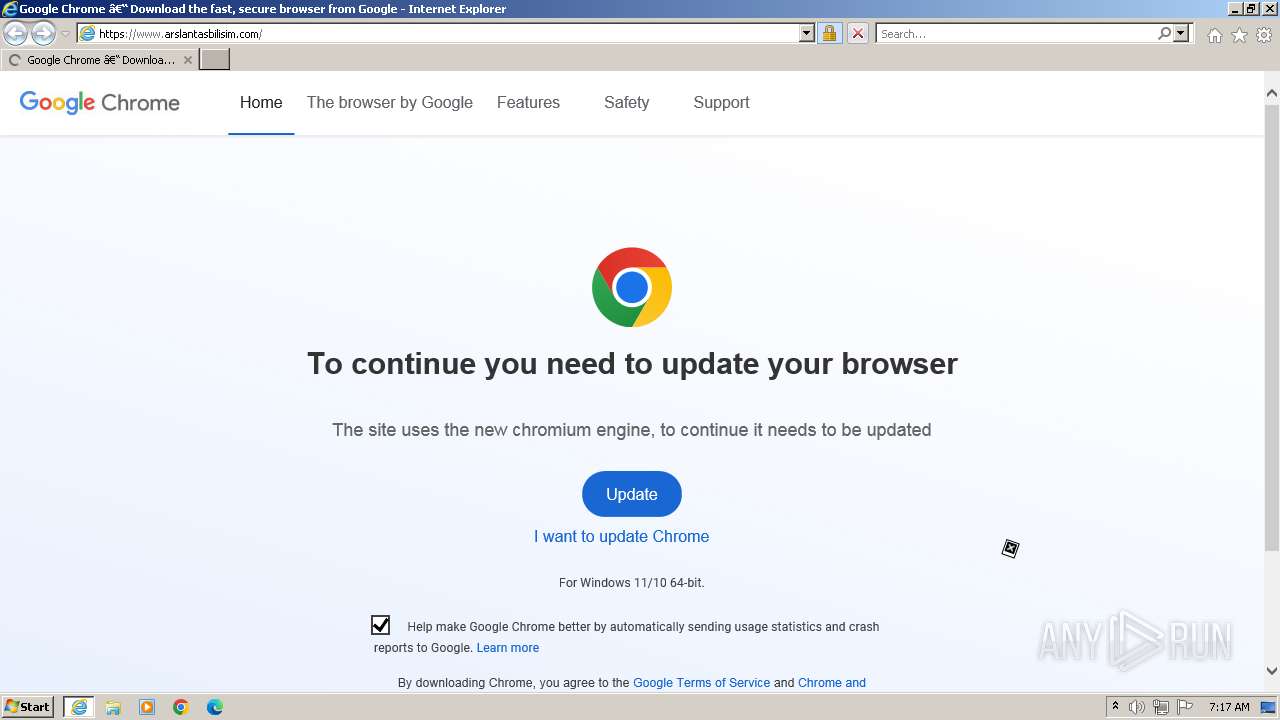
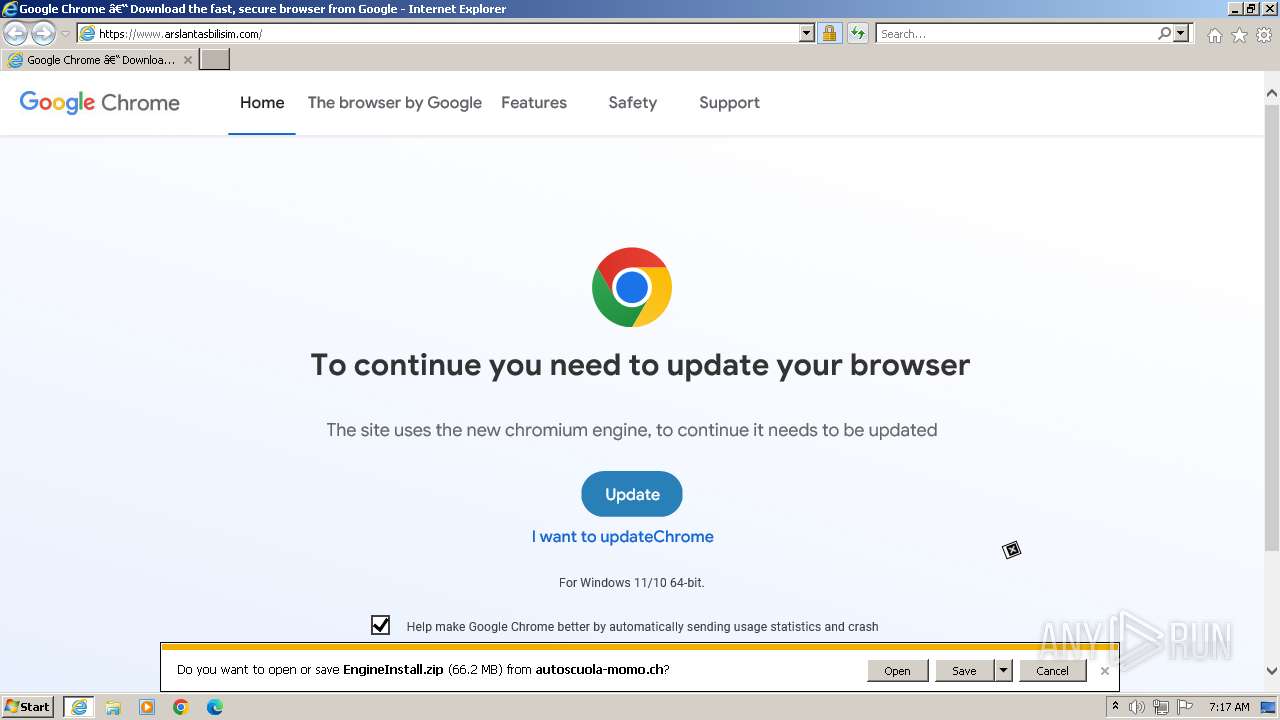
| URL: | https://www.arslantasbilisim.com |
| Full analysis: | https://app.any.run/tasks/bd122fbf-04e1-4ba5-980a-87db2091739b |
| Verdict: | Malicious activity |
| Analysis date: | October 27, 2023, 06:16:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| SHA1: | 5F3C1C2D0004CA80B10EBA549D0443D54B2C8D24 |
| SHA256: | 2CA4EB5FA0222A6AD27B9A5281AA32DC18039AD4BEB6A8F85DC7F8677941EC67 |
| SSDEEP: | 3:N8DSLQxYI:2OLM |
MALICIOUS
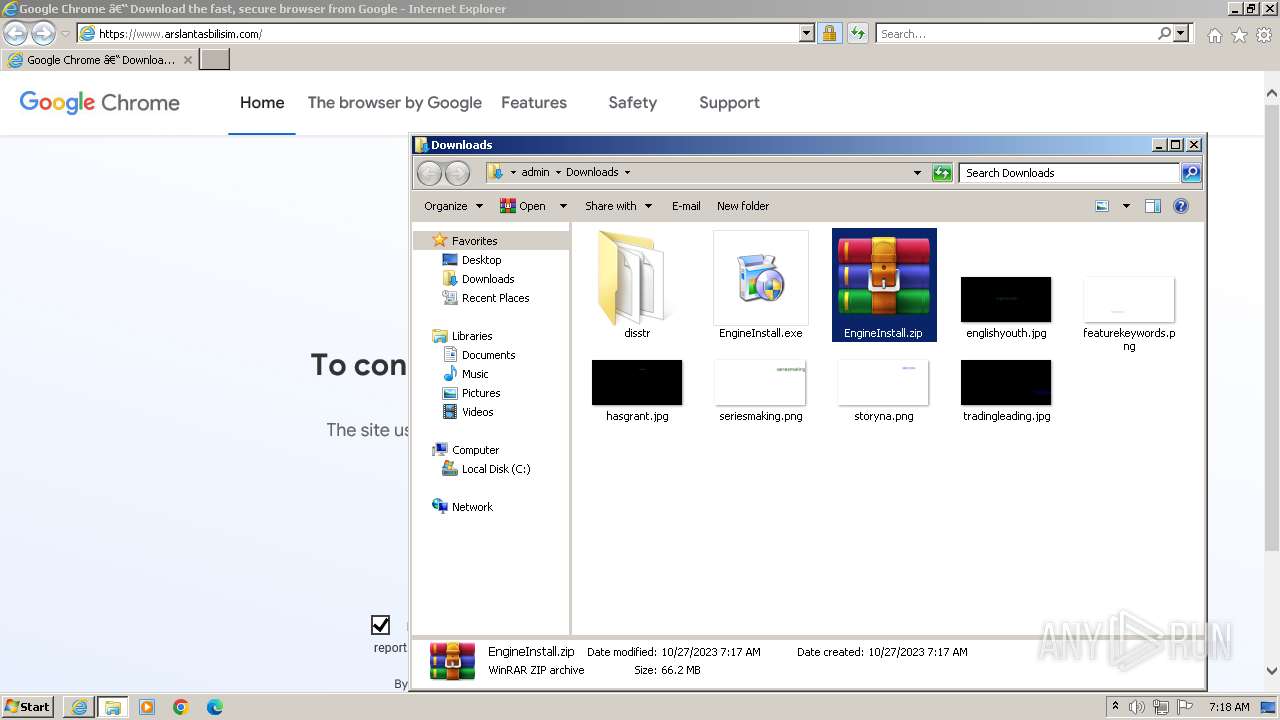
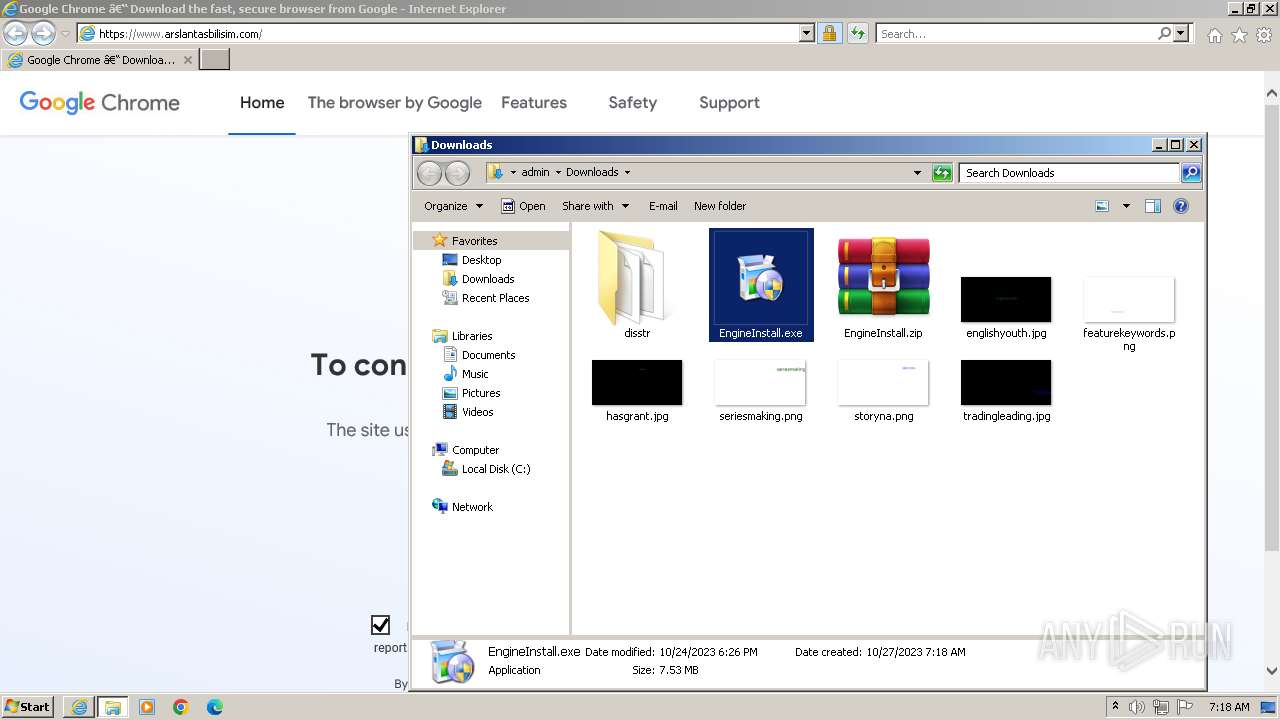
Application was dropped or rewritten from another process
- EngineInstall.exe (PID: 3396)
- javaw.exe (PID: 2484)
Loads dropped or rewritten executable
- EngineInstall.exe (PID: 3396)
- javaw.exe (PID: 2484)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 3120)
Adds path to the Windows Defender exclusion list
- cmd.exe (PID: 3120)
Bypass execution policy to execute commands
- powershell.exe (PID: 3808)
SUSPICIOUS
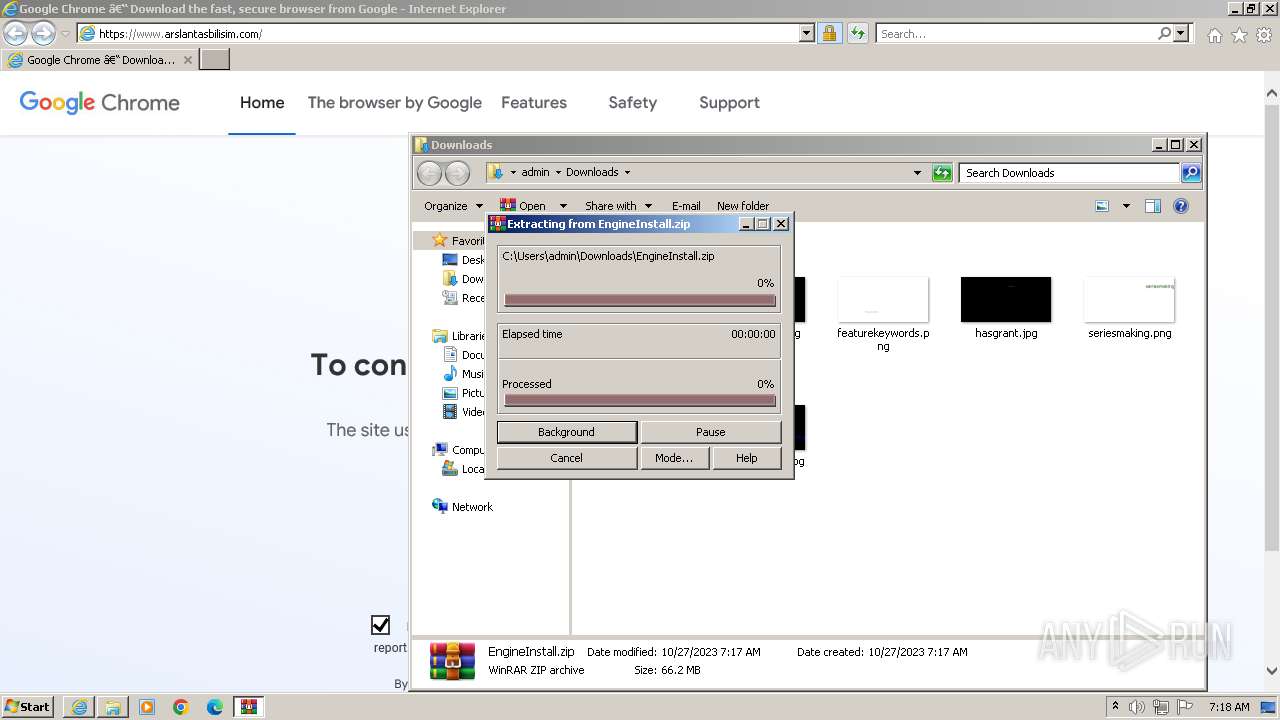
Process drops legitimate windows executable
- WinRAR.exe (PID: 4036)
Executing commands from a ".bat" file
- javaw.exe (PID: 2484)
Starts CMD.EXE for commands execution
- javaw.exe (PID: 2484)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 3120)
The process hide an interactive prompt from the user
- cmd.exe (PID: 3120)
Powershell version downgrade attack
- powershell.exe (PID: 3808)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 3120)
INFO
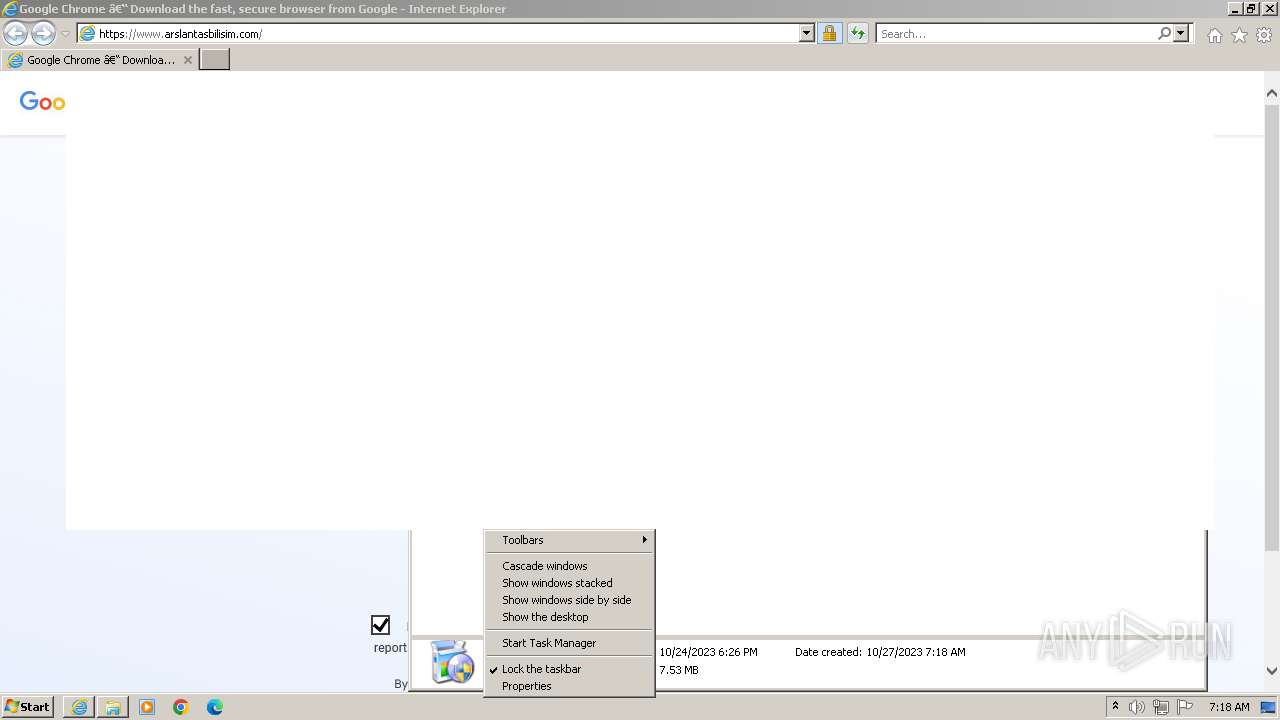
Application launched itself
- iexplore.exe (PID: 1824)
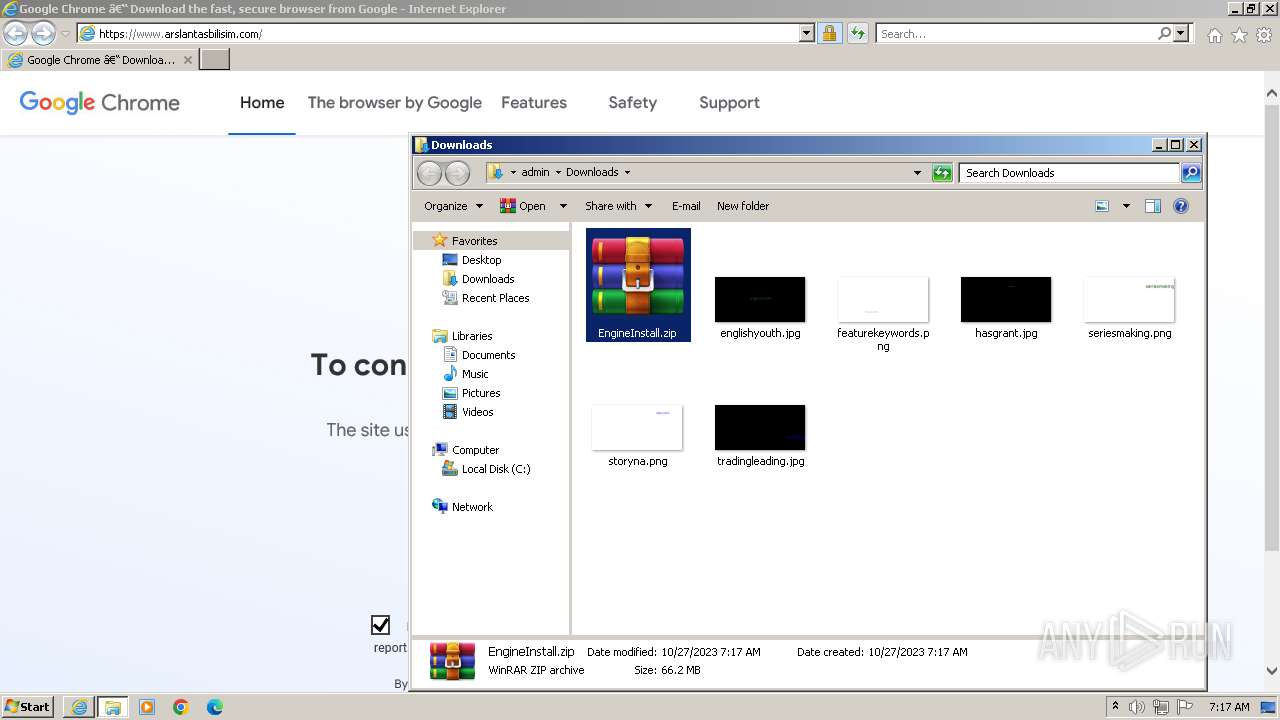
The process uses the downloaded file
- iexplore.exe (PID: 1824)
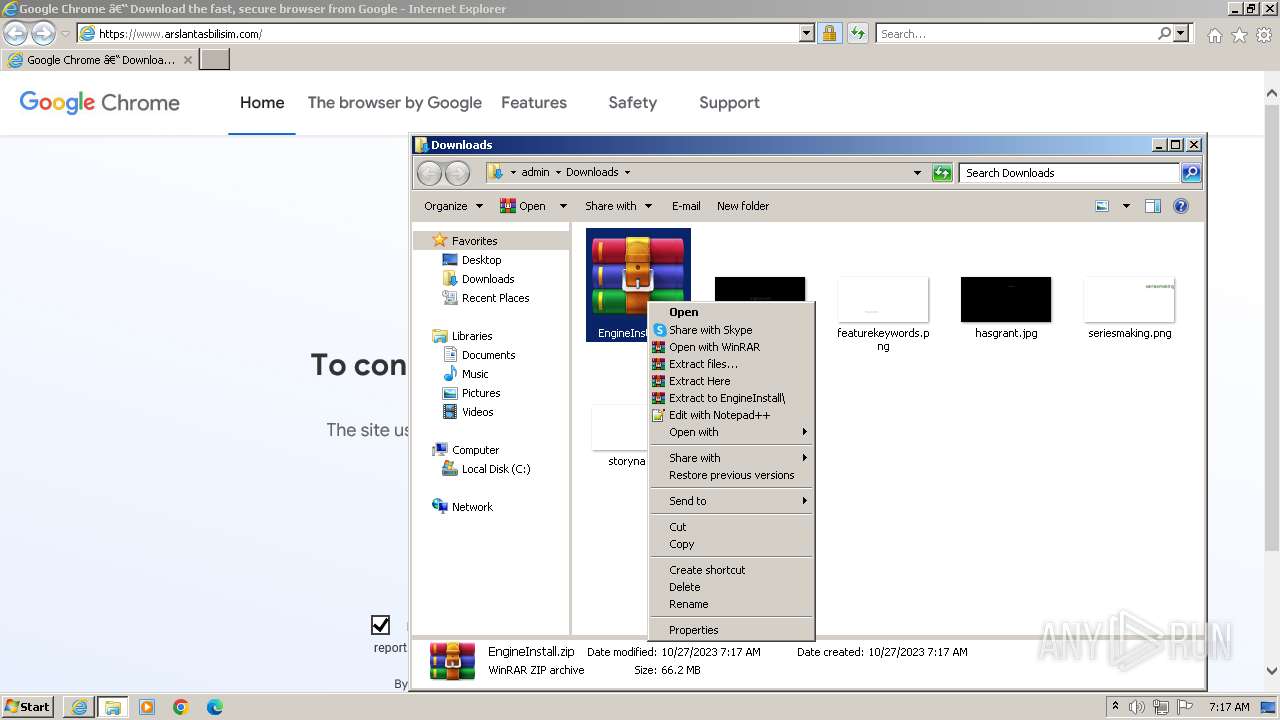
- WinRAR.exe (PID: 4036)
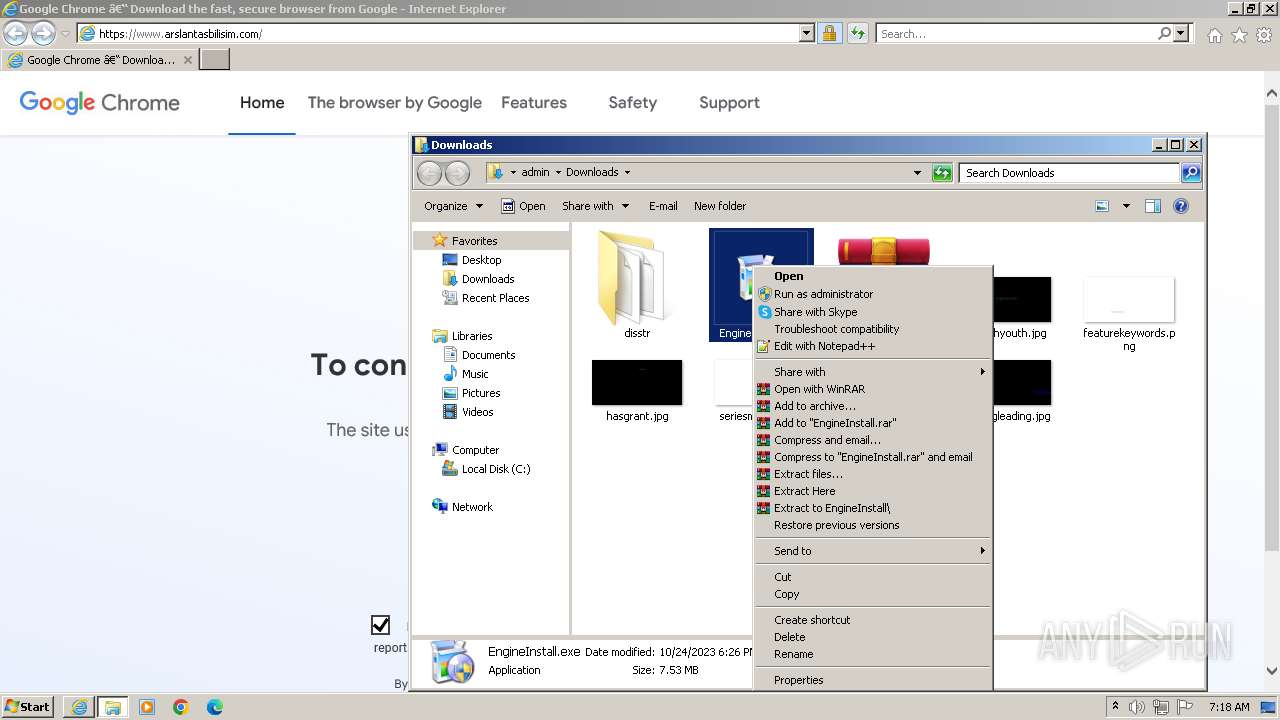
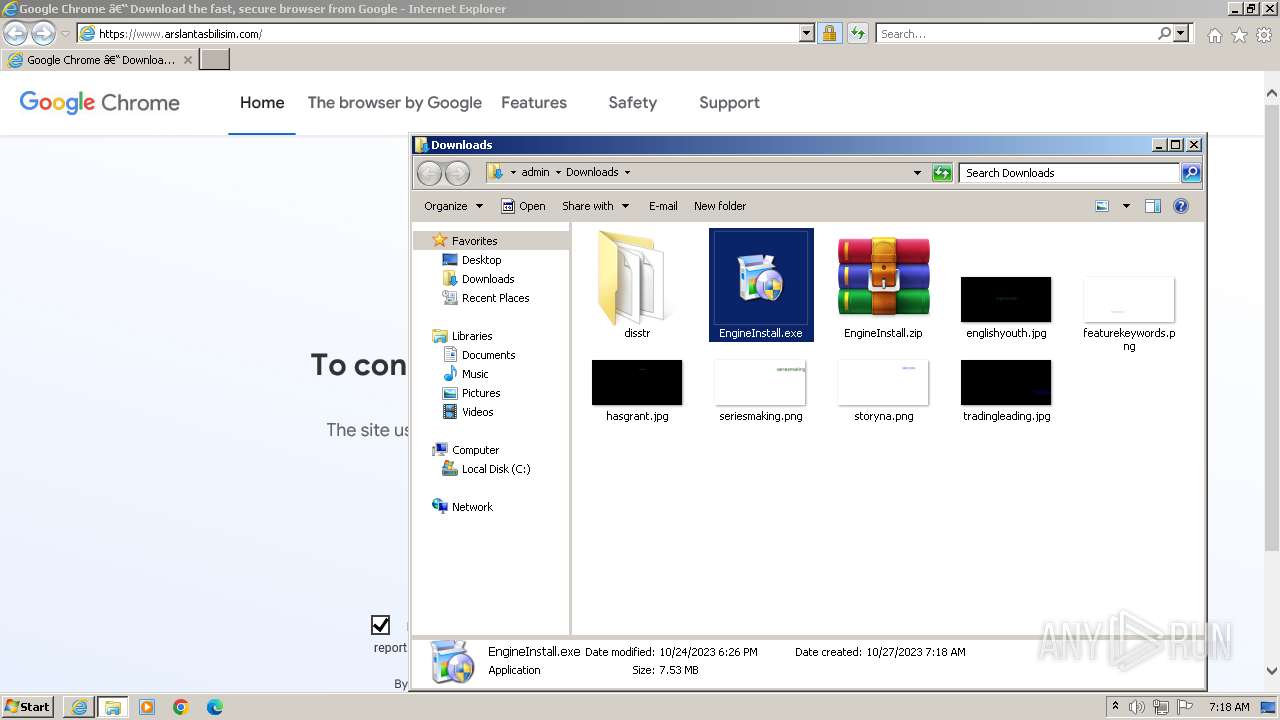
Manual execution by a user
- EngineInstall.exe (PID: 3396)
- WinRAR.exe (PID: 4036)
Checks supported languages
- EngineInstall.exe (PID: 3396)
- javaw.exe (PID: 2484)
Reads the machine GUID from the registry
- javaw.exe (PID: 2484)
Create files in a temporary directory
- javaw.exe (PID: 2484)
Reads the computer name
- javaw.exe (PID: 2484)
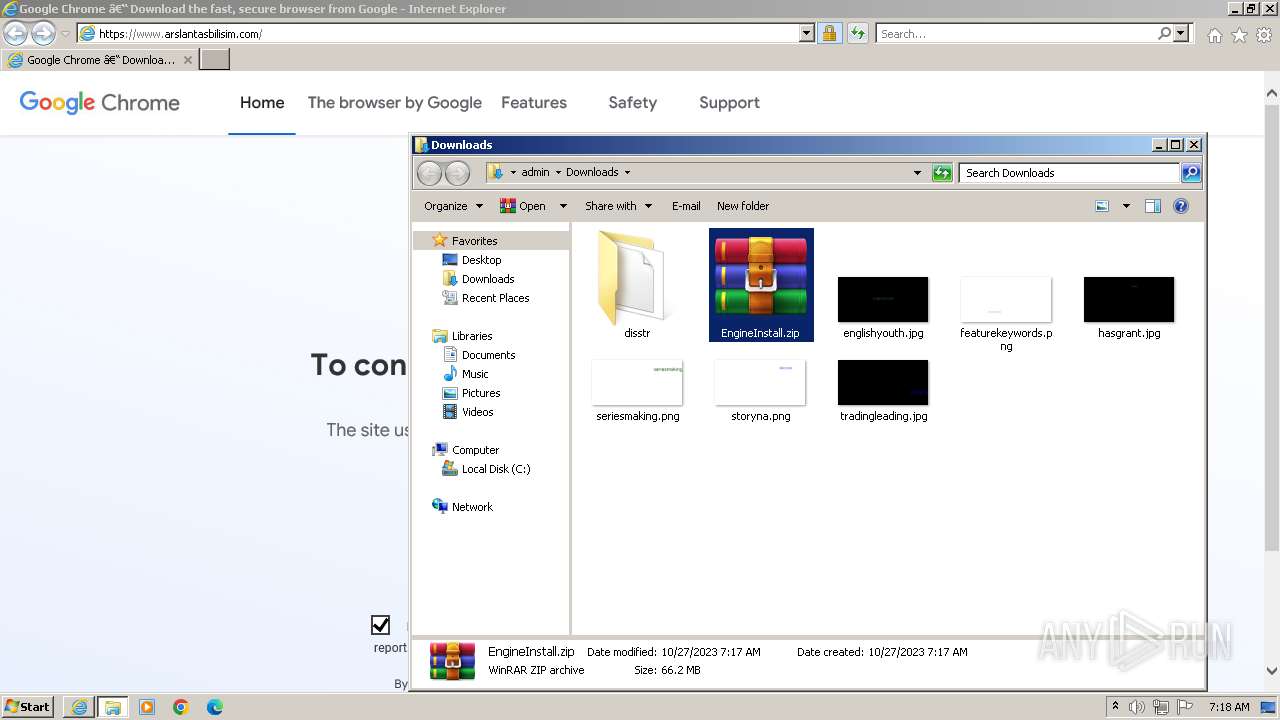
Drops the executable file immediately after the start
- WinRAR.exe (PID: 4036)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
50
Monitored processes
8
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1824 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://www.arslantasbilisim.com" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2484 | "C:\Users\admin\Downloads\disstr\bin\javaw.exe" -Dfile.encoding=UTF-8 -classpath "C:\Users\admin\Downloads\EngineInstall.exe" org.develnext.jphp.ext.javafx.FXLauncher | C:\Users\admin\Downloads\disstr\bin\javaw.exe | EngineInstall.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: HIGH Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.1010.13 Modules
| |||||||||||||||
| 2744 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe6_ Global\UsGthrCtrlFltPipeMssGthrPipe6 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7601.24542 (win7sp1_ldr_escrow.191209-2211) Modules
| |||||||||||||||
| 3120 | C:\Windows\system32\cmd.exe /c C:\Users\admin\AppData\Local\Temp\aa2cd1e551208546ccb3bbfb24440ab1.bat | C:\Windows\System32\cmd.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3396 | "C:\Users\admin\Downloads\EngineInstall.exe" | C:\Users\admin\Downloads\EngineInstall.exe | explorer.exe | ||||||||||||
User: admin Company: Sibly Integrity Level: HIGH Description: No matter your industry or goal, better information means be Exit code: 0 Version: 3.17.10.8 Modules
| |||||||||||||||
| 3808 | powershell -inputformat none -outputformat none -NonInteractive -ExecutionPolicy Bypass -Command Add-MpPreference -ExclusionPath 'C:\' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3996 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1824 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
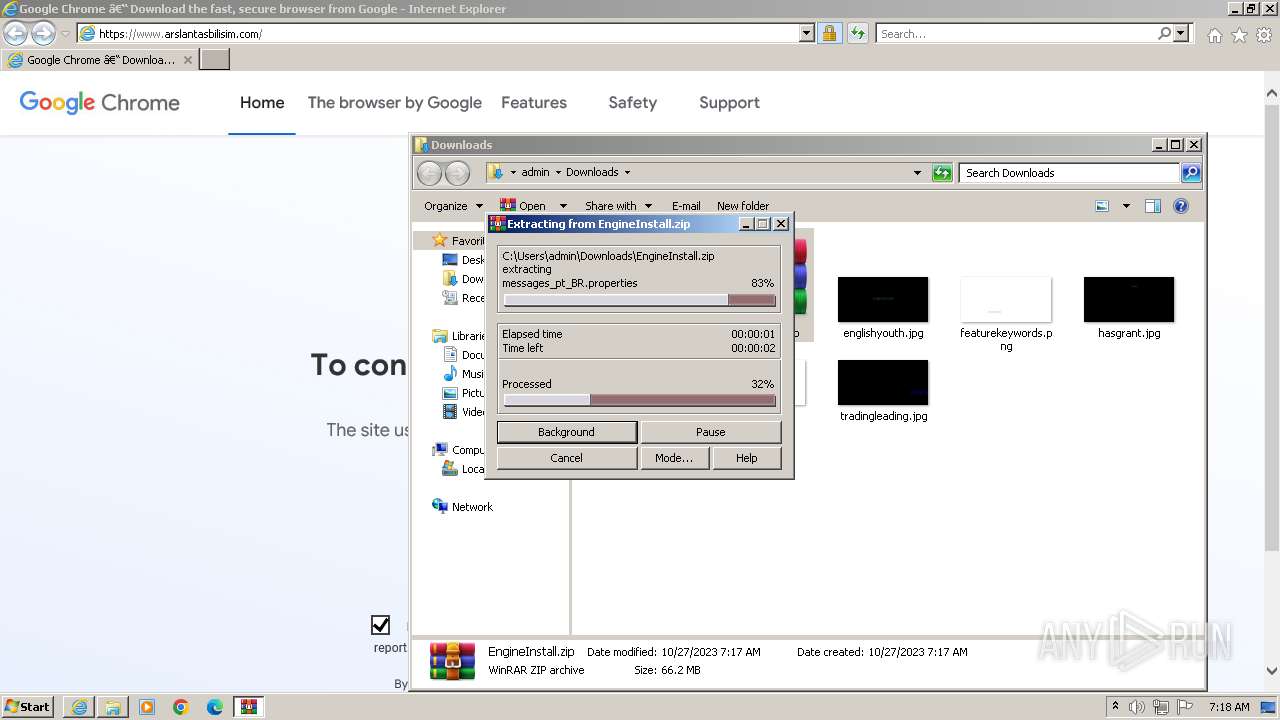
| 4036 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Downloads\EngineInstall.zip" C:\Users\admin\Downloads\ | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
Total events
22 979
Read events
22 843
Write events
132
Delete events
4
Modification events
| (PID) Process: | (1824) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (1824) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (1824) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (1824) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1824) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1824) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1824) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1824) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1824) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1824) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
111
Suspicious files
82
Text files
97
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3996 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:1BFE591A4FE3D91B03CDF26EAACD8F89 | SHA256:9CF94355051BF0F4A45724CA20D1CC02F76371B963AB7D1E38BD8997737B13D8 | |||
| 3996 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabB219.tmp | compressed | |
MD5:F3441B8572AAE8801C04F3060B550443 | SHA256:6720349E7D82EE0A8E73920D3C2B7CB2912D9FCF2EDB6FD98F2F12820158B0BF | |||
| 3996 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarB21A.tmp | binary | |
MD5:9441737383D21192400ECA82FDA910EC | SHA256:BC3A6E84E41FAEB57E7C21AA3B60C2A64777107009727C5B7C0ED8FE658909E5 | |||
| 3996 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\2E815A3599B12A41F53A175671B9F3C7 | binary | |
MD5:9D5253896804575C292DCA244C79AE65 | SHA256:FB289908B36842E30E235DBFD3312AF4EAB672C9DE381C6EF8B9585693551553 | |||
| 3996 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\2E815A3599B12A41F53A175671B9F3C7 | binary | |
MD5:9523E64A03EE9395995428BE42585A5C | SHA256:6F6ADDC6D10B359E137671413064BBA9F067A5CD01A6BD9E8C19E9773F8DB61D | |||
| 3996 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabB217.tmp | compressed | |
MD5:F3441B8572AAE8801C04F3060B550443 | SHA256:6720349E7D82EE0A8E73920D3C2B7CB2912D9FCF2EDB6FD98F2F12820158B0BF | |||
| 3996 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:F3441B8572AAE8801C04F3060B550443 | SHA256:6720349E7D82EE0A8E73920D3C2B7CB2912D9FCF2EDB6FD98F2F12820158B0BF | |||
| 3996 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\N4JTK60B.htm | html | |
MD5:8AA872788F1E825EC6E4EBC3760263E3 | SHA256:D9EC51A3AB80F04F8B5D38D23B319DA5AE2E24F2A9F91C59119CD0894BEC786E | |||
| 3996 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:35FDB8D67C42478EF6A701AC7CAC6651 | SHA256:7AB1257A16FC004F31C36CC7762836AEC3B4712B383AEE58FD53C66A8F53E15C | |||
| 3996 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:C96D86BEB79598092D20FA20E43F5C74 | SHA256:66729426286CA9192828304847C06677D28F0B63EA18D8F562941F4810F669EC | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
20
TCP/UDP connections
47
DNS requests
26
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3996 | iexplore.exe | GET | 200 | 142.250.184.227:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEGAy%2Fdiu84vFCW7%2FIayIdNI%3D | unknown | binary | 471 b | unknown |
3996 | iexplore.exe | GET | 200 | 142.250.184.227:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCED0DQO7sPXWsCXu6cFHQzsU%3D | unknown | binary | 471 b | unknown |
3996 | iexplore.exe | GET | 200 | 142.250.184.227:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDXjiTYwV9zDBJXr%2BzP1lEY | unknown | binary | 472 b | unknown |
3996 | iexplore.exe | GET | 200 | 67.26.73.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?f96a15a63697bdc6 | unknown | compressed | 4.66 Kb | unknown |
3996 | iexplore.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTJQc3Tq6hsExhem%2B5NMZOft299pgQU%2FhmImZNISNLCpWcVlV81ATGOc4sCEGLud9uAl2TcC4tgy7bW3Bg%3D | unknown | binary | 282 b | unknown |
3996 | iexplore.exe | GET | 200 | 67.26.73.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?44b7f016ec3320f4 | unknown | compressed | 4.66 Kb | unknown |
3996 | iexplore.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEBblhnjgcJQ5S9%2FbTvymO98%3D | unknown | binary | 1.42 Kb | unknown |
1824 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAqvpsXKY8RRQeo74ffHUxc%3D | unknown | binary | 471 b | unknown |
3996 | iexplore.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.comodoca.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTrJdiQ%2Ficg9B19asFe73bPYs%2BreAQUdXGnGUgZvJ2d6kFH35TESHeZ03kCEQCkR3oluViGYvxpqmNI5DO5 | unknown | binary | 976 b | unknown |
1824 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | binary | 471 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3996 | iexplore.exe | 67.26.73.254:80 | ctldl.windowsupdate.com | LEVEL3 | US | unknown |
2656 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3996 | iexplore.exe | 23.212.210.158:80 | x1.c.lencr.org | AKAMAI-AS | AU | unknown |
3996 | iexplore.exe | 184.24.77.48:80 | r3.o.lencr.org | Akamai International B.V. | DE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3996 | iexplore.exe | 109.232.216.235:443 | — | Aerotek Bilisim Sanayi ve Ticaret AS | TR | unknown |
3996 | iexplore.exe | 172.217.18.10:443 | fonts.googleapis.com | GOOGLE | US | whitelisted |
3996 | iexplore.exe | 142.250.184.196:443 | www.google.com | GOOGLE | US | whitelisted |
3996 | iexplore.exe | 142.250.184.227:80 | ocsp.pki.goog | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
r3.o.lencr.org |
| shared |
fonts.googleapis.com |
| whitelisted |
www.google.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
www.google-analytics.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.google.comhttps |
| unknown |