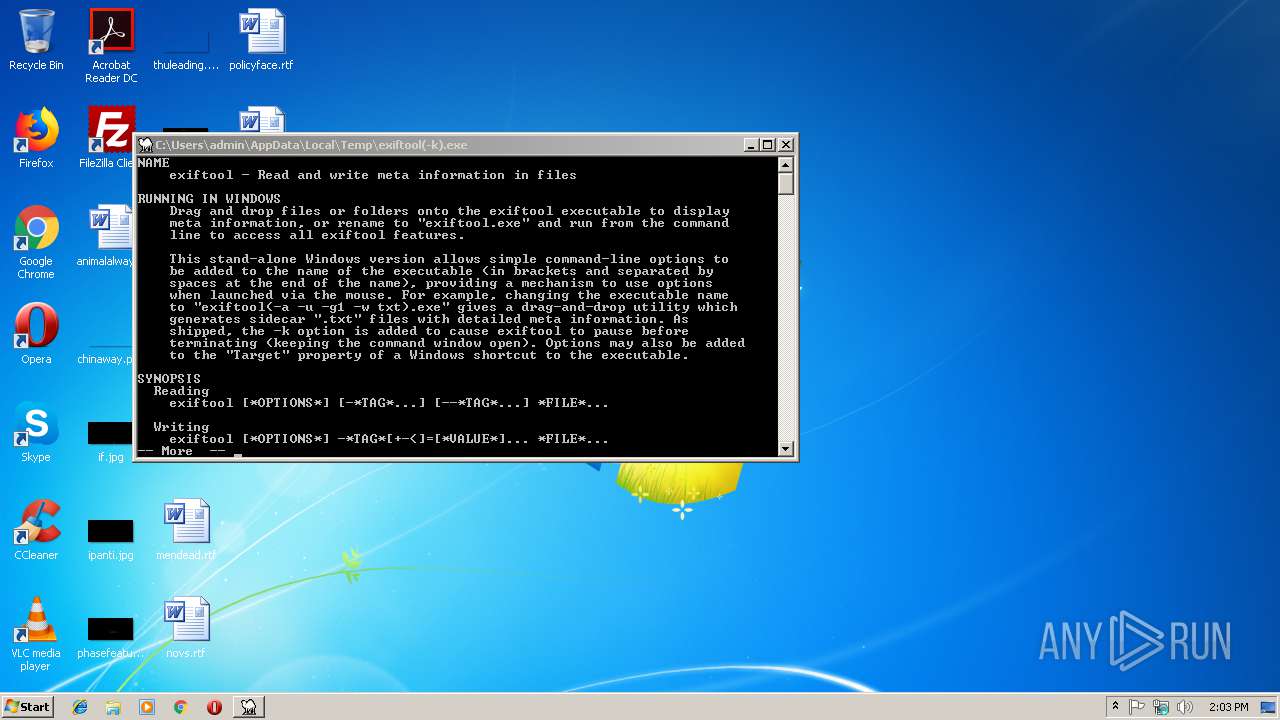
| File name: | exiftool(-k).exe |
| Full analysis: | https://app.any.run/tasks/b0e24ded-c21f-4b55-8781-1d1bb56be79f |
| Verdict: | Malicious activity |
| Analysis date: | January 29, 2019, 14:03:13 |
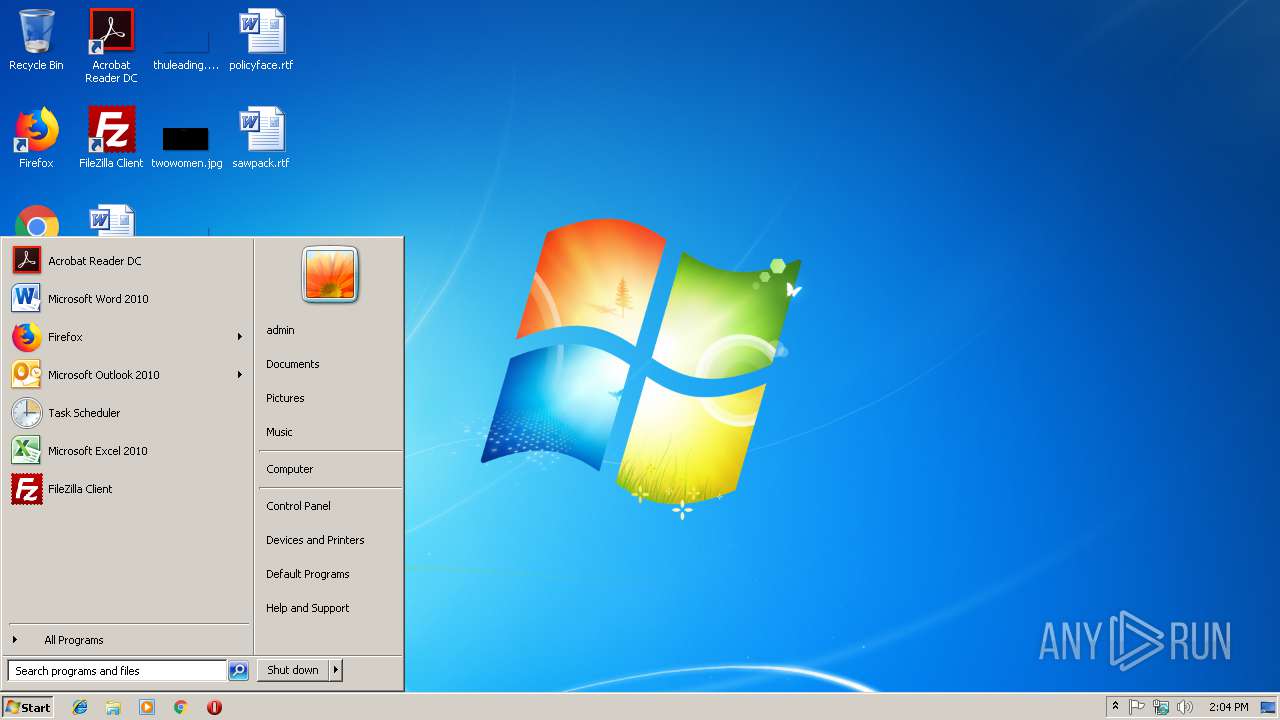
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386 (stripped to external PDB), for MS Windows |
| MD5: | C50F902CBBFBDF22C54E6BB5CCCF9BBB |
| SHA1: | C542240491A9D62EDA27A8217B6D85631989336B |
| SHA256: | 2CFFF1EF6EC3073166C1C15B09E059434ECB41A54AF96D8C685255CD399BB7FD |
| SSDEEP: | 196608:rhT227p+VDtj4Z/X8SxFC/KnfzNg1mPvKQ2jptOjt6W4vkljNWIsH6GXAG6gedVz:7Jhlj8IsH6GwG/2Vk+SGOoD |
MALICIOUS
Application was dropped or rewritten from another process
- exiftool(-k).exe (PID: 1428)
Loads dropped or rewritten executable
- exiftool(-k).exe (PID: 1428)
SUSPICIOUS
Executable content was dropped or overwritten
- exiftool(-k).exe (PID: 1428)
- exiftool(-k).exe (PID: 3260)
Starts CMD.EXE for commands execution
- exiftool(-k).exe (PID: 1428)
Starts application with an unusual extension
- cmd.exe (PID: 2136)
INFO
Dropped object may contain Bitcoin addresses
- exiftool(-k).exe (PID: 1428)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
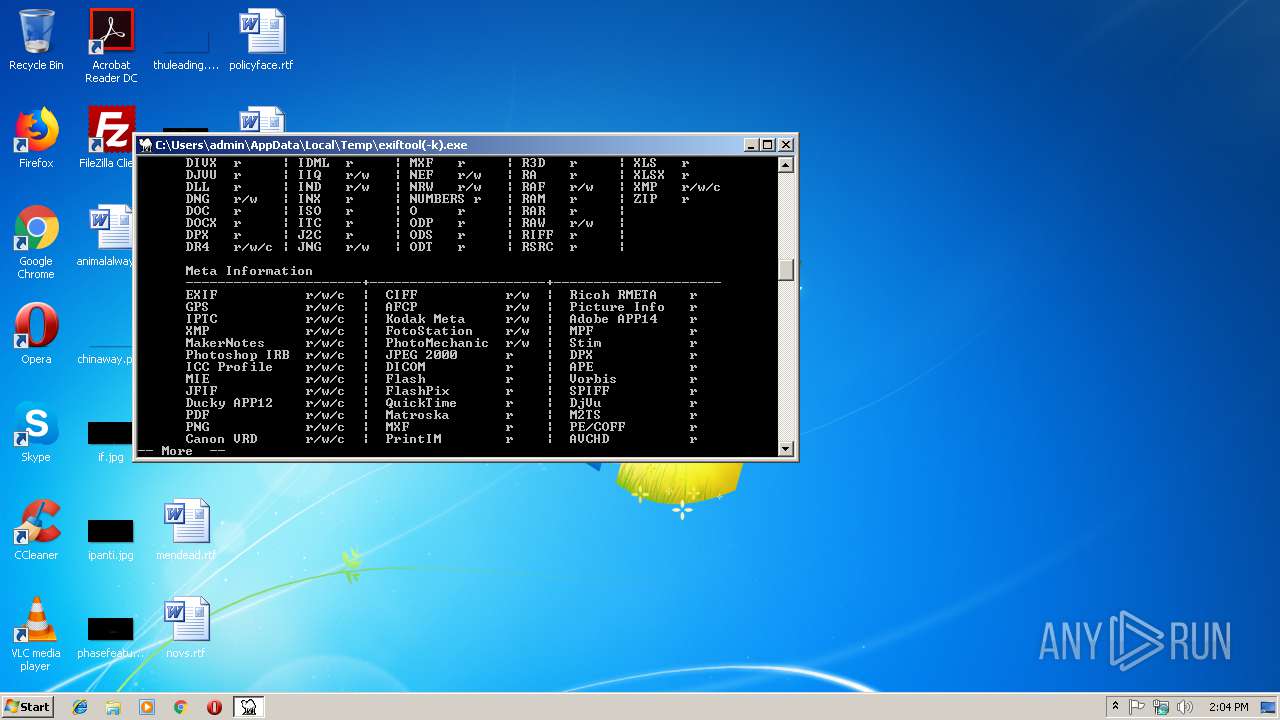
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:11:11 17:04:47+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.23 |
| CodeSize: | 16896 |
| InitializedDataSize: | 2024960 |
| UninitializedDataSize: | 34304 |
| EntryPoint: | 0x14e0 |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 11.2.6.0 |
| ProductVersionNumber: | 11.2.6.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| CompanyName: | - |
| FileDescription: | - |
| FileVersion: | 11.2.6.0 |
| InternalName: | exiftool.exe |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFileName: | exiftool.exe |
| ProductName: | - |
| ProductVersion: | 11.2.6.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 11-Nov-2016 16:04:47 |
| Detected languages: |
|
| TLS Callbacks: | 2 callback(s) detected. |
| CompanyName: | - |
| FileDescription: | - |
| FileVersion: | 11.2.6.0 |
| InternalName: | exiftool.exe |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFilename: | exiftool.exe |
| ProductName: | - |
| ProductVersion: | 11.2.6.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 11-Nov-2016 16:04:47 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00004164 | 0x00004200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.33156 |
.data | 0x00006000 | 0x001E6A48 | 0x001E6C00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.10105 |
.rdata | 0x001ED000 | 0x000005F0 | 0x00000600 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.39957 |
.bss | 0x001EE000 | 0x0000840C | 0x00000000 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x001F7000 | 0x00000928 | 0x00000A00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.76085 |
.CRT | 0x001F8000 | 0x00000034 | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.24913 |
.tls | 0x001F9000 | 0x00000020 | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.22482 |
.rsrc | 0x001FA000 | 0x000023F0 | 0x00002400 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.4425 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.94733 | 830 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 6.19723 | 2216 | UNKNOWN | English - United States | RT_ICON |
3 | 2.96054 | 1384 | UNKNOWN | English - United States | RT_ICON |
4 | 6.19723 | 2216 | UNKNOWN | English - United States | RT_ICON |
WINEXE | 2.48614 | 62 | UNKNOWN | English - United States | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
KERNEL32.dll |
msvcrt.dll |
Total processes
34
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
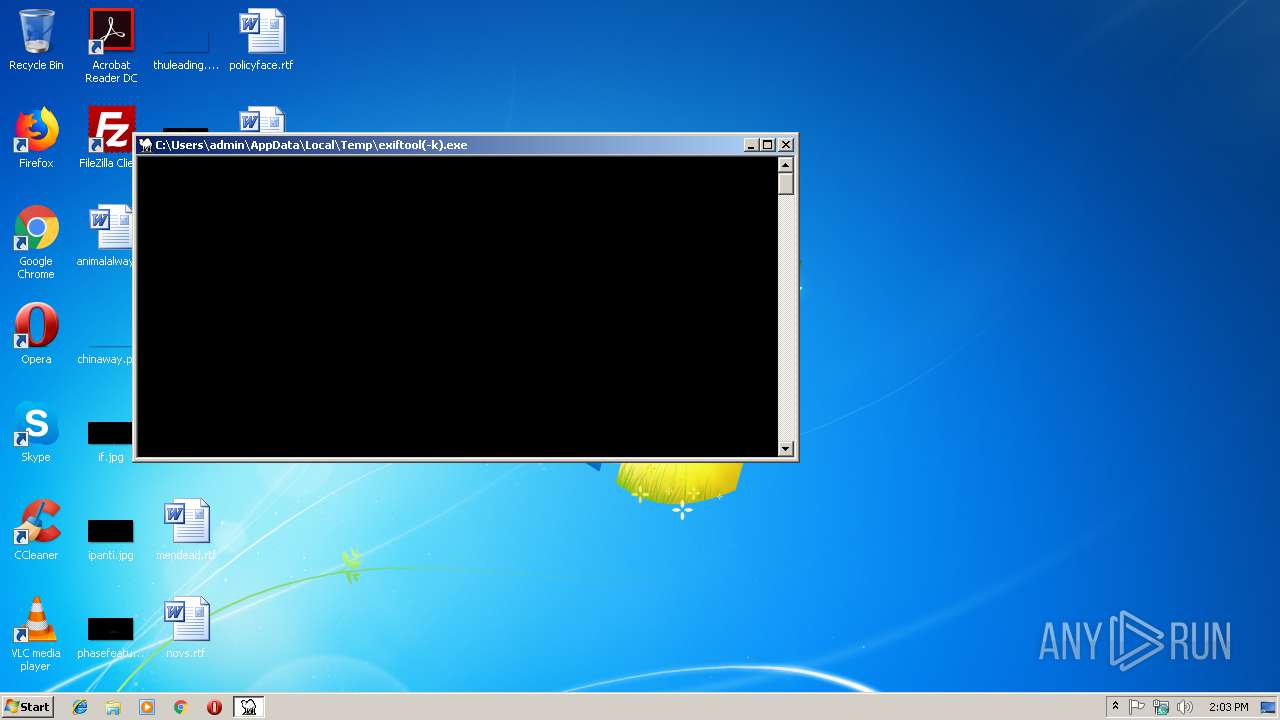
| 1428 | C:\Users\admin\AppData\Local\Temp\exiftool(-k).exe | C:\Users\admin\AppData\Local\Temp\par-61646d696e\cache-exiftool-11.26\exiftool(-k).exe | exiftool(-k).exe | ||||||||||||
User: admin Company: Integrity Level: MEDIUM Description: Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
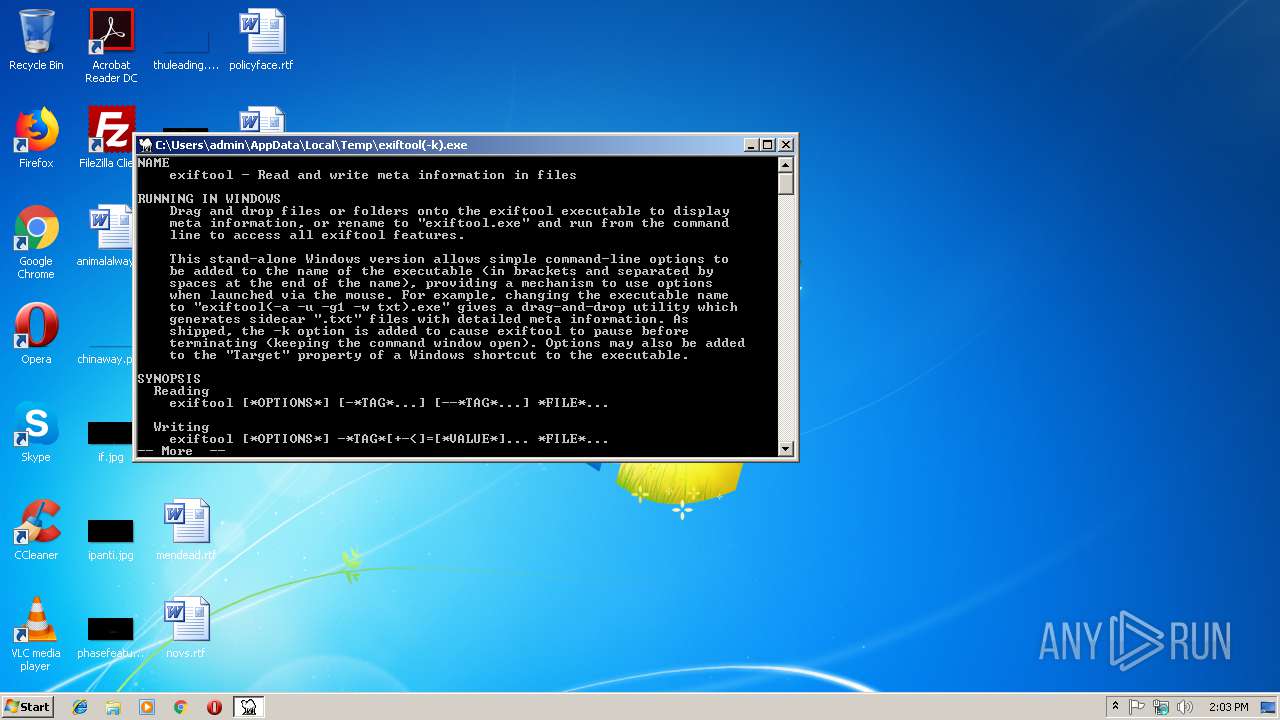
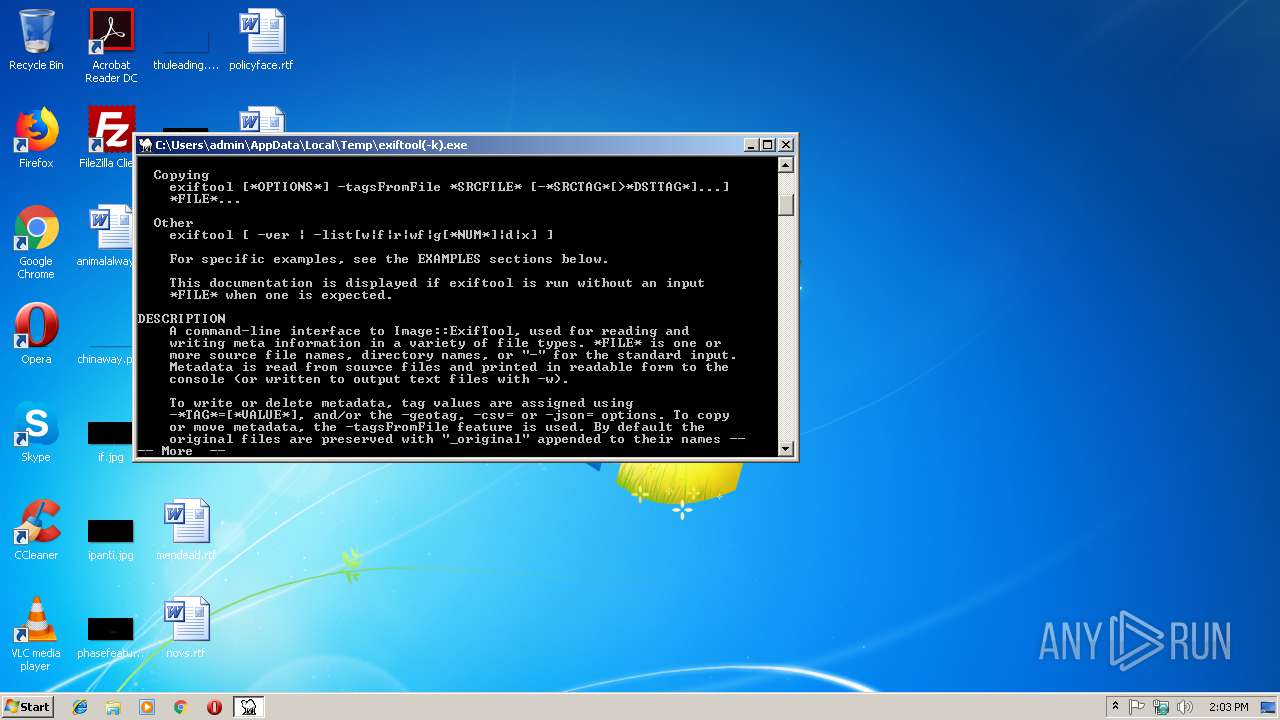
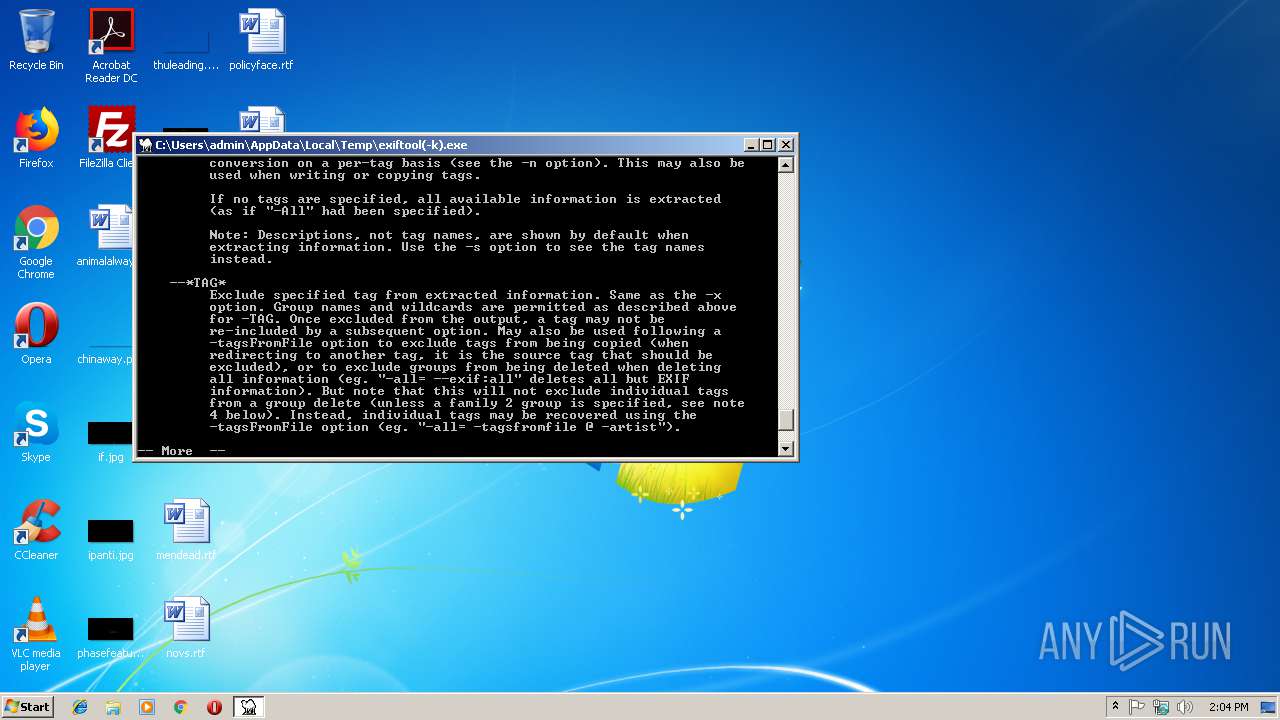
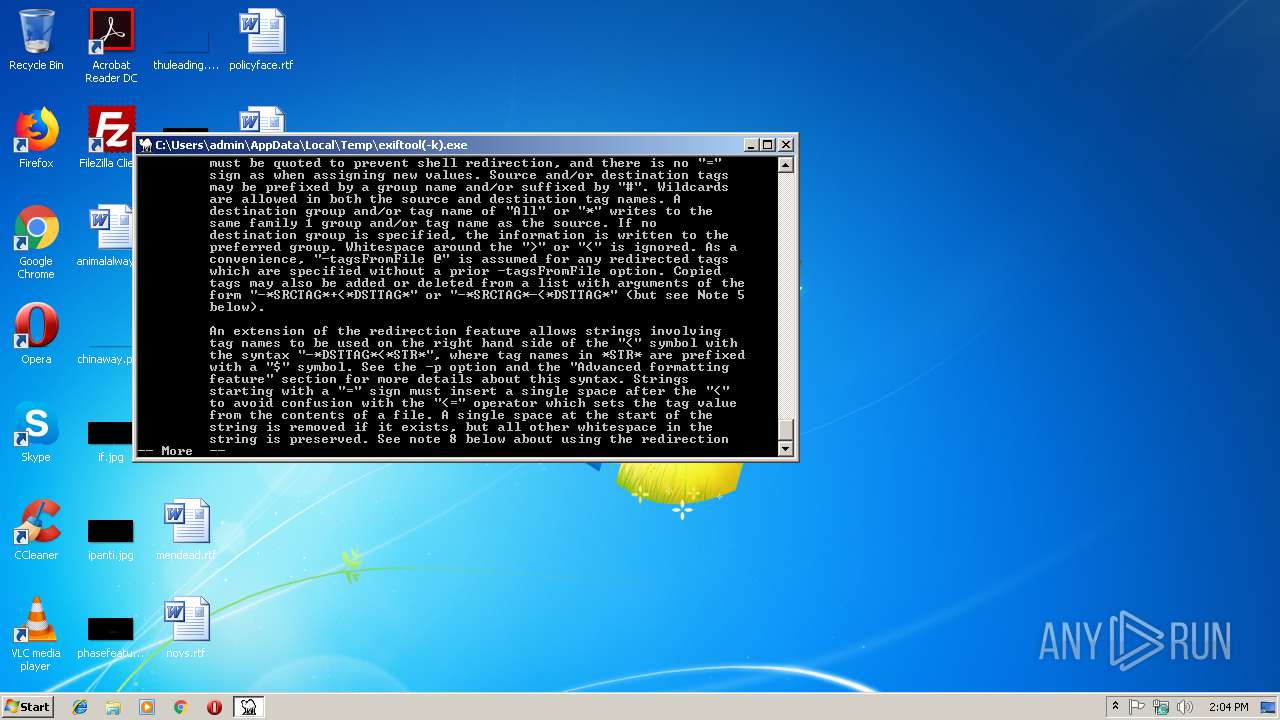
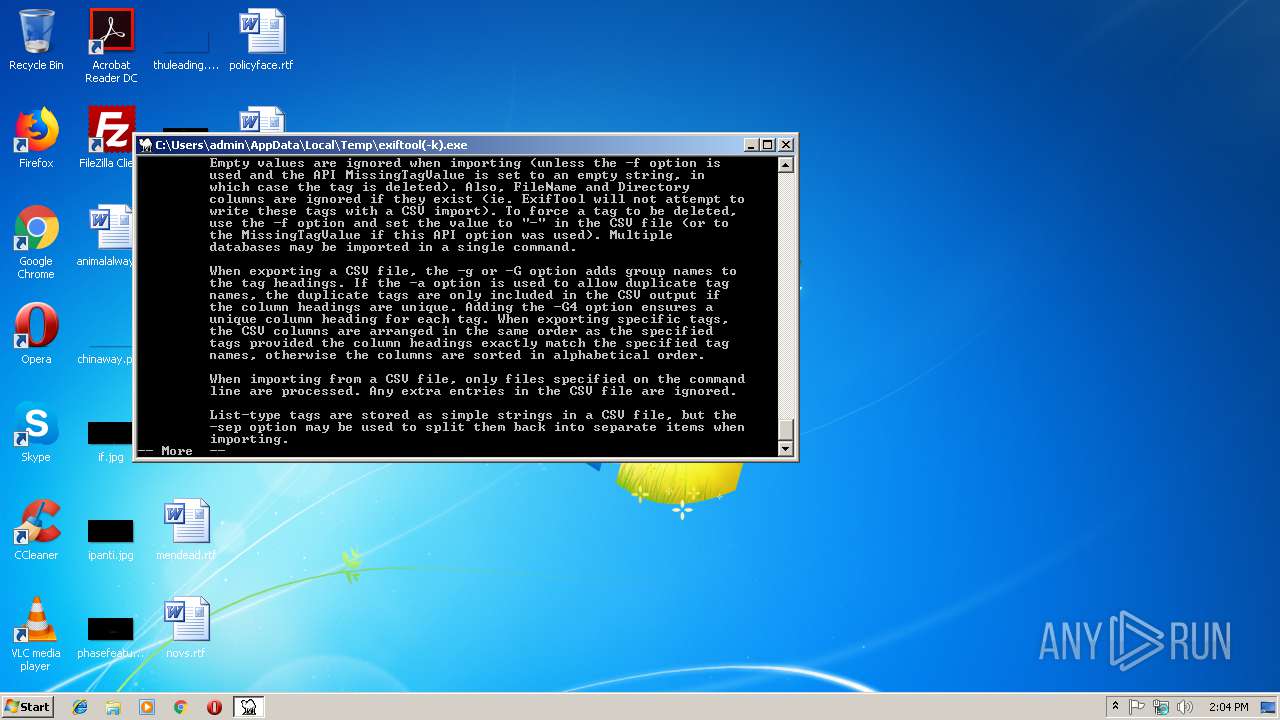
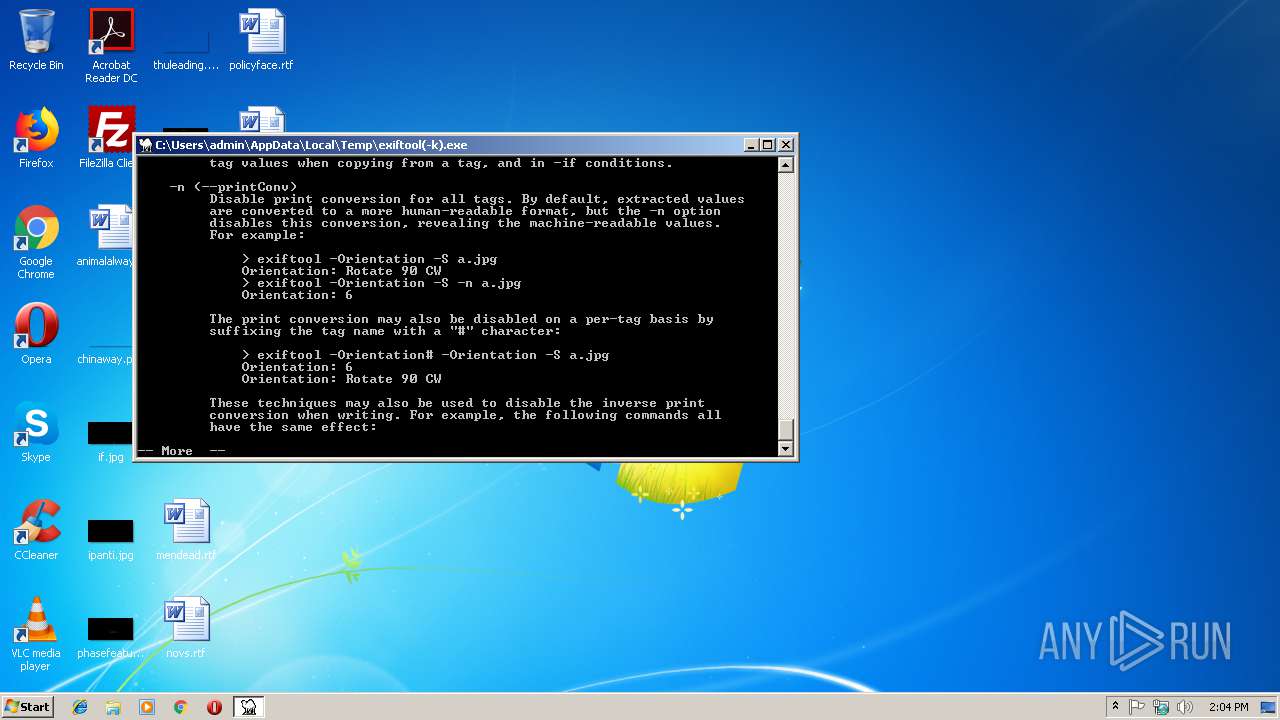
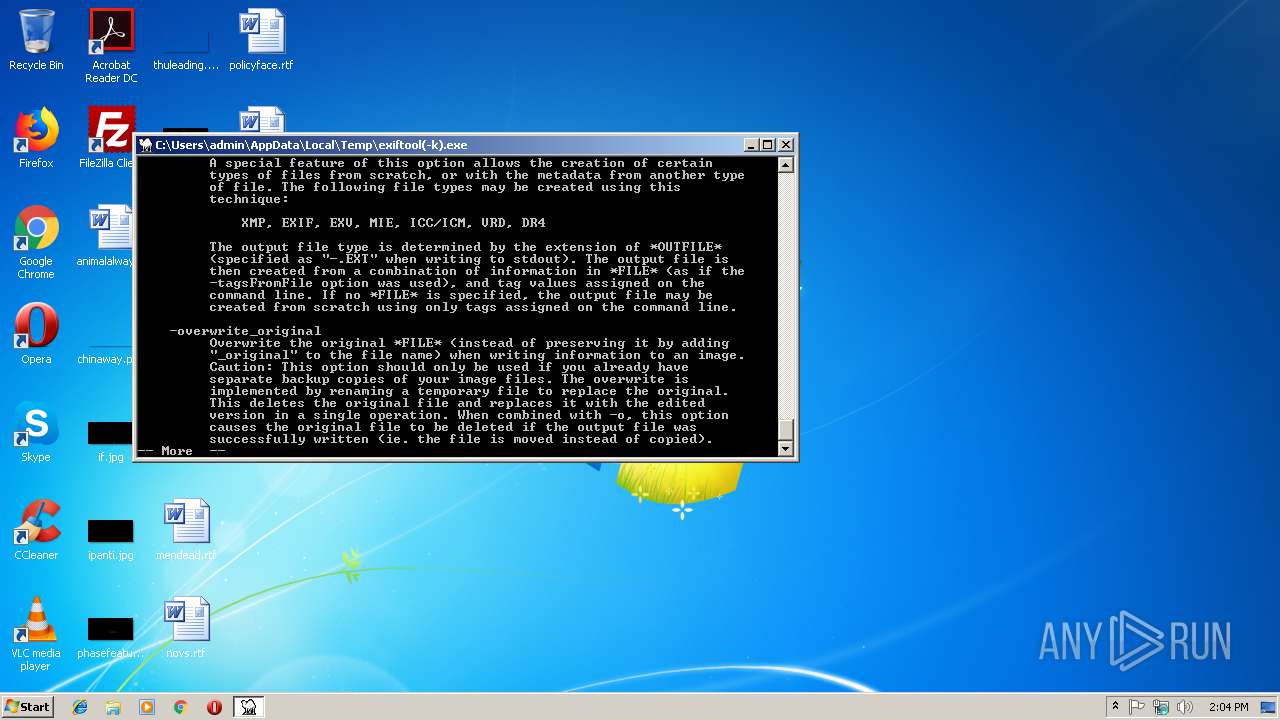
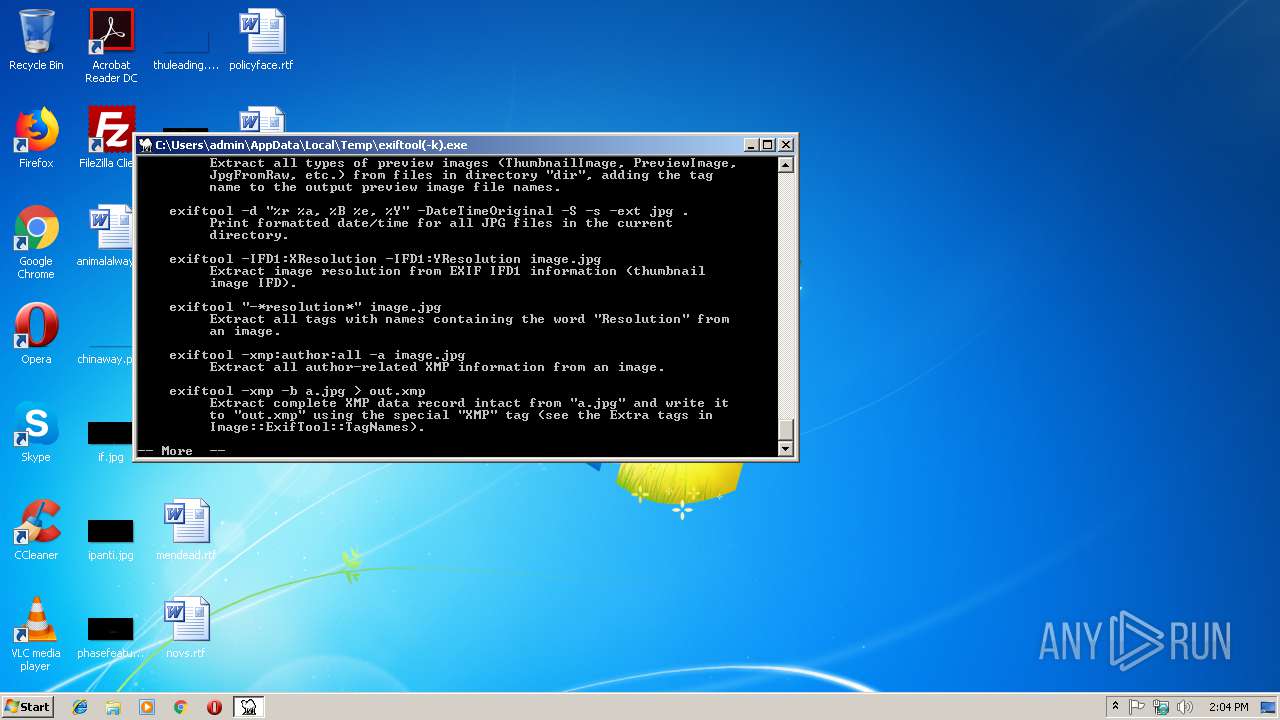
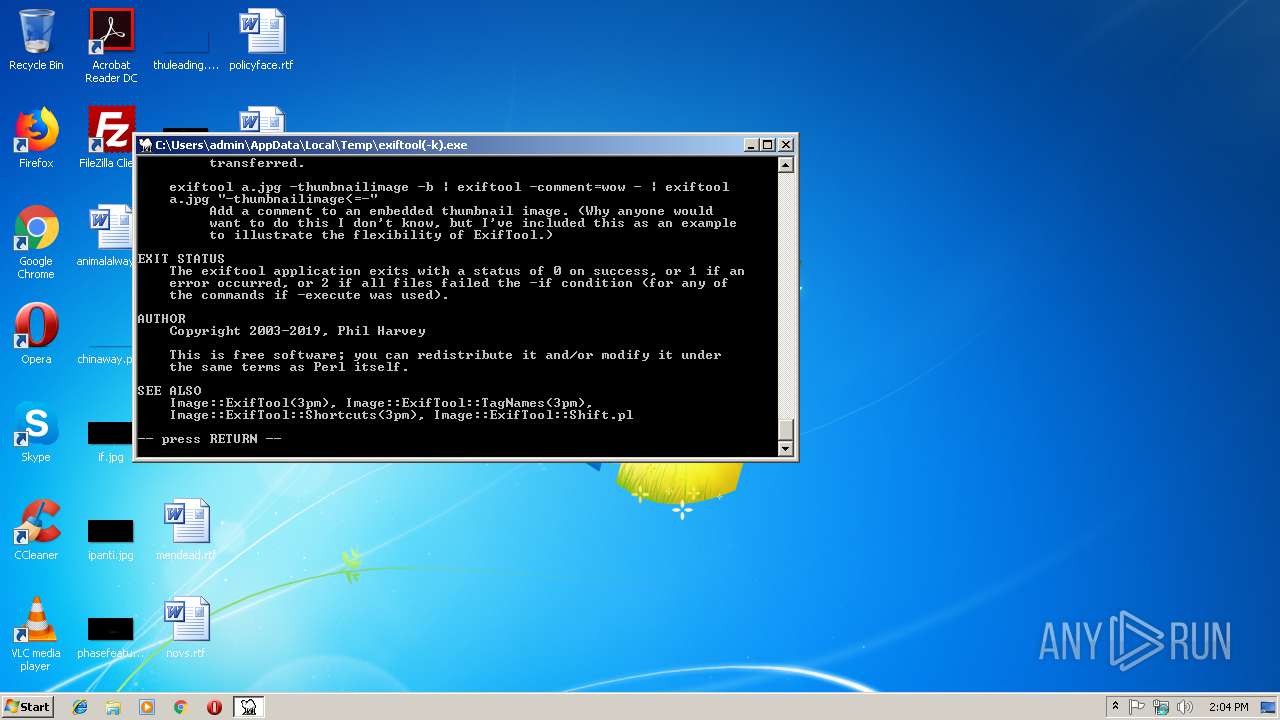
| 2136 | cmd.exe /x/d/c "more < "C:\Users\admin\AppData\Local\Temp\par-61646d696e\\exiftool_doc.txt"" | C:\Windows\system32\cmd.exe | — | exiftool(-k).exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2352 | more | C:\Windows\system32\more.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: More Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3260 | "C:\Users\admin\AppData\Local\Temp\exiftool(-k).exe" | C:\Users\admin\AppData\Local\Temp\exiftool(-k).exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 11.2.6.0 Modules
| |||||||||||||||
Total events
6
Read events
6
Write events
0
Delete events
0
Modification events
Executable files
40
Suspicious files
0
Text files
905
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3260 | exiftool(-k).exe | C:\Users\admin\AppData\Local\Temp\par-61646d696e\cache-exiftool-11.26\exiftool(-k).exe | executable | |
MD5:44D73F3664153A38A9CD02F9DE9C3E69 | SHA256:190FA21BCA88E2C4AC0EBEA467BE79F2FDA63CCD45915D72A2582CA30A3C7C67 | |||
| 1428 | exiftool(-k).exe | C:\Users\admin\AppData\Local\Temp\par-61646d696e\cache-exiftool-11.26\17d23068.pm | text | |
MD5:C5E041CA85C3220A127B1800DAC52B42 | SHA256:F6EA00190AFC89445065D6C3D66D6B0C257C460294B2B743CEAFC2C89B2620AB | |||
| 1428 | exiftool(-k).exe | C:\Users\admin\AppData\Local\Temp\par-61646d696e\cache-exiftool-11.26\6b9bcbc1.dll | executable | |
MD5:83E4A46C2DA50A551469DF4C299570FC | SHA256:9C0FA5A8BF5A0DCF7777C32A4DE912DC1844296995F7468C1152CACC2A8E2AC3 | |||
| 1428 | exiftool(-k).exe | C:\Users\admin\AppData\Local\Temp\par-61646d696e\cache-exiftool-11.26\349957b9.pm | text | |
MD5:089971C080D38FF3A2E14F1F2A2D1C33 | SHA256:BD51792E348BA19142700D4FC6A04E8CE7A74240C51A8A45291A3DFDC6CB0A8F | |||
| 1428 | exiftool(-k).exe | C:\Users\admin\AppData\Local\Temp\par-61646d696e\cache-exiftool-11.26\3165f85e.pm | text | |
MD5:8E60F0E521CD93DC4BCD536111D6EBEF | SHA256:57E212B12D516AEBAD05E791C9318CB5817C32231CDA7988910F0E2C3693B7A2 | |||
| 1428 | exiftool(-k).exe | C:\Users\admin\AppData\Local\Temp\par-61646d696e\cache-exiftool-11.26\db3a8f47.pm | text | |
MD5:44805CDE6A6B41E34D1CFE88452CBFCE | SHA256:F93FE254786F63D5A527F05BFD48A6B6A3FC5DD383420129C3AA0C736FD3BF5D | |||
| 1428 | exiftool(-k).exe | C:\Users\admin\AppData\Local\Temp\par-61646d696e\cache-exiftool-11.26\a09139d7.dll | executable | |
MD5:3B6B94455B45924FA688ECAD75EC182C | SHA256:D3FECA741DDC93F8646E74740BAB7DB17569A7A2594A8FFEA40A73F07B418870 | |||
| 1428 | exiftool(-k).exe | C:\Users\admin\AppData\Local\Temp\par-61646d696e\cache-exiftool-11.26\8b4e2b00.dll | executable | |
MD5:707F6CD0BA39238095A7CA6925708223 | SHA256:FA2960FE31C5DC687D11A93C22DDF03BE20714E7EE038BCEB54EC035CAC086A5 | |||
| 1428 | exiftool(-k).exe | C:\Users\admin\AppData\Local\Temp\par-61646d696e\cache-exiftool-11.26\6bc3ec17.pm | text | |
MD5:75AAFAF50168A3C6CBA70DB8E68C44DD | SHA256:2C8151EED953A979BBE8BE6B2C3C6435026C49E38C939D2C10B74B135D602EBD | |||
| 3260 | exiftool(-k).exe | C:\Users\admin\AppData\Local\Temp\par-61646d696e\cache-exiftool-11.26\perl524.dll | executable | |
MD5:8C356C17C26109175105543EF9289C3A | SHA256:E7BB8D0C256FFD88D050620D3817EA1699CA4EFAD5D3B4904A854EE88985104C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report