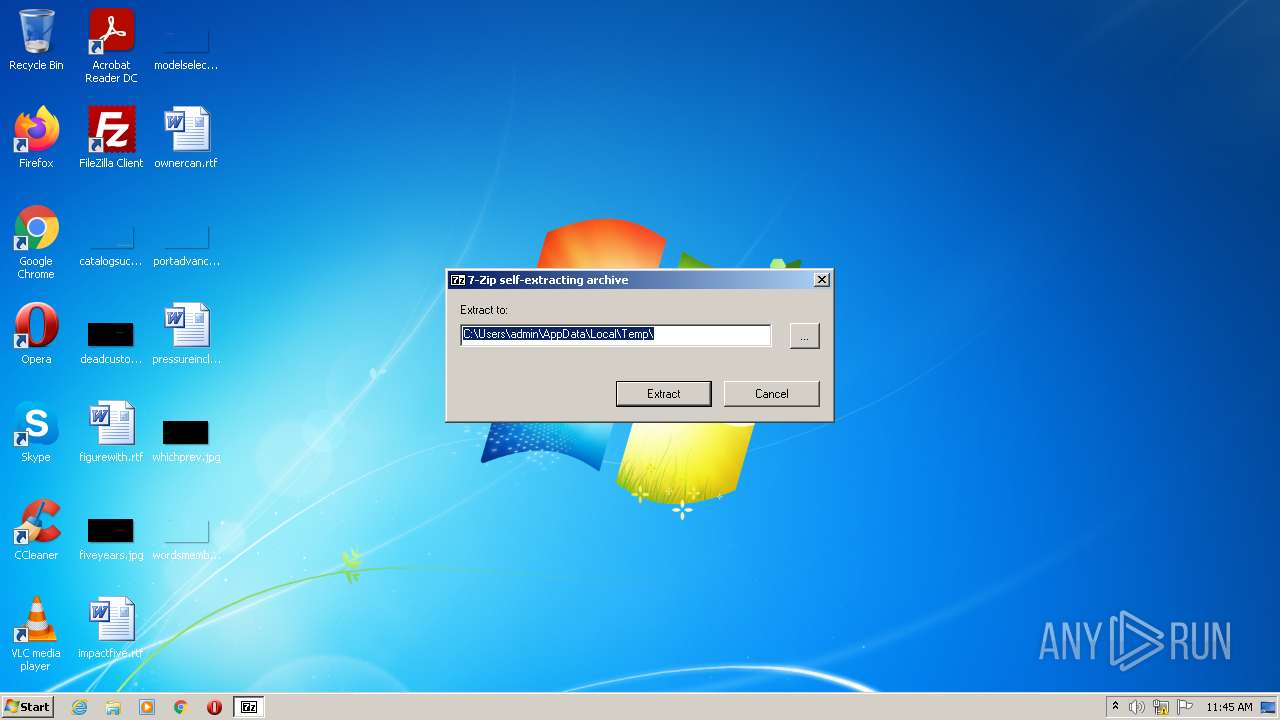
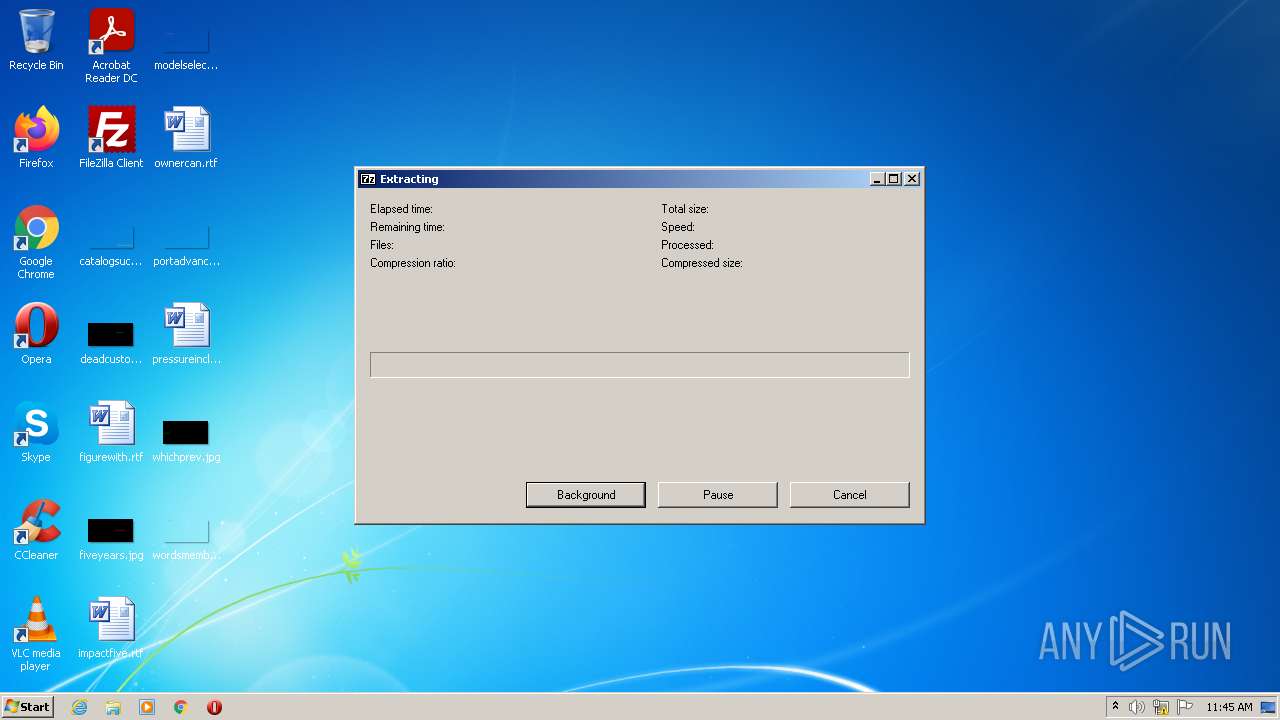
| File name: | DesktopGoose v0.3 Extractor.exe |
| Full analysis: | https://app.any.run/tasks/92052df6-5ac8-4168-8248-f843fc7c252d |
| Verdict: | Malicious activity |
| Analysis date: | May 21, 2022, 10:45:41 |
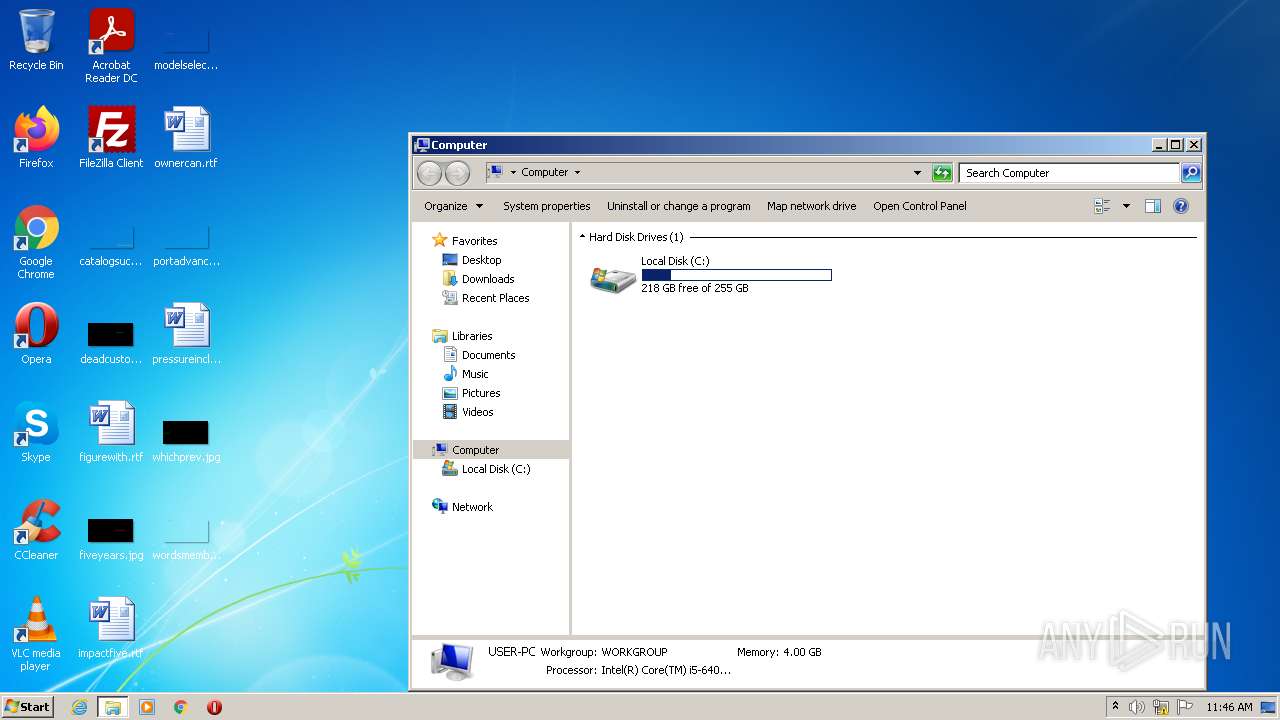
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 4794142776C35938D65AEC9AAC022C2F |
| SHA1: | F9E281B20D51E0DB73D124D172DFCE8ADA1B1368 |
| SHA256: | 2D97BBBEB28B7836841AAD642AA9C36F5C8F388BDE0A0B22D8B17C8B9D417FD8 |
| SSDEEP: | 98304:Hh3Mmu0KoAIkOkMUAtcokAvw8UzTacT6sFxy6T1+MaZWWY4B+IrA:HIvAmWSC6x+MaM4Y |
MALICIOUS
Drops executable file immediately after starts
- DesktopGoose v0.3 Extractor.exe (PID: 3024)
SUSPICIOUS
Executable content was dropped or overwritten
- DesktopGoose v0.3 Extractor.exe (PID: 3024)
Checks supported languages
- DesktopGoose v0.3 Extractor.exe (PID: 3024)
Drops a file with a compile date too recent
- DesktopGoose v0.3 Extractor.exe (PID: 3024)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| ProductVersion: | 19 |
|---|---|
| ProductName: | 7-Zip |
| OriginalFileName: | 7z.sfx.exe |
| LegalCopyright: | Copyright (c) 1999-2018 Igor Pavlov |
| InternalName: | 7z.sfx |
| FileVersion: | 19 |
| FileDescription: | 7z SFX |
| CompanyName: | Igor Pavlov |
| CharacterSet: | Unicode |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Windows NT 32-bit |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 19.0.0.0 |
| FileVersionNumber: | 19.0.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x277c6 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 53248 |
| CodeSize: | 168960 |
| LinkerVersion: | 6 |
| PEType: | PE32 |
| TimeStamp: | 2019:02:21 17:00:00+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 21-Feb-2019 16:00:00 |
| Detected languages: |
|
| CompanyName: | Igor Pavlov |
| FileDescription: | 7z SFX |
| FileVersion: | 19.00 |
| InternalName: | 7z.sfx |
| LegalCopyright: | Copyright (c) 1999-2018 Igor Pavlov |
| OriginalFilename: | 7z.sfx.exe |
| ProductName: | 7-Zip |
| ProductVersion: | 19.00 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 21-Feb-2019 16:00:00 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000293F5 | 0x00029400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.67671 |
.rdata | 0x0002B000 | 0x00006500 | 0x00006600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.42967 |
.data | 0x00032000 | 0x0000453C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.39005 |
.sxdata | 0x00037000 | 0x00000004 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_LNK_INFO, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.0203931 |
.rsrc | 0x00038000 | 0x00002090 | 0x00002200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.16079 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.40193 | 688 | UNKNOWN | English - United States | RT_VERSION |
2 | 1.68942 | 296 | UNKNOWN | English - United States | RT_ICON |
26 | 1.80688 | 62 | UNKNOWN | English - United States | RT_STRING |
28 | 1.93734 | 66 | UNKNOWN | English - United States | RT_STRING |
29 | 2.18408 | 96 | UNKNOWN | English - United States | RT_STRING |
64 | 1.20724 | 48 | UNKNOWN | English - United States | RT_STRING |
97 | 3.34731 | 1088 | UNKNOWN | English - United States | RT_DIALOG |
188 | 3.1595 | 524 | UNKNOWN | English - United States | RT_STRING |
189 | 2.80372 | 228 | UNKNOWN | English - United States | RT_STRING |
207 | 1.43775 | 52 | UNKNOWN | English - United States | RT_STRING |
Imports
KERNEL32.dll |
MSVCRT.dll |
OLEAUT32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
38
Monitored processes
1
Malicious processes
1
Suspicious processes
0
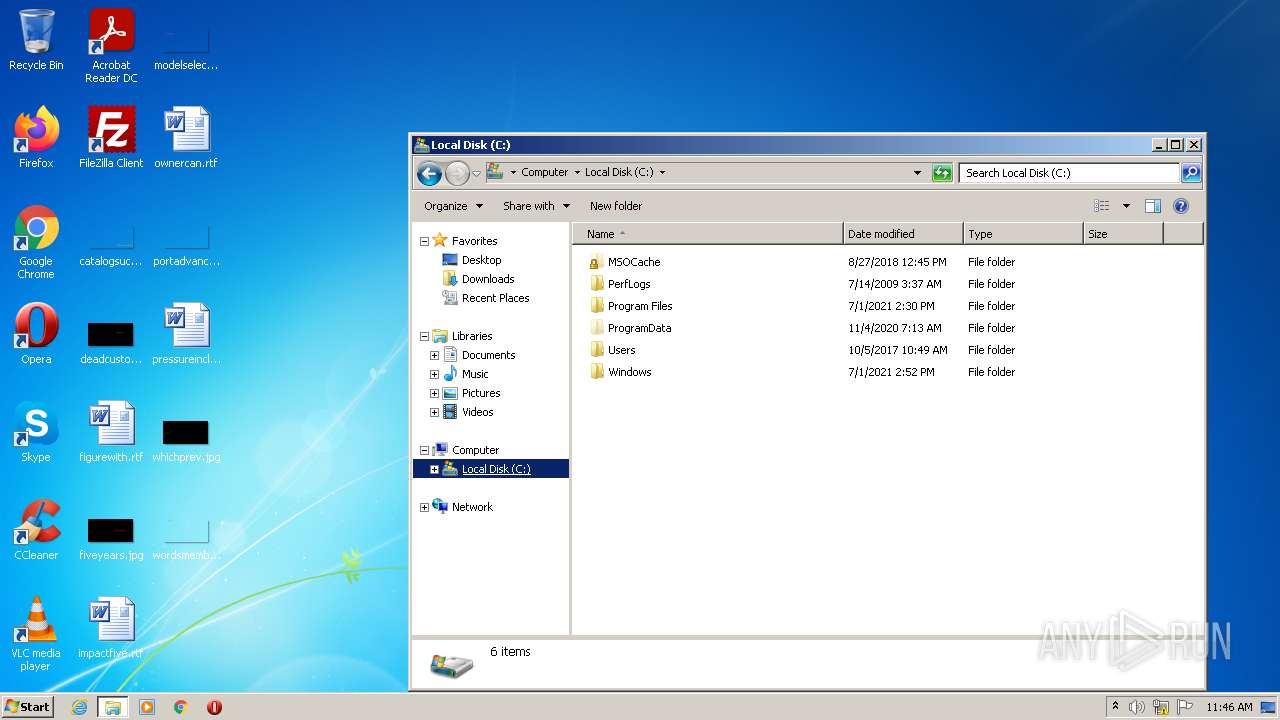
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3024 | "C:\Users\admin\AppData\Local\Temp\DesktopGoose v0.3 Extractor.exe" | C:\Users\admin\AppData\Local\Temp\DesktopGoose v0.3 Extractor.exe | Explorer.EXE | ||||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7z SFX Exit code: 0 Version: 19.00 Modules
| |||||||||||||||
Total events
21
Read events
21
Write events
0
Delete events
0
Modification events
Executable files
9
Suspicious files
2
Text files
34
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3024 | DesktopGoose v0.3 Extractor.exe | C:\Users\admin\AppData\Local\Temp\DesktopGoose v0.3\Assets\Images\Memes\GooseDance.gif | image | |
MD5:B89E8C268B06E14D2DACABADCC1B7BFC | SHA256:F1D46D538348EC2405F3A68291029B062129D8253DE275E22584E22539989E8A | |||
| 3024 | DesktopGoose v0.3 Extractor.exe | C:\Users\admin\AppData\Local\Temp\DesktopGoose v0.3\Assets\Images\MemeAttributions.txt | text | |
MD5:FC280867F6CF727FF169B24371019A93 | SHA256:C6134785BB0927CCE100B3B02EC08EDFA0A3E485F16B2481EE28F8CFAD208AB7 | |||
| 3024 | DesktopGoose v0.3 Extractor.exe | C:\Users\admin\AppData\Local\Temp\DesktopGoose v0.3\Assets\Images\Memes\Meme5.png | image | |
MD5:01F620EDA22AE06FBCC60500374FDD88 | SHA256:F8A5D603018A04375B7B19FE72034F904E6A91237B68E196BD2B626519D6EF03 | |||
| 3024 | DesktopGoose v0.3 Extractor.exe | C:\Users\admin\AppData\Local\Temp\DesktopGoose v0.3\Assets\Images\Memes\Meme4.png | image | |
MD5:AF4BEF7B9F4F37AC62E782B5B59D02AA | SHA256:9FCC9A9ADCD231656E848B9B42BAB449EA5A083CBF3A7A987C2E52963D9CF6D0 | |||
| 3024 | DesktopGoose v0.3 Extractor.exe | C:\Users\admin\AppData\Local\Temp\DesktopGoose v0.3\Assets\Text\NotepadMessages\good work.txt | text | |
MD5:742D0427481D1A2C7171C4BD931BBA03 | SHA256:8DE6495CF102AB13B0189635CF4B6C8376EA8ED879AD32D885D52D01B1C5A6F6 | |||
| 3024 | DesktopGoose v0.3 Extractor.exe | C:\Users\admin\AppData\Local\Temp\DesktopGoose v0.3\Assets\Images\Memes\Meme6.png | image | |
MD5:E46D6D7154CEBF37D064C537F5D01F36 | SHA256:A078C89DE64C606313E251122A4D6025FF3F76CD941F1FB2195938E6173CF9F1 | |||
| 3024 | DesktopGoose v0.3 Extractor.exe | C:\Users\admin\AppData\Local\Temp\DesktopGoose v0.3\Assets\Images\OtherGfx\heart.png | image | |
MD5:76F468AA187E5C042C7EF5AE6A8A0753 | SHA256:11AE0A796817293FA0FB66978614A0BB87D249299AB4A75439BF56502358C0ED | |||
| 3024 | DesktopGoose v0.3 Extractor.exe | C:\Users\admin\AppData\Local\Temp\DesktopGoose v0.3\Assets\Images\Memes\Meme1.png | image | |
MD5:EC6A7941AA0D1C3CD0A7B724324FBB96 | SHA256:FE5EE195C07EBFC789F15CE771CC0F003AE43C0D5115C193D0F876DE00C18DBE | |||
| 3024 | DesktopGoose v0.3 Extractor.exe | C:\Users\admin\AppData\Local\Temp\DesktopGoose v0.3\Assets\Images\Memes\Meme3.png | image | |
MD5:CEF6B9818BC01655614FB969CFFC155F | SHA256:37BC0E217C6D6BF3EAF31072C02F010E785F4935ABE9849FBEE96D586D0904A7 | |||
| 3024 | DesktopGoose v0.3 Extractor.exe | C:\Users\admin\AppData\Local\Temp\DesktopGoose v0.3\Assets\Sound\NotEmbedded\BITE.mp3 | mp3 | |
MD5:5436E6AEBABF071C1D832071A01B8BCD | SHA256:2BF822B86E4ADABCE83A796DE15FBBFEB75FF82C3BC1ED2A0F5286962915D362 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.2:53 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.microsoft.com |
| whitelisted |