| File name: | Antiban.exe |
| Full analysis: | https://app.any.run/tasks/e93a8c93-e87e-418d-86fe-b8e27259275b |
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2019, 04:39:52 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 3D436384AB1A72676FEB6E7FAED449A6 |
| SHA1: | 57CFACB979F1692F9972225E3417F1B0B9A2EF44 |
| SHA256: | 2DA6E1EA286AFF362A1F4E2529006281574EE16EFCAC533ABD827CAE093AF616 |
| SSDEEP: | 49152:jNQ6j0NQSd6vuoFCP4Zx9jDR3lUPmdm7OTOMsf7deXHBo0MslUkB:jNQ6oNQSd6vuos+tF1wmdmgfwxOBo0Mq |
MALICIOUS
Changes settings of System certificates
- Antiban.exe (PID: 1308)
SUSPICIOUS
Low-level read access rights to disk partition
- Antiban.exe (PID: 1308)
Creates files in the user directory
- Antiban.exe (PID: 1308)
Adds / modifies Windows certificates
- Antiban.exe (PID: 1308)
Reads internet explorer settings
- Antiban.exe (PID: 1308)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (18) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (2.9) |
| .exe | | | Generic Win/DOS Executable (1.3) |
| .exe | | | DOS Executable Generic (1.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:08:02 08:51:31+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 446976 |
| InitializedDataSize: | 1270784 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x5346c |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
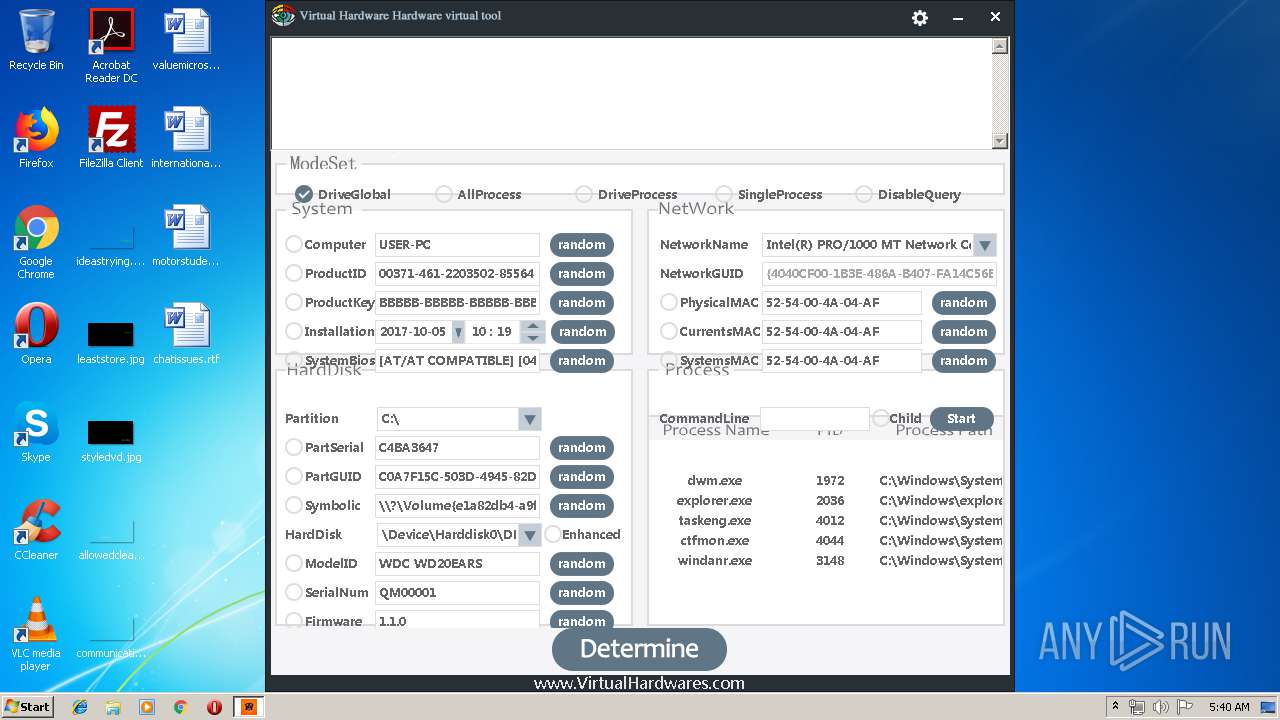
| CompanyName: | hardware |
| FileDescription: | hardware |
| FileVersion: | 1, 0, 0, 0 |
| InternalName: | hardware.exe |
| LegalCopyright: | (C) virtualhardwares All Rights Reserved |
| OriginalFileName: | hardware |
| ProductName: | hardware |
| ProductVersion: | 1, 0, 0, 0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 02-Aug-2018 06:51:31 |
| Detected languages: |
|
| CompanyName: | hardware |
| FileDescription: | hardware |
| FileVersion: | 1, 0, 0, 0 |
| InternalName: | hardware.exe |
| LegalCopyright: | (C) virtualhardwares All Rights Reserved |
| OriginalFilename: | hardware |
| ProductName: | hardware |
| ProductVersion: | 1, 0, 0, 0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 02-Aug-2018 06:51:31 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0006D11E | 0x0006D200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.60589 |
.rdata | 0x0006F000 | 0x00017E7E | 0x00018000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.35541 |
.data | 0x00087000 | 0x00009BD8 | 0x00004A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.20731 |
.rsrc | 0x00091000 | 0x0011114D | 0x00111200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.83883 |
.reloc | 0x001A3000 | 0x000086B8 | 0x00008800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 5.70908 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.01229 | 633 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 4.62743 | 4264 | UNKNOWN | English - United States | RT_ICON |
3 | 4.61427 | 9640 | UNKNOWN | English - United States | RT_ICON |
4 | 7.98702 | 51397 | UNKNOWN | English - United States | RT_ICON |
5 | 2.44608 | 62 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
10 | 5.19906 | 19973 | Latin 1 / Western European | English - United States | XML |
11 | 4.97839 | 463 | Latin 1 / Western European | English - United States | XML |
13 | 5.31532 | 1302 | Latin 1 / Western European | English - United States | XML |
14 | 5.19827 | 782 | Latin 1 / Western European | English - United States | XML |
15 | 5.01732 | 7630 | Latin 1 / Western European | English - United States | XML |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
IMM32.dll |
IPHLPAPI.DLL |
KERNEL32.dll |
OLEAUT32.dll |
PSAPI.DLL |
USER32.dll |
Total processes
36
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 828 | "C:\Users\admin\AppData\Local\Temp\Antiban.exe" | C:\Users\admin\AppData\Local\Temp\Antiban.exe | — | explorer.exe | |||||||||||
User: admin Company: hardware Integrity Level: MEDIUM Description: hardware Exit code: 3221226540 Version: 1, 0, 0, 0 Modules
| |||||||||||||||
| 1308 | "C:\Users\admin\AppData\Local\Temp\Antiban.exe" | C:\Users\admin\AppData\Local\Temp\Antiban.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
155
Read events
118
Write events
36
Delete events
1
Modification events
| (PID) Process: | (1308) Antiban.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1308) Antiban.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1308) Antiban.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Antiban_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1308) Antiban.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Antiban_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (1308) Antiban.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Antiban_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (1308) Antiban.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Antiban_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (1308) Antiban.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Antiban_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (1308) Antiban.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Antiban_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (1308) Antiban.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Antiban_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1308) Antiban.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Antiban_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
0
Suspicious files
0
Text files
8
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1308 | Antiban.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\gg[1].png | image | |
MD5:— | SHA256:— | |||
| 1308 | Antiban.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@virtualhardwares[1].txt | text | |
MD5:— | SHA256:— | |||
| 1308 | Antiban.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@www.virtualhardwares[1].txt | text | |
MD5:— | SHA256:— | |||
| 1308 | Antiban.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\z_stat[1].php | text | |
MD5:— | SHA256:— | |||
| 1308 | Antiban.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\gg[1].htm | html | |
MD5:— | SHA256:— | |||
| 1308 | Antiban.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\core[1].php | html | |
MD5:— | SHA256:— | |||
| 1308 | Antiban.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\History.IE5\MSHist012019052020190521\index.dat | dat | |
MD5:— | SHA256:— | |||
| 1308 | Antiban.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@mmstat[1].txt | text | |
MD5:— | SHA256:— | |||
| 1308 | Antiban.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\stat[1].htm | text | |
MD5:444BCB3A3FCF8389296C49467F27E1D6 | SHA256:2689367B205C16CE32ED4200942B8B8B1E262DFC70D9BC9FBC77C49699A4F1DF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
5
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1308 | Antiban.exe | GET | 200 | 162.215.255.54:80 | http://www.virtualhardwares.com/English/hardware/gg.png | US | image | 19.0 Kb | unknown |
1308 | Antiban.exe | GET | 200 | 162.215.255.54:80 | http://www.virtualhardwares.com/English/hardware/gg.html | US | html | 897 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1308 | Antiban.exe | 162.215.255.54:80 | www.virtualhardwares.com | Krypt Technologies | US | unknown |
1308 | Antiban.exe | 218.92.0.81:443 | s22.cnzz.com | No.31,Jin-rong Street | CN | unknown |
1308 | Antiban.exe | 218.92.0.82:443 | s22.cnzz.com | No.31,Jin-rong Street | CN | unknown |
1308 | Antiban.exe | 203.119.129.115:443 | z1.cnzz.com | — | CN | malicious |
1308 | Antiban.exe | 198.11.132.221:443 | cnzz.mmstat.com | Alibaba (China) Technology Co., Ltd. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.virtualhardwares.com |
| unknown |
s22.cnzz.com |
| suspicious |
z1.cnzz.com |
| whitelisted |
c.cnzz.com |
| whitelisted |
cnzz.mmstat.com |
| whitelisted |