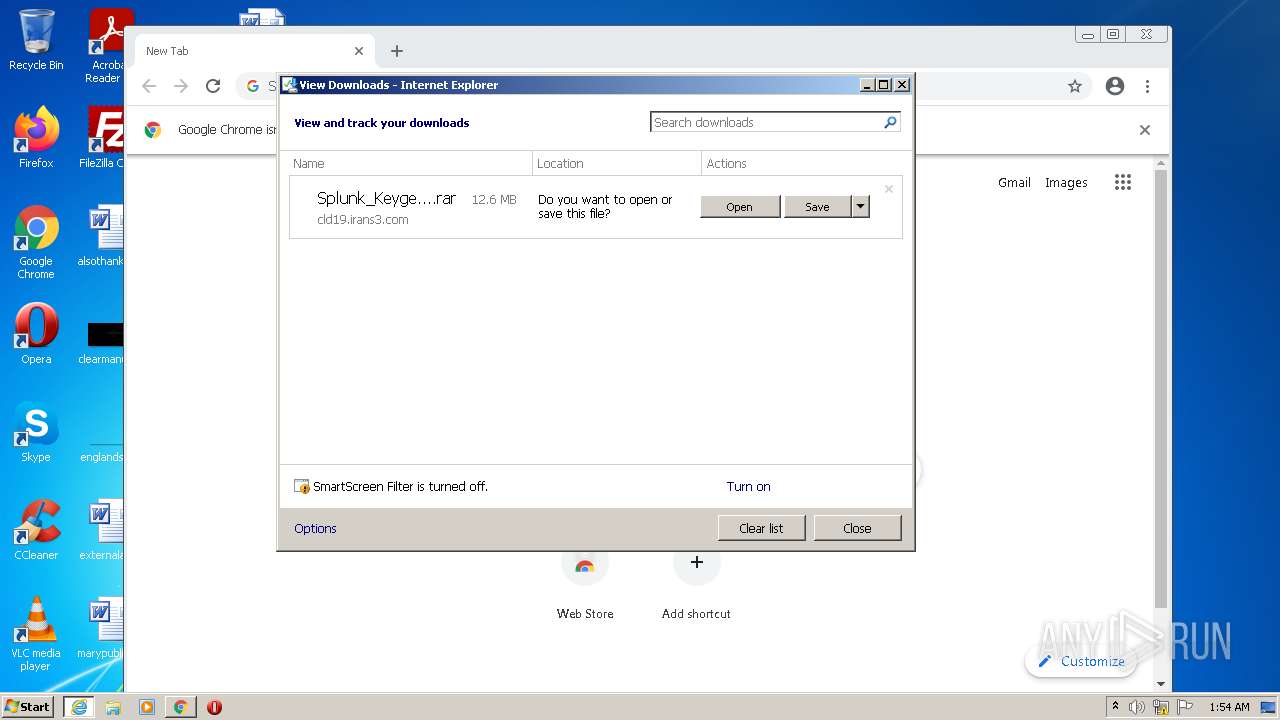
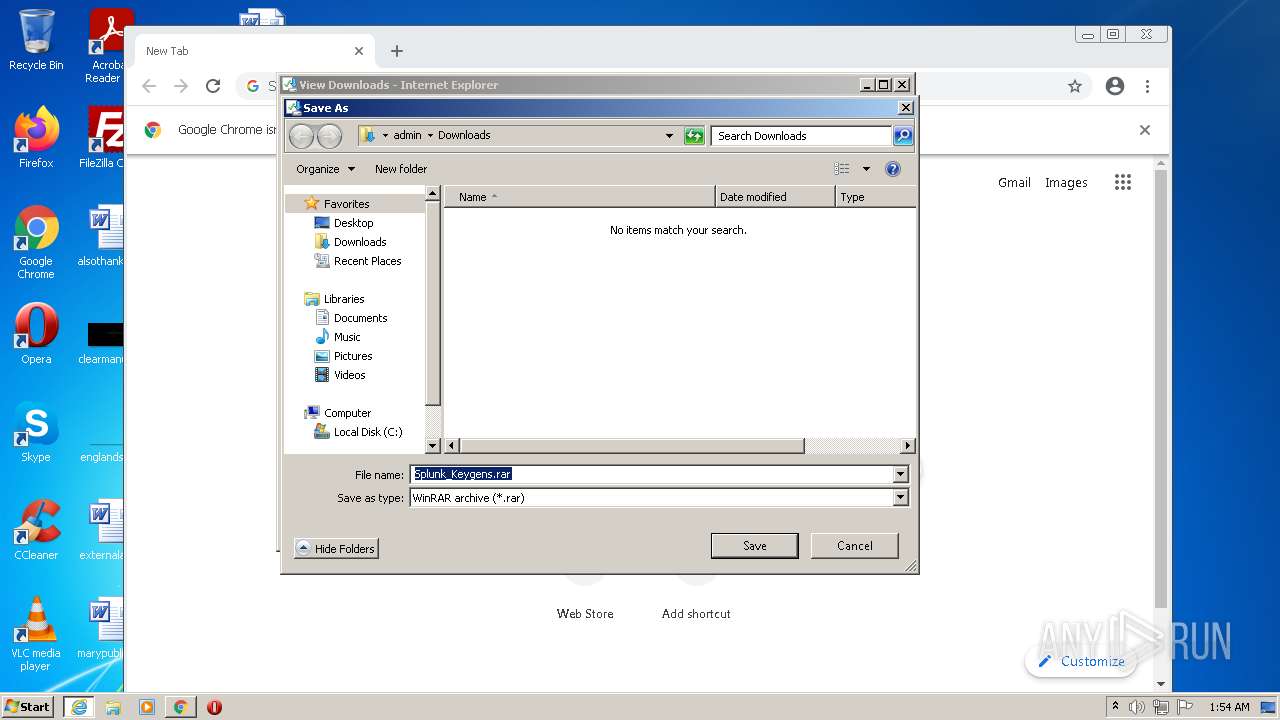
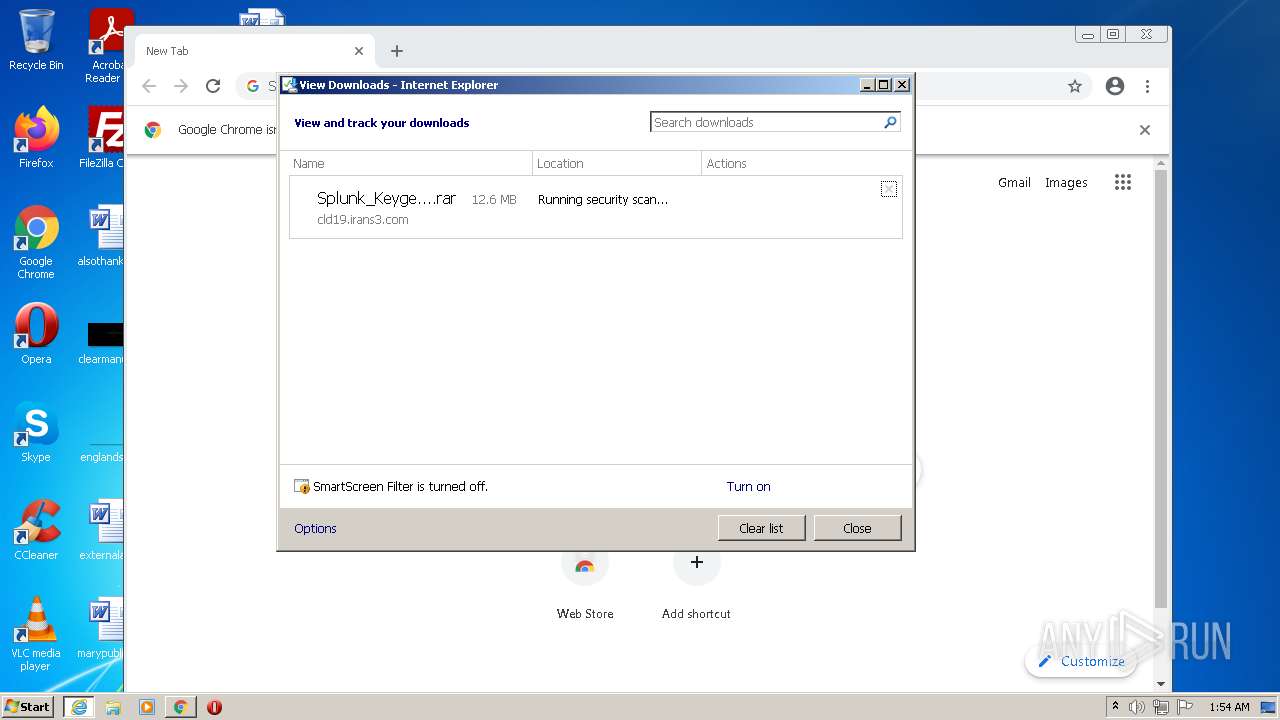
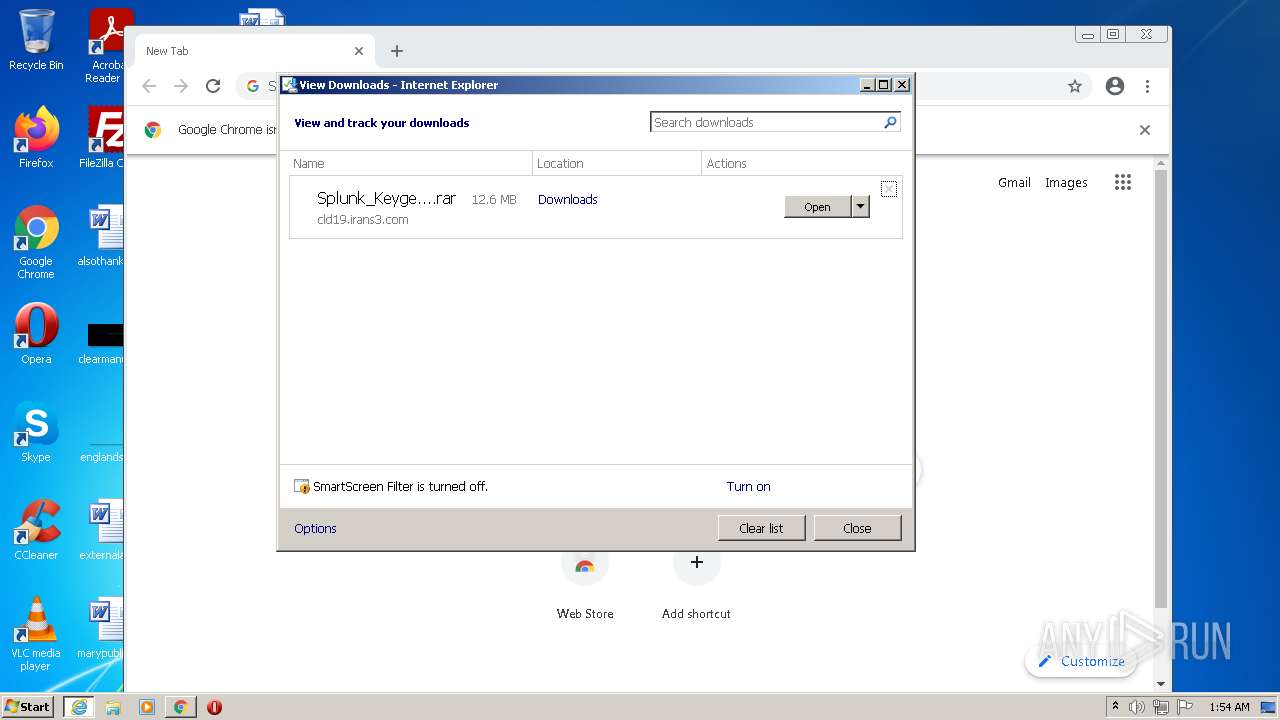
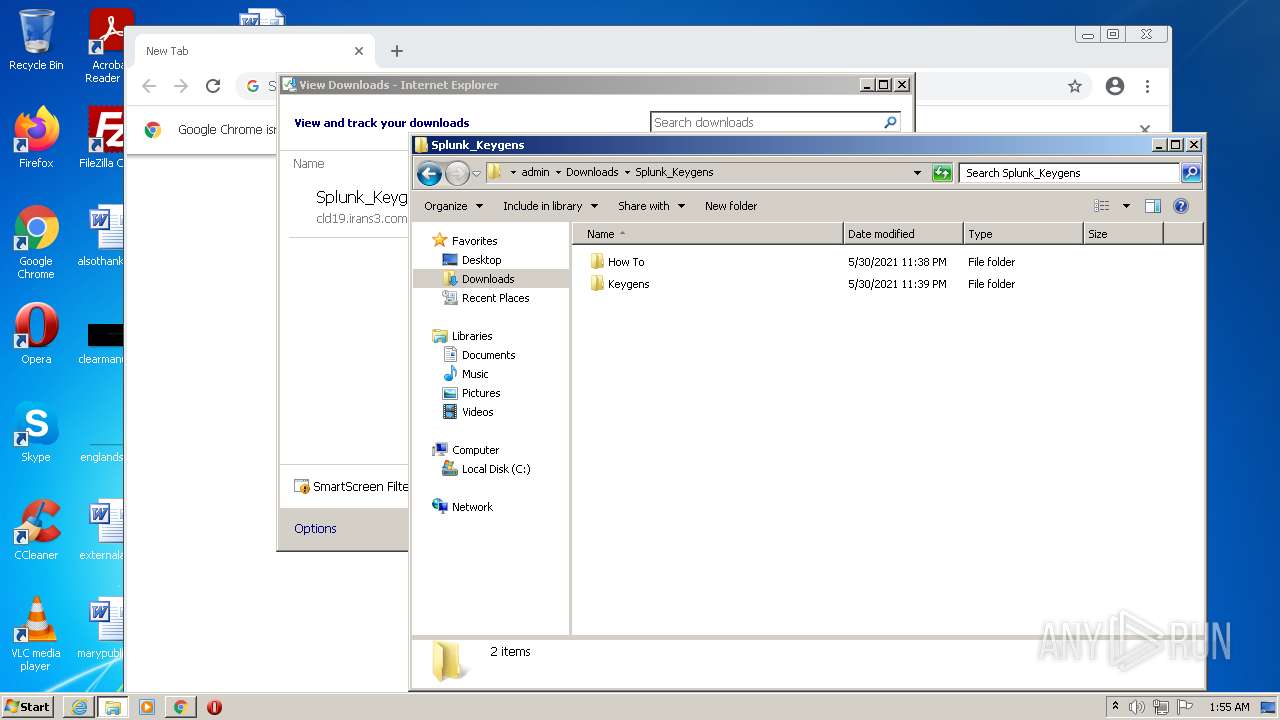
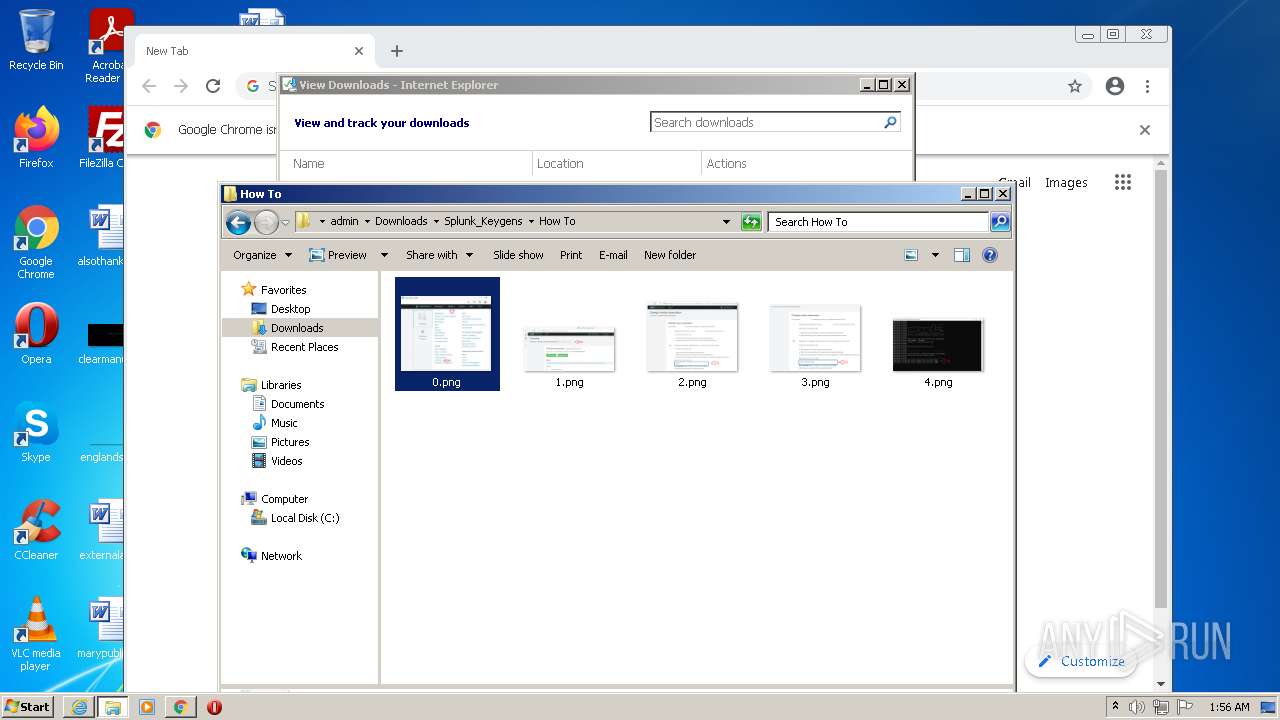
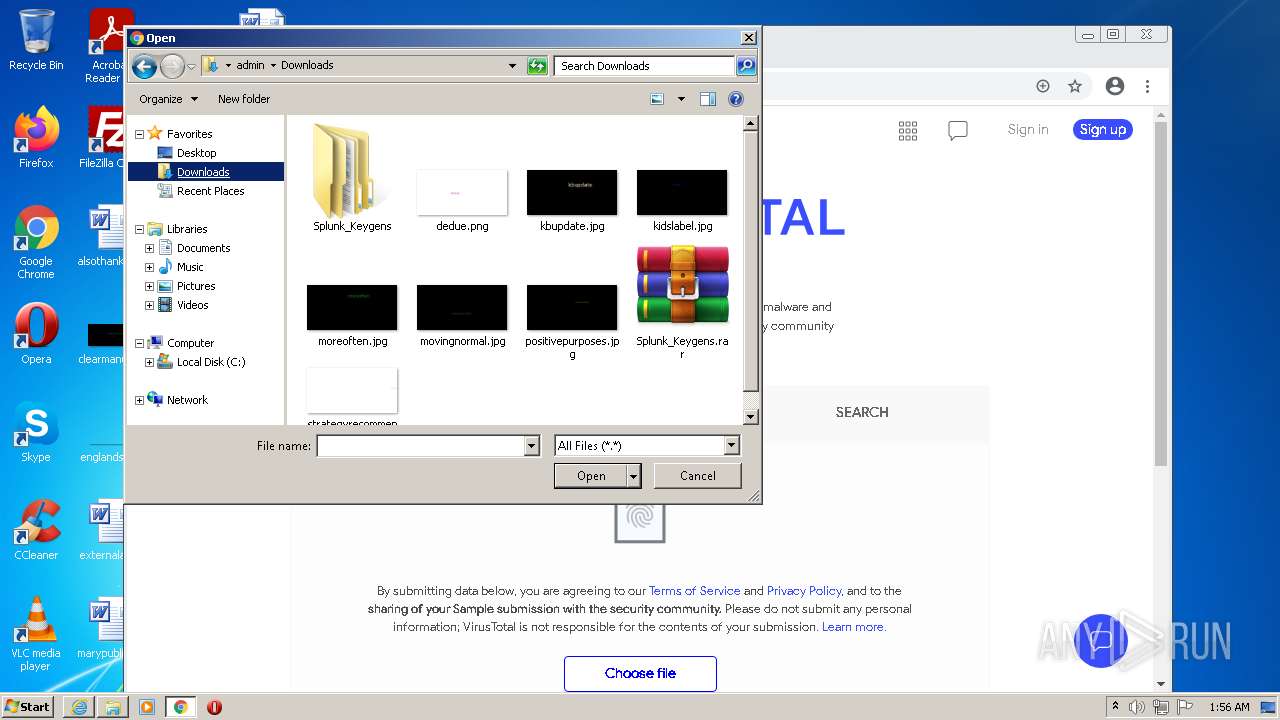
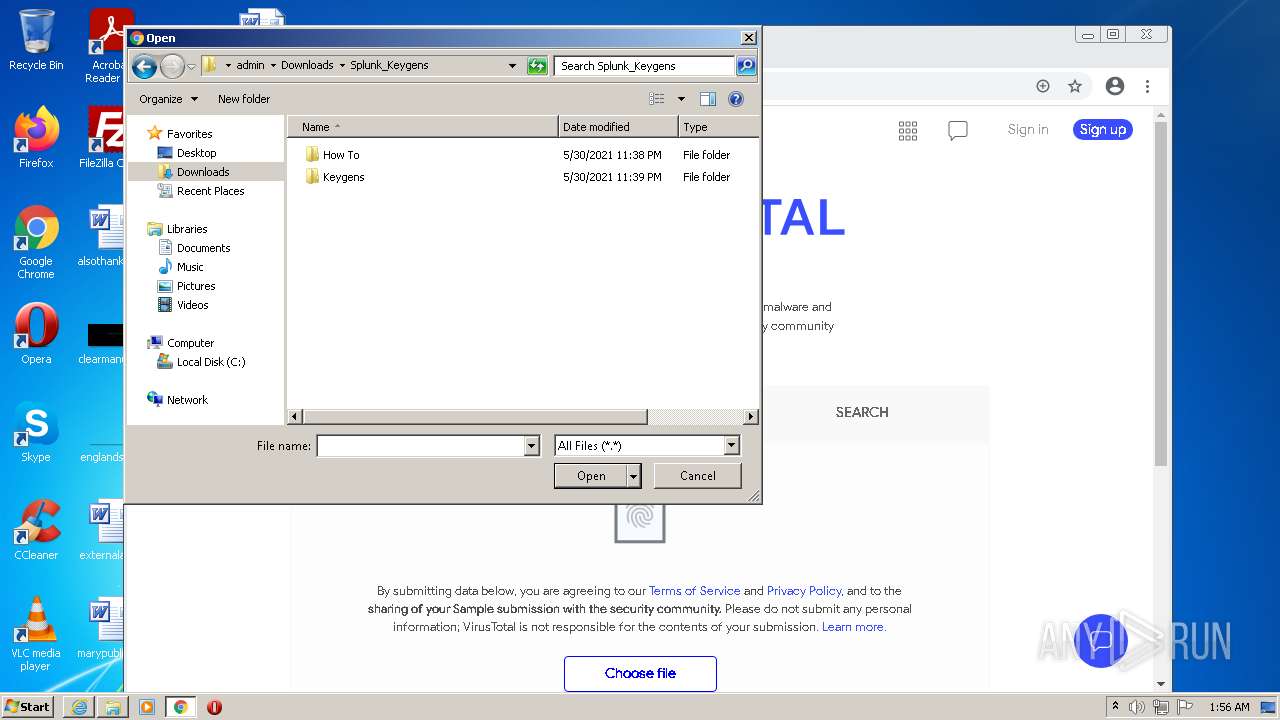
| URL: | https://cdn.digiboy.ir/?b=dlir-s3&f=Splunk_Keygens.rar |
| Full analysis: | https://app.any.run/tasks/8d5b4a86-7482-4447-a0b8-53f25c2cd5ba |
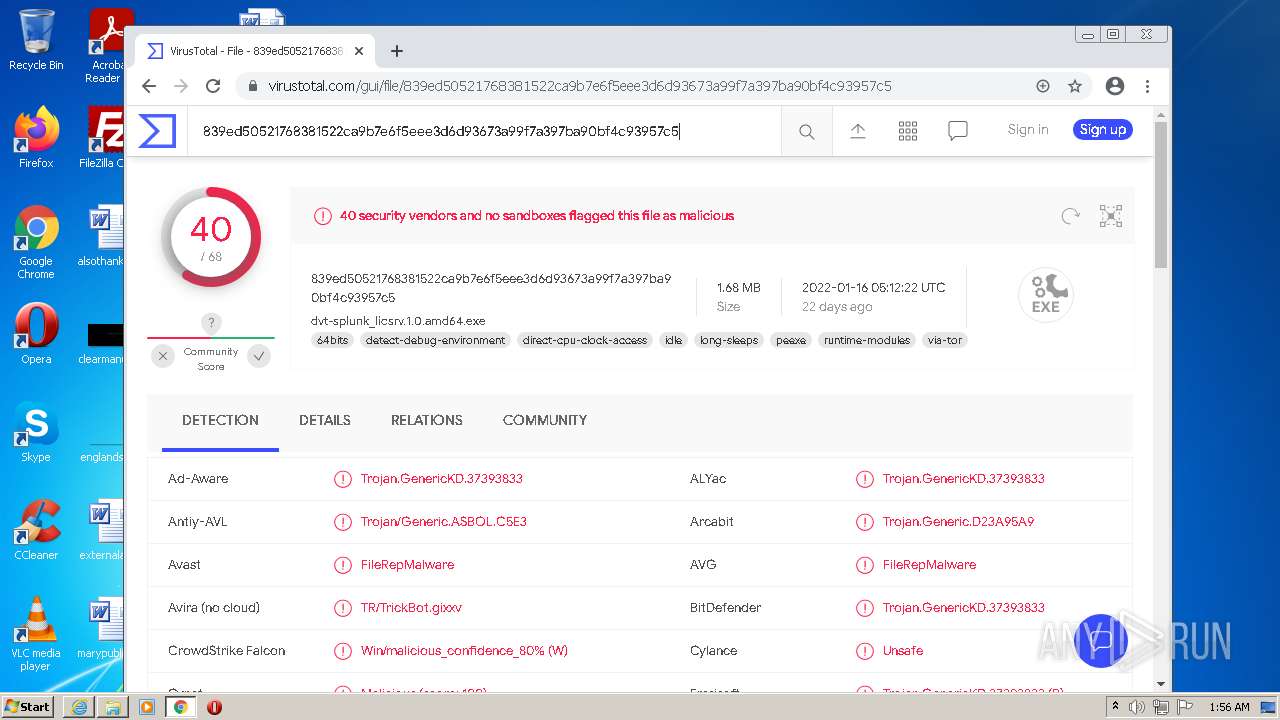
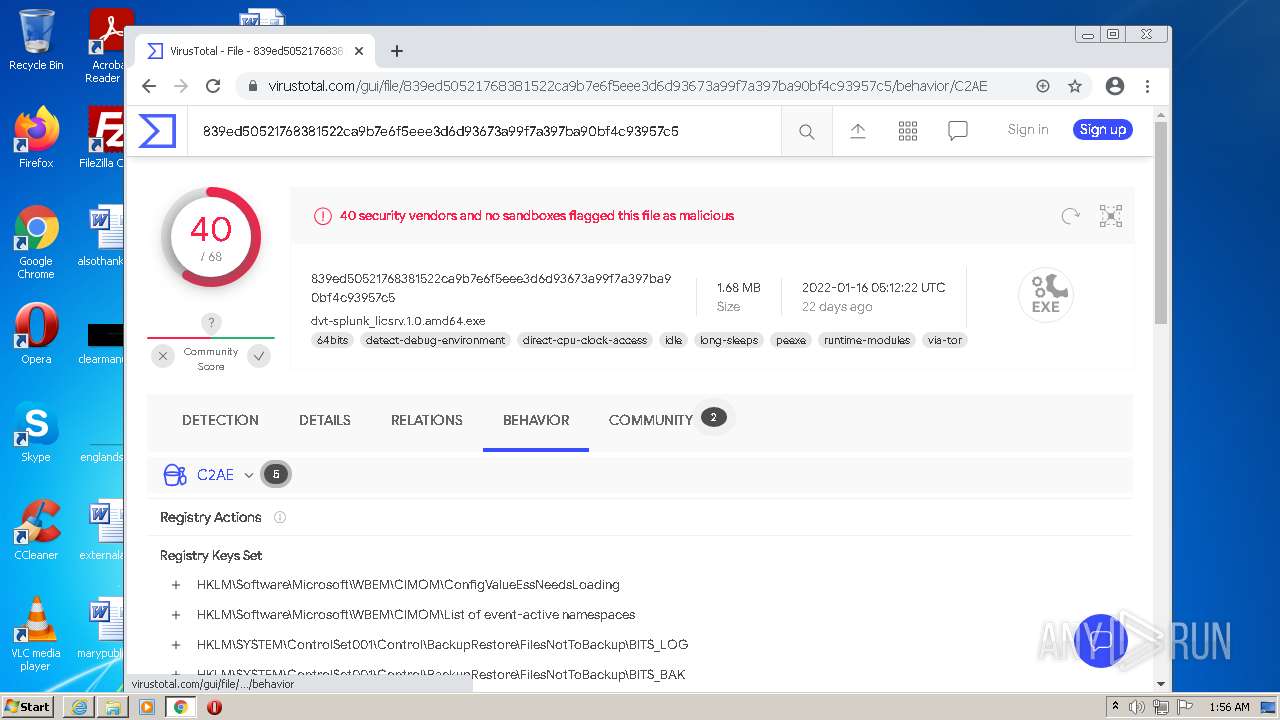
| Verdict: | Malicious activity |
| Analysis date: | February 08, 2022, 01:54:30 |
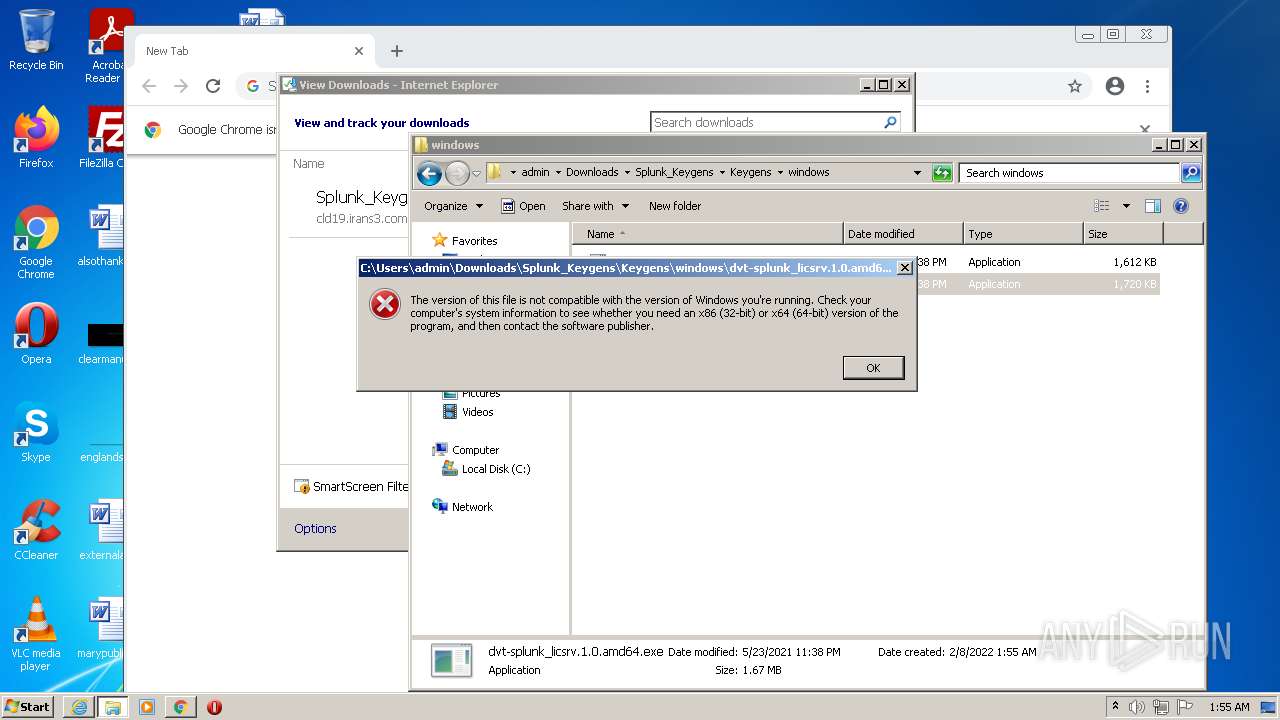
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | FE5BA14DD1ACD21A213AB16884790AEA |
| SHA1: | ADFAA722ABF2780117BB7D4753E8D4052F0E45FC |
| SHA256: | 2D92B95AD194D058D8EB86308D735669F2E6CF95EA3F0275F388D74EBC567134 |
| SSDEEP: | 3:N8cCCoMs/DWOFxLWj+n:2cF+D9Wj+n |
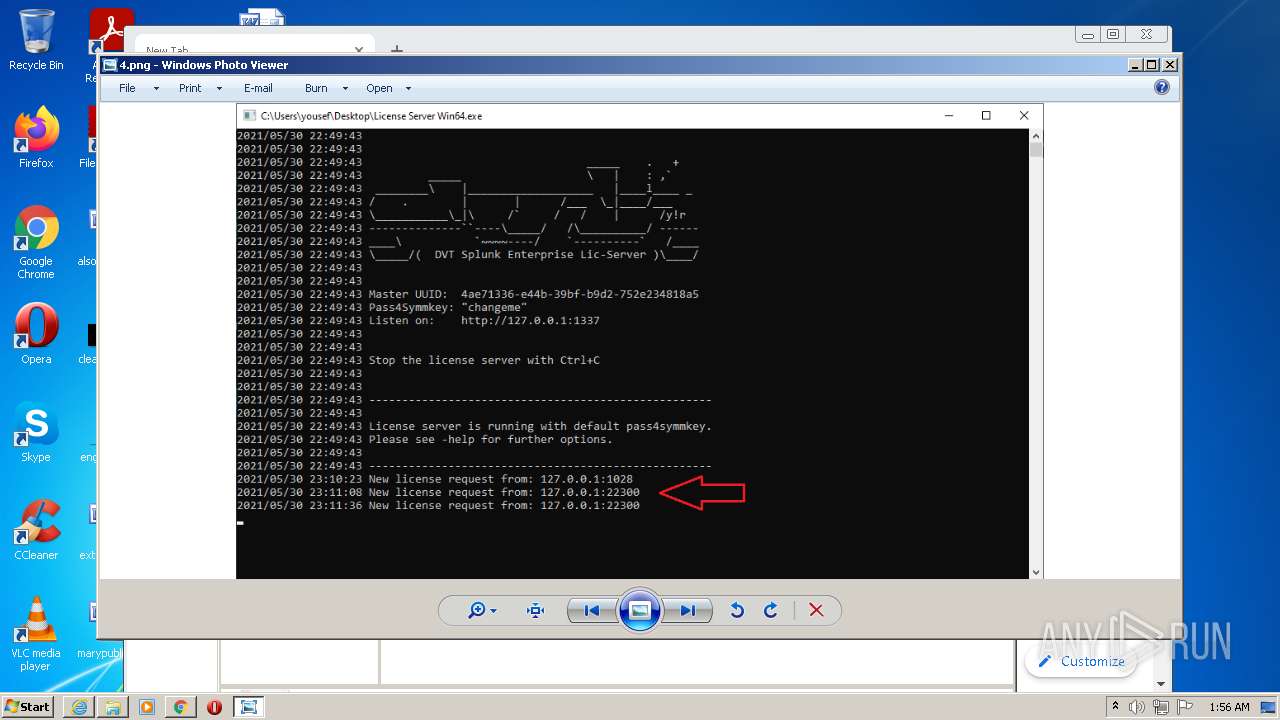
MALICIOUS
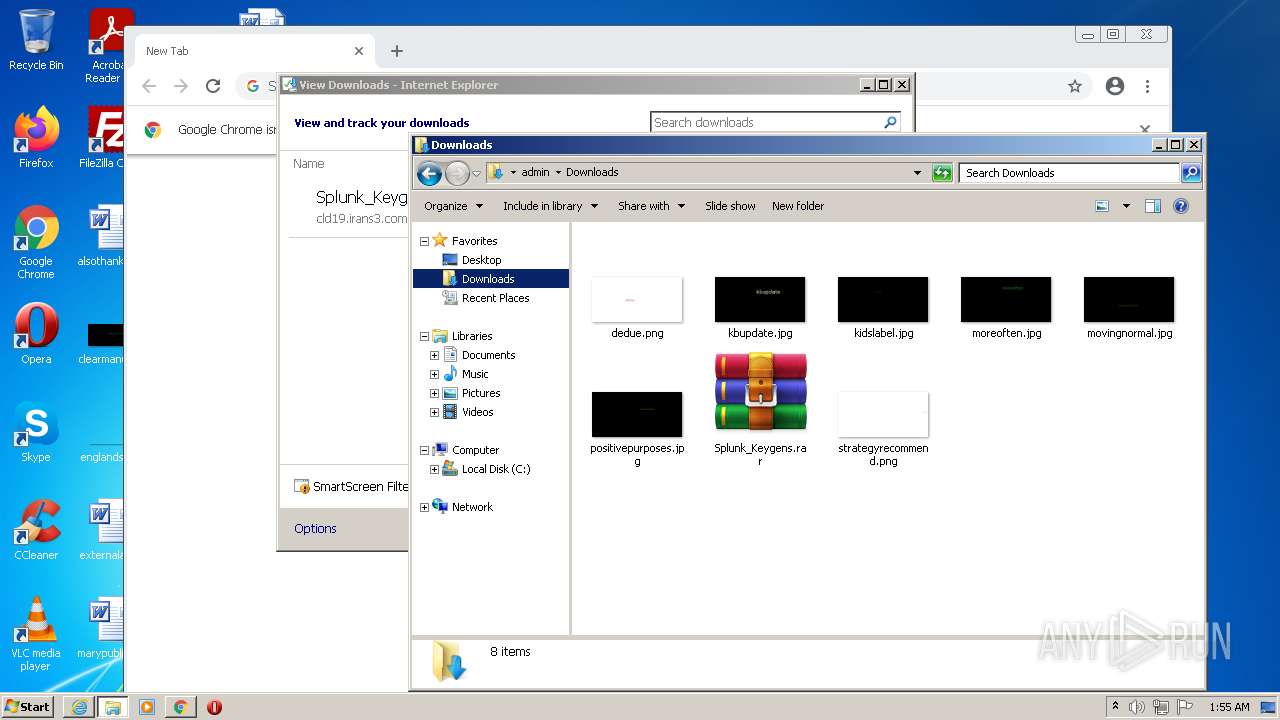
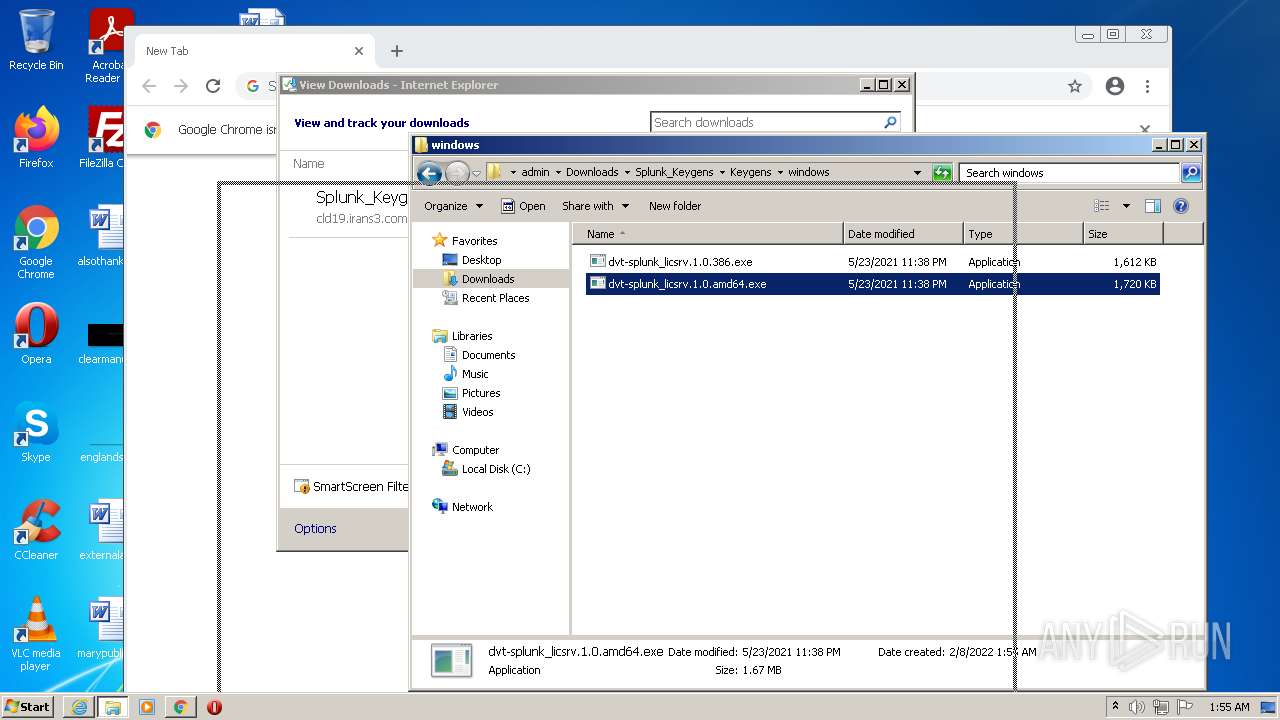
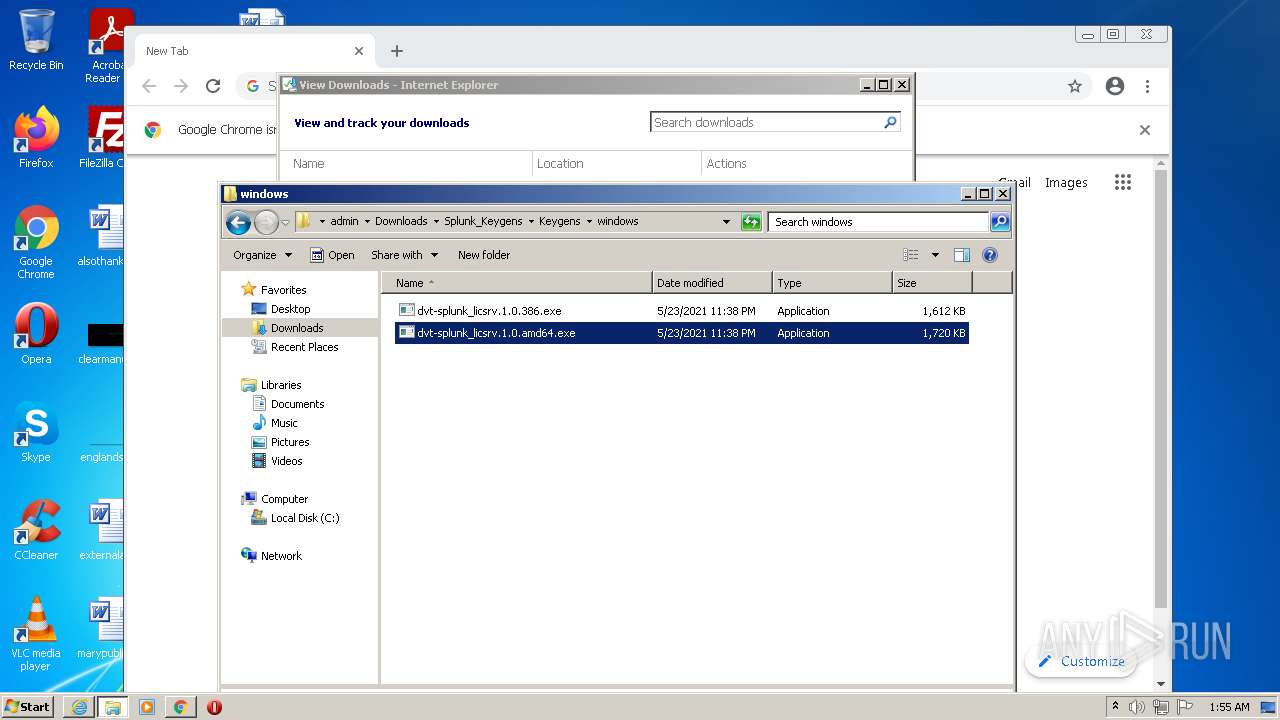
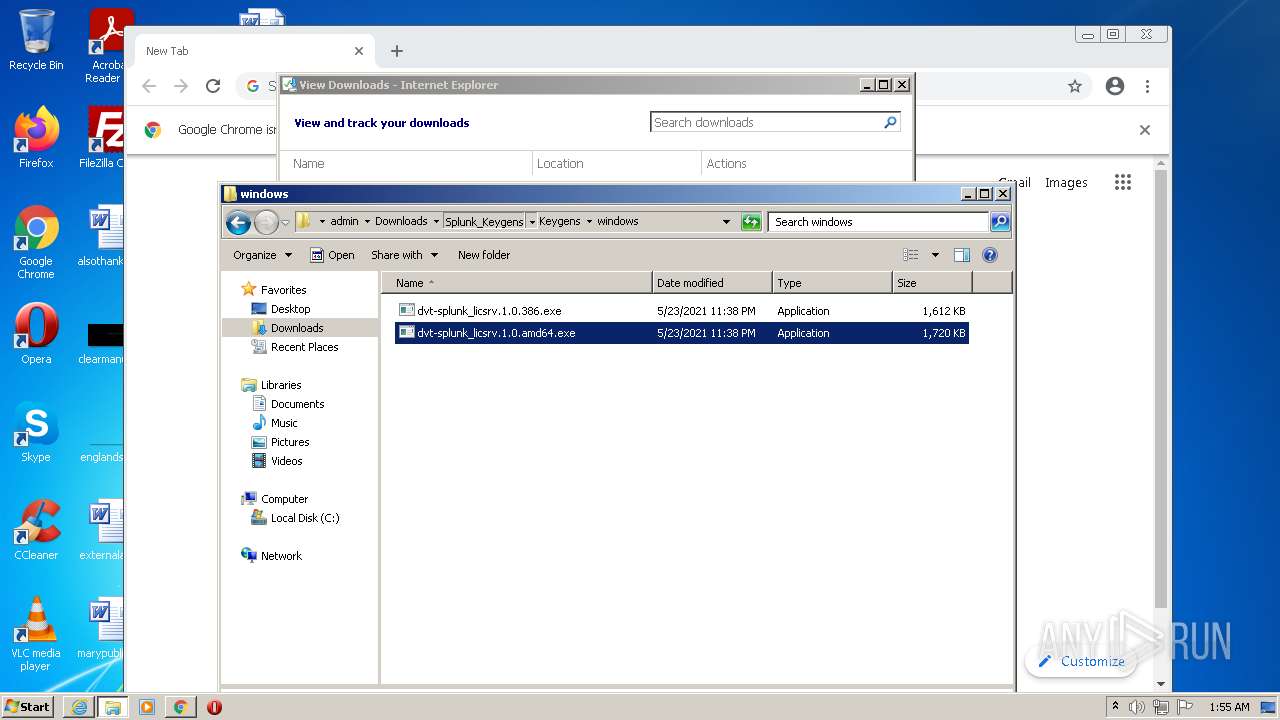
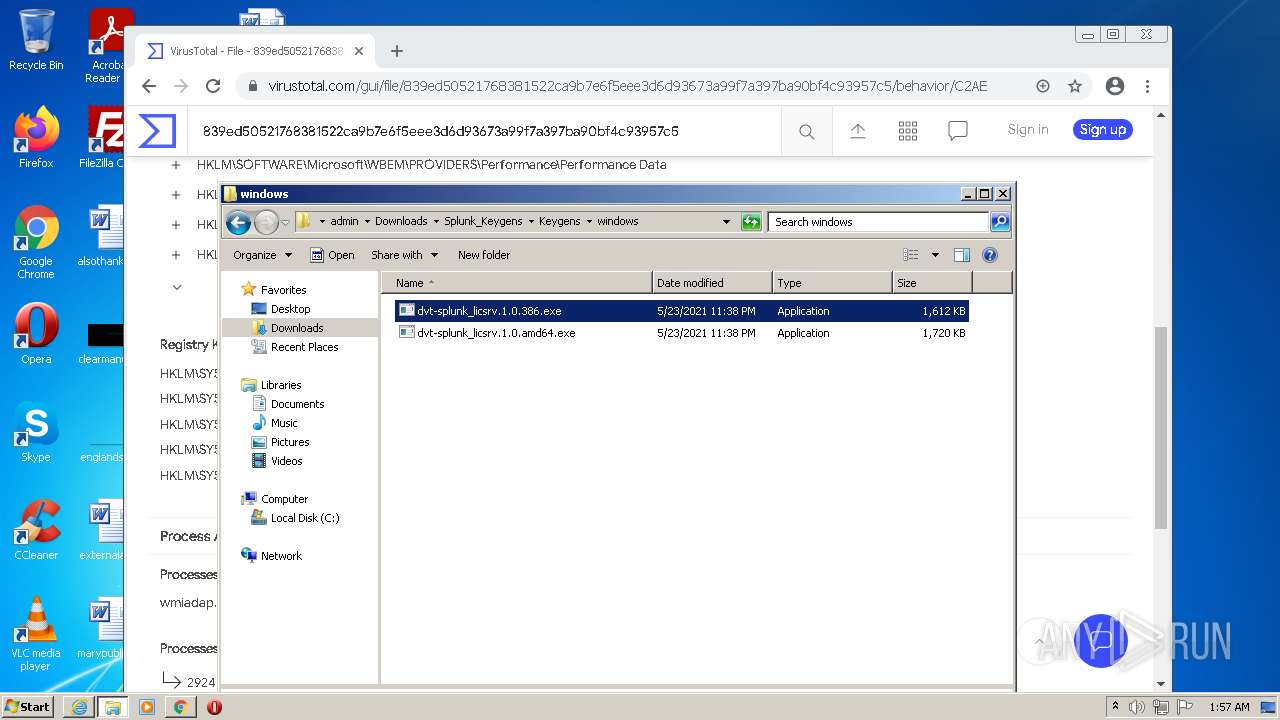
Drops executable file immediately after starts
- chrome.exe (PID: 3320)
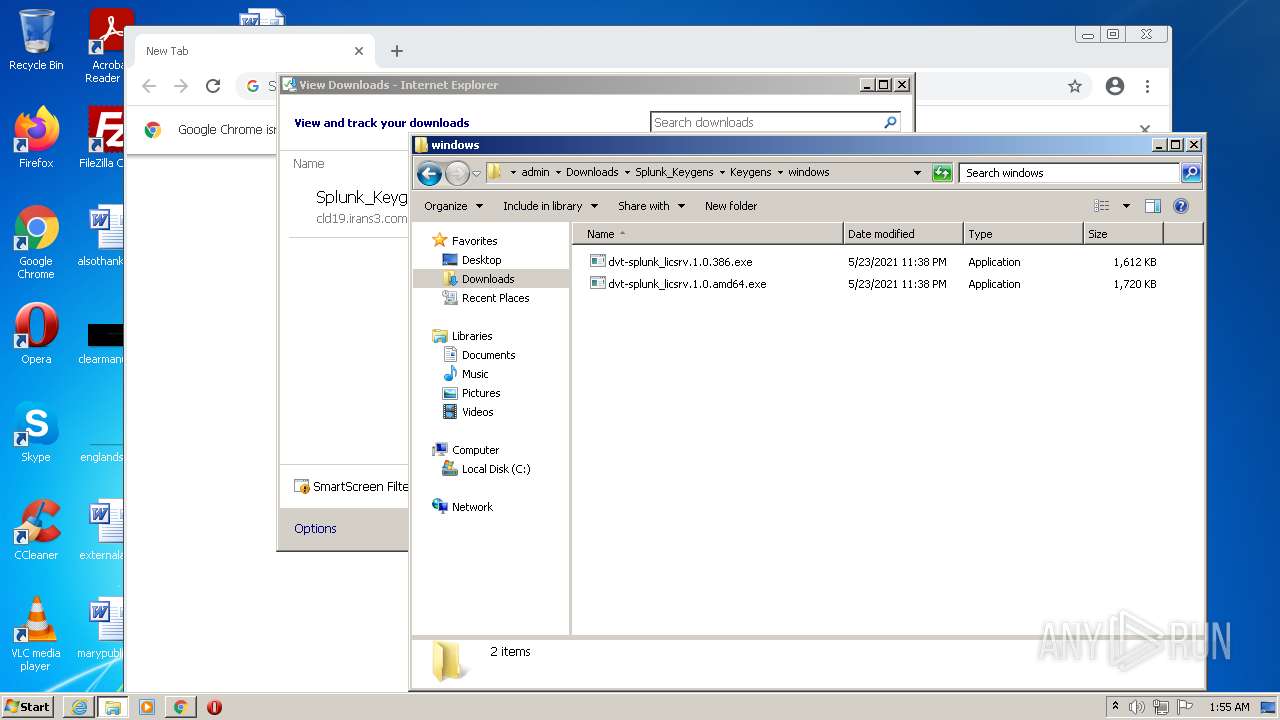
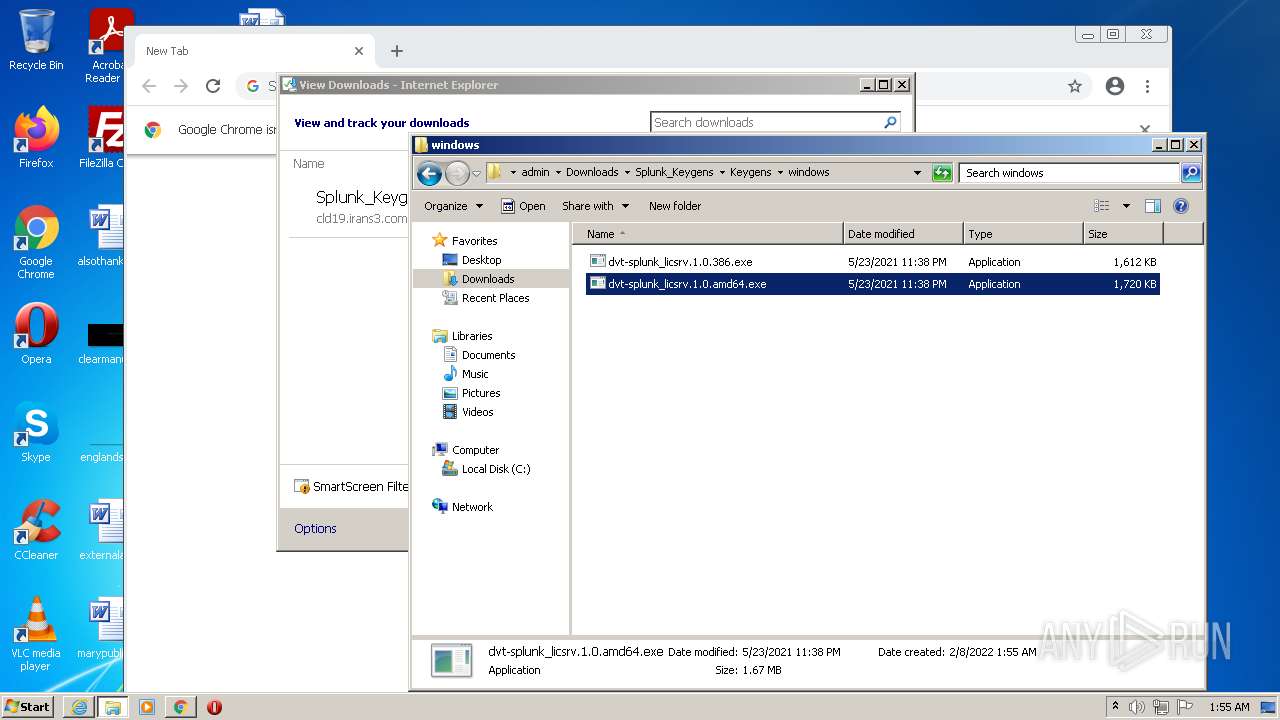
Application was dropped or rewritten from another process
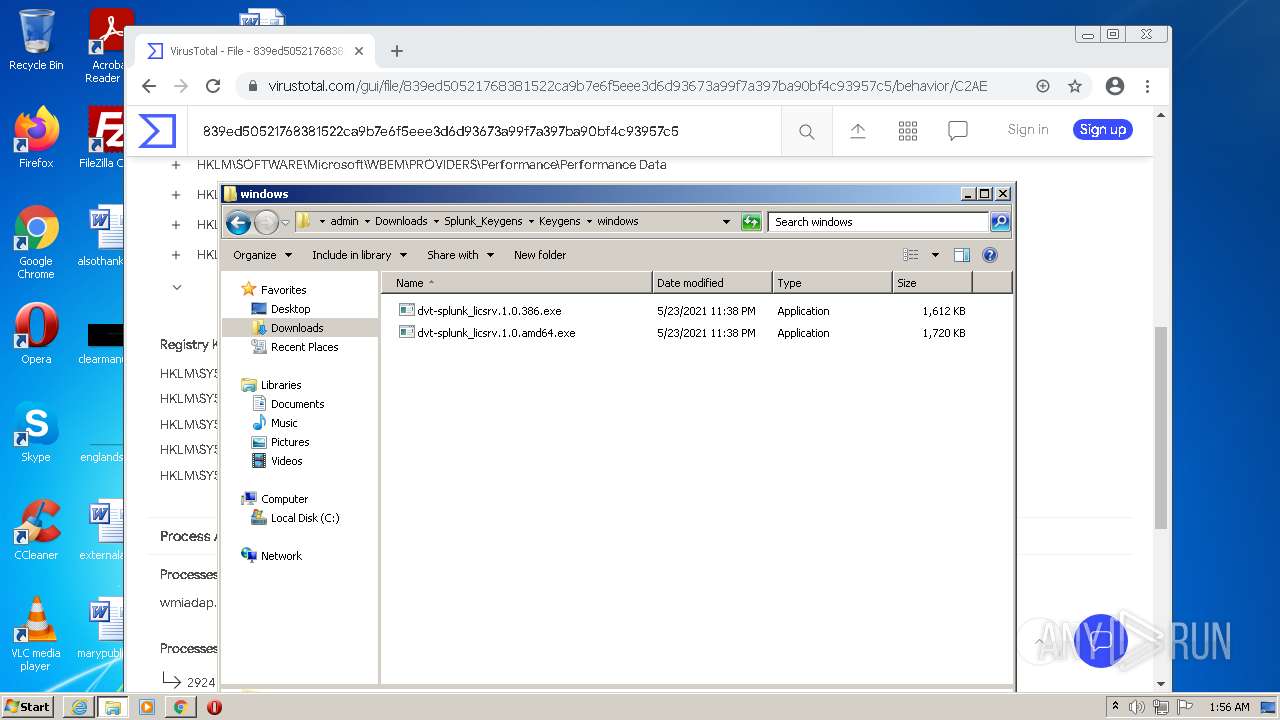
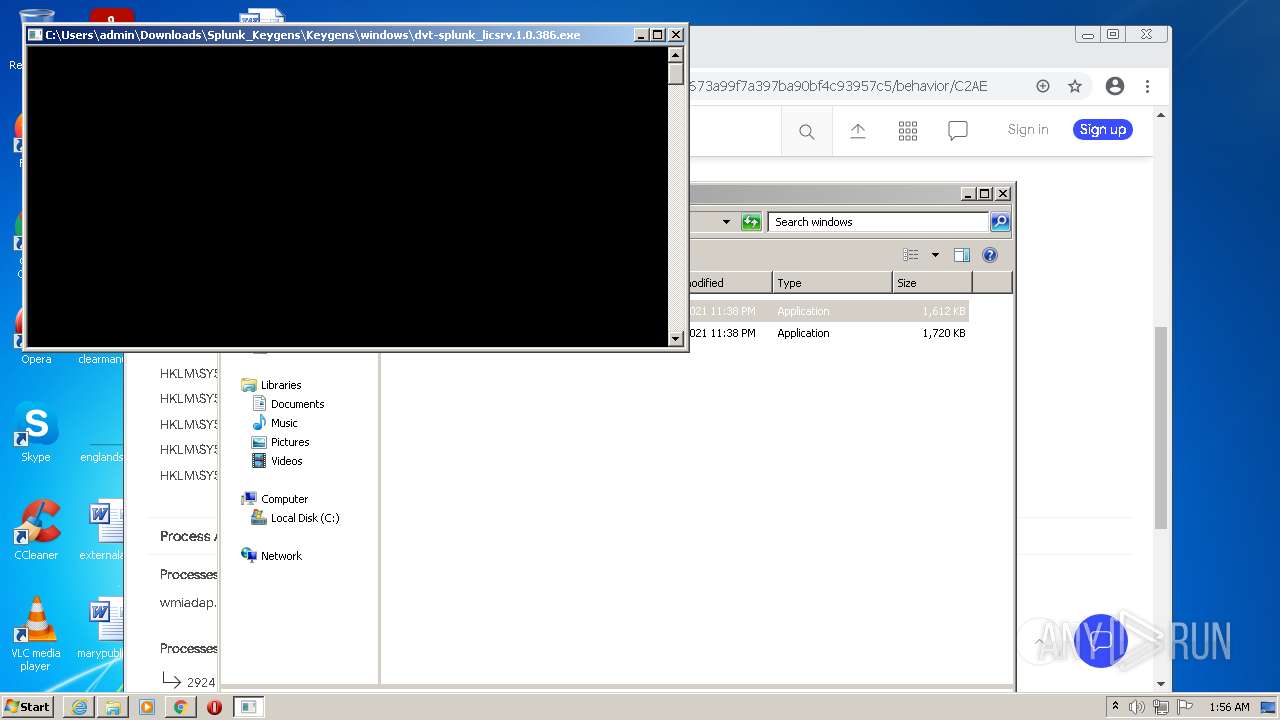
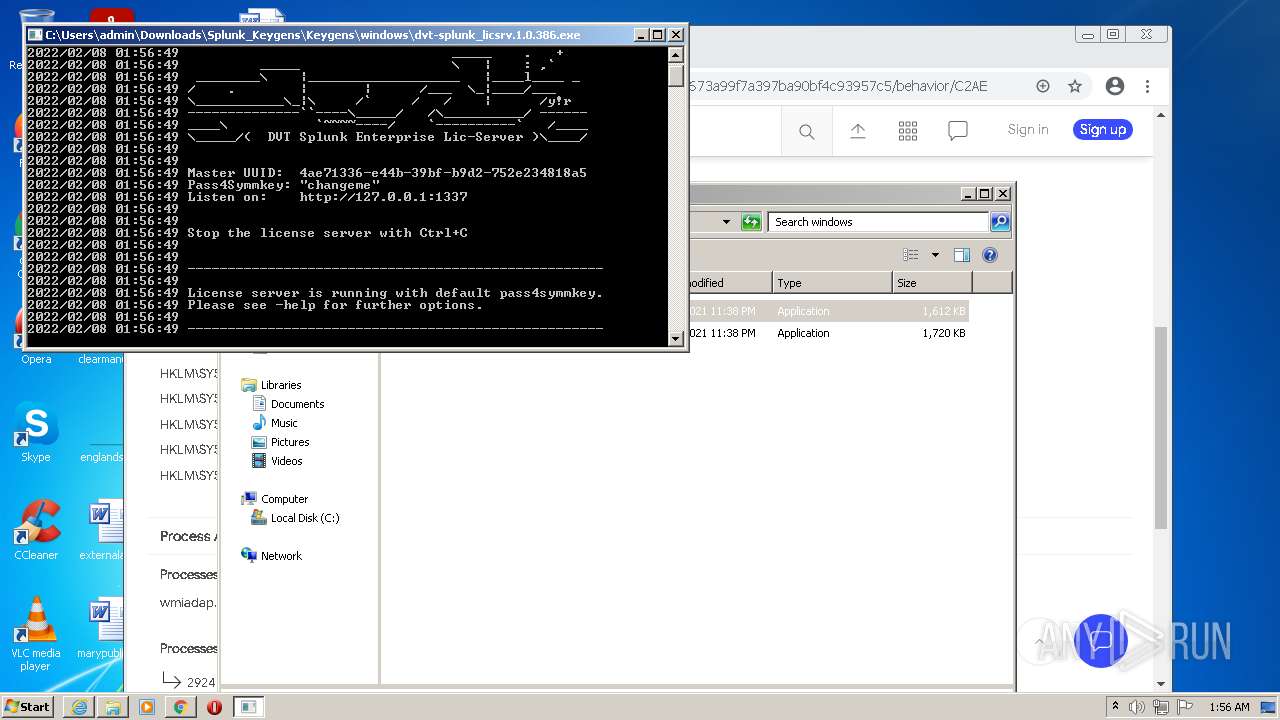
- dvt-splunk_licsrv.1.0.386.exe (PID: 3924)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3436)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2332)
Reads the computer name
- WinRAR.exe (PID: 1812)
Checks supported languages
- WinRAR.exe (PID: 1812)
- dvt-splunk_licsrv.1.0.386.exe (PID: 3924)
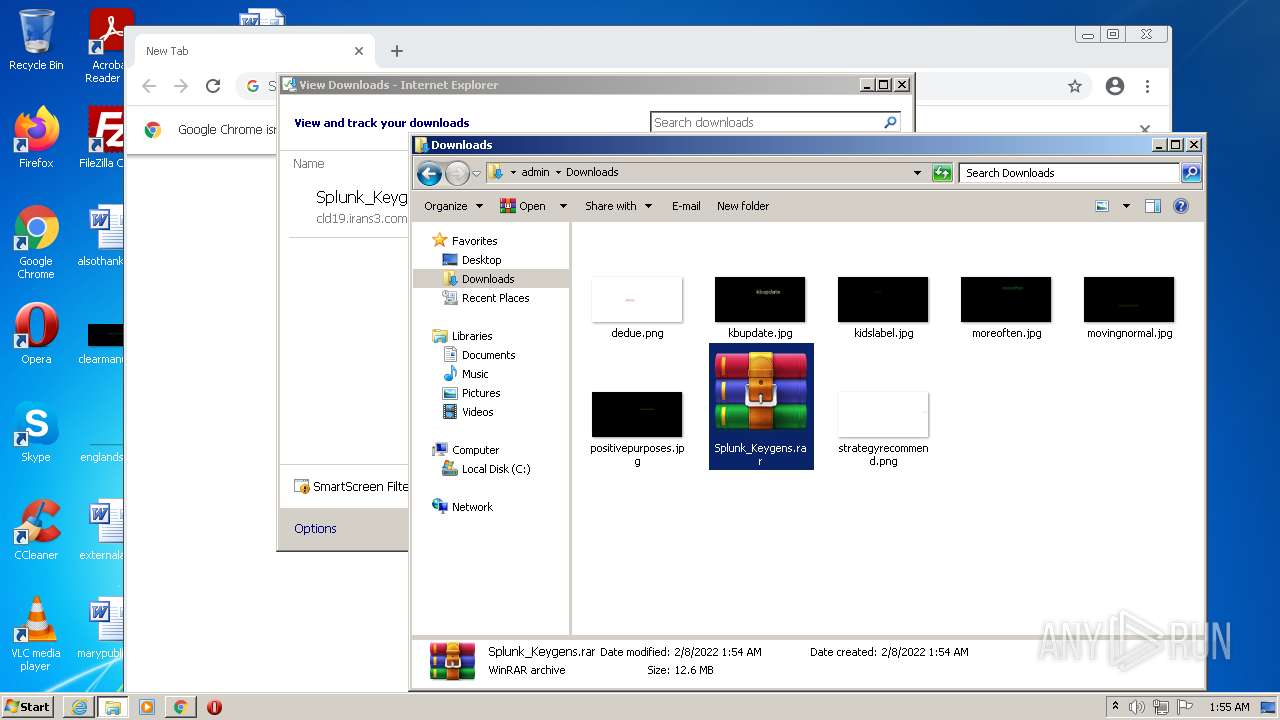
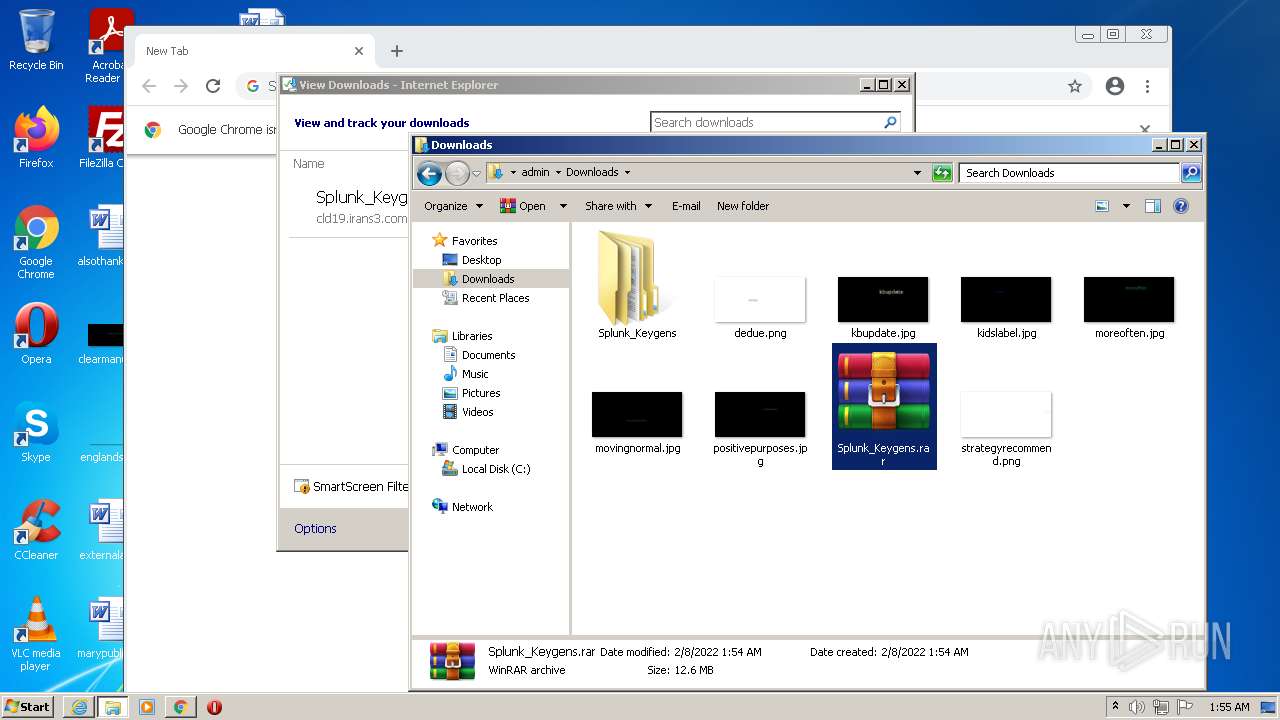
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1812)
- chrome.exe (PID: 3320)
Drops a file with too old compile date
- WinRAR.exe (PID: 1812)
Executed via COM
- DllHost.exe (PID: 3284)
Reads default file associations for system extensions
- chrome.exe (PID: 2140)
Drops a file that was compiled in debug mode
- chrome.exe (PID: 3320)
INFO
Reads the computer name
- iexplore.exe (PID: 3928)
- iexplore.exe (PID: 3436)
- chrome.exe (PID: 2332)
- chrome.exe (PID: 2148)
- chrome.exe (PID: 2084)
- chrome.exe (PID: 3616)
- chrome.exe (PID: 2680)
- explorer.exe (PID: 3440)
- chrome.exe (PID: 1628)
- chrome.exe (PID: 2064)
- chrome.exe (PID: 2596)
- DllHost.exe (PID: 3284)
- chrome.exe (PID: 2140)
Checks supported languages
- iexplore.exe (PID: 3928)
- iexplore.exe (PID: 3436)
- chrome.exe (PID: 2084)
- chrome.exe (PID: 2332)
- chrome.exe (PID: 2148)
- chrome.exe (PID: 3140)
- chrome.exe (PID: 2152)
- chrome.exe (PID: 520)
- chrome.exe (PID: 2460)
- chrome.exe (PID: 2112)
- chrome.exe (PID: 2680)
- chrome.exe (PID: 1464)
- chrome.exe (PID: 1612)
- chrome.exe (PID: 3616)
- chrome.exe (PID: 1184)
- explorer.exe (PID: 3440)
- chrome.exe (PID: 3432)
- chrome.exe (PID: 1628)
- chrome.exe (PID: 2064)
- DllHost.exe (PID: 3284)
- chrome.exe (PID: 3440)
- chrome.exe (PID: 2596)
- chrome.exe (PID: 2580)
- chrome.exe (PID: 2232)
- chrome.exe (PID: 2908)
- chrome.exe (PID: 272)
- chrome.exe (PID: 2892)
- chrome.exe (PID: 3388)
- chrome.exe (PID: 2352)
- chrome.exe (PID: 2400)
- chrome.exe (PID: 2936)
- chrome.exe (PID: 2708)
- chrome.exe (PID: 3396)
- chrome.exe (PID: 2812)
- chrome.exe (PID: 2444)
- chrome.exe (PID: 1960)
- chrome.exe (PID: 3628)
- chrome.exe (PID: 3668)
- chrome.exe (PID: 2140)
- chrome.exe (PID: 2924)
- chrome.exe (PID: 2796)
- chrome.exe (PID: 1572)
- chrome.exe (PID: 3320)
- chrome.exe (PID: 2588)
- chrome.exe (PID: 2320)
Changes internet zones settings
- iexplore.exe (PID: 3928)
Checks Windows Trust Settings
- iexplore.exe (PID: 3436)
- iexplore.exe (PID: 3928)
Reads settings of System Certificates
- iexplore.exe (PID: 3436)
- iexplore.exe (PID: 3928)
- chrome.exe (PID: 2148)
Application launched itself
- iexplore.exe (PID: 3928)
- chrome.exe (PID: 2332)
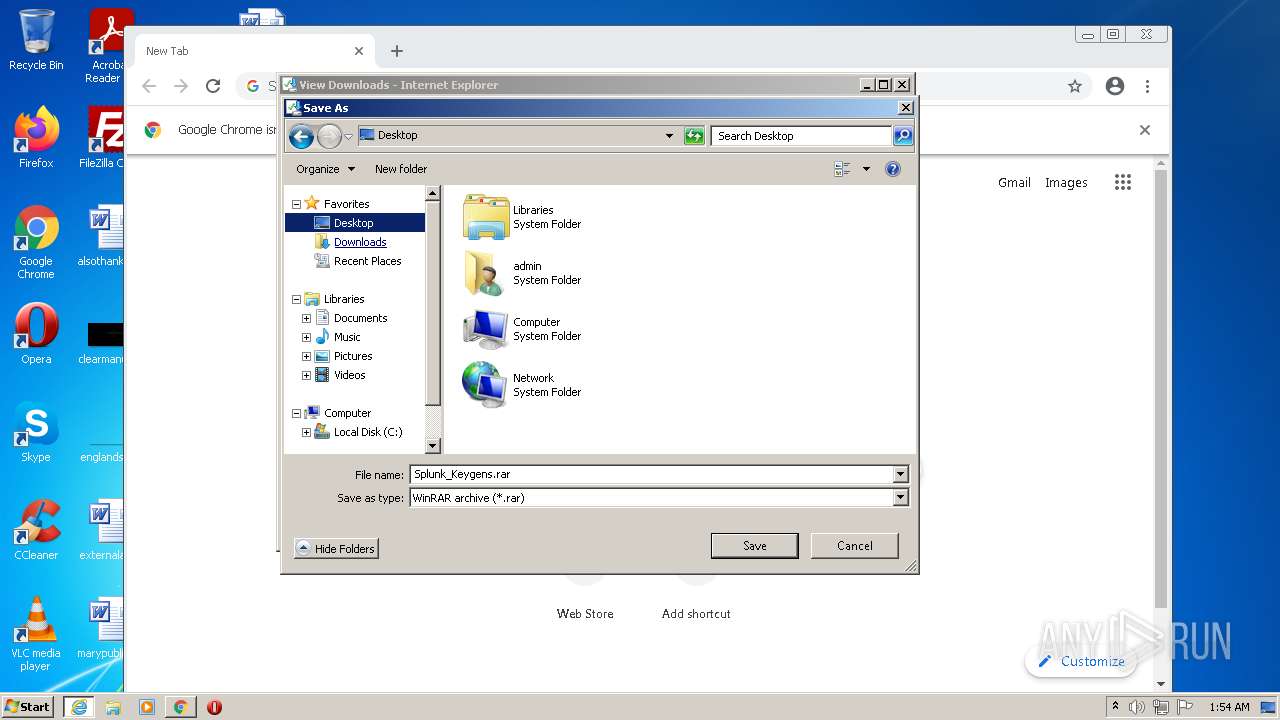
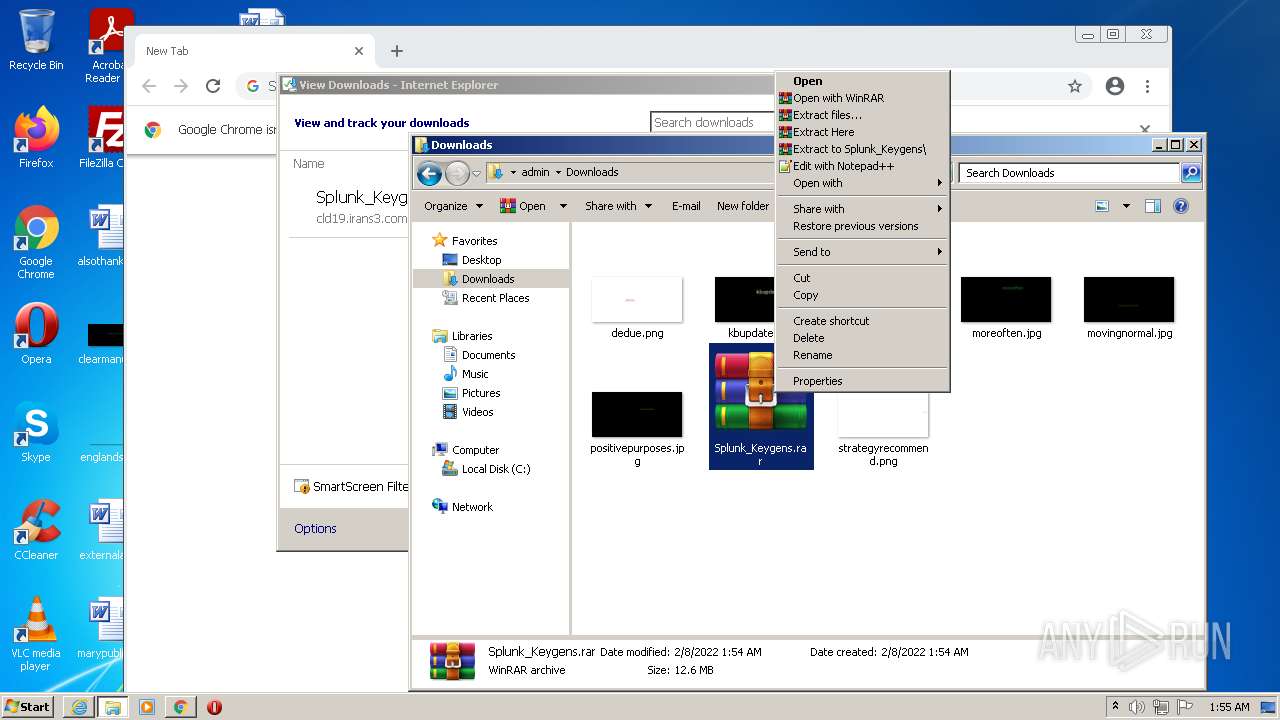
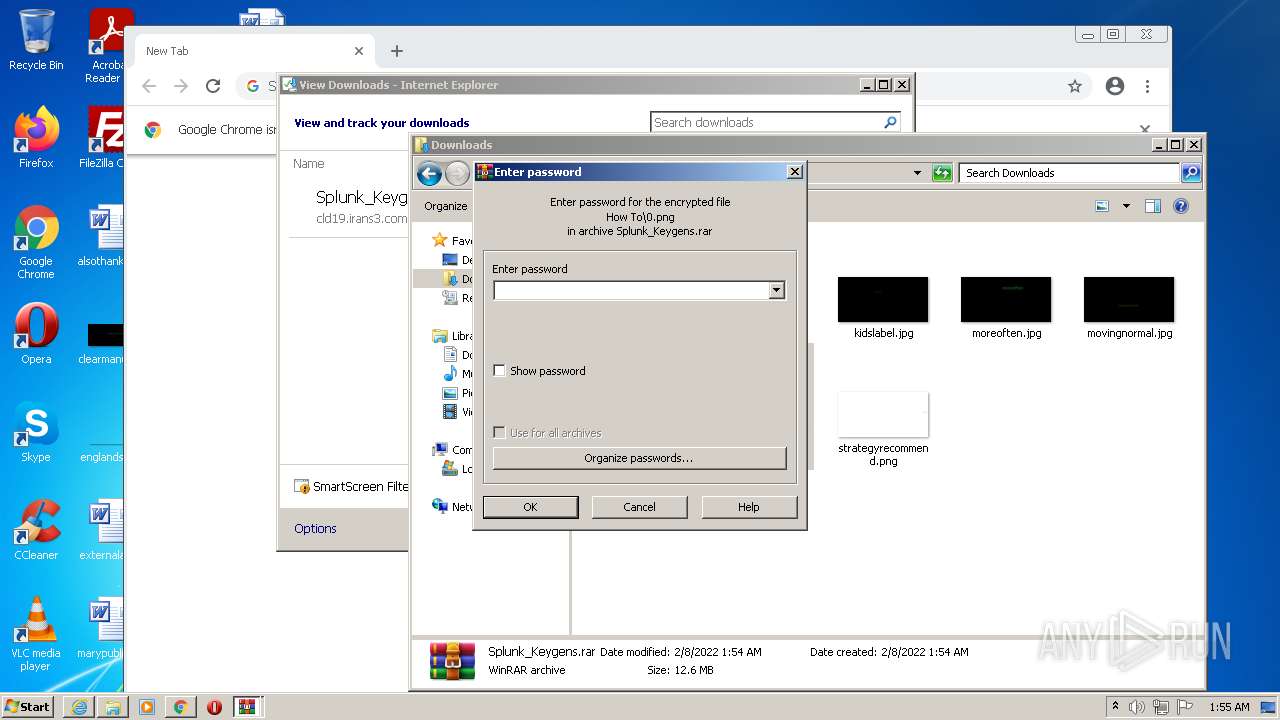
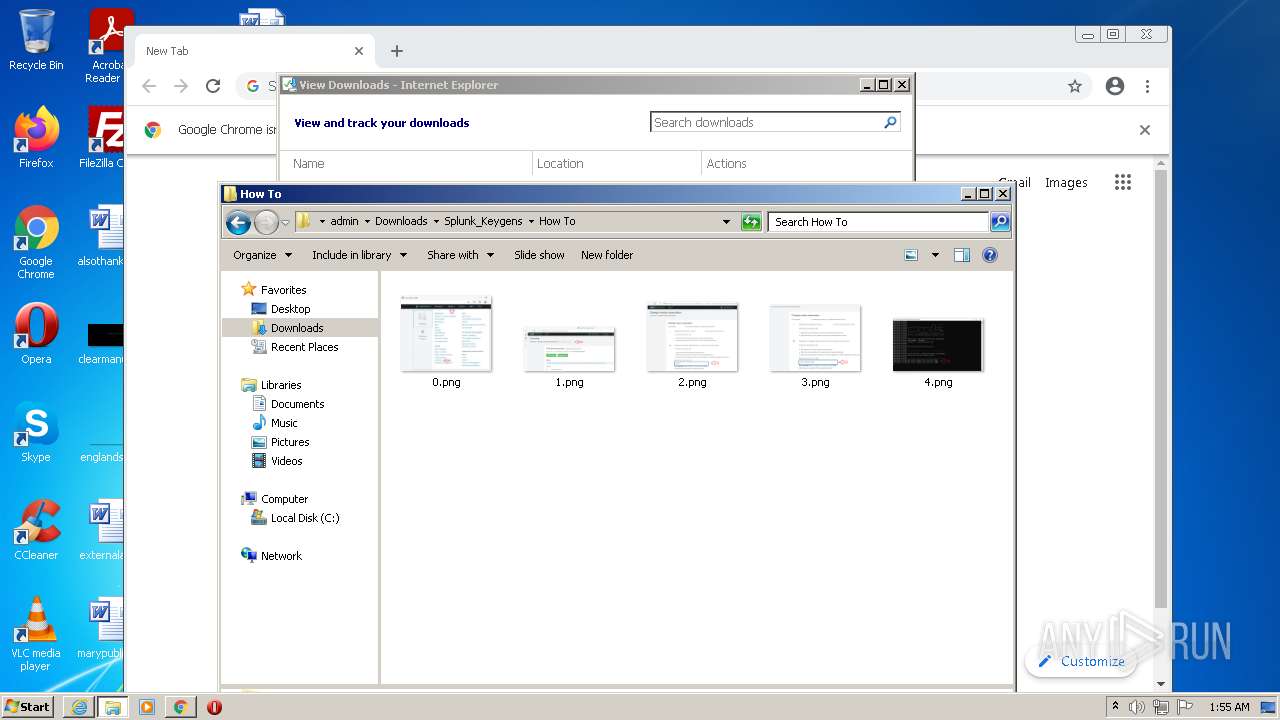
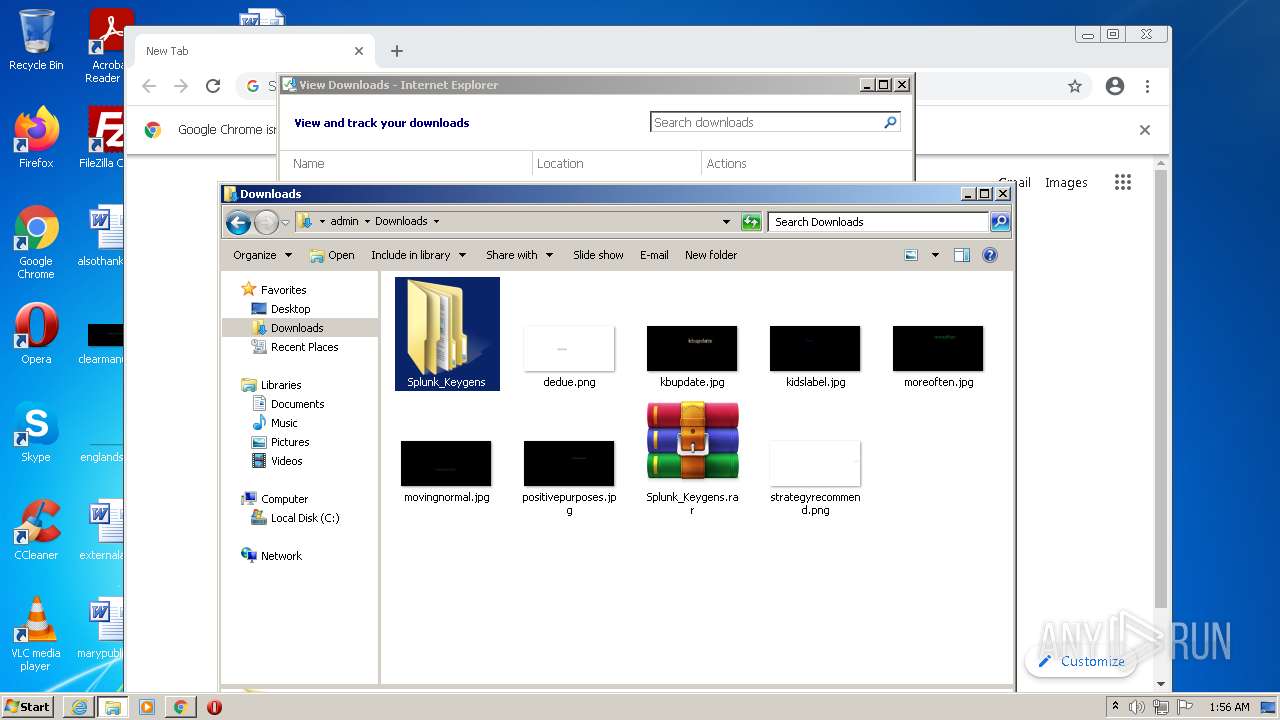
Manual execution by user
- chrome.exe (PID: 2332)
- explorer.exe (PID: 3440)
- WinRAR.exe (PID: 1812)
- dvt-splunk_licsrv.1.0.386.exe (PID: 3924)
Reads the hosts file
- chrome.exe (PID: 2332)
- chrome.exe (PID: 2148)
Modifies the phishing filter of IE
- iexplore.exe (PID: 3928)
Reads the date of Windows installation
- iexplore.exe (PID: 3928)
- chrome.exe (PID: 2064)
Creates files in the user directory
- iexplore.exe (PID: 3928)
Changes settings of System certificates
- iexplore.exe (PID: 3928)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3928)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 2332)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
90
Monitored processes
47
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1016,1776946431935678858,15326495908177951796,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=952 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
| 520 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,1776946431935678858,15326495908177951796,131072 --enable-features=PasswordImport --lang=en-US --instant-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1932 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
| 1184 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1016,1776946431935678858,15326495908177951796,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3296 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
| 1464 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1016,1776946431935678858,15326495908177951796,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2920 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
| 1572 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1016,1776946431935678858,15326495908177951796,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=4064 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
| 1612 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1016,1776946431935678858,15326495908177951796,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3088 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
| 1628 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1016,1776946431935678858,15326495908177951796,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1852 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
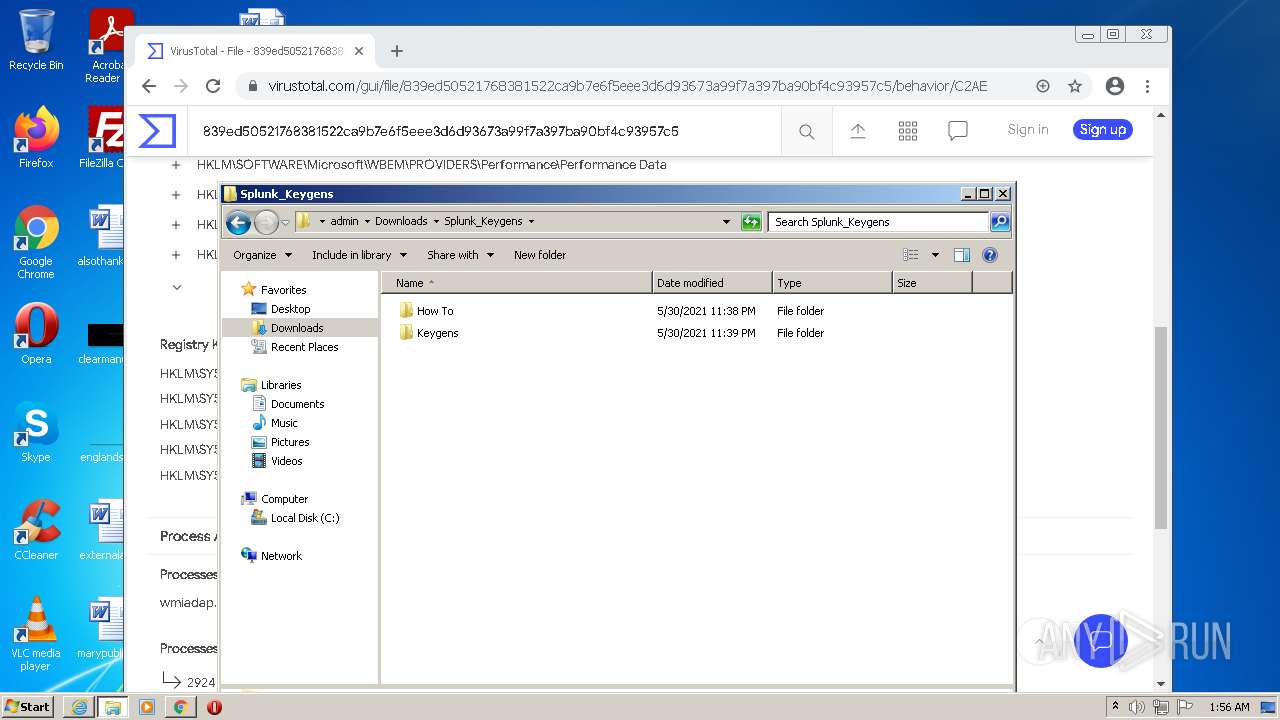
| 1812 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Downloads\Splunk_Keygens.rar" C:\Users\admin\Downloads\Splunk_Keygens\ | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | |
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 | ||||
| 1960 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,1776946431935678858,15326495908177951796,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=31 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1824 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
| 2064 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1016,1776946431935678858,15326495908177951796,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1684 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
3
Suspicious files
201
Text files
180
Unknown types
22
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-6201CD65-91C.pma | — | |
MD5:— | SHA256:— | |||
| 3436 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3928 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:— | SHA256:— | |||
| 3928 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:— | SHA256:— | |||
| 3436 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B857119BB214FB4DF0CFE003A05E1B11 | der | |
MD5:— | SHA256:— | |||
| 3436 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:— | SHA256:— | |||
| 3436 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B857119BB214FB4DF0CFE003A05E1B11 | binary | |
MD5:— | SHA256:— | |||
| 3436 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:— | SHA256:— | |||
| 3436 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:F7DCB24540769805E5BB30D193944DCE | SHA256:6B88C6AC55BBD6FEA0EBE5A760D1AD2CFCE251C59D0151A1400701CB927E36EA | |||
| 3436 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarE5B9.tmp | cat | |
MD5:D99661D0893A52A0700B8AE68457351A | SHA256:BDD5111162A6FA25682E18FA74E37E676D49CAFCB5B7207E98E5256D1EF0D003 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
38
TCP/UDP connections
59
DNS requests
40
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
884 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acbfkuit6arxh6st7mymgvvwoa3q_7146/hfnkpimlhhgieaddgfemjhofmfblmnib_7146_all_ace6a6s5v3cjocmowfswdrtfuy4a.crx3 | US | — | — | whitelisted |
3436 | iexplore.exe | GET | 200 | 23.202.229.179:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgTWCSbM4mihpzhNf%2BaiJh8Zkg%3D%3D | NL | der | 503 b | shared |
3436 | iexplore.exe | GET | 200 | 84.53.185.217:80 | http://subca.ocsp-certum.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBR5iK7tYk9tqQEoeQhZNkKcAol9bgQUjEPEy22YwaechGnr30oNYJY6w%2FsCEQCTkoVAAWVxX5R%2FKI%2FvyZso | US | der | 1.50 Kb | whitelisted |
3928 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
3436 | iexplore.exe | GET | 200 | 84.53.185.217:80 | http://subca.ocsp-certum.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTYOkzrrCGQj08njZXbUQQpkoUmuQQUCHbNywf%2FJPbFze27kLzihDdGdfcCECbd0itGycRNWmlNOYB%2Bcq0%3D | US | der | 1.54 Kb | whitelisted |
3436 | iexplore.exe | GET | 200 | 84.53.185.137:80 | http://dvcasha2.ocsp-certum.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNcCPjJ499lHmfPUvPsRjzr1YchwQU5TGtvzoRlvSDvFA81LeQm5Du3iUCEErwTK9rQ%2BM0w%2FTQvVLJ7Ks%3D | US | der | 1.56 Kb | whitelisted |
3928 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
3928 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA177el9ggmWelJjG4vdGL0%3D | US | der | 471 b | whitelisted |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acbfkuit6arxh6st7mymgvvwoa3q_7146/hfnkpimlhhgieaddgfemjhofmfblmnib_7146_all_ace6a6s5v3cjocmowfswdrtfuy4a.crx3 | US | binary | 5.66 Kb | whitelisted |
3436 | iexplore.exe | GET | 200 | 8.238.21.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?23a30a180a0f2e22 | US | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3928 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3436 | iexplore.exe | 188.114.97.0:443 | cdn.digiboy.ir | Cloudflare Inc | US | malicious |
3436 | iexplore.exe | 8.238.21.254:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | unknown |
3928 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3928 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3436 | iexplore.exe | 104.73.131.204:80 | x1.c.lencr.org | Akamai International B.V. | NL | unknown |
3436 | iexplore.exe | 23.202.229.179:80 | r3.o.lencr.org | Akamai International B.V. | NL | unknown |
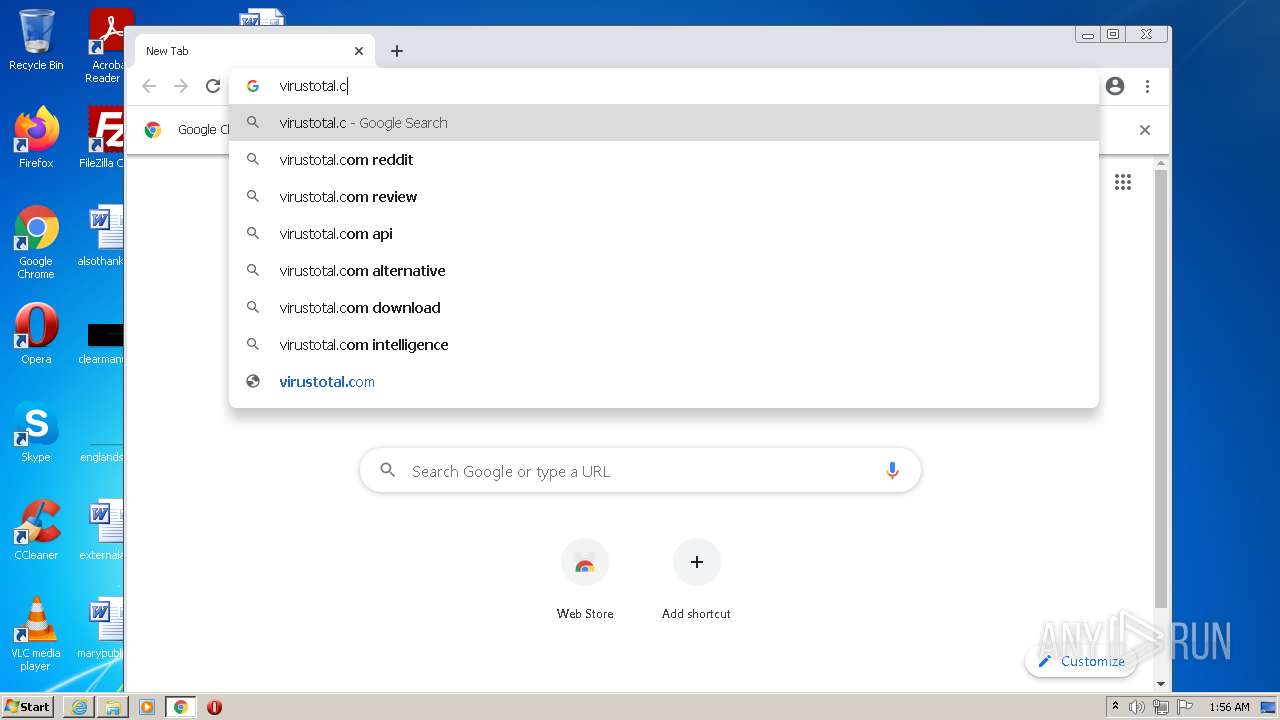
2148 | chrome.exe | 142.250.179.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2148 | chrome.exe | 142.250.179.142:443 | clients2.google.com | Google Inc. | US | whitelisted |
2148 | chrome.exe | 142.250.179.132:443 | www.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cdn.digiboy.ir |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
r3.o.lencr.org |
| shared |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
clients2.google.com |
| whitelisted |