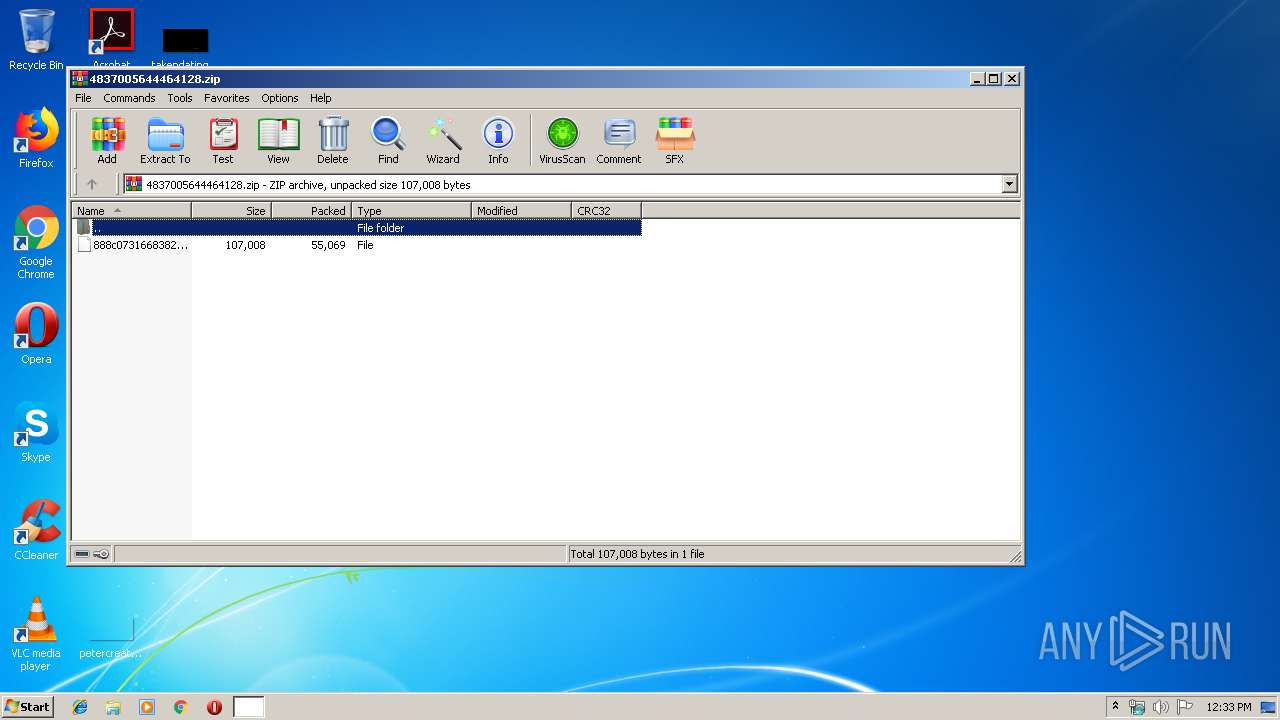
| File name: | 4837005644464128.zip |
| Full analysis: | https://app.any.run/tasks/20dad6a6-9b42-4976-ba77-5ecc064a6b47 |
| Verdict: | Malicious activity |
| Analysis date: | August 17, 2019, 11:33:10 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | DF7857EE42958585CD426417CD553AC3 |
| SHA1: | 6E38449B17AD4C3056F87C61797B1EB93CE88859 |
| SHA256: | 2CFC9FA5DF7FE60B91F0D57BBAD8F70C4C0F351DAFFF131C77D024422C9A34AC |
| SSDEEP: | 1536:SZbZ8JM8iqCaG9uPTYq0dZyO5PO6nbhUO2huf:kbZz/qQuPTcJ5Gk2huf |
MALICIOUS
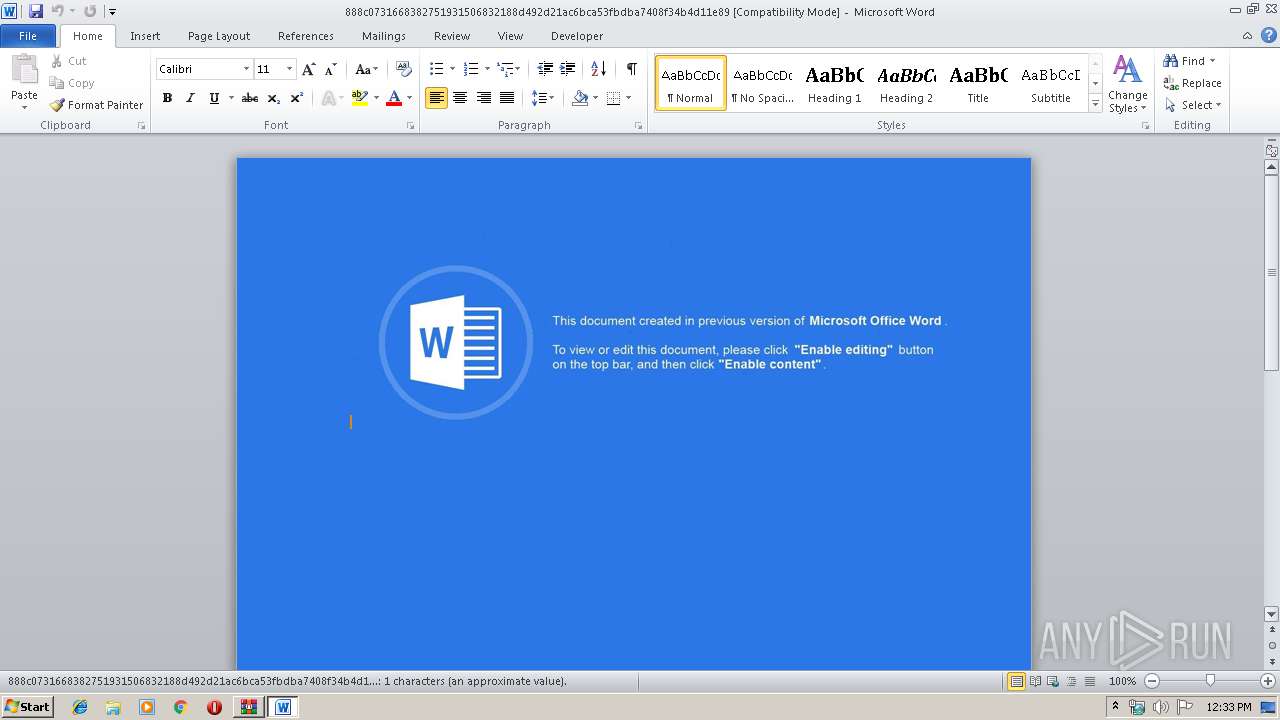
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 3896)
Uses WMIC.EXE to invoke XSL script
- WINWORD.EXE (PID: 3896)
SUSPICIOUS
Uses RUNDLL32.EXE to load library
- WinRAR.exe (PID: 3496)
Starts Microsoft Office Application
- rundll32.exe (PID: 2276)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 3896)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3896)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 1980:00:00 00:00:00 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | 55069 |
| ZipUncompressedSize: | 107008 |
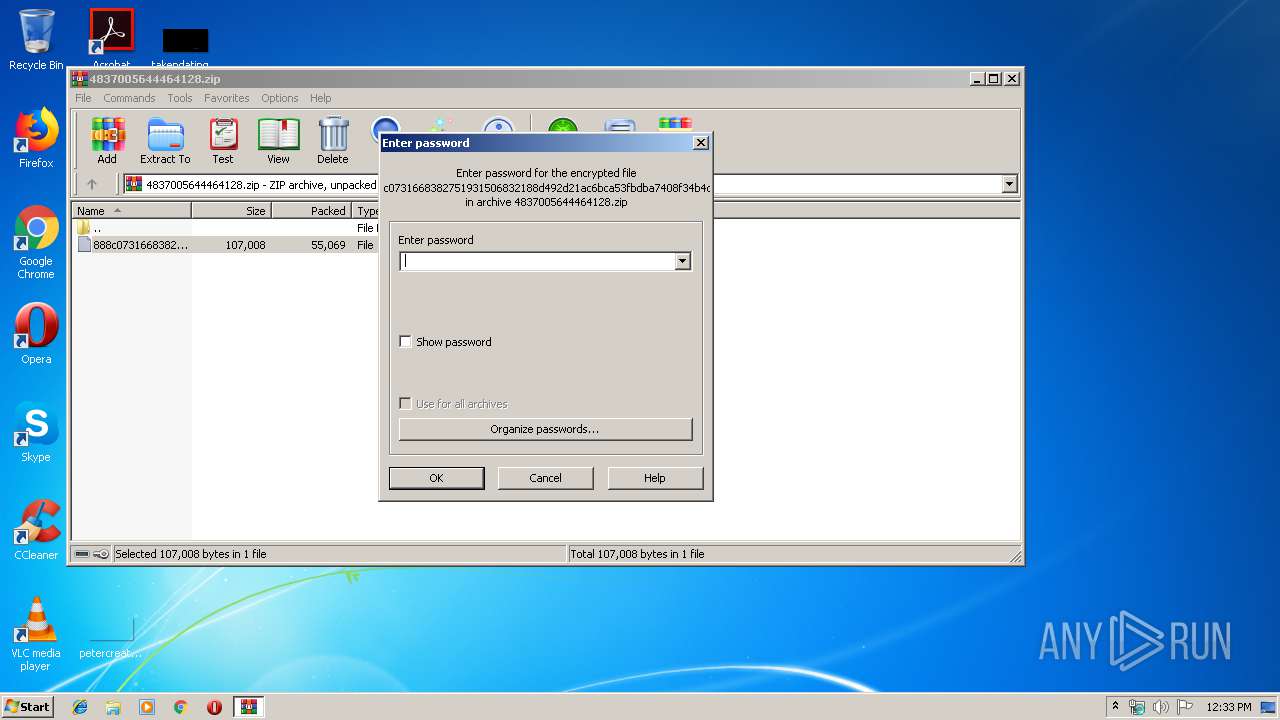
| ZipFileName: | 888c0731668382751931506832188d492d21ac6bca53fbdba7408f34b4d11e89 |
Total processes
38
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
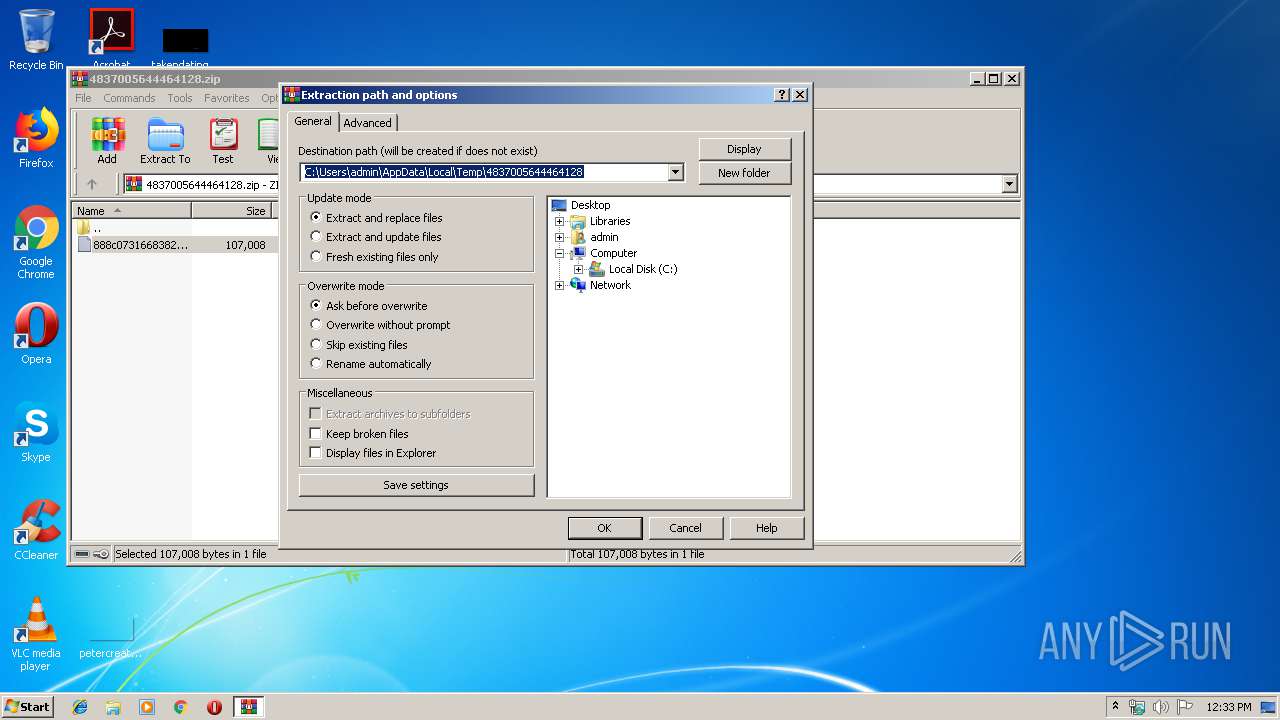
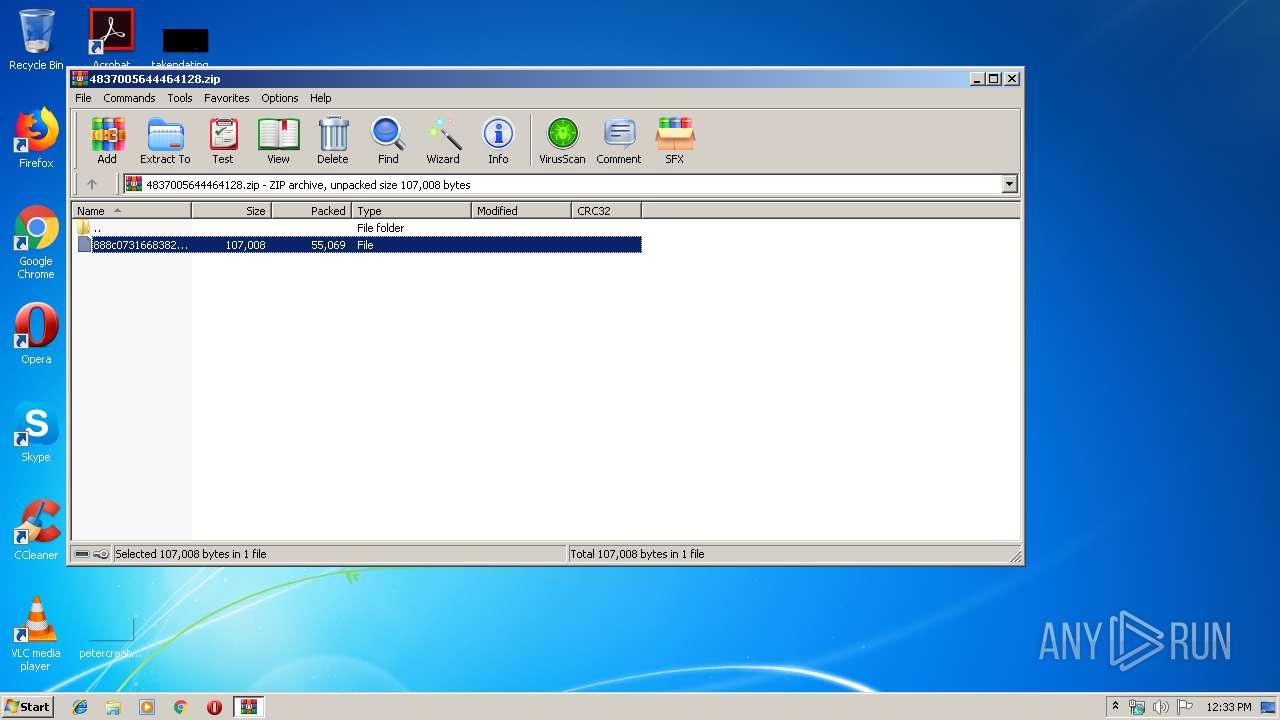
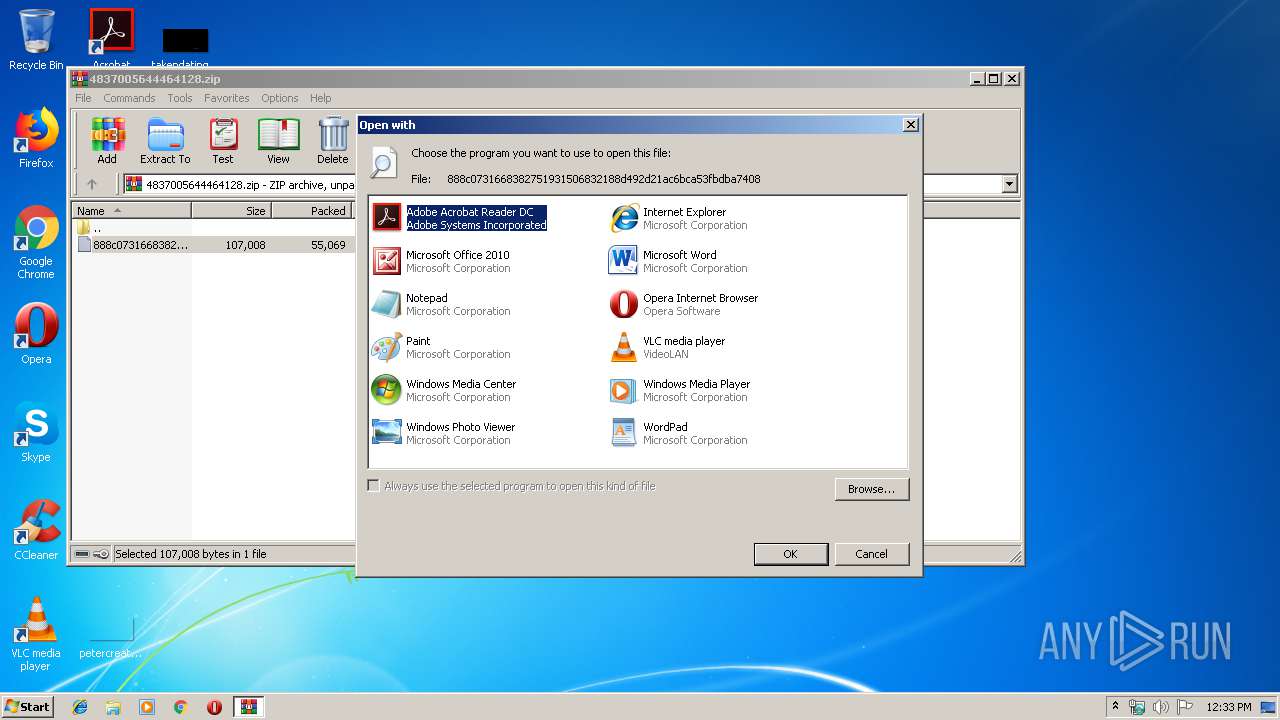
| 2276 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\AppData\Local\Temp\Rar$DIb3496.12735\888c0731668382751931506832188d492d21ac6bca53fbdba7408f34b4d11e89 | C:\Windows\system32\rundll32.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3496 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\4837005644464128.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3740 | "C:\Windows\System32\wbem\wmic.exe" process list /format:"aOlNZc.xsl" | C:\Windows\System32\wbem\wmic.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 2147614729 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3896 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Rar$DIb3496.12735\888c0731668382751931506832188d492d21ac6bca53fbdba7408f34b4d11e89" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
2 070
Read events
1 583
Write events
482
Delete events
5
Modification events
| (PID) Process: | (3496) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3496) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3496) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3496) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\4837005644464128.zip | |||
| (PID) Process: | (3496) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3496) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3496) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3496) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3496) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (3496) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
1
Text files
1
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3896 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVREE4.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3896 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\aOlNZc.xsl | xml | |
MD5:— | SHA256:— | |||
| 3896 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3896 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 3896 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Rar$DIb3496.12735\~$8c0731668382751931506832188d492d21ac6bca53fbdba7408f34b4d11e89 | pgc | |
MD5:— | SHA256:— | |||
| 3496 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb3496.12735\888c0731668382751931506832188d492d21ac6bca53fbdba7408f34b4d11e89 | document | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
mgregyoherminio.com |
| unknown |