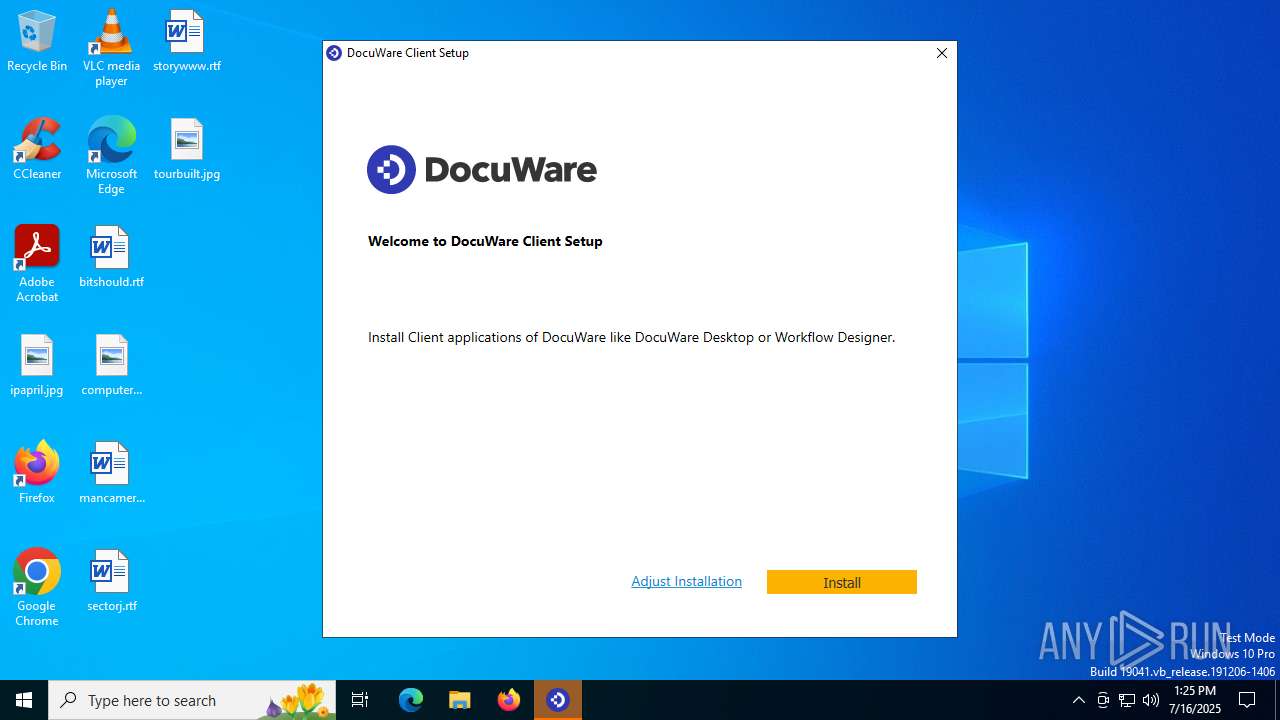
| File name: | ClientSetup.https#bpnl.docuware.cloud#443#.exe |
| Full analysis: | https://app.any.run/tasks/f74e3a42-3f71-4433-8548-70d323b74184 |
| Verdict: | Malicious activity |
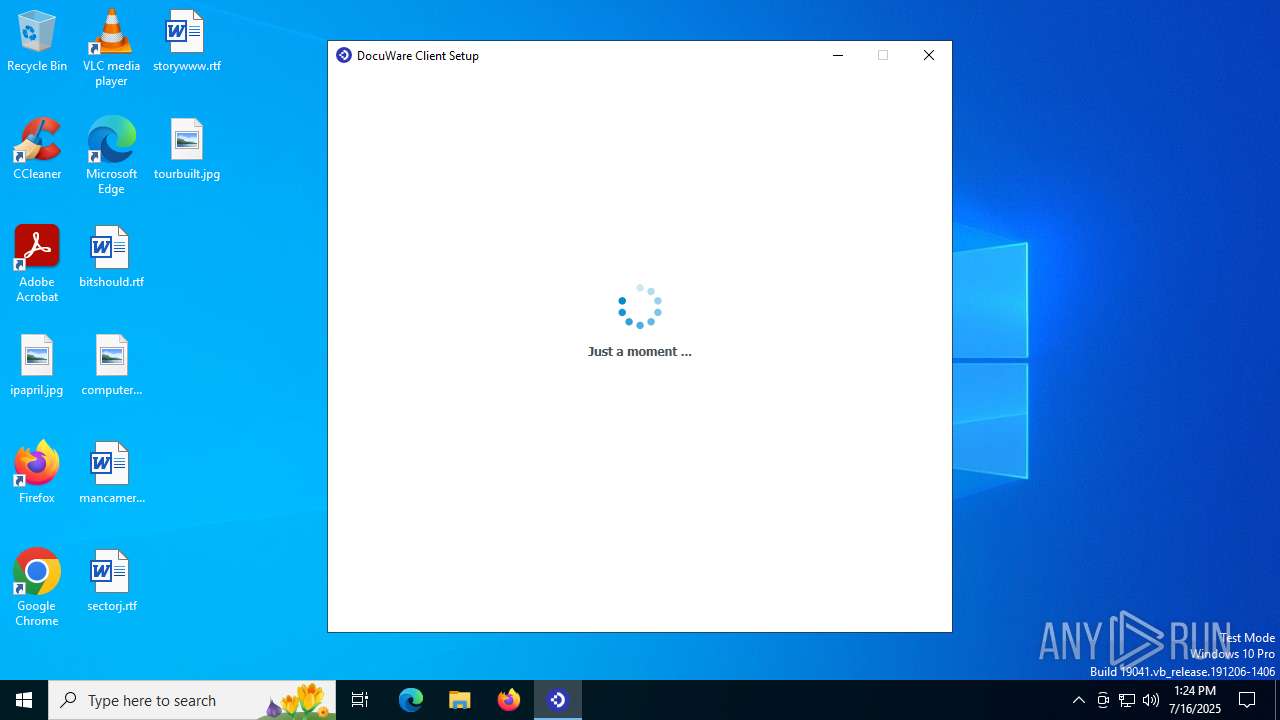
| Analysis date: | July 16, 2025, 13:24:44 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | FCE57E764B6242B2C736FF22529BB015 |
| SHA1: | B7E399A6493FD99FE416A8FAA76F6E9C98607A59 |
| SHA256: | 2CE2C2F737D7D70B058B8E4D9DAAC3EA88D2449EBA74B795C2EDD0030CA255D0 |
| SSDEEP: | 49152:tSb2xpQbl3H+DgB4hUARefOCWZUGRQxRY47rzoKUMhDLft6DOOz:tShAP |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads security settings of Internet Explorer
- ClientSetup.https#bpnl.docuware.cloud#443#.exe (PID: 1392)
- DocuWare.Setup.Client.Bootstrapper.exe (PID: 2280)
- DocuWare.Setup.Client.Bootstrapper.exe (PID: 7080)
- DocuWare.Setup.Client.exe (PID: 5236)
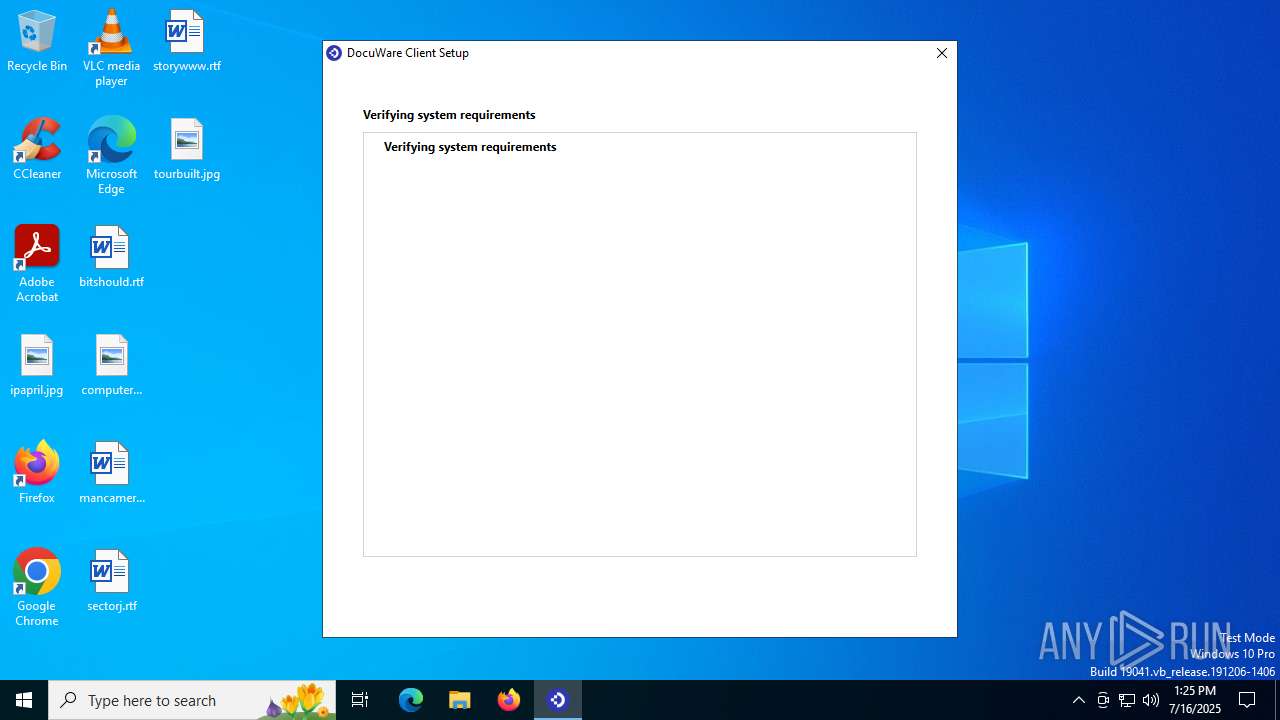
Application launched itself
- DocuWare.Setup.Client.Bootstrapper.exe (PID: 2280)
- updater.exe (PID: 4760)
Process drops legitimate windows executable
- DocuWare.Setup.Client.Bootstrapper.exe (PID: 7080)
- msiexec.exe (PID: 6664)
- DocuWare.Setup.Client.exe (PID: 5236)
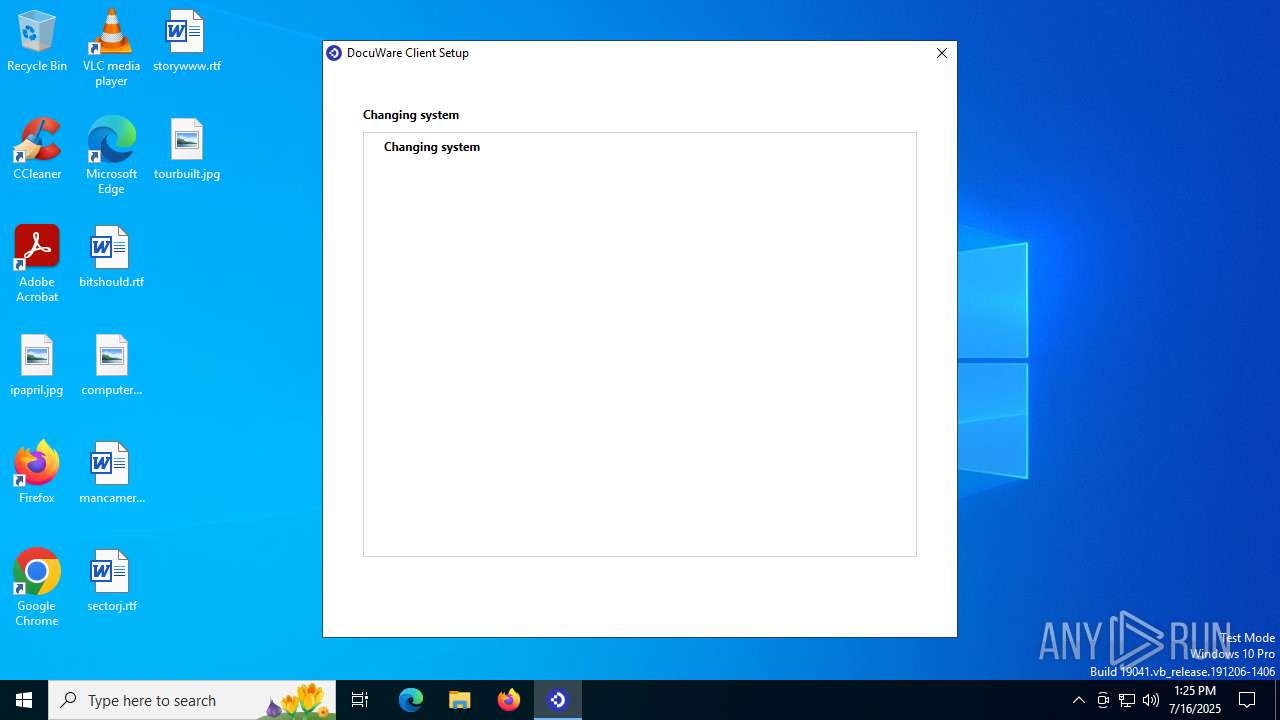
Executable content was dropped or overwritten
- DocuWare.Setup.Client.Bootstrapper.exe (PID: 7080)
- DocuWare.Setup.Client.exe (PID: 5236)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 6664)
The process creates files with name similar to system file names
- msiexec.exe (PID: 6664)
Starts CMD.EXE for commands execution
- DocuWare.Setup.Client.exe (PID: 5236)
Executing commands from ".cmd" file
- DocuWare.Setup.Client.exe (PID: 5236)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 5348)
The process executes via Task Scheduler
- updater.exe (PID: 4760)
INFO
Checks supported languages
- ClientSetup.https#bpnl.docuware.cloud#443#.exe (PID: 1392)
- DocuWare.Setup.Client.Bootstrapper.exe (PID: 2280)
- msiexec.exe (PID: 6664)
- DocuWare.Setup.Client.exe (PID: 5236)
- updater.exe (PID: 4760)
- updater.exe (PID: 3932)
- DocuWare.Setup.Client.Bootstrapper.exe (PID: 7080)
The sample compiled with german language support
- ClientSetup.https#bpnl.docuware.cloud#443#.exe (PID: 1392)
- msiexec.exe (PID: 6664)
Process checks computer location settings
- DocuWare.Setup.Client.Bootstrapper.exe (PID: 2280)
- ClientSetup.https#bpnl.docuware.cloud#443#.exe (PID: 1392)
- DocuWare.Setup.Client.Bootstrapper.exe (PID: 7080)
Reads the computer name
- DocuWare.Setup.Client.Bootstrapper.exe (PID: 2280)
- ClientSetup.https#bpnl.docuware.cloud#443#.exe (PID: 1392)
- DocuWare.Setup.Client.Bootstrapper.exe (PID: 7080)
- msiexec.exe (PID: 6664)
- DocuWare.Setup.Client.exe (PID: 5236)
- updater.exe (PID: 4760)
Create files in a temporary directory
- ClientSetup.https#bpnl.docuware.cloud#443#.exe (PID: 1392)
- DocuWare.Setup.Client.exe (PID: 5236)
- DocuWare.Setup.Client.Bootstrapper.exe (PID: 7080)
Reads the machine GUID from the registry
- DocuWare.Setup.Client.Bootstrapper.exe (PID: 2280)
- DocuWare.Setup.Client.Bootstrapper.exe (PID: 7080)
- msiexec.exe (PID: 6664)
- DocuWare.Setup.Client.exe (PID: 5236)
Creates files in the program directory
- DocuWare.Setup.Client.Bootstrapper.exe (PID: 7080)
- msiexec.exe (PID: 7056)
- DocuWare.Setup.Client.exe (PID: 5236)
Disables trace logs
- DocuWare.Setup.Client.Bootstrapper.exe (PID: 7080)
- DocuWare.Setup.Client.exe (PID: 5236)
Reads the software policy settings
- DocuWare.Setup.Client.Bootstrapper.exe (PID: 7080)
- msiexec.exe (PID: 6664)
- DocuWare.Setup.Client.exe (PID: 5236)
Executable content was dropped or overwritten
- msiexec.exe (PID: 6664)
Creates a software uninstall entry
- msiexec.exe (PID: 6664)
The sample compiled with english language support
- msiexec.exe (PID: 6664)
- DocuWare.Setup.Client.exe (PID: 5236)
Creates files or folders in the user directory
- DocuWare.Setup.Client.Bootstrapper.exe (PID: 7080)
Reads CPU info
- DocuWare.Setup.Client.exe (PID: 5236)
Process checks whether UAC notifications are on
- updater.exe (PID: 4760)
Checks proxy server information
- DocuWare.Setup.Client.Bootstrapper.exe (PID: 7080)
- DocuWare.Setup.Client.exe (PID: 5236)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (17.3) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (4.1) |
| .exe | | | Win32 Executable (generic) (2.8) |
| .exe | | | Generic Win/DOS Executable (1.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:02:18 09:02:41+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.16 |
| CodeSize: | 46592 |
| InitializedDataSize: | 1693696 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2144 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 7.11.364.0 |
| ProductVersionNumber: | 7.11.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | German |
| CharacterSet: | Unicode |
| CompanyName: | DocuWare GmbH |
| FileDescription: | DocuWare Client Setup |
| FileVersion: | 7,11,364,0 |
| InternalName: | ClientSetup.exe |
| LegalCopyright: | Copyright © DocuWare 2024 |
| OriginalFileName: | ClientSetup.exe |
| ProductName: | DocuWare |
| ProductVersion: | Version 7.11 [DocuWare.Setup.Client Release [Viper]_20250218.1] |
Total processes
148
Monitored processes
12
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1392 | "C:\Users\admin\AppData\Local\Temp\ClientSetup.https#bpnl.docuware.cloud#443#.exe" | C:\Users\admin\AppData\Local\Temp\ClientSetup.https#bpnl.docuware.cloud#443#.exe | — | explorer.exe | |||||||||||
User: admin Company: DocuWare GmbH Integrity Level: MEDIUM Description: DocuWare Client Setup Exit code: 0 Version: 7,11,364,0 Modules
| |||||||||||||||
| 2280 | "C:\Users\admin\AppData\Local\Temp\DocuWare\Temp\ClientSetup\DocuWare.Setup.Client.Bootstrapper.exe" ClientSetup.https#bpnl.docuware.cloud#443#.exe | C:\Users\admin\AppData\Local\Temp\DocuWare\Temp\ClientSetup\DocuWare.Setup.Client.Bootstrapper.exe | — | ClientSetup.https#bpnl.docuware.cloud#443#.exe | |||||||||||
User: admin Company: DocuWare GmbH Integrity Level: MEDIUM Description: DocuWare Client Setup Exit code: 0 Version: 7.11.364.0 Modules
| |||||||||||||||
| 3160 | "C:\WINDOWS\system32\reg.exe" add HKLM\SOFTWARE\DocuWare\Setup /v SettingsPath /t REG_SZ /d "https://bpnl.docuware.cloud/DocuWare/Platform/Home/ClientSetupInfo?orgId=&baseAddress=https%3a%2f%2fbpnl.docuware.cloud%2fDocuWare%2fPlatform" /f /reg:32 | C:\Windows\SysWOW64\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3932 | "C:\Program Files (x86)\Google\GoogleUpdater\134.0.6985.0\updater.exe" --crash-handler --system "--database=C:\Program Files (x86)\Google\GoogleUpdater\134.0.6985.0\Crashpad" --url=https://clients2.google.com/cr/report --annotation=prod=Update4 --annotation=ver=134.0.6985.0 "--attachment=C:\Program Files (x86)\Google\GoogleUpdater\updater.log" --initial-client-data=0x2a0,0x2a4,0x2a8,0x27c,0x2ac,0x111c460,0x111c46c,0x111c478 | C:\Program Files (x86)\Google\GoogleUpdater\134.0.6985.0\updater.exe | — | updater.exe | |||||||||||
User: SYSTEM Company: Google LLC Integrity Level: SYSTEM Description: Google Updater Exit code: 0 Version: 134.0.6985.0 Modules
| |||||||||||||||
| 4120 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4760 | "C:\Program Files (x86)\Google\GoogleUpdater\134.0.6985.0\updater.exe" --wake --system | C:\Program Files (x86)\Google\GoogleUpdater\134.0.6985.0\updater.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Google LLC Integrity Level: SYSTEM Description: Google Updater Exit code: 0 Version: 134.0.6985.0 Modules
| |||||||||||||||
| 5236 | "C:\Program Files (x86)\DocuWare\Client Setup\DocuWare.Setup.Client.exe" PLATFORMPATH=https://bpnl.docuware.cloud/DocuWare/Platform/Home/ClientSetupInfo?orgId=&baseAddress=https%3a%2f%2fbpnl.docuware.cloud%2fDocuWare%2fPlatform | C:\Program Files (x86)\DocuWare\Client Setup\DocuWare.Setup.Client.exe | DocuWare.Setup.Client.Bootstrapper.exe | ||||||||||||
User: admin Company: DocuWare GmbH Integrity Level: HIGH Description: DocuWare Client Setup Version: 7.11.364.0 Modules
| |||||||||||||||
| 5348 | "C:\WINDOWS\system32\cmd.exe" /Q /C C:\Users\admin\AppData\Local\Temp\tmpfbdd1f1c08e54e2e84698d172df226c7.exec.cmd | C:\Windows\SysWOW64\cmd.exe | — | DocuWare.Setup.Client.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5712 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6664 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
16 112
Read events
15 868
Write events
235
Delete events
9
Modification events
| (PID) Process: | (7080) DocuWare.Setup.Client.Bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\DocuWare_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (7080) DocuWare.Setup.Client.Bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\DocuWare_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (7080) DocuWare.Setup.Client.Bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\DocuWare_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (7080) DocuWare.Setup.Client.Bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\DocuWare_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (7080) DocuWare.Setup.Client.Bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\DocuWare_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (7080) DocuWare.Setup.Client.Bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\DocuWare_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (7080) DocuWare.Setup.Client.Bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\DocuWare_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (7080) DocuWare.Setup.Client.Bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\DocuWare_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (7080) DocuWare.Setup.Client.Bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\DocuWare_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (7080) DocuWare.Setup.Client.Bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\DocuWare_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
90
Suspicious files
14
Text files
29
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7080 | DocuWare.Setup.Client.Bootstrapper.exe | C:\Users\admin\AppData\Local\Temp\DocuWare\Temp\ClientSetup\DocuWare.ClientSetup.msi | executable | |
MD5:86056D7857859B27CD4F21EF48232126 | SHA256:B8DB5D1076DF7F45F35503205CC6C930B2DCC327886AB1BA489EEC9EAE6A767D | |||
| 7080 | DocuWare.Setup.Client.Bootstrapper.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\698460A0B6E60F2F602361424D832905_8BB23D43DE574E82F2BEE0DF0EC47EEB | der | |
MD5:54E5C0D7AC2F50BC892222404806CD75 | SHA256:C7EF0359B42407FEC3CA4036852859B3CB7686F13D9E481D884B5A274B737AD5 | |||
| 7080 | DocuWare.Setup.Client.Bootstrapper.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\C8E534EE129F27D55460CE17FD628216_1130D9B25898B0DB0D4F04DC5B93F141 | binary | |
MD5:27922B249669C3EBDF6D1FAD88B246D4 | SHA256:B460A042B4B9AFB3F9B511C4C854CE5C236C155ADC55585B025709214DB489FB | |||
| 7080 | DocuWare.Setup.Client.Bootstrapper.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\C8E534EE129F27D55460CE17FD628216_1130D9B25898B0DB0D4F04DC5B93F141 | der | |
MD5:9C4FF868311518A564112496F64DC263 | SHA256:C426916634841E120E7193BD31575BD7ADA9B7DC400E71EB9D39B6E6771B8E24 | |||
| 7080 | DocuWare.Setup.Client.Bootstrapper.exe | C:\ProgramData\DocuWare\ClientSetup\DocuWare.ClientSetupBootstrapper.log | text | |
MD5:43302DF8E33E2AE7C5504A82763ACC41 | SHA256:CE797E2F85507ED8D9C5E6039980C454ED55285F29F08F219C1967322D7D51B3 | |||
| 6664 | msiexec.exe | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\ngen.log | text | |
MD5:F575E331552CE7CE07FFF14A8AD1884D | SHA256:09DF9970D1669AB406CC0BA4C91B825ACBC1C65C809ACFE541BEC734C6C0F2A4 | |||
| 7080 | DocuWare.Setup.Client.Bootstrapper.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\8EC9B1D0ABBD7F98B401D425828828CE_E03DBDC17E023613021073057466889B | der | |
MD5:E015FCF0F197760D79C36A5E68CA8CBE | SHA256:838516E4212D24BBF99D0F5B452CFF95FCA42438553F73EDA1BB49575209AD4D | |||
| 7080 | DocuWare.Setup.Client.Bootstrapper.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\698460A0B6E60F2F602361424D832905_8BB23D43DE574E82F2BEE0DF0EC47EEB | binary | |
MD5:2C461C04D875C9046E5BFCEC72F7B5DE | SHA256:A39C79B8C69189CDEFBF95A8D3054CEAC5F278EFD5EF0C4039B139A32478A7B6 | |||
| 6664 | msiexec.exe | C:\Windows\Installer\MSIE23D.tmp | binary | |
MD5:2420F951856A7E0246A1E08A33524150 | SHA256:B2C1C71968319675FB4AC3750500F38553408DAFAA219159E0FB8BA686E9FA99 | |||
| 7080 | DocuWare.Setup.Client.Bootstrapper.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\8EC9B1D0ABBD7F98B401D425828828CE_E03DBDC17E023613021073057466889B | binary | |
MD5:D7A1C94B5D3998C13F9B88599D7F6230 | SHA256:A54D90FAF43009456A005055A67E1114B92FDE8E2BDDC4DB6D56CB1E1309CF31 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
27
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7080 | DocuWare.Setup.Client.Bootstrapper.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | unknown | — | — | whitelisted |
4168 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5236 | DocuWare.Setup.Client.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicCodSigPCA2011_2011-07-08.crl | unknown | — | — | whitelisted |
5236 | DocuWare.Setup.Client.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1128 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1128 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7080 | DocuWare.Setup.Client.Bootstrapper.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEAczIDTUQQ1smFqVgzK0WF8%3D | unknown | — | — | whitelisted |
7080 | DocuWare.Setup.Client.Bootstrapper.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5968 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7080 | DocuWare.Setup.Client.Bootstrapper.exe | 135.236.236.160:443 | bpnl.docuware.cloud | LUCENT-CIO | US | unknown |
7080 | DocuWare.Setup.Client.Bootstrapper.exe | 13.107.246.45:443 | dwcloudstatic202310.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7080 | DocuWare.Setup.Client.Bootstrapper.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
4168 | svchost.exe | 20.190.159.71:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4168 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
bpnl.docuware.cloud |
| unknown |
dwcloudstatic202310.azureedge.net |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
DocuWare.Setup.Client.exe | Creating new DocuWare.Setup.Client.exe Pipe Server stream...
|
DocuWare.Setup.Client.exe | DocuWare.Setup.Client.exe Pipe Server is waiting for Pipe Client to connect...
|