| File name: | WinLocker.exe |
| Full analysis: | https://app.any.run/tasks/9d8bd346-cda9-4dbf-b6e4-6600baeb21ef |
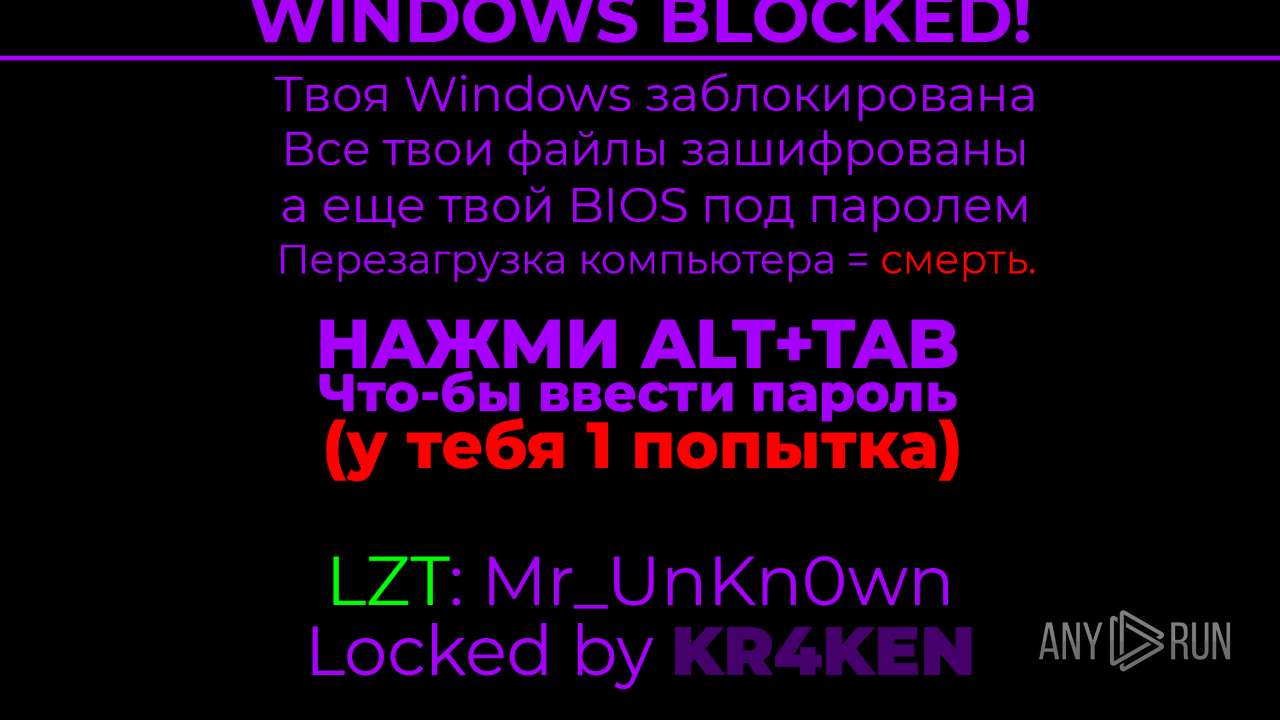
| Verdict: | Malicious activity |
| Analysis date: | August 10, 2024, 08:16:34 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 3815AA012F2F134A37379AEFA88A03D3 |
| SHA1: | 82F863FD02D5C55EF71522FC8FDFFF318266D2AD |
| SHA256: | 2DB6D68C8AA2E02FC8CC3F9EB3E37F60AC4DF82E1428C6A0F9477C649242BC15 |
| SSDEEP: | 98304:/eWZB1zJa59KMLKVAz4WtJ2D/KC+iSY2IsizAuj/gTAeVxDSachN+ex77o/mEqzy:HhE44RfwBRCPekmxYNvL6 |
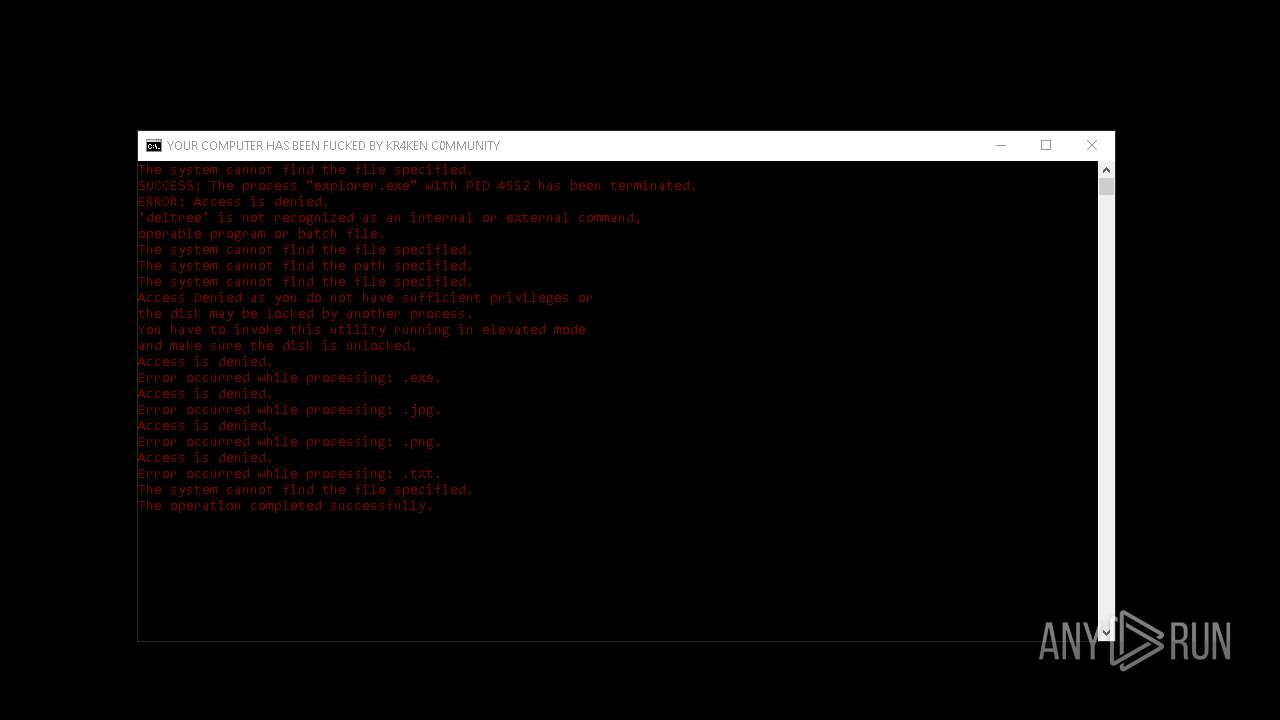
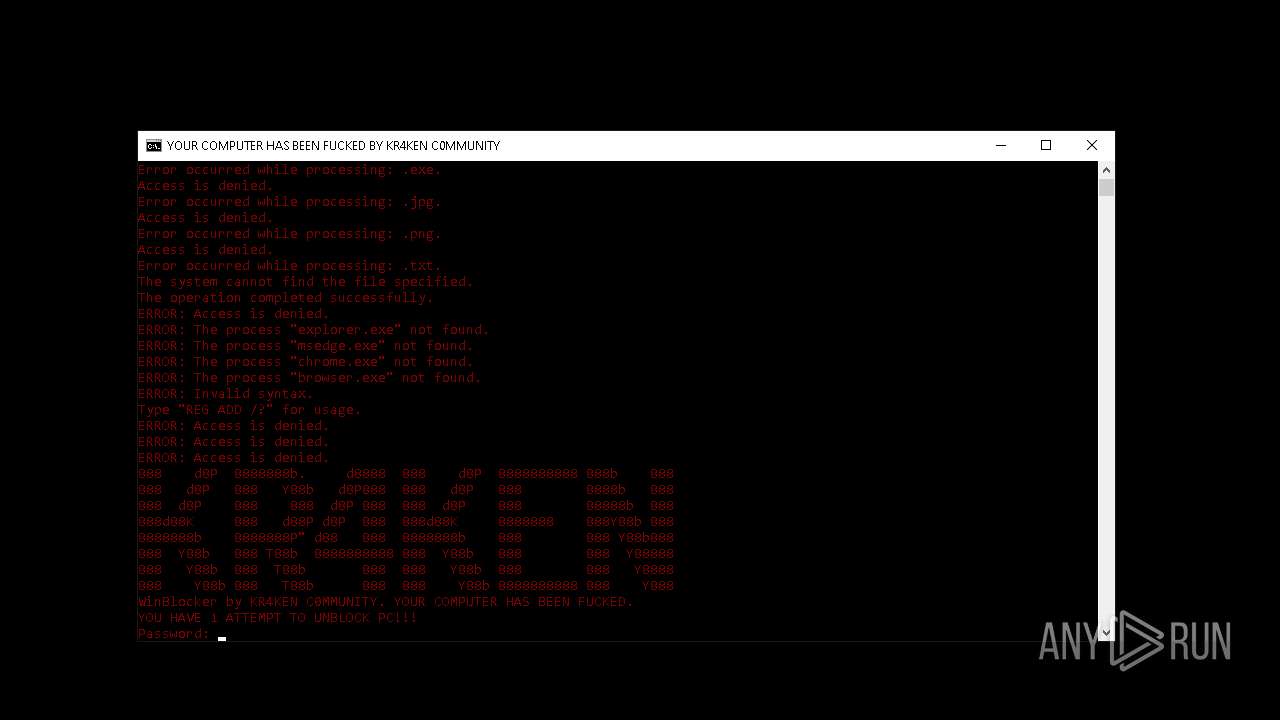
MALICIOUS
Changes the autorun value in the registry
- reg.exe (PID: 6856)
Uses Task Scheduler to autorun other applications
- cmd.exe (PID: 6496)
Uses sleep, probably for evasion detection (SCRIPT)
- wscript.exe (PID: 6304)
SUSPICIOUS
Drops the executable file immediately after the start
- WinLocker.exe (PID: 6444)
Reads security settings of Internet Explorer
- WinLocker.exe (PID: 6444)
Reads the date of Windows installation
- WinLocker.exe (PID: 6444)
- scream.exe (PID: 6684)
Starts CMD.EXE for commands execution
- WinLocker.exe (PID: 6444)
- cmd.exe (PID: 6496)
Executing commands from a ".bat" file
- WinLocker.exe (PID: 6444)
Starts application with an unusual extension
- cmd.exe (PID: 6496)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 6496)
Runs shell command (SCRIPT)
- wscript.exe (PID: 6304)
The process executes VB scripts
- scream.exe (PID: 6684)
Executable content was dropped or overwritten
- WinLocker.exe (PID: 6444)
Application launched itself
- cmd.exe (PID: 6496)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 6496)
INFO
Creates files or folders in the user directory
- WinLocker.exe (PID: 6444)
Checks supported languages
- WinLocker.exe (PID: 6444)
- chcp.com (PID: 6560)
- scream.exe (PID: 6684)
Reads the machine GUID from the registry
- WinLocker.exe (PID: 6444)
Process checks computer location settings
- WinLocker.exe (PID: 6444)
- scream.exe (PID: 6684)
Reads the computer name
- WinLocker.exe (PID: 6444)
- scream.exe (PID: 6684)
Changes the display of characters in the console
- chcp.com (PID: 6560)
Reads Internet Explorer settings
- mshta.exe (PID: 964)
Checks proxy server information
- wscript.exe (PID: 6304)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:08:10 07:48:15+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 10783232 |
| InitializedDataSize: | 40448 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xa4a84e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | |
| FileVersion: | 1.0.0.0 |
| InternalName: | WinLocker.exe |
| LegalCopyright: | |
| OriginalFileName: | WinLocker.exe |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
134
Monitored processes
16
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 964 | "C:\Windows\SysWOW64\mshta.exe" "C:\scream\gif.hta" {1E460BD7-F1C3-4B2E-88BF-4E770A288AF5}{1E460BD7-F1C3-4B2E-88BF-4E770A288AF5} | C:\Windows\SysWOW64\mshta.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6304 | "C:\WINDOWS\System32\WScript.exe" "C:\scream\sound.vbs" | C:\Windows\SysWOW64\wscript.exe | — | scream.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 6444 | "C:\Users\admin\Desktop\WinLocker.exe" | C:\Users\admin\Desktop\WinLocker.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 6444 | C:\WINDOWS\system32\svchost.exe -k wusvcs -p -s WaaSMedicSvc | C:\Windows\System32\svchost.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6496 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Roaming\WinBlocker.bat" " | C:\Windows\System32\cmd.exe | WinLocker.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6504 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6560 | chcp 65001 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6584 | taskkill /F /IM explorer.exe | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6684 | "C:\Users\admin\AppData\Roaming\scream.exe" | C:\Users\admin\AppData\Roaming\scream.exe | — | WinLocker.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 6692 | reg add "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System" /v EnableLUA /t REG_DWORD /d 0 /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
10 739
Read events
10 642
Write events
96
Delete events
1
Modification events
| (PID) Process: | (6444) WinLocker.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6444) WinLocker.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (6444) WinLocker.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (6444) WinLocker.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (6856) reg.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | WinBlocker.bat |
Value: WinBlocker.bat | |||
| (PID) Process: | (6304) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows Media\WMSDK\General |
| Operation: | write | Name: | UniqueID |
Value: {F638C670-FAE1-4882-8ACE-207C3C521E6F} | |||
| (PID) Process: | (6304) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows Media\WMSDK\General |
| Operation: | write | Name: | ComputerName |
Value: DESKTOP-JGLLJLD | |||
| (PID) Process: | (6304) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows Media\WMSDK\General |
| Operation: | write | Name: | VolumeSerialNumber |
Value: 649566714 | |||
| (PID) Process: | (6304) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\MediaPlayer\Player\Settings |
| Operation: | delete value | Name: | Client ID |
Value: {CECDFD5C-8F08-4FEF-8713-FAA895A422EB} | |||
| (PID) Process: | (6304) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows Media\WMSDK\Namespace |
| Operation: | write | Name: | LocalBase |
Value: C:\Users\admin\AppData\Local\Microsoft\Windows Media\12.0\WMSDKNS.XML | |||
Executable files
1
Suspicious files
2
Text files
8
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6684 | scream.exe | C:\scream\sound.mp3 | — | |
MD5:— | SHA256:— | |||
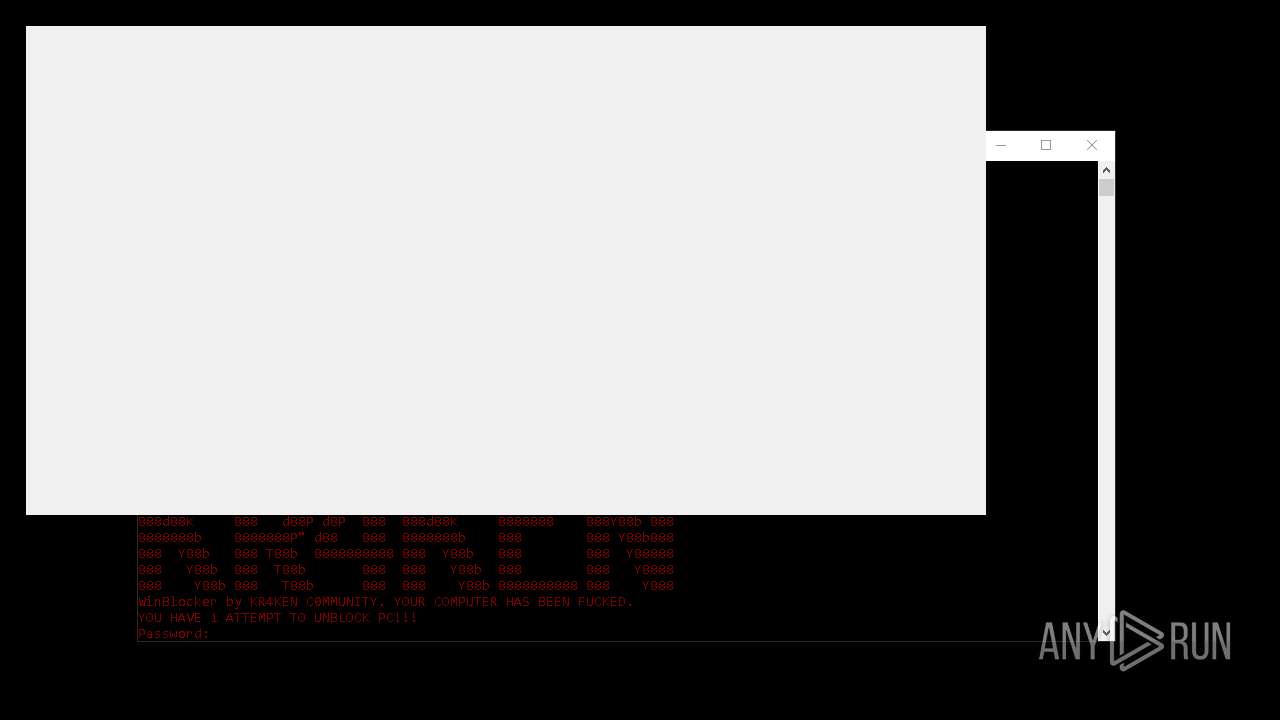
| 6684 | scream.exe | C:\scream\tenor.gif | image | |
MD5:69C4602BCAE7644FF1191D4D4E766A95 | SHA256:8269D52BDDAC08BC246D0738312BD26BEAC35CC3430A2CEDA9A3EFCF8DCC16DC | |||
| 964 | mshta.exe | C:\Users\admin\AppData\Local\Temp\~DF2370B2C9EC764FC7.TMP | binary | |
MD5:68E572EB0119E5C7150FAE387D7B1CC2 | SHA256:32425BD05A08E0BD7F3F42D09B9AB94632F4A1911CF7A4562E5E548EA4634F7F | |||
| 6304 | wscript.exe | C:\Users\admin\AppData\Local\Microsoft\Windows Media\12.0\WMSDKNS.XML | text | |
MD5:5433EAB10C6B5C6D55B7CBD302426A39 | SHA256:23DBF7014E99E93AF5F2760F18EE1370274F06A453145C8D539B66D798DAD131 | |||
| 6684 | scream.exe | C:\scream\gif.hta | html | |
MD5:74E44289C376074367616125C02C3DDE | SHA256:306E5356EDDAF0F9C3A81435BB3649ADFAD37F0DC78BC6D7D495C19977EE874F | |||
| 6444 | WinLocker.exe | C:\Users\admin\AppData\Roaming\WinBlocker.bat | text | |
MD5:B5BE2B7994B3FBBC9A96B1191C16619D | SHA256:CE79961D220806505D161E79AAF0696C43C623D55D2CF2917A404E7910EEA67C | |||
| 6304 | wscript.exe | C:\Users\admin\AppData\Local\Microsoft\Windows Media\12.0\WMSDKNS.XML.bak | text | |
MD5:7050D5AE8ACFBE560FA11073FEF8185D | SHA256:CB87767C4A384C24E4A0F88455F59101B1AE7B4FB8DE8A5ADB4136C5F7EE545B | |||
| 6304 | wscript.exe | C:\Users\admin\AppData\Local\Microsoft\Media Player\CurrentDatabase_400.wmdb | vc | |
MD5:F5690A51757988A8DE58364CF89D1C29 | SHA256:7CFC7C47EFE2BDBADC40C415554F0CBE9BFBEA434BFEA273877D37C8815A2395 | |||
| 6444 | WinLocker.exe | C:\Users\admin\AppData\Roaming\scream.exe | executable | |
MD5:4075DFB25D605866252215C880F5A410 | SHA256:03F52BEB7774B81B8933393E8BFE39A5C4130438C508E948B6EB6B28163F2C05 | |||
| 6496 | cmd.exe | C:\Users\admin\AppData\Local\Temp\admin.vbs | text | |
MD5:C4082F230B2E53254891D4EBB75A3482 | SHA256:4939A50842B5A63373180463EA84B5BD098977E3E6A03F3D21B6C8CACFC45748 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
15
DNS requests
5
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3140 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4060 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4324 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3140 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |