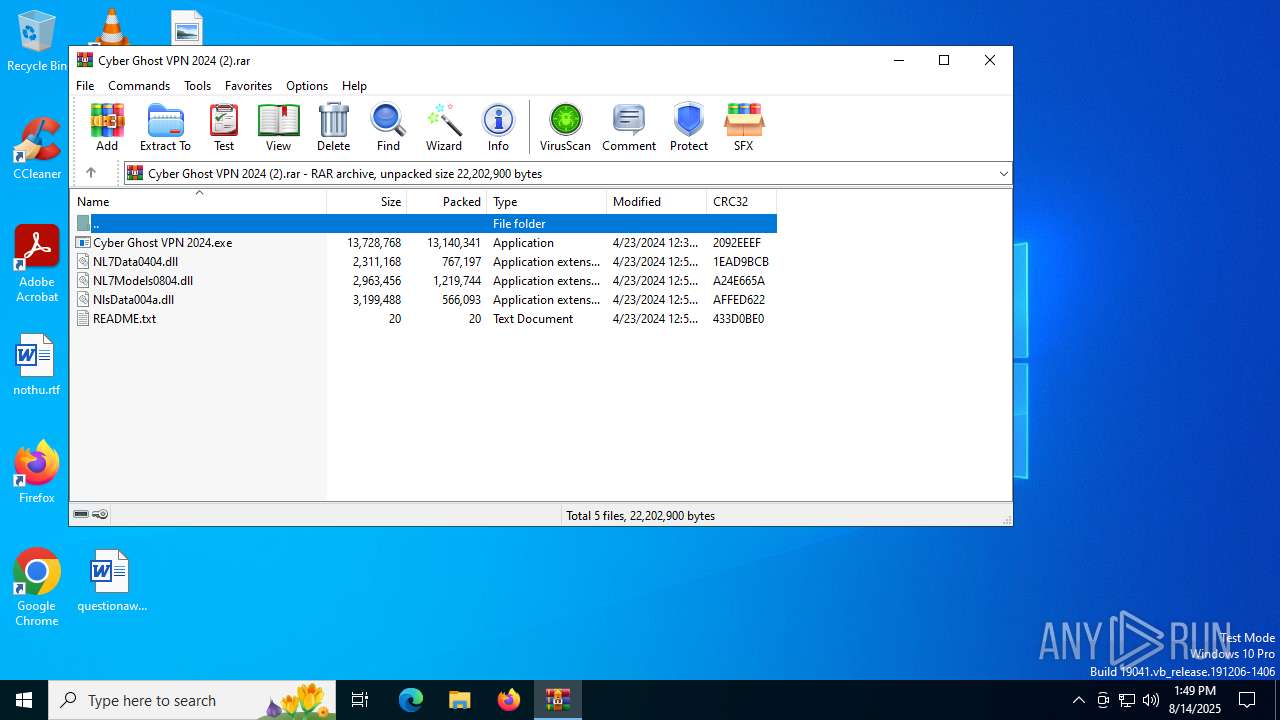
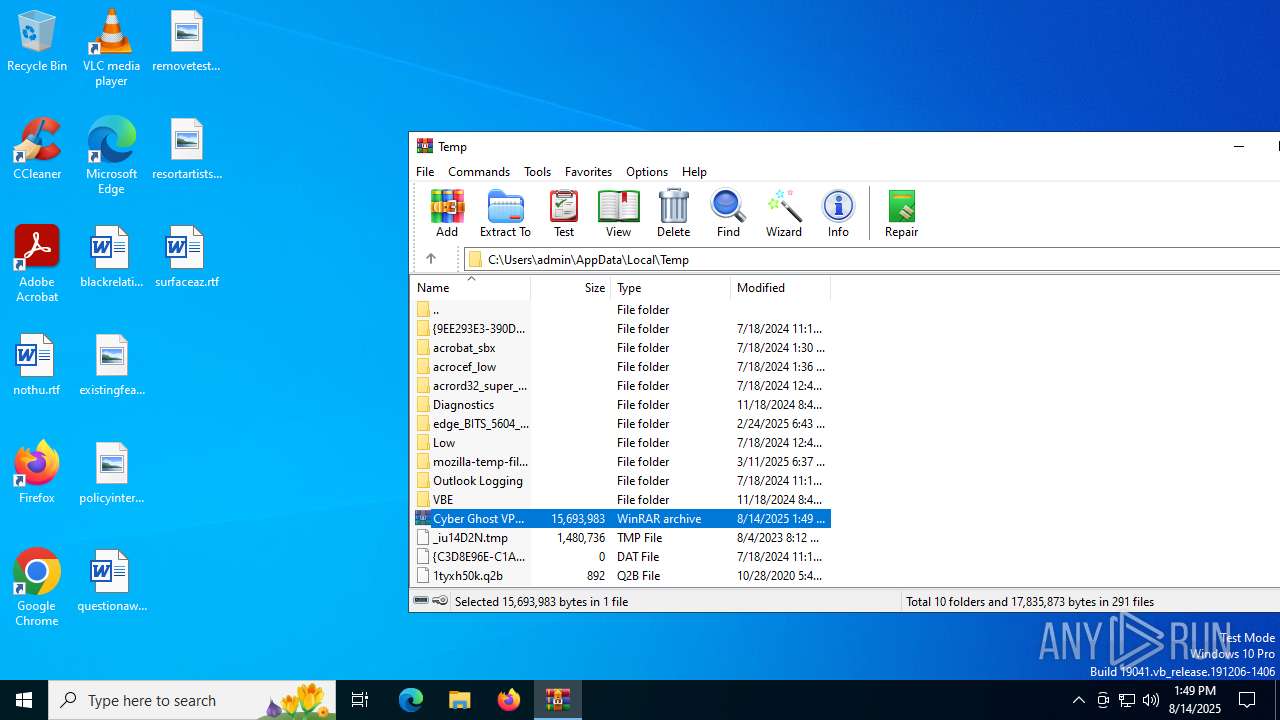
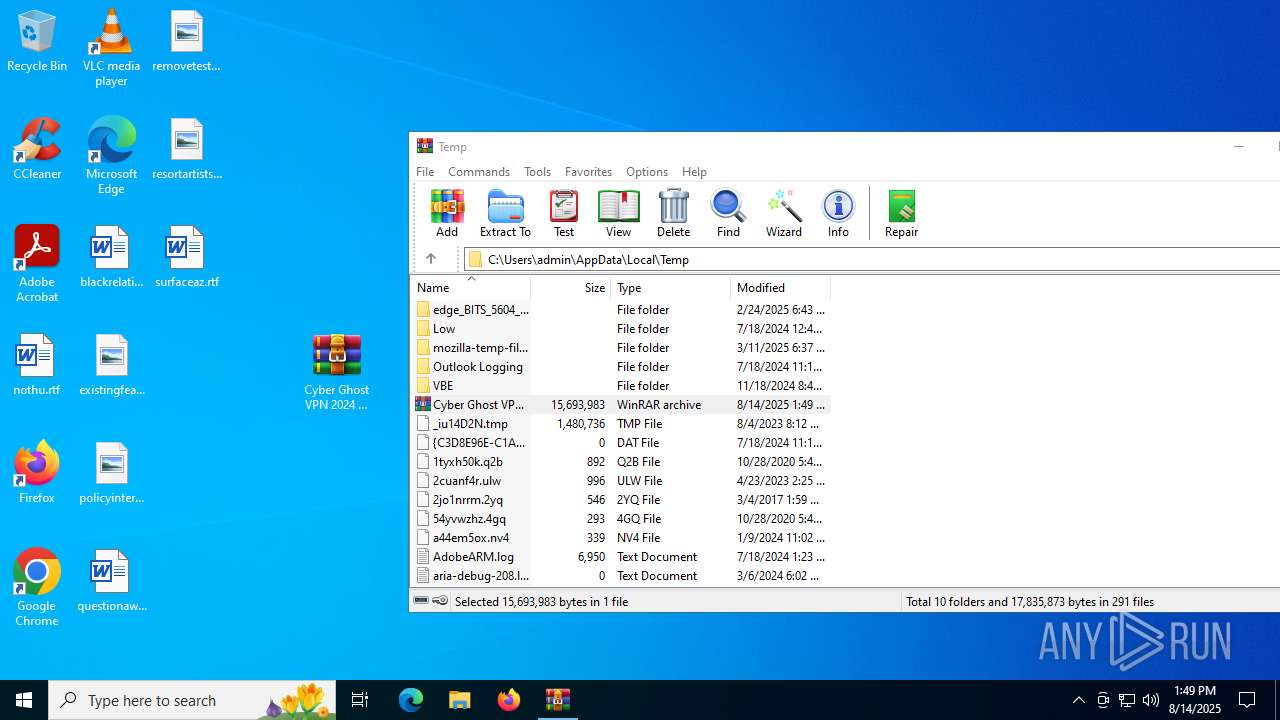
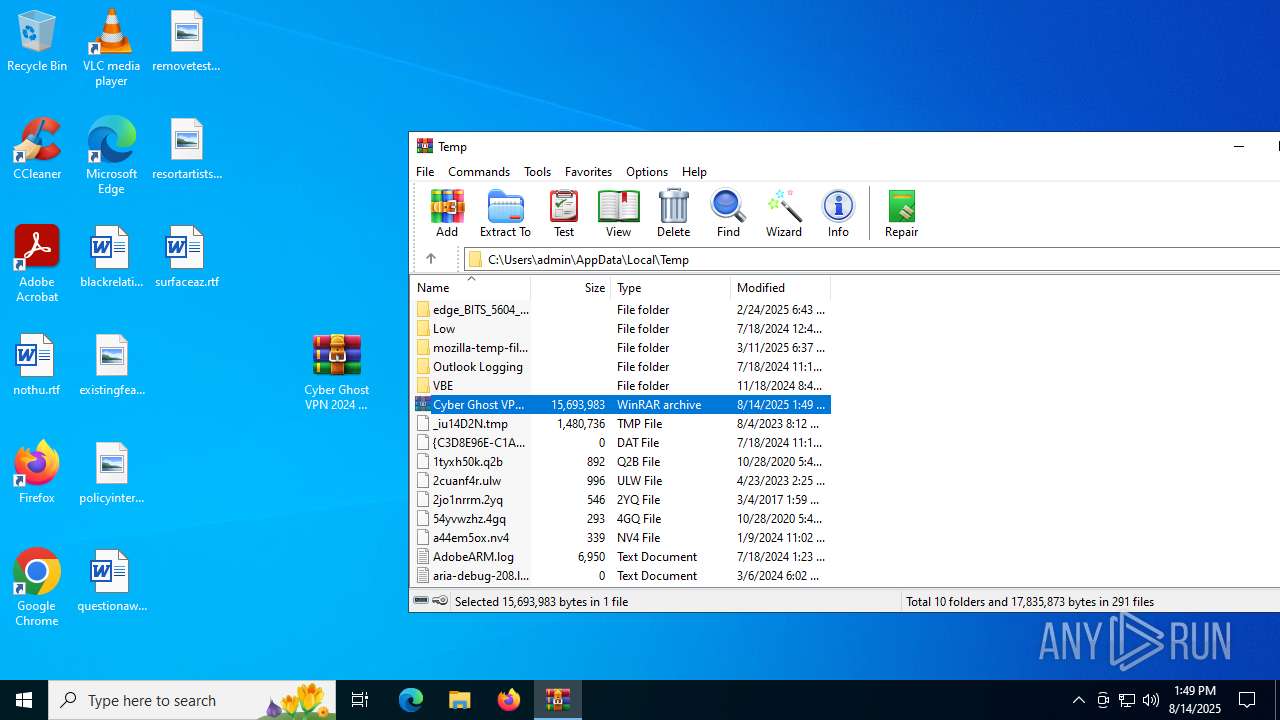
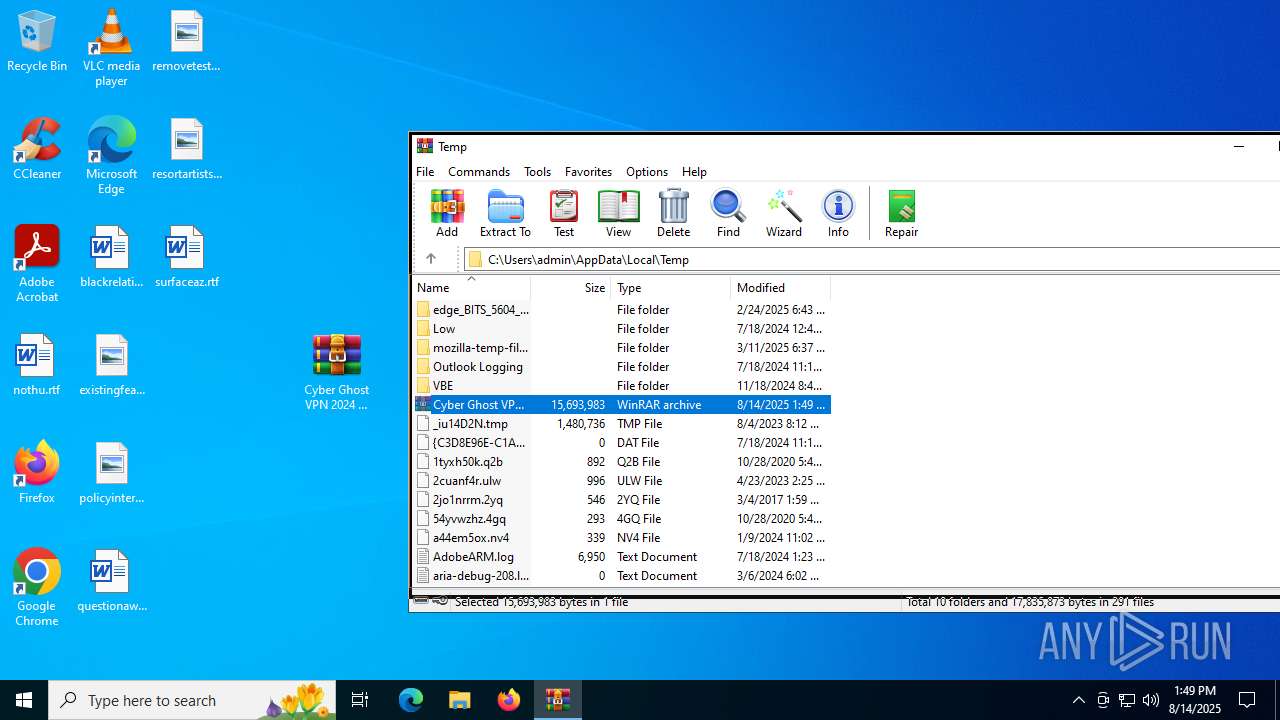
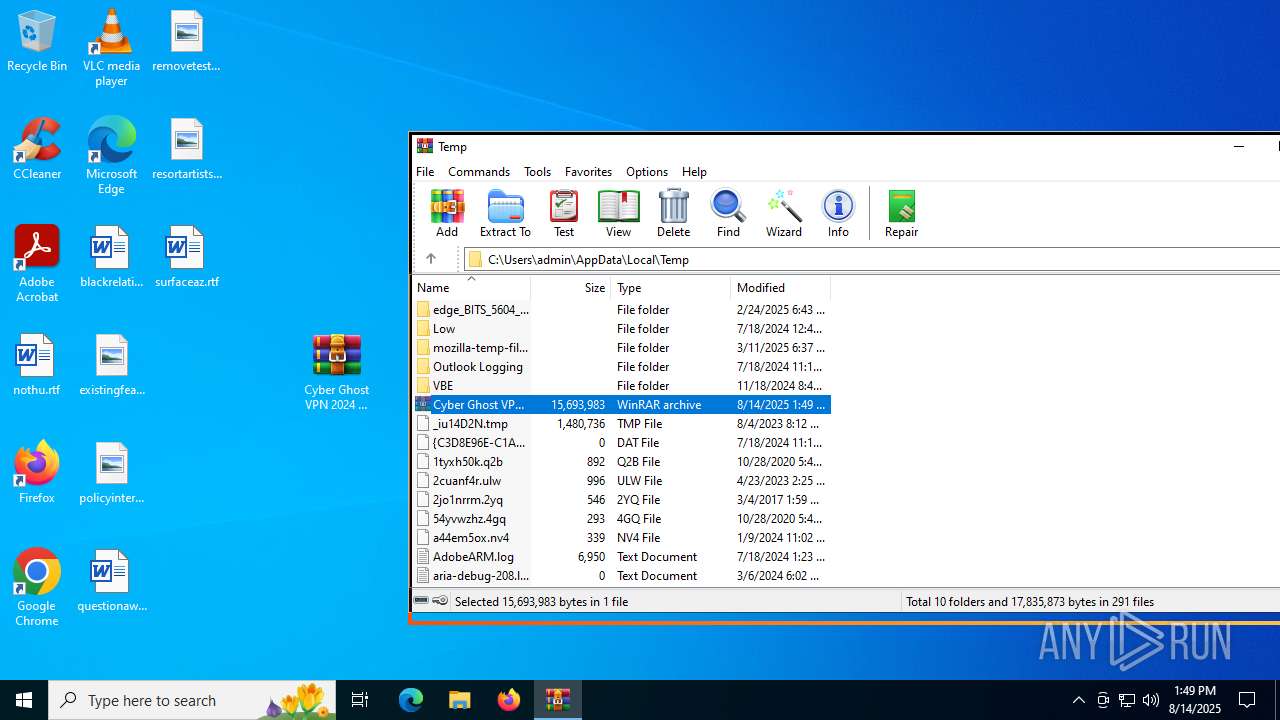
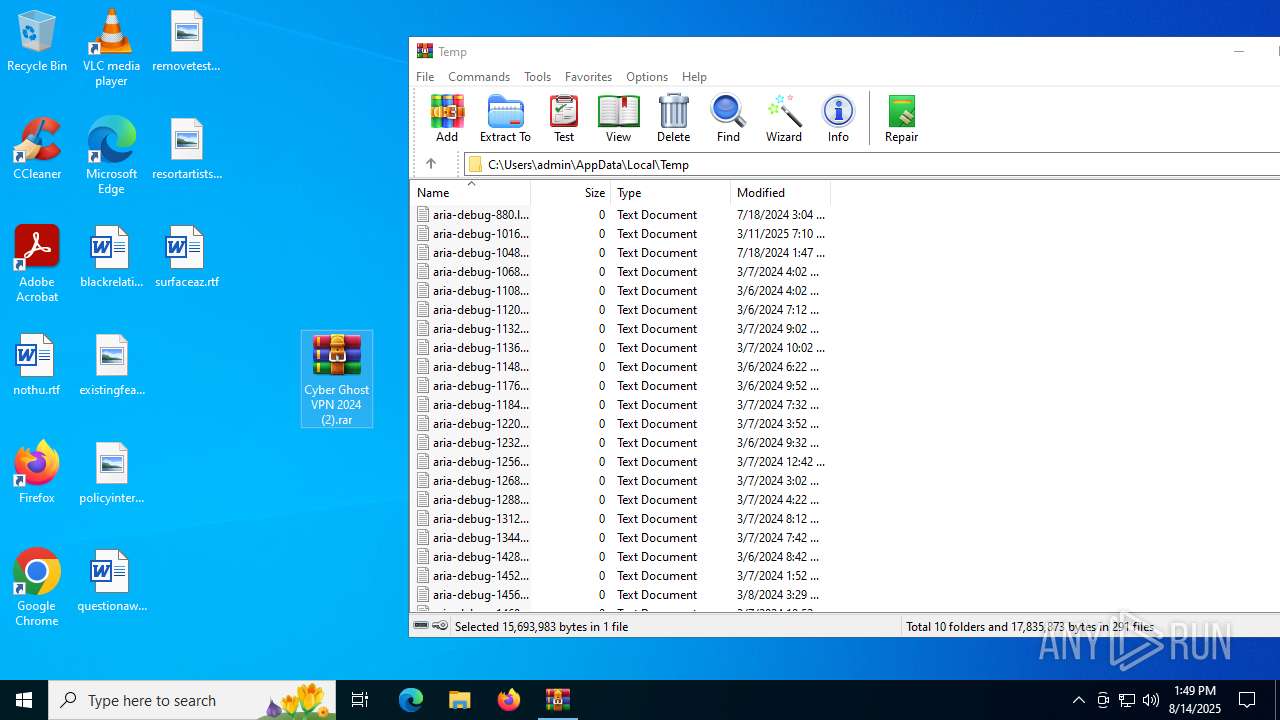
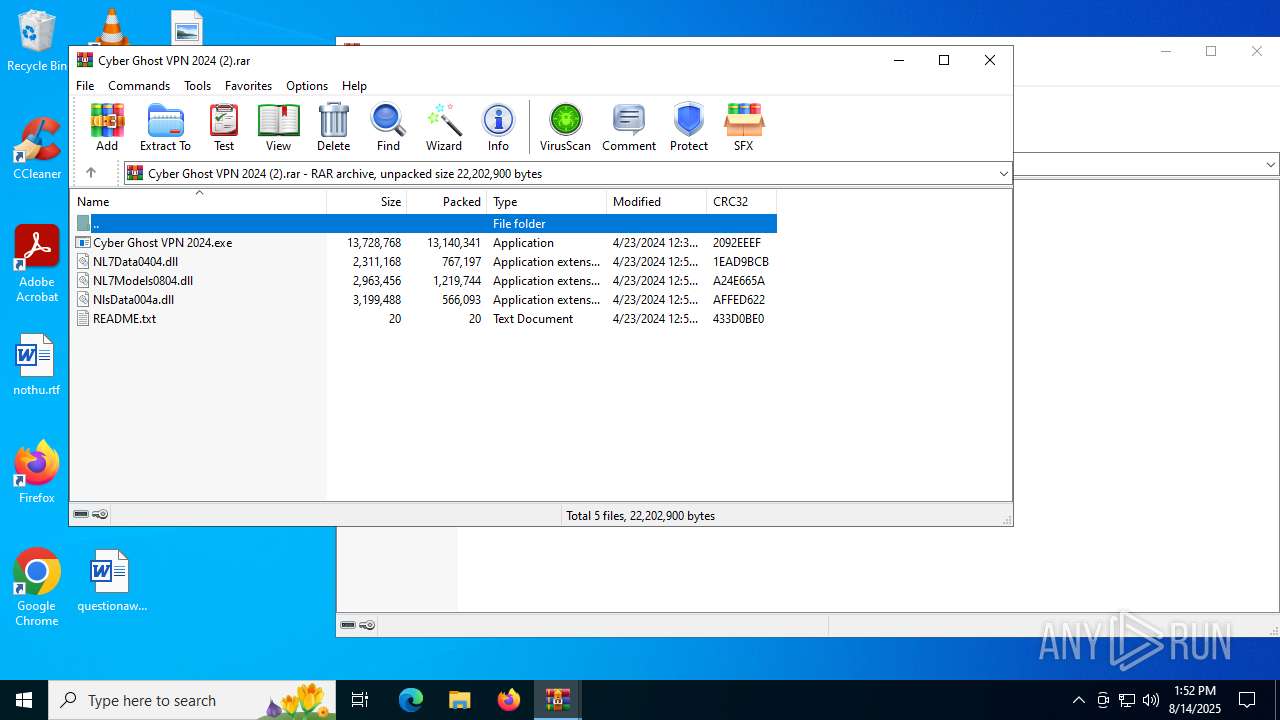
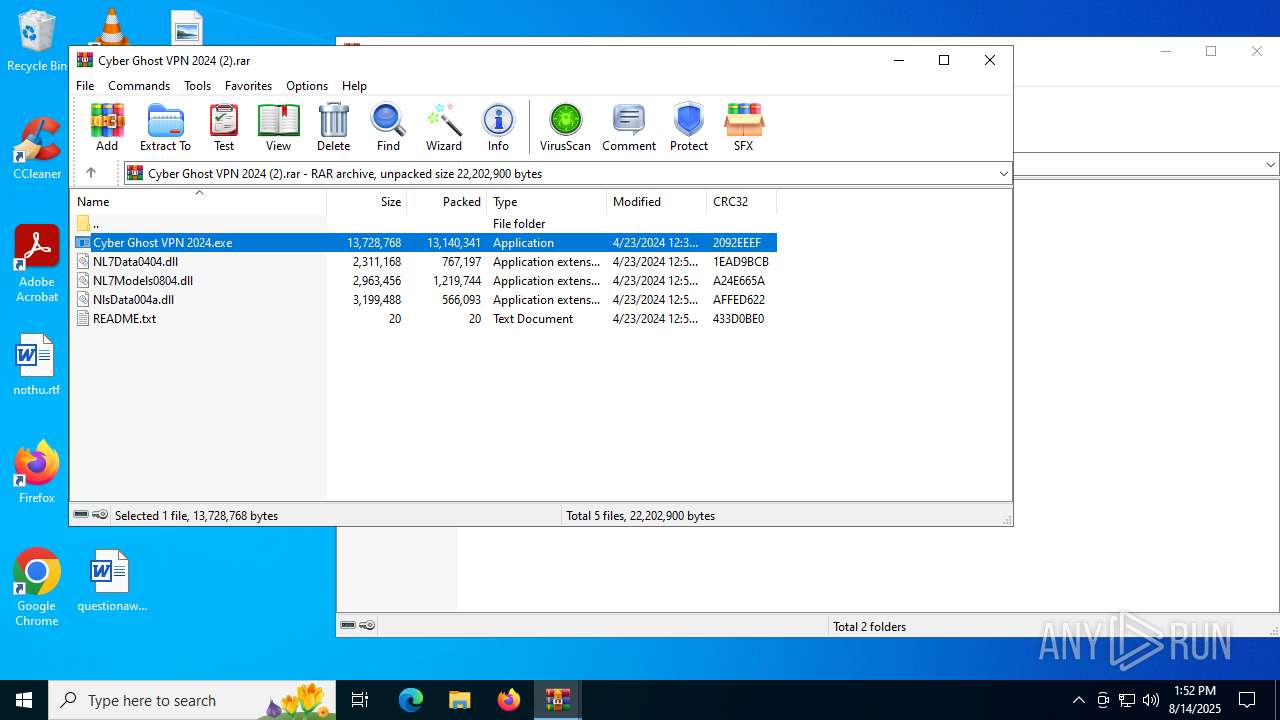
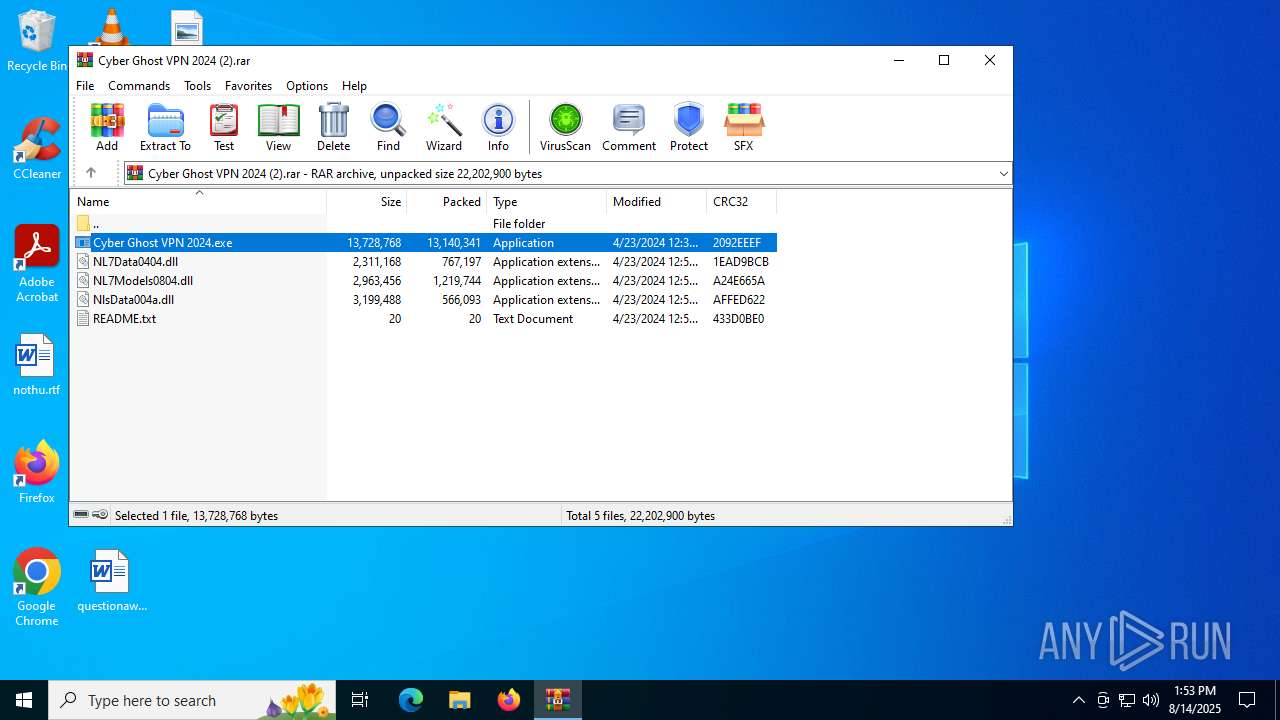
| File name: | Cyber Ghost VPN 2024 (2).rar |
| Full analysis: | https://app.any.run/tasks/4051241f-bce4-46ae-b639-fd027fe1c3d5 |
| Verdict: | Malicious activity |
| Threats: | DCrat, also known as Dark Crystal RAT, is a remote access trojan (RAT), which was first introduced in 2018. It is a modular malware that can be customized to perform different tasks. For instance, it can steal passwords, crypto wallet information, hijack Telegram and Steam accounts, and more. Attackers may use a variety of methods to distribute DCrat, but phishing email campaigns are the most common. |
| Analysis date: | August 14, 2025, 13:49:03 |
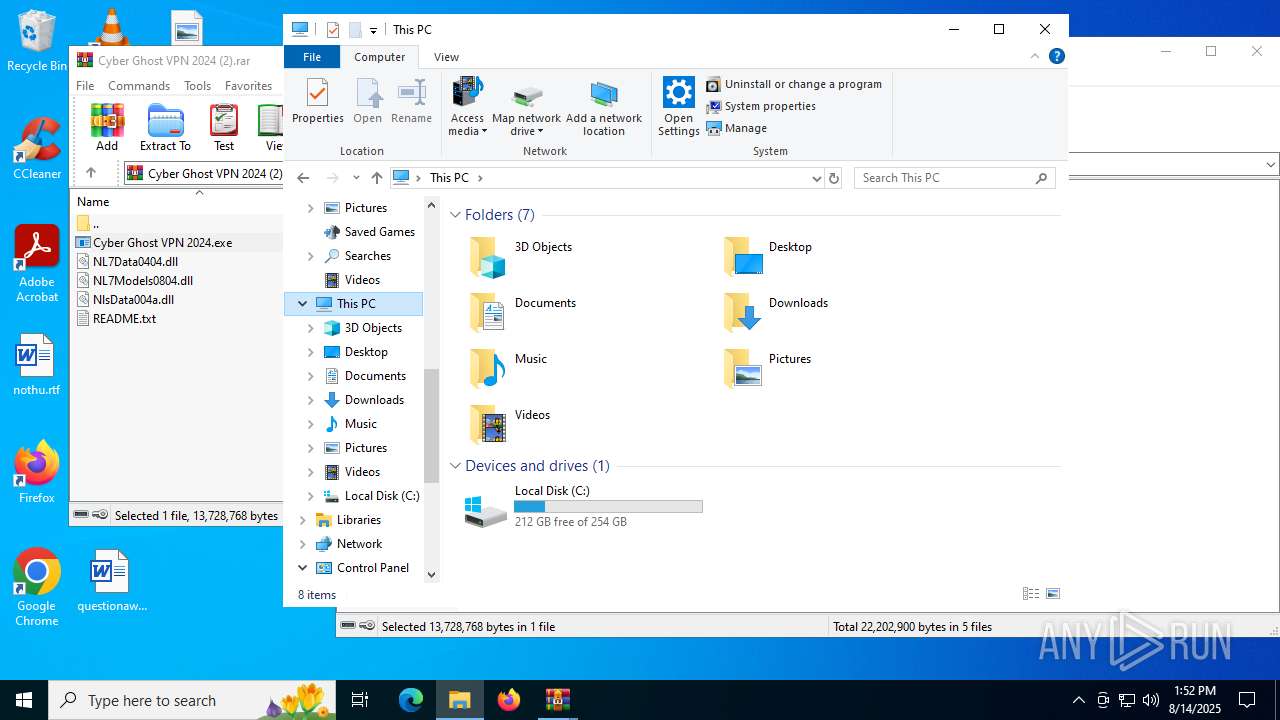
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
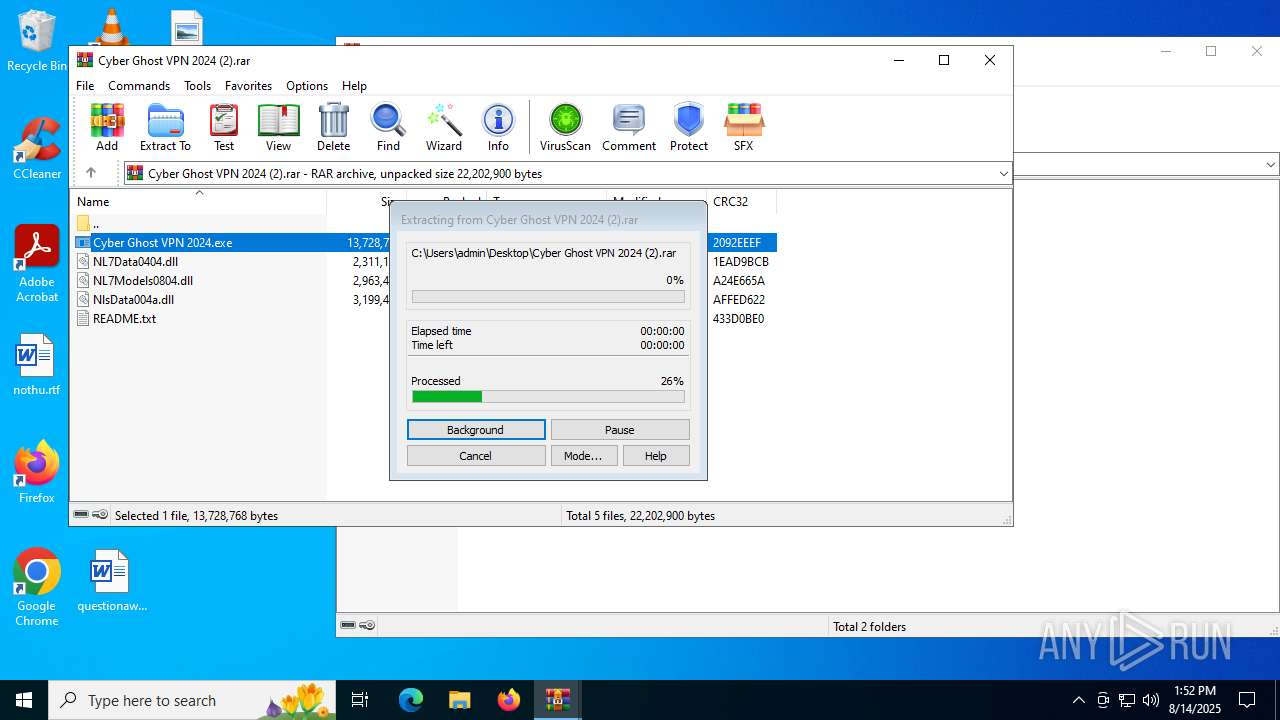
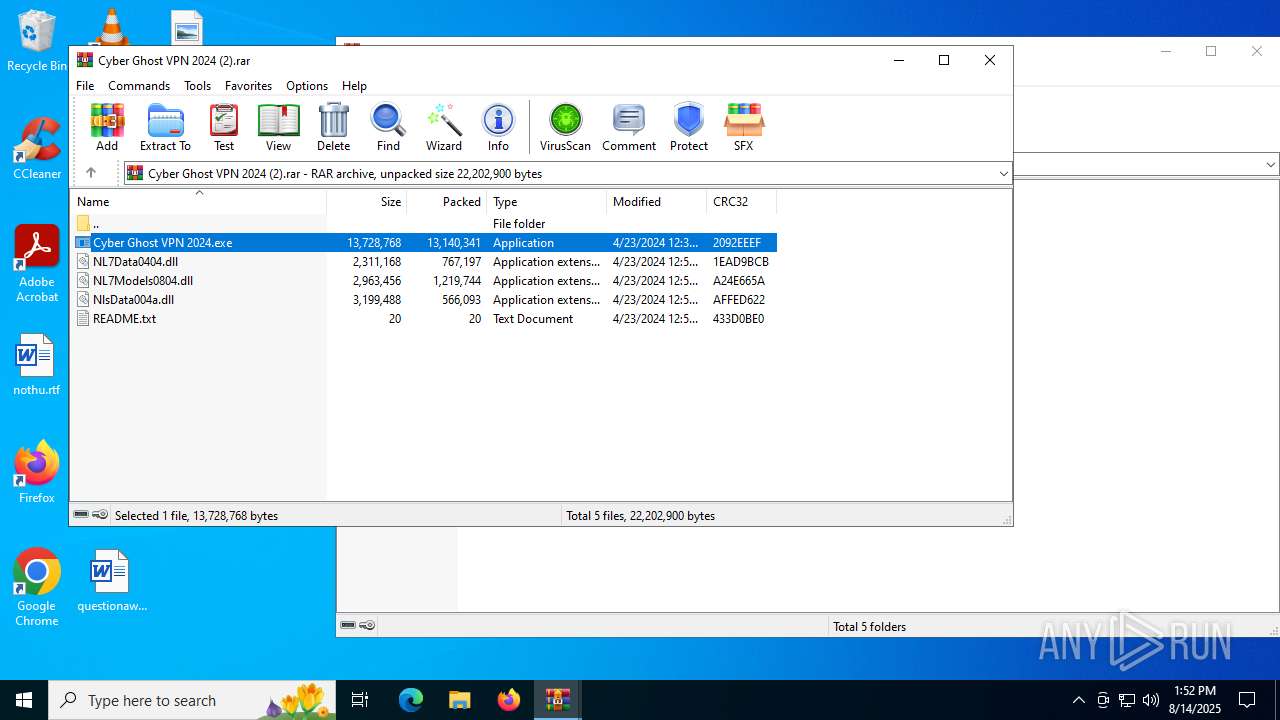
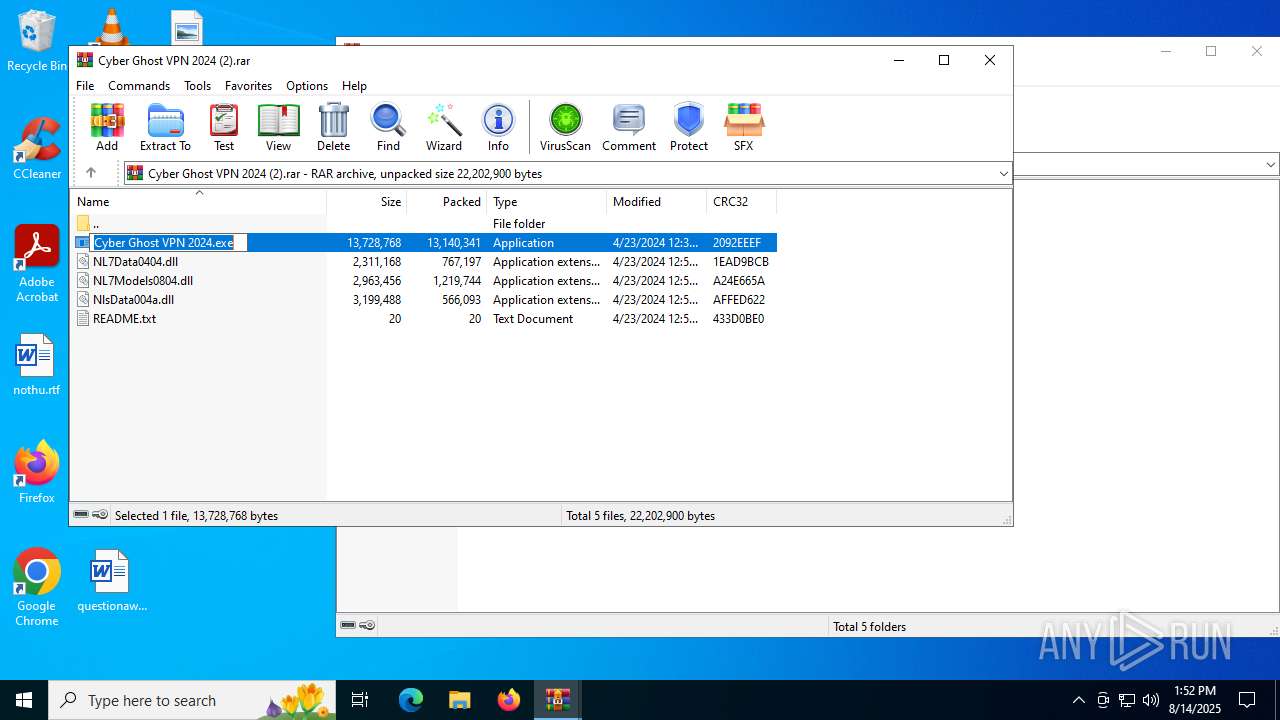
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 2AA9C51D699AA0B05421F246D61182B3 |
| SHA1: | 52743A631D4147E47145EDA40F810214793B9361 |
| SHA256: | 2DB0FEEF7BBB3656D21490E7962A09B62F72FBDA5B60382D973CE6D2395C9DE0 |
| SSDEEP: | 98304:7fzi723gXWkAUDRdrpYBjd6j0EZAPd5vUYAuTGNA2QNH7Jt2sVV59h/zRweEr3C9:WIum1LwRDynSe77tKFlJZ2H |
MALICIOUS
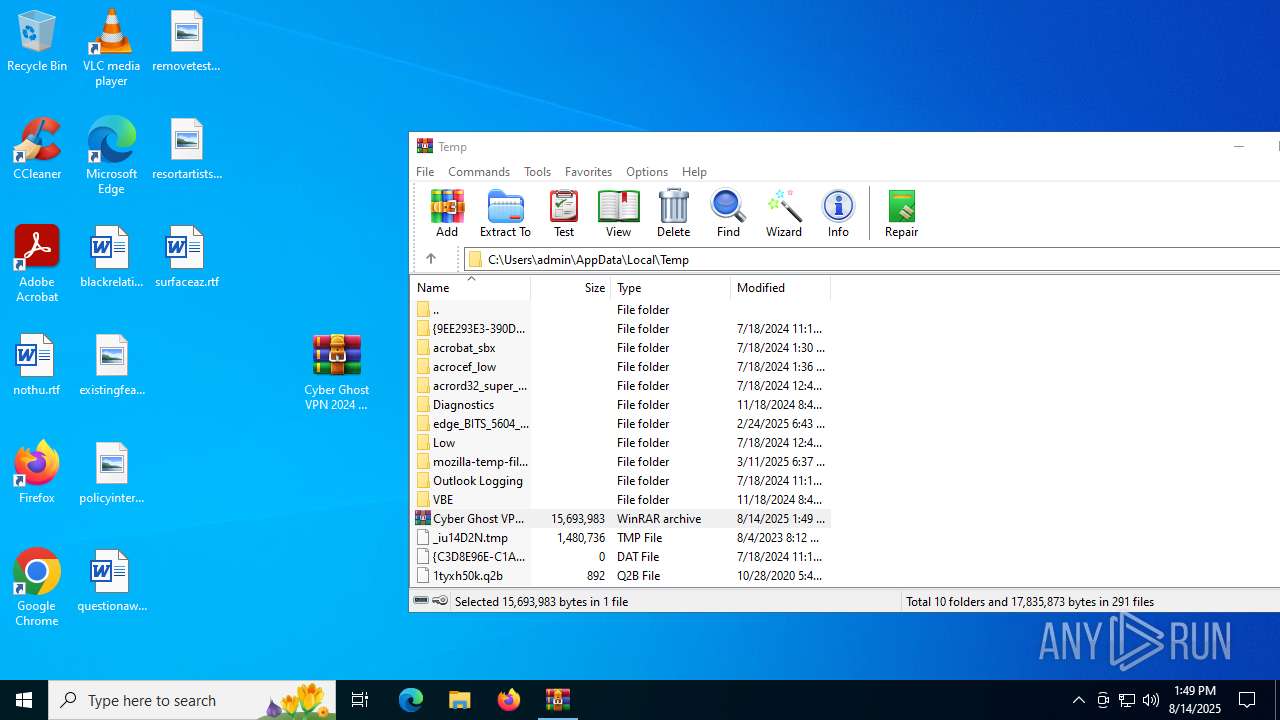
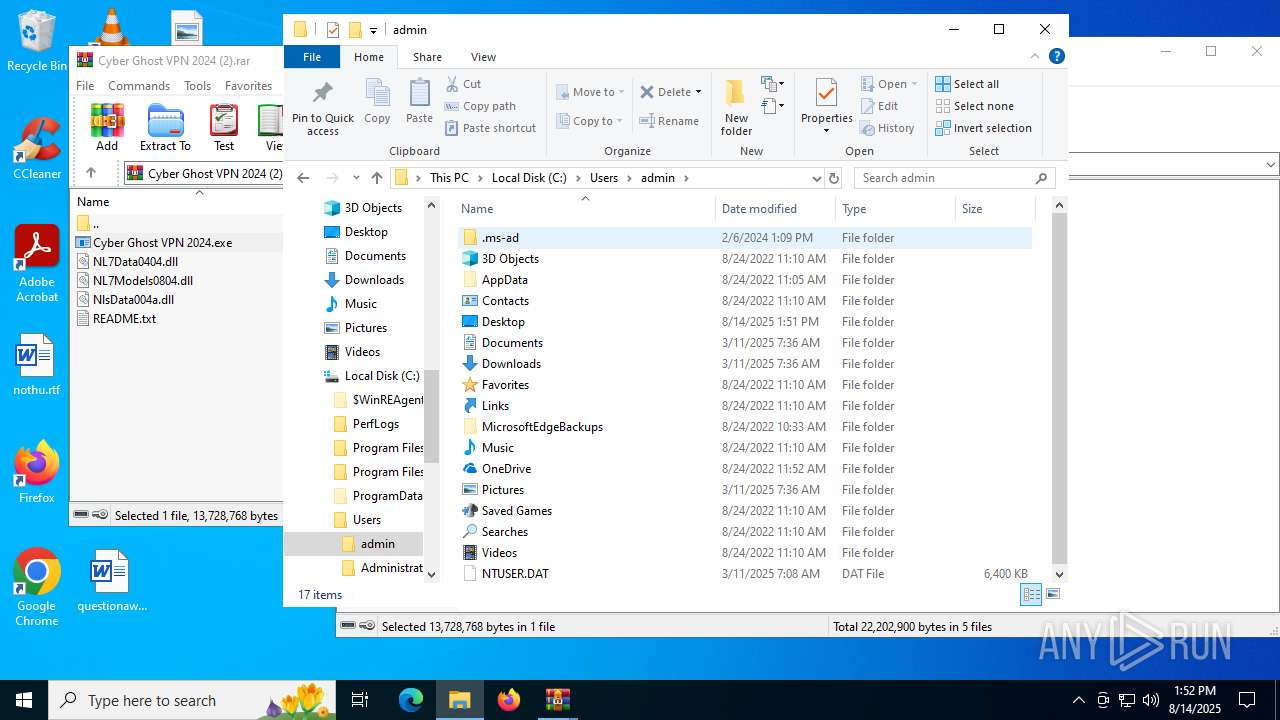
Create files in the Startup directory
- ms_tool.exe (PID: 4788)
DCRAT mutex has been found
- ms_updater.exe (PID: 4676)
- ms_updater.exe (PID: 4116)
- ms_updater.exe (PID: 436)
- ms_updater.exe (PID: 6408)
- ms_updater.exe (PID: 1028)
- ms_updater.exe (PID: 4664)
- ms_updater.exe (PID: 4112)
- ms_updater.exe (PID: 5504)
- ms_updater.exe (PID: 700)
- ms_updater.exe (PID: 6756)
DARKCRYSTAL has been detected (SURICATA)
- ms_updater.exe (PID: 4676)
- ms_updater.exe (PID: 4116)
- ms_updater.exe (PID: 436)
- ms_updater.exe (PID: 6408)
- ms_updater.exe (PID: 1028)
- ms_updater.exe (PID: 4664)
- ms_updater.exe (PID: 4112)
- ms_updater.exe (PID: 5504)
- ms_updater.exe (PID: 6756)
Connects to the CnC server
- ms_updater.exe (PID: 4676)
- ms_updater.exe (PID: 4116)
- ms_updater.exe (PID: 436)
- ms_updater.exe (PID: 6408)
- ms_updater.exe (PID: 1028)
- ms_updater.exe (PID: 4664)
- ms_updater.exe (PID: 4112)
- ms_updater.exe (PID: 5504)
- ms_updater.exe (PID: 6756)
SUSPICIOUS
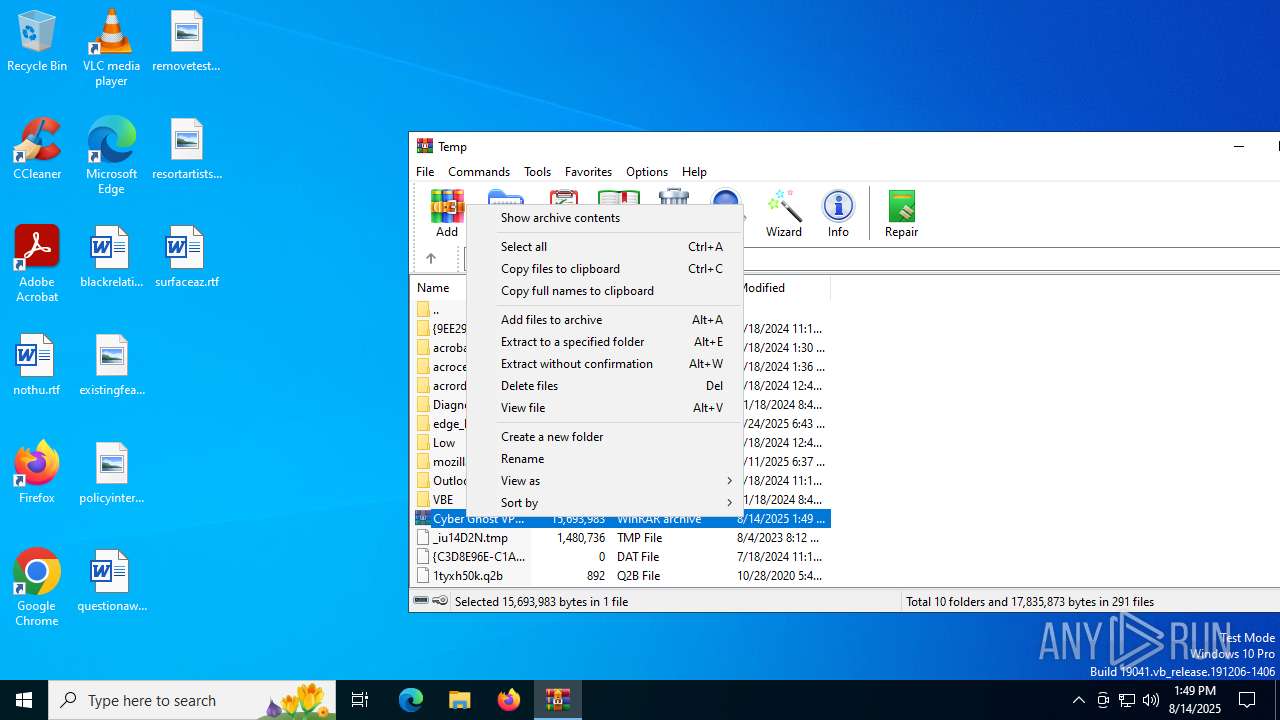
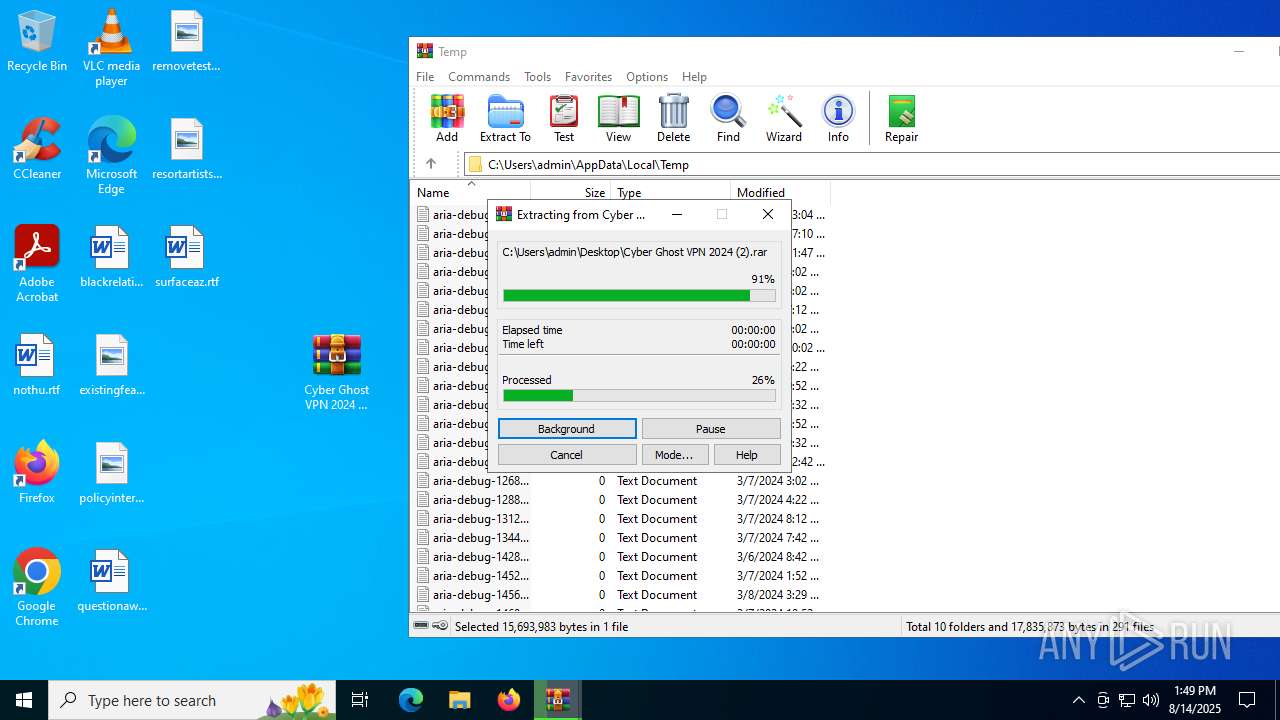
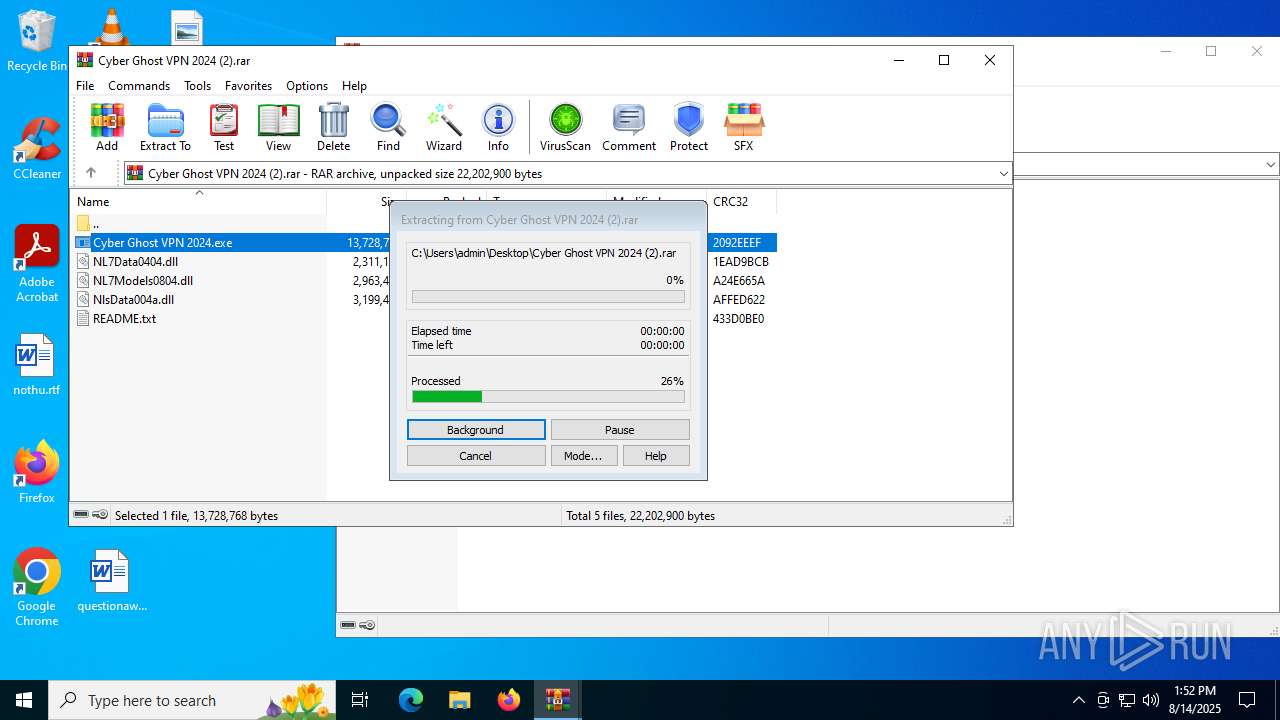
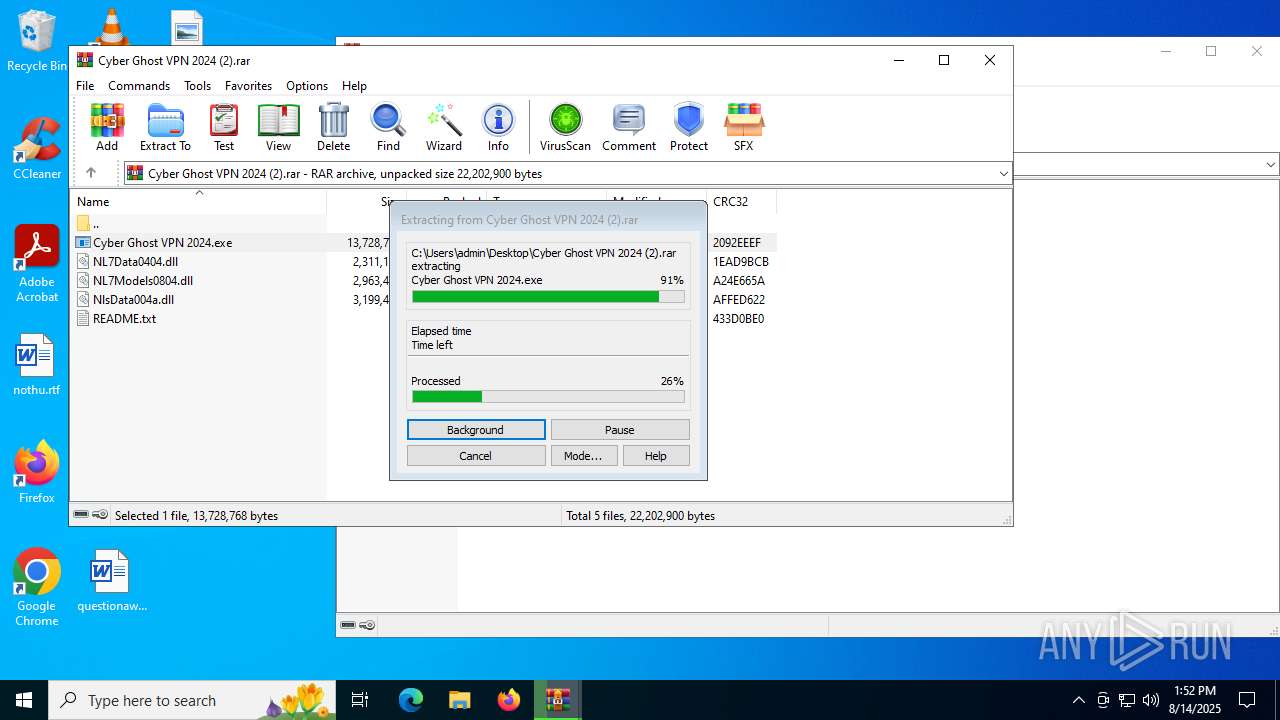
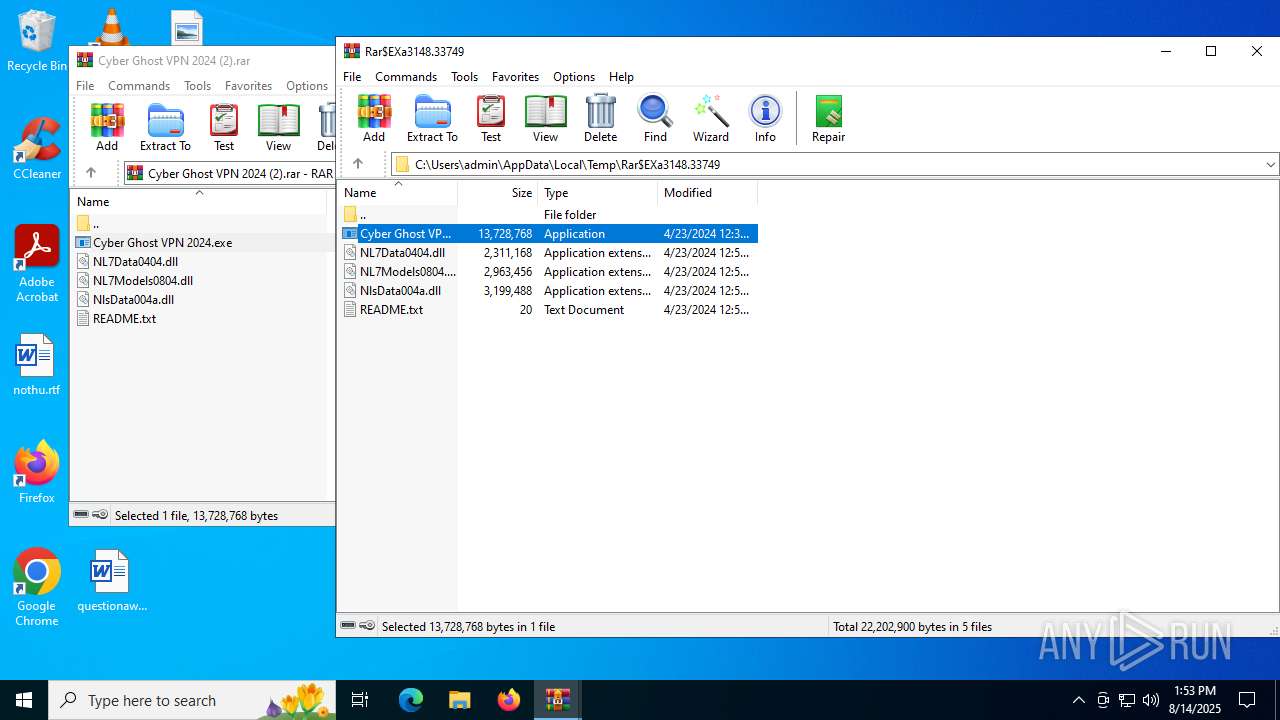
Process drops legitimate windows executable
- WinRAR.exe (PID: 6704)
- WinRAR.exe (PID: 3620)
- WinRAR.exe (PID: 3148)
Executable content was dropped or overwritten
- Cyber Ghost VPN 2024.exe (PID: 2324)
- ms_tool.exe (PID: 4788)
- ms_updater.exe (PID: 4676)
- ms_updater.exe (PID: 4116)
- ms_updater.exe (PID: 436)
- ms_updater.exe (PID: 6408)
- ms_updater.exe (PID: 1028)
- ms_updater.exe (PID: 4664)
- ms_updater.exe (PID: 4112)
- ms_updater.exe (PID: 5504)
- ms_updater.exe (PID: 700)
- ms_updater.exe (PID: 6756)
Reads security settings of Internet Explorer
- Cyber Ghost VPN 2024.exe (PID: 2324)
- ms_updater.exe (PID: 4676)
- ms_updater.exe (PID: 4116)
- ms_updater.exe (PID: 436)
- ms_updater.exe (PID: 6408)
- ms_updater.exe (PID: 1028)
- WinRAR.exe (PID: 6704)
- ms_updater.exe (PID: 4664)
- ms_updater.exe (PID: 4112)
- ms_updater.exe (PID: 5504)
- ms_updater.exe (PID: 700)
- ms_updater.exe (PID: 6756)
- WinRAR.exe (PID: 3148)
Reads the date of Windows installation
- ms_updater.exe (PID: 4676)
- ms_updater.exe (PID: 4116)
- ms_updater.exe (PID: 436)
- ms_updater.exe (PID: 6408)
- ms_updater.exe (PID: 1028)
- ms_updater.exe (PID: 4664)
- ms_updater.exe (PID: 4112)
- ms_updater.exe (PID: 5504)
- ms_updater.exe (PID: 700)
- ms_updater.exe (PID: 6756)
- SearchApp.exe (PID: 4824)
Starts CMD.EXE for commands execution
- ms_updater.exe (PID: 4676)
- ms_updater.exe (PID: 4116)
- ms_updater.exe (PID: 436)
- ms_updater.exe (PID: 6408)
- ms_updater.exe (PID: 1028)
- ms_updater.exe (PID: 4664)
- ms_updater.exe (PID: 4112)
- ms_updater.exe (PID: 5504)
- ms_updater.exe (PID: 700)
- ms_updater.exe (PID: 6756)
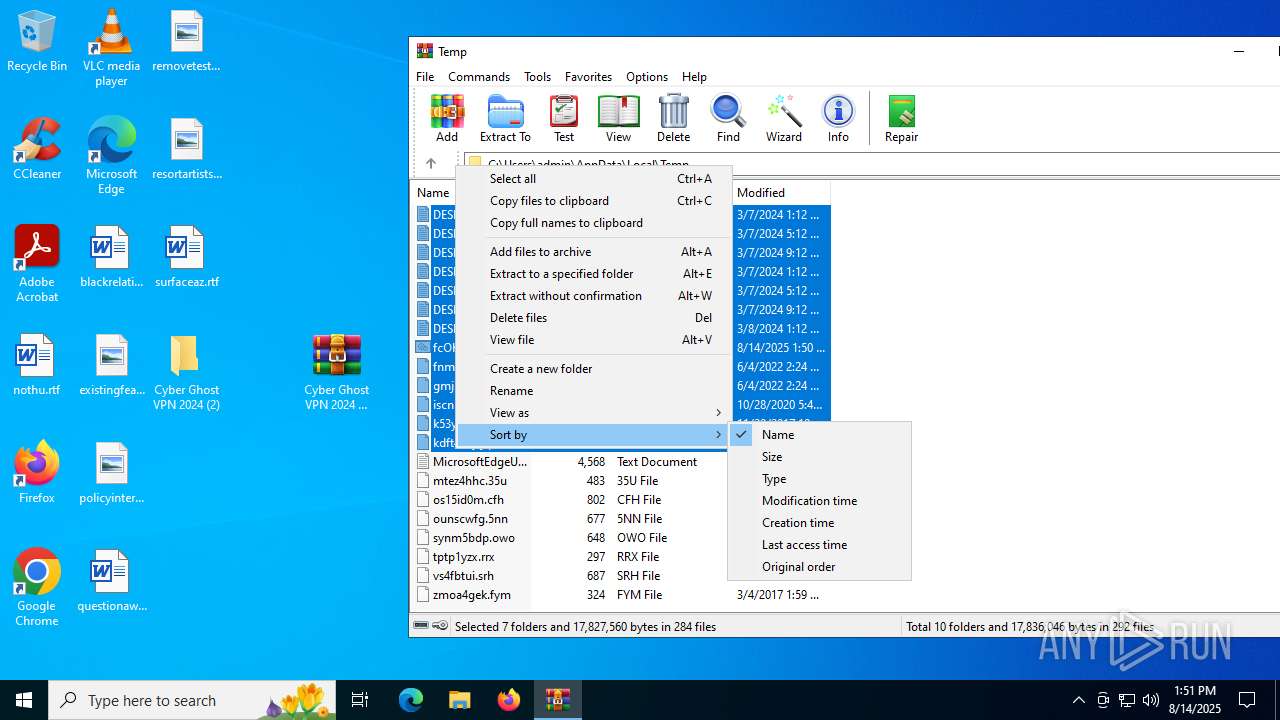
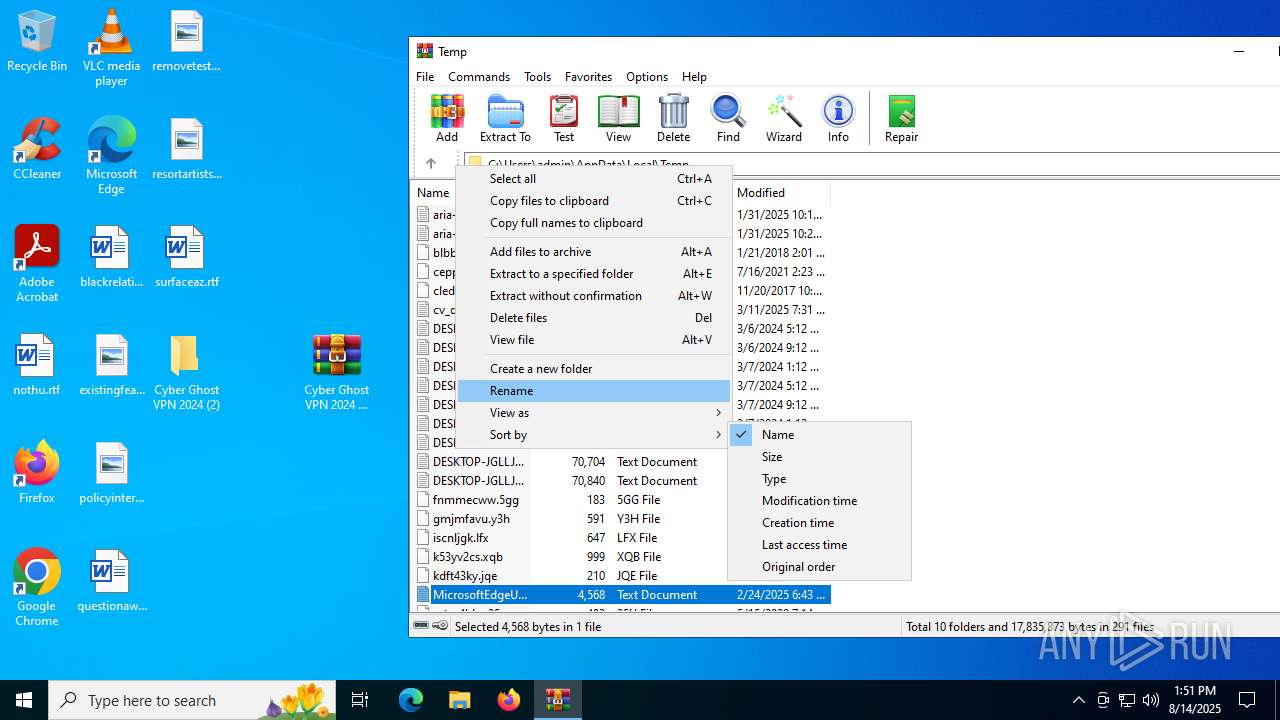
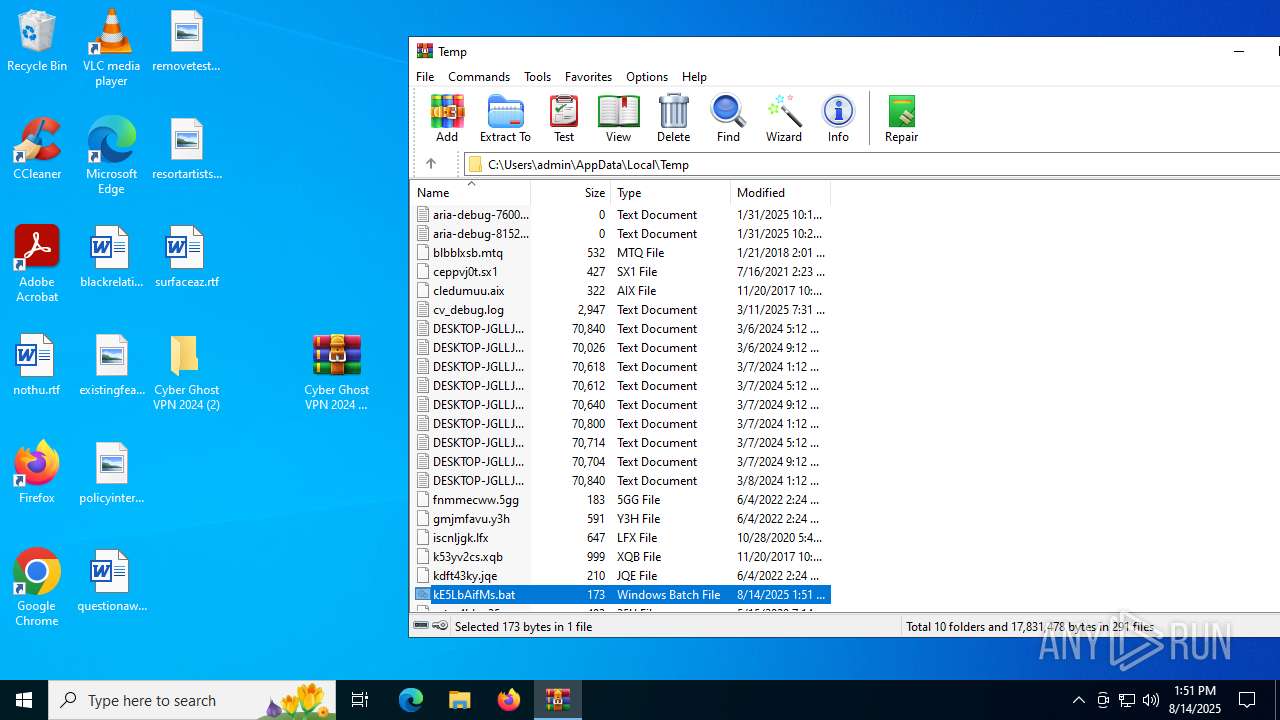
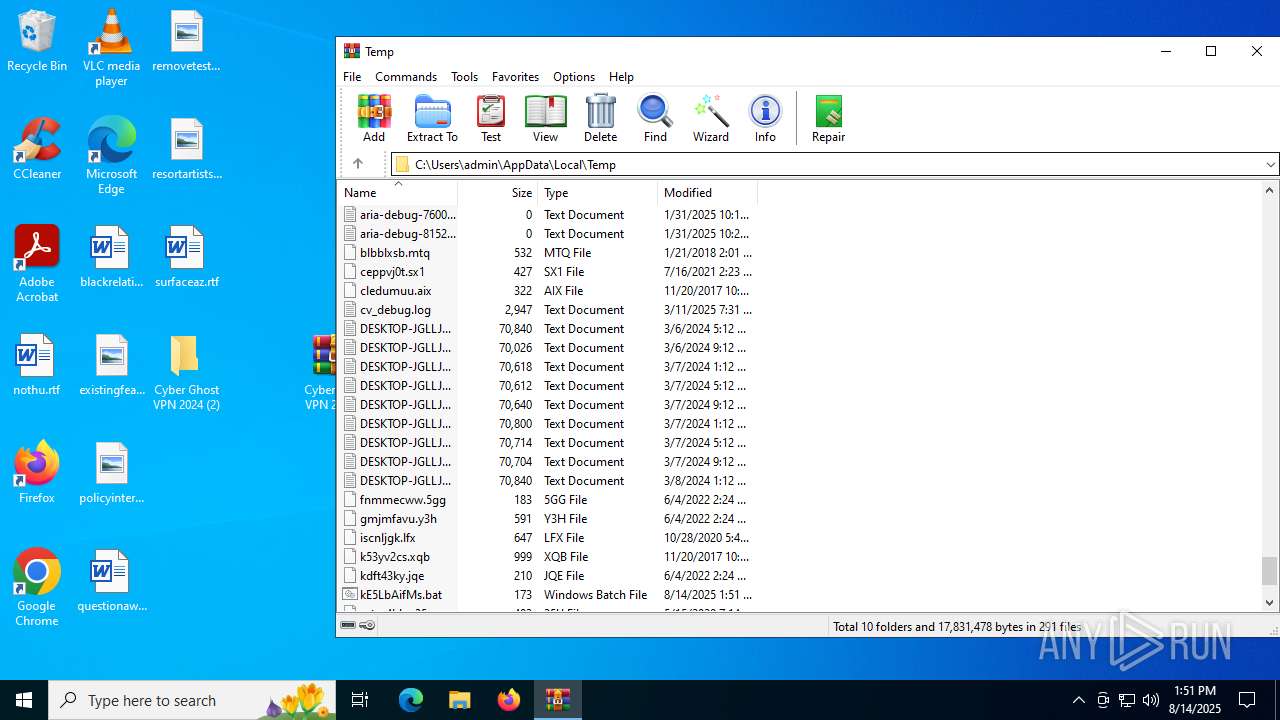
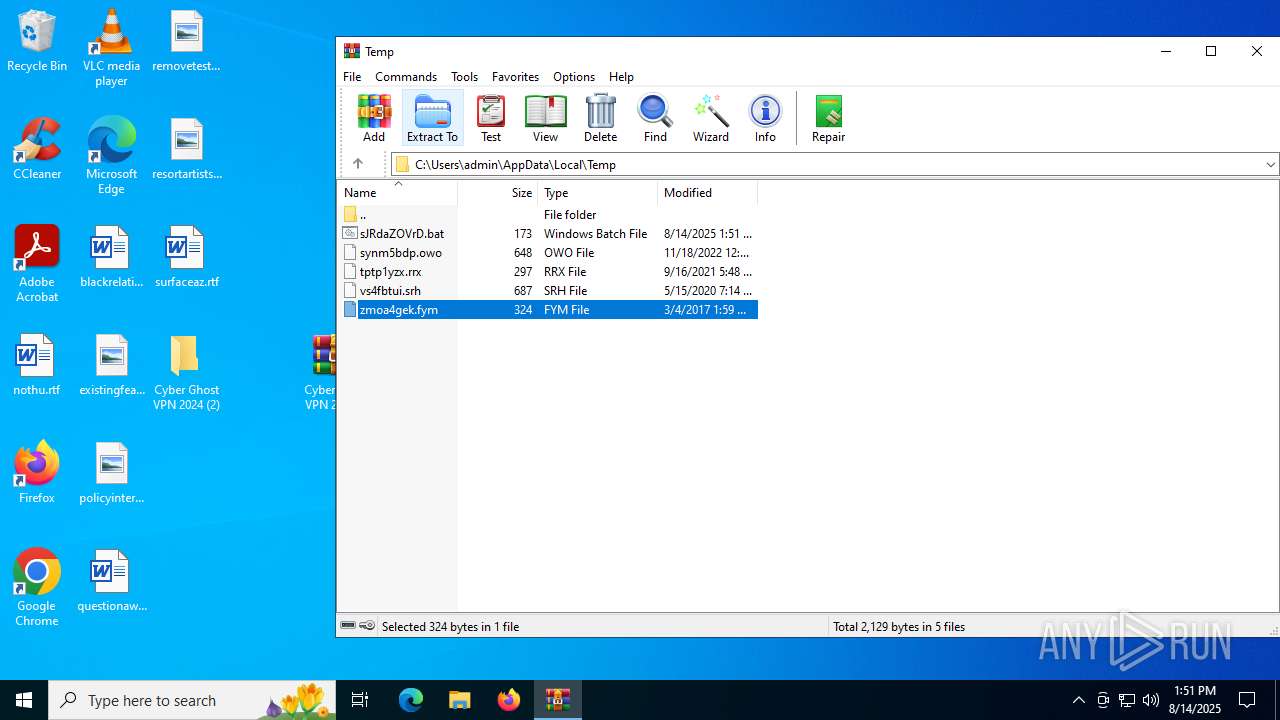
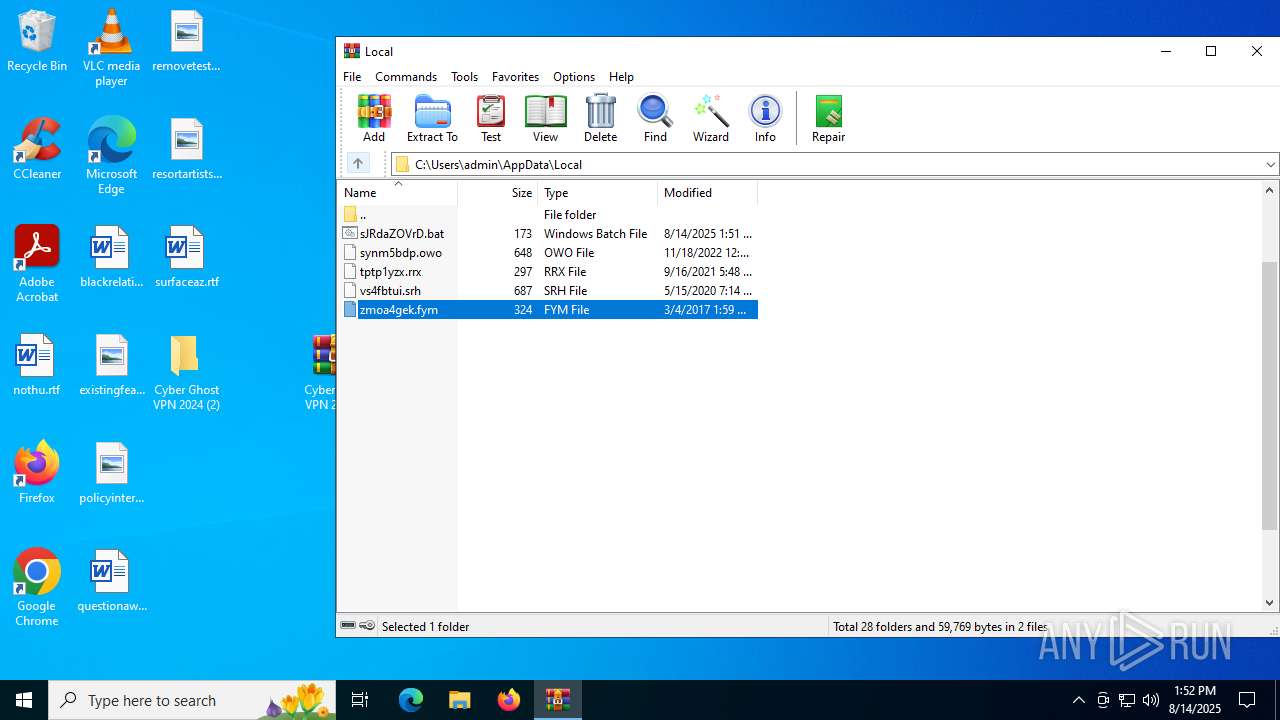
Executing commands from a ".bat" file
- ms_updater.exe (PID: 4676)
- ms_updater.exe (PID: 4116)
- ms_updater.exe (PID: 436)
- ms_updater.exe (PID: 6408)
- ms_updater.exe (PID: 1028)
- ms_updater.exe (PID: 4664)
- ms_updater.exe (PID: 4112)
- ms_updater.exe (PID: 5504)
- ms_updater.exe (PID: 700)
- ms_updater.exe (PID: 6756)
Starts application with an unusual extension
- cmd.exe (PID: 6408)
- cmd.exe (PID: 6648)
- cmd.exe (PID: 6812)
- cmd.exe (PID: 4884)
- cmd.exe (PID: 7076)
- cmd.exe (PID: 4552)
- cmd.exe (PID: 2996)
- cmd.exe (PID: 6356)
- cmd.exe (PID: 512)
- cmd.exe (PID: 4444)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 6408)
- cmd.exe (PID: 6812)
- cmd.exe (PID: 4884)
- cmd.exe (PID: 7076)
- cmd.exe (PID: 4552)
- cmd.exe (PID: 2996)
- cmd.exe (PID: 6356)
- cmd.exe (PID: 512)
- cmd.exe (PID: 4444)
The executable file from the user directory is run by the CMD process
- ms_updater.exe (PID: 4116)
- ms_updater.exe (PID: 436)
- ms_updater.exe (PID: 6408)
- ms_updater.exe (PID: 1028)
- ms_updater.exe (PID: 4664)
- ms_updater.exe (PID: 4112)
- ms_updater.exe (PID: 5504)
- ms_updater.exe (PID: 700)
- ms_updater.exe (PID: 6756)
Found regular expressions for crypto-addresses (YARA)
- ms_tool.exe (PID: 4788)
Probably delay the execution using 'w32tm.exe'
- cmd.exe (PID: 6648)
Executes application which crashes
- Cyber Ghost VPN 2024.exe (PID: 6720)
- Cyber Ghost VPN 2024.exe (PID: 984)
- Cyber Ghost VPN 2024.exe (PID: 4084)
- Cyber Ghost VPN 2024.exe (PID: 4984)
- Cyber Ghost VPN 2024.exe (PID: 5616)
- Cyber Ghost VPN 2024.exe (PID: 5252)
- Cyber Ghost VPN 2024.exe (PID: 5652)
- Cyber Ghost VPN 2024.exe (PID: 2996)
- Cyber Ghost VPN 2024.exe (PID: 6104)
- Cyber Ghost VPN 2024.exe (PID: 1740)
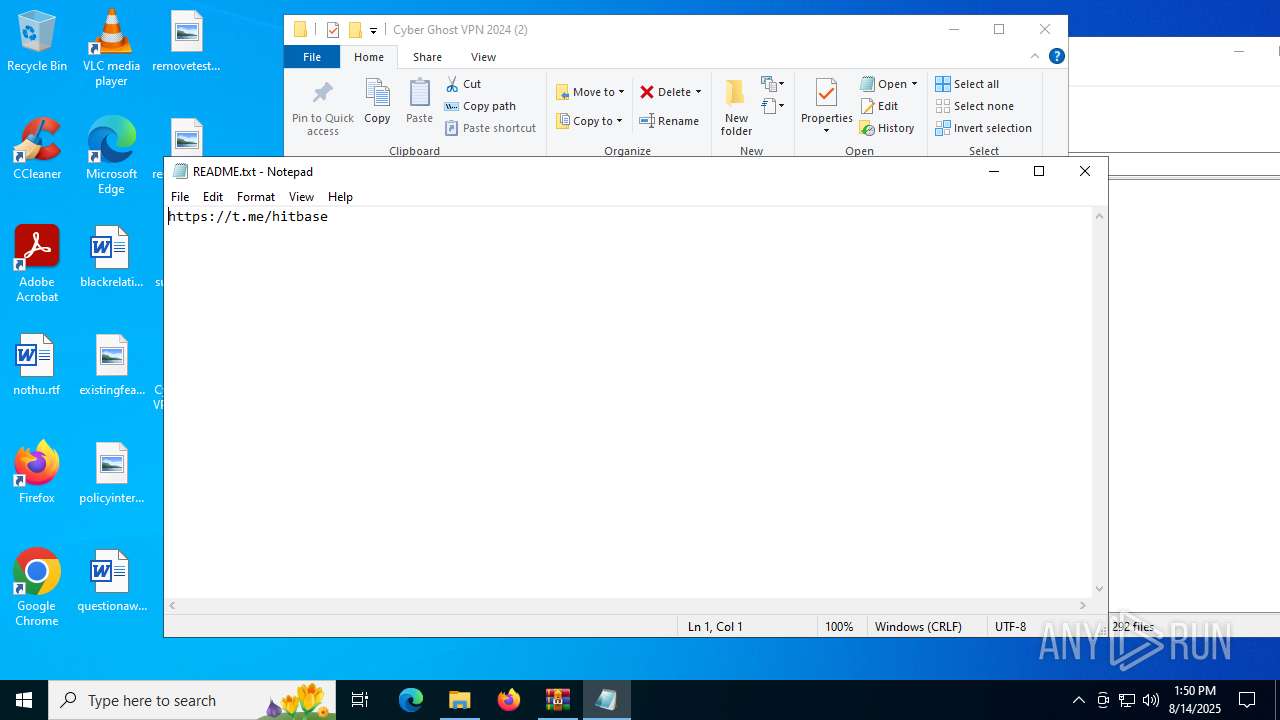
Start notepad (likely ransomware note)
- WinRAR.exe (PID: 6704)
INFO
The sample compiled with english language support
- WinRAR.exe (PID: 6704)
- WinRAR.exe (PID: 3620)
- WinRAR.exe (PID: 3148)
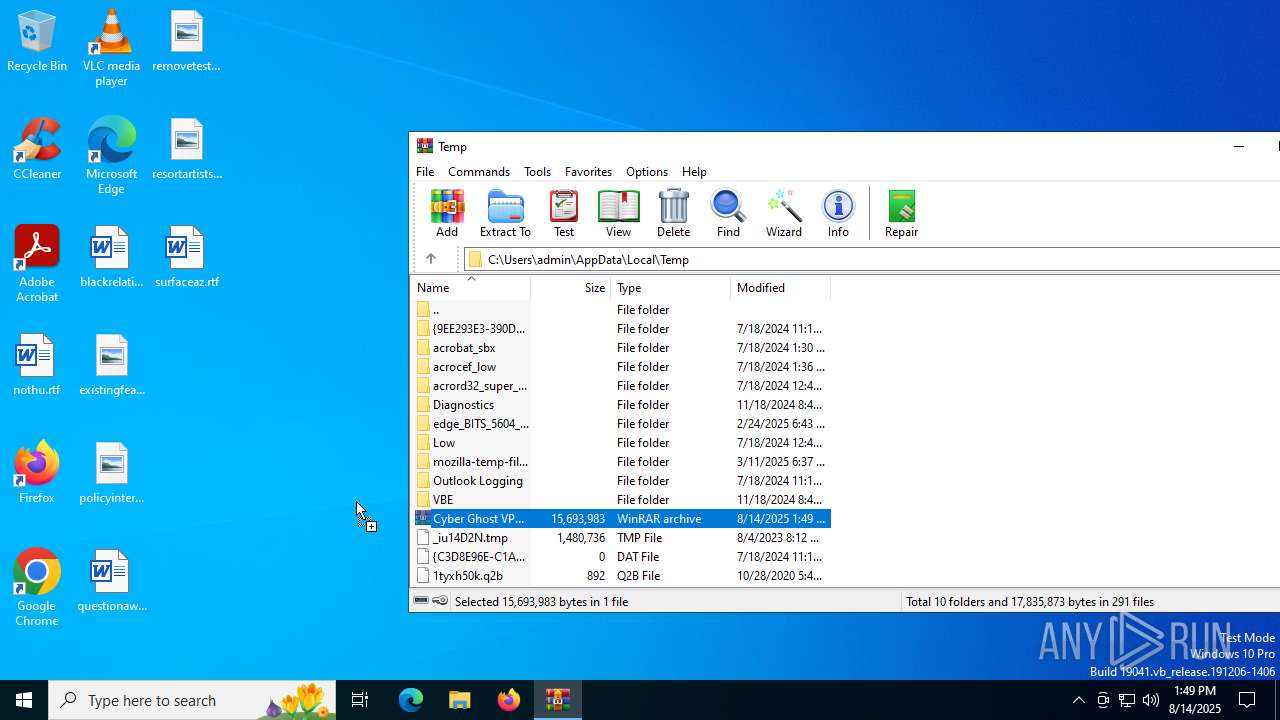
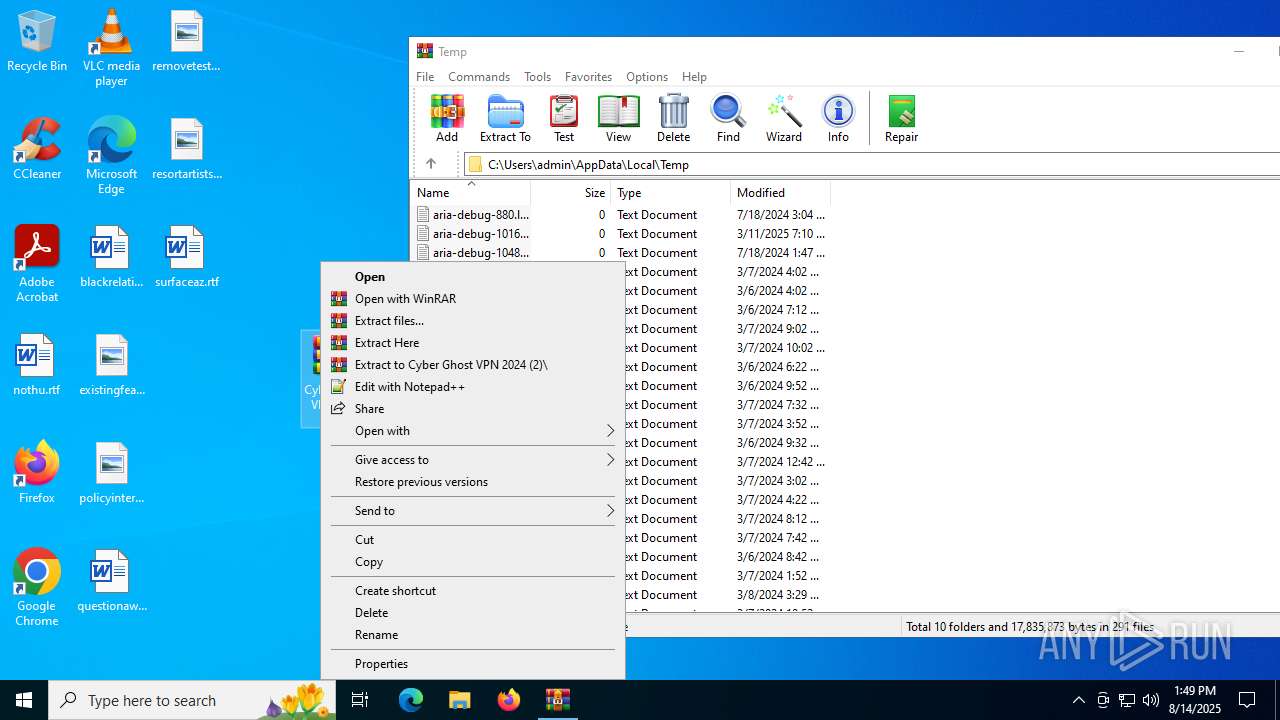
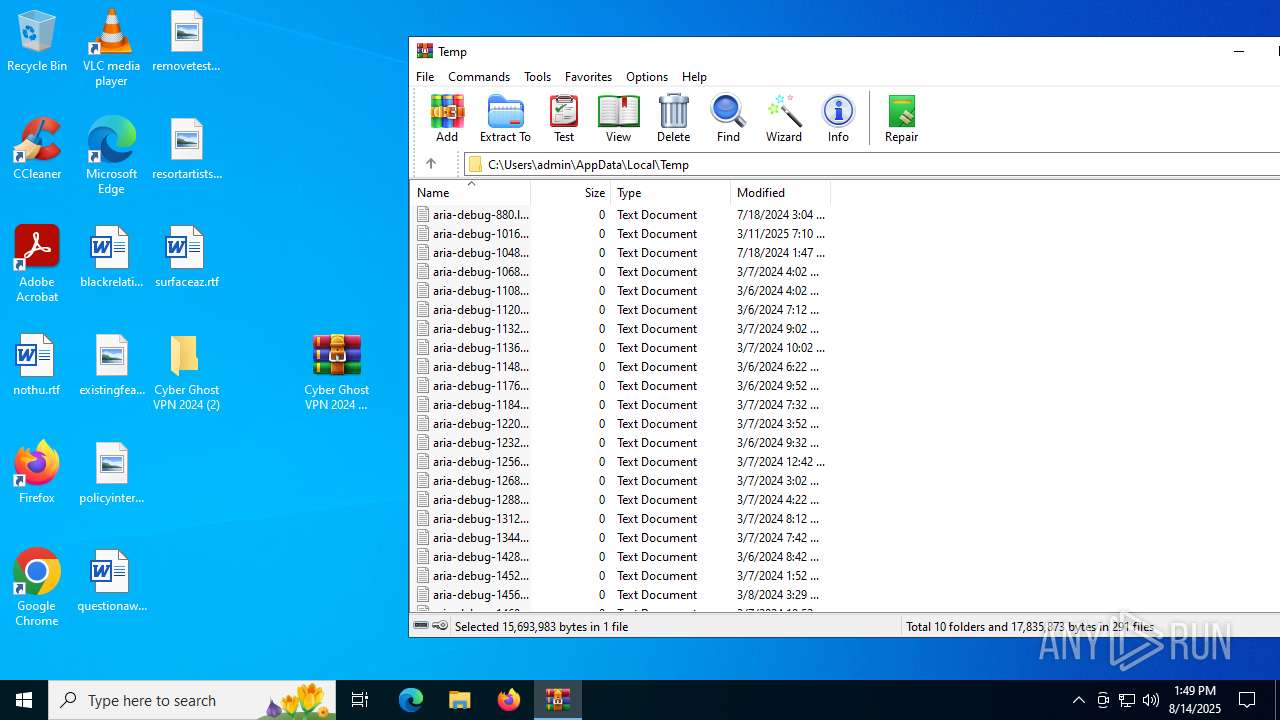
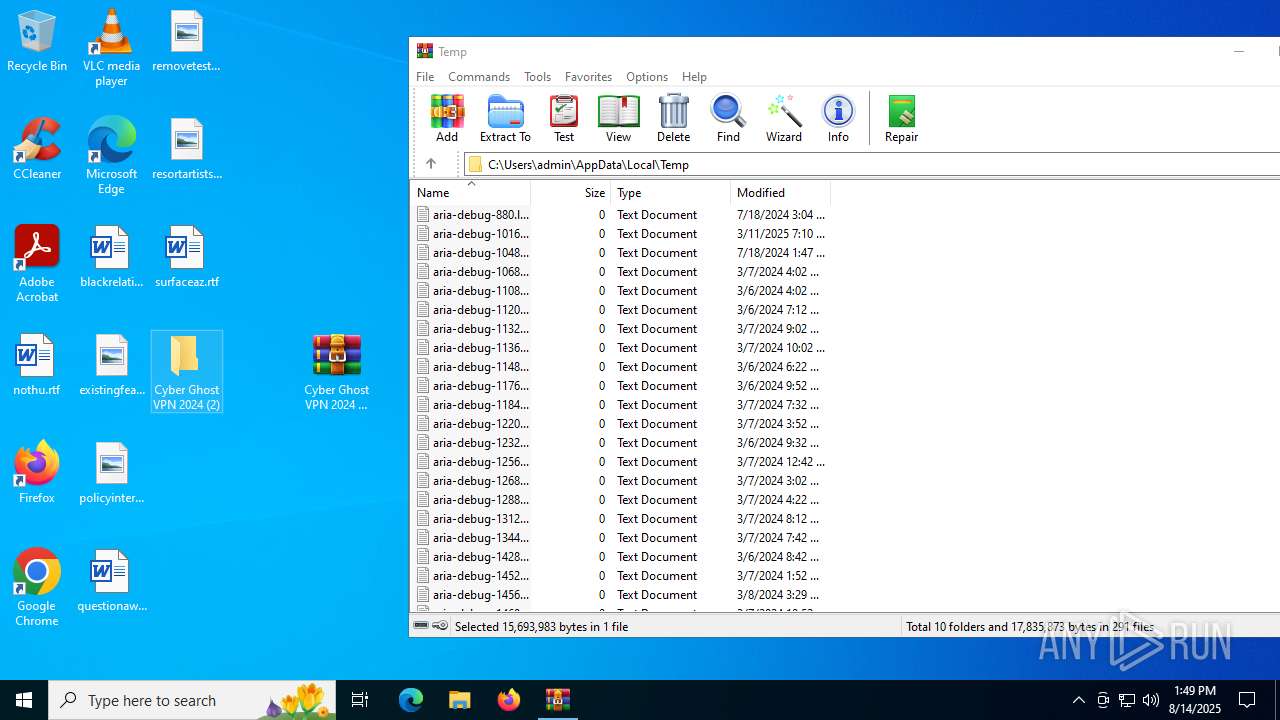
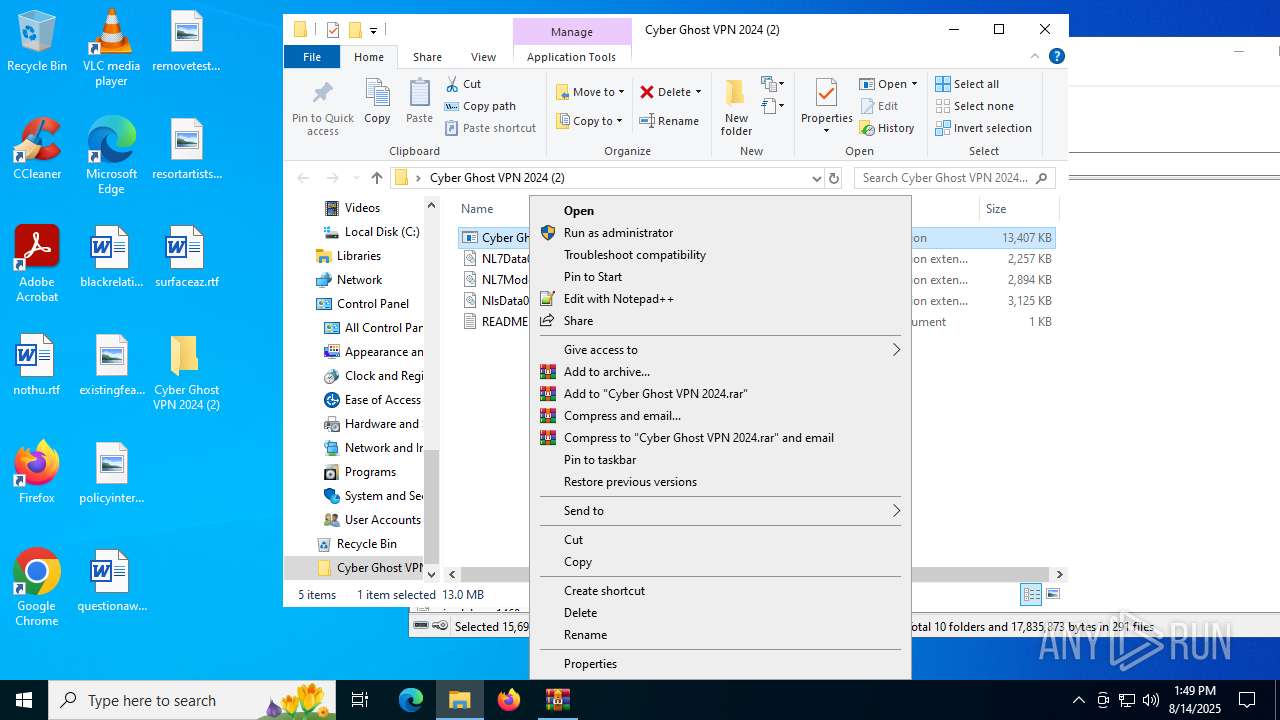
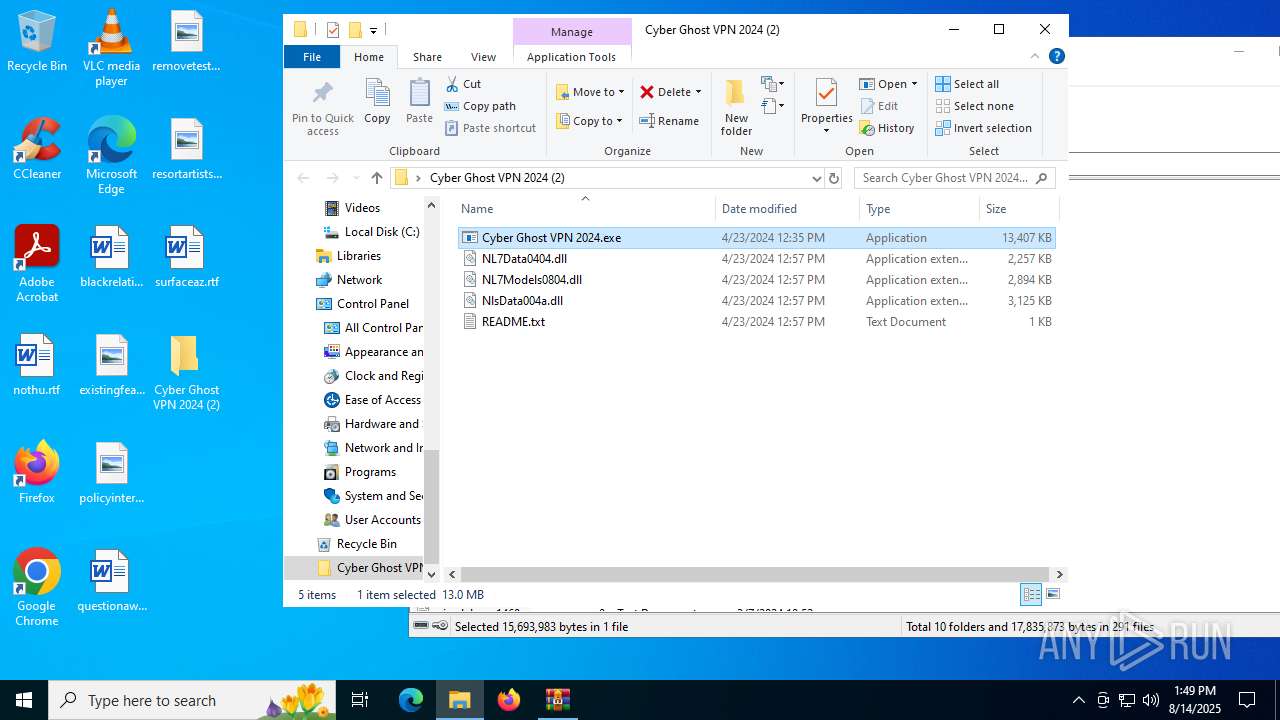
Manual execution by a user
- WinRAR.exe (PID: 3620)
- Cyber Ghost VPN 2024.exe (PID: 2324)
- Cyber Ghost VPN 2024.exe (PID: 6720)
- Cyber Ghost VPN 2024.exe (PID: 984)
- notepad.exe (PID: 2028)
- WinRAR.exe (PID: 3148)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3620)
- WinRAR.exe (PID: 3148)
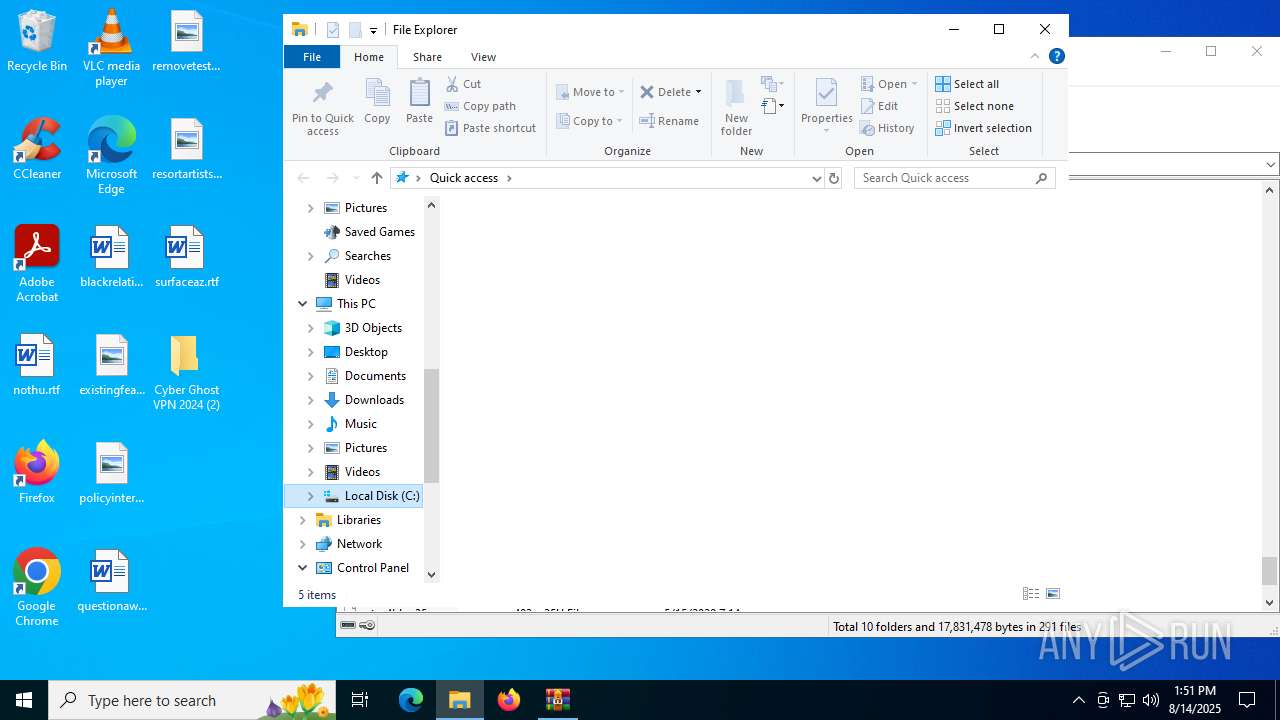
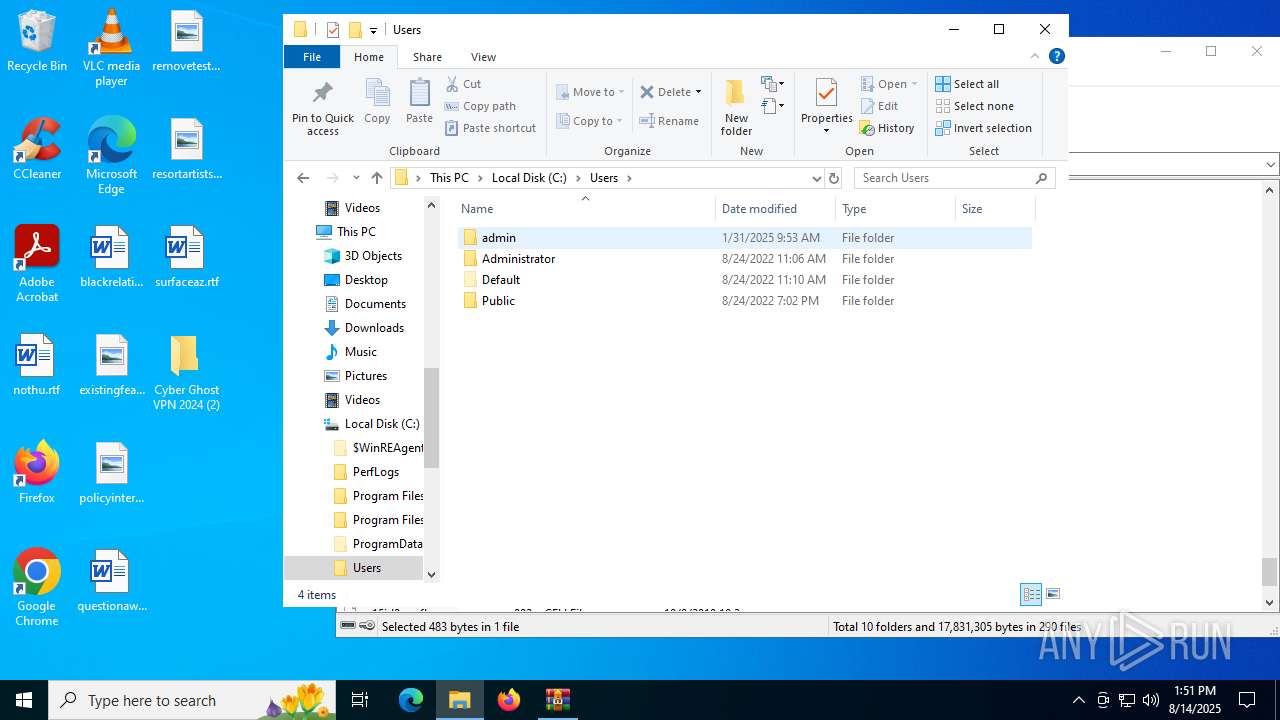
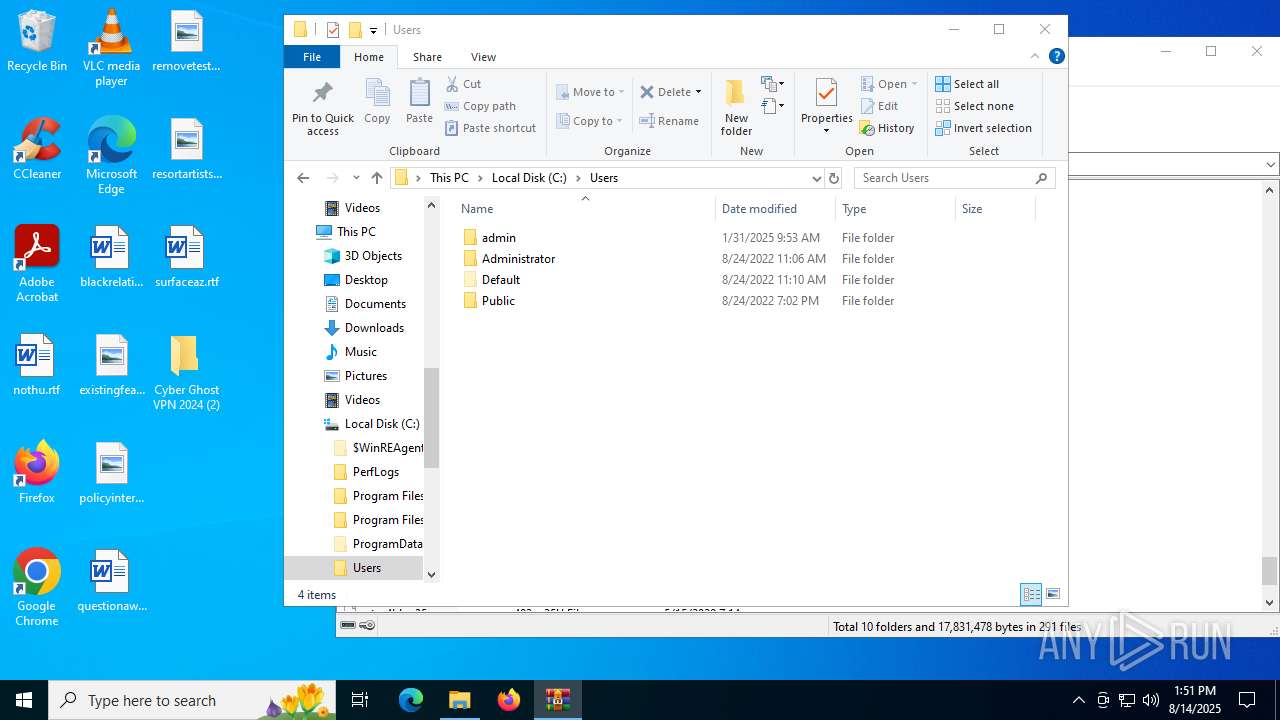
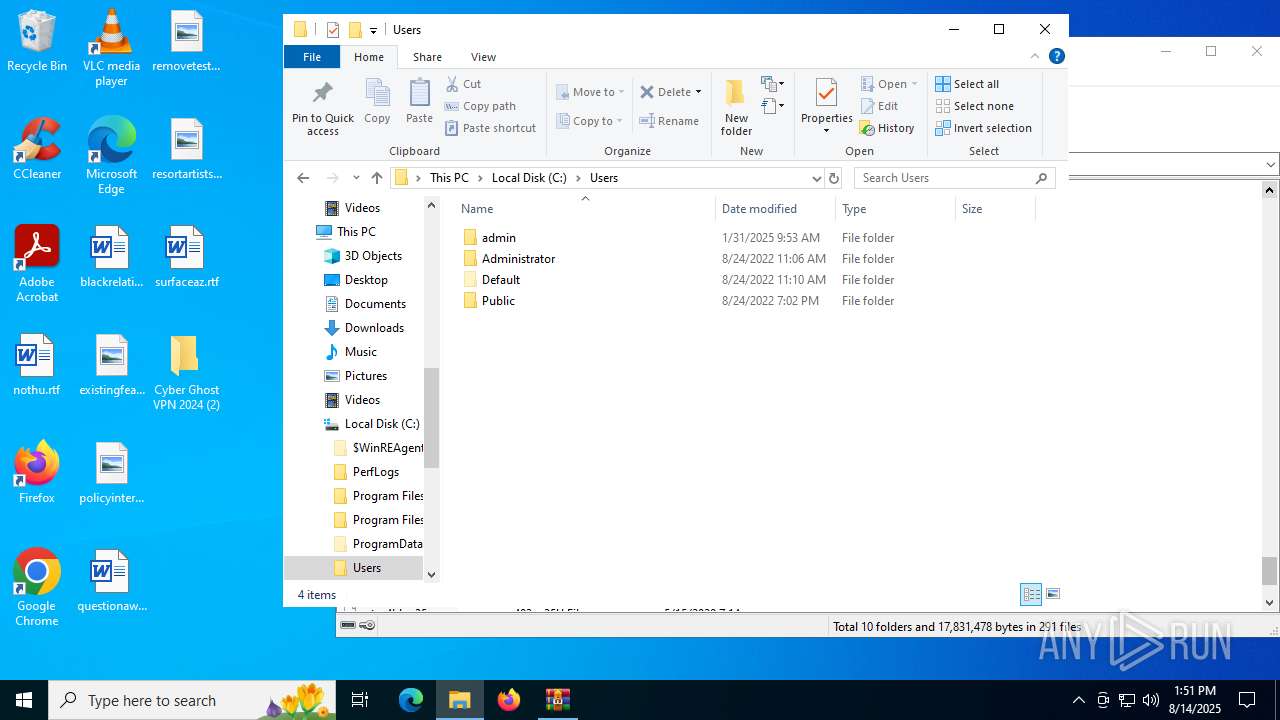
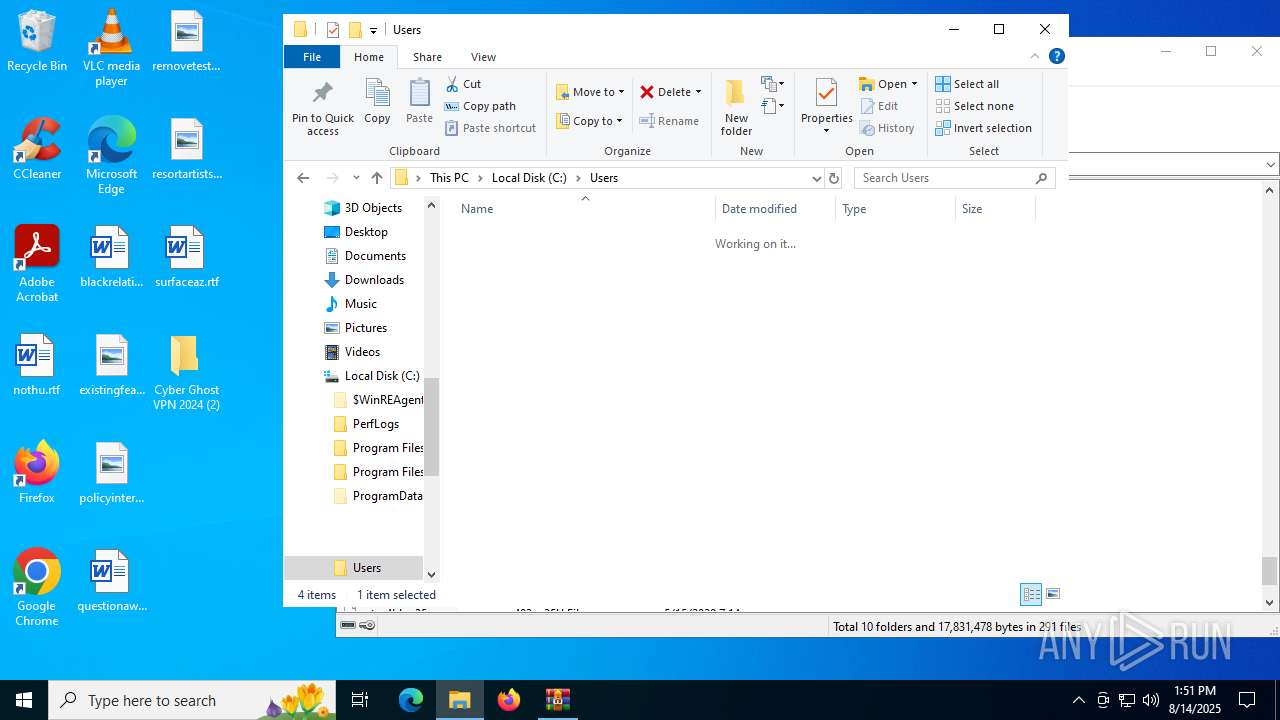
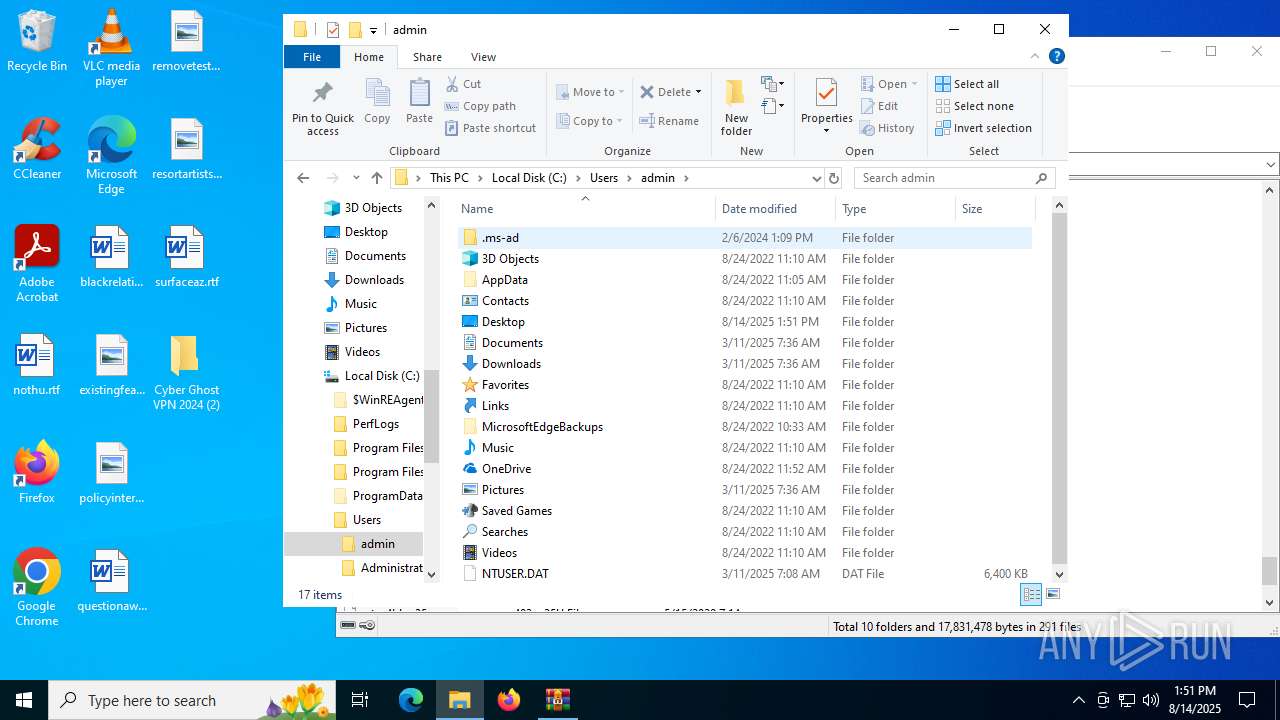
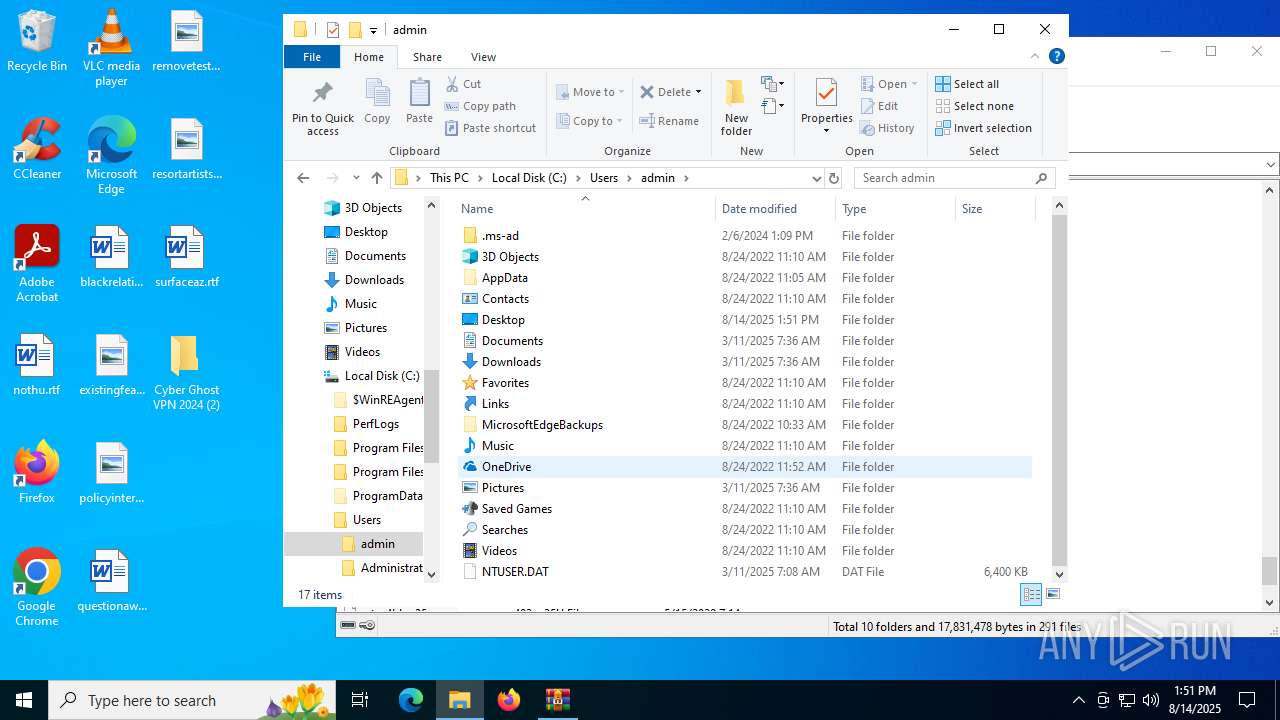
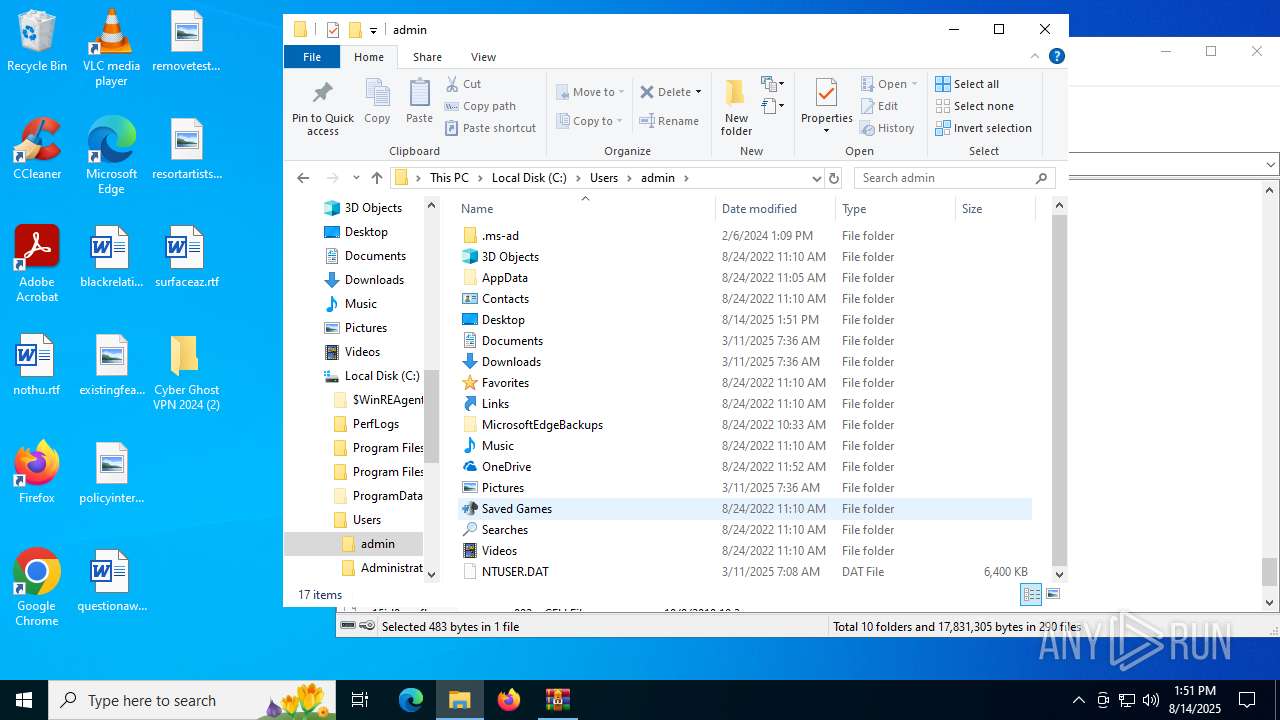
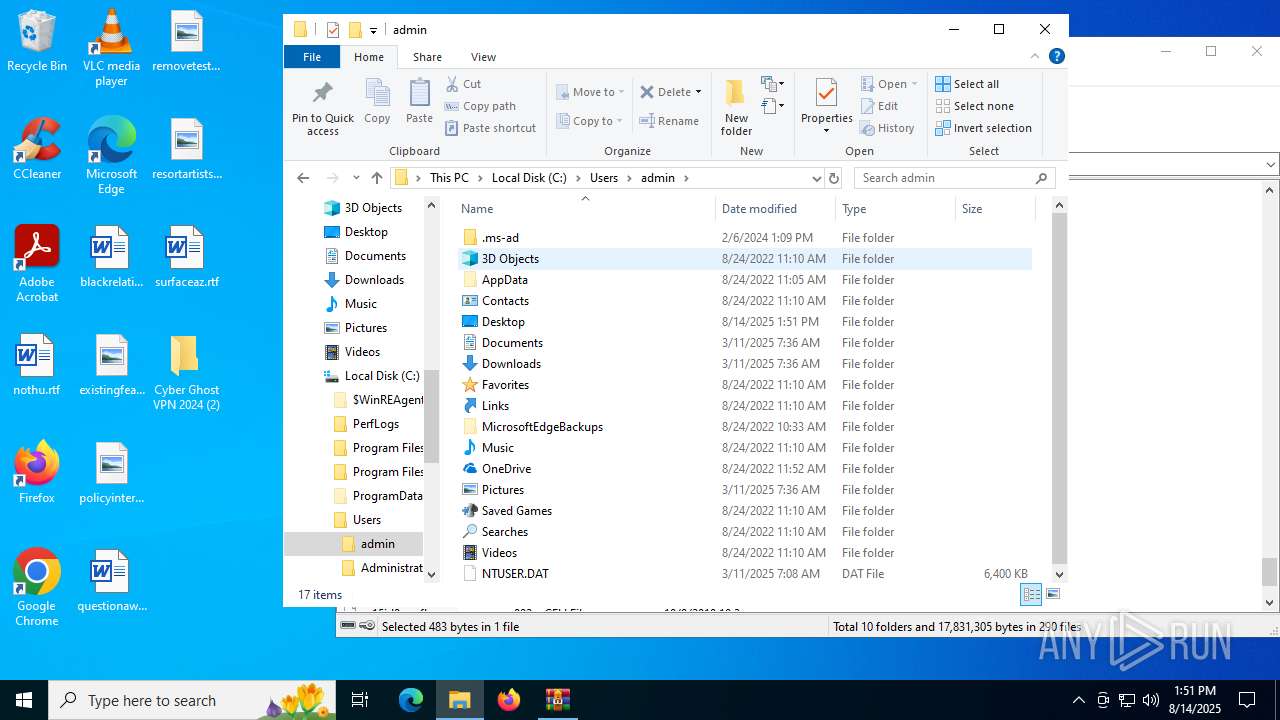
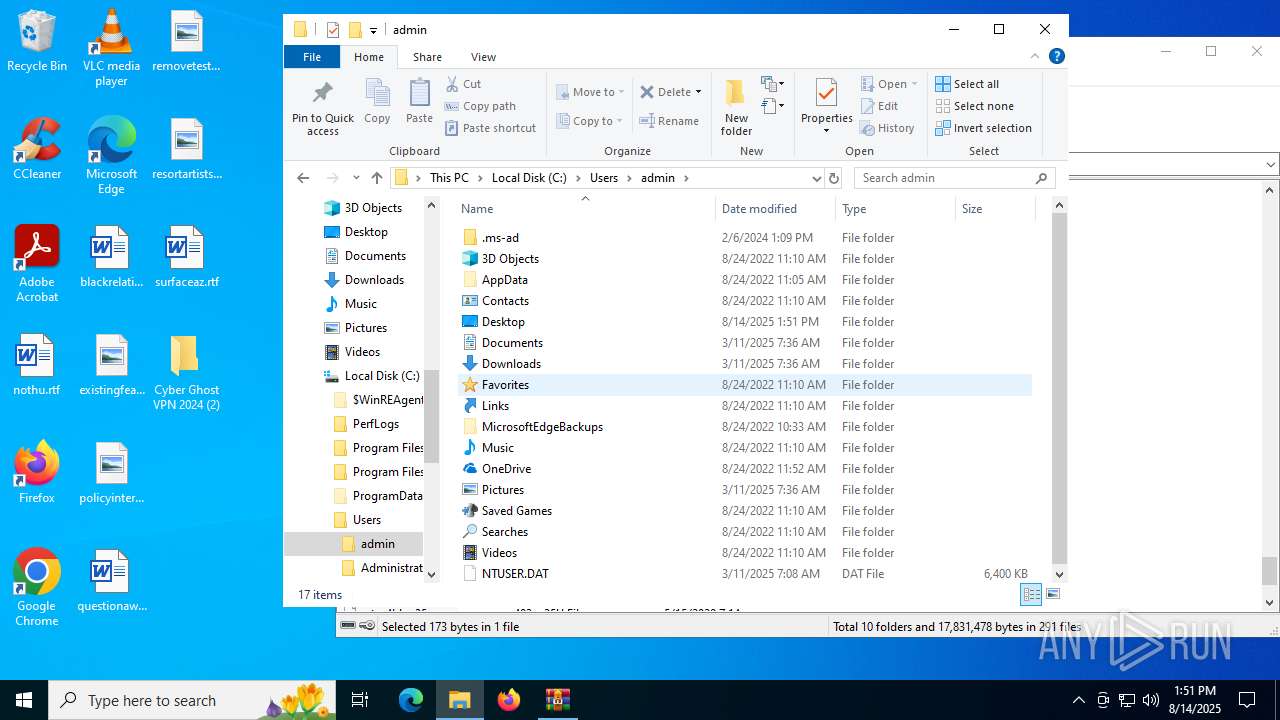
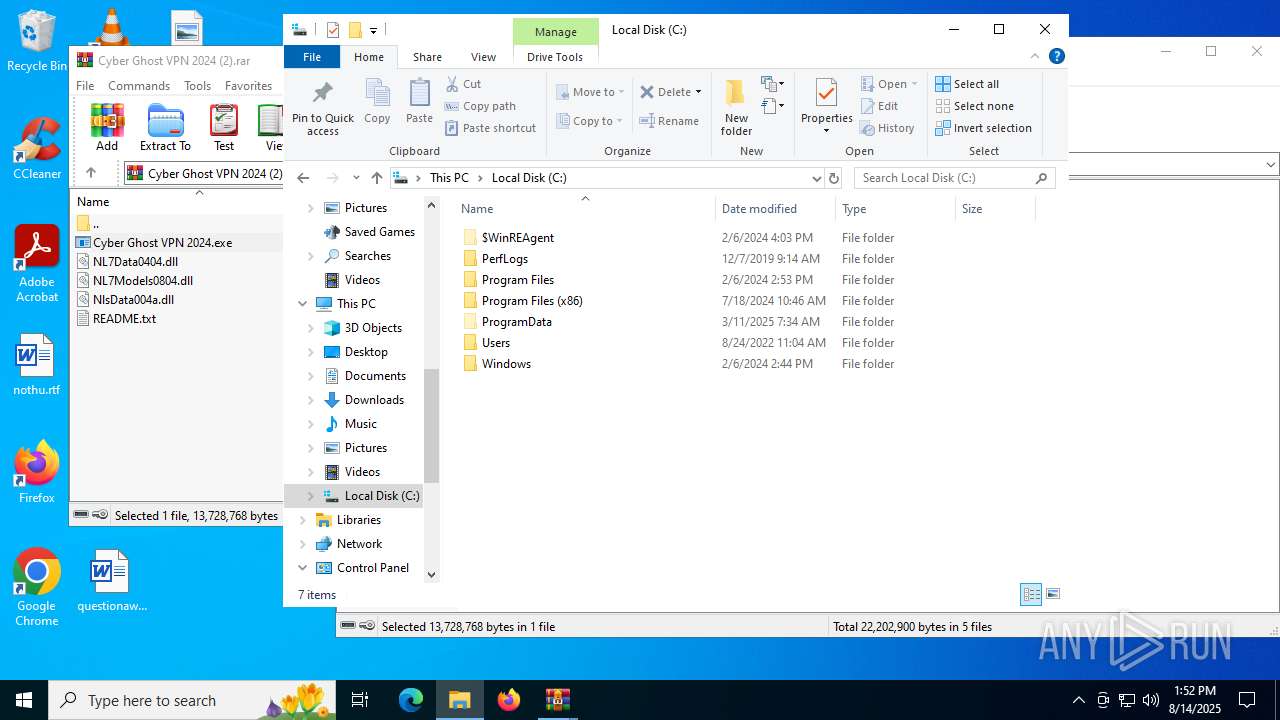
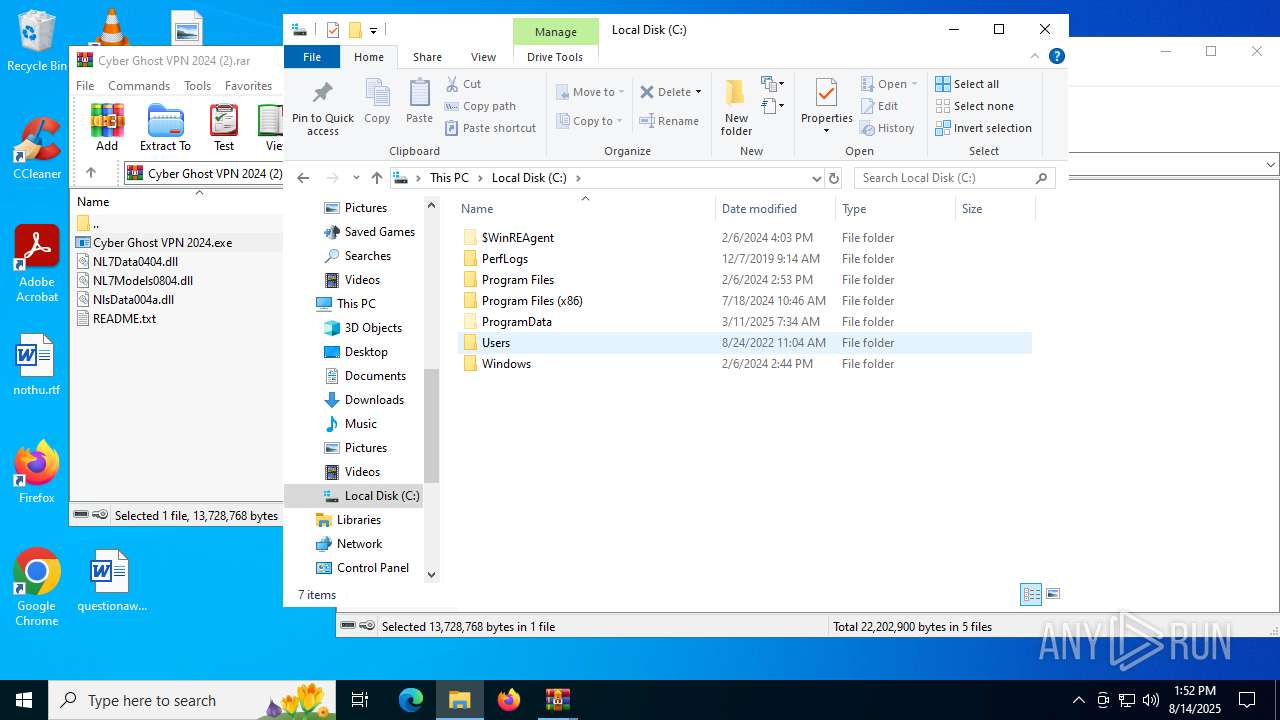
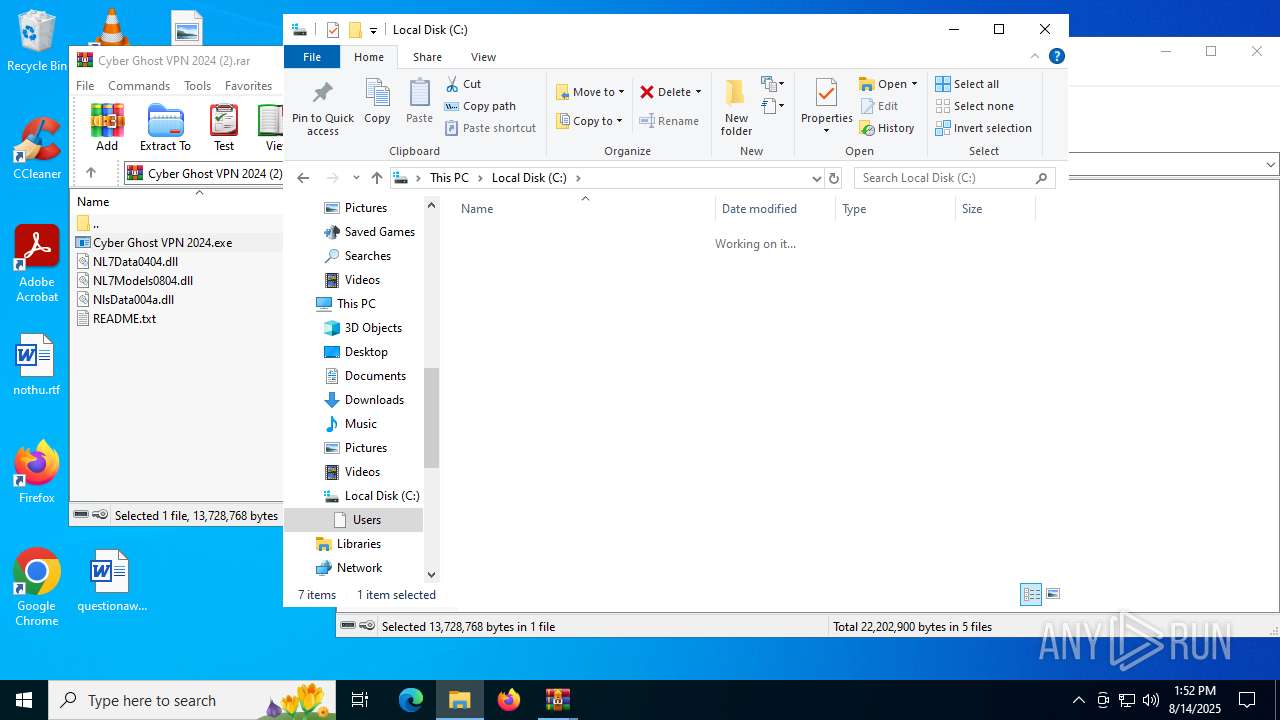
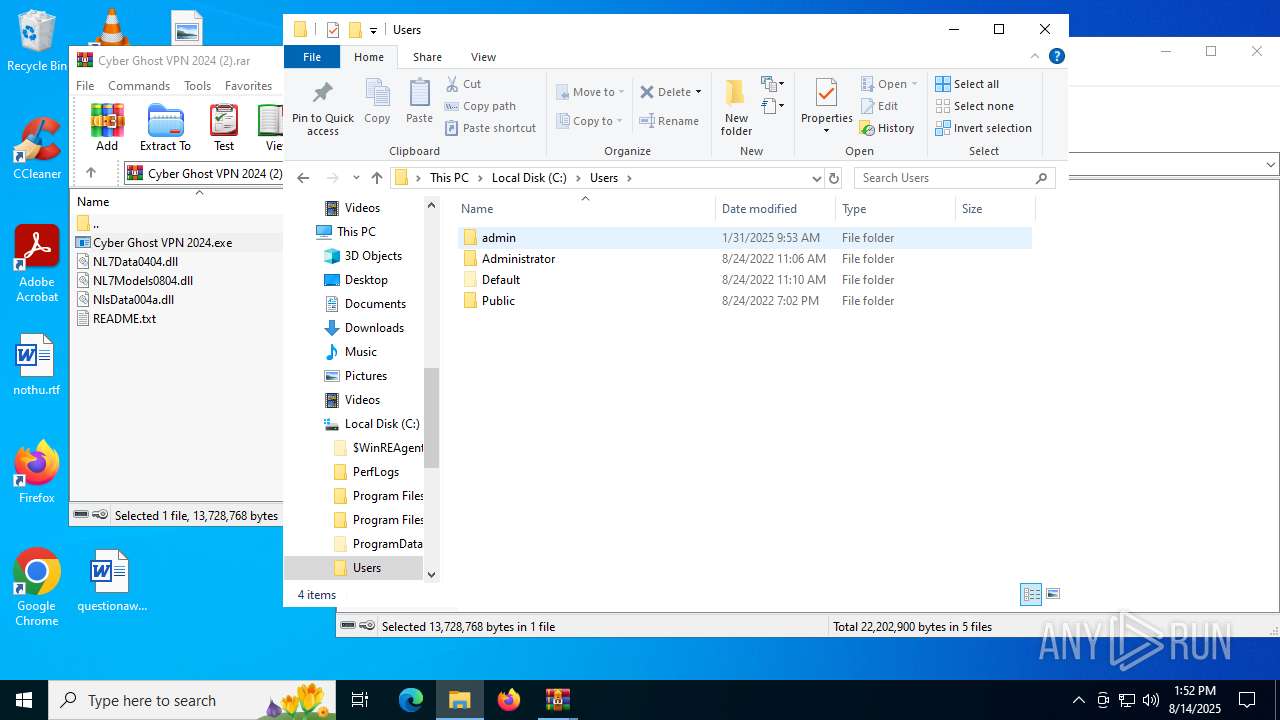
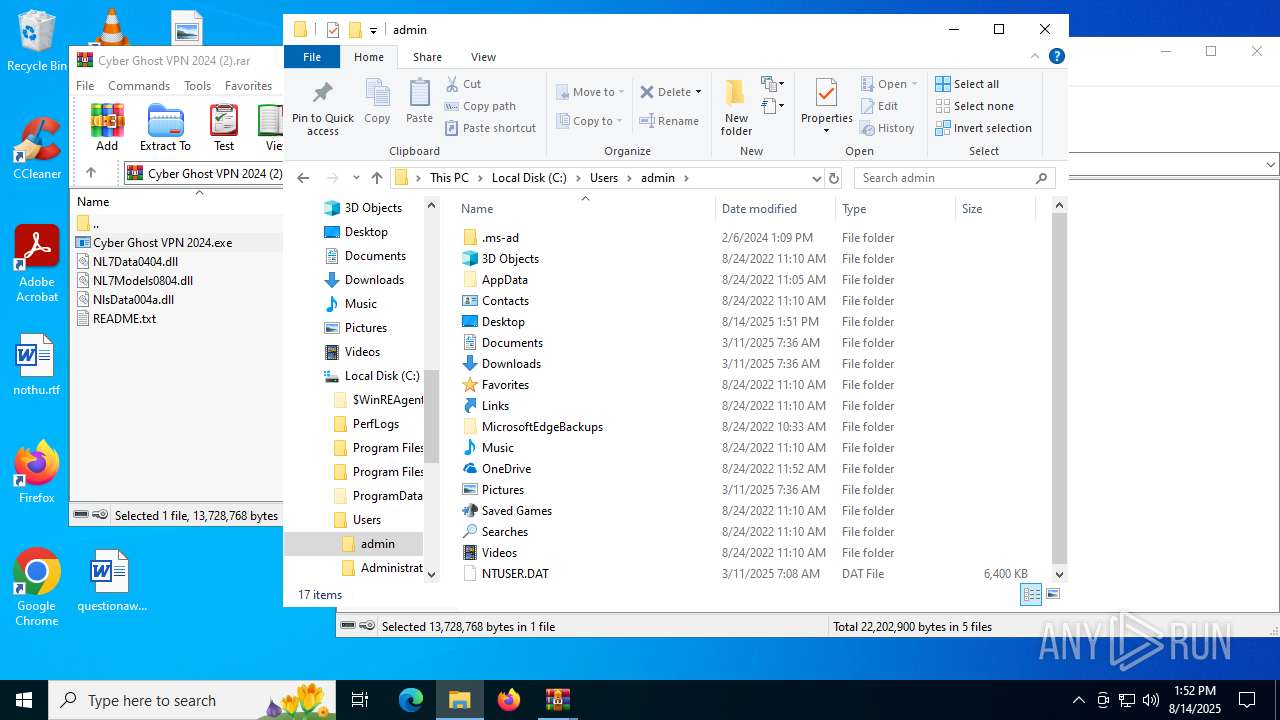
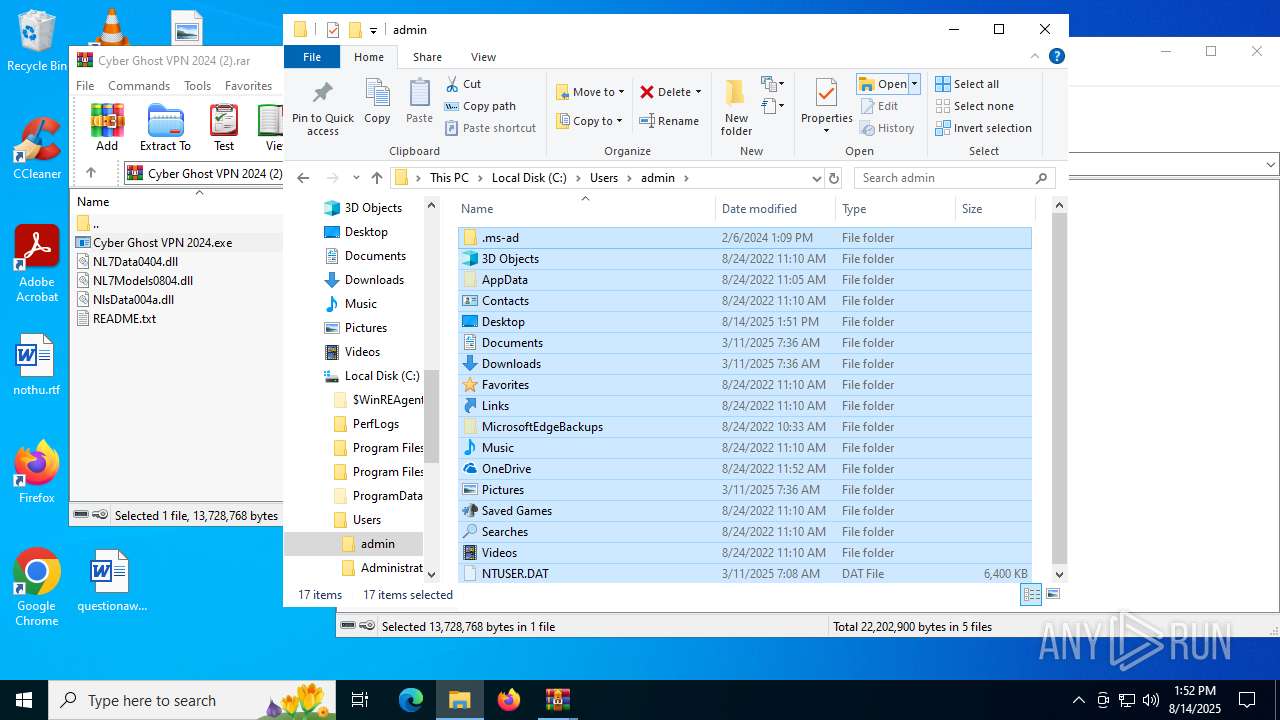
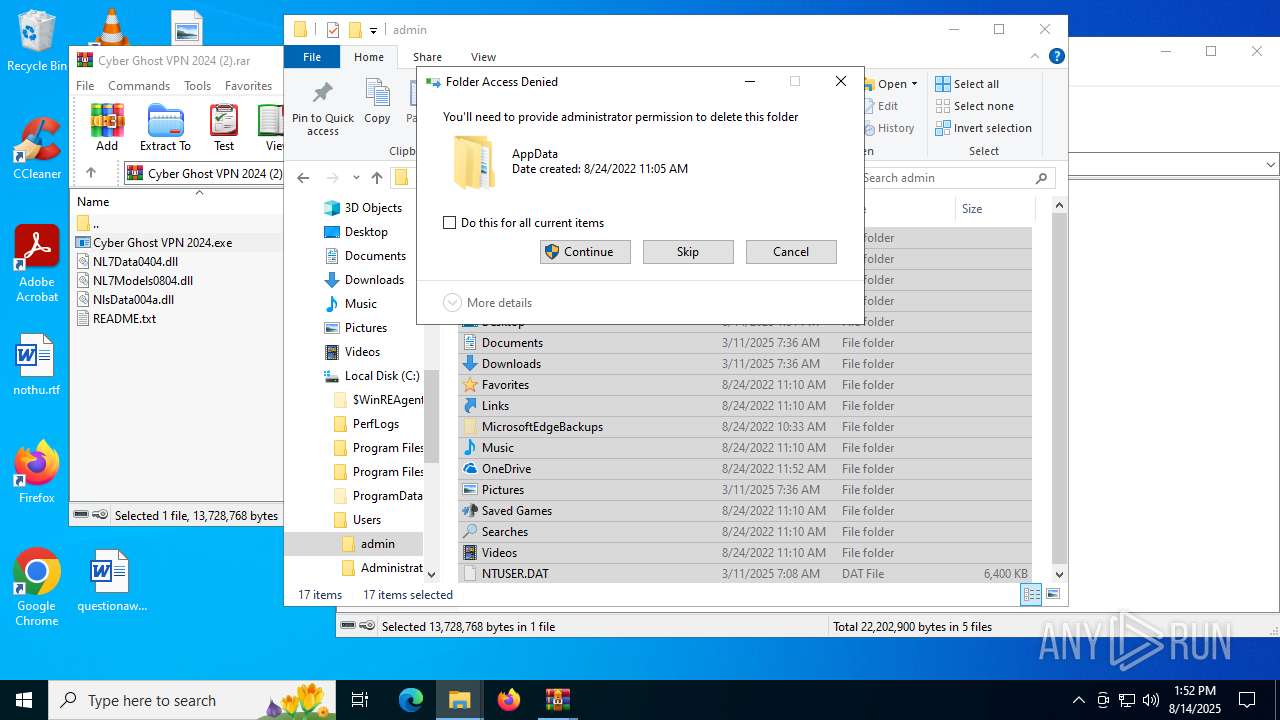
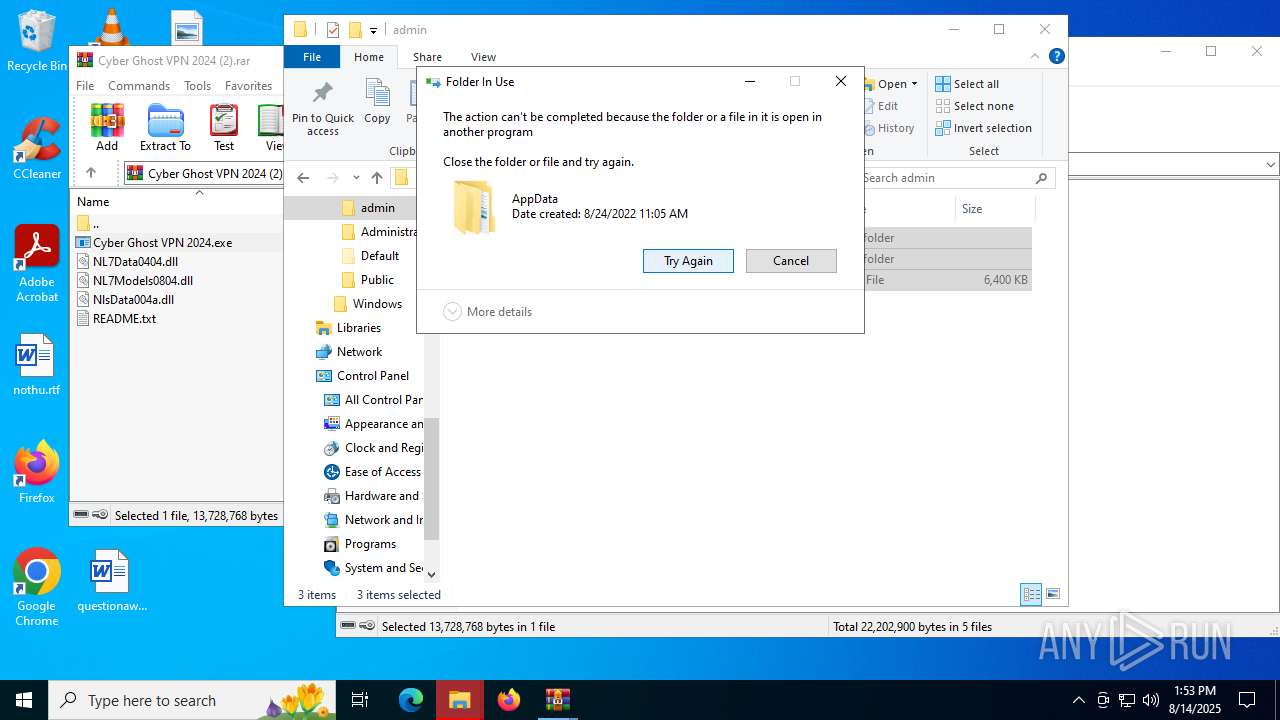
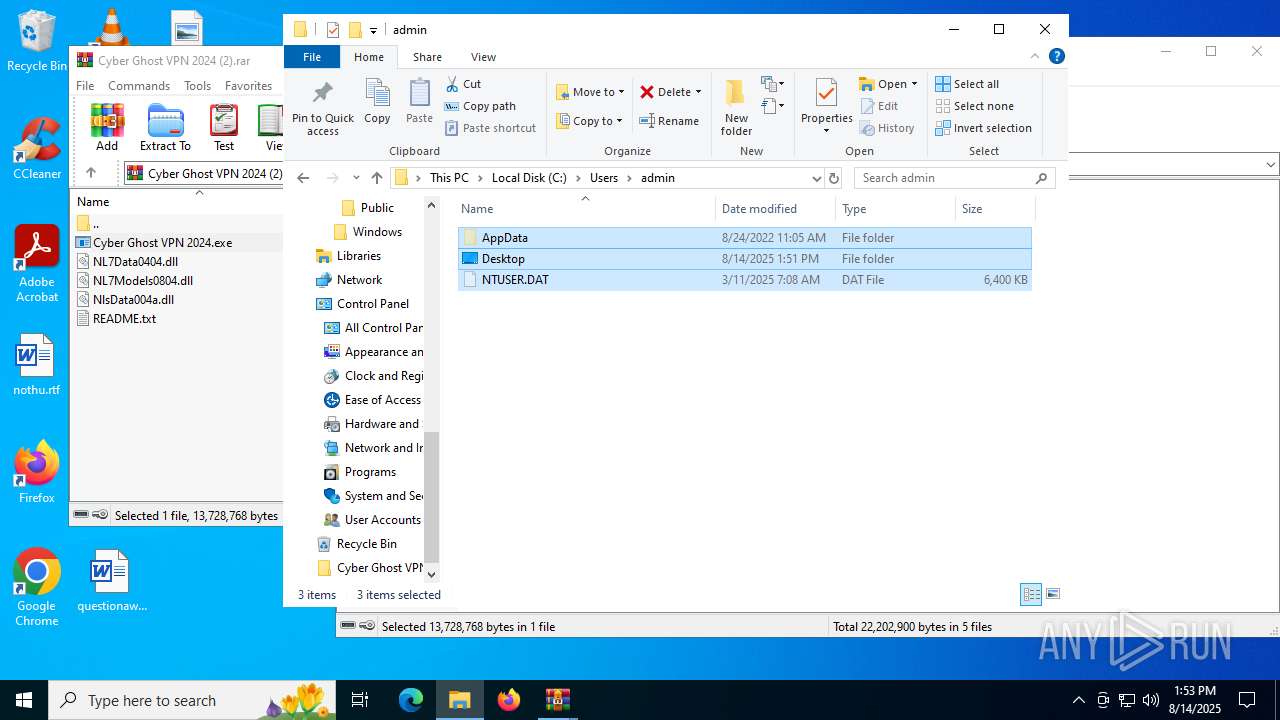
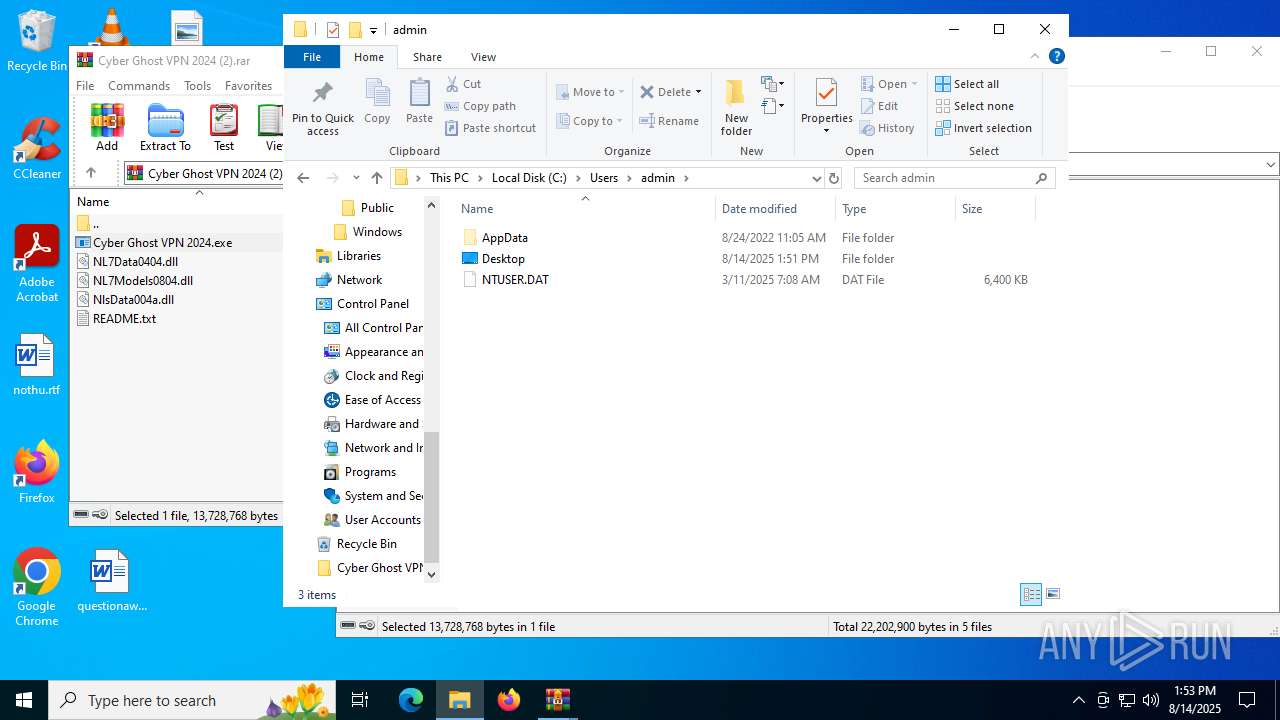
Creates files or folders in the user directory
- Cyber Ghost VPN 2024.exe (PID: 2324)
- ms_tool.exe (PID: 4788)
- WerFault.exe (PID: 4544)
- WerFault.exe (PID: 6348)
- WerFault.exe (PID: 1712)
- WerFault.exe (PID: 6768)
- WerFault.exe (PID: 2836)
- WerFault.exe (PID: 3860)
- WerFault.exe (PID: 2108)
- WerFault.exe (PID: 4808)
- WerFault.exe (PID: 5416)
- WerFault.exe (PID: 1964)
Checks supported languages
- Cyber Ghost VPN 2024.exe (PID: 2324)
- ms_tool.exe (PID: 4788)
- ms_updater.exe (PID: 4676)
- chcp.com (PID: 1180)
- Cyber Ghost VPN 2024.exe (PID: 6720)
- ms_updater.exe (PID: 4116)
- Cyber Ghost VPN 2024.exe (PID: 984)
- ms_updater.exe (PID: 436)
- chcp.com (PID: 2696)
- chcp.com (PID: 864)
- ms_updater.exe (PID: 6408)
- chcp.com (PID: 1636)
- ms_updater.exe (PID: 1028)
- chcp.com (PID: 1180)
- ms_updater.exe (PID: 4664)
- chcp.com (PID: 3392)
- ms_updater.exe (PID: 4112)
- chcp.com (PID: 3896)
- chcp.com (PID: 5600)
- ms_updater.exe (PID: 5504)
- ms_updater.exe (PID: 700)
- chcp.com (PID: 3860)
- ms_updater.exe (PID: 6756)
- chcp.com (PID: 4080)
- Cyber Ghost VPN 2024.exe (PID: 4984)
- Cyber Ghost VPN 2024.exe (PID: 5616)
- Cyber Ghost VPN 2024.exe (PID: 544)
- Cyber Ghost VPN 2024.exe (PID: 4084)
- Cyber Ghost VPN 2024.exe (PID: 5252)
- Cyber Ghost VPN 2024.exe (PID: 4684)
- Cyber Ghost VPN 2024.exe (PID: 2168)
- Cyber Ghost VPN 2024.exe (PID: 2996)
- Cyber Ghost VPN 2024.exe (PID: 1740)
- Cyber Ghost VPN 2024.exe (PID: 6104)
- Cyber Ghost VPN 2024.exe (PID: 1044)
- Cyber Ghost VPN 2024.exe (PID: 5652)
- Cyber Ghost VPN 2024.exe (PID: 2096)
- Cyber Ghost VPN 2024.exe (PID: 6216)
- SearchApp.exe (PID: 4824)
Reads the computer name
- Cyber Ghost VPN 2024.exe (PID: 2324)
- ms_updater.exe (PID: 4676)
- ms_tool.exe (PID: 4788)
- ms_updater.exe (PID: 4116)
- ms_updater.exe (PID: 436)
- ms_updater.exe (PID: 6408)
- ms_updater.exe (PID: 1028)
- ms_updater.exe (PID: 4664)
- ms_updater.exe (PID: 4112)
- ms_updater.exe (PID: 5504)
- ms_updater.exe (PID: 700)
- ms_updater.exe (PID: 6756)
- SearchApp.exe (PID: 4824)
Process checks computer location settings
- Cyber Ghost VPN 2024.exe (PID: 2324)
- ms_updater.exe (PID: 4676)
- ms_updater.exe (PID: 4116)
- ms_updater.exe (PID: 436)
- ms_updater.exe (PID: 6408)
- ms_updater.exe (PID: 1028)
- ms_updater.exe (PID: 4664)
- ms_updater.exe (PID: 4112)
- ms_updater.exe (PID: 5504)
- ms_updater.exe (PID: 700)
- ms_updater.exe (PID: 6756)
- SearchApp.exe (PID: 4824)
Launching a file from the Startup directory
- ms_tool.exe (PID: 4788)
Reads the machine GUID from the registry
- ms_updater.exe (PID: 4676)
- ms_updater.exe (PID: 4116)
- ms_updater.exe (PID: 436)
- ms_updater.exe (PID: 6408)
- ms_updater.exe (PID: 1028)
- ms_updater.exe (PID: 4664)
- ms_updater.exe (PID: 4112)
- ms_updater.exe (PID: 5504)
- ms_updater.exe (PID: 700)
- ms_updater.exe (PID: 6756)
- SearchApp.exe (PID: 4824)
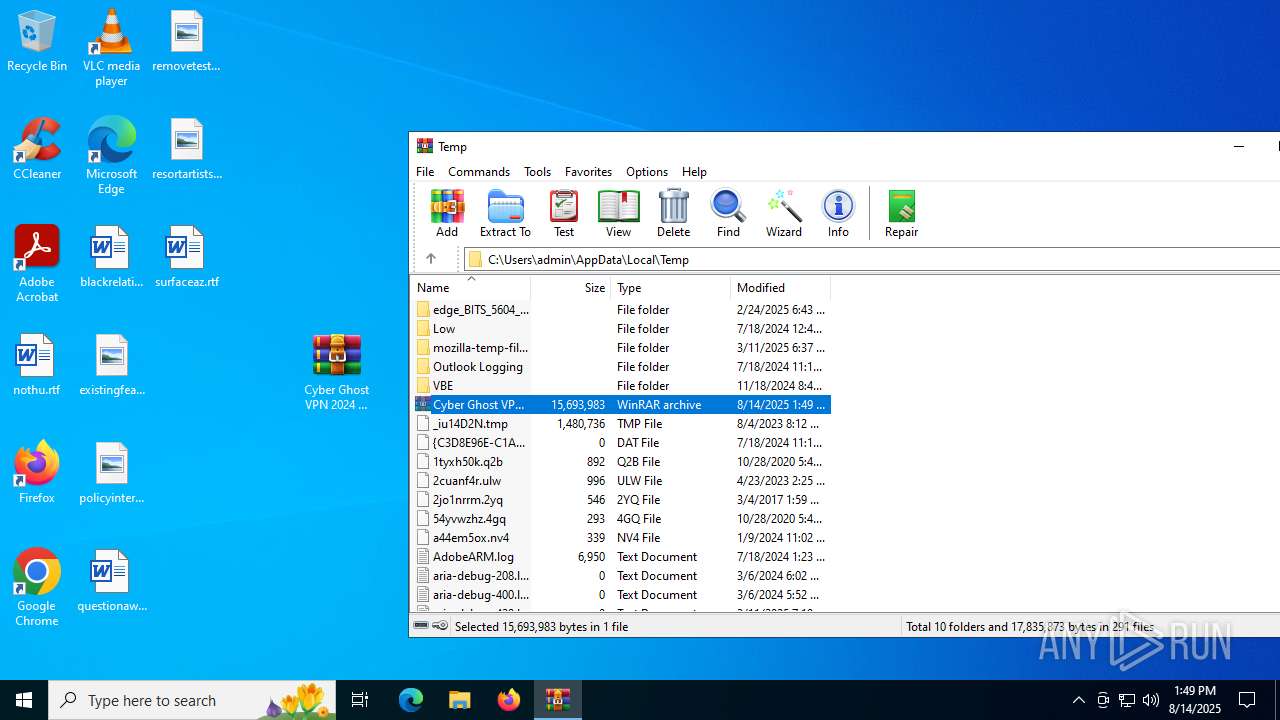
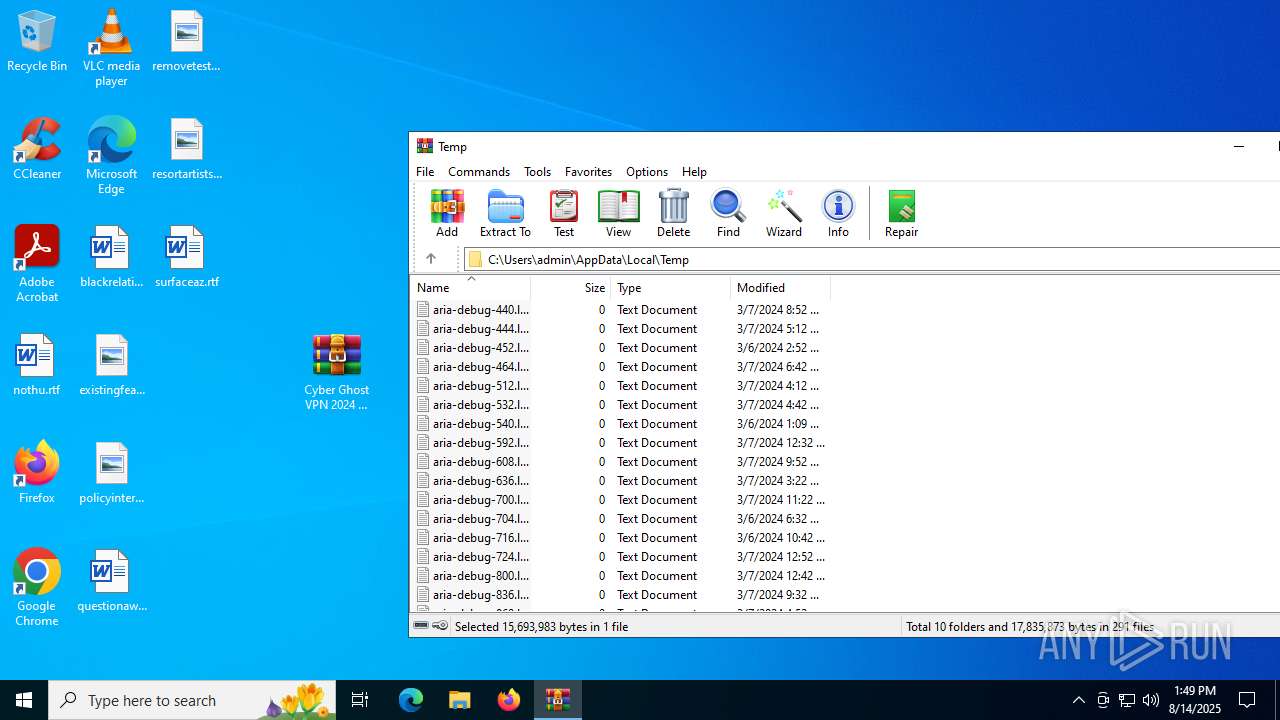
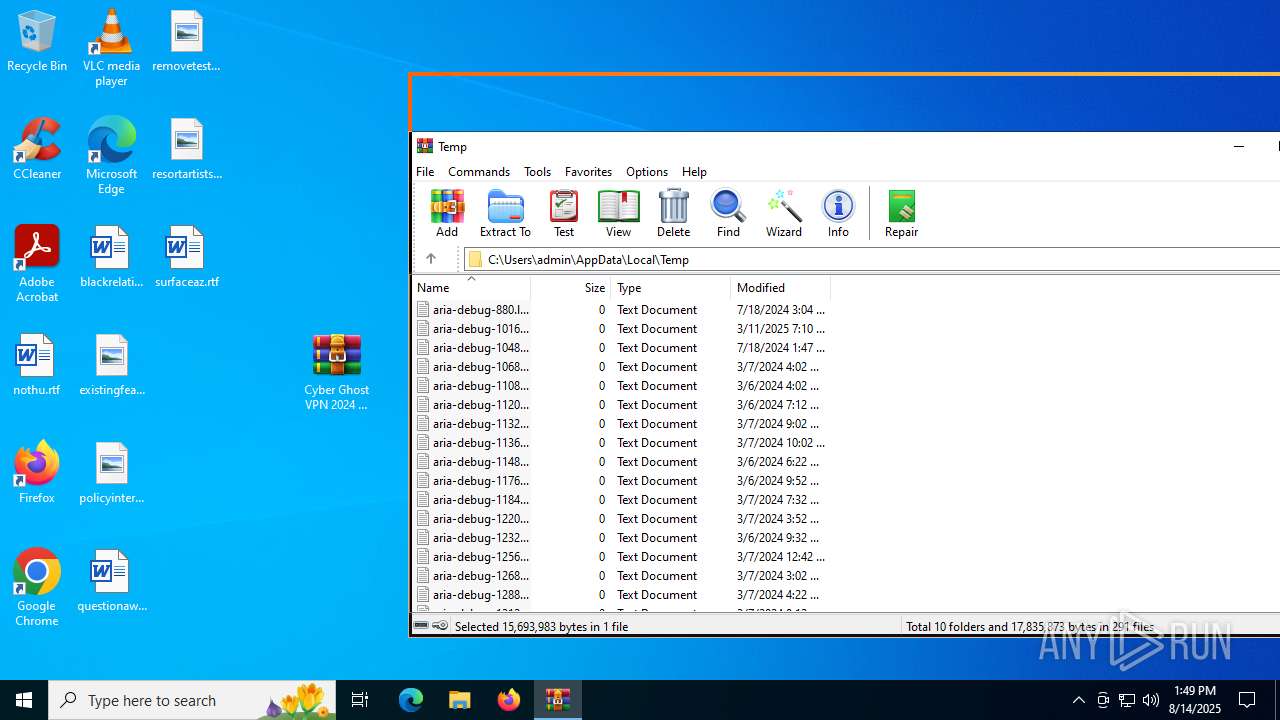
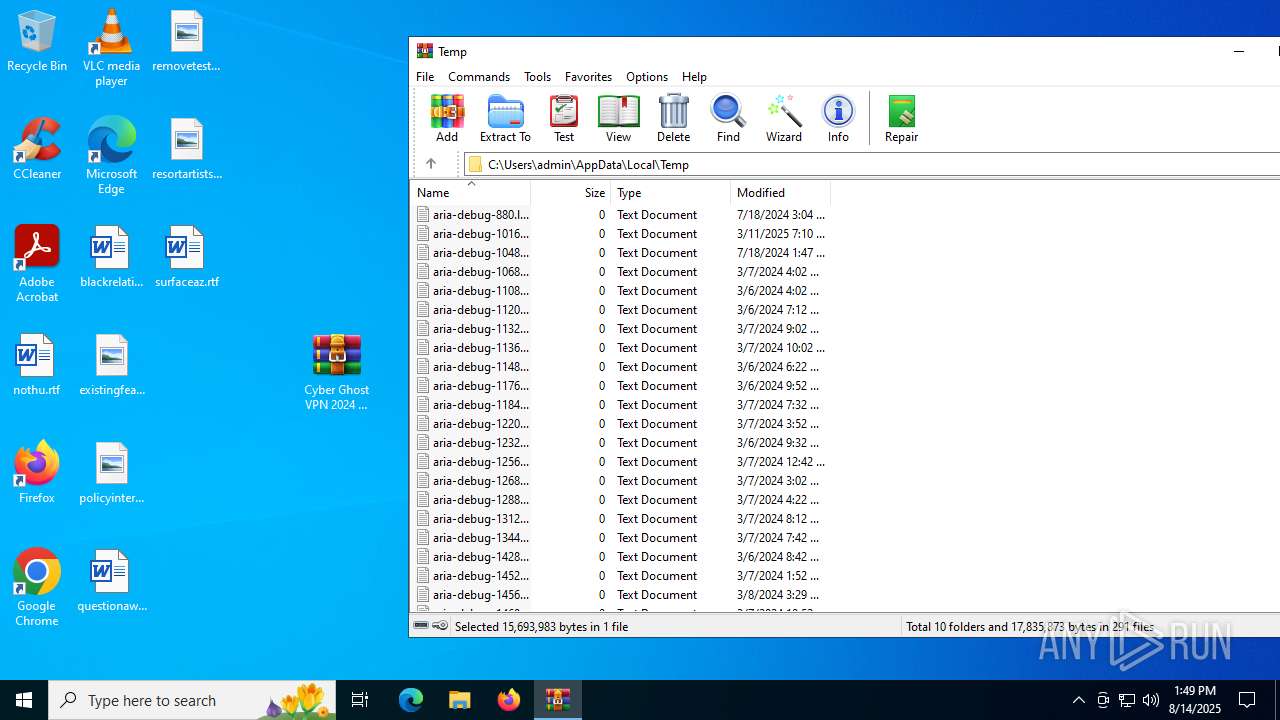
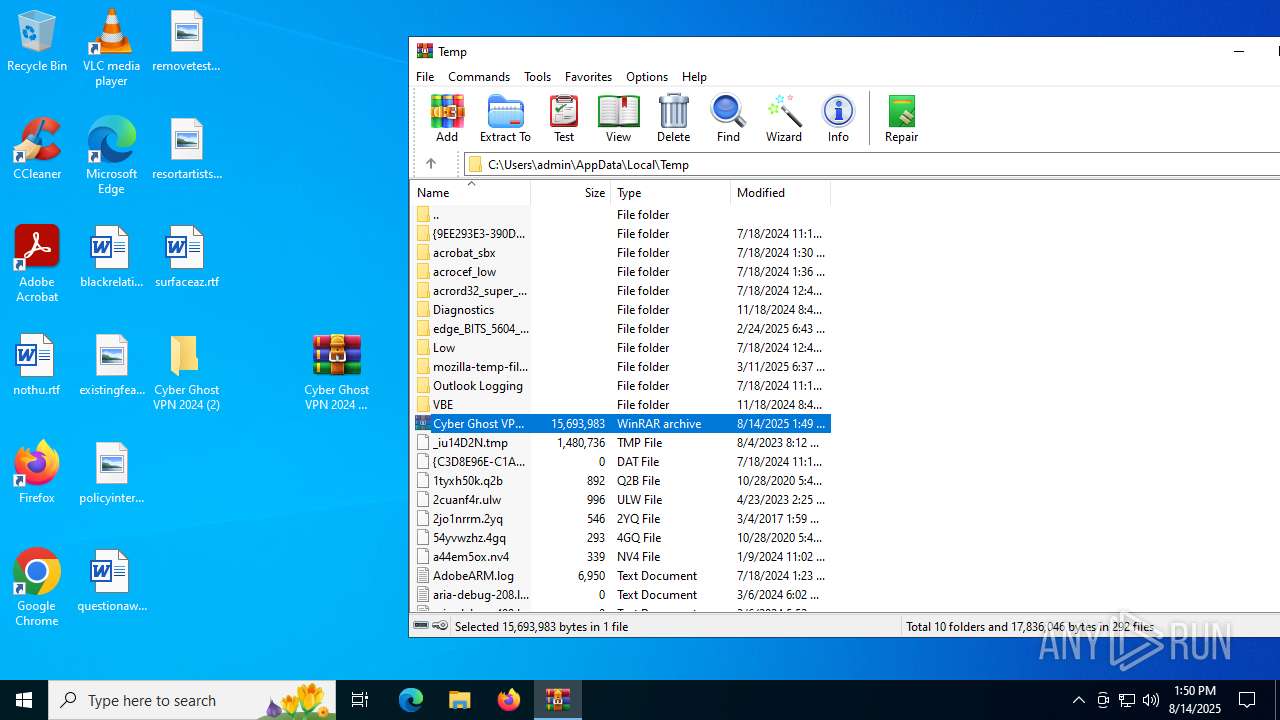
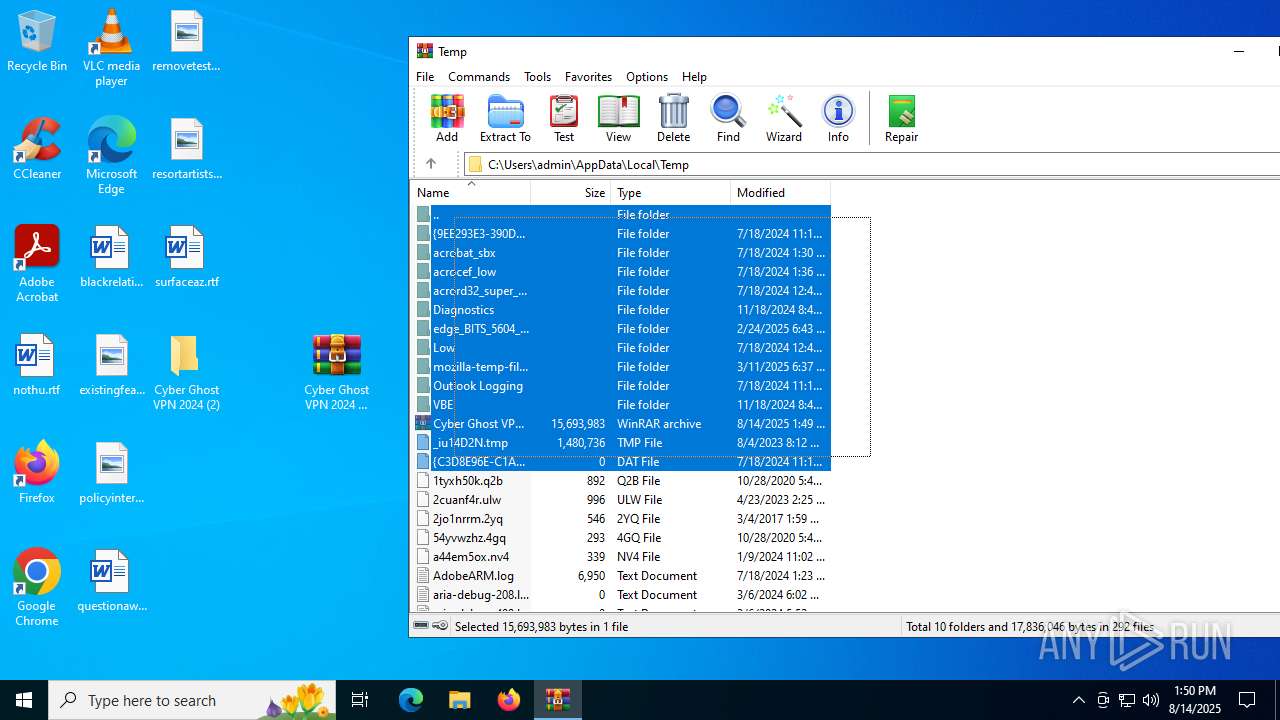
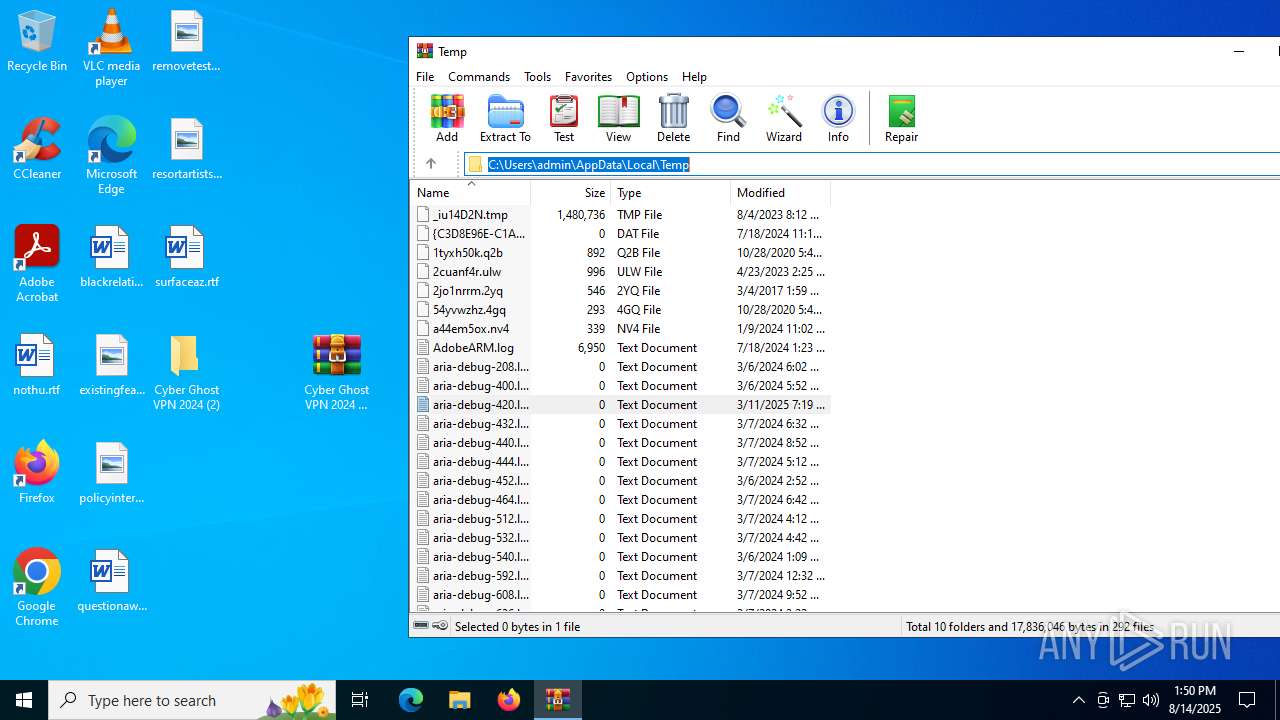
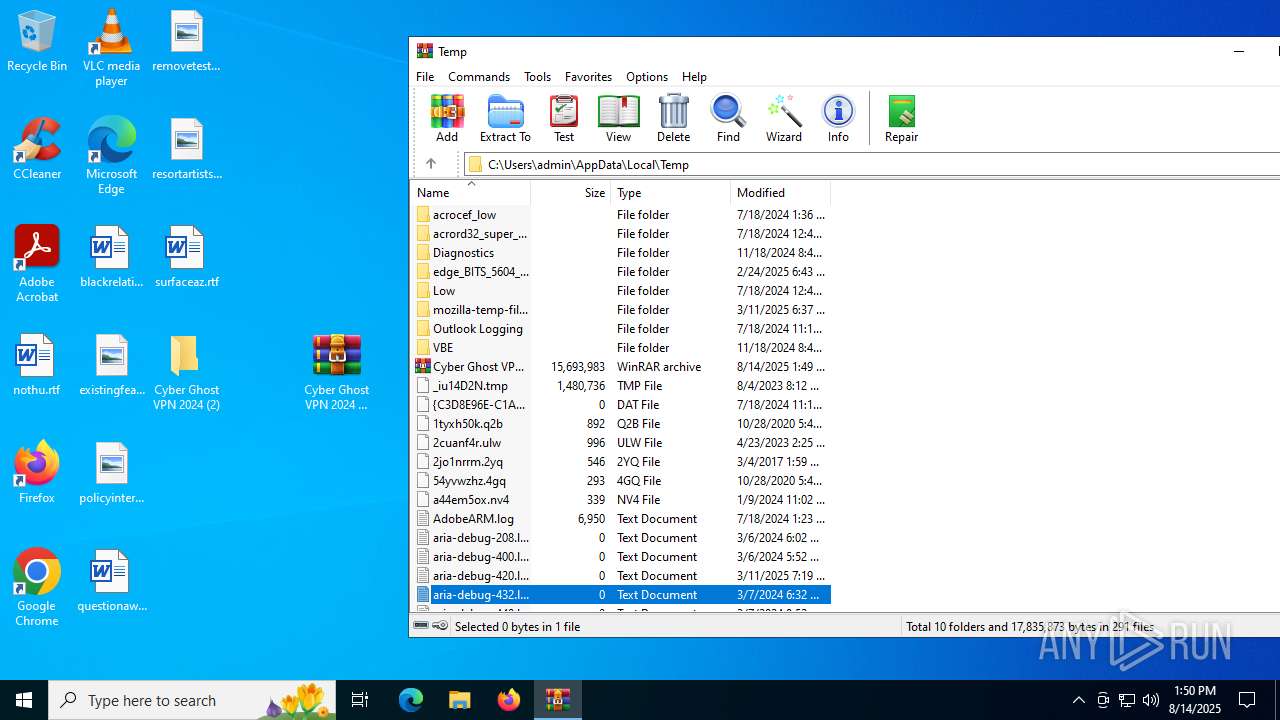
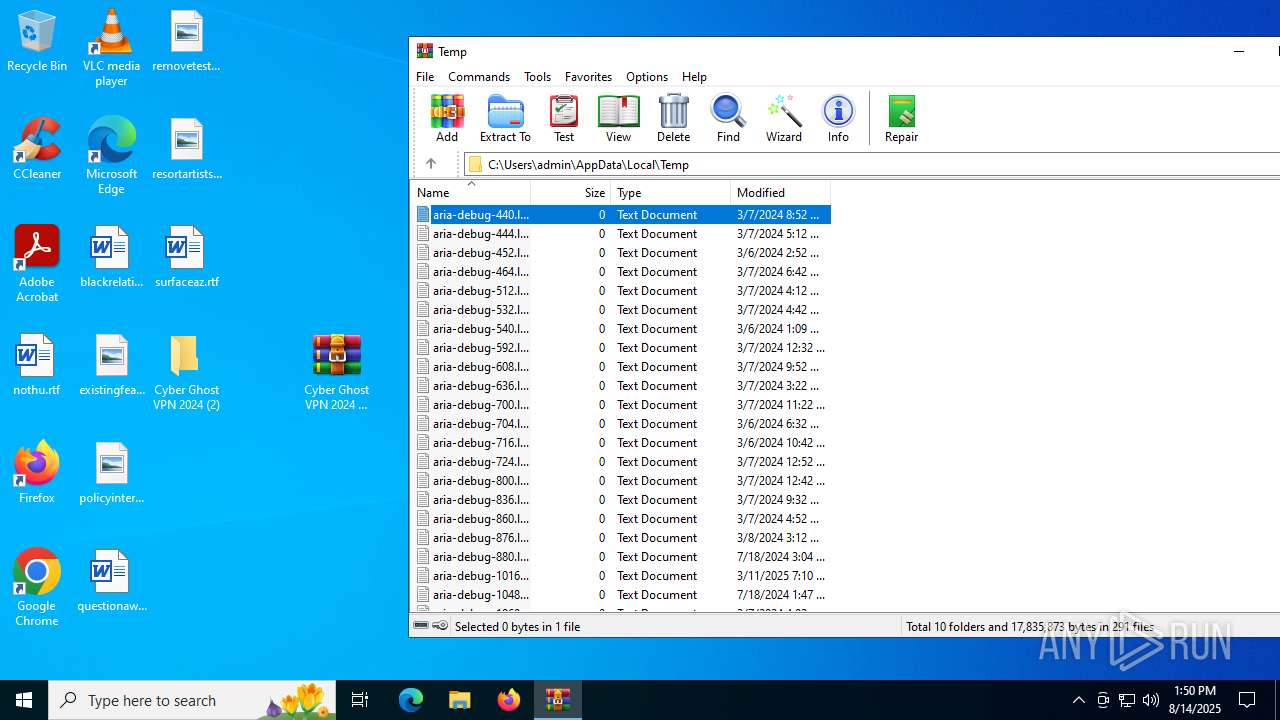
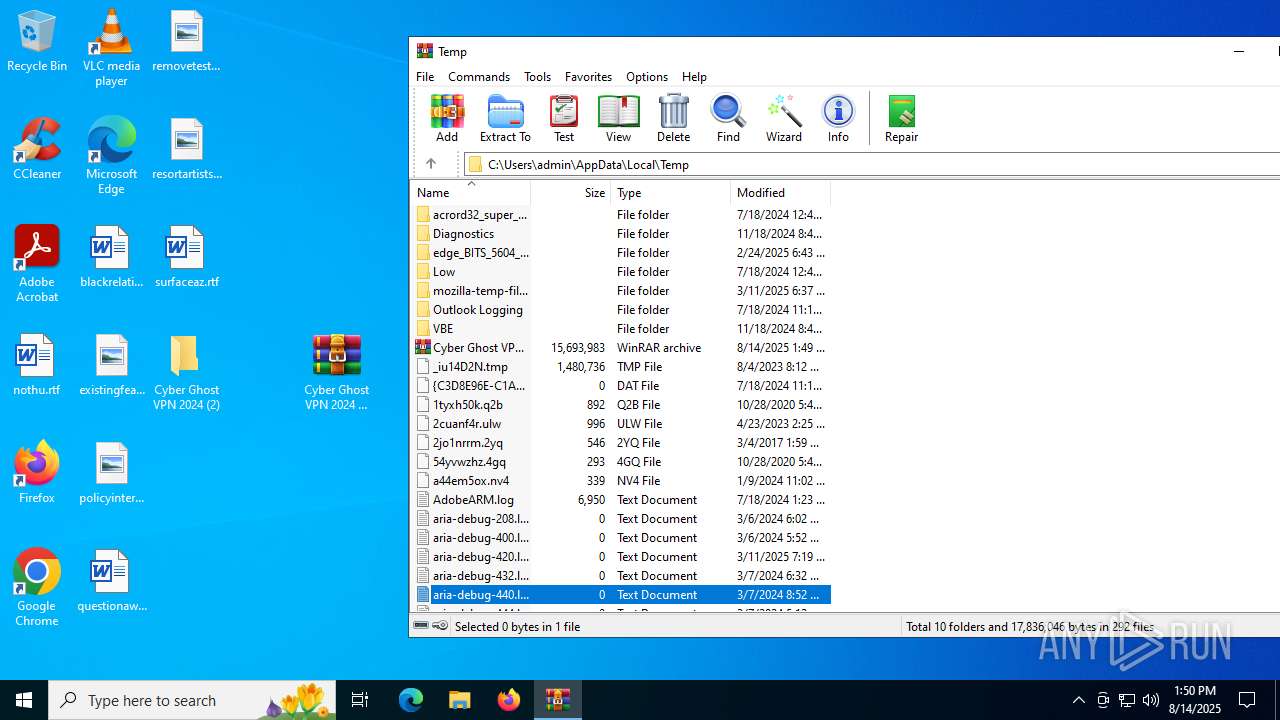
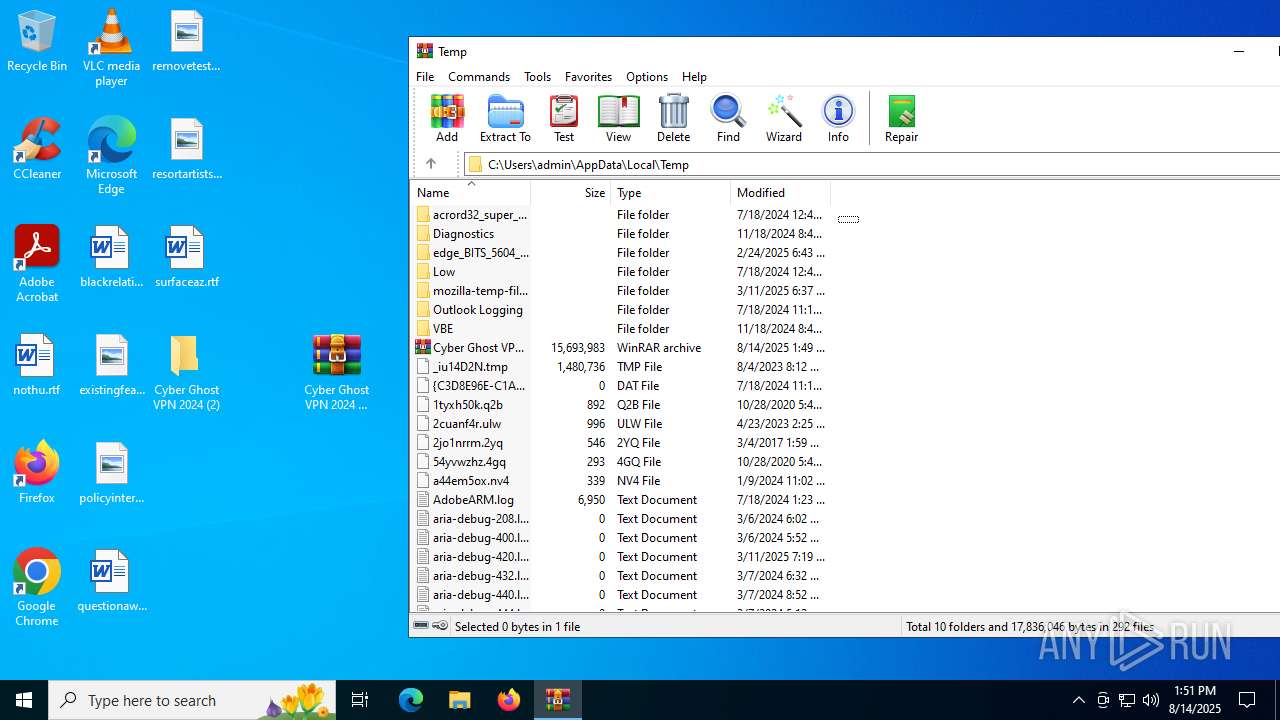
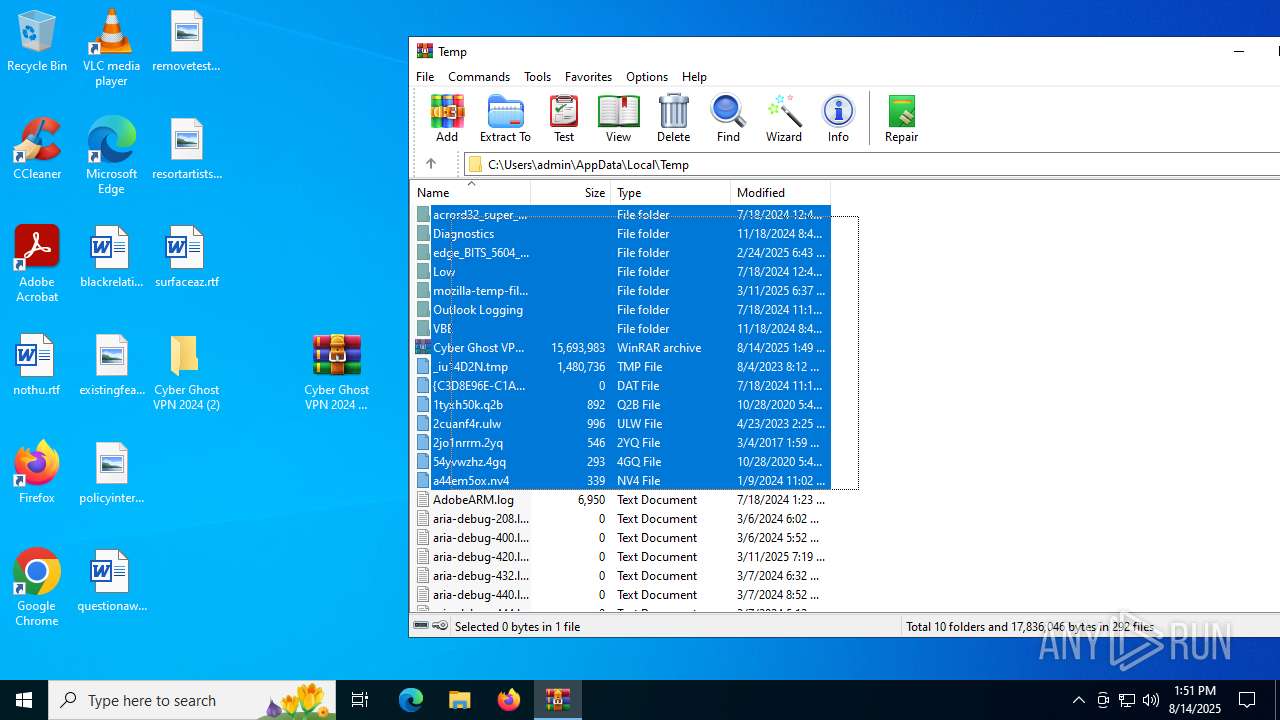
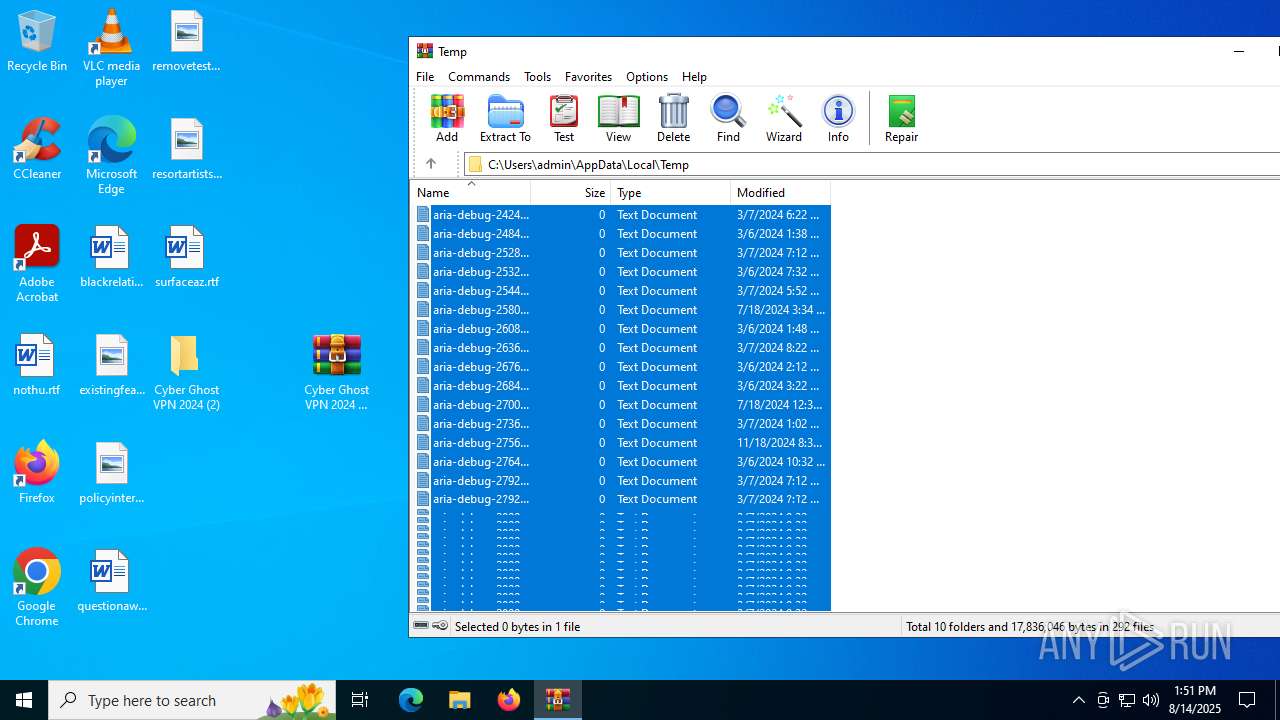
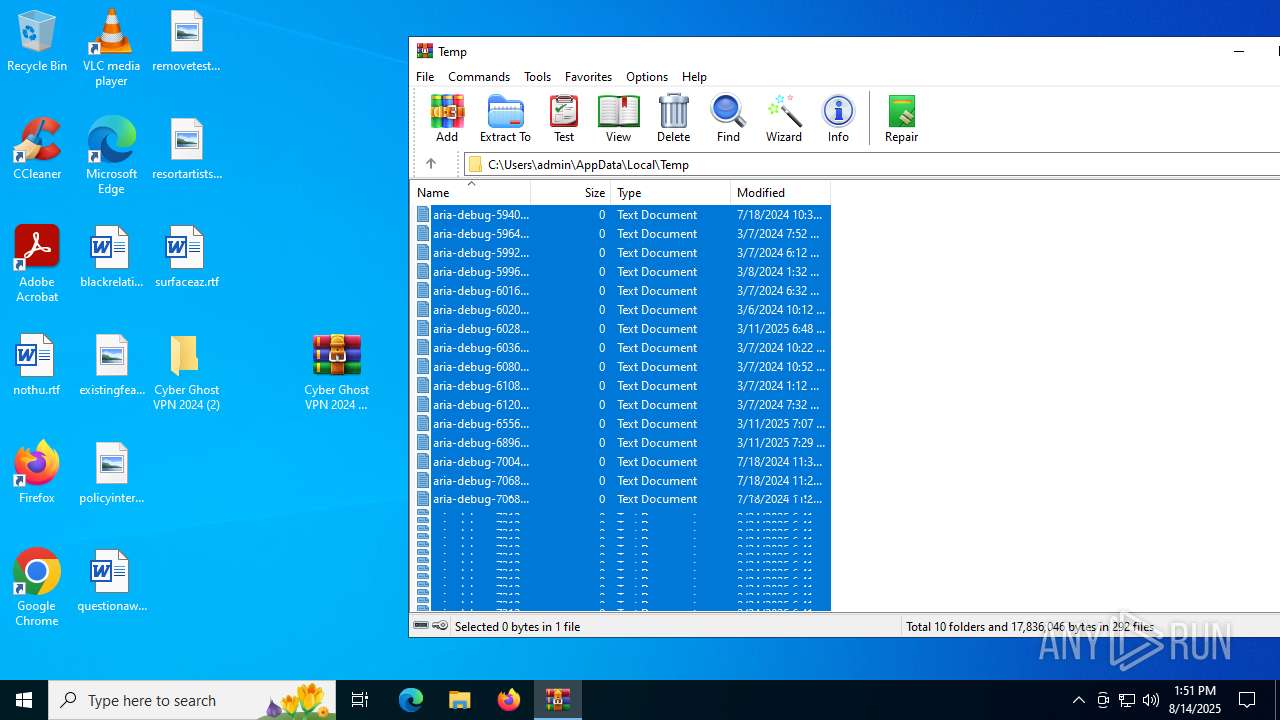
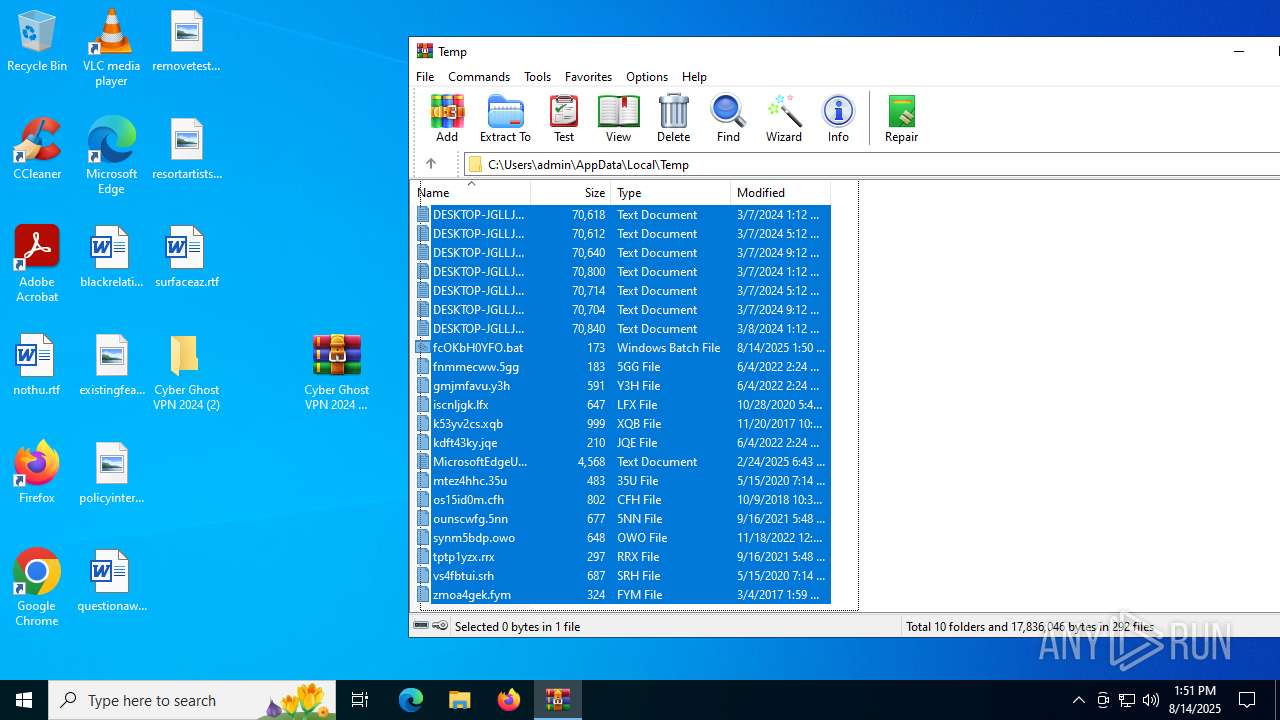
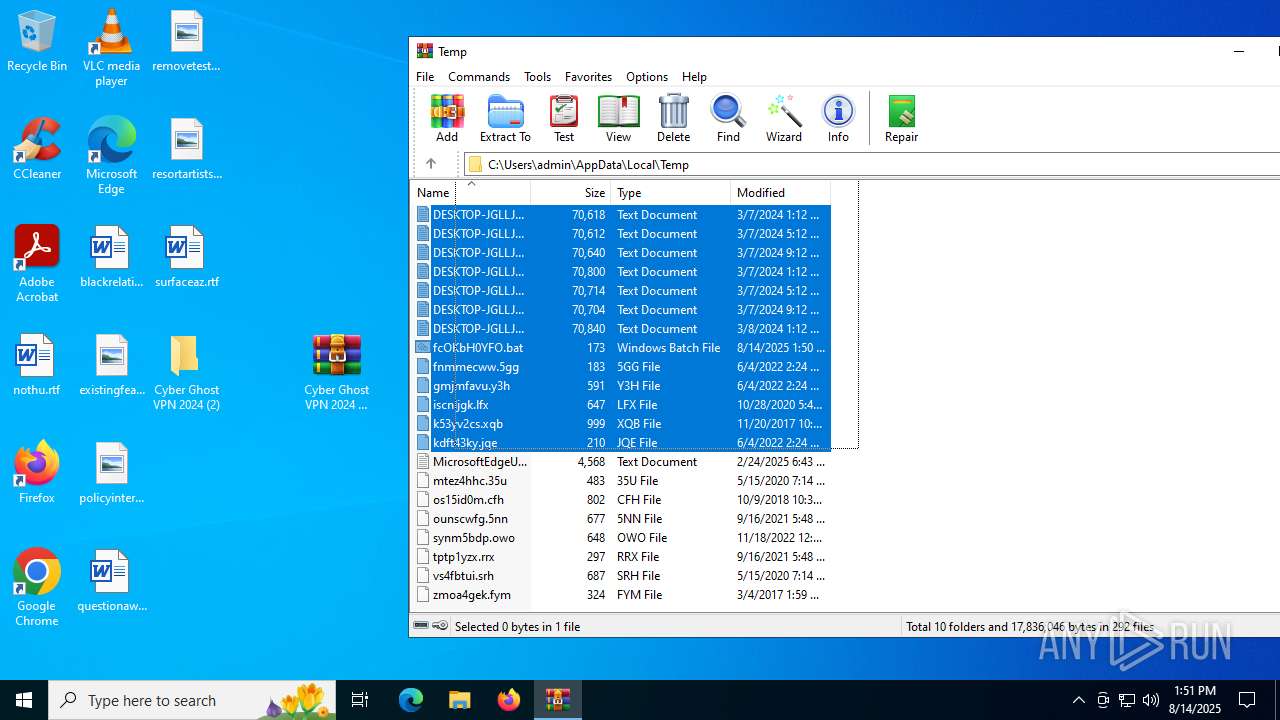
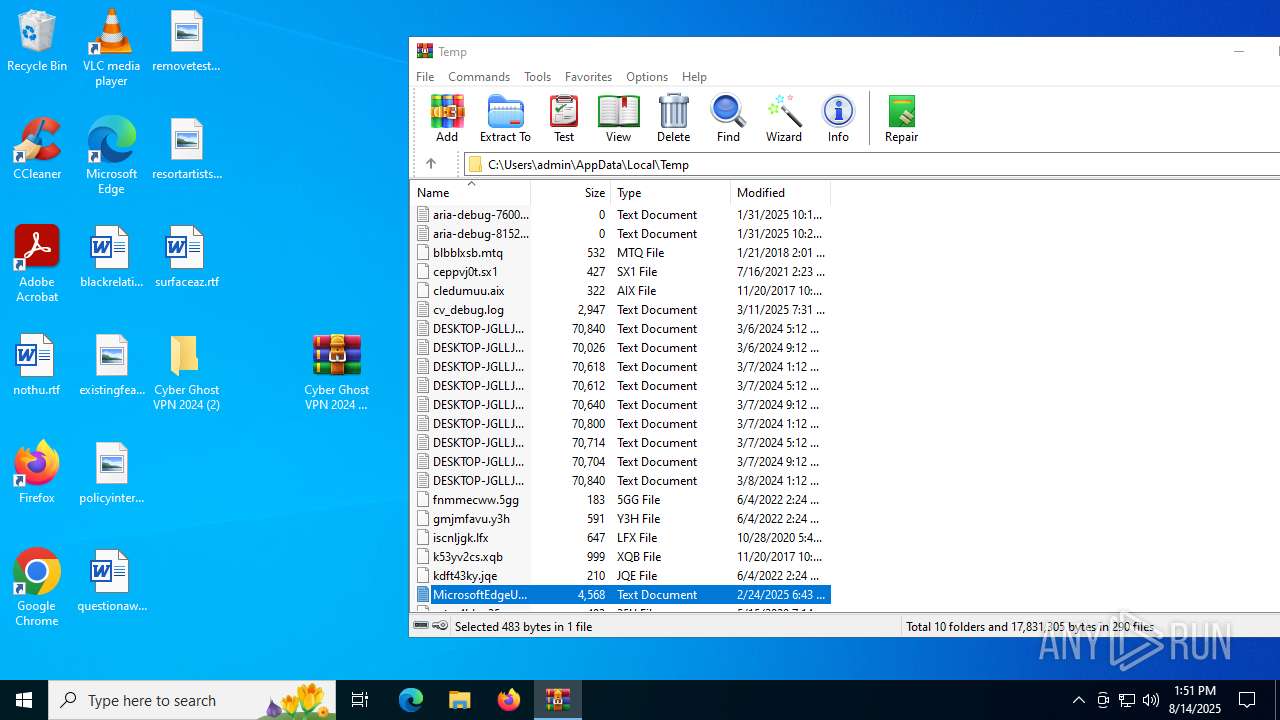
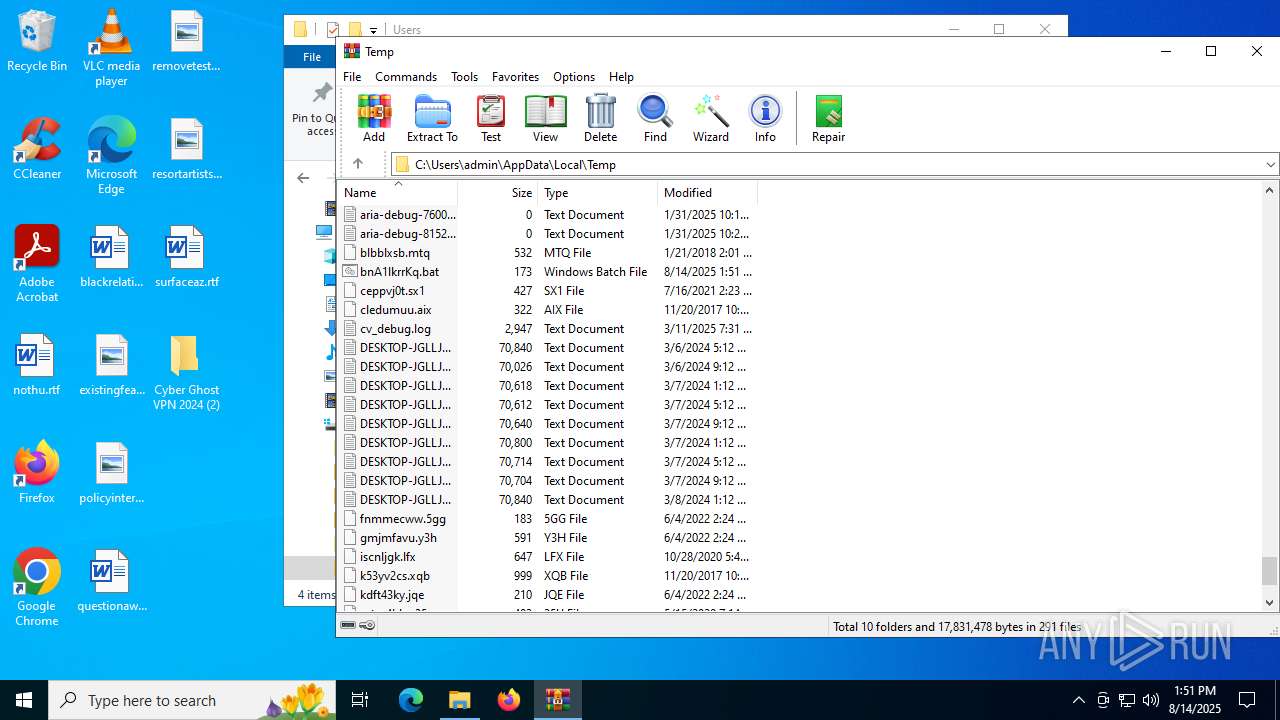
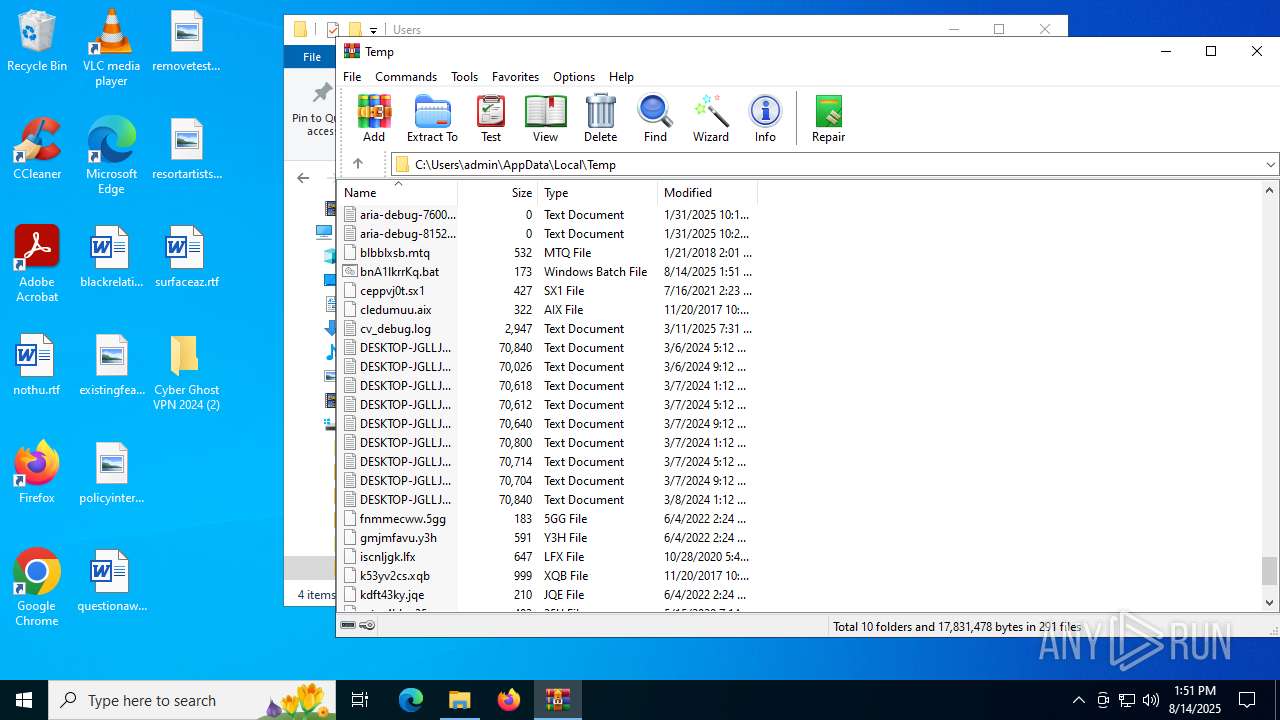
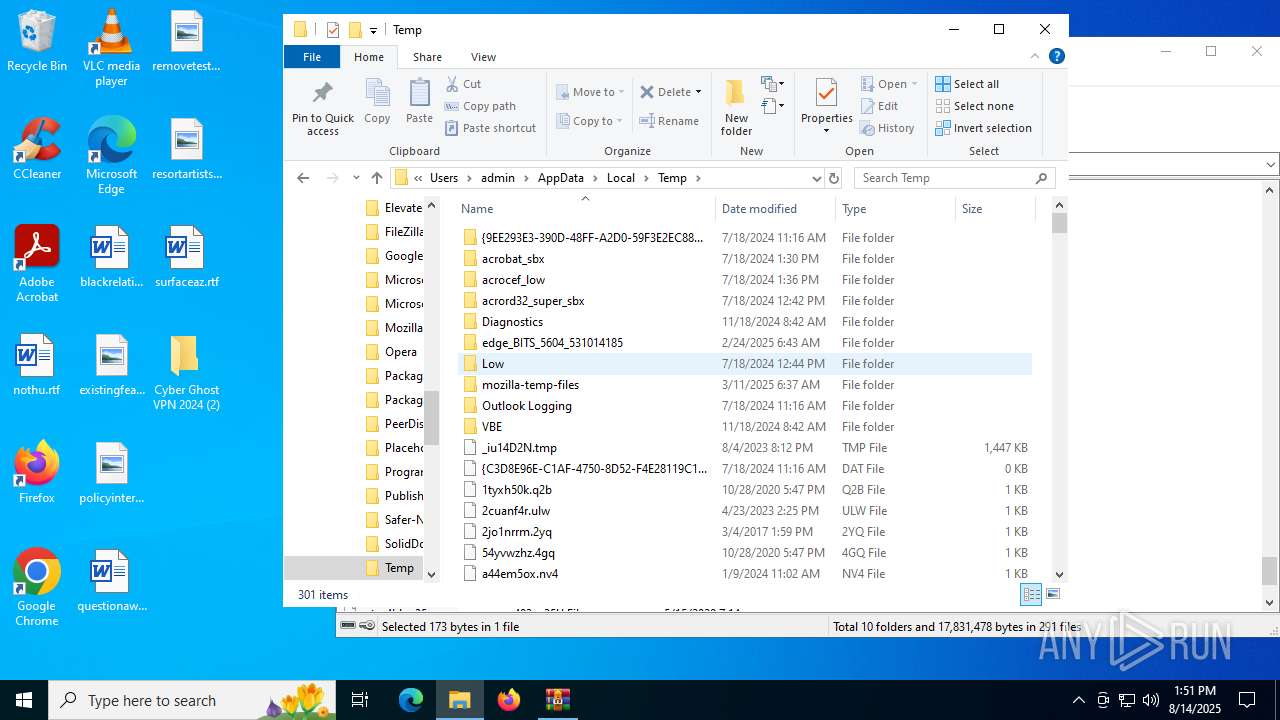
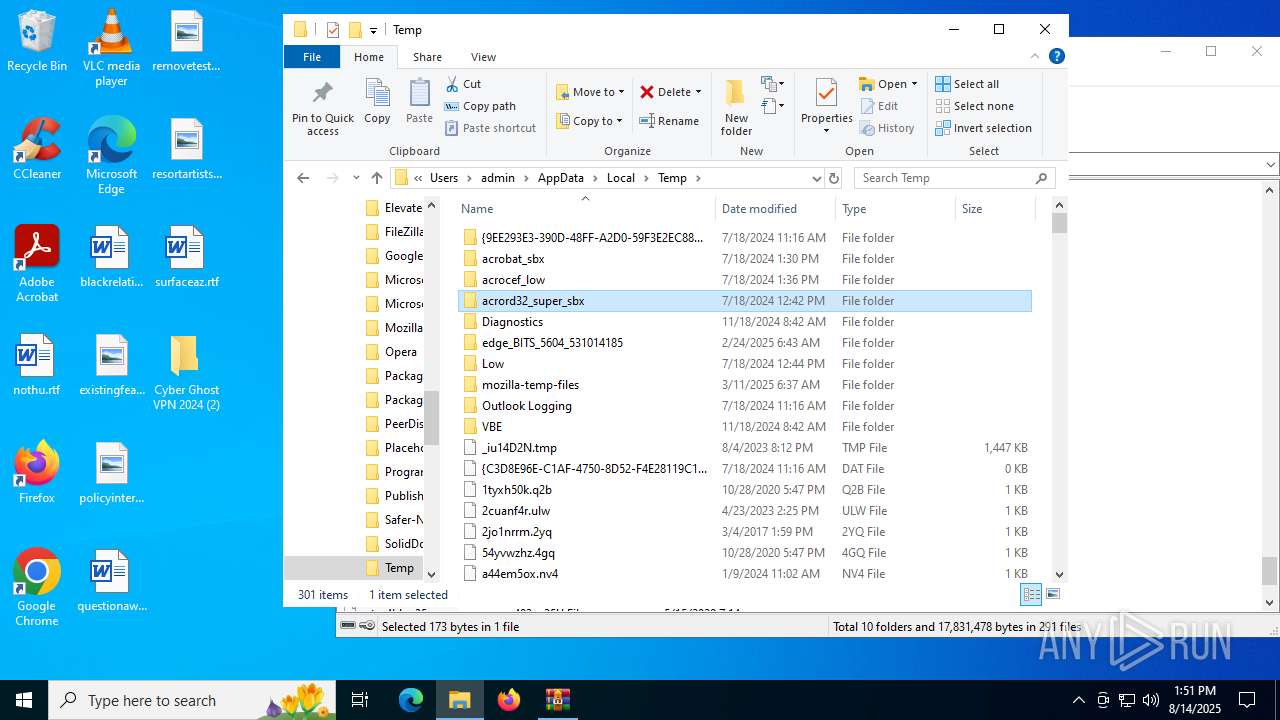
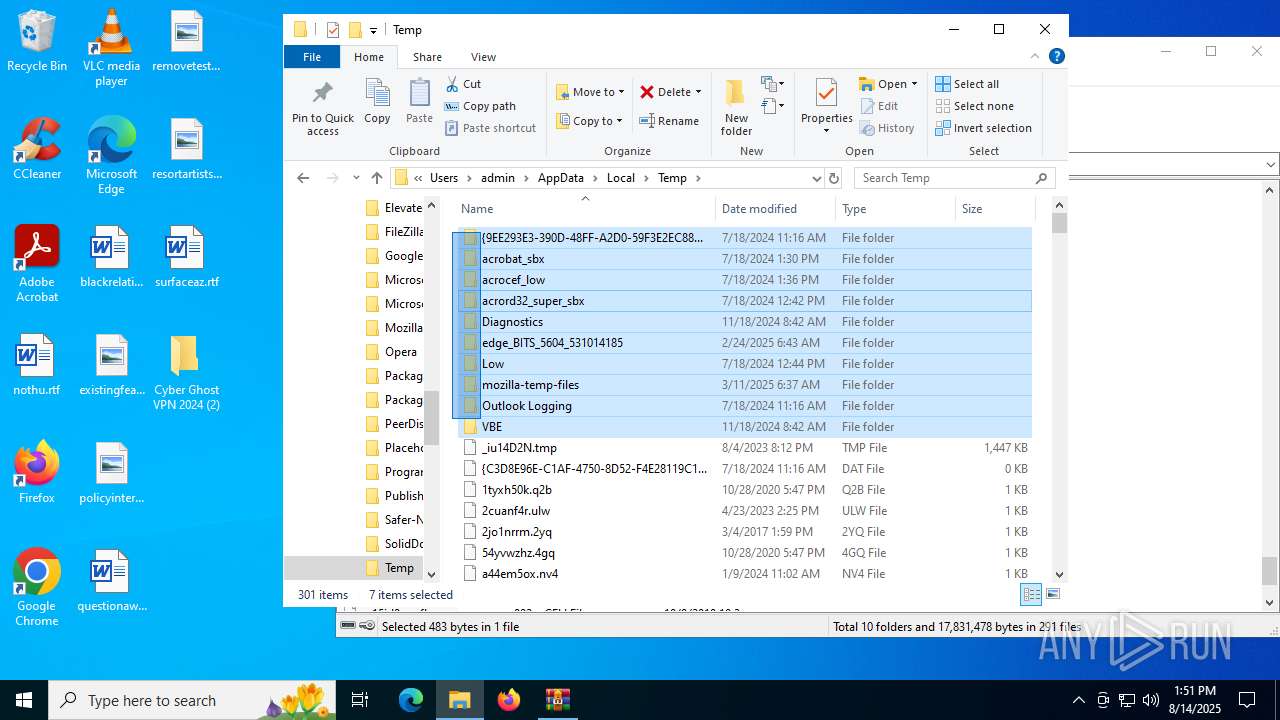
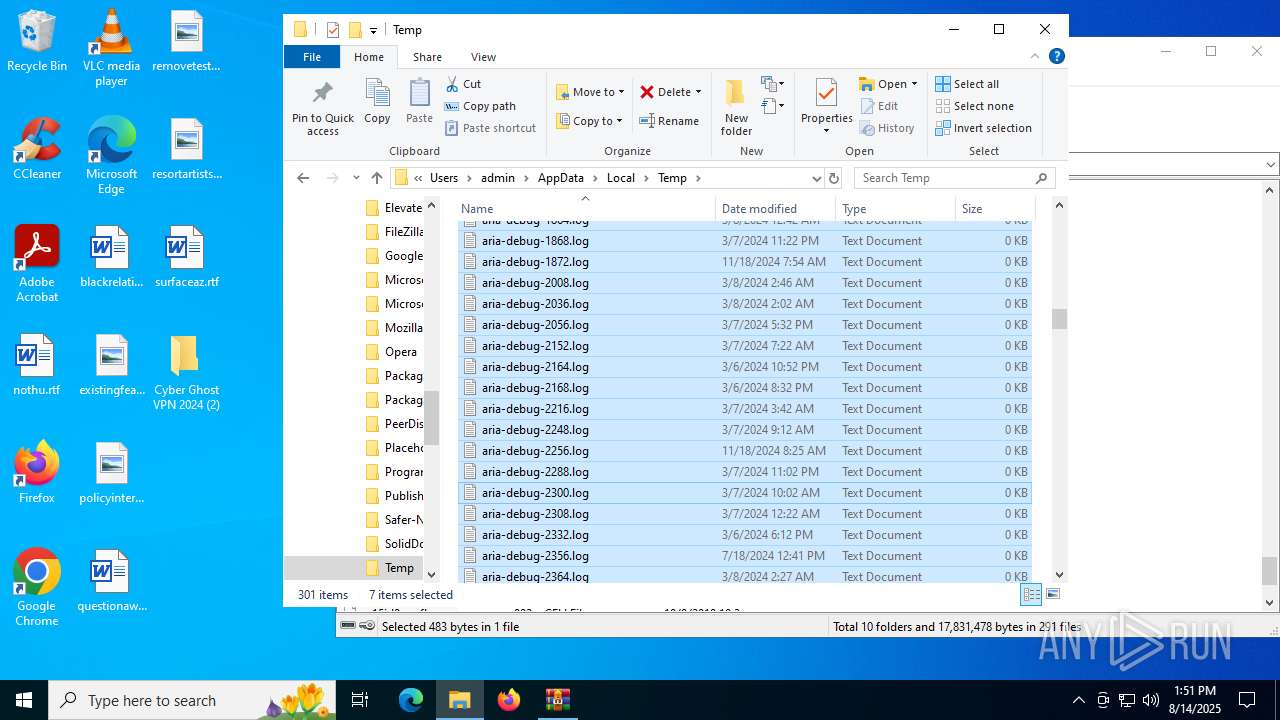
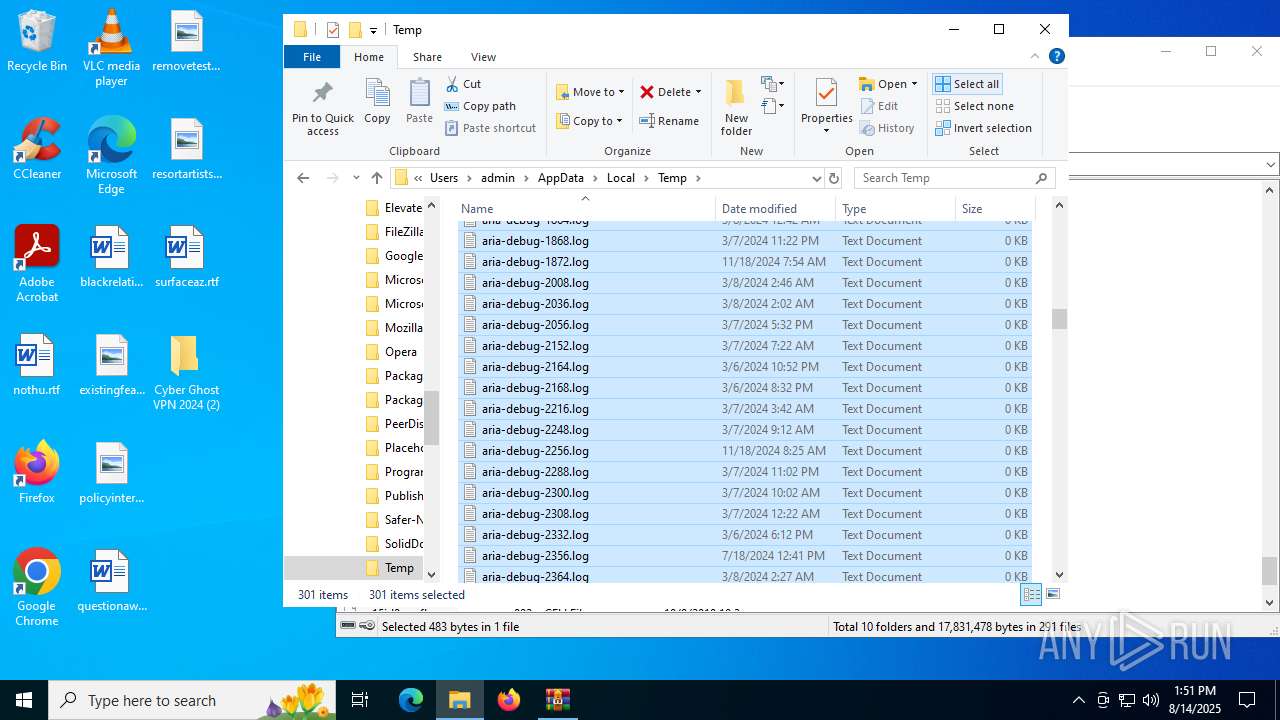
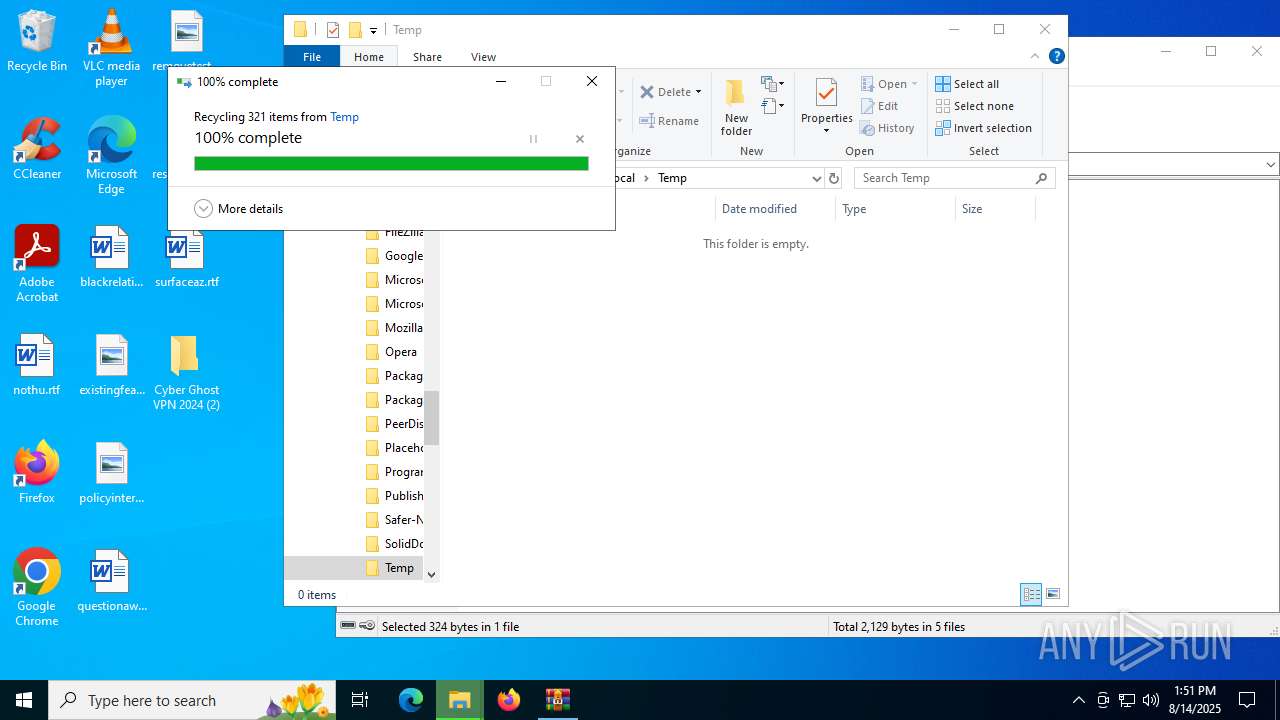
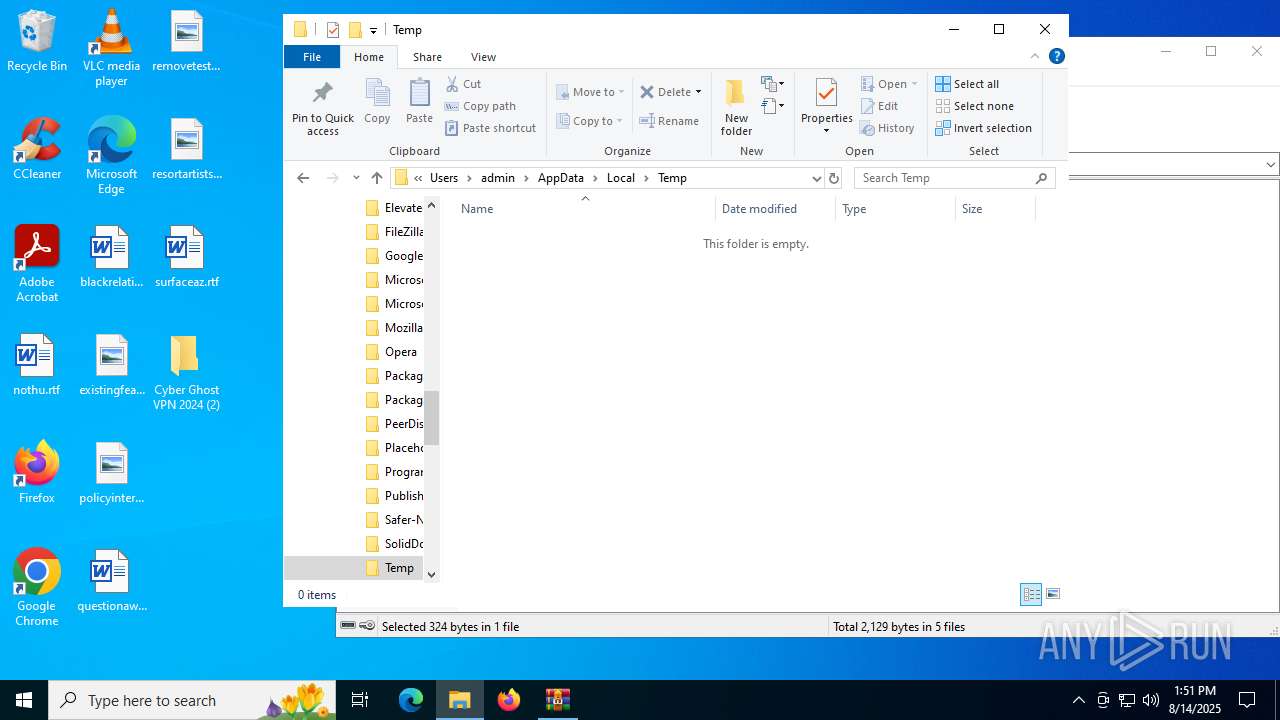
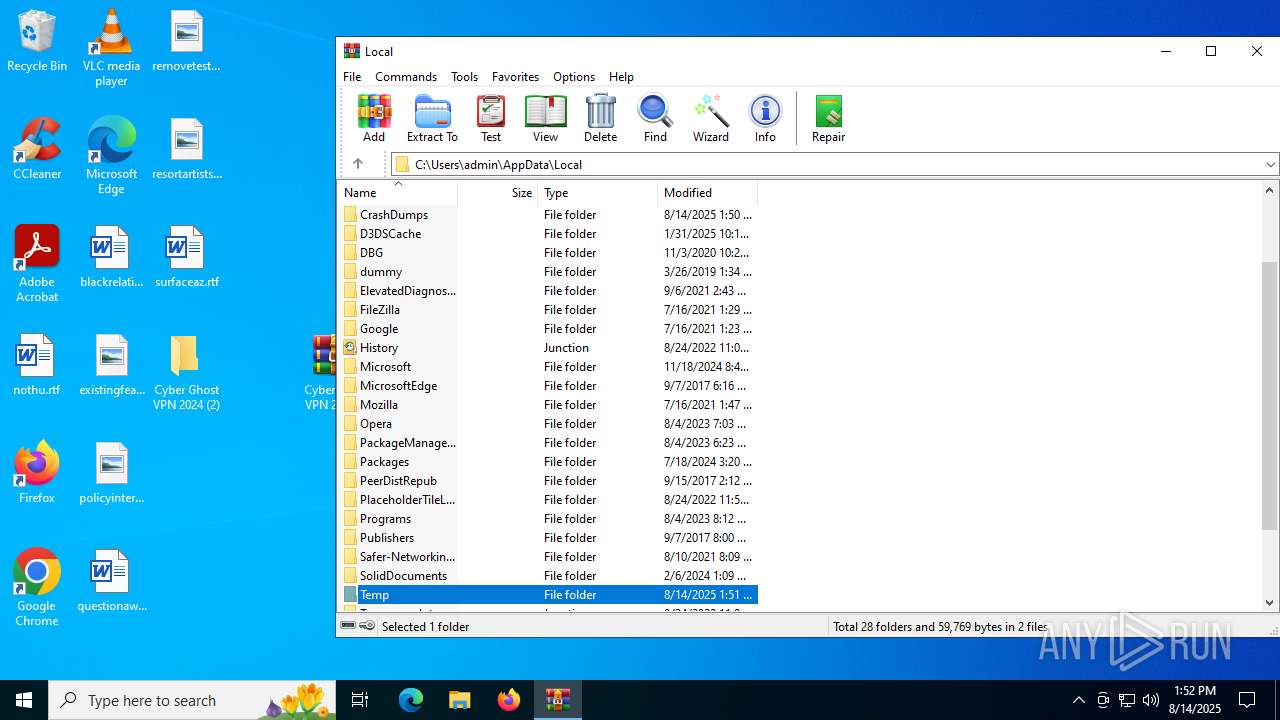
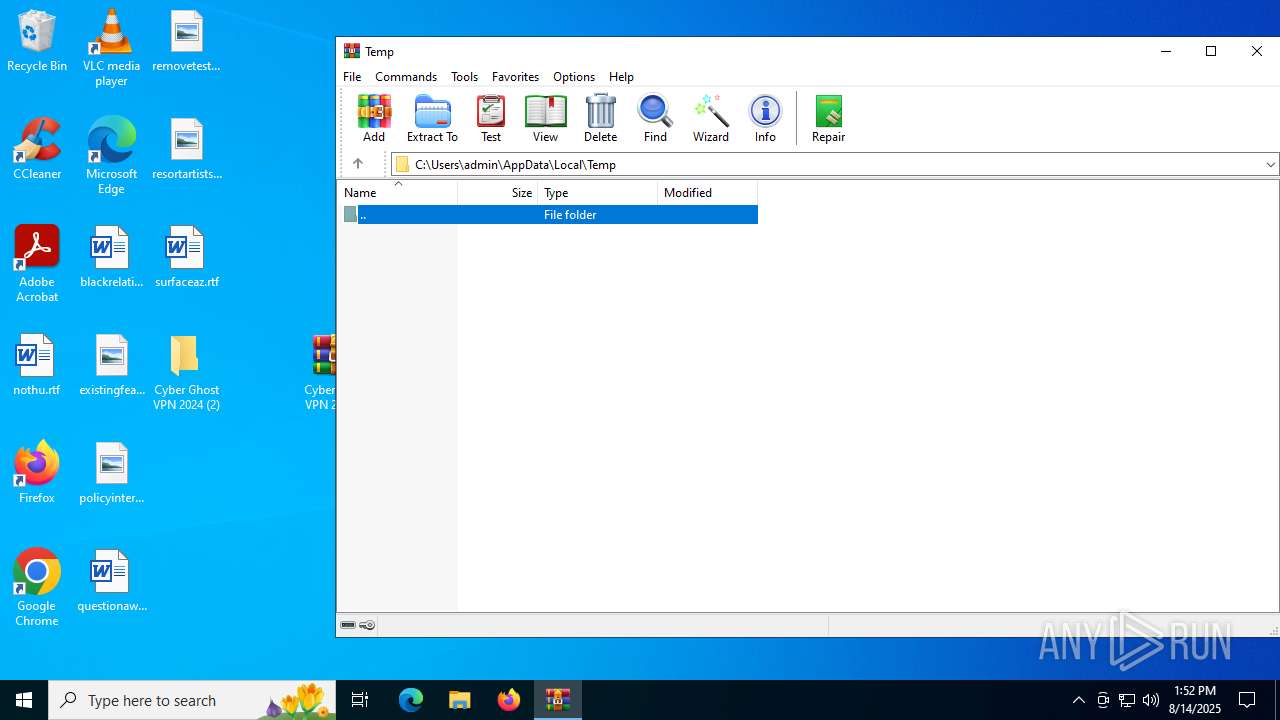
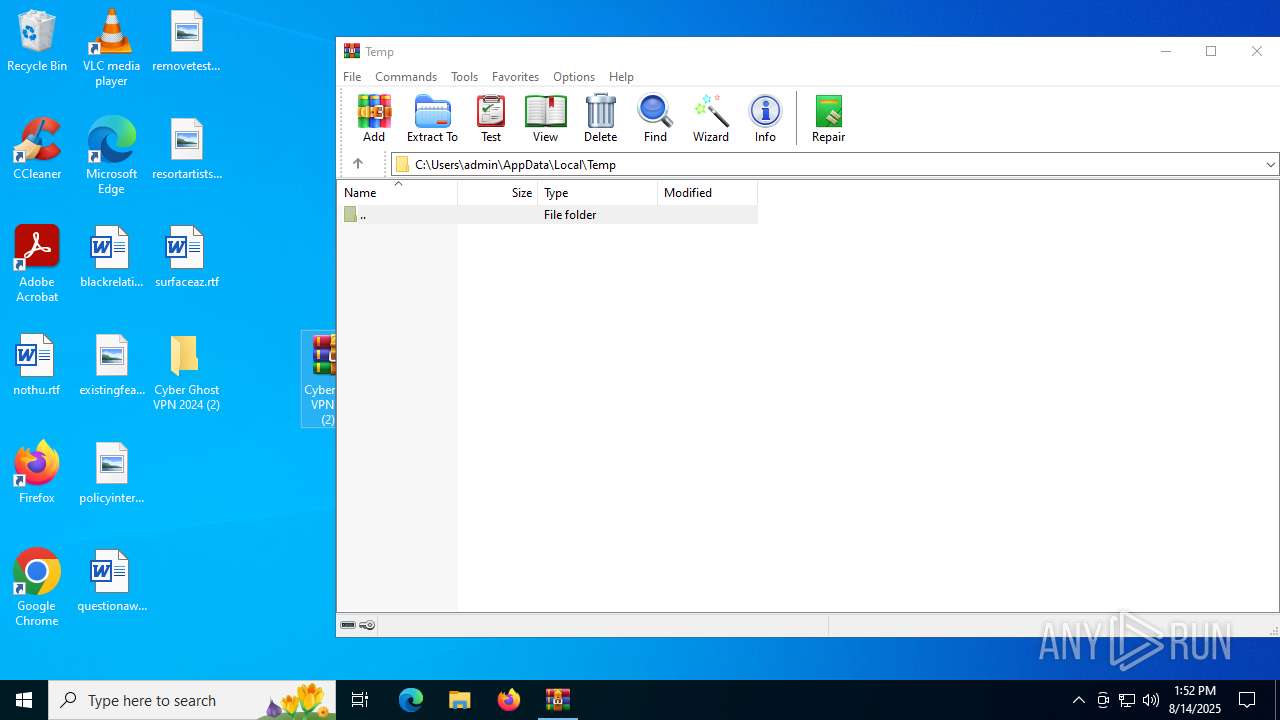
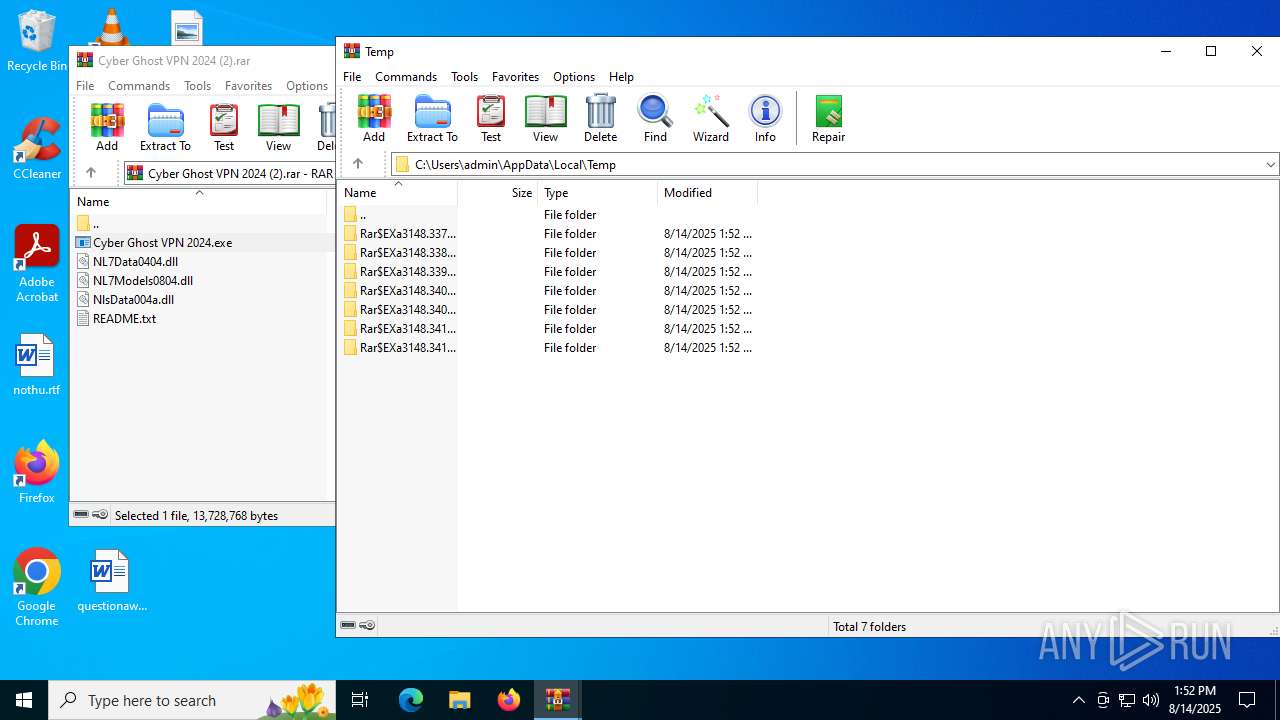
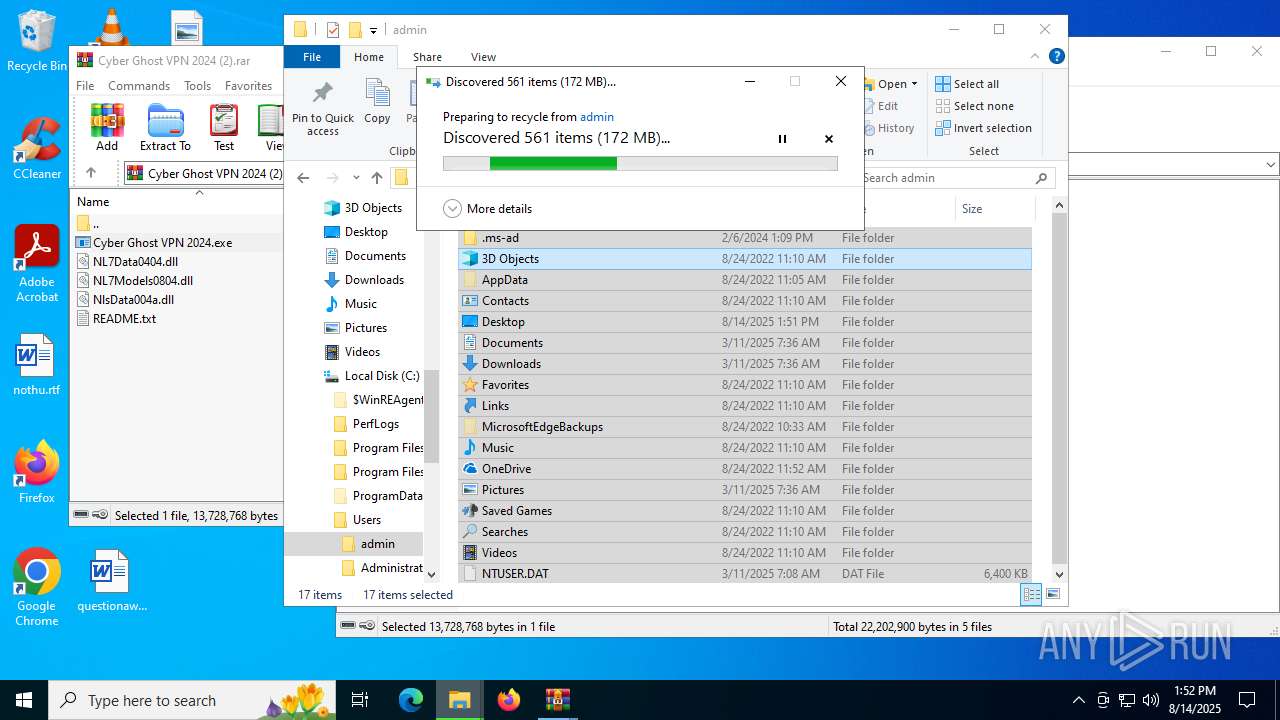
Create files in a temporary directory
- ms_updater.exe (PID: 4676)
- ms_updater.exe (PID: 4116)
- ms_updater.exe (PID: 436)
- ms_updater.exe (PID: 6408)
- ms_updater.exe (PID: 1028)
- ms_updater.exe (PID: 4664)
- ms_updater.exe (PID: 4112)
- ms_updater.exe (PID: 5504)
- ms_updater.exe (PID: 700)
- ms_updater.exe (PID: 6756)
Checks proxy server information
- ms_updater.exe (PID: 4676)
- ms_updater.exe (PID: 4116)
- WerFault.exe (PID: 4544)
- WerFault.exe (PID: 6348)
- ms_updater.exe (PID: 436)
- ms_updater.exe (PID: 6408)
- ms_updater.exe (PID: 1028)
- ms_updater.exe (PID: 4664)
- slui.exe (PID: 4800)
- ms_updater.exe (PID: 4112)
- ms_updater.exe (PID: 5504)
- ms_updater.exe (PID: 700)
- ms_updater.exe (PID: 6756)
- WerFault.exe (PID: 3860)
- WerFault.exe (PID: 1712)
- WerFault.exe (PID: 6768)
- WerFault.exe (PID: 2836)
- WerFault.exe (PID: 2108)
- WerFault.exe (PID: 4808)
- WerFault.exe (PID: 1964)
- WerFault.exe (PID: 5416)
- SearchApp.exe (PID: 4824)
Disables trace logs
- ms_updater.exe (PID: 4676)
- ms_updater.exe (PID: 4116)
- ms_updater.exe (PID: 436)
- ms_updater.exe (PID: 6408)
- ms_updater.exe (PID: 1028)
- ms_updater.exe (PID: 4664)
- ms_updater.exe (PID: 4112)
- ms_updater.exe (PID: 5504)
- ms_updater.exe (PID: 700)
- ms_updater.exe (PID: 6756)
Changes the display of characters in the console
- cmd.exe (PID: 6408)
- cmd.exe (PID: 6648)
- cmd.exe (PID: 6812)
- cmd.exe (PID: 4884)
- cmd.exe (PID: 7076)
- cmd.exe (PID: 4552)
- cmd.exe (PID: 2996)
- cmd.exe (PID: 6356)
- cmd.exe (PID: 512)
- cmd.exe (PID: 4444)
Reads Environment values
- ms_updater.exe (PID: 4676)
- ms_updater.exe (PID: 4116)
- ms_updater.exe (PID: 436)
- ms_updater.exe (PID: 6408)
- ms_updater.exe (PID: 1028)
- ms_updater.exe (PID: 4664)
- ms_updater.exe (PID: 4112)
- ms_updater.exe (PID: 5504)
- ms_updater.exe (PID: 700)
- ms_updater.exe (PID: 6756)
- SearchApp.exe (PID: 4824)
Reads the software policy settings
- WerFault.exe (PID: 4544)
- WerFault.exe (PID: 6348)
- slui.exe (PID: 4800)
- WerFault.exe (PID: 1712)
- WerFault.exe (PID: 3860)
- WerFault.exe (PID: 2836)
- WerFault.exe (PID: 6768)
- WerFault.exe (PID: 2108)
- WerFault.exe (PID: 4808)
- WerFault.exe (PID: 1964)
- WerFault.exe (PID: 5416)
- SearchApp.exe (PID: 4824)
Reads security settings of Internet Explorer
- notepad.exe (PID: 2028)
- dllhost.exe (PID: 5400)
Reads Microsoft Office registry keys
- WinRAR.exe (PID: 6704)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
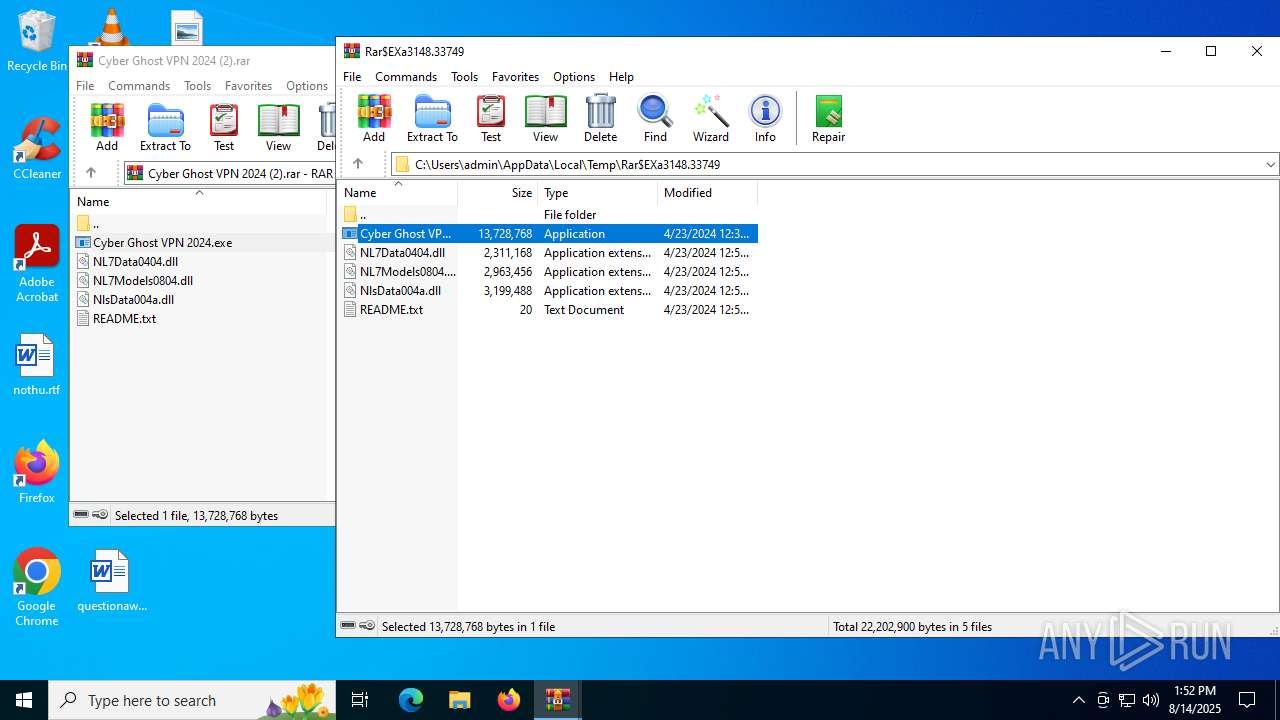
| FileVersion: | RAR v5 |
|---|---|
| CompressedSize: | 13140341 |
| UncompressedSize: | 13728768 |
| OperatingSystem: | Win32 |
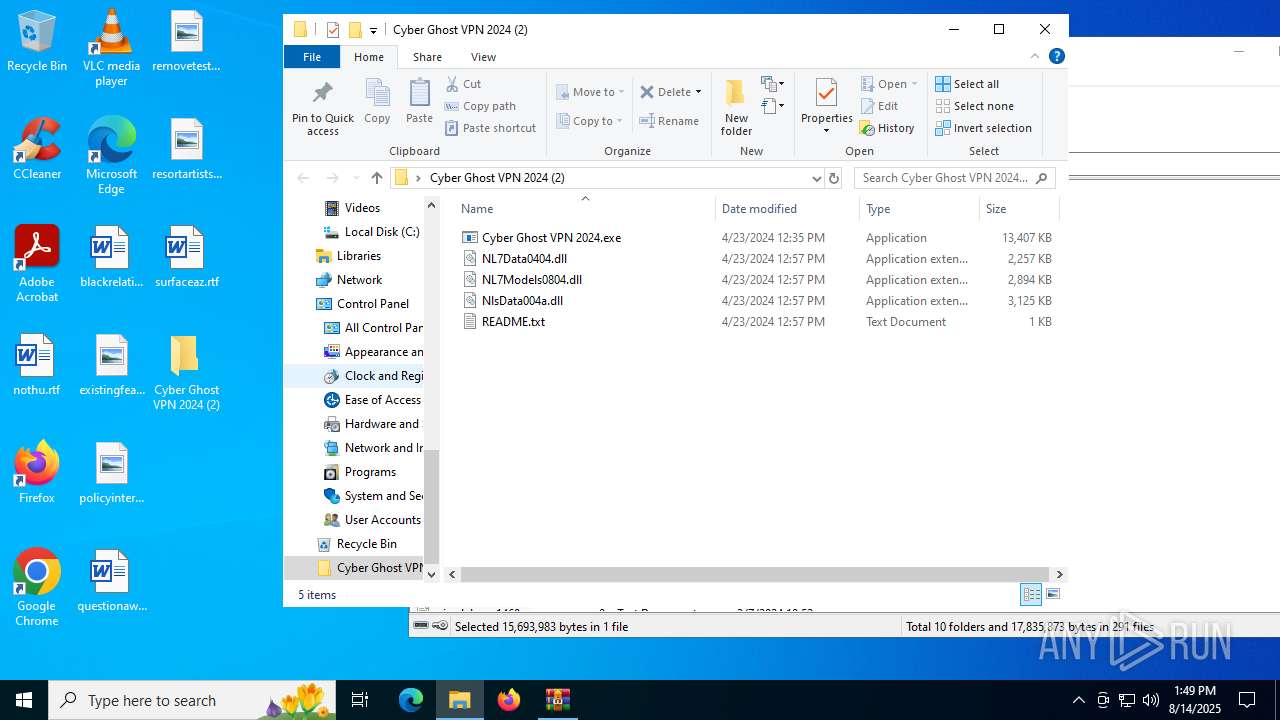
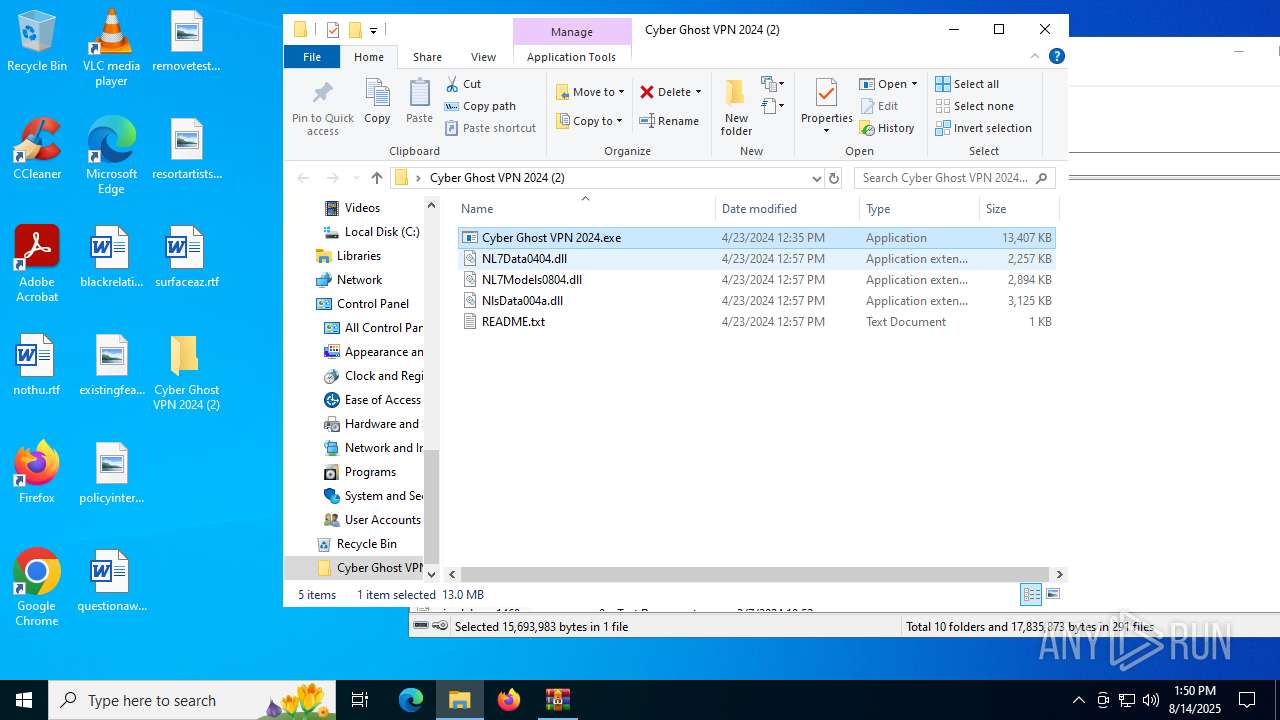
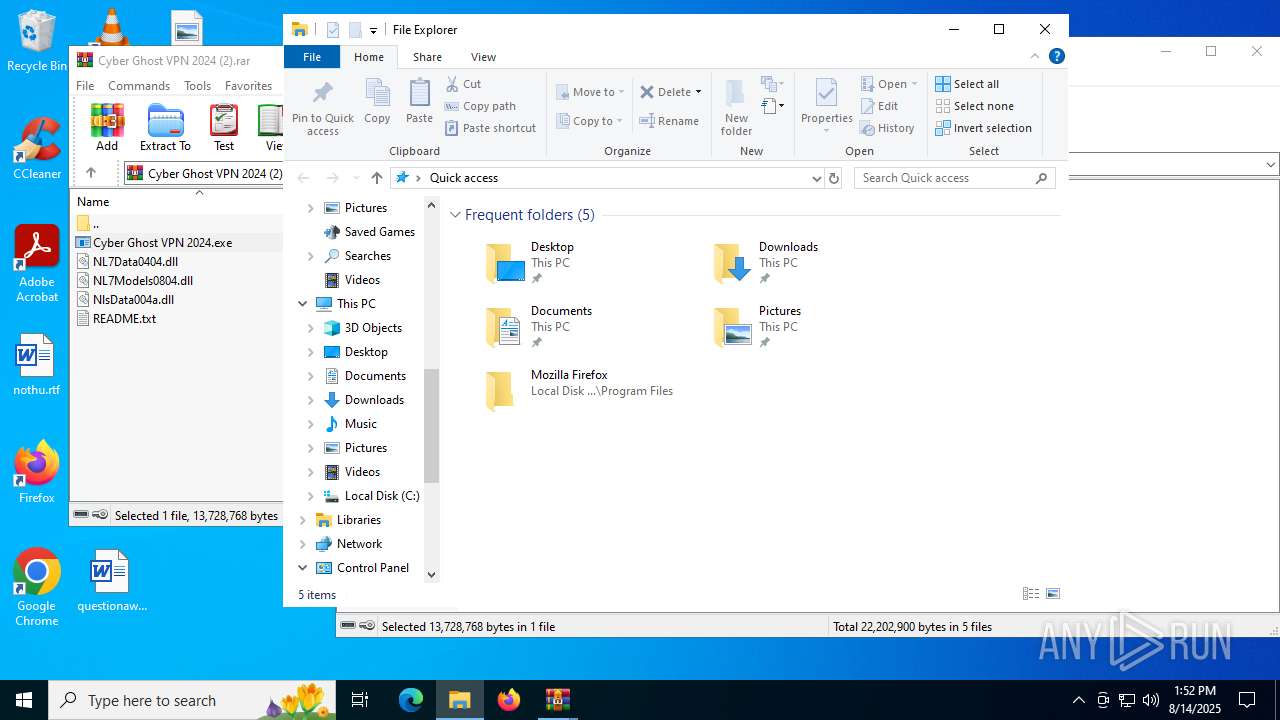
| ArchivedFileName: | Cyber Ghost VPN 2024.exe |
Total processes
253
Monitored processes
88
Malicious processes
22
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
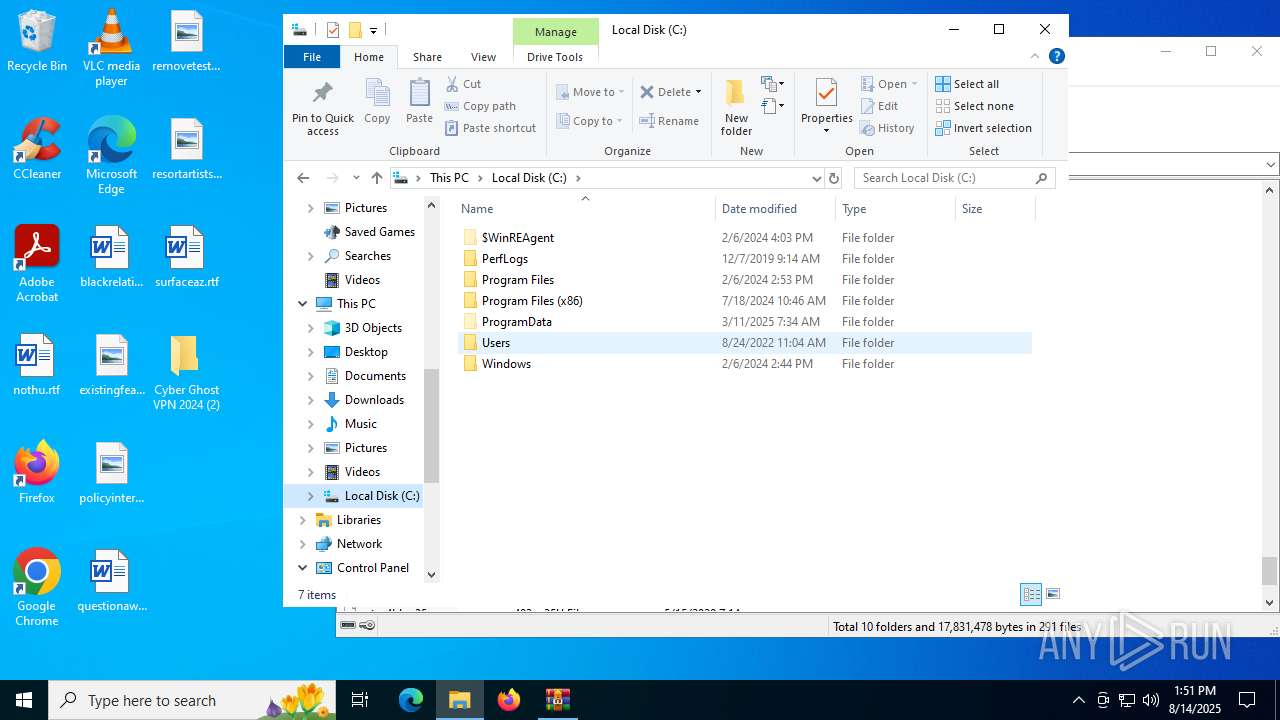
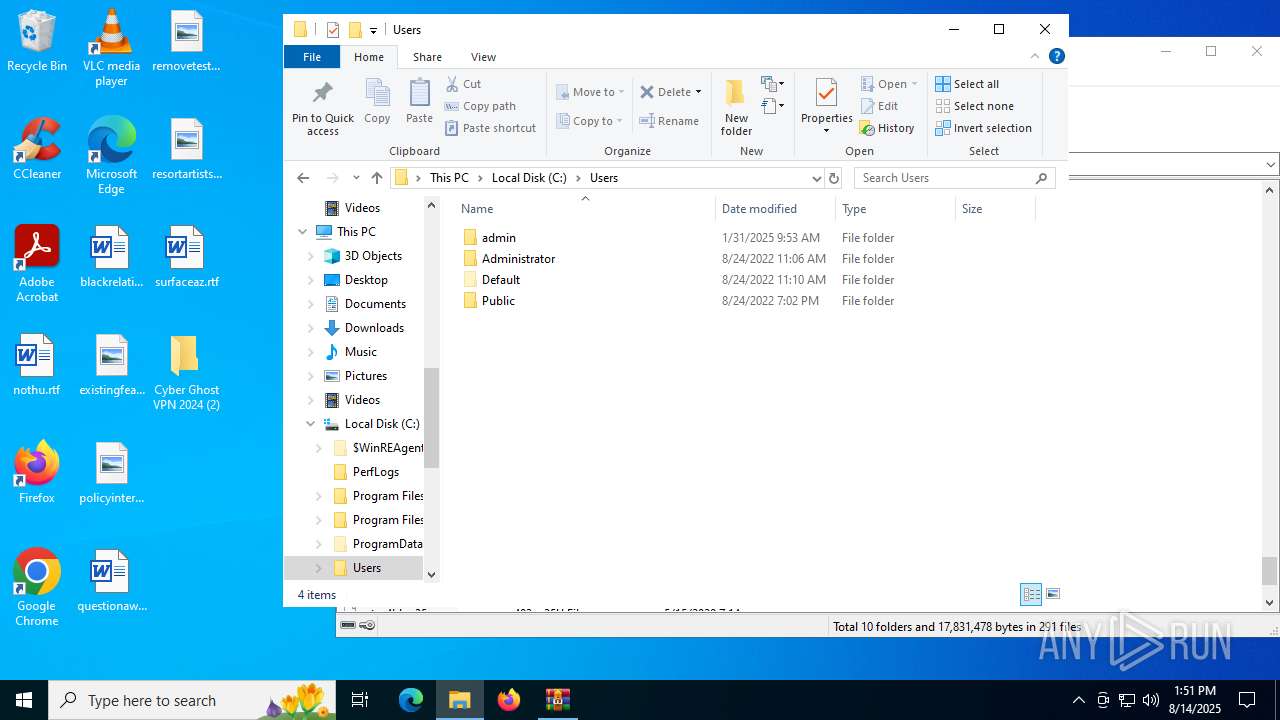
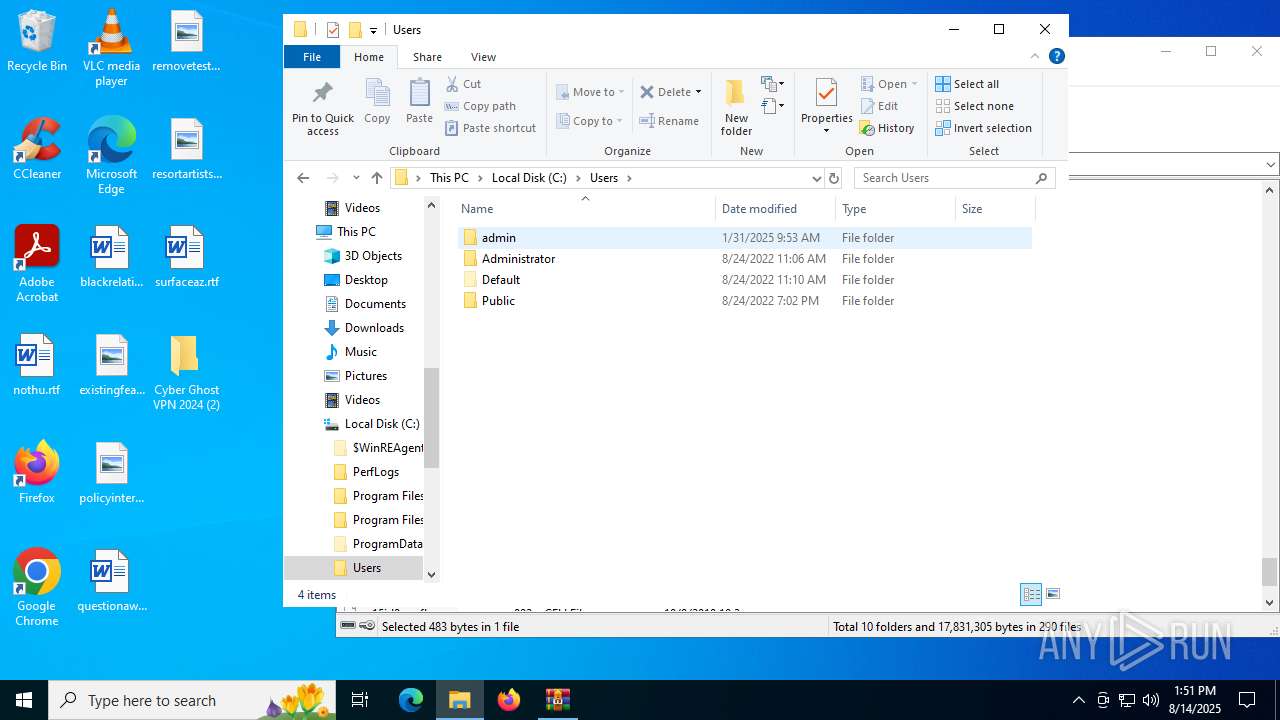
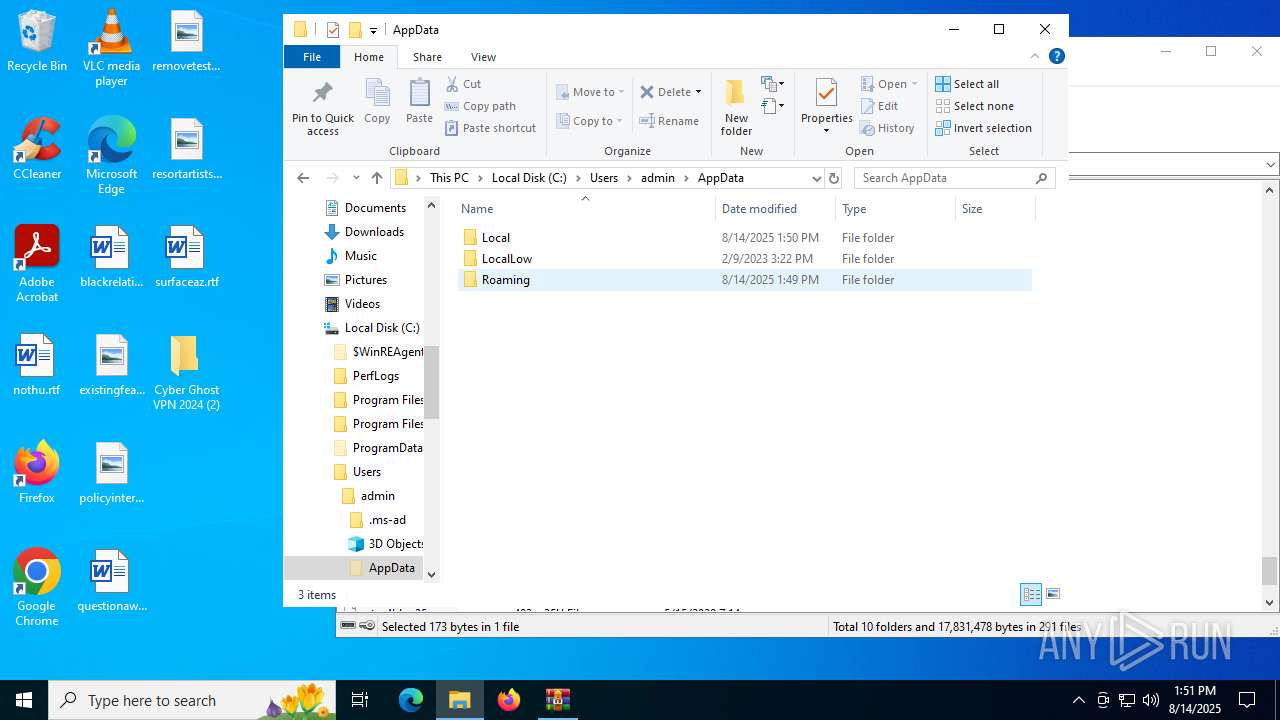
| 436 | "C:\Users\admin\AppData\Roaming\ms_updater.exe" | C:\Users\admin\AppData\Roaming\ms_updater.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.2.7.1277 Modules
| |||||||||||||||
| 512 | "C:\WINDOWS\System32\cmd.exe" /C "C:\Users\admin\AppData\Local\Temp\LHuPvvKEnU.bat" | C:\Windows\System32\cmd.exe | — | ms_updater.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 544 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3148.34056\Cyber Ghost VPN 2024.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3148.34056\Cyber Ghost VPN 2024.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226505 Modules
| |||||||||||||||
| 700 | "C:\Users\admin\AppData\Roaming\ms_updater.exe" | C:\Users\admin\AppData\Roaming\ms_updater.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.2.7.1277 Modules
| |||||||||||||||
| 864 | chcp 65001 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
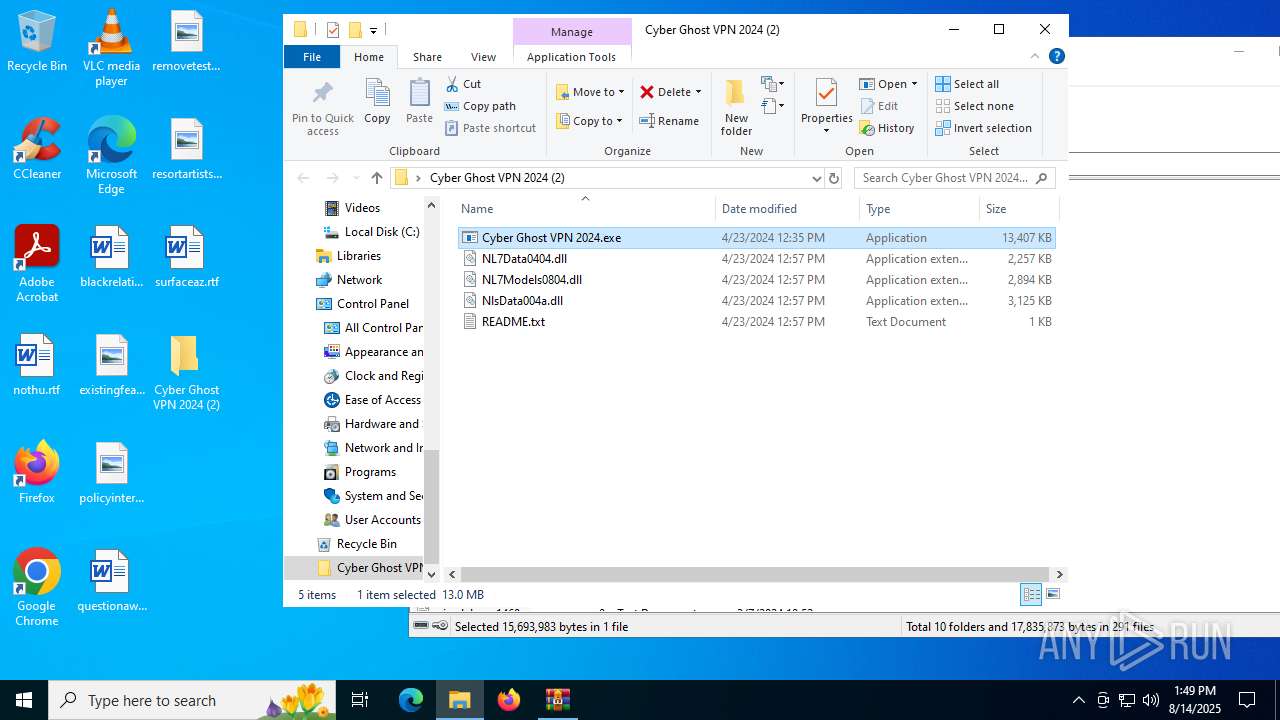
| 984 | "C:\Users\admin\Desktop\Cyber Ghost VPN 2024 (2)\Cyber Ghost VPN 2024.exe" | C:\Users\admin\Desktop\Cyber Ghost VPN 2024 (2)\Cyber Ghost VPN 2024.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226505 Modules
| |||||||||||||||
| 1028 | "C:\Users\admin\AppData\Roaming\ms_updater.exe" | C:\Users\admin\AppData\Roaming\ms_updater.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.2.7.1277 Modules
| |||||||||||||||
| 1044 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3148.33749\Cyber Ghost VPN 2024.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3148.33749\Cyber Ghost VPN 2024.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226505 Modules
| |||||||||||||||
| 1180 | chcp 65001 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1180 | chcp 65001 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
162 224
Read events
162 074
Write events
147
Delete events
3
Modification events
| (PID) Process: | (6704) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6704) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6704) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6704) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Cyber Ghost VPN 2024 (2).rar | |||
| (PID) Process: | (6704) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6704) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6704) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6704) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6704) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
| (PID) Process: | (6704) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
Executable files
115
Suspicious files
39
Text files
63
Unknown types
30
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4116 | ms_updater.exe | C:\Users\admin\Desktop\wRjNQnDD.log | executable | |
MD5:E9CE850DB4350471A62CC24ACB83E859 | SHA256:7C95D3B38114E7E4126CB63AADAF80085ED5461AB0868D2365DD6A18C946EA3A | |||
| 4676 | ms_updater.exe | C:\Users\admin\AppData\Local\Temp\OOvkeHfEc2 | text | |
MD5:D68D766256D1B5E66F6594A0F7568191 | SHA256:8F094155C106C95241094B39D5F1174D652EC76AABB73DC6F2986B9C598D3C40 | |||
| 4116 | ms_updater.exe | C:\Users\admin\Desktop\RgyBGscN.log | executable | |
MD5:F4B38D0F95B7E844DD288B441EBC9AAF | SHA256:AAB95596475CA74CEDE5BA50F642D92FA029F6F74F6FAEAE82A9A07285A5FB97 | |||
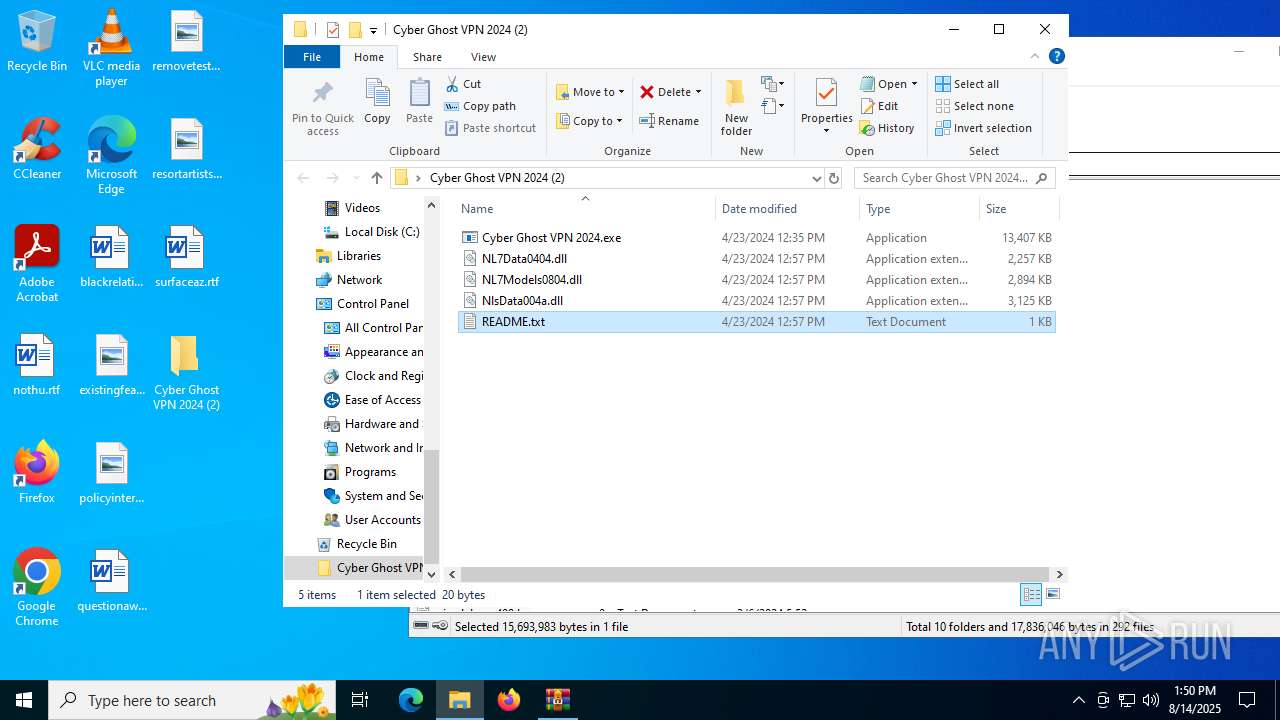
| 3620 | WinRAR.exe | C:\Users\admin\Desktop\Cyber Ghost VPN 2024 (2)\NL7Models0804.dll | executable | |
MD5:65525C7B89204D241120B7638934A0D2 | SHA256:18F7F52F14986133F9A9676D5AB959349377A53C0936CEA6EB9880E72F85BC54 | |||
| 3620 | WinRAR.exe | C:\Users\admin\Desktop\Cyber Ghost VPN 2024 (2)\NlsData004a.dll | executable | |
MD5:BE007B645B9D1332E3346107727320D9 | SHA256:7B128BE8D77398CBC3BB789A34E21AFC984C2E87276907A01326F8FB4504E9DA | |||
| 2324 | Cyber Ghost VPN 2024.exe | C:\Users\admin\AppData\Roaming\ms_tool.exe | executable | |
MD5:F8701952B62A7E52652271A20B824128 | SHA256:5B0B886143FFE9F5C5750C9B171656783668B655E559EA95D002A265586E3413 | |||
| 4676 | ms_updater.exe | C:\Users\admin\Desktop\geJyXWWP.log | executable | |
MD5:E9CE850DB4350471A62CC24ACB83E859 | SHA256:7C95D3B38114E7E4126CB63AADAF80085ED5461AB0868D2365DD6A18C946EA3A | |||
| 4788 | ms_tool.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\system32.exe | executable | |
MD5:F8701952B62A7E52652271A20B824128 | SHA256:5B0B886143FFE9F5C5750C9B171656783668B655E559EA95D002A265586E3413 | |||
| 2324 | Cyber Ghost VPN 2024.exe | C:\Users\admin\AppData\Roaming\ms_updater.exe | executable | |
MD5:31E5E3AC5A03D60D67188B6B0C3D152B | SHA256:DC73CE51066FDCD5F0C7C88FD6FDFB9A4A3722EBE3D2DEF1DC593FBC1AF9E467 | |||
| 3620 | WinRAR.exe | C:\Users\admin\Desktop\Cyber Ghost VPN 2024 (2)\Cyber Ghost VPN 2024.exe | executable | |
MD5:95F7A7D1658B372CBCBD6CC1EF91BEF9 | SHA256:841D63D65E18B16579FF539E49EA437EF27C488D52D463B0105CDD4B19D2EA37 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
19
TCP/UDP connections
54
DNS requests
30
Threats
35
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4892 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
1268 | svchost.exe | GET | 200 | 23.216.77.7:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 814 b | whitelisted |
4820 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 420 b | whitelisted |
4820 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 408 b | whitelisted |
4676 | ms_updater.exe | POST | 200 | 15.197.130.221:80 | http://968620cm.nyashkoon.top/PythonLowProcesswpdownloads.php | US | html | 3.60 Kb | malicious |
4544 | WerFault.exe | GET | 200 | 23.216.77.15:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
4544 | WerFault.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 814 b | whitelisted |
4116 | ms_updater.exe | POST | 200 | 15.197.130.221:80 | http://968620cm.nyashkoon.top/PythonLowProcesswpdownloads.php | US | html | 16.5 Kb | malicious |
436 | ms_updater.exe | POST | 200 | 15.197.130.221:80 | http://968620cm.nyashkoon.top/PythonLowProcesswpdownloads.php | US | html | 16.5 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3852 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4892 | svchost.exe | 40.126.31.130:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4892 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
1268 | svchost.exe | 23.216.77.7:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
968620cm.nyashkoon.top |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
2200 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
4676 | ms_updater.exe | A Network Trojan was detected | ET MALWARE [ANY.RUN] DarkCrystal Rat Check-in (POST) |
4676 | ms_updater.exe | A Network Trojan was detected | REMOTE [ANY.RUN] DarkCrystal Rat Check-in (POST) |
4676 | ms_updater.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.top domain |
4676 | ms_updater.exe | Misc Attack | ET Threatview.io High Confidence Cobalt Strike C2 IP group 5 |
4676 | ms_updater.exe | Misc Attack | ET Threatview.io High Confidence Cobalt Strike C2 IP group 4 |
4676 | ms_updater.exe | Generic Protocol Command Decode | SURICATA HTTP status 100-Continue already seen |
4116 | ms_updater.exe | Generic Protocol Command Decode | SURICATA HTTP status 100-Continue already seen |
4116 | ms_updater.exe | A Network Trojan was detected | ET MALWARE [ANY.RUN] DarkCrystal Rat Check-in (POST) |