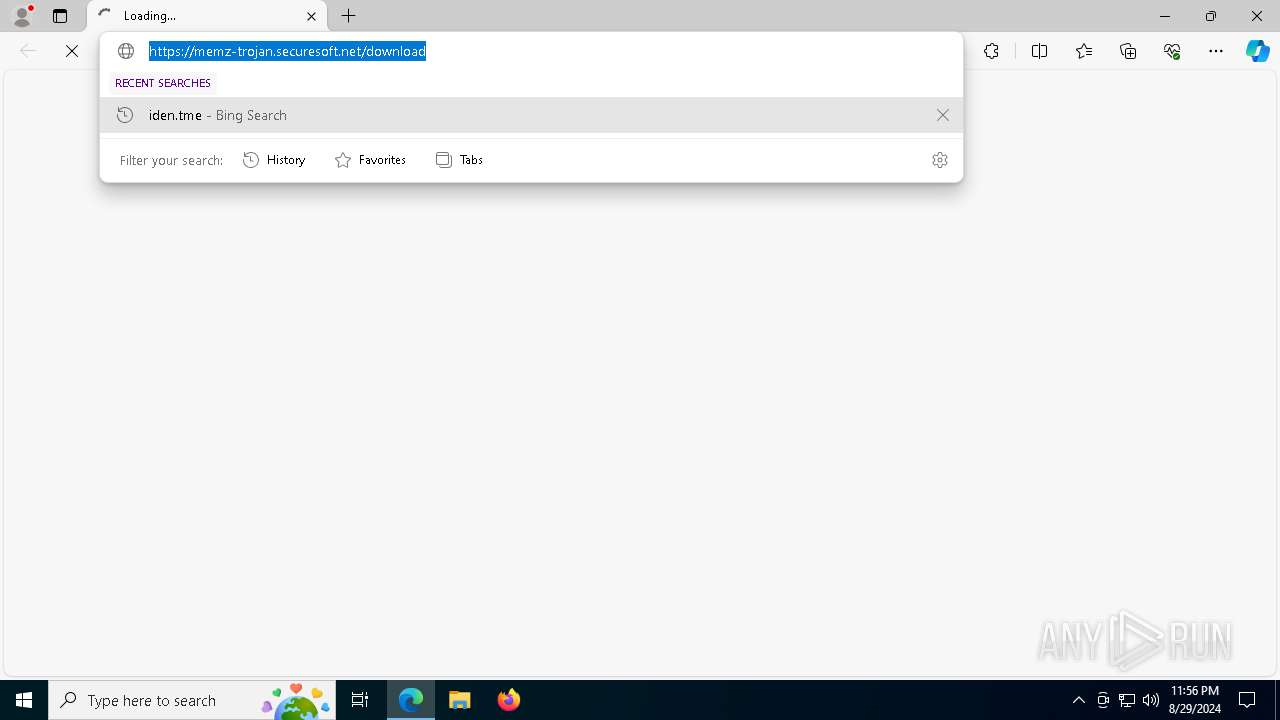
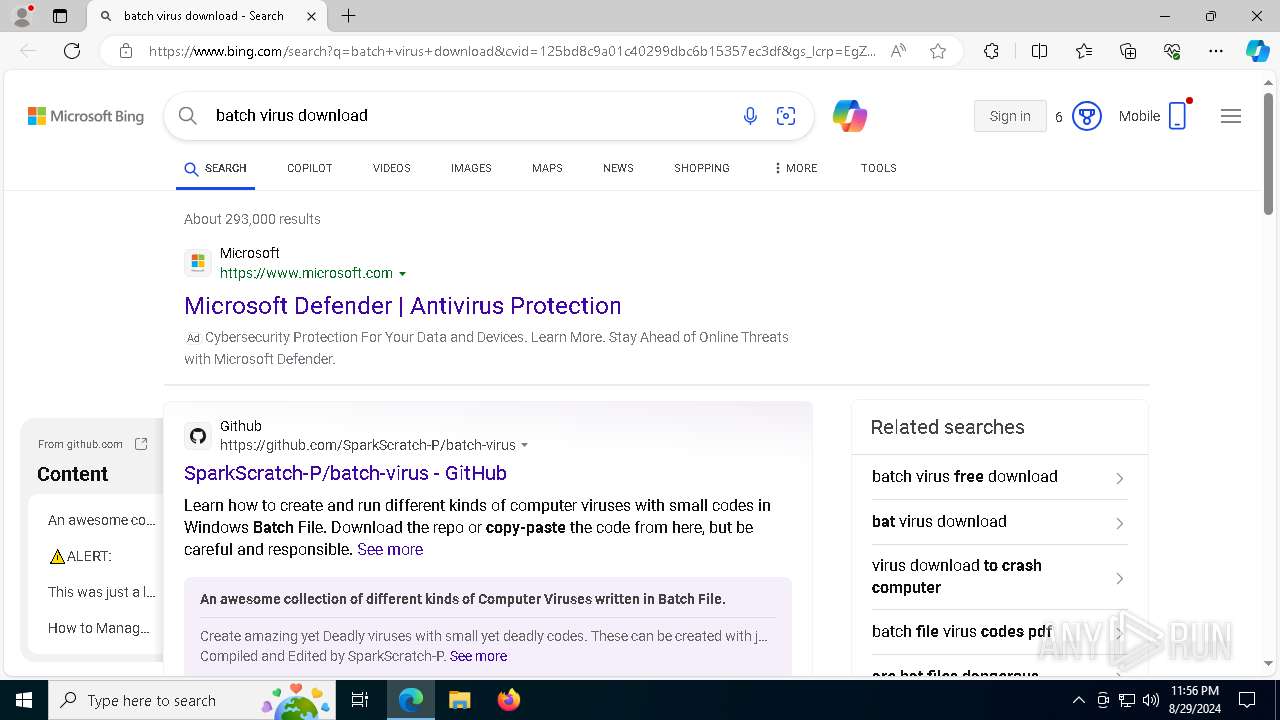
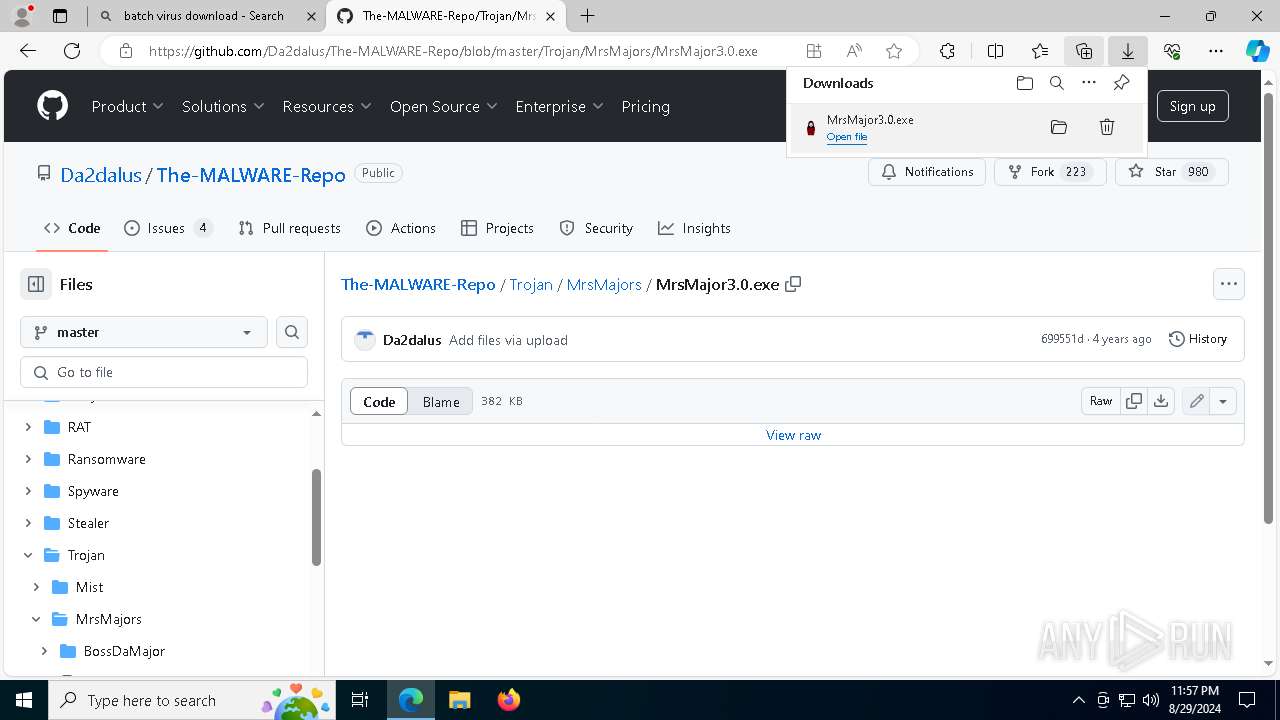
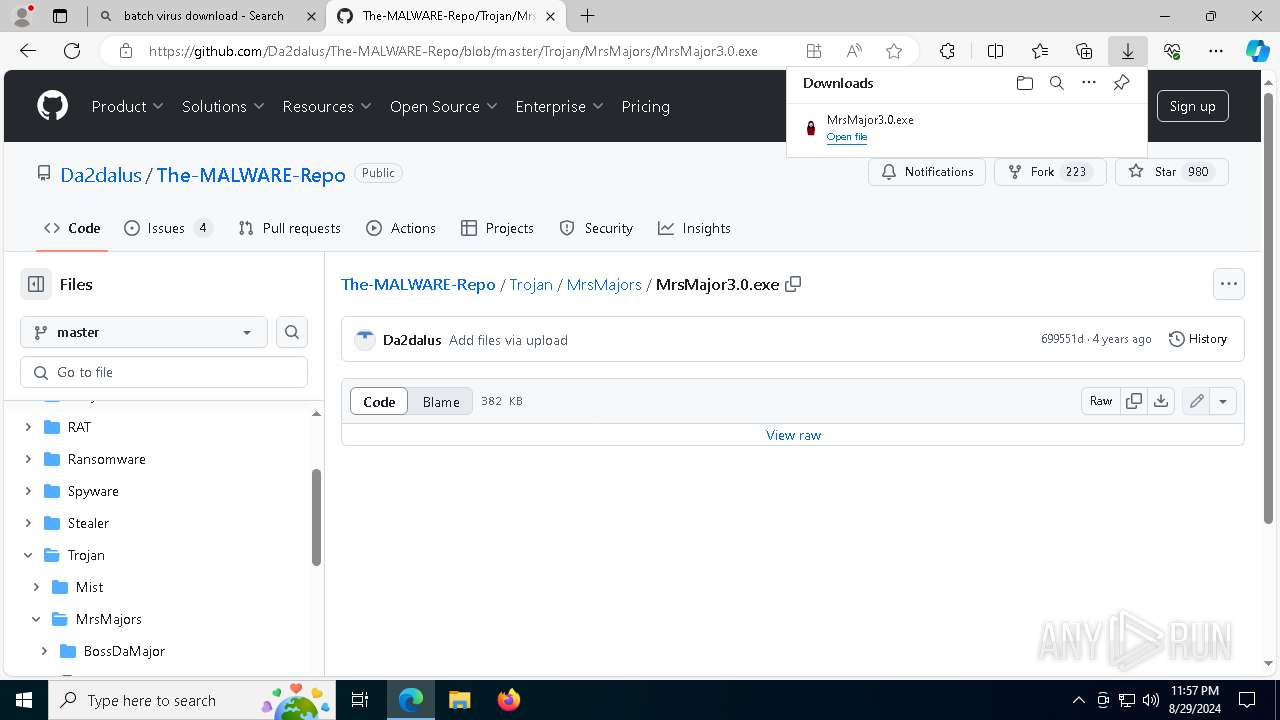
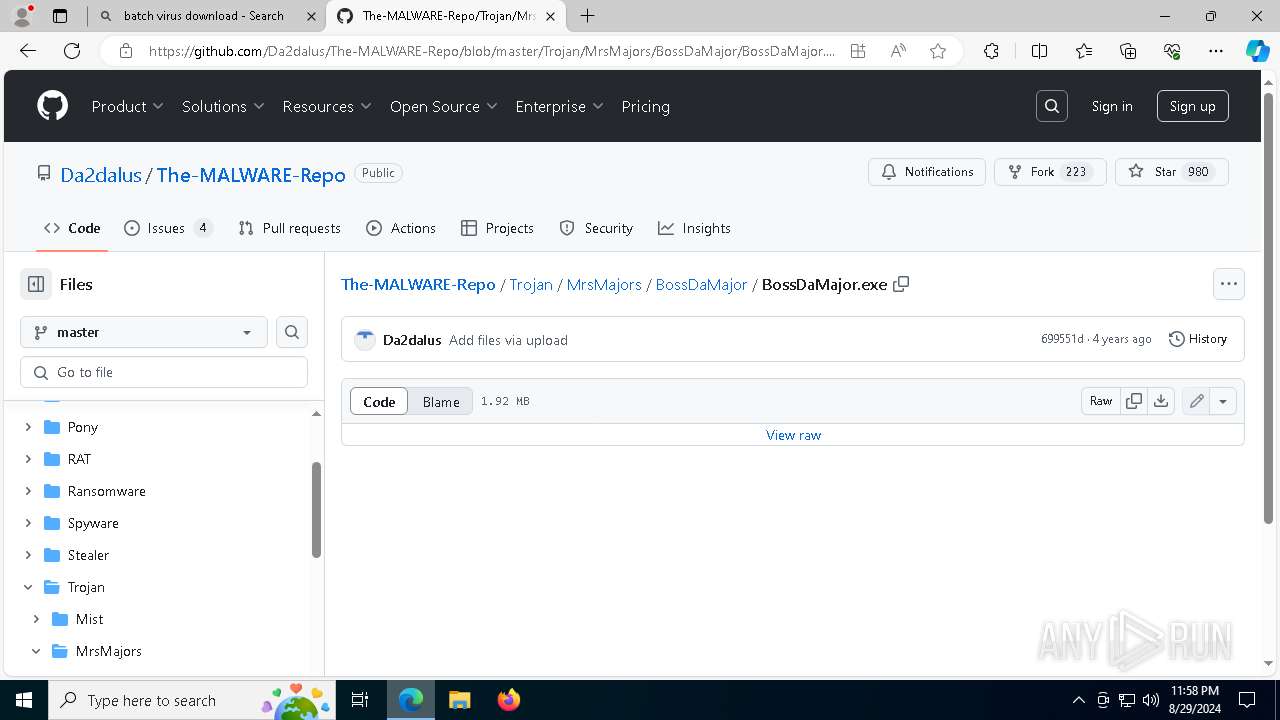
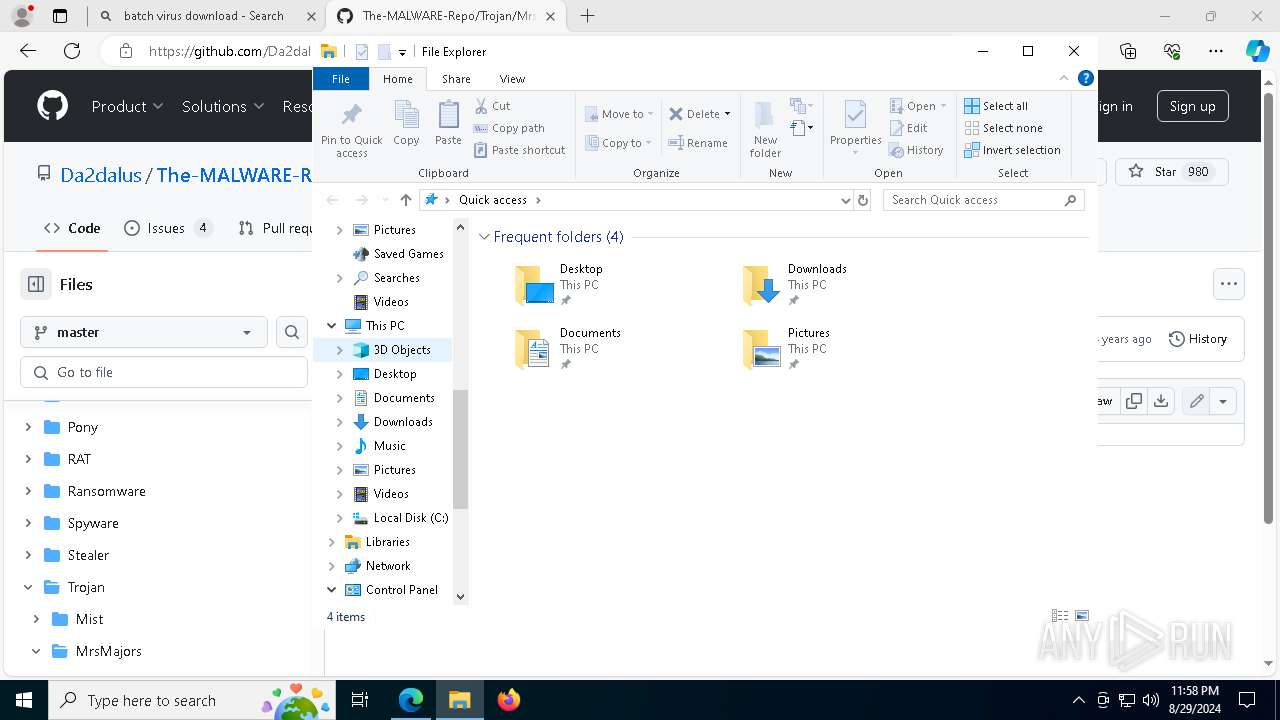
| URL: | https://memz-trojan.securesoft.net/download |
| Full analysis: | https://app.any.run/tasks/acd6d564-a7a7-462b-bbc5-61b537f87707 |
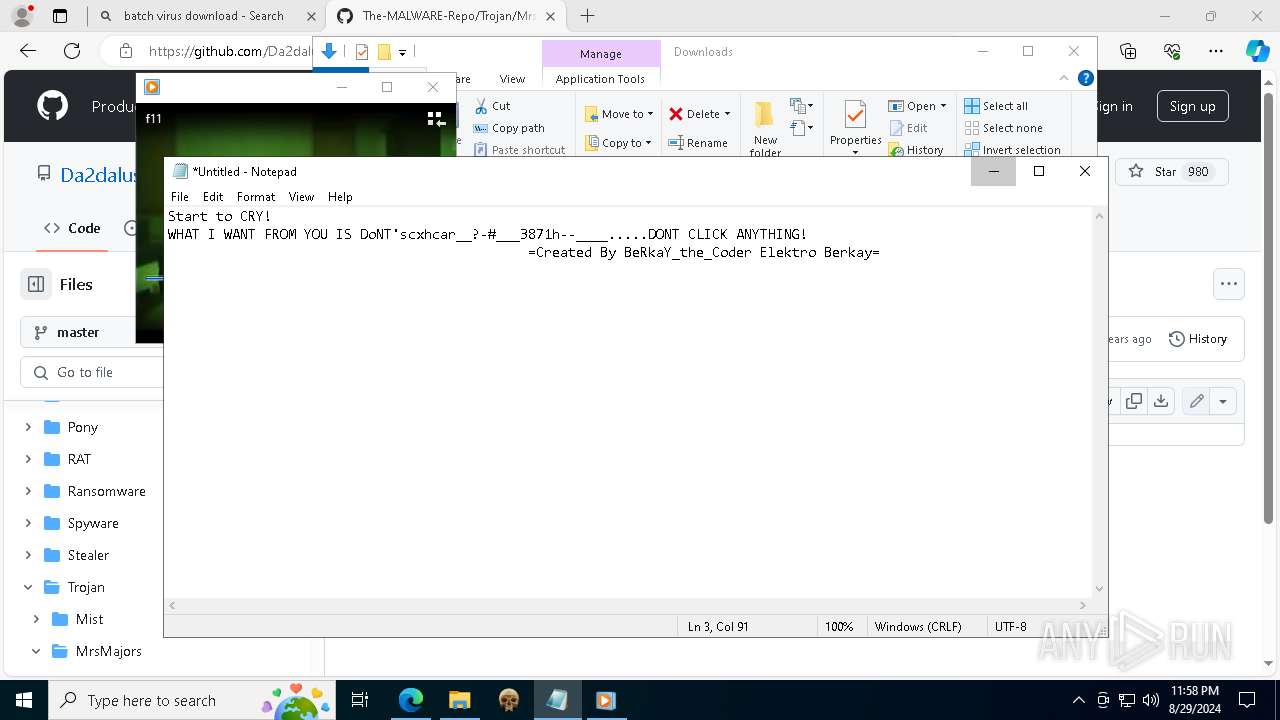
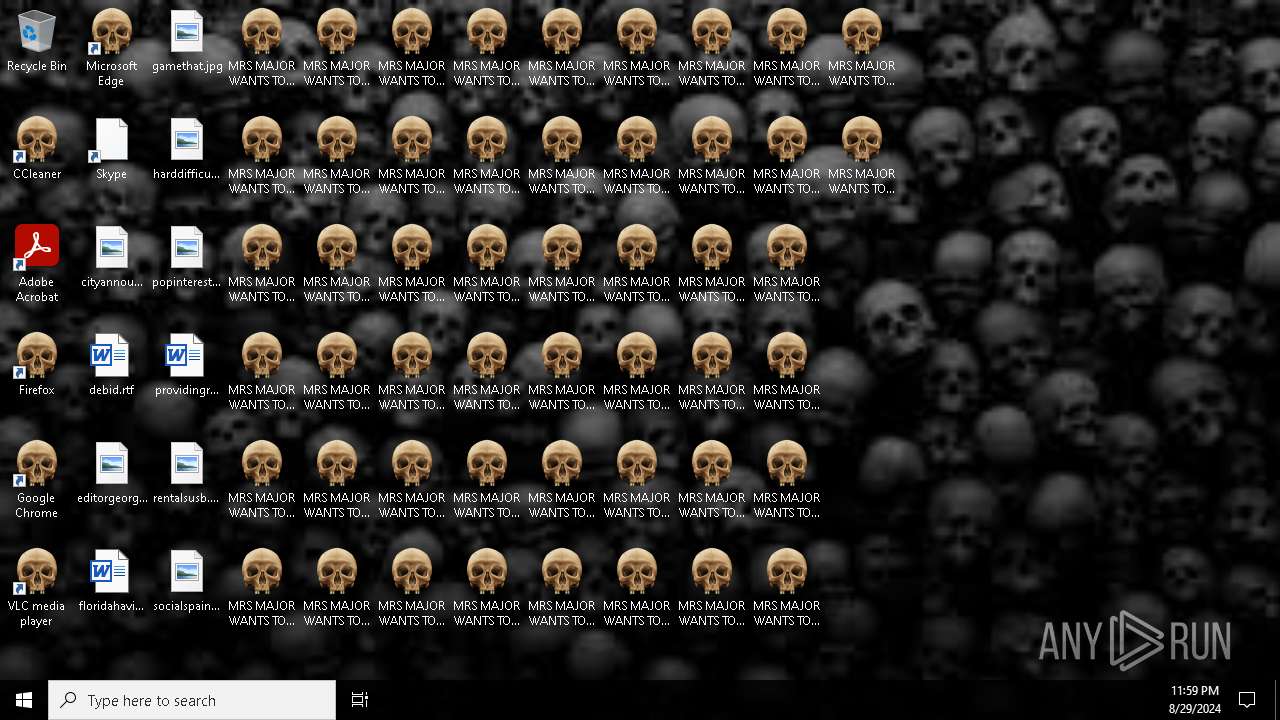
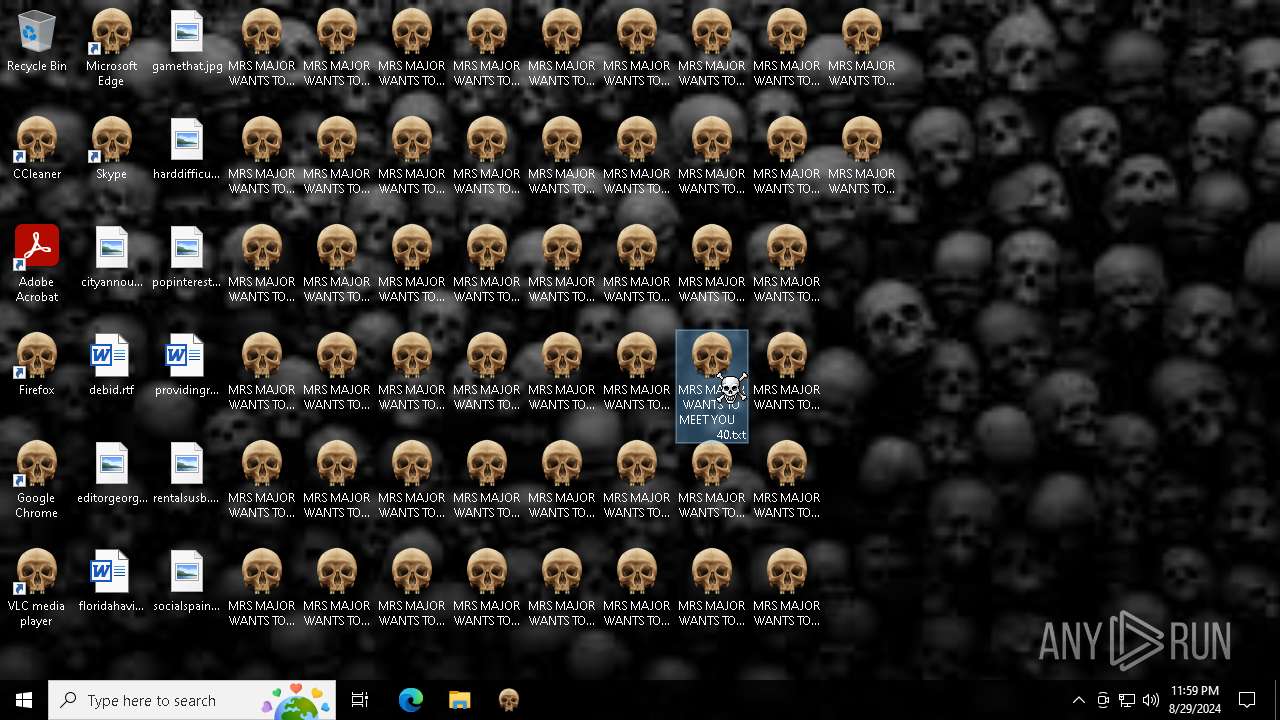
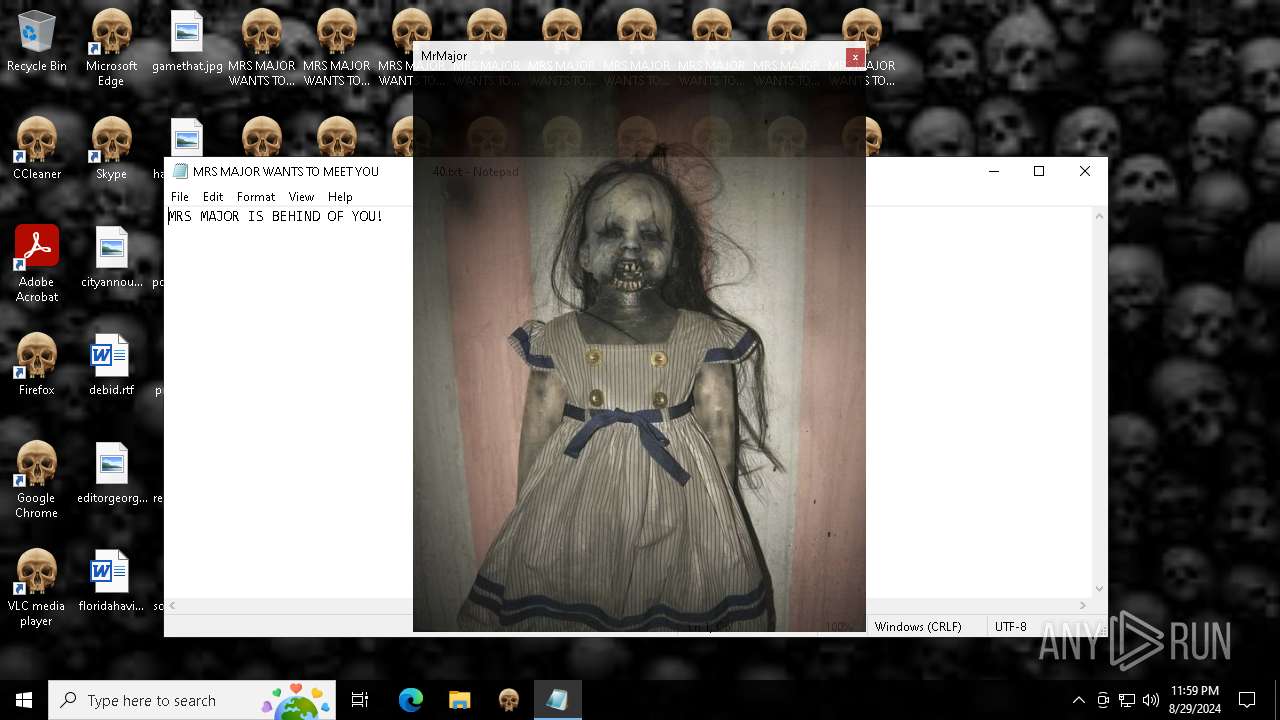
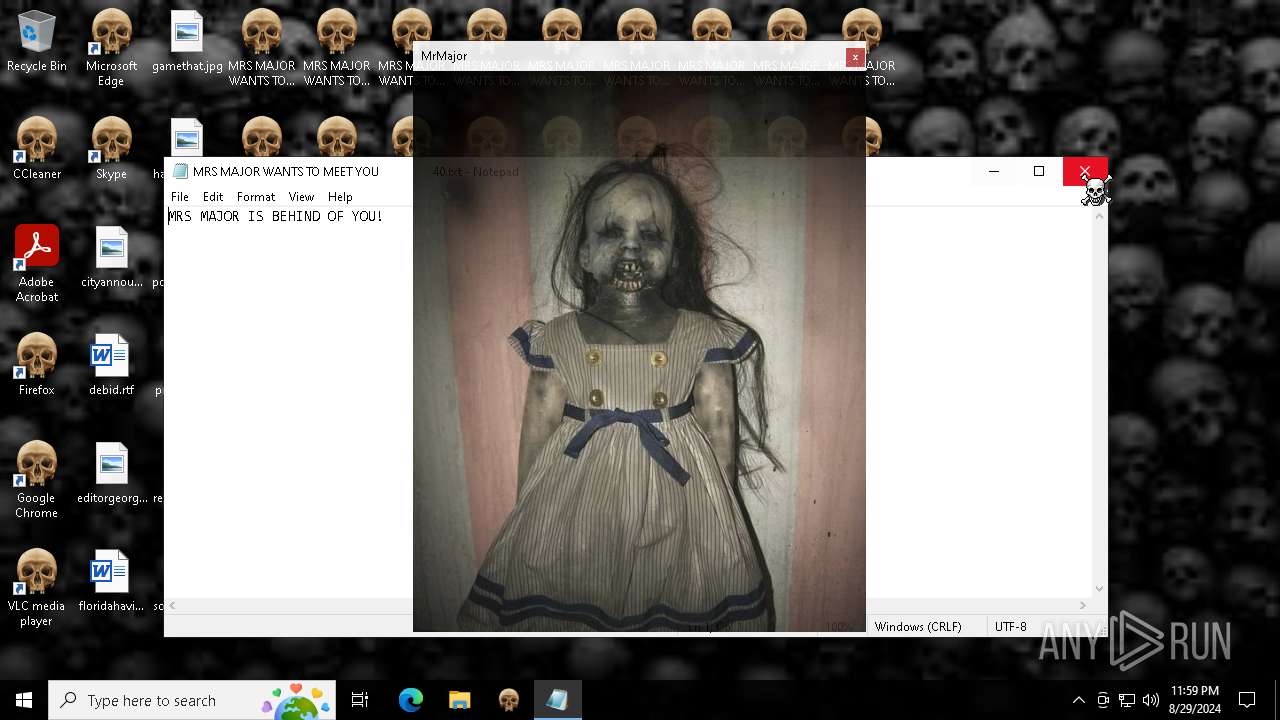
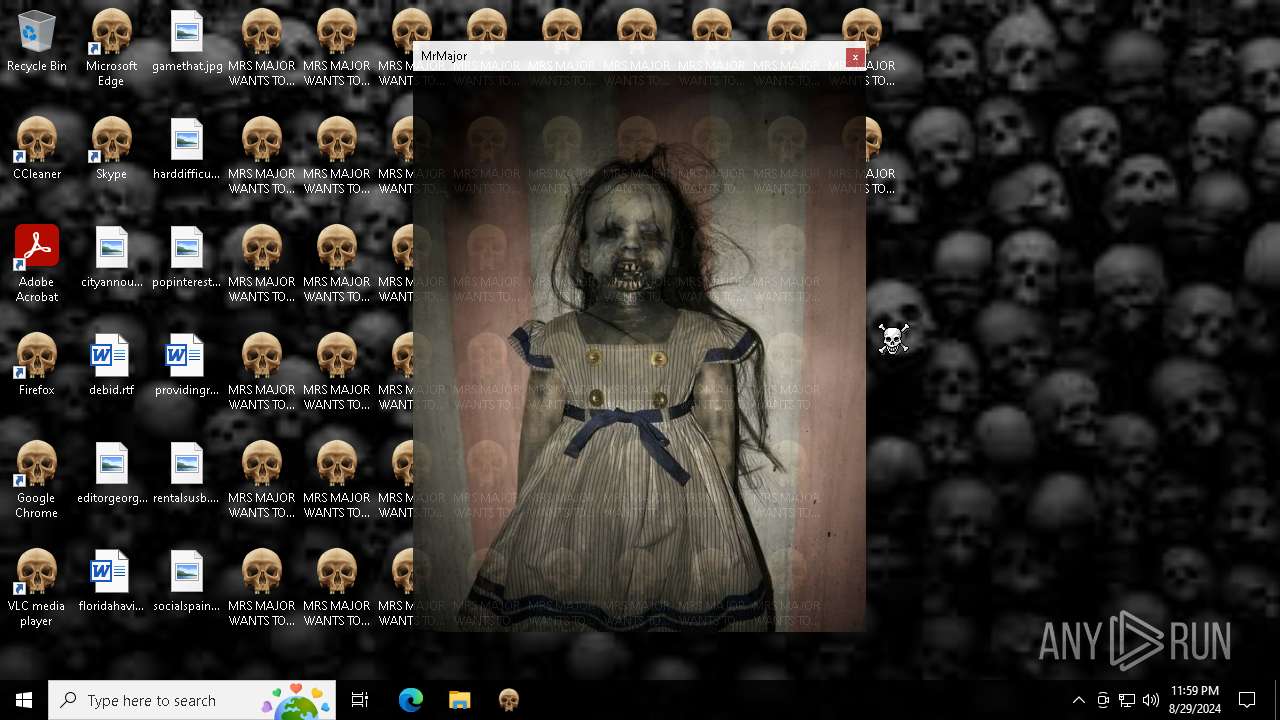
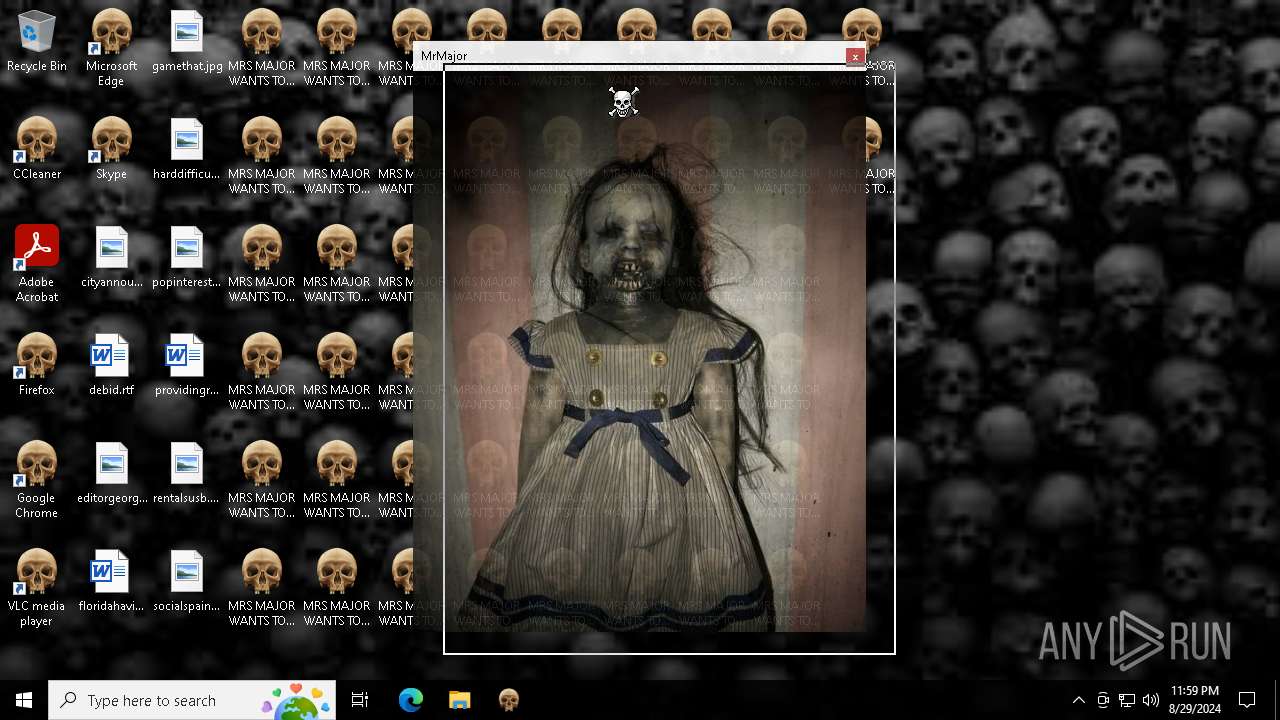
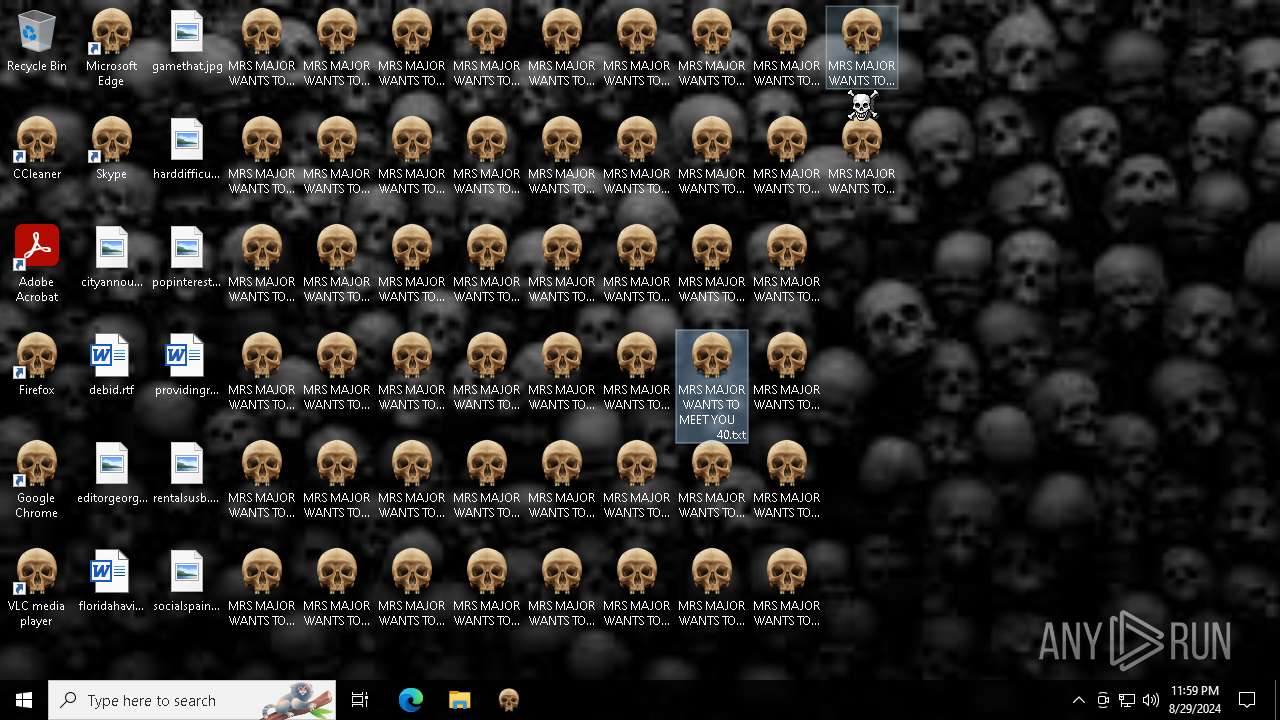
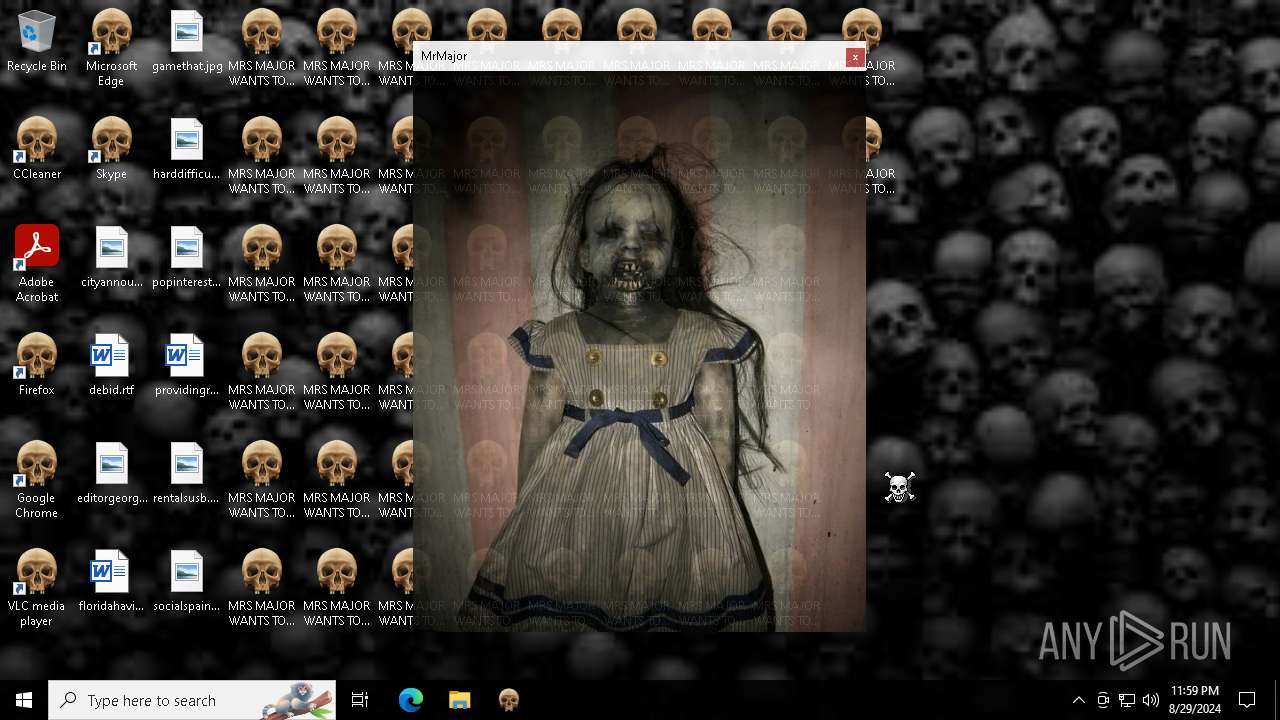
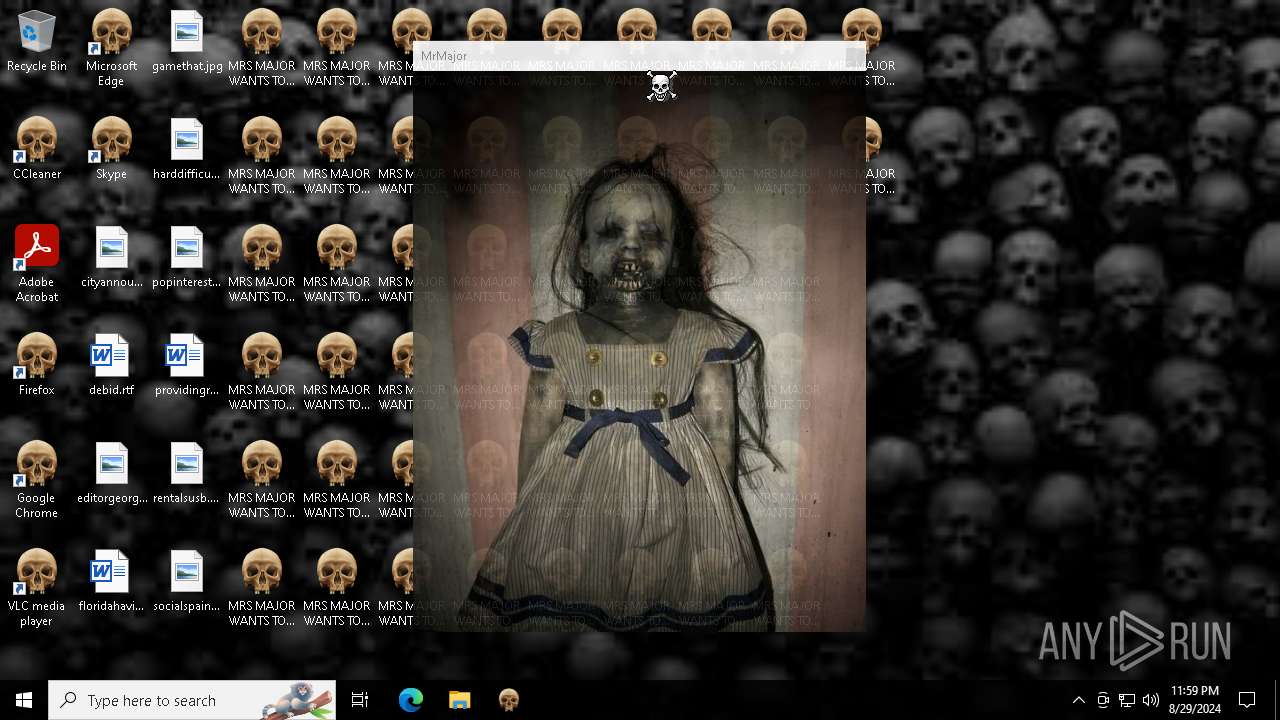
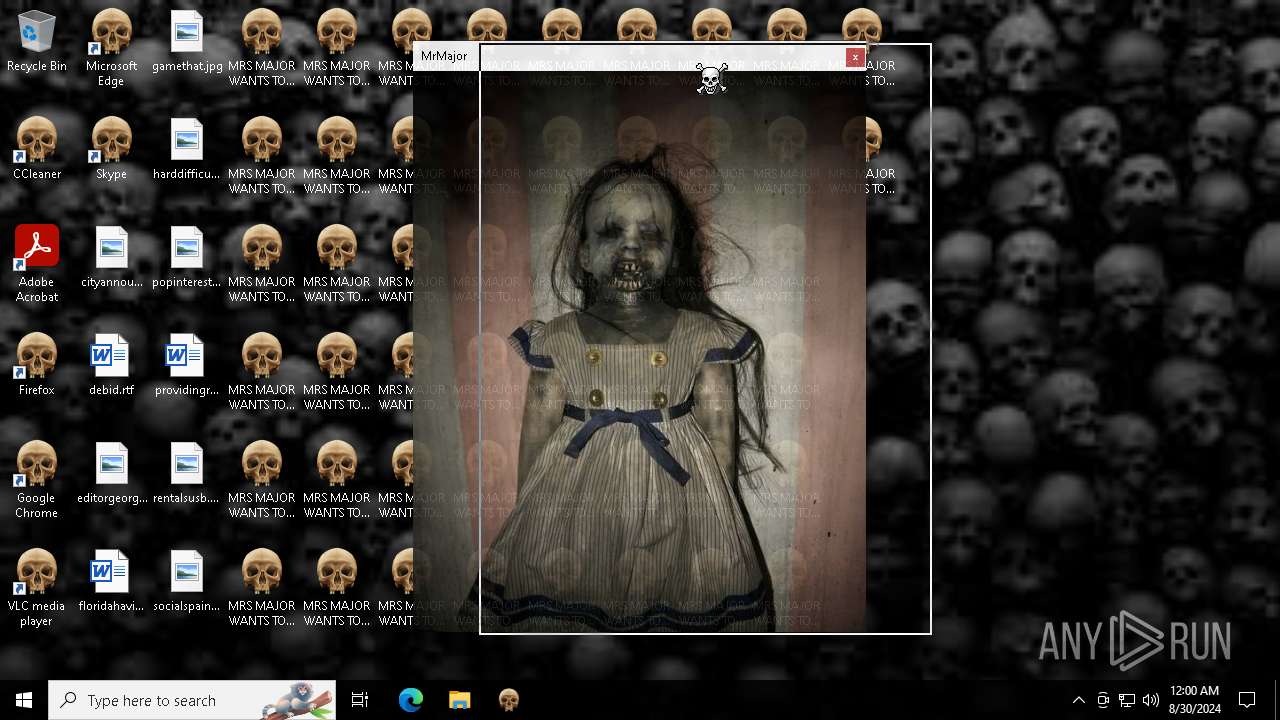
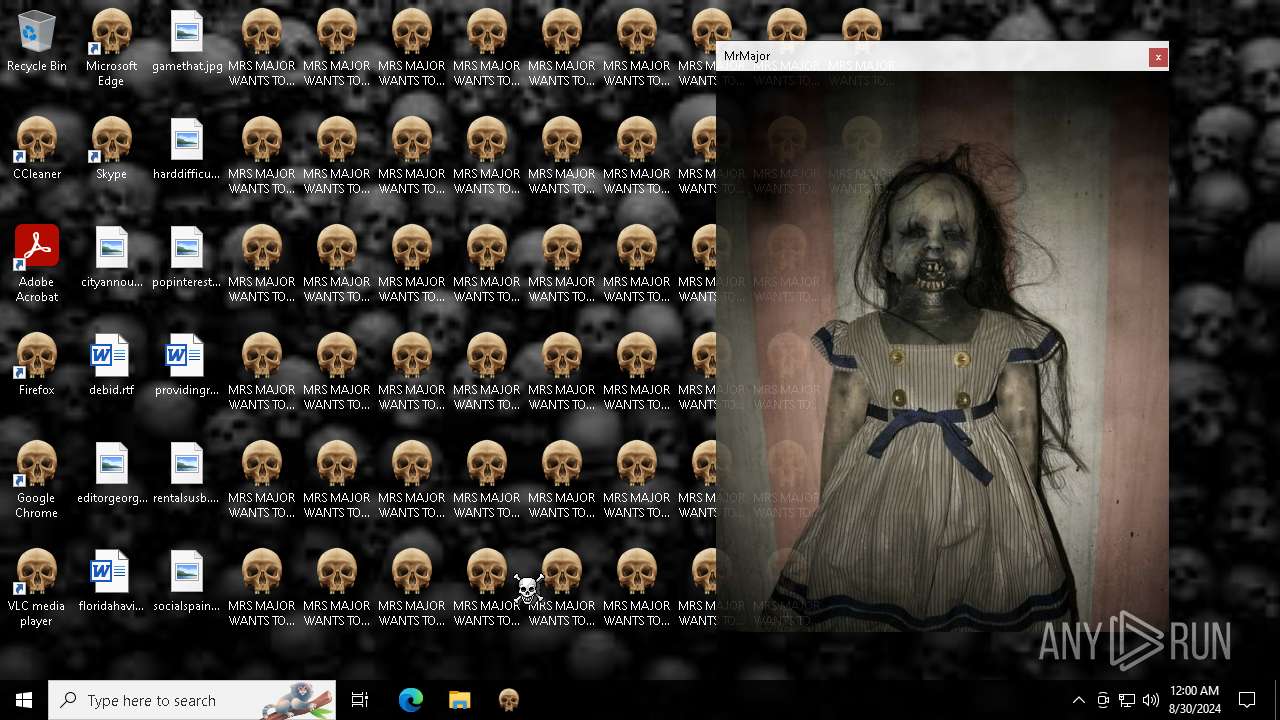
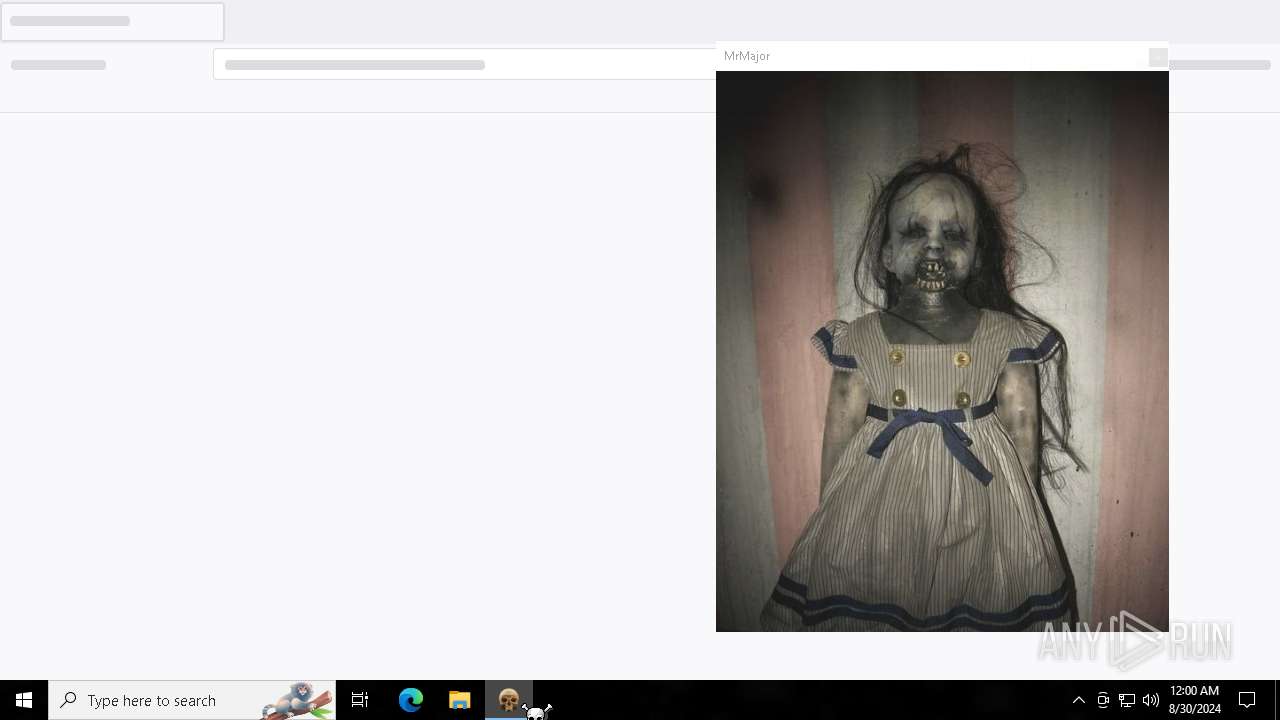
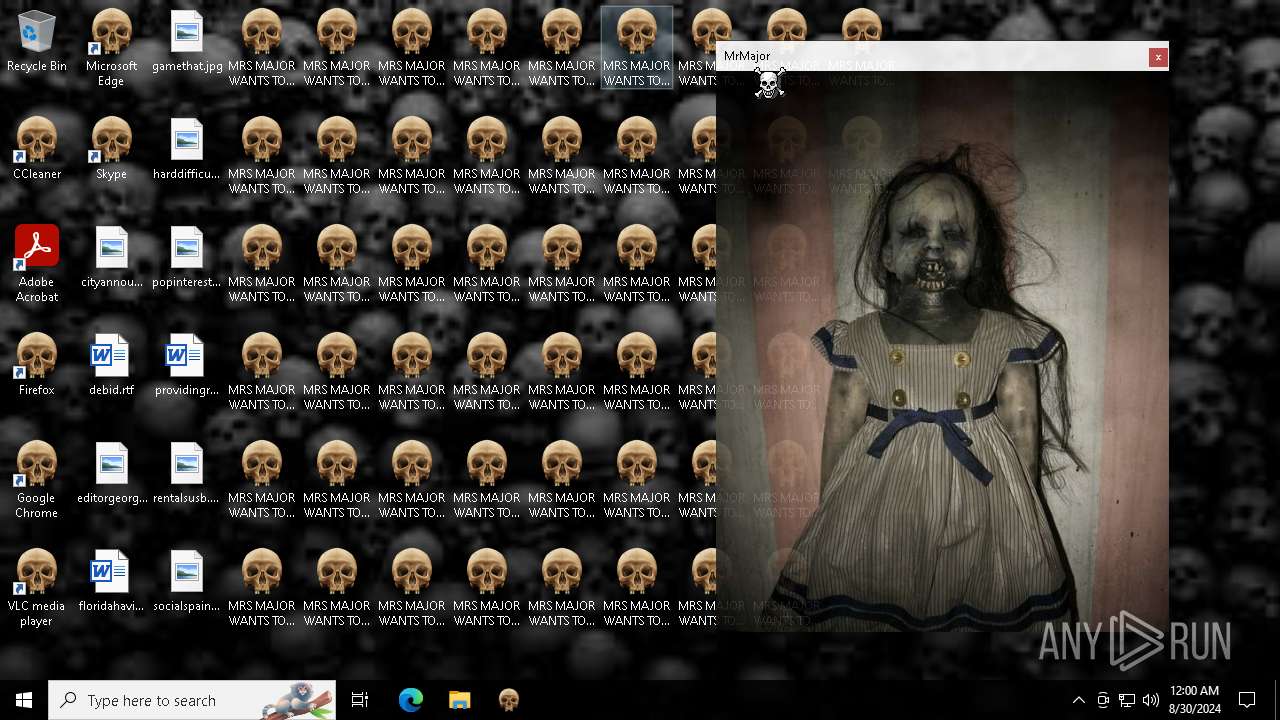
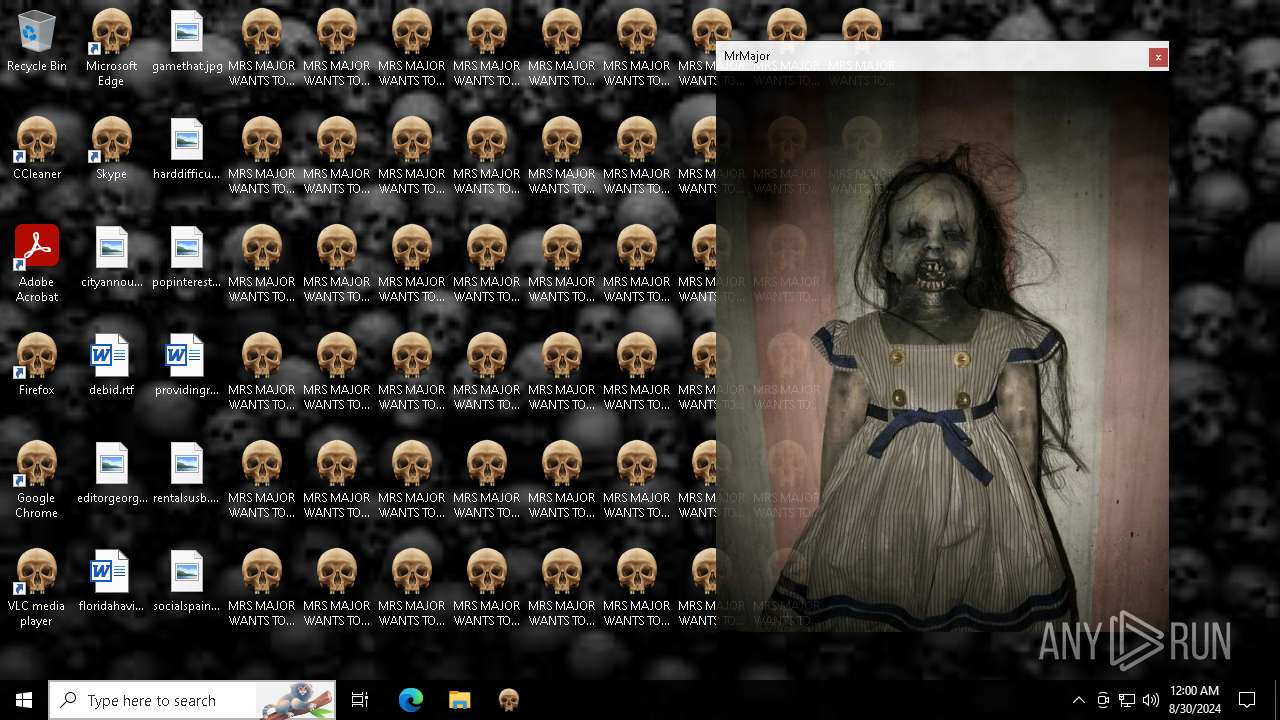
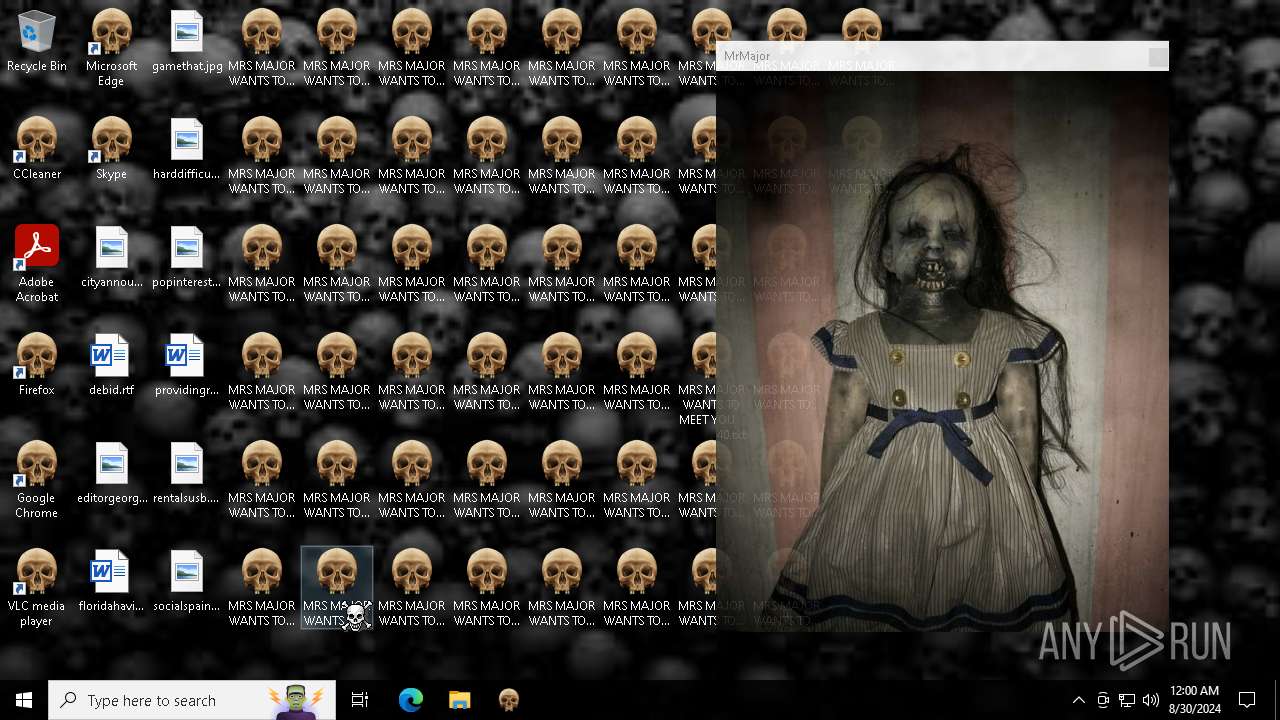
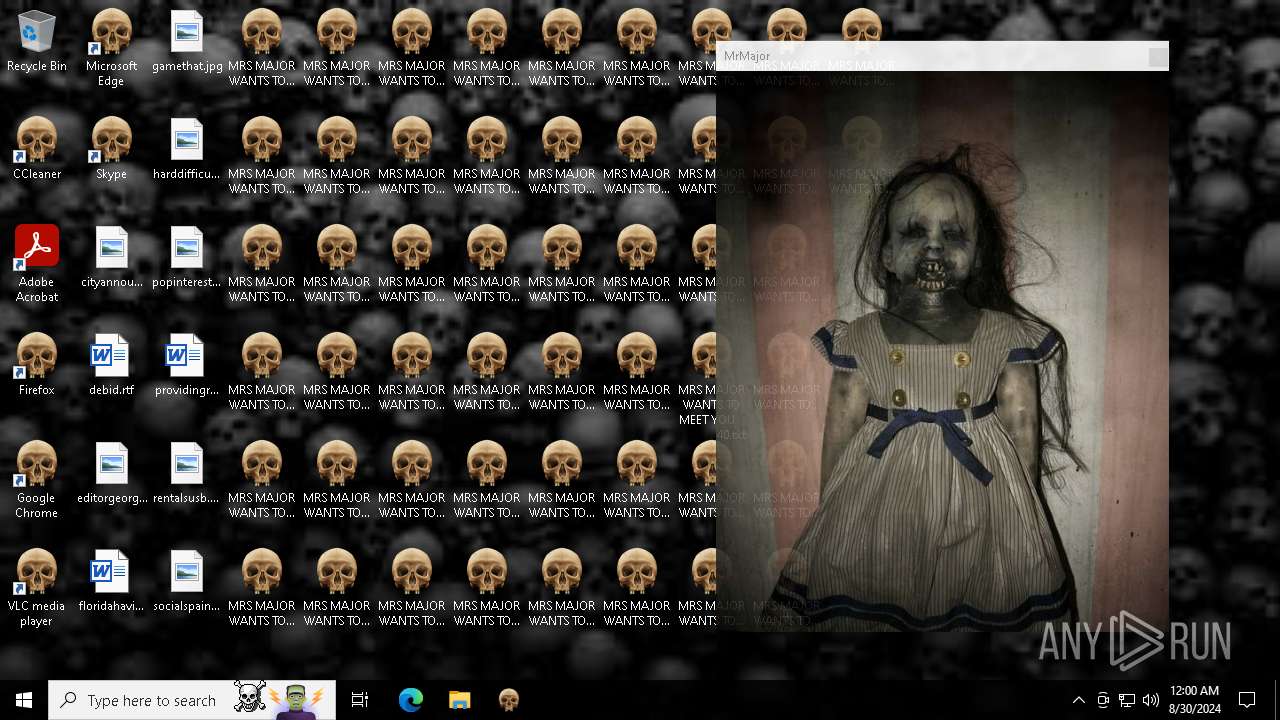
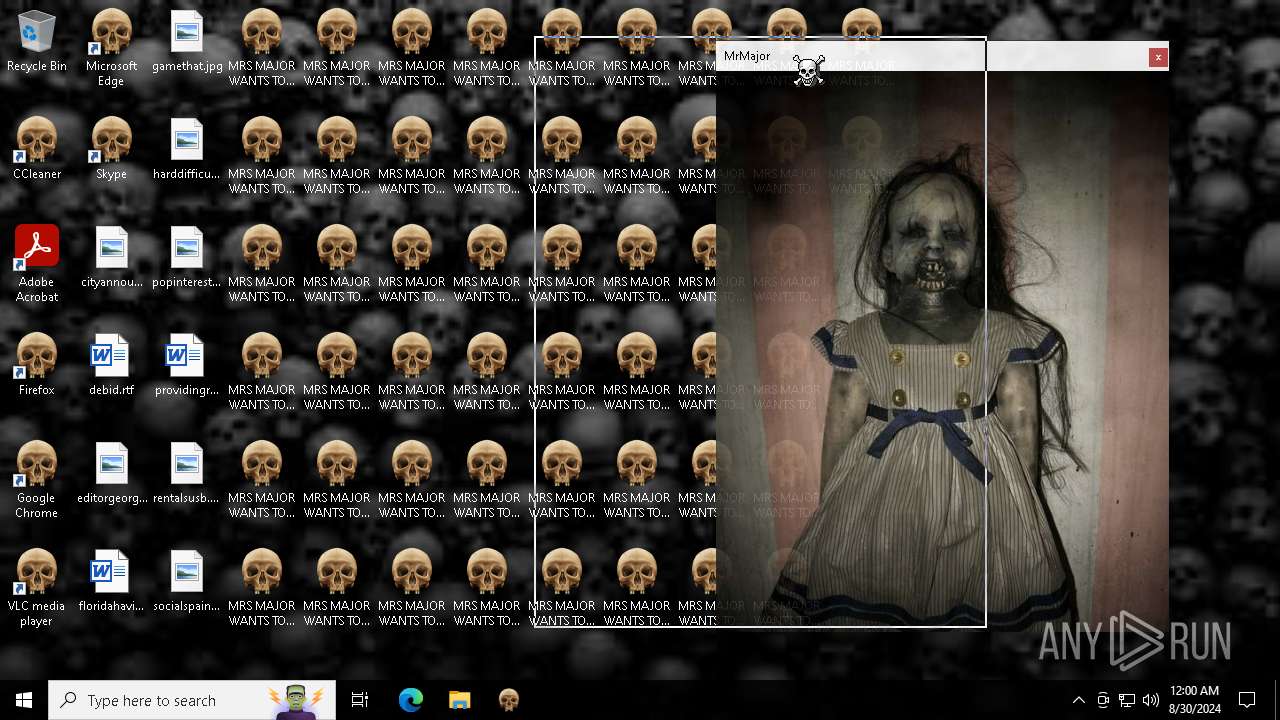
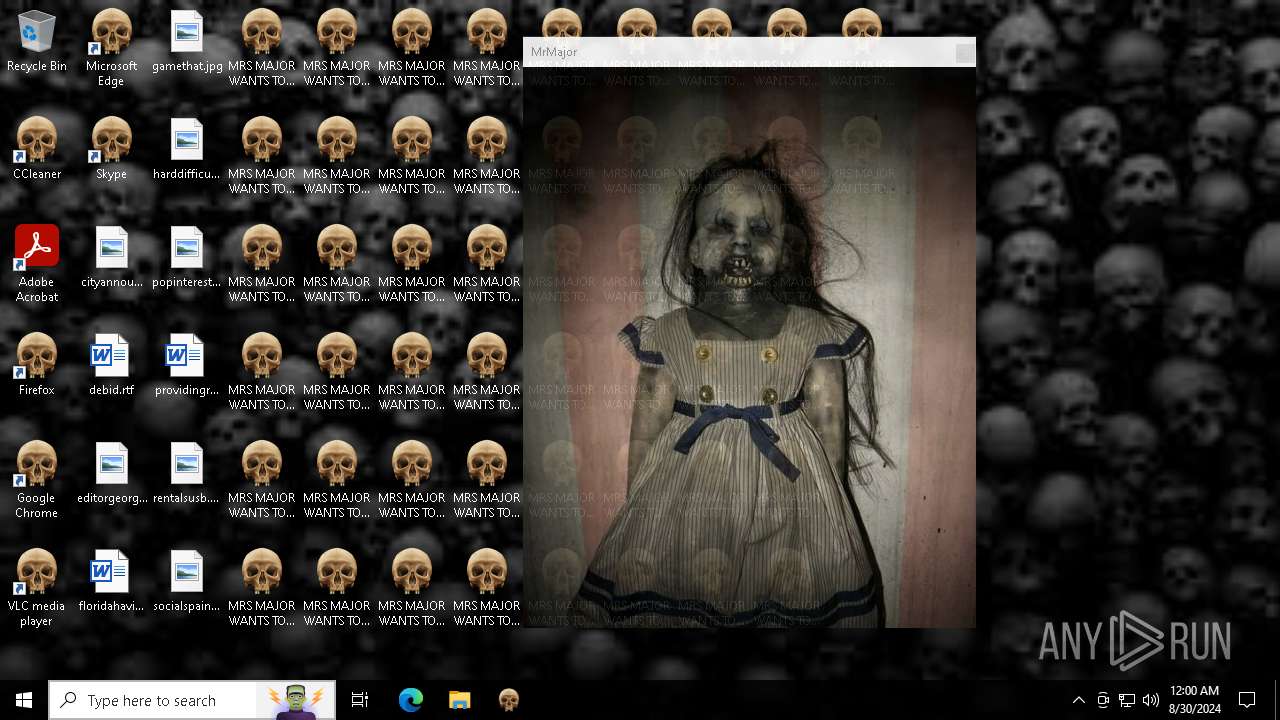
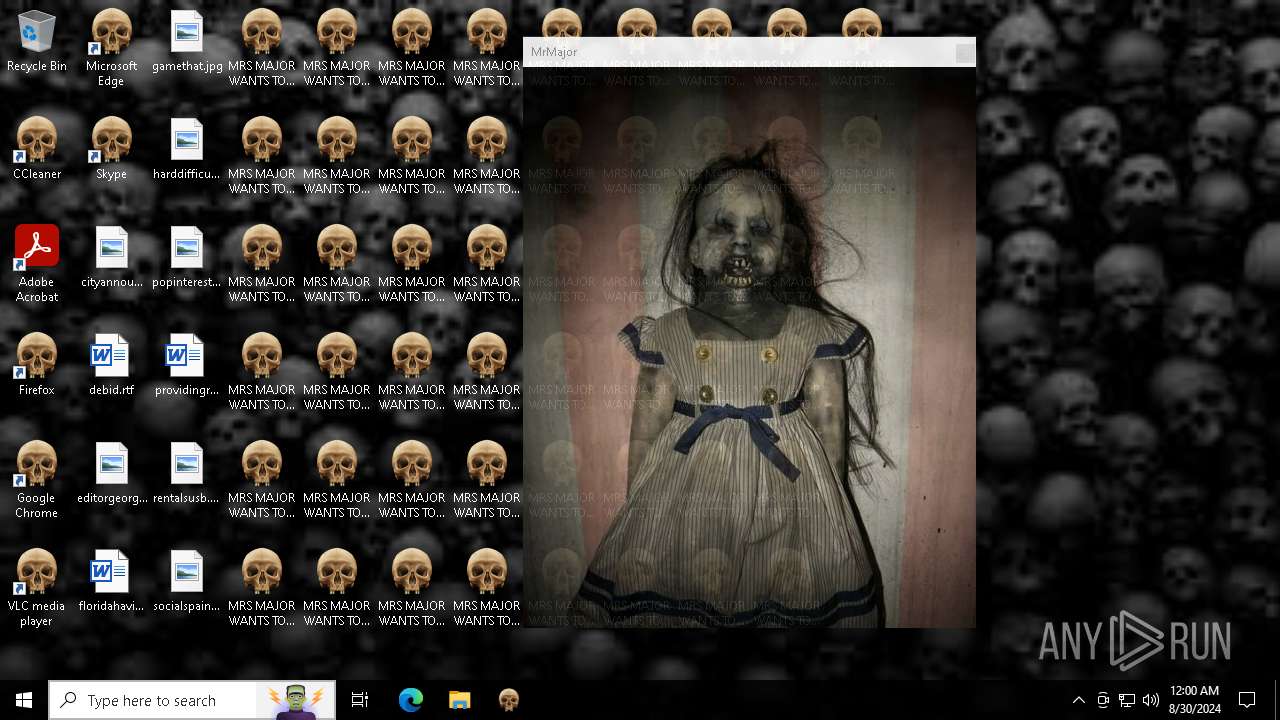
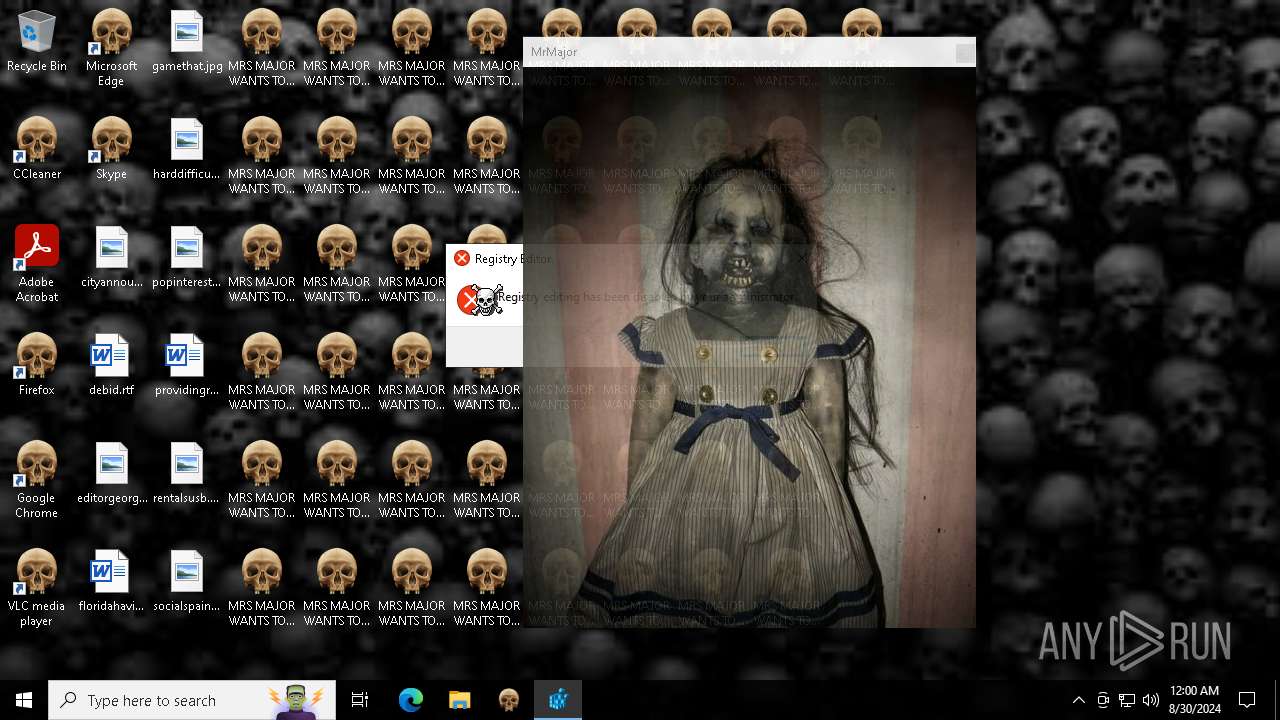
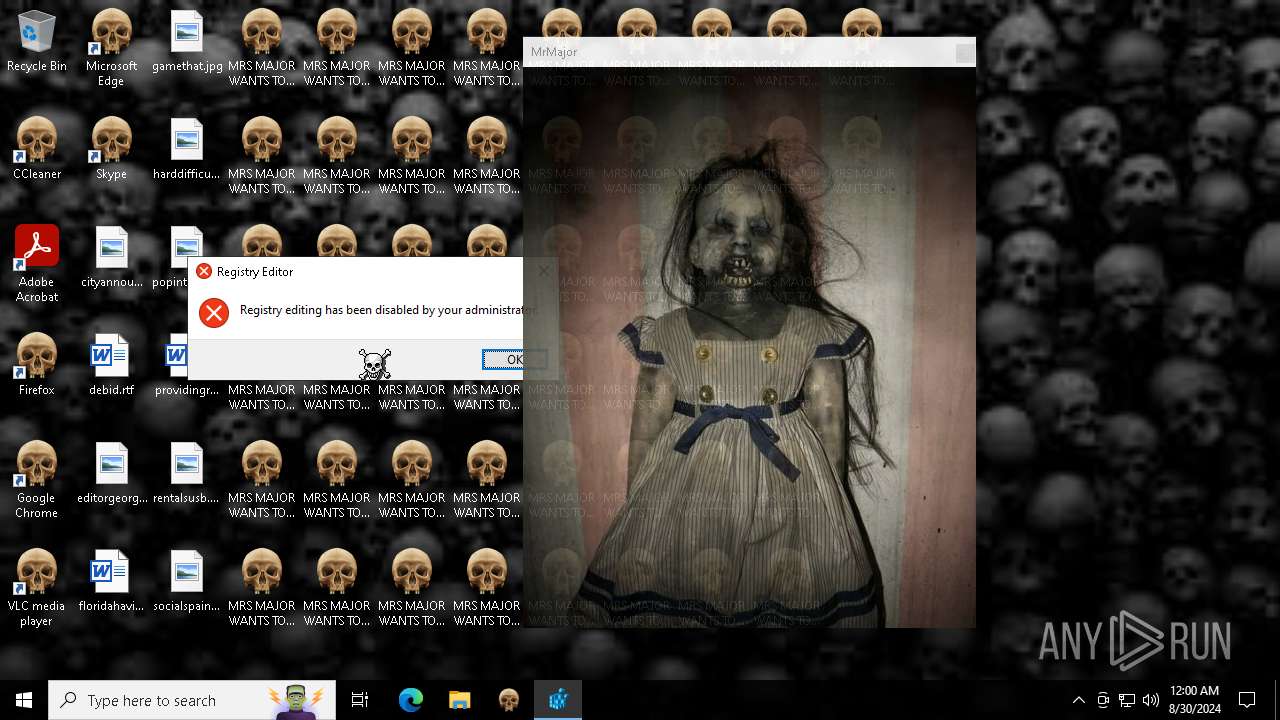
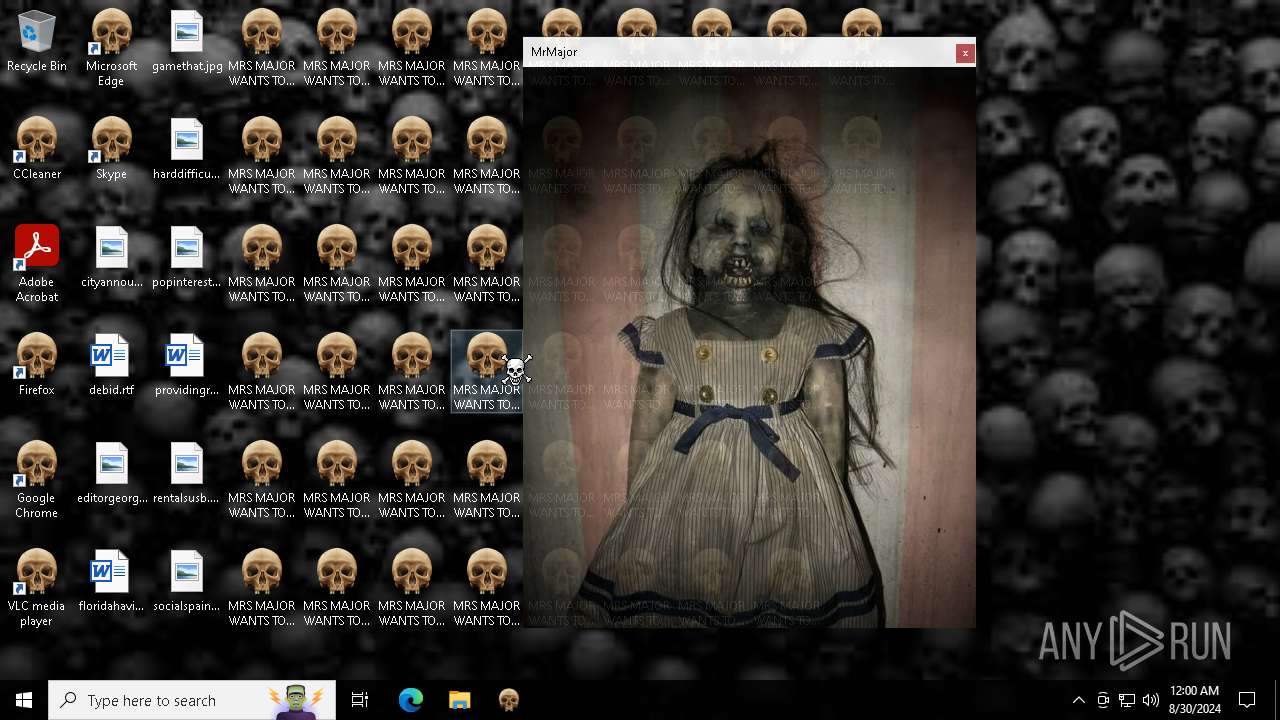
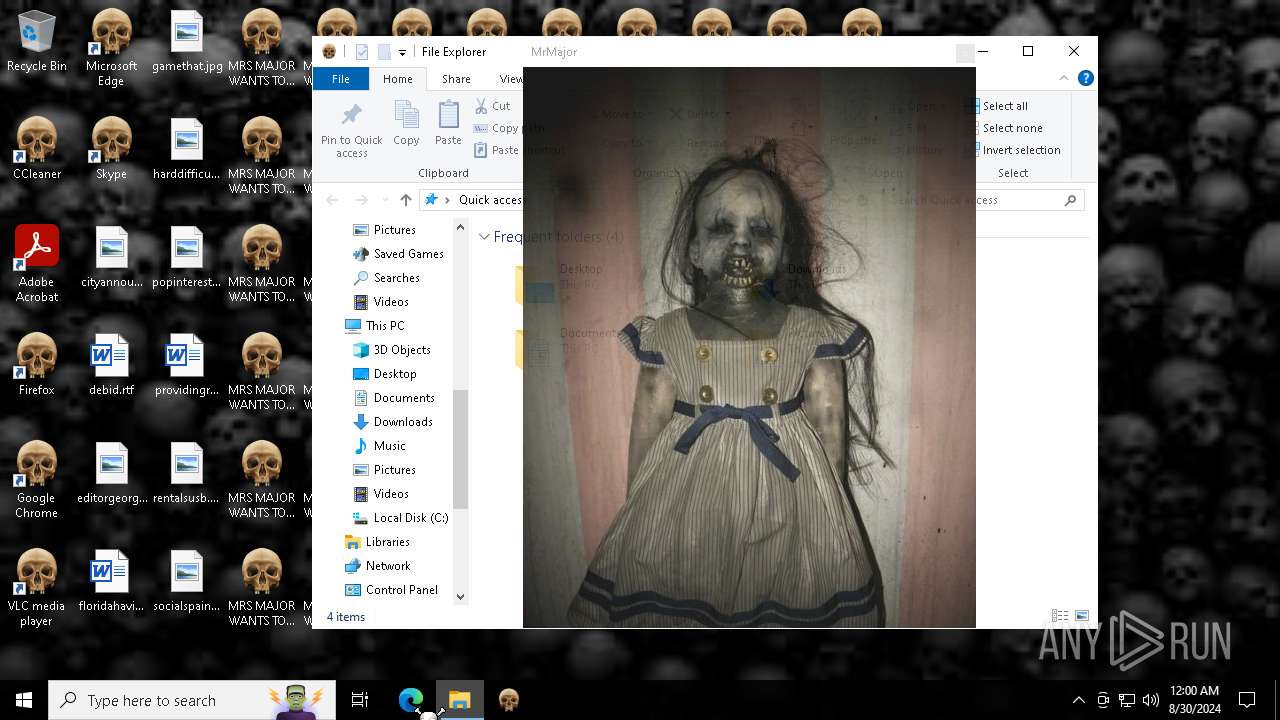
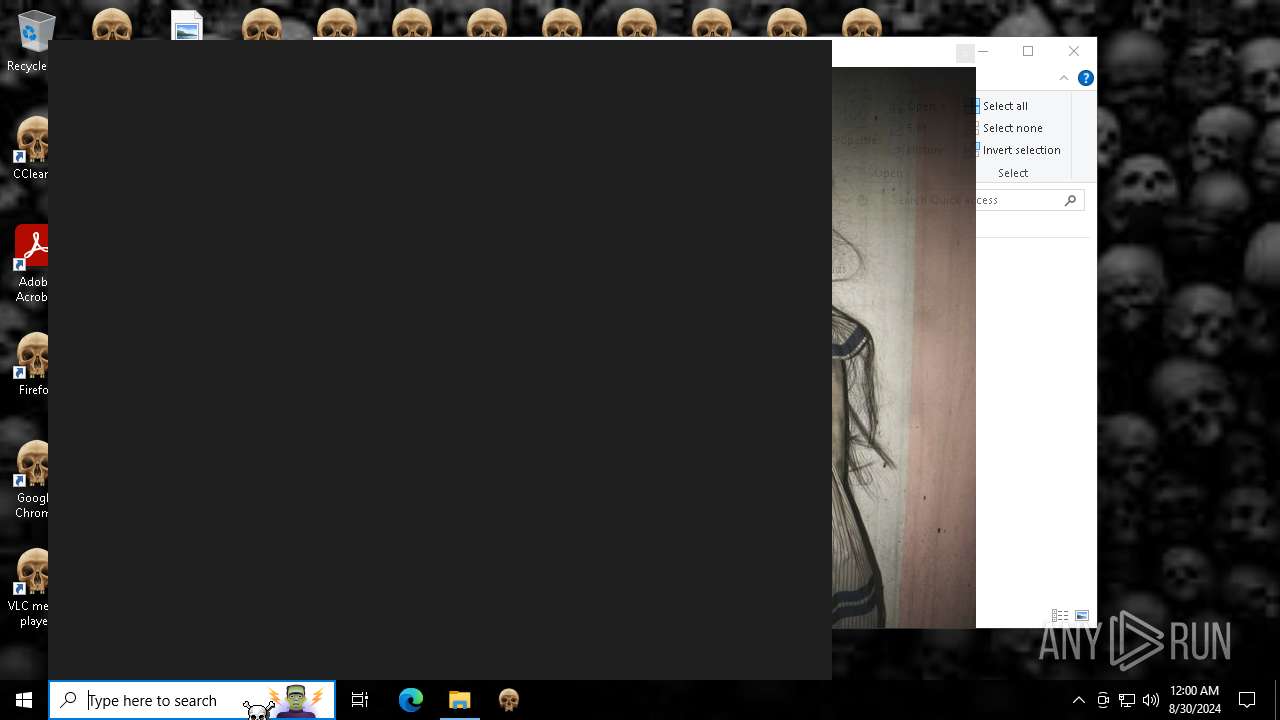
| Verdict: | Malicious activity |
| Analysis date: | August 29, 2024, 23:55:45 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | FADC860CA6FC88D37BB3018676F39C36 |
| SHA1: | 94A3145817F60D93B4BE62067A322575676DEB0A |
| SHA256: | 2D6712D72074159267E8BDA3693631F808DA4B0A115BB6F053E393E0449A7D0E |
| SSDEEP: | 3:N8VteA3zKZsM:2V8NKM |
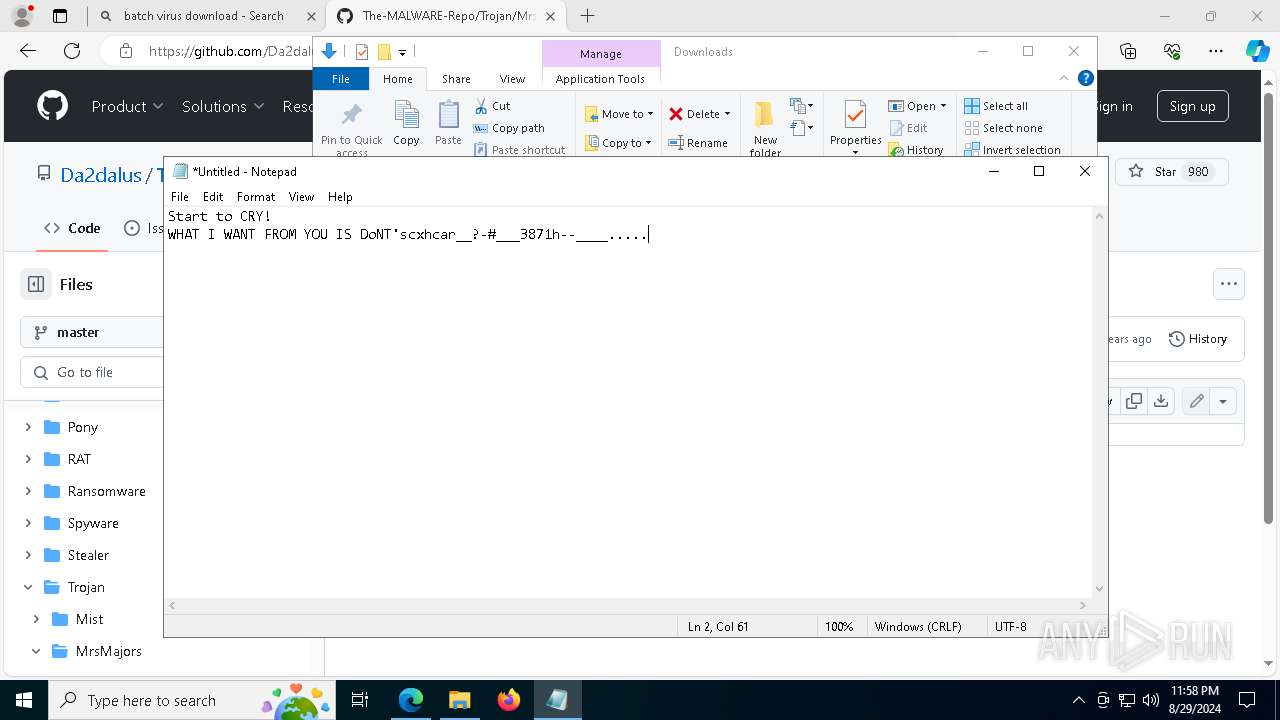
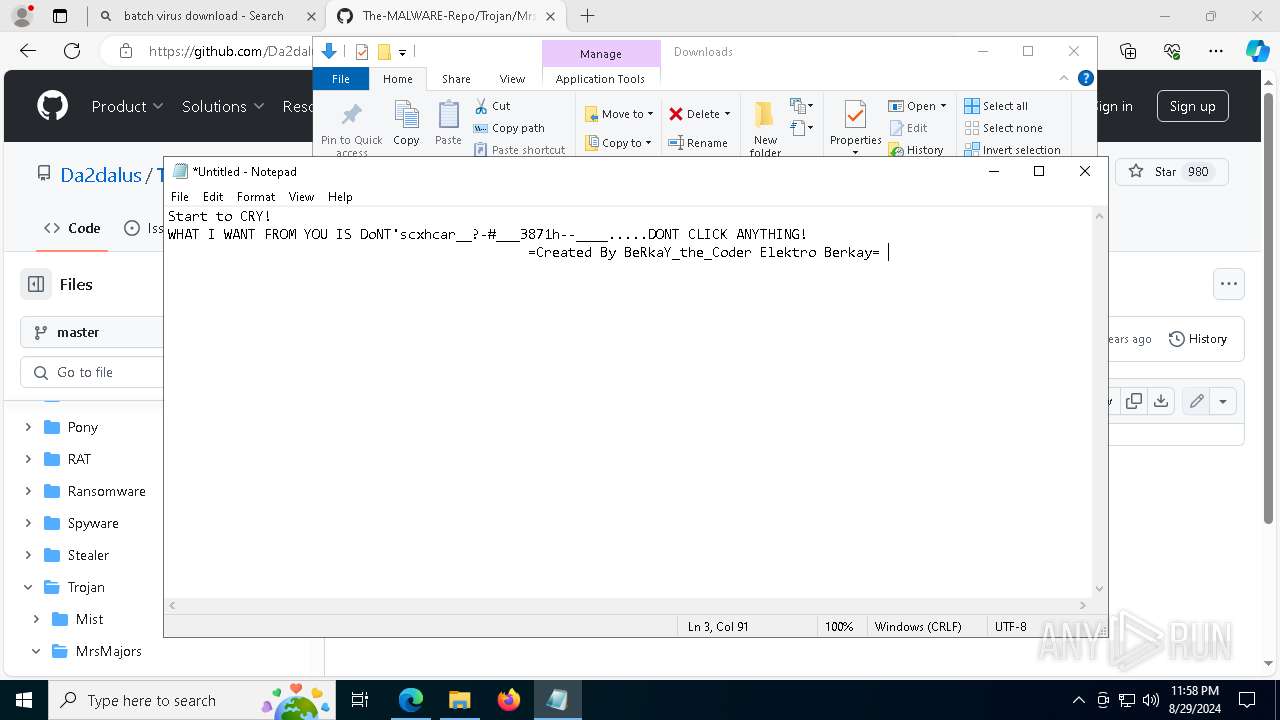
MALICIOUS
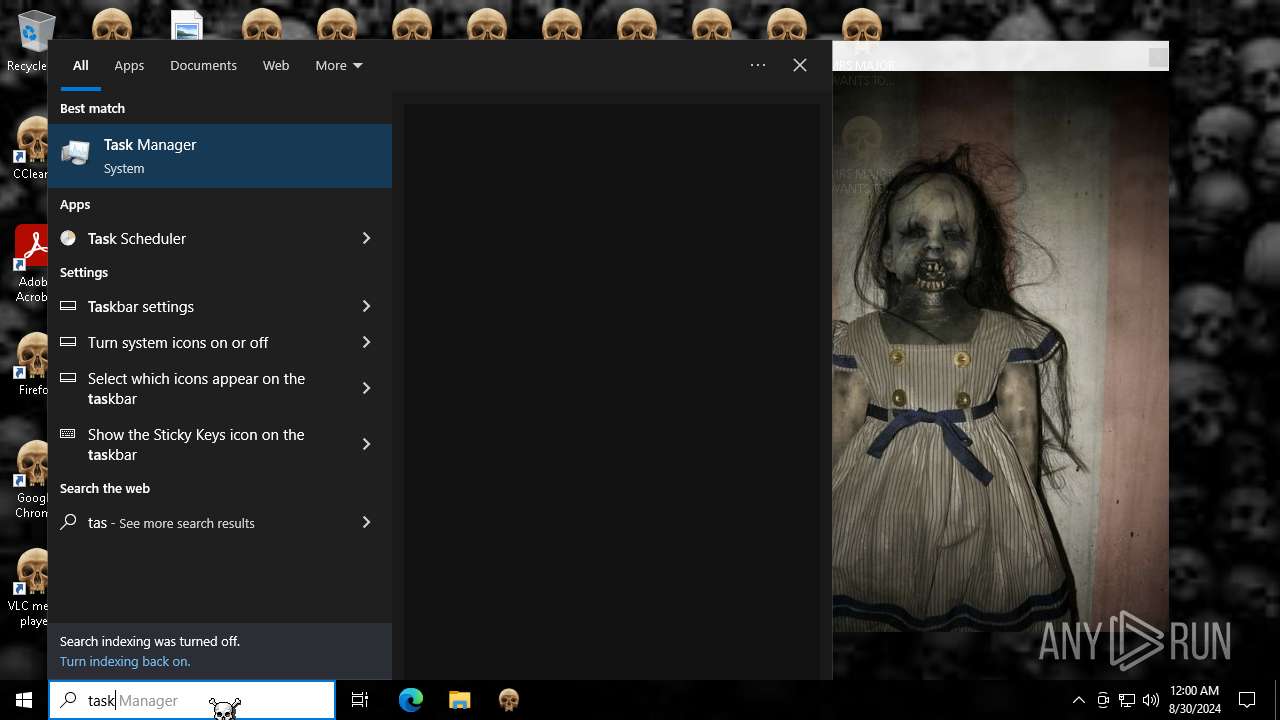
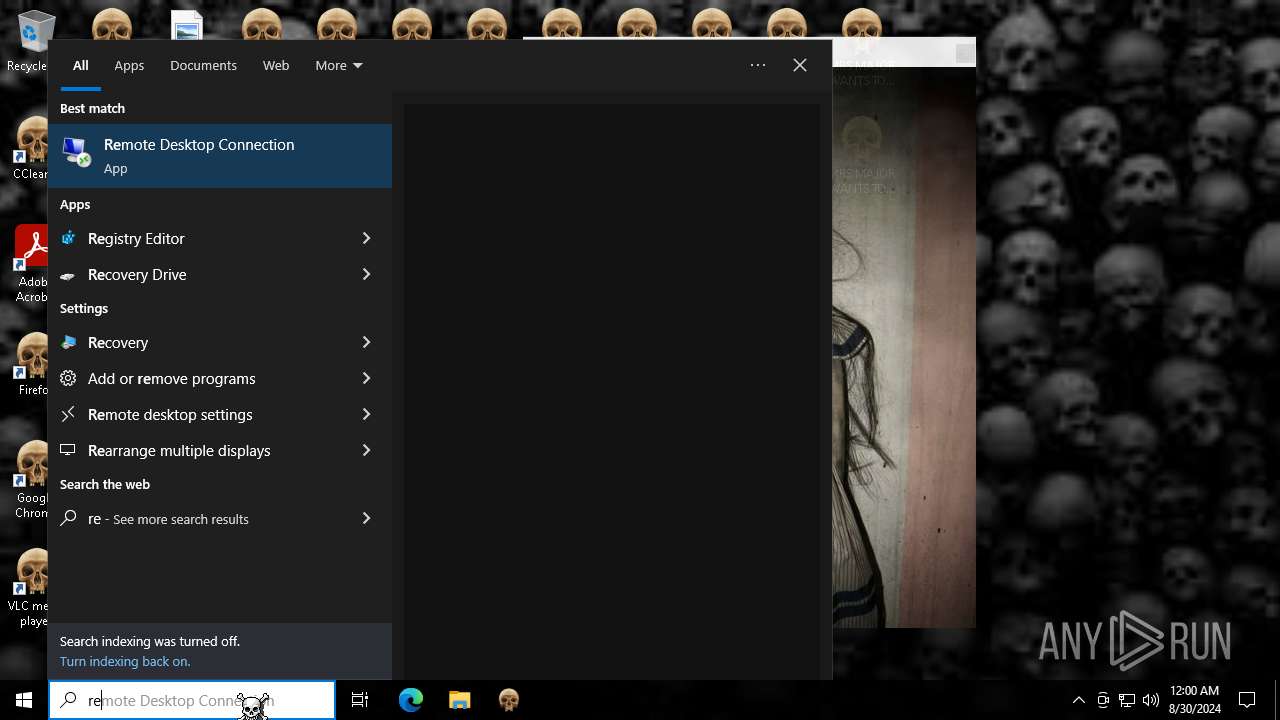
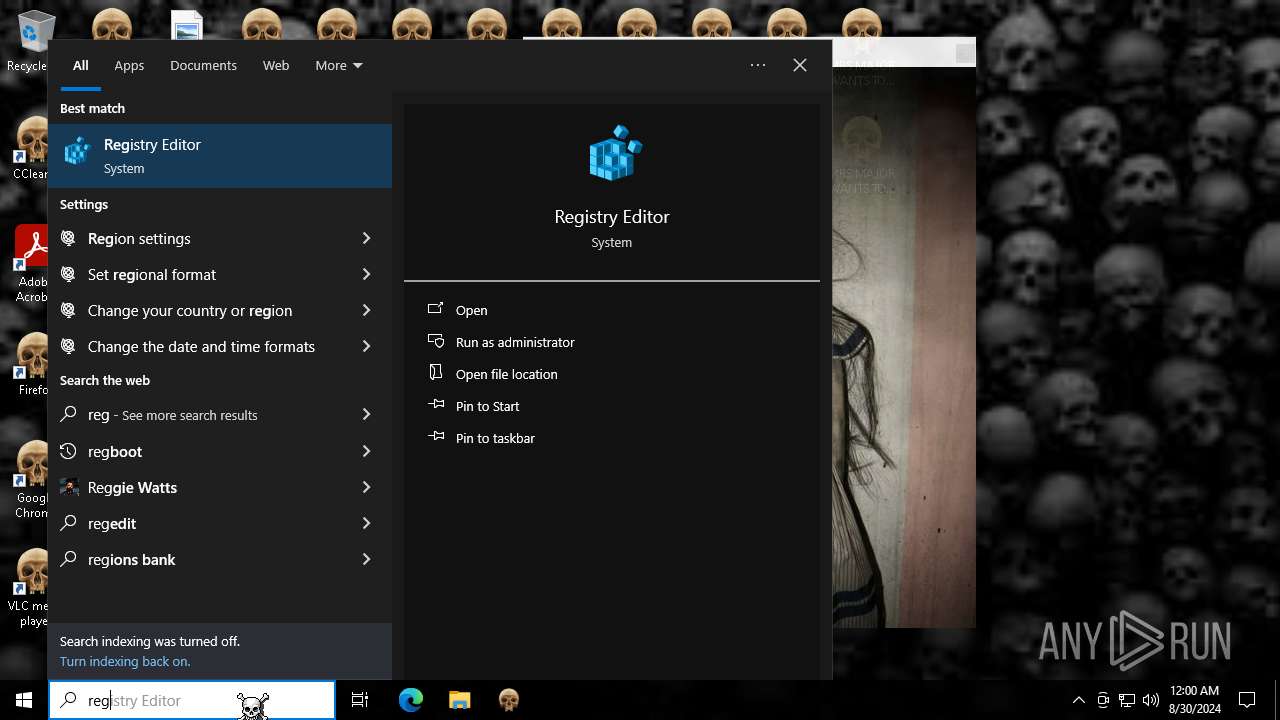
Creates a new registry key or changes the value of an existing one (SCRIPT)
- wscript.exe (PID: 6928)
- wscript.exe (PID: 6816)
- wscript.exe (PID: 6824)
Uses sleep, probably for evasion detection (SCRIPT)
- wscript.exe (PID: 6816)
- wscript.exe (PID: 6824)
Copies file to a new location (SCRIPT)
- wscript.exe (PID: 6824)
Changes the login/logoff helper path in the registry
- wscript.exe (PID: 6824)
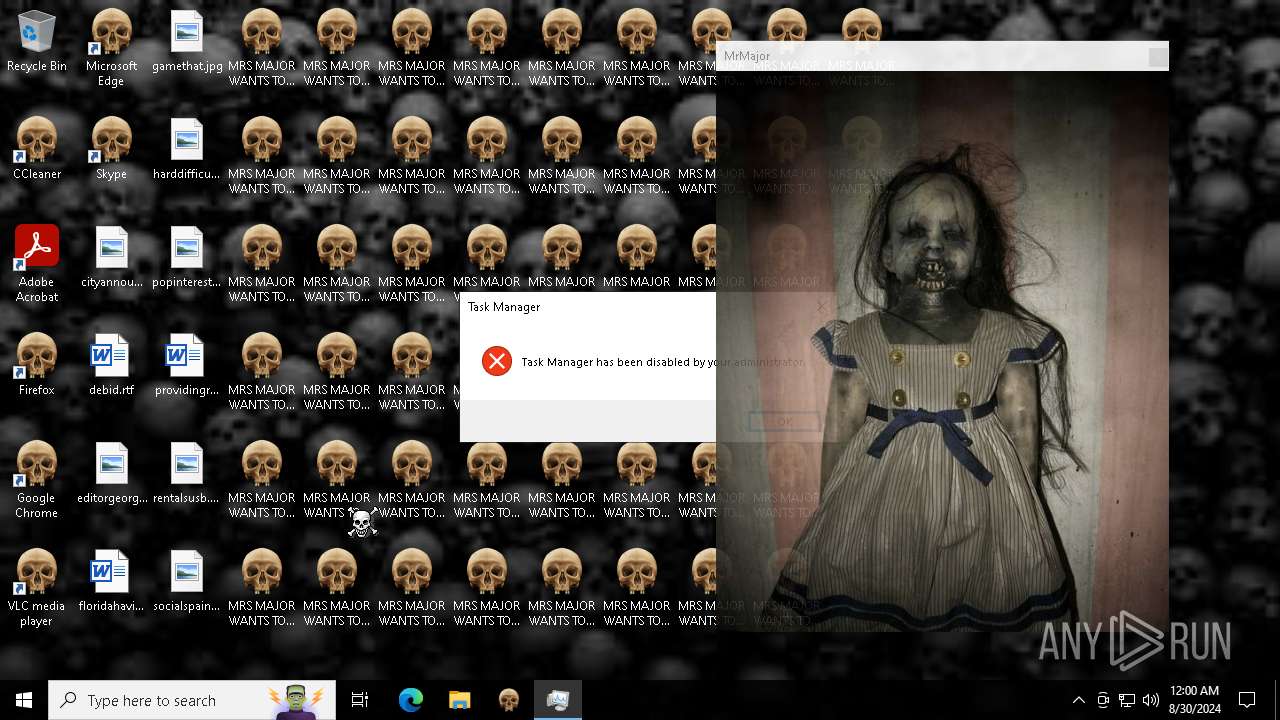
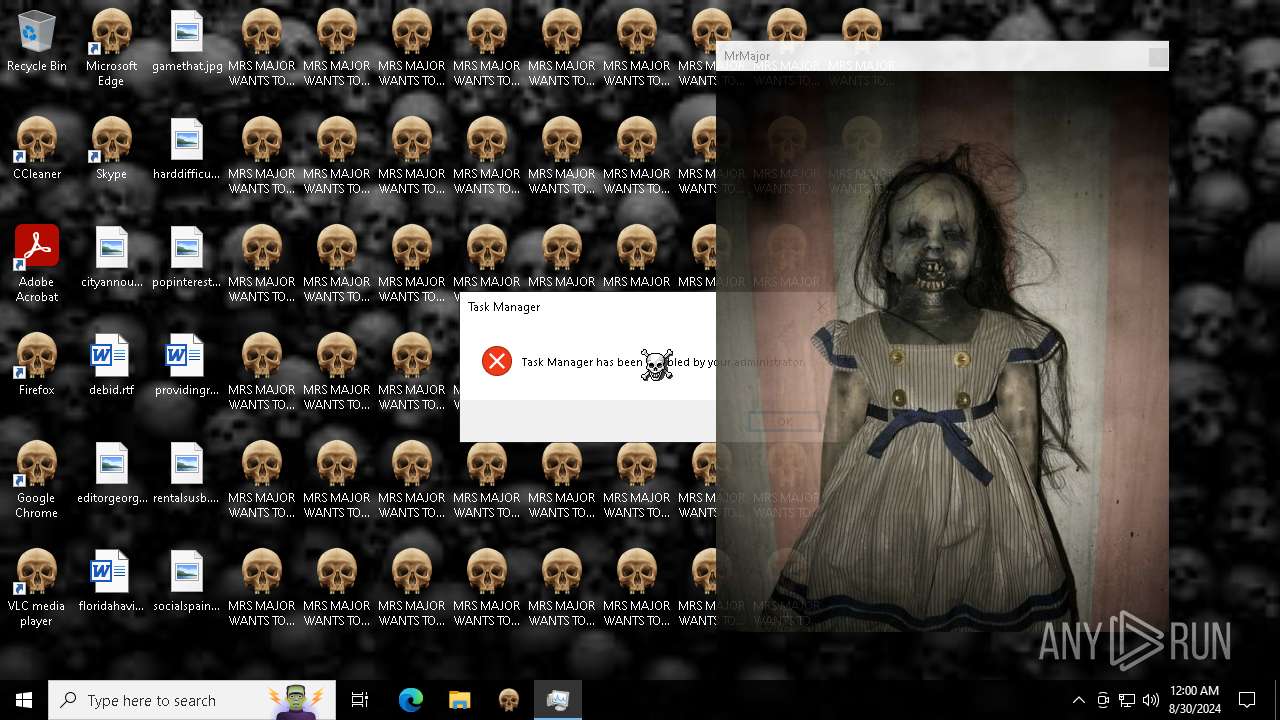
Disables Windows Defender
- wscript.exe (PID: 6824)
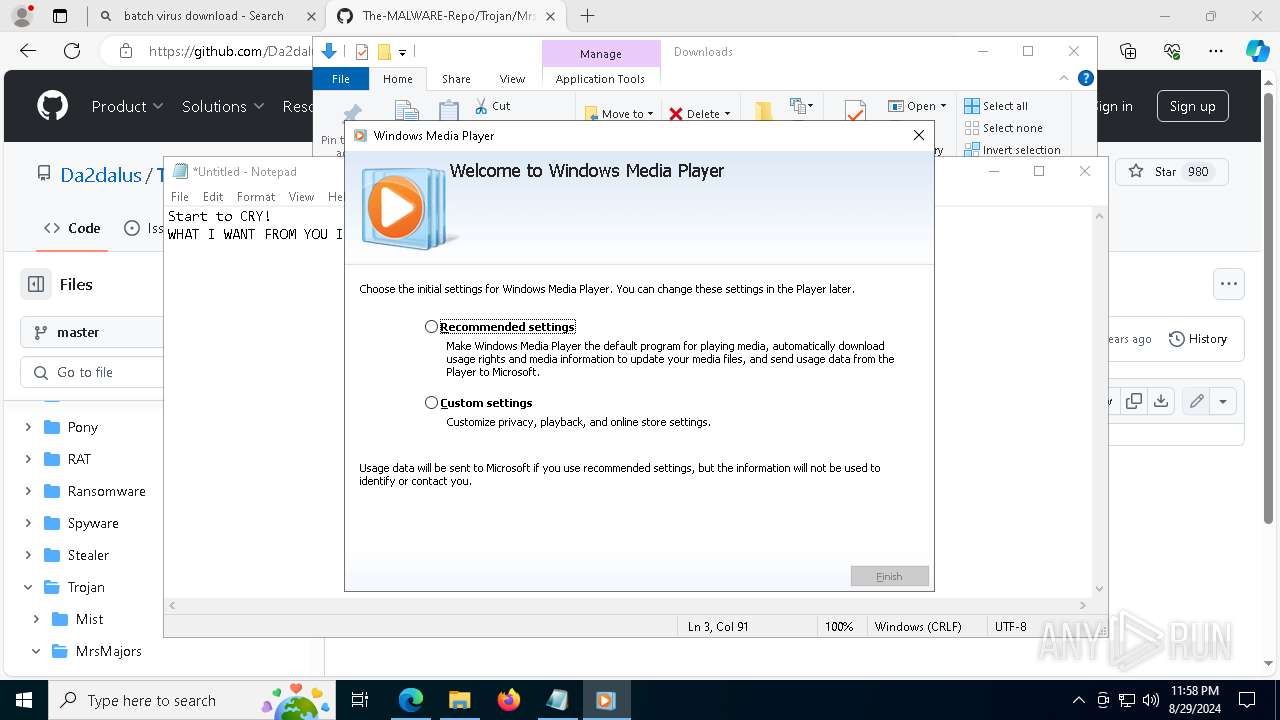
Changes the autorun value in the registry
- unregmp2.exe (PID: 3244)
Scans artifacts that could help determine the target
- wmplayer.exe (PID: 7012)
SUSPICIOUS
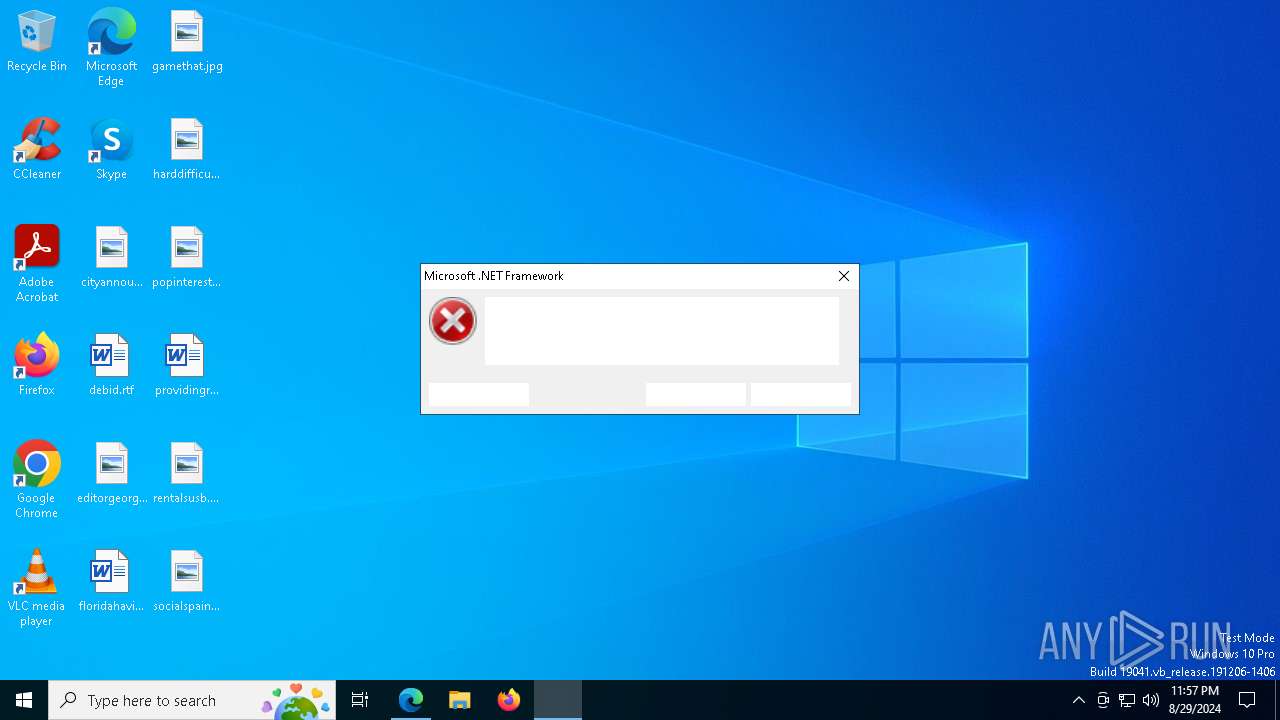
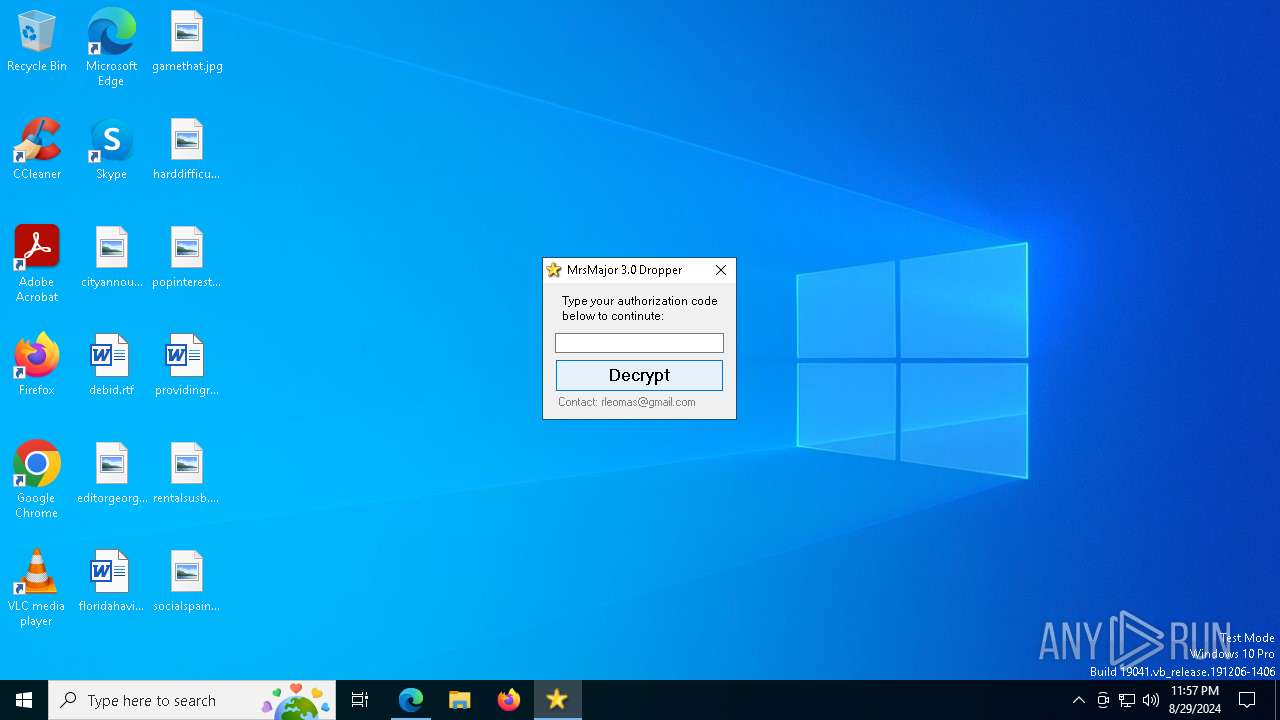
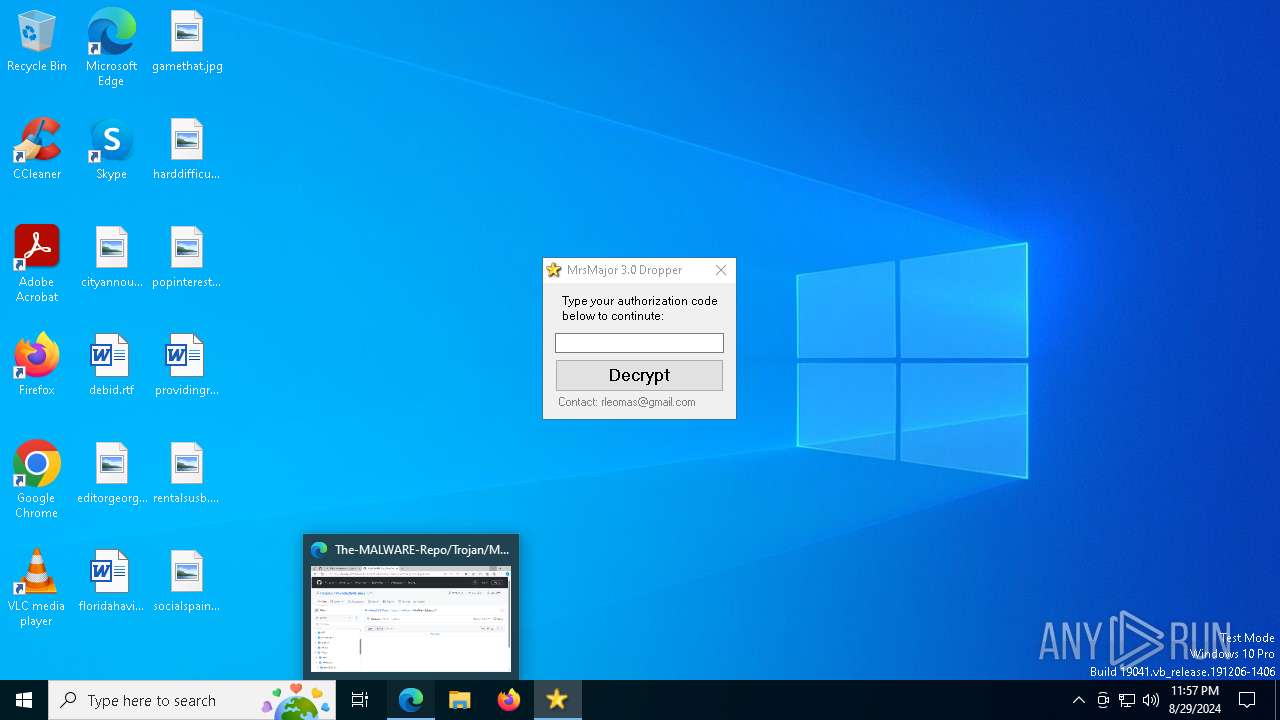
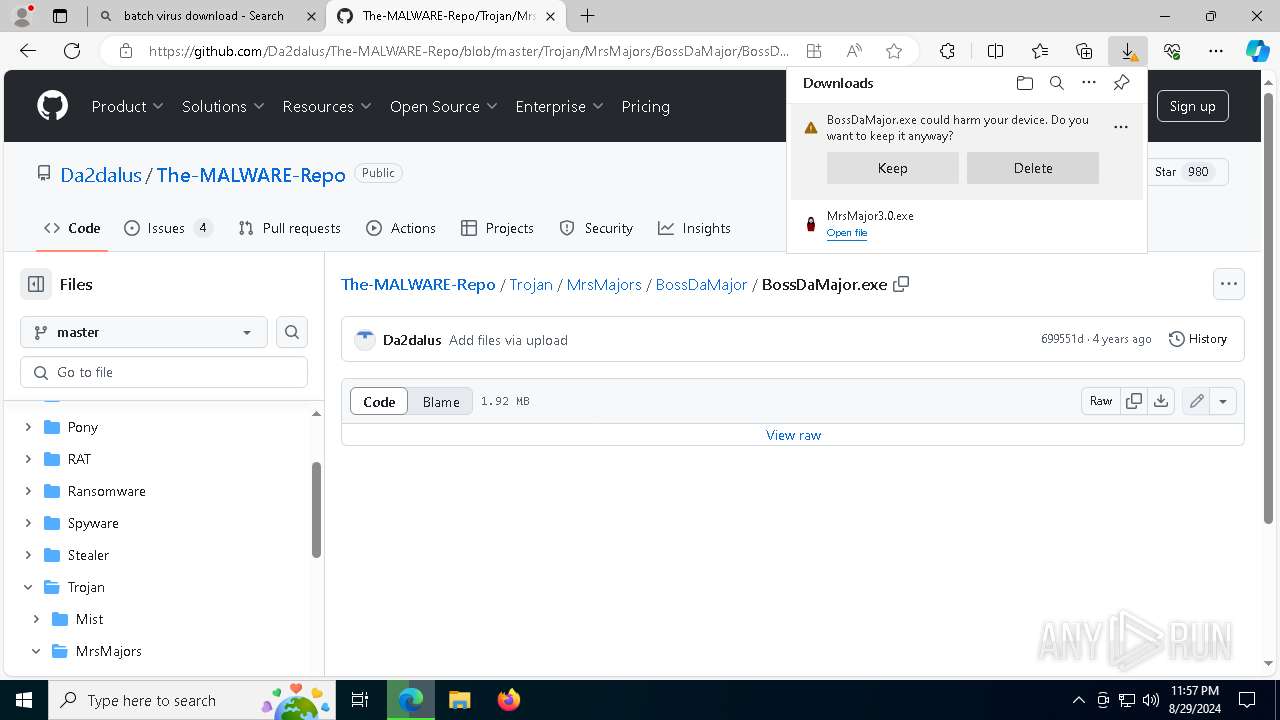
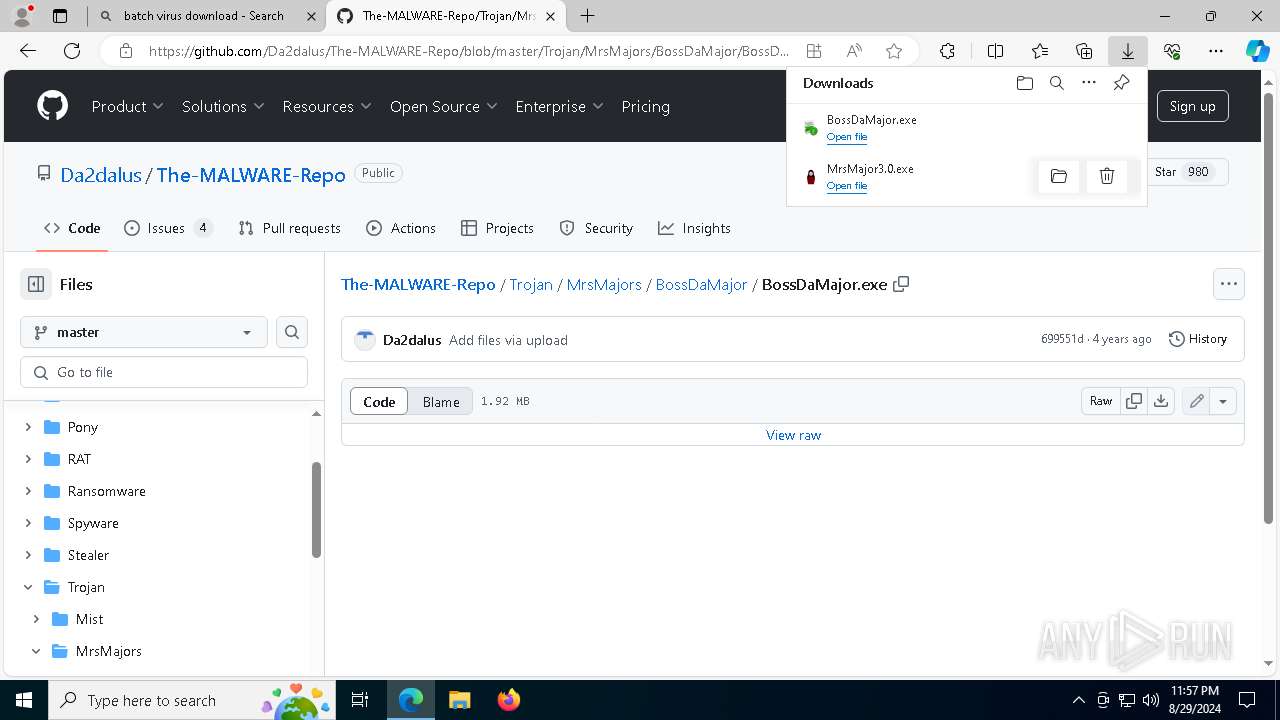
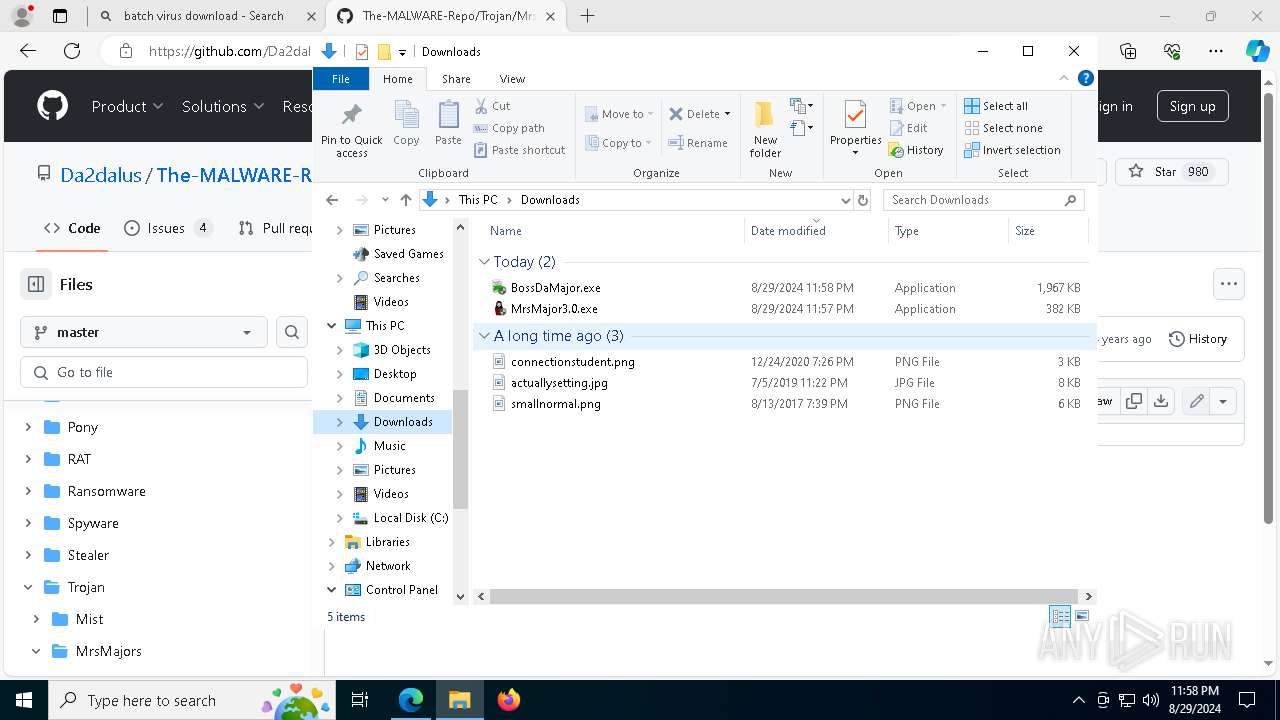
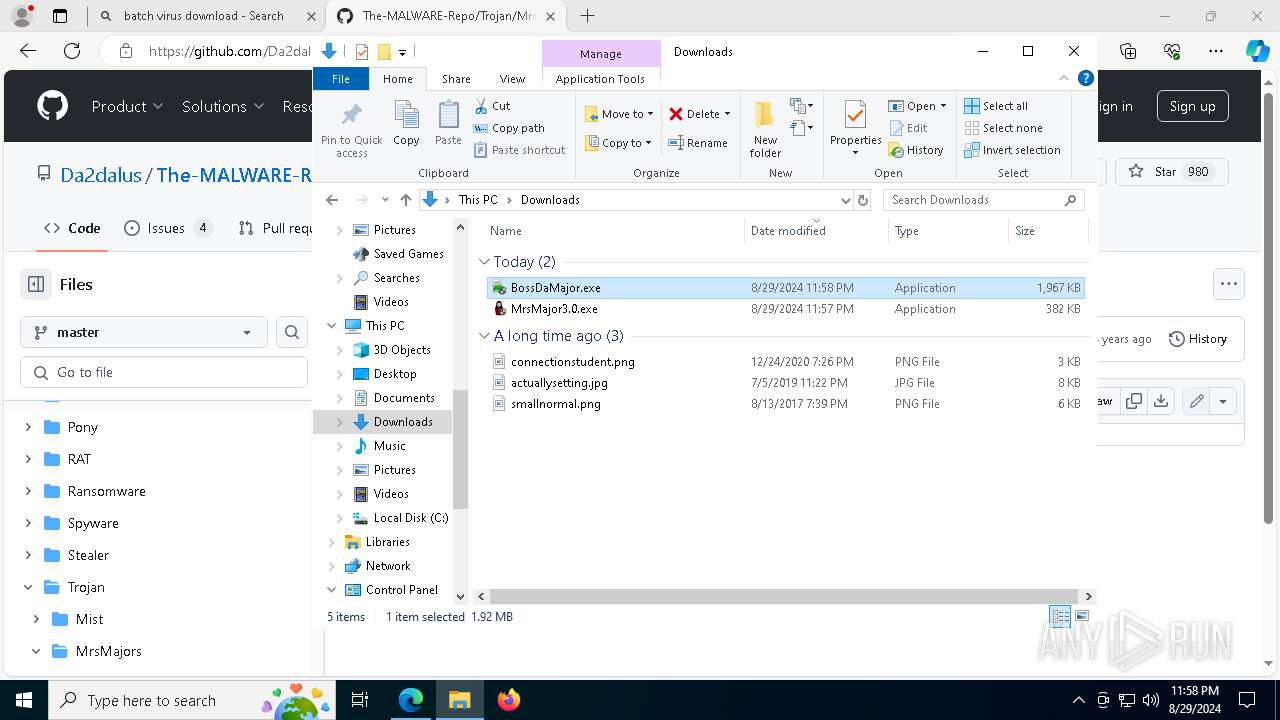
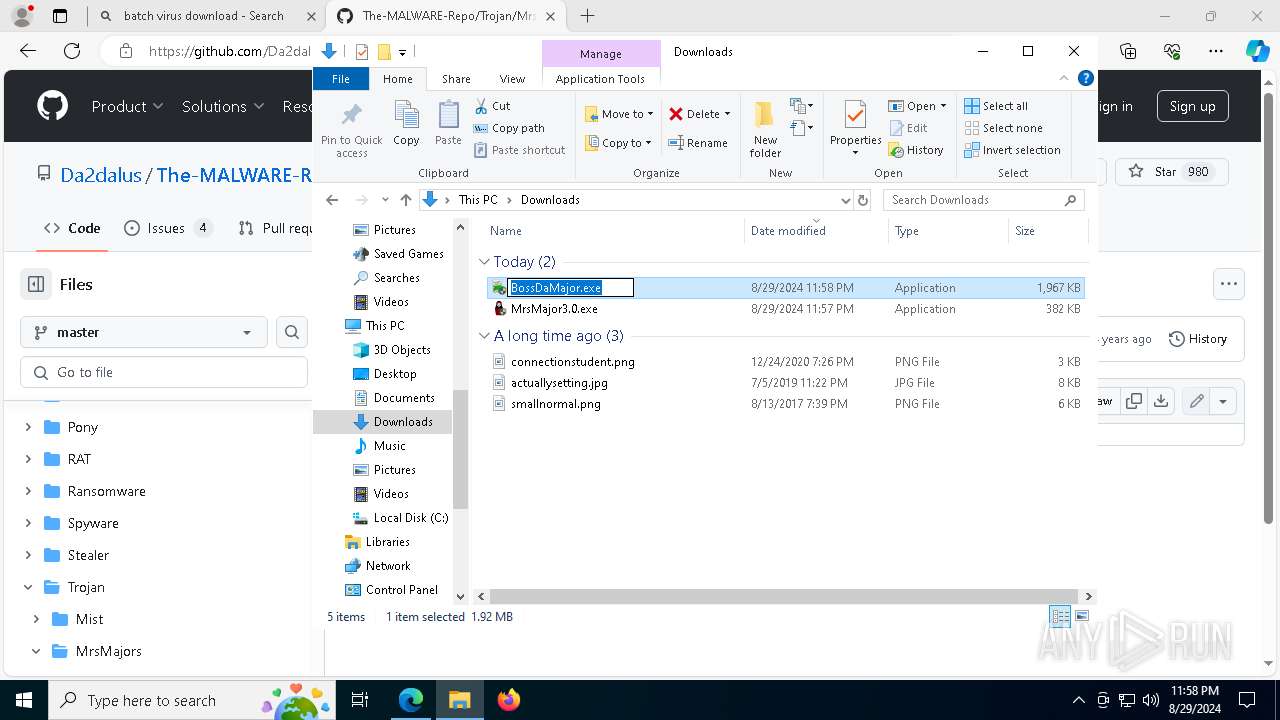
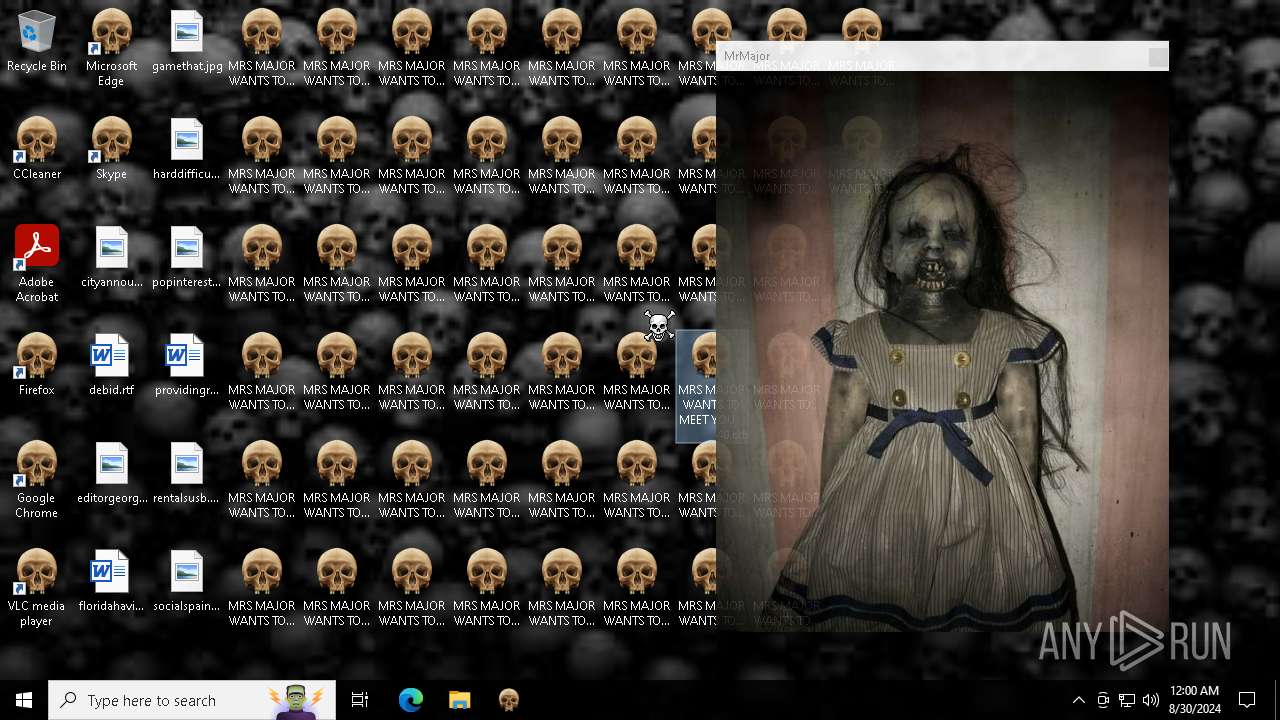
Executable content was dropped or overwritten
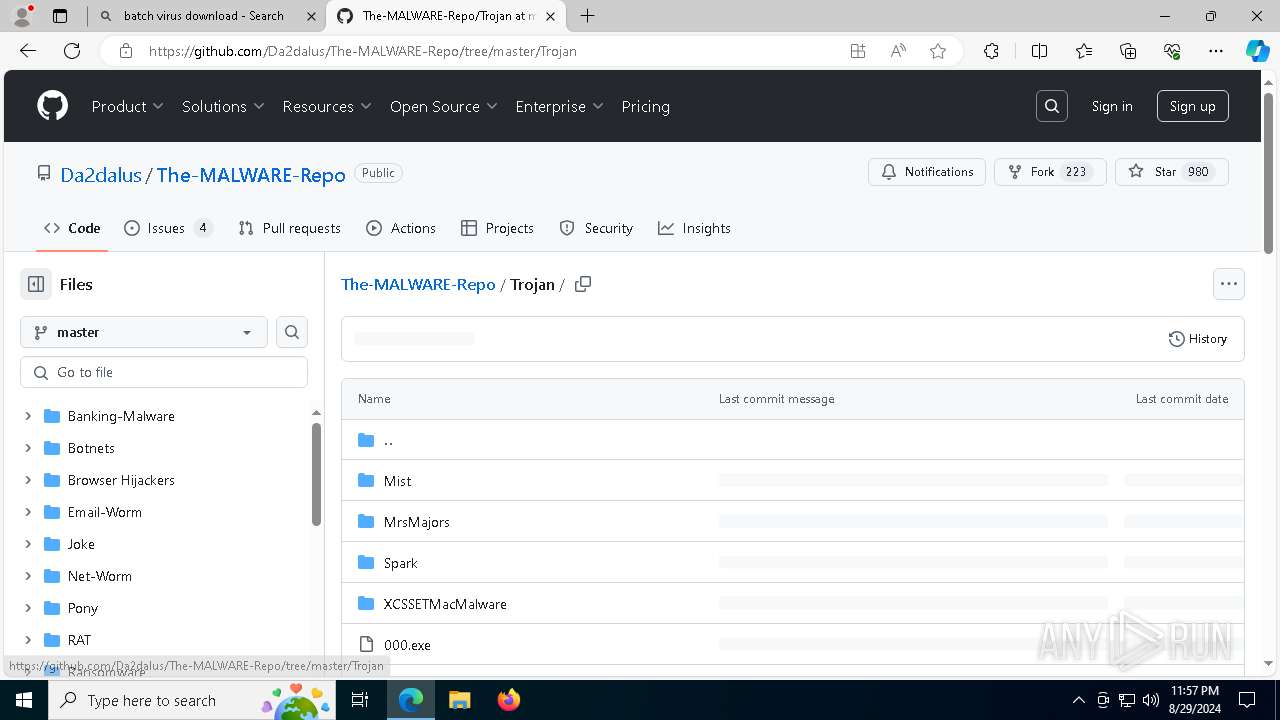
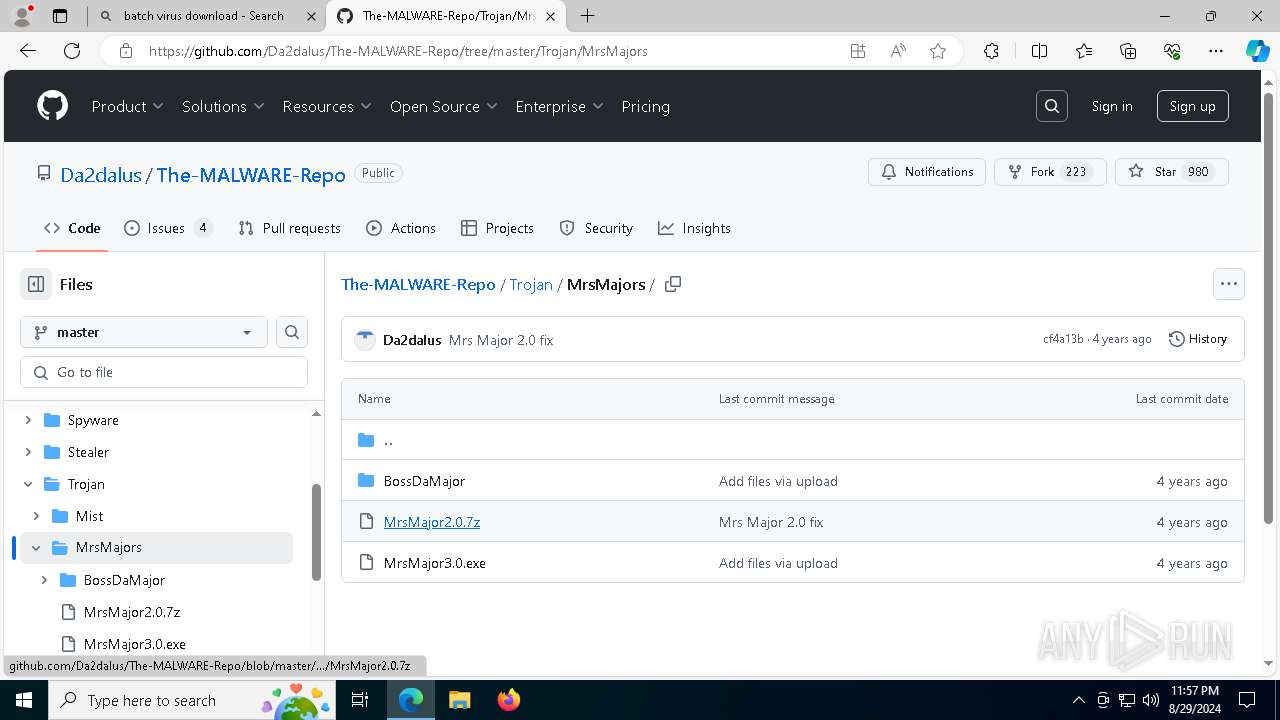
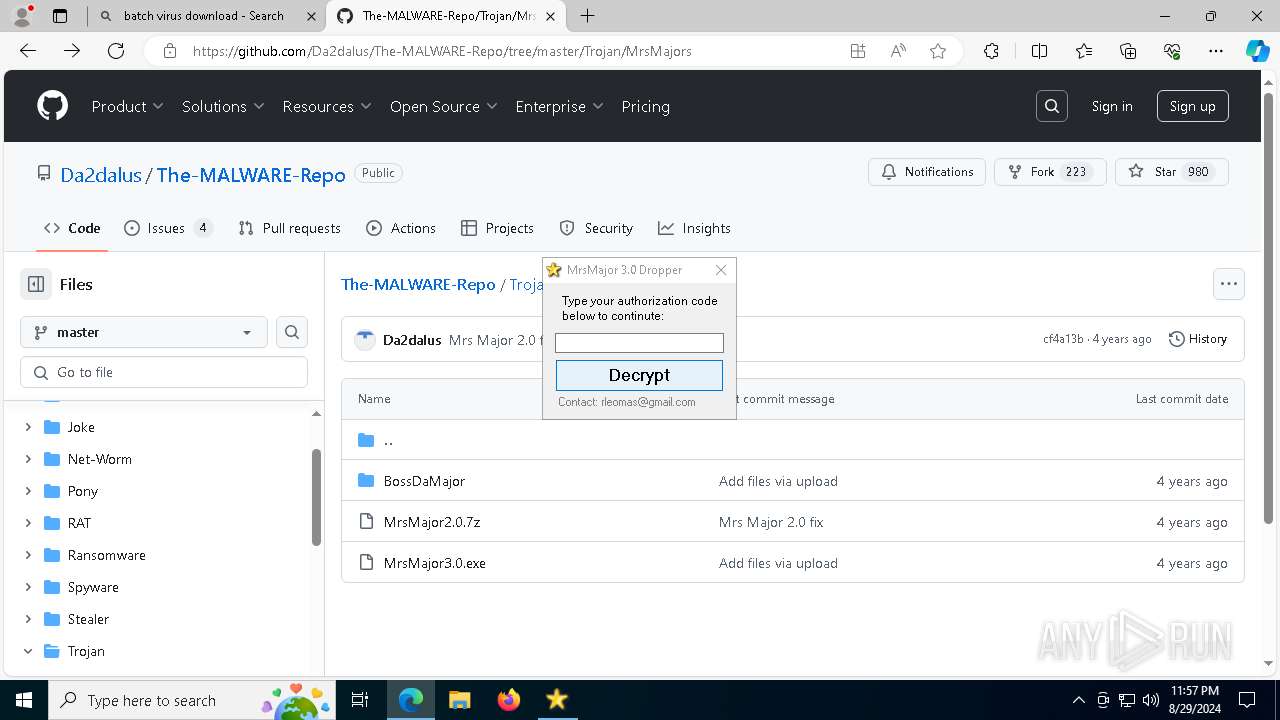
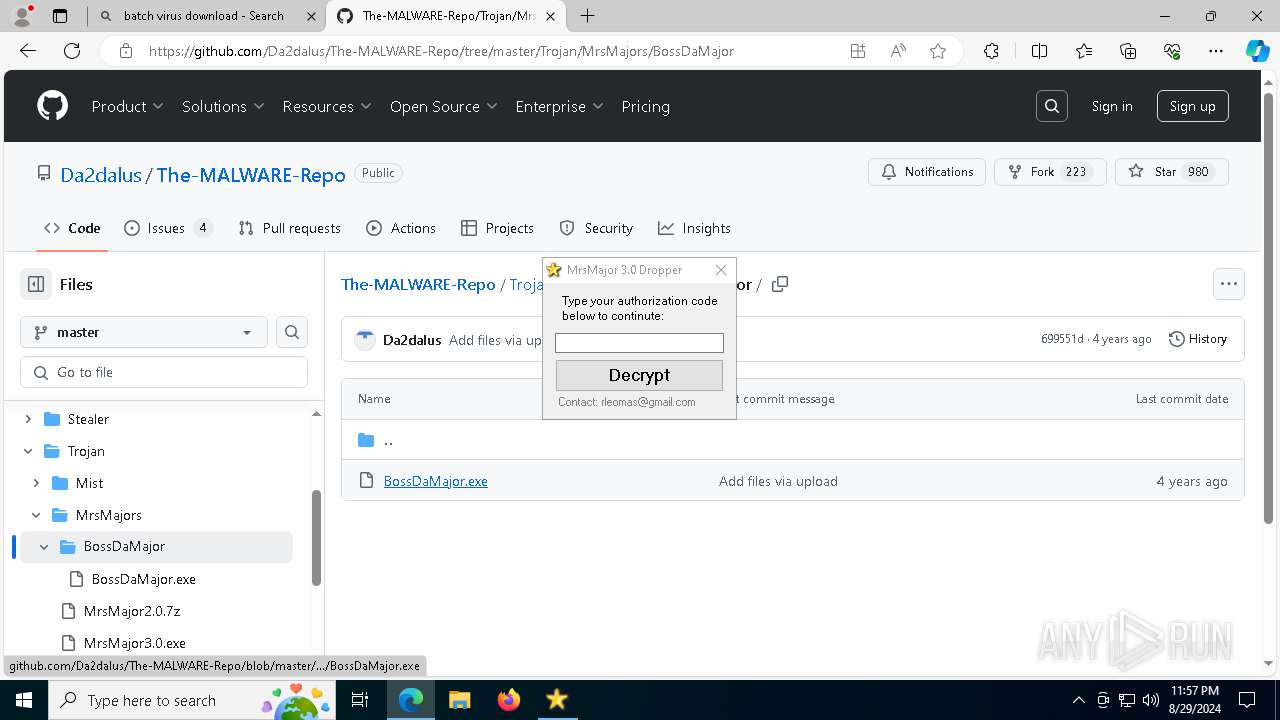
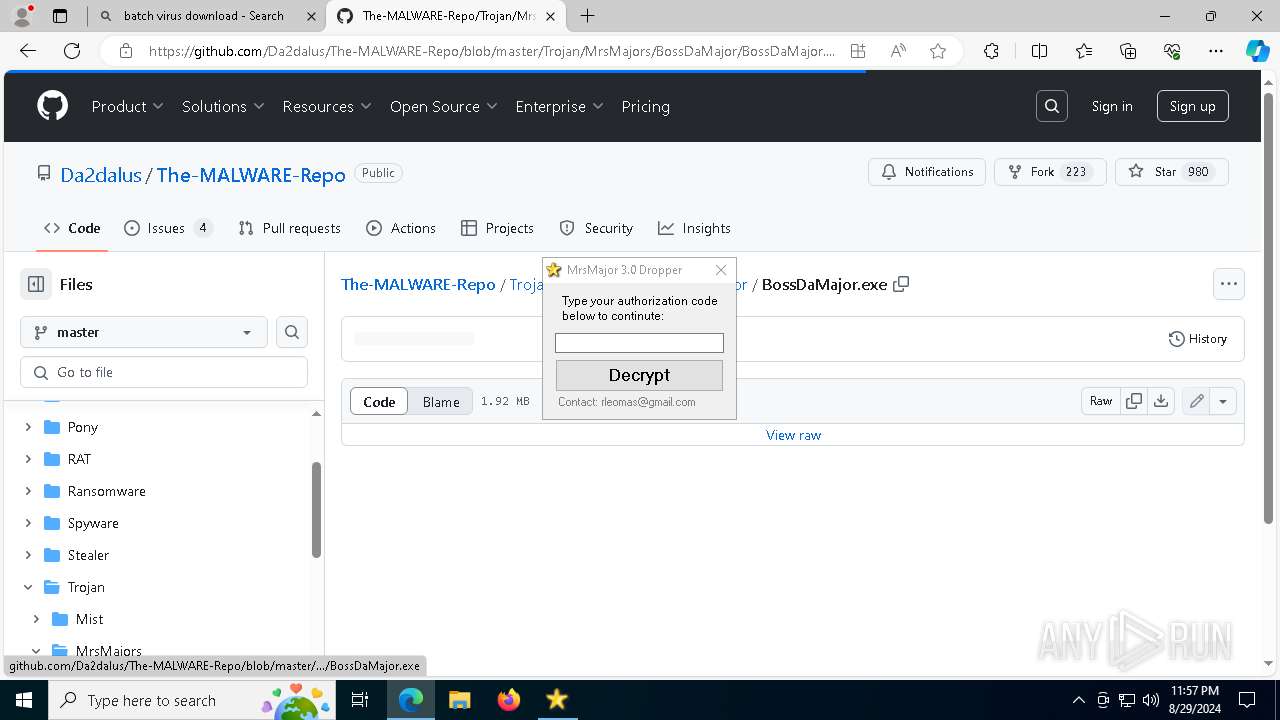
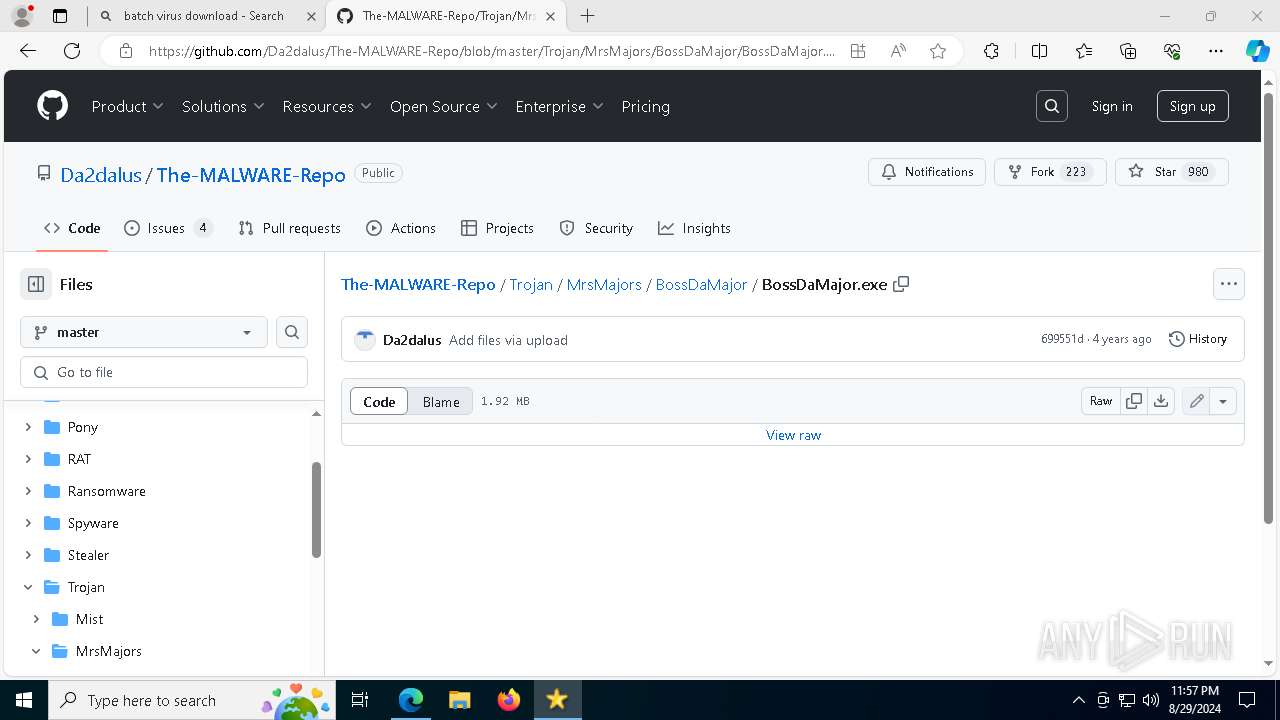
- MrsMajor3.0.exe (PID: 2040)
- eulascr.exe (PID: 3708)
- BossDaMajor.exe (PID: 2660)
- wscript.exe (PID: 6816)
Reads security settings of Internet Explorer
- MrsMajor3.0.exe (PID: 2040)
- BossDaMajor.exe (PID: 2660)
- wmplayer.exe (PID: 1744)
- setup_wm.exe (PID: 1944)
- wmplayer.exe (PID: 7012)
Drops the executable file immediately after the start
- MrsMajor3.0.exe (PID: 2040)
- BossDaMajor.exe (PID: 2660)
- eulascr.exe (PID: 3708)
Reads the date of Windows installation
- MrsMajor3.0.exe (PID: 2040)
- BossDaMajor.exe (PID: 2660)
- wmplayer.exe (PID: 1744)
- setup_wm.exe (PID: 1944)
The process executes VB scripts
- MrsMajor3.0.exe (PID: 2040)
- BossDaMajor.exe (PID: 2660)
- wscript.exe (PID: 6816)
Runs WScript without displaying logo
- wscript.exe (PID: 6928)
Runs shell command (SCRIPT)
- wscript.exe (PID: 6928)
- wscript.exe (PID: 6816)
- wscript.exe (PID: 6824)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 6816)
- wscript.exe (PID: 6824)
Application launched itself
- wscript.exe (PID: 6816)
Writes binary data to a Stream object (SCRIPT)
- wscript.exe (PID: 6824)
Write to the desktop.ini file (may be used to cloak folders)
- unregmp2.exe (PID: 3244)
Changes default file association
- unregmp2.exe (PID: 3244)
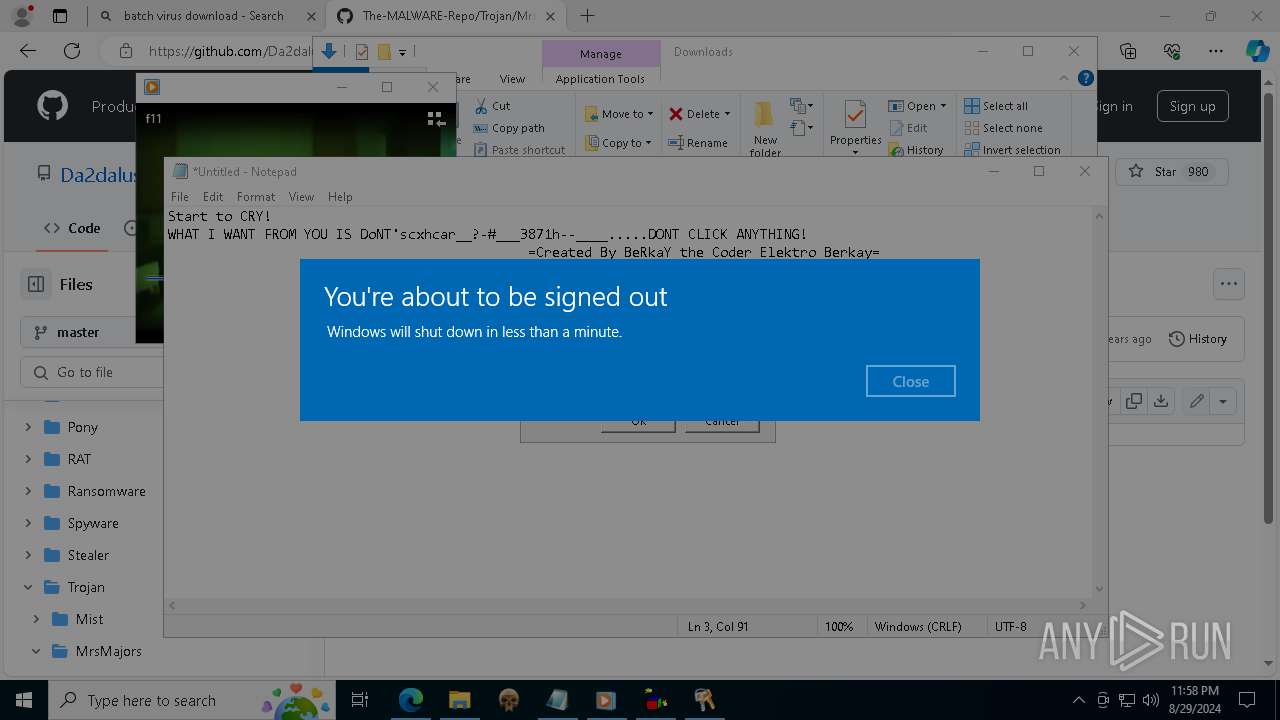
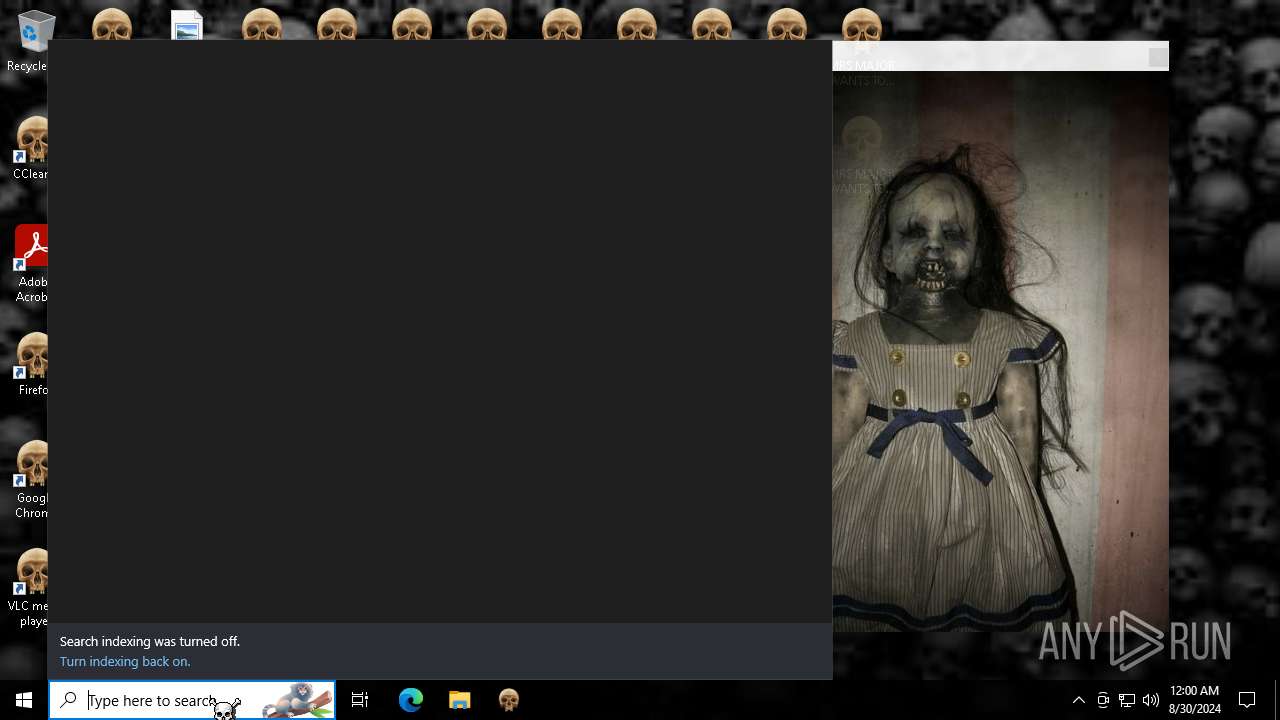
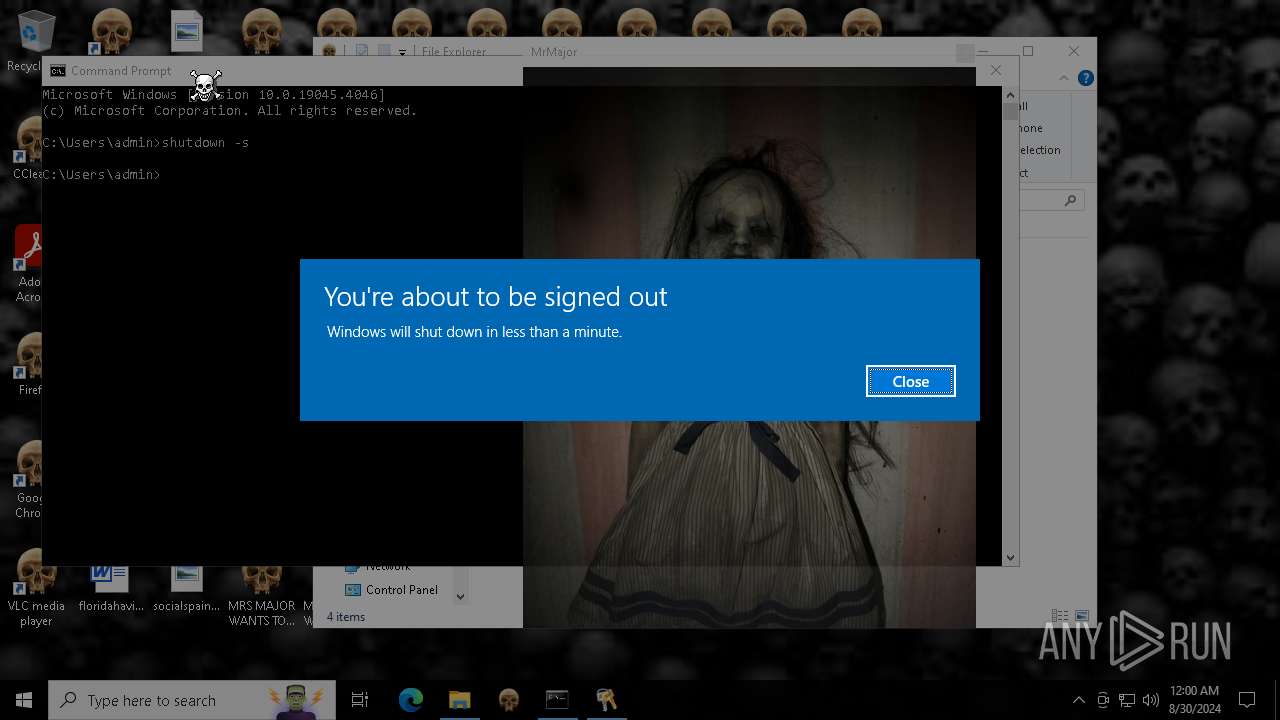
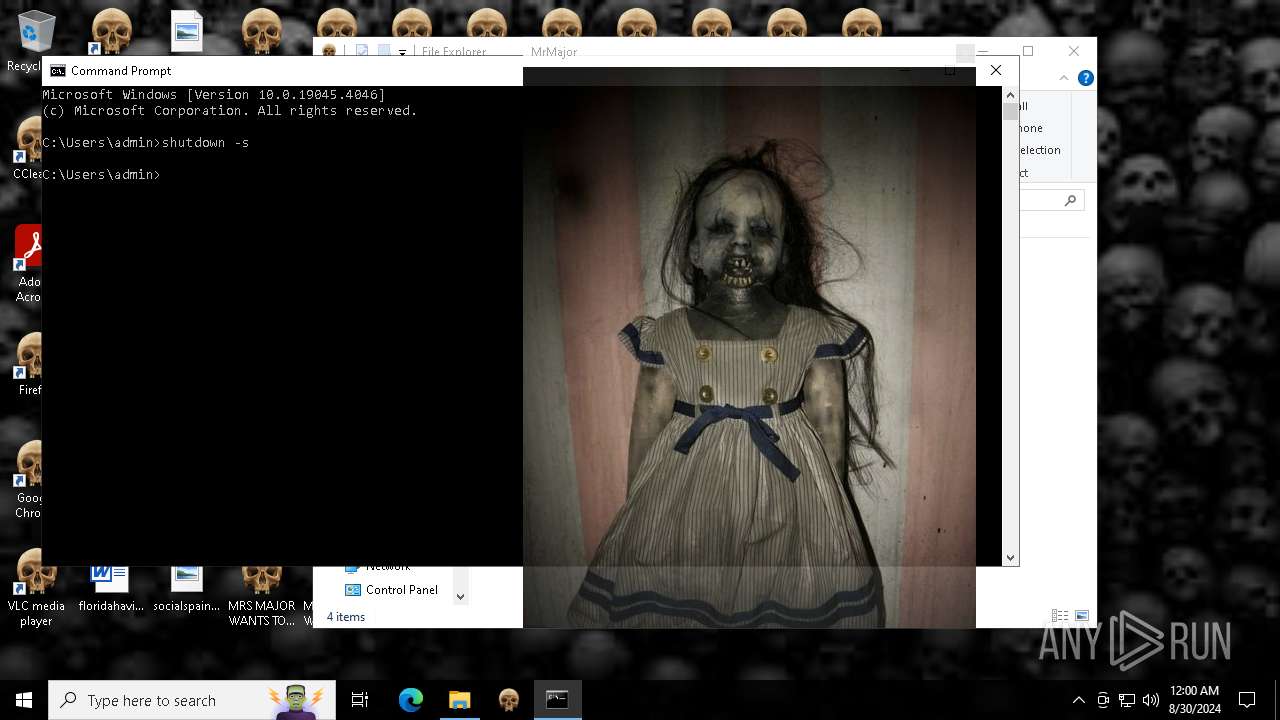
The system shut down or reboot
- wscript.exe (PID: 6824)
- cmd.exe (PID: 4072)
Detected use of alternative data streams (AltDS)
- wmplayer.exe (PID: 7012)
The process executes via Task Scheduler
- PLUGScheduler.exe (PID: 4136)
INFO
Reads the software policy settings
- slui.exe (PID: 876)
- slui.exe (PID: 5540)
- wmplayer.exe (PID: 7012)
Checks supported languages
- identity_helper.exe (PID: 4076)
- MrsMajor3.0.exe (PID: 2040)
- eulascr.exe (PID: 3708)
- BossDaMajor.exe (PID: 2660)
- wmplayer.exe (PID: 1744)
- setup_wm.exe (PID: 1944)
- wmplayer.exe (PID: 7012)
- PLUGScheduler.exe (PID: 4136)
Application launched itself
- msedge.exe (PID: 7132)
- firefox.exe (PID: 5844)
Reads the computer name
- identity_helper.exe (PID: 4076)
- MrsMajor3.0.exe (PID: 2040)
- eulascr.exe (PID: 3708)
- BossDaMajor.exe (PID: 2660)
- wmplayer.exe (PID: 1744)
- setup_wm.exe (PID: 1944)
- wmplayer.exe (PID: 7012)
- PLUGScheduler.exe (PID: 4136)
Executable content was dropped or overwritten
- msedge.exe (PID: 5532)
- msedge.exe (PID: 7132)
The process uses the downloaded file
- msedge.exe (PID: 6356)
- MrsMajor3.0.exe (PID: 2040)
- wscript.exe (PID: 6928)
- msedge.exe (PID: 7020)
- msedge.exe (PID: 7132)
- BossDaMajor.exe (PID: 2660)
- wscript.exe (PID: 6816)
- wmplayer.exe (PID: 1744)
- unregmp2.exe (PID: 6956)
- unregmp2.exe (PID: 368)
- setup_wm.exe (PID: 1944)
- wscript.exe (PID: 6824)
Create files in a temporary directory
- MrsMajor3.0.exe (PID: 2040)
- eulascr.exe (PID: 3708)
- BossDaMajor.exe (PID: 2660)
- unregmp2.exe (PID: 6956)
- setup_wm.exe (PID: 1944)
Process checks computer location settings
- MrsMajor3.0.exe (PID: 2040)
- BossDaMajor.exe (PID: 2660)
- wmplayer.exe (PID: 1744)
- setup_wm.exe (PID: 1944)
- wmplayer.exe (PID: 7012)
Reads Environment values
- identity_helper.exe (PID: 4076)
- setup_wm.exe (PID: 1944)
- wmplayer.exe (PID: 7012)
Reads Microsoft Office registry keys
- msedge.exe (PID: 7132)
Checks proxy server information
- slui.exe (PID: 5540)
- setup_wm.exe (PID: 1944)
- wmplayer.exe (PID: 7012)
Manual execution by a user
- BossDaMajor.exe (PID: 2660)
- BossDaMajor.exe (PID: 3244)
- regedit.exe (PID: 6700)
- Taskmgr.exe (PID: 6856)
- regedit.exe (PID: 4144)
- Taskmgr.exe (PID: 6644)
- notepad.exe (PID: 6744)
- firefox.exe (PID: 5844)
- taskkill.exe (PID: 912)
- taskkill.exe (PID: 2124)
- cmd.exe (PID: 4072)
Reads the machine GUID from the registry
- eulascr.exe (PID: 3708)
- wmplayer.exe (PID: 7012)
Reads security settings of Internet Explorer
- wscript.exe (PID: 6816)
- unregmp2.exe (PID: 6956)
- unregmp2.exe (PID: 368)
- notepad.exe (PID: 6744)
Creates files in the program directory
- wscript.exe (PID: 6816)
- wscript.exe (PID: 6824)
- unregmp2.exe (PID: 5940)
- unregmp2.exe (PID: 3244)
- PLUGScheduler.exe (PID: 4136)
Creates files or folders in the user directory
- unregmp2.exe (PID: 5940)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
528
Monitored processes
104
Malicious processes
11
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 32 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6124 --field-trial-handle=2420,i,2452813311172929139,6188806571145106881,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 320 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=audio.mojom.AudioService --lang=en-US --service-sandbox-type=audio --no-appcompat-clear --mojo-platform-channel-handle=5900 --field-trial-handle=2420,i,2452813311172929139,6188806571145106881,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 368 | C:\WINDOWS\system32\unregmp2.exe /ShowWMP /SetShowState /CreateMediaLibrary | C:\Windows\SysWOW64\unregmp2.exe | — | setup_wm.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Windows Media Player Setup Utility Exit code: 0 Version: 12.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 608 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_xpay_wallet.mojom.EdgeXPayWalletService --lang=en-US --service-sandbox-type=utility --no-appcompat-clear --mojo-platform-channel-handle=3752 --field-trial-handle=2420,i,2452813311172929139,6188806571145106881,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 876 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 912 | taskkill /f /im bing.exe | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 964 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6656 --field-trial-handle=2420,i,2452813311172929139,6188806571145106881,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1020 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7260 --field-trial-handle=2420,i,2452813311172929139,6188806571145106881,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1020 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7916 --field-trial-handle=2420,i,2452813311172929139,6188806571145106881,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1076 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6964 --field-trial-handle=2420,i,2452813311172929139,6188806571145106881,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
42 515
Read events
41 922
Write events
509
Delete events
84
Modification events
| (PID) Process: | (7132) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7132) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7132) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (7132) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (7132) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7132) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\ClientState\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (7132) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7132) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge |
| Operation: | write | Name: | UsageStatsInSample |
Value: 1 | |||
| (PID) Process: | (7132) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (7132) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | urlstats |
Value: 0 | |||
Executable files
19
Suspicious files
559
Text files
235
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7132 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF129f36.TMP | — | |
MD5:— | SHA256:— | |||
| 7132 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7132 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF129f65.TMP | — | |
MD5:— | SHA256:— | |||
| 7132 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF129f65.TMP | — | |
MD5:— | SHA256:— | |||
| 7132 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7132 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7132 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF129f65.TMP | — | |
MD5:— | SHA256:— | |||
| 7132 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7132 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF129f65.TMP | — | |
MD5:— | SHA256:— | |||
| 7132 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
38
TCP/UDP connections
151
DNS requests
139
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7008 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1752 | svchost.exe | HEAD | 200 | 2.19.126.155:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4e7e4c6f-7b62-49ca-a1fd-f625399e76b3?P1=1725568016&P2=404&P3=2&P4=J5s3ZdtM3xQ%2f4QQxxj1pjpJ08l%2f6OJ4kTx5ZkzIZrPw8E%2fwJLb2Uv4%2fuuhKqoREV9KKdKMQ57vnIULcUark5Ng%3d%3d | unknown | — | — | whitelisted |
2036 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1752 | svchost.exe | GET | 206 | 2.19.126.155:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4e7e4c6f-7b62-49ca-a1fd-f625399e76b3?P1=1725568016&P2=404&P3=2&P4=J5s3ZdtM3xQ%2f4QQxxj1pjpJ08l%2f6OJ4kTx5ZkzIZrPw8E%2fwJLb2Uv4%2fuuhKqoREV9KKdKMQ57vnIULcUark5Ng%3d%3d | unknown | — | — | whitelisted |
1752 | svchost.exe | GET | 206 | 2.19.126.155:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4e7e4c6f-7b62-49ca-a1fd-f625399e76b3?P1=1725568016&P2=404&P3=2&P4=J5s3ZdtM3xQ%2f4QQxxj1pjpJ08l%2f6OJ4kTx5ZkzIZrPw8E%2fwJLb2Uv4%2fuuhKqoREV9KKdKMQ57vnIULcUark5Ng%3d%3d | unknown | — | — | whitelisted |
1752 | svchost.exe | GET | 206 | 2.19.126.155:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4e7e4c6f-7b62-49ca-a1fd-f625399e76b3?P1=1725568016&P2=404&P3=2&P4=J5s3ZdtM3xQ%2f4QQxxj1pjpJ08l%2f6OJ4kTx5ZkzIZrPw8E%2fwJLb2Uv4%2fuuhKqoREV9KKdKMQ57vnIULcUark5Ng%3d%3d | unknown | — | — | whitelisted |
1752 | svchost.exe | GET | 206 | 2.19.126.155:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/39120fc9-de56-4074-ab8a-7c851c15af3c?P1=1725568015&P2=404&P3=2&P4=h2A4EK9Wru3l3yJOcFV12g%2fBe76r25D%2bhAb7qQwyUwduWtK9pmEv00XPEkec%2fqIMD0Y%2b4fgQdnWTeO7Vq17Pcw%3d%3d | unknown | — | — | whitelisted |
1752 | svchost.exe | GET | 206 | 2.19.126.155:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4e7e4c6f-7b62-49ca-a1fd-f625399e76b3?P1=1725568016&P2=404&P3=2&P4=J5s3ZdtM3xQ%2f4QQxxj1pjpJ08l%2f6OJ4kTx5ZkzIZrPw8E%2fwJLb2Uv4%2fuuhKqoREV9KKdKMQ57vnIULcUark5Ng%3d%3d | unknown | — | — | whitelisted |
1752 | svchost.exe | HEAD | 200 | 2.19.126.155:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/39120fc9-de56-4074-ab8a-7c851c15af3c?P1=1725568015&P2=404&P3=2&P4=h2A4EK9Wru3l3yJOcFV12g%2fBe76r25D%2bhAb7qQwyUwduWtK9pmEv00XPEkec%2fqIMD0Y%2b4fgQdnWTeO7Vq17Pcw%3d%3d | unknown | — | — | whitelisted |
1752 | svchost.exe | GET | 206 | 2.19.126.155:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/39120fc9-de56-4074-ab8a-7c851c15af3c?P1=1725568015&P2=404&P3=2&P4=h2A4EK9Wru3l3yJOcFV12g%2fBe76r25D%2bhAb7qQwyUwduWtK9pmEv00XPEkec%2fqIMD0Y%2b4fgQdnWTeO7Vq17Pcw%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6164 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6268 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7132 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
5532 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5532 | msedge.exe | 52.71.57.184:443 | memz-trojan.securesoft.net | AMAZON-AES | US | unknown |
5532 | msedge.exe | 13.107.21.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5532 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5532 | msedge.exe | 94.245.104.56:443 | api.edgeoffer.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
memz-trojan.securesoft.net |
| unknown |
edge.microsoft.com |
| whitelisted |
api.edgeoffer.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
client.wns.windows.com |
| whitelisted |
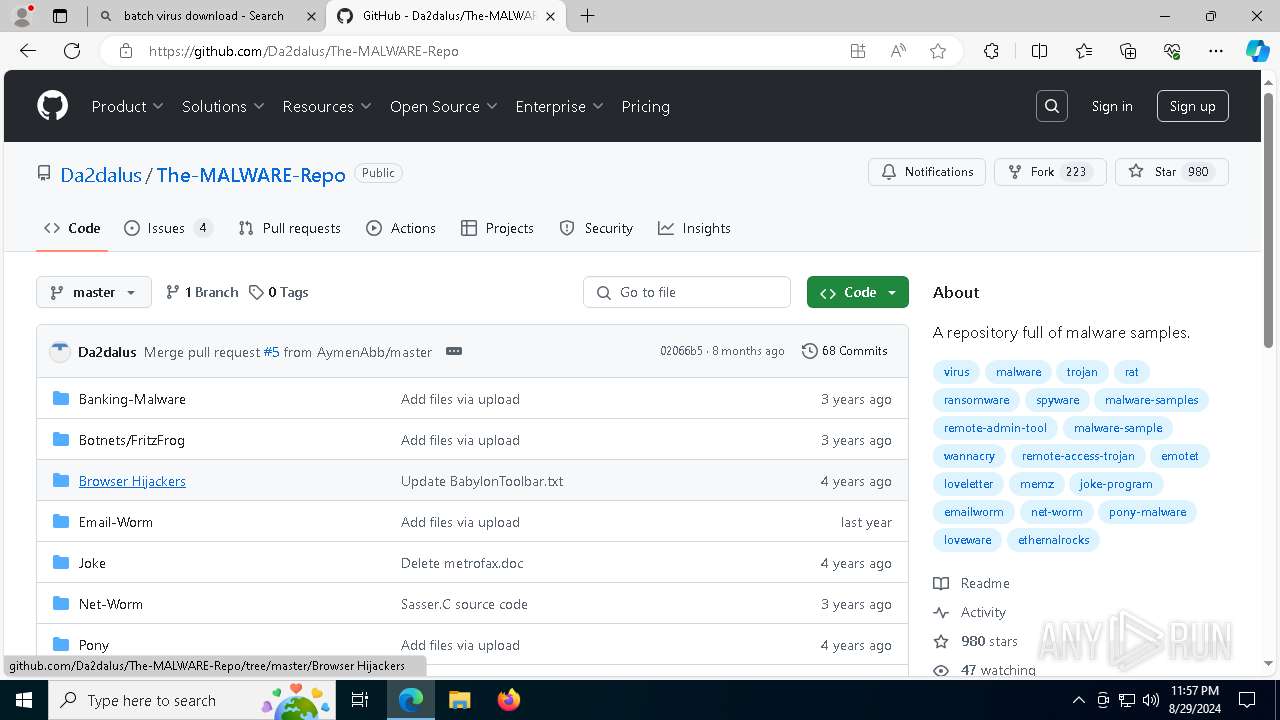
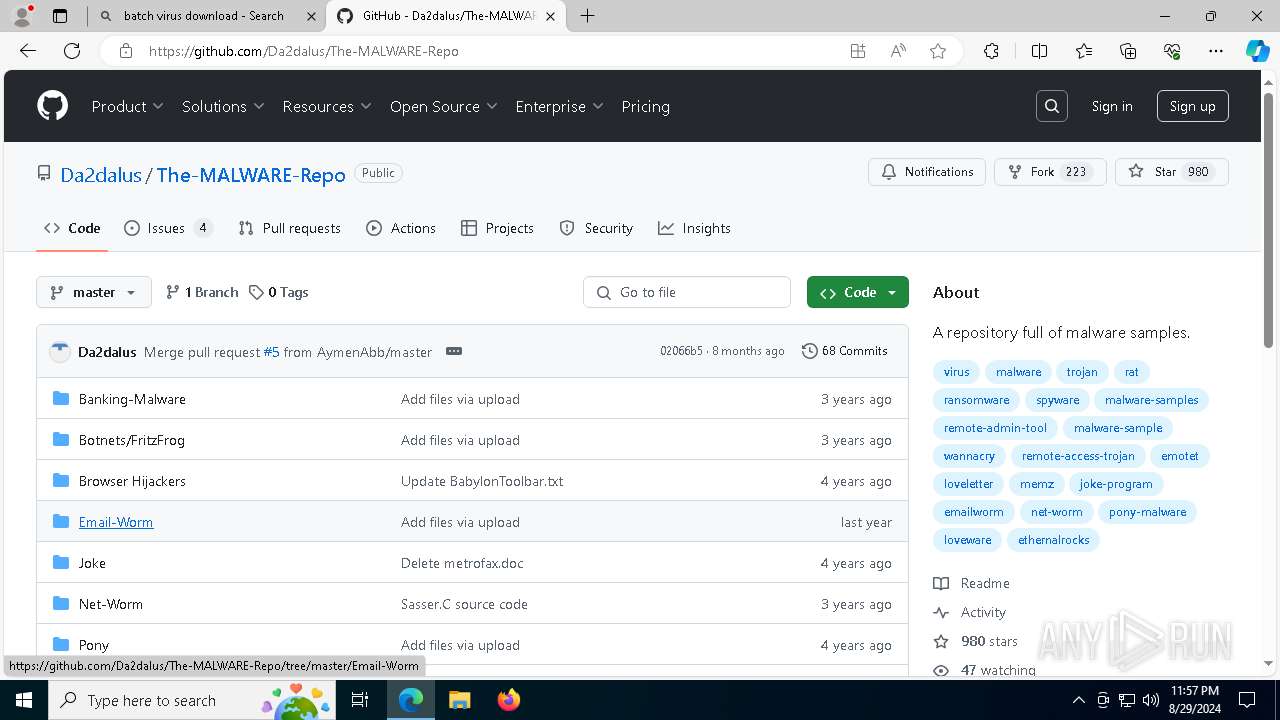
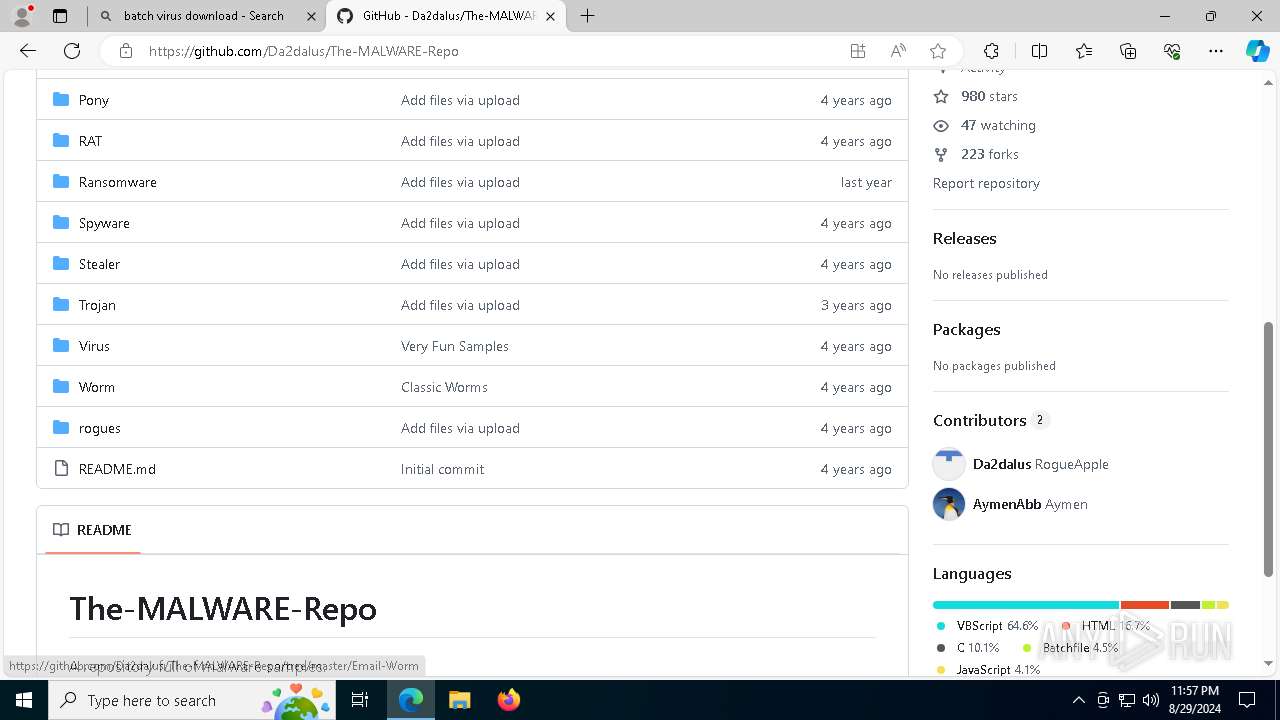
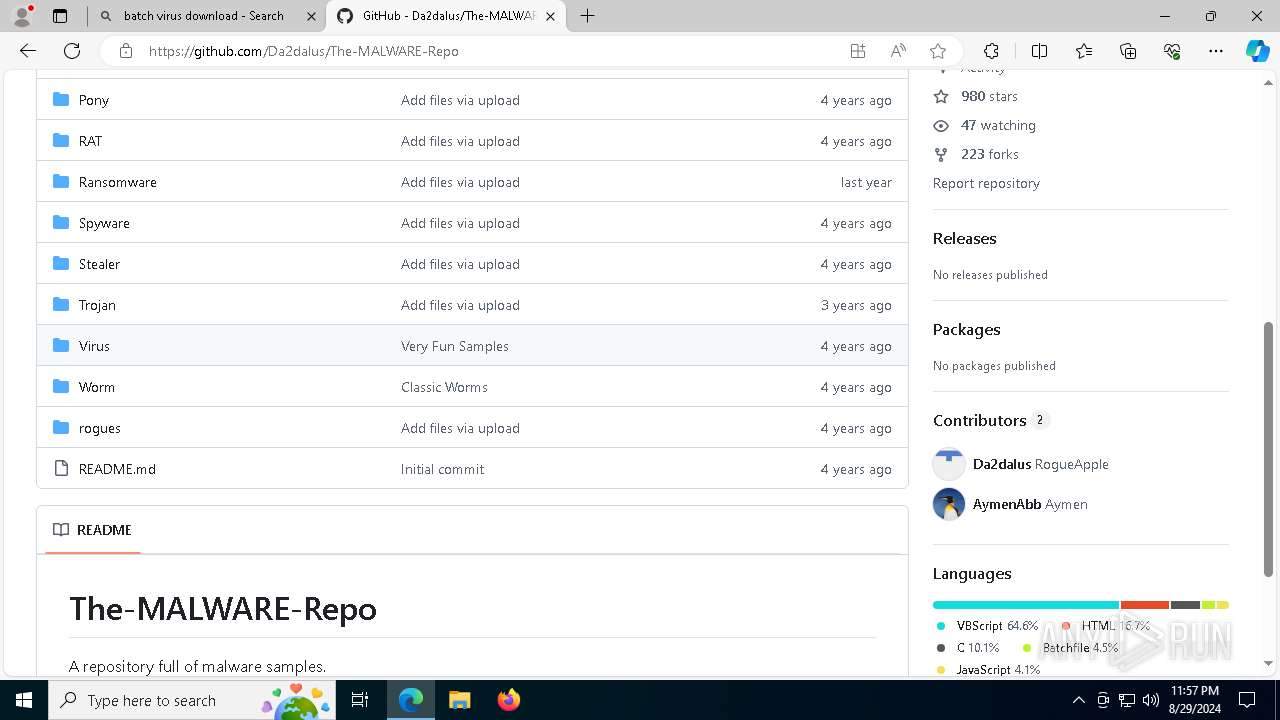
Threats
PID | Process | Class | Message |
|---|---|---|---|
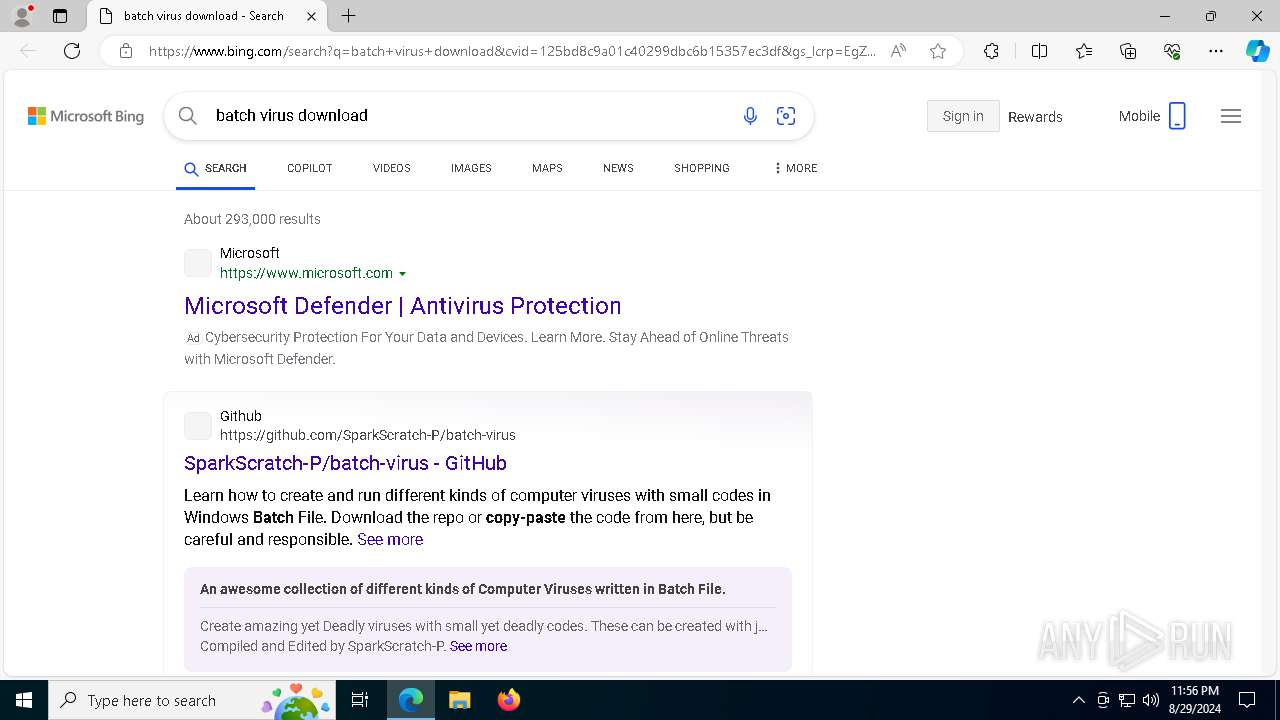
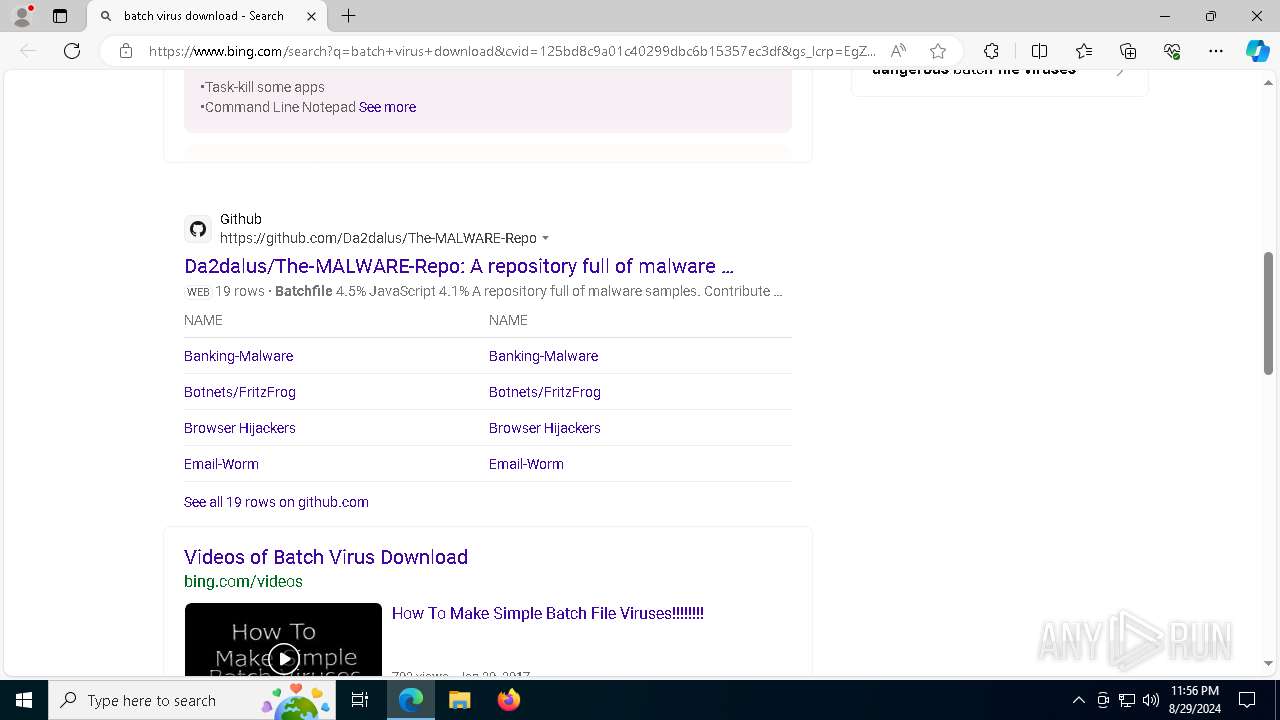
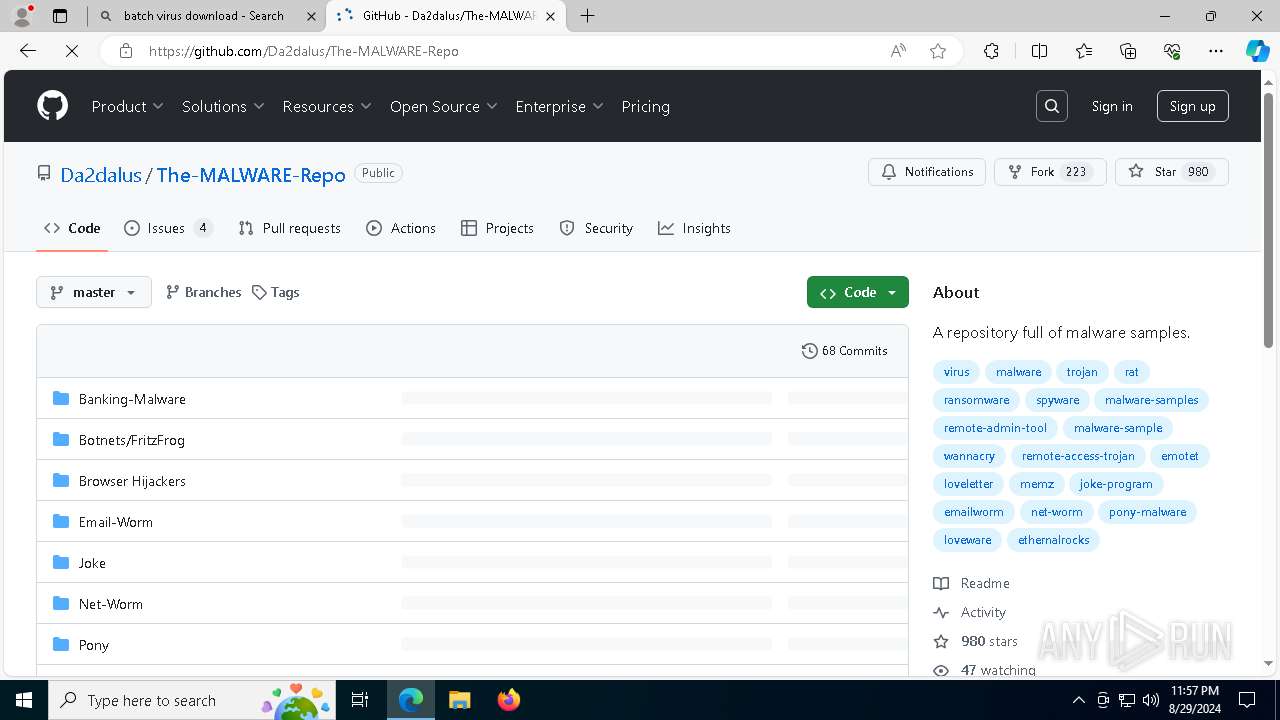
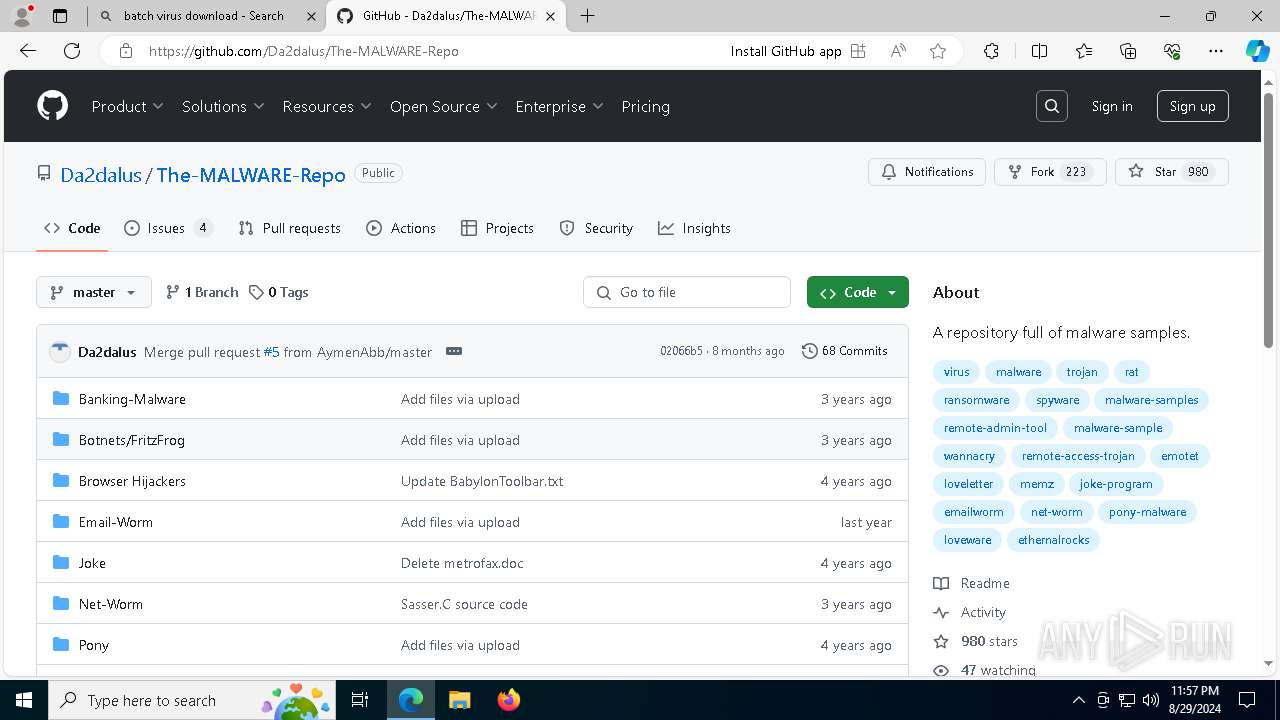
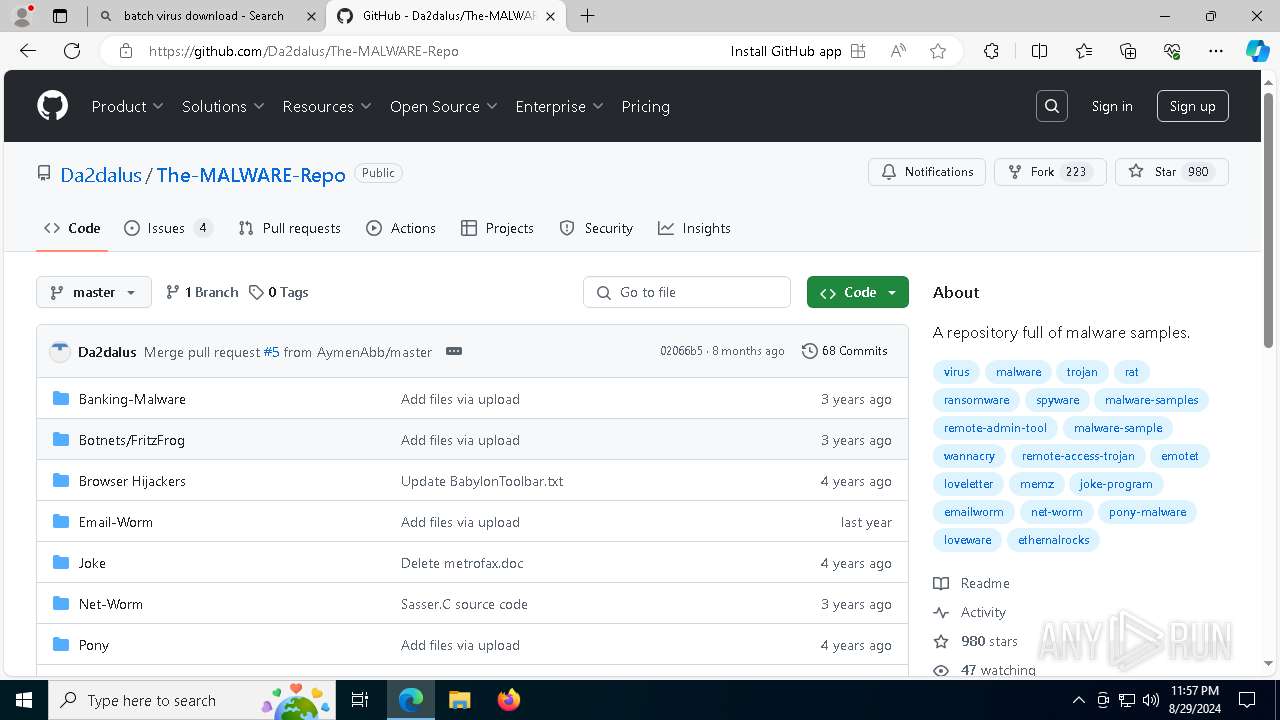
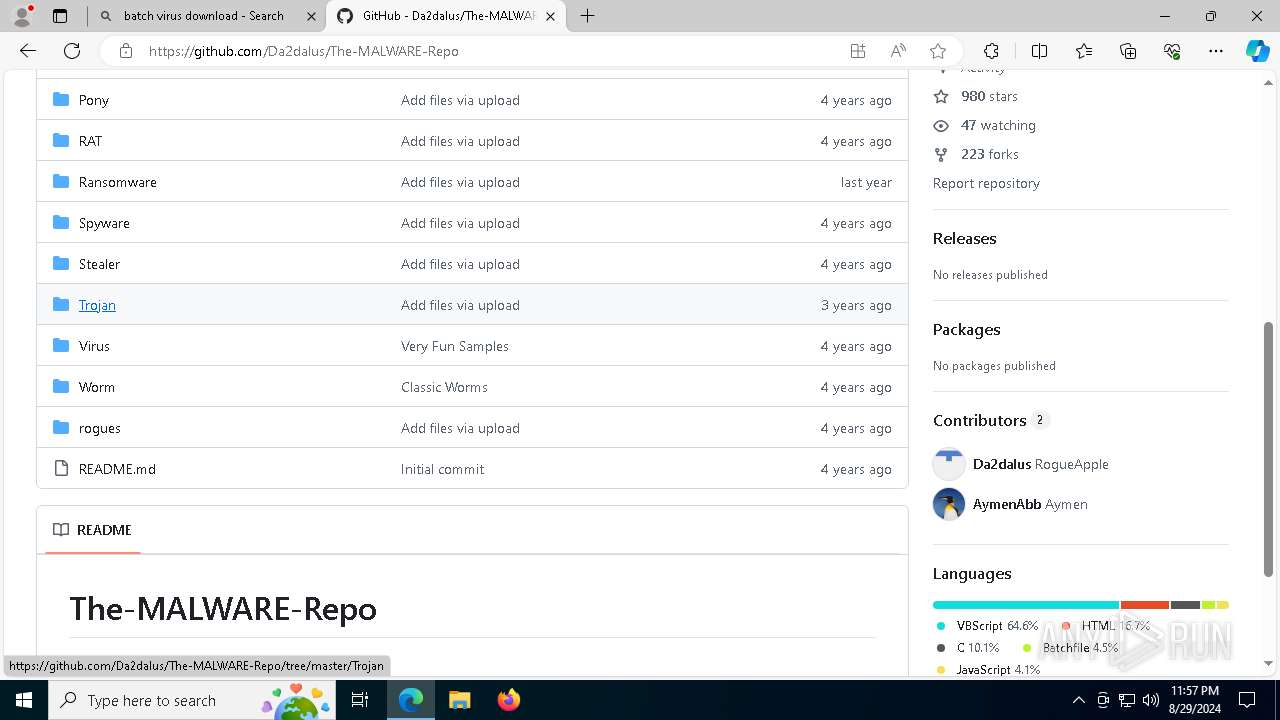
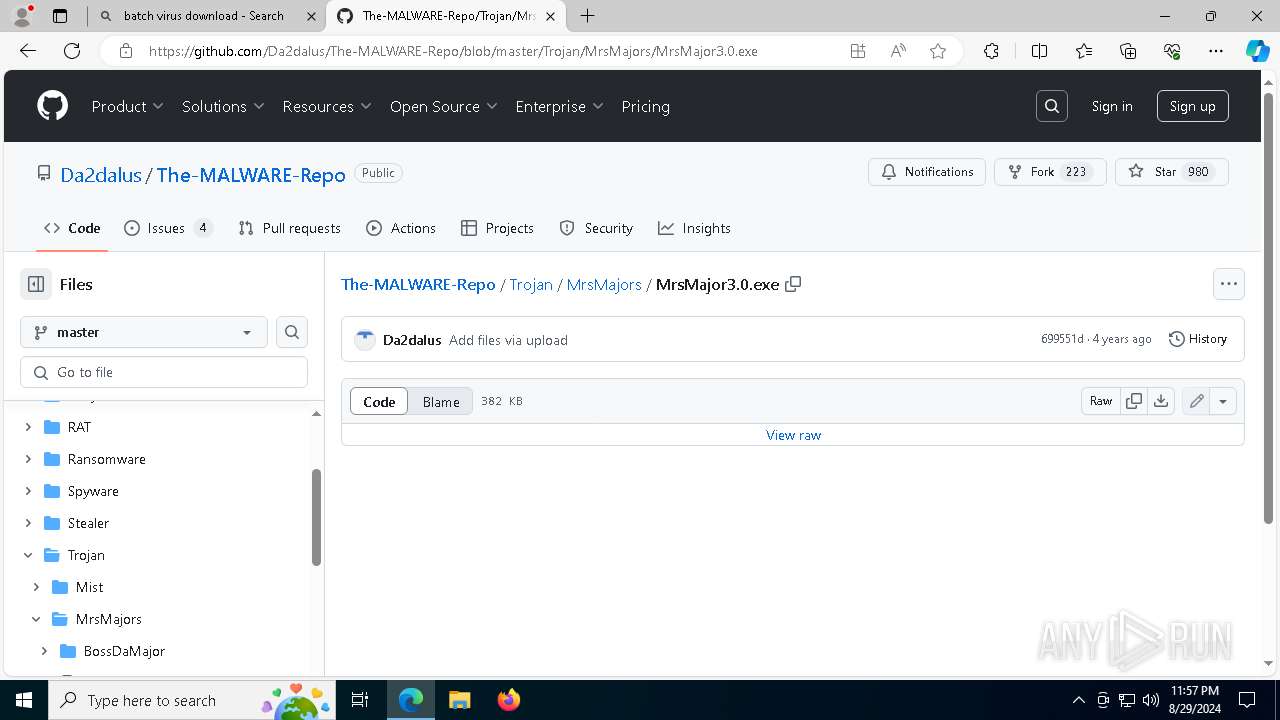
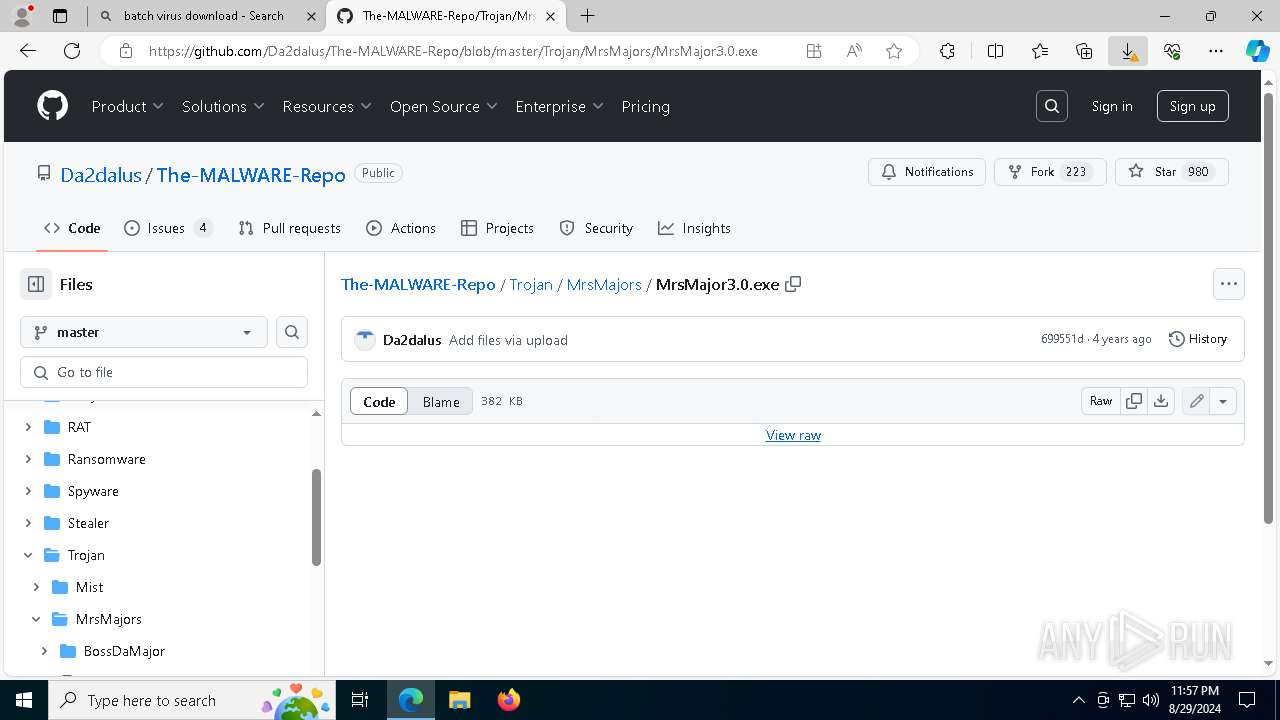
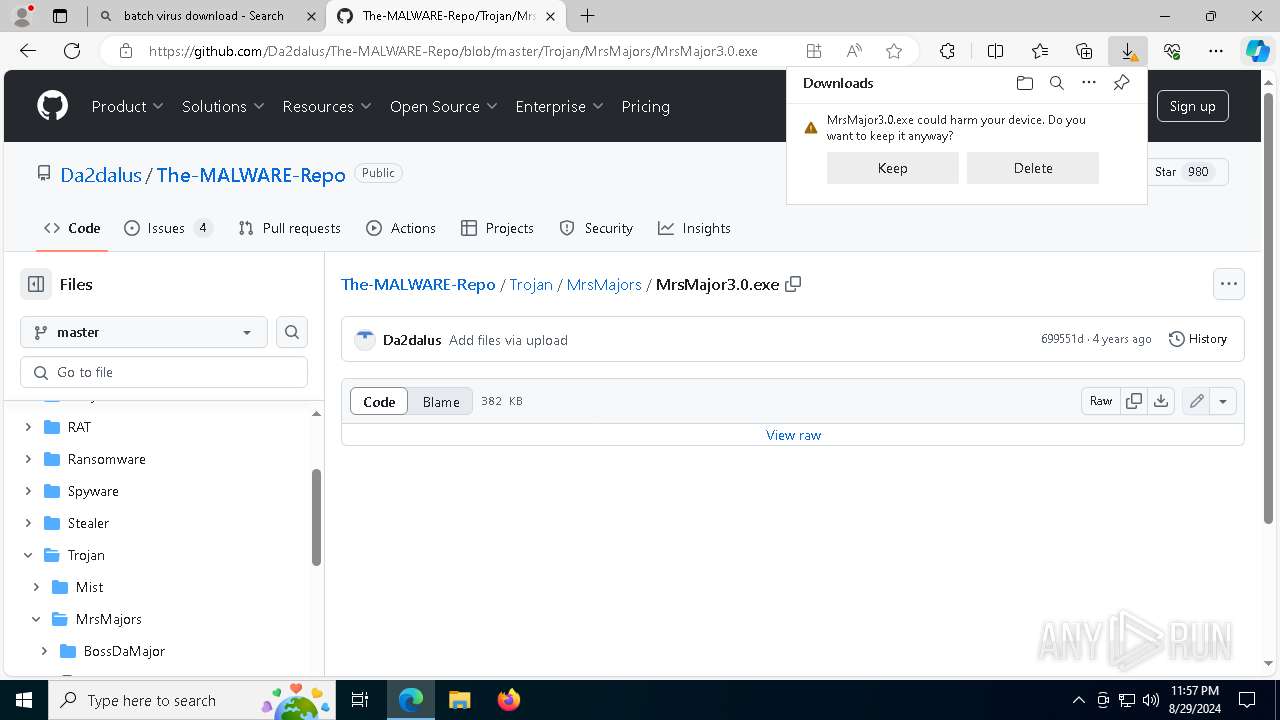
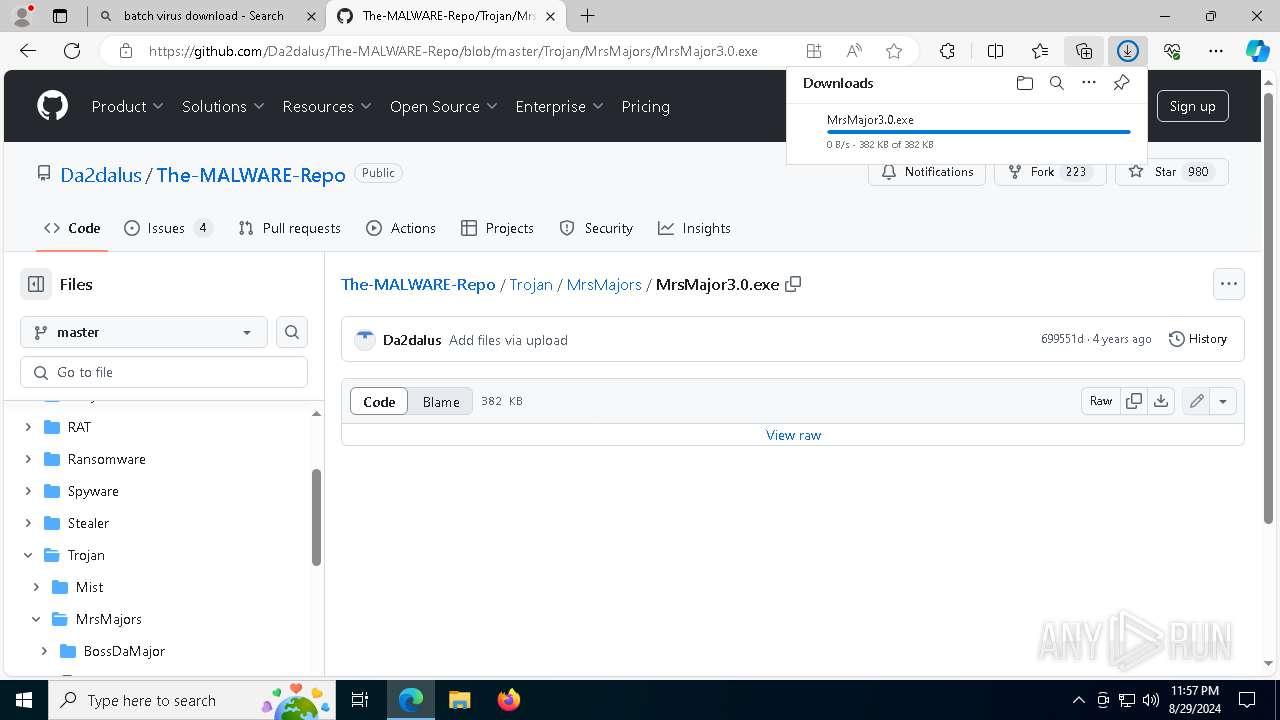
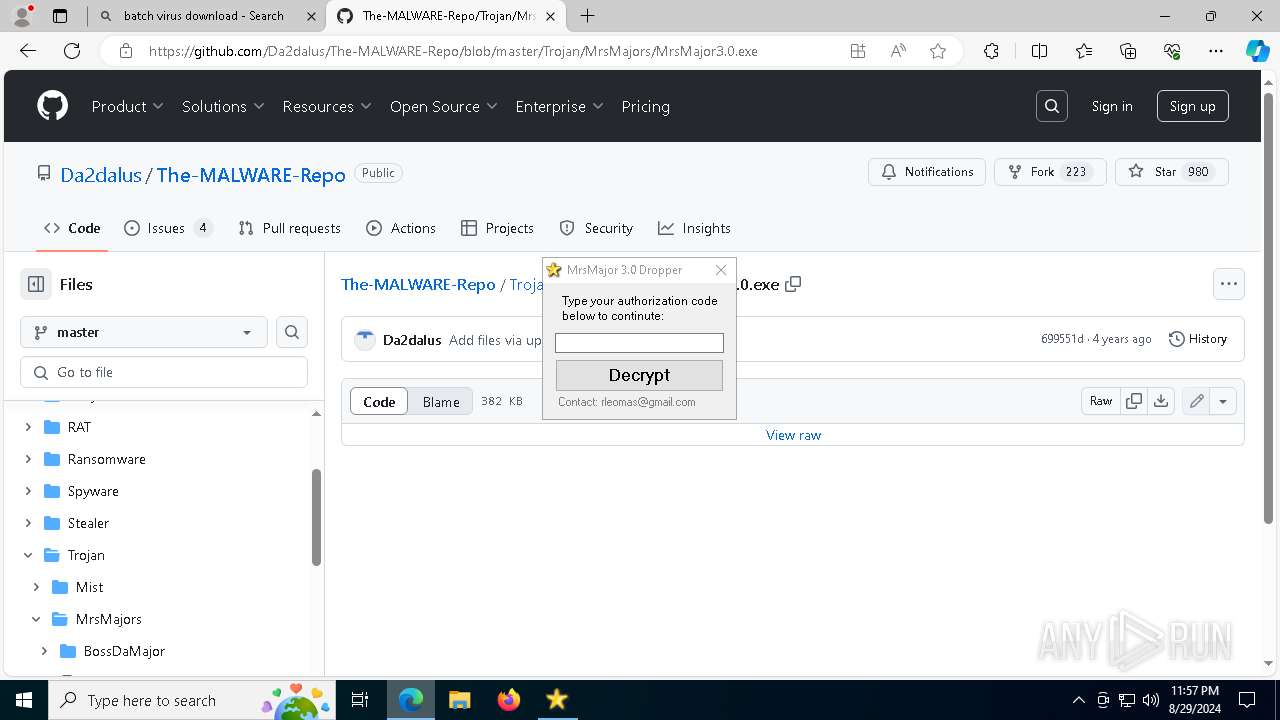
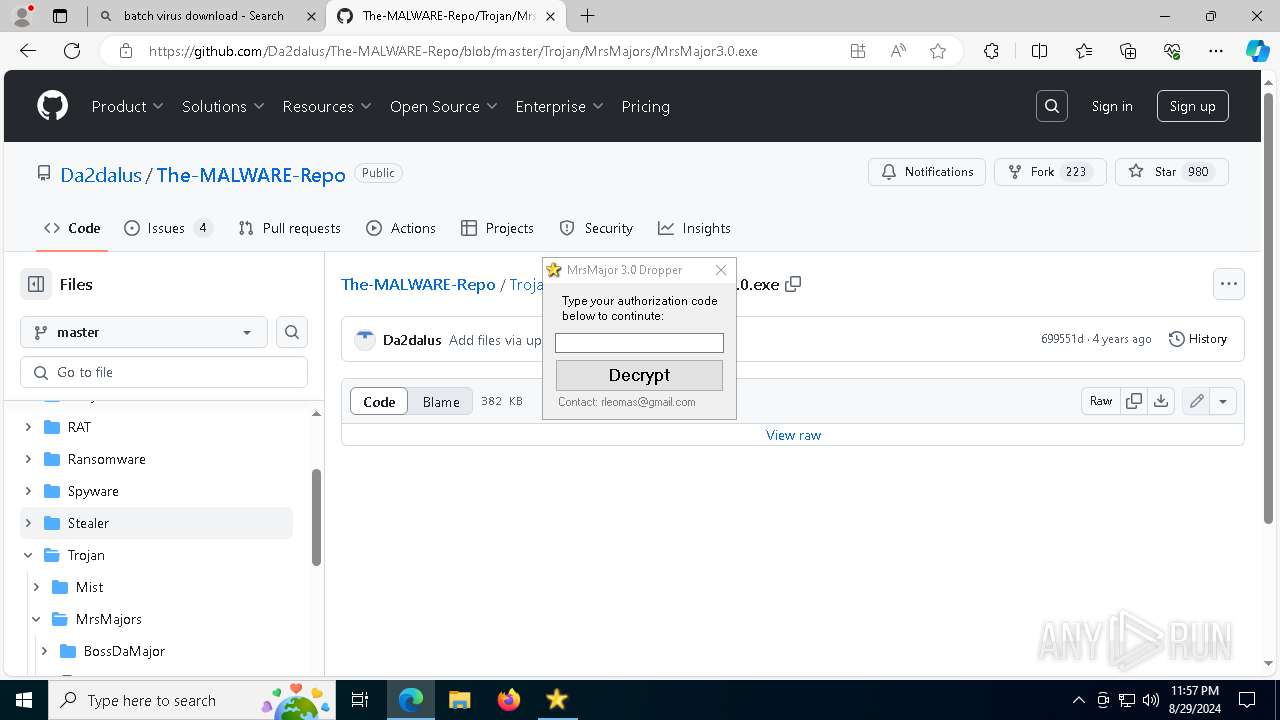
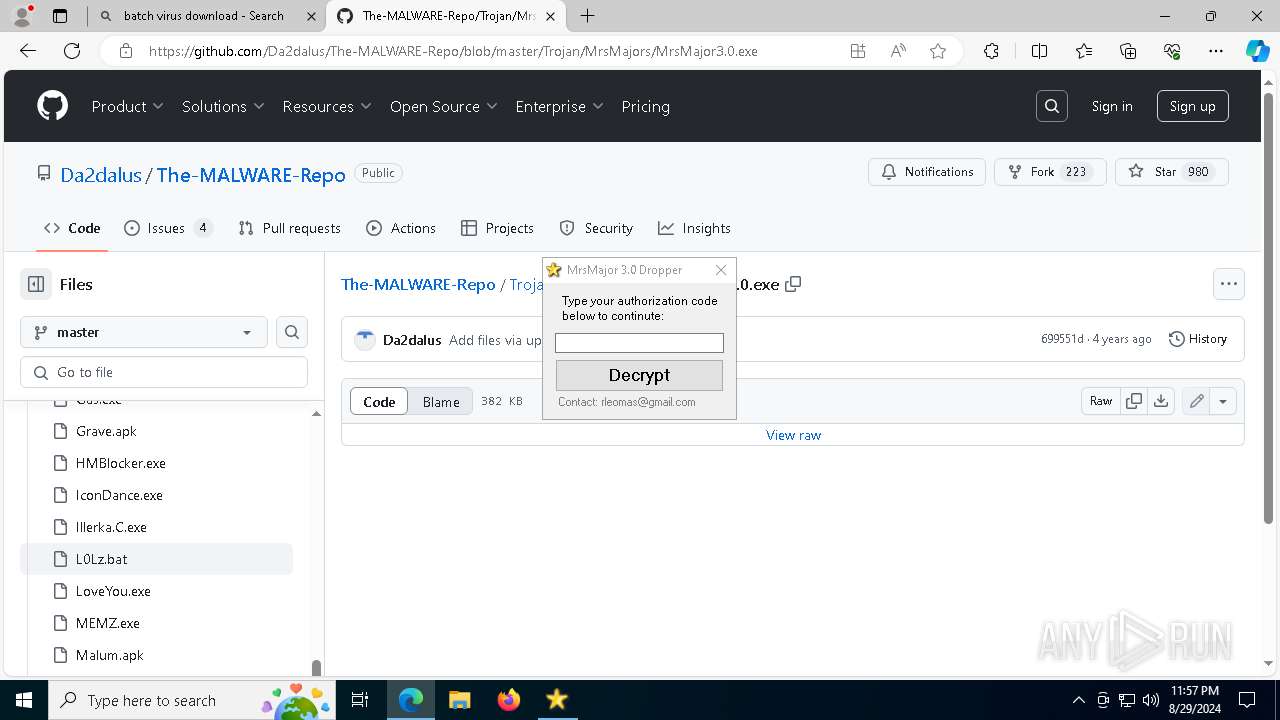
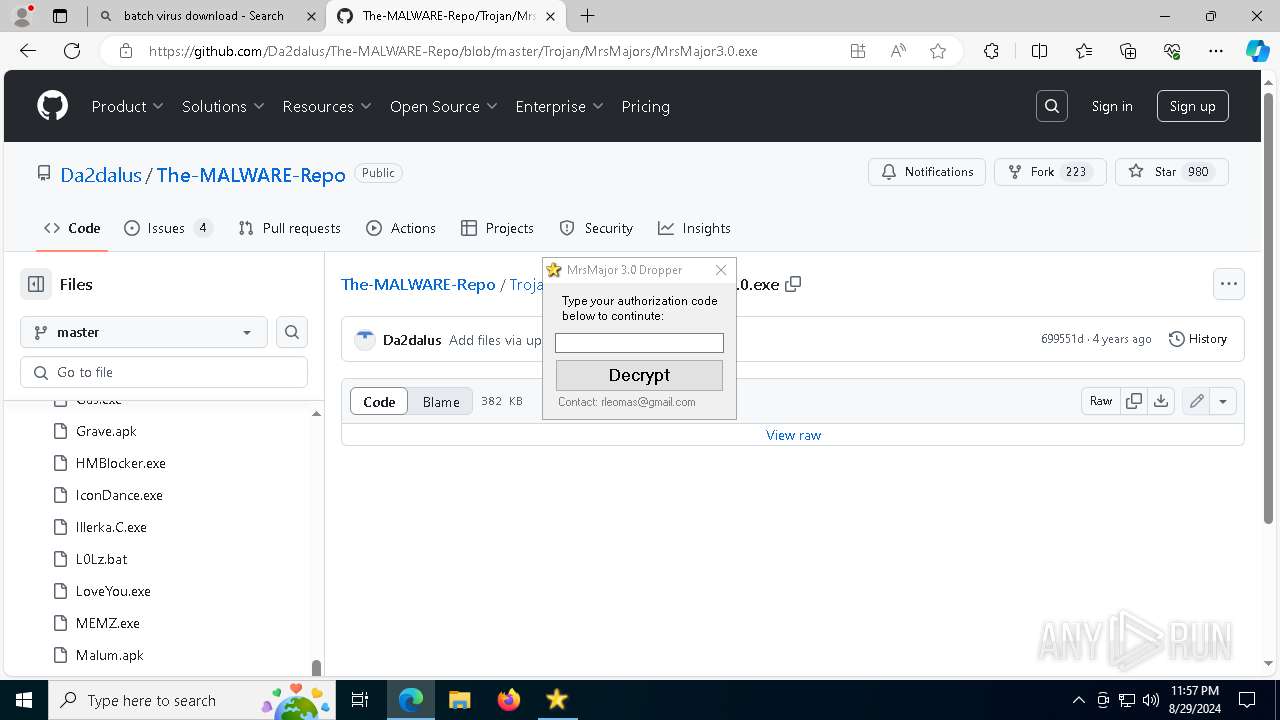
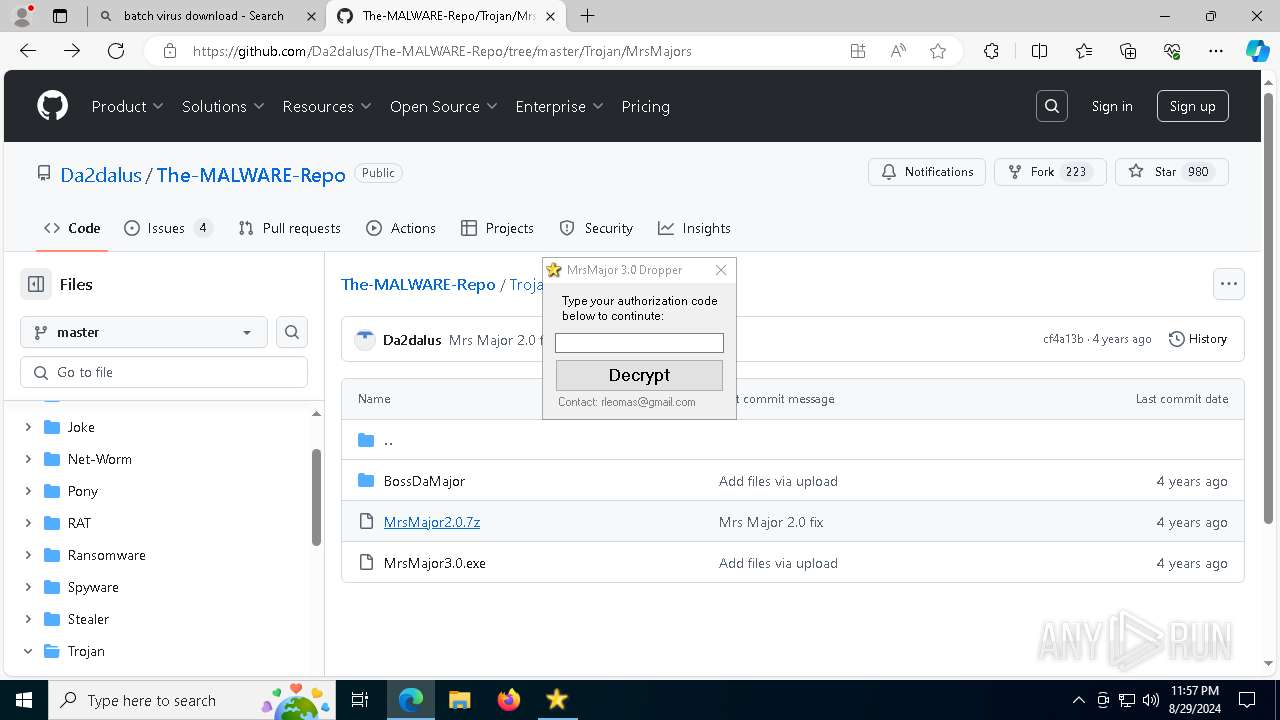
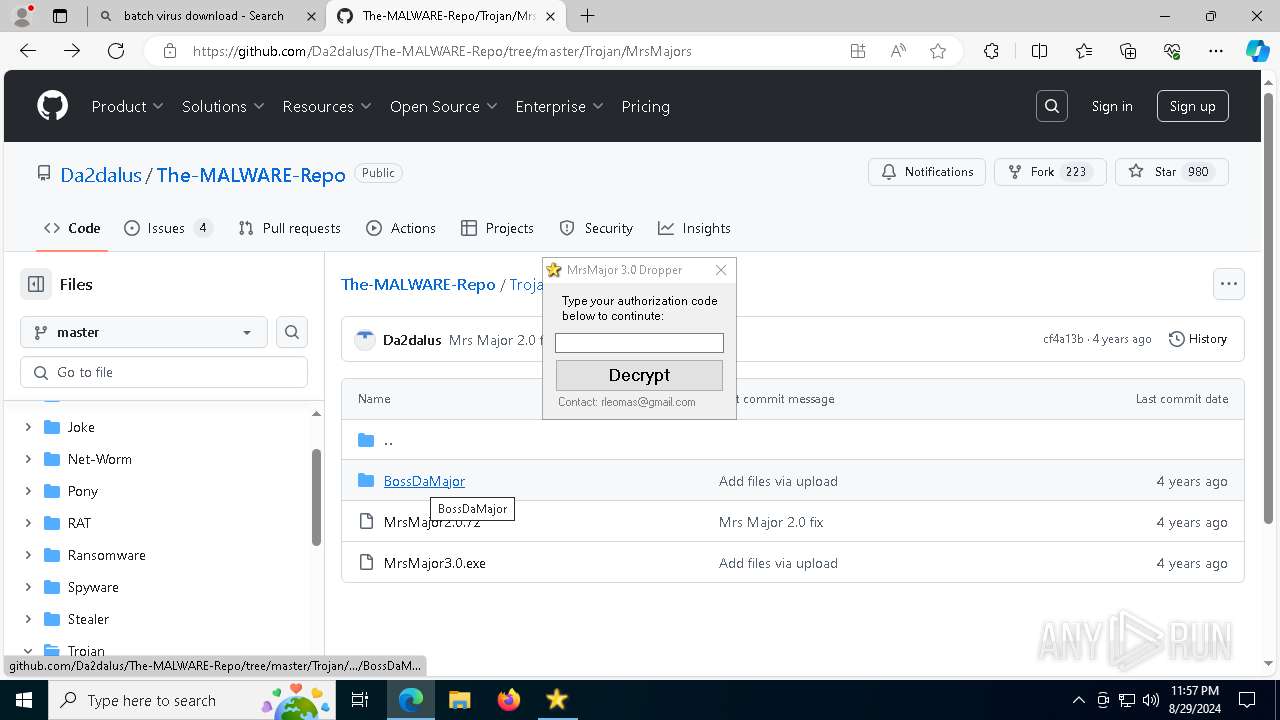
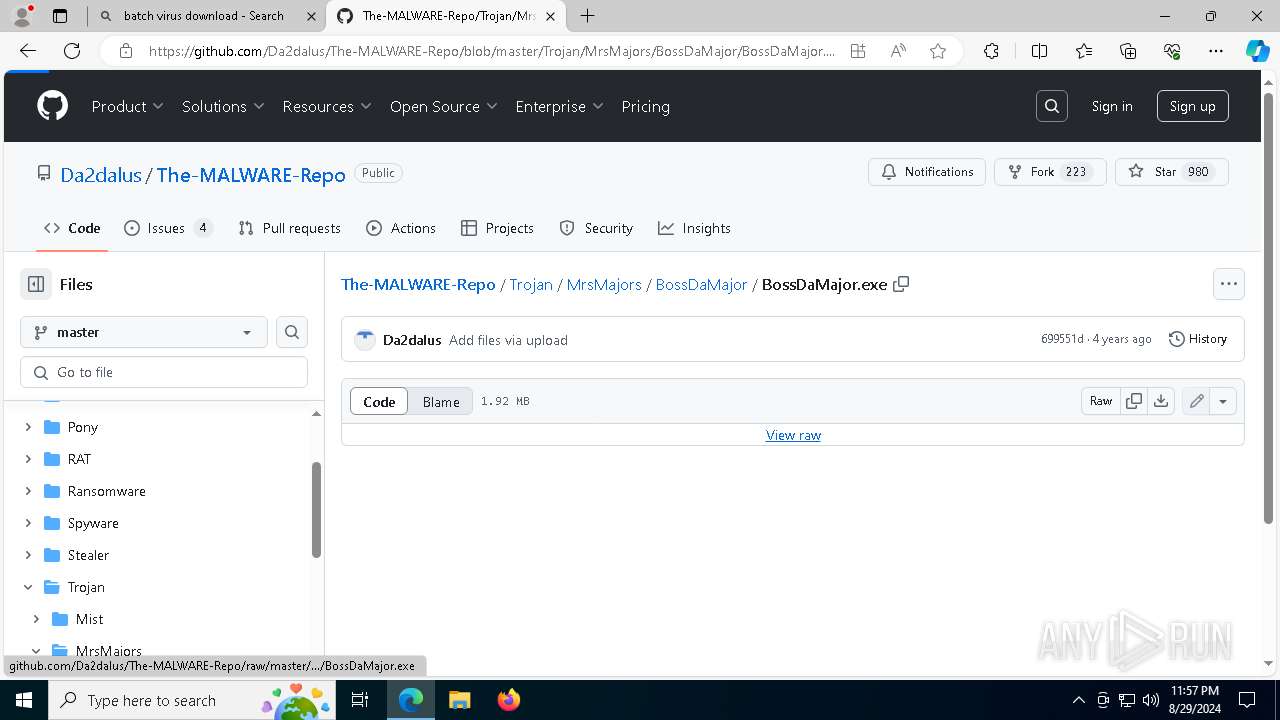
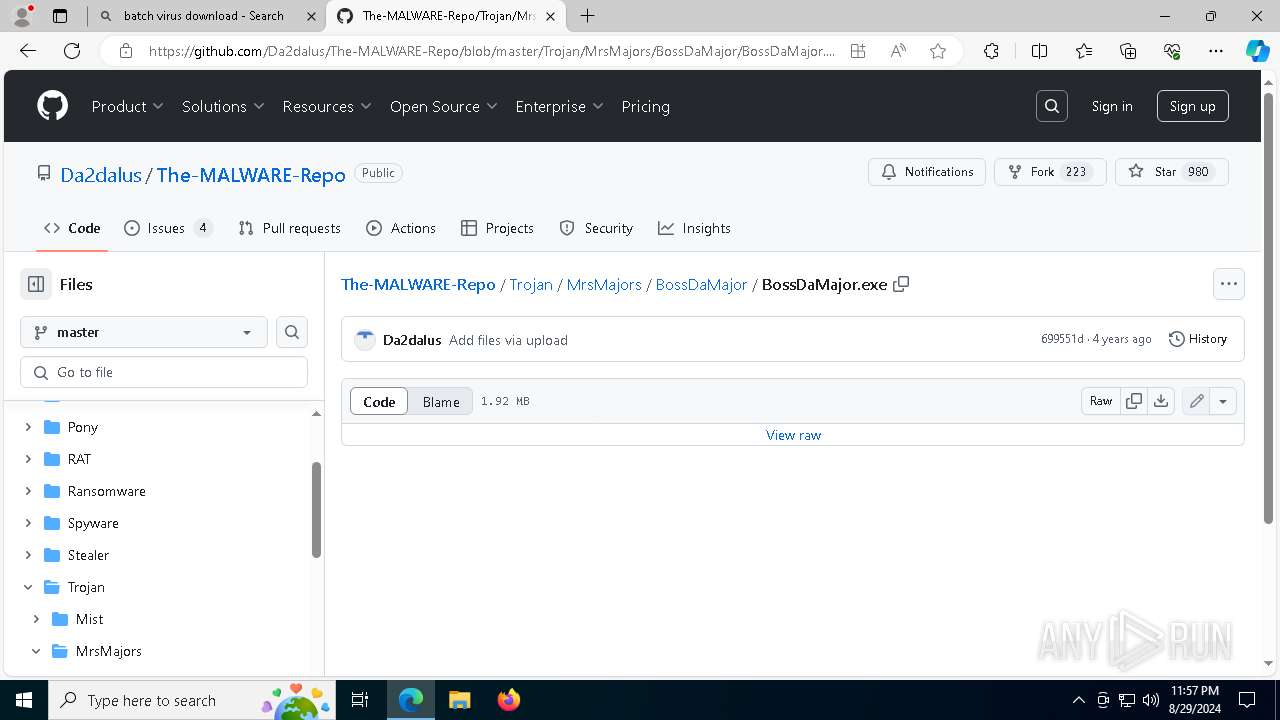
5532 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
5532 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
5532 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
5532 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
Process | Message |
|---|---|
msedge.exe | [0829/235701.645:WARNING:device_ticket.cc(151)] Timed out waiting for device ticket. Canceling async operation.
|
msedge.exe | [0829/235702.239:ERROR:process_memory_win.cc(74)] ReadMemory at 0x7ff6278d0000 of 64 bytes failed: Only part of a ReadProcessMemory or WriteProcessMemory request was completed. (0x12B)
|
msedge.exe | [0829/235702.241:WARNING:pe_image_reader.cc(340)] could not read dos header from C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe
|
msedge.exe | [0829/235702.241:ERROR:process_memory_win.cc(74)] ReadMemory at 0x7ffff85f0000 of 64 bytes failed: Only part of a ReadProcessMemory or WriteProcessMemory request was completed. (0x12B)
|
msedge.exe | [0829/235702.241:WARNING:pe_image_reader.cc(340)] could not read dos header from C:\WINDOWS\SYSTEM32\ntdll.dll
|
msedge.exe | [0829/235702.241:ERROR:process_memory_win.cc(74)] ReadMemory at 0x7ffff6f10000 of 64 bytes failed: Only part of a ReadProcessMemory or WriteProcessMemory request was completed. (0x12B)
|
msedge.exe | [0829/235702.241:WARNING:pe_image_reader.cc(340)] could not read dos header from C:\WINDOWS\System32\KERNEL32.DLL
|
msedge.exe | [0829/235702.241:ERROR:process_memory_win.cc(74)] ReadMemory at 0x7ffff5da0000 of 64 bytes failed: Only part of a ReadProcessMemory or WriteProcessMemory request was completed. (0x12B)
|
msedge.exe | [0829/235702.241:WARNING:pe_image_reader.cc(340)] could not read dos header from C:\WINDOWS\System32\KERNELBASE.dll
|
msedge.exe | [0829/235702.241:ERROR:process_memory_win.cc(74)] ReadMemory at 0x7fffd24a0000 of 64 bytes failed: Only part of a ReadProcessMemory or WriteProcessMemory request was completed. (0x12B)
|