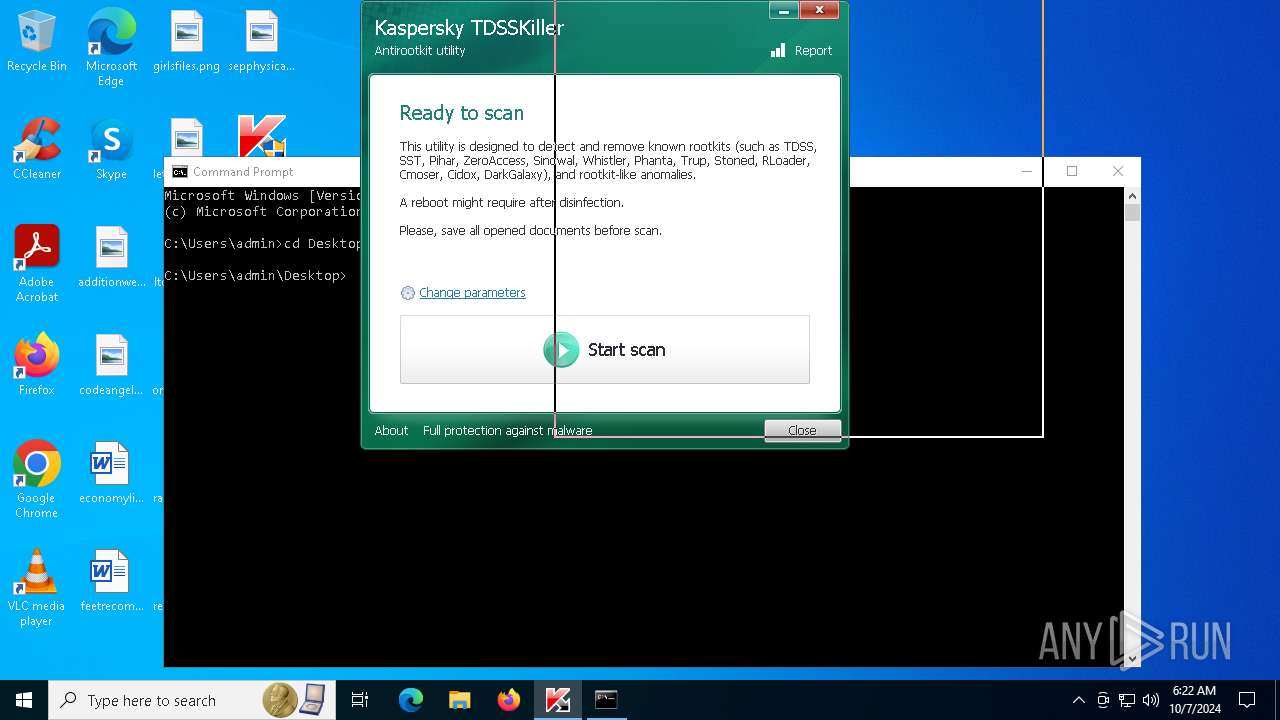
| File name: | tdsskiller.exe |
| Full analysis: | https://app.any.run/tasks/64157917-6de1-4d73-abd2-0a3abbe0f6da |
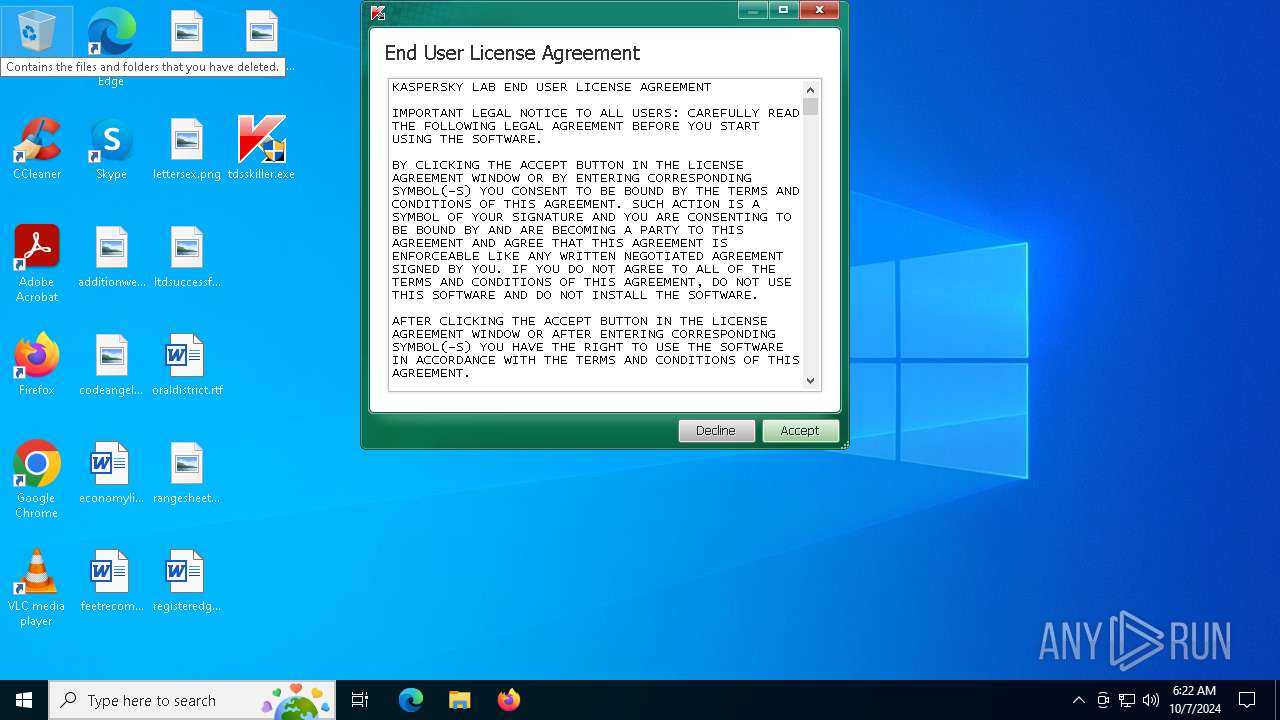
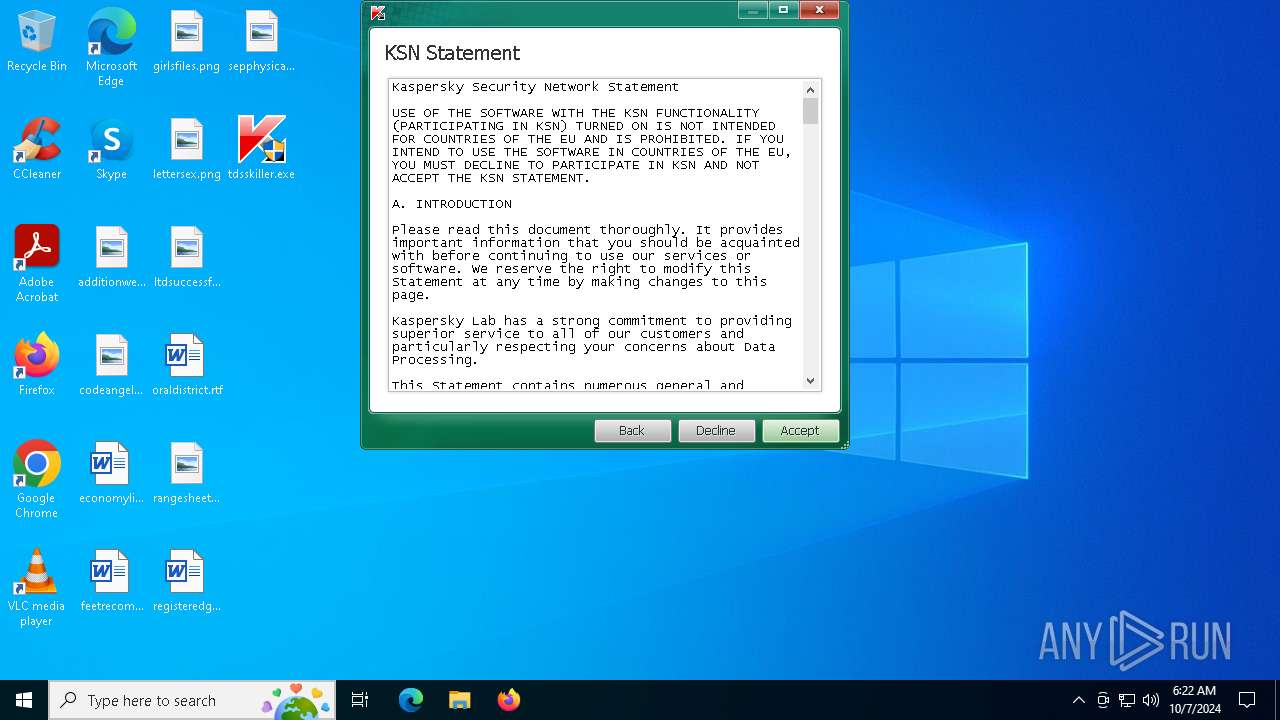
| Verdict: | Malicious activity |
| Analysis date: | October 07, 2024, 06:22:15 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | FF1EFF0E0F1F2EABE1199AE71194E560 |
| SHA1: | 3B035DA6C69F9B05868FFE55D7A267D098C6F290 |
| SHA256: | 2D823C8B6076E932D696E8CB8A2C5C5DF6D392526CBA8E39B64C43635F683009 |
| SSDEEP: | 98304:NV92pm4i4yxEKvBaKrL1D3iTtFyYbRpINzBnOFr9LYUuv6A2:hHeryYbRCPU9UfiA2 |
MALICIOUS
MIMIKATZ has been detected (YARA)
- {1766D45B-6694-4488-81EA-F165807BBFD7}.exe (PID: 4936)
SUSPICIOUS
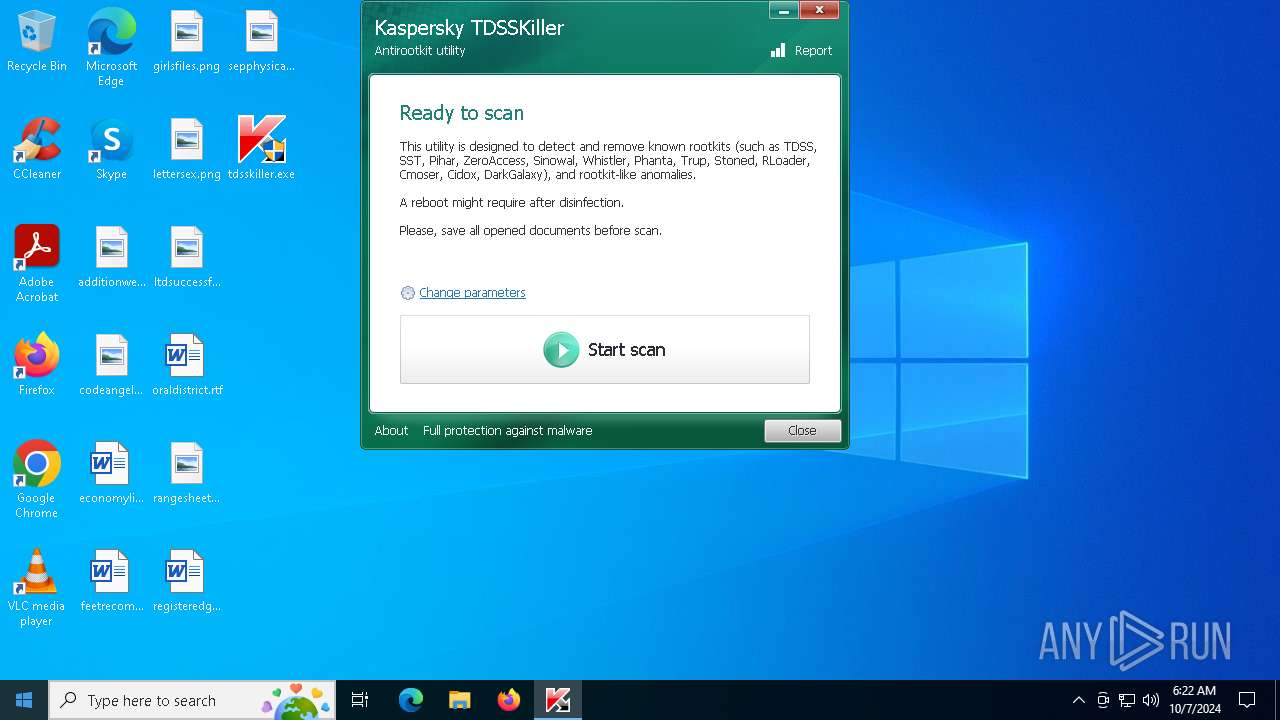
Executable content was dropped or overwritten
- tdsskiller.exe (PID: 5040)
- {1766D45B-6694-4488-81EA-F165807BBFD7}.exe (PID: 4936)
Potential Corporate Privacy Violation
- {1766D45B-6694-4488-81EA-F165807BBFD7}.exe (PID: 4936)
Drops a system driver (possible attempt to evade defenses)
- {1766D45B-6694-4488-81EA-F165807BBFD7}.exe (PID: 4936)
INFO
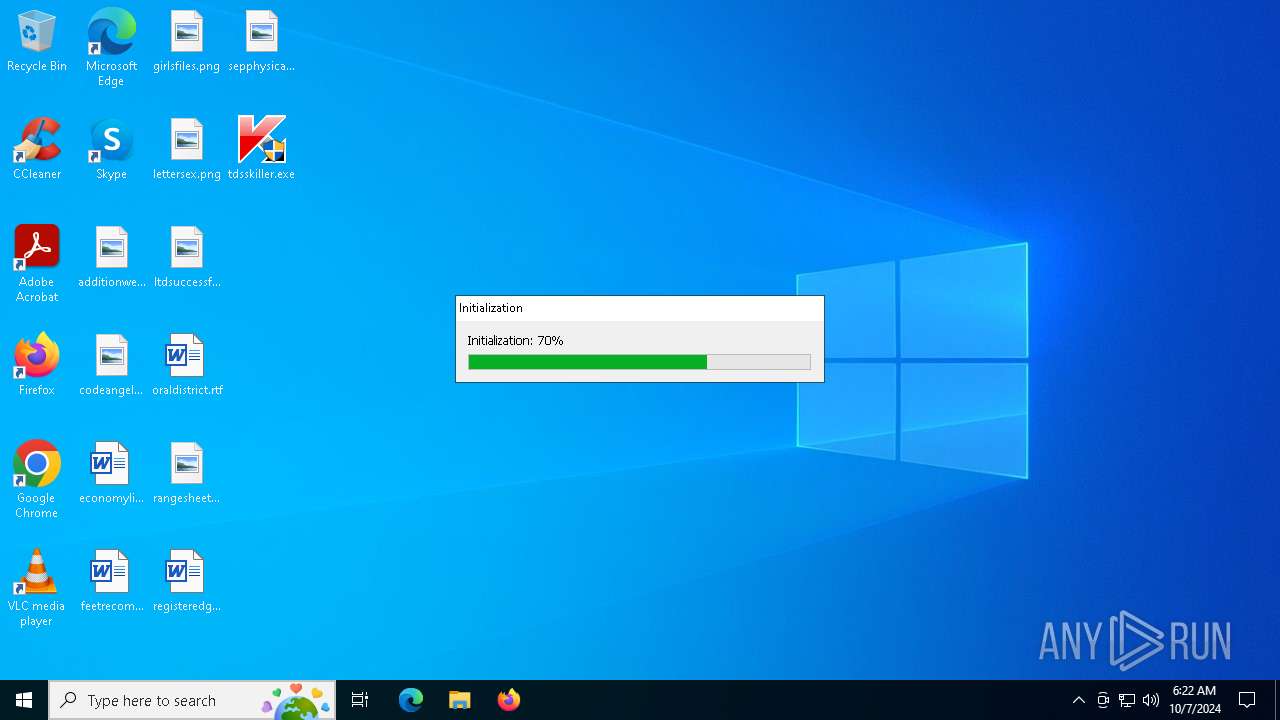
Create files in a temporary directory
- tdsskiller.exe (PID: 5040)
Checks supported languages
- tdsskiller.exe (PID: 5040)
- {1766D45B-6694-4488-81EA-F165807BBFD7}.exe (PID: 4936)
Reads the computer name
- {1766D45B-6694-4488-81EA-F165807BBFD7}.exe (PID: 4936)
Reads the software policy settings
- {1766D45B-6694-4488-81EA-F165807BBFD7}.exe (PID: 4936)
UPX packer has been detected
- tdsskiller.exe (PID: 5040)
- {1766D45B-6694-4488-81EA-F165807BBFD7}.exe (PID: 4936)
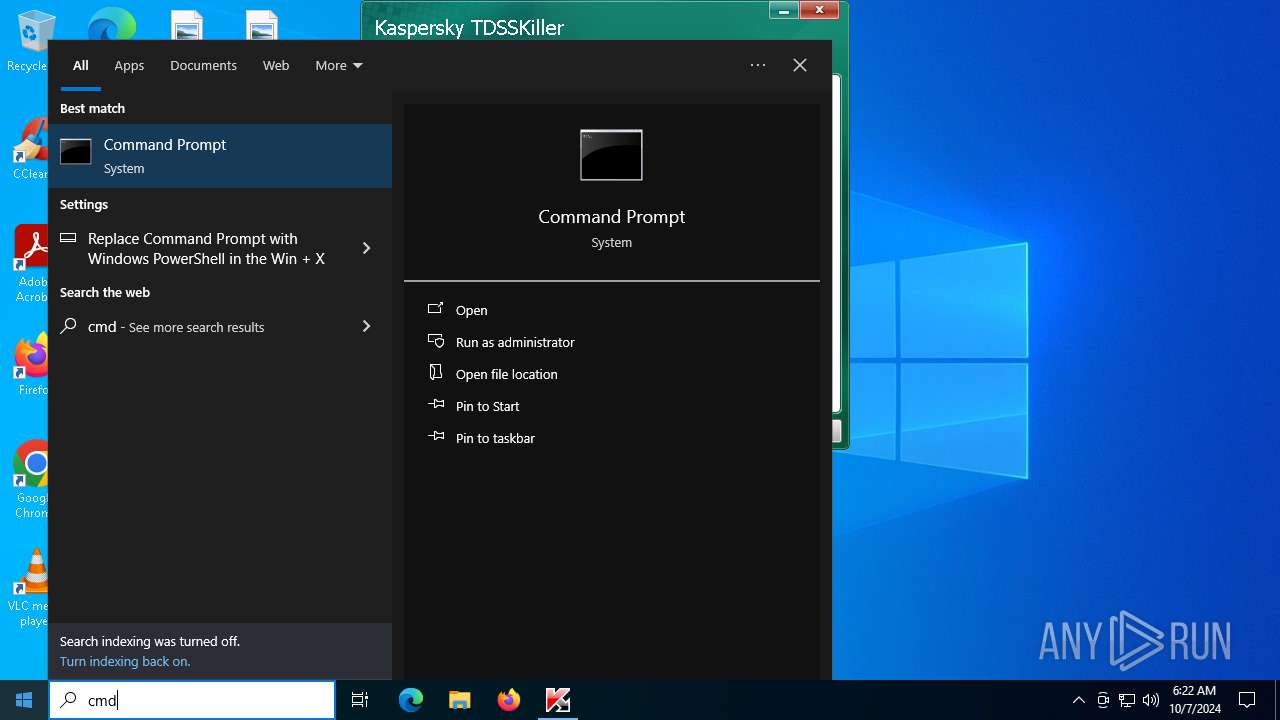
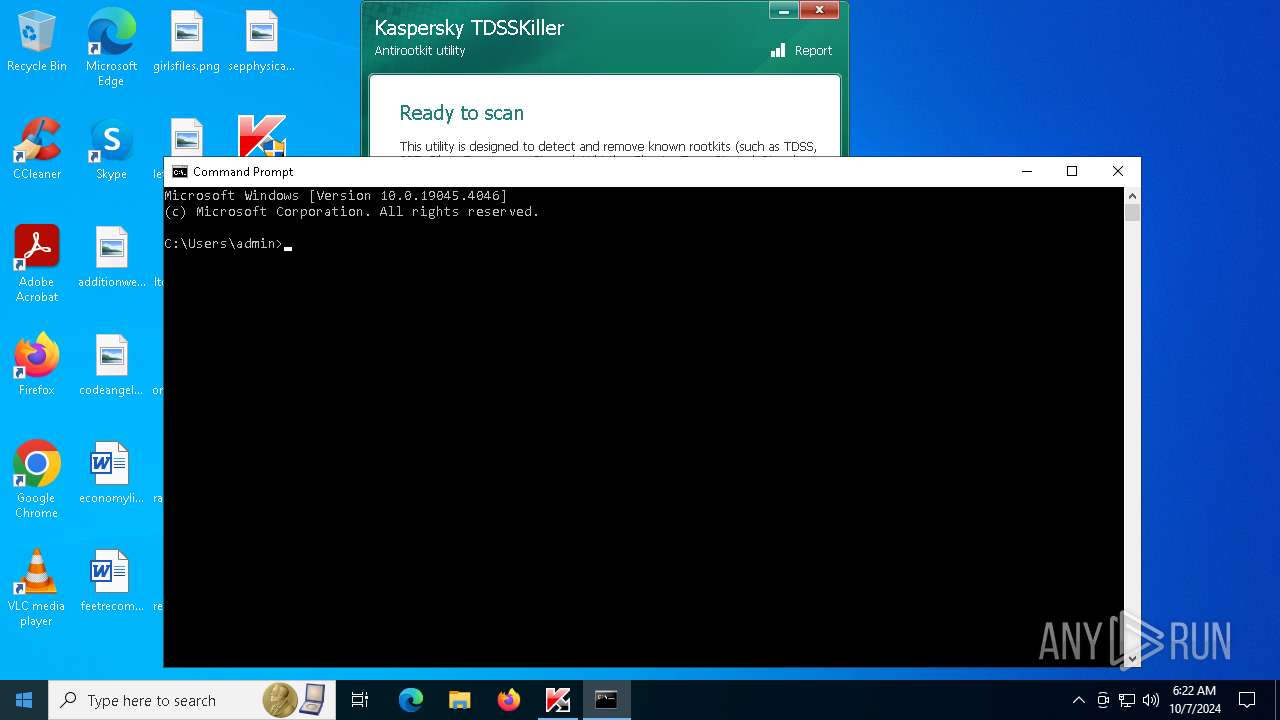
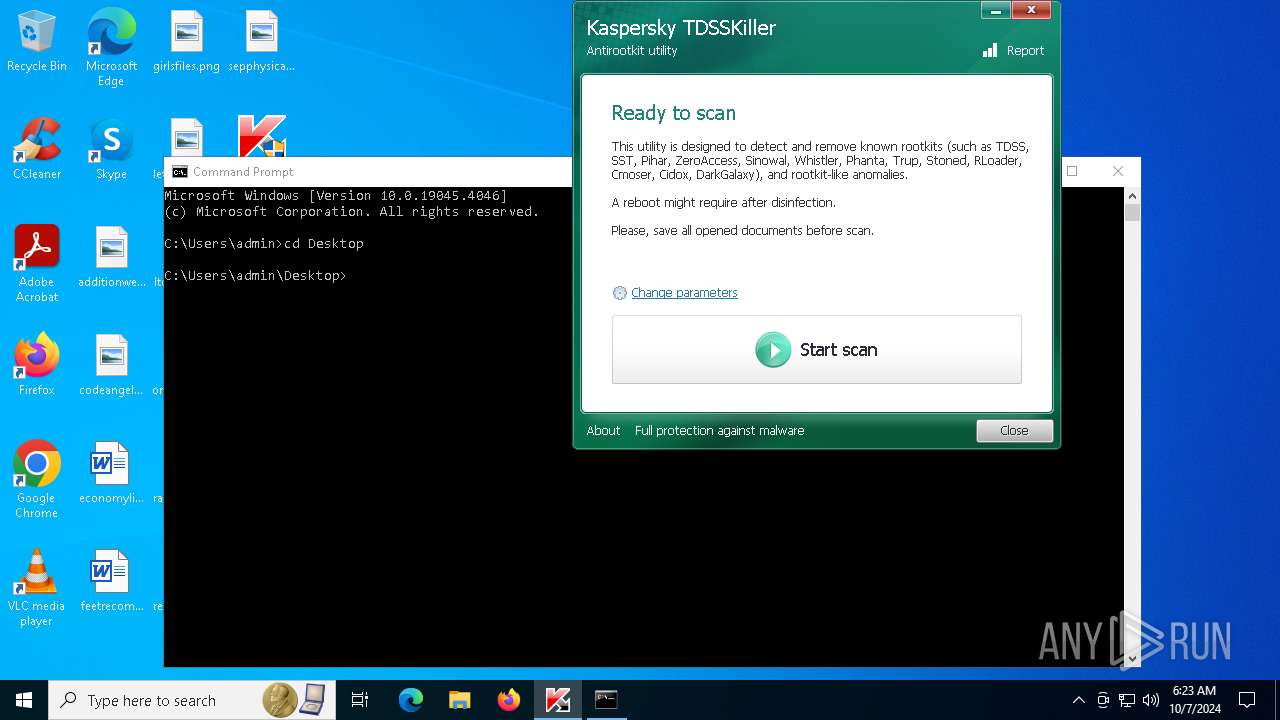
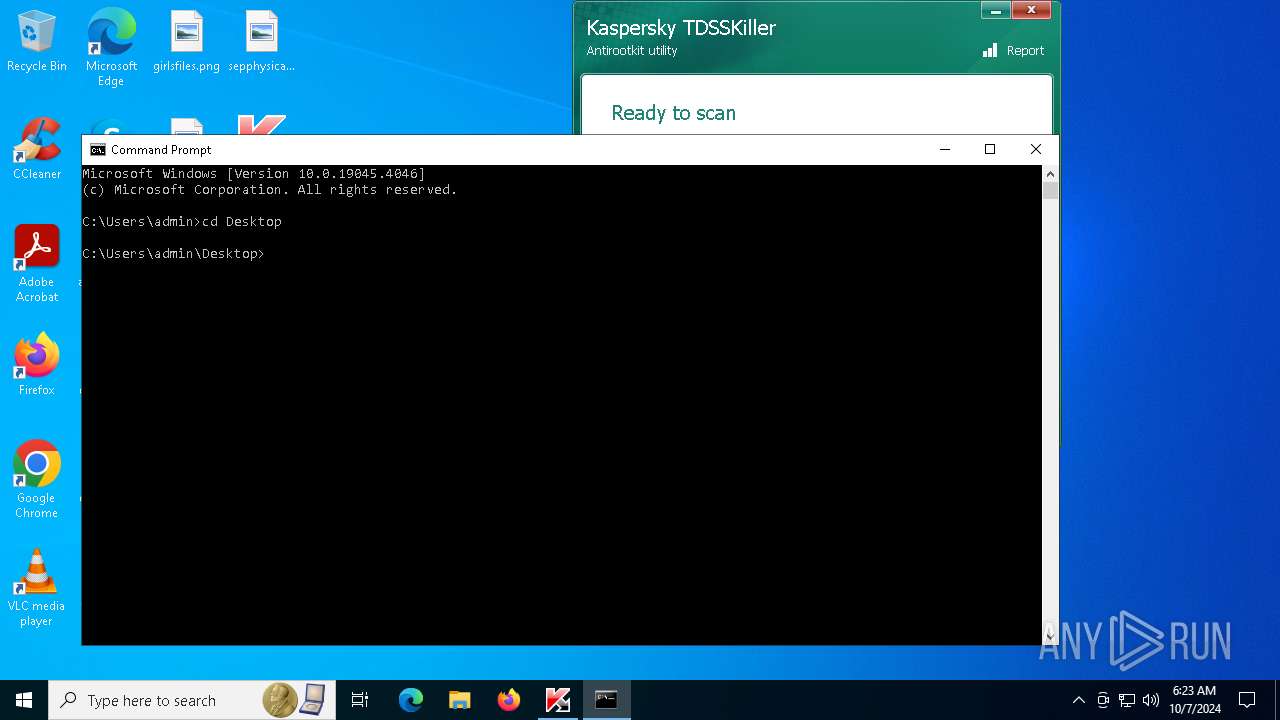
Manual execution by a user
- cmd.exe (PID: 3832)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (30.7) |
|---|---|---|
| .exe | | | UPX compressed Win32 Executable (30.1) |
| .exe | | | Win32 EXE Yoda's Crypter (29.5) |
| .exe | | | Win32 Executable (generic) (5) |
| .exe | | | Generic Win/DOS Executable (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2015:12:11 18:13:14+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 75776 |
| InitializedDataSize: | 4888064 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3200 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
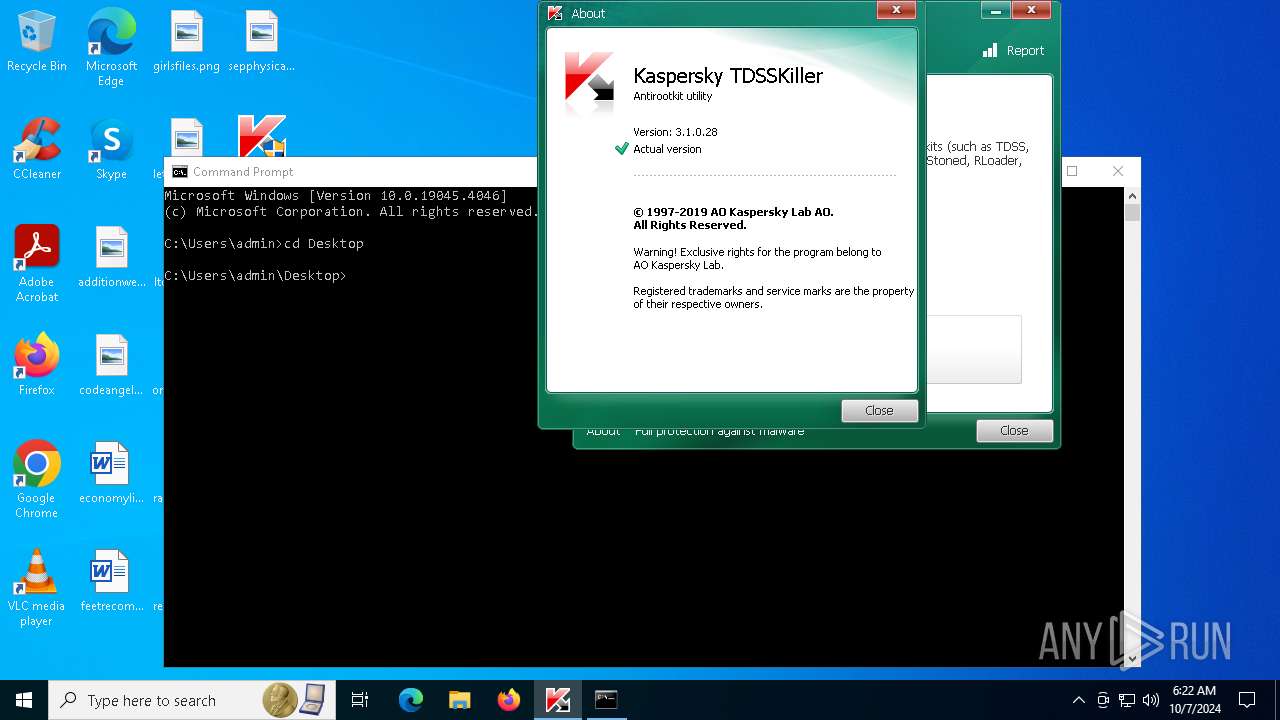
| FileVersionNumber: | 3.1.0.28 |
| ProductVersionNumber: | 3.1.0.28 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | AO Kaspersky Lab |
| LegalCopyright: | © 1997-2019 AO Kaspersky Lab. |
| LegalTrademarks: | Kaspersky™ Anti-Virus ® is registered trademark of AO Kaspersky Lab. |
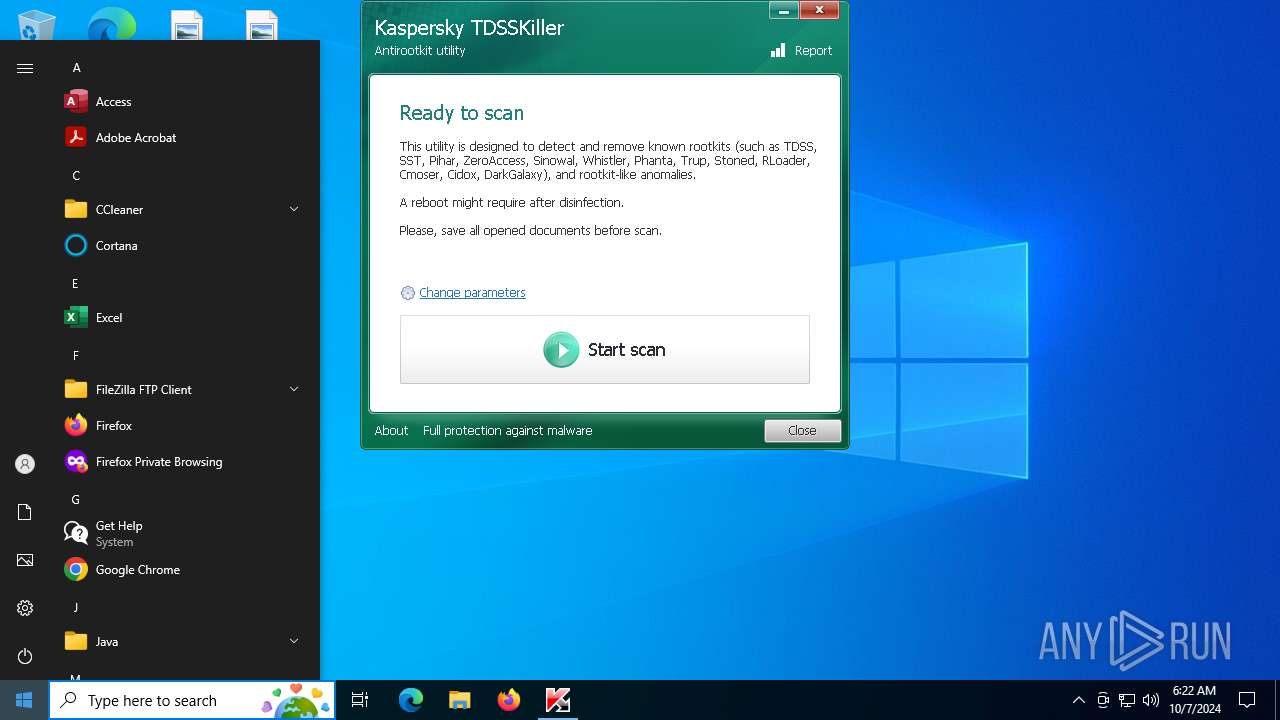
| ProductName: | TDSSKiller |
| ProductVersion: | 3.1.0.28 |
| FileVersion: | 3.1.0.28 |
| FileDescription: | TDSS rootkit removing tool |
| InternalName: | TDSSKiller |
| OriginalFileName: | TDSSKiller.exe |
Total processes
132
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3372 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3832 | "C:\WINDOWS\system32\cmd.exe" | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4936 | "C:\Users\admin\AppData\Local\Temp\{6E1F686E-9756-4217-A1B8-AF6A2FF880BE}\{1766D45B-6694-4488-81EA-F165807BBFD7}.exe" | C:\Users\admin\AppData\Local\Temp\{6E1F686E-9756-4217-A1B8-AF6A2FF880BE}\{1766D45B-6694-4488-81EA-F165807BBFD7}.exe | tdsskiller.exe | ||||||||||||
User: admin Company: AO Kaspersky Lab Integrity Level: HIGH Description: TDSS rootkit removing tool Version: 3.1.0.28 Modules
| |||||||||||||||
| 5040 | "C:\Users\admin\Desktop\tdsskiller.exe" | C:\Users\admin\Desktop\tdsskiller.exe | explorer.exe | ||||||||||||
User: admin Company: AO Kaspersky Lab Integrity Level: HIGH Description: TDSS rootkit removing tool Version: 3.1.0.28 Modules
| |||||||||||||||
| 6412 | "C:\Users\admin\Desktop\tdsskiller.exe" | C:\Users\admin\Desktop\tdsskiller.exe | — | explorer.exe | |||||||||||
User: admin Company: AO Kaspersky Lab Integrity Level: MEDIUM Description: TDSS rootkit removing tool Exit code: 3221226540 Version: 3.1.0.28 Modules
| |||||||||||||||
Total events
617
Read events
610
Write events
4
Delete events
3
Modification events
| (PID) Process: | (4936) {1766D45B-6694-4488-81EA-F165807BBFD7}.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\66172066 |
| Operation: | write | Name: | Type |
Value: 1 | |||
| (PID) Process: | (4936) {1766D45B-6694-4488-81EA-F165807BBFD7}.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\66172066 |
| Operation: | write | Name: | ErrorControl |
Value: 1 | |||
| (PID) Process: | (4936) {1766D45B-6694-4488-81EA-F165807BBFD7}.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\66172066 |
| Operation: | write | Name: | Start |
Value: 3 | |||
| (PID) Process: | (4936) {1766D45B-6694-4488-81EA-F165807BBFD7}.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\66172066 |
| Operation: | write | Name: | ImagePath |
Value: system32\drivers\47972708.sys | |||
| (PID) Process: | (4936) {1766D45B-6694-4488-81EA-F165807BBFD7}.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\66172066 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (4936) {1766D45B-6694-4488-81EA-F165807BBFD7}.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\SafeBoot\Minimal\66172066.sys |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (4936) {1766D45B-6694-4488-81EA-F165807BBFD7}.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\SafeBoot\Network\66172066.sys |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
12
Suspicious files
1
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4936 | {1766D45B-6694-4488-81EA-F165807BBFD7}.exe | C:\Users\admin\AppData\Local\Temp\{B7510BEB-9ADE-423A-9207-7B6A9B6D59B1}\{FA58135A-D52D-40CF-9798-8C6AB8B7C10C}.tmp | executable | |
MD5:E027A6E99EF709AFD195FD6329224C47 | SHA256:B31B85BF369DC36363B0E527AE3B8E95B33699D17D09C6313C43E7373A3E6874 | |||
| 4936 | {1766D45B-6694-4488-81EA-F165807BBFD7}.exe | C:\Users\admin\AppData\Local\Temp\{B7510BEB-9ADE-423A-9207-7B6A9B6D59B1}\{15293A09-3196-4857-888F-9A52F315047D}.tmp | executable | |
MD5:AB67816718E5C65CC326BE56AC0B9E73 | SHA256:D6F19026CB87C9BB5521D668B13347B68F297FCE34C5F1BFE530574B16ADB2D5 | |||
| 5040 | tdsskiller.exe | C:\Users\admin\AppData\Local\Temp\{6E1F686E-9756-4217-A1B8-AF6A2FF880BE}\{1766D45B-6694-4488-81EA-F165807BBFD7}.exe | executable | |
MD5:A290E9849A0C0948136A785F5096F48B | SHA256:FB3269CDA55197891F2FE9971D4C933D3C8BB4CCBE8EA6676F4CA3288B5A7EAD | |||
| 4936 | {1766D45B-6694-4488-81EA-F165807BBFD7}.exe | C:\Users\admin\AppData\Local\Temp\{B7510BEB-9ADE-423A-9207-7B6A9B6D59B1}\{EDCDBC31-D5D8-4E8C-B594-8C8CB6036913}.tmp | executable | |
MD5:85D8D497E3CFCD66607DAD332378DE8B | SHA256:FEB2FF9315B41A7D13C9F3EB4CFDD612C951CA02330BC5A9129881E148769C7F | |||
| 4936 | {1766D45B-6694-4488-81EA-F165807BBFD7}.exe | C:\Windows\System32\drivers\47972708.sys | executable | |
MD5:4C58AFFCD0C9B0C7528C05D71EA08C63 | SHA256:3EFDFB47B0556E97256447F7D619A293D713327496A9524BFBE6A3294E9A7DF4 | |||
| 4936 | {1766D45B-6694-4488-81EA-F165807BBFD7}.exe | C:\Users\admin\AppData\Local\Temp\{B7510BEB-9ADE-423A-9207-7B6A9B6D59B1}\{0B1476A0-7441-4287-80AC-F7658159FEE0}.tmp | executable | |
MD5:CD0DAF878147B723108C428370FF0355 | SHA256:A5C3D8A516FD0A15DAAB442DA424E996112C355239B985413EAA4DC1FAB76303 | |||
| 4936 | {1766D45B-6694-4488-81EA-F165807BBFD7}.exe | C:\Users\admin\AppData\Local\Temp\{B7510BEB-9ADE-423A-9207-7B6A9B6D59B1}\{60B2249D-A936-4FF9-BFAA-0ECAEAAE4FC2}.tmp | text | |
MD5:52669129A8521AD58AE5BF859D66F7DD | SHA256:09A97C2B223BDD638647227E9733C96590AE8403ED24C2D9B28DEA83C435A2FE | |||
| 4936 | {1766D45B-6694-4488-81EA-F165807BBFD7}.exe | C:\Users\admin\AppData\Local\Temp\{B7510BEB-9ADE-423A-9207-7B6A9B6D59B1}\{207918B5-6F50-485F-96B5-70D6574C3ACC}.tmp | executable | |
MD5:C74D46C1F542F5FEB9B7E1A8EC04986D | SHA256:FA83733A81BA8D96EDFD15C1914D5A6056D73C61540C8747E9AE1343DA47A63D | |||
| 4936 | {1766D45B-6694-4488-81EA-F165807BBFD7}.exe | C:\Users\admin\AppData\Local\Temp\{B7510BEB-9ADE-423A-9207-7B6A9B6D59B1}\{96F7519E-6FDC-41B3-8C6B-973CFC4AECA4}.tmp | text | |
MD5:0A52D6A1DD74FEB5F50D5D35BC1A51C6 | SHA256:96EDFD40D55FEC6F56E6C6089750211C42427E488ADADB3765FEF7357346BDCF | |||
| 4936 | {1766D45B-6694-4488-81EA-F165807BBFD7}.exe | C:\Users\admin\AppData\Local\Temp\{B7510BEB-9ADE-423A-9207-7B6A9B6D59B1}\{722C05D7-C545-4EA1-BBD0-938C701553F0}.tmp | executable | |
MD5:96D681B7DE0BA6BFA1DC55915003CD05 | SHA256:26CDA6A9A67F20A494F0EF3577D14F5DDA1F0D4428891DBD271A757833285939 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
67
DNS requests
23
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2120 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4936 | {1766D45B-6694-4488-81EA-F165807BBFD7}.exe | GET | 301 | 185.85.15.38:80 | http://support.kaspersky.com/viruses/tdsskiller.xml | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
1984 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5732 | SIHClient.exe | GET | 200 | 104.79.89.142:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5732 | SIHClient.exe | GET | 200 | 104.79.89.142:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3916 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
— | — | 40.126.31.73:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
— | — | 40.113.103.199:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1768 | svchost.exe | 40.126.31.73:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
support.kaspersky.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
Threats
1 ETPRO signatures available at the full report