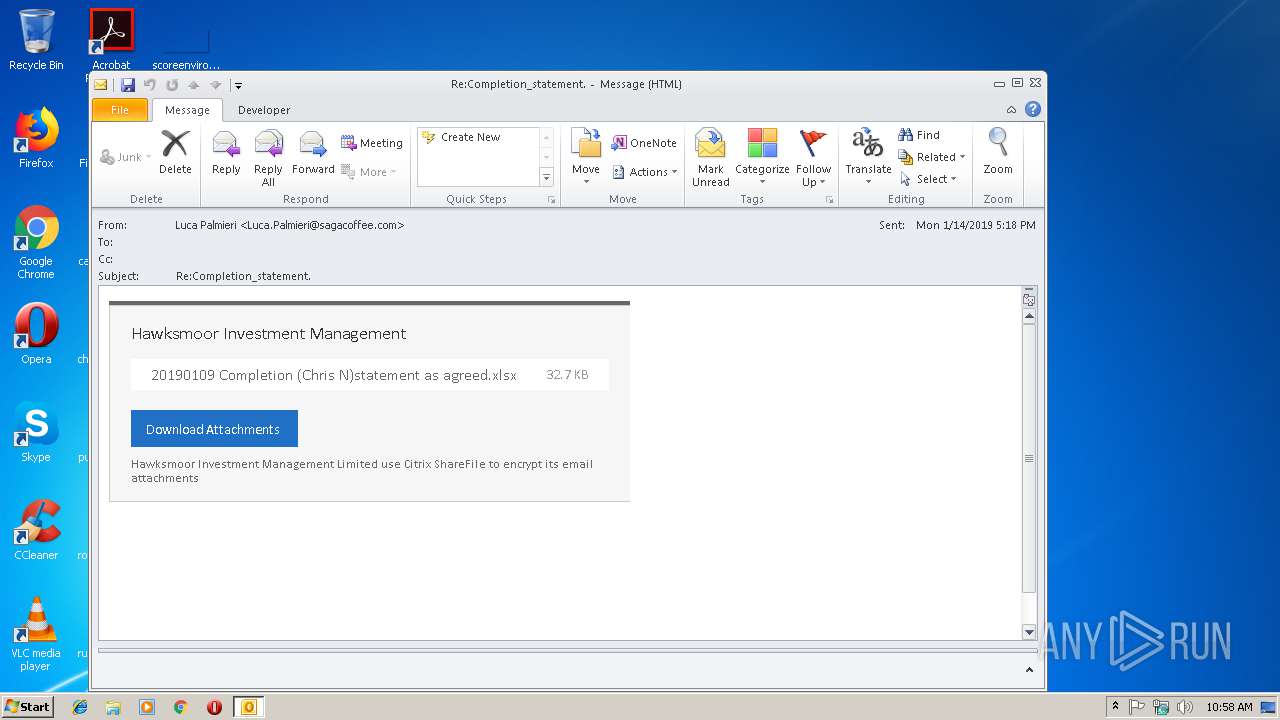
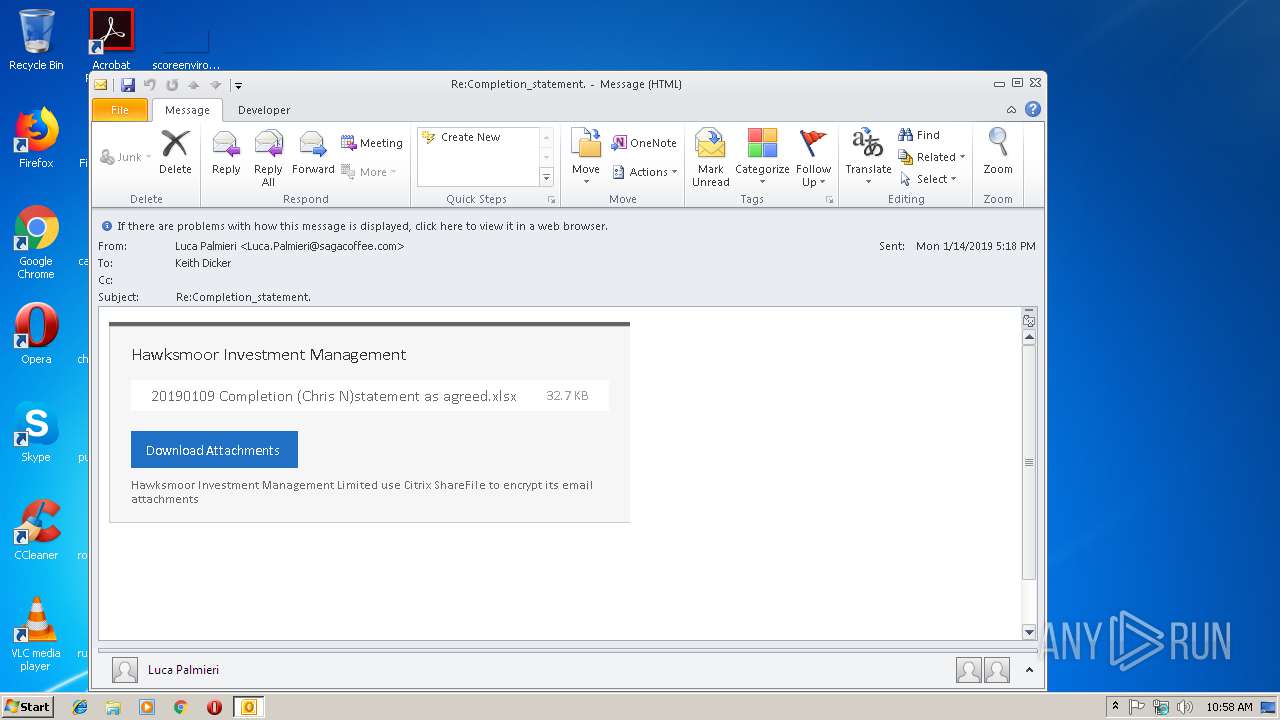
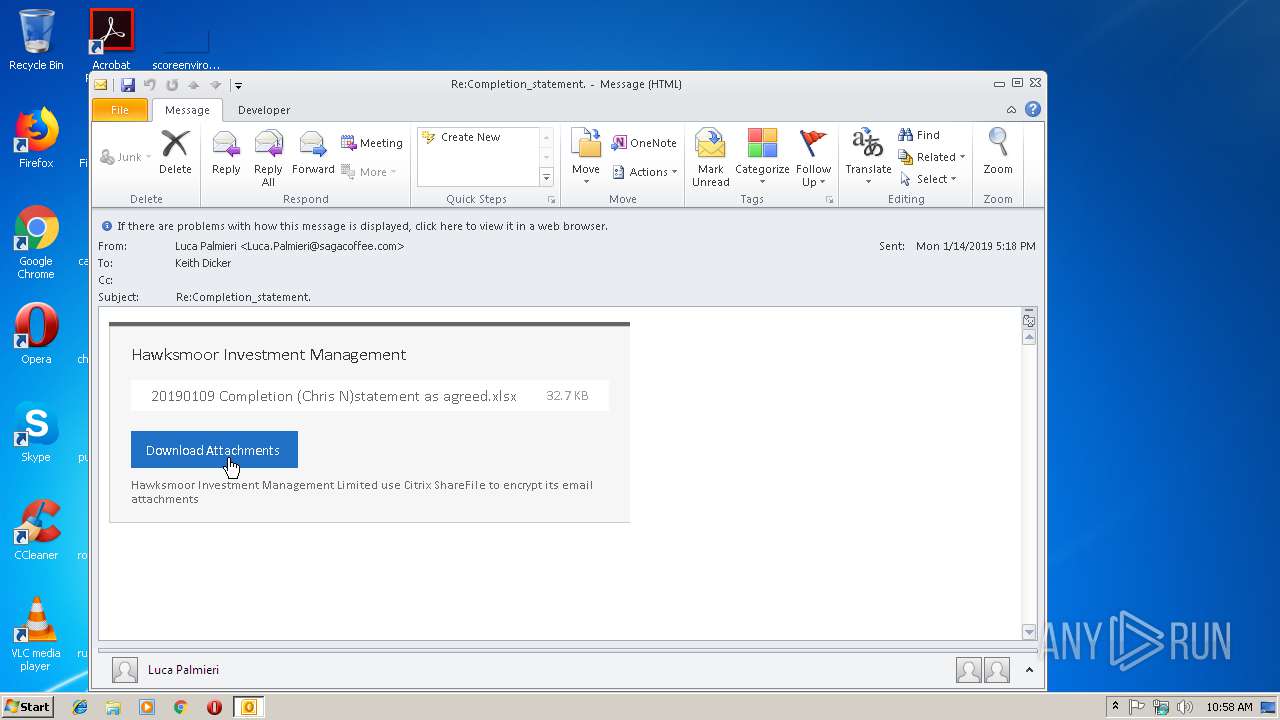
| File name: | ReCompletion_statement.eml |
| Full analysis: | https://app.any.run/tasks/7b087bed-202e-487e-b818-c2464ab816fd |
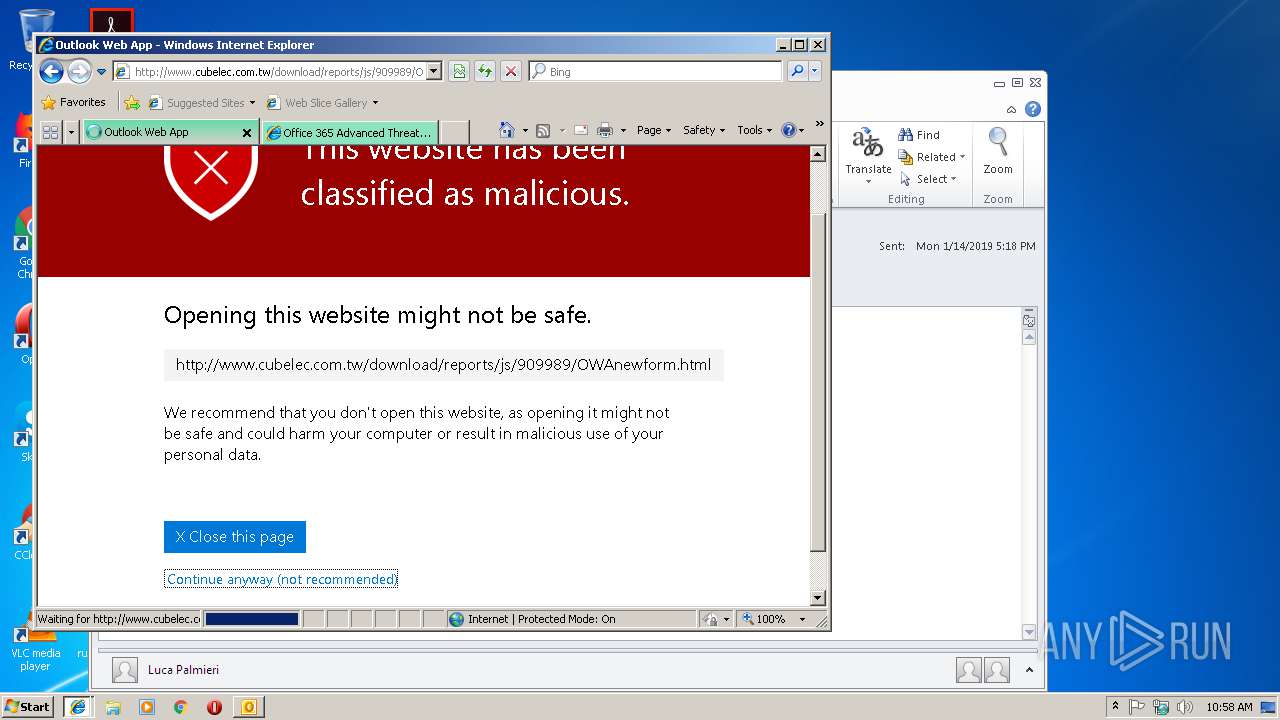
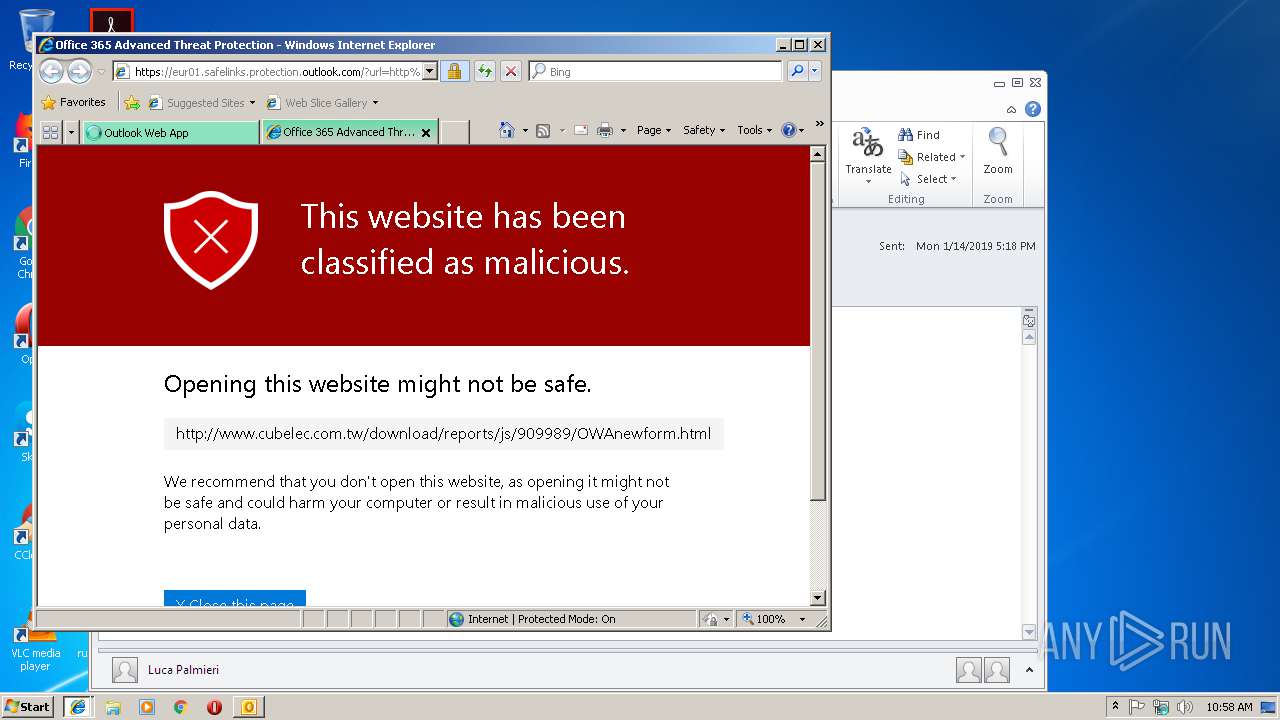
| Verdict: | Malicious activity |
| Analysis date: | January 18, 2019, 10:57:56 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | message/rfc822 |
| File info: | RFC 822 mail, ASCII text, with very long lines, with CRLF line terminators |
| MD5: | 60566AE0908AE5CB10B1D1966B8EC0AC |
| SHA1: | A3AAB48E6E3B764B59DFA9DB64A5A3A50AD13031 |
| SHA256: | 2D45EEBB786D70EFDD888917AF992D9516E25F3515AB810724C6DCC790A51DD2 |
| SSDEEP: | 192:cd8Cwg8SedZV4ws/Eb8AAegLxn3KVMYpL46aSo1IWcGiR/9PEuHApm5tiUYn:OXhgq/3JLx361totIRlkCtiPn |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 3004)
Creates files in the user directory
- OUTLOOK.EXE (PID: 3004)
Starts Internet Explorer
- OUTLOOK.EXE (PID: 3004)
INFO
Application launched itself
- iexplore.exe (PID: 2304)
Changes internet zones settings
- iexplore.exe (PID: 2304)
Reads settings of System Certificates
- iexplore.exe (PID: 3056)
- iexplore.exe (PID: 2304)
- iexplore.exe (PID: 1972)
Reads internet explorer settings
- iexplore.exe (PID: 3056)
- iexplore.exe (PID: 1972)
Reads Internet Cache Settings
- iexplore.exe (PID: 3056)
- iexplore.exe (PID: 1972)
Changes settings of System certificates
- iexplore.exe (PID: 2304)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2304)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 3004)
Creates files in the user directory
- iexplore.exe (PID: 3056)
- iexplore.exe (PID: 2304)
- iexplore.exe (PID: 1972)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .eml | | | E-Mail message (Var. 5) (100) |
|---|
Total processes
36
Monitored processes
4
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1972 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2304 CREDAT:71938 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
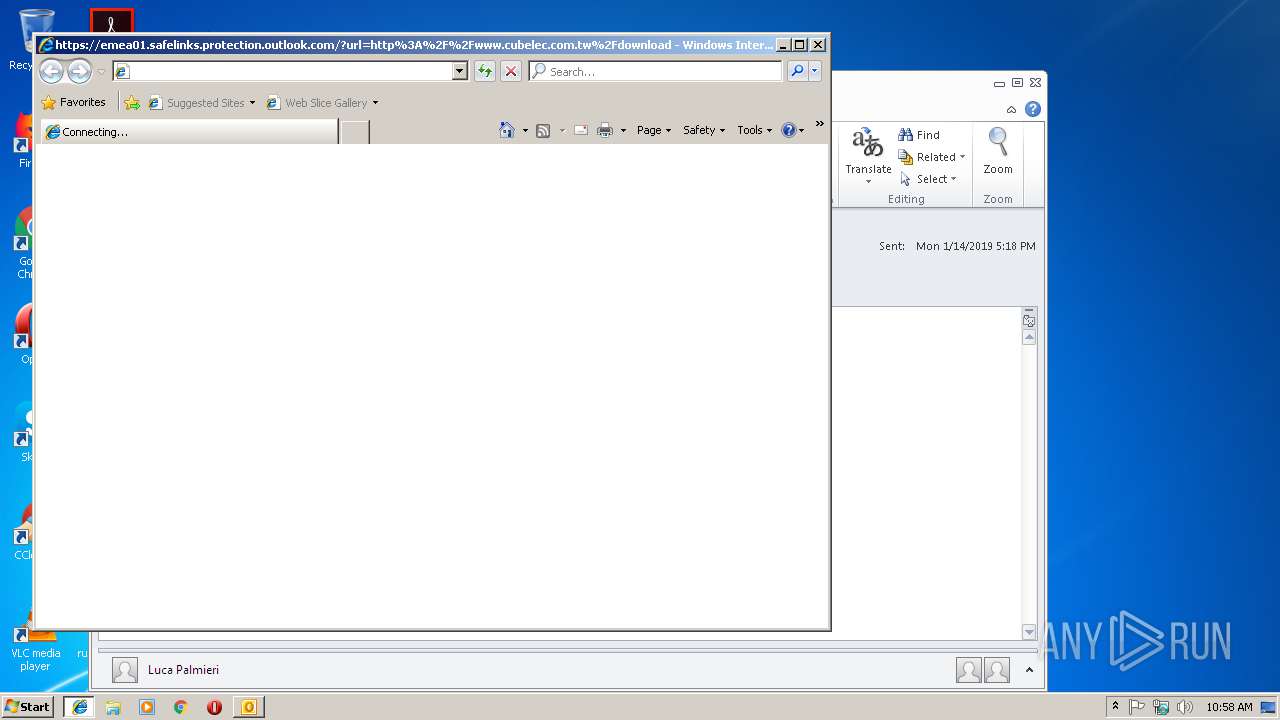
| 2304 | "C:\Program Files\Internet Explorer\iexplore.exe" https://emea01.safelinks.protection.outlook.com/?url=http%3A%2F%2Fwww.cubelec.com.tw%2Fdownload%2Freports%2Fjs%2F909989%2FOWAnewform.html&data=01%7C01%7Ckeith.dicker%40generationim.com%7C4a5e433145f64783484708d67a5247cc%7Cbf4450a2bfcb472d8c401425eafb1a3b%7C1&sdata=S0qIxp7O%2FK%2B%2F1XkE4a1KMObkGuhCTa6%2Fe4x2giU1XPE%3D&reserved=0 | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3004 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" /eml "C:\Users\admin\AppData\Local\Temp\ReCompletion_statement.eml" | C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 3056 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2304 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 853
Read events
1 355
Write events
475
Delete events
23
Modification events
| (PID) Process: | (3004) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3004) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3004) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Resiliency\StartupItems |
| Operation: | write | Name: | >k% |
Value: 3E6B2500BC0B0000010000000000000000000000 | |||
| (PID) Process: | (3004) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook |
| Operation: | write | Name: | MTTT |
Value: BC0B000028105AB71CAFD40100000000 | |||
| (PID) Process: | (3004) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionNumber |
Value: 0 | |||
| (PID) Process: | (3004) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionDate |
Value: 219870720 | |||
| (PID) Process: | (3004) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\0a0d020000000000c000000000000046 |
| Operation: | write | Name: | 00030429 |
Value: 03000000 | |||
| (PID) Process: | (3004) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | {ED475418-B0D6-11D2-8C3B-00104B2A6676} |
Value: | |||
| (PID) Process: | (3004) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | LastChangeVer |
Value: 1200000000000000 | |||
| (PID) Process: | (3004) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109A10090400000000000F01FEC\Usage |
| Operation: | write | Name: | OutlookMAPI2Intl_1033 |
Value: 1311899669 | |||
Executable files
0
Suspicious files
14
Text files
47
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3004 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR8B00.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2304 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2304 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3056 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\eur01_safelinks_protection_outlook_com[1].txt | — | |
MD5:— | SHA256:— | |||
| 1972 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\BWPPCY0O\eur01_safelinks_protection_outlook_com[1].txt | — | |
MD5:— | SHA256:— | |||
| 3056 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab102E.tmp | — | |
MD5:— | SHA256:— | |||
| 3056 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab103F.tmp | — | |
MD5:— | SHA256:— | |||
| 3056 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar102F.tmp | — | |
MD5:— | SHA256:— | |||
| 3056 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab1041.tmp | — | |
MD5:— | SHA256:— | |||
| 3056 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar1040.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
36
DNS requests
10
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
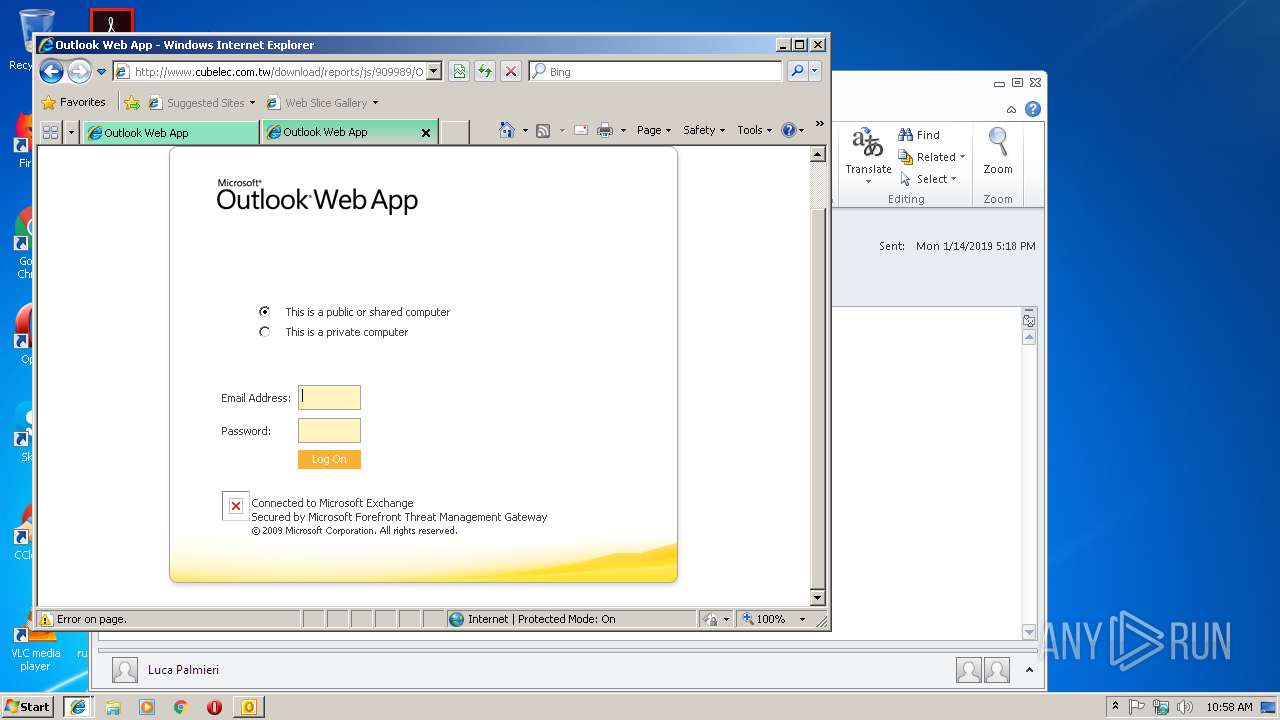
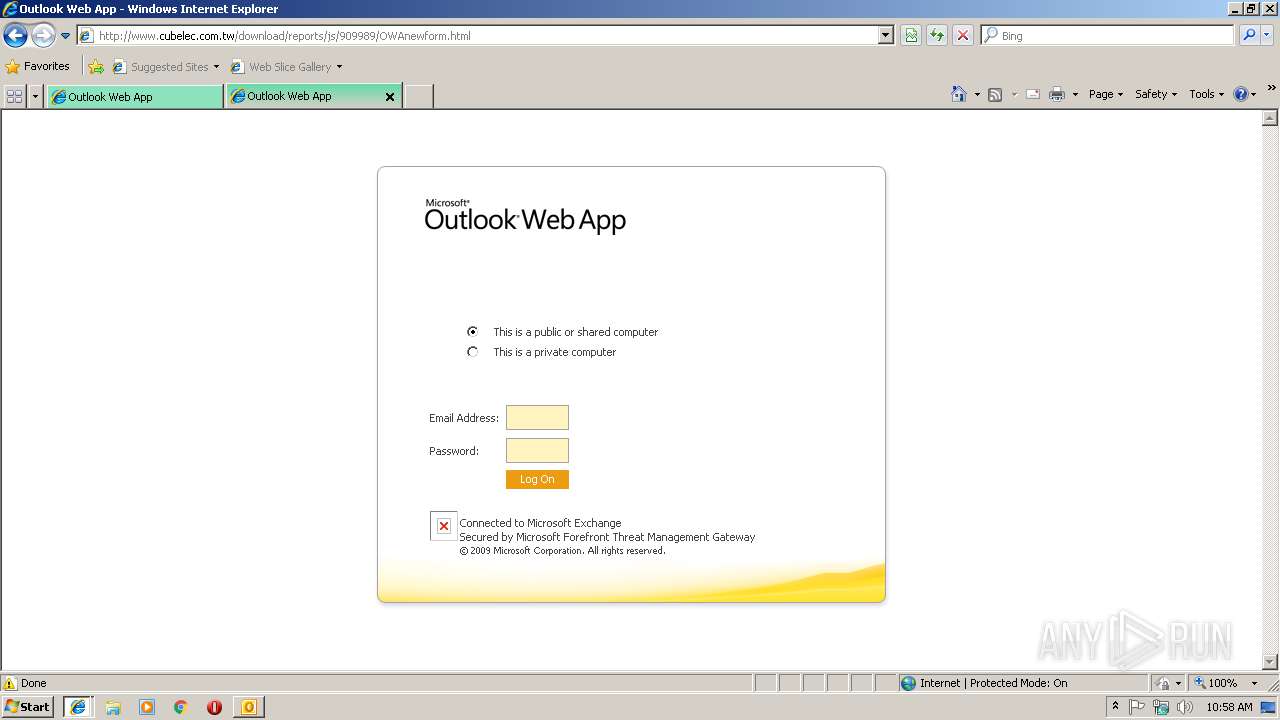
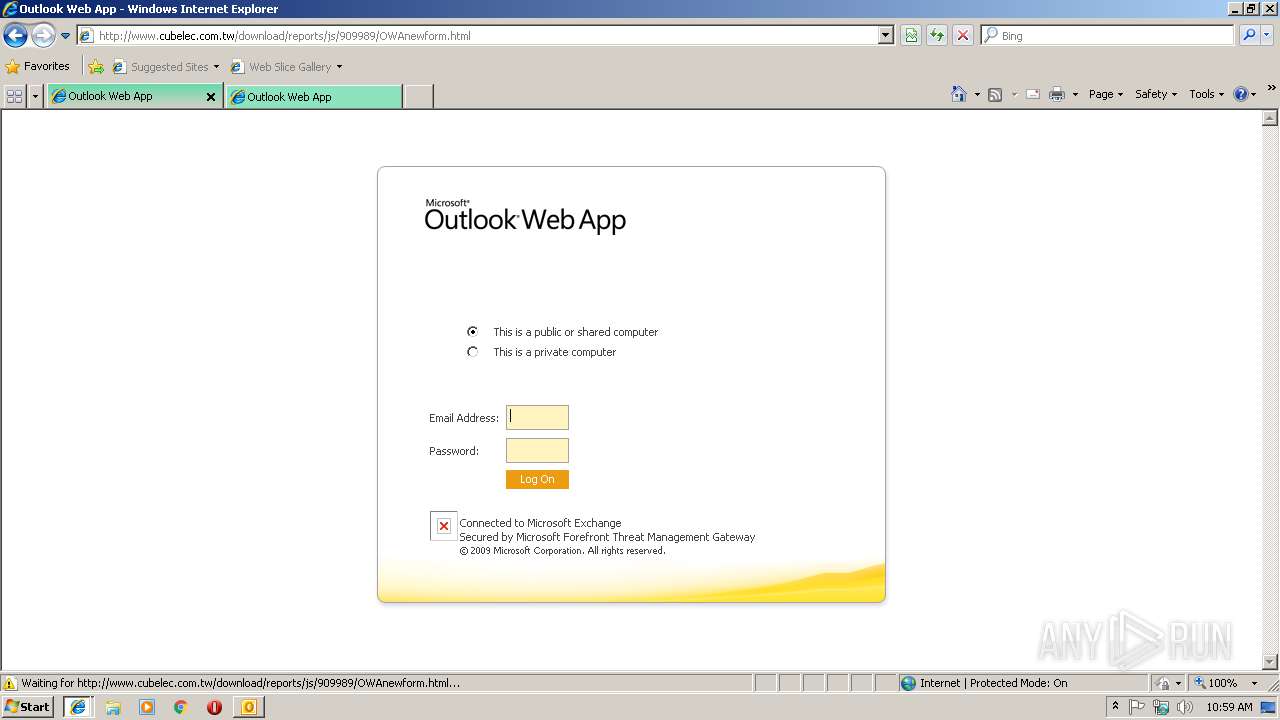
2304 | iexplore.exe | GET | — | 203.69.42.195:80 | http://www.cubelec.com.tw/CookieAuth.dll?GetPic?formdir=1&image=favicon.ico | TW | — | — | suspicious |
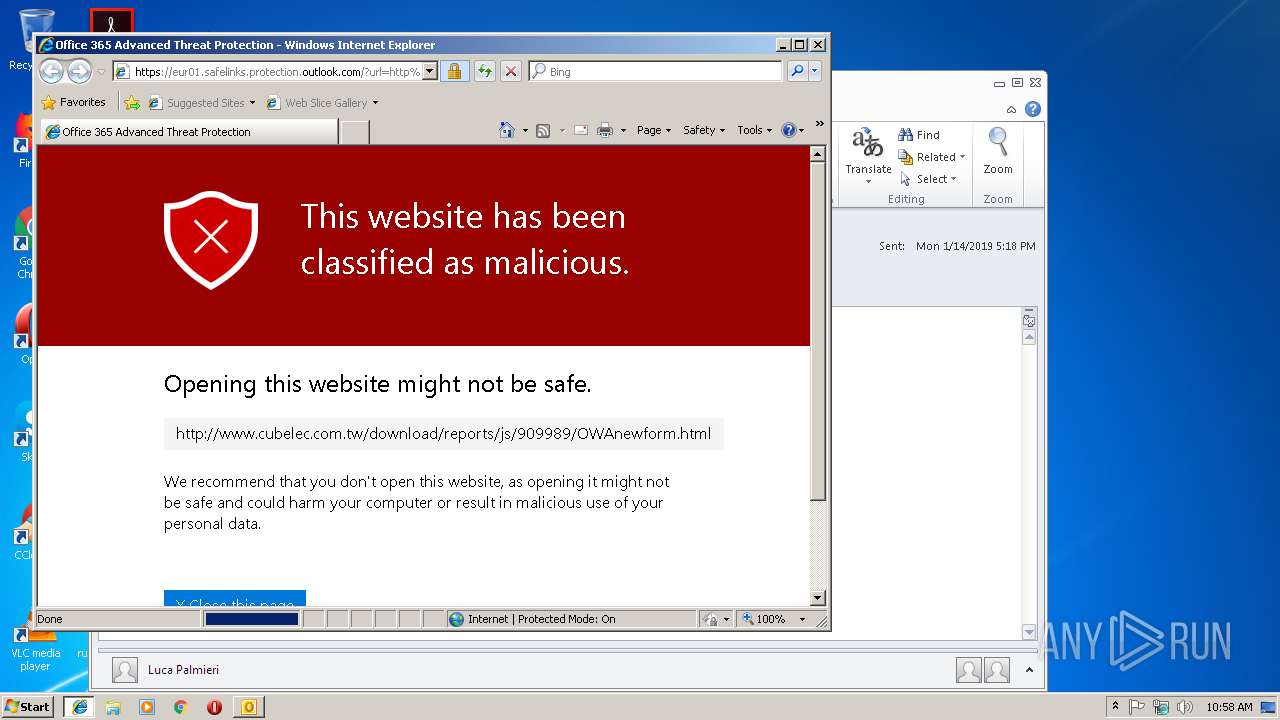
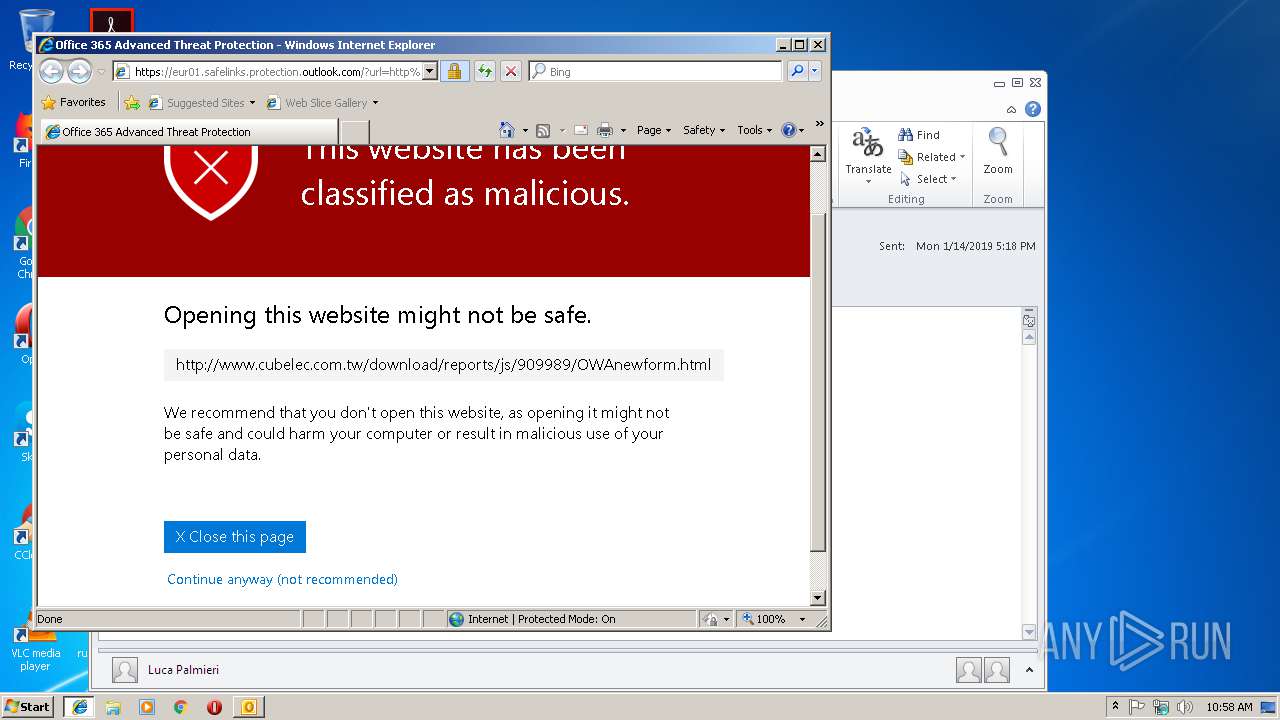
3056 | iexplore.exe | GET | 200 | 203.69.42.195:80 | http://www.cubelec.com.tw/download/reports/js/909989/OWAnewform.html | TW | html | 9.32 Kb | suspicious |
3056 | iexplore.exe | GET | 200 | 67.26.115.254:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.2 Kb | whitelisted |
3056 | iexplore.exe | GET | 200 | 2.16.186.56:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | compressed | 55.2 Kb | whitelisted |
2304 | iexplore.exe | GET | 404 | 203.69.42.195:80 | http://www.cubelec.com.tw/CookieAuth.dll?GetPic?formdir=1&image=favicon.ico | TW | xml | 992 b | suspicious |
3056 | iexplore.exe | GET | 404 | 203.69.42.195:80 | http://www.cubelec.com.tw/CookieAuth.dll?GetPic?formdir=1&image=lgnexlogo.gif | TW | xml | 1.18 Kb | suspicious |
1972 | iexplore.exe | GET | 404 | 203.69.42.195:80 | http://www.cubelec.com.tw/CookieAuth.dll?GetPic?formdir=1&image=lgnexlogo.gif | TW | xml | 1.18 Kb | suspicious |
1972 | iexplore.exe | GET | 200 | 203.69.42.195:80 | http://www.cubelec.com.tw/download/reports/js/909989/OWAnewform.html | TW | html | 9.32 Kb | suspicious |
3004 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
2304 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3056 | iexplore.exe | 67.26.115.254:80 | www.download.windowsupdate.com | Level 3 Communications, Inc. | US | unknown |
3056 | iexplore.exe | 2.16.186.56:80 | www.download.windowsupdate.com | Akamai International B.V. | — | whitelisted |
1972 | iexplore.exe | 203.69.42.195:80 | www.cubelec.com.tw | Data Communication Business Group | TW | suspicious |
2304 | iexplore.exe | 203.69.42.195:80 | www.cubelec.com.tw | Data Communication Business Group | TW | suspicious |
1972 | iexplore.exe | 162.130.196.190:443 | owa.marriott.com | Marriot Corporation | US | unknown |
3004 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
3056 | iexplore.exe | 157.56.112.46:443 | emea01.safelinks.protection.outlook.com | Microsoft Corporation | US | whitelisted |
2304 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2304 | iexplore.exe | 104.47.1.28:443 | eur01.safelinks.protection.outlook.com | Microsoft Corporation | AT | whitelisted |
3056 | iexplore.exe | 203.69.42.195:80 | www.cubelec.com.tw | Data Communication Business Group | TW | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
emea01.safelinks.protection.outlook.com |
| whitelisted |
www.bing.com |
| whitelisted |
eur01.safelinks.protection.outlook.com |
| whitelisted |
www.cubelec.com.tw |
| suspicious |
owa.marriott.com |
| unknown |
www.download.windowsupdate.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3056 | iexplore.exe | Potentially Bad Traffic | ET CURRENT_EVENTS Possible OWA Mail Phishing Landing - Title over non SSL |
1972 | iexplore.exe | Potentially Bad Traffic | ET CURRENT_EVENTS Possible OWA Mail Phishing Landing - Title over non SSL |