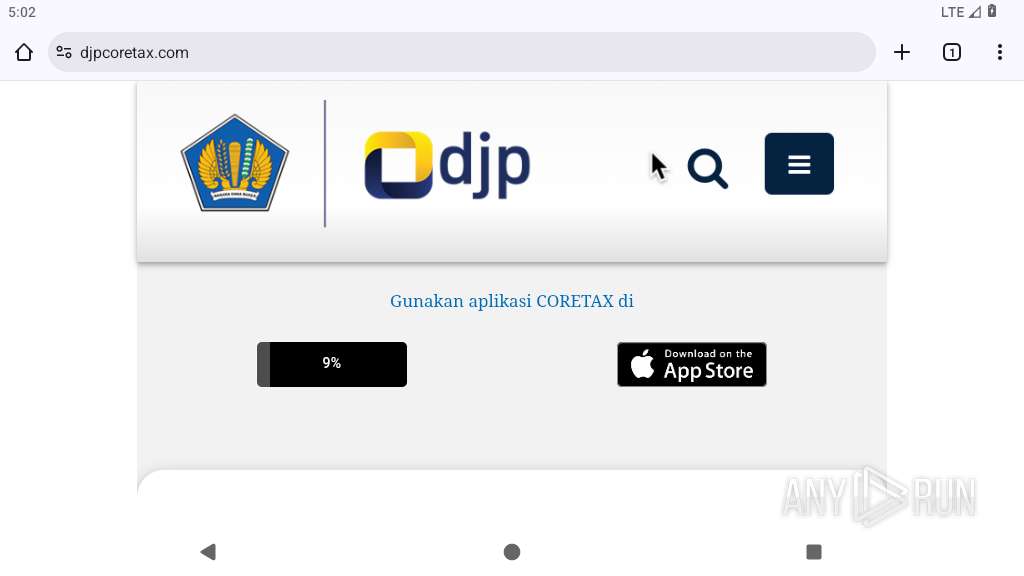
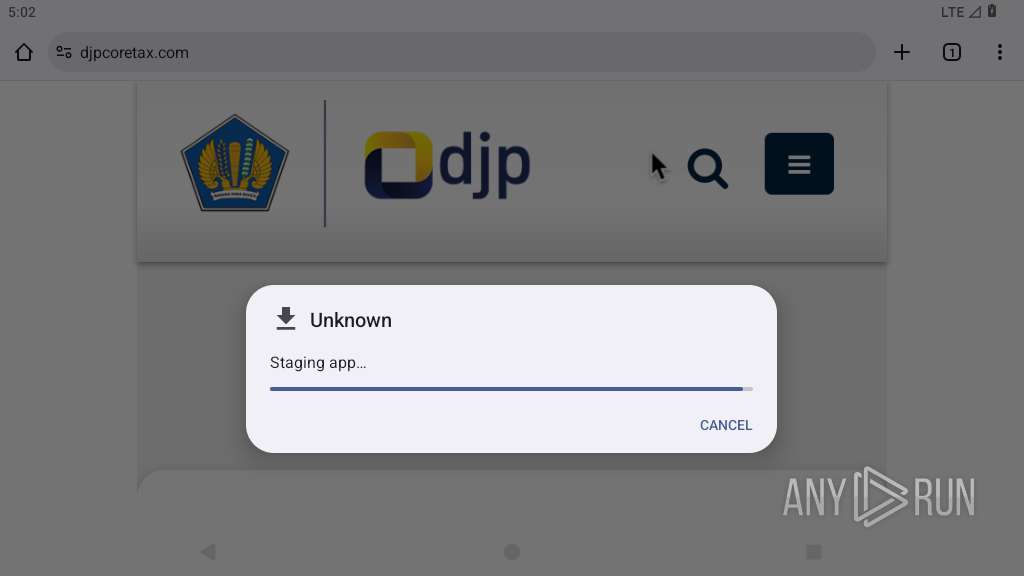
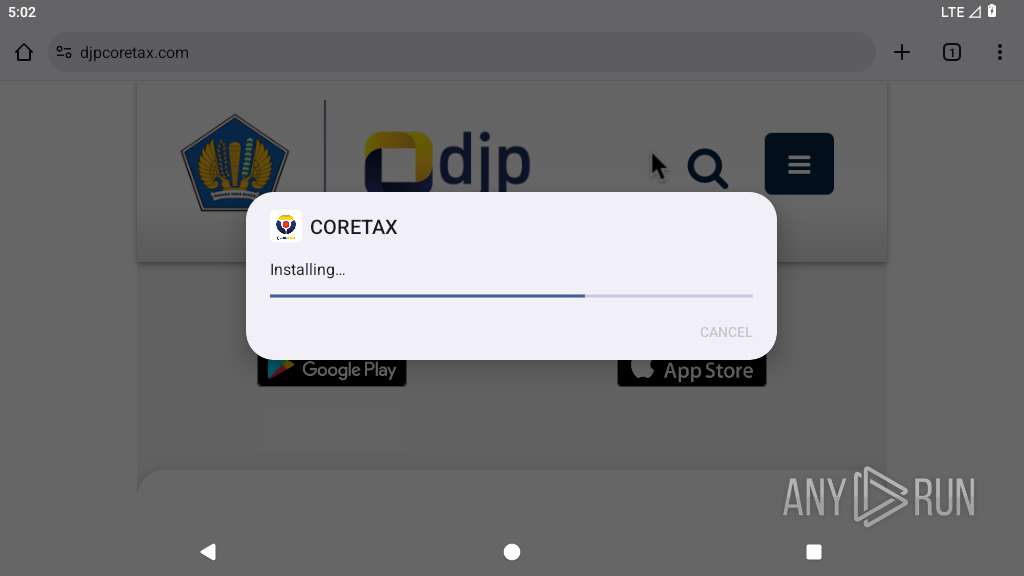
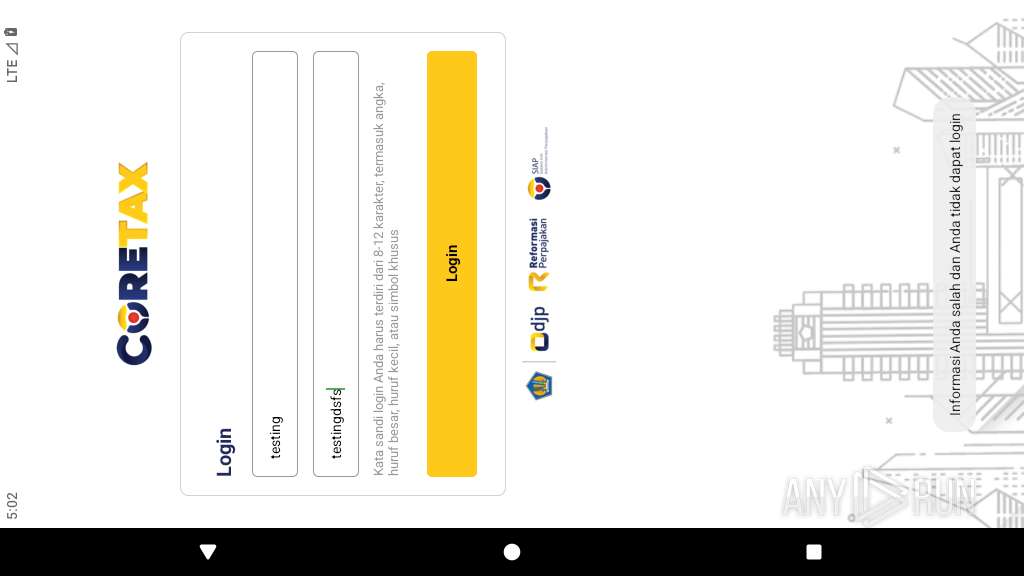
| URL: | djpcoretax.com |
| Full analysis: | https://app.any.run/tasks/15bd70eb-1e80-44bb-a105-be47fcb49b63 |
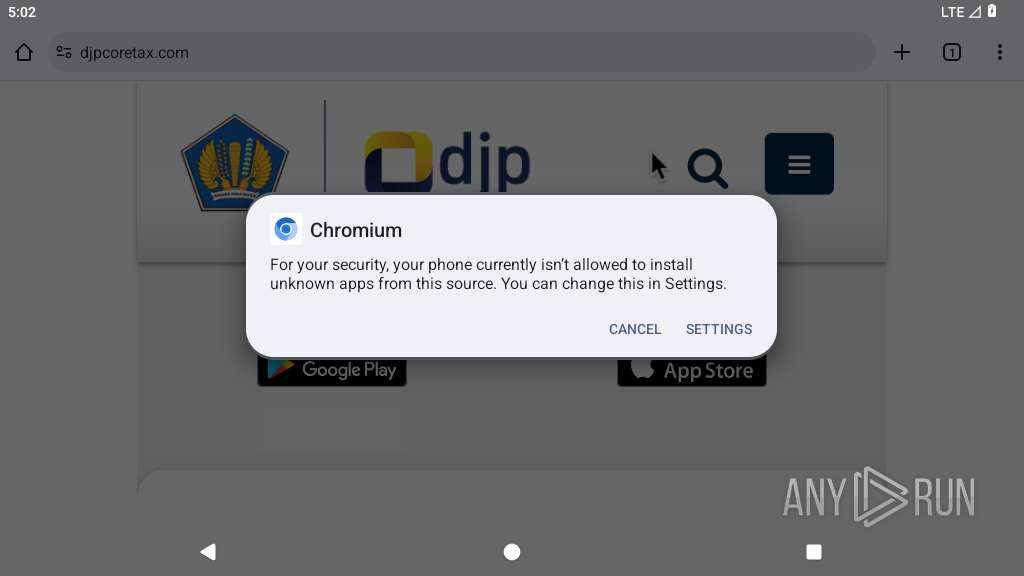
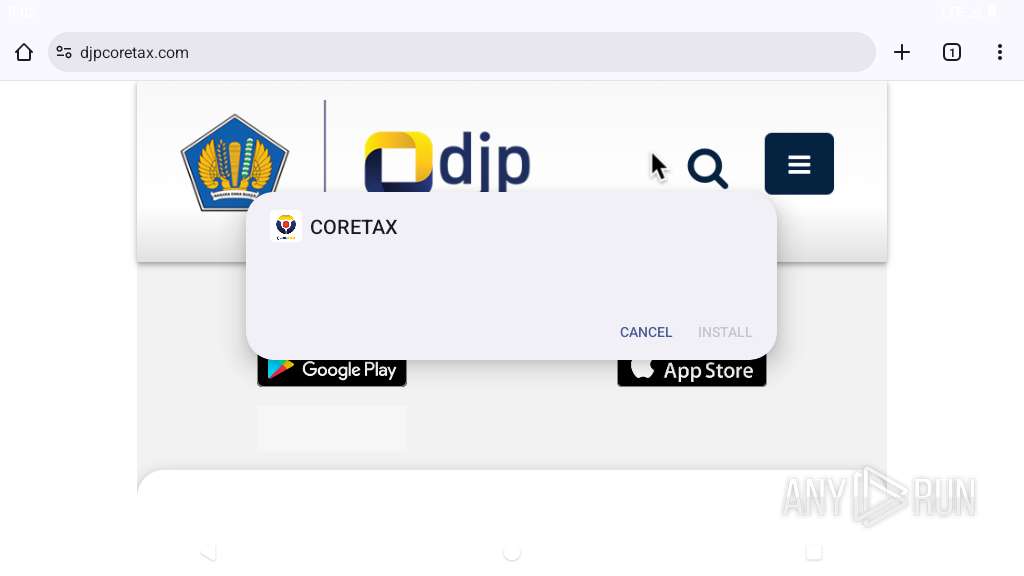
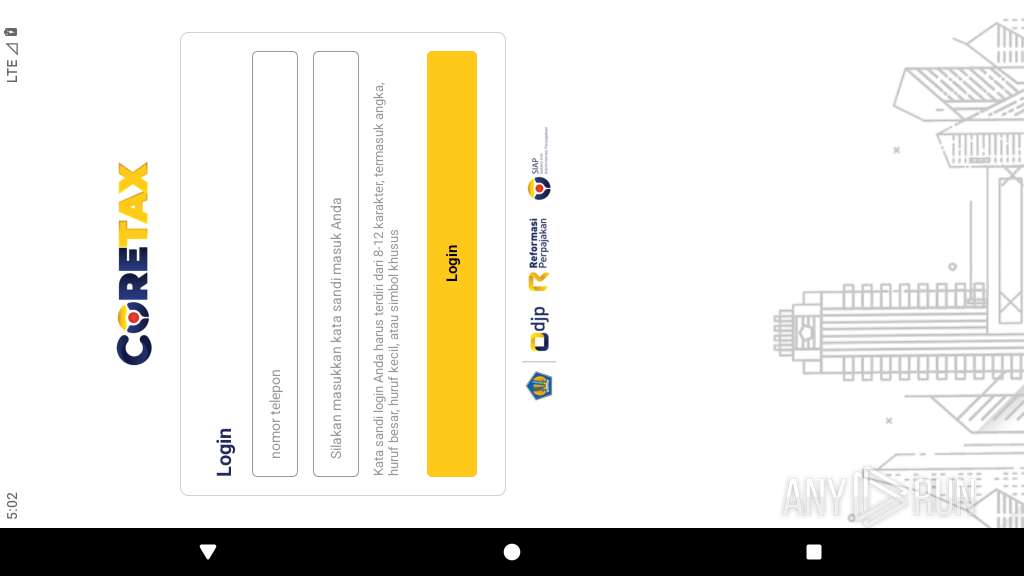
| Verdict: | Malicious activity |
| Analysis date: | February 23, 2026, 05:01:40 |
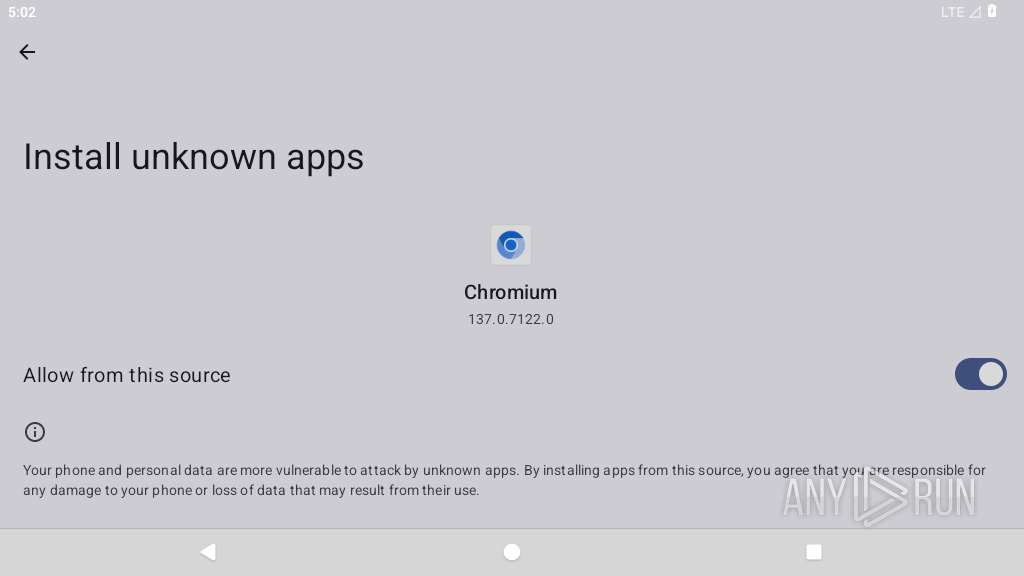
| OS: | Android 14 |
| Tags: | |
| Indicators: | |
| MD5: | FFCCFC7C9A94A672FB82E1C3939DC2A3 |
| SHA1: | 5D335CE744CEE83B45A288BCF4C9D86C7E894BA6 |
| SHA256: | 2D20A8B73835B410C41407F456B2F51371ABD99BD0F2081C4375F91BA14D42B6 |
| SSDEEP: | 3:LdQL:c |
MALICIOUS
Executes system commands or scripts
- app_process64 (PID: 4341)
GOLDDIGGER has been detected
- app_process64 (PID: 4433)
- app_process64 (PID: 4434)
- app_process64 (PID: 4433)
- app_process64 (PID: 4434)
- app_process64 (PID: 4492)
- app_process64 (PID: 4507)
- app_process64 (PID: 4507)
- crash_dump64 (PID: 4491)
SUSPICIOUS
Collects data about the device's environment (JVM version)
- app_process64 (PID: 4341)
Accesses system-level resources
- app_process64 (PID: 4341)
Uses encryption API functions
- app_process64 (PID: 4341)
Retrieves Android OS build information
- app_process64 (PID: 4341)
Establishing a connection
- app_process64 (PID: 4341)
- app_process64 (PID: 4507)
- app_process64 (PID: 4433)
Starts a service
- app_process64 (PID: 4341)
- app_process64 (PID: 4507)
- app_process64 (PID: 4433)
Updates data in the storage of application settings (SharedPreferences)
- app_process64 (PID: 4341)
- app_process64 (PID: 4433)
- app_process64 (PID: 4507)
Checks exemption from battery optimization
- app_process64 (PID: 4341)
Detects when screen powers off
- app_process64 (PID: 4341)
Creates a WakeLock to manage power state
- app_process64 (PID: 4341)
Acquires a wake lock to keep the device awake
- app_process64 (PID: 4341)
Creates new saved account
- app_process64 (PID: 4341)
Retrieves a list of running application processes
- app_process64 (PID: 4433)
Overlays content on other applications
- app_process64 (PID: 4341)
Accesses external device storage files
- app_process64 (PID: 4341)
INFO
Loads a native library into the application
- app_process64 (PID: 4341)
- app_process64 (PID: 4433)
- app_process64 (PID: 4507)
Retrieves CPU core information
- app_process64 (PID: 4341)
Dynamically inspects or modifies classes, methods, and fields at runtime
- app_process64 (PID: 4341)
Gets file name without full path
- app_process64 (PID: 4341)
Gets the display metrics associated with the device's screen
- app_process64 (PID: 4341)
Returns elapsed time since boot
- app_process64 (PID: 4341)
Verifies whether the device is connected to the internet
- app_process64 (PID: 4341)
Retrieves data from storage of application settings (SharedPreferences)
- app_process64 (PID: 4341)
- app_process64 (PID: 4433)
- app_process64 (PID: 4507)
Dynamically registers broadcast event listeners
- app_process64 (PID: 4341)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
156
Monitored processes
28
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 3976 | org.chromium.chrome | /system/bin/app_process64 | app_process64 | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 4022 | org.chromium.chrome_zygote | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 4038 | org.chromium.chrome_zygote | /system/bin/app_process64 | — | app_process64 |
User: u0_a72 Integrity Level: UNKNOWN Exit code: 0 | ||||
| 4052 | com.android.traceur | /system/bin/app_process64 | — | app_process64 |
User: u0_a54 Integrity Level: UNKNOWN Exit code: 512 | ||||
| 4073 | org.chromium.chrome:privileged_process0 | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 4088 | com.android.adservices.api | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 4150 | org.chromium.chrome_zygote | /system/bin/app_process64 | — | app_process64 |
User: u0_a72 Integrity Level: UNKNOWN Exit code: 0 | ||||
| 4176 | com.android.providers.partnerbookmarks | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 4302 | /system/bin/dmesgd | /system/bin/dmesgd | — | init |
User: dmesgd Integrity Level: UNKNOWN Exit code: 0 | ||||
| 4303 | dmesg | /system/bin/toybox | — | dmesgd |
User: dmesgd Integrity Level: UNKNOWN Exit code: 0 | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
41
Text files
27
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4341 | app_process64 | /data/data/org.rcitv.pmbdu/dpt-libs/arm64/libdpt.so | binary | |
MD5:— | SHA256:— | |||
| 4341 | app_process64 | /data/data/org.rcitv.pmbdu/files/INSTALLATION | text | |
MD5:— | SHA256:— | |||
| 4341 | app_process64 | /data/data/org.rcitv.pmbdu/cache/sentry/d3e81cbe7758f863a016e5f45d0f9b395a6feb8e/.options-cache/release.json | text | |
MD5:— | SHA256:— | |||
| 4341 | app_process64 | /data/data/org.rcitv.pmbdu/cache/sentry/d3e81cbe7758f863a016e5f45d0f9b395a6feb8e/.options-cache/sdk-version.json | text | |
MD5:— | SHA256:— | |||
| 4341 | app_process64 | /data/data/org.rcitv.pmbdu/cache/sentry/d3e81cbe7758f863a016e5f45d0f9b395a6feb8e/.options-cache/environment.json | text | |
MD5:— | SHA256:— | |||
| 4341 | app_process64 | /data/data/org.rcitv.pmbdu/cache/sentry/d3e81cbe7758f863a016e5f45d0f9b395a6feb8e/session.json | text | |
MD5:— | SHA256:— | |||
| 4341 | app_process64 | /data/data/org.rcitv.pmbdu/cache/sentry/d3e81cbe7758f863a016e5f45d0f9b395a6feb8e/.options-cache/tags.json | text | |
MD5:— | SHA256:— | |||
| 4341 | app_process64 | /data/data/org.rcitv.pmbdu/cache/sentry/d3e81cbe7758f863a016e5f45d0f9b395a6feb8e/.scope-cache/breadcrumbs.json.tmp | binary | |
MD5:— | SHA256:— | |||
| 4341 | app_process64 | /data/data/org.rcitv.pmbdu/cache/sentry/d3e81cbe7758f863a016e5f45d0f9b395a6feb8e/683b1118201d4a4c8088178f644eb101.envelope | text | |
MD5:— | SHA256:— | |||
| 4341 | app_process64 | /data/data/org.rcitv.pmbdu/no_backup/androidx.work.workdb-journal | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
25
DNS requests
21
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1921 | app_process64 | GET | 204 | 142.251.127.147:443 | https://www.google.com/generate_204 | unknown | — | — | whitelisted |
1921 | app_process64 | GET | 204 | 142.251.127.99:80 | http://www.google.com/gen_204 | unknown | — | — | whitelisted |
3976 | app_process64 | POST | 200 | 142.251.127.84:443 | https://accounts.google.com/ListAccounts?gpsia=1&source=ChromiumBrowser&laf=b64bin&json=standard | unknown | — | — | whitelisted |
1921 | app_process64 | GET | 204 | 142.250.186.67:80 | http://connectivitycheck.gstatic.com/generate_204 | unknown | — | — | whitelisted |
3976 | app_process64 | GET | 200 | 216.58.206.78:80 | http://clients2.google.com/time/1/current?cup2key=9:fqyaZn1PVB4DN81yLqejjrWHewqYfhxPRZeZf5Fg7YI&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
2931 | app_process64 | POST | 403 | 74.125.206.81:443 | https://staging-remoteprovisioning.sandbox.googleapis.com/v1:fetchEekChain | unknown | — | 1.56 Kb | whitelisted |
3976 | app_process64 | POST | 400 | 142.251.208.10:443 | https://androidchromeprotect.pa.googleapis.com/v1/download | unknown | text | 586 b | whitelisted |
4341 | app_process64 | GET | 200 | 103.235.46.115:80 | http://www.baidu.com/ | unknown | — | — | unknown |
4341 | app_process64 | POST | 403 | 172.67.169.10:443 | https://sentry.absu.cc/api/6/envelope/ | unknown | text | 61 b | unknown |
4341 | app_process64 | POST | 403 | 172.67.169.10:443 | https://sentry.absu.cc/api/6/envelope/ | unknown | text | 61 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
452 | mdnsd | 224.0.0.251:5353 | — | — | — | whitelisted |
1921 | app_process64 | 142.251.127.99:80 | www.google.com | GOOGLE | US | whitelisted |
— | — | 142.251.127.104:443 | www.google.com | GOOGLE | US | whitelisted |
— | — | 142.250.186.67:80 | connectivitycheck.gstatic.com | GOOGLE | US | whitelisted |
3976 | app_process64 | 216.58.206.78:80 | google.com | GOOGLE | US | whitelisted |
3976 | app_process64 | 142.251.127.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
3976 | app_process64 | 142.251.127.106:443 | www.google.com | GOOGLE | US | whitelisted |
3976 | app_process64 | 104.21.2.26:443 | djpcoretax.com | CLOUDFLARENET | US | whitelisted |
1921 | app_process64 | 142.251.127.147:443 | www.google.com | GOOGLE | US | whitelisted |
1921 | app_process64 | 142.250.186.67:80 | connectivitycheck.gstatic.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
www.google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
accounts.google.com |
| whitelisted |
djpcoretax.com |
| unknown |
connectivitycheck.gstatic.com |
| whitelisted |
time.android.com |
| whitelisted |
staging-remoteprovisioning.sandbox.googleapis.com |
| whitelisted |
androidchromeprotect.pa.googleapis.com |
| whitelisted |
www.baidu.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1921 | app_process64 | Misc activity | ET INFO Android Device Connectivity Check |
347 | netd | Misc activity | INFO [ANY.RUN] .cc TLD domain request |
4341 | app_process64 | Unknown Traffic | ET HUNTING Suspicious Empty Accept-Encoding Header |
4341 | app_process64 | Misc activity | ET INFO Observed request to common DOH pattern in URI M1 |
4341 | app_process64 | Misc activity | ET INFO Observed HTTP Content-Type Common to DoH Services |