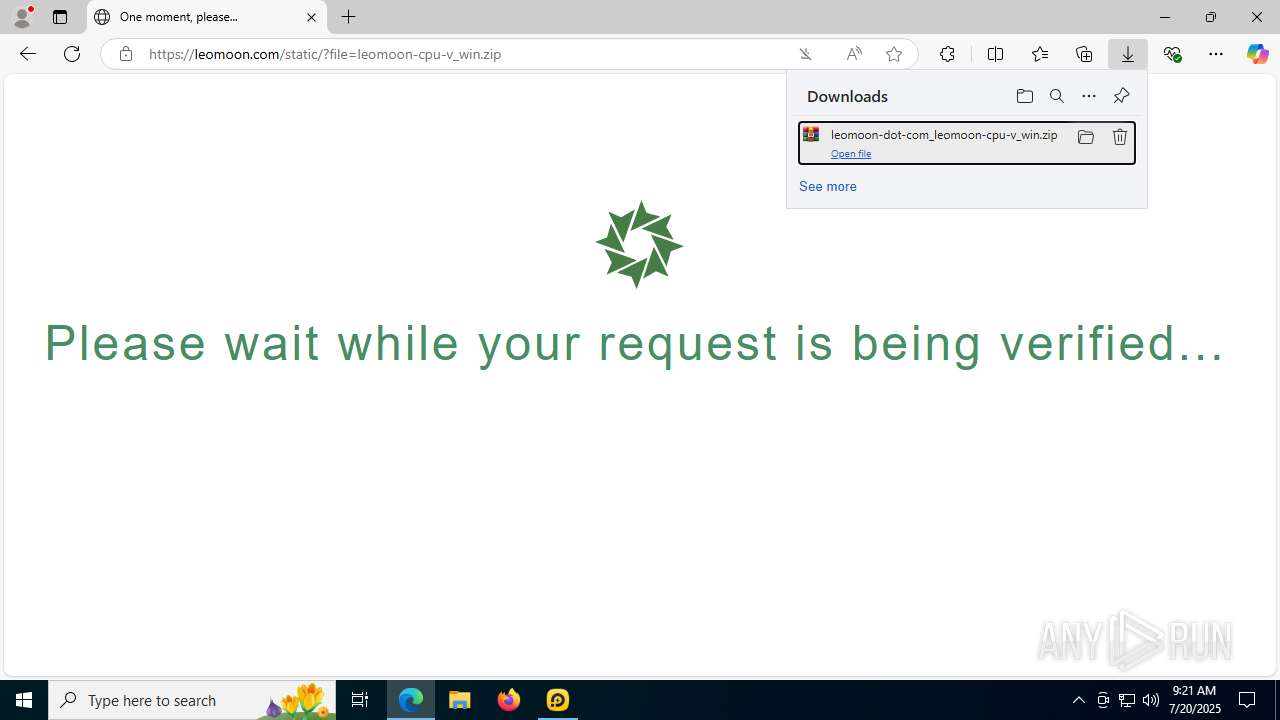
| URL: | https://res.ldrescdn.com/download/LDPlayer9.exe?n=LDPlayer9_ens_1001_ld.exe |
| Full analysis: | https://app.any.run/tasks/96408228-aaa0-490e-8a54-e726b3479e18 |
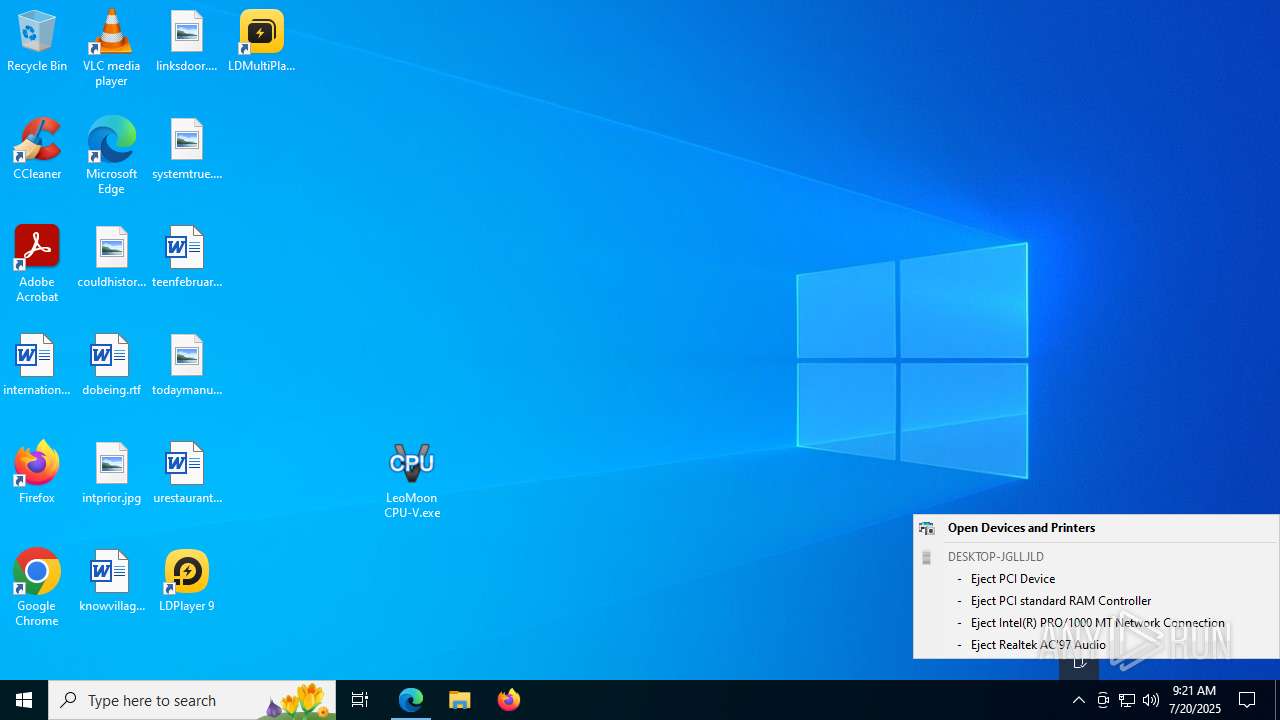
| Verdict: | Malicious activity |
| Analysis date: | July 20, 2025, 09:18:41 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | FEB3594FC52975F9315A95BA81A54532 |
| SHA1: | 19C59E18FD46B942BF74E0BEEDA5CBB81D9CC1D7 |
| SHA256: | 2D8AB53B07A68FFD1E7929472B90E2E47313755FD43F70B8F19865509792C71E |
| SSDEEP: | 3:N8F71aKLPG5/Bx7uyeCn:2tjmeyDn |
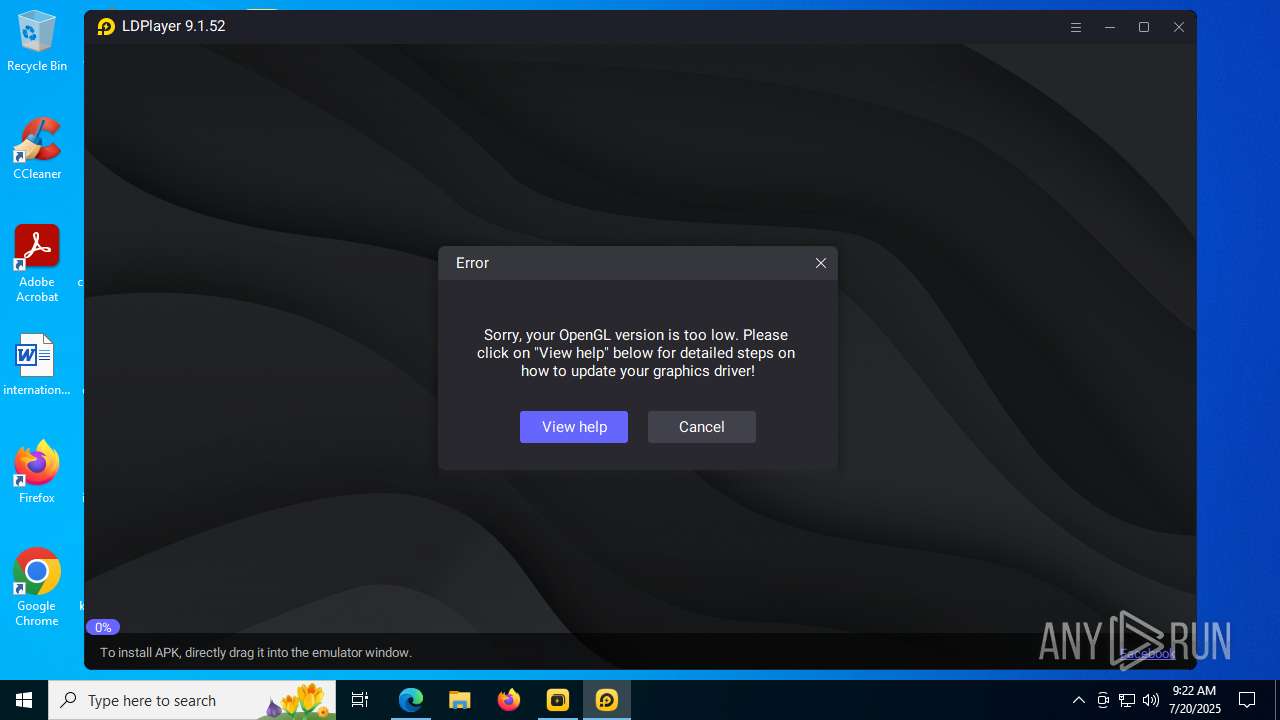
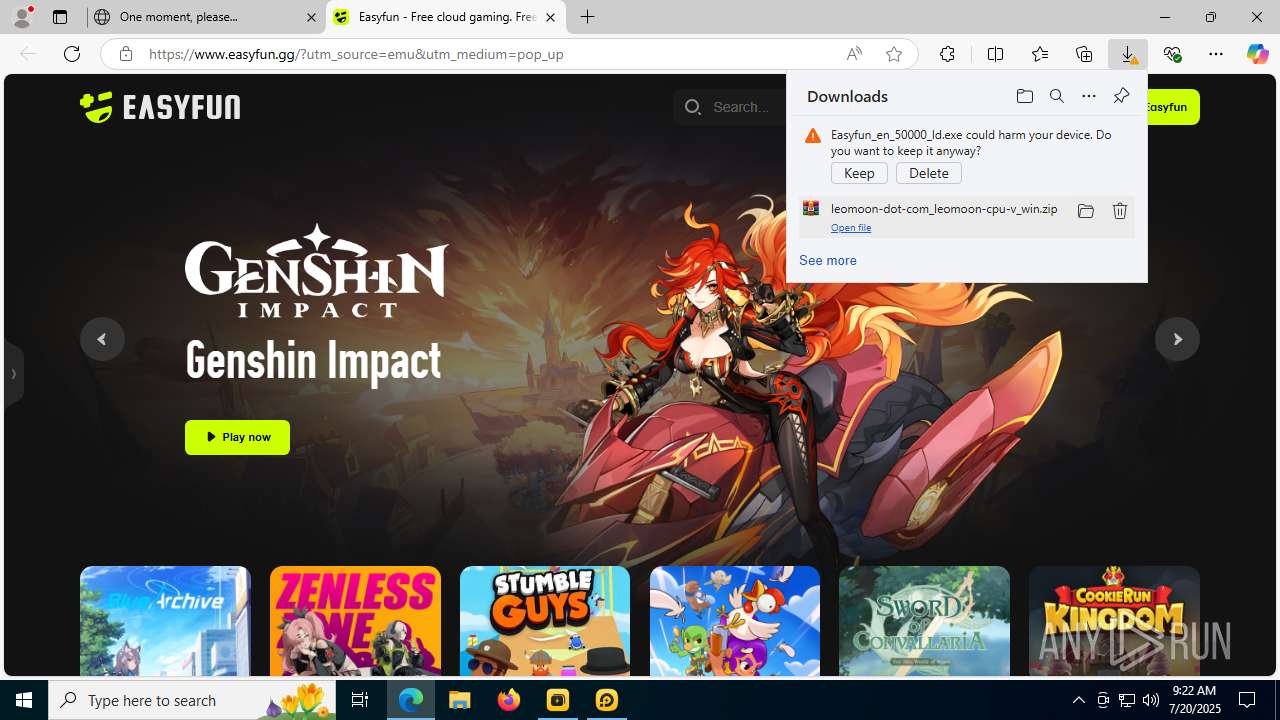
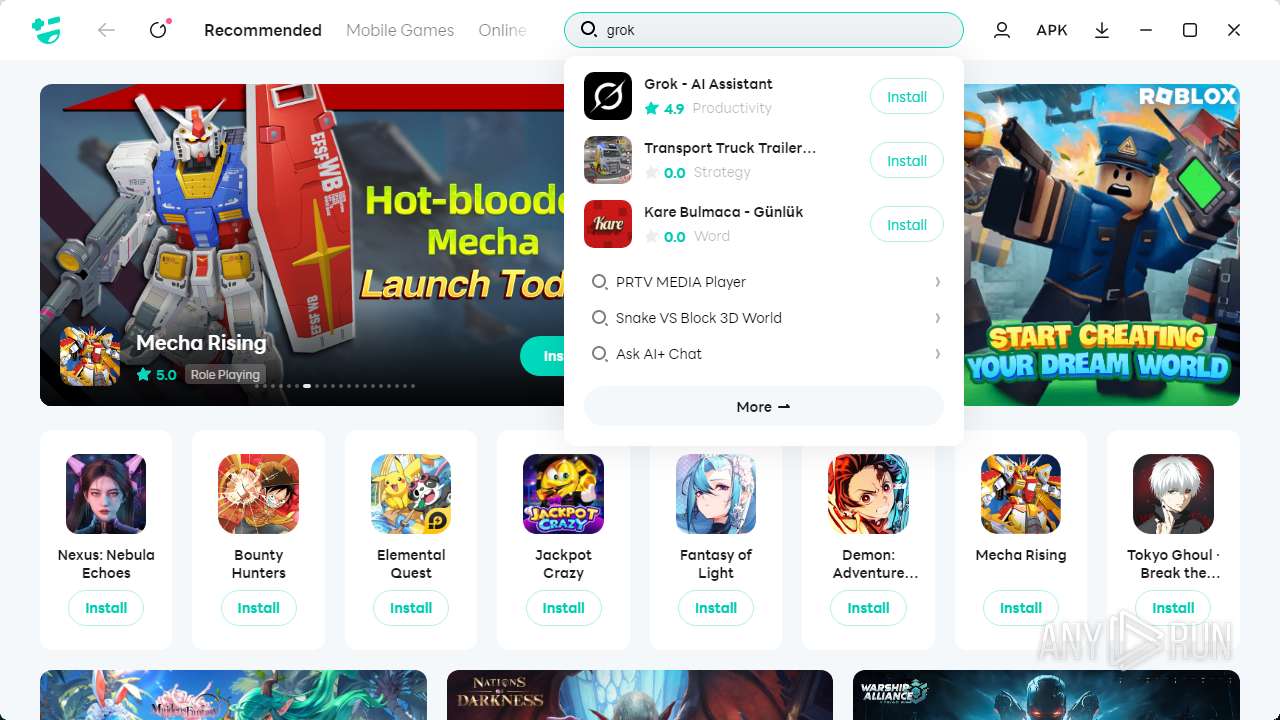
MALICIOUS
Signed with known abused certificate
- LDPlayer9_ens_1001_ld.exe (PID: 1132)
- LDPlayer.exe (PID: 2508)
- dnplayer.exe (PID: 1728)
- msedge.exe (PID: 1800)
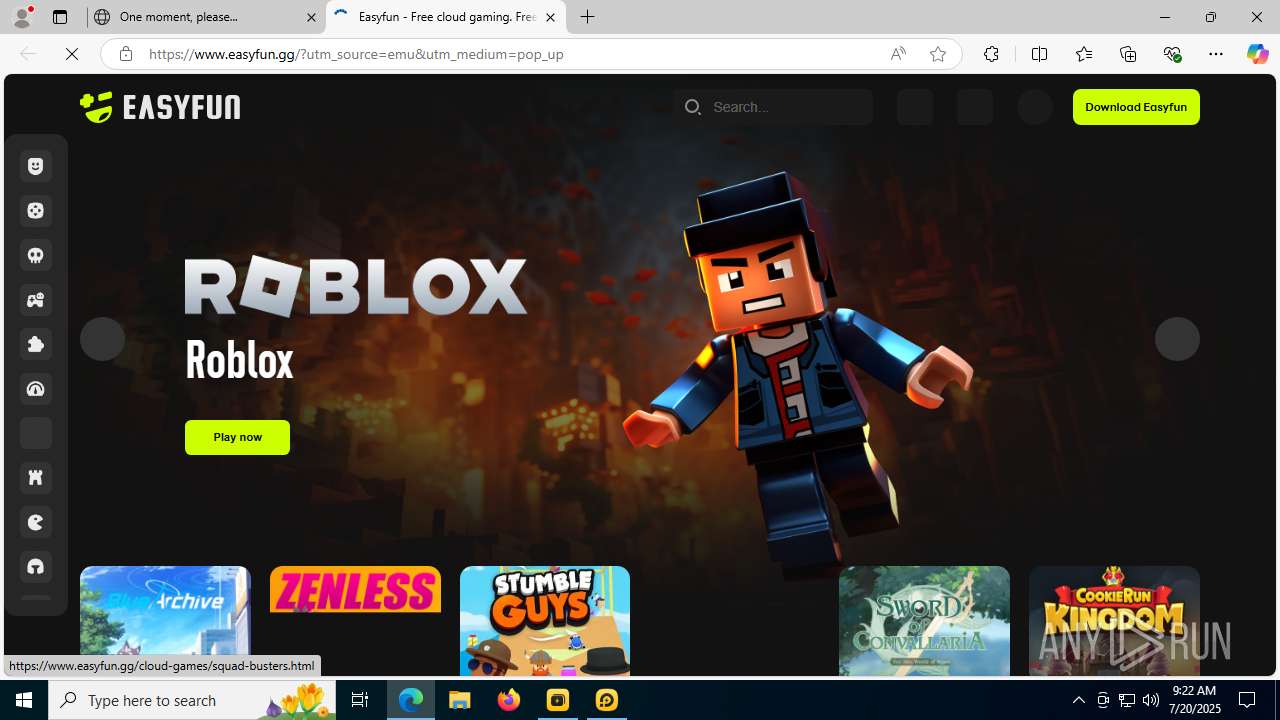
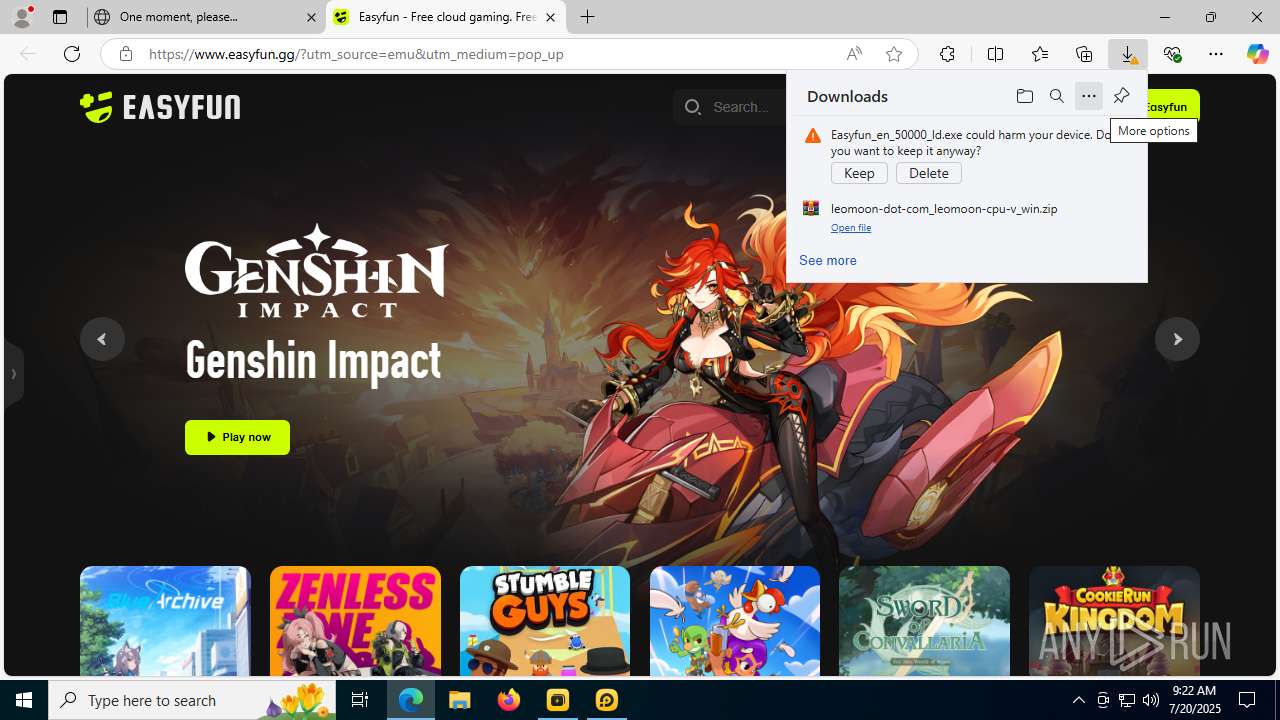
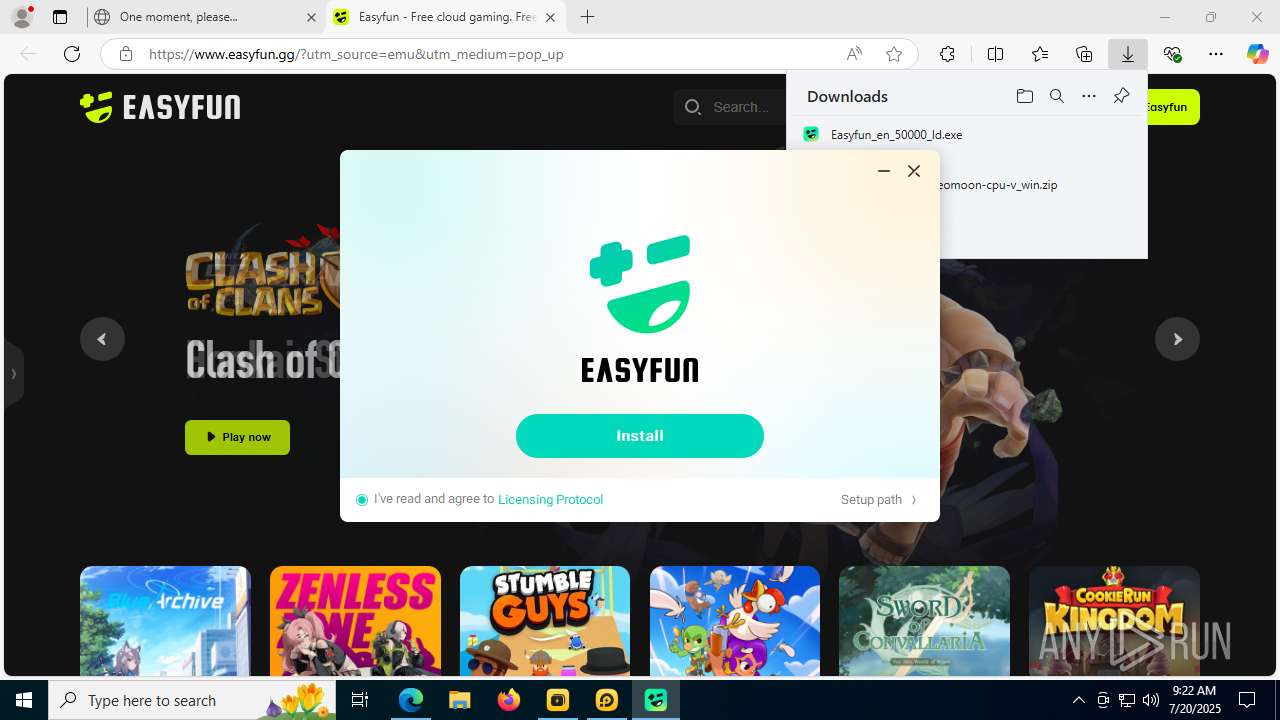
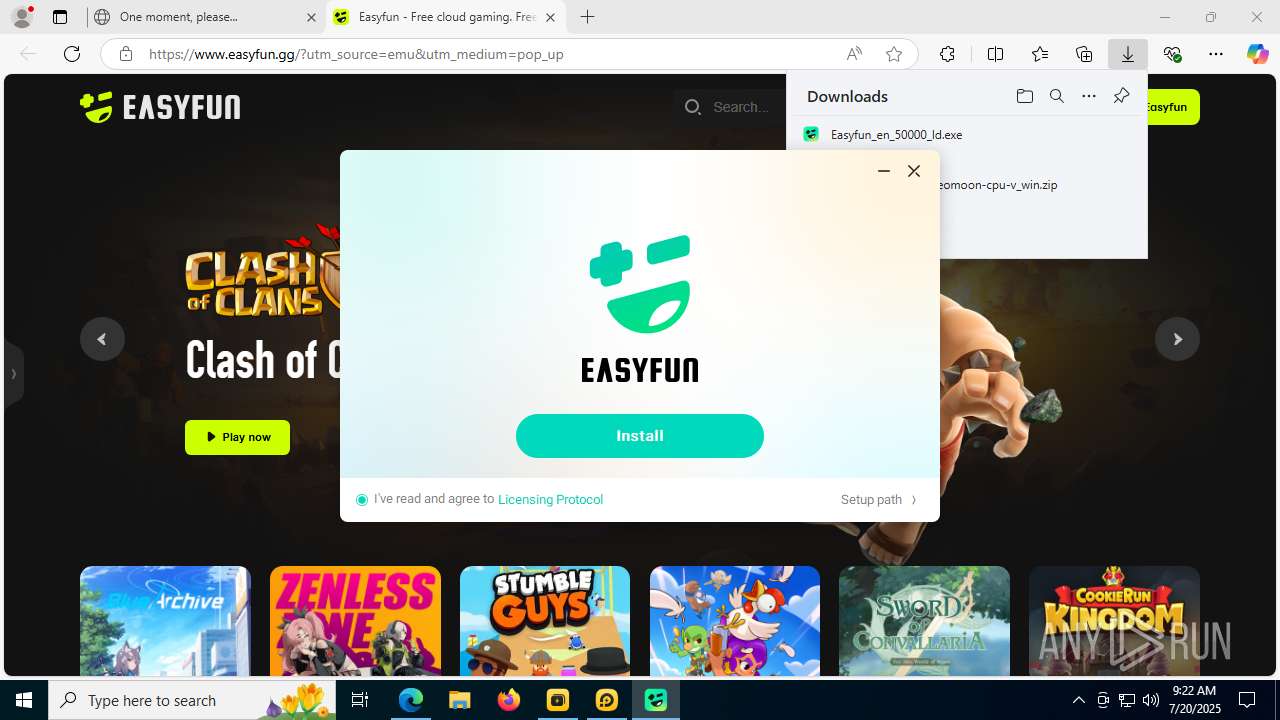
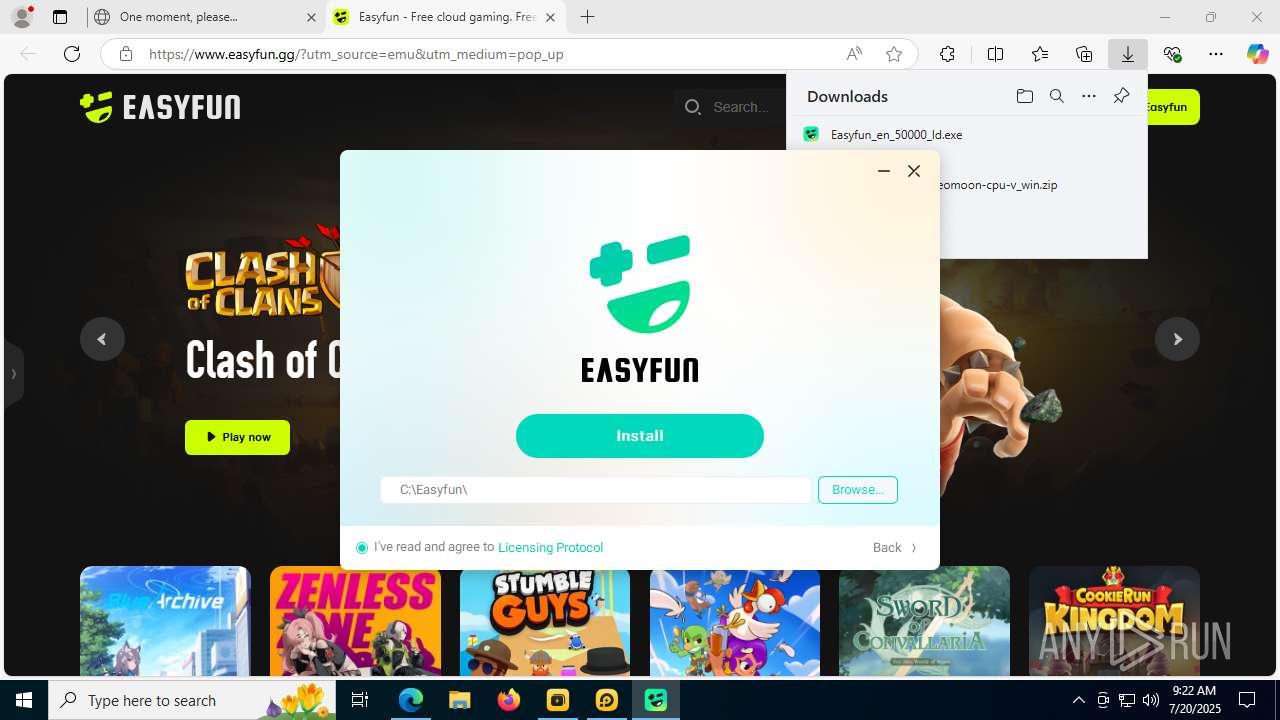
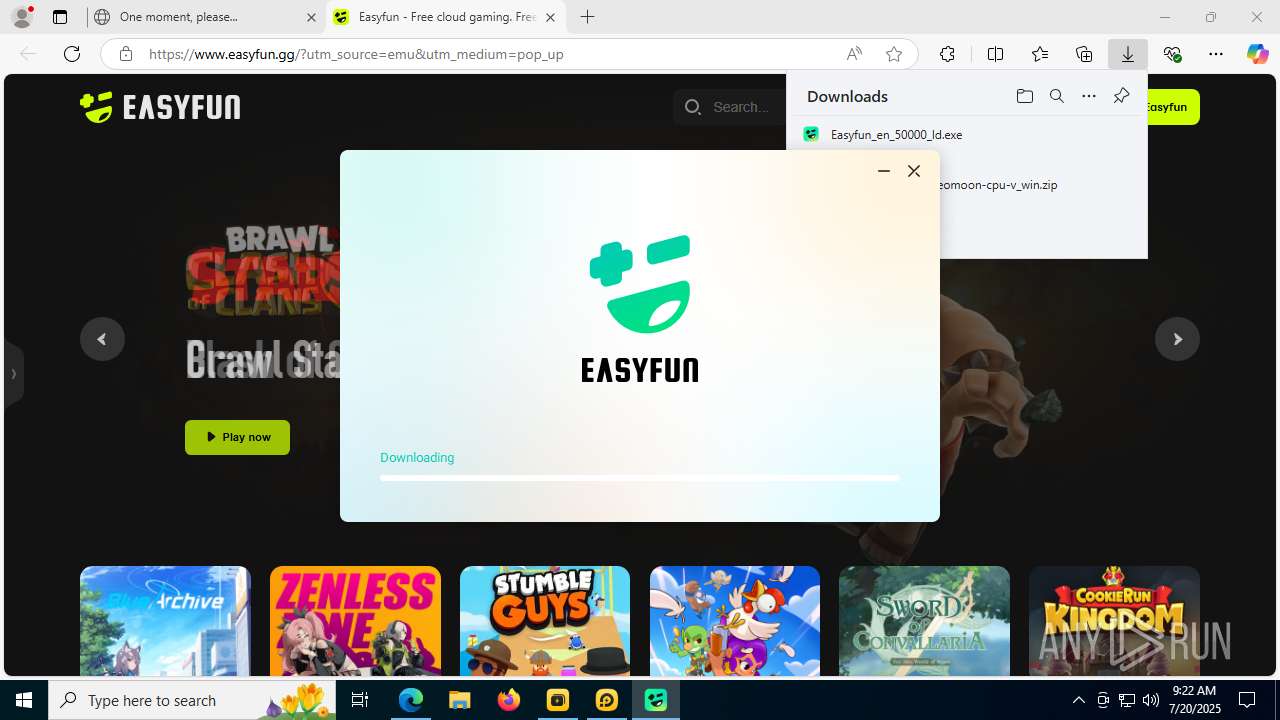
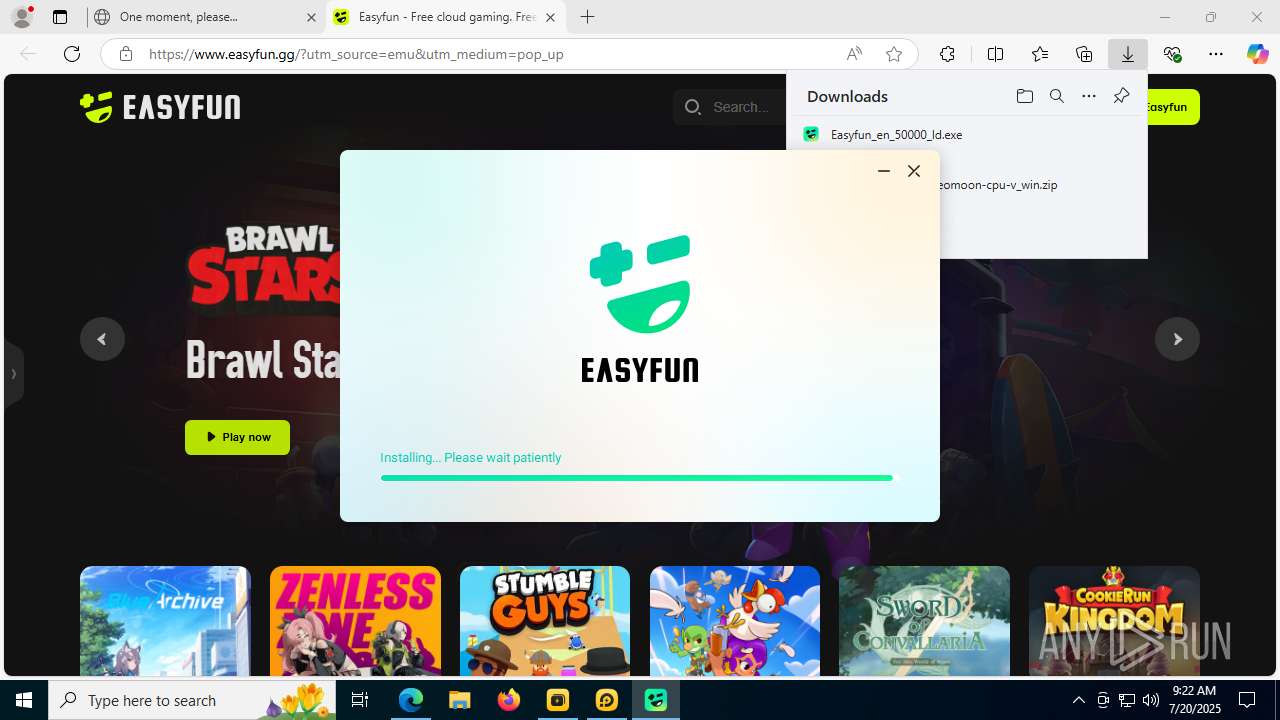
- Easyfun_en_50000_ld.exe (PID: 12020)
- Easyfun.exe (PID: 5300)
- dnmultiplayerex.exe (PID: 10836)
GENERIC has been found (auto)
- LDPlayer.exe (PID: 2508)
- inst_X.exe (PID: 10724)
Registers / Runs the DLL via REGSVR32.EXE
- dnrepairer.exe (PID: 2188)
Starts NET.EXE for service management
- dnrepairer.exe (PID: 2188)
- net.exe (PID: 892)
Changes the autorun value in the registry
- inst_X.exe (PID: 10724)
SUSPICIOUS
Reads security settings of Internet Explorer
- LDPlayer.exe (PID: 2508)
- LDPlayer9_ens_1001_ld.exe (PID: 1132)
- dnplayer.exe (PID: 1728)
- dnplayer.exe (PID: 10620)
- dnmultiplayerex.exe (PID: 10836)
- Easyfun_en_50000_ld.exe (PID: 12020)
- inst_X.exe (PID: 10724)
- Easyfun.exe (PID: 5300)
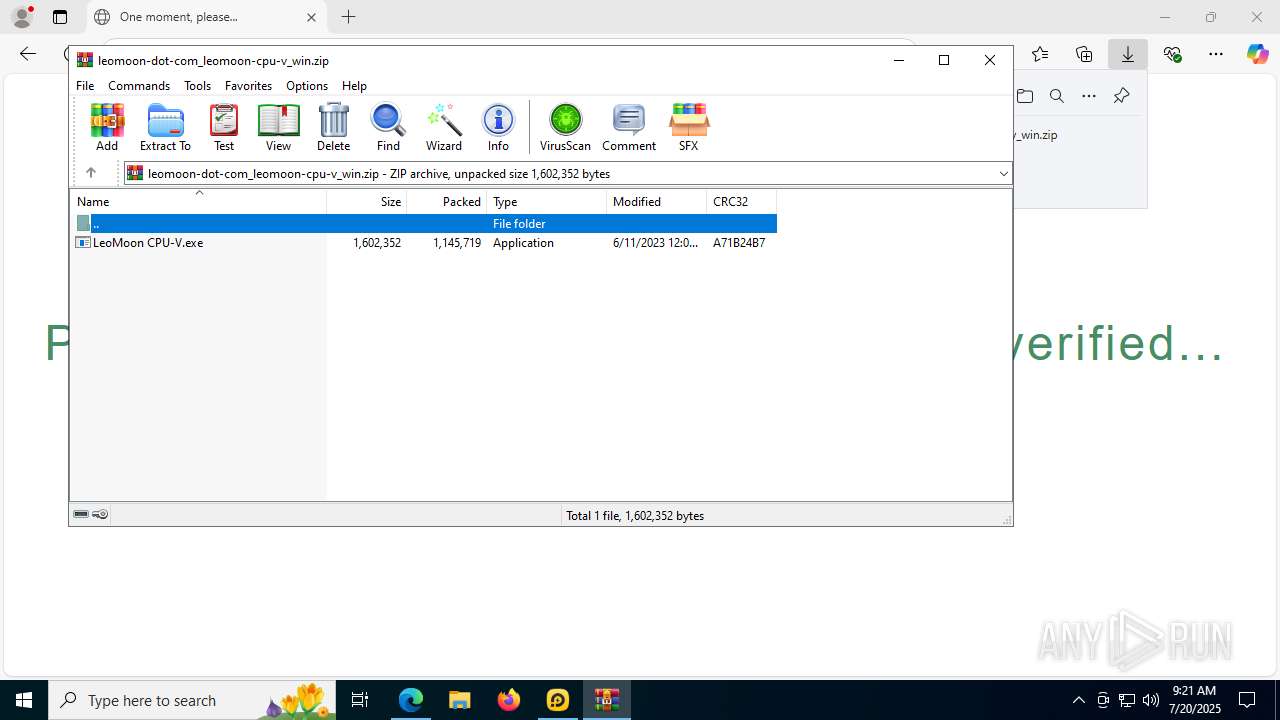
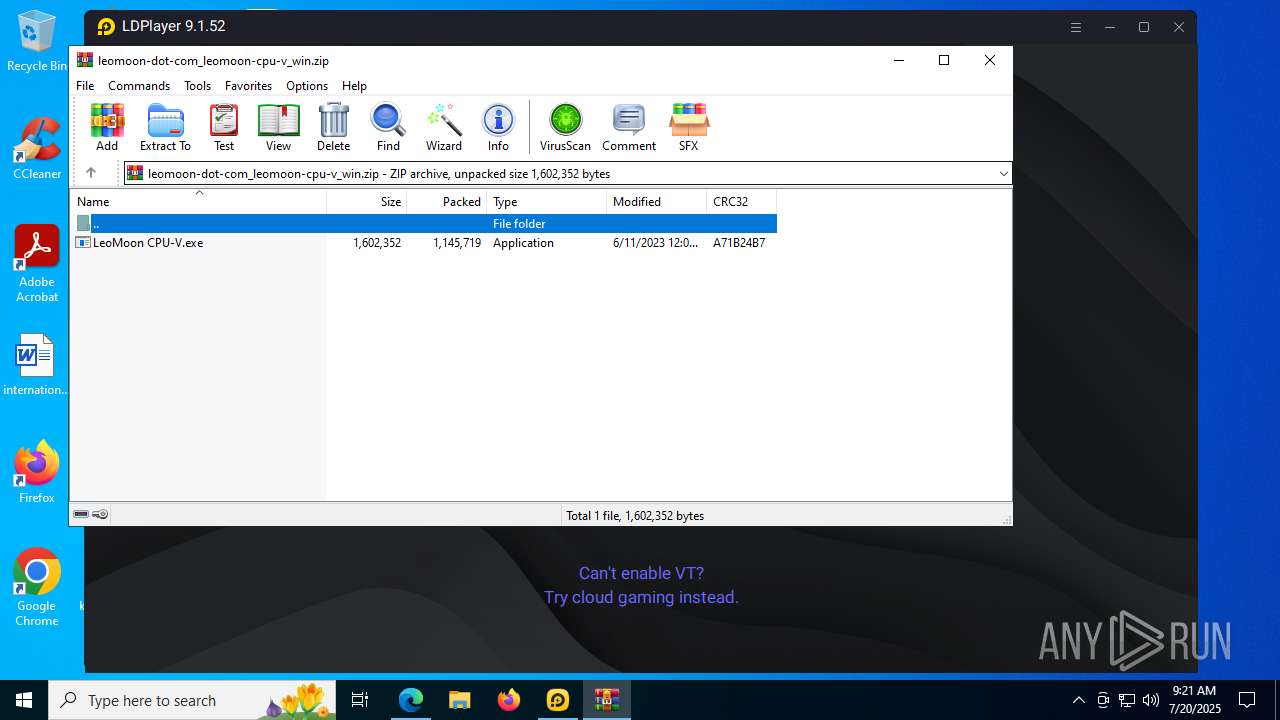
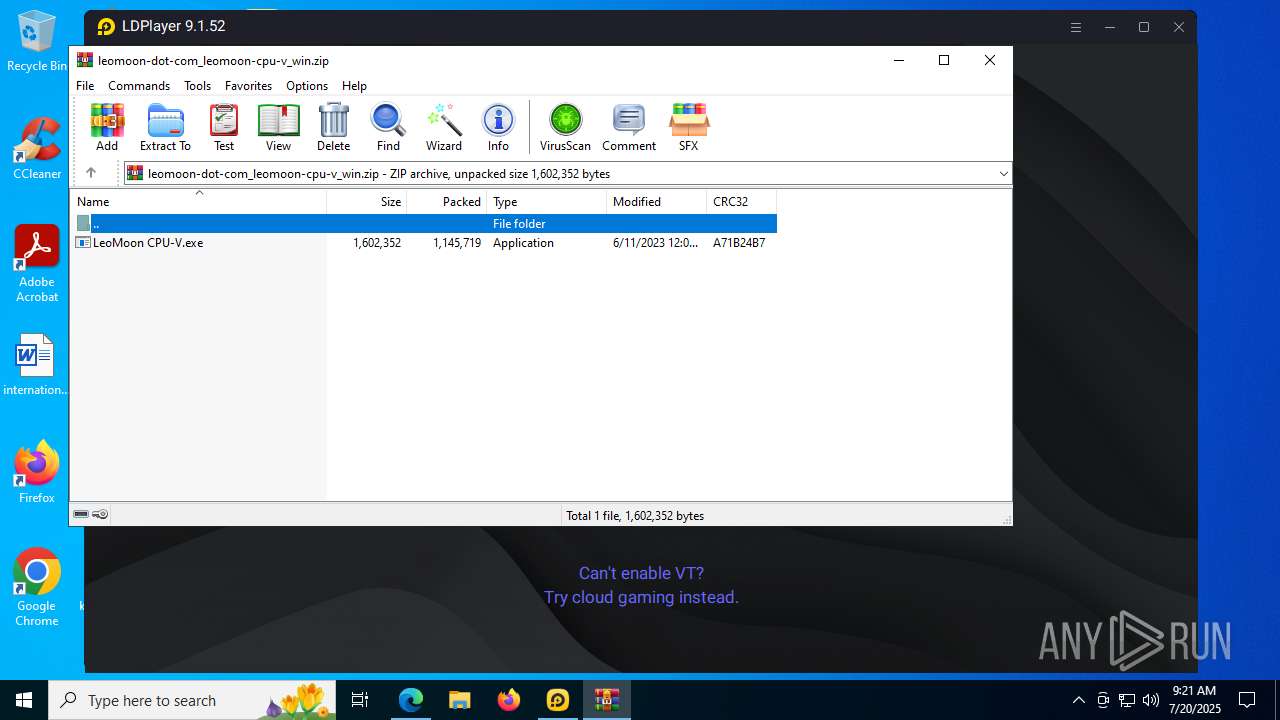
Executable content was dropped or overwritten
- LDPlayer.exe (PID: 2508)
- dnrepairer.exe (PID: 2188)
- dnplayer.exe (PID: 1728)
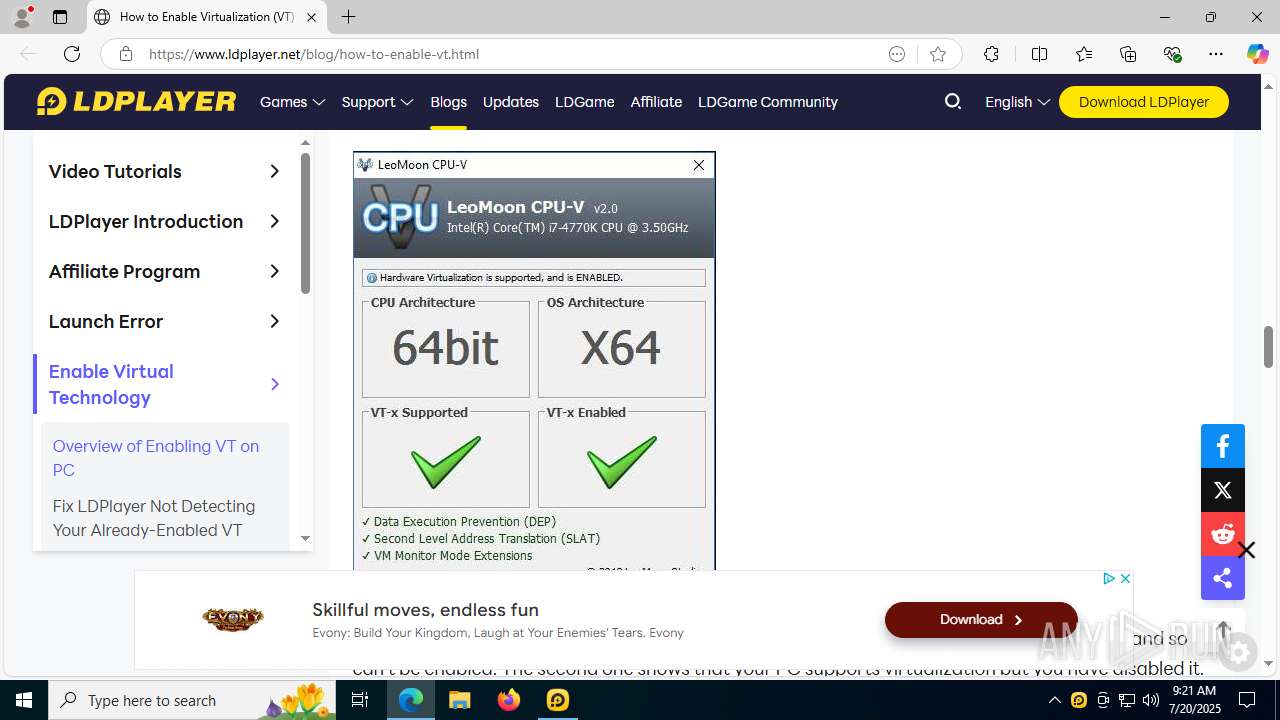
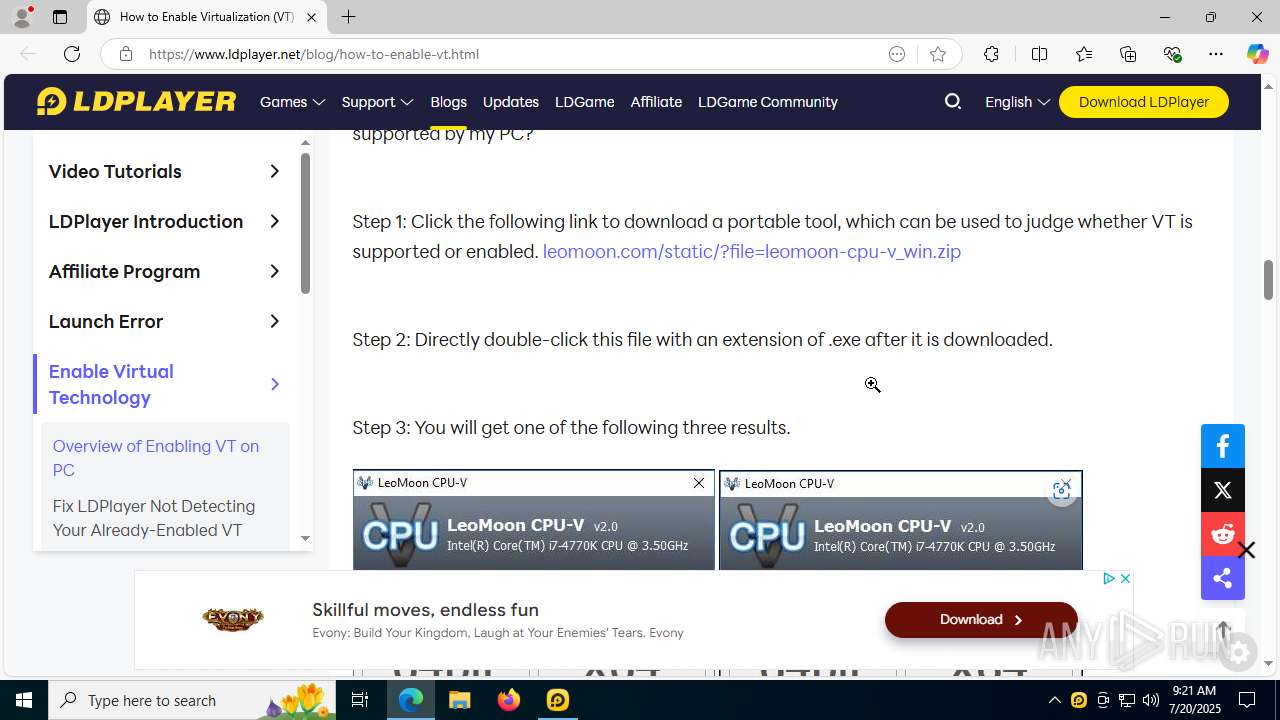
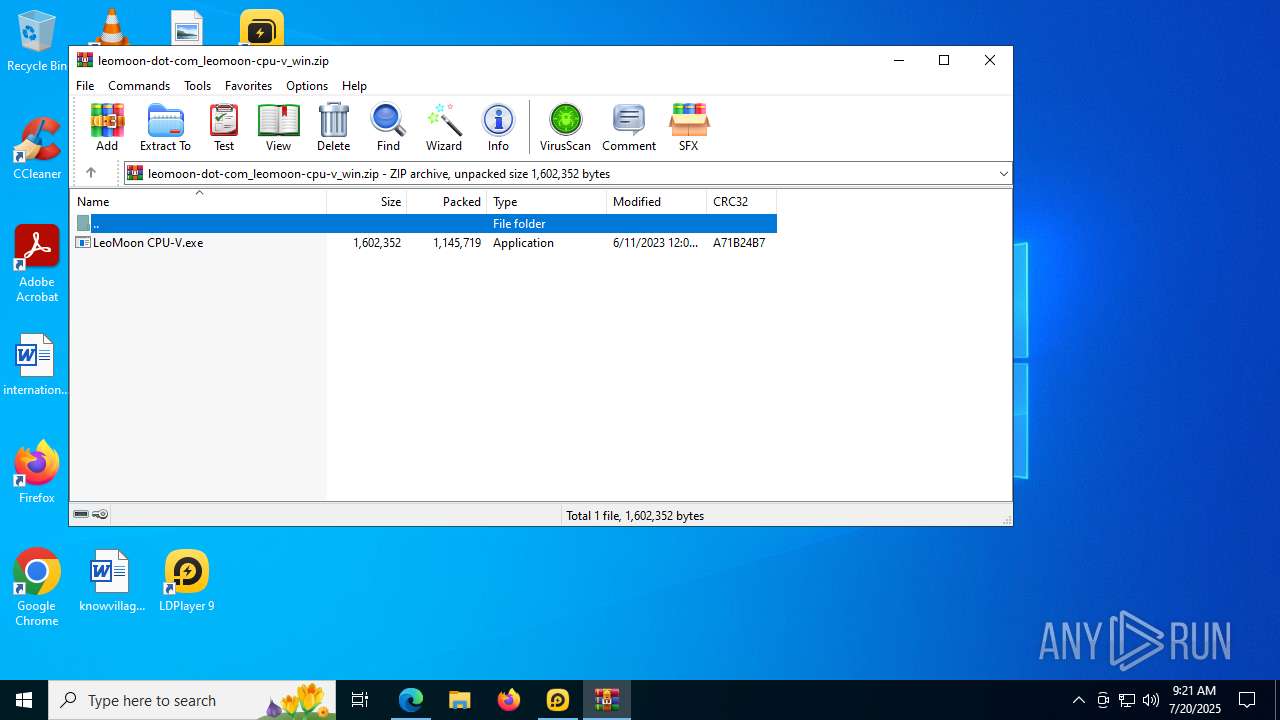
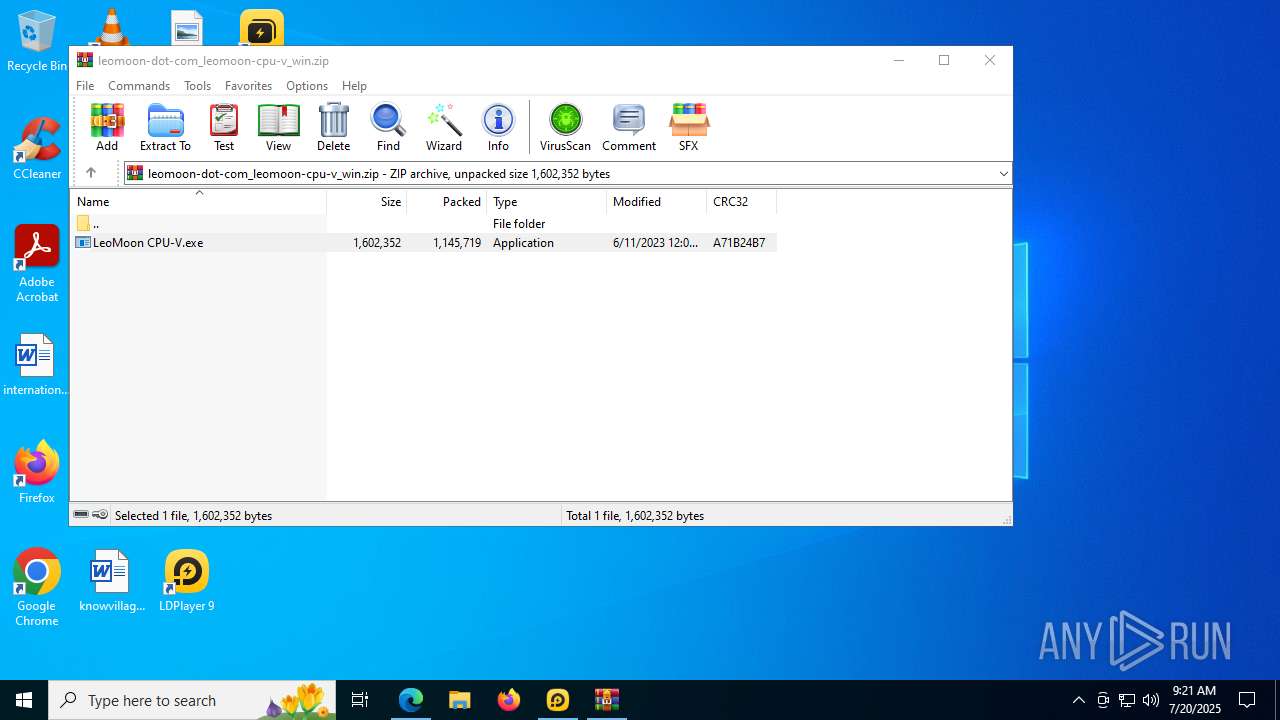
- LeoMoon CPU-V.exe (PID: 10384)
- inst_X.exe (PID: 10724)
The process creates files with name similar to system file names
- LDPlayer.exe (PID: 2508)
Process drops legitimate windows executable
- LDPlayer.exe (PID: 2508)
- dnrepairer.exe (PID: 2188)
- dnplayer.exe (PID: 1728)
- inst_X.exe (PID: 10724)
Drops 7-zip archiver for unpacking
- LDPlayer.exe (PID: 2508)
- inst_X.exe (PID: 10724)
The process drops C-runtime libraries
- LDPlayer.exe (PID: 2508)
- dnrepairer.exe (PID: 2188)
- dnplayer.exe (PID: 1728)
- inst_X.exe (PID: 10724)
Takes ownership (TAKEOWN.EXE)
- dnrepairer.exe (PID: 2188)
- LDPlayer.exe (PID: 2508)
Uses ICACLS.EXE to modify access control lists
- dnrepairer.exe (PID: 2188)
- LDPlayer.exe (PID: 2508)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 8180)
- regsvr32.exe (PID: 7400)
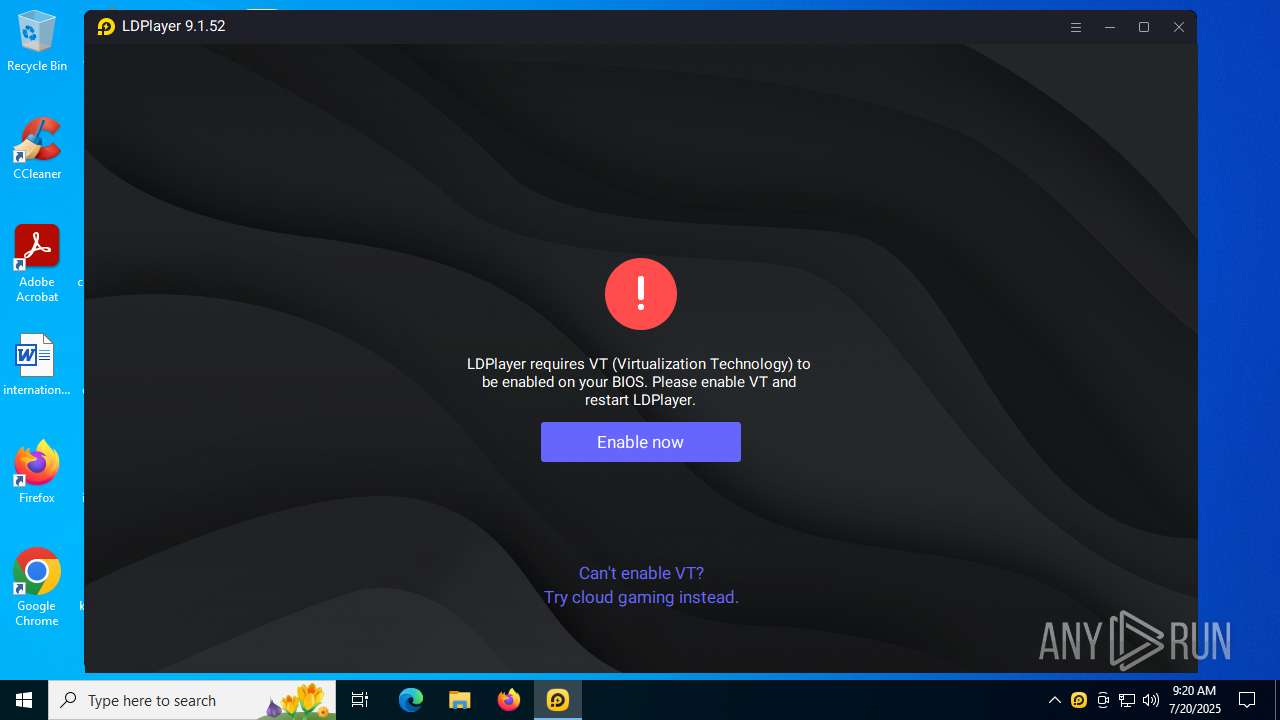
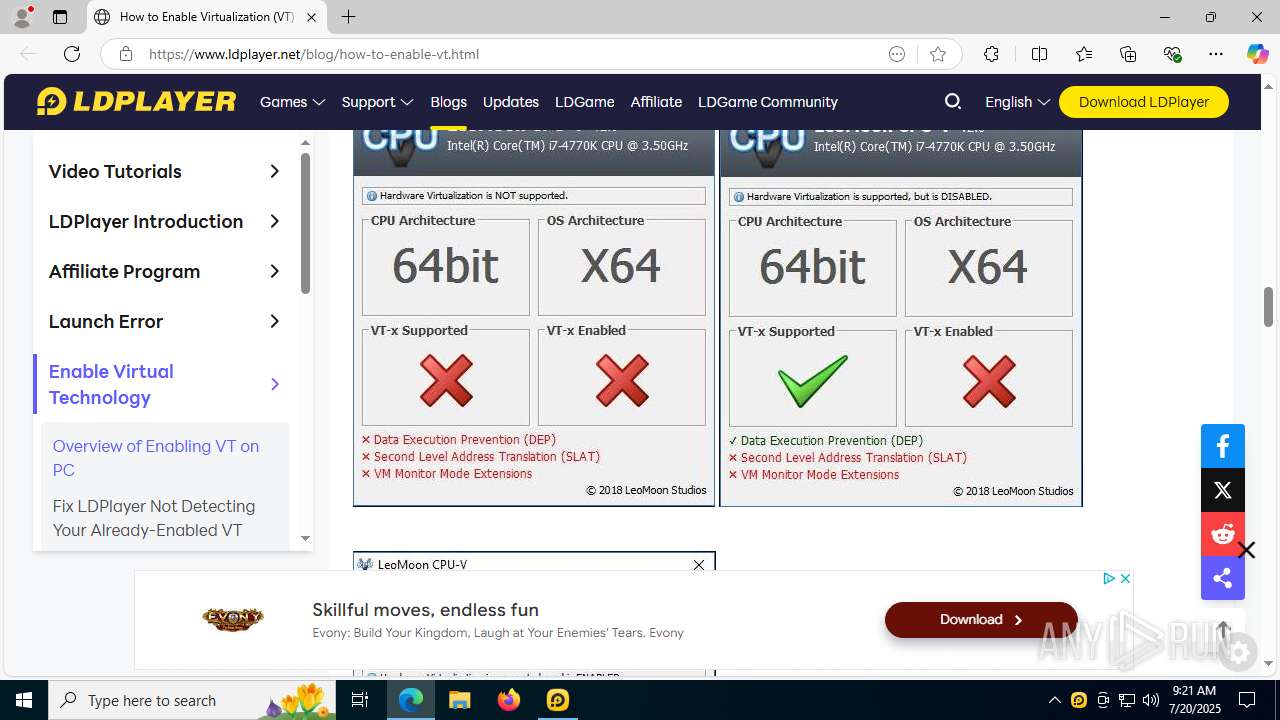
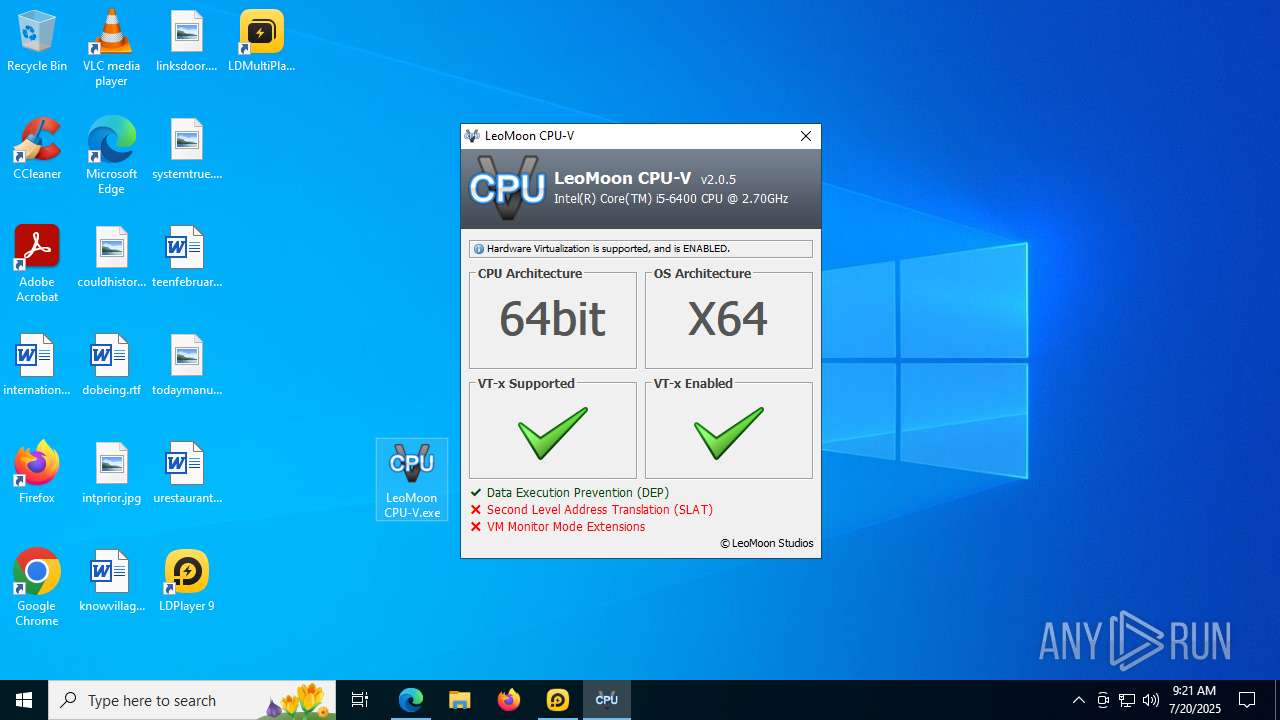
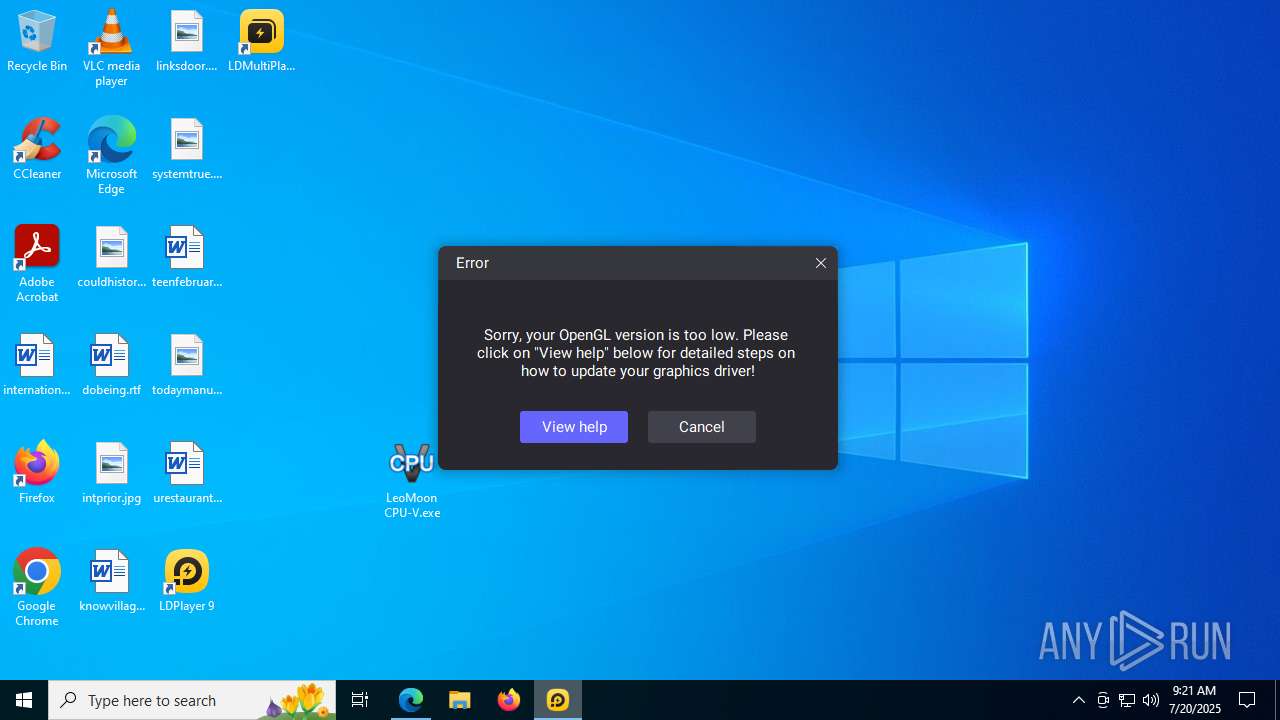
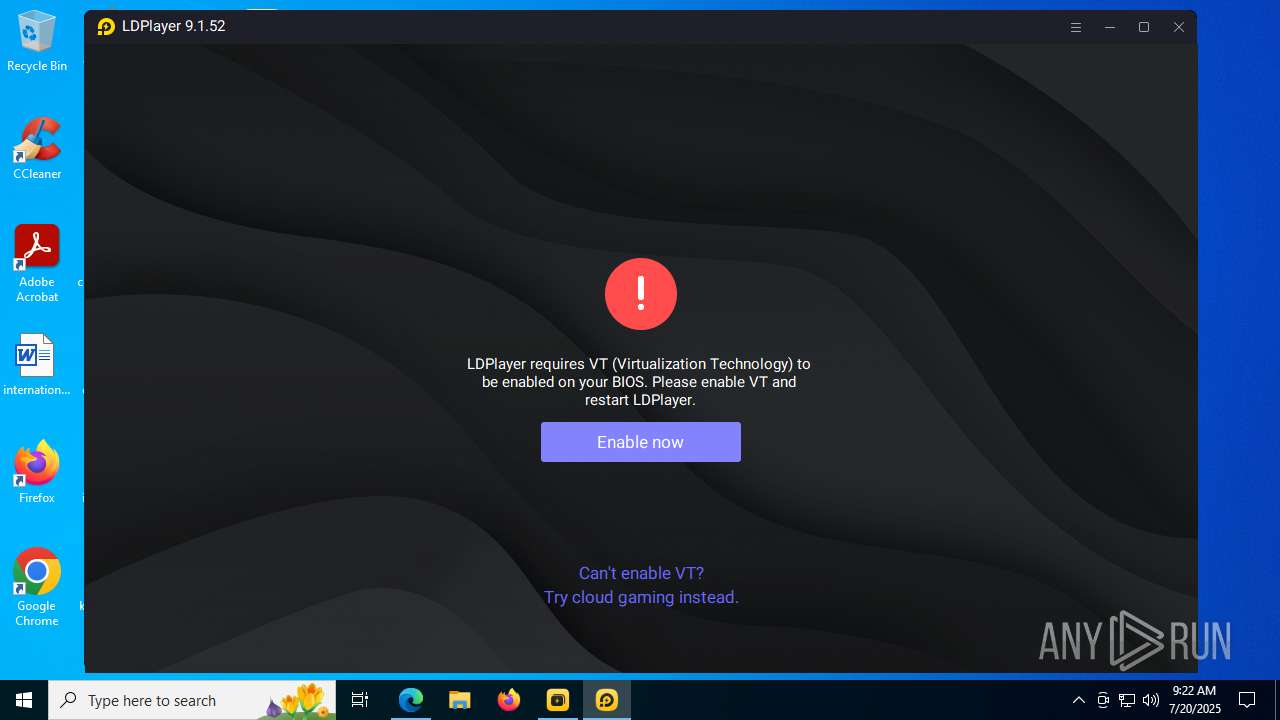
The process checks if it is being run in the virtual environment
- regsvr32.exe (PID: 7336)
- Ld9BoxSVC.exe (PID: 7432)
- regsvr32.exe (PID: 7304)
- regsvr32.exe (PID: 7400)
- regsvr32.exe (PID: 8180)
- dnplayer.exe (PID: 1728)
- conhost.exe (PID: 6776)
- conhost.exe (PID: 7400)
- conhost.exe (PID: 7320)
Creates a software uninstall entry
- LDPlayer.exe (PID: 2508)
- inst_X.exe (PID: 10724)
Creates a new Windows service
- sc.exe (PID: 7460)
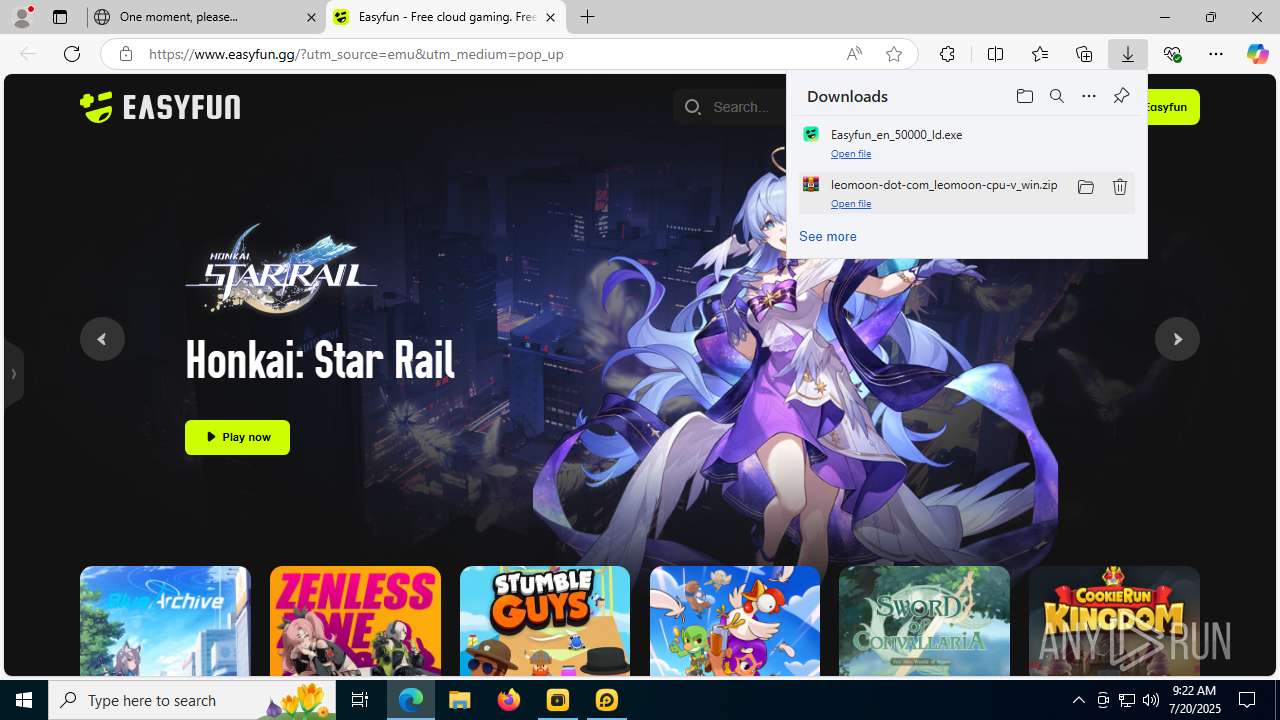
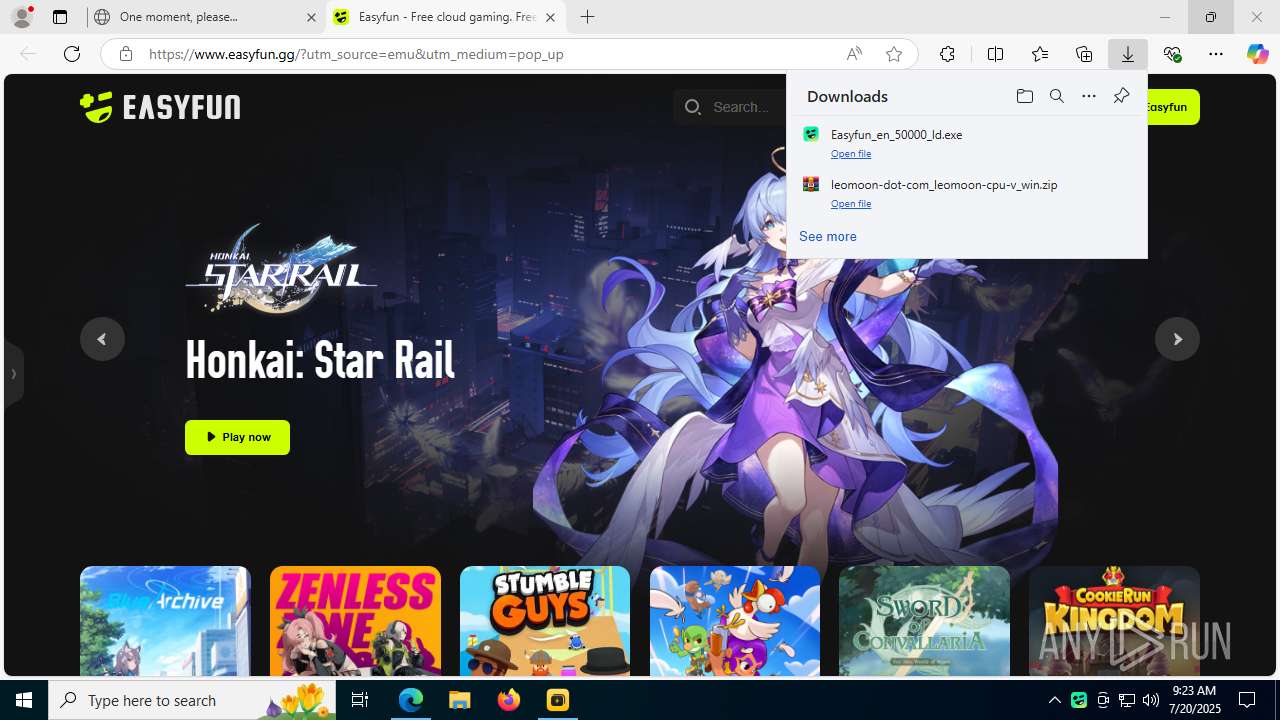
Starts POWERSHELL.EXE for commands execution
- dnrepairer.exe (PID: 2188)
- Easyfun_en_50000_ld.exe (PID: 12020)
Windows service management via SC.EXE
- sc.exe (PID: 7964)
- sc.exe (PID: 4380)
- sc.exe (PID: 7004)
- sc.exe (PID: 11140)
- sc.exe (PID: 12064)
There is functionality for taking screenshot (YARA)
- dnrepairer.exe (PID: 2188)
- dnplayer.exe (PID: 1728)
Drops a system driver (possible attempt to evade defenses)
- dnrepairer.exe (PID: 2188)
There is functionality for communication over UDP network (YARA)
- dnplayer.exe (PID: 1728)
There is functionality for VM detection VirtualBox (YARA)
- dnplayer.exe (PID: 1728)
Detected use of alternative data streams (AltDS)
- LeoMoon CPU-V.exe (PID: 10384)
Uses TASKKILL.EXE to kill process
- inst_X.exe (PID: 10724)
INFO
Reads Microsoft Office registry keys
- firefox.exe (PID: 5436)
- msedge.exe (PID: 1800)
Application launched itself
- firefox.exe (PID: 4948)
- firefox.exe (PID: 5436)
- msedge.exe (PID: 1800)
- msedge.exe (PID: 5684)
- msedge.exe (PID: 12008)
Executable content was dropped or overwritten
- firefox.exe (PID: 5436)
- WinRAR.exe (PID: 9128)
- msedge.exe (PID: 1800)
- msedge.exe (PID: 5504)
Reads the computer name
- LDPlayer9_ens_1001_ld.exe (PID: 1132)
- LDPlayer.exe (PID: 2508)
- Ld9BoxSVC.exe (PID: 7432)
- dnplayer.exe (PID: 1728)
- Ld9BoxSVC.exe (PID: 7748)
- Ld9BoxHeadless.exe (PID: 7460)
- Ld9BoxHeadless.exe (PID: 7740)
- Ld9BoxHeadless.exe (PID: 1828)
- Ld9BoxHeadless.exe (PID: 2704)
- Ld9BoxHeadless.exe (PID: 2848)
- identity_helper.exe (PID: 10724)
- identity_helper.exe (PID: 12172)
- dnmultiplayerex.exe (PID: 10836)
- bugreport.exe (PID: 8480)
- LeoMoon CPU-V.exe (PID: 10384)
- Ld9BoxSVC.exe (PID: 11448)
- Ld9BoxHeadless.exe (PID: 11012)
- dnplayer.exe (PID: 10620)
- Ld9BoxHeadless.exe (PID: 10628)
- Ld9BoxHeadless.exe (PID: 6492)
- Easyfun_en_50000_ld.exe (PID: 12020)
- Ld9BoxHeadless.exe (PID: 11196)
- Ld9BoxHeadless.exe (PID: 12196)
- inst_X.exe (PID: 10724)
- EasyfunCef.exe (PID: 9648)
- Easyfun.exe (PID: 5300)
- identity_helper.exe (PID: 9008)
Checks supported languages
- LDPlayer9_ens_1001_ld.exe (PID: 1132)
- LDPlayer.exe (PID: 2508)
- dnrepairer.exe (PID: 2188)
- Ld9BoxSVC.exe (PID: 7432)
- driverconfig.exe (PID: 5708)
- dnplayer.exe (PID: 1728)
- Ld9BoxSVC.exe (PID: 7748)
- vbox-img.exe (PID: 6732)
- vbox-img.exe (PID: 7432)
- vbox-img.exe (PID: 7412)
- Ld9BoxHeadless.exe (PID: 2704)
- Ld9BoxHeadless.exe (PID: 7460)
- Ld9BoxHeadless.exe (PID: 2848)
- Ld9BoxHeadless.exe (PID: 7740)
- Ld9BoxHeadless.exe (PID: 1828)
- identity_helper.exe (PID: 12172)
- identity_helper.exe (PID: 10724)
- LeoMoon CPU-V.exe (PID: 10384)
- bugreport.exe (PID: 8480)
- Ld9BoxSVC.exe (PID: 11448)
- Ld9BoxHeadless.exe (PID: 11012)
- Ld9BoxHeadless.exe (PID: 11196)
- dnmultiplayerex.exe (PID: 10836)
- Ld9BoxHeadless.exe (PID: 12196)
- Ld9BoxHeadless.exe (PID: 6492)
- Ld9BoxHeadless.exe (PID: 10628)
- Easyfun_en_50000_ld.exe (PID: 12020)
- inst_X.exe (PID: 10724)
- Easyfun.exe (PID: 5300)
- EasyfunCef.exe (PID: 9648)
- identity_helper.exe (PID: 9008)
- dnplayer.exe (PID: 10620)
Checks proxy server information
- LDPlayer9_ens_1001_ld.exe (PID: 1132)
- LDPlayer.exe (PID: 2508)
- dnplayer.exe (PID: 1728)
- slui.exe (PID: 7184)
- dnplayer.exe (PID: 10620)
- Easyfun_en_50000_ld.exe (PID: 12020)
- inst_X.exe (PID: 10724)
- Easyfun.exe (PID: 5300)
- EasyfunCef.exe (PID: 9648)
Reads the software policy settings
- LDPlayer9_ens_1001_ld.exe (PID: 1132)
- LDPlayer.exe (PID: 2508)
- dnplayer.exe (PID: 1728)
- slui.exe (PID: 7184)
- dnplayer.exe (PID: 10620)
- Easyfun_en_50000_ld.exe (PID: 12020)
- inst_X.exe (PID: 10724)
- Easyfun.exe (PID: 5300)
- EasyfunCef.exe (PID: 9648)
Creates files or folders in the user directory
- LDPlayer9_ens_1001_ld.exe (PID: 1132)
- LDPlayer.exe (PID: 2508)
- dnrepairer.exe (PID: 2188)
- dnplayer.exe (PID: 1728)
- dnplayer.exe (PID: 10620)
- Easyfun_en_50000_ld.exe (PID: 12020)
- inst_X.exe (PID: 10724)
- EasyfunCef.exe (PID: 9648)
Reads the machine GUID from the registry
- LDPlayer.exe (PID: 2508)
- LDPlayer9_ens_1001_ld.exe (PID: 1132)
- dnrepairer.exe (PID: 2188)
- dnplayer.exe (PID: 1728)
- dnplayer.exe (PID: 10620)
- dnmultiplayerex.exe (PID: 10836)
- Easyfun_en_50000_ld.exe (PID: 12020)
- inst_X.exe (PID: 10724)
- Easyfun.exe (PID: 5300)
- EasyfunCef.exe (PID: 9648)
The sample compiled with english language support
- LDPlayer.exe (PID: 2508)
- dnrepairer.exe (PID: 2188)
- dnplayer.exe (PID: 1728)
- msedge.exe (PID: 1800)
- WinRAR.exe (PID: 9128)
- inst_X.exe (PID: 10724)
The sample compiled with chinese language support
- LDPlayer.exe (PID: 2508)
Creates files in the program directory
- dnrepairer.exe (PID: 2188)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7980)
- powershell.exe (PID: 7228)
- powershell.exe (PID: 7276)
- powershell.exe (PID: 9280)
- powershell.exe (PID: 11792)
- powershell.exe (PID: 11944)
- powershell.exe (PID: 10428)
Reads CPU info
- dnplayer.exe (PID: 1728)
- dnplayer.exe (PID: 10620)
Reads Environment values
- identity_helper.exe (PID: 12172)
- identity_helper.exe (PID: 10724)
- identity_helper.exe (PID: 9008)
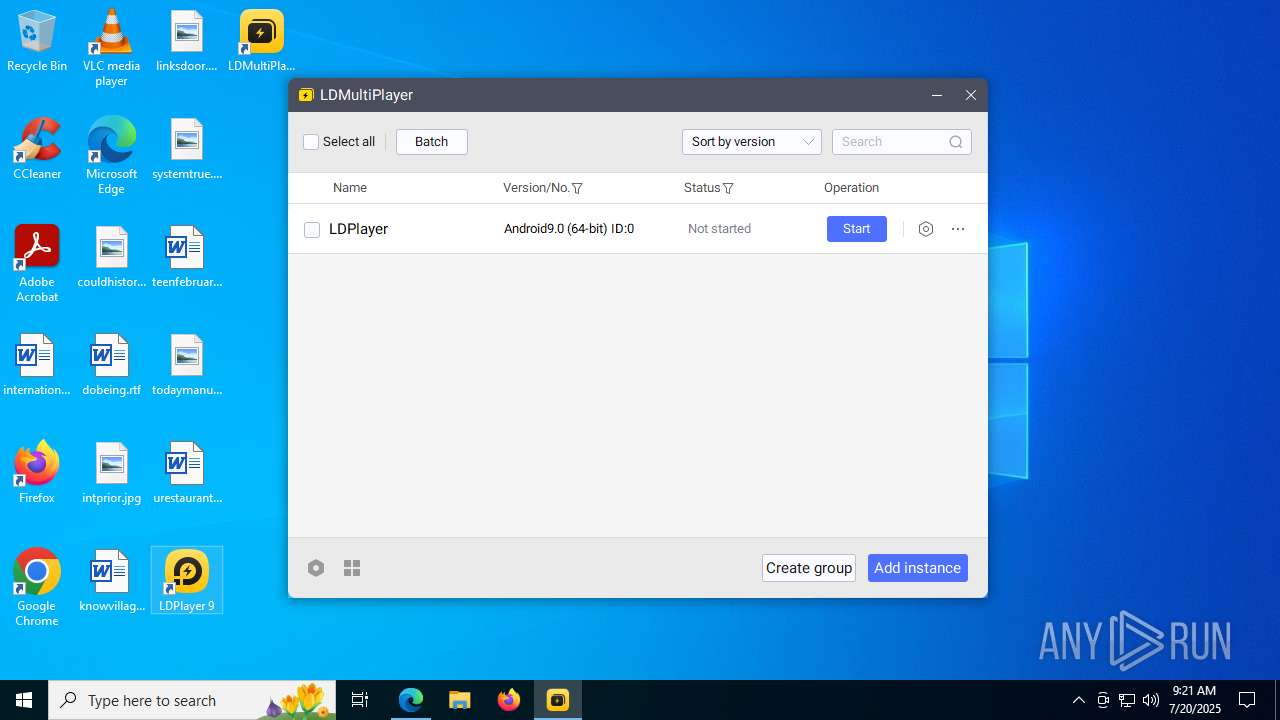
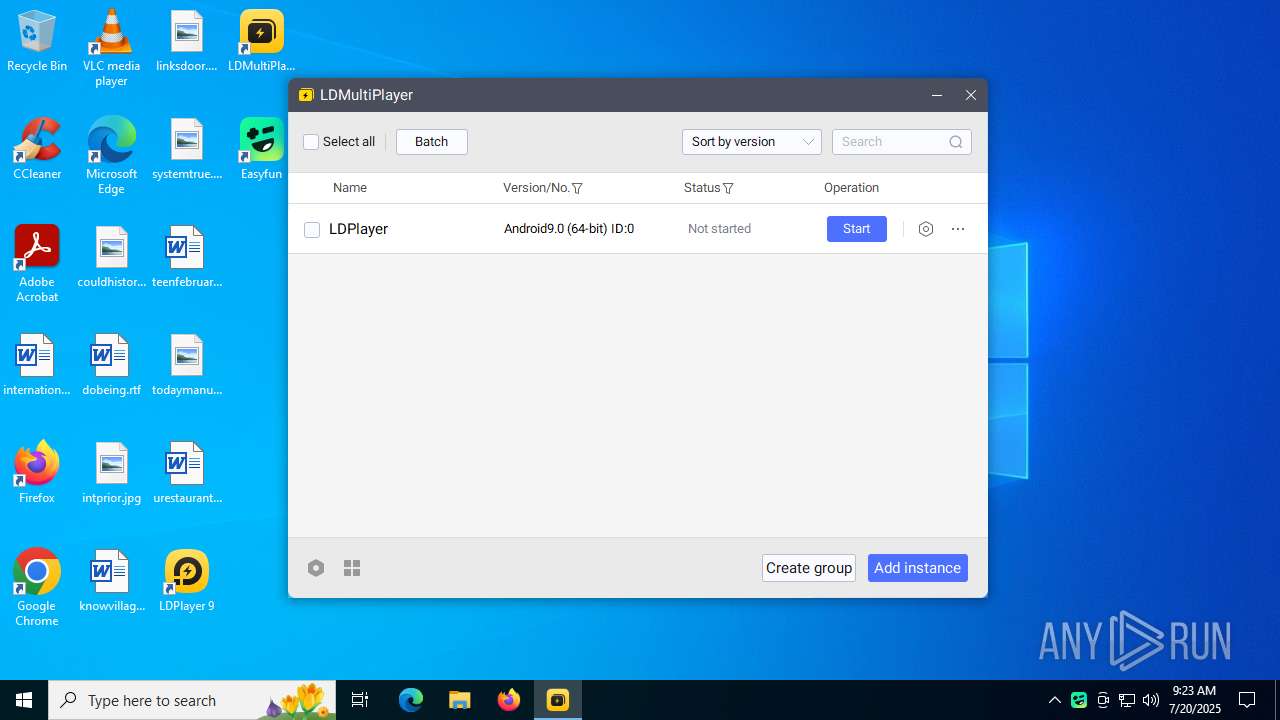
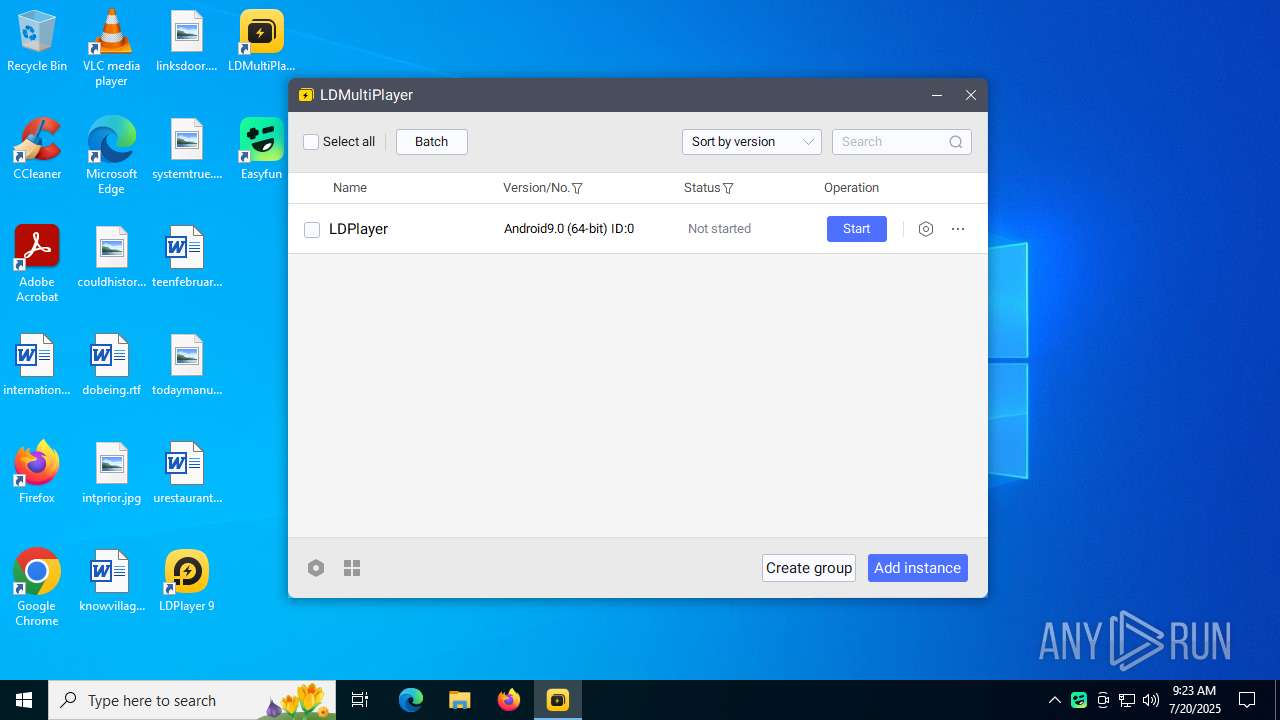
Manual execution by a user
- LeoMoon CPU-V.exe (PID: 10384)
- dnmultiplayerex.exe (PID: 10836)
Reads mouse settings
- LeoMoon CPU-V.exe (PID: 10384)
Create files in a temporary directory
- LeoMoon CPU-V.exe (PID: 10384)
- bugreport.exe (PID: 8480)
- EasyfunCef.exe (PID: 9648)
Launching a file from a Registry key
- inst_X.exe (PID: 10724)
Process checks computer location settings
- Easyfun.exe (PID: 5300)
- EasyfunCef.exe (PID: 9648)
- dnmultiplayerex.exe (PID: 10836)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
419
Monitored processes
261
Malicious processes
12
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 472 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | Ld9BoxHeadless.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 472 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 892 | "net" start cryptsvc | C:\Windows\SysWOW64\net.exe | — | dnrepairer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1132 | "C:\Users\admin\Downloads\LDPlayer9_ens_1001_ld.exe" | C:\Users\admin\Downloads\LDPlayer9_ens_1001_ld.exe | firefox.exe | ||||||||||||
User: admin Company: JUST OKAY Integrity Level: HIGH Description: JUST OKAY Exit code: 5765164 Version: 1.0.0.6 Modules
| |||||||||||||||
| 1268 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2760,i,8205273506809250291,5694751265366868933,262144 --variations-seed-version --mojo-platform-channel-handle=2768 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1328 | "regsvr32" Wintrust.dll /s | C:\Windows\SysWOW64\regsvr32.exe | — | dnrepairer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1576 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --extension-process --renderer-sub-type=extension --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=112 --always-read-main-dll --field-trial-handle=3704,i,8205273506809250291,5694751265366868933,262144 --variations-seed-version --mojo-platform-channel-handle=14828 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1728 | "C:\LDPlayer\LDPlayer9\dnplayer.exe" | C:\LDPlayer\LDPlayer9\dnplayer.exe | LDPlayer9_ens_1001_ld.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225477 Modules
| |||||||||||||||
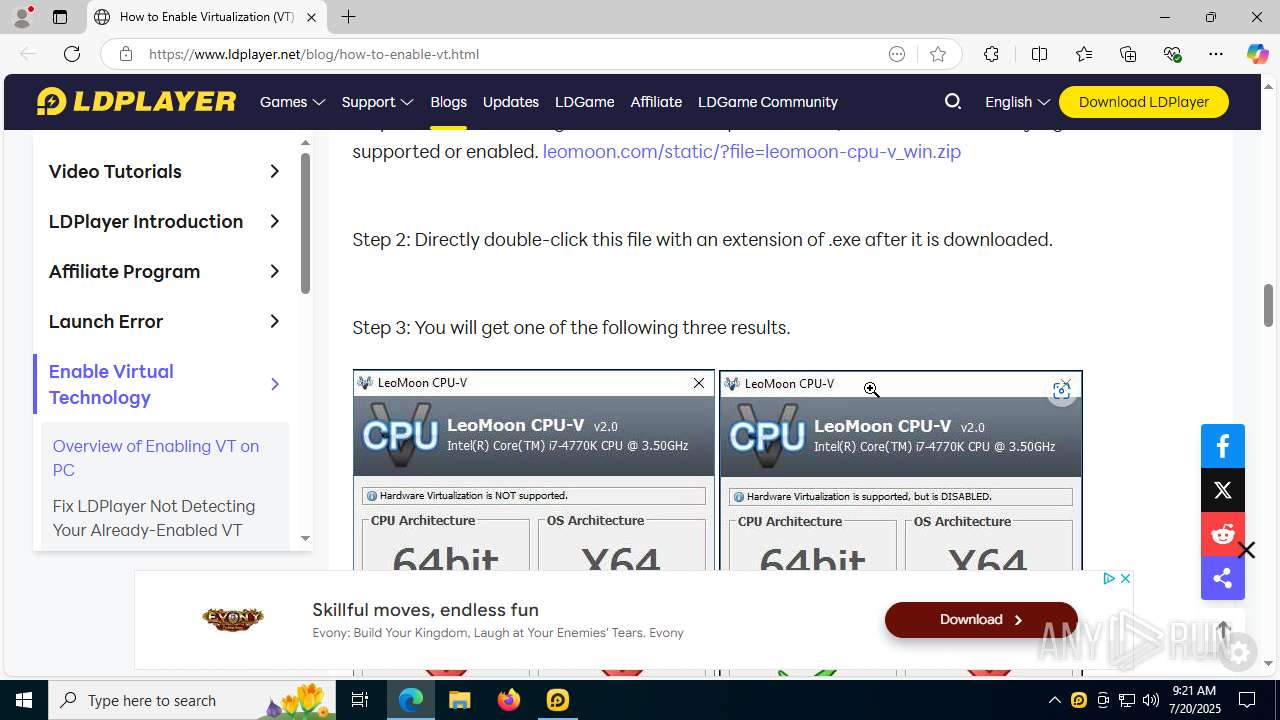
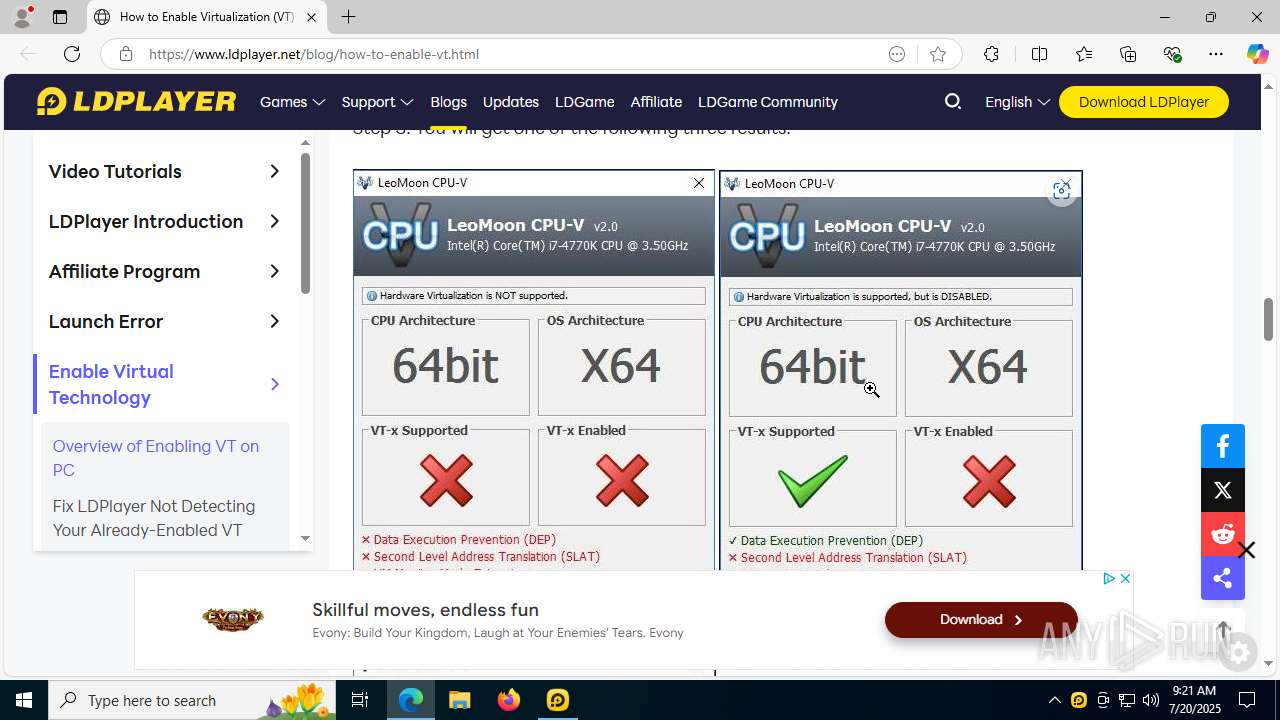
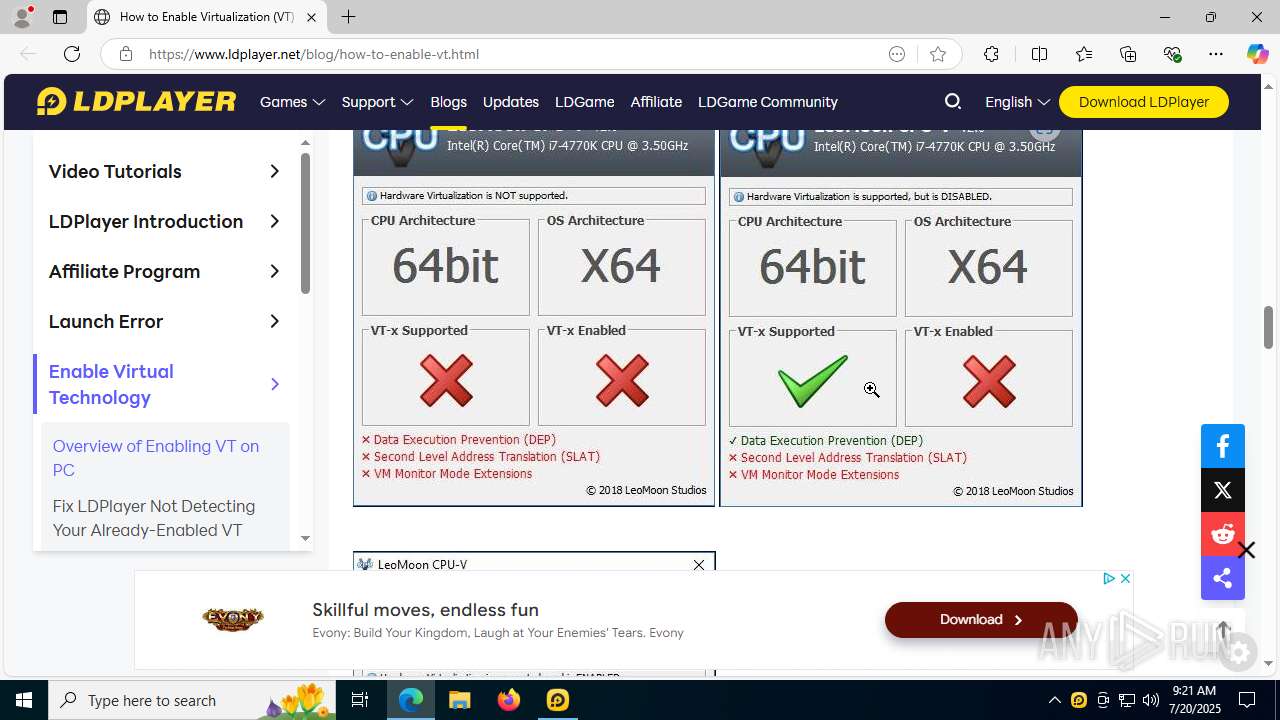
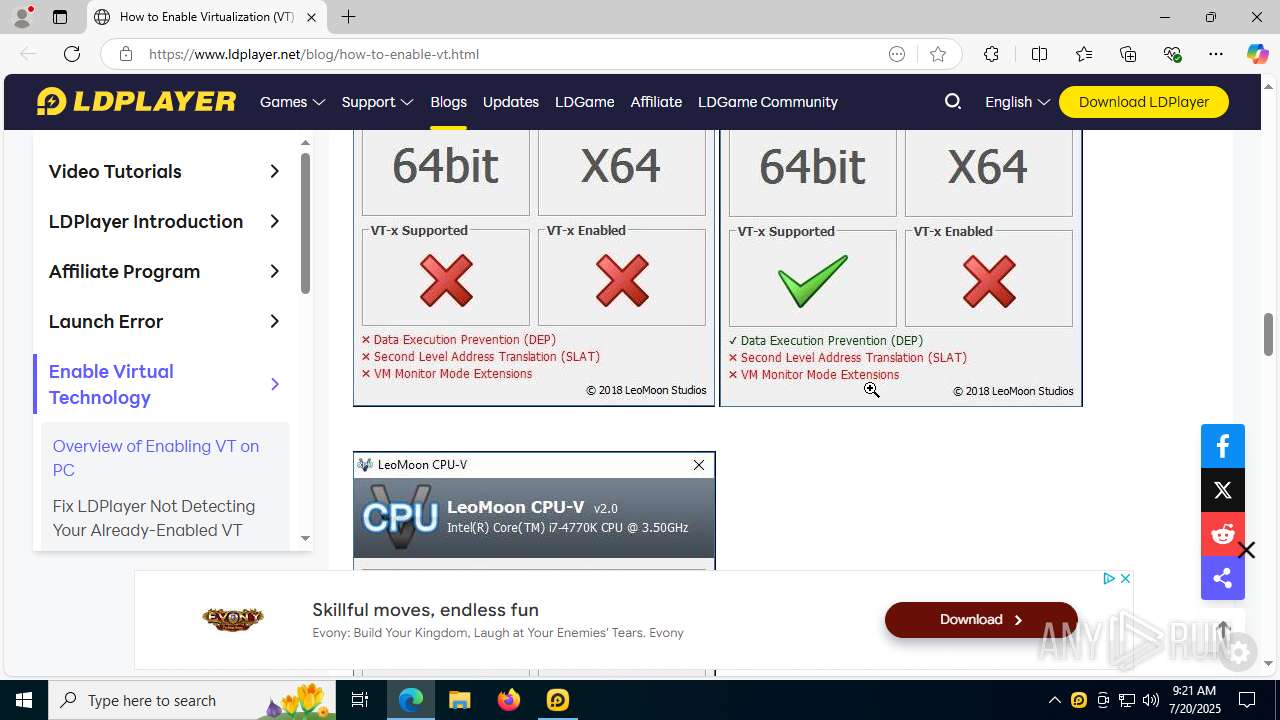
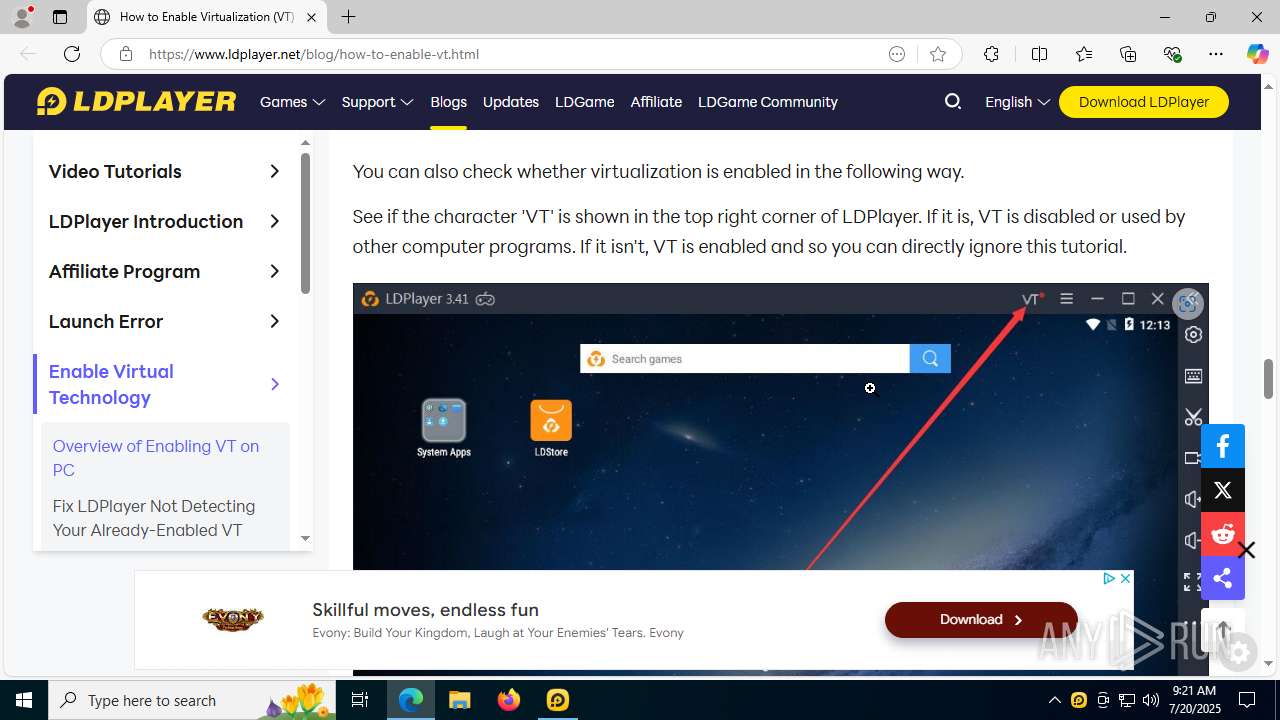
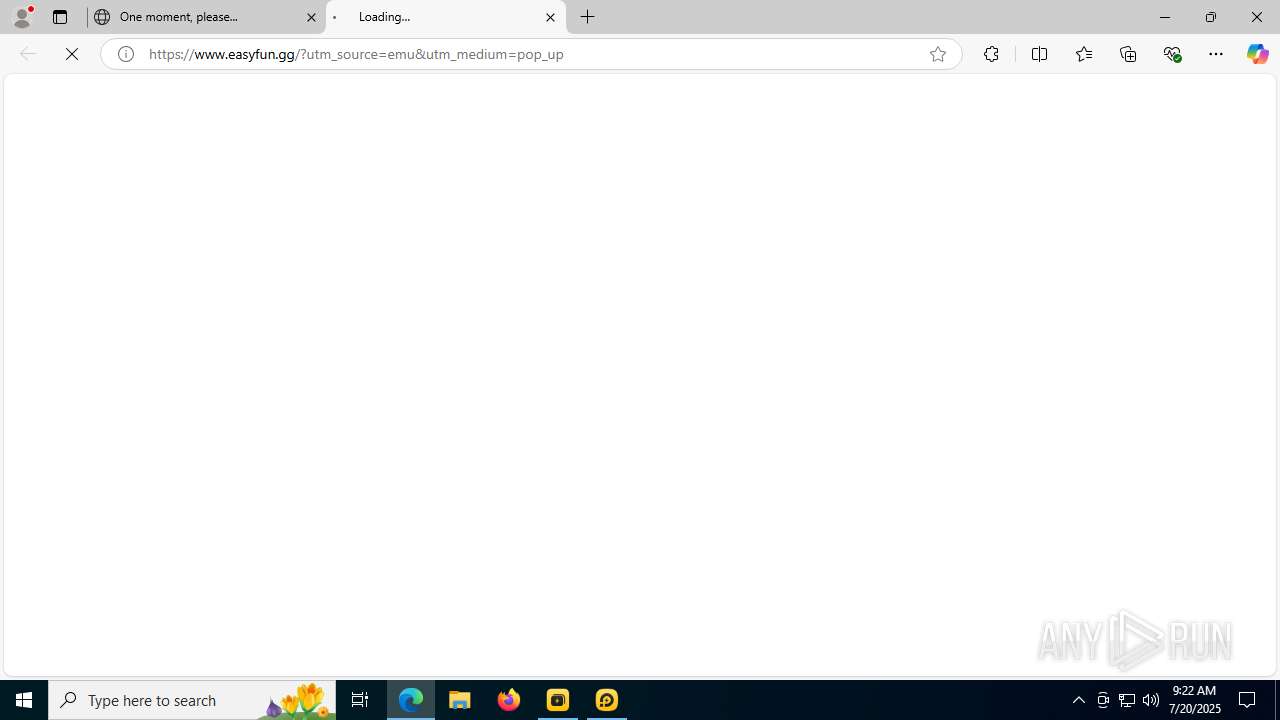
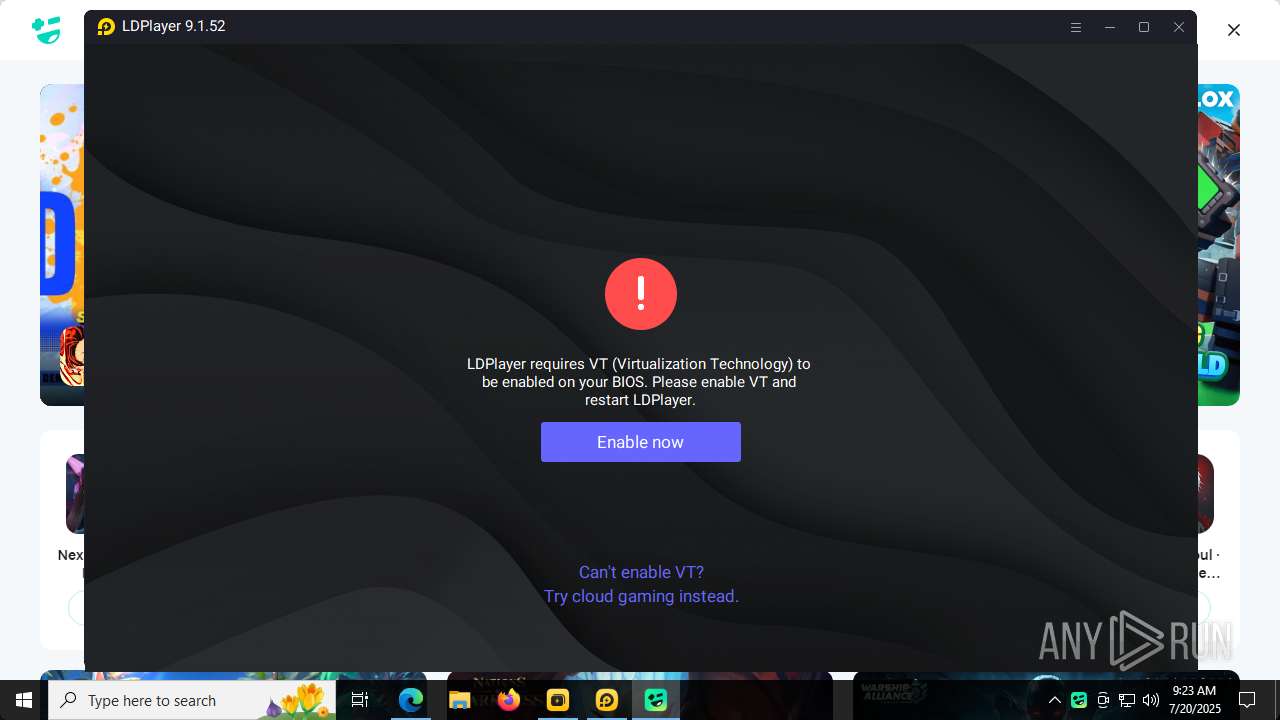
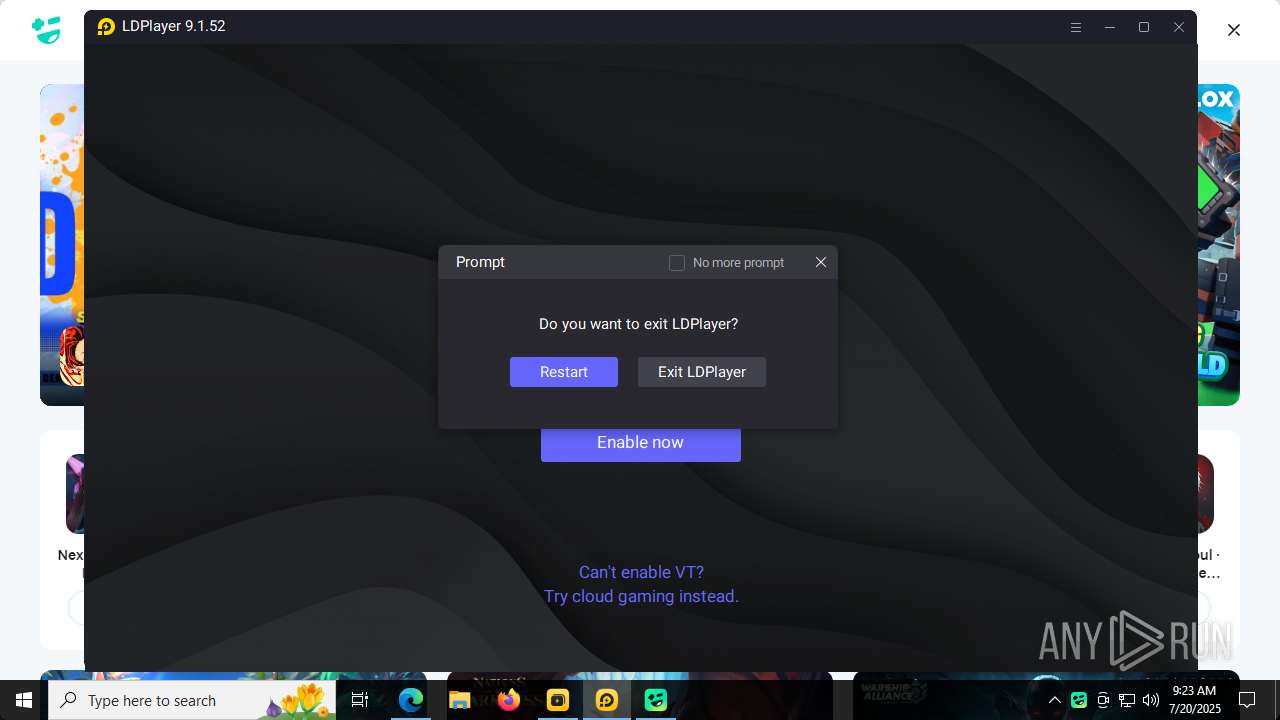
| 1800 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --single-argument https://www.ldplayer.net/blog/how-to-enable-vt.html | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | dnplayer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1808 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --always-read-main-dll --field-trial-handle=3672,i,8205273506809250291,5694751265366868933,262144 --variations-seed-version --mojo-platform-channel-handle=3684 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
107 206
Read events
106 618
Write events
564
Delete events
24
Modification events
| (PID) Process: | (5436) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (1132) LDPlayer9_ens_1001_ld.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\lden |
| Operation: | write | Name: | pcmac |
Value: bd7621d48bf5a0ad3f08a25aa681a252 | |||
| (PID) Process: | (2508) LDPlayer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\ld\dnplayer_en |
| Operation: | write | Name: | pcid |
Value: bd7621d48bf5a0ad3f08a25aa681a252 | |||
| (PID) Process: | (5264) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Cryptography\Providers\Trust\Usages\1.3.6.1.5.5.7.3.3 |
| Operation: | write | Name: | DefaultId |
Value: {00AAC56B-CD44-11D0-8CC2-00C04FC295EE} | |||
| (PID) Process: | (5264) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Cryptography\Providers\Trust\FinalPolicy\{00AAC56B-CD44-11D0-8CC2-00C04FC295EE} |
| Operation: | write | Name: | $DLL |
Value: WINTRUST.DLL | |||
| (PID) Process: | (5264) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Cryptography\Providers\Trust\FinalPolicy\{00AAC56B-CD44-11D0-8CC2-00C04FC295EE} |
| Operation: | write | Name: | $Function |
Value: SoftpubAuthenticode | |||
| (PID) Process: | (5264) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Cryptography\Providers\Trust\Initialization\{64B9D180-8DA2-11CF-8736-00AA00A485EB} |
| Operation: | write | Name: | $DLL |
Value: WINTRUST.DLL | |||
| (PID) Process: | (5264) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Cryptography\Providers\Trust\Initialization\{64B9D180-8DA2-11CF-8736-00AA00A485EB} |
| Operation: | write | Name: | $Function |
Value: SoftpubInitialize | |||
| (PID) Process: | (5264) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Cryptography\Providers\Trust\Message\{64B9D180-8DA2-11CF-8736-00AA00A485EB} |
| Operation: | write | Name: | $DLL |
Value: WINTRUST.DLL | |||
| (PID) Process: | (5264) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Cryptography\Providers\Trust\Message\{64B9D180-8DA2-11CF-8736-00AA00A485EB} |
| Operation: | write | Name: | $Function |
Value: SoftpubLoadMessage | |||
Executable files
523
Suspicious files
959
Text files
651
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5436 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 5436 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 5436 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json.tmp | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 5436 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 5436 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\urlCache-current.bin | binary | |
MD5:3134ED3F12E4F4F8643DB90043B0FD7B | SHA256:26E4F122034D7A03F6DA0E707799B09CBEEBDAF8D7A3133A1F7BD894AC72EEA1 | |||
| 5436 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 5436 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs.js | text | |
MD5:2FD670934FEF0C60E2119BD874AAF470 | SHA256:771A7C83CA015BDBC6AB86A7BD9B1D54E40062E28942D311A9178A0FE6433CF2 | |||
| 5436 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs-1.js | text | |
MD5:2FD670934FEF0C60E2119BD874AAF470 | SHA256:771A7C83CA015BDBC6AB86A7BD9B1D54E40062E28942D311A9178A0FE6433CF2 | |||
| 5436 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 5436 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3561288849sdhlie.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
37
TCP/UDP connections
802
DNS requests
709
Threats
37
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5436 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
5436 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
5436 | firefox.exe | POST | 200 | 142.250.185.227:80 | http://o.pki.goog/s/wr3/k58 | unknown | — | — | whitelisted |
5436 | firefox.exe | POST | 200 | 142.250.185.227:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
5436 | firefox.exe | POST | 200 | 142.250.185.227:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
5436 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
1132 | LDPlayer9_ens_1001_ld.exe | GET | 200 | 104.18.21.213:80 | http://r11.c.lencr.org/62.crl | unknown | — | — | whitelisted |
1132 | LDPlayer9_ens_1001_ld.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSXi0cW5bD2WLrmnasWibg2OuPDpgQUVXRPsnJP9WC6UNHX5lFcmgGHGtcCEAaLh8TalJ4a1%2BN4jLQPsGY%3D | unknown | — | — | whitelisted |
1132 | LDPlayer9_ens_1001_ld.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ5rEWLwbJFq%2FmAU80sm7E%3D | unknown | — | — | whitelisted |
4912 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4916 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5436 | firefox.exe | 34.160.144.191:443 | content-signature-2.cdn.mozilla.net | GOOGLE | US | whitelisted |
5436 | firefox.exe | 23.48.23.26:443 | res.ldrescdn.com | Akamai International B.V. | DE | whitelisted |
5436 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
5436 | firefox.exe | 34.36.137.203:443 | contile.services.mozilla.com | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
5436 | firefox.exe | 34.149.100.209:443 | firefox.settings.services.mozilla.com | GOOGLE | US | whitelisted |
5436 | firefox.exe | 142.250.185.227:80 | o.pki.goog | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
content-signature-2.cdn.mozilla.net |
| whitelisted |
content-signature-chains.prod.autograph.services.mozaws.net |
| whitelisted |
res.ldrescdn.com |
| unknown |
detectportal.firefox.com |
| whitelisted |
a209.dscd.akamai.net |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
spocs.getpocket.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5504 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
5504 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
5504 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
5504 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
5504 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
5504 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
5504 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
5504 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
5504 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
5504 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
Process | Message |
|---|---|
dnplayer.exe | audio wait from recv
|
Ld9BoxHeadless.exe | ldutils myhook enter |
Ld9BoxHeadless.exe | ldutils backgroundPreread enter |
Ld9BoxHeadless.exe | ldutils backgroundPreread leave |
Ld9BoxHeadless.exe | ldutils myhook enter |
Ld9BoxHeadless.exe | ldutils backgroundPreread enter |
Ld9BoxHeadless.exe | ldutils backgroundPreread leave |
Ld9BoxHeadless.exe | ldutils myhook enter |
Ld9BoxHeadless.exe | ldutils backgroundPreread enter |
Ld9BoxHeadless.exe | ldutils backgroundPreread leave |