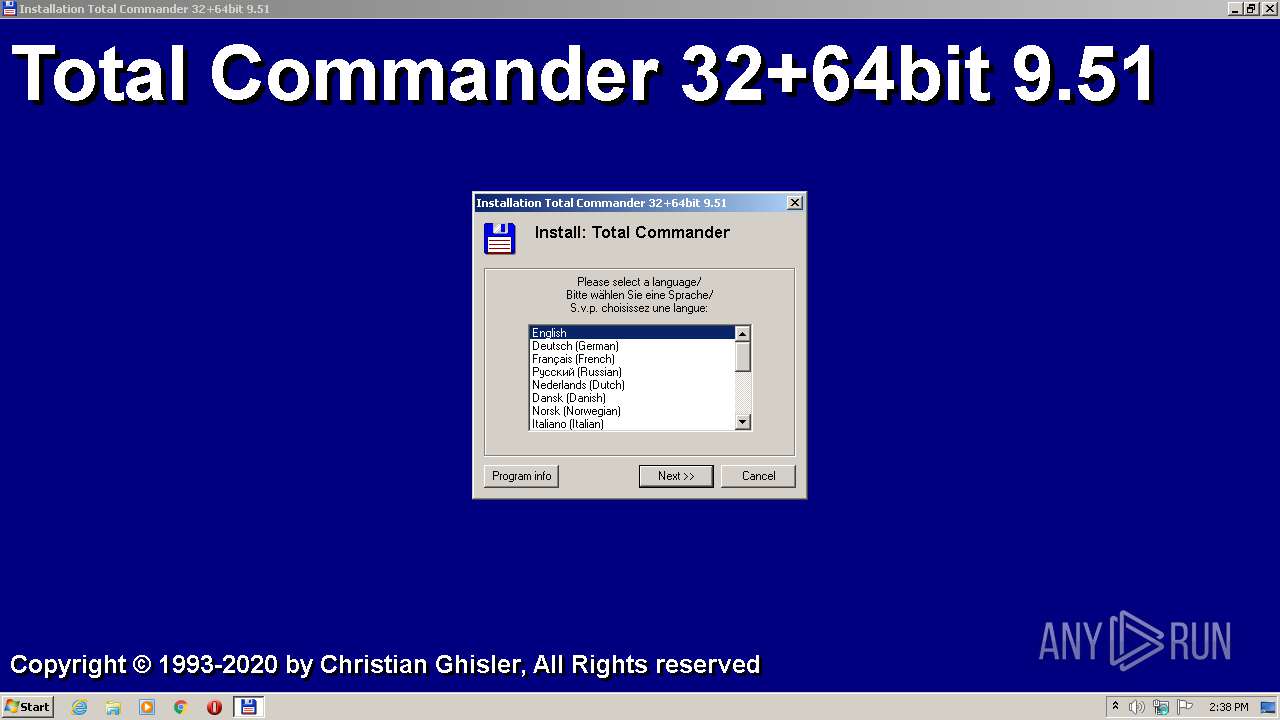
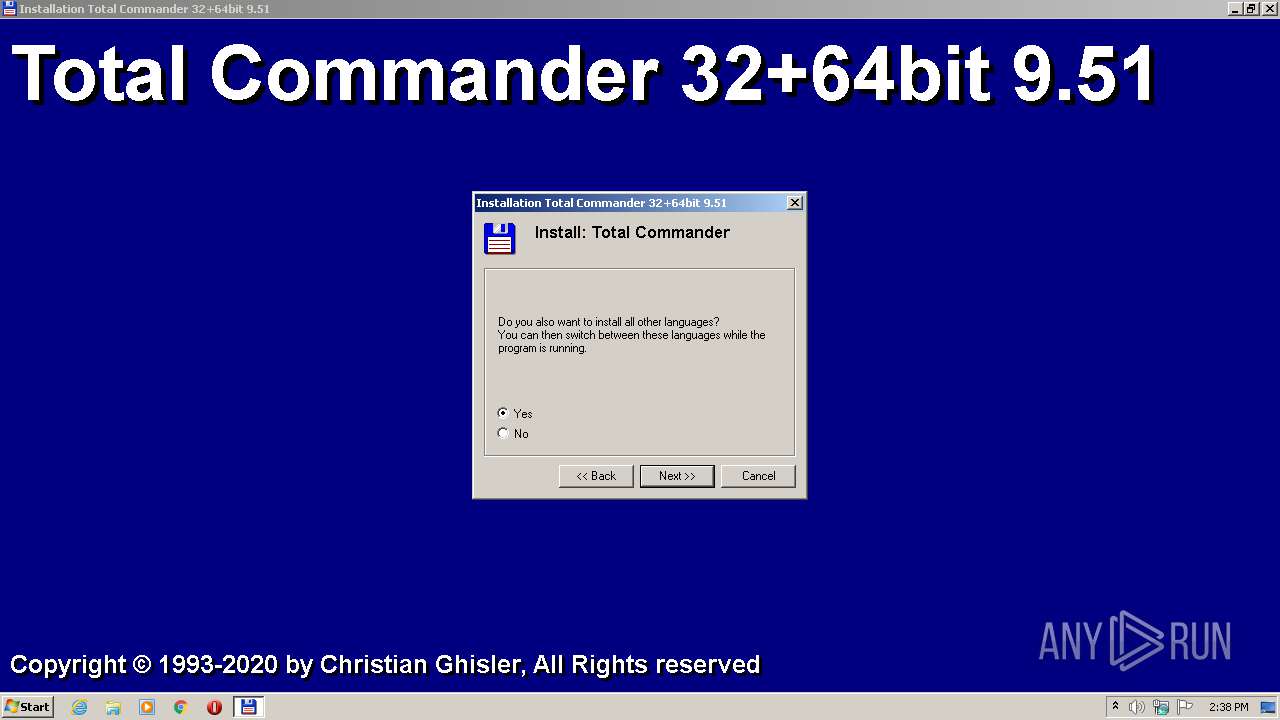
| File name: | tcmd951x32_64.exe |
| Full analysis: | https://app.any.run/tasks/d9933dd9-5197-432e-b51a-51baa0a4a9c9 |
| Verdict: | Malicious activity |
| Analysis date: | August 27, 2020, 13:37:41 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, InstallShield self-extracting archive |
| MD5: | F5F66AC1A808E40C00FC6E9C88420CFA |
| SHA1: | 011F15F4D063698660052671201C420CF673FF75 |
| SHA256: | 2D2115049AEA04C0AF4090571F212AC553811338FA6C9EAEBFF88D6B61D35448 |
| SSDEEP: | 196608:3lh01jbJ6PnPiD3uyotWIUTyhxqVxfYClY4QmoLg02j:3X84vPnWkKlJm4/or2 |
MALICIOUS
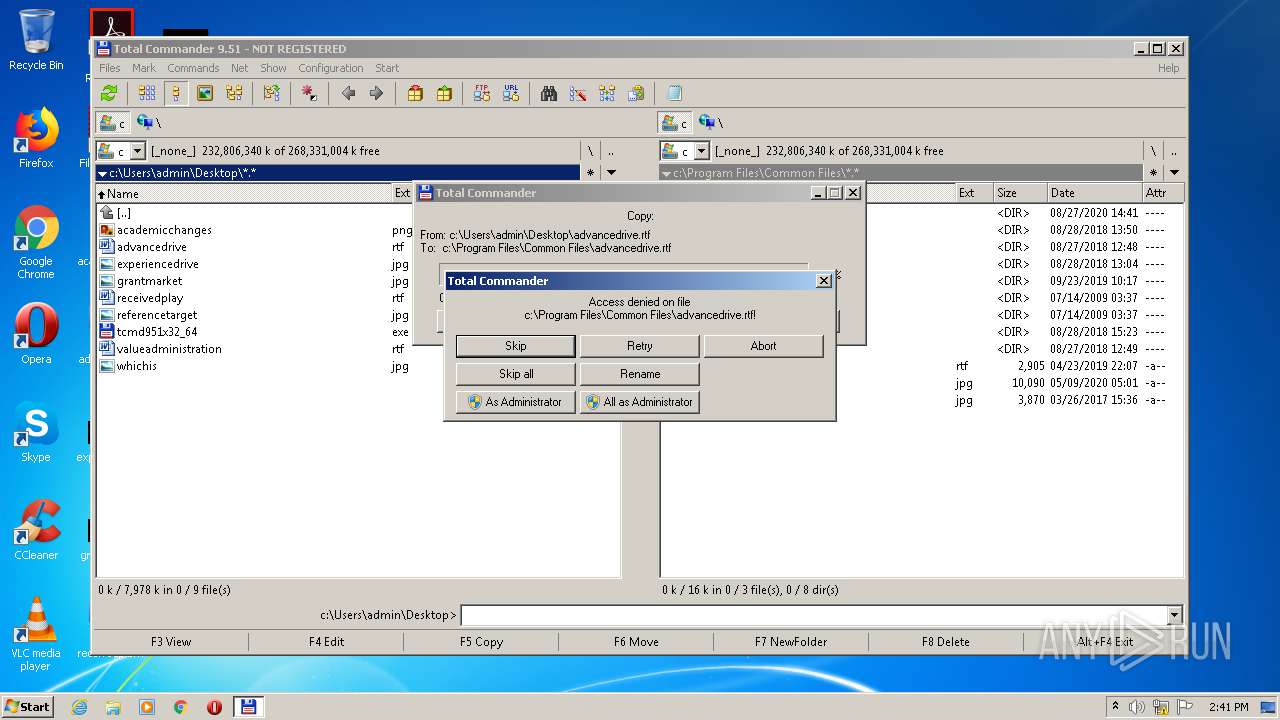
Loads dropped or rewritten executable
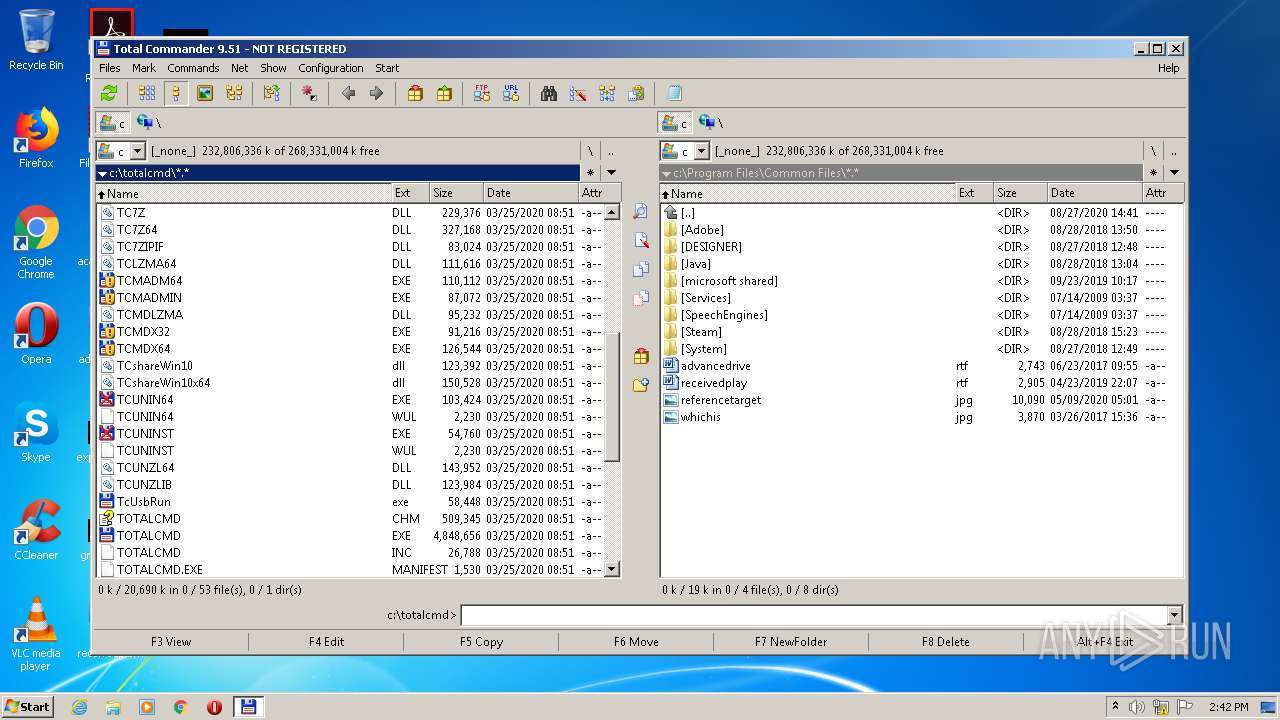
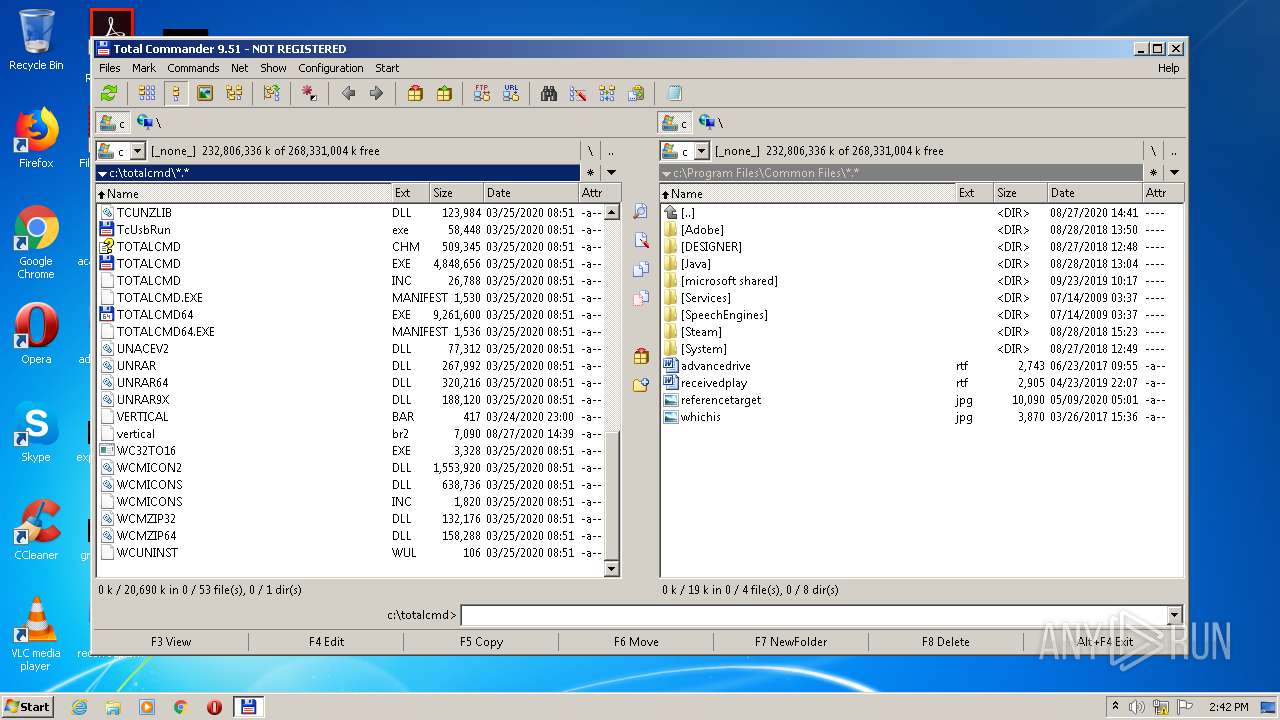
- TOTALCMD.EXE (PID: 2188)
Application was dropped or rewritten from another process
- TOTALCMD.EXE (PID: 2188)
- tcmadmin.exe (PID: 744)
SUSPICIOUS
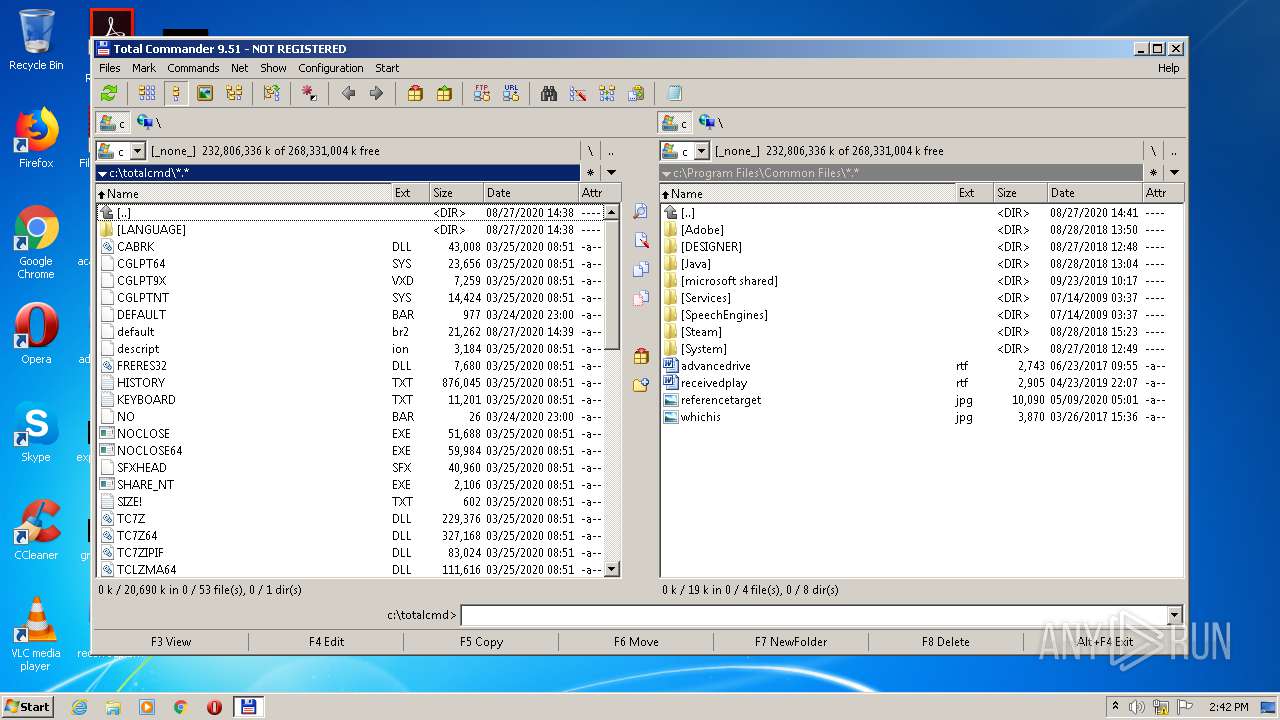
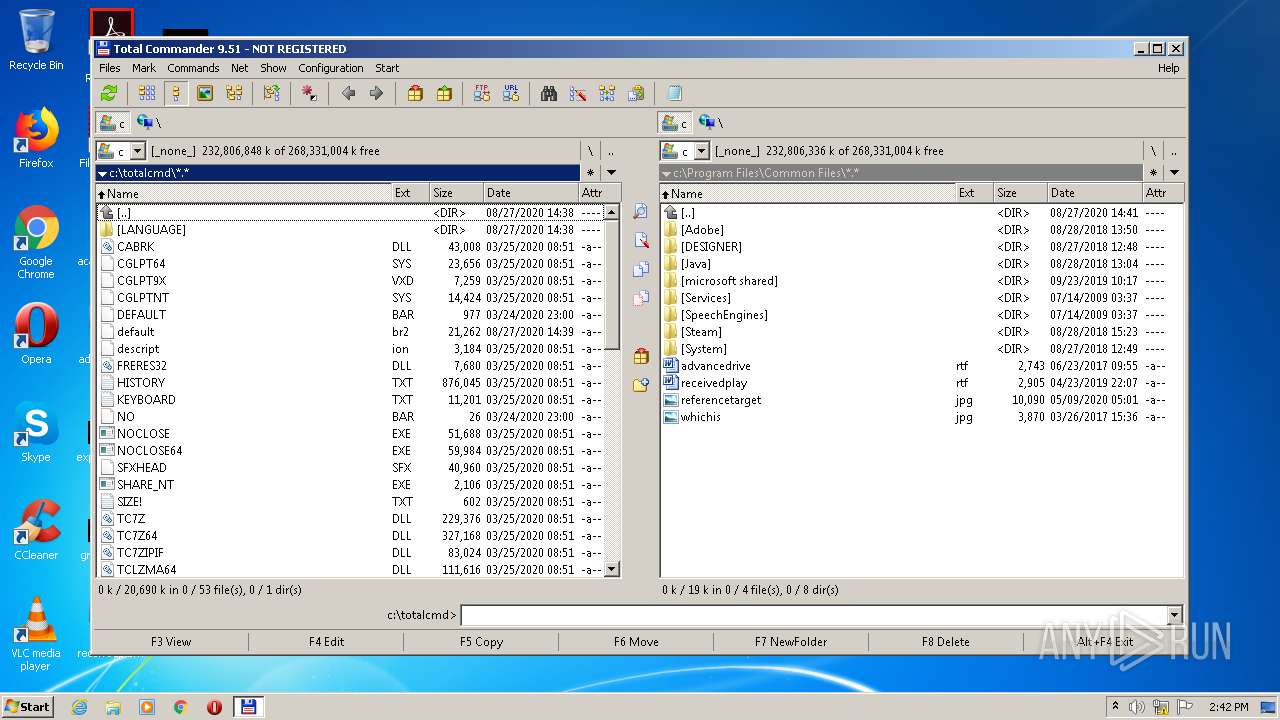
Executable content was dropped or overwritten
- tcmd951x32_64.exe (PID: 3924)
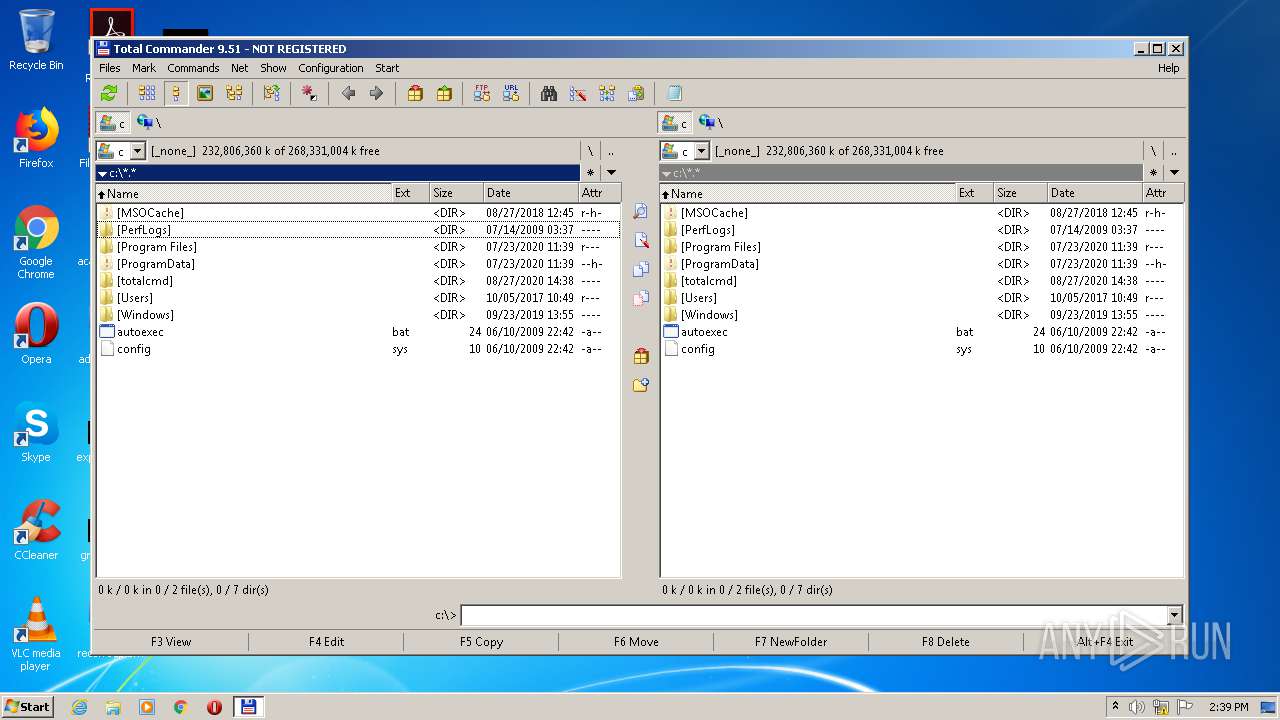
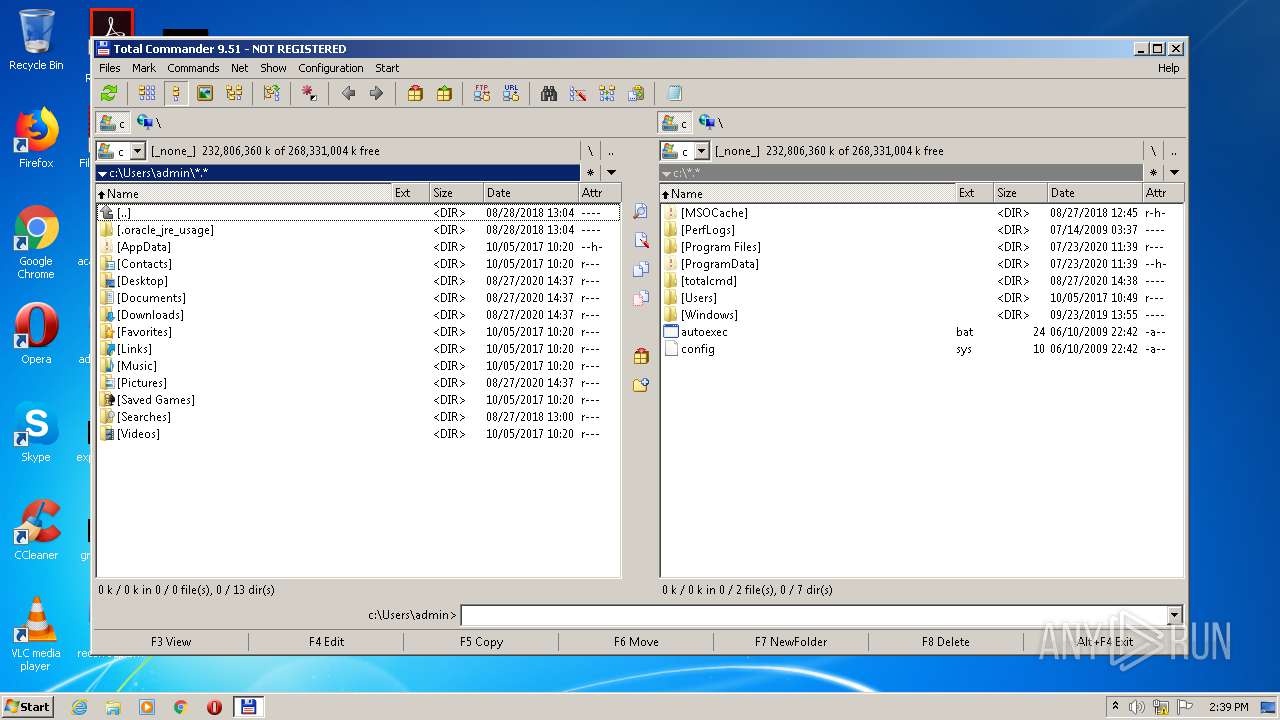
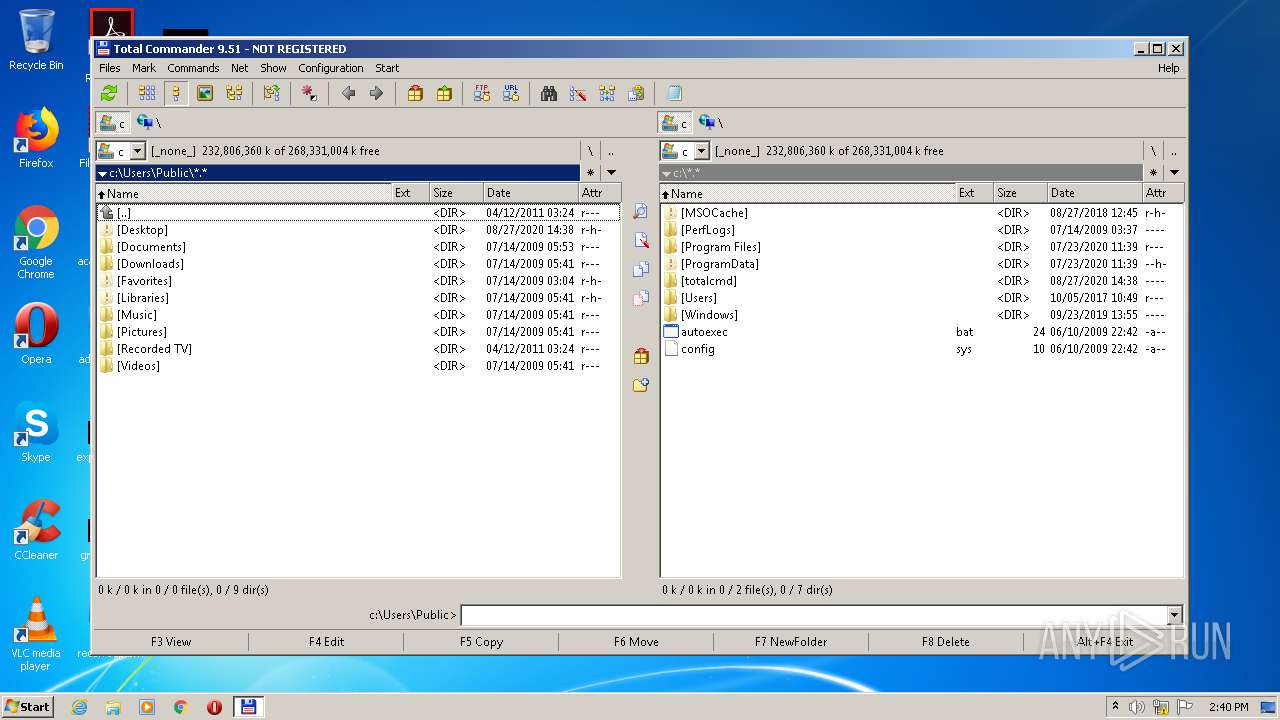
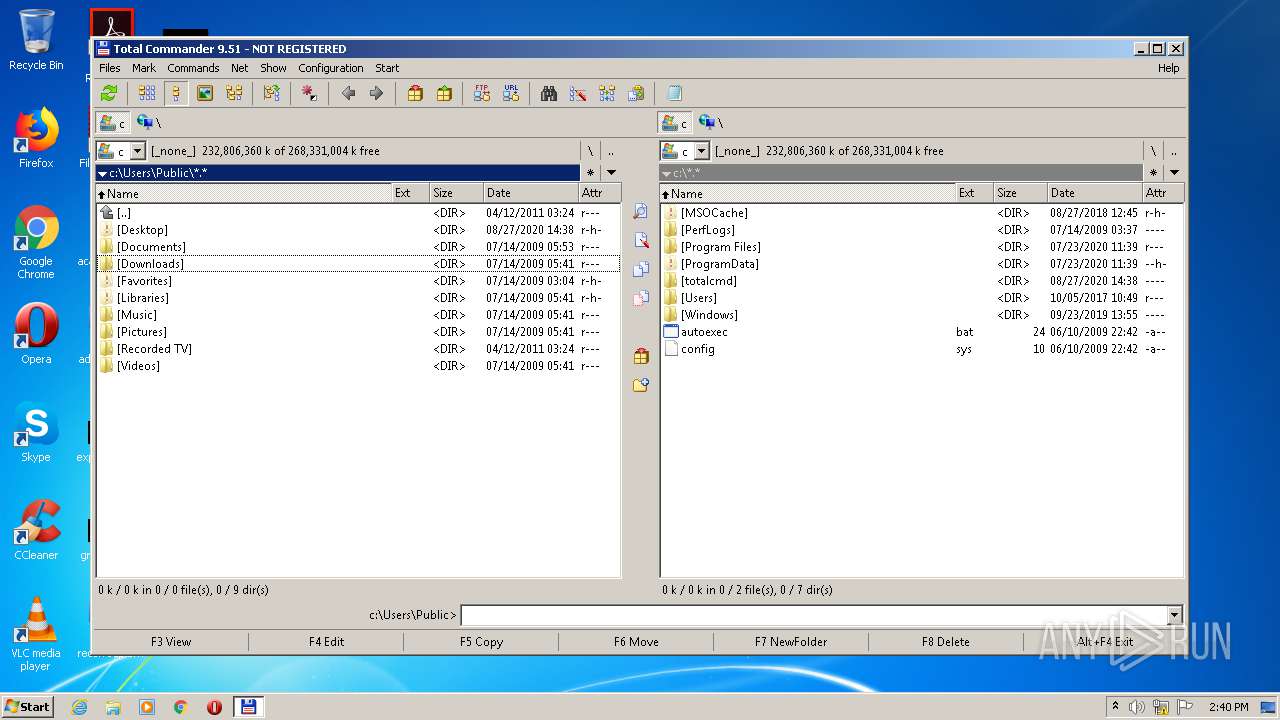
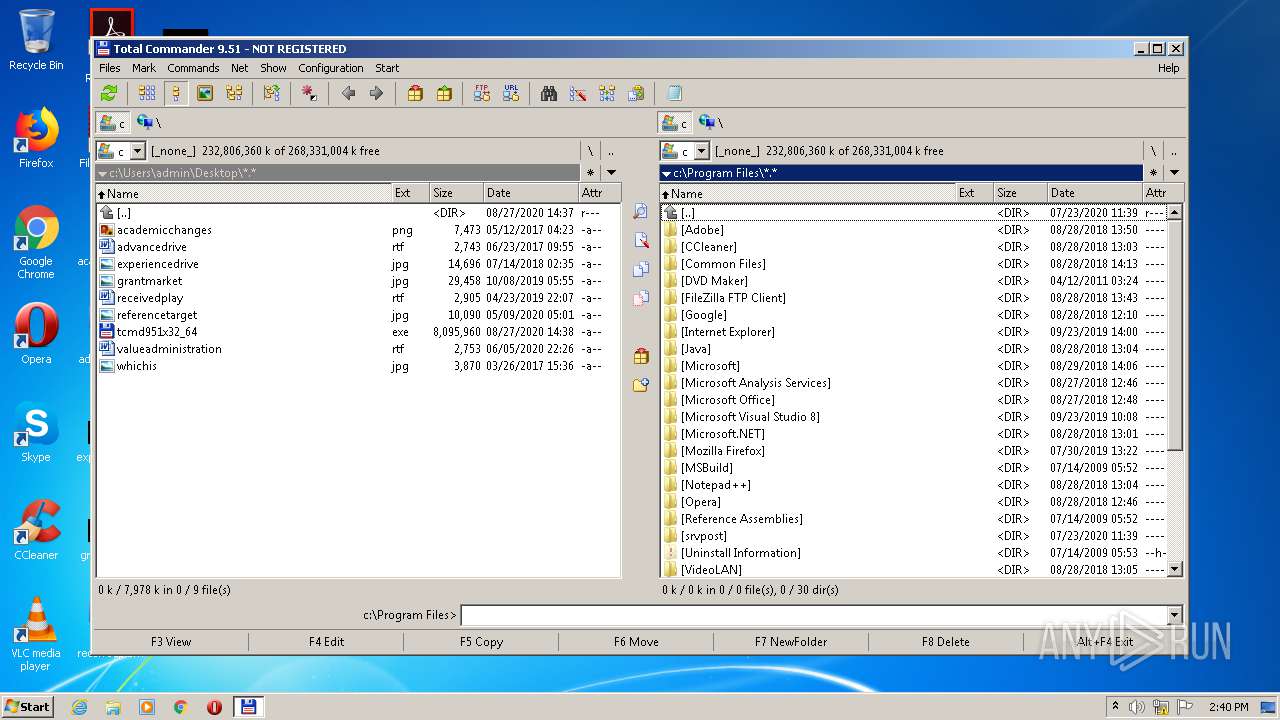
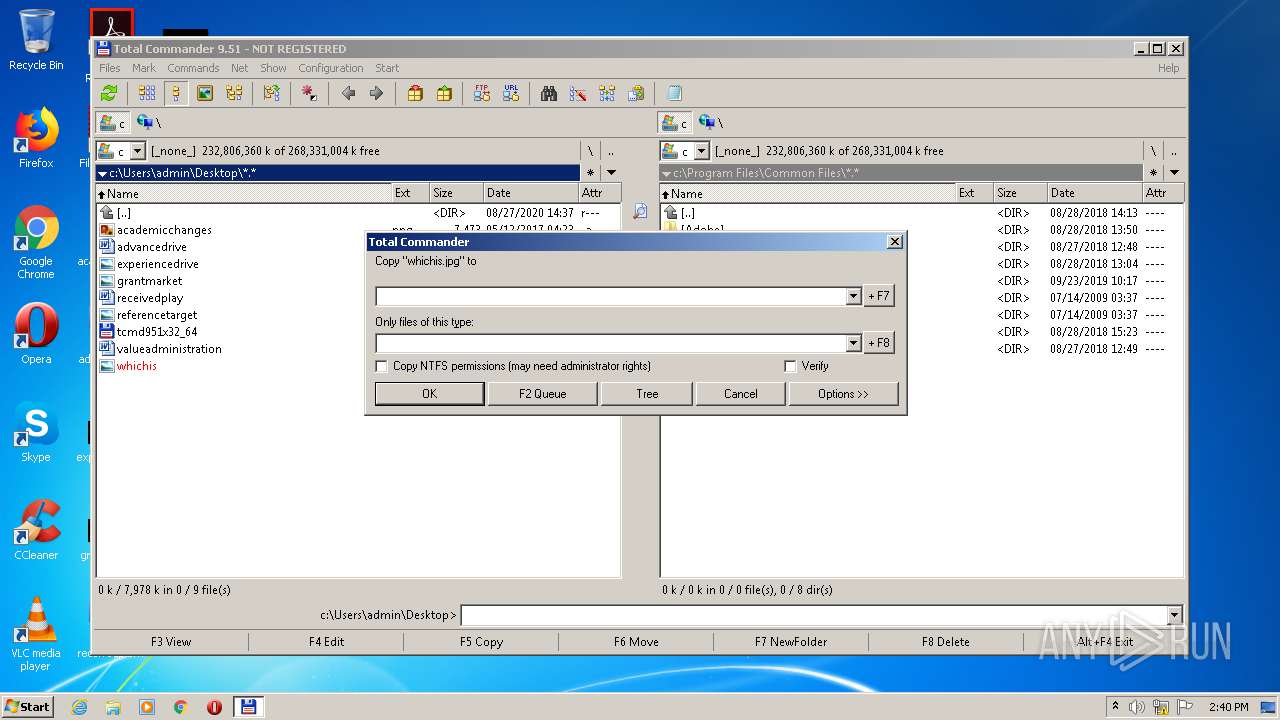
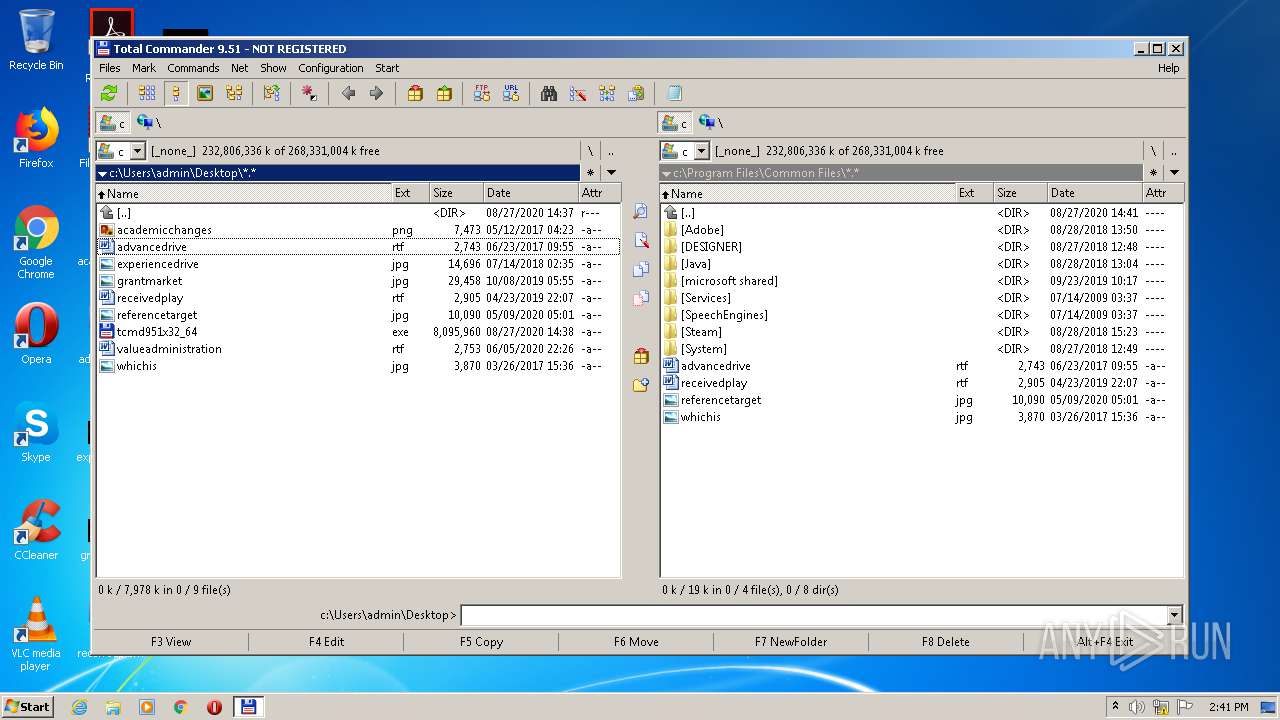
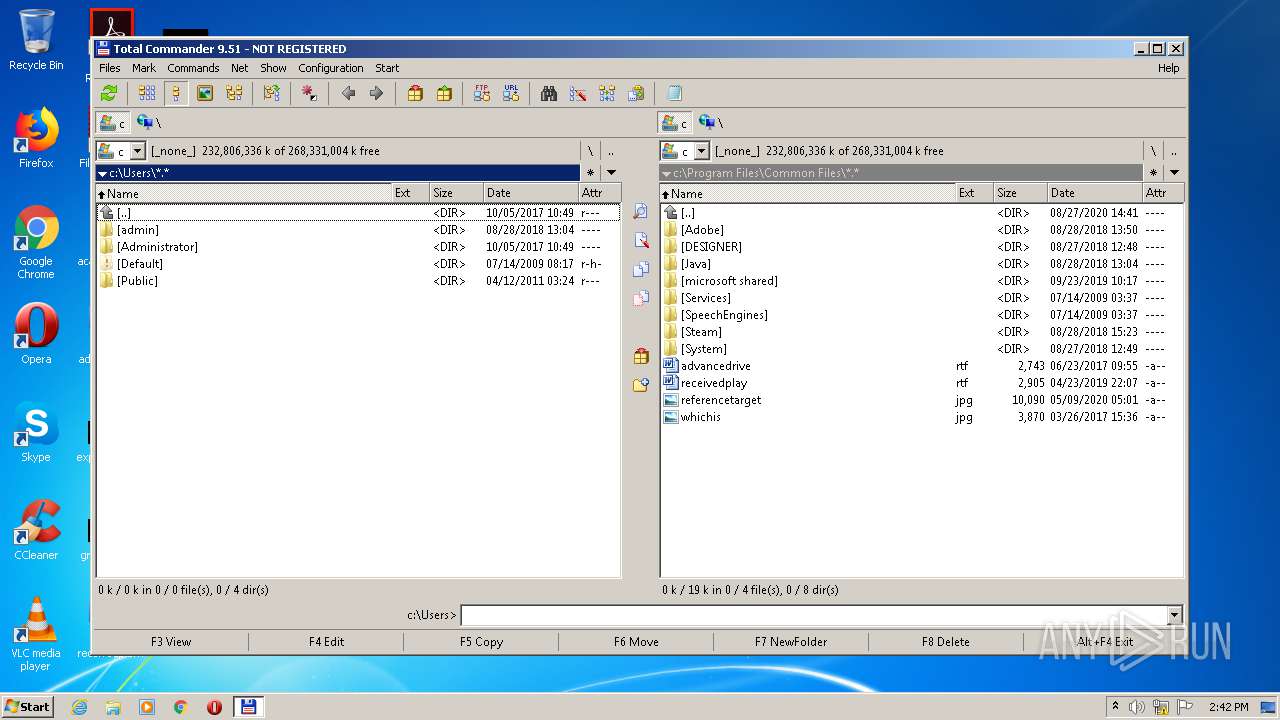
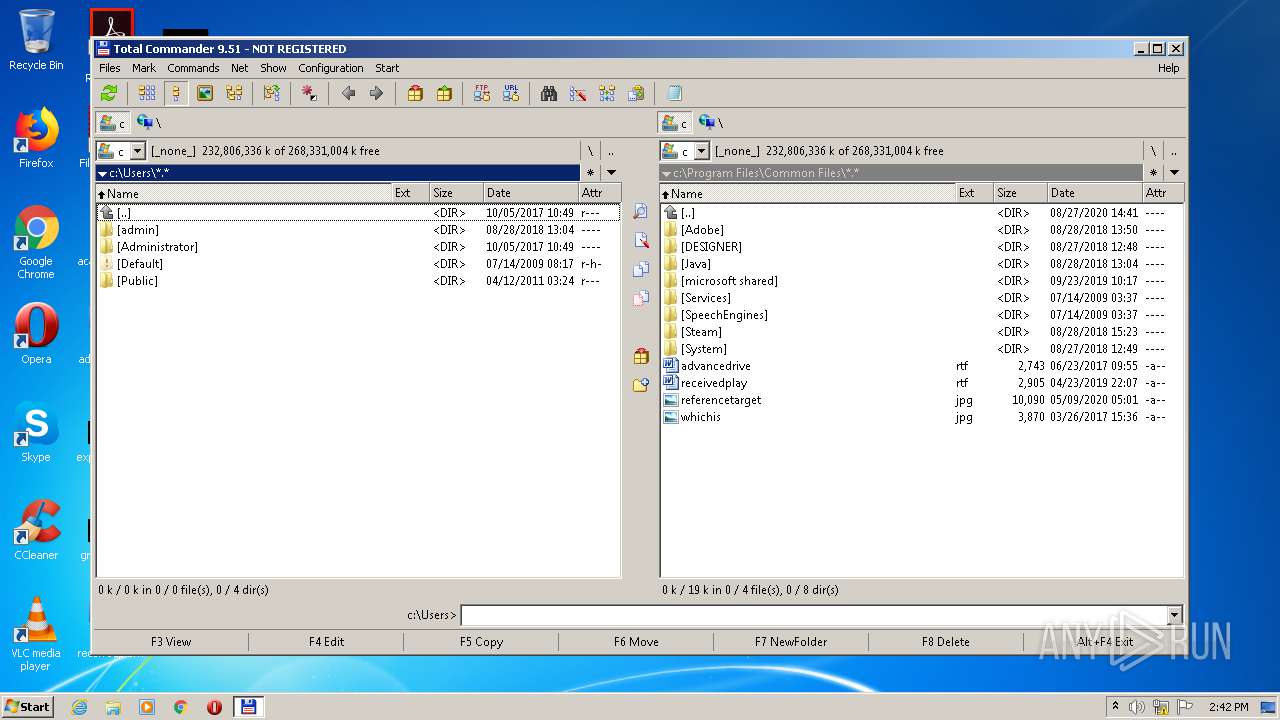
Creates files in the user directory
- tcmd951x32_64.exe (PID: 3924)
Creates a software uninstall entry
- tcmd951x32_64.exe (PID: 3924)
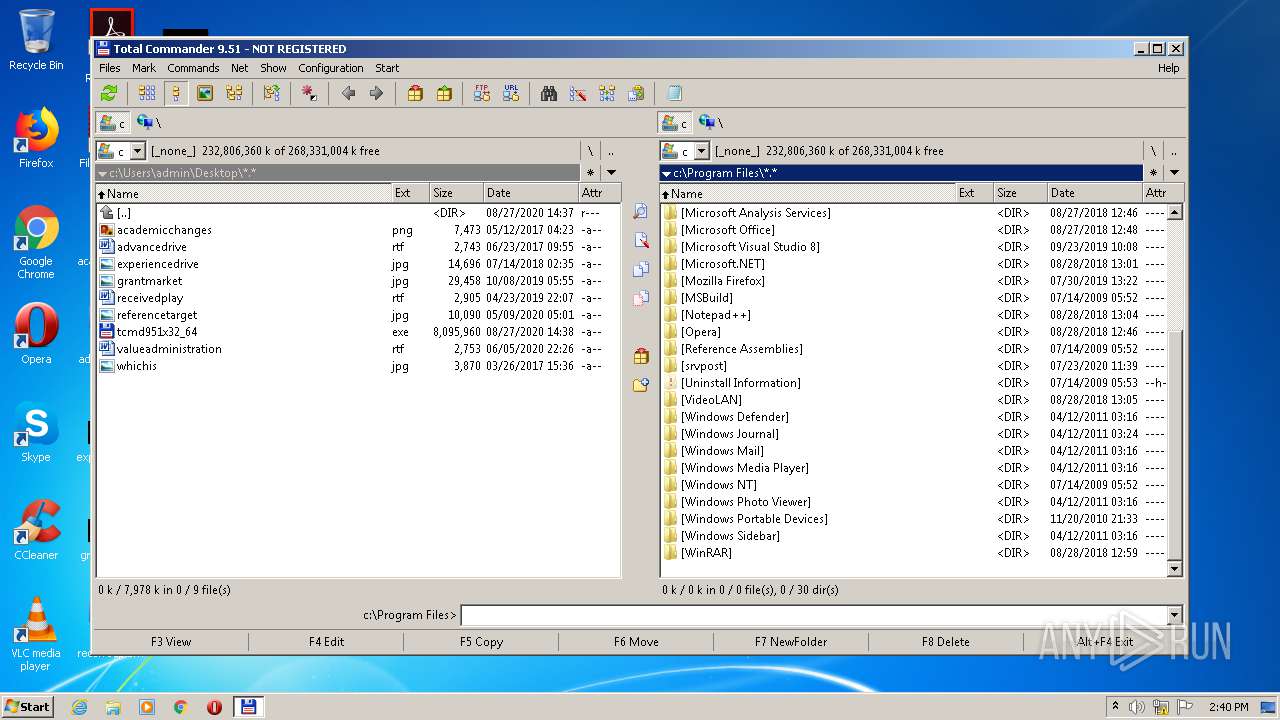
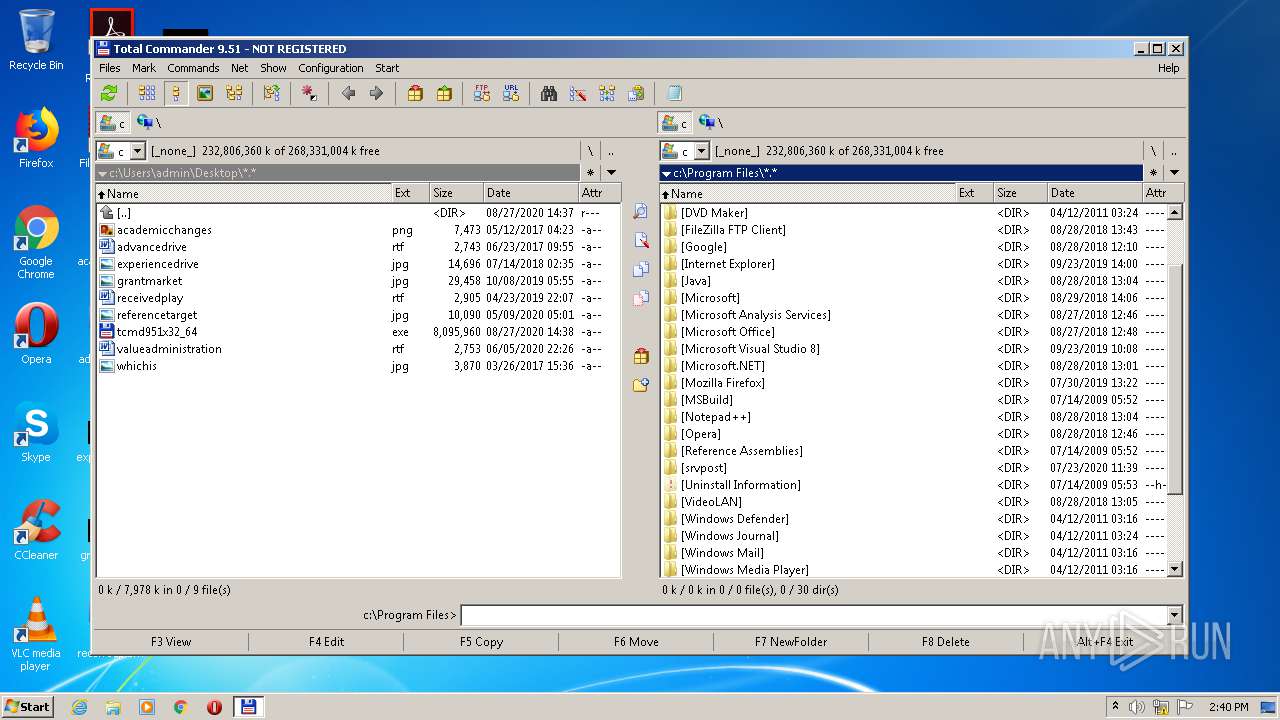
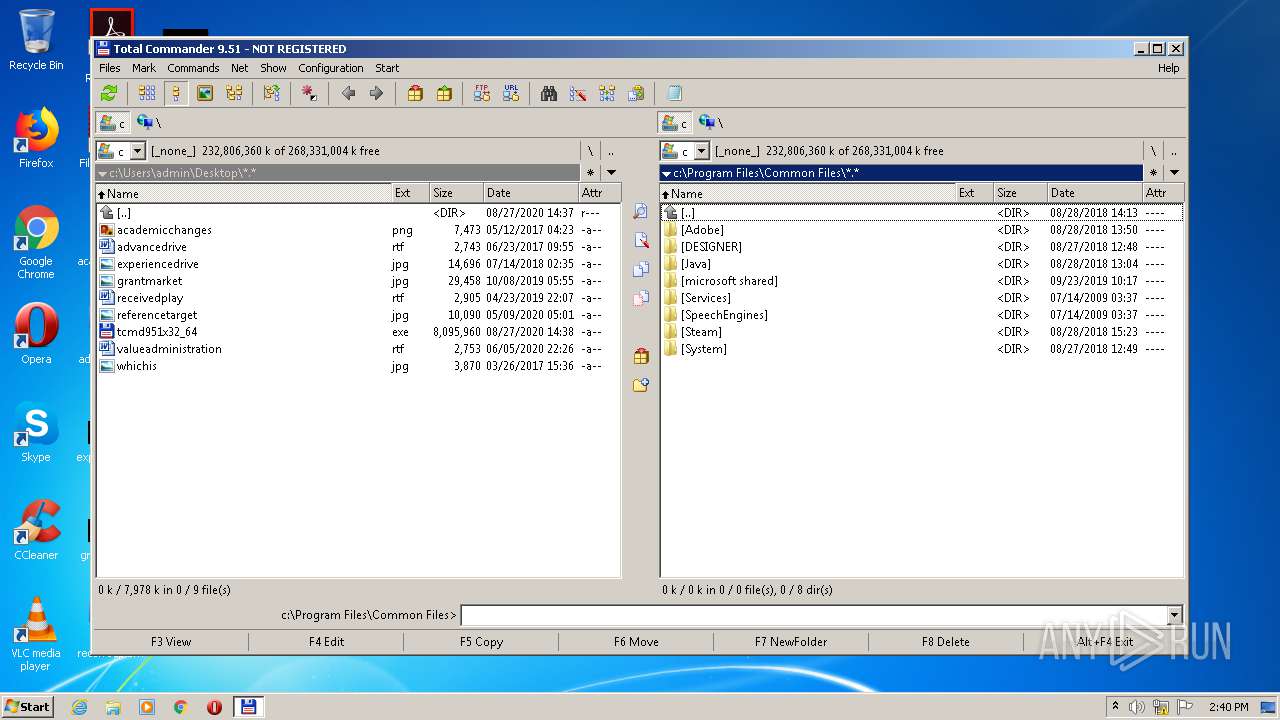
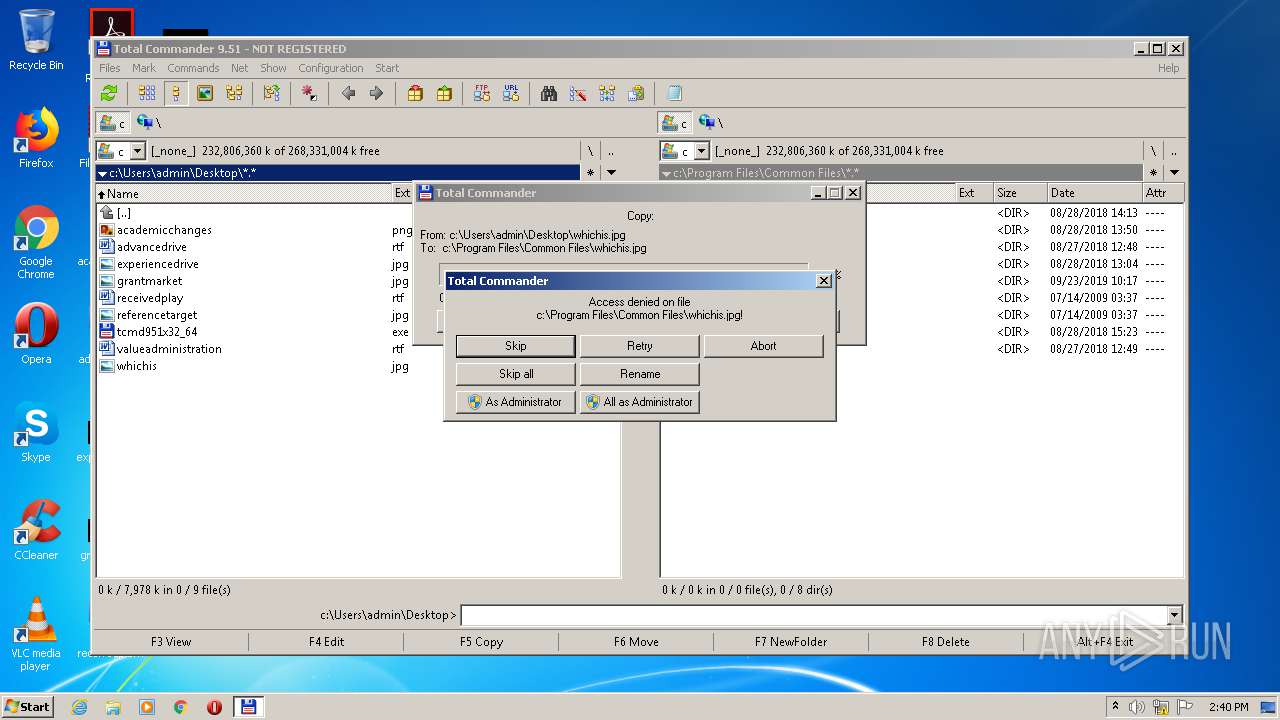
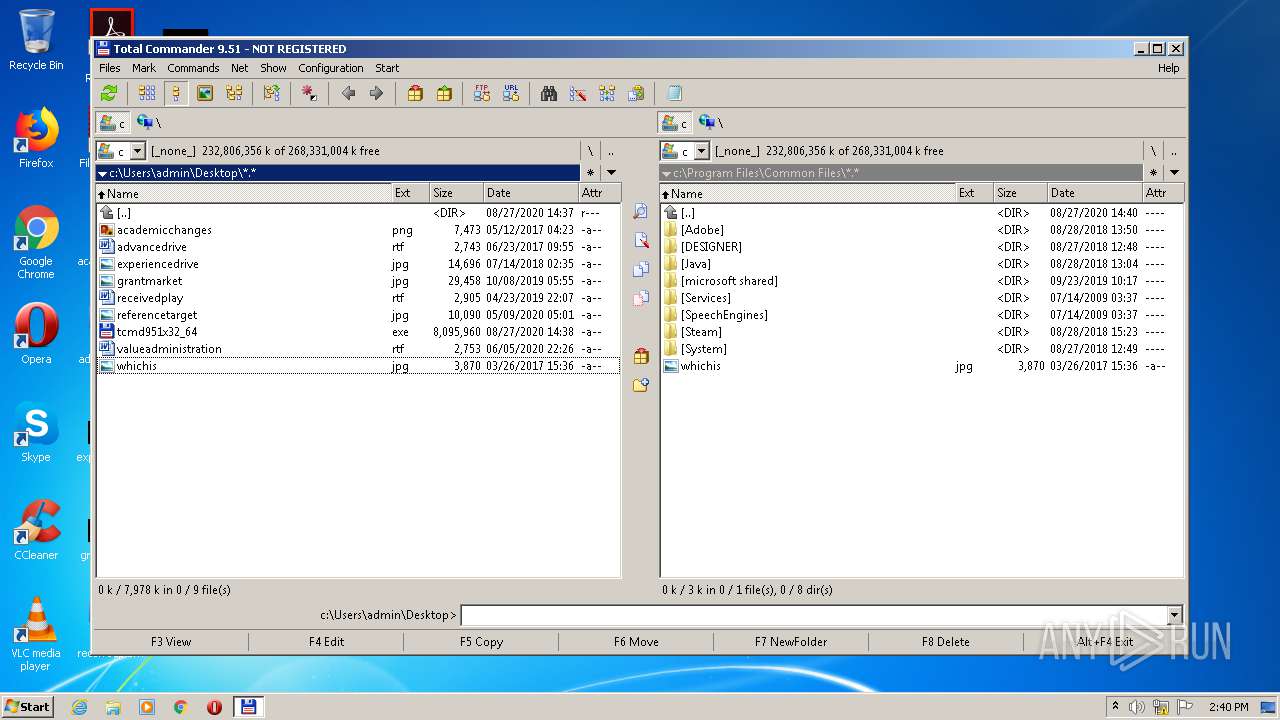
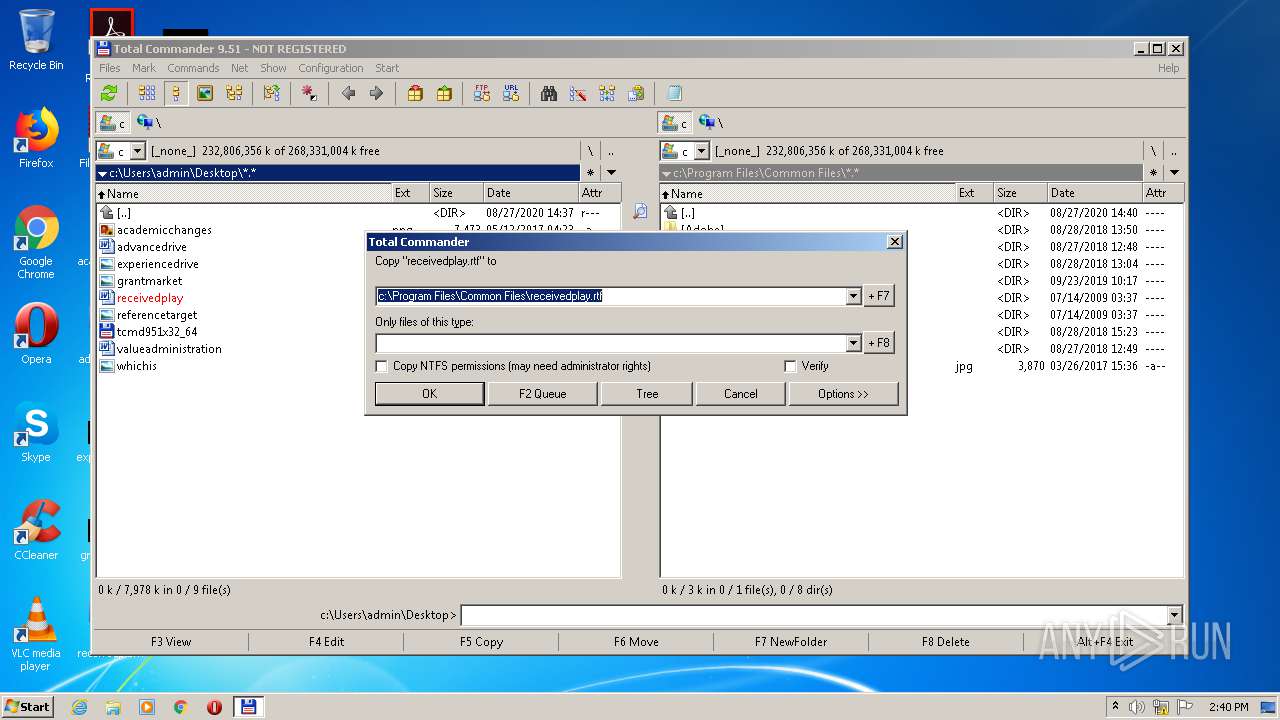
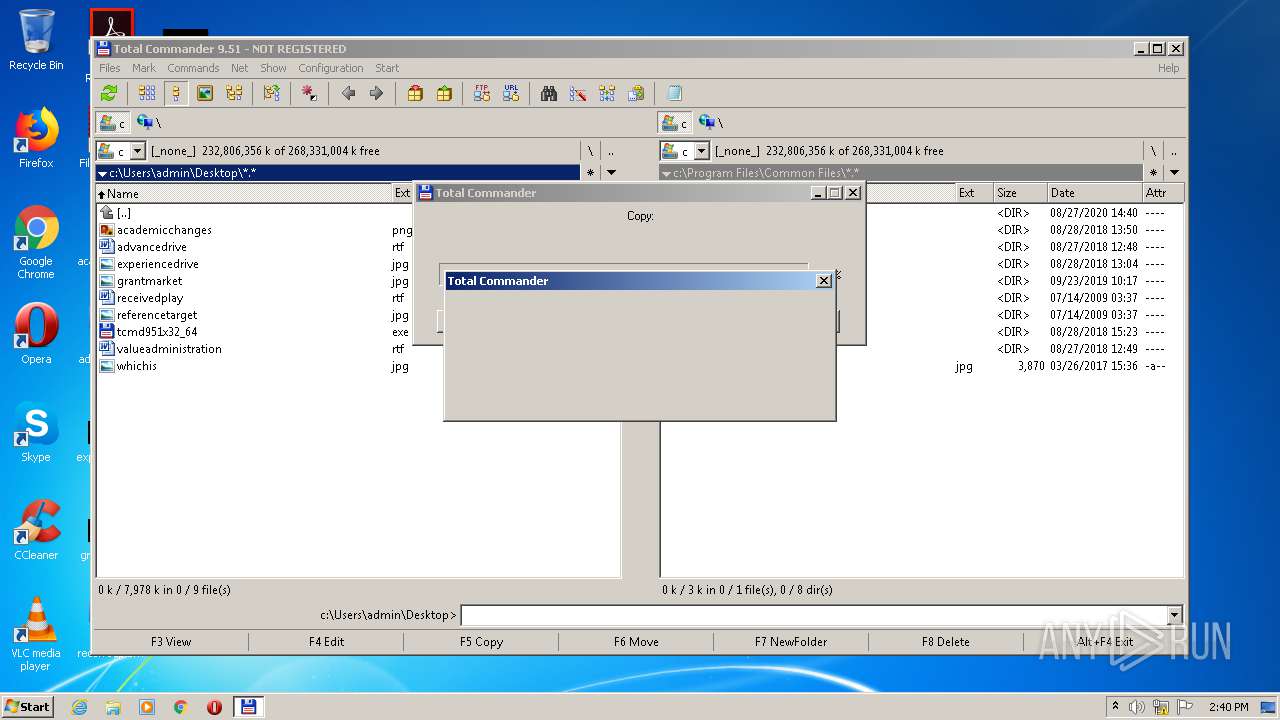
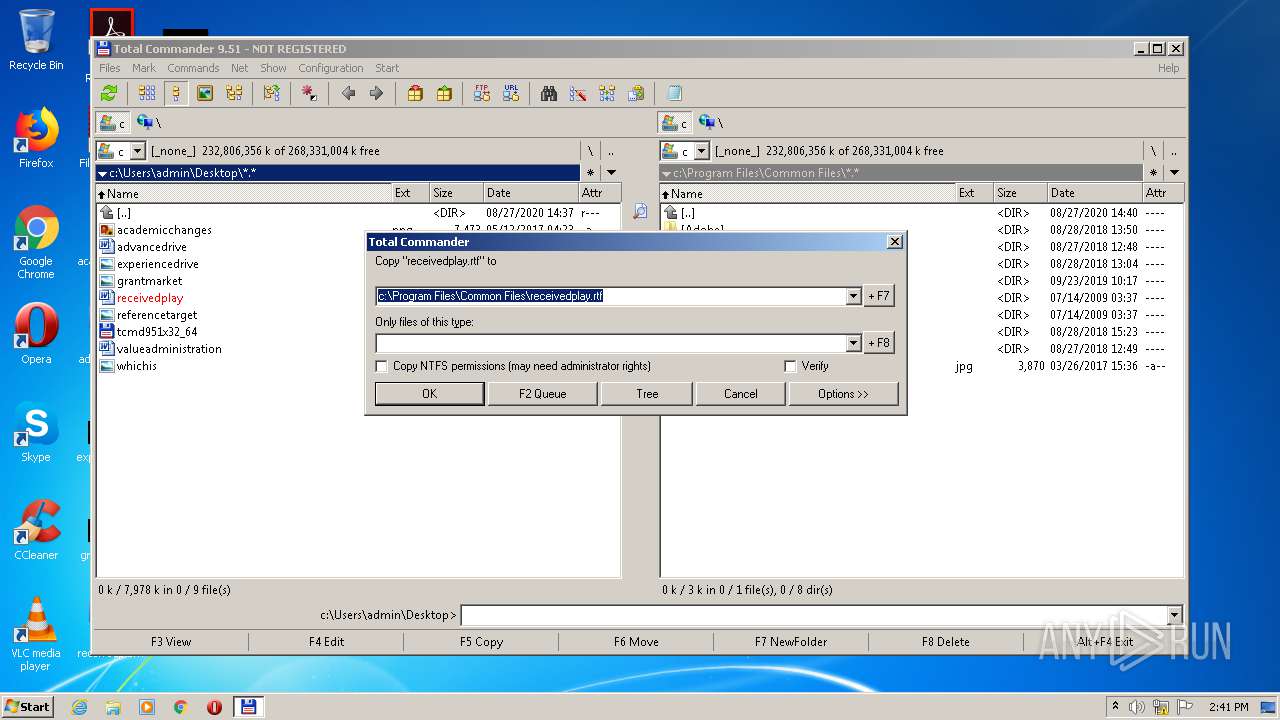
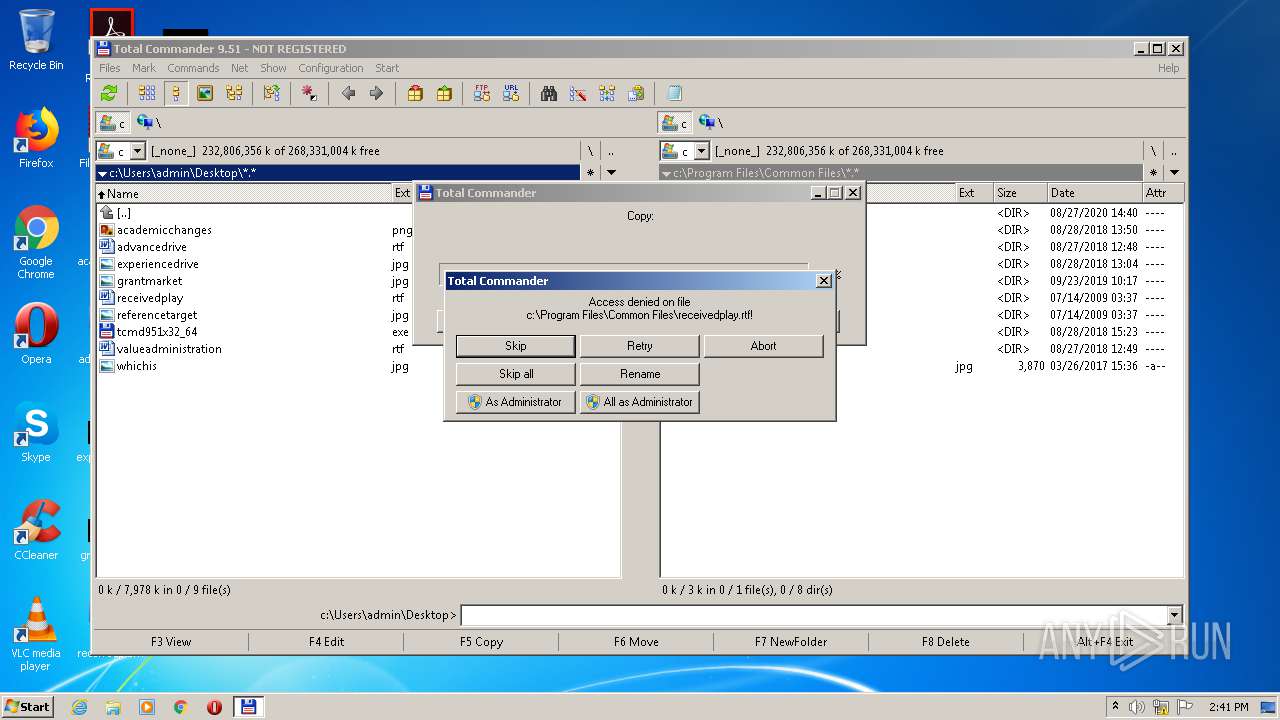
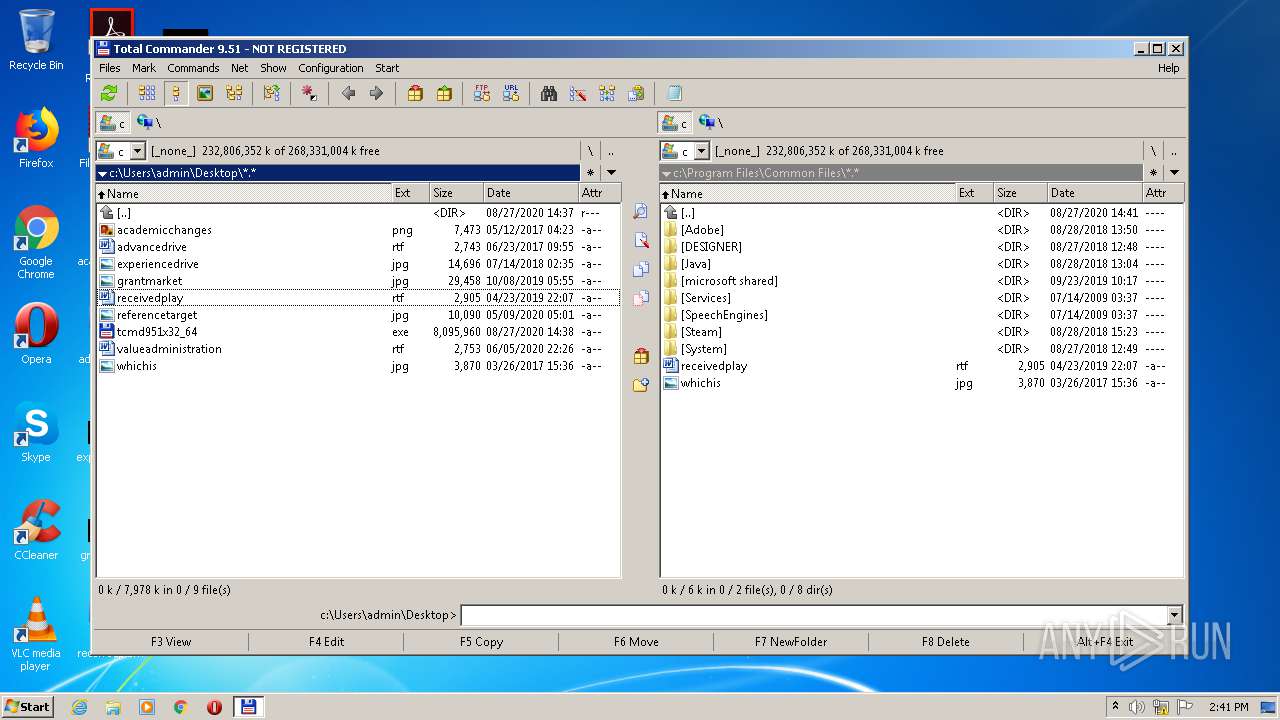
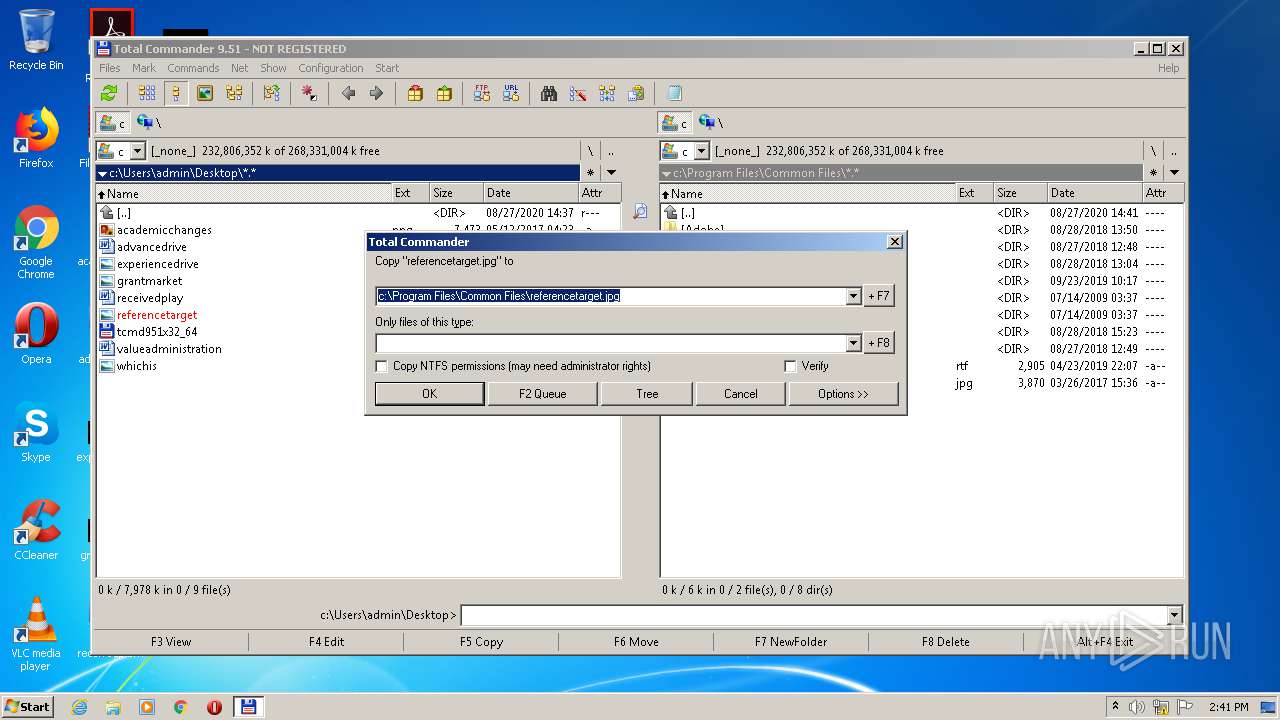
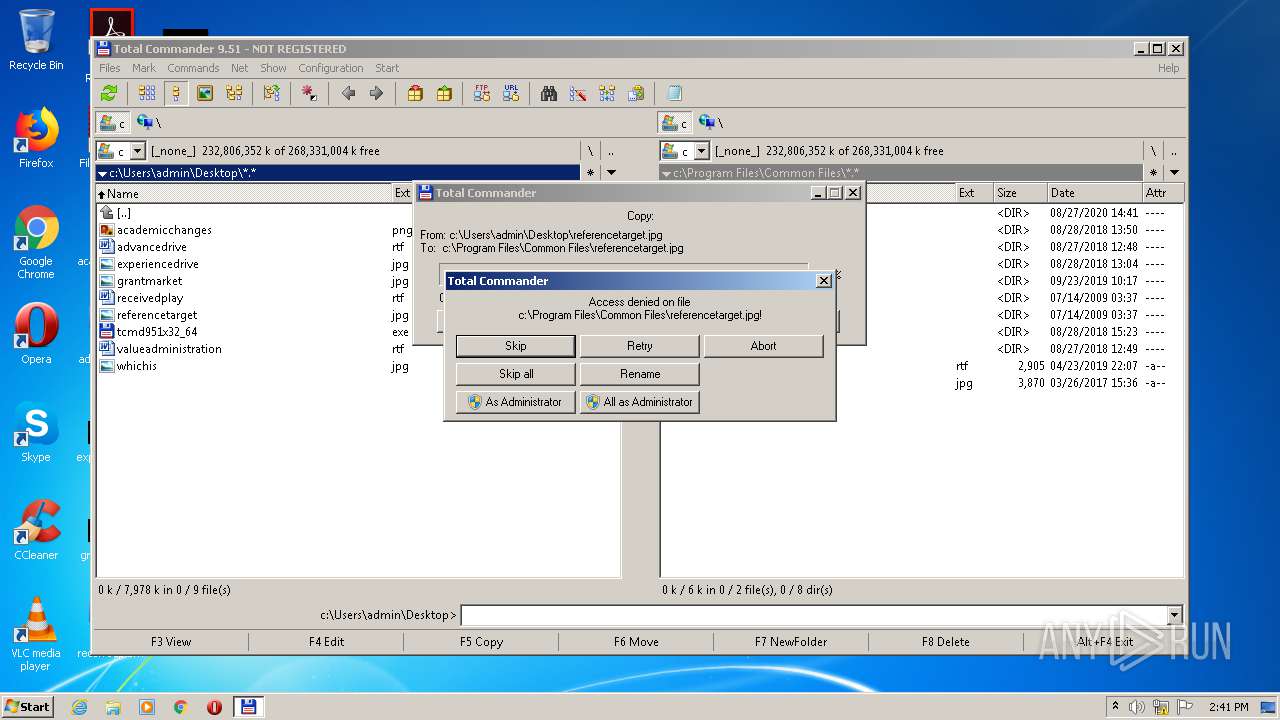
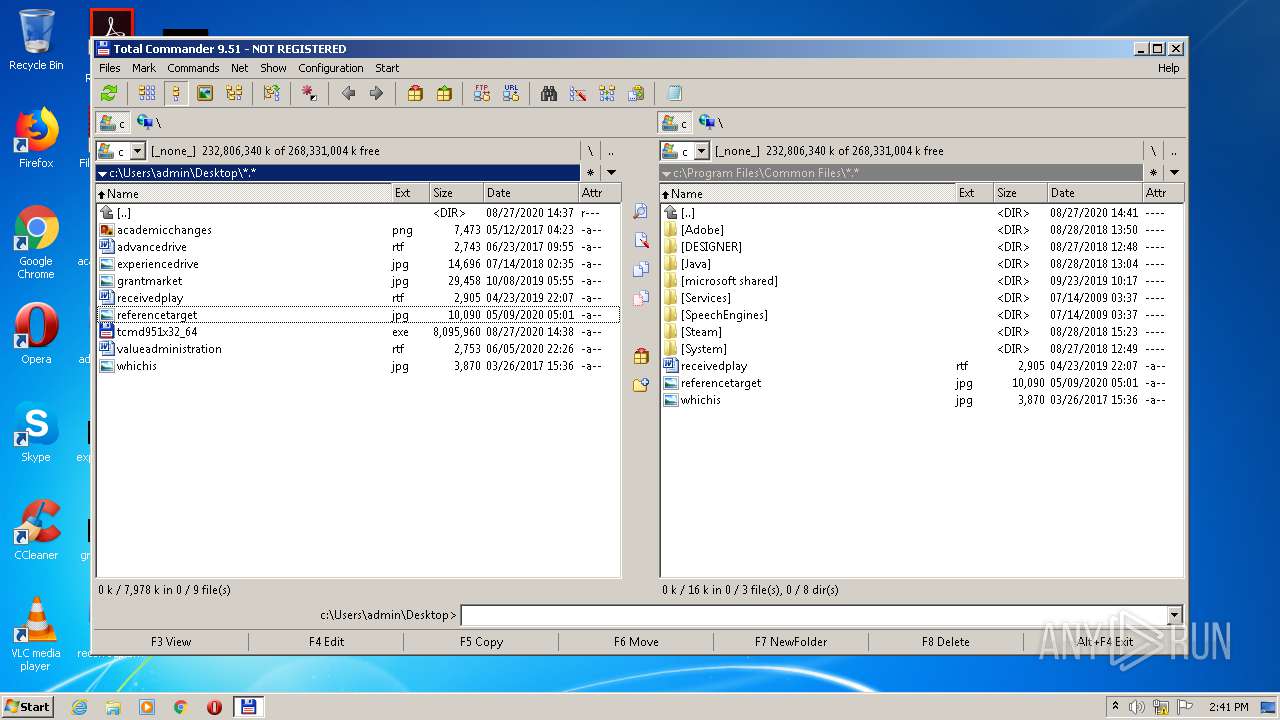
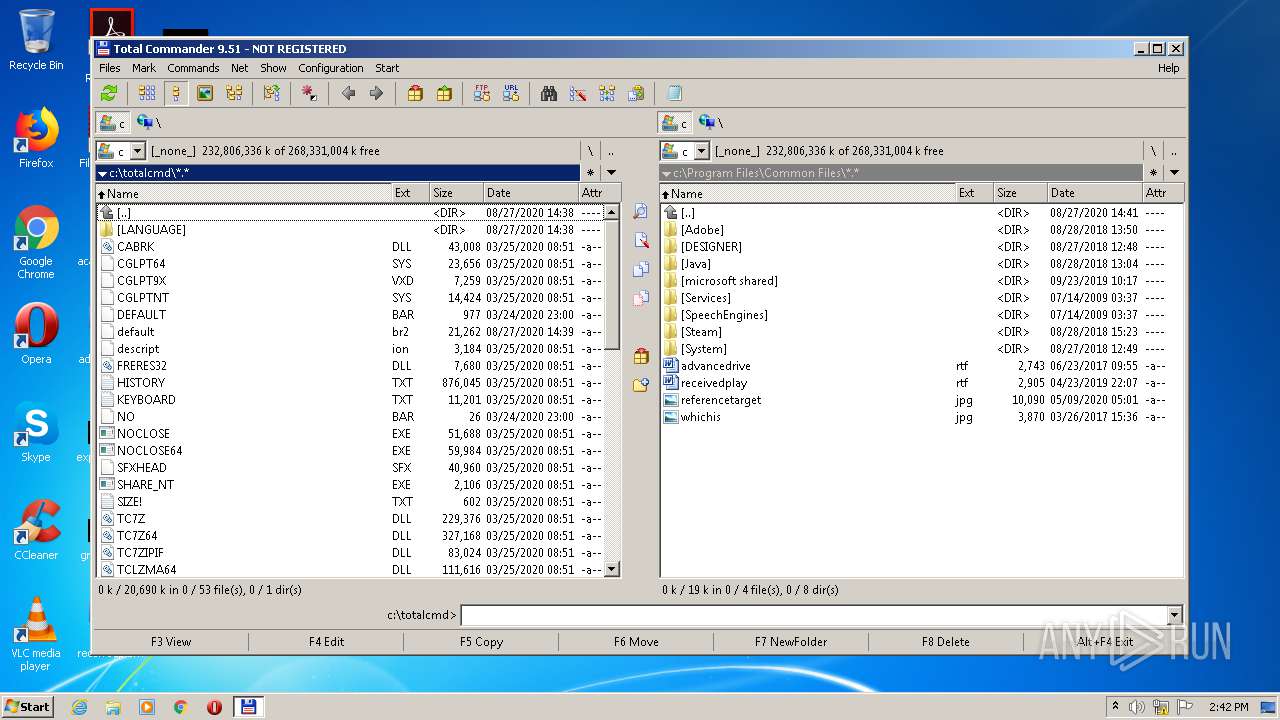
Creates files in the program directory
- tcmd951x32_64.exe (PID: 3924)
- tcmadmin.exe (PID: 744)
INFO
Dropped object may contain Bitcoin addresses
- tcmd951x32_64.exe (PID: 3924)
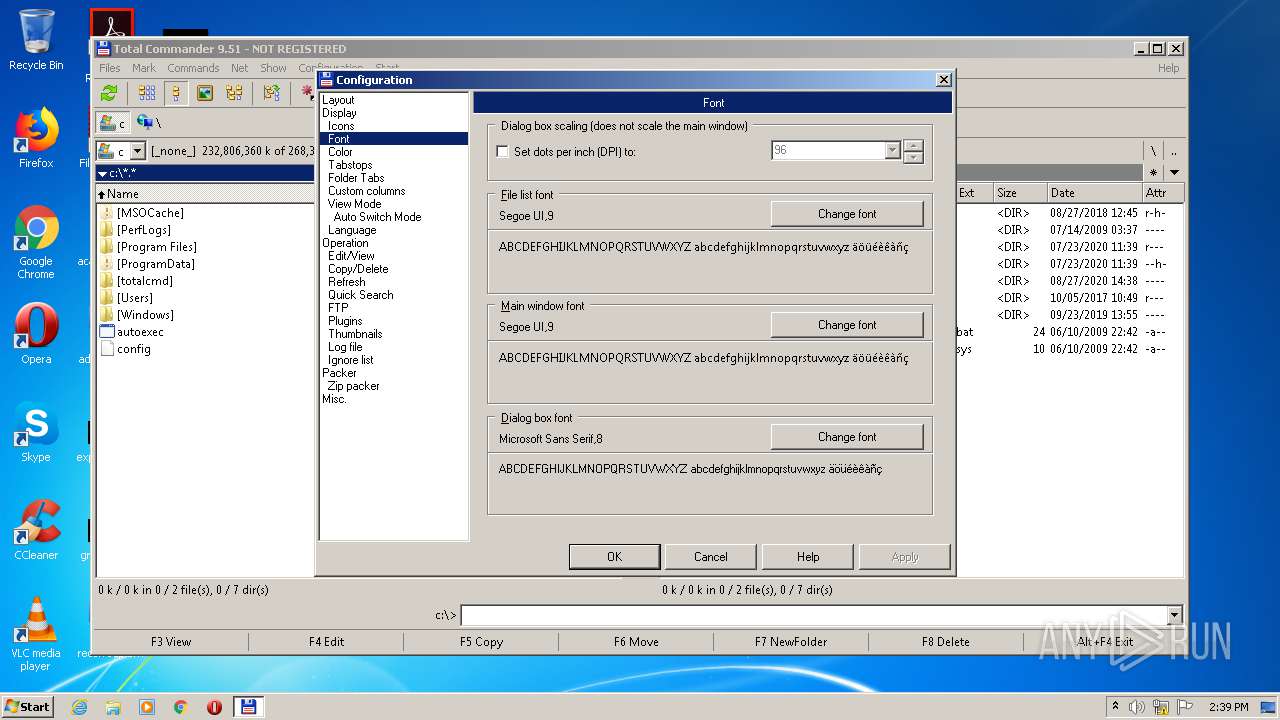
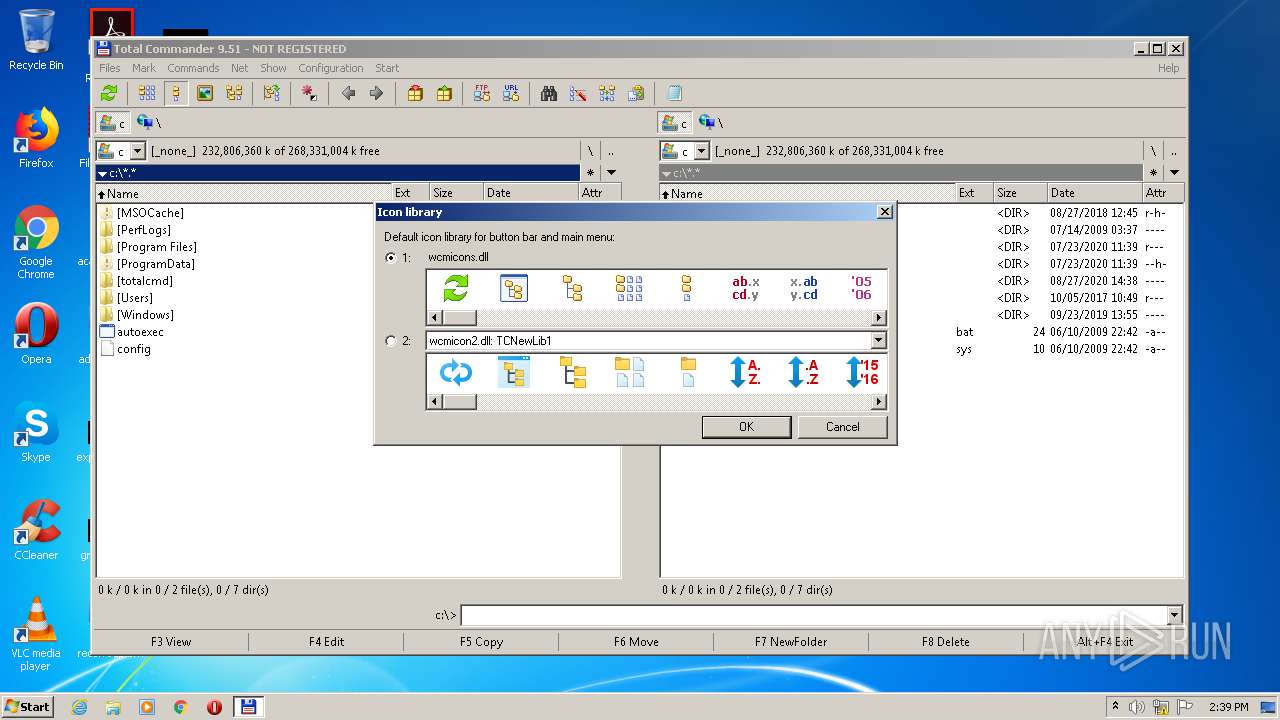
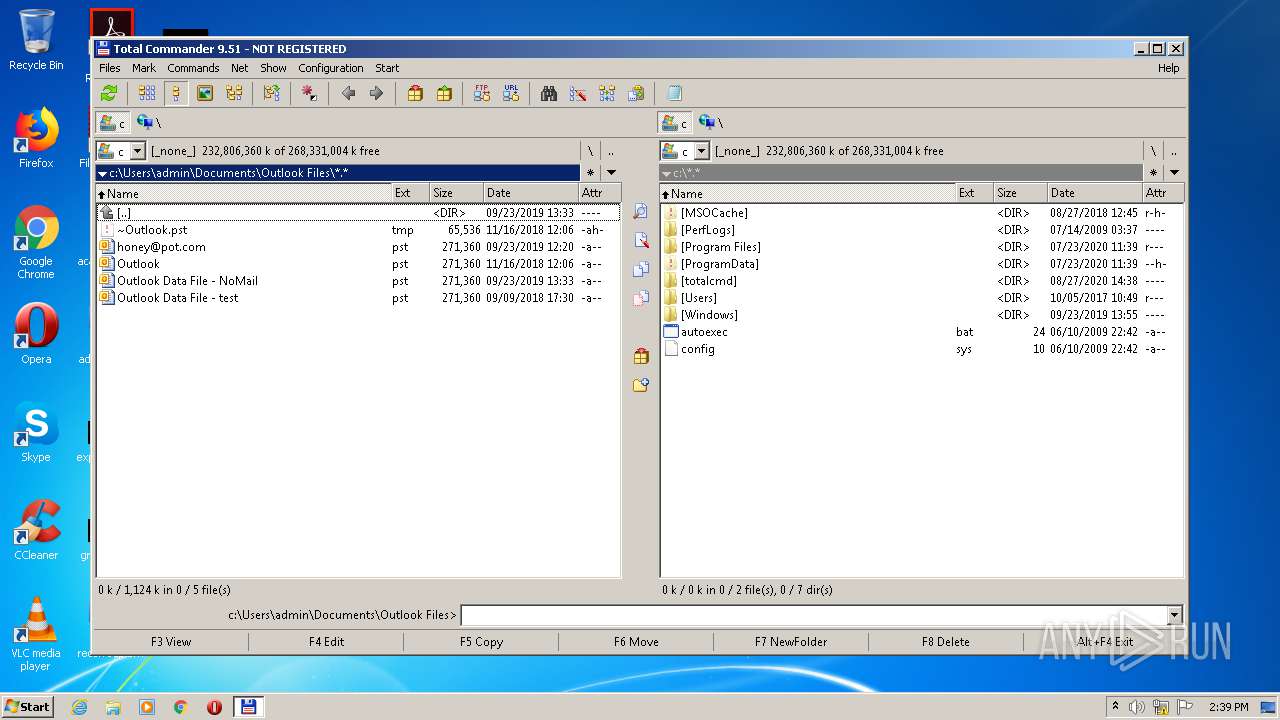
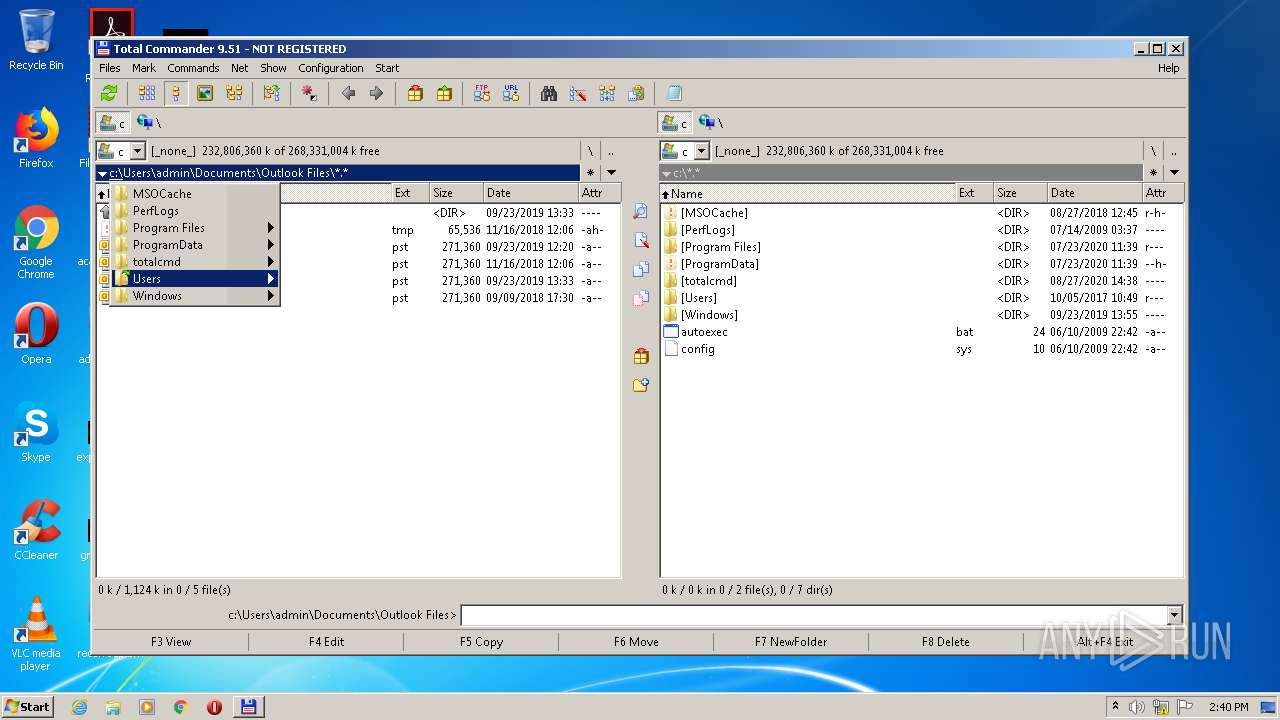
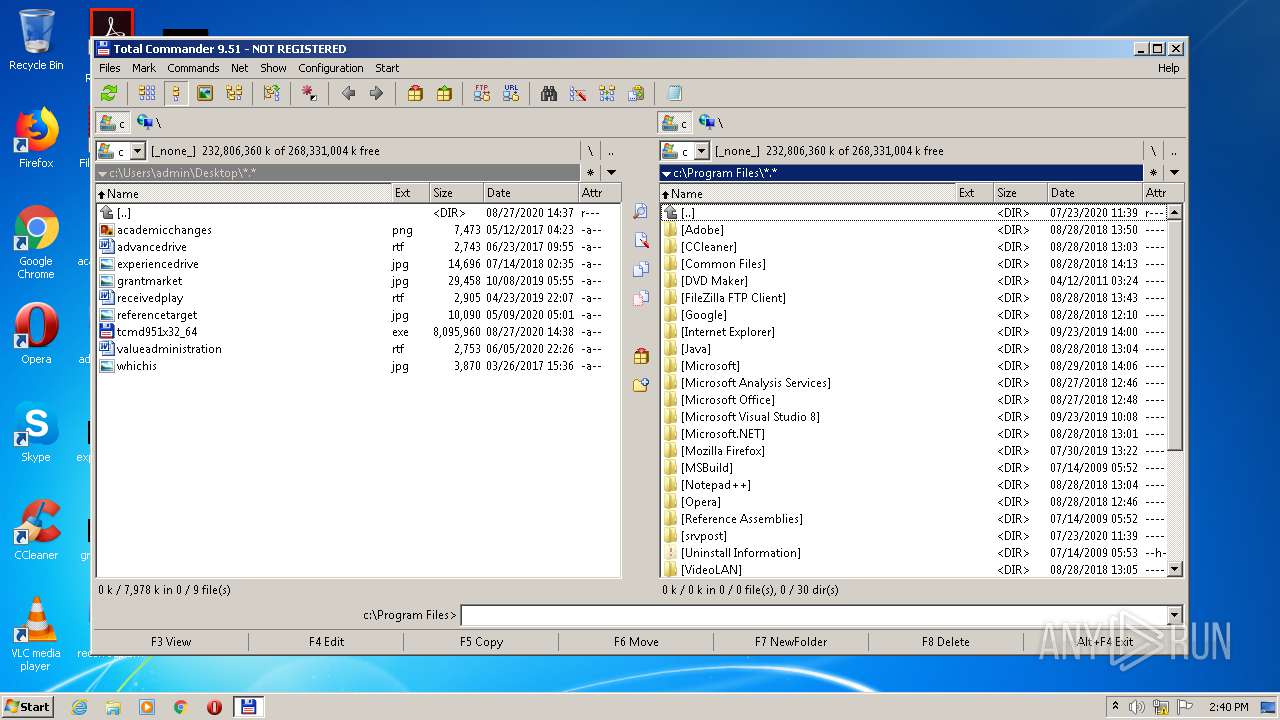
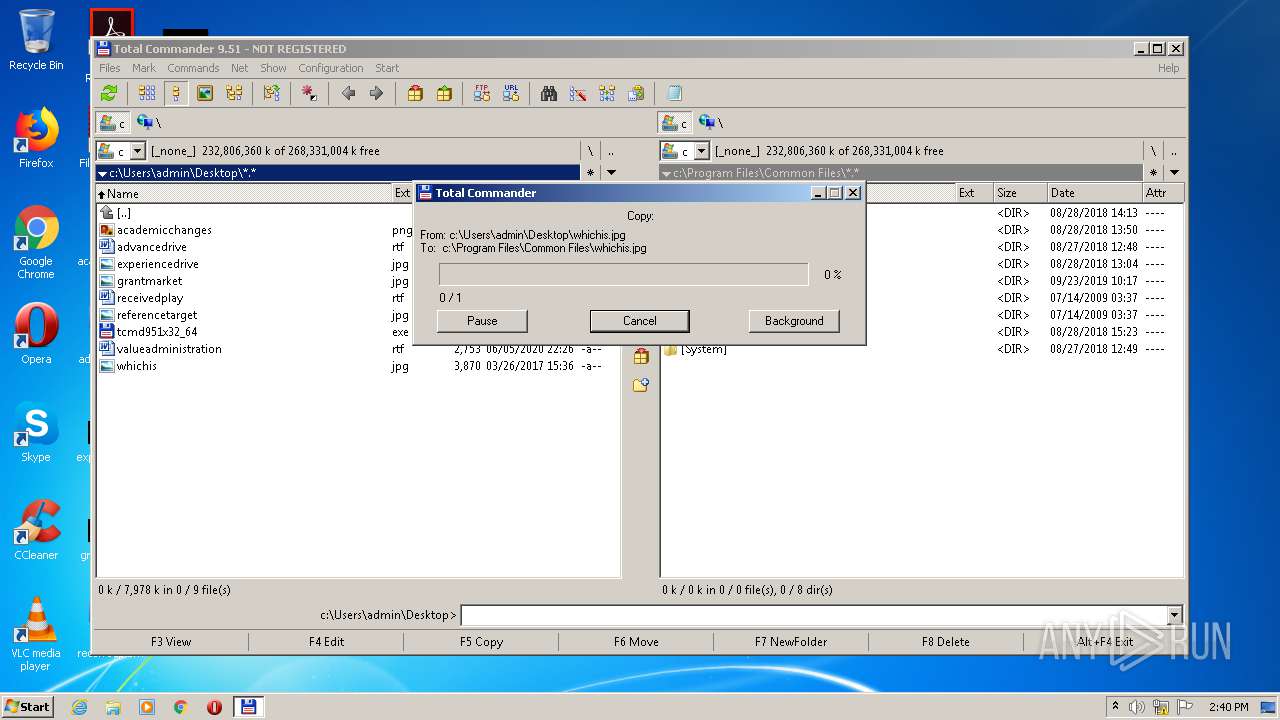
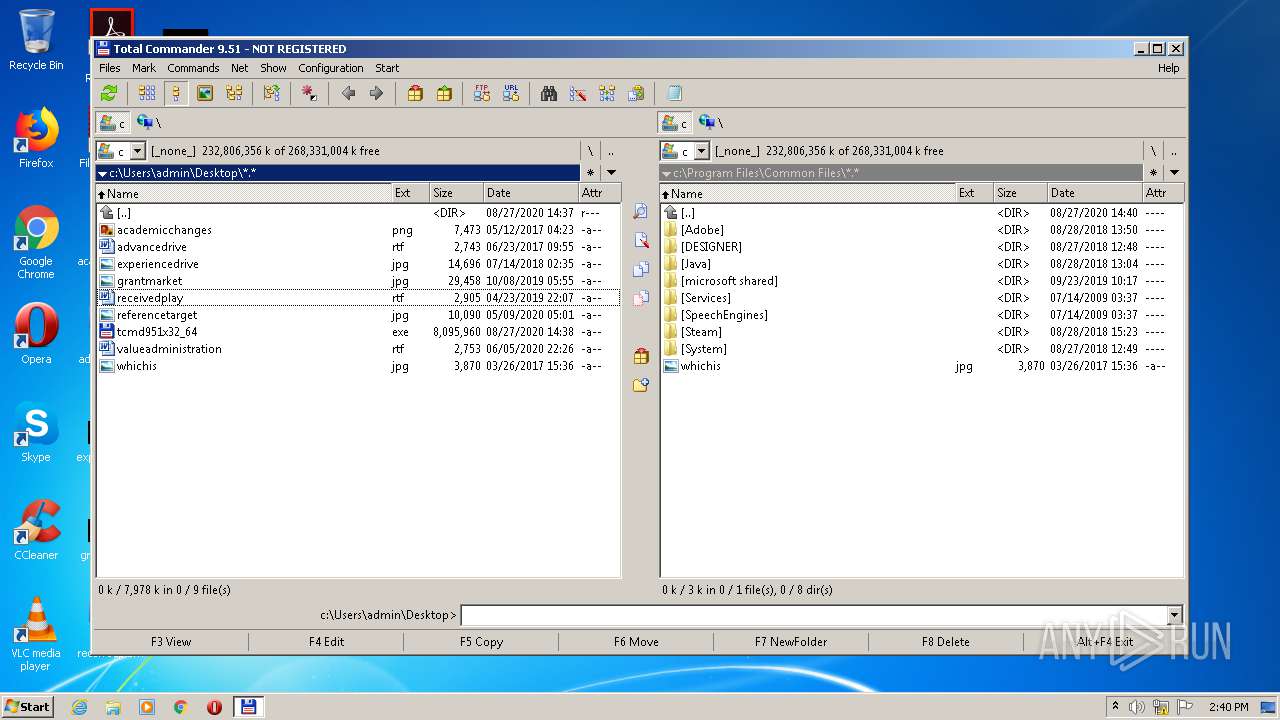
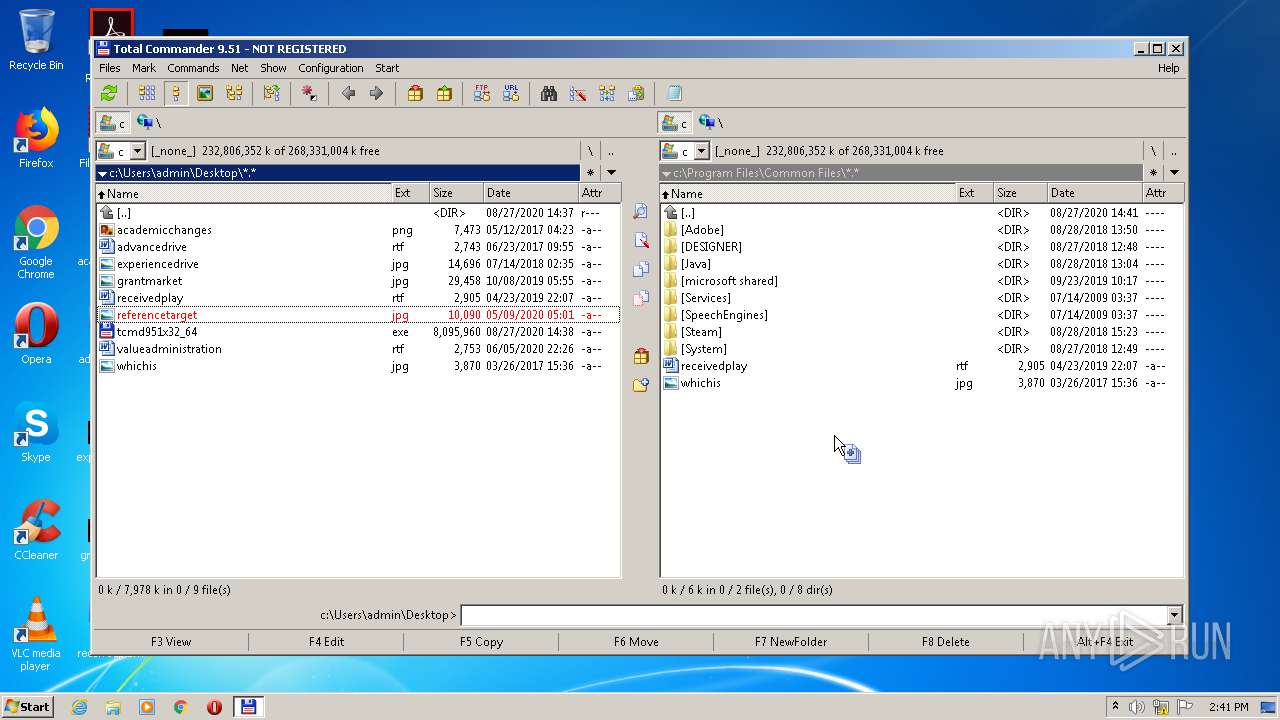
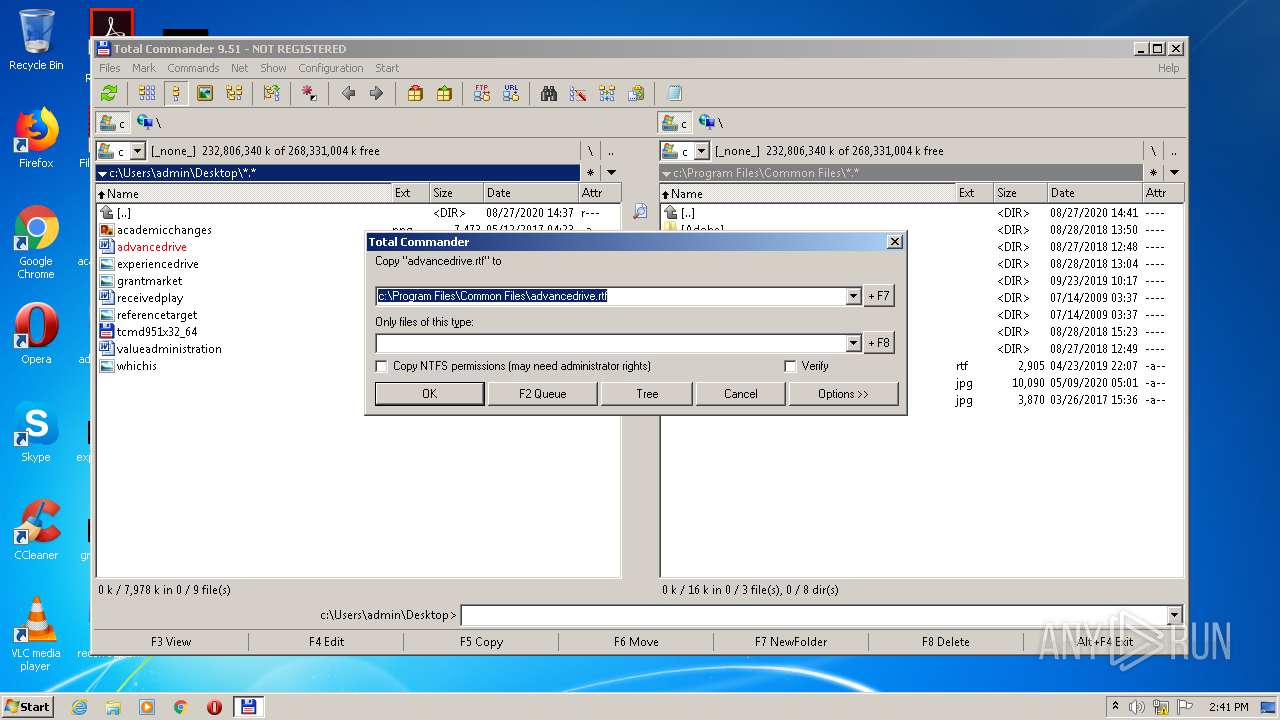
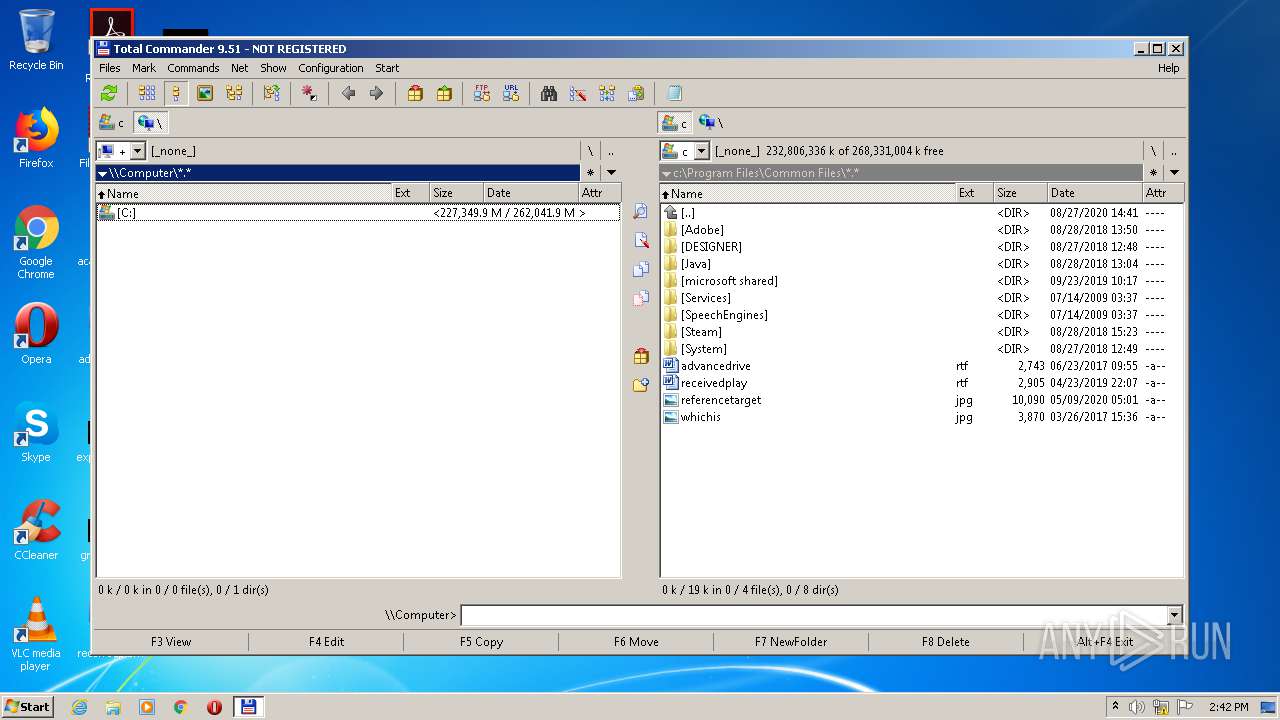
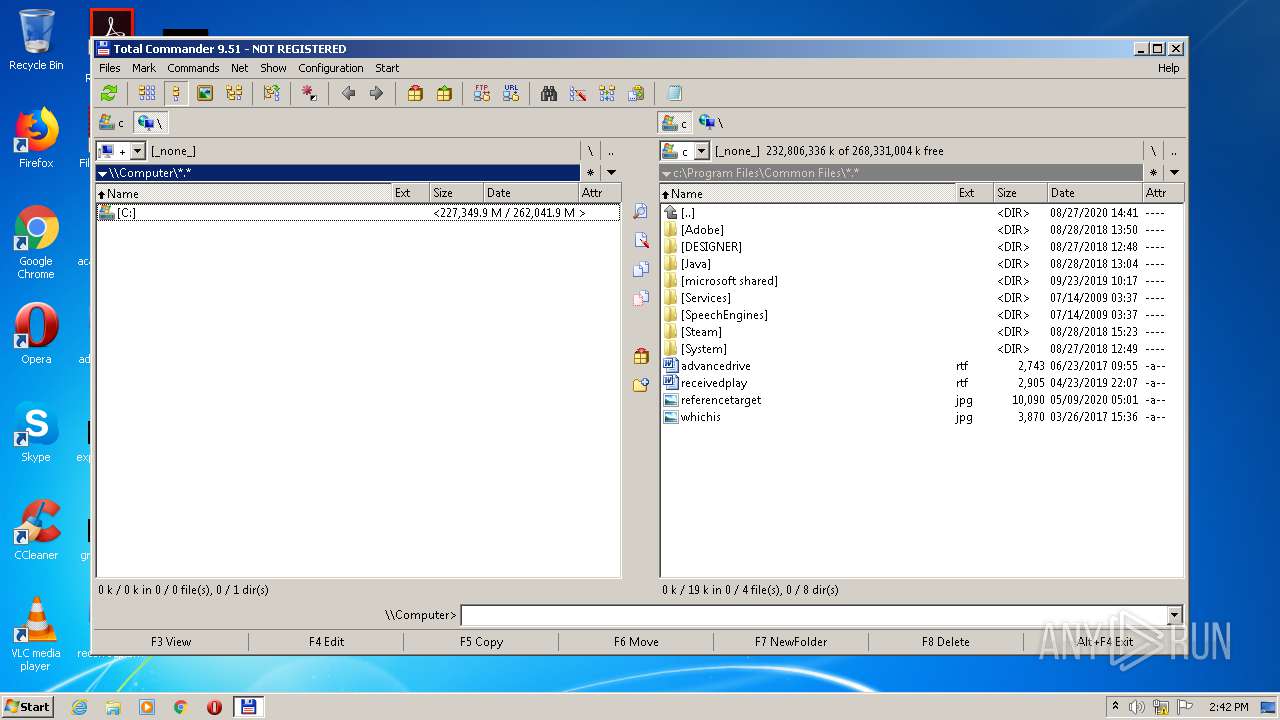
Manual execution by user
- TOTALCMD.EXE (PID: 2188)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 EXE PECompact compressed (generic) (35.9) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (27) |
| .exe | | | Win64 Executable (generic) (23.9) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:03:18 08:17:09+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 98304 |
| InitializedDataSize: | 61440 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1350d |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
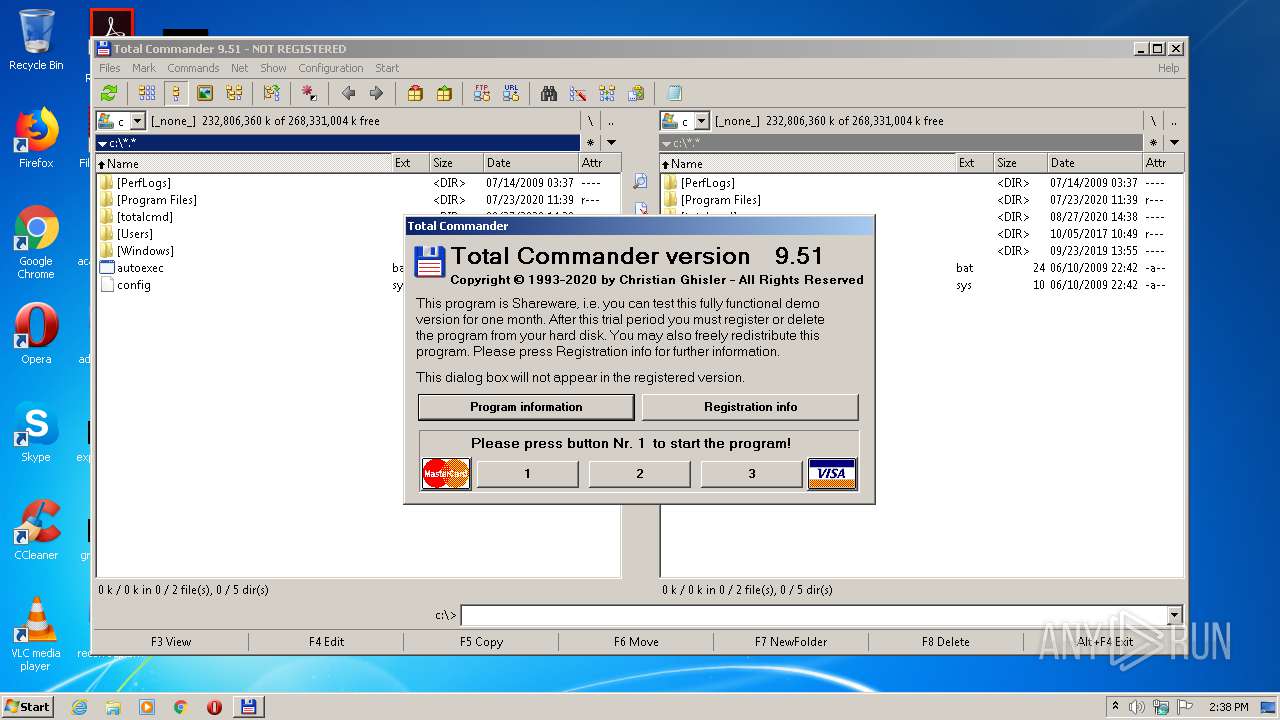
| FileVersionNumber: | 9.5.1.0 |
| ProductVersionNumber: | 9.5.1.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| Comments: | - |
| CompanyName: | Ghisler Software GmbH |
| FileDescription: | Total Commander Installer |
| FileVersion: | 9.51 |
| InternalName: | INSTALL |
| LegalCopyright: | Copyright © Ghisler Software GmbH 1993-2020 |
| LegalTrademarks: | - |
| OriginalFileName: | install.exe |
| PrivateBuild: | - |
| ProductName: | Total Commander Installer |
| ProductVersion: | 9.51 |
| SpecialBuild: | - |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 18-Mar-2020 07:17:09 |
| Detected languages: |
|
| Comments: | - |
| CompanyName: | Ghisler Software GmbH |
| FileDescription: | Total Commander Installer |
| FileVersion: | 9.51 |
| InternalName: | INSTALL |
| LegalCopyright: | Copyright © Ghisler Software GmbH 1993-2020 |
| LegalTrademarks: | - |
| OriginalFilename: | install.exe |
| PrivateBuild: | - |
| ProductName: | Total Commander Installer |
| ProductVersion: | 9.51 |
| SpecialBuild: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 18-Mar-2020 07:17:09 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00017CB0 | 0x00018000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.58194 |
.rdata | 0x00019000 | 0x00001B9A | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.21041 |
.data | 0x0001B000 | 0x0000993C | 0x00005000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.93379 |
.rsrc | 0x00025000 | 0x000027B0 | 0x00003000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.81333 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.16857 | 1646 | UNKNOWN | German - Switzerland | RT_MANIFEST |
2 | 3.43362 | 296 | UNKNOWN | German - Switzerland | RT_ICON |
3 | 3.16448 | 1384 | UNKNOWN | German - Switzerland | RT_ICON |
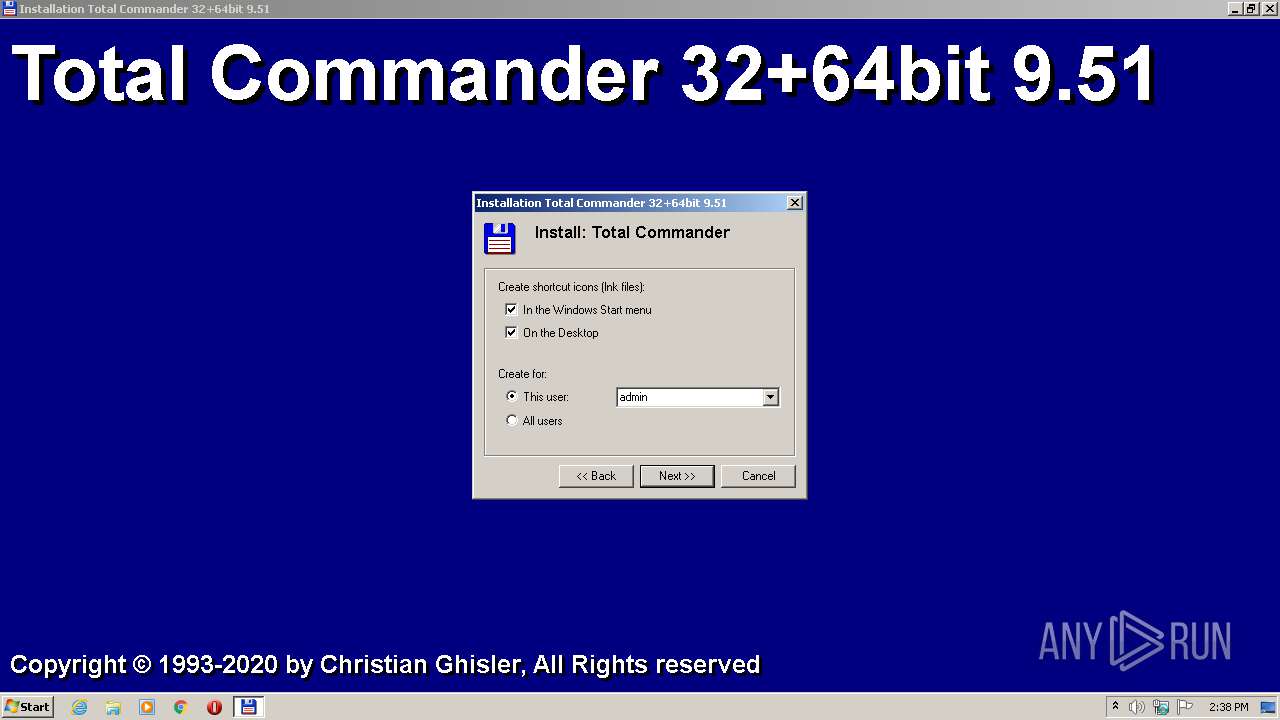
CREATELNKDLG | 3.50578 | 658 | UNKNOWN | German - Switzerland | RT_DIALOG |
DLG2FILEACTIONMIN | 2.96201 | 202 | UNKNOWN | German - Switzerland | RT_DIALOG |
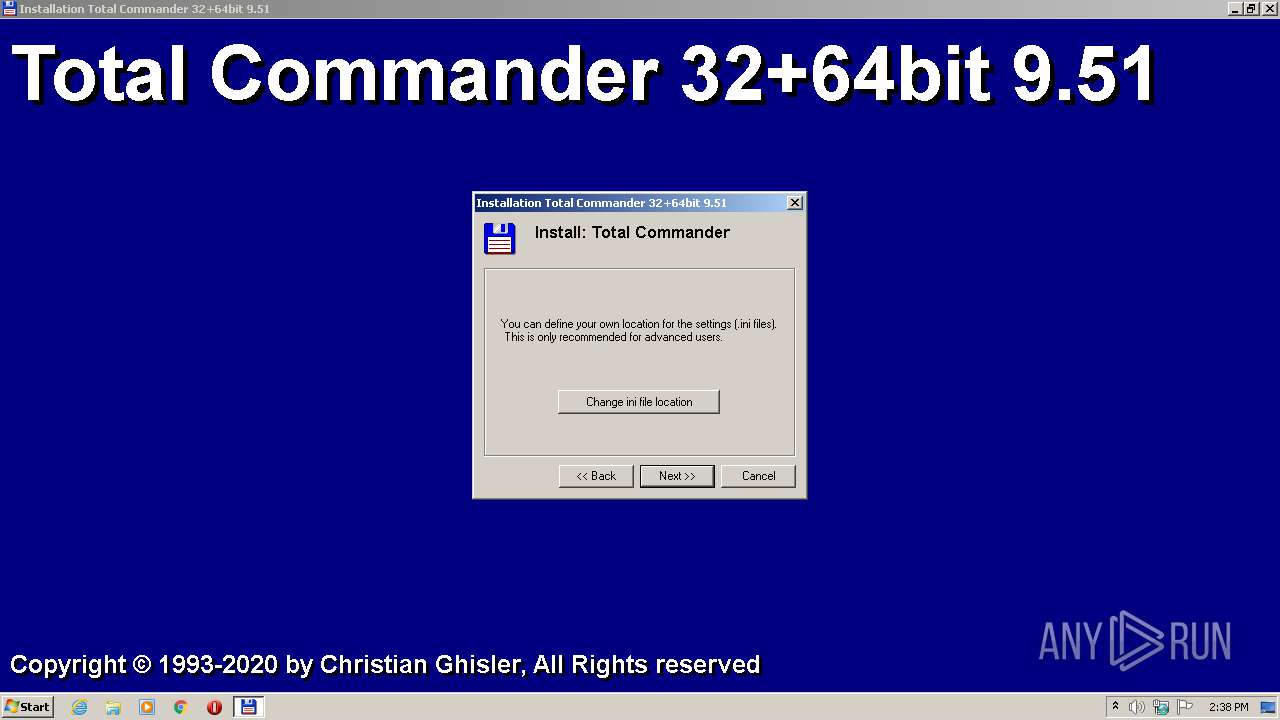
INILOCATION | 3.58674 | 1154 | UNKNOWN | German - Switzerland | RT_DIALOG |
LANGUAGEDIALOG | 3.428 | 506 | UNKNOWN | German - Switzerland | RT_DIALOG |
MESSAGEBOXDLG | 3.14063 | 362 | UNKNOWN | German - Switzerland | RT_DIALOG |
MYINPUTDIALOG | 3.09404 | 342 | UNKNOWN | German - Switzerland | RT_DIALOG |
TEXTBOXDLG | 3.05155 | 110 | UNKNOWN | German - Switzerland | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
Total processes
47
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
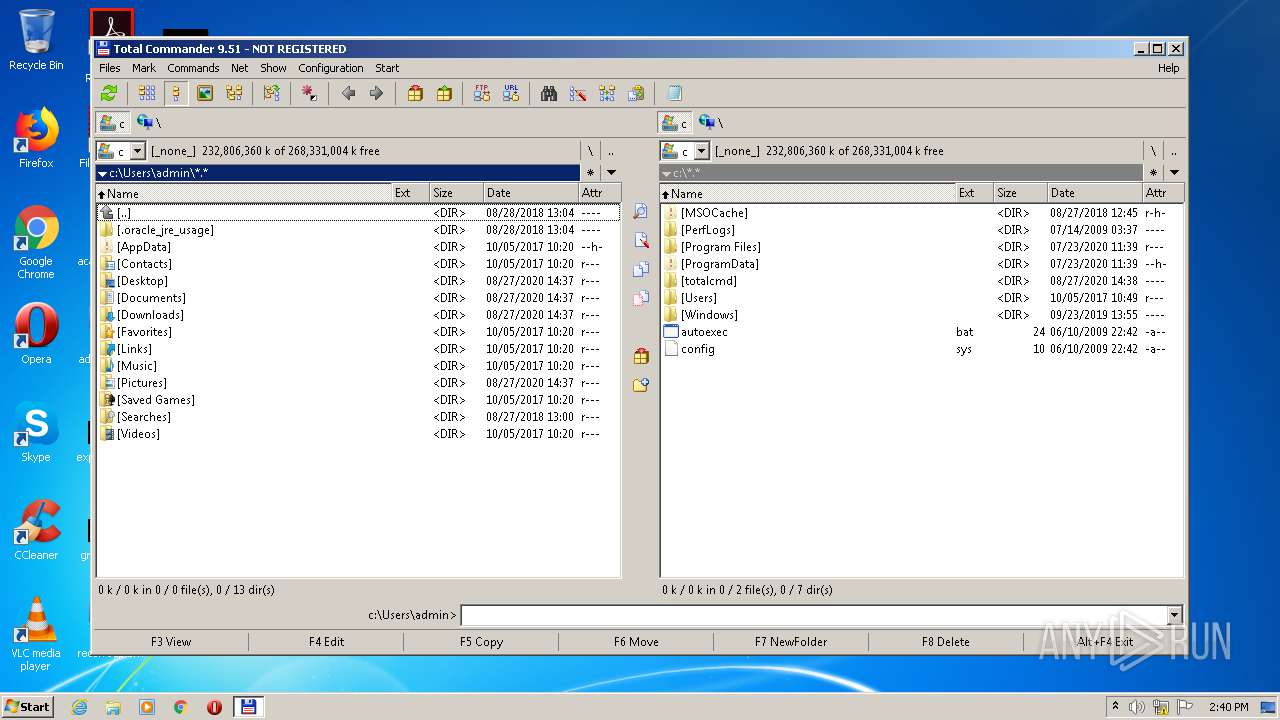
| 308 | "C:\Users\admin\Desktop\tcmd951x32_64.exe" | C:\Users\admin\Desktop\tcmd951x32_64.exe | — | explorer.exe | |||||||||||
User: admin Company: Ghisler Software GmbH Integrity Level: MEDIUM Description: Total Commander Installer Exit code: 3221226540 Version: 9.51 Modules
| |||||||||||||||
| 744 | "C:\totalcmd\tcmadmin.exe" 2188 USER-PC\admin | C:\totalcmd\tcmadmin.exe | TOTALCMD.EXE | ||||||||||||
User: admin Company: Ghisler Software GmbH Integrity Level: HIGH Description: Total Commander Administrator Tool Exit code: 0 Version: 1, 0, 0, 8 Modules
| |||||||||||||||
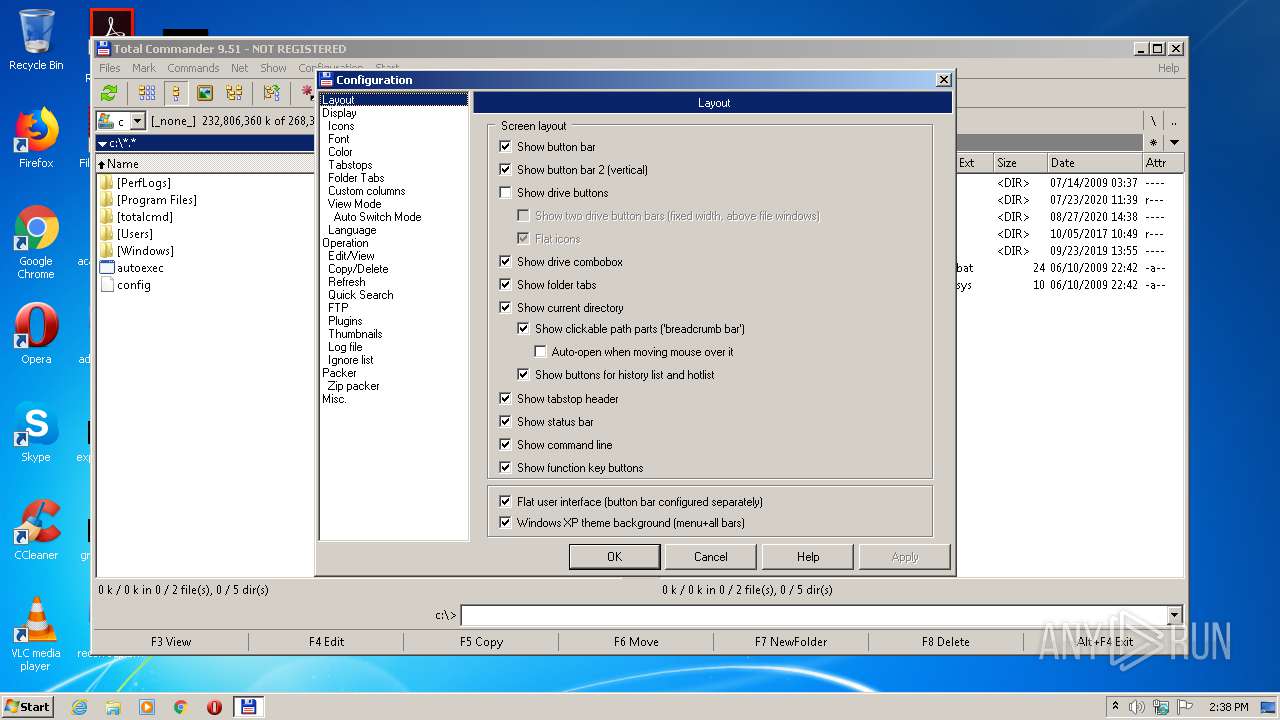
| 2188 | "C:\totalcmd\TOTALCMD.EXE" | C:\totalcmd\TOTALCMD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Ghisler Software GmbH Integrity Level: MEDIUM Description: Total Commander 32 bit Exit code: 0 Version: 9.51 Modules
| |||||||||||||||
| 3924 | "C:\Users\admin\Desktop\tcmd951x32_64.exe" | C:\Users\admin\Desktop\tcmd951x32_64.exe | explorer.exe | ||||||||||||
User: admin Company: Ghisler Software GmbH Integrity Level: HIGH Description: Total Commander Installer Exit code: 0 Version: 9.51 Modules
| |||||||||||||||
Total events
604
Read events
575
Write events
29
Delete events
0
Modification events
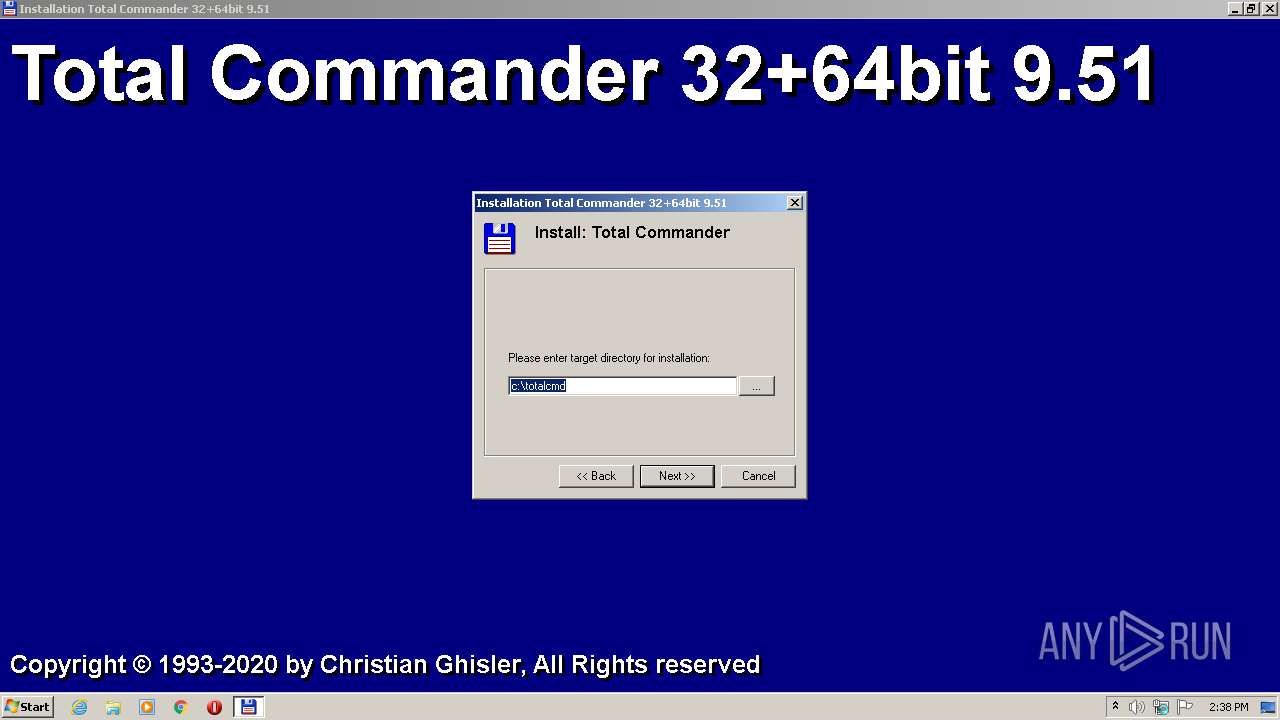
| (PID) Process: | (3924) tcmd951x32_64.exe | Key: | HKEY_CURRENT_USER\Software\Ghisler\Total Commander |
| Operation: | write | Name: | IniFileName |
Value: %APPDATA%\GHISLER\wincmd.ini | |||
| (PID) Process: | (3924) tcmd951x32_64.exe | Key: | HKEY_CURRENT_USER\Software\Ghisler\Total Commander |
| Operation: | write | Name: | FtpIniName |
Value: %APPDATA%\GHISLER\wcx_ftp.ini | |||
| (PID) Process: | (3924) tcmd951x32_64.exe | Key: | HKEY_CURRENT_USER\Software\Ghisler\Total Commander |
| Operation: | write | Name: | InstallDir |
Value: c:\totalcmd | |||
| (PID) Process: | (3924) tcmd951x32_64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Ghisler\Total Commander |
| Operation: | write | Name: | IniFileName |
Value: %APPDATA%\GHISLER\wincmd.ini | |||
| (PID) Process: | (3924) tcmd951x32_64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Ghisler\Total Commander |
| Operation: | write | Name: | FtpIniName |
Value: %APPDATA%\GHISLER\wcx_ftp.ini | |||
| (PID) Process: | (3924) tcmd951x32_64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Ghisler\Total Commander |
| Operation: | write | Name: | InstallDir |
Value: c:\totalcmd | |||
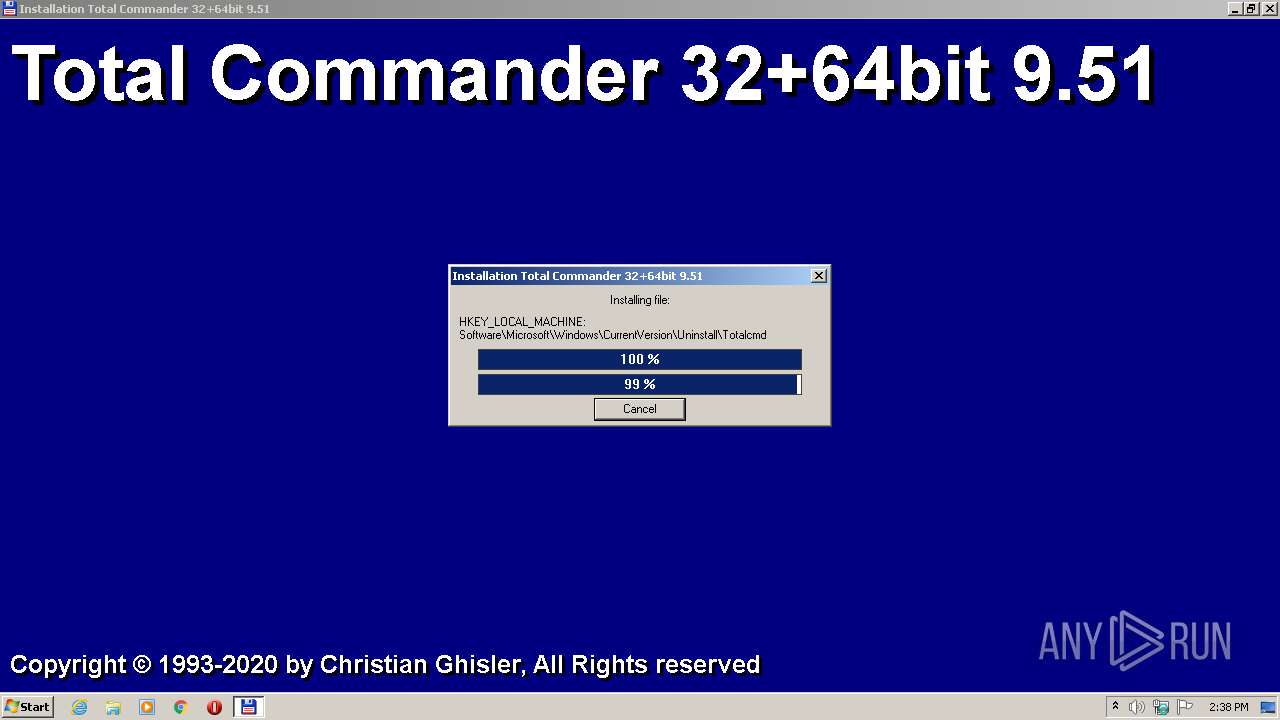
| (PID) Process: | (3924) tcmd951x32_64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Totalcmd |
| Operation: | write | Name: | DisplayName |
Value: Total Commander (Remove or Repair) | |||
| (PID) Process: | (3924) tcmd951x32_64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Totalcmd |
| Operation: | write | Name: | InstallLocation |
Value: c:\totalcmd\ | |||
| (PID) Process: | (3924) tcmd951x32_64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Totalcmd |
| Operation: | write | Name: | UninstallString |
Value: c:\totalcmd\tcuninst.exe | |||
| (PID) Process: | (3924) tcmd951x32_64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Totalcmd |
| Operation: | write | Name: | DisplayIcon |
Value: c:\totalcmd\tcuninst.exe | |||
Executable files
35
Suspicious files
3
Text files
106
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3924 | tcmd951x32_64.exe | C:\totalcmd\LANGUAGE\WCMD_CZ.INC | text | |
MD5:— | SHA256:— | |||
| 3924 | tcmd951x32_64.exe | C:\totalcmd\LANGUAGE\WCMD_DAN.LNG | text | |
MD5:— | SHA256:— | |||
| 3924 | tcmd951x32_64.exe | C:\totalcmd\LANGUAGE\WCMD_DEU.MNU | text | |
MD5:— | SHA256:— | |||
| 3924 | tcmd951x32_64.exe | C:\totalcmd\LANGUAGE\WCMD_DAN.INC | text | |
MD5:— | SHA256:— | |||
| 3924 | tcmd951x32_64.exe | C:\totalcmd\LANGUAGE\WCMD_DEU.LNG | text | |
MD5:— | SHA256:— | |||
| 3924 | tcmd951x32_64.exe | C:\totalcmd\LANGUAGE\WCMD_DUT.LNG | text | |
MD5:— | SHA256:— | |||
| 3924 | tcmd951x32_64.exe | C:\totalcmd\LANGUAGE\WCMD_CZ.LNG | text | |
MD5:— | SHA256:— | |||
| 3924 | tcmd951x32_64.exe | C:\totalcmd\KEYBOARD.TXT | text | |
MD5:09280943F18EA54E63BFC4706A586C1D | SHA256:3F2E42C54863797869F567BF25DBFE11F586977A572E22ADF706B0427717B3F1 | |||
| 3924 | tcmd951x32_64.exe | C:\Users\admin\AppData\Roaming\GHISLER\wincmd.ini | text | |
MD5:926EB45A00D3C2C4AFEF6CE8AC07691B | SHA256:BF16FB4BAC9923E4327E3DD4F8398F0996B7395509123830F52A9B6EF66E3467 | |||
| 3924 | tcmd951x32_64.exe | C:\totalcmd\LANGUAGE\WCMD_DUT.INC | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report