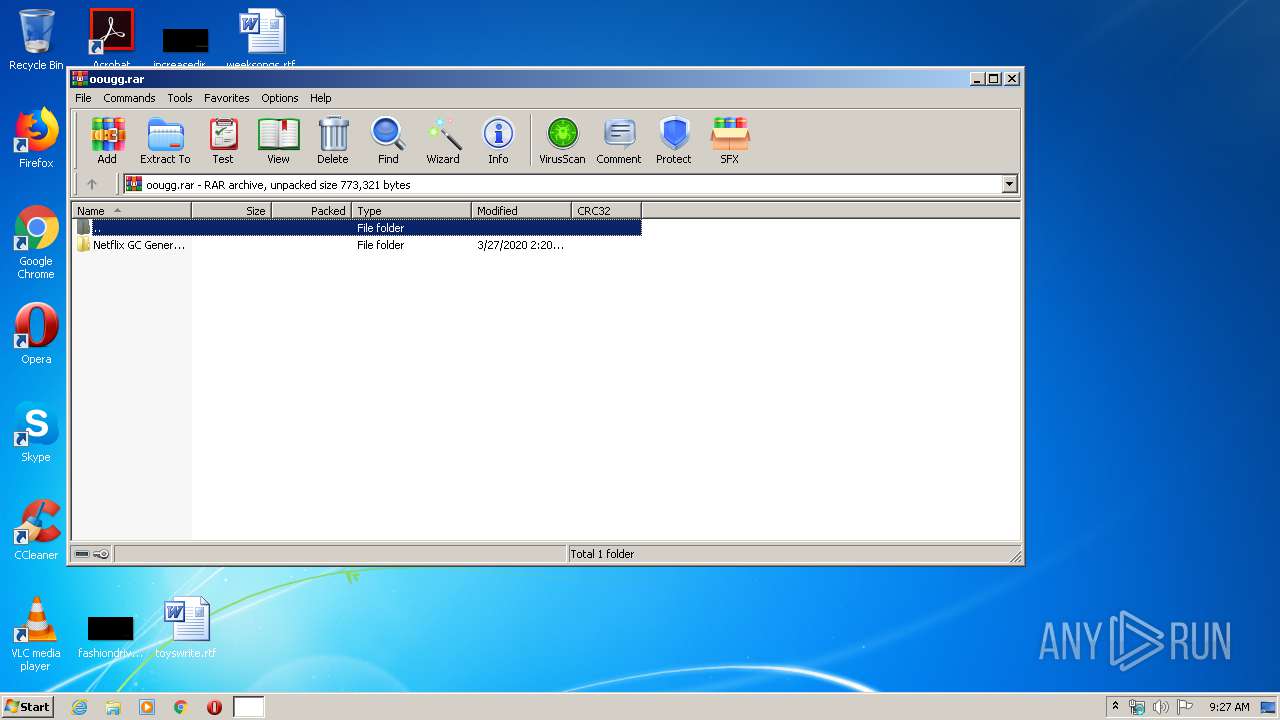
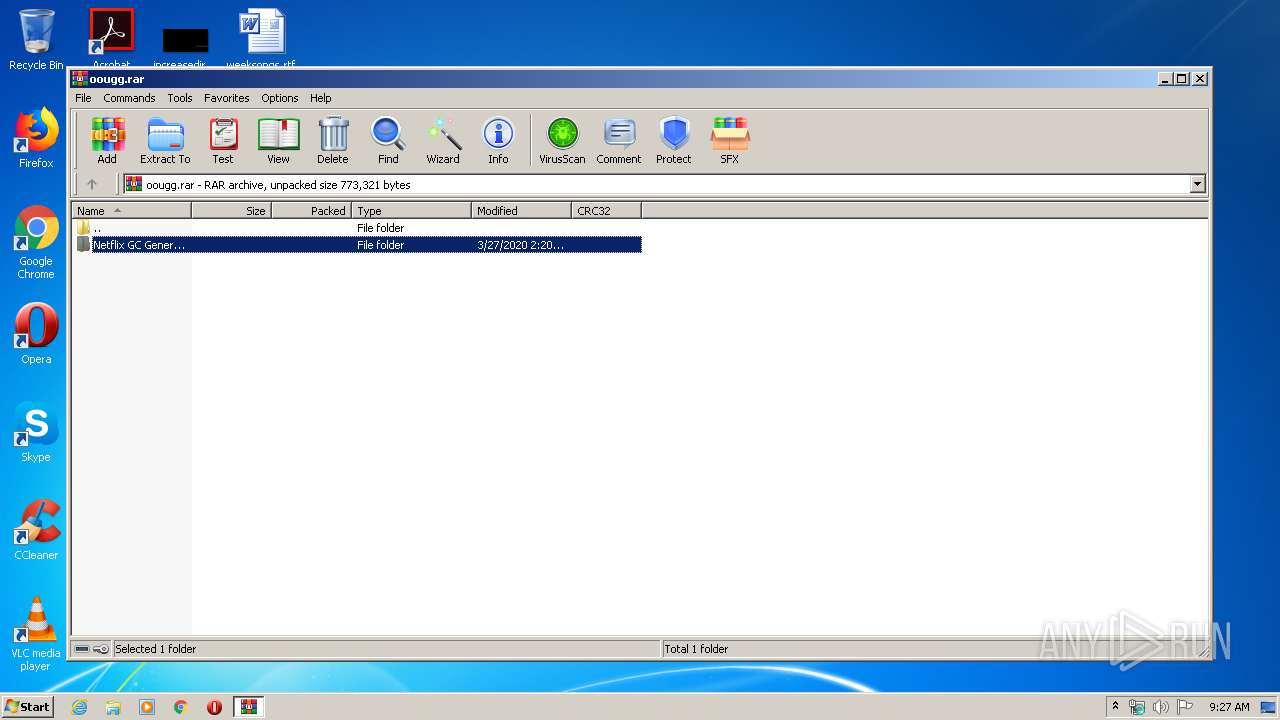
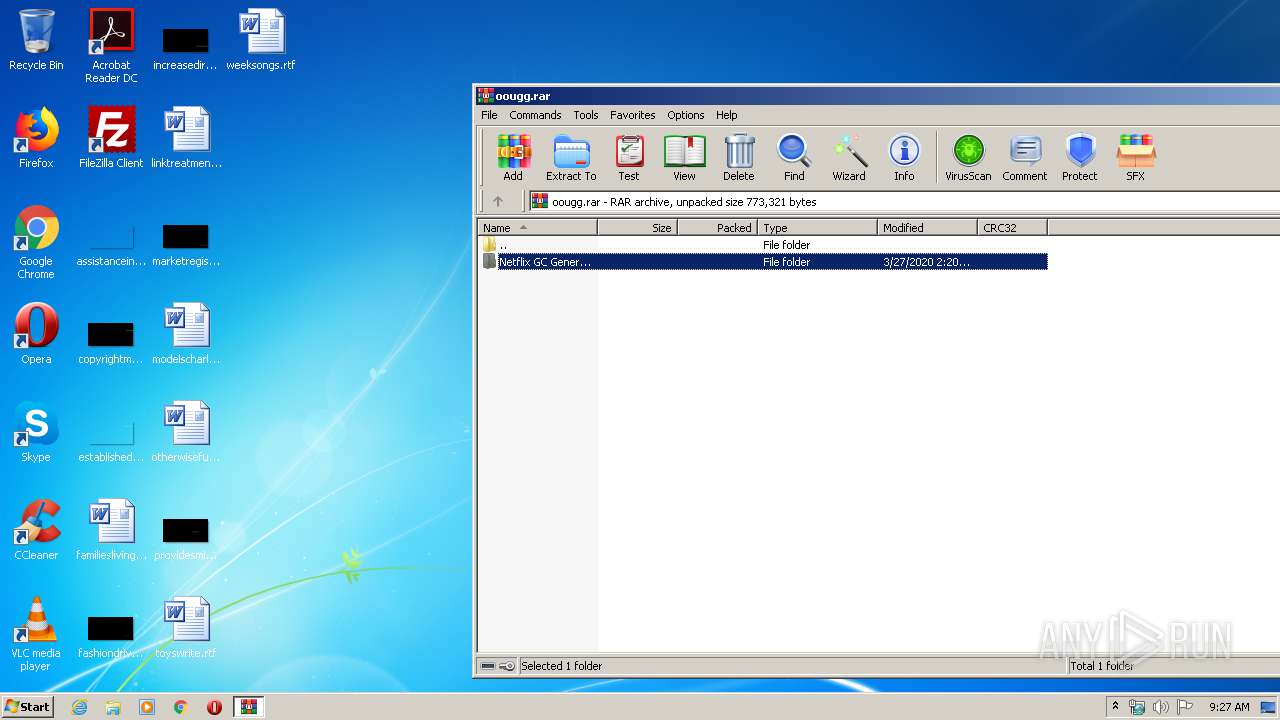
| File name: | oougg.rar |
| Full analysis: | https://app.any.run/tasks/ea84d56a-b369-40d6-952b-0dfecd555081 |
| Verdict: | Malicious activity |
| Analysis date: | March 31, 2020, 08:27:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 02AB0F0C4F4A87E1C5ED3122FB99C1AA |
| SHA1: | 369E9504540C227EF6AD51767861308597E261D5 |
| SHA256: | 2C9E35F4FB54A8670807DE6C7EDACA60F5FA213BEF94158AD12D54682631E360 |
| SSDEEP: | 6144:oaS4MJLD2kRlSMS66Ow4YHaGHQRQt79HtoPdPK5MNVwhkNZCr2AEZhsaajbVoe:9S4y24lSMyOVearmtd0dy5Y9N423hs1L |
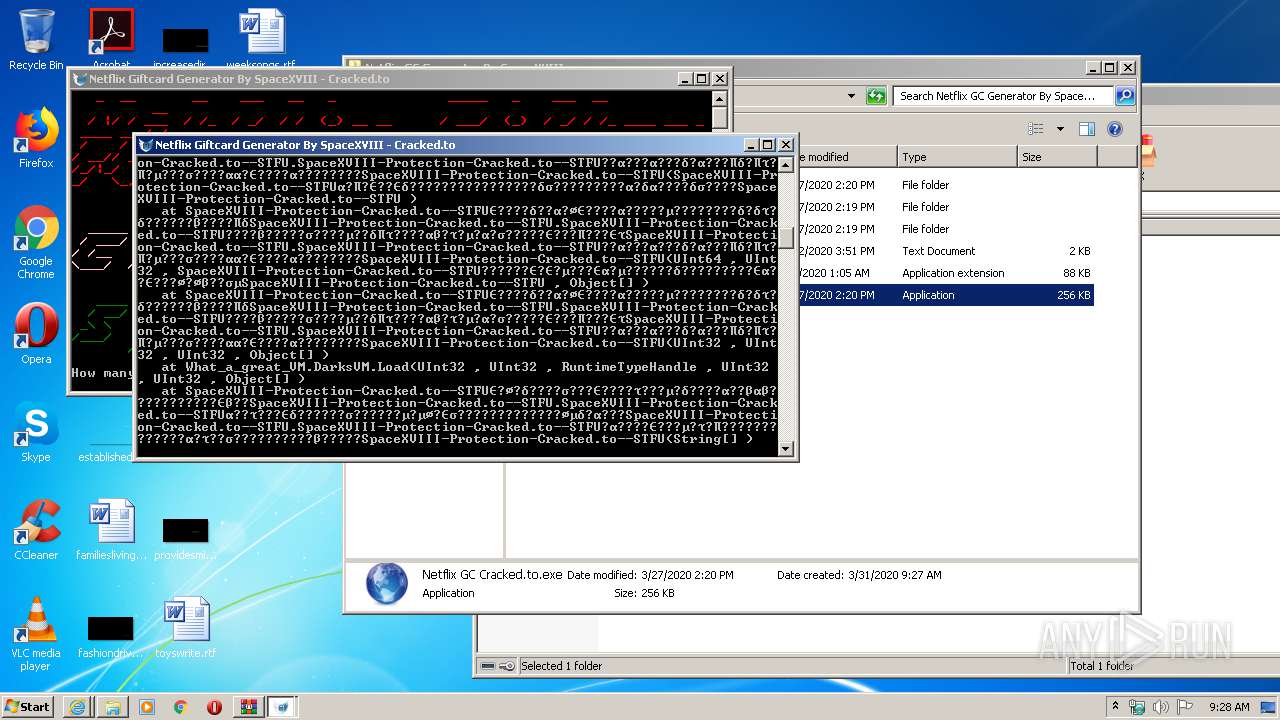
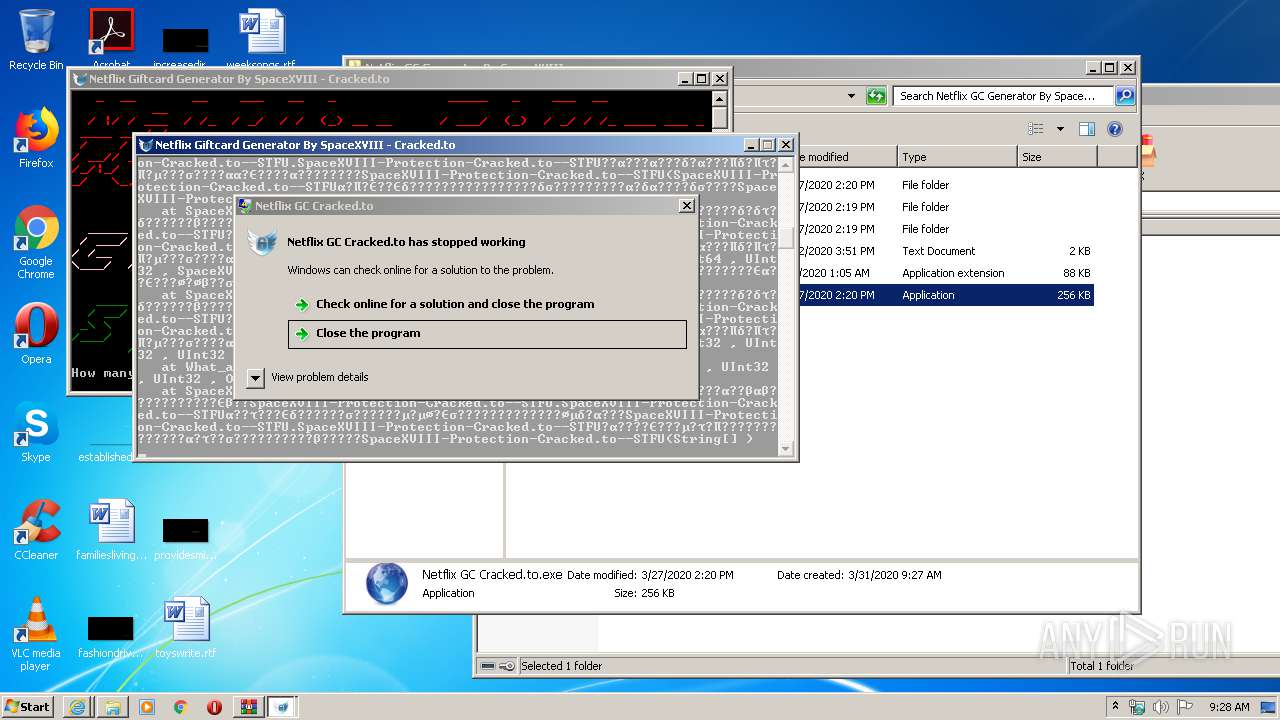
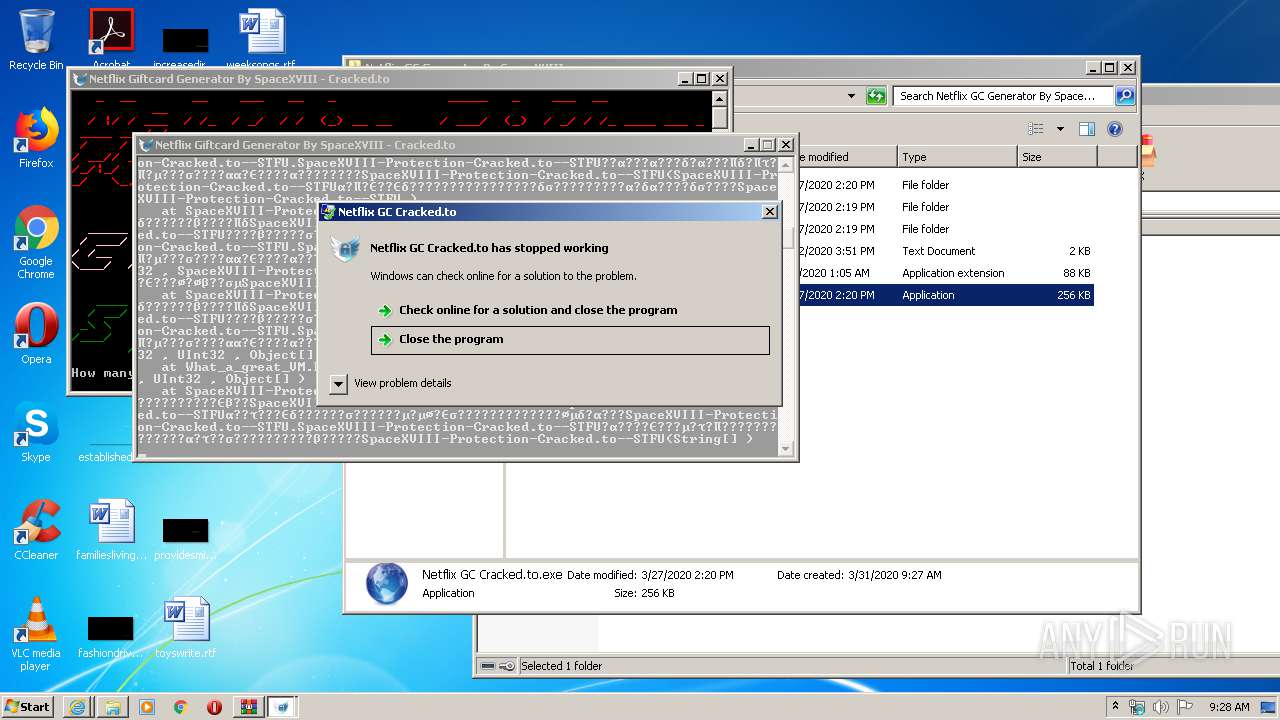
MALICIOUS
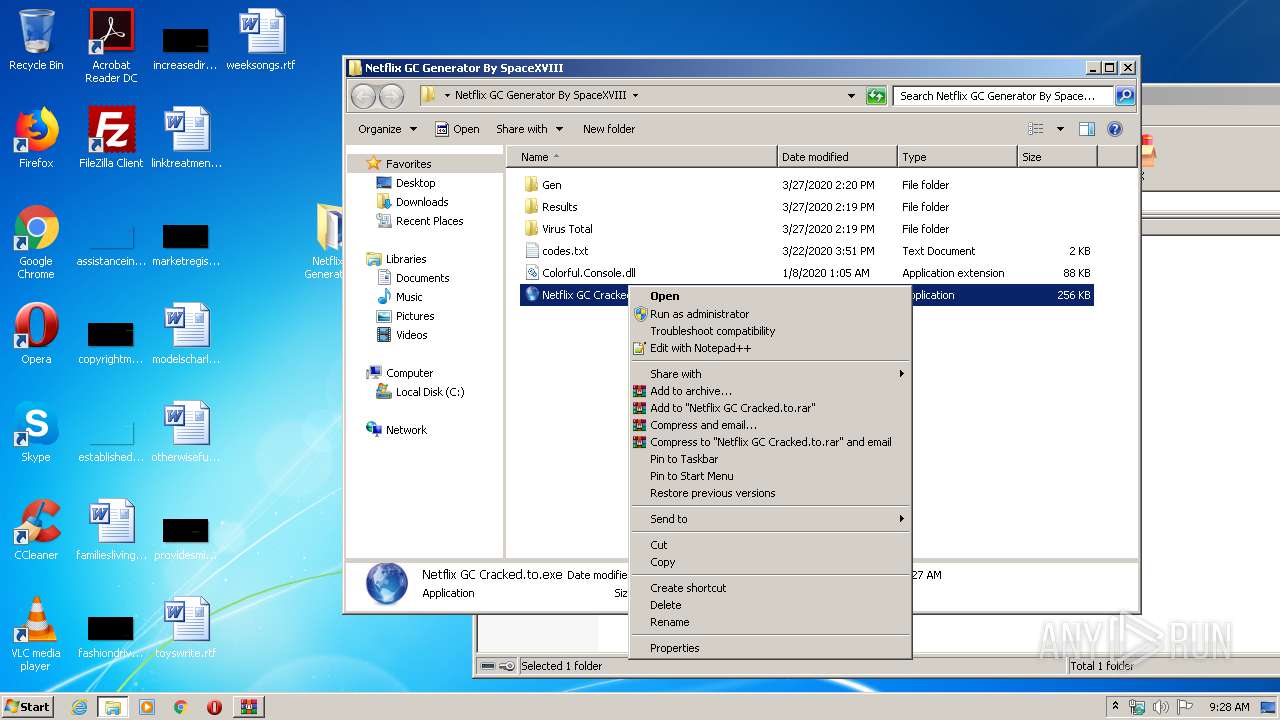
Writes to a start menu file
- Netflix GC Cracked.to.exe (PID: 2056)
- Netflix GC Cracked.to.exe (PID: 2384)
- Netflix GC Cracked.to.exe (PID: 1140)
Application was dropped or rewritten from another process
- Host del servicio Monitor.exe (PID: 1888)
- Microsoft Windows Protocol Services Host.exe (PID: 2884)
- Microsoft Windows Protocol Services Host.exe (PID: 3976)
- Microsoft Windows Protocol Services Host.exe (PID: 1084)
SUSPICIOUS
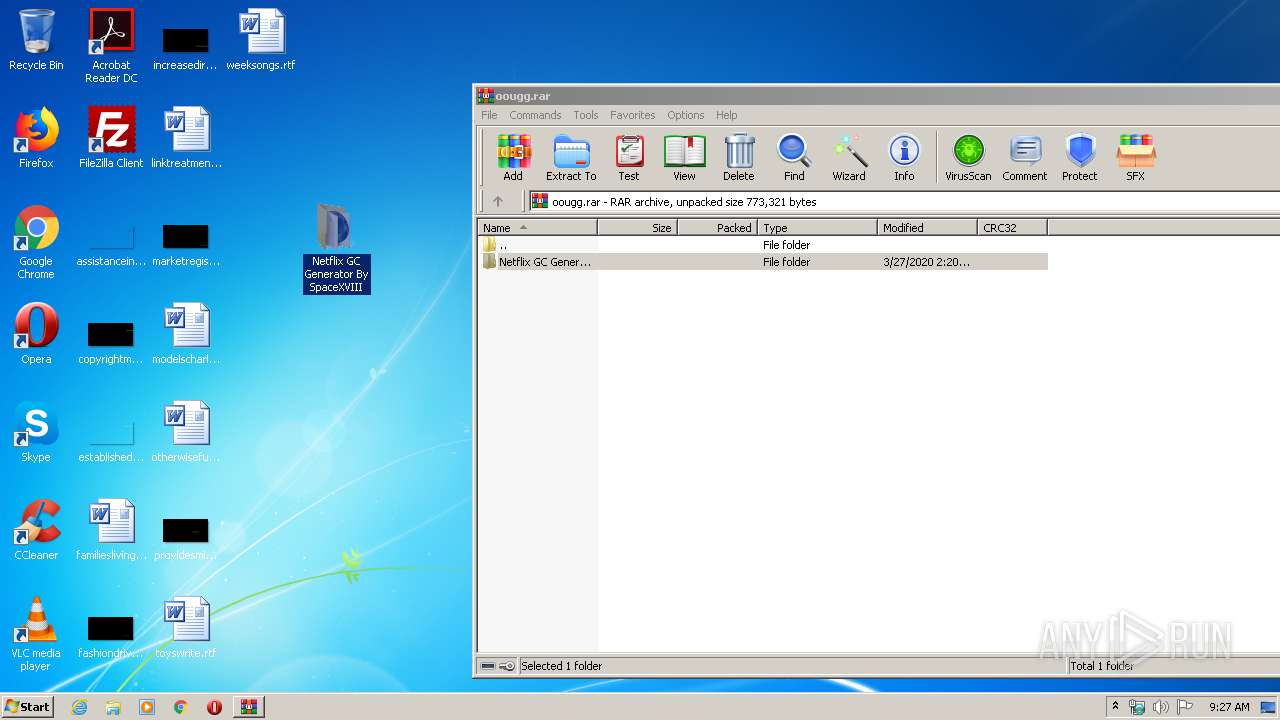
Writes to a desktop.ini file (may be used to cloak folders)
- WinRAR.exe (PID: 3052)
Creates files in the user directory
- Netflix GC Cracked.to.exe (PID: 2056)
Executable content was dropped or overwritten
- Netflix GC Cracked.to.exe (PID: 2384)
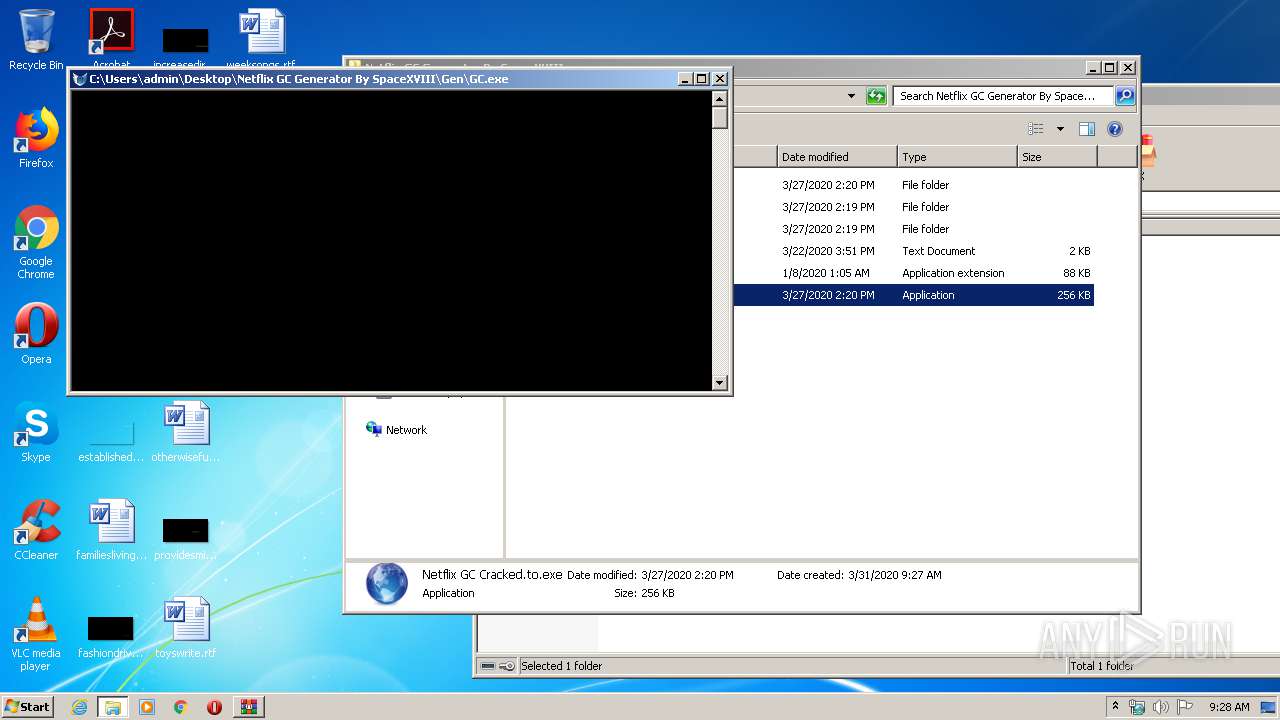
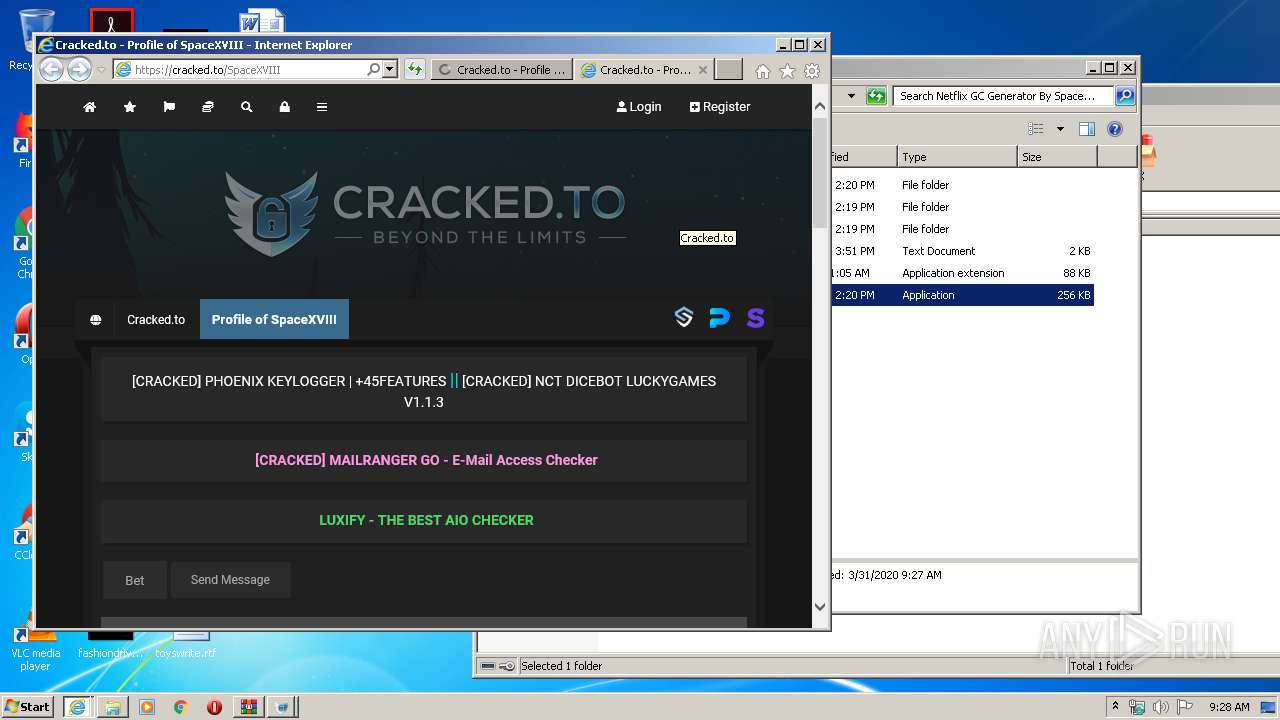
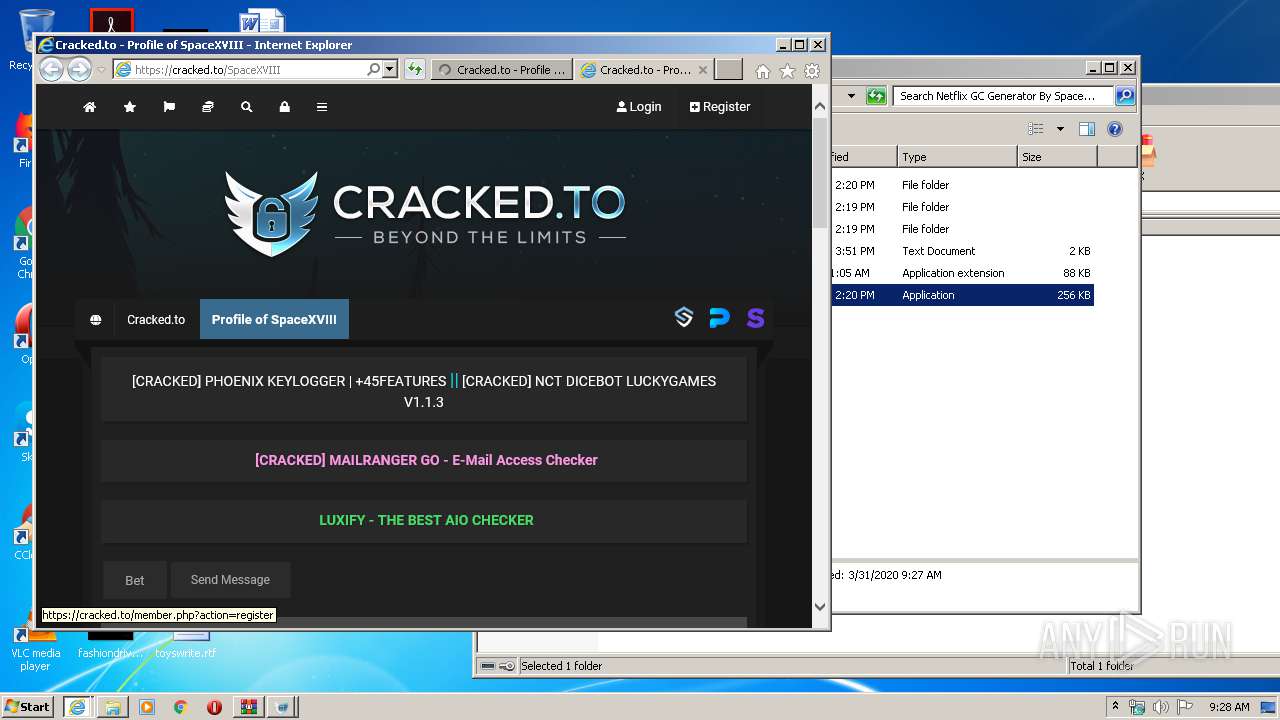
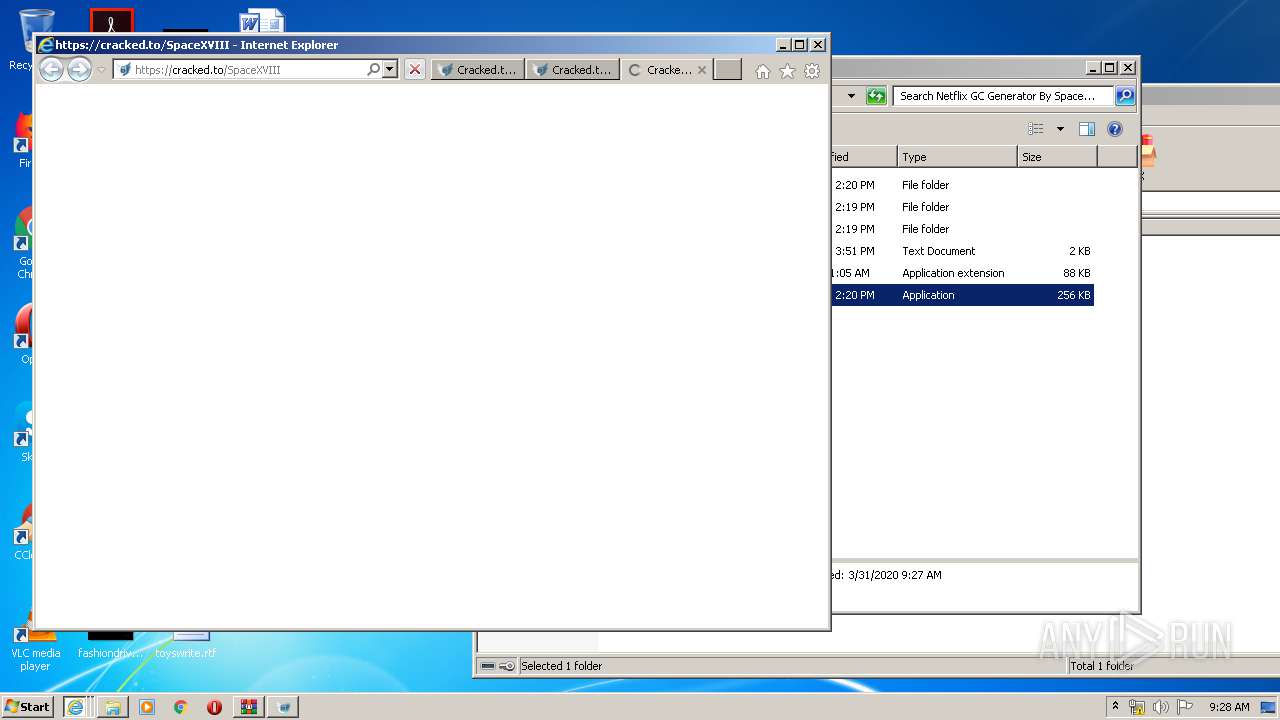
Starts Internet Explorer
- GC.exe (PID: 1720)
Creates files in the Windows directory
- Netflix GC Cracked.to.exe (PID: 2384)
Creates files in the program directory
- Netflix GC Cracked.to.exe (PID: 2384)
INFO
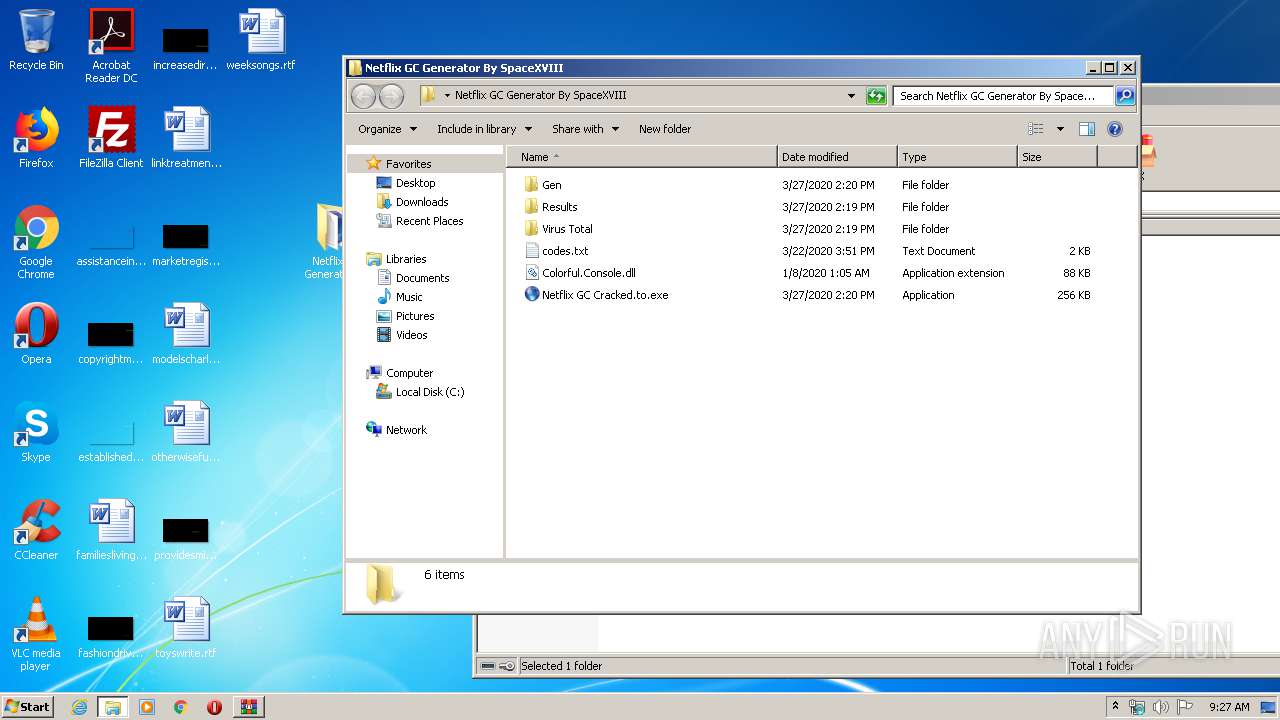
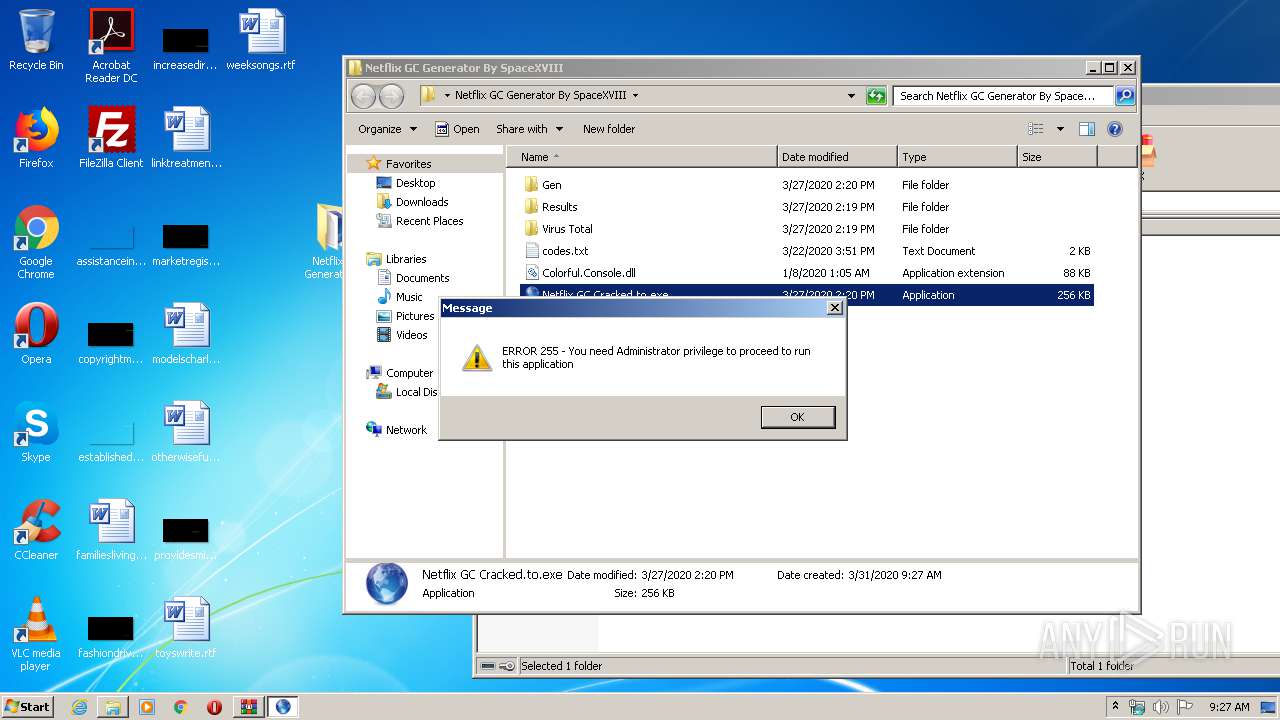
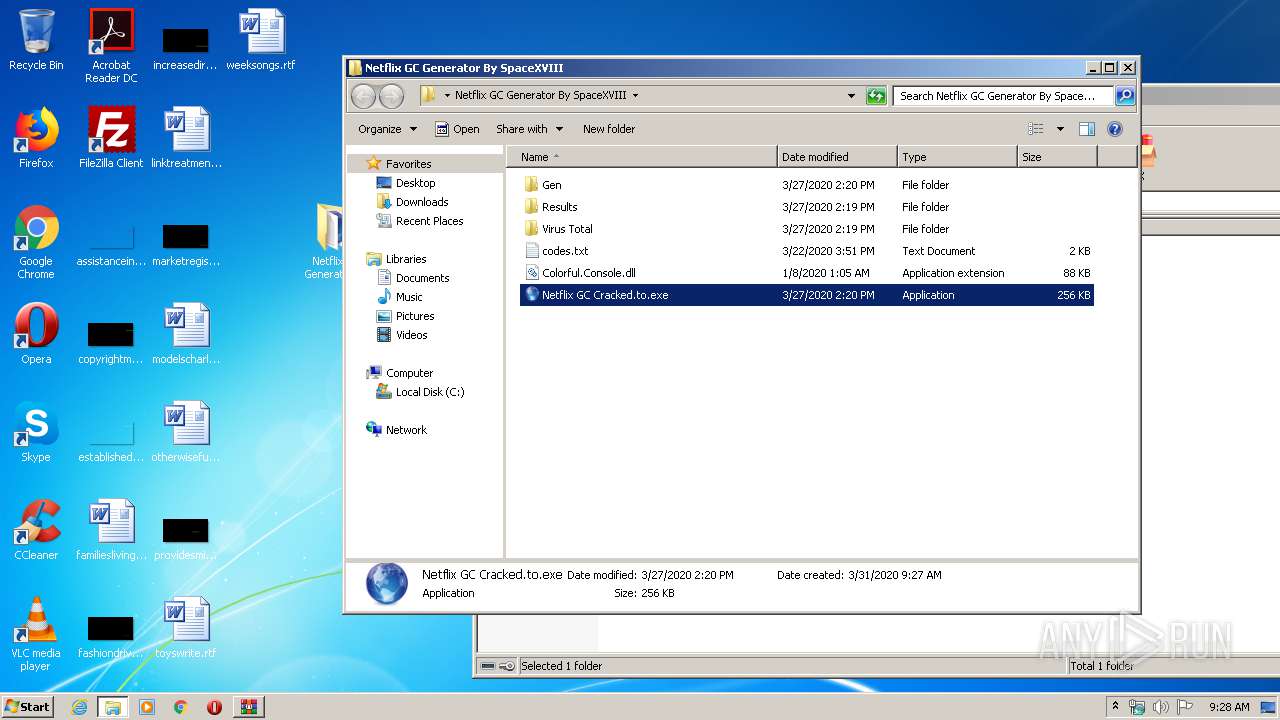
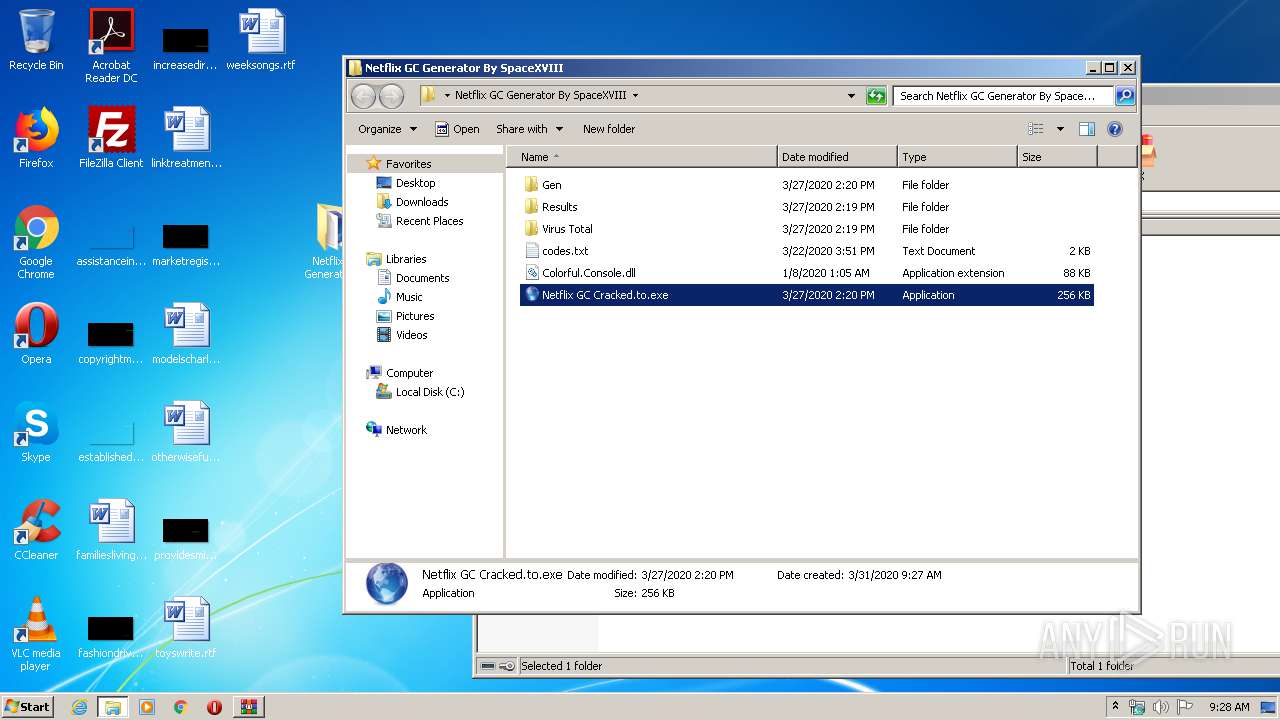
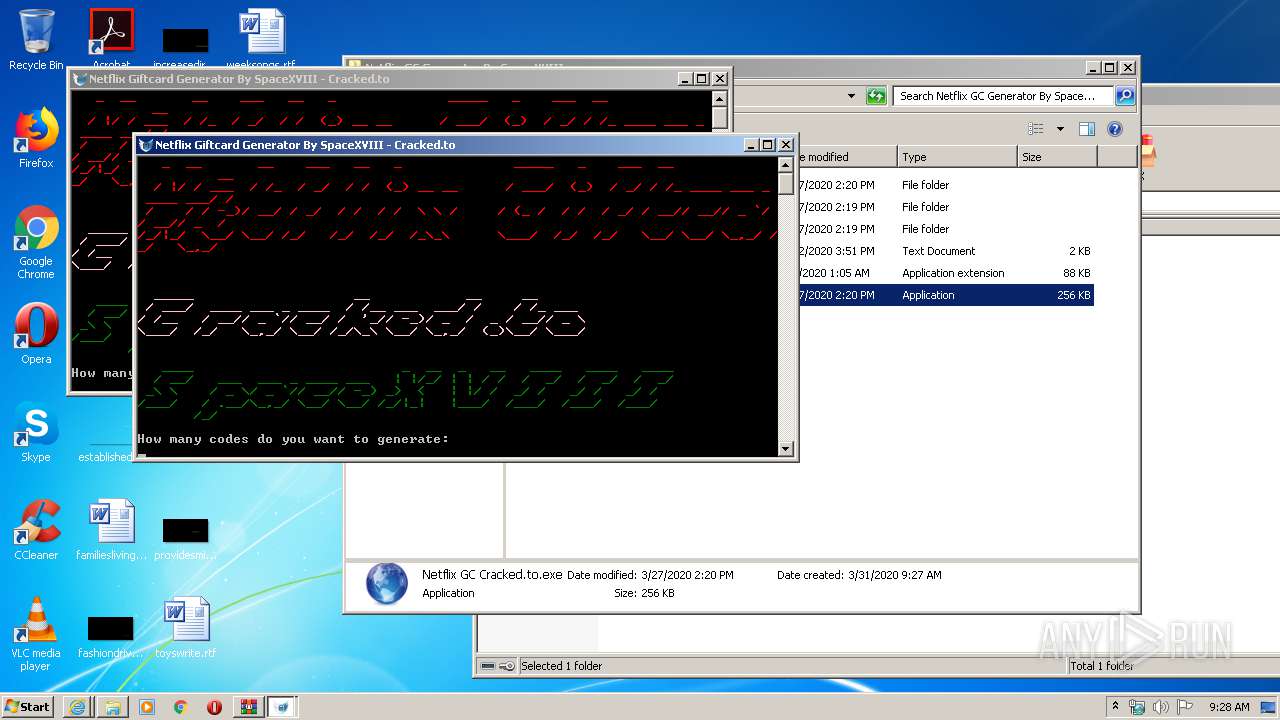
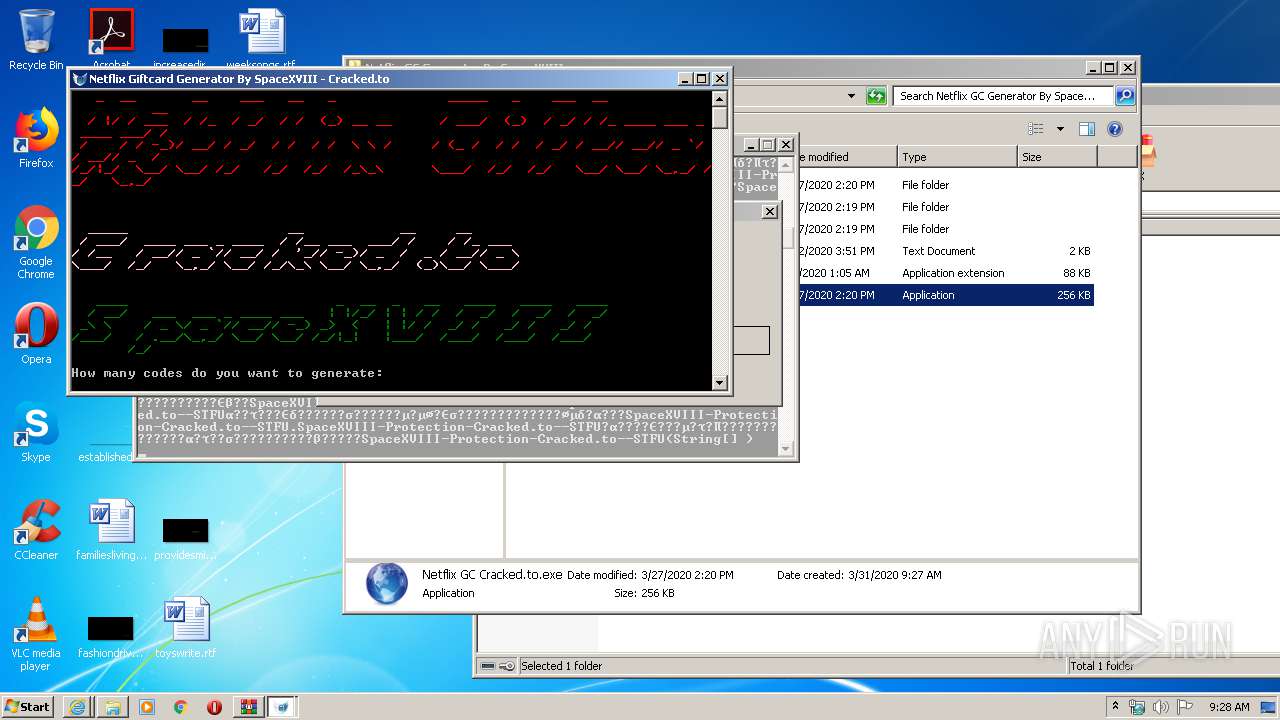
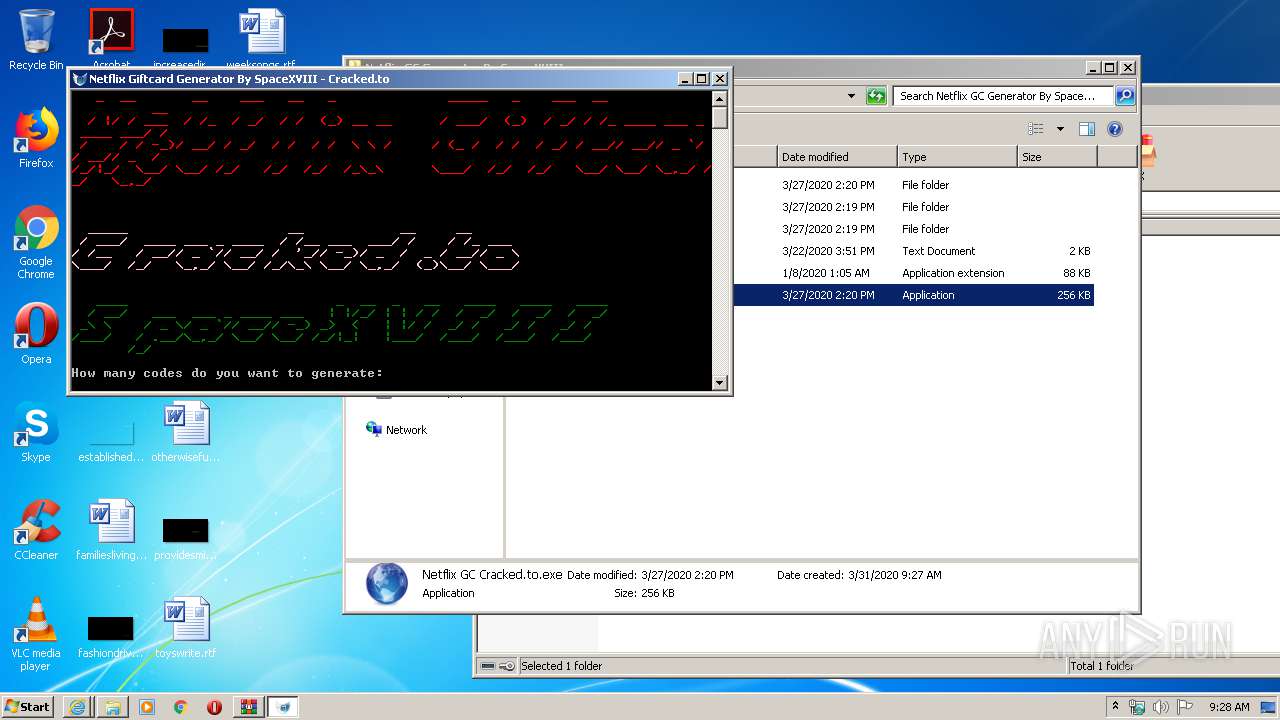
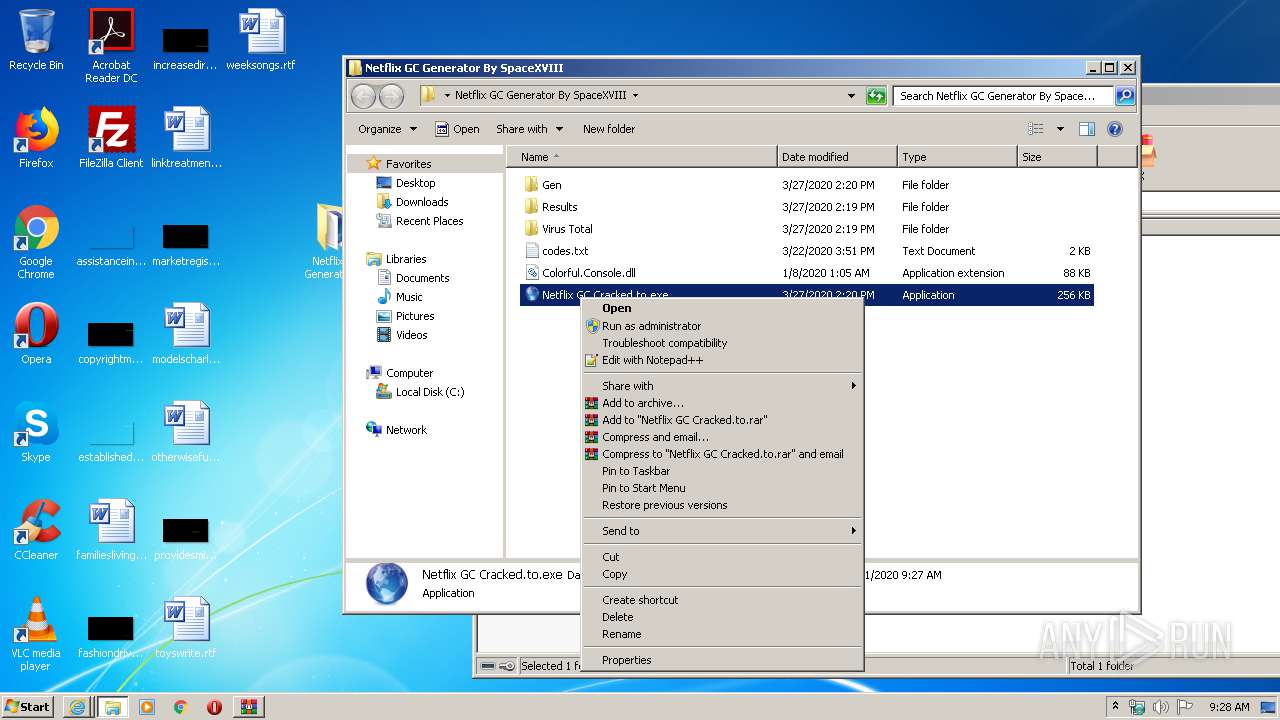
Manual execution by user
- Netflix GC Cracked.to.exe (PID: 2056)
- Netflix GC Cracked.to.exe (PID: 2384)
- Netflix GC Cracked.to.exe (PID: 1140)
Reads Internet Cache Settings
- iexplore.exe (PID: 3528)
- iexplore.exe (PID: 3928)
- iexplore.exe (PID: 2272)
- iexplore.exe (PID: 3460)
Changes internet zones settings
- iexplore.exe (PID: 3528)
Creates files in the user directory
- iexplore.exe (PID: 3928)
- iexplore.exe (PID: 3528)
- iexplore.exe (PID: 2272)
Reads internet explorer settings
- iexplore.exe (PID: 3928)
- iexplore.exe (PID: 2272)
Application launched itself
- iexplore.exe (PID: 3528)
Reads settings of System Certificates
- iexplore.exe (PID: 3528)
- iexplore.exe (PID: 3928)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3528)
Changes settings of System certificates
- iexplore.exe (PID: 3528)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
62
Monitored processes
15
Malicious processes
1
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1084 | "C:\Windows\Program Files (x86)\Microsoft Host Interface\Gen\Microsoft Windows Protocol Services Host.exe" {Arguments If Needed} | C:\Windows\Program Files (x86)\Microsoft Host Interface\Gen\Microsoft Windows Protocol Services Host.exe | — | Netflix GC Cracked.to.exe | |||||||||||
User: admin Integrity Level: HIGH Description: Microsoft Windows Protocol Services Host Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
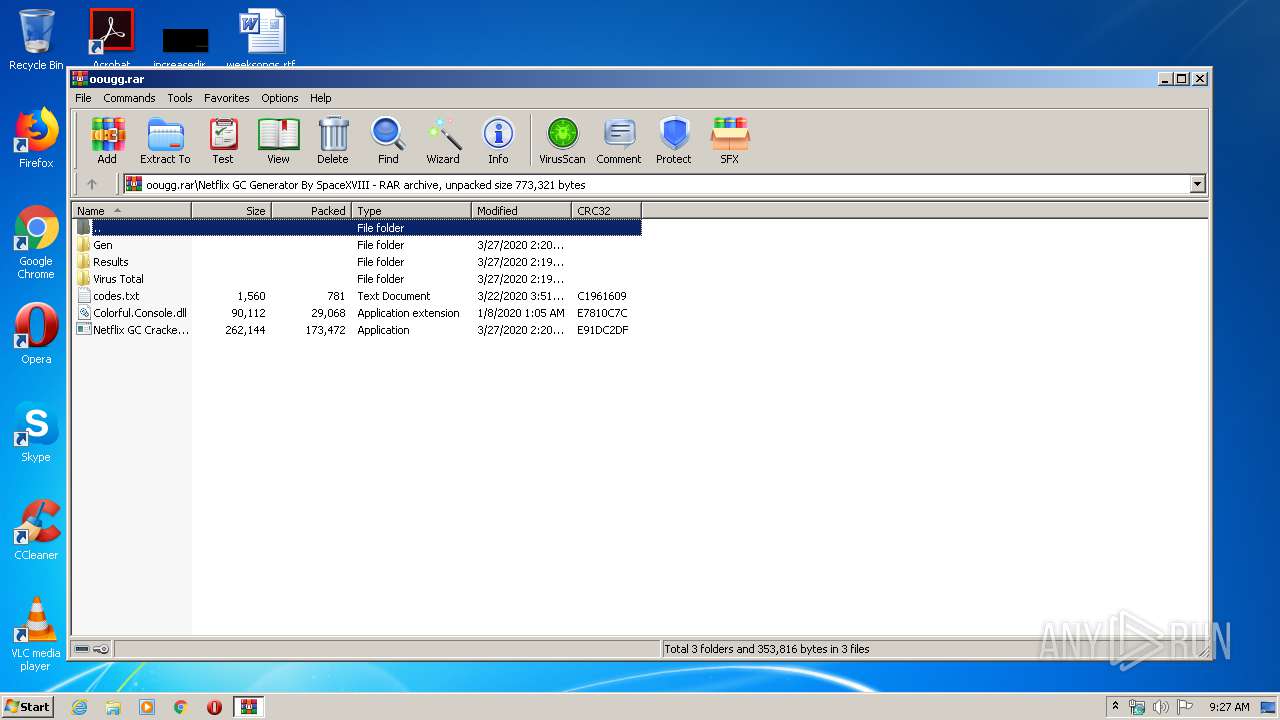
| 1140 | "C:\Users\admin\Desktop\Netflix GC Generator By SpaceXVIII\Netflix GC Cracked.to.exe" | C:\Users\admin\Desktop\Netflix GC Generator By SpaceXVIII\Netflix GC Cracked.to.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: interface Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1720 | "C:\Users\admin\Desktop\Netflix GC Generator By SpaceXVIII\Gen\GC.exe" {Arguments If Needed} | C:\Users\admin\Desktop\Netflix GC Generator By SpaceXVIII\Gen\GC.exe | Netflix GC Cracked.to.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Netflix GC Cracked.to Exit code: 3762504530 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1888 | "C:\Windows\Program Files (x86)\Microsoft Host Interface\Gen\Host del servicio Monitor.exe" | C:\Windows\Program Files (x86)\Microsoft Host Interface\Gen\Host del servicio Monitor.exe | — | Microsoft Windows Protocol Services Host.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Microsoft Windows Protocol Monitor Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2056 | "C:\Users\admin\Desktop\Netflix GC Generator By SpaceXVIII\Netflix GC Cracked.to.exe" | C:\Users\admin\Desktop\Netflix GC Generator By SpaceXVIII\Netflix GC Cracked.to.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: interface Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2272 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3528 CREDAT:4134157 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2384 | "C:\Users\admin\Desktop\Netflix GC Generator By SpaceXVIII\Netflix GC Cracked.to.exe" | C:\Users\admin\Desktop\Netflix GC Generator By SpaceXVIII\Netflix GC Cracked.to.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: interface Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2400 | "C:\Users\admin\Desktop\Netflix GC Generator By SpaceXVIII\Gen\GC.exe" {Arguments If Needed} | C:\Users\admin\Desktop\Netflix GC Generator By SpaceXVIII\Gen\GC.exe | — | Netflix GC Cracked.to.exe | |||||||||||
User: admin Integrity Level: HIGH Description: Netflix GC Cracked.to Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2816 | "C:\Users\admin\Desktop\Netflix GC Generator By SpaceXVIII\Gen\GC.exe" {Arguments If Needed} | C:\Users\admin\Desktop\Netflix GC Generator By SpaceXVIII\Gen\GC.exe | Netflix GC Cracked.to.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Netflix GC Cracked.to Exit code: 3762504530 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2884 | "C:\Windows\Program Files (x86)\Microsoft Host Interface\Gen\Microsoft Windows Protocol Services Host.exe" {Arguments If Needed} | C:\Windows\Program Files (x86)\Microsoft Host Interface\Gen\Microsoft Windows Protocol Services Host.exe | — | Netflix GC Cracked.to.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Microsoft Windows Protocol Services Host Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
6 011
Read events
1 555
Write events
2 998
Delete events
1 458
Modification events
| (PID) Process: | (3052) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3052) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3052) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3052) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\oougg.rar | |||
| (PID) Process: | (3052) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3052) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3052) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3052) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2056) Netflix GC Cracked.to.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2056) Netflix GC Cracked.to.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
2
Suspicious files
58
Text files
51
Unknown types
34
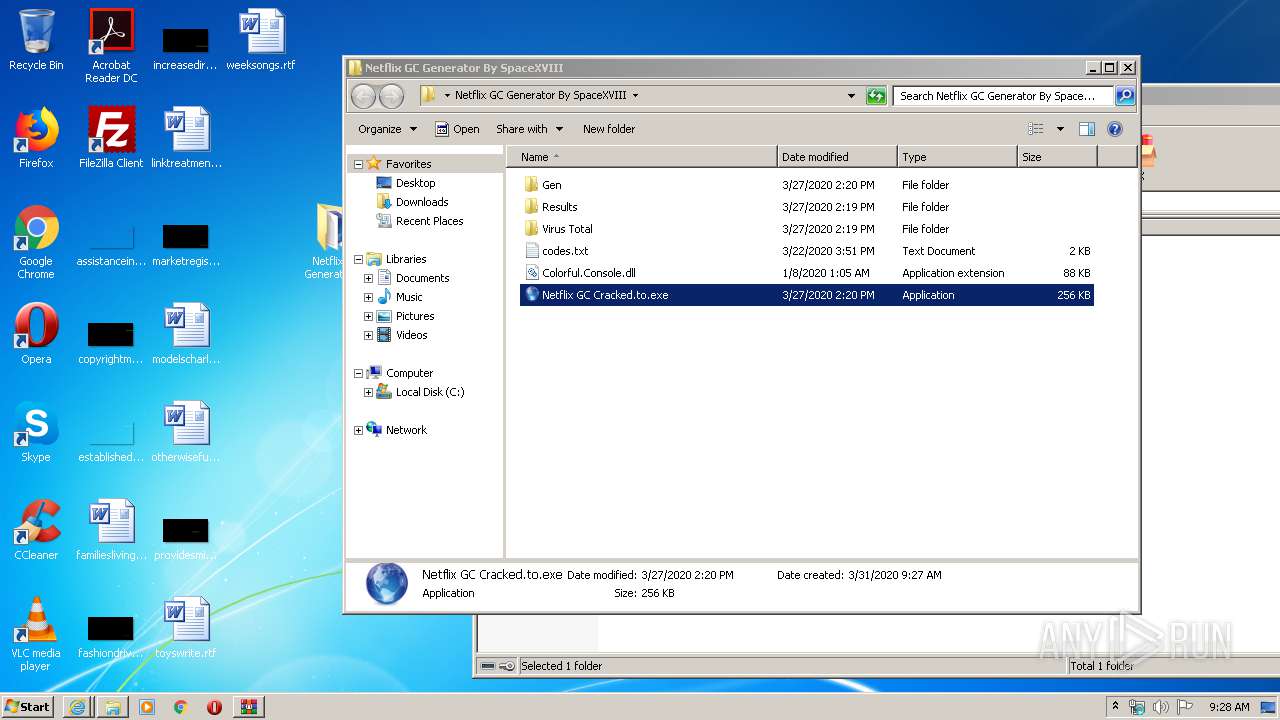
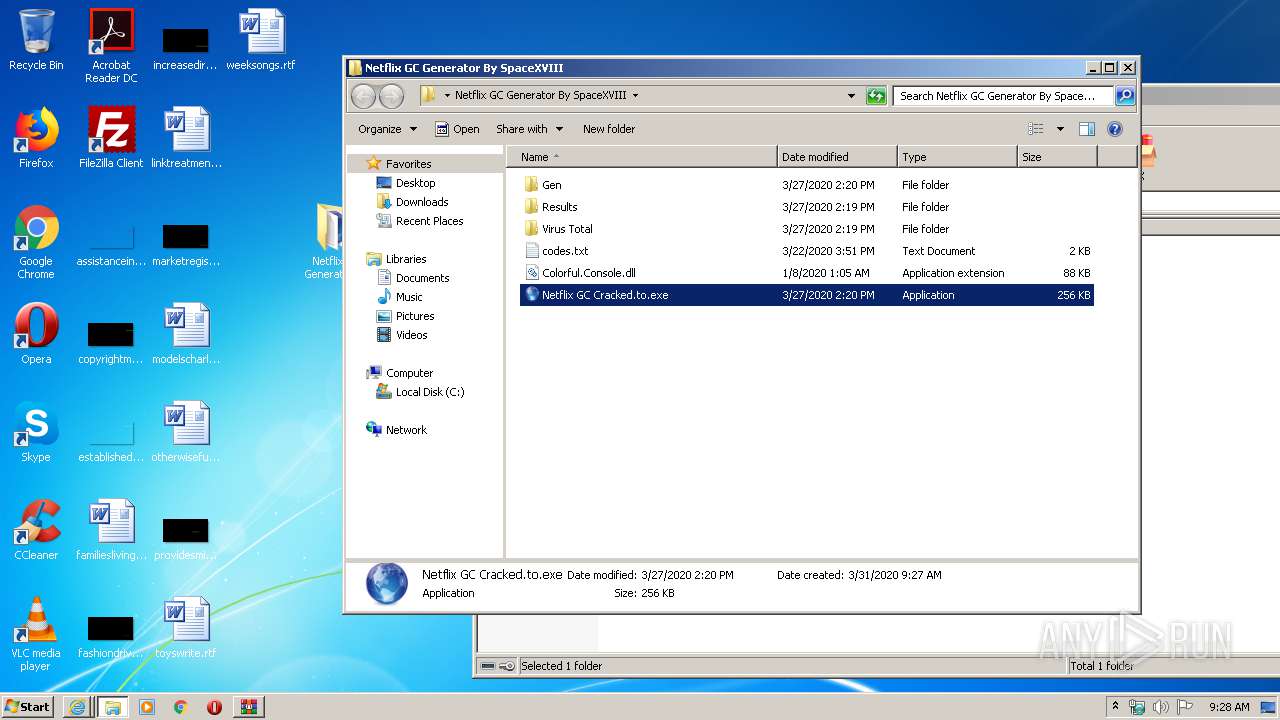
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
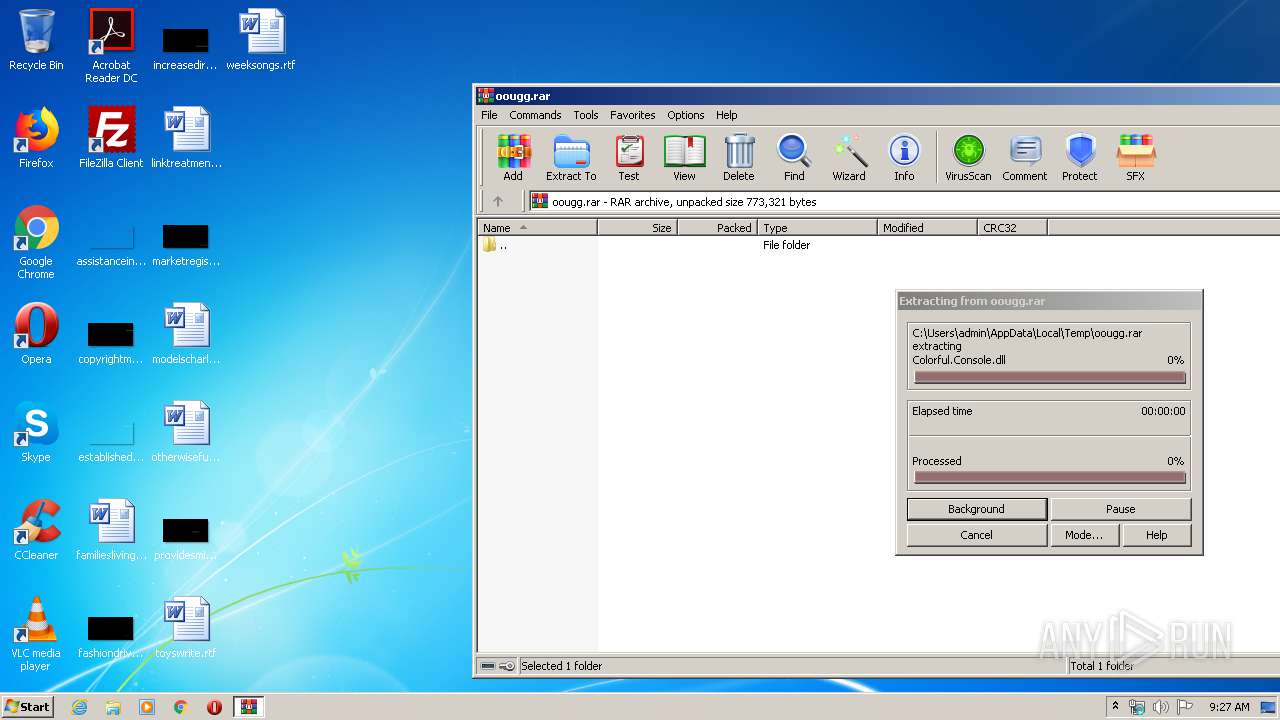
| 3052 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3052.10386\Netflix GC Generator By SpaceXVIII\codes.txt | — | |
MD5:— | SHA256:— | |||
| 3052 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3052.10386\Netflix GC Generator By SpaceXVIII\Colorful.Console.dll | — | |
MD5:— | SHA256:— | |||
| 3052 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3052.10386\Netflix GC Generator By SpaceXVIII\Gen\codes.txt | — | |
MD5:— | SHA256:— | |||
| 3052 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3052.10386\Netflix GC Generator By SpaceXVIII\Gen\Colorful.Console.dll | — | |
MD5:— | SHA256:— | |||
| 3052 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3052.10386\Netflix GC Generator By SpaceXVIII\Gen\GC.exe | — | |
MD5:— | SHA256:— | |||
| 3052 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3052.10386\Netflix GC Generator By SpaceXVIII\Gen\Host del servicio Monitor.exe | — | |
MD5:— | SHA256:— | |||
| 3052 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3052.10386\Netflix GC Generator By SpaceXVIII\Gen\Microsoft Windows Protocol Services Host.exe | — | |
MD5:— | SHA256:— | |||
| 3052 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3052.10386\Netflix GC Generator By SpaceXVIII\Netflix GC Cracked.to.exe | — | |
MD5:— | SHA256:— | |||
| 3052 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3052.10386\Netflix GC Generator By SpaceXVIII\Virus Total\desktop.ini | — | |
MD5:— | SHA256:— | |||
| 3052 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3052.10386\Netflix GC Generator By SpaceXVIII\Virus Total\scan.txt | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
26
TCP/UDP connections
74
DNS requests
22
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3928 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.trust-provider.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCEENSAj%2F6qJAfE5%2Fj9OXBRE4%3D | US | der | 471 b | whitelisted |
3928 | iexplore.exe | GET | 200 | 216.58.208.35:80 | http://ocsp.pki.goog/gts1o1/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDy4NKedukSQwgAAAAAMgpY | US | der | 472 b | whitelisted |
3928 | iexplore.exe | GET | 200 | 216.58.208.35:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
3928 | iexplore.exe | GET | 200 | 216.58.208.35:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
3928 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca4.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrJdiQ%2Ficg9B19asFe73bPYs%2BreAQUdXGnGUgZvJ2d6kFH35TESHeZ03kCEFslzmkHxCZVZtM5DJmpVK0%3D | US | der | 313 b | whitelisted |
3928 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQrBBNpPfHTPX6Jy6BVzyBPnBWMnQQUPnQtH89FdQR%2BP8Cihz5MQ4NRE8YCEAUI1xTz%2FIA59ca8CEavehY%3D | US | der | 280 b | whitelisted |
3928 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca4.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTOpjOEf6LG1z52jqAxwDlTxoaOCgQUQAlhZ%2FC8g3FP3hIILG%2FU1Ct2PZYCEQCNmx6n%2FS%2FCc0UBRhCdwaxd | US | der | 280 b | whitelisted |
3928 | iexplore.exe | GET | 200 | 216.58.208.35:80 | http://ocsp.pki.goog/gts1o1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEFFu4wHRKPokCAAAAAAyCoE%3D | US | der | 471 b | whitelisted |
3928 | iexplore.exe | GET | 200 | 216.58.208.35:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
3928 | iexplore.exe | GET | 200 | 216.58.208.35:80 | http://ocsp.pki.goog/gts1o1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEFFu4wHRKPokCAAAAAAyCoE%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3928 | iexplore.exe | 216.58.208.35:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
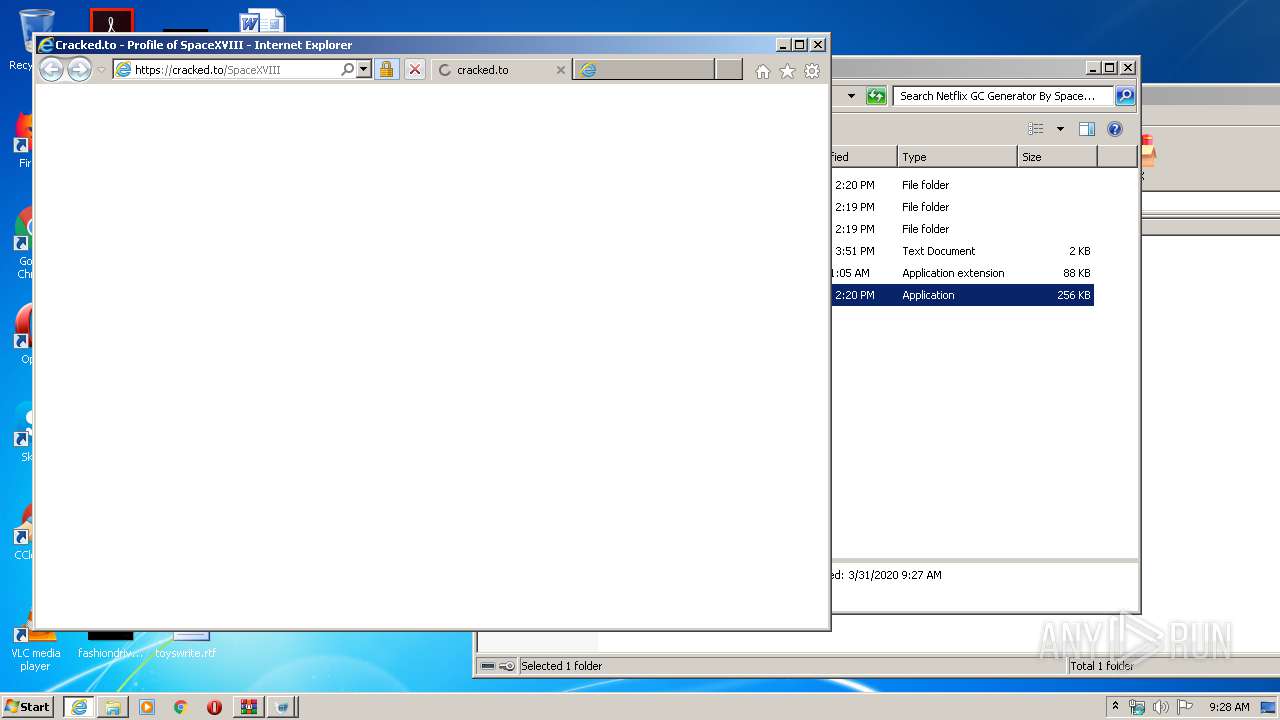
3928 | iexplore.exe | 104.26.7.55:443 | cracked.to | Cloudflare Inc | US | malicious |
3928 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3928 | iexplore.exe | 104.17.64.4:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | unknown |
3928 | iexplore.exe | 172.217.22.74:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3928 | iexplore.exe | 216.58.210.14:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
3928 | iexplore.exe | 64.233.184.156:443 | stats.g.doubleclick.net | Google Inc. | US | whitelisted |
3928 | iexplore.exe | 172.217.22.34:443 | googleads.g.doubleclick.net | Google Inc. | US | whitelisted |
3928 | iexplore.exe | 172.217.22.68:443 | www.google.com | Google Inc. | US | whitelisted |
2272 | iexplore.exe | 172.217.22.35:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cracked.to |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
static.cracked.to |
| suspicious |
fonts.googleapis.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
cache.cracked.to |
| whitelisted |
ocsp.trust-provider.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
ocsp.comodoca4.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |