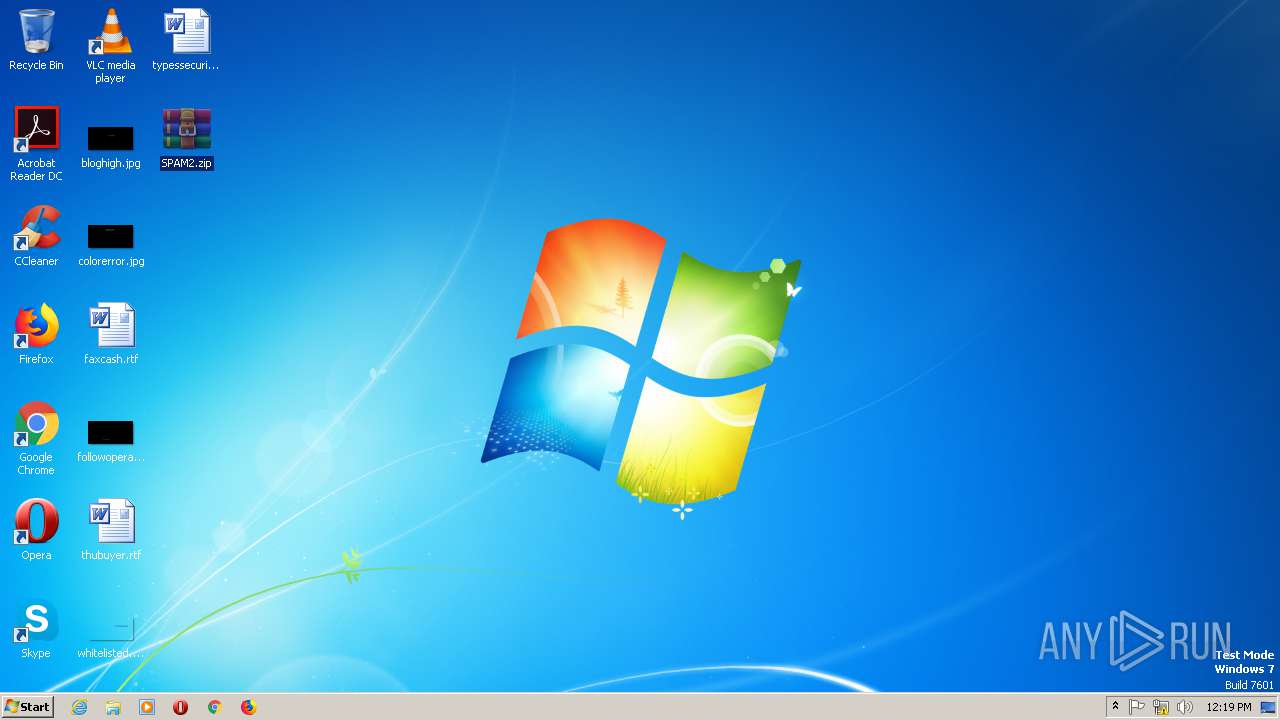
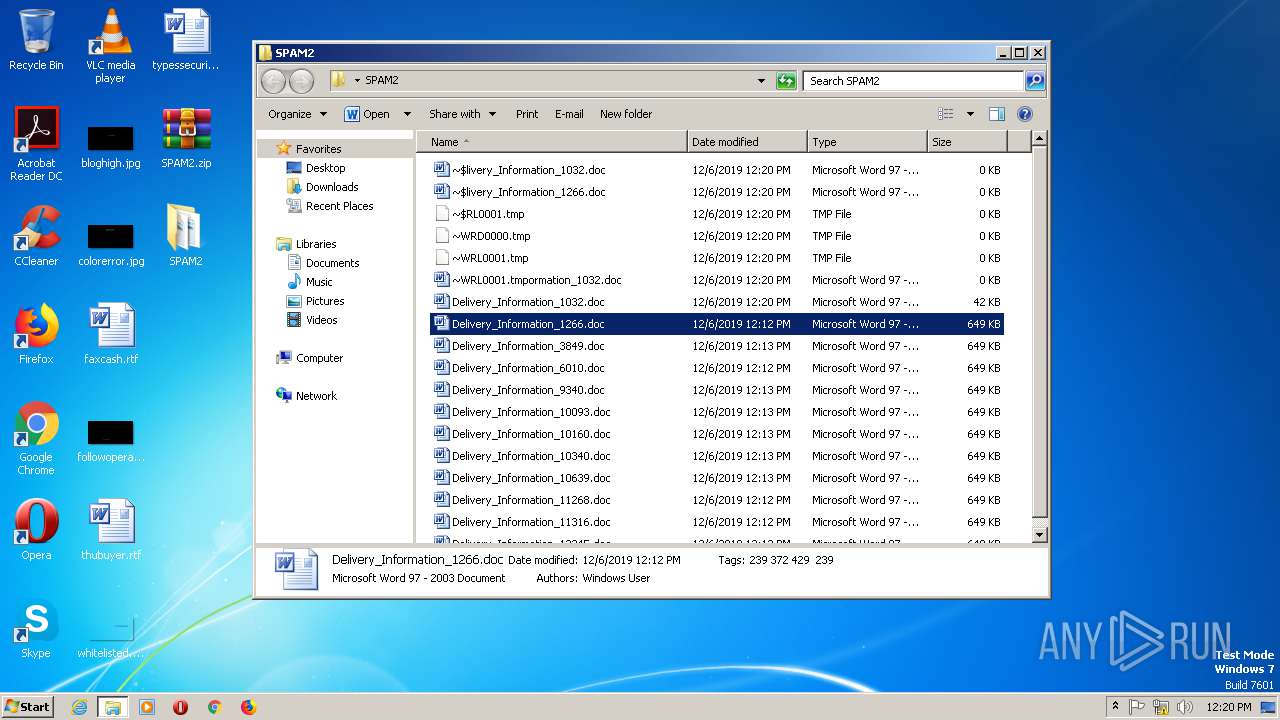
| File name: | SPAM2.zip |
| Full analysis: | https://app.any.run/tasks/14831d4e-99ee-4764-b395-3a695161c0ee |
| Verdict: | Malicious activity |
| Analysis date: | December 06, 2019, 12:19:09 |
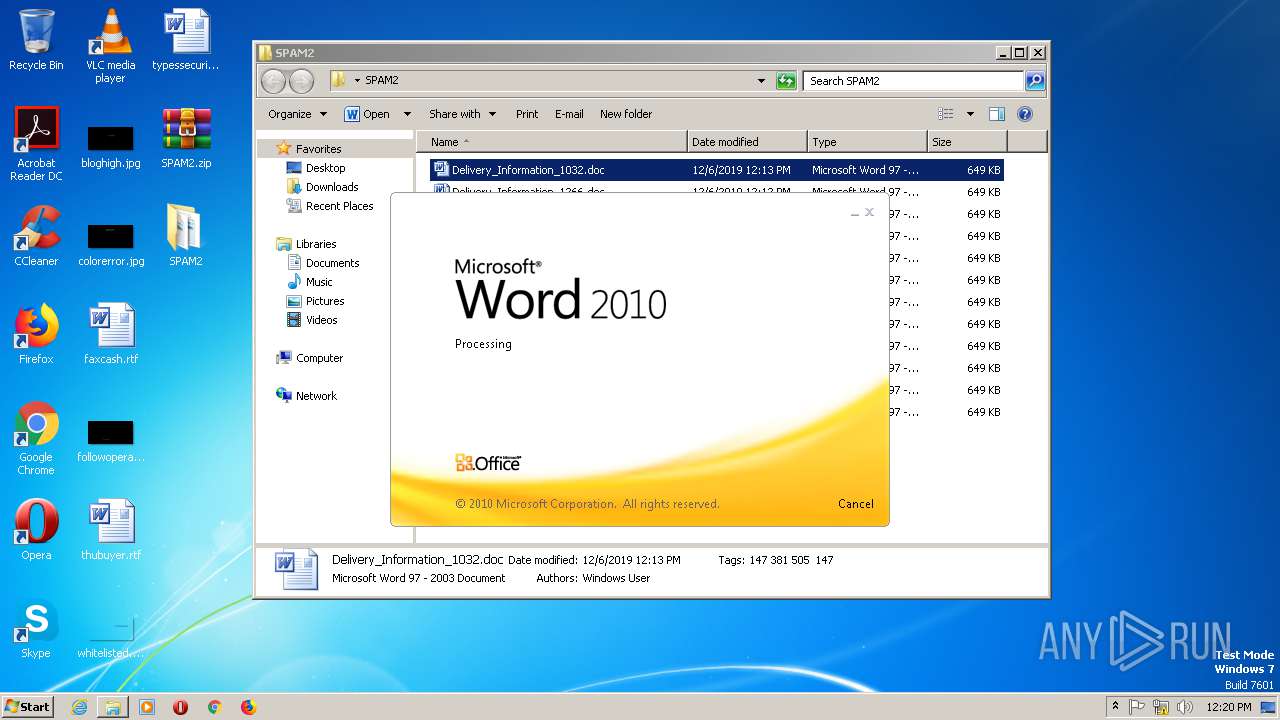
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 69187989C5D4461D4D6884AC225C1FE5 |
| SHA1: | AF6F5065B14E1C705F04CF8FFE7B9A214671636B |
| SHA256: | 2D6E1783704BDE8119698D2BE7F6221A94047F34BDFCE8BCB3CD6EC2A8FDEA6E |
| SSDEEP: | 98304:VTPS3OTPS3GTPS3gnTPS33TPS3NTPS3cTPS3sTPS3CTPS3TTPS3iTPS3tSTPS36:4lt5uAP/Za5n6 |
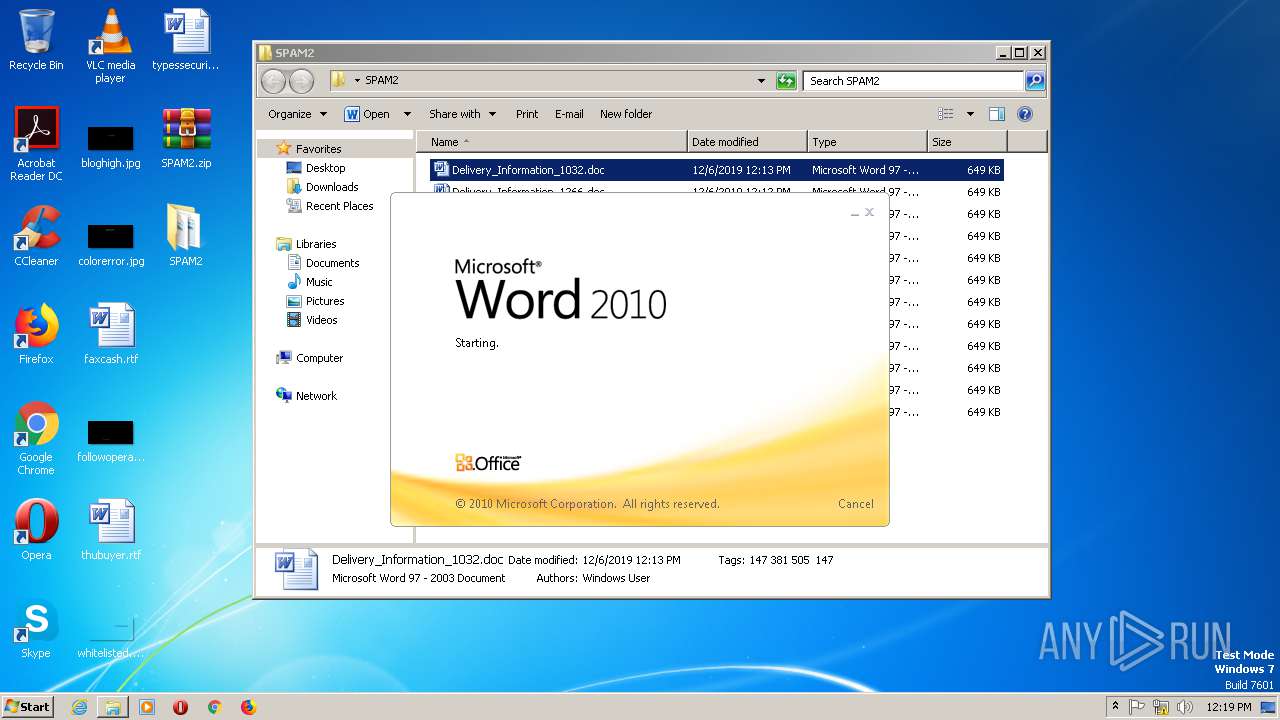
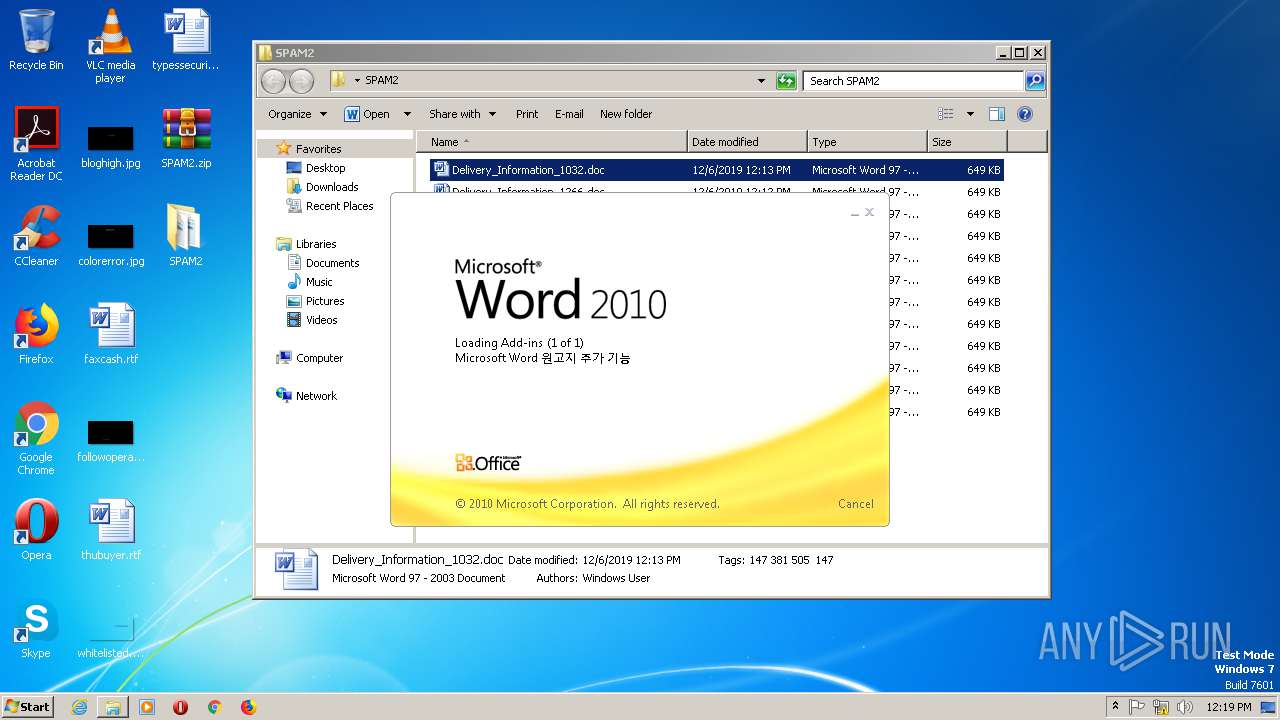
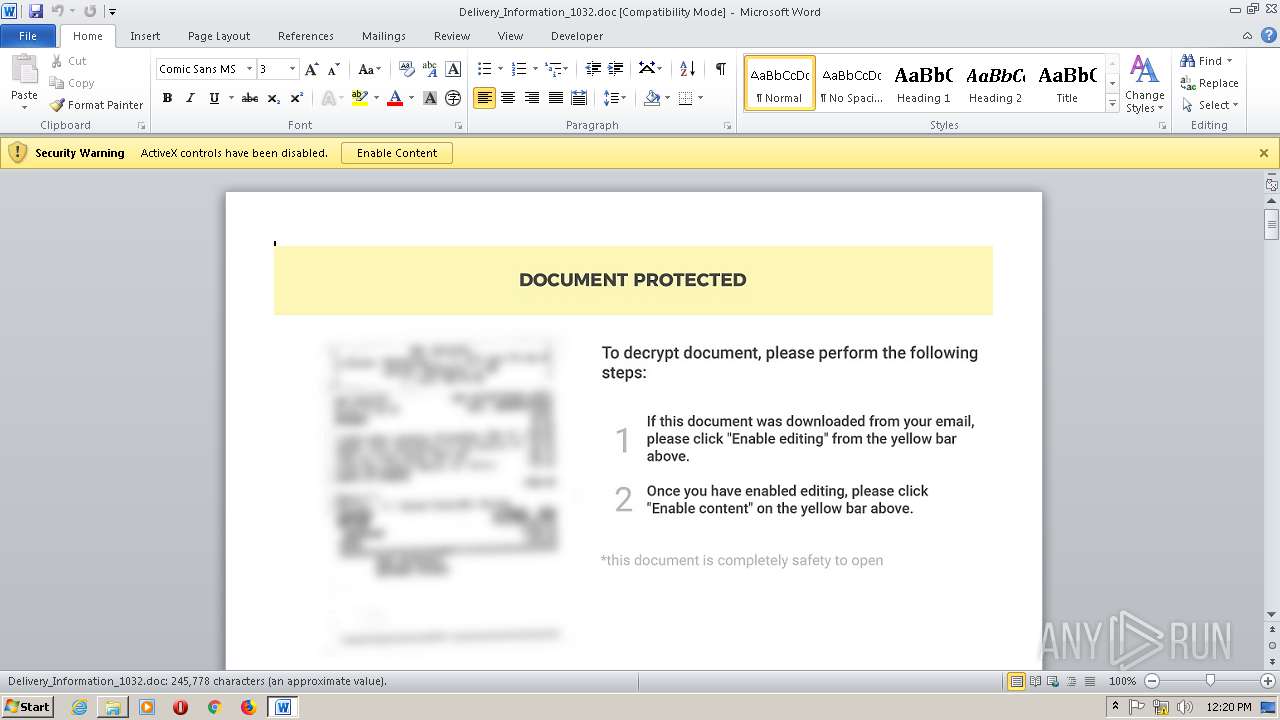
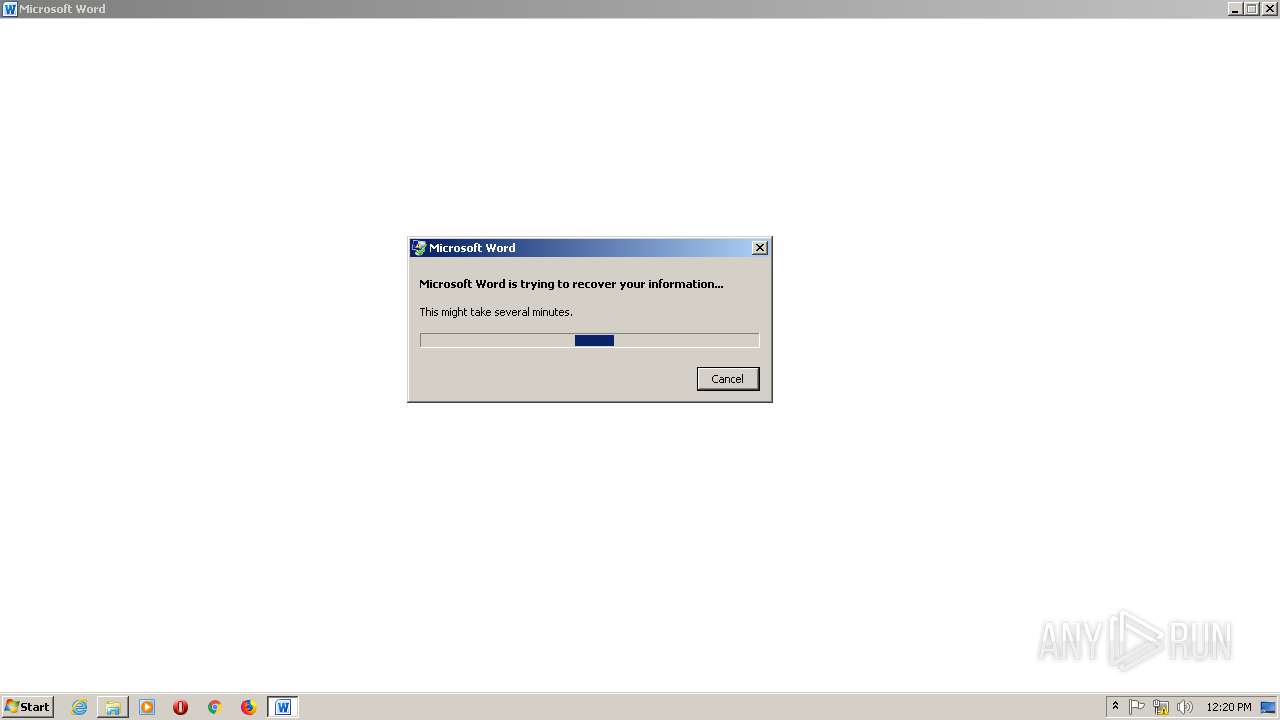
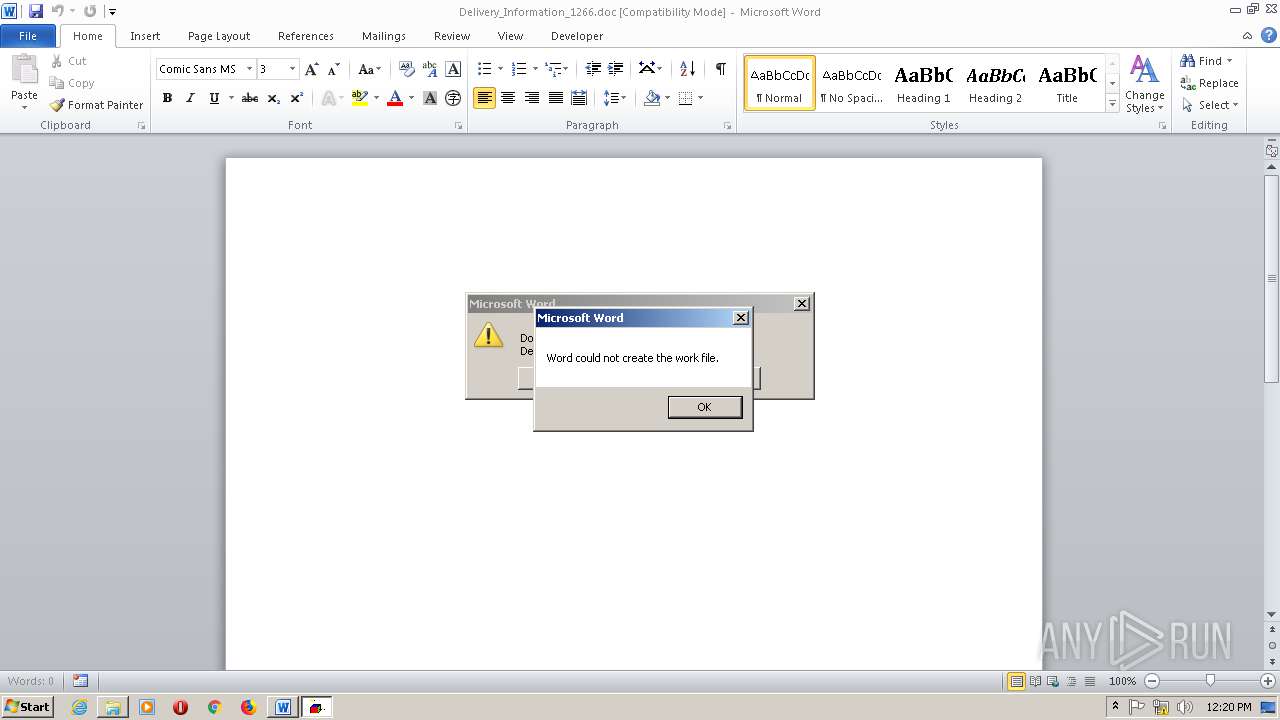
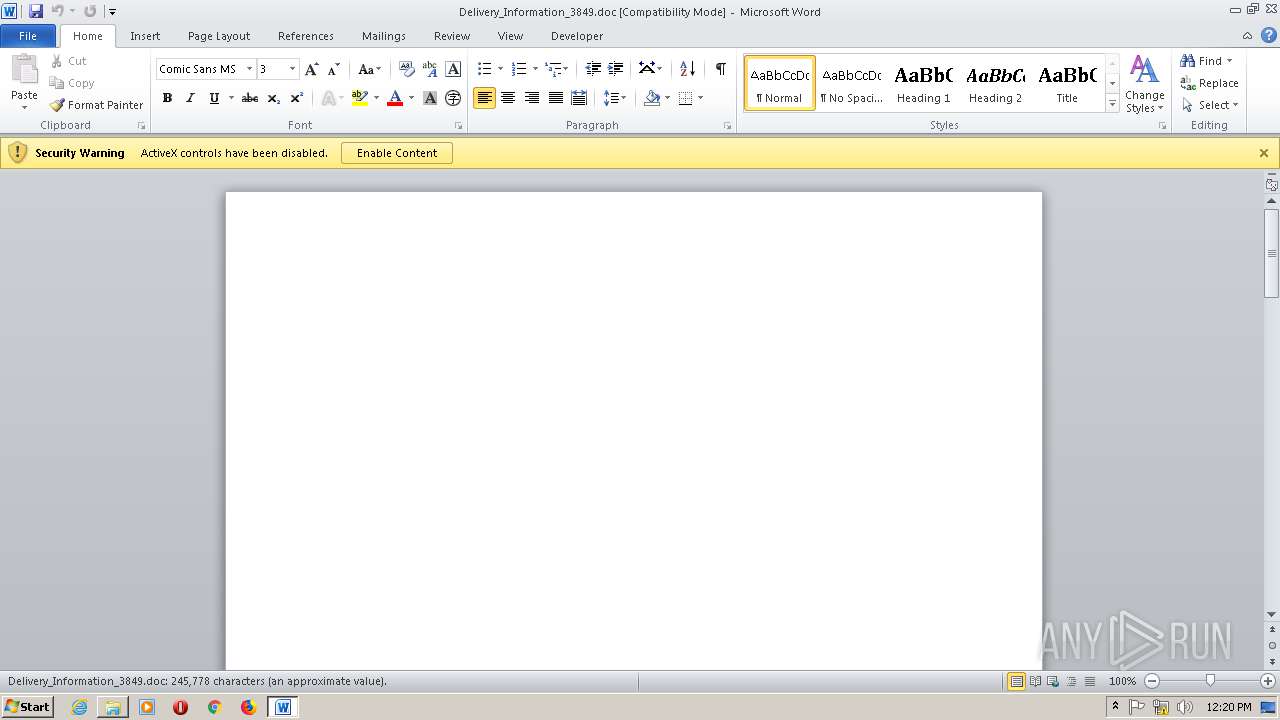
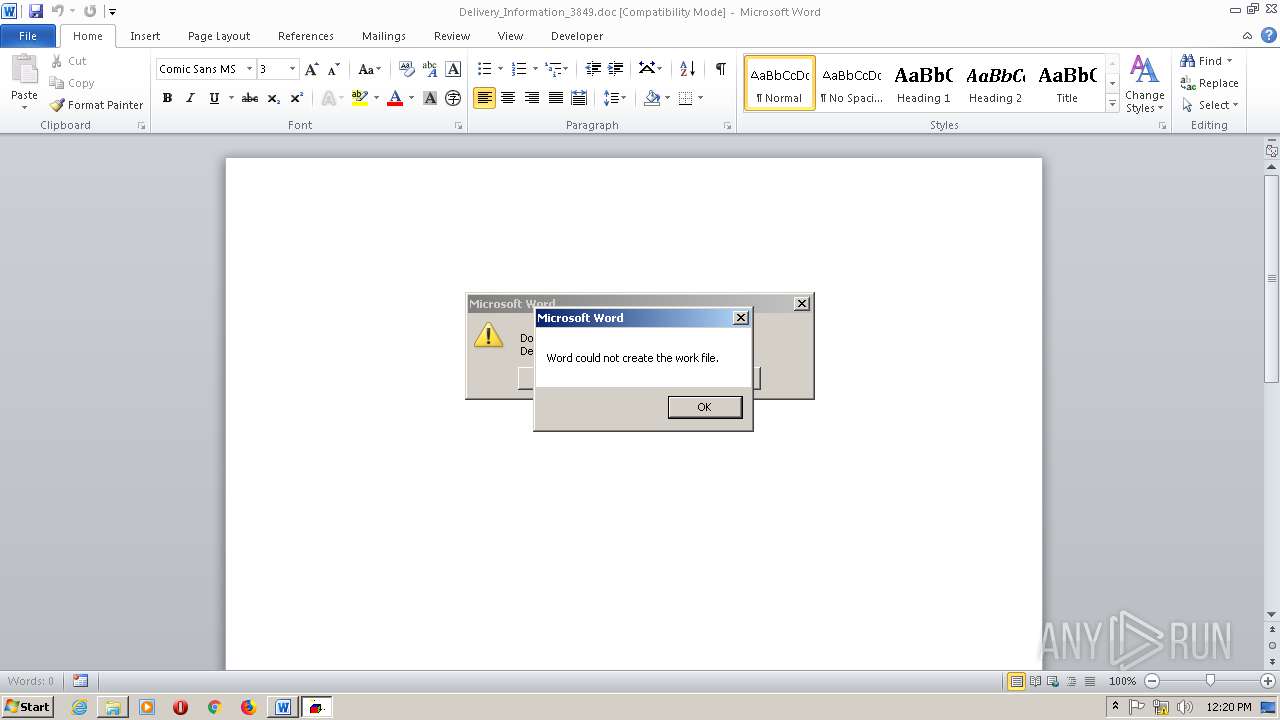
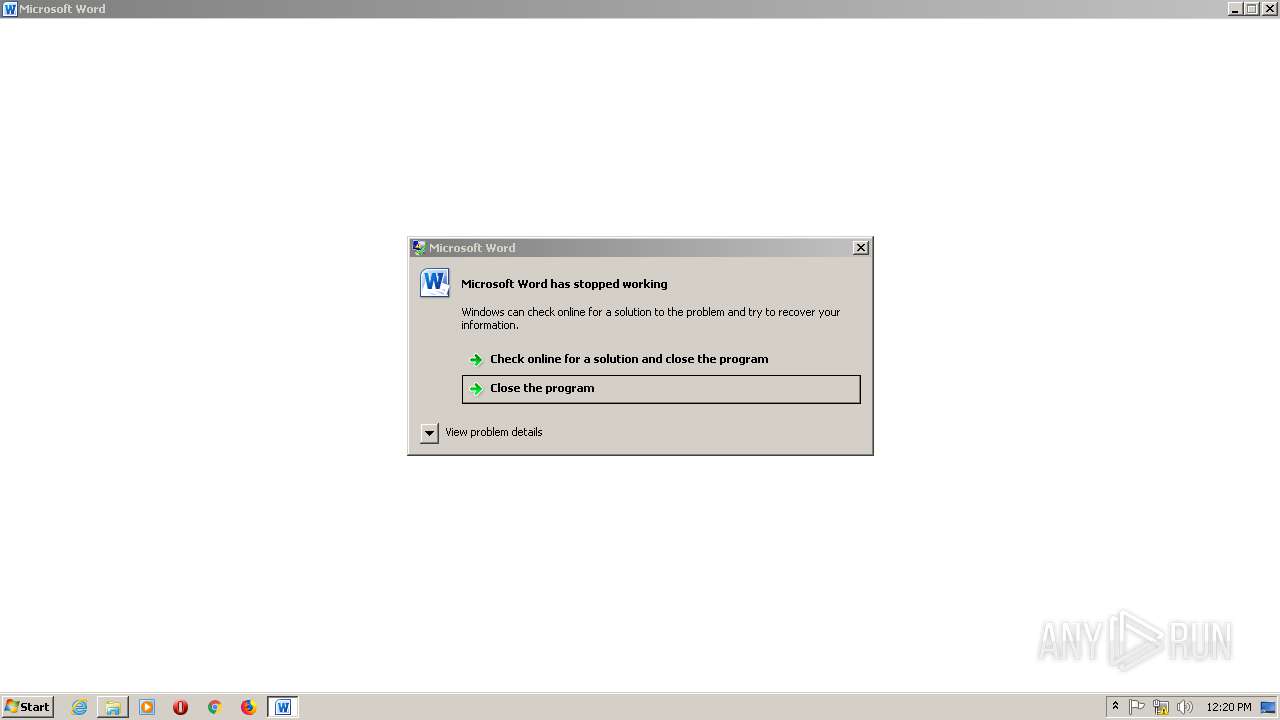
MALICIOUS
Executes scripts
- WINWORD.EXE (PID: 2804)
- WINWORD.EXE (PID: 2332)
- WINWORD.EXE (PID: 1508)
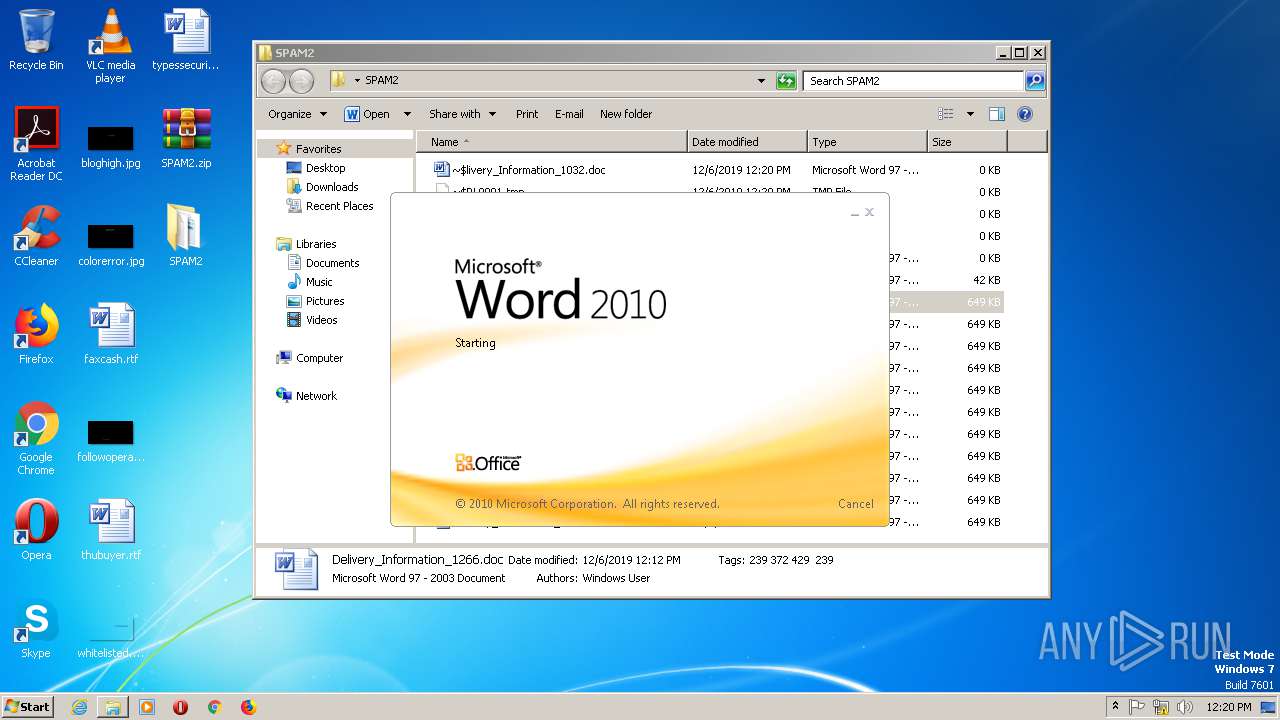
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2804)
- WINWORD.EXE (PID: 2332)
- WINWORD.EXE (PID: 1508)
SUSPICIOUS
Reads the machine GUID from the registry
- WScript.exe (PID: 2416)
- WScript.exe (PID: 1176)
- WScript.exe (PID: 2100)
- WScript.exe (PID: 312)
INFO
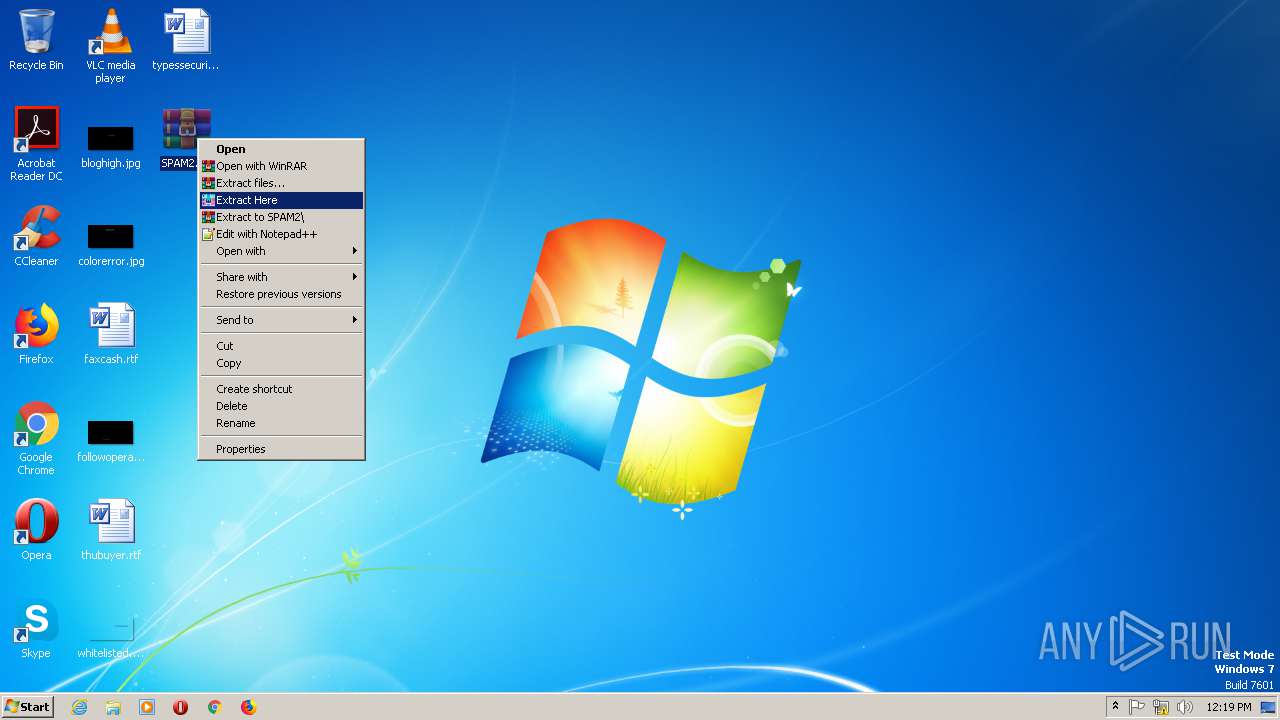
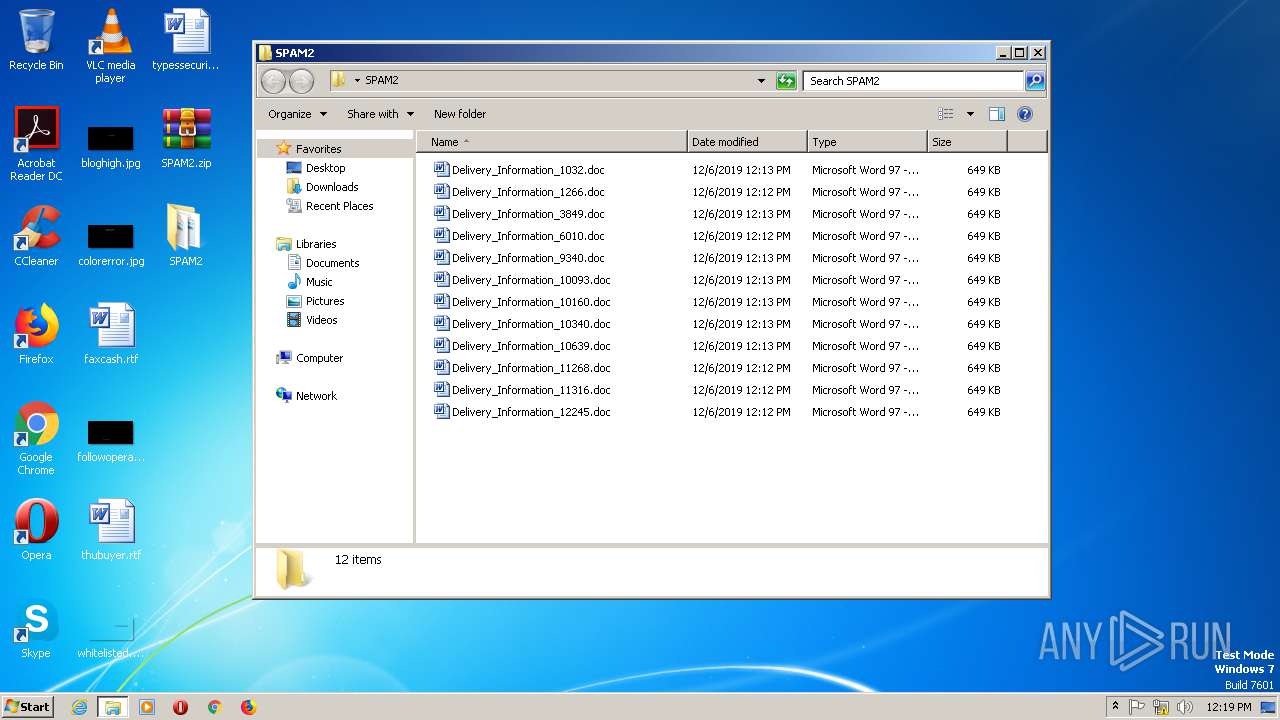
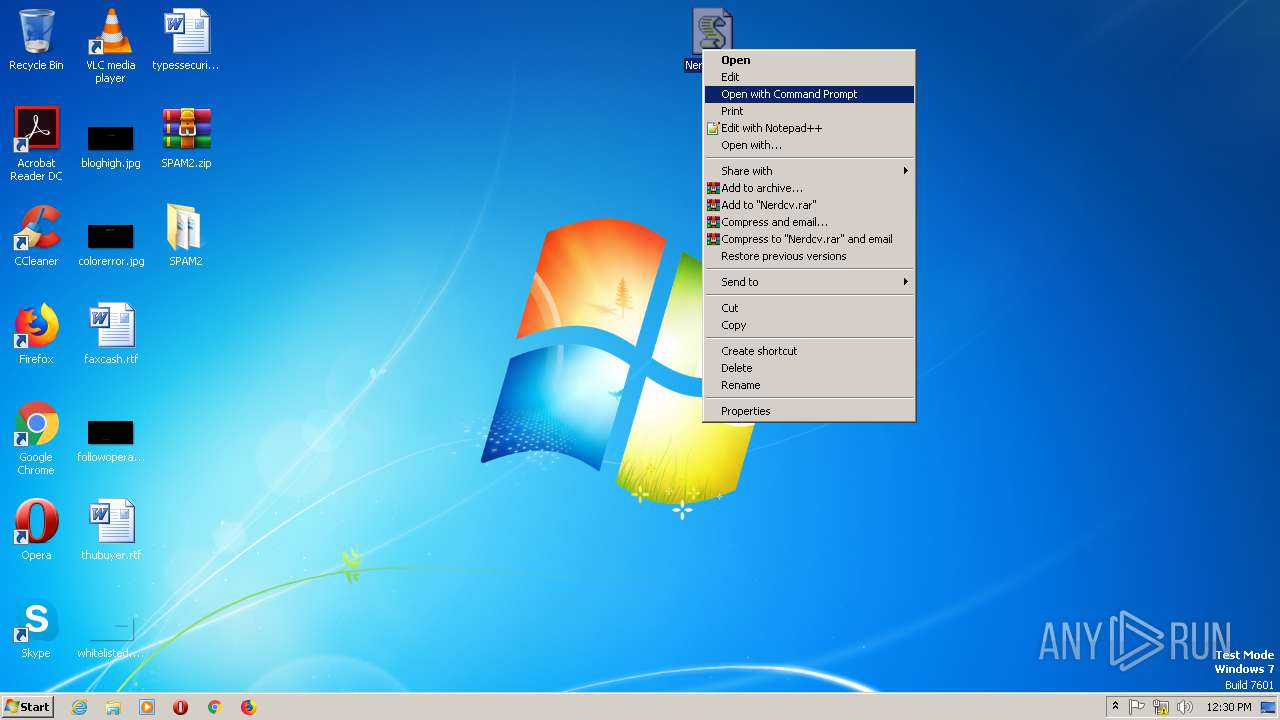
Manual execution by user
- WinRAR.exe (PID: 2712)
- WINWORD.EXE (PID: 2332)
- WINWORD.EXE (PID: 1508)
- WScript.exe (PID: 2100)
- Notepad.exe (PID: 400)
- WINWORD.EXE (PID: 2804)
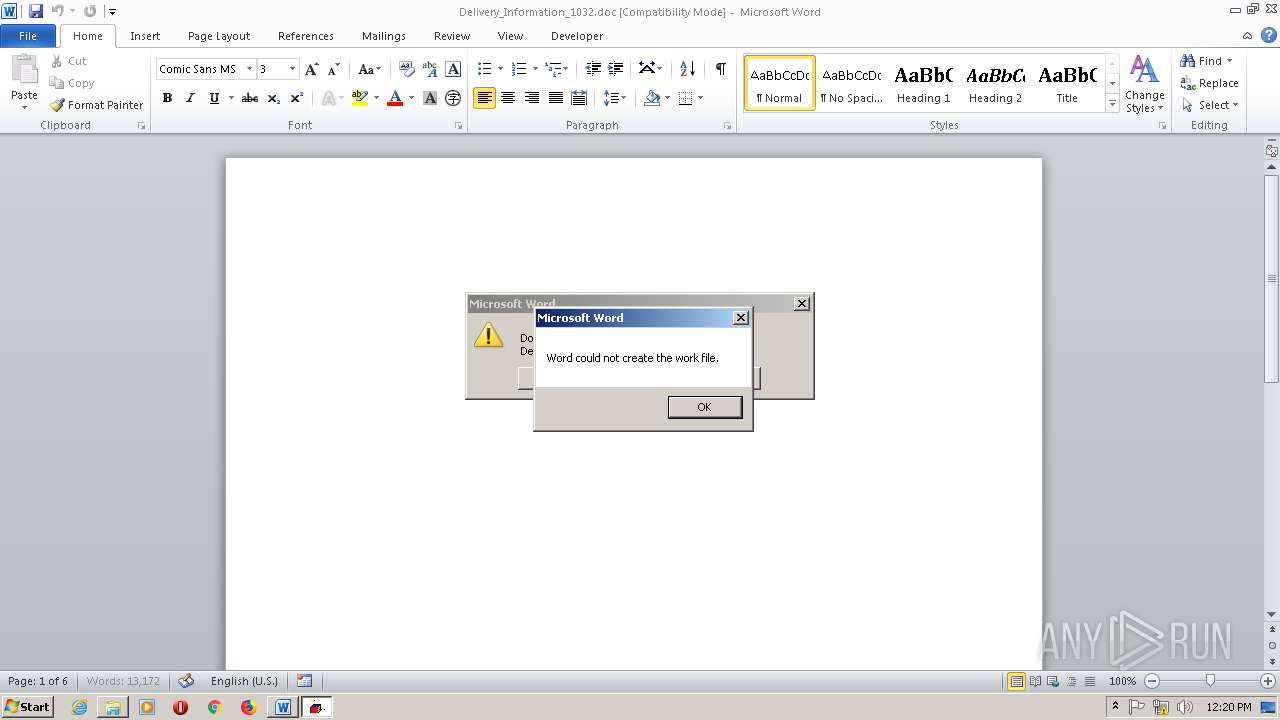
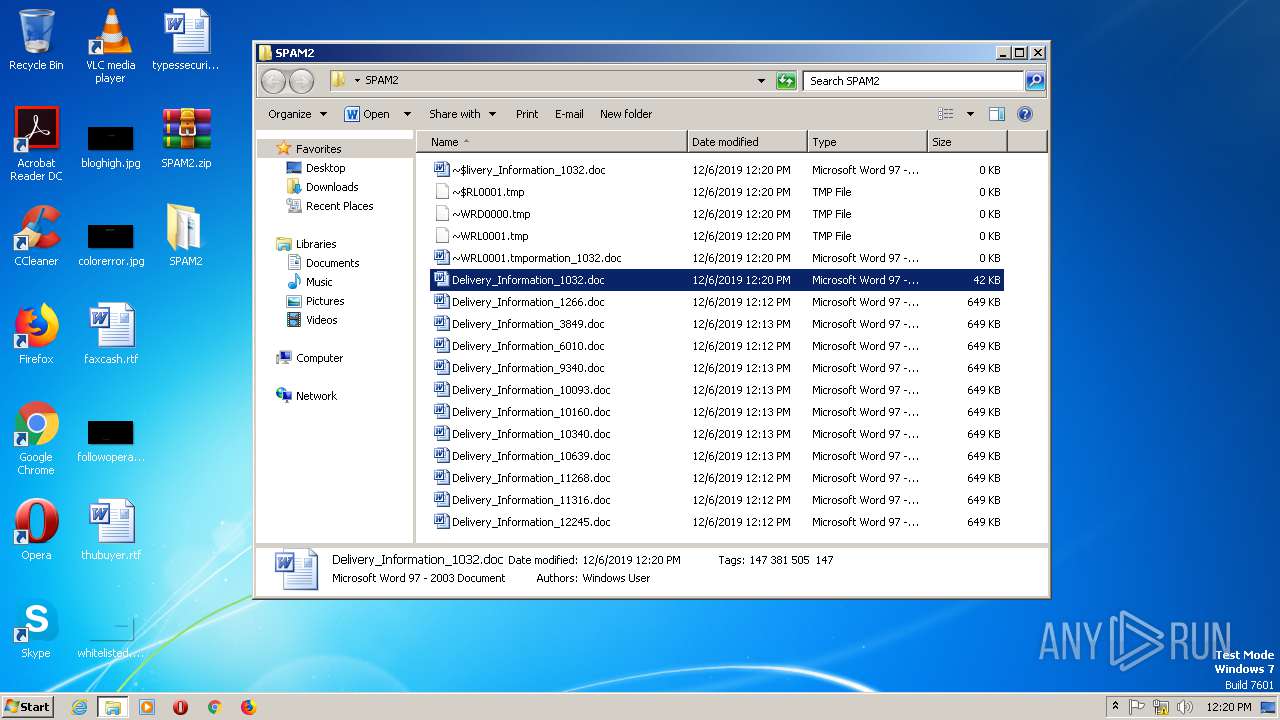
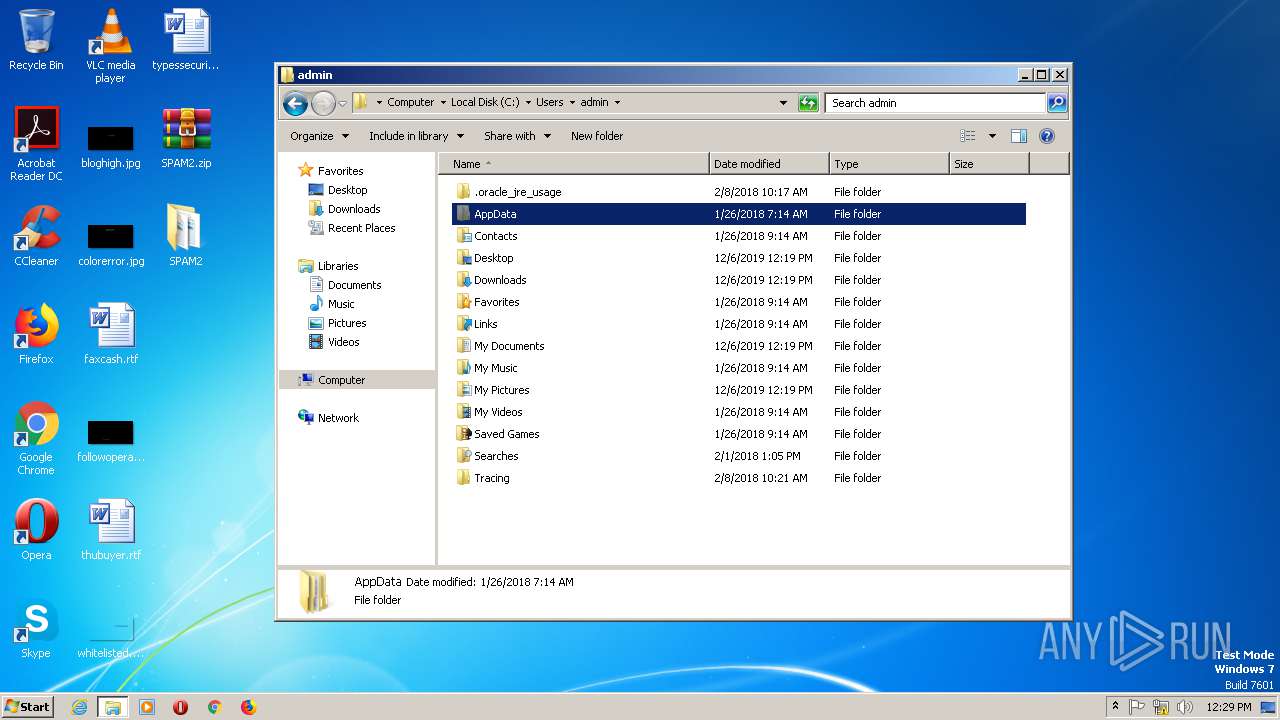
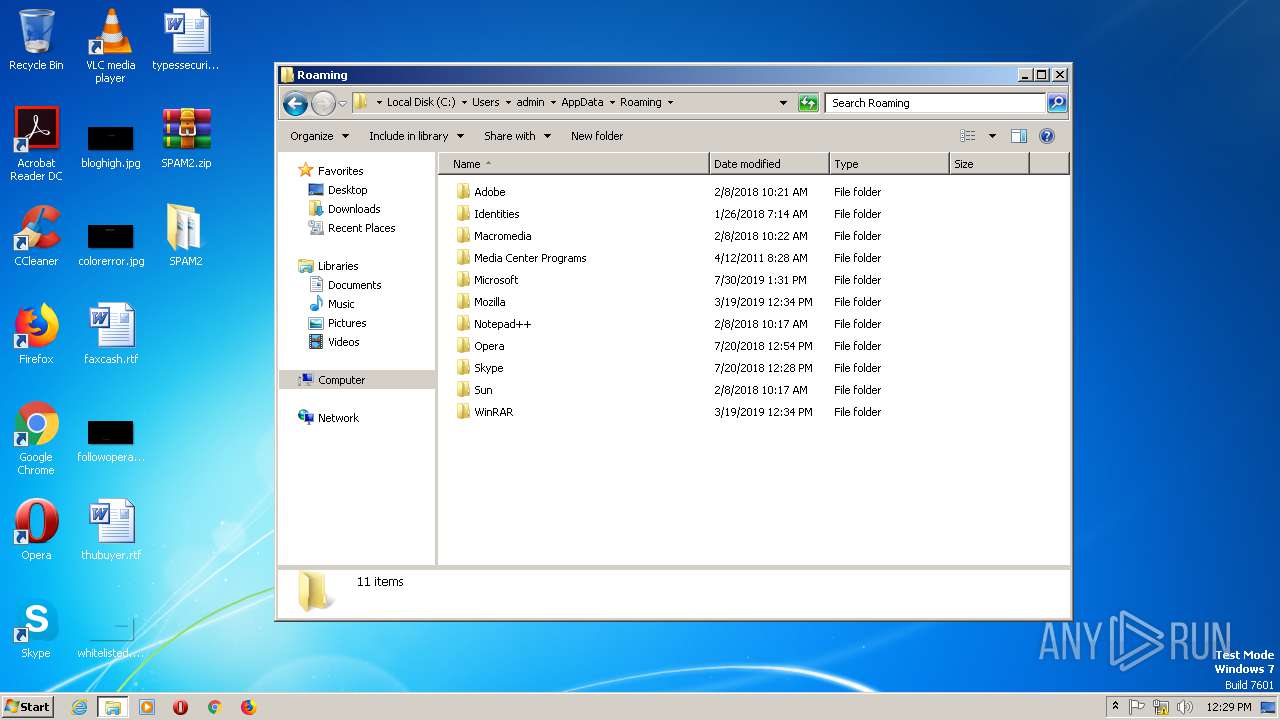
Creates files in the user directory
- WINWORD.EXE (PID: 2804)
- WINWORD.EXE (PID: 1508)
- WINWORD.EXE (PID: 2332)
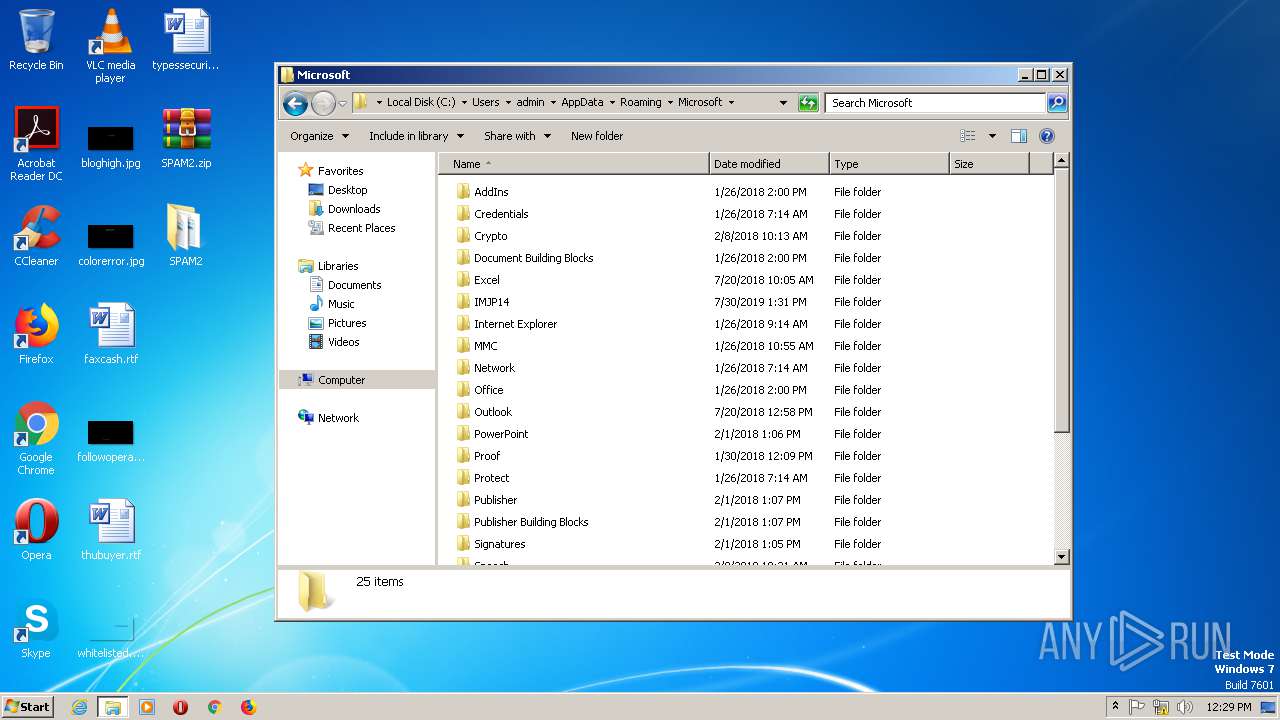
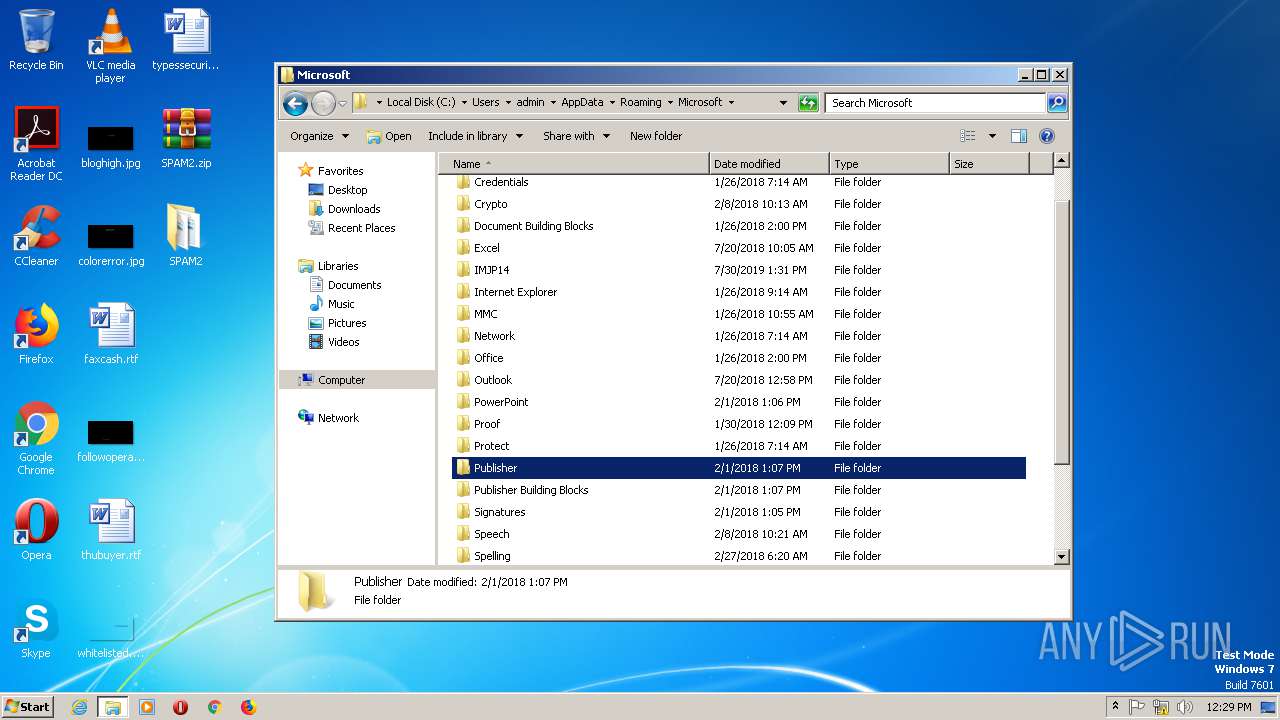
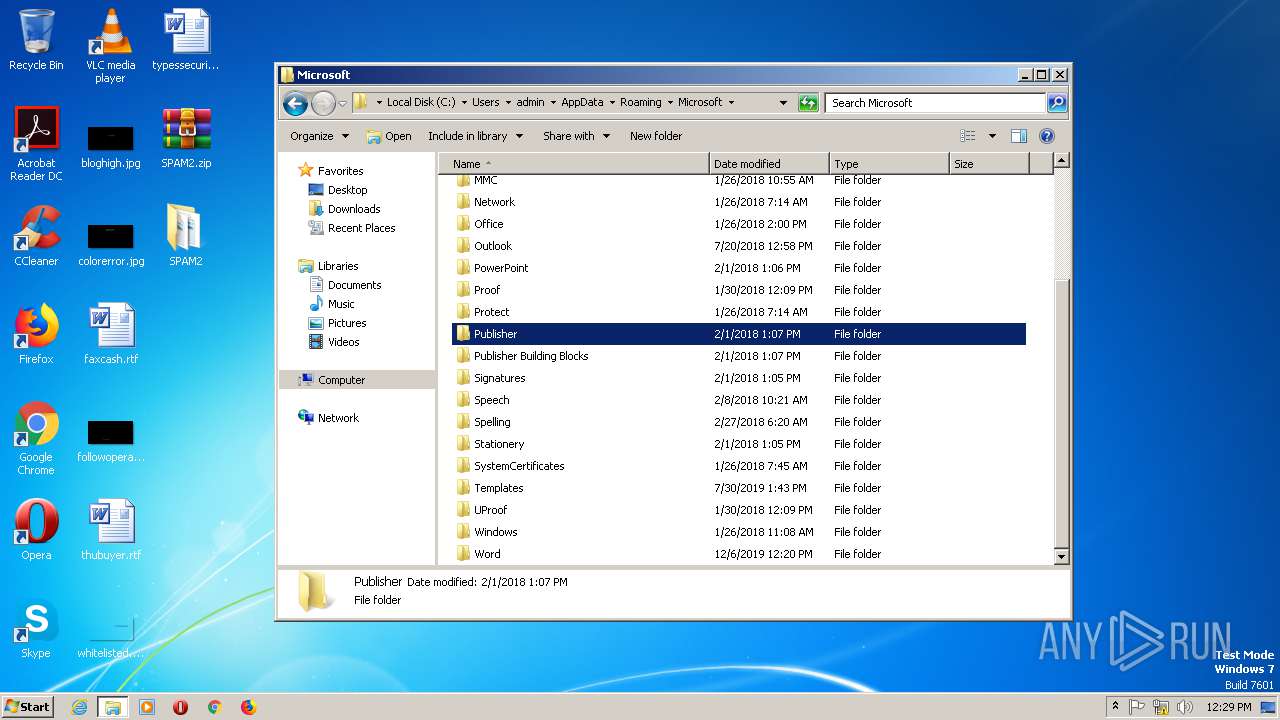
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2804)
- WINWORD.EXE (PID: 2332)
- WINWORD.EXE (PID: 1508)
Reads the machine GUID from the registry
- WINWORD.EXE (PID: 2804)
- WINWORD.EXE (PID: 2332)
- WINWORD.EXE (PID: 1508)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
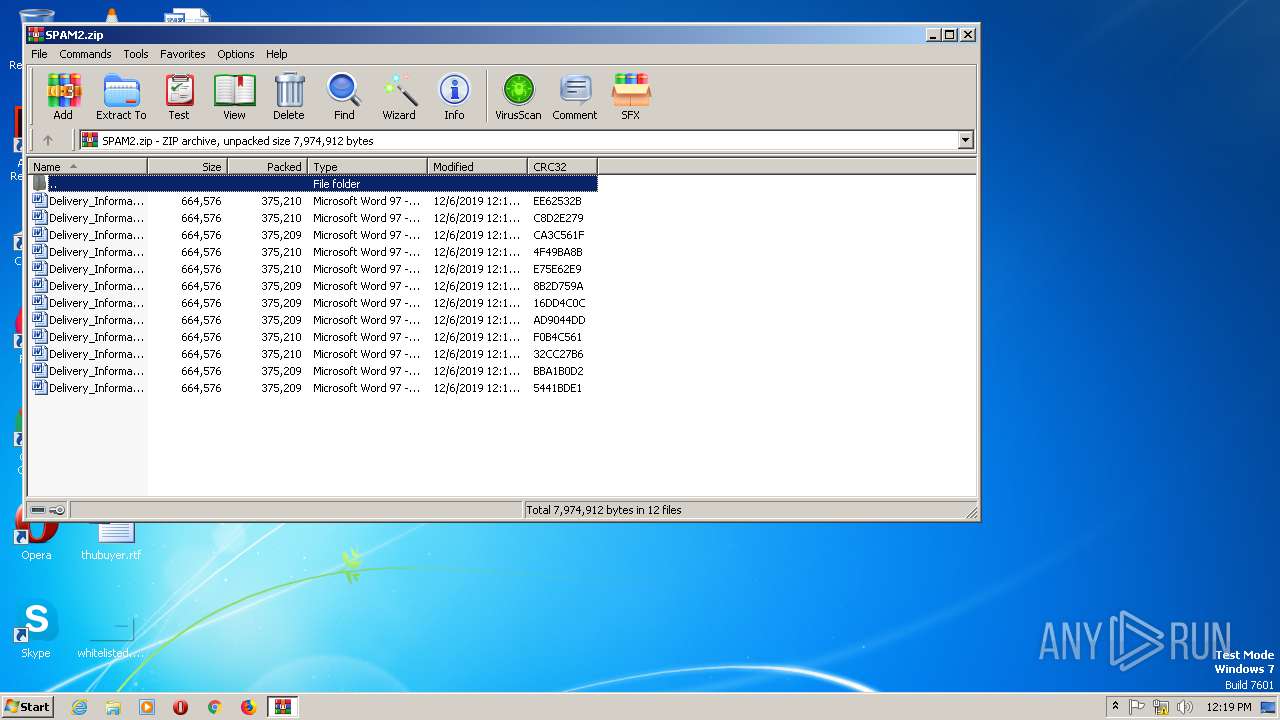
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:12:06 13:13:10 |
| ZipCRC: | 0x8b2d759a |
| ZipCompressedSize: | 375209 |
| ZipUncompressedSize: | 664576 |
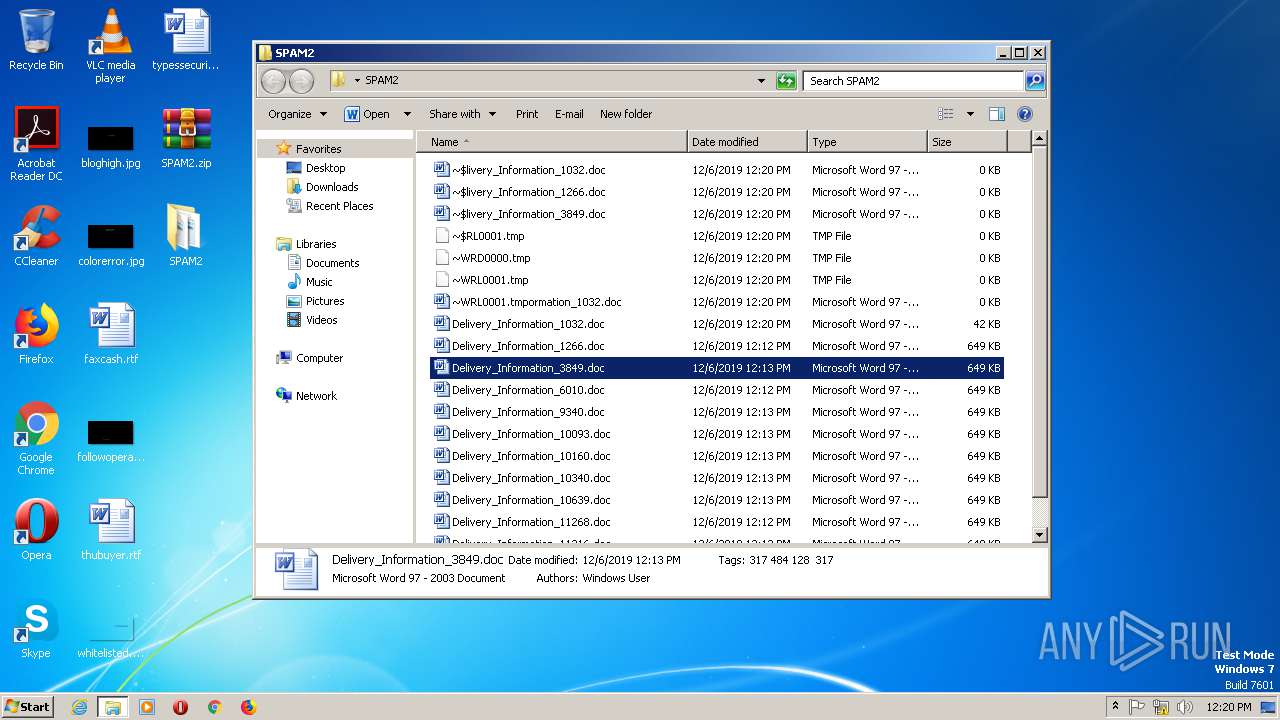
| ZipFileName: | Delivery_Information_10093.doc |
Total processes
166
Monitored processes
16
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
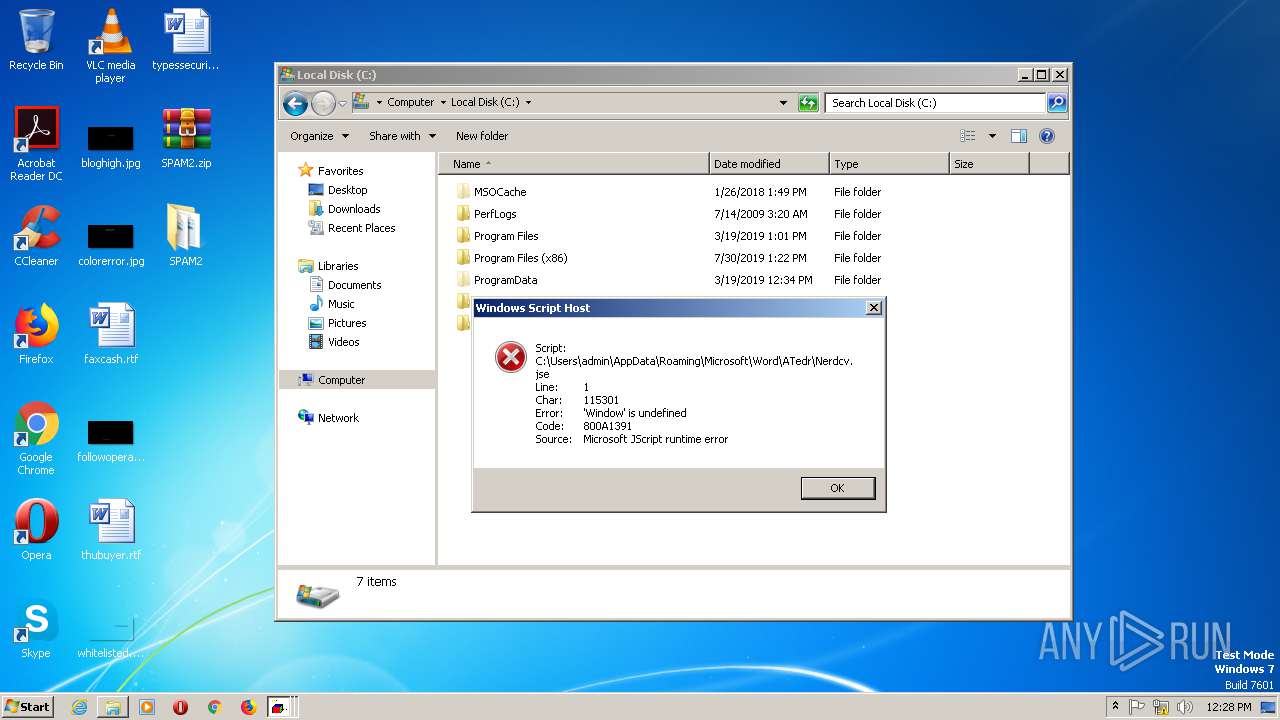
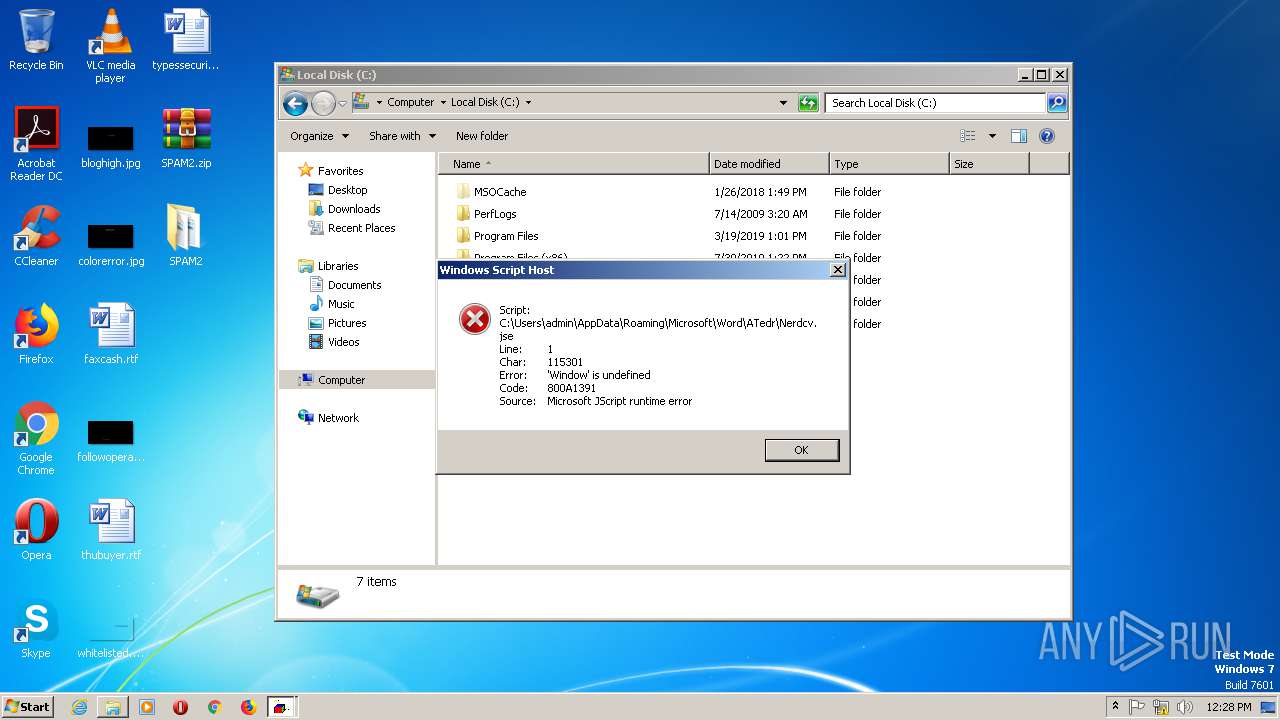
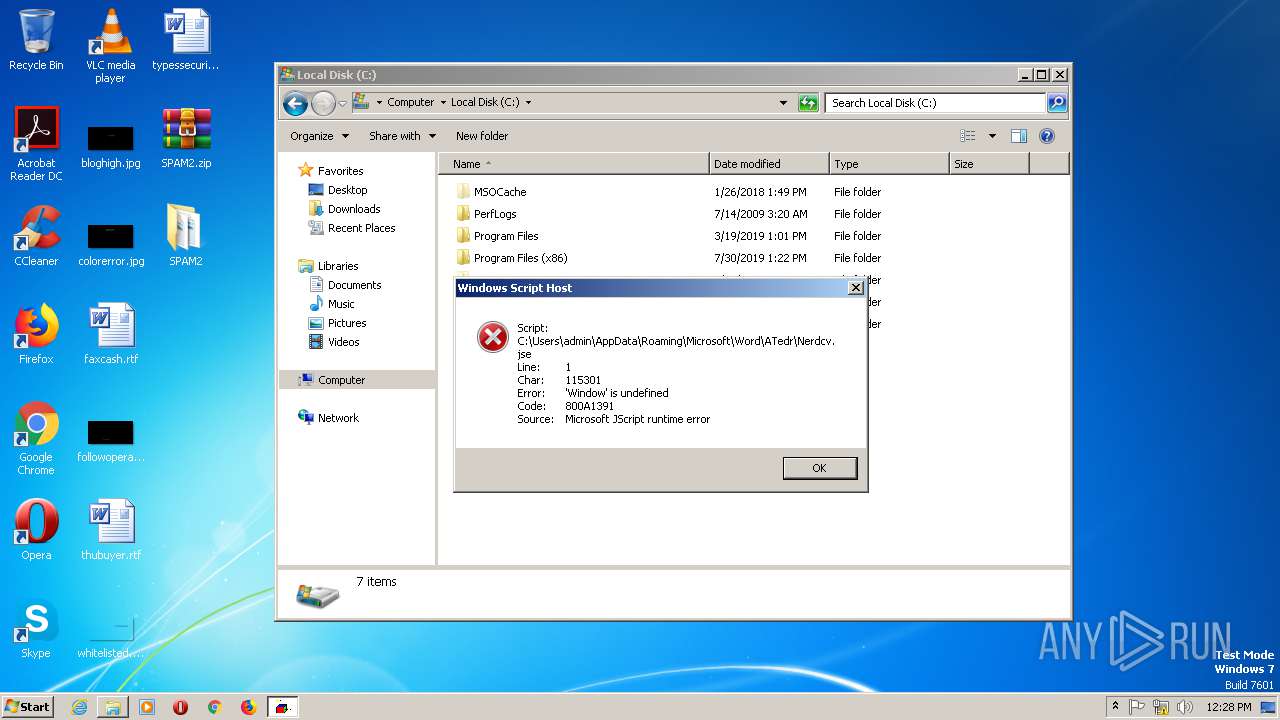
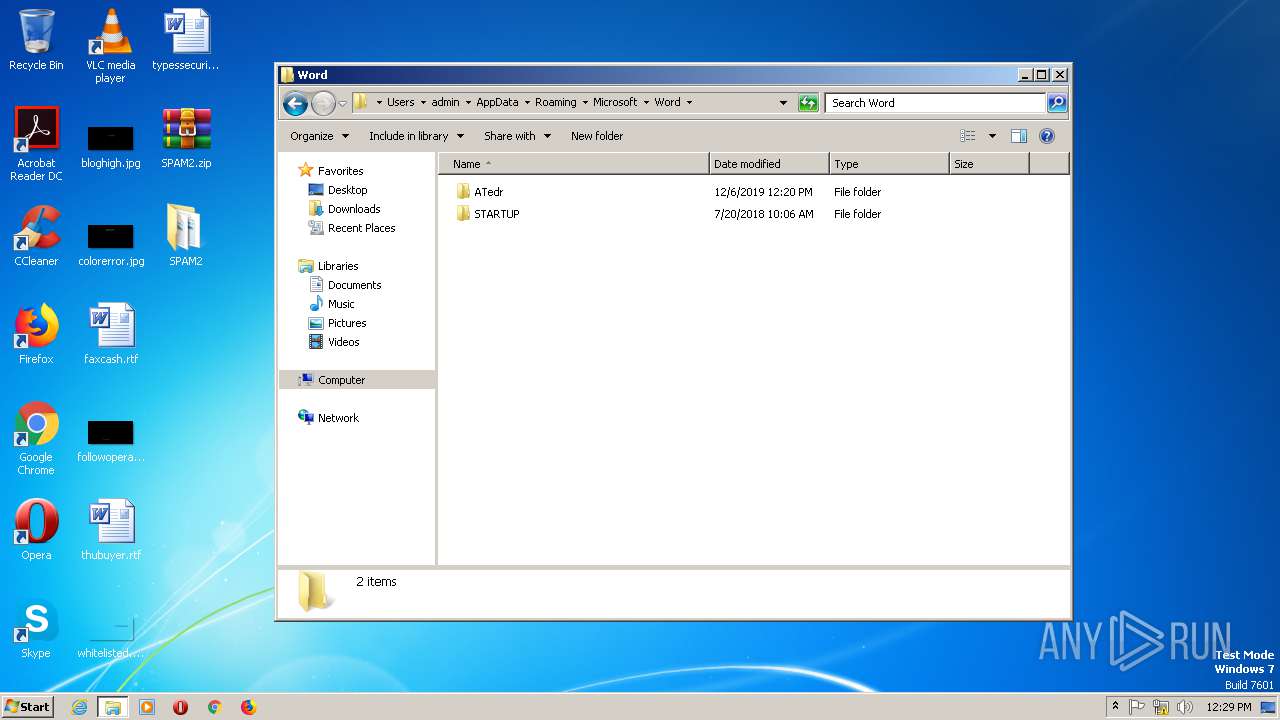
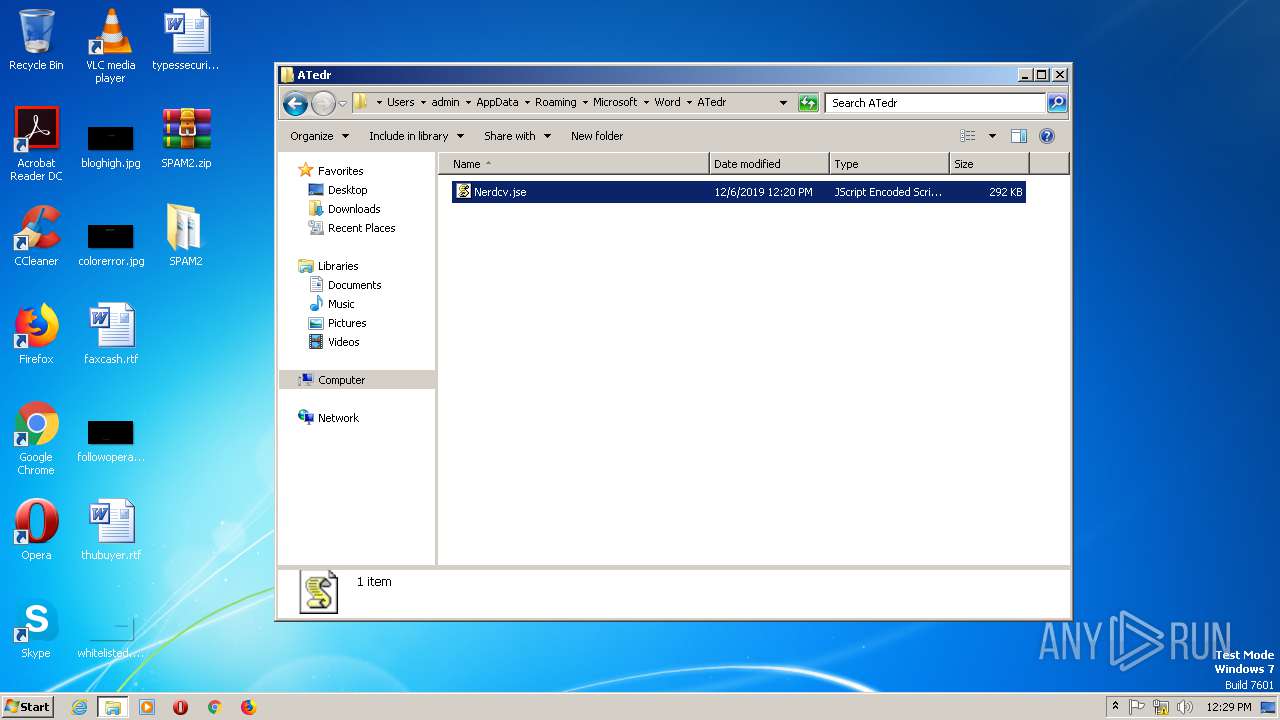
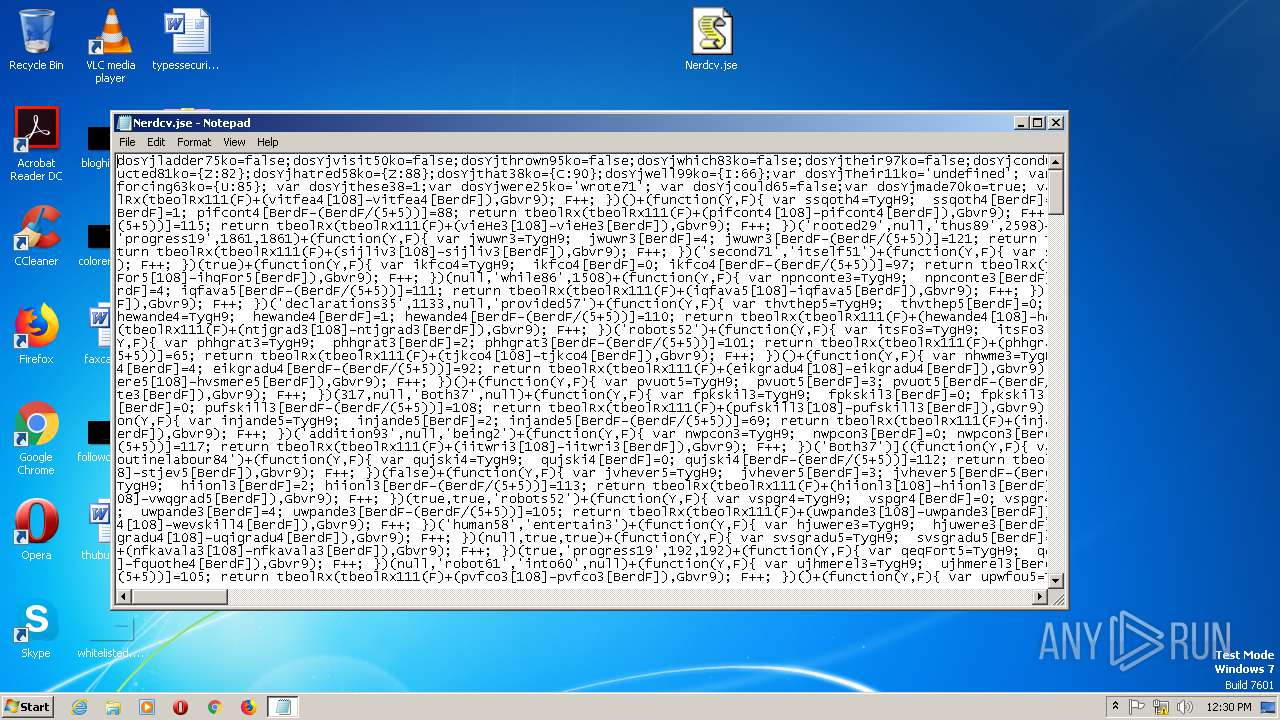
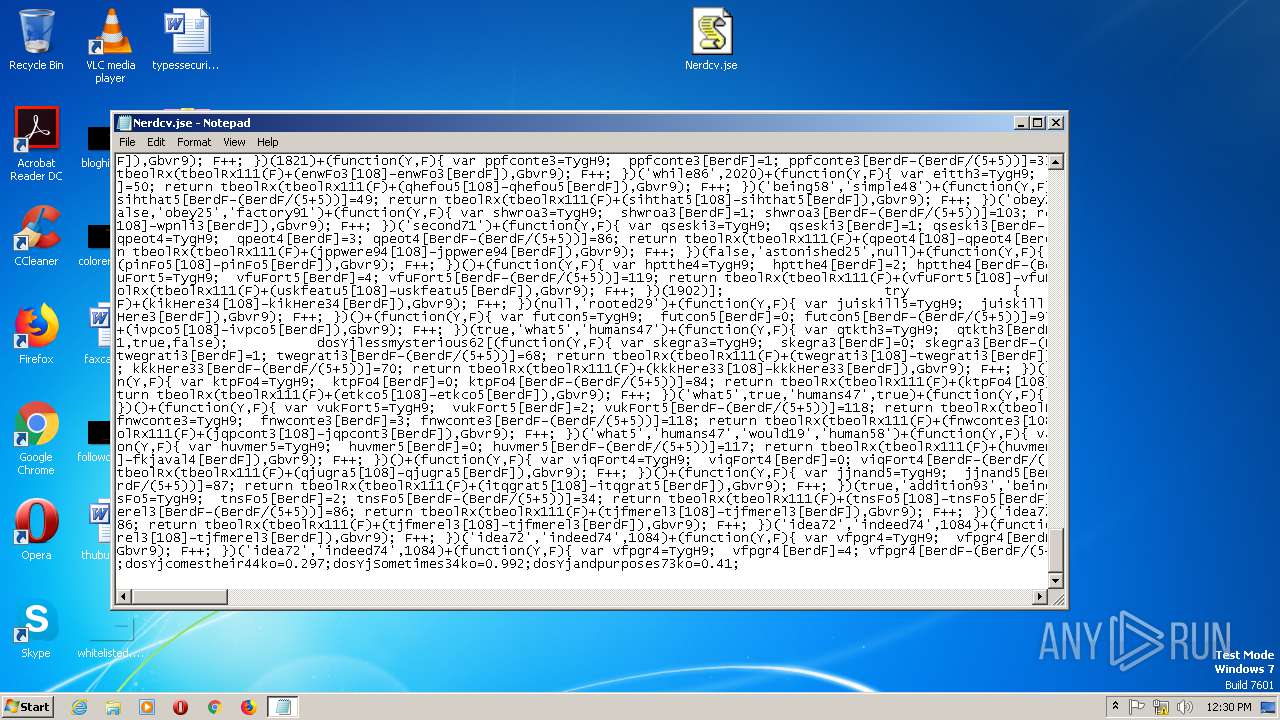
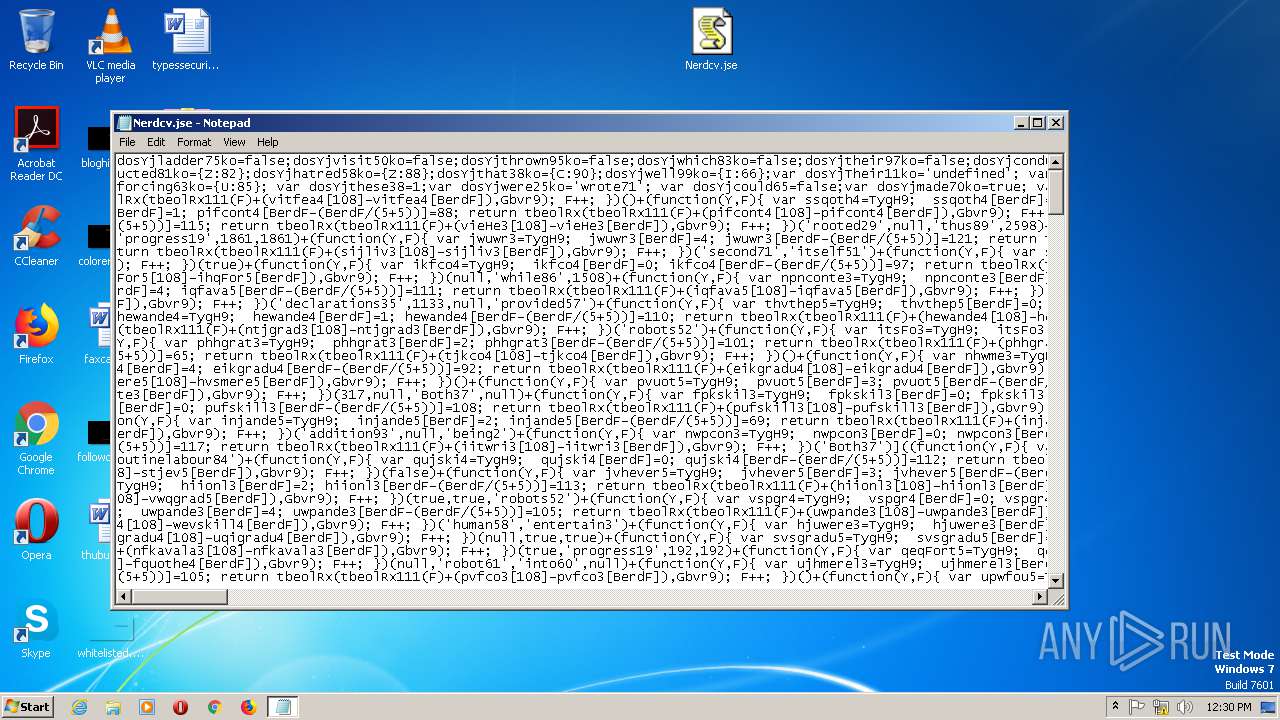
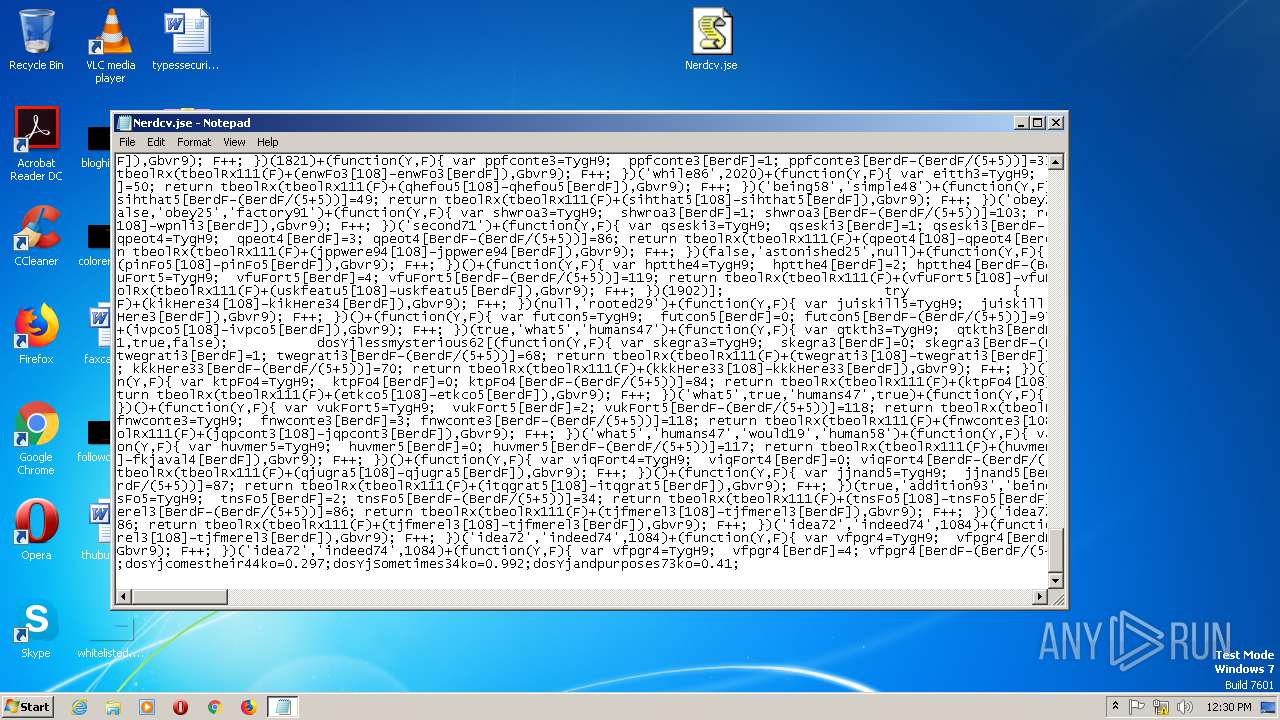
| 312 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Roaming\Microsoft\Word\ATedr\Nerdcv.jse" | C:\Windows\System32\WScript.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 344 | C:\Windows\system32\dwwin.exe -x -s 1076 | C:\Windows\system32\dwwin.exe | — | DW20.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Watson Client Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 400 | "C:\Windows\System32\Notepad.exe" C:\Users\admin\Desktop\Nerdcv.jse | C:\Windows\System32\Notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
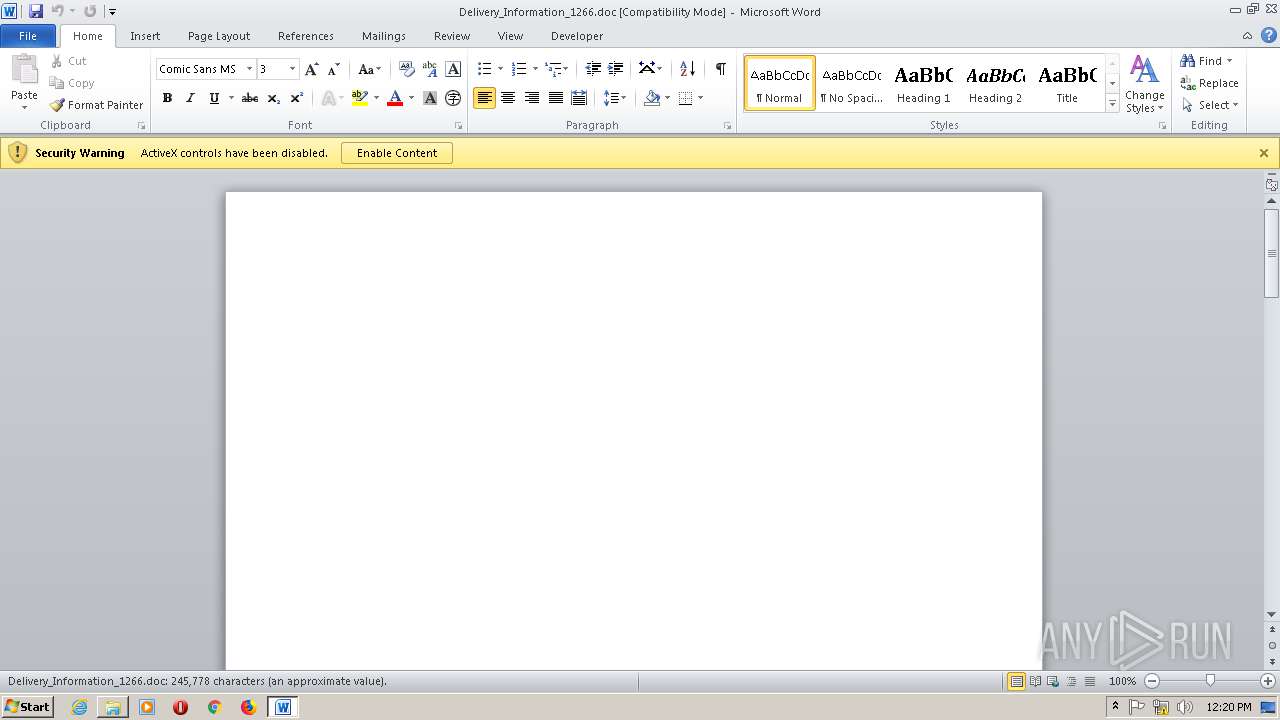
| 1176 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Roaming\Microsoft\Word\ATedr\Nerdcv.jse" | C:\Windows\System32\WScript.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
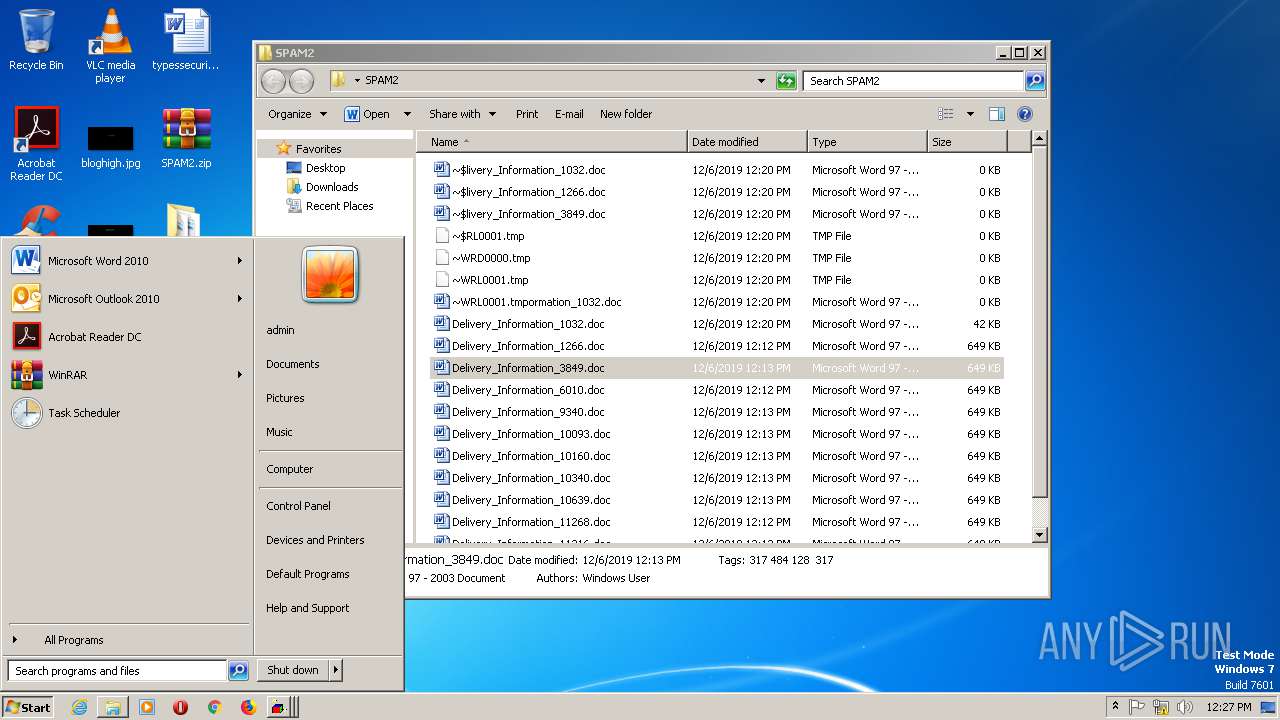
| 1508 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\SPAM2\Delivery_Information_3849.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.5123.5000 Modules
| |||||||||||||||
| 1700 | "C:\PROGRA~1\COMMON~1\MICROS~1\DW\DW20.EXE" -x -s 424 | C:\PROGRA~1\COMMON~1\MICROS~1\DW\DW20.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Application Error Reporting Exit code: 0 Version: 14.0.4750.1000 Modules
| |||||||||||||||
| 1788 | C:\Windows\system32\dwwin.exe -x -s 424 | C:\Windows\system32\dwwin.exe | — | DW20.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Watson Client Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2040 | "C:\PROGRA~1\COMMON~1\MICROS~1\DW\DW20.EXE" -x -s 1080 | C:\PROGRA~1\COMMON~1\MICROS~1\DW\DW20.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Application Error Reporting Exit code: 0 Version: 14.0.4750.1000 Modules
| |||||||||||||||
| 2100 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Desktop\Nerdcv.jse" | C:\Windows\System32\WScript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2128 | "C:\PROGRA~1\COMMON~1\MICROS~1\DW\DW20.EXE" -x -s 1076 | C:\PROGRA~1\COMMON~1\MICROS~1\DW\DW20.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Application Error Reporting Exit code: 0 Version: 14.0.4750.1000 Modules
| |||||||||||||||
Total events
5 177
Read events
4 087
Write events
662
Delete events
428
Modification events
| (PID) Process: | (2612) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2612) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2612) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2612) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\SPAM2.zip | |||
| (PID) Process: | (2612) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2612) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2612) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2612) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2612) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF1600000016000000D60300000B020000 | |||
| (PID) Process: | (2612) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\Desktop | |||
Executable files
0
Suspicious files
23
Text files
6
Unknown types
20
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2804 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRAC98.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2804 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\F790FF89.wmf | — | |
MD5:— | SHA256:— | |||
| 2804 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\BF9F537F.wmf | — | |
MD5:— | SHA256:— | |||
| 2712 | WinRAR.exe | C:\Users\admin\Desktop\SPAM2\Delivery_Information_11316.doc | document | |
MD5:— | SHA256:— | |||
| 2804 | WINWORD.EXE | C:\Users\admin\Desktop\SPAM2\~WRD0000.tmp | — | |
MD5:— | SHA256:— | |||
| 2804 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF77C5319DAE46F780.TMP | — | |
MD5:— | SHA256:— | |||
| 2712 | WinRAR.exe | C:\Users\admin\Desktop\SPAM2\Delivery_Information_11268.doc | document | |
MD5:— | SHA256:— | |||
| 2804 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\46051783.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2804 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFFF0A77A0CF72E235.TMP | — | |
MD5:— | SHA256:— | |||
| 2804 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF456D24747B769890.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
192 | mscorsvw.exe | GET | 200 | 8.248.123.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?4cc838c554051176 | US | compressed | 6.73 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
192 | mscorsvw.exe | 8.248.123.254:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ctldl.windowsupdate.com |
| whitelisted |