| File name: | HorionInjector.exe |
| Full analysis: | https://app.any.run/tasks/c537813b-cd4f-4e60-94a4-19013db6c79c |
| Verdict: | Malicious activity |
| Analysis date: | November 16, 2024, 07:25:06 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64 Mono/.Net assembly, for MS Windows, 2 sections |
| MD5: | 6B5B6E625DE774E5C285712B7C4A0DA7 |
| SHA1: | 317099AEF530AFBE3A0C5D6A2743D51E04805267 |
| SHA256: | 2D79AF8E1FF3465703E1DC73D3EF2182FD269EA2609C8AFABDF1B80693405C1D |
| SSDEEP: | 3072:ckgHqUGSCoEslON/q178+oO3BAE4T/DvueXd:cNHqUGSCPBh+7VST/Ket |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads security settings of Internet Explorer
- HorionInjector.exe (PID: 6548)
INFO
Checks supported languages
- HorionInjector.exe (PID: 6548)
Reads the software policy settings
- HorionInjector.exe (PID: 6548)
Checks proxy server information
- HorionInjector.exe (PID: 6548)
Reads Environment values
- HorionInjector.exe (PID: 6548)
Disables trace logs
- HorionInjector.exe (PID: 6548)
Reads the computer name
- HorionInjector.exe (PID: 6548)
Reads the machine GUID from the registry
- HorionInjector.exe (PID: 6548)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2050:11:10 11:43:35+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 48 |
| CodeSize: | 80896 |
| InitializedDataSize: | 69632 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x0000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.1.2.0 |
| ProductVersionNumber: | 1.1.2.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
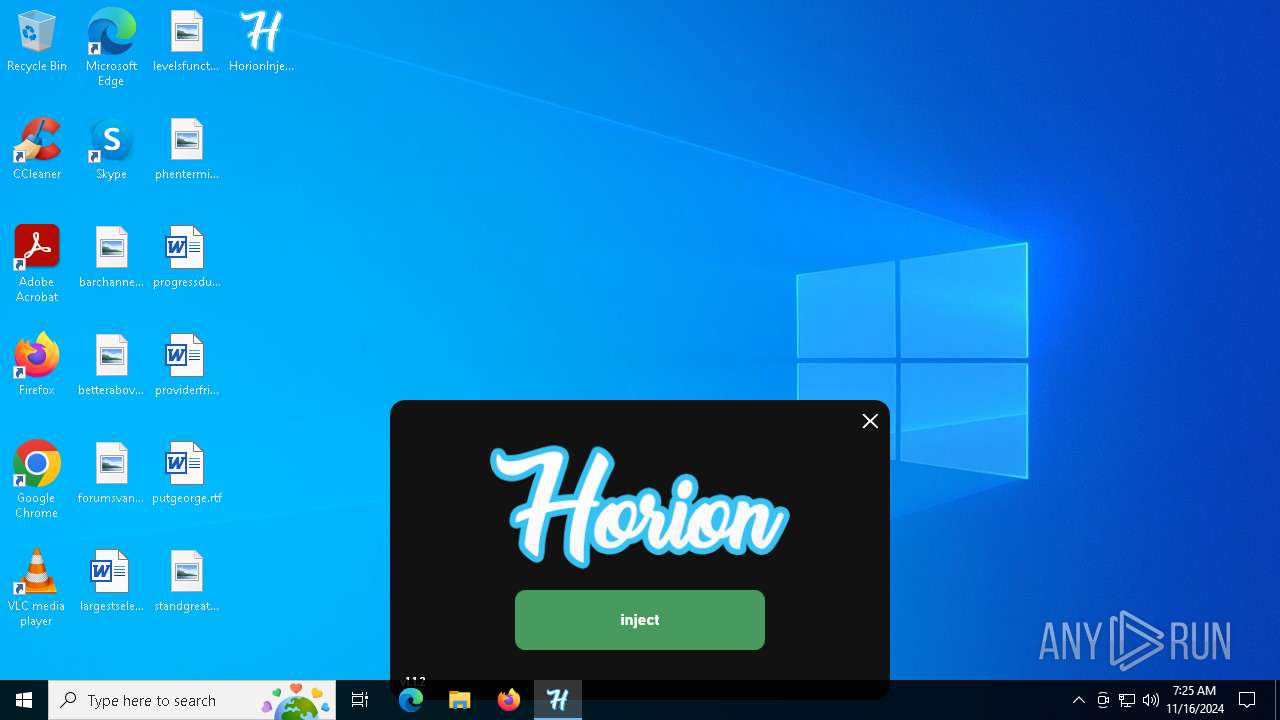
| Comments: | Injector for Horion, a Minecraft: Bedrock Edition utility mod |
| CompanyName: | Horion Developers |
| FileDescription: | HorionInjector |
| FileVersion: | 1.1.2.0 |
| InternalName: | HorionInjector.exe |
| LegalCopyright: | ©2021 |
| OriginalFileName: | HorionInjector.exe |
| ProductName: | Horion Injector |
| ProductVersion: | 1.1.2 |
| AssemblyVersion: | 1.1.2.0 |
Total processes
122
Monitored processes
1
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 6548 | "C:\Users\admin\Desktop\HorionInjector.exe" | C:\Users\admin\Desktop\HorionInjector.exe | explorer.exe | ||||||||||||
User: admin Company: Horion Developers Integrity Level: MEDIUM Description: HorionInjector Version: 1.1.2.0 Modules
| |||||||||||||||
Total events
4 344
Read events
4 330
Write events
14
Delete events
0
Modification events
| (PID) Process: | (6548) HorionInjector.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\HorionInjector_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6548) HorionInjector.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\HorionInjector_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (6548) HorionInjector.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\HorionInjector_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (6548) HorionInjector.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\HorionInjector_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (6548) HorionInjector.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\HorionInjector_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (6548) HorionInjector.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\HorionInjector_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (6548) HorionInjector.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\HorionInjector_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (6548) HorionInjector.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\HorionInjector_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6548) HorionInjector.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\HorionInjector_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (6548) HorionInjector.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\HorionInjector_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
28
DNS requests
8
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
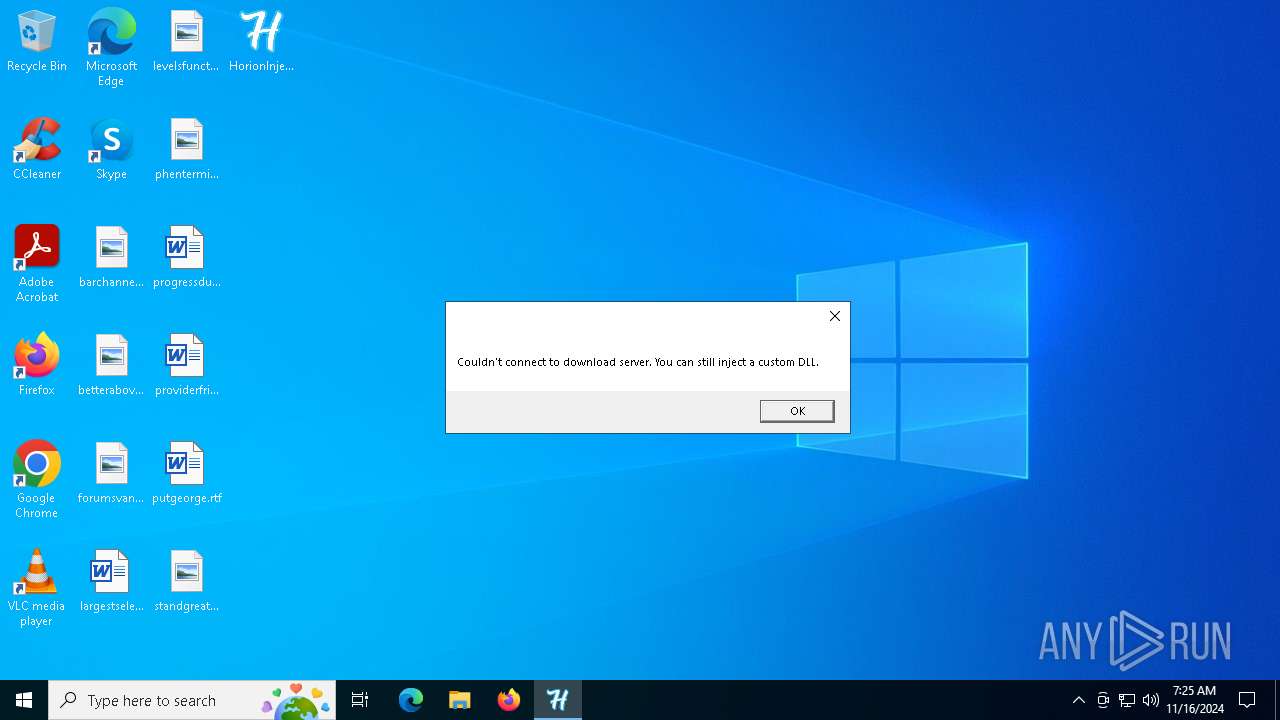
— | — | GET | — | 188.114.97.3:443 | https://horion.download/ | unknown | — | — | unknown |
5488 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6944 | svchost.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5700 | RUXIMICS.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6944 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5700 | RUXIMICS.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6944 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5700 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5488 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 104.126.37.162:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6548 | HorionInjector.exe | 188.114.97.3:443 | horion.download | CLOUDFLARENET | NL | unknown |
5488 | MoUsoCoreWorker.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
6944 | svchost.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5700 | RUXIMICS.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
horion.download |
| unknown |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
Threats
1 ETPRO signatures available at the full report