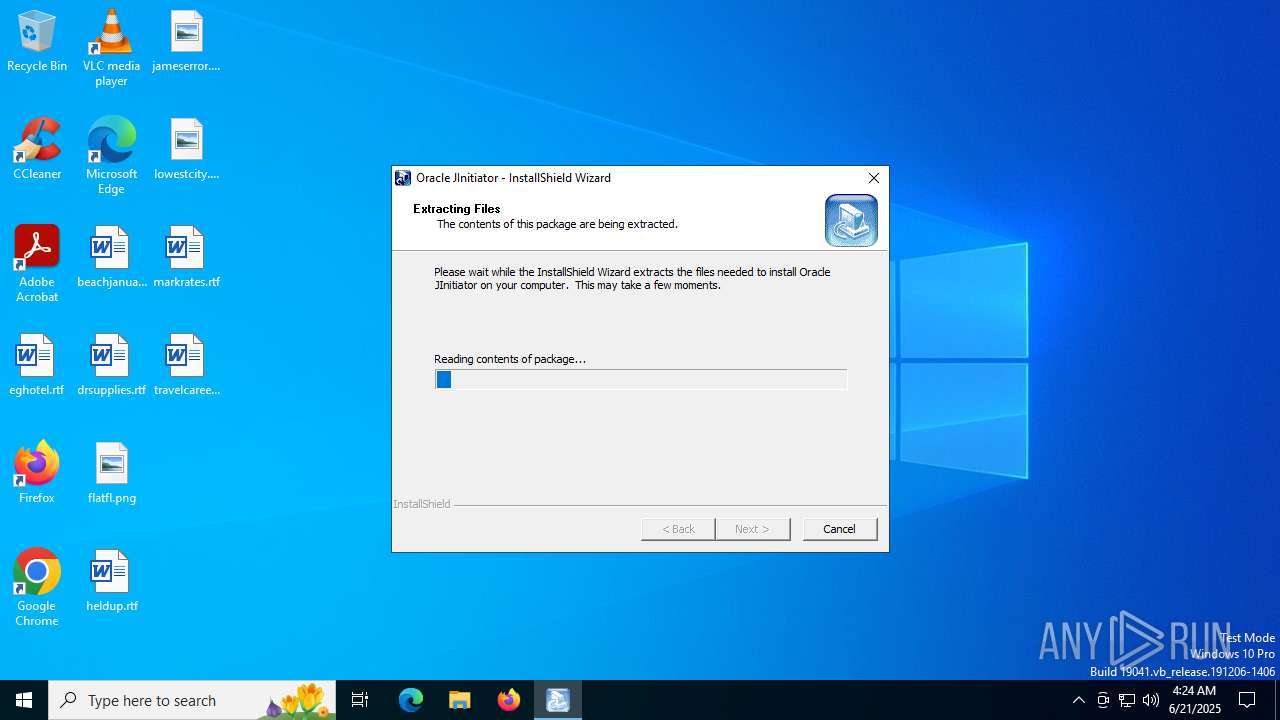
| File name: | jinit.exe_ |
| Full analysis: | https://app.any.run/tasks/b88e9999-7ba9-42c0-a071-1fc9a1fc104b |
| Verdict: | Malicious activity |
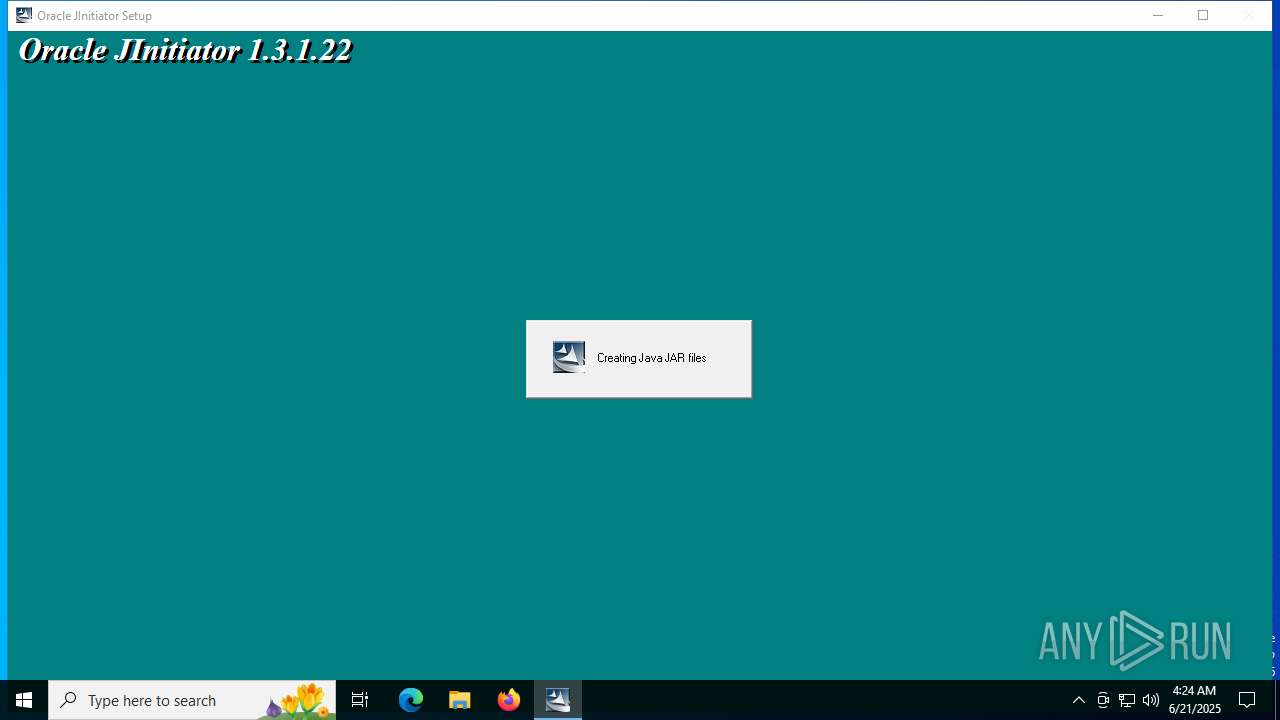
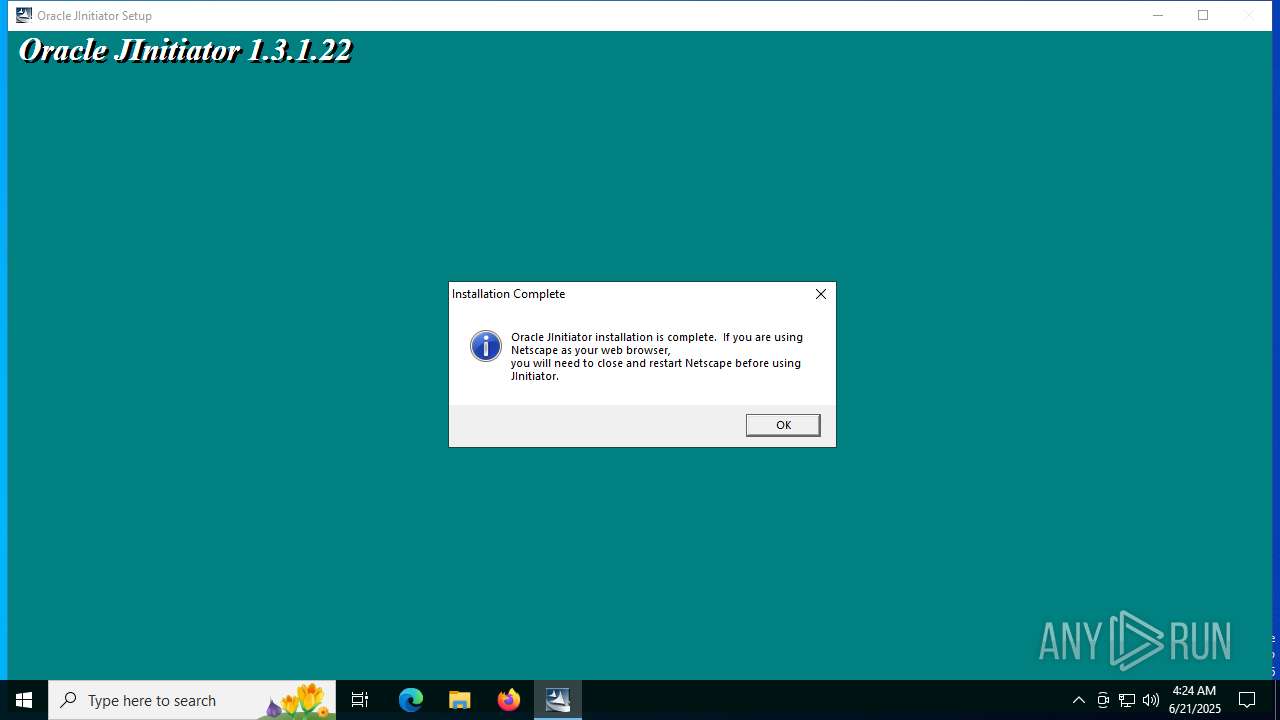
| Analysis date: | June 21, 2025, 04:24:01 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | 9B47A70190E4641EABF851F073B133C7 |
| SHA1: | AF31C4D807C8B61EAD0EEA284093D99BC2E4FAC9 |
| SHA256: | 2DBB95D37D273CF321F6C0BA9F3F86FBB49C9F52BA04CD9BBE59E9A94852BA22 |
| SSDEEP: | 98304:Mv3fHhV+1LrnluZgdaeGnwqKp0WxqcSJA0za7eXXCXUahg9N0jKlwv6E3SE5aSN1:OCkoVY110qVqzaj+ |
MALICIOUS
Changes the autorun value in the registry
- IKernel.exe (PID: 3656)
SUSPICIOUS
Executable content was dropped or overwritten
- jinit.exe_.exe (PID: 6892)
- Setup.exe (PID: 6412)
- IKernel.exe (PID: 3656)
Creates/Modifies COM task schedule object
- IKernel.exe (PID: 3656)
Application launched itself
- IKernel.exe (PID: 3656)
- updater.exe (PID: 5552)
There is functionality for taking screenshot (YARA)
- Setup.exe (PID: 6412)
- IKernel.exe (PID: 3656)
- jinit.exe_.exe (PID: 6892)
Process drops legitimate windows executable
- IKernel.exe (PID: 3656)
Searches for installed software
- IKernel.exe (PID: 3656)
Creates a software uninstall entry
- IKernel.exe (PID: 3656)
The process executes via Task Scheduler
- updater.exe (PID: 5552)
INFO
The sample compiled with english language support
- jinit.exe_.exe (PID: 6892)
- Setup.exe (PID: 6412)
- IKernel.exe (PID: 3656)
Reads the computer name
- jinit.exe_.exe (PID: 6892)
- Setup.exe (PID: 6412)
- IKernel.exe (PID: 1068)
- IKernel.exe (PID: 3656)
- IKernel.exe (PID: 6520)
- updater.exe (PID: 5552)
Checks supported languages
- jinit.exe_.exe (PID: 6892)
- Setup.exe (PID: 6412)
- IKernel.exe (PID: 1068)
- IKernel.exe (PID: 3656)
- uncrunch.exe (PID: 3740)
- uncrunch.exe (PID: 2188)
- uncrunch.exe (PID: 6852)
- IKernel.exe (PID: 6520)
- updater.exe (PID: 5552)
- updater.exe (PID: 5924)
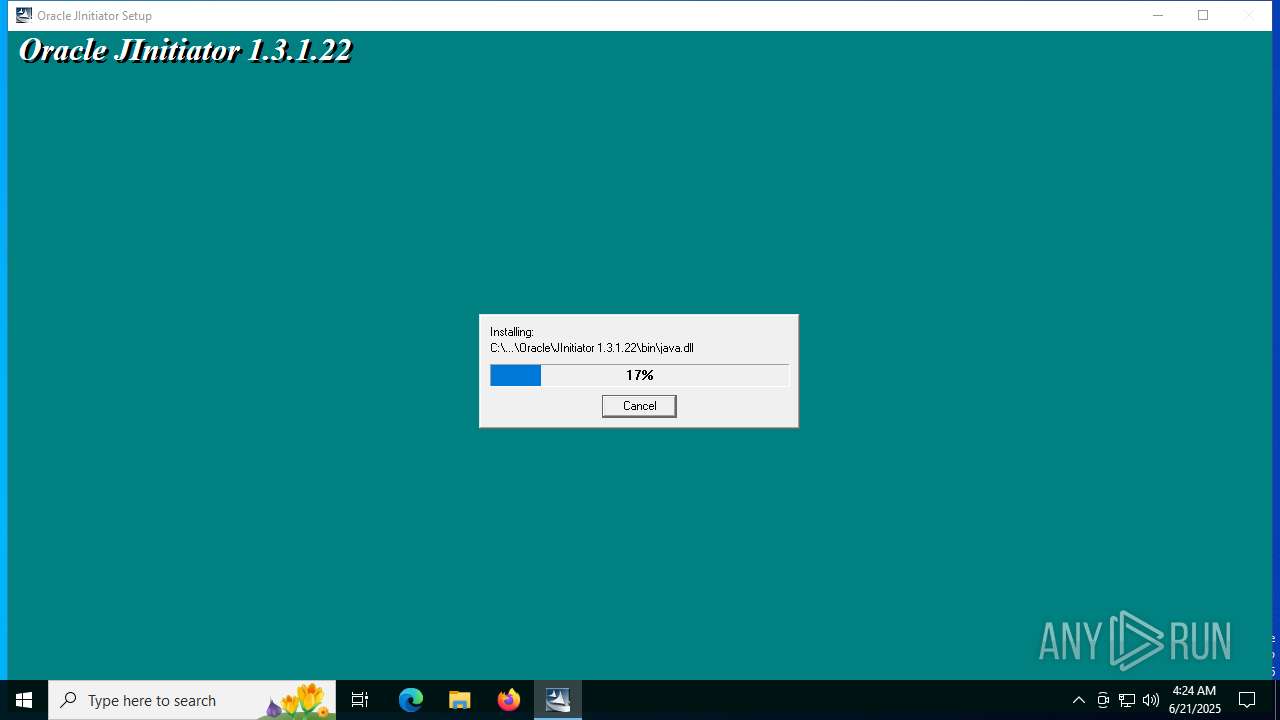
Create files in a temporary directory
- jinit.exe_.exe (PID: 6892)
- Setup.exe (PID: 6412)
- IKernel.exe (PID: 3656)
- uncrunch.exe (PID: 2188)
- uncrunch.exe (PID: 3740)
- uncrunch.exe (PID: 6852)
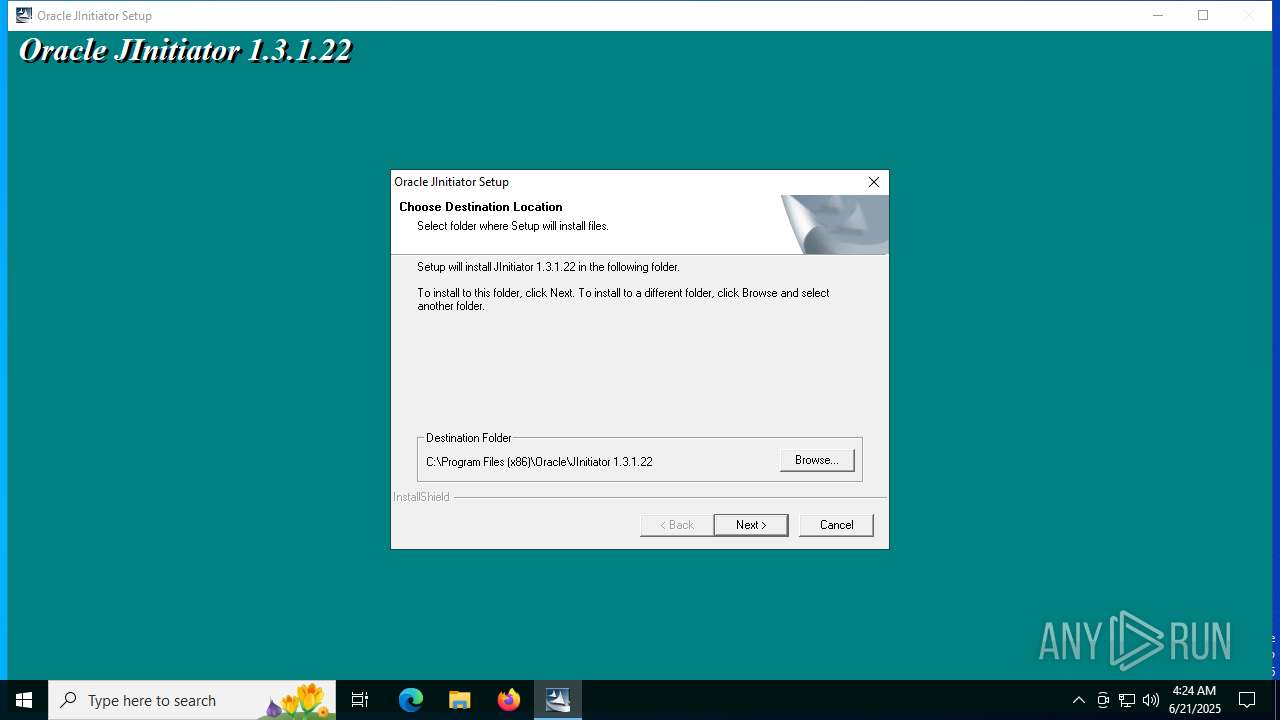
Creates files in the program directory
- Setup.exe (PID: 6412)
- IKernel.exe (PID: 3656)
- uncrunch.exe (PID: 3740)
- uncrunch.exe (PID: 2188)
- uncrunch.exe (PID: 6852)
Checks proxy server information
- slui.exe (PID: 4576)
Process checks whether UAC notifications are on
- updater.exe (PID: 5552)
Reads the software policy settings
- slui.exe (PID: 4576)
Launching a file from a Registry key
- IKernel.exe (PID: 3656)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2000:03:27 18:09:58+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 69632 |
| InitializedDataSize: | 98304 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x83f7 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.11.15.0 |
| ProductVersionNumber: | 2.11.15.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | Oracle |
| FileDescription: | - |
| FileVersion: | 1.3.1.22 |
| InternalName: | stub32i.exe |
| LegalCopyright: | - |
| OriginalFileName: | stub32i.exe |
| ProductName: | Oracle JInitiator |
| ProductVersion: | 1.3.1.22 |
Total processes
167
Monitored processes
14
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1068 | "C:\Program Files (x86)\Common Files\InstallShield\Engine\6\Intel 32\IKernel.exe" -RegServer | C:\Program Files (x86)\Common Files\InstallShield\Engine\6\Intel 32\IKernel.exe | — | Setup.exe | |||||||||||
User: admin Company: InstallShield Software Corporation Integrity Level: HIGH Description: InstallShield (R) Setup Engine Exit code: 0 Version: 6, 31, 100, 1190 Modules
| |||||||||||||||
| 1096 | "C:\Users\admin\AppData\Local\Temp\jinit.exe_.exe" | C:\Users\admin\AppData\Local\Temp\jinit.exe_.exe | — | explorer.exe | |||||||||||
User: admin Company: Oracle Integrity Level: MEDIUM Exit code: 3221226540 Version: 1.3.1.22 Modules
| |||||||||||||||
| 2188 | C:\Users\admin\AppData\Local\Temp\{CAFECAFE-0013-0001-0122-ABCDEFABCDEF}\uncrunch.exe "C:\Program Files (x86)\Oracle\JInitiator 1.3.1.22\tmp\rt.out" "C:\Program Files (x86)\Oracle\JInitiator 1.3.1.22\lib\rt.jar" | C:\Users\admin\AppData\Local\Temp\{CAFECAFE-0013-0001-0122-ABCDEFABCDEF}\uncrunch.exe | — | IKernel.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3656 | C:\PROGRA~2\COMMON~1\INSTAL~1\Engine\6\INTEL3~1\IKernel.exe -Embedding | C:\Program Files (x86)\Common Files\InstallShield\Engine\6\Intel 32\IKernel.exe | svchost.exe | ||||||||||||
User: admin Company: InstallShield Software Corporation Integrity Level: HIGH Description: InstallShield (R) Setup Engine Exit code: 0 Version: 6, 31, 100, 1190 Modules
| |||||||||||||||
| 3740 | C:\Users\admin\AppData\Local\Temp\{CAFECAFE-0013-0001-0122-ABCDEFABCDEF}\uncrunch.exe "C:\Program Files (x86)\Oracle\JInitiator 1.3.1.22\tmp\i18n.out" "C:\Program Files (x86)\Oracle\JInitiator 1.3.1.22\lib\i18n.jar" | C:\Users\admin\AppData\Local\Temp\{CAFECAFE-0013-0001-0122-ABCDEFABCDEF}\uncrunch.exe | — | IKernel.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 4576 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5552 | "C:\Program Files (x86)\Google\GoogleUpdater\134.0.6985.0\updater.exe" --wake --system | C:\Program Files (x86)\Google\GoogleUpdater\134.0.6985.0\updater.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Google LLC Integrity Level: SYSTEM Description: Google Updater Exit code: 0 Version: 134.0.6985.0 Modules
| |||||||||||||||
| 5884 | "C:\WINDOWS\system32\UCPDMgr.exe" | C:\Windows\System32\UCPDMgr.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: User Choice Protection Manager Exit code: 0 Version: 1.0.0.414301 Modules
| |||||||||||||||
| 5924 | "C:\Program Files (x86)\Google\GoogleUpdater\134.0.6985.0\updater.exe" --crash-handler --system "--database=C:\Program Files (x86)\Google\GoogleUpdater\134.0.6985.0\Crashpad" --url=https://clients2.google.com/cr/report --annotation=prod=Update4 --annotation=ver=134.0.6985.0 "--attachment=C:\Program Files (x86)\Google\GoogleUpdater\updater.log" --initial-client-data=0x298,0x29c,0x2a0,0x274,0x2a4,0x111c460,0x111c46c,0x111c478 | C:\Program Files (x86)\Google\GoogleUpdater\134.0.6985.0\updater.exe | — | updater.exe | |||||||||||
User: SYSTEM Company: Google LLC Integrity Level: SYSTEM Description: Google Updater Exit code: 0 Version: 134.0.6985.0 Modules
| |||||||||||||||
| 6412 | "C:\Users\admin\AppData\Local\Temp\pft5E00~tmp\Disk1\Setup.exe" /SMS | C:\Users\admin\AppData\Local\Temp\pft5E00~tmp\Disk1\Setup.exe | jinit.exe_.exe | ||||||||||||
User: admin Company: InstallShield Software Corporation Integrity Level: HIGH Description: InstallShield (R) Setup Launcher Exit code: 0 Version: 6, 31, 100, 1190 Modules
| |||||||||||||||
Total events
1 680
Read events
1 434
Write events
246
Delete events
0
Modification events
| (PID) Process: | (1068) IKernel.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\Interface\{AA7E2068-CB55-11D2-8094-00104B1F9838}\TypeLib |
| Operation: | write | Name: | Version |
Value: 1.0 | |||
| (PID) Process: | (1068) IKernel.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{AA7E2068-CB55-11D2-8094-00104B1F9838}\TypeLib |
| Operation: | write | Name: | Version |
Value: 1.0 | |||
| (PID) Process: | (1068) IKernel.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\Interface\{AA7E2066-CB55-11D2-8094-00104B1F9838}\TypeLib |
| Operation: | write | Name: | Version |
Value: 1.0 | |||
| (PID) Process: | (1068) IKernel.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{AA7E2066-CB55-11D2-8094-00104B1F9838}\TypeLib |
| Operation: | write | Name: | Version |
Value: 1.0 | |||
| (PID) Process: | (1068) IKernel.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\Interface\{CC096170-E2CB-11D2-80C8-00104B1F6CEA}\TypeLib |
| Operation: | write | Name: | Version |
Value: 1.0 | |||
| (PID) Process: | (1068) IKernel.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{CC096170-E2CB-11D2-80C8-00104B1F6CEA}\TypeLib |
| Operation: | write | Name: | Version |
Value: 1.0 | |||
| (PID) Process: | (1068) IKernel.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\Interface\{8C3C1B11-E59D-11D2-B40B-00A024B9DDDD}\TypeLib |
| Operation: | write | Name: | Version |
Value: 1.0 | |||
| (PID) Process: | (1068) IKernel.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{8C3C1B11-E59D-11D2-B40B-00A024B9DDDD}\TypeLib |
| Operation: | write | Name: | Version |
Value: 1.0 | |||
| (PID) Process: | (1068) IKernel.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\Interface\{8C3C1B13-E59D-11D2-B40B-00A024B9DDDD}\TypeLib |
| Operation: | write | Name: | Version |
Value: 1.0 | |||
| (PID) Process: | (1068) IKernel.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{8C3C1B13-E59D-11D2-B40B-00A024B9DDDD}\TypeLib |
| Operation: | write | Name: | Version |
Value: 1.0 | |||
Executable files
113
Suspicious files
47
Text files
108
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6892 | jinit.exe_.exe | C:\Users\admin\AppData\Local\Temp\pft5E00~tmp\pftw1.pkg | — | |
MD5:— | SHA256:— | |||
| 6892 | jinit.exe_.exe | C:\Users\admin\AppData\Local\Temp\pft5E00~tmp\Disk1\data2.cab | — | |
MD5:— | SHA256:— | |||
| 6892 | jinit.exe_.exe | C:\Users\admin\AppData\Local\Temp\ext5DA1.tmp | text | |
MD5:414378BEE661B0DF11BDB2BE32E15B84 | SHA256:F9EFB3E6FE099C649FB4CC20AC6F9B7E90D3F60B8D98F48FB5D167F1A0B1B7F2 | |||
| 6892 | jinit.exe_.exe | C:\Users\admin\AppData\Local\Temp\pft5E00~tmp\Disk1\data1.cab | compressed | |
MD5:4A50FEF77AA8F5CCEC731453C9784D2E | SHA256:409D3D991C740BE2A1E378FCA026F3D0A2BFDA677A050012A5A1F025DA001AAD | |||
| 6892 | jinit.exe_.exe | C:\Users\admin\AppData\Local\Temp\pft5E00~tmp\Disk1\data1.hdr | binary | |
MD5:A4404E2F269B056FB0A47127F0BD641F | SHA256:5565D46B2C40373134291D9BA0174A09B7232DD22EBAA4B75F1752E72AB834C2 | |||
| 3656 | IKernel.exe | C:\Program Files (x86)\Common Files\InstallShield\Engine\6\Intel 32\objectps.dll | executable | |
MD5:8F02B204853939F8AEFE6B07B283BE9A | SHA256:32C6AD91DC66BC12E1273B1E13EB7A15D6E8F63B93447909CA2163DD21B22998 | |||
| 3656 | IKernel.exe | C:\Program Files (x86)\Common Files\InstallShield\Engine\6\Intel 32\core615a.rra | text | |
MD5:62D5F9827D867EB3E4AB9E6B338348A1 | SHA256:5214789C08EE573E904990DCD29E9E03AAF5CF12E86FAE368005FD8F4E371BD5 | |||
| 3656 | IKernel.exe | C:\Program Files (x86)\Common Files\InstallShield\Engine\6\Intel 32\obje6198.rra | executable | |
MD5:8F02B204853939F8AEFE6B07B283BE9A | SHA256:32C6AD91DC66BC12E1273B1E13EB7A15D6E8F63B93447909CA2163DD21B22998 | |||
| 3656 | IKernel.exe | C:\Program Files (x86)\Common Files\InstallShield\Engine\6\Intel 32\iuse61a8.rra | executable | |
MD5:377765FD4DE3912C0F814EE9F182FEDA | SHA256:8EFCBD8752D8BBFD7EE559502D1AA28134C9BF391BF7FC5CE6FDFD4473599AFB | |||
| 3656 | IKernel.exe | C:\Program Files (x86)\Common Files\InstallShield\Engine\6\Intel 32\ctor.dll | executable | |
MD5:003A6C011AAC993BCDE8C860988CE49B | SHA256:590BE865DDF8C8D0431D8F92AA3948CC3C1685FD0649D607776B81CD1E267D0A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
33
DNS requests
24
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1200 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.55.104.190:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
3960 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2940 | svchost.exe | GET | 200 | 23.209.209.135:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
6016 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3960 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6548 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1488 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2336 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
1200 | svchost.exe | 20.190.160.14:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1200 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
1268 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 23.55.104.190:80 | crl.microsoft.com | Akamai International B.V. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |