| File name: | tdsskiller.exe |
| Full analysis: | https://app.any.run/tasks/1219db37-1026-473d-bb16-4b5185e56112 |
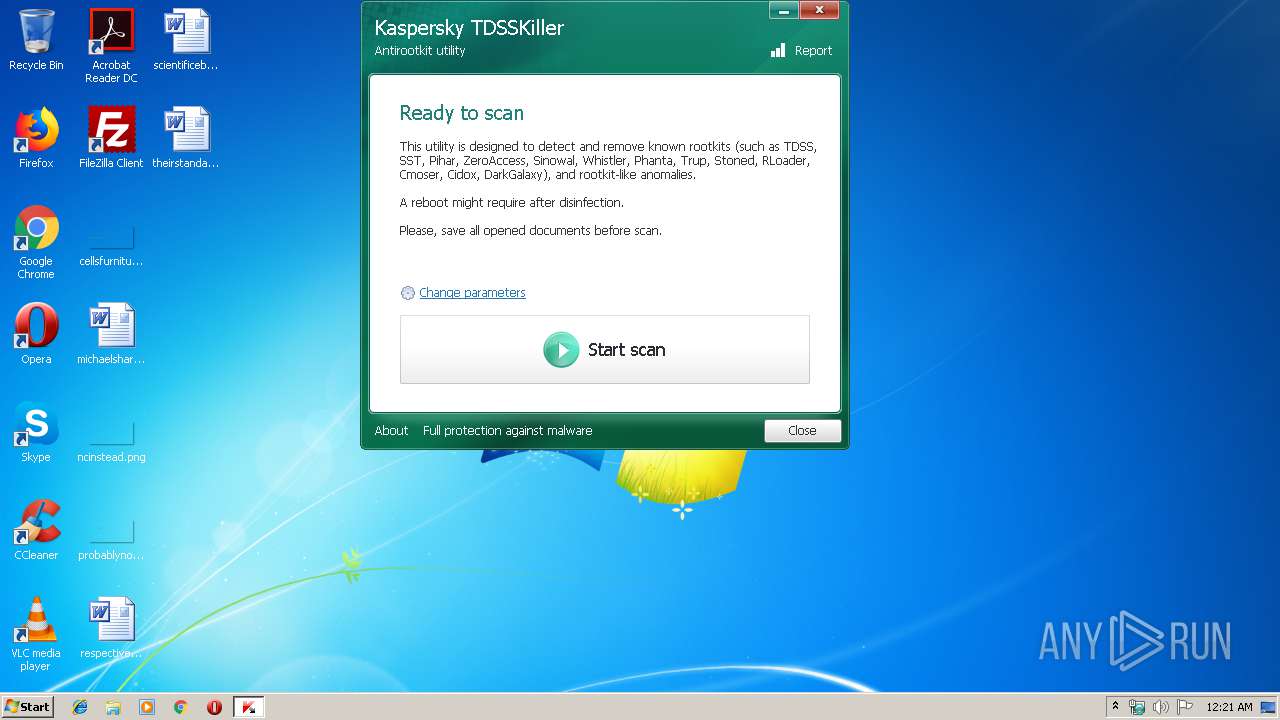
| Verdict: | Malicious activity |
| Analysis date: | October 13, 2019, 23:20:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | FF1EFF0E0F1F2EABE1199AE71194E560 |
| SHA1: | 3B035DA6C69F9B05868FFE55D7A267D098C6F290 |
| SHA256: | 2D823C8B6076E932D696E8CB8A2C5C5DF6D392526CBA8E39B64C43635F683009 |
| SSDEEP: | 98304:NV92pm4i4yxEKvBaKrL1D3iTtFyYbRpINzBnOFr9LYUuv6A2:hHeryYbRCPU9UfiA2 |
MALICIOUS
Application was dropped or rewritten from another process
- {248B0CB9-6123-4D20-82AE-62163260F936}.exe (PID: 2468)
Deletes the SafeBoot registry key
- {248B0CB9-6123-4D20-82AE-62163260F936}.exe (PID: 2468)
SUSPICIOUS
Creates files in the driver directory
- {248B0CB9-6123-4D20-82AE-62163260F936}.exe (PID: 2468)
Executable content was dropped or overwritten
- tdsskiller.exe (PID: 2184)
- {248B0CB9-6123-4D20-82AE-62163260F936}.exe (PID: 2468)
Low-level read access rights to disk partition
- {248B0CB9-6123-4D20-82AE-62163260F936}.exe (PID: 2468)
Creates files in the Windows directory
- {248B0CB9-6123-4D20-82AE-62163260F936}.exe (PID: 2468)
Creates or modifies windows services
- {248B0CB9-6123-4D20-82AE-62163260F936}.exe (PID: 2468)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (30.7) |
|---|---|---|
| .exe | | | UPX compressed Win32 Executable (30.1) |
| .exe | | | Win32 EXE Yoda's Crypter (29.5) |
| .exe | | | Win32 Executable (generic) (5) |
| .exe | | | Generic Win/DOS Executable (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2015:12:11 19:13:14+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 75776 |
| InitializedDataSize: | 4888064 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3200 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.1.0.28 |
| ProductVersionNumber: | 3.1.0.28 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
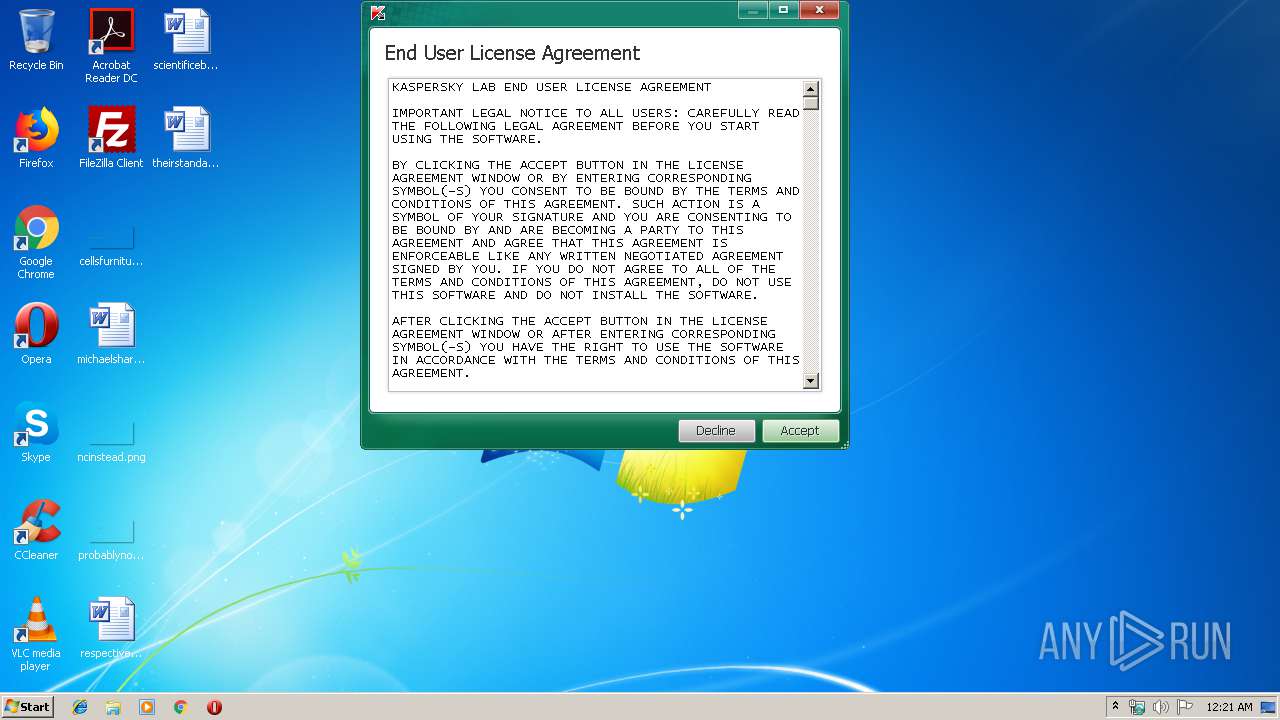
| CompanyName: | AO Kaspersky Lab |
| LegalCopyright: | © 1997-2019 AO Kaspersky Lab. |
| LegalTrademarks: | Kaspersky™ Anti-Virus ® is registered trademark of AO Kaspersky Lab. |
| ProductName: | TDSSKiller |
| ProductVersion: | 3.1.0.28 |
| FileVersion: | 3.1.0.28 |
| FileDescription: | TDSS rootkit removing tool |
| InternalName: | TDSSKiller |
| OriginalFileName: | TDSSKiller.exe |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 11-Dec-2015 18:13:14 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | AO Kaspersky Lab |
| LegalCopyright: | © 1997-2019 AO Kaspersky Lab. |
| LegalTrademarks: | Kaspersky™ Anti-Virus ® is registered trademark of AO Kaspersky Lab. |
| ProductName: | TDSSKiller |
| ProductVersion: | 3.1.0.28 |
| FileVersion: | 3.1.0.28 |
| FileDescription: | TDSS rootkit removing tool |
| InternalName: | TDSSKiller |
| OriginalFilename: | TDSSKiller.exe |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 11-Dec-2015 18:13:14 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001269F | 0x00012800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.61234 |
.rdata | 0x00014000 | 0x0000714A | 0x00007200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.20588 |
.data | 0x0001C000 | 0x000013D4 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.39338 |
.rsrc | 0x0001E000 | 0x004A0640 | 0x004A0800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.99583 |
.reloc | 0x004BF000 | 0x0000110C | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.41549 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.28771 | 1117 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 2.70591 | 488 | Latin 1 / Western European | Russian - Russia | RT_ICON |
3 | 2.72293 | 296 | Latin 1 / Western European | Russian - Russia | RT_ICON |
4 | 3.39609 | 3752 | Latin 1 / Western European | Russian - Russia | RT_ICON |
5 | 2.99642 | 2216 | Latin 1 / Western European | Russian - Russia | RT_ICON |
6 | 3.04565 | 1736 | Latin 1 / Western European | Russian - Russia | RT_ICON |
7 | 1.27489 | 1384 | Latin 1 / Western European | Russian - Russia | RT_ICON |
101 | 7.99752 | 4837808 | Latin 1 / Western European | Russian - Russia | RT_RCDATA |
102 | 2.95517 | 104 | Latin 1 / Western European | Russian - Russia | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
KERNEL32.dll |
RPCRT4.dll |
Total processes
39
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2184 | "C:\Users\admin\AppData\Local\Temp\tdsskiller.exe" | C:\Users\admin\AppData\Local\Temp\tdsskiller.exe | explorer.exe | ||||||||||||
User: admin Company: AO Kaspersky Lab Integrity Level: HIGH Description: TDSS rootkit removing tool Exit code: 0 Version: 3.1.0.28 Modules
| |||||||||||||||
| 2468 | "C:\Users\admin\AppData\Local\Temp\{E23A222A-893C-4C9B-91EC-2F2351B81A9B}\{248B0CB9-6123-4D20-82AE-62163260F936}.exe" | C:\Users\admin\AppData\Local\Temp\{E23A222A-893C-4C9B-91EC-2F2351B81A9B}\{248B0CB9-6123-4D20-82AE-62163260F936}.exe | tdsskiller.exe | ||||||||||||
User: admin Company: AO Kaspersky Lab Integrity Level: HIGH Description: TDSS rootkit removing tool Exit code: 0 Version: 3.1.0.28 Modules
| |||||||||||||||
| 2996 | "C:\Users\admin\AppData\Local\Temp\tdsskiller.exe" | C:\Users\admin\AppData\Local\Temp\tdsskiller.exe | — | explorer.exe | |||||||||||
User: admin Company: AO Kaspersky Lab Integrity Level: MEDIUM Description: TDSS rootkit removing tool Exit code: 3221226540 Version: 3.1.0.28 Modules
| |||||||||||||||
Total events
204
Read events
184
Write events
16
Delete events
4
Modification events
| (PID) Process: | (2468) {248B0CB9-6123-4D20-82AE-62163260F936}.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2468) {248B0CB9-6123-4D20-82AE-62163260F936}.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\70645339 |
| Operation: | write | Name: | Type |
Value: 1 | |||
| (PID) Process: | (2468) {248B0CB9-6123-4D20-82AE-62163260F936}.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\70645339 |
| Operation: | write | Name: | ErrorControl |
Value: 1 | |||
| (PID) Process: | (2468) {248B0CB9-6123-4D20-82AE-62163260F936}.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\70645339 |
| Operation: | write | Name: | Start |
Value: 3 | |||
| (PID) Process: | (2468) {248B0CB9-6123-4D20-82AE-62163260F936}.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\70645339 |
| Operation: | write | Name: | ImagePath |
Value: system32\drivers\72869179.sys | |||
| (PID) Process: | (2468) {248B0CB9-6123-4D20-82AE-62163260F936}.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\SafeBoot\Minimal\70645339.sys |
| Operation: | write | Name: | |
Value: Driver | |||
| (PID) Process: | (2468) {248B0CB9-6123-4D20-82AE-62163260F936}.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\SafeBoot\Network\70645339.sys |
| Operation: | write | Name: | |
Value: Driver | |||
| (PID) Process: | (2468) {248B0CB9-6123-4D20-82AE-62163260F936}.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\70645339\Enum |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2468) {248B0CB9-6123-4D20-82AE-62163260F936}.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\70645339 |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2468) {248B0CB9-6123-4D20-82AE-62163260F936}.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\SafeBoot\Minimal\70645339.sys |
| Operation: | delete key | Name: | |
Value: | |||
Executable files
12
Suspicious files
1
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2468 | {248B0CB9-6123-4D20-82AE-62163260F936}.exe | C: | — | |
MD5:— | SHA256:— | |||
| 2468 | {248B0CB9-6123-4D20-82AE-62163260F936}.exe | C:\Users\admin\AppData\Local\Temp\{99D5952C-13AE-4C0F-B17C-FF72BB8FD1B2}\{9740C23E-43EA-47B3-8237-00AEE005479A}.tmp | text | |
MD5:52669129A8521AD58AE5BF859D66F7DD | SHA256:09A97C2B223BDD638647227E9733C96590AE8403ED24C2D9B28DEA83C435A2FE | |||
| 2468 | {248B0CB9-6123-4D20-82AE-62163260F936}.exe | C:\Windows\system32\drivers\72869179.sys | executable | |
MD5:63F28E09736179FC57CDD4B2FFB44A0C | SHA256:1964D072661074069960F05DF11A622D750A3AA997FE2F4620BE0067DF11BEB2 | |||
| 2468 | {248B0CB9-6123-4D20-82AE-62163260F936}.exe | C:\Users\admin\AppData\Local\Temp\{99D5952C-13AE-4C0F-B17C-FF72BB8FD1B2}\{A340B2F9-4855-4EBC-A383-FDEDA163A8CB}.tmp | executable | |
MD5:517ECD823EB9A03368294C6C33A695D0 | SHA256:7BA4EF2C5E9D15A4EE8ACC169CA233010DF8D1BC7088665E06C9E71BBA0CD40C | |||
| 2468 | {248B0CB9-6123-4D20-82AE-62163260F936}.exe | C:\Users\admin\AppData\Local\Temp\{99D5952C-13AE-4C0F-B17C-FF72BB8FD1B2}\{DCC89C04-DBDA-4C09-800F-DF87BA202A27}.tmp | executable | |
MD5:DC6DB08D85337C9675F94B01043279AE | SHA256:B09E491113F9E95F4EE00BB51BB21D4967BAC333C0DCD030A10AEA9B9E52032B | |||
| 2468 | {248B0CB9-6123-4D20-82AE-62163260F936}.exe | C:\Users\admin\AppData\Local\Temp\{99D5952C-13AE-4C0F-B17C-FF72BB8FD1B2}\{84426CBA-D900-4B03-90F7-EC8F6910C81E}.tmp | executable | |
MD5:3428F170E1953B4C4EA10A5F58B55908 | SHA256:B554E04021472C3C2BBDED2B4BBB4F6648932356F8DA409A2A7F6AC02E54B306 | |||
| 2468 | {248B0CB9-6123-4D20-82AE-62163260F936}.exe | C:\Users\admin\AppData\Local\Temp\{99D5952C-13AE-4C0F-B17C-FF72BB8FD1B2}\{74F6CC76-8C51-4C12-889A-1ED87AC3D87E}.tmp | executable | |
MD5:96D681B7DE0BA6BFA1DC55915003CD05 | SHA256:26CDA6A9A67F20A494F0EF3577D14F5DDA1F0D4428891DBD271A757833285939 | |||
| 2468 | {248B0CB9-6123-4D20-82AE-62163260F936}.exe | C:\Users\admin\AppData\Local\Temp\{99D5952C-13AE-4C0F-B17C-FF72BB8FD1B2}\{319F75CB-6D39-4481-B7C9-F31F05DE2DB4}.tmp | executable | |
MD5:C74D46C1F542F5FEB9B7E1A8EC04986D | SHA256:FA83733A81BA8D96EDFD15C1914D5A6056D73C61540C8747E9AE1343DA47A63D | |||
| 2468 | {248B0CB9-6123-4D20-82AE-62163260F936}.exe | C:\Users\admin\AppData\Local\Temp\{99D5952C-13AE-4C0F-B17C-FF72BB8FD1B2}\{9AFEE31A-CA67-4B5A-A3FF-4358A07021A7}.tmp | text | |
MD5:0A52D6A1DD74FEB5F50D5D35BC1A51C6 | SHA256:96EDFD40D55FEC6F56E6C6089750211C42427E488ADADB3765FEF7357346BDCF | |||
| 2468 | {248B0CB9-6123-4D20-82AE-62163260F936}.exe | C:\Users\admin\AppData\Local\Temp\{99D5952C-13AE-4C0F-B17C-FF72BB8FD1B2}\{85B55F45-7634-4607-B4C8-7D8F979BEFFC}.tmp | executable | |
MD5:E027A6E99EF709AFD195FD6329224C47 | SHA256:B31B85BF369DC36363B0E527AE3B8E95B33699D17D09C6313C43E7373A3E6874 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
7
DNS requests
11
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2468 | {248B0CB9-6123-4D20-82AE-62163260F936}.exe | 185.85.15.30:80 | support.kaspersky.com | Kaspersky Lab AO | RU | suspicious |
2468 | {248B0CB9-6123-4D20-82AE-62163260F936}.exe | 185.85.15.30:443 | support.kaspersky.com | Kaspersky Lab AO | RU | suspicious |
2468 | {248B0CB9-6123-4D20-82AE-62163260F936}.exe | 62.67.238.140:443 | ksn-file-geo.kaspersky-labs.com | Level 3 Communications, Inc. | GB | unknown |
2468 | {248B0CB9-6123-4D20-82AE-62163260F936}.exe | 195.122.177.135:443 | ksn-file-geo.kaspersky-labs.com | Level 3 Communications, Inc. | GB | unknown |
2468 | {248B0CB9-6123-4D20-82AE-62163260F936}.exe | 62.67.238.144:443 | ksn-file-geo.kaspersky-labs.com | Level 3 Communications, Inc. | GB | unknown |
2468 | {248B0CB9-6123-4D20-82AE-62163260F936}.exe | 62.128.100.45:443 | ksn-file-geo.kaspersky-labs.com | Linx Telecommunications B.V. | RU | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
support.kaspersky.com |
| whitelisted |
ksn-file-geo.kaspersky-labs.com |
| suspicious |
ksn-stat-geo.kaspersky-labs.com |
| unknown |
Threats
1 ETPRO signatures available at the full report