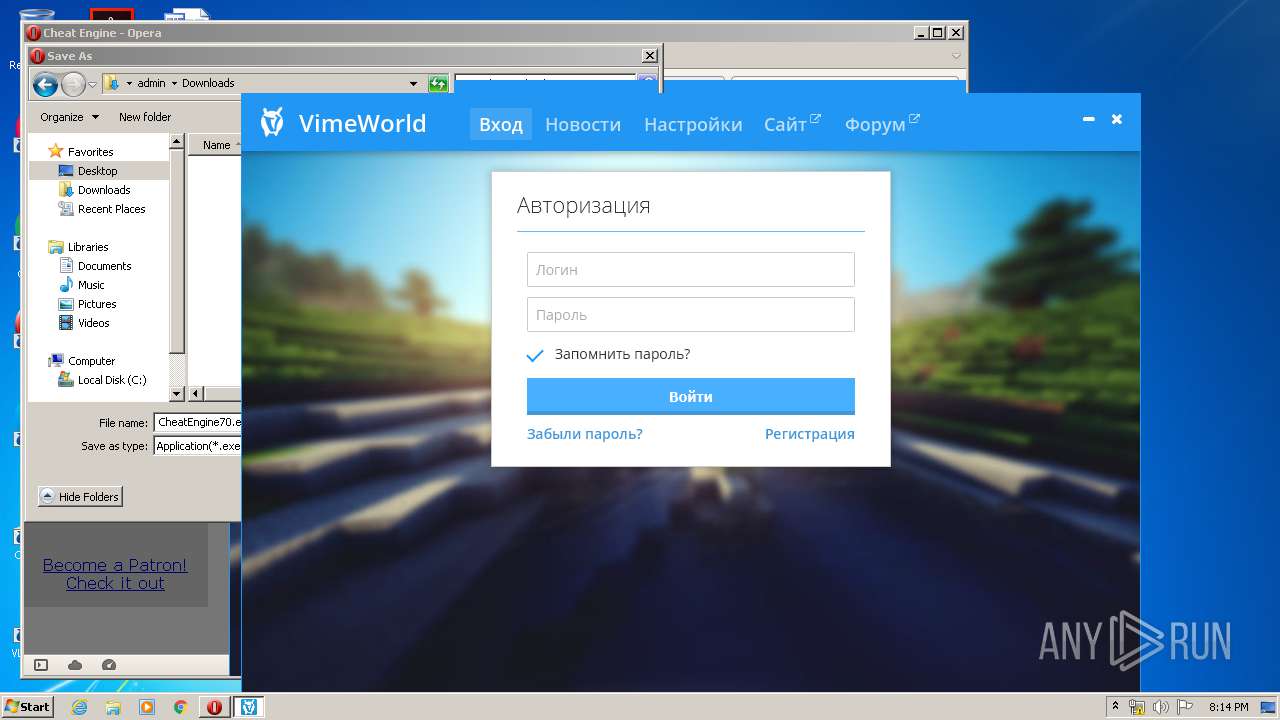
| File name: | VimeWorld.exe |
| Full analysis: | https://app.any.run/tasks/e1336027-7042-4303-85dc-ccf7bb642a5d |
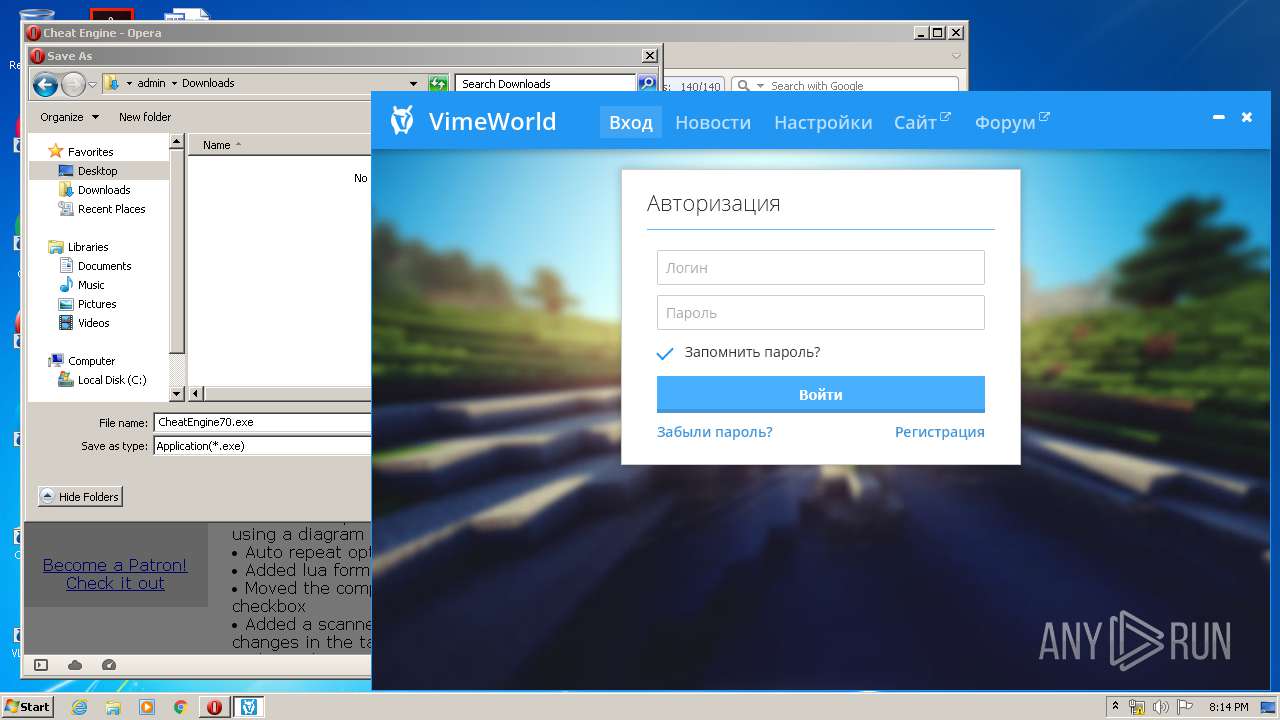
| Verdict: | Malicious activity |
| Analysis date: | February 16, 2020, 20:13:36 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows |
| MD5: | AE01F96AF91A216D7EC695FADBE17761 |
| SHA1: | 00B2C7CAE57DEFEEBC8DD440DFE586007AFCE7B7 |
| SHA256: | 2CB52060F3E856F6C561B16FEF538E5A8E2B3BAF7098B9884B31C9DDDF335BC0 |
| SSDEEP: | 3072:bqGFxfxTJHBOAZSYGxkczkaoQlFS0q9jheHTEekhfdnqCd:blFlsNxkqkaoS0HjheHTEekrqK |
MALICIOUS
Application was dropped or rewritten from another process
- VimeWorld.exe (PID: 968)
- VimeWorld.exe (PID: 4048)
- VimeWorld.exe (PID: 3620)
Loads dropped or rewritten executable
- VimeWorld.exe (PID: 968)
SUSPICIOUS
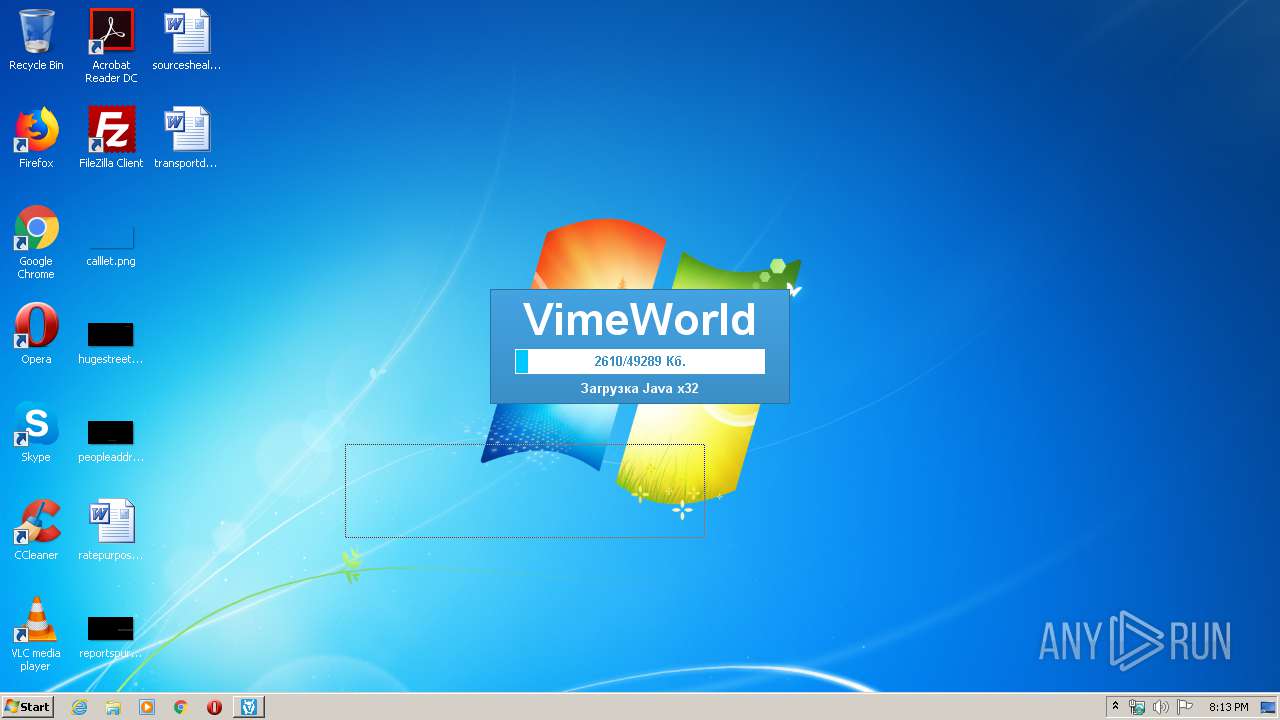
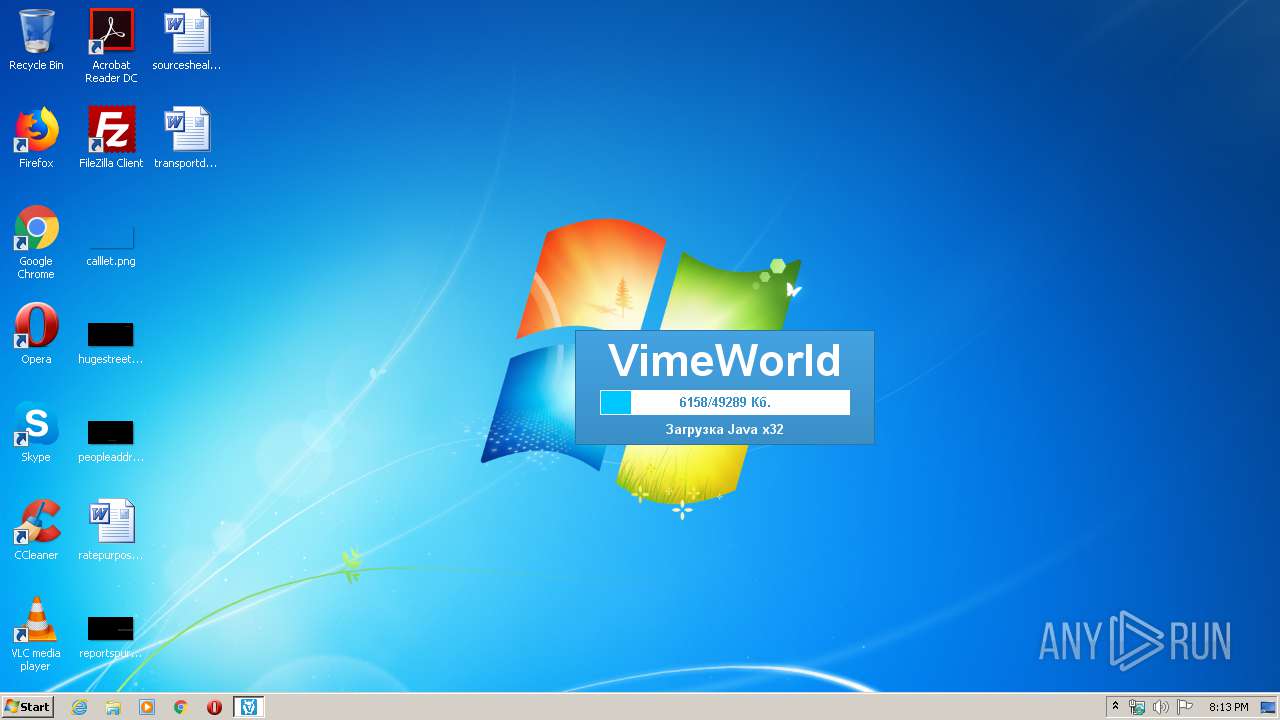
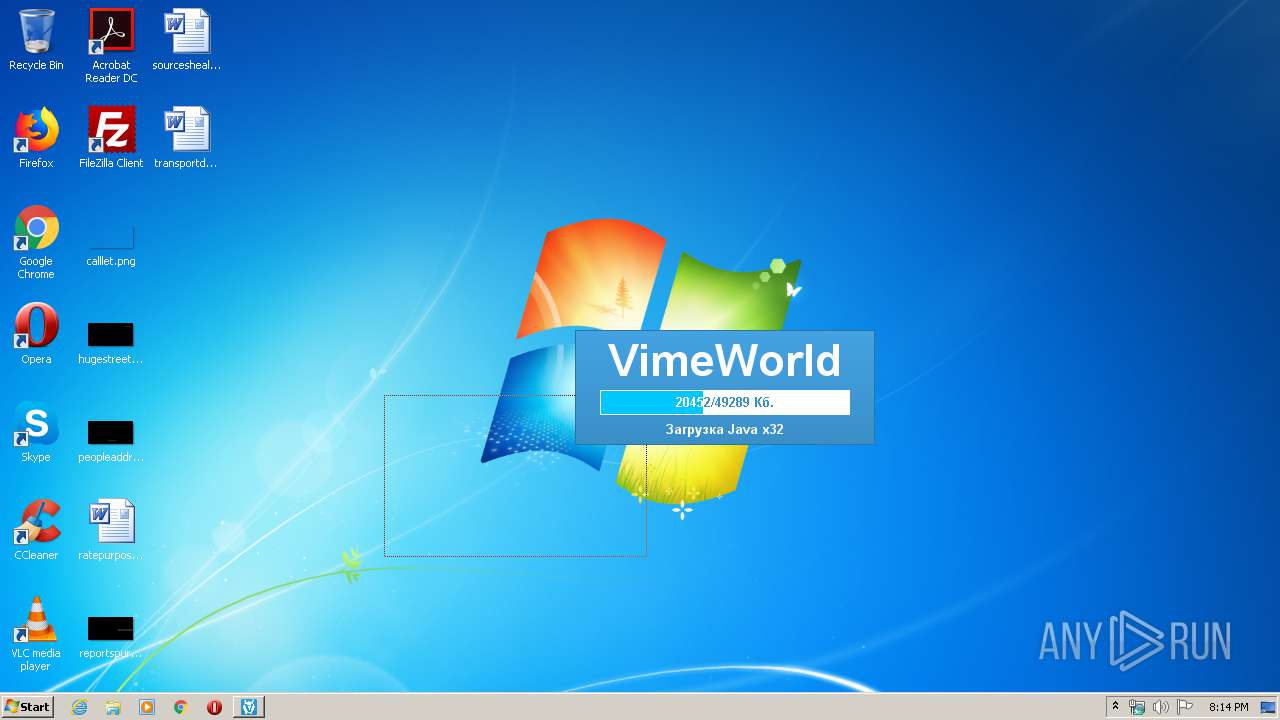
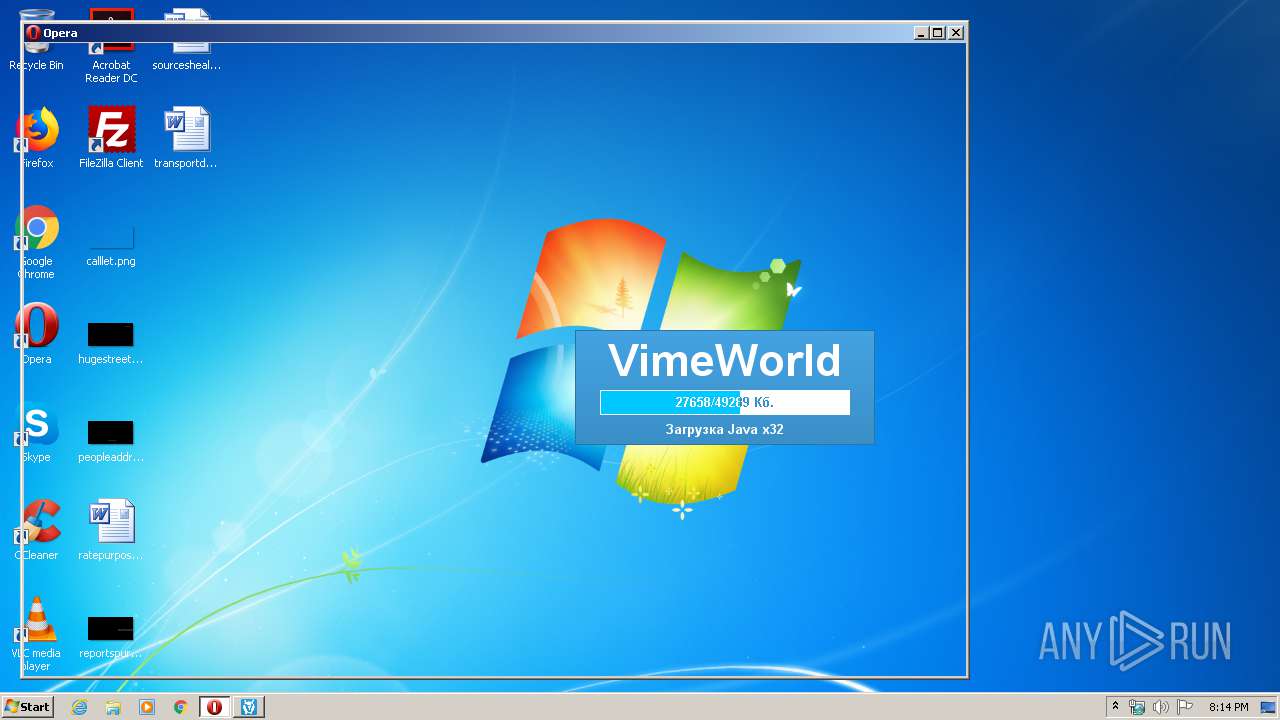
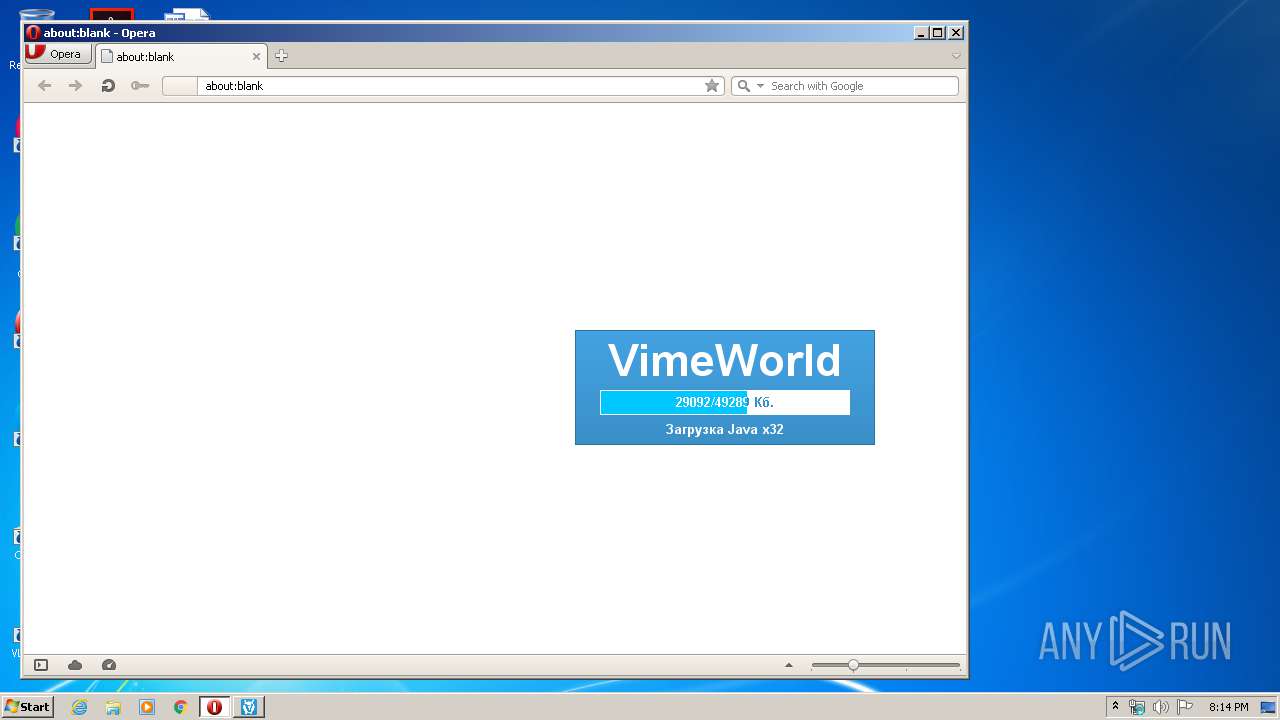
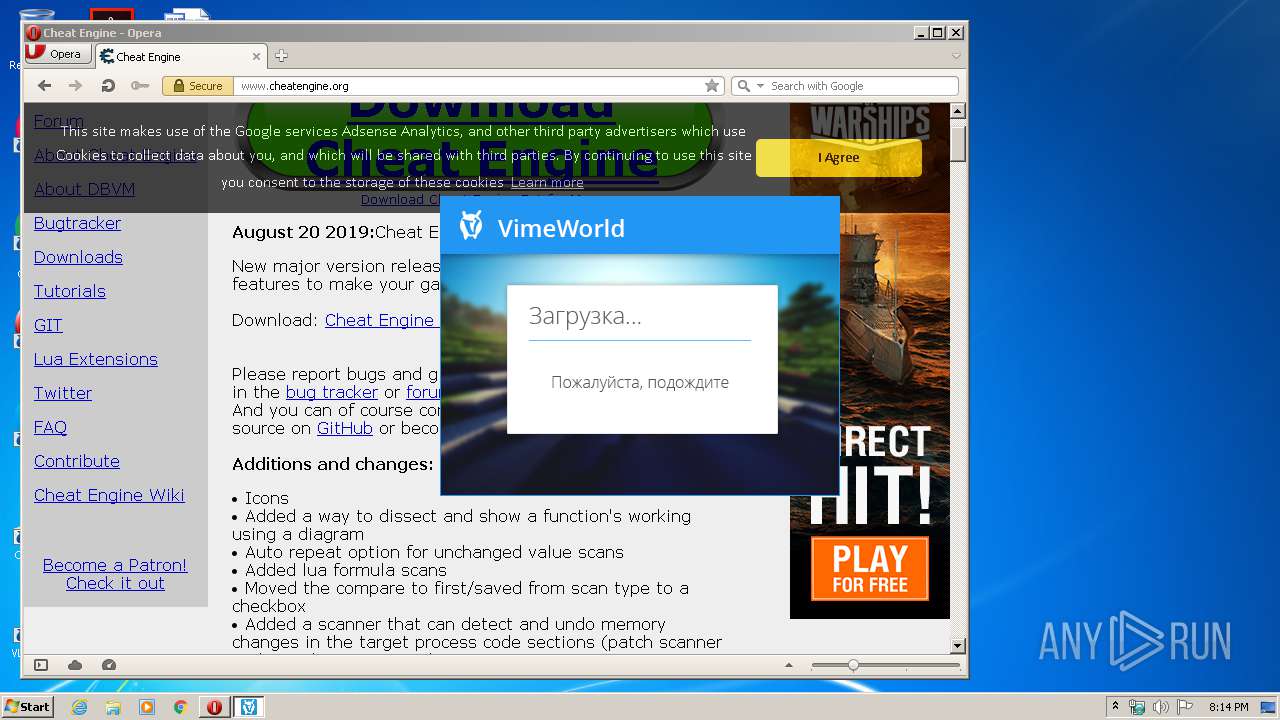
Executes JAVA applets
- VimeWorld.exe (PID: 3976)
Starts CMD.EXE for commands execution
- javaw.exe (PID: 2716)
Executable content was dropped or overwritten
- javaw.exe (PID: 2716)
- opera.exe (PID: 2436)
Creates files in the user directory
- VimeWorld.exe (PID: 968)
- javaw.exe (PID: 2716)
INFO
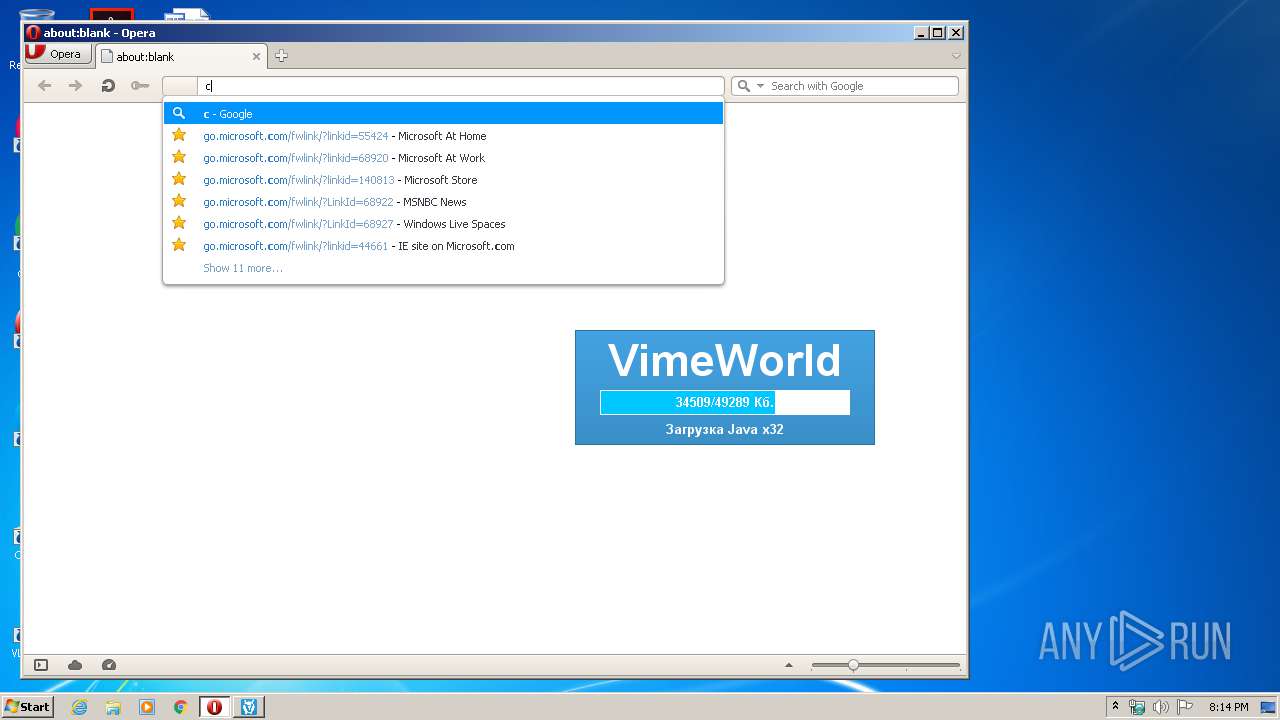
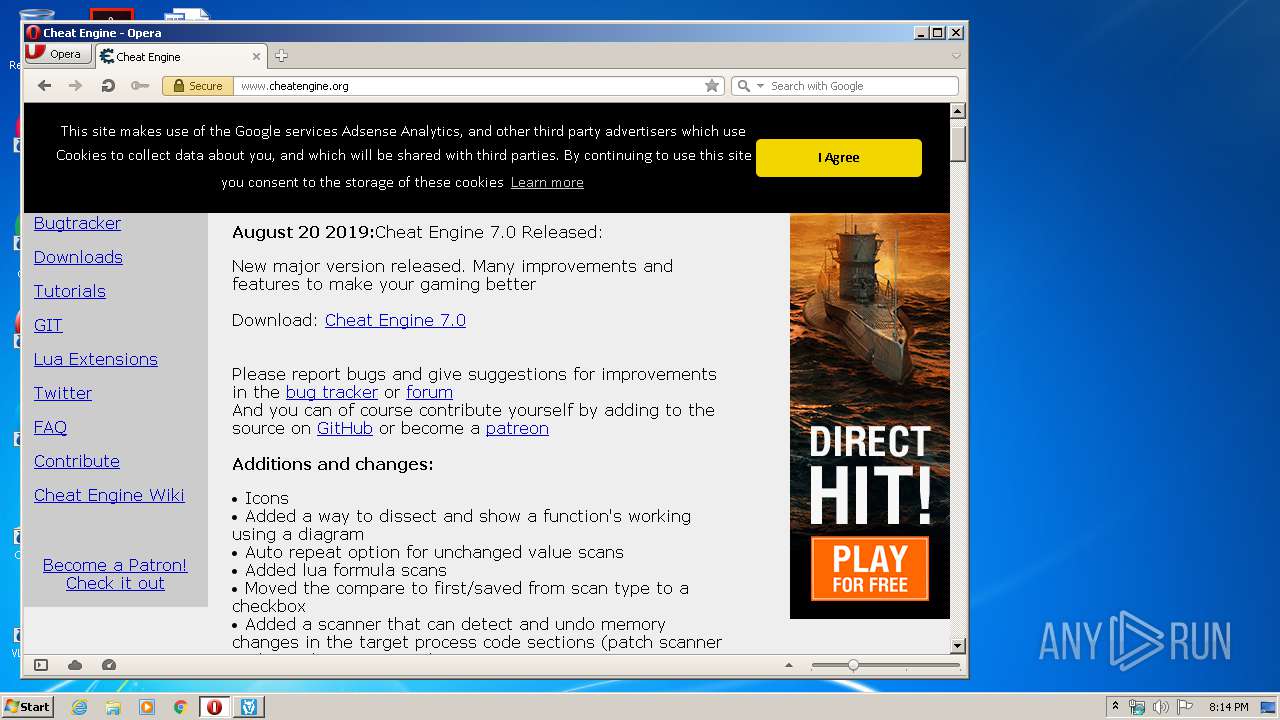
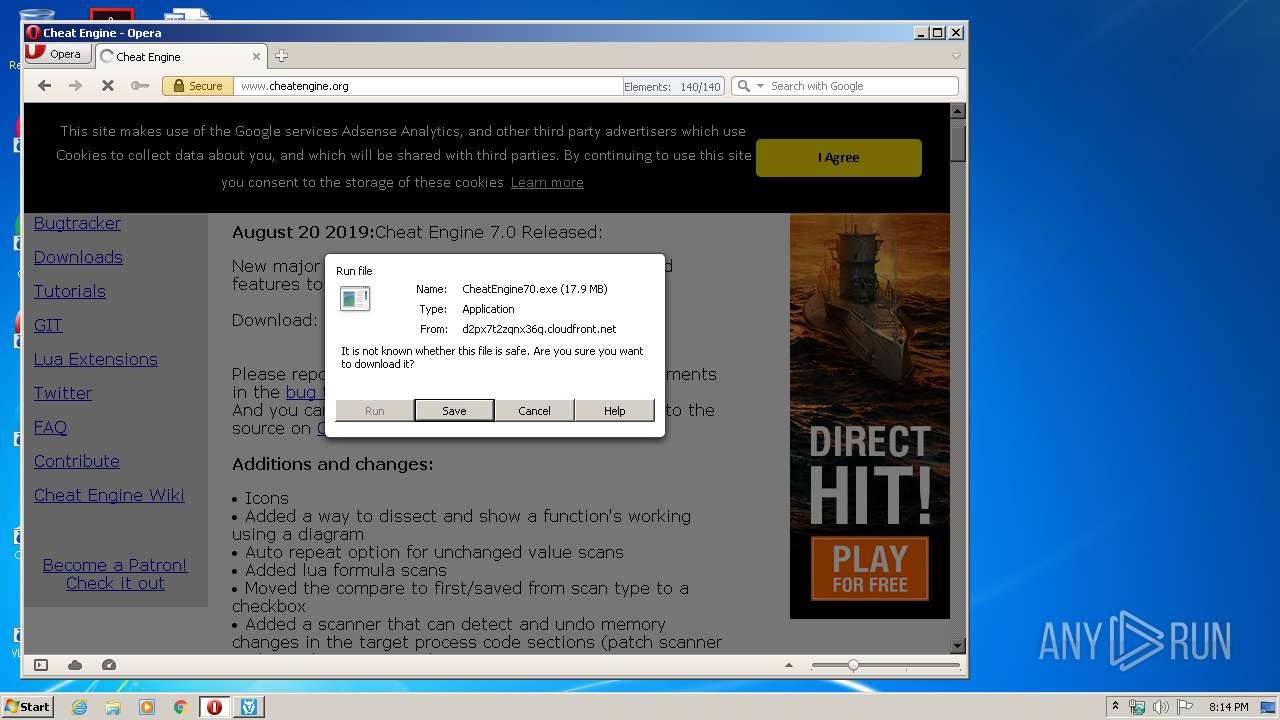
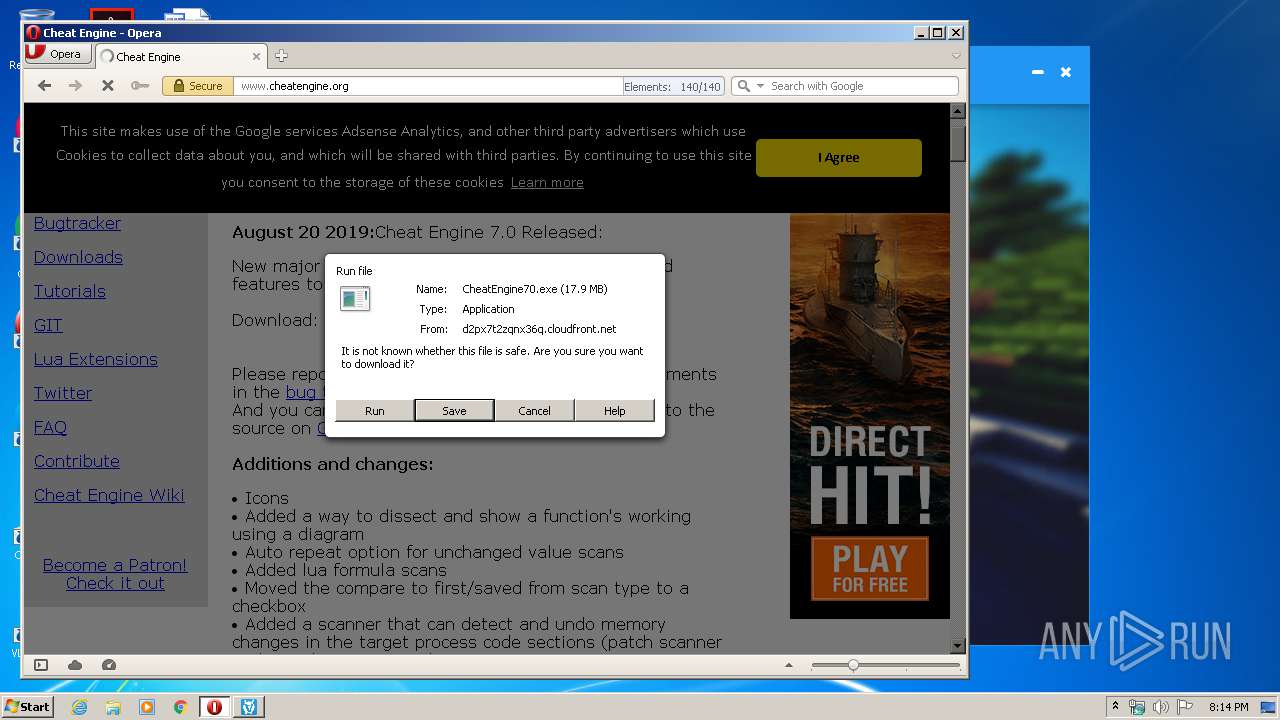
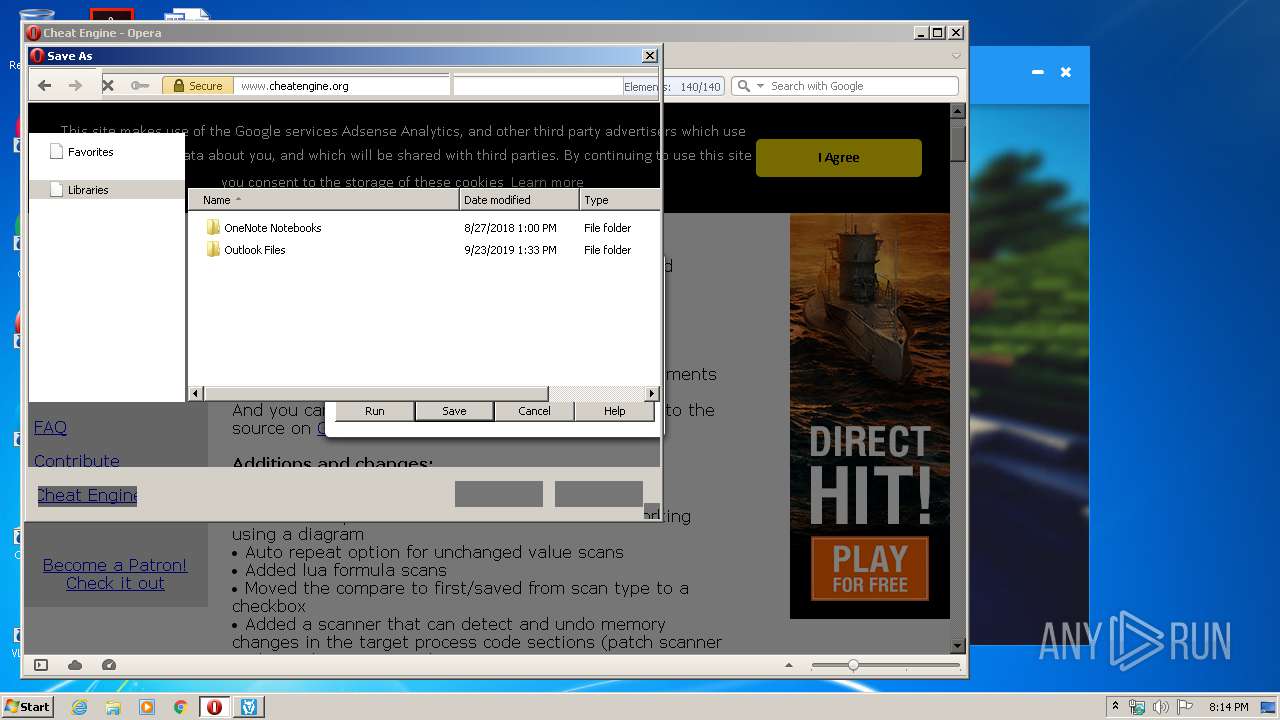
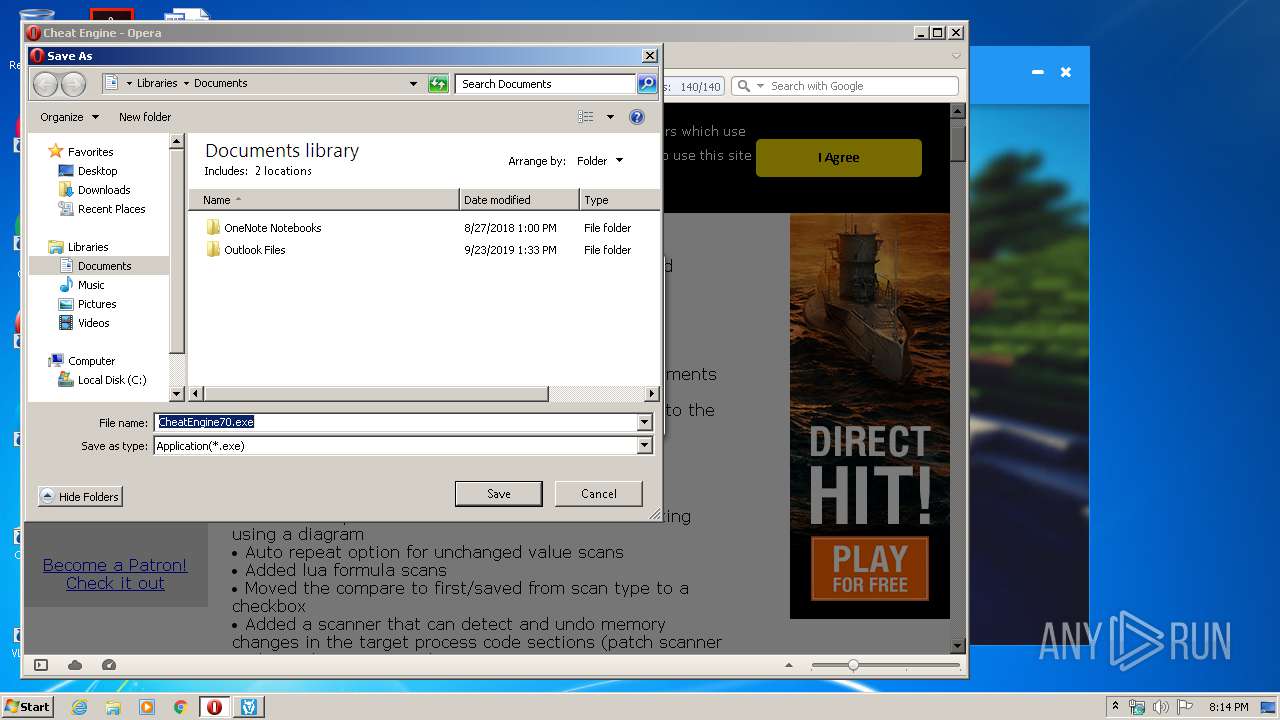
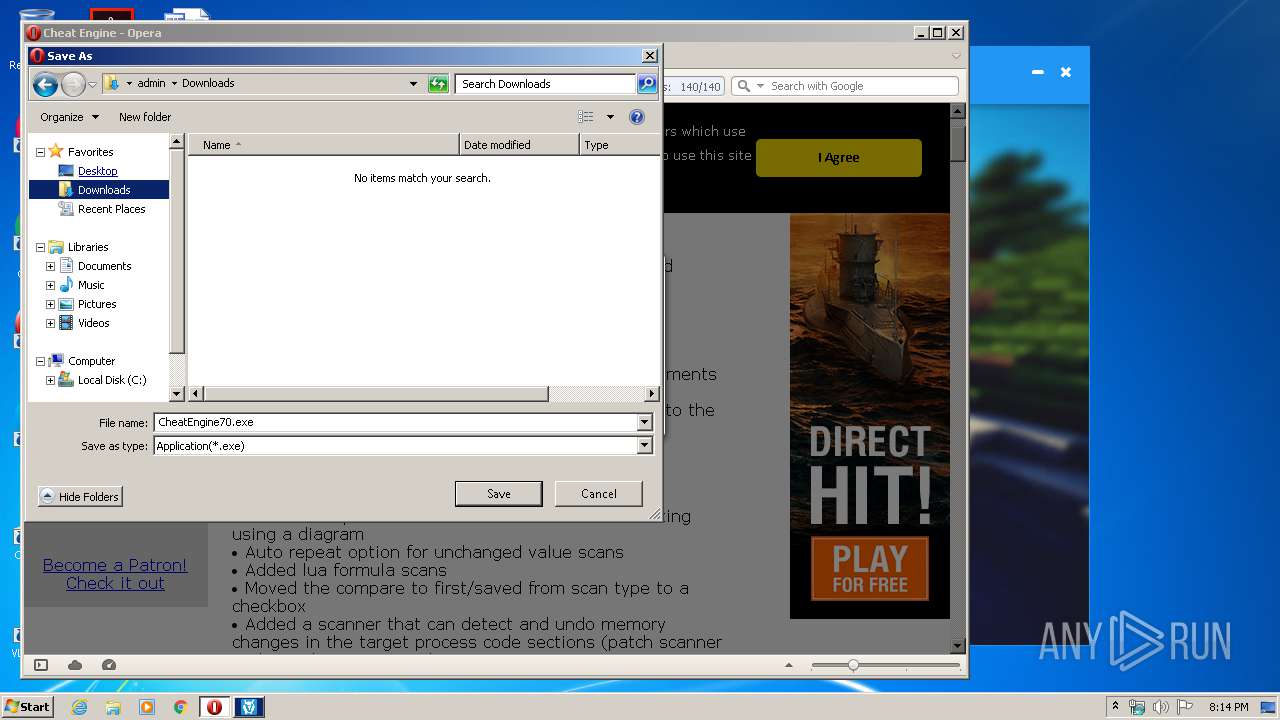
Manual execution by user
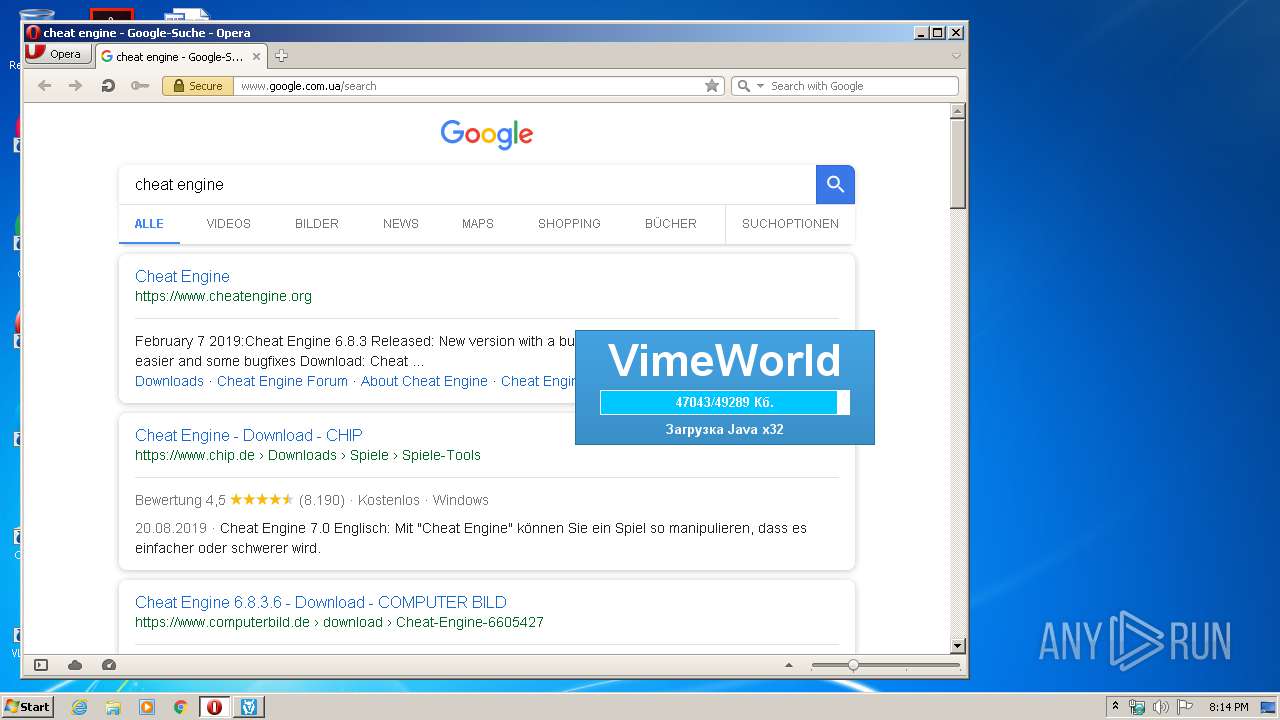
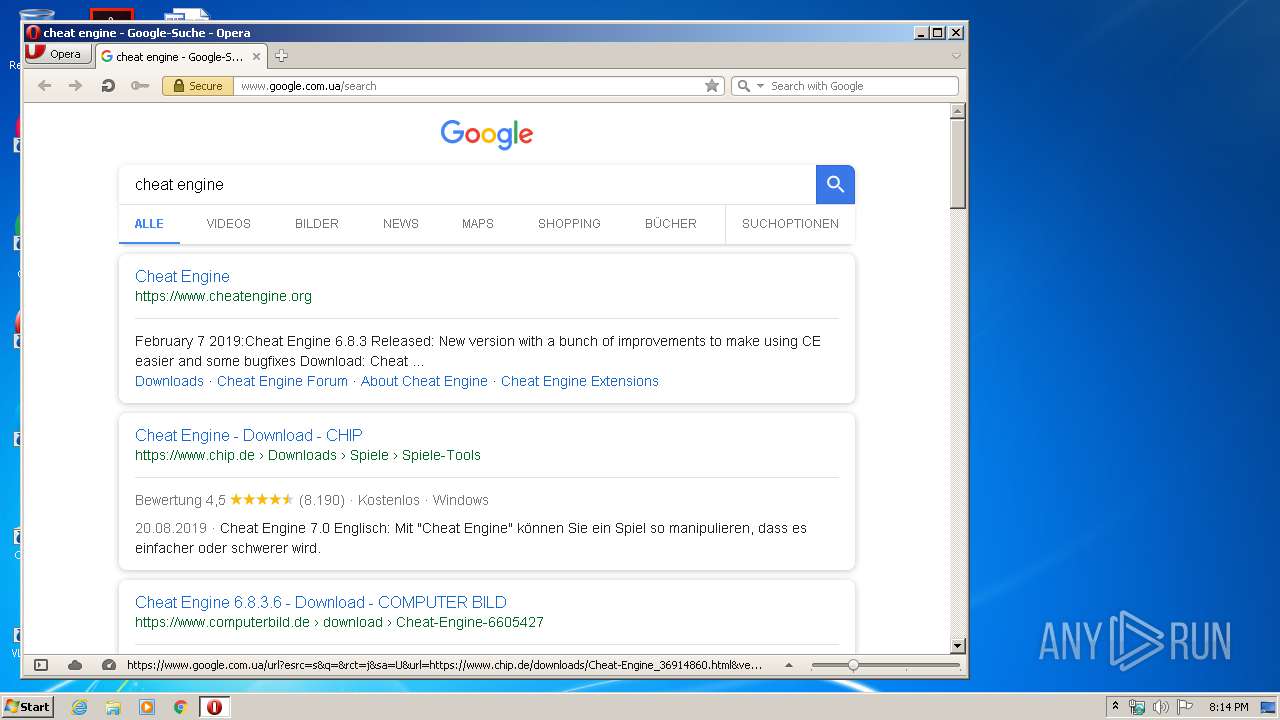
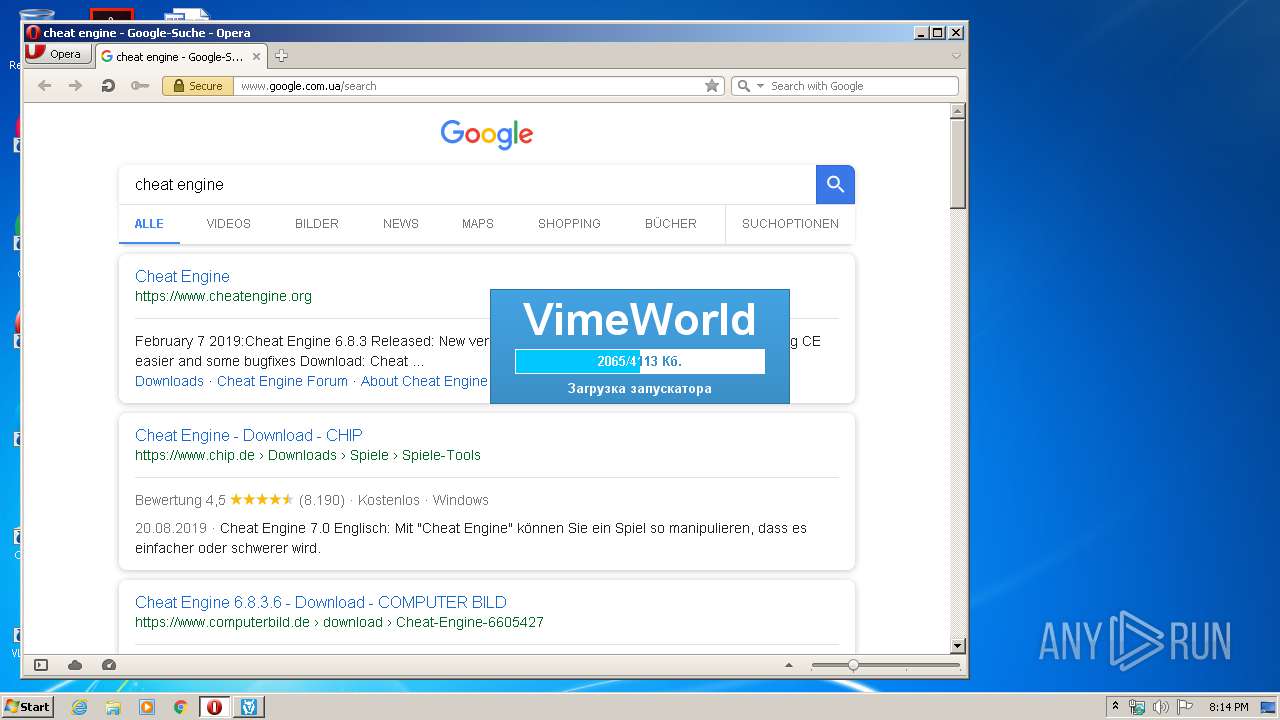
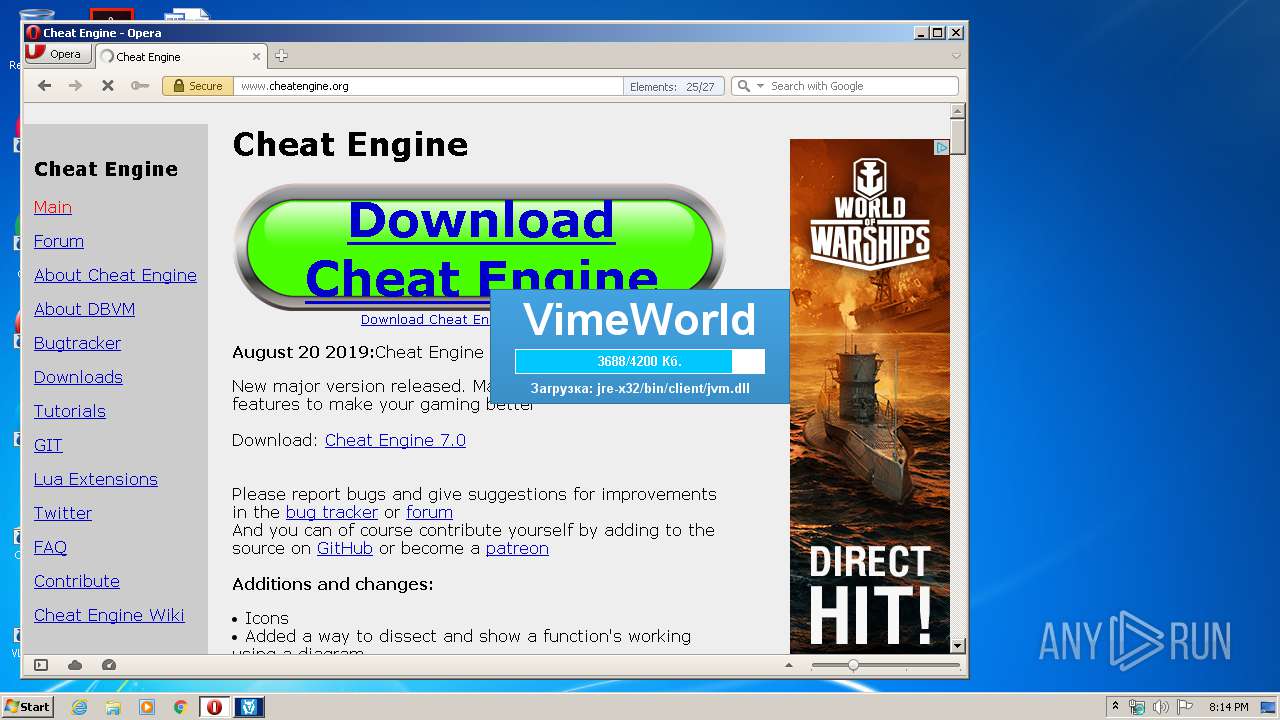
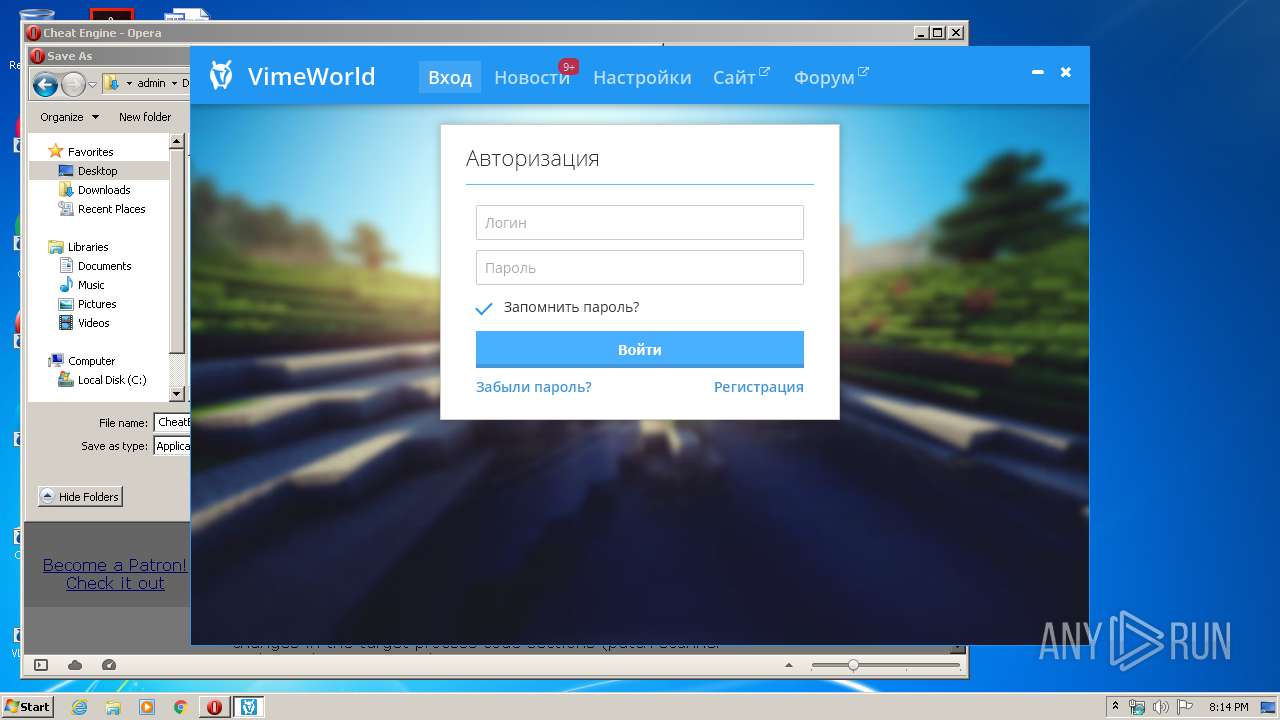
- opera.exe (PID: 2436)
Creates files in the user directory
- opera.exe (PID: 2436)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (41) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.6) |
| .exe | | | Win32 Executable (generic) (5.9) |
| .exe | | | Win16/32 Executable Delphi generic (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:01:10 23:11:02+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.22 |
| CodeSize: | 19456 |
| InitializedDataSize: | 378368 |
| UninitializedDataSize: | 36864 |
| EntryPoint: | 0x1290 |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.3.0.0 |
| ProductVersionNumber: | 2.3.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Windows NT |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Russian |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | VimeWorld.ru |
| FileDescription: | VimeWorld.ru PC |
| FileVersion: | 2.3.0.0 |
| InternalName: | VimeWorldPC |
| LegalCopyright: | xtrafrancyz |
| LegalTrademarks: | - |
| OriginalFileName: | VimeWorldPC.exe |
| ProductName: | VimeWorld.ru PC |
| ProductVersion: | 2.3.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 10-Jan-2019 22:11:02 |
| Detected languages: |
|
| CompanyName: | VimeWorld.ru |
| FileDescription: | VimeWorld.ru PC |
| FileVersion: | 2.3.0.0 |
| InternalName: | VimeWorldPC |
| LegalCopyright: | xtrafrancyz |
| LegalTrademarks: | - |
| OriginalFilename: | VimeWorldPC.exe |
| ProductName: | VimeWorld.ru PC |
| ProductVersion: | 2.3.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 10-Jan-2019 22:11:02 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00004A70 | 0x00004C00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.9841 |
.data | 0x00006000 | 0x00000040 | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.163808 |
.rdata | 0x00007000 | 0x00000610 | 0x00000800 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.7319 |
.bss | 0x00008000 | 0x00008E30 | 0x00000000 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00011000 | 0x00000AA8 | 0x00000C00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.65099 |
.rsrc | 0x00012000 | 0x0005AE7C | 0x0005B000 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.07131 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.30949 | 748 | UNKNOWN | Process Default Language | RT_VERSION |
2 | 2.25163 | 6 | UNKNOWN | Process Default Language | RT_RCDATA |
3 | 4.78152 | 9640 | UNKNOWN | Process Default Language | RT_ICON |
4 | 4.32193 | 16936 | UNKNOWN | Process Default Language | RT_ICON |
5 | 4.06642 | 67624 | UNKNOWN | Process Default Language | RT_ICON |
6 | 3.94051 | 270376 | UNKNOWN | Process Default Language | RT_ICON |
10 | 3.54659 | 13 | UNKNOWN | Process Default Language | RT_RCDATA |
12 | 3.75 | 16 | UNKNOWN | Process Default Language | RT_RCDATA |
17 | 2.32193 | 5 | UNKNOWN | Process Default Language | RT_RCDATA |
18 | 1 | 2 | UNKNOWN | Process Default Language | RT_RCDATA |
Imports
ADVAPI32.DLL |
KERNEL32.dll |
SHELL32.DLL |
USER32.dll |
msvcrt.dll |
Total processes
44
Monitored processes
7
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 968 | "C:\Users\admin\AppData\Roaming\.vimeworld\VimeWorld.exe" -home "C:\Users\admin\AppData\Roaming\.vimeworld\" -jre "C:\Users\admin\AppData\Roaming\.vimeworld\jre-x32" -jvmargs -Xmx768M -XX:+UnlockExperimentalVMOptions -XX:+UseG1GC -jar "launcher.jar" -updater QzpcVXNlcnNcYWRtaW5cQXBwRGF0YVxMb2NhbFxUZW1wXFZpbWVXb3JsZC5leGU= -appdata QzpcVXNlcnNcYWRtaW5cQXBwRGF0YVxSb2FtaW5n | C:\Users\admin\AppData\Roaming\.vimeworld\VimeWorld.exe | cmd.exe | ||||||||||||
User: admin Company: VimeWorld Integrity Level: HIGH Description: VimeWorld Exit code: 0 Version: 2.0.0.0 Modules
| |||||||||||||||
| 2436 | "C:\Program Files\Opera\opera.exe" | C:\Program Files\Opera\opera.exe | explorer.exe | ||||||||||||
User: admin Company: Opera Software Integrity Level: MEDIUM Description: Opera Internet Browser Exit code: 0 Version: 1748 Modules
| |||||||||||||||
| 2716 | "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -Dvw-l4j="true" -jar "C:\Users\admin\AppData\Local\Temp\VimeWorld.exe" | C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe | VimeWorld.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
| 3072 | cmd /d /c start "" /D "C:\Users\admin\AppData\Roaming\.vimeworld" "C:\Users\admin\AppData\Roaming\.vimeworld\VimeWorld.exe" -home "C:\Users\admin\AppData\Roaming\.vimeworld\" -jre "C:\Users\admin\AppData\Roaming\.vimeworld\jre-x32" -jvmargs -Xmx768M -XX:+UnlockExperimentalVMOptions -XX:+UseG1GC -jar "launcher.jar" -updater QzpcVXNlcnNcYWRtaW5cQXBwRGF0YVxMb2NhbFxUZW1wXFZpbWVXb3JsZC5leGU= -appdata QzpcVXNlcnNcYWRtaW5cQXBwRGF0YVxSb2FtaW5n | C:\Windows\system32\cmd.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3620 | "C:\Users\admin\AppData\Roaming\.vimeworld\VimeWorld.exe" -home "C:\Users\admin\AppData\Roaming\.vimeworld\" -jre "C:\Users\admin\AppData\Roaming\.vimeworld\jre-x32" -jvmargs -Xmx768M -XX:+UnlockExperimentalVMOptions -XX:+UseG1GC -jar "launcher.jar" -updater QzpcVXNlcnNcYWRtaW5cQXBwRGF0YVxMb2NhbFxUZW1wXFZpbWVXb3JsZC5leGU= -appdata QzpcVXNlcnNcYWRtaW5cQXBwRGF0YVxSb2FtaW5n | C:\Users\admin\AppData\Roaming\.vimeworld\VimeWorld.exe | — | cmd.exe | |||||||||||
User: admin Company: VimeWorld Integrity Level: MEDIUM Description: VimeWorld Exit code: 3221226540 Version: 2.0.0.0 Modules
| |||||||||||||||
| 3976 | "C:\Users\admin\AppData\Local\Temp\VimeWorld.exe" | C:\Users\admin\AppData\Local\Temp\VimeWorld.exe | — | explorer.exe | |||||||||||
User: admin Company: VimeWorld.ru Integrity Level: MEDIUM Description: VimeWorld.ru PC Exit code: 0 Version: 2.3.0.0 Modules
| |||||||||||||||
| 4048 | "C:\Users\admin\AppData\Roaming\.vimeworld\VimeWorld.exe" -home "C:\Users\admin\AppData\Roaming\.vimeworld\" -jre "C:\Users\admin\AppData\Roaming\.vimeworld\jre-x32" -jvmargs -Xmx768M -XX:+UnlockExperimentalVMOptions -XX:+UseG1GC -jar "launcher.jar" -updater QzpcVXNlcnNcYWRtaW5cQXBwRGF0YVxMb2NhbFxUZW1wXFZpbWVXb3JsZC5leGU= -appdata QzpcVXNlcnNcYWRtaW5cQXBwRGF0YVxSb2FtaW5n | C:\Users\admin\AppData\Roaming\.vimeworld\VimeWorld.exe | — | cmd.exe | |||||||||||
User: admin Company: VimeWorld Integrity Level: MEDIUM Description: VimeWorld Exit code: 3221226540 Version: 2.0.0.0 Modules
| |||||||||||||||
Total events
1 043
Read events
941
Write events
102
Delete events
0
Modification events
| (PID) Process: | (2716) javaw.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: javaw.exe | |||
| (PID) Process: | (2436) opera.exe | Key: | HKEY_CURRENT_USER\Software\Opera Software |
| Operation: | write | Name: | Last CommandLine v2 |
Value: C:\Program Files\Opera\opera.exe | |||
| (PID) Process: | (2436) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3072) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3072) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (968) VimeWorld.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: VimeWorld.exe | |||
| (PID) Process: | (968) VimeWorld.exe | Key: | HKEY_CURRENT_USER\Software\VimeWorld |
| Operation: | write | Name: | osuuid |
Value: b4acf5a0-ad5e-4f04-9215-1a1a1a9857ea | |||
| (PID) Process: | (2436) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 02020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (2436) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 02000000010000000A0000000700000009000000080000000000000006000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (2436) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\2 |
| Operation: | write | Name: | MRUListEx |
Value: 0000000001000000FFFFFFFF | |||
Executable files
77
Suspicious files
75
Text files
209
Unknown types
33
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2716 | javaw.exe | C:\Users\admin\AppData\Local\Temp\imageio687826424444835269.tmp | — | |
MD5:— | SHA256:— | |||
| 2436 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\oprB195.tmp | — | |
MD5:— | SHA256:— | |||
| 2436 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\oprB1D5.tmp | — | |
MD5:— | SHA256:— | |||
| 2436 | opera.exe | C:\Users\admin\AppData\Local\Opera\Opera\cache\sesn\opr00001.tmp | — | |
MD5:— | SHA256:— | |||
| 2436 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\RKS40KBX5I5UK1EKQO5S.temp | — | |
MD5:— | SHA256:— | |||
| 2436 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\sessions\oprD8C6.tmp | — | |
MD5:— | SHA256:— | |||
| 2716 | javaw.exe | C:\Users\admin\AppData\Roaming\.vimeworld\jre-x32\jre.zip | — | |
MD5:— | SHA256:— | |||
| 2436 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\tasks.xml | xml | |
MD5:— | SHA256:— | |||
| 2716 | javaw.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | text | |
MD5:— | SHA256:— | |||
| 2436 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opssl6.dat | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
40
TCP/UDP connections
180
DNS requests
57
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
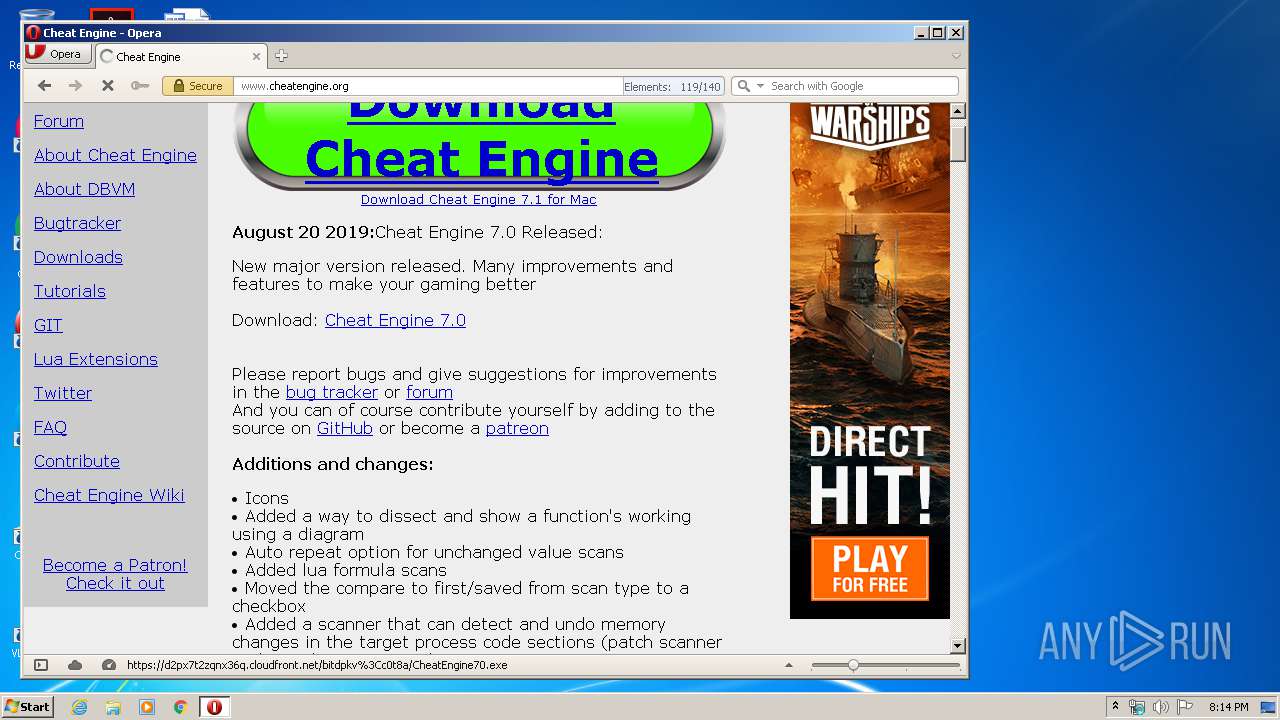
2436 | opera.exe | GET | — | 185.26.182.111:80 | http://sitecheck2.opera.com/?host=www.google.com.ua&hdn=Nxr6KEmdGjdmqcWka8dkkA== | unknown | — | — | whitelisted |
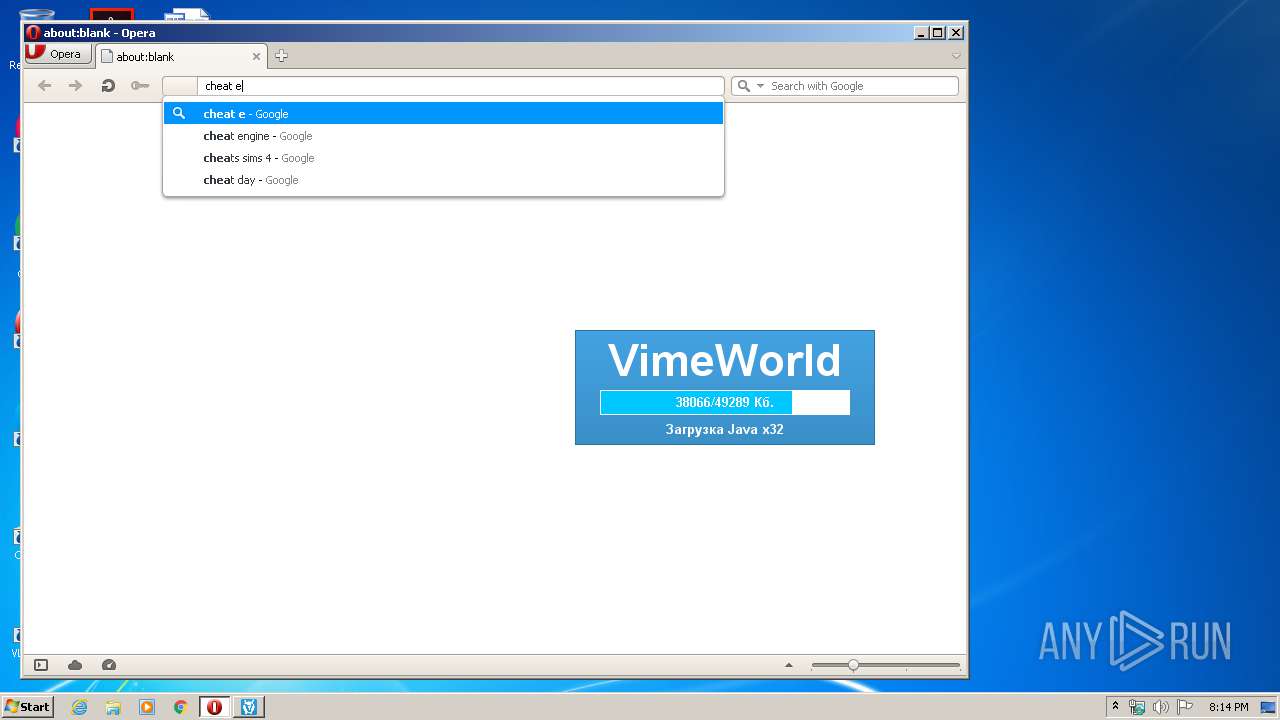
2436 | opera.exe | GET | 200 | 216.58.208.46:80 | http://clients1.google.com/complete/search?q=cheat+en&client=opera-suggest-omnibox&hl=de | US | text | 113 b | whitelisted |
2436 | opera.exe | GET | 200 | 216.58.208.46:80 | http://clients1.google.com/complete/search?q=cheat+engin&client=opera-suggest-omnibox&hl=de | US | text | 112 b | whitelisted |
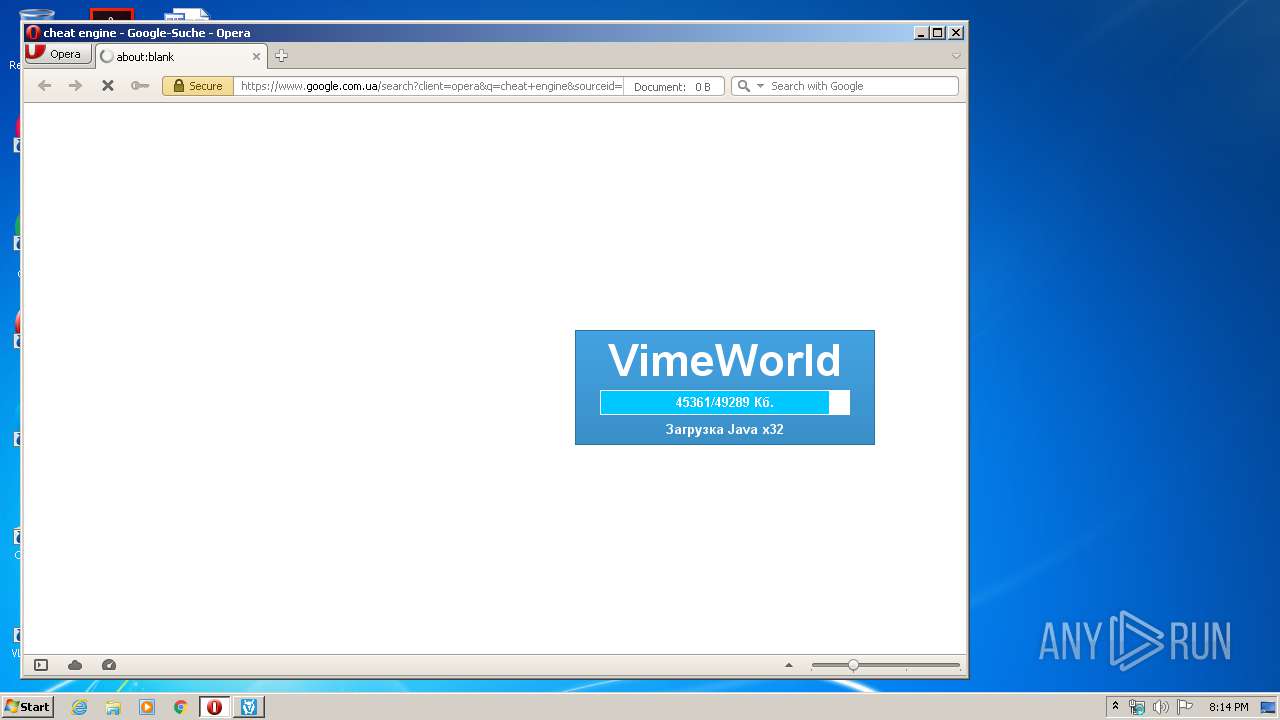
2436 | opera.exe | GET | 302 | 172.217.22.35:80 | http://www.google.com.ua/search?q=cheat+engine&sourceid=opera&ie=utf-8&oe=utf-8&channel=suggest | US | html | 325 b | whitelisted |
2436 | opera.exe | GET | 200 | 216.58.208.46:80 | http://clients1.google.com/complete/search?q=cheat+engi&client=opera-suggest-omnibox&hl=de | US | text | 112 b | whitelisted |
2436 | opera.exe | GET | 200 | 93.184.220.29:80 | http://crl4.digicert.com/DigiCertHighAssuranceEVRootCA.crl | US | der | 564 b | whitelisted |
2436 | opera.exe | GET | 200 | 216.58.208.46:80 | http://clients1.google.com/complete/search?q=cheat+engine&client=opera-suggest-omnibox&hl=de | US | text | 110 b | whitelisted |
2716 | javaw.exe | GET | 200 | 5.39.71.168:80 | http://dl2.vimeworld.ru/files/9ac101fa08d5fd803357c450c590ed33.zip | FR | compressed | 48.1 Mb | unknown |
2436 | opera.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/Omniroot2025.crl | US | der | 5.21 Kb | whitelisted |
2716 | javaw.exe | GET | 200 | 5.39.71.168:80 | http://dl2.vimeworld.ru/files/ed06583c66c253acd25121c4a7ef40ed.deflated | FR | skn | 4.02 Mb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2716 | javaw.exe | 104.26.4.104:443 | cdn.vimeworld.ru | Cloudflare Inc | US | suspicious |
2716 | javaw.exe | 5.39.71.168:80 | dl2.vimeworld.ru | OVH SAS | FR | unknown |
2436 | opera.exe | 93.184.220.29:80 | crl4.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2436 | opera.exe | 185.26.182.93:443 | certs.opera.com | Opera Software AS | — | whitelisted |
2436 | opera.exe | 216.58.208.46:80 | clients1.google.com | Google Inc. | US | whitelisted |
2436 | opera.exe | 172.217.22.35:80 | www.google.com.ua | Google Inc. | US | whitelisted |
2436 | opera.exe | 185.26.182.111:80 | sitecheck2.opera.com | Opera Software AS | — | whitelisted |
2436 | opera.exe | 172.217.22.35:443 | www.google.com.ua | Google Inc. | US | whitelisted |
2436 | opera.exe | 172.217.16.163:80 | crl.pki.goog | Google Inc. | US | whitelisted |
2436 | opera.exe | 104.20.174.30:443 | www.cheatengine.org | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cdn.vimeworld.ru |
| suspicious |
dl2.vimeworld.ru |
| unknown |
certs.opera.com |
| whitelisted |
crl4.digicert.com |
| whitelisted |
clients1.google.com |
| whitelisted |
www.google.com.ua |
| whitelisted |
sitecheck2.opera.com |
| whitelisted |
crl.pki.goog |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
id.google.com.ua |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2436 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |