/skins/common/common.css | LU | text | 17.7 Kb | whitelisted |
3280 | iexplore.exe | GET | 200 | 188.42.196.32:80 | http://lurkmore.to/skins/ventus/main.css?303 | LU | text | 16.1 Kb | whitelisted |
3280 | iexplore.exe | GET | 200 | 178.154.131.215:80 | http://yastatic.net/pcode/adfox/header-bidding.js | RU | text | 37.3 Kb | whitelisted |
3280 | iexplore.exe | GET | 200 | 188.42.196.32:80 | http://lurkmore.to/load.php?debug=false&lang=ru&modules=startup&only=scripts&skin=ventus&* | LU | text | 3.39 Kb | whitelisted |
3280 | iexplore.exe | GET | 200 | 188.42.196.32:80 | http://lurkmore.to/skins/common/title/titlepage.css | LU | text | 15.9 Kb | whitelisted |
3280 | iexplore.exe | GET | 200 | 178.154.131.216:80 | http://yastatic.net/pcode/adfox/loader.js | RU | text | 41.9 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 188.42.196.32:445 | lurkmore.to | Servers.com, Inc. | LU | suspicious |
4 | System | 216.58.205.226:445 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
3280 | iexplore.exe | 188.42.196.32:80 | lurkmore.to | Servers.com, Inc. | LU | suspicious |
3280 | iexplore.exe | 216.58.205.226:80 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
3280 | iexplore.exe | 77.88.21.90:80 | an.yandex.ru | YANDEX LLC | RU | whitelisted |
3280 | iexplore.exe | 178.154.131.215:80 | yastatic.net | YANDEX LLC | RU | whitelisted |
3280 | iexplore.exe | 94.100.180.197:80 | ad.mail.ru | Limited liability company Mail.Ru | RU | unknown |
4 | System | 77.88.21.90:445 | an.yandex.ru | YANDEX LLC | RU | whitelisted |
4 | System | 93.158.134.90:445 | an.yandex.ru | YANDEX LLC | RU | whitelisted |
4 | System | 213.180.193.90:445 | an.yandex.ru | YANDEX LLC | RU | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
lurkmore.to |
| whitelisted |
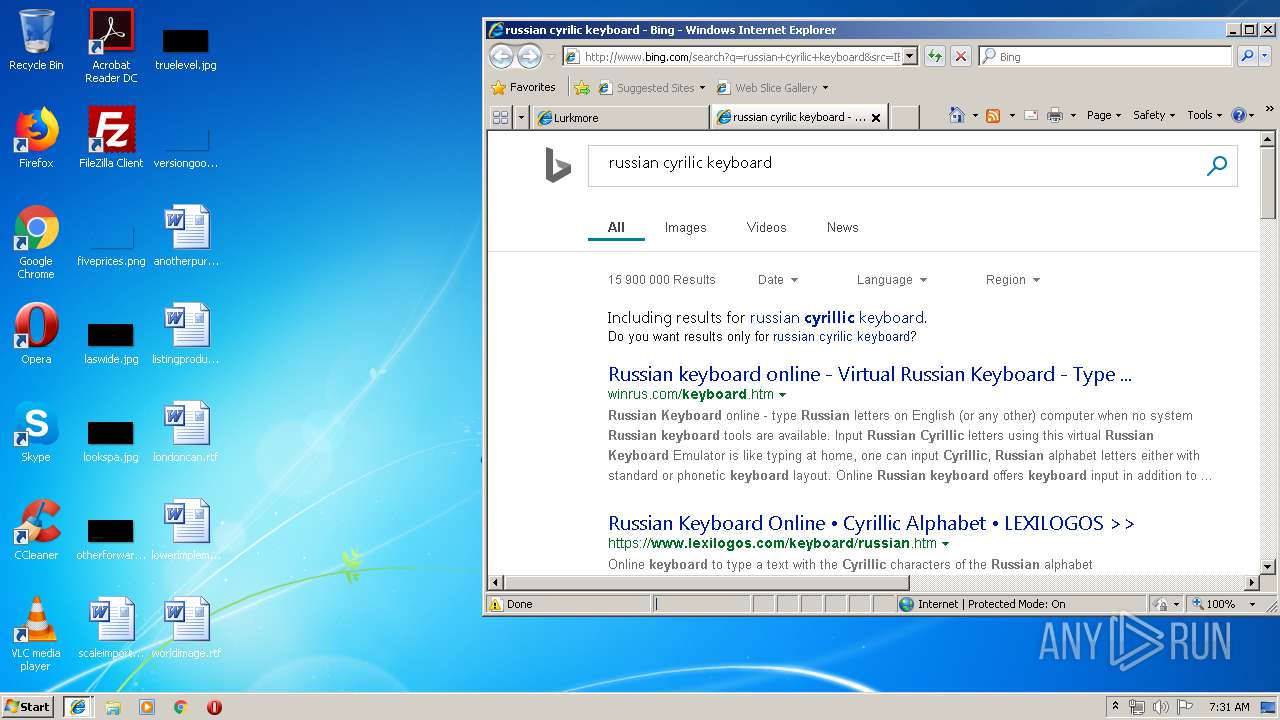
www.bing.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
an.yandex.ru |
| whitelisted |
yastatic.net |
| whitelisted |
abc.rareru.ru |
| unknown |
ax.rareru.ru |
| unknown |
ad.mail.ru |
| whitelisted |
ads.betweendigital.com |
| whitelisted |
counter.yadro.ru |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1060 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
1060 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
1060 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |