| File name: | setup.exe |
| Full analysis: | https://app.any.run/tasks/7eba6998-7283-4c2f-b55d-70d27789ce62 |
| Verdict: | Malicious activity |
| Analysis date: | February 21, 2020, 17:53:56 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 628DD1CE66FE6E8CDB17CCDC98AAC5BC |
| SHA1: | 6833ADDCDD5625C0C4A08503006A96EFECABEACD |
| SHA256: | 2DA0E52A6BE708DF8F157B5148241B59BA8824521C27F7480C460457B4A4F988 |
| SSDEEP: | 196608:WRFfGMkASVqV26hgDneSydczoVU6FB9LREFD:uuMkqE5NzwUQ4Z |
MALICIOUS
Loads dropped or rewritten executable
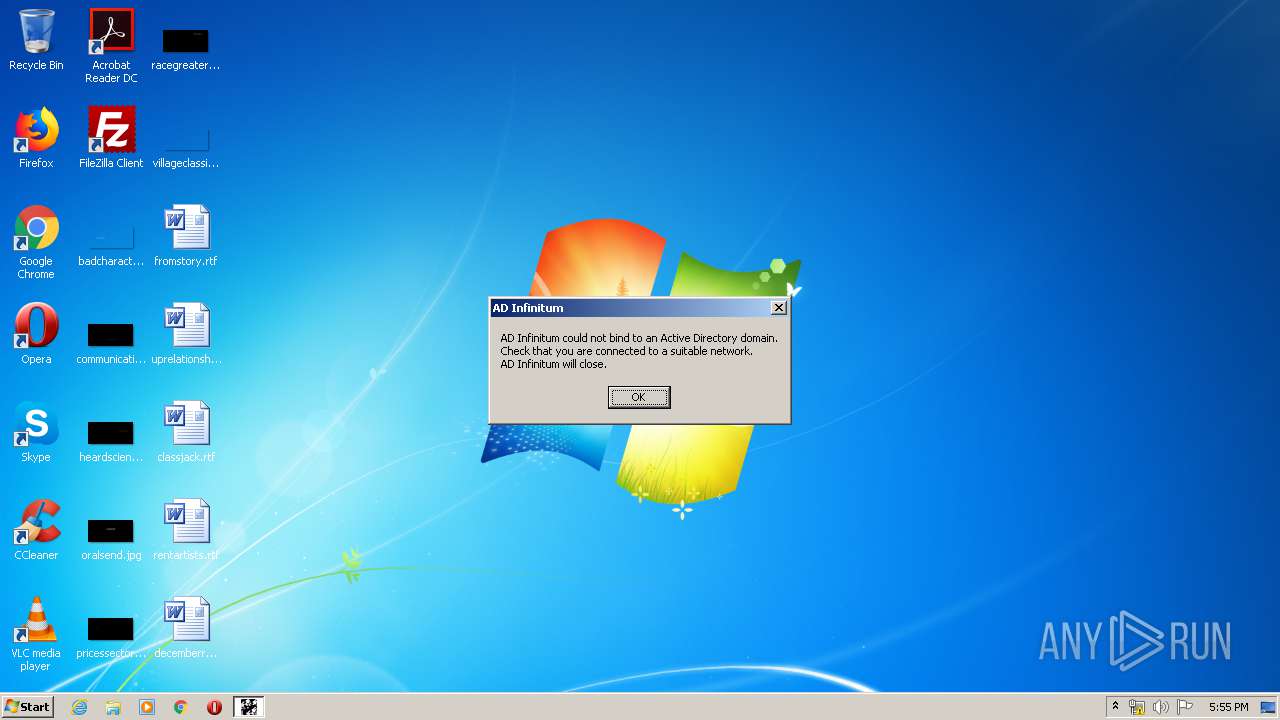
- AD Infinitum 2.exe (PID: 1760)
Application was dropped or rewritten from another process
- AD Infinitum 2.exe (PID: 1760)
SUSPICIOUS
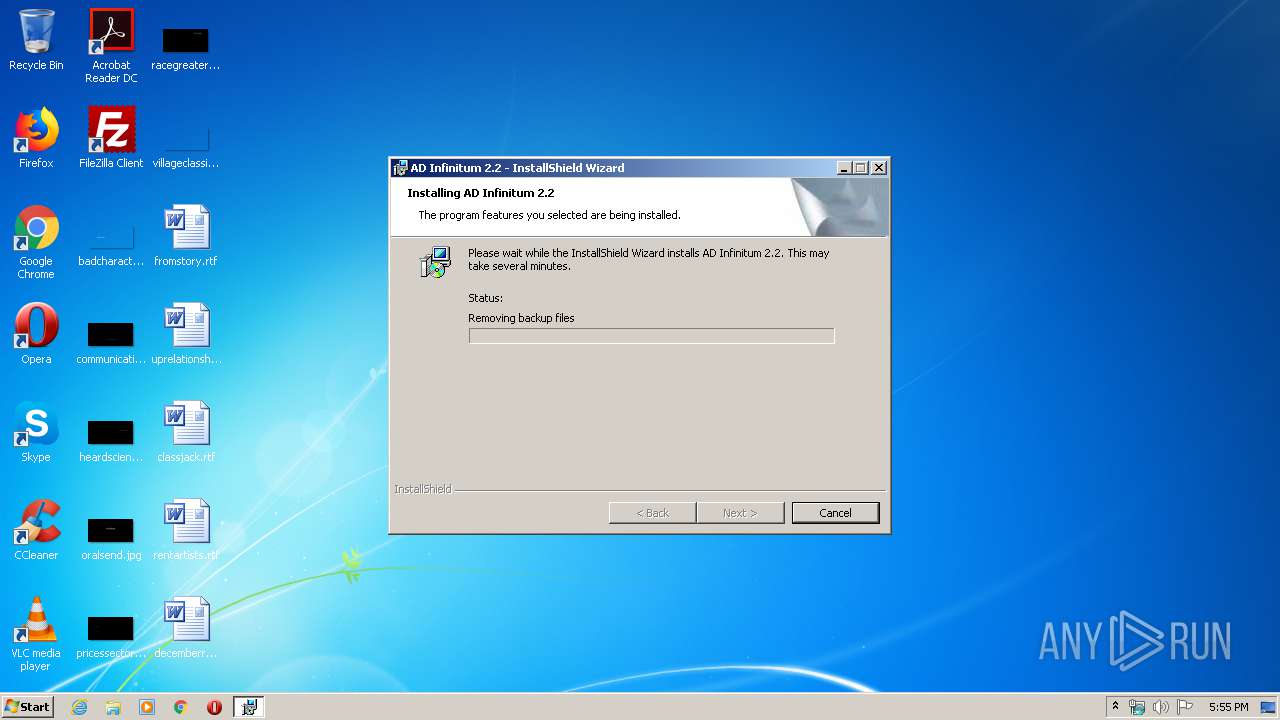
Executable content was dropped or overwritten
- setup.exe (PID: 3076)
- MSIEXEC.EXE (PID: 3944)
- msiexec.exe (PID: 3360)
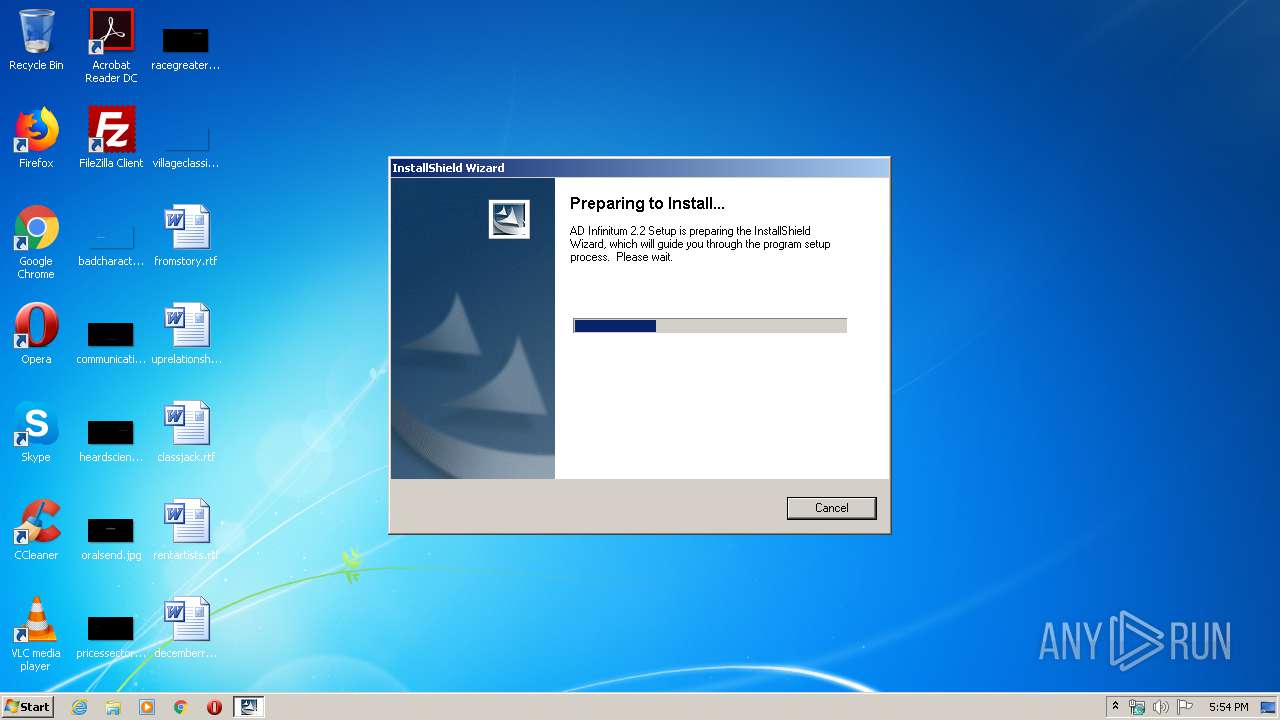
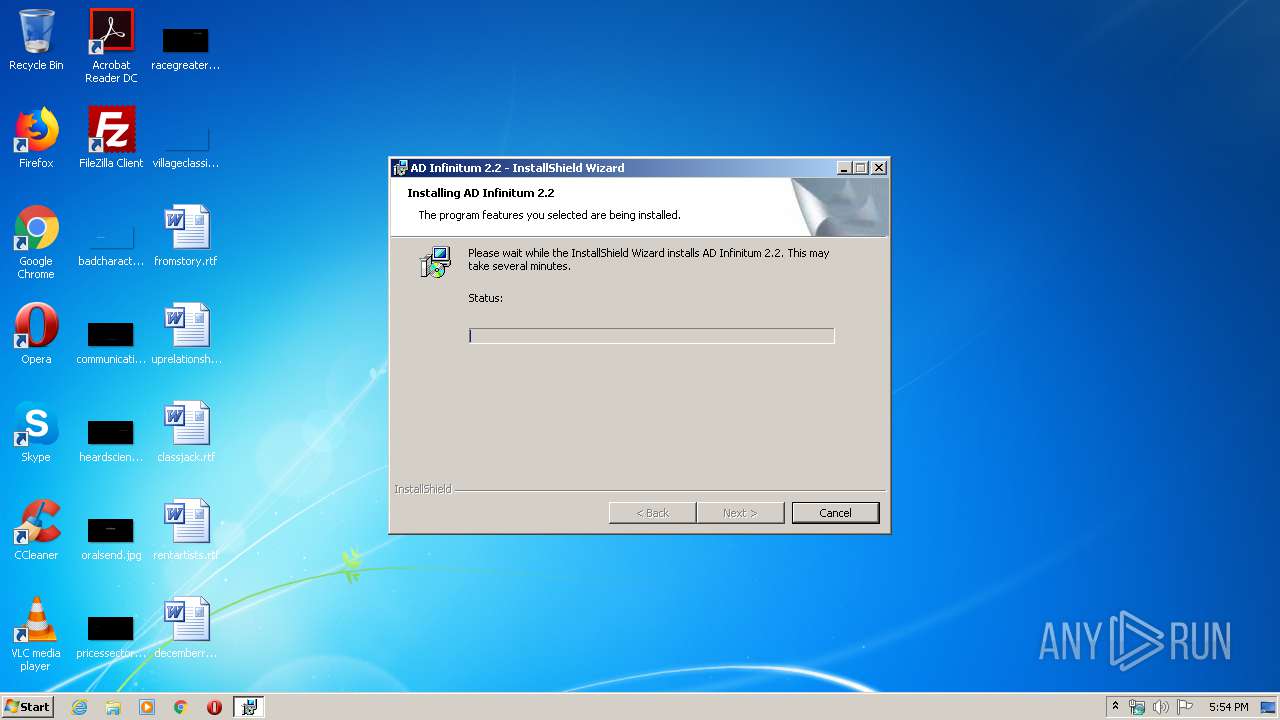
Starts Microsoft Installer
- setup.exe (PID: 3076)
Creates files in the Windows directory
- setup.exe (PID: 3076)
- msiexec.exe (PID: 3360)
Executed as Windows Service
- vssvc.exe (PID: 2376)
Reads Internet Cache Settings
- setup.exe (PID: 3076)
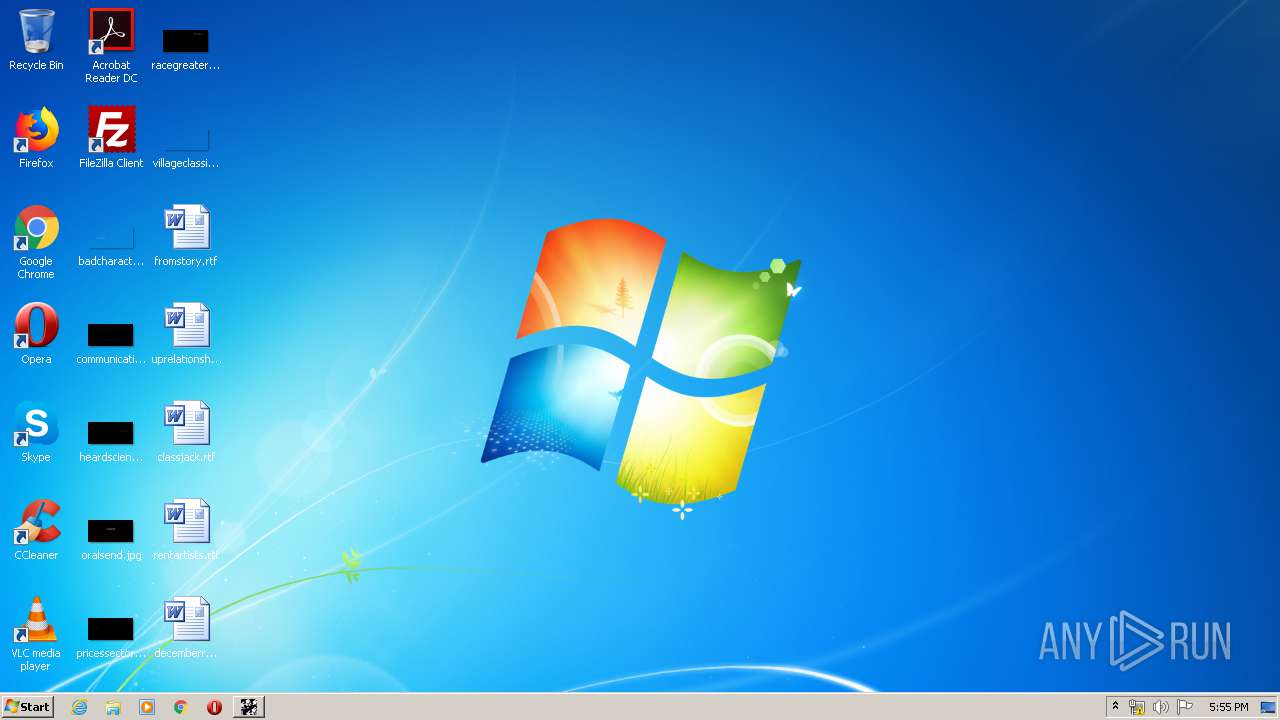
Creates files in the program directory
- AD Infinitum 2.exe (PID: 1760)
INFO
Application launched itself
- msiexec.exe (PID: 3360)
Searches for installed software
- msiexec.exe (PID: 3360)
Low-level read access rights to disk partition
- vssvc.exe (PID: 2376)
Dropped object may contain Bitcoin addresses
- msiexec.exe (PID: 3360)
Creates files in the program directory
- msiexec.exe (PID: 3360)
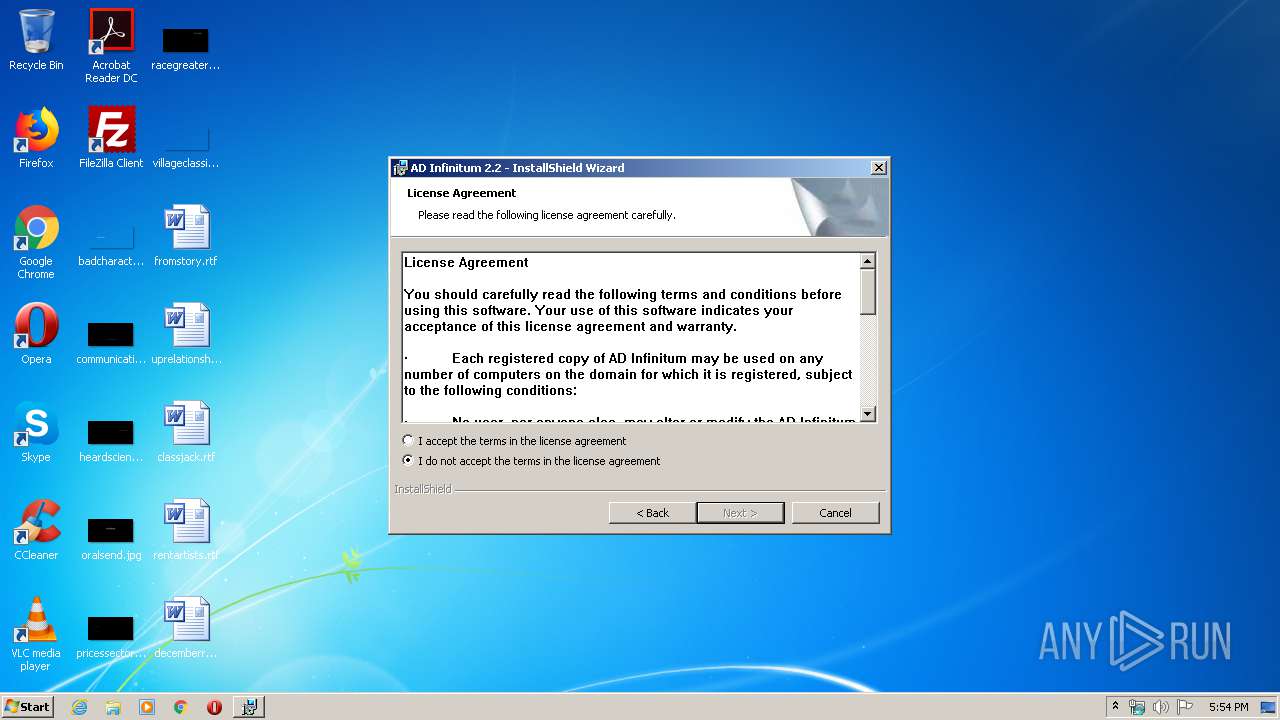
Creates a software uninstall entry
- msiexec.exe (PID: 3360)
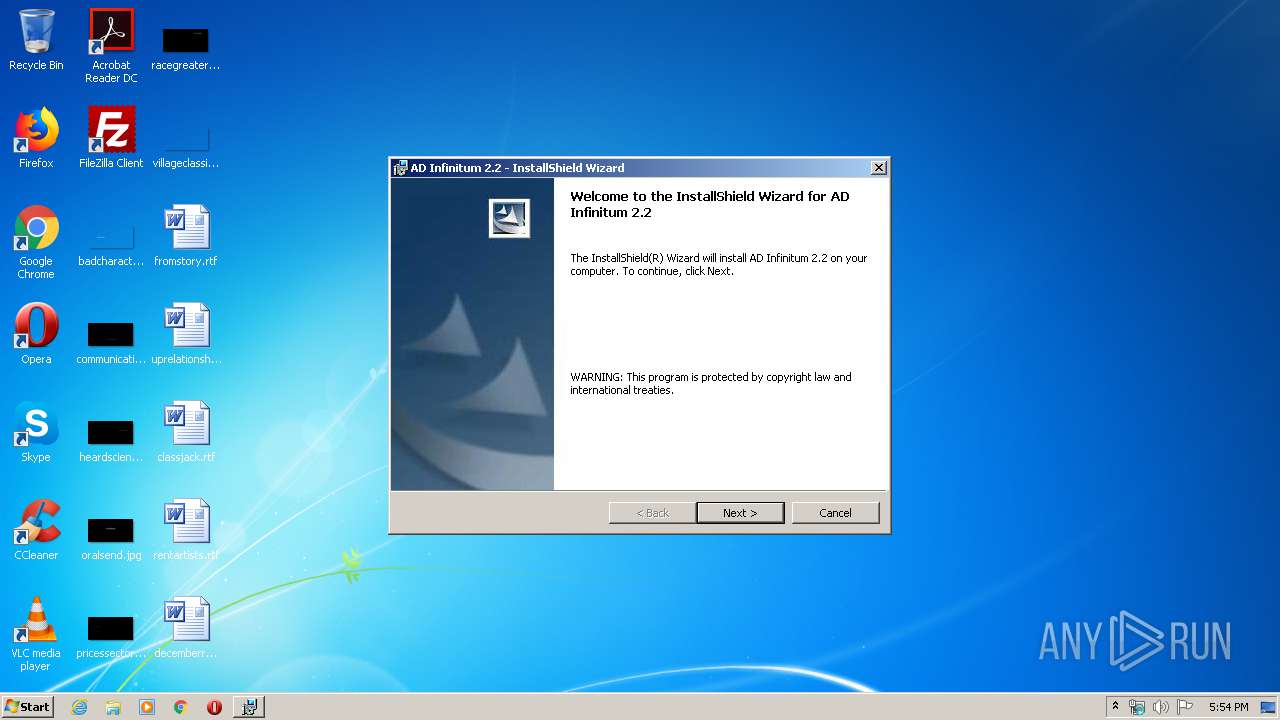
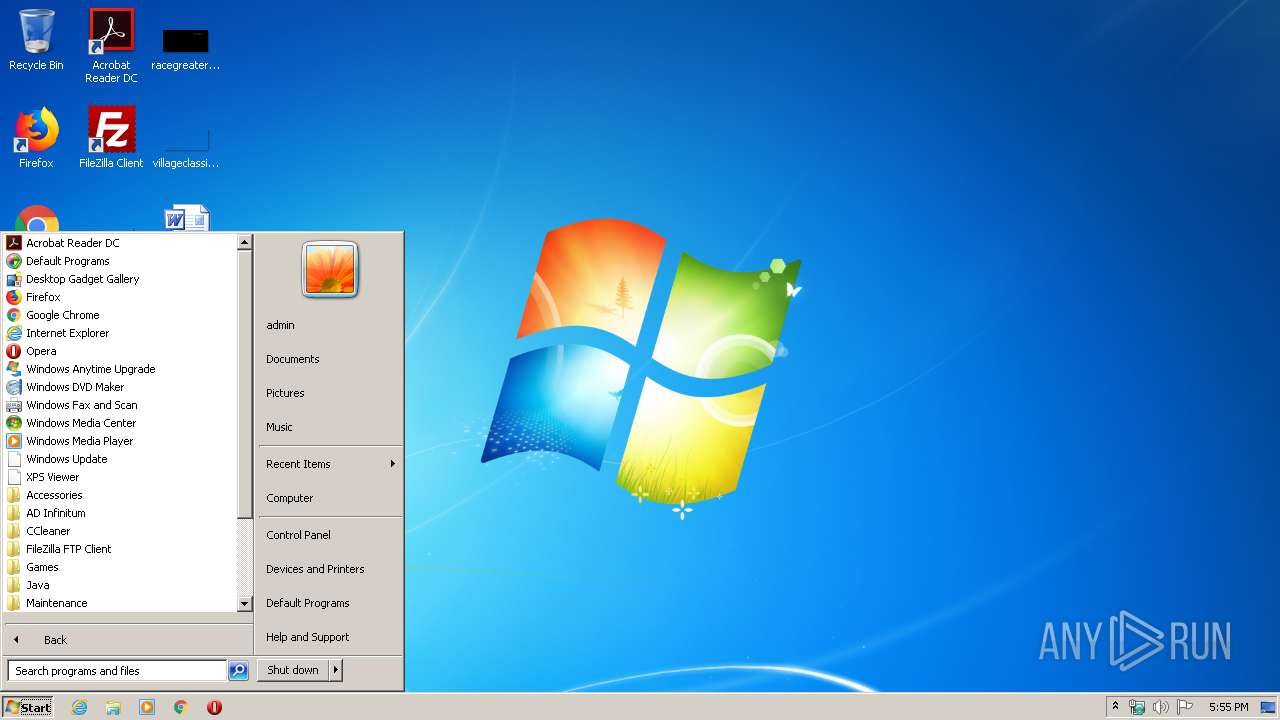
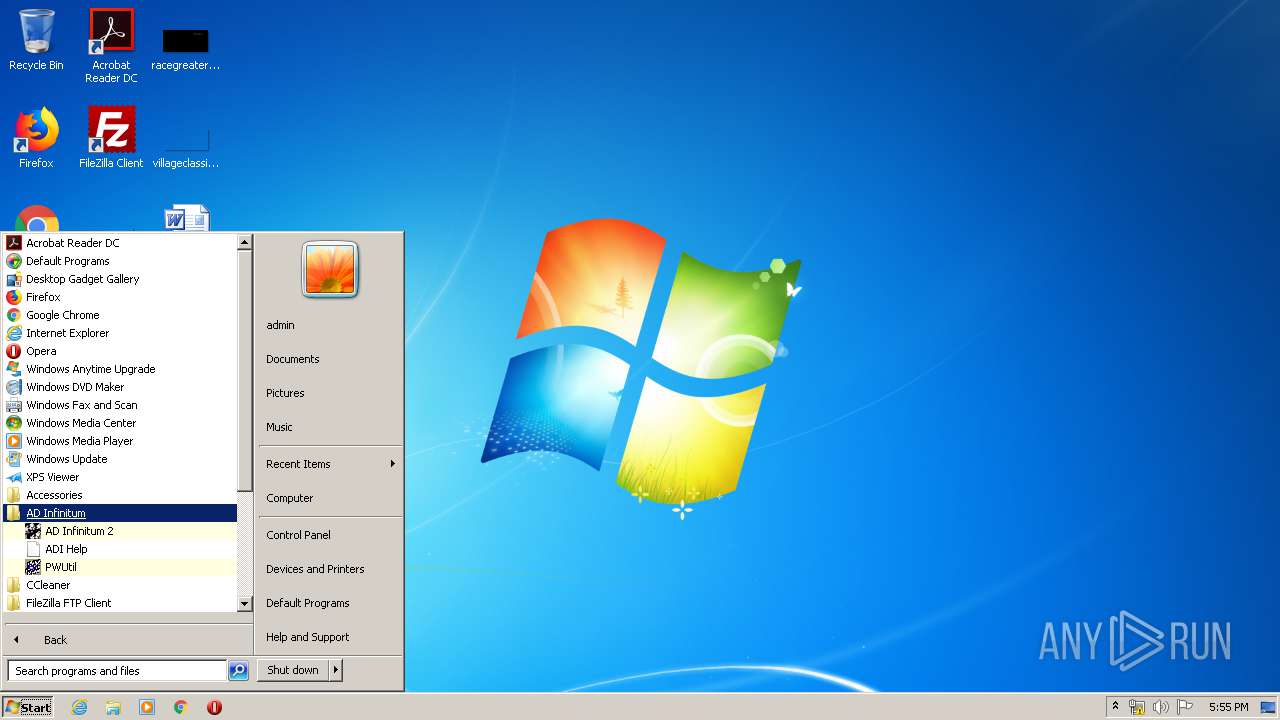
Manual execution by user
- AD Infinitum 2.exe (PID: 1760)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (36.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (26.6) |
| .exe | | | Win64 Executable (generic) (23.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2003:05:19 09:10:10+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 139264 |
| InitializedDataSize: | 102400 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1891c |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.1.248.0 |
| ProductVersionNumber: | 4.1.0.0 |
| FileFlagsMask: | 0x0002 |
| FileFlags: | Pre-release |
| FileOS: | Windows 16-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| Comments: | |
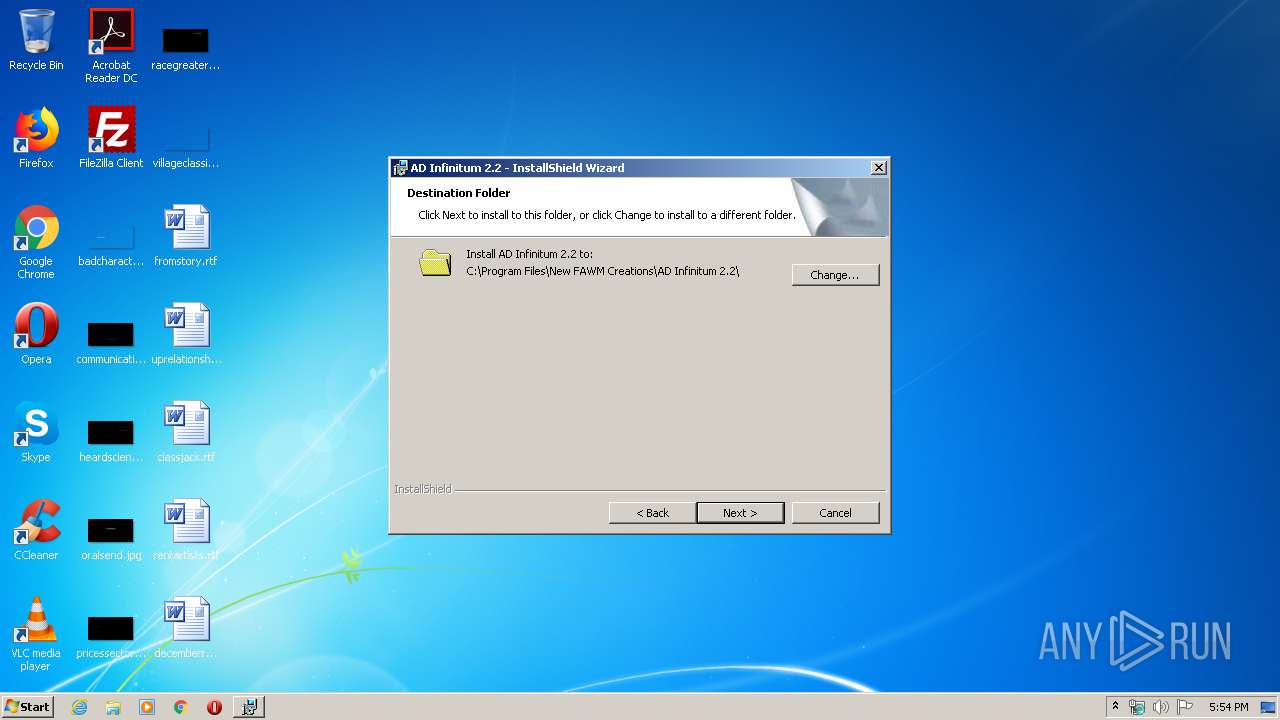
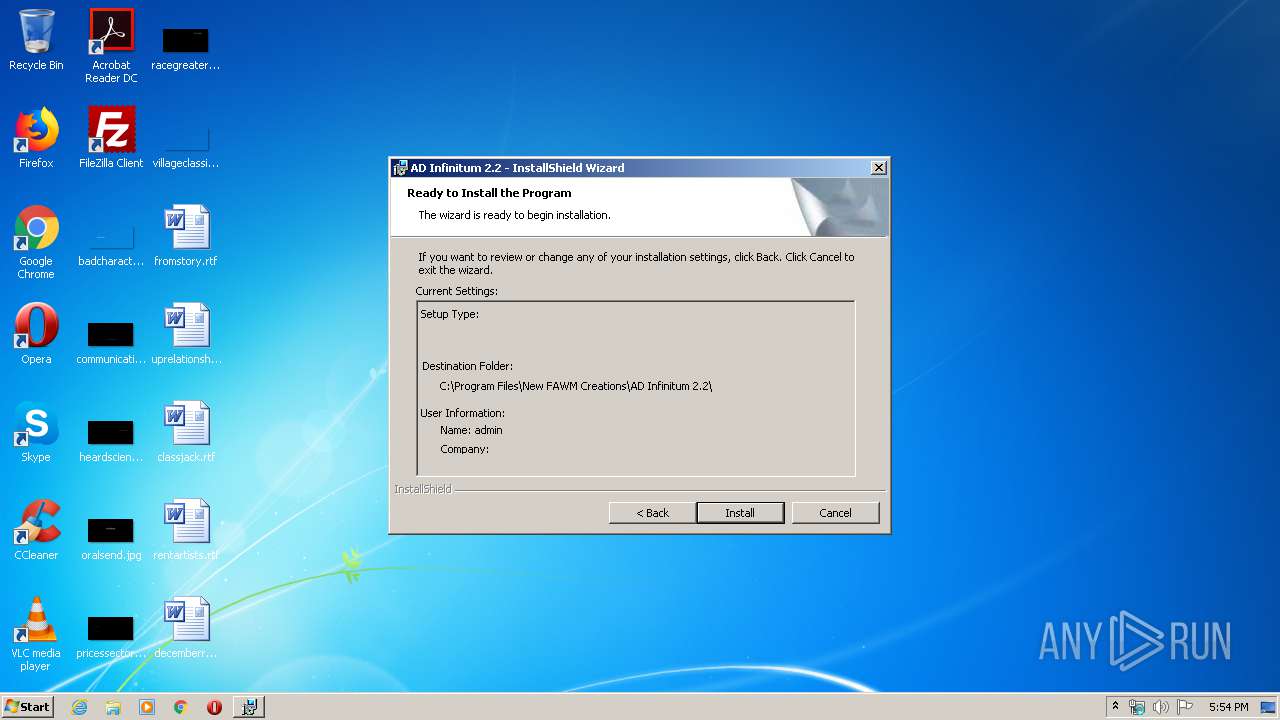
| CompanyName: | New FAWM Creations |
| FileDescription: | Setup Launcher |
| FileVersion: | 2.2.9.5 |
| InternalName: | setup.exe |
| OriginalFileName: | setup.exe |
| LegalCopyright: | Copyright (C) 2003 InstallShield Software Corp. |
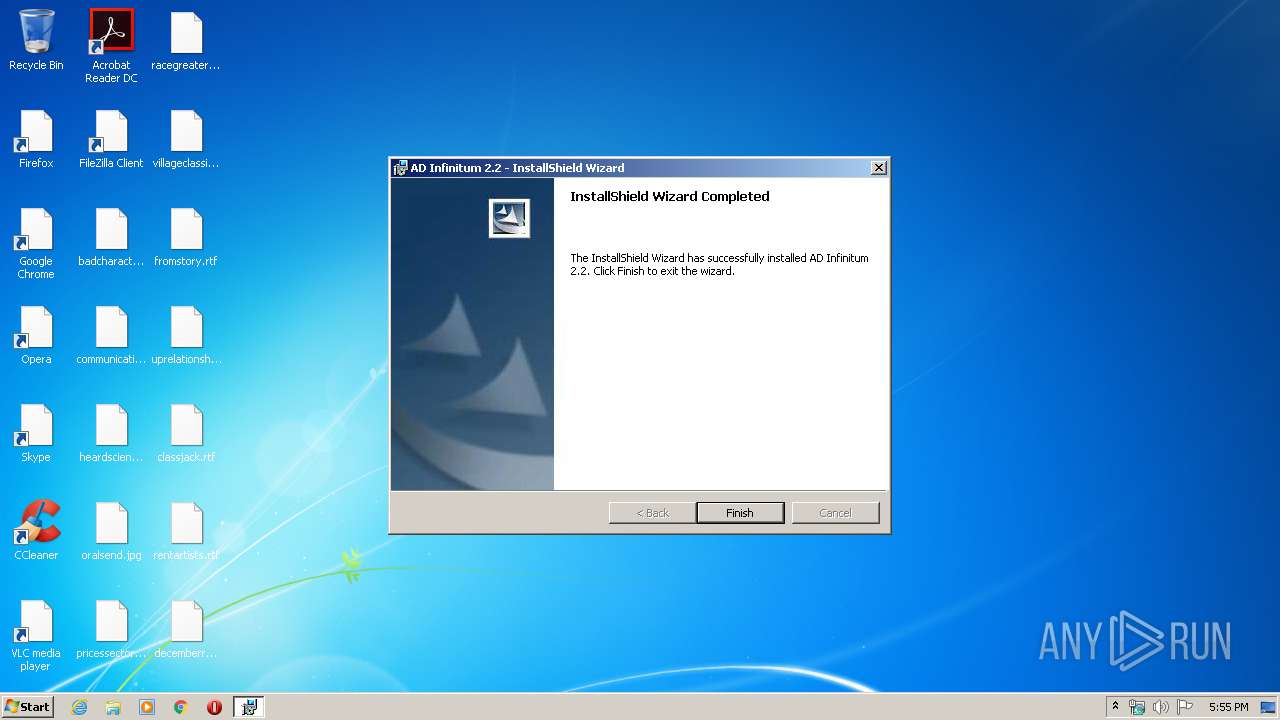
| ProductName: | AD Infinitum 2.2 |
| ProductVersion: | 2.2.9.5 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-May-2003 07:10:10 |
| Detected languages: |
|
| Comments: | - |
| CompanyName: | New FAWM Creations |
| FileDescription: | Setup Launcher |
| FileVersion: | 2.2.9.5 |
| InternalName: | setup.exe |
| OriginalFilename: | setup.exe |
| LegalCopyright: | Copyright (C) 2003 InstallShield Software Corp. |
| ProductName: | AD Infinitum 2.2 |
| ProductVersion: | 2.2.9.5 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 19-May-2003 07:10:10 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0002124E | 0x00022000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.48226 |
.rdata | 0x00023000 | 0x00003DFA | 0x00004000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.19377 |
.data | 0x00027000 | 0x00009218 | 0x00005000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.12631 |
.rsrc | 0x00031000 | 0x0000A2E0 | 0x0000B000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.23942 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.87924 | 666 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 6.39652 | 1384 | UNKNOWN | English - United States | RT_ICON |
3 | 3.9625 | 744 | UNKNOWN | English - United States | RT_ICON |
4 | 6.7616 | 2216 | UNKNOWN | English - United States | RT_ICON |
5 | 2.48972 | 308 | UNKNOWN | English - United States | RT_CURSOR |
69 | 2.47806 | 110 | UNKNOWN | English - United States | RT_STRING |
72 | 2.32551 | 110 | UNKNOWN | English - United States | RT_STRING |
73 | 2.76648 | 204 | UNKNOWN | English - United States | RT_STRING |
100 | 2.64576 | 62 | UNKNOWN | English - United States | RT_GROUP_ICON |
104 | 2.01924 | 20 | UNKNOWN | English - United States | RT_GROUP_CURSOR |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
47
Monitored processes
7
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1760 | "C:\Program Files\New FAWM Creations\AD Infinitum 2.2\AD Infinitum 2.exe" | C:\Program Files\New FAWM Creations\AD Infinitum 2.2\AD Infinitum 2.exe | — | explorer.exe | |||||||||||
User: admin Company: New FAWM Creations Integrity Level: MEDIUM Exit code: 3 Version: 2.2.9.97 Modules
| |||||||||||||||
| 2376 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2904 | "C:\Users\admin\AppData\Local\Temp\setup.exe" | C:\Users\admin\AppData\Local\Temp\setup.exe | — | explorer.exe | |||||||||||
User: admin Company: New FAWM Creations Integrity Level: MEDIUM Description: Setup Launcher Exit code: 3221226540 Version: 2.2.9.5 Modules
| |||||||||||||||
| 2948 | C:\Windows\system32\MsiExec.exe -Embedding 6303DE00F5A4B6FCA381F80D1749E929 C | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3076 | "C:\Users\admin\AppData\Local\Temp\setup.exe" | C:\Users\admin\AppData\Local\Temp\setup.exe | explorer.exe | ||||||||||||
User: admin Company: New FAWM Creations Integrity Level: HIGH Description: Setup Launcher Exit code: 0 Version: 2.2.9.5 Modules
| |||||||||||||||
| 3360 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3944 | MSIEXEC.EXE /i "C:\Windows\Downloaded Installations\{7B457862-8926-4280-800D-22EB1432F08C}\AD Infinitum 2.2.msi" SETUPEXEDIR="C:\Users\admin\AppData\Local\Temp" | C:\Windows\system32\MSIEXEC.EXE | setup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
865
Read events
612
Write events
241
Delete events
12
Modification events
| (PID) Process: | (3360) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 40000000000000003AE2C2FDDFE8D501200D000090090000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3360) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 40000000000000003AE2C2FDDFE8D501200D000090090000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3360) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 34 | |||
| (PID) Process: | (3360) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4000000000000000FE0427FEDFE8D501200D000090090000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3360) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000B2C92BFEDFE8D501200D000048050000E803000001000000000000000000000095FF21BD0F3180458F3D4B0CBB3C36AE0000000000000000 | |||
| (PID) Process: | (2376) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000EA6548FEDFE8D50148090000300D0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2376) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000EA6548FEDFE8D50148090000BC030000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2376) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000EA6548FEDFE8D501480900004C0B0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2376) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000EA6548FEDFE8D5014809000020090000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2376) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Leave) |
Value: 4000000000000000601659FEDFE8D501480900004C0B0000E8030000000000000100000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
12
Suspicious files
5
Text files
16
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3076 | setup.exe | C:\Users\admin\AppData\Local\Temp\~892D.tmp | — | |
MD5:— | SHA256:— | |||
| 3360 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 3360 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DF47A5866E0A602871.TMP | — | |
MD5:— | SHA256:— | |||
| 3076 | setup.exe | C:\Users\admin\AppData\Local\Temp\_is892E\Setup.INI | text | |
MD5:— | SHA256:— | |||
| 3076 | setup.exe | C:\Users\admin\AppData\Local\Temp\_is892E\_ISMSIDEL.INI | text | |
MD5:— | SHA256:— | |||
| 3076 | setup.exe | C:\Windows\Downloaded Installations\{7B457862-8926-4280-800D-22EB1432F08C}\AD Infinitum 2.2.msi | executable | |
MD5:— | SHA256:— | |||
| 3076 | setup.exe | C:\Users\admin\AppData\Local\Temp\_is892E\AD Infinitum 2.2.msi | executable | |
MD5:— | SHA256:— | |||
| 3360 | msiexec.exe | C:\Program Files\New FAWM Creations\AD Infinitum 2.2\ADI LogFile.txt | text | |
MD5:— | SHA256:— | |||
| 3360 | msiexec.exe | C:\Windows\Installer\a70c96.msi | executable | |
MD5:— | SHA256:— | |||
| 3360 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{bd21ff95-310f-4580-8f3d-4b0cbb3c36ae}_OnDiskSnapshotProp | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report